| File name: | C:\Users\admin\Downloads\easiinvest-qt.exe |
| Full analysis: | https://app.any.run/tasks/eb52e800-ea23-44ce-912d-f9f66e8b89d9 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2021, 22:43:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6AA4E5305A1B711B9A347A9120E7FBB1 |
| SHA1: | ABDA6B9527159CA17CD849DD75C8EAB818D45DA1 |
| SHA256: | C23F2BD57F1BA882A864DB7A1D1BB283DEAD20550899E21AAF69A49DC2750D5D |
| SSDEEP: | 393216:tOha0ZRYNLyt2zne3hnRvSoR9nJxQqNXjcY4TpFPPqN1dbJsv6tWKFdu9C:+BW0tKexnRvSa9J3NXInTpFPqfd |
MALICIOUS
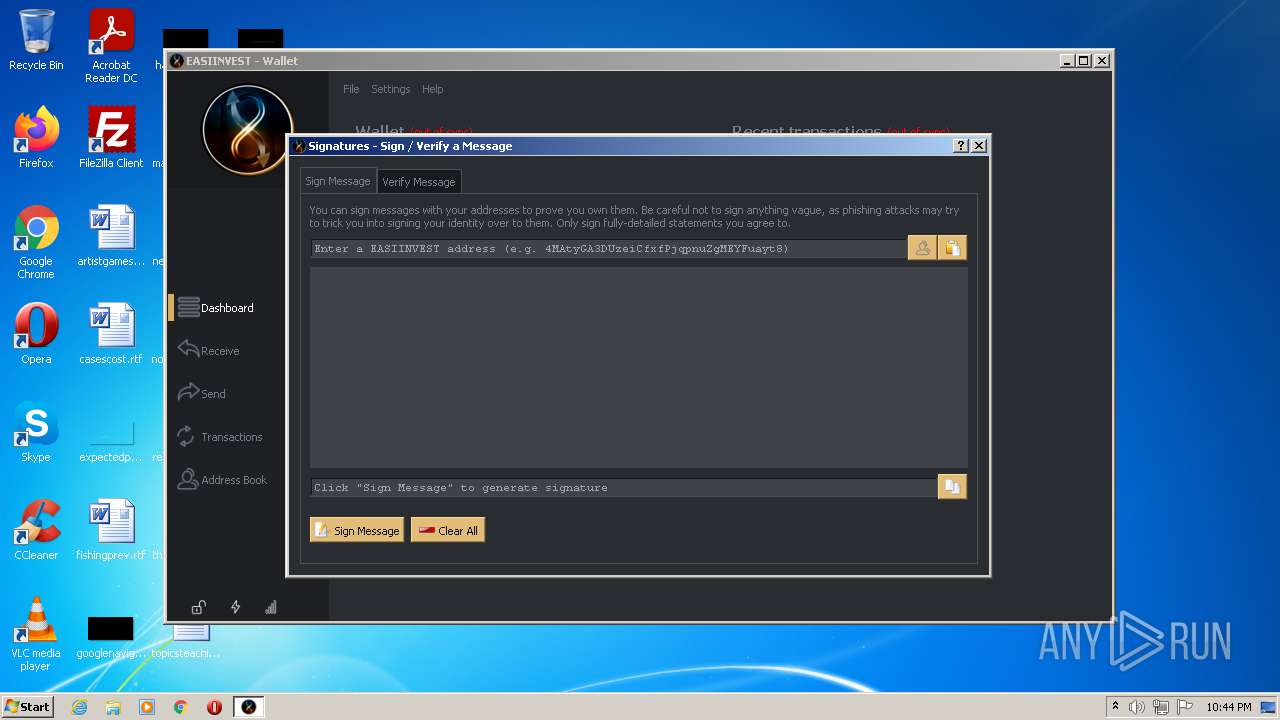
No malicious indicators.SUSPICIOUS
Checks supported languages
- easiinvest-qt.exe (PID: 2216)
Reads the computer name
- easiinvest-qt.exe (PID: 2216)
Creates files in the user directory
- easiinvest-qt.exe (PID: 2216)
Reads Environment values
- easiinvest-qt.exe (PID: 2216)
INFO
Checks supported languages
- NOTEPAD.EXE (PID: 2572)
- NOTEPAD.EXE (PID: 508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:29 10:58:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.28 |
| CodeSize: | 17860096 |
| InitializedDataSize: | 24671232 |
| UninitializedDataSize: | 23040 |
| EntryPoint: | 0x1470 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
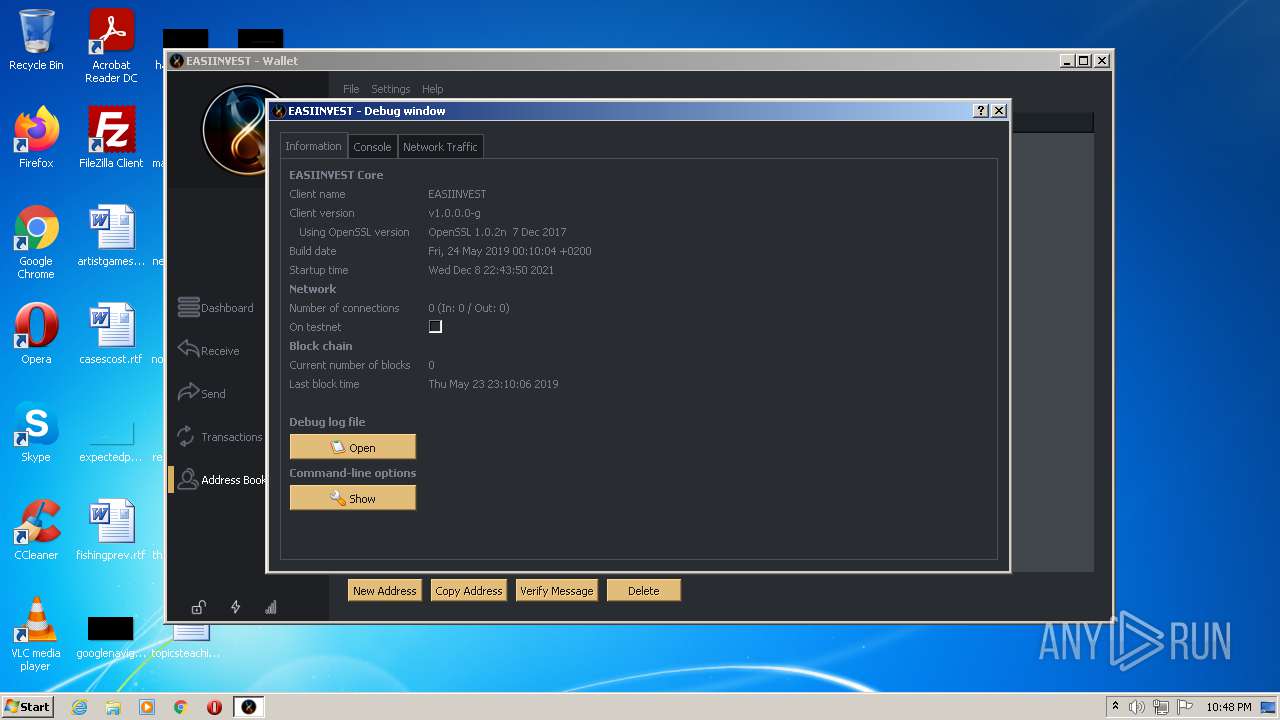
| CompanyName: | EASIINVEST |
| FileDescription: | EASIINVEST-Qt (OSS GUI client for EASIINVEST) |
| FileVersion: | 1.0.0.0 |
| InternalName: | easiinvest-qt |
| LegalCopyright: | 2009-2014 The Bitcoin developers, 2012-2014 The NovaCoin & PPCoin developers, 2014 The BlackCoin developers, 2019 The EASIINVEST developers |
| LegalTrademarks1: | Distributed under the MIT/X11 software license, see the accompanying file COPYING or http://www.opensource.org/licenses/mit-license.php. |
| OriginalFileName: | easiinvest-qt.exe |
| ProductName: | EASIINVEST-Qt |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jun-2020 08:58:53 |
| Detected languages: |
|
| TLS Callbacks: | 4 callback(s) detected. |
| CompanyName: | EASIINVEST |
| FileDescription: | EASIINVEST-Qt (OSS GUI client for EASIINVEST) |
| FileVersion: | 1.0.0.0 |
| InternalName: | easiinvest-qt |
| LegalCopyright: | 2009-2014 The Bitcoin developers, 2012-2014 The NovaCoin & PPCoin developers, 2014 The BlackCoin developers, 2019 The EASIINVEST developers |
| LegalTrademarks1: | Distributed under the MIT/X11 software license, see the accompanying file COPYING or http://www.opensource.org/licenses/mit-license.php. |
| OriginalFilename: | easiinvest-qt.exe |
| ProductName: | EASIINVEST-Qt |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 29-Jun-2020 08:58:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x01108418 | 0x01108600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27107 |
.data | 0x0110A000 | 0x00067AC4 | 0x00067C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.875591 |
.rdata | 0x01172000 | 0x005DC960 | 0x005DCA00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.58526 |
.qtmetad`\x03 | 0x0174F000 | 0x00000360 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70681 |
.bss | 0x01750000 | 0x00005960 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x01756000 | 0x000055C4 | 0x00005600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.72079 |
.CRT | 0x0175C000 | 0x0000003C | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.388978 |
.tls | 0x0175D000 | 0x00000008 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0175E000 | 0x000349B8 | 0x00034A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.13159 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.53679 | 1336 | UNKNOWN | English - United States | RT_VERSION |
2 | 5.07743 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.85749 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.71318 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 4.4761 | 38056 | UNKNOWN | English - United States | RT_ICON |
6 | 4.32452 | 67624 | UNKNOWN | English - United States | RT_ICON |
7 | 7.98939 | 75841 | UNKNOWN | English - United States | RT_ICON |
IDI_ICON1 | 2.88864 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
IMM32.DLL |
IPHLPAPI.DLL |
KERNEL32.dll |
MSWSOCK.DLL |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
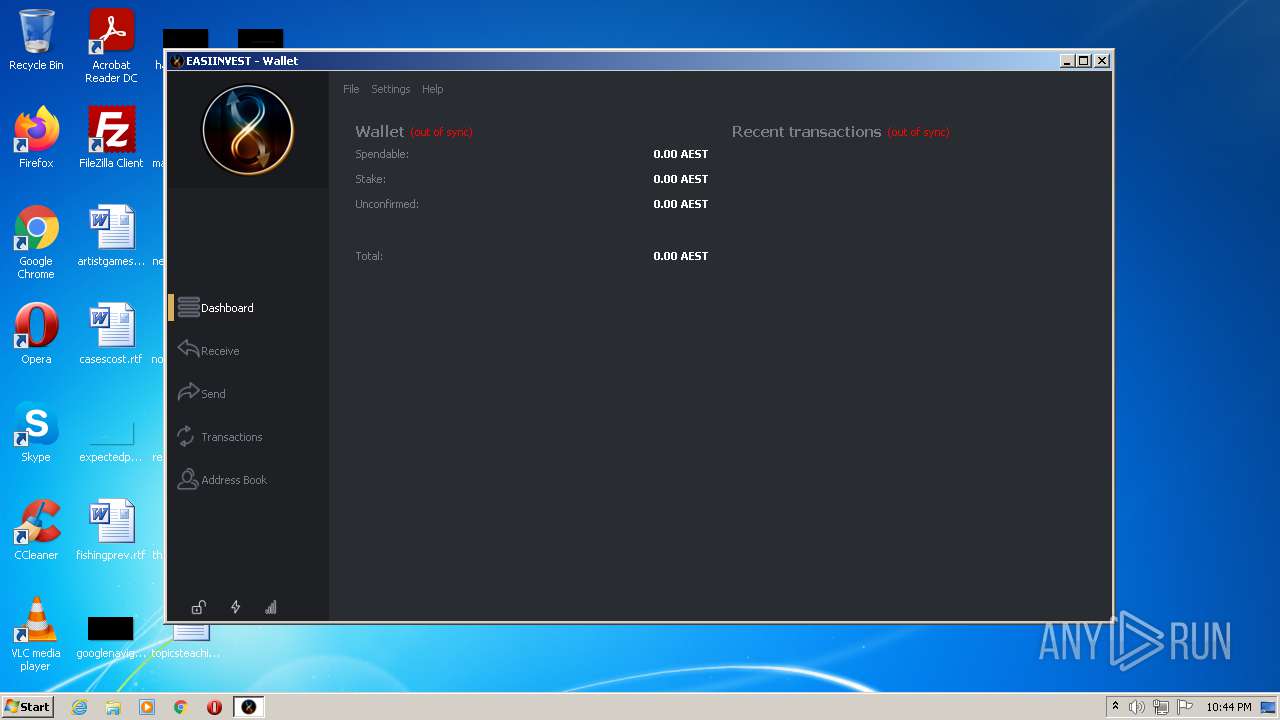
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
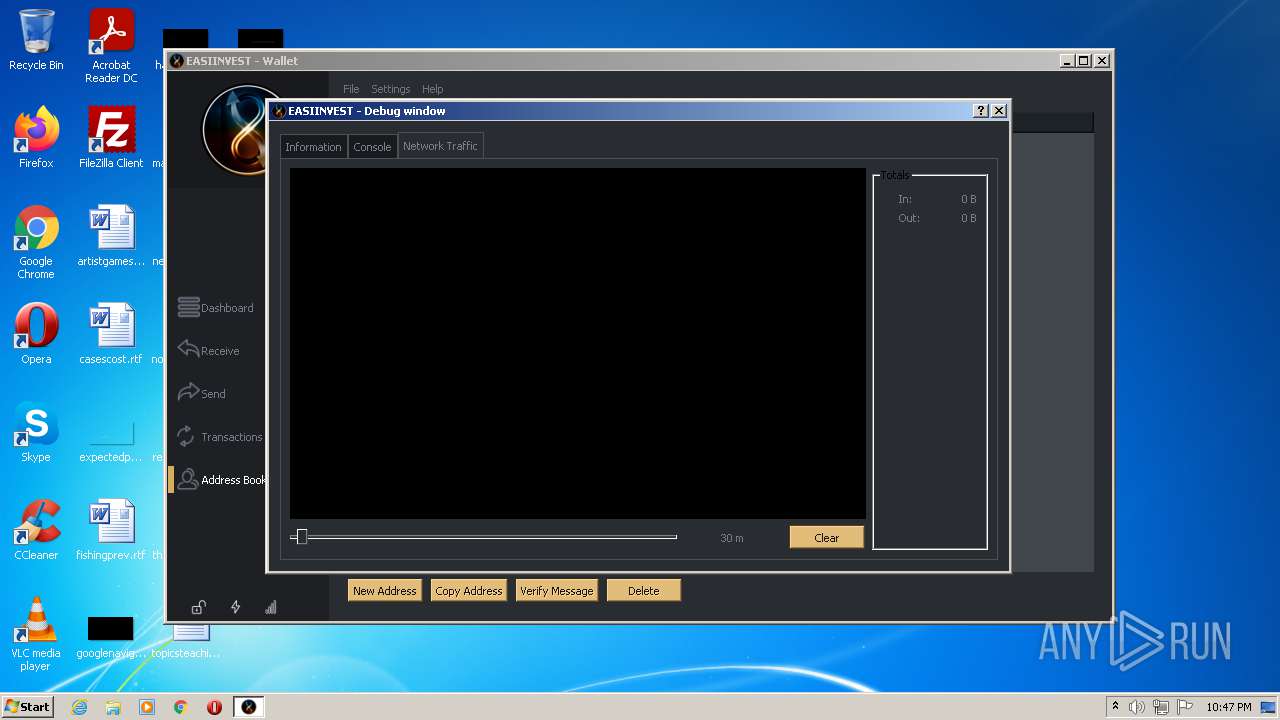
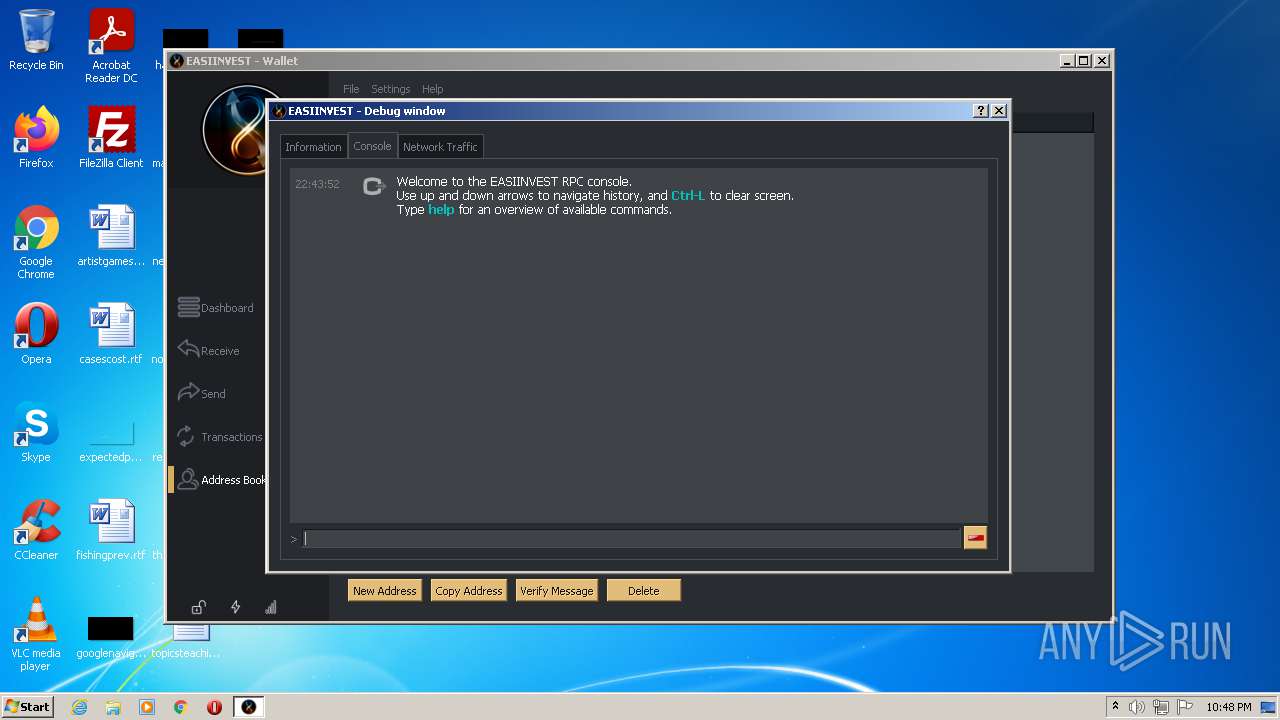
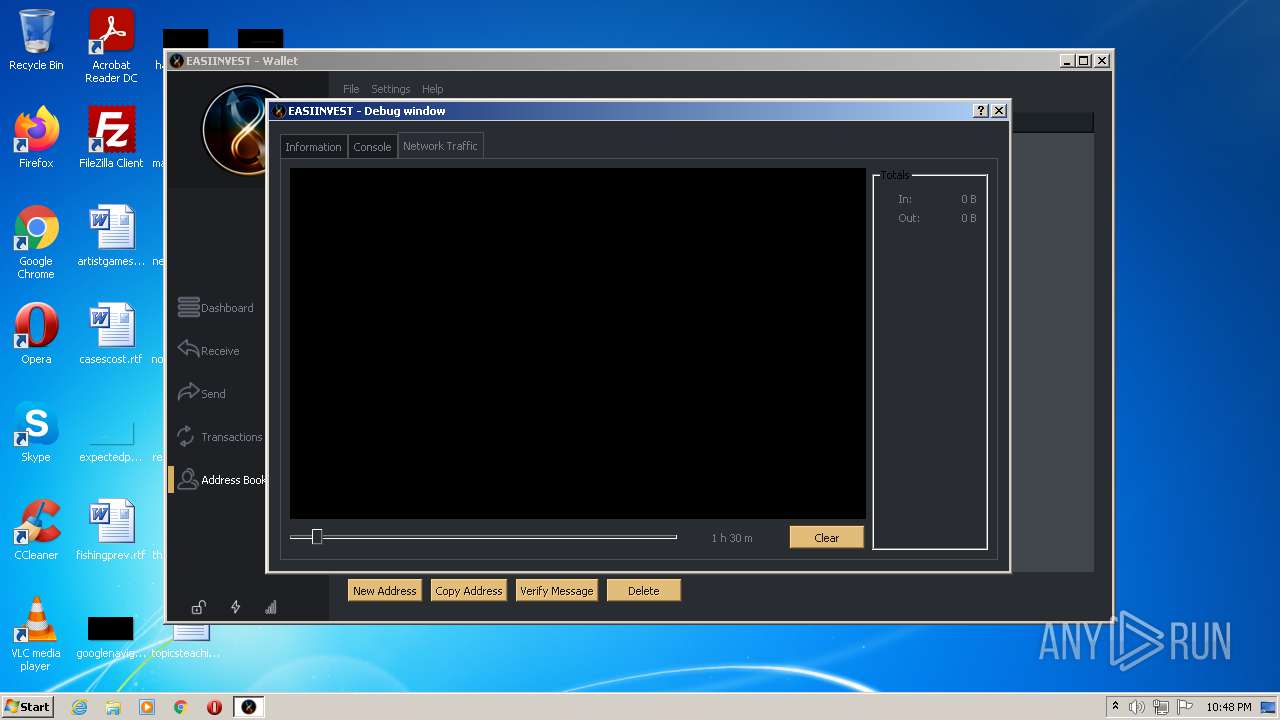
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
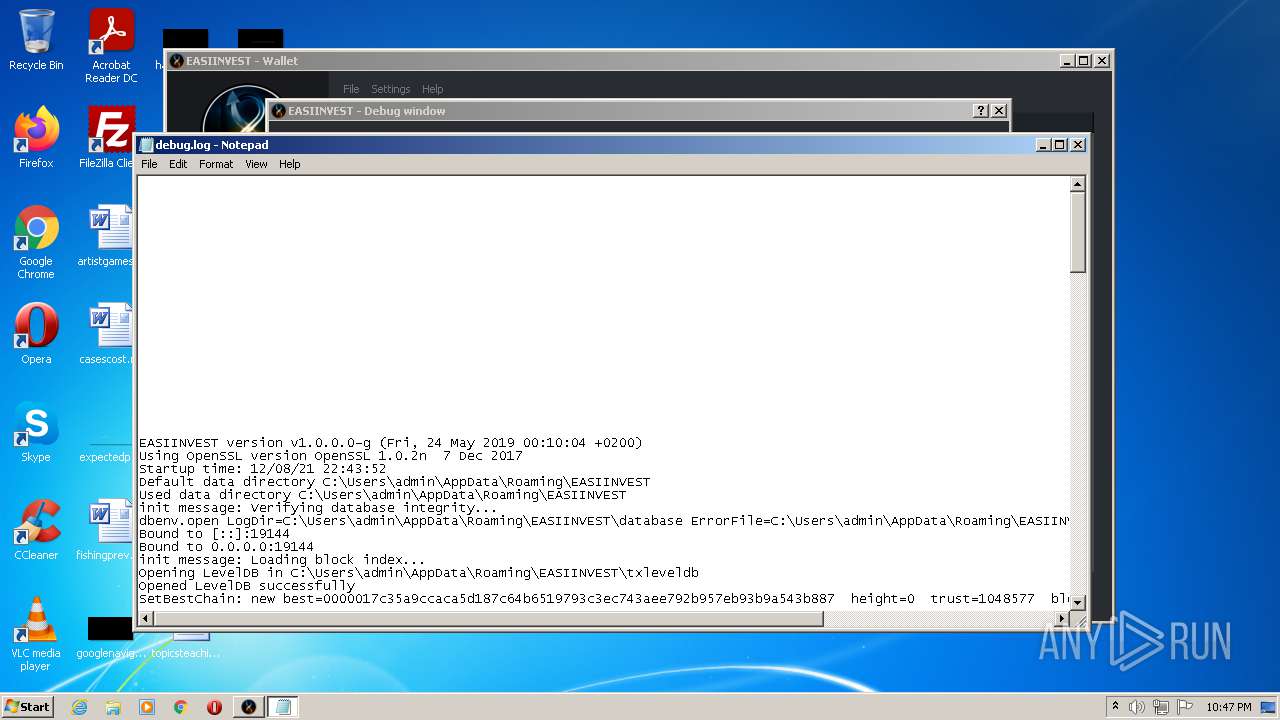
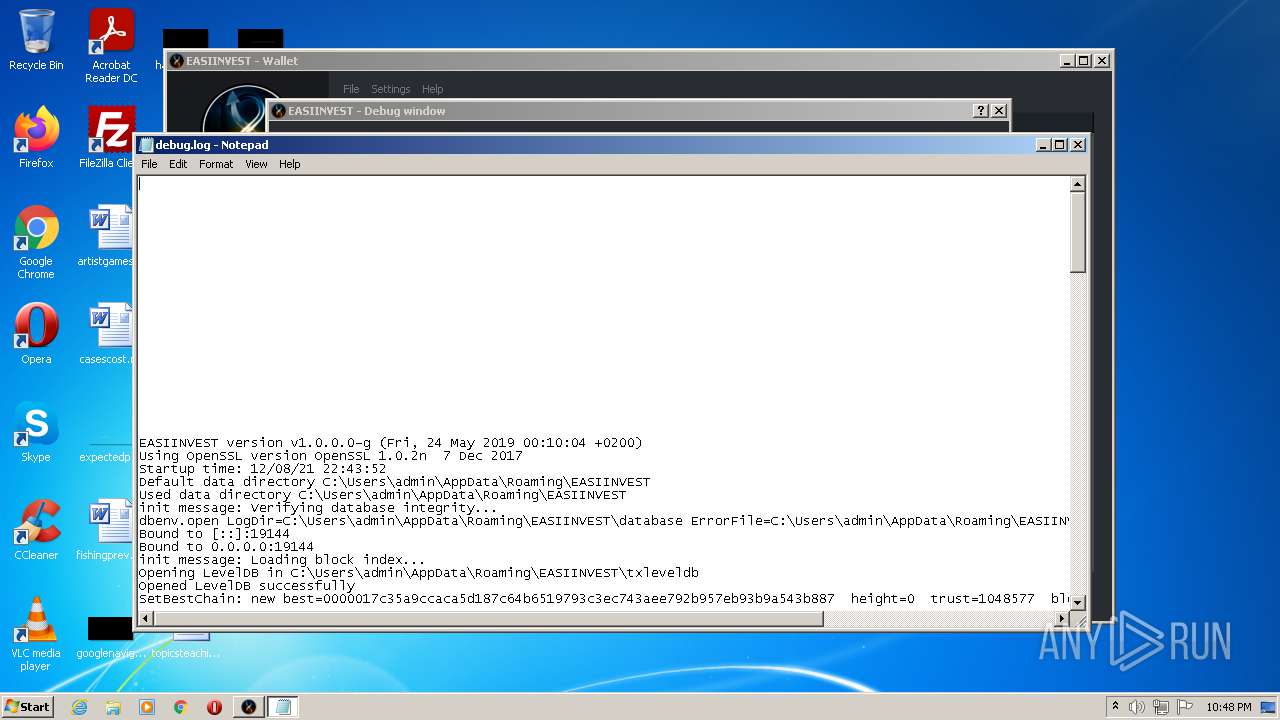
| 508 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\EASIINVEST\debug.log | C:\Windows\system32\NOTEPAD.EXE | — | easiinvest-qt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
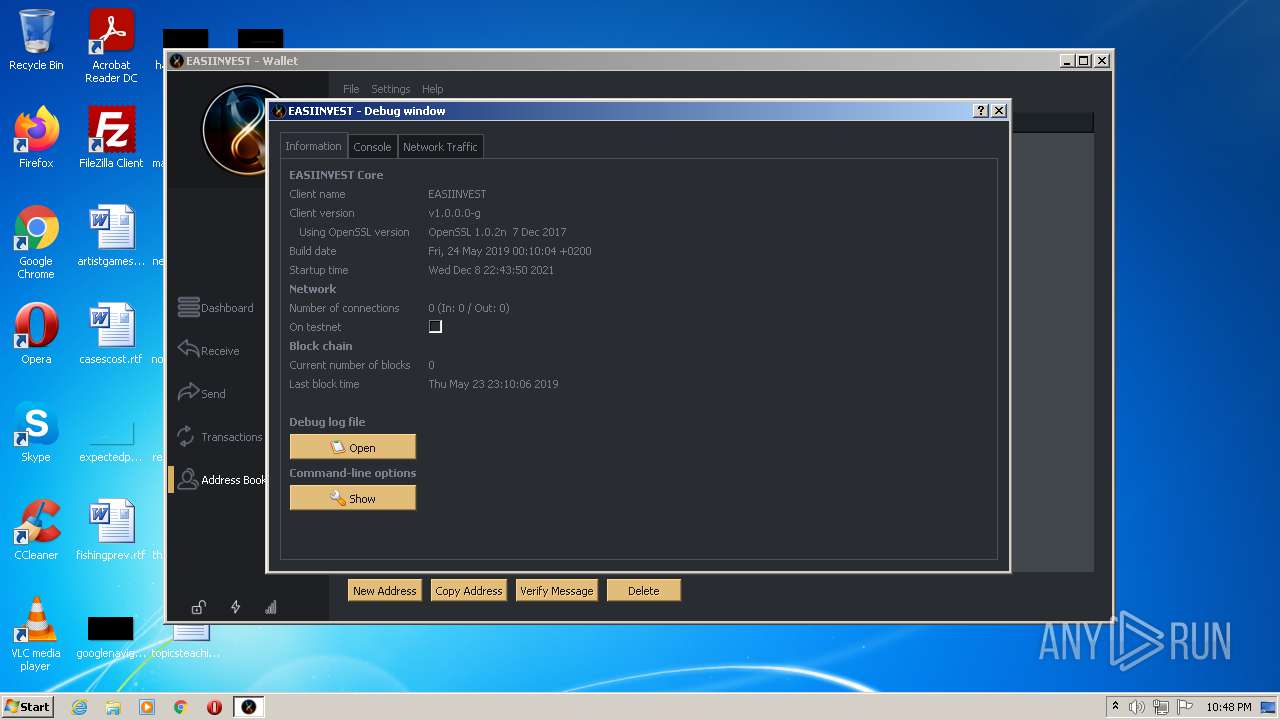
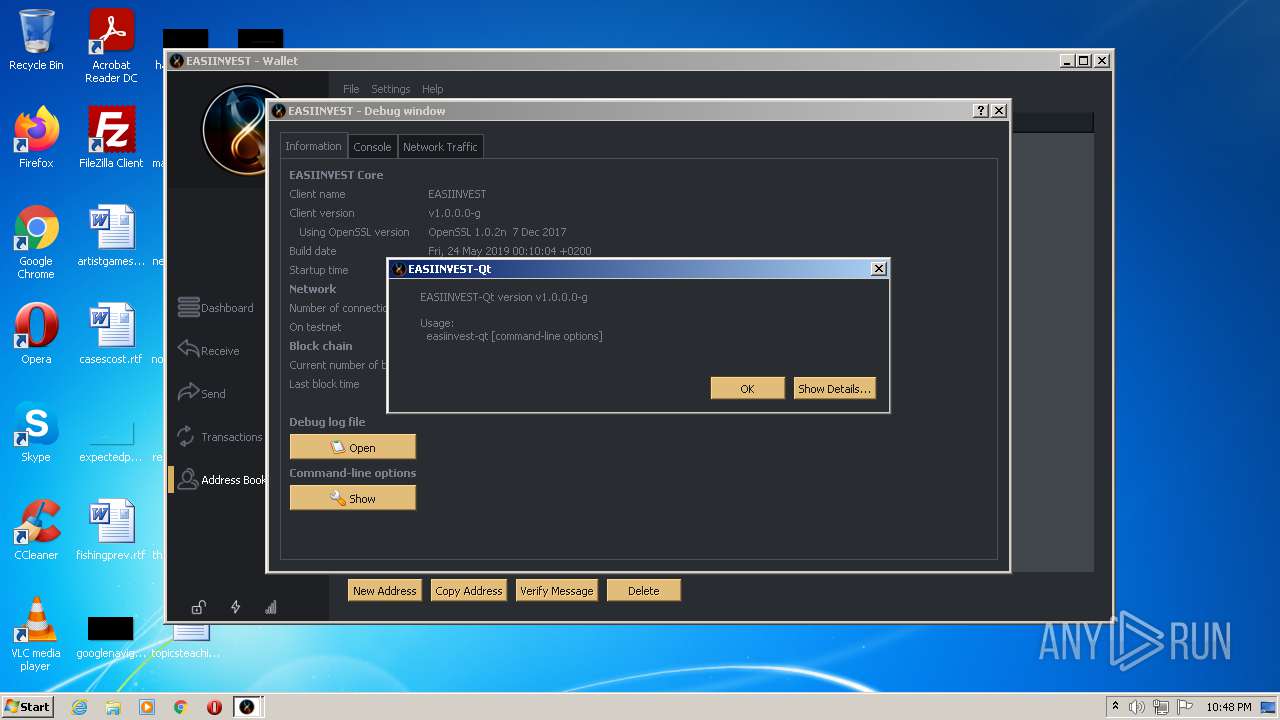
| 2216 | "C:\easiinvest-qt.exe" | C:\easiinvest-qt.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2572 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\EASIINVEST\debug.log | C:\Windows\system32\NOTEPAD.EXE | — | easiinvest-qt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 074
Read events
2 073
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2216) easiinvest-qt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: easiinvest-qt.exe | |||
Executable files
0
Suspicious files
3
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\__db.80000001.33119470 | binary | |
MD5:— | SHA256:— | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\wallet.dat | binary | |
MD5:— | SHA256:— | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\blk0001.dat | dbf | |
MD5:— | SHA256:— | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\txleveldb\000002.dbtmp | text | |
MD5:206702161F94C5CD39FADD03F4014D98 | SHA256:1005A525006F148C86EFCBFB36C6EAC091B311532448010F70F7DE9A68007167 | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\txleveldb\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\txleveldb\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\txleveldb\CURRENT | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 2216 | easiinvest-qt.exe | C:\Users\admin\AppData\Roaming\EASIINVEST\debug.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
141
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
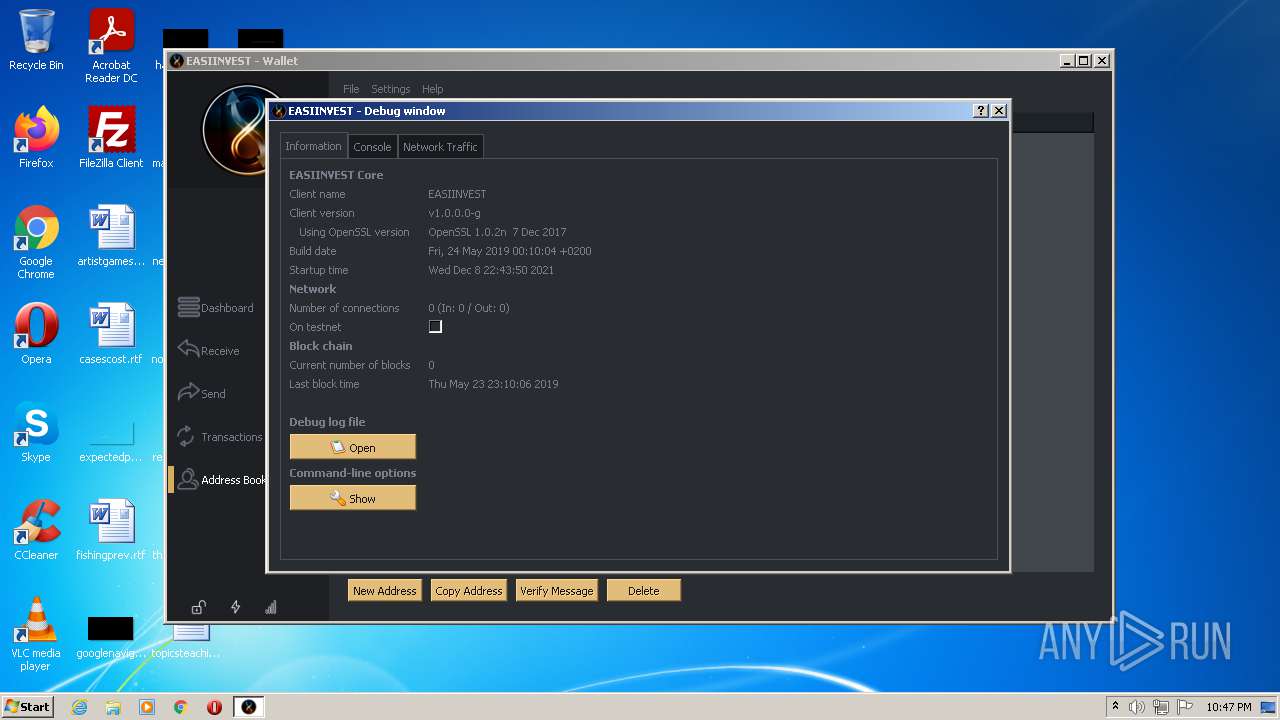
2216 | easiinvest-qt.exe | 136.144.171.201:19144 | node1.walletbuilders.com | Transip B.V. | NL | unknown |
— | — | 136.144.171.201:19144 | node1.walletbuilders.com | Transip B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
node1.walletbuilders.com |
| unknown |
walletbuilders.com |
| unknown |