| File name: | Goldnet.exe |
| Full analysis: | https://app.any.run/tasks/547d3eaf-5253-4d33-8284-84c48331aec9 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2019, 18:16:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | E067E530E4588CE7ABE77B649C07ED77 |
| SHA1: | 652735D6090B566FF2C18CF1BF91F62810CB043A |
| SHA256: | C22BD3B7F558C3137D2003404F2D89ED1BD8718EDA89EF55711643AD0F16F14B |
| SSDEEP: | 98304:1WABqrnkIv97GJAn5jMmHX5WT6uakPUA7x+mueihrnkIv97GaAn5MmHX5WT6uaUo:Me6n97GMRg6uaVAF/ueUn97GRg6uaEfk |
MALICIOUS
No malicious indicators.SUSPICIOUS
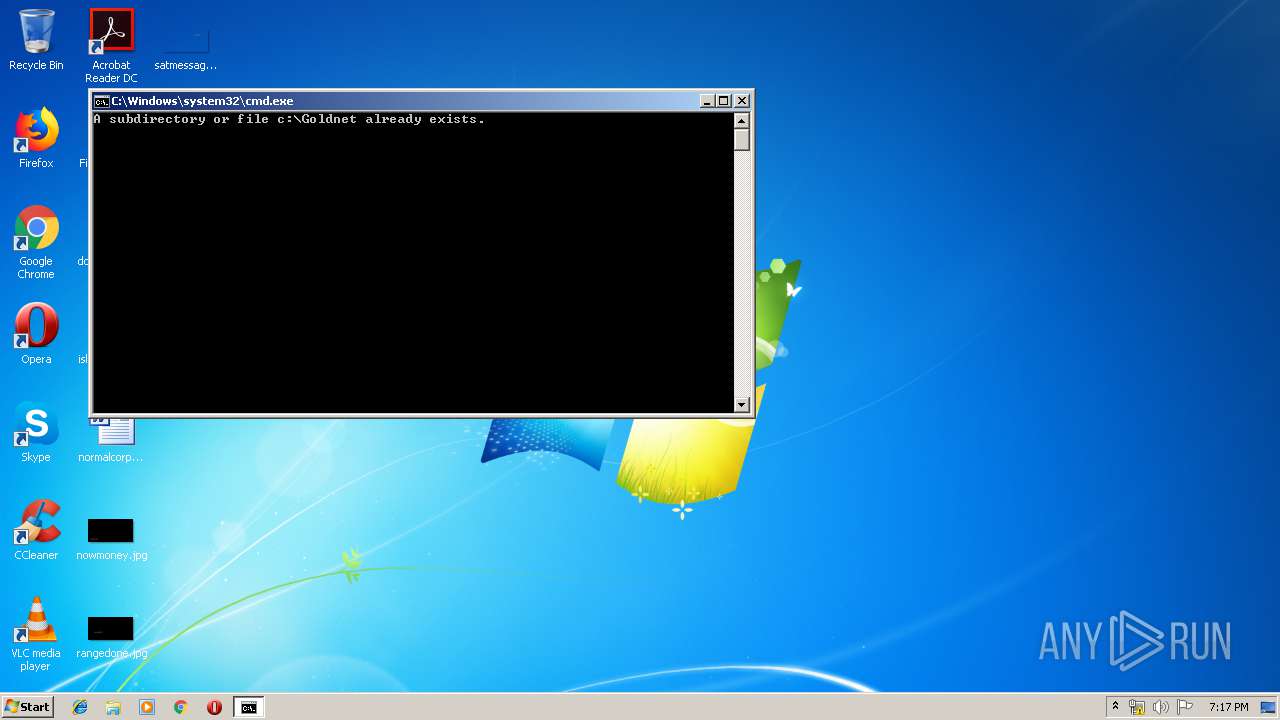
Application launched itself
- cmd.exe (PID: 3704)
Reads internet explorer settings
- Goldnet.exe (PID: 2132)
Starts CMD.EXE for commands execution
- Goldnet.exe (PID: 2132)
- cmd.exe (PID: 3704)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 920)
Executable content was dropped or overwritten
- Goldnet.exe (PID: 2132)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3704)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:03 20:38:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 169984 |
| InitializedDataSize: | 178688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e64b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Feb-2016 19:38:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Feb-2016 19:38:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00029604 | 0x00029800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.7094 |
.rdata | 0x0002B000 | 0x000058A3 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09421 |
.data | 0x00031000 | 0x00021608 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.58964 |
.rsrc | 0x00053000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63388 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
50
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | xcopy C:\Goldnet\go.bat c:\attplus\ | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | Reg.exe add "HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\GoldNET\Automate" /v "ExecApplication4" /t REG_SZ /d "c:\AttPlus\go.bat,,\"Arj a -y <MivzaqBakDataPath>{MivIx}.arj <MivzaqMsgsDataPath>*.ms*\",,\"<BankExplore> -I <MivzaqMsgsDataPath>*.msq -E\"" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | C:\Windows\system32\cmd.exe /c "wmic path win32_useraccount where name='admin' get sid" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1100 | REG ADD "HKEY_CURRENT_USER\Software\GoldNET\Automate\Variables" /v "MsgCabinet" /f /t REG_SZ /d "C:\Program Files (x86)\AttMsg\\" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1416 | wmic path win32_useraccount where name='admin' get sid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\Goldnet.exe" | C:\Users\admin\AppData\Local\Temp\Goldnet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2392 | REG ADD "HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers" /v "C:\Program Files (x86)\Goldnet\BusinessNet\BusinessNET.exe" /t REG_SZ /d "RUNASADMIN" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | REG ADD "HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers" /v "C:\Program Files (x86)\Goldnet\BusinessNet\MailRoute.exe" /t REG_SZ /d "RUNASADMIN" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3428 | reg add "HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment" /f /v EDIHOST_DIR /t REG_SZ /d "C:\goldnet\System\account\\" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | REG ADD "HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers" /v "C:\Program Files (x86)\Goldnet\BusinessNet\EAccount.exe" /t REG_SZ /d "RUNASADMIN" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
121
Read events
111
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2132) Goldnet.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2132) Goldnet.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1100) reg.exe | Key: | HKEY_CURRENT_USER\Software\GoldNET\Automate\Variables |
| Operation: | write | Name: | MsgCabinet |
Value: C:\Program Files (x86)\AttMsg\ | |||
| (PID) Process: | (3980) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files (x86)\Goldnet\BusinessNet\ECurrency.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (2392) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files (x86)\Goldnet\BusinessNet\BusinessNET.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (584) reg.exe | Key: | HKEY_CURRENT_USER\Software\GoldNET\Automate |
| Operation: | write | Name: | ExecApplication4 |
Value: c:\AttPlus\go.bat,,"Arj a -y <MivzaqBakDataPath>{MivIx}.arj <MivzaqMsgsDataPath>*.ms*",,"<BankExplore> -I <MivzaqMsgsDataPath>*.msq -E" | |||
| (PID) Process: | (3264) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files (x86)\Goldnet\BusinessNet\MailRoute.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (3548) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files (x86)\Goldnet\BusinessNet\EAccount.exe |
Value: RUNASADMIN | |||
Executable files
34
Suspicious files
9
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | Goldnet.exe | C:\goldnet\System\account\DATA\EDIEDI | — | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\CASAUDIT.dll | executable | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\catav.exe | executable | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\backUp.tmp | binary | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\64bit.bat | text | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\DATA\EDIPRTY | binary | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\casenc01.exe | executable | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\catav01.exe | executable | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\DATA\EDIPRTY.1 | binary | |
MD5:— | SHA256:— | |||
| 2132 | Goldnet.exe | C:\goldnet\System\account\EDIEDI | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report