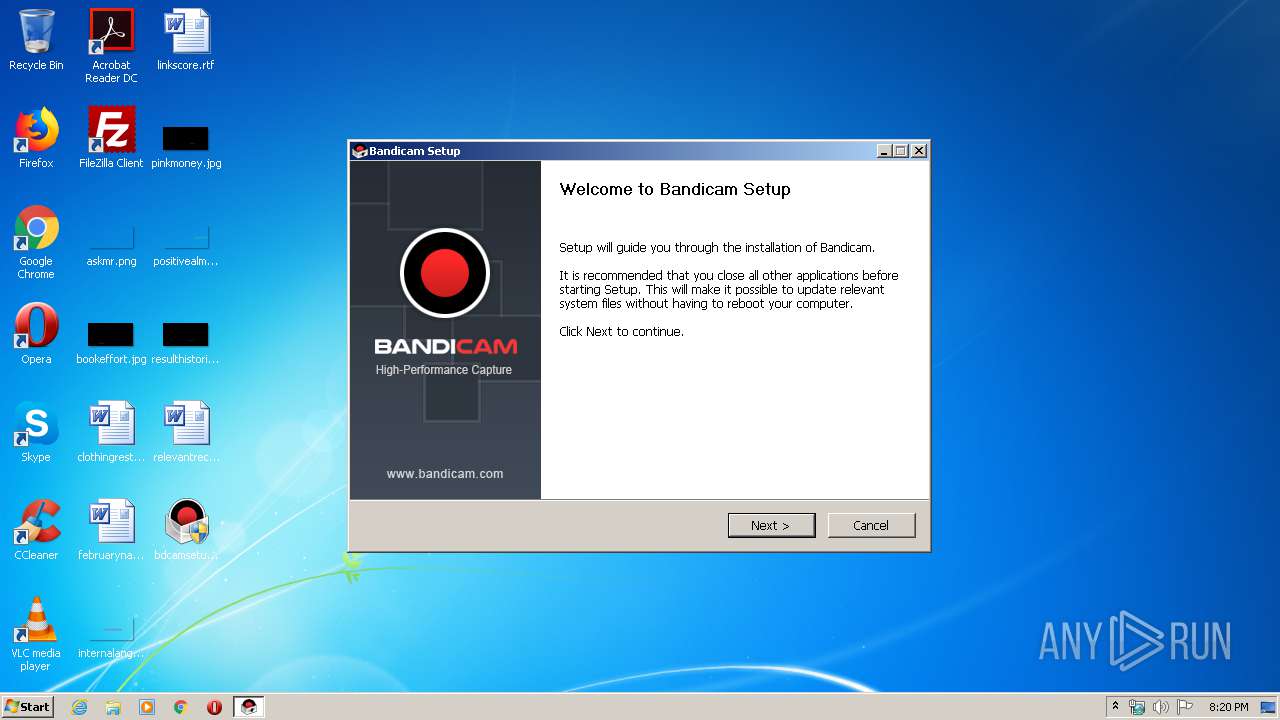
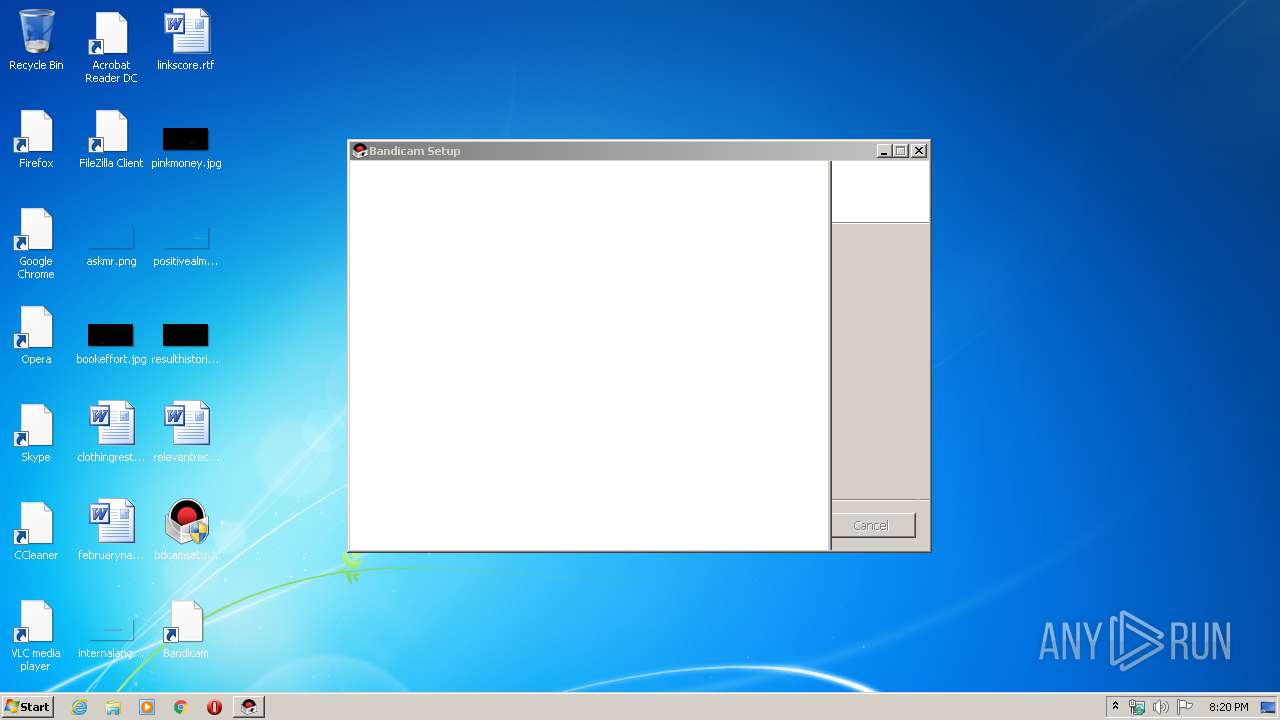
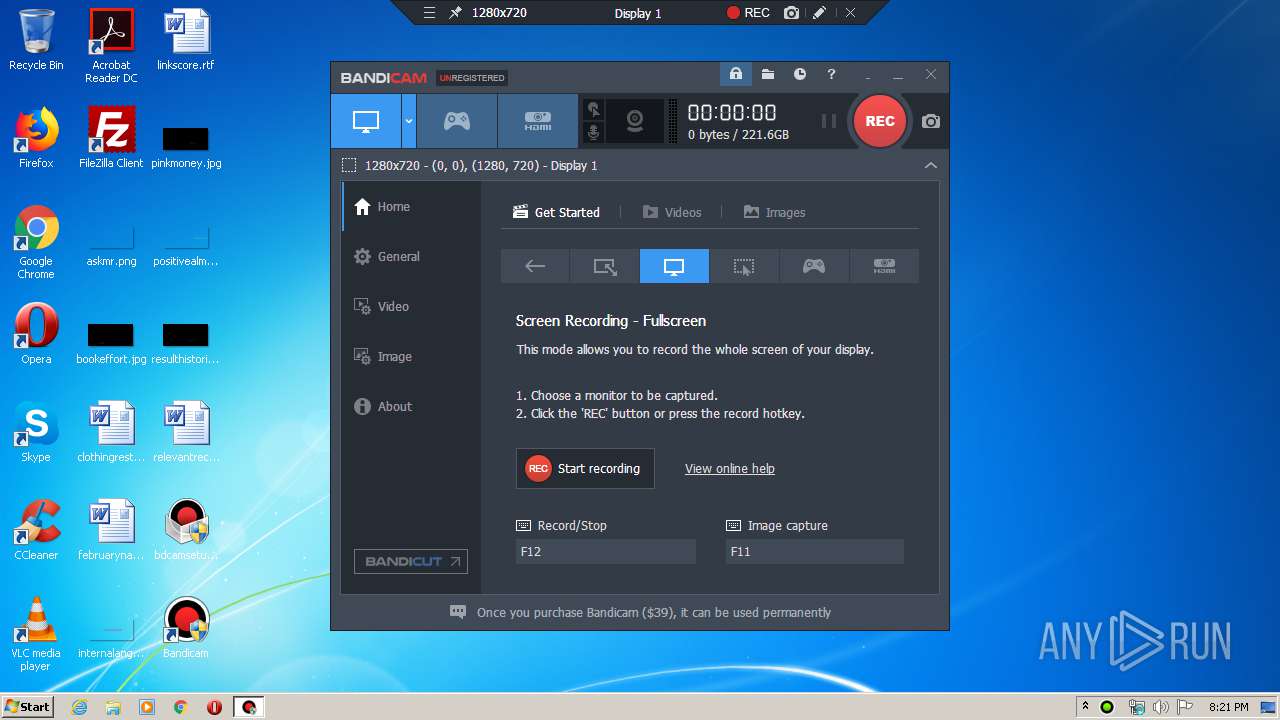
| download: | bdcamsetup.exe |
| Full analysis: | https://app.any.run/tasks/c43bd7d1-f95a-4838-882d-0a1c685fed51 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 20:19:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | DC27BFE7D7CCE351FA95EA11E3603319 |
| SHA1: | 1CC2FFF1D12A68A738F9CC5D6A5D78E64E284026 |
| SHA256: | C228A8B9DB1B2E368D2900F12AE7CA842920C9932225F3E29356C249B604297C |
| SSDEEP: | 393216:ftmg+LSxRbEKpBktGw5qg1eJmJB4k920w2alwbYwjahPuXHvtWNfznm4h4vp:VmgjhEKpByqeekjZjw5lwbYwja0PYNrg |
MALICIOUS
Application was dropped or rewritten from another process
- BDMPEG1SETUP.EXE (PID: 2976)
- bdcam.exe (PID: 3352)
- bdcam.exe (PID: 3308)
- bdcam.exe (PID: 2736)
Loads dropped or rewritten executable
- bdcamsetup.exe (PID: 3296)
- BDMPEG1SETUP.EXE (PID: 2976)
- rundll32.exe (PID: 1740)
- bdcam.exe (PID: 3352)
- rundll32.exe (PID: 1940)
- bdcam.exe (PID: 3308)
Registers / Runs the DLL via REGSVR32.EXE
- BDMPEG1SETUP.EXE (PID: 2976)
Changes settings of System certificates
- bdcam.exe (PID: 3308)
SUSPICIOUS
Executable content was dropped or overwritten
- bdcamsetup.exe (PID: 3296)
- BDMPEG1SETUP.EXE (PID: 2976)
Creates files in the program directory
- BDMPEG1SETUP.EXE (PID: 2976)
- bdcamsetup.exe (PID: 3296)
Creates COM task schedule object
- BDMPEG1SETUP.EXE (PID: 2976)
Creates a software uninstall entry
- BDMPEG1SETUP.EXE (PID: 2976)
- bdcamsetup.exe (PID: 3296)
Creates files in the Windows directory
- BDMPEG1SETUP.EXE (PID: 2976)
Modifies the open verb of a shell class
- bdcam.exe (PID: 3352)
- bdcam.exe (PID: 2736)
Uses RUNDLL32.EXE to load library
- bdcam.exe (PID: 3352)
- bdcam.exe (PID: 2736)
Changes IE settings (feature browser emulation)
- bdcamsetup.exe (PID: 3296)
Reads Internet Cache Settings
- bdcamsetup.exe (PID: 3296)
- bdcam.exe (PID: 3308)
Starts Internet Explorer
- bdcamsetup.exe (PID: 3296)
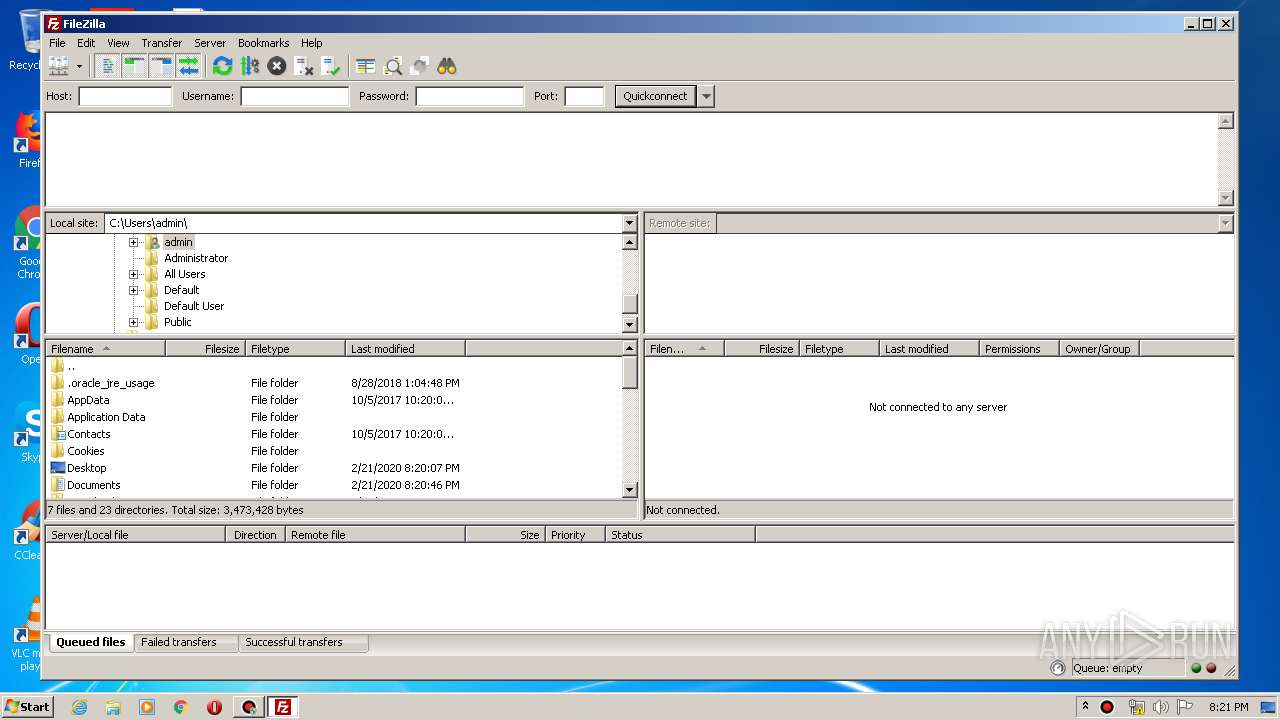
Creates files in the user directory
- bdcam.exe (PID: 3308)
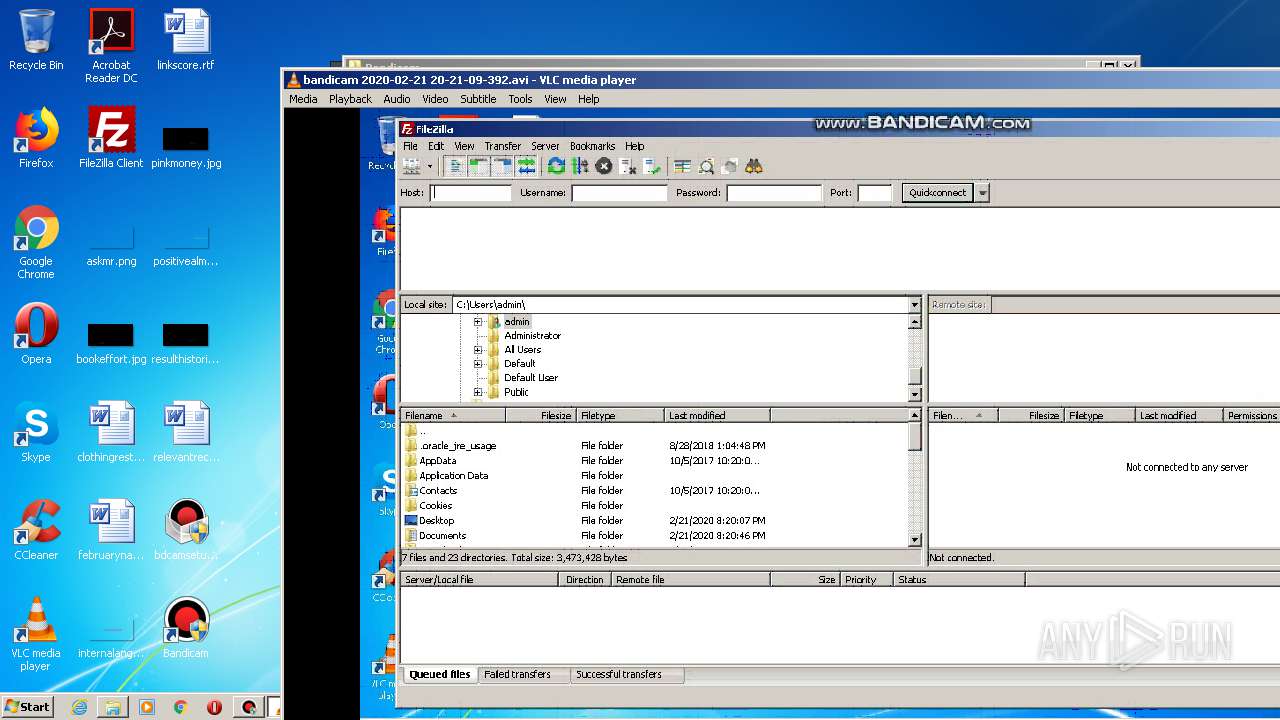
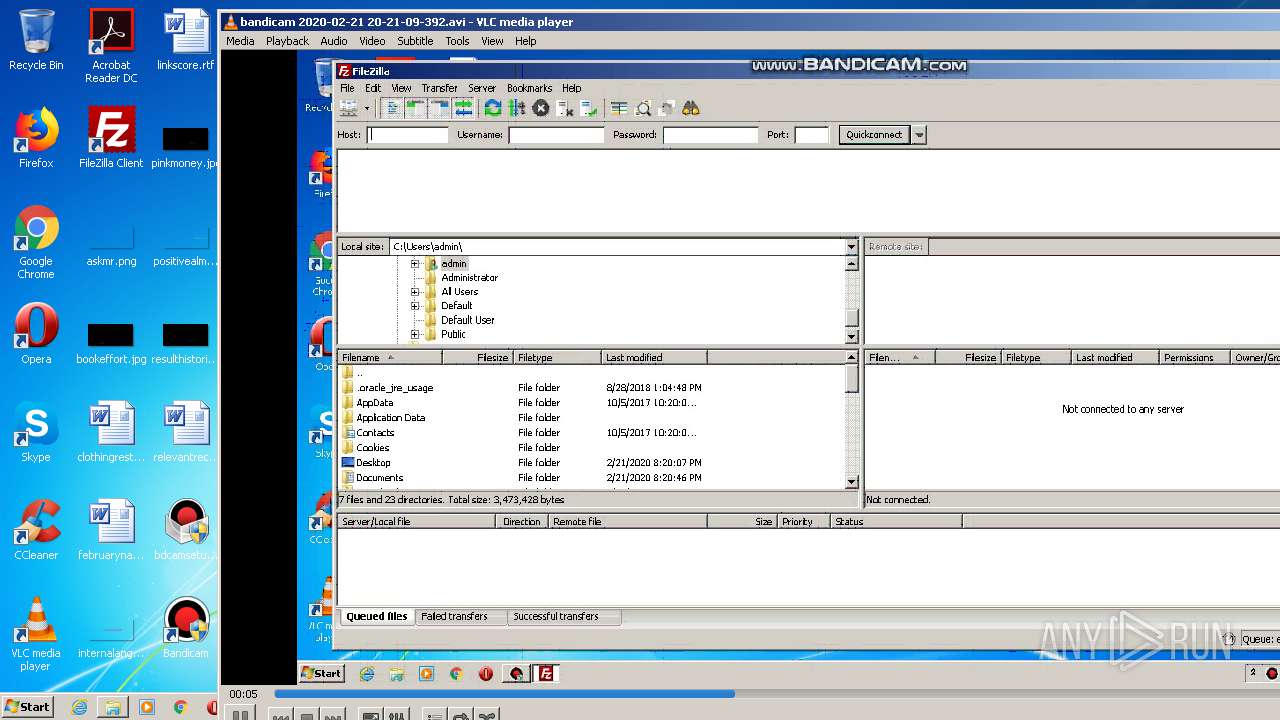
- filezilla.exe (PID: 2872)
- vlc.exe (PID: 820)
Reads internet explorer settings
- bdcam.exe (PID: 3308)
Adds / modifies Windows certificates
- bdcam.exe (PID: 3308)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1944)
- iexplore.exe (PID: 3828)
Application launched itself
- iexplore.exe (PID: 1944)
Changes internet zones settings
- iexplore.exe (PID: 1944)
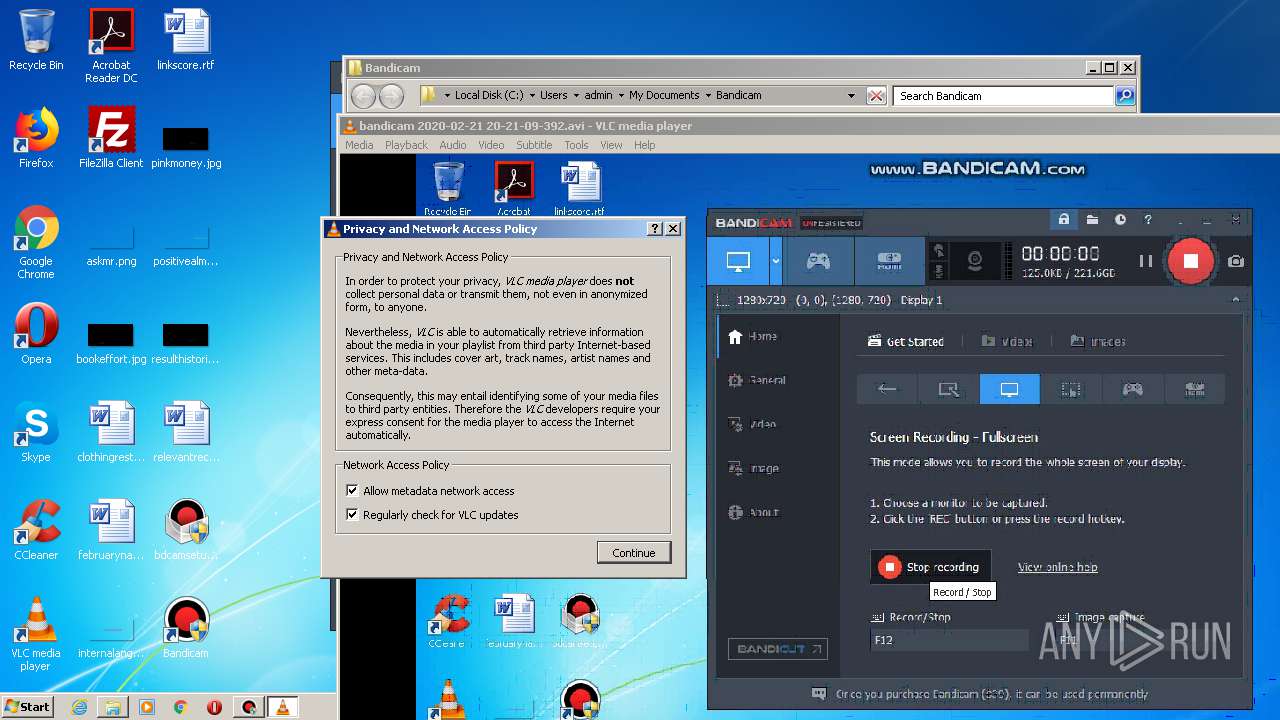
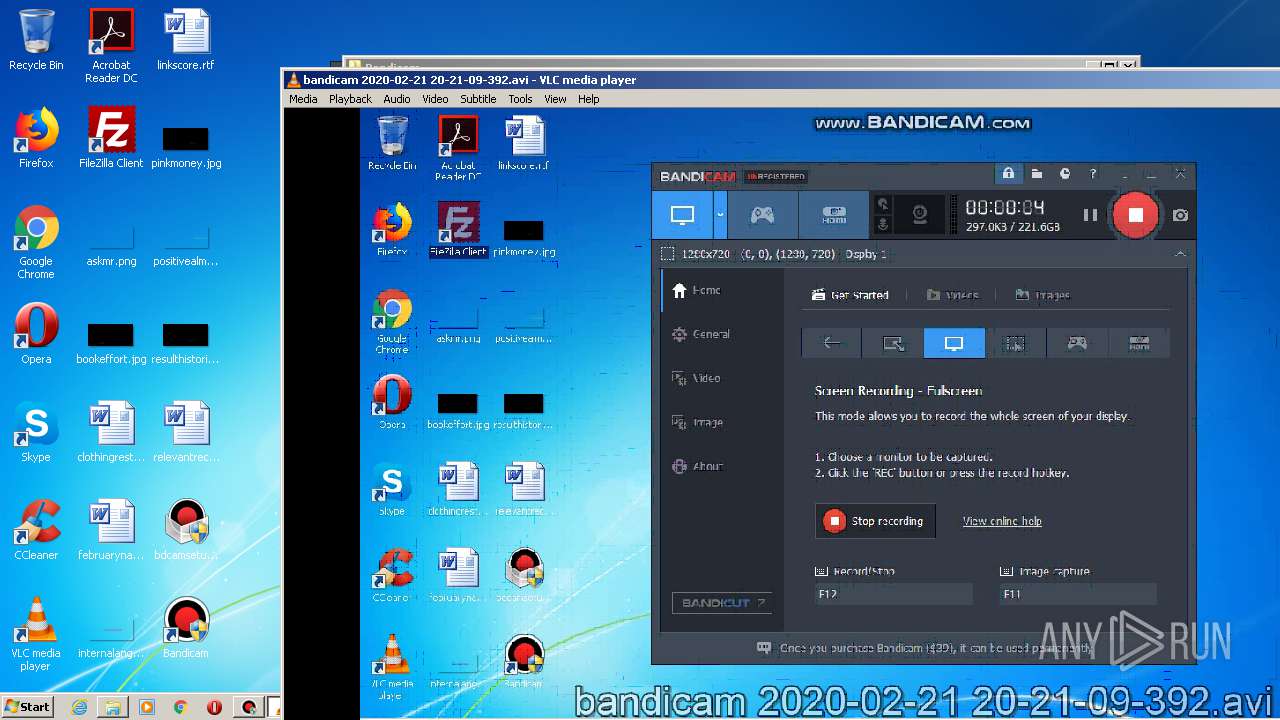
Manual execution by user
- filezilla.exe (PID: 2872)
- vlc.exe (PID: 820)
- vlc.exe (PID: 3188)
Reads settings of System Certificates
- iexplore.exe (PID: 3828)
- bdcam.exe (PID: 3308)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3828)
Changes settings of System certificates
- iexplore.exe (PID: 3828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32fe |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.6.1647 |
| ProductVersionNumber: | 4.5.6.1647 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
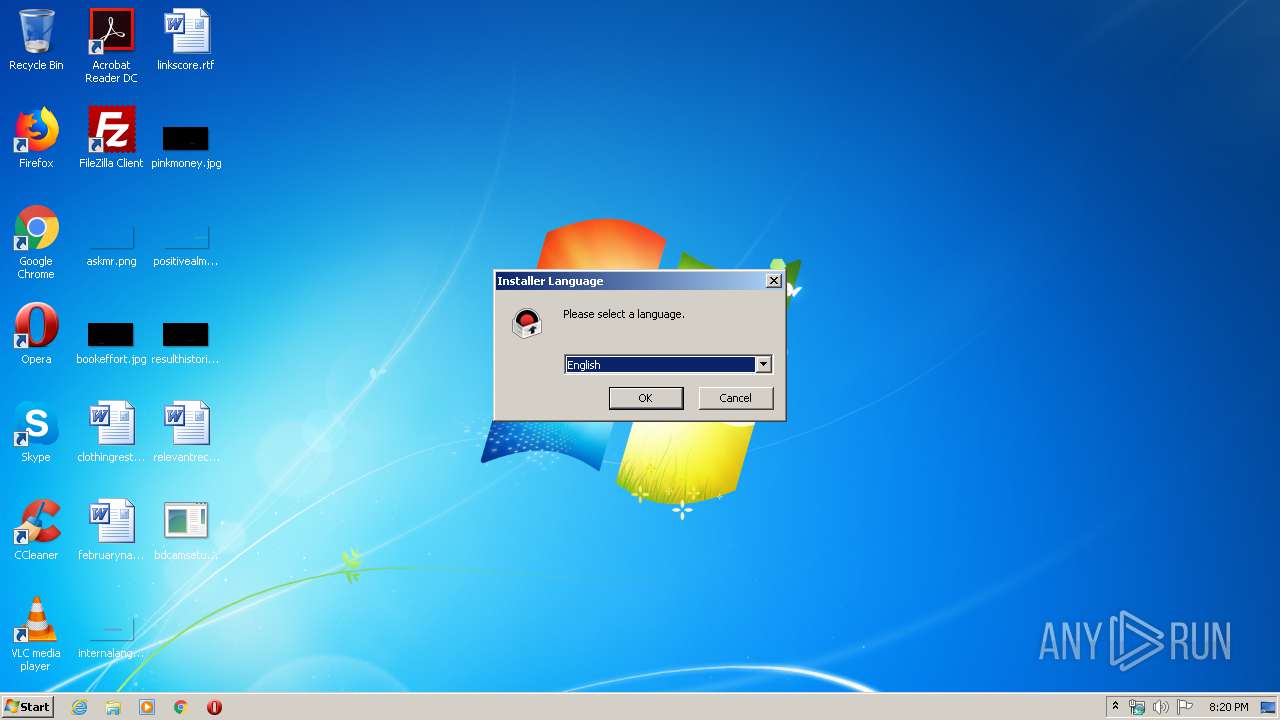
| LanguageCode: | Arabic |
| CharacterSet: | Windows, Arabic |
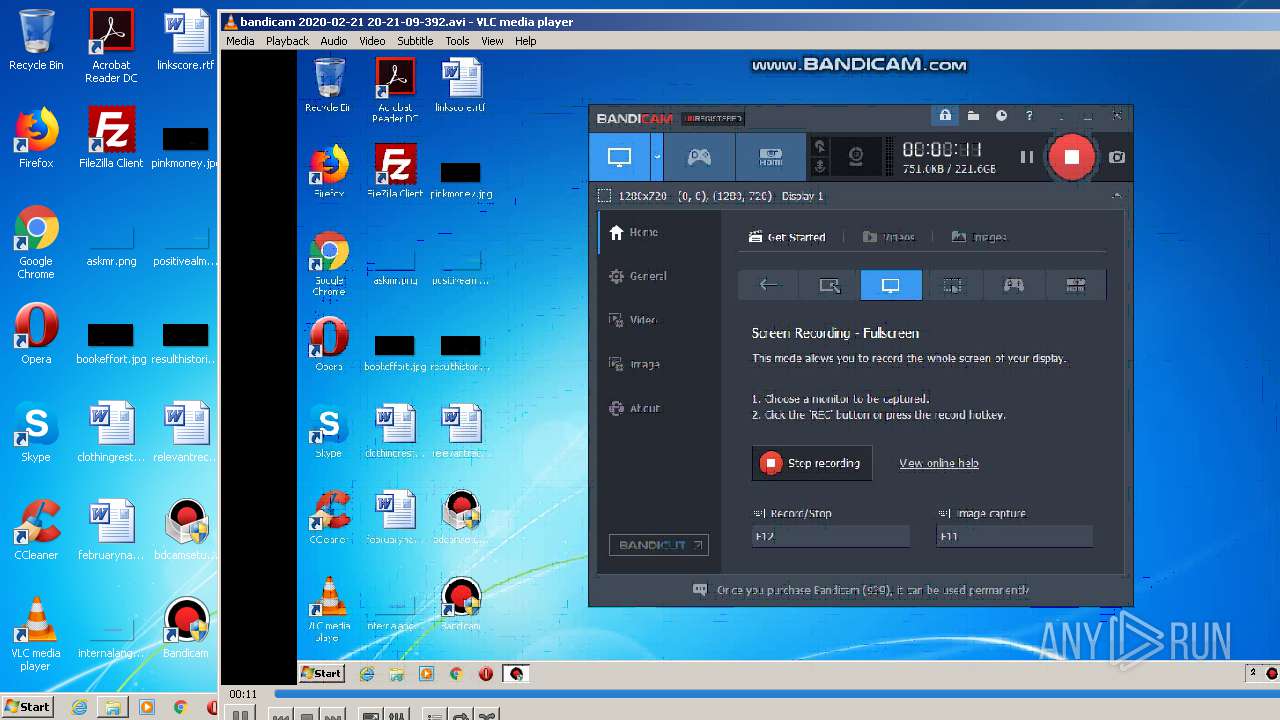
| Comments: | Bandicam Setup File (2020-02-20 오전 12:52:41) |
| CompanyName: | Bandicam Company |
| FileDescription: | Bandicam Setup File |
| FileVersion: | 4.5.6.1647 |
| LegalCopyright: | Copyright(C) 2009-2020 Bandicam.com, All rights reserved. |
| ProductName: | Bandicam |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:41 |
| Detected languages: |
|
| Comments: | Bandicam Setup File (2020-02-20 오전 12:52:41) |
| CompanyName: | Bandicam Company |
| FileDescription: | Bandicam Setup File |
| FileVersion: | 4.5.6.1647 |
| LegalCopyright: | Copyright(C) 2009-2020 Bandicam.com, All rights reserved. |
| ProductName: | Bandicam |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000608D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4239 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16231 |
.data | 0x0000A000 | 0x000202F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.89813 |
.ndata | 0x0002B000 | 0x00017000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00042000 | 0x00019AD8 | 0x00019C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.81214 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.67767 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.31734 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.28764 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.66571 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.26475 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.82212 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.72924 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.71858 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6693 | 280 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
58
Monitored processes
14
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
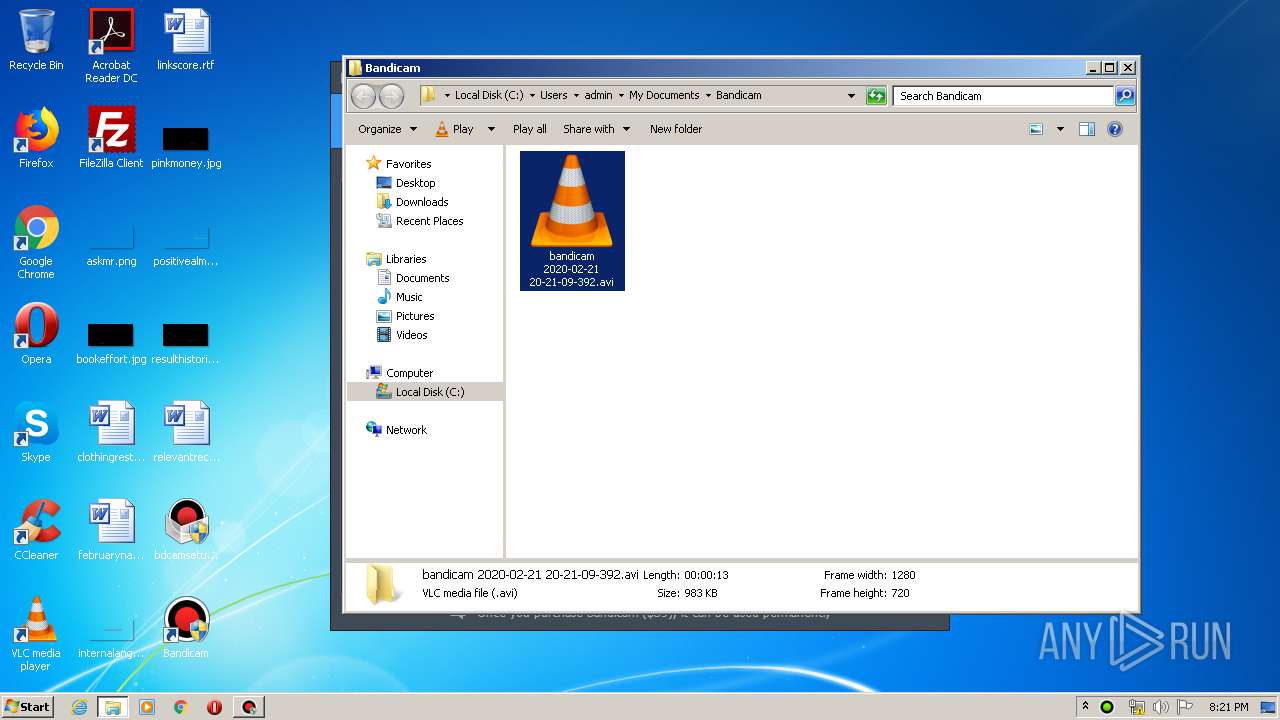
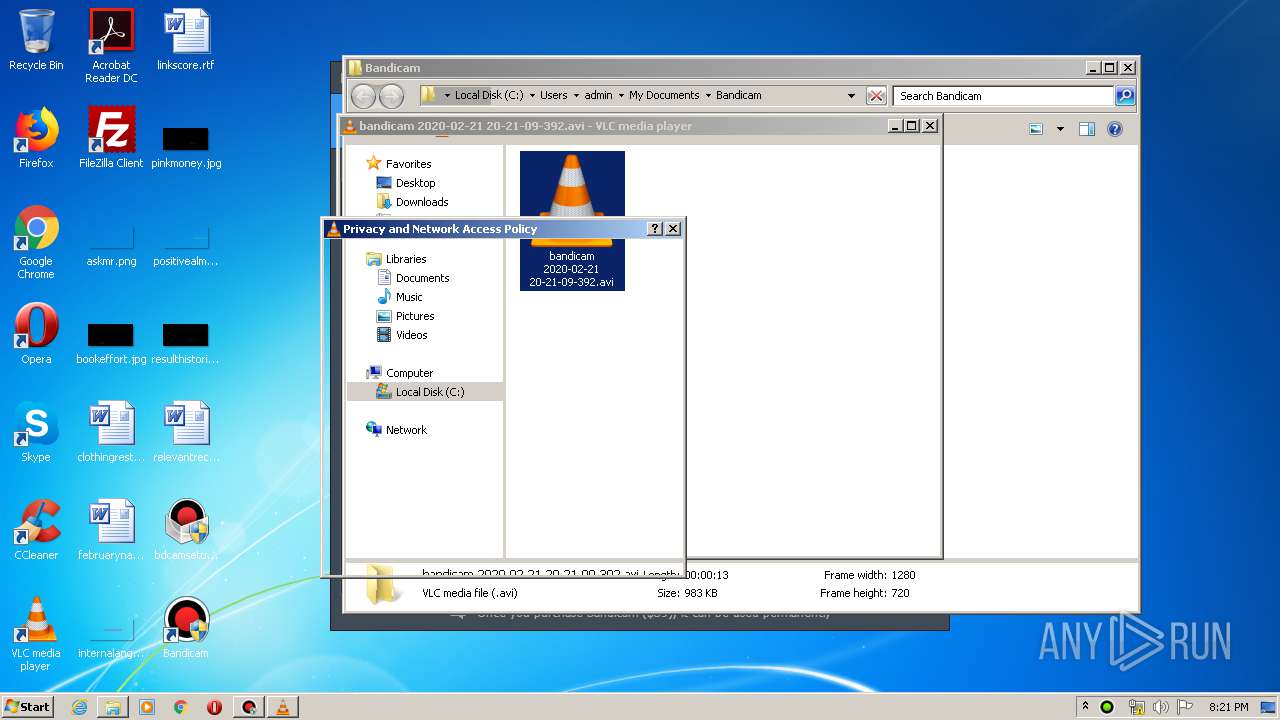
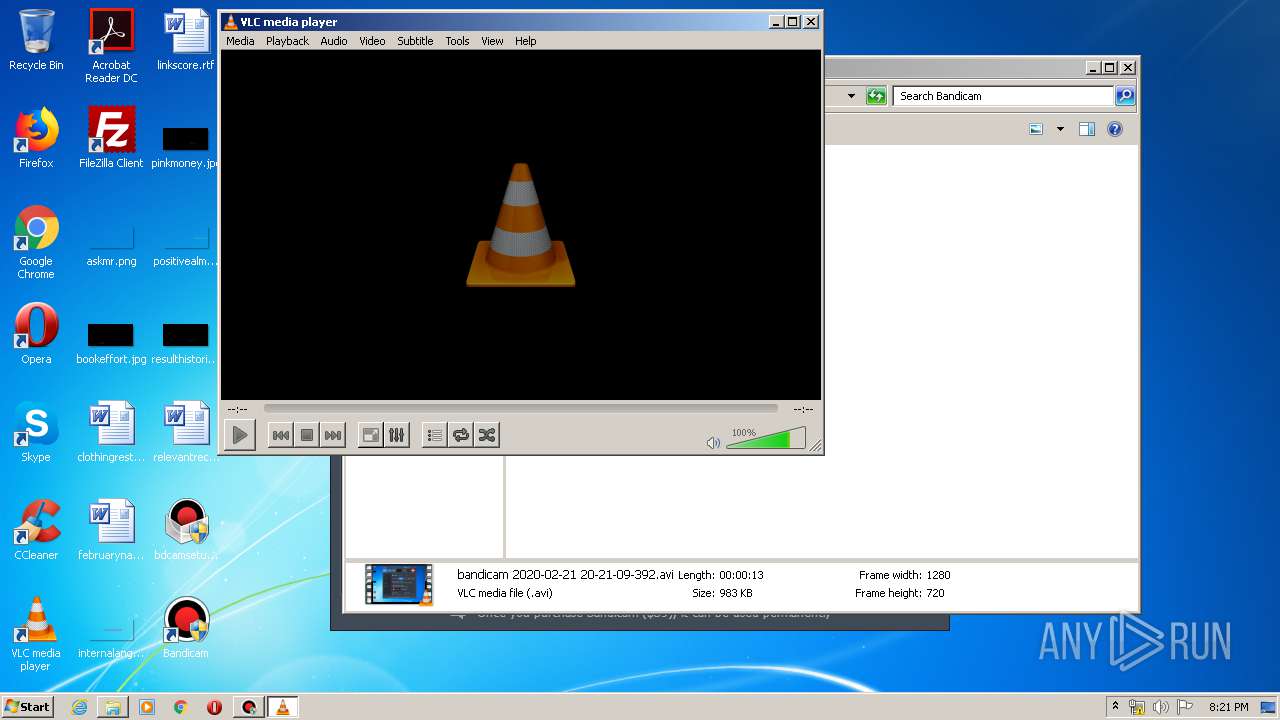
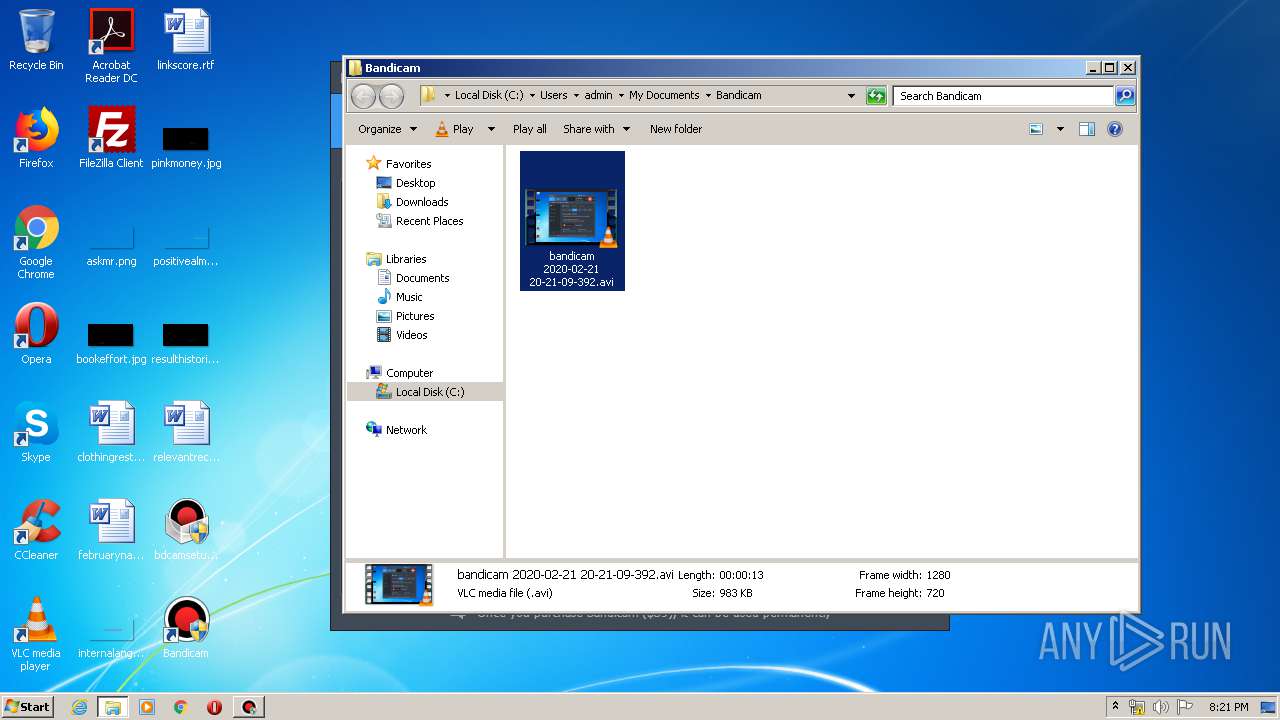
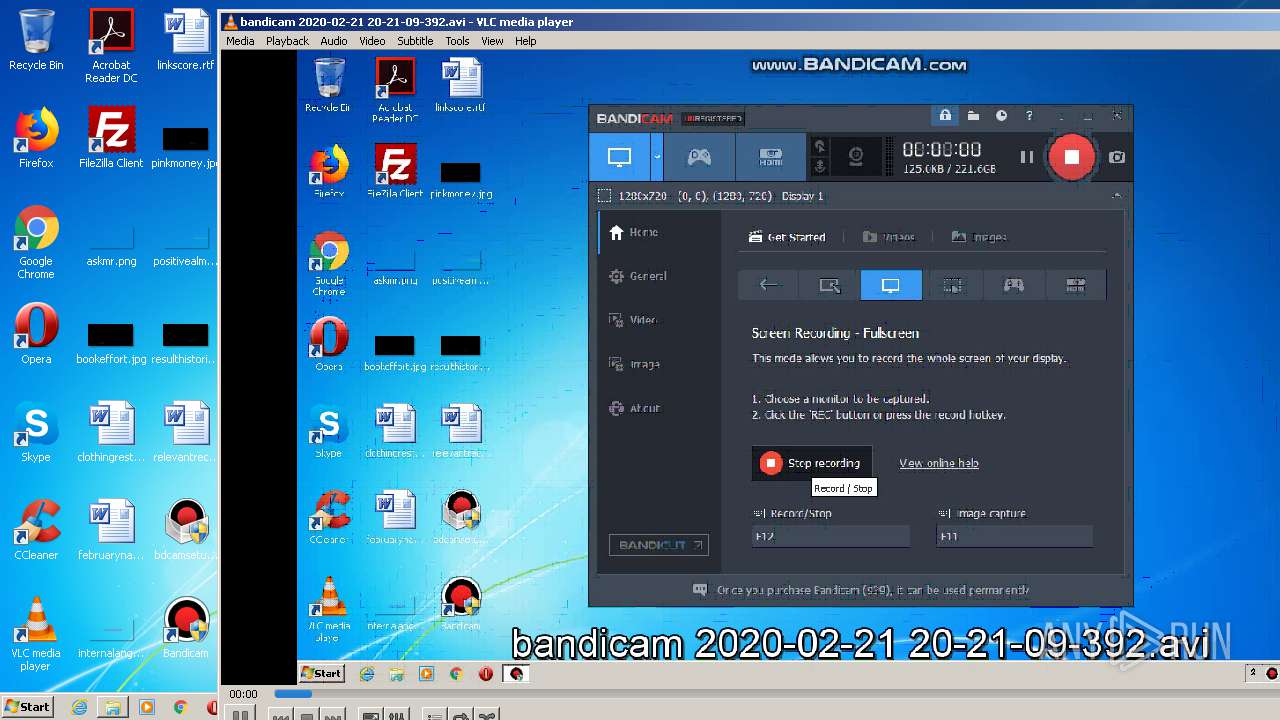
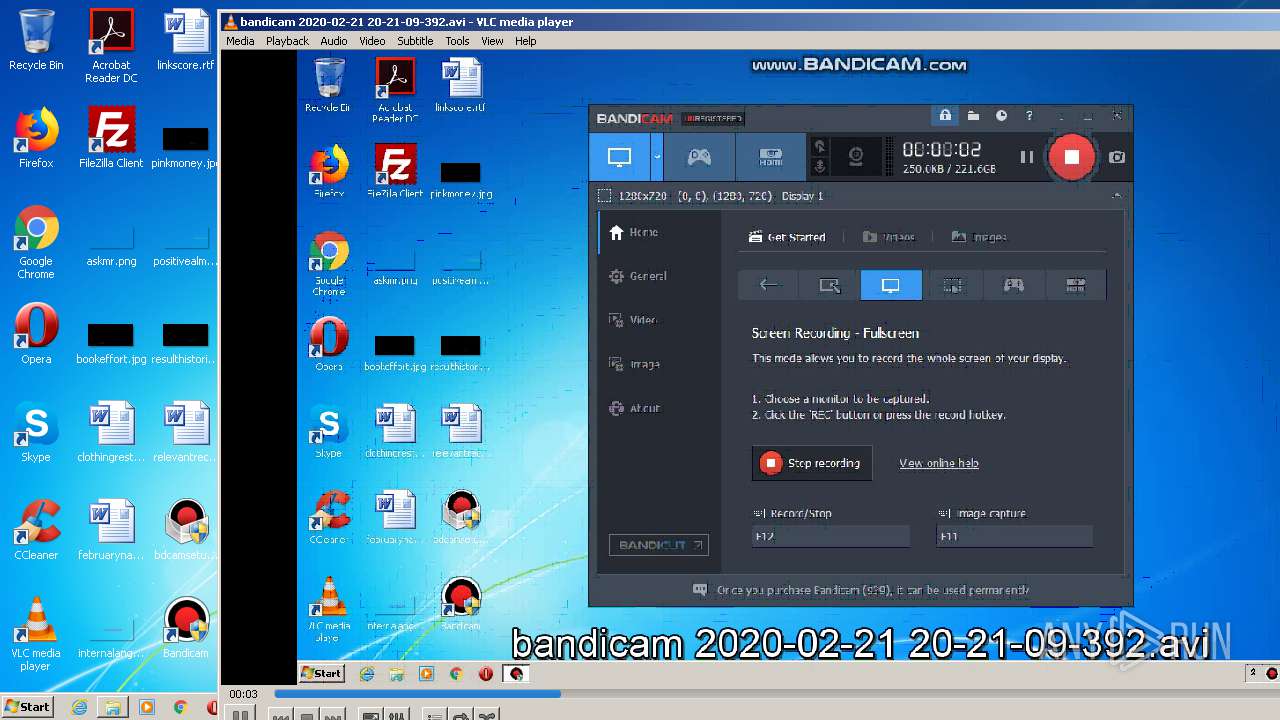
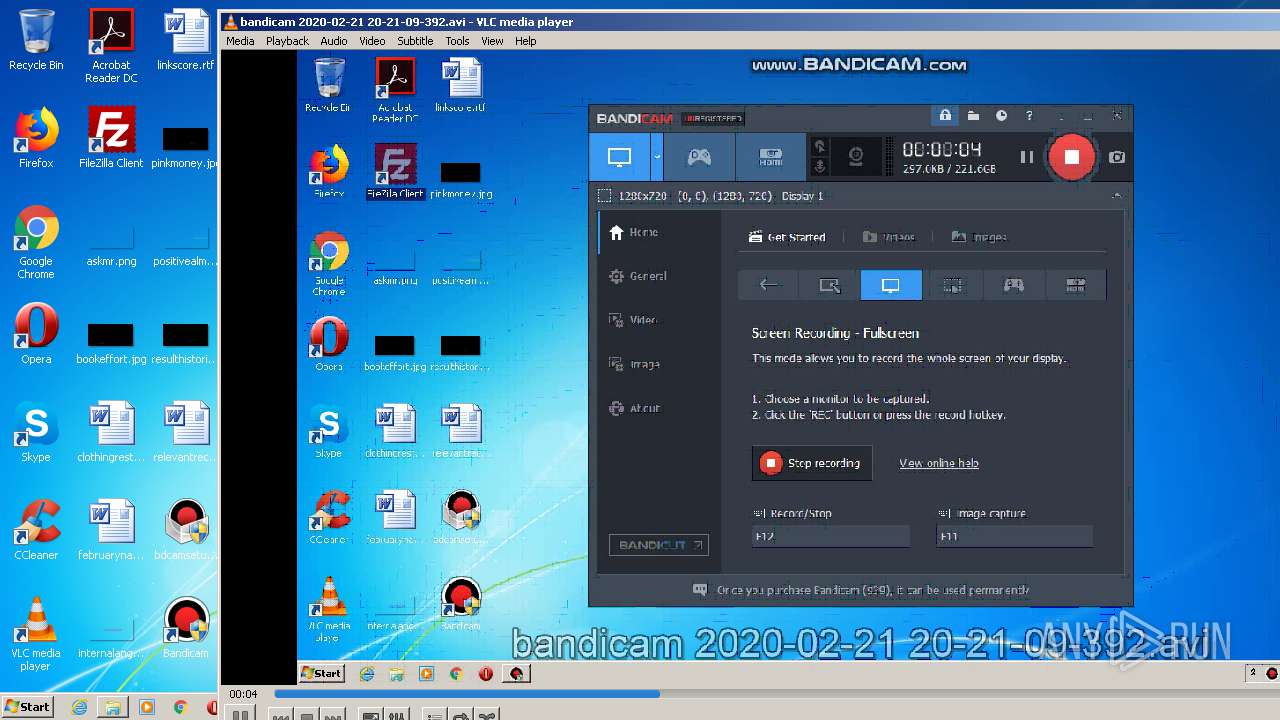
| 820 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\Documents\Bandicam\bandicam 2020-02-21 20-21-09-392.avi" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 1740 | "C:\Windows\system32\rundll32.exe" "C:\Program Files\Bandicam\bdcamvk32.dll",RegDll | C:\Windows\system32\rundll32.exe | — | bdcam.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1940 | "C:\Windows\system32\rundll32.exe" "C:\Program Files\Bandicam\bdcamvk32.dll",RegDll | C:\Windows\system32\rundll32.exe | — | bdcam.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.bandicam.com/f.php?id=eng_app_complete_install&v=2&lang=en | C:\Program Files\Internet Explorer\iexplore.exe | — | bdcamsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Bandicam\bdcam.exe" /install | C:\Program Files\Bandicam\bdcam.exe | — | bdcamsetup.exe | |||||||||||
User: admin Company: Bandicam Company Integrity Level: HIGH Description: Bandicam - bdcam.exe Exit code: 0 Version: 4.5.6.1647 Modules
| |||||||||||||||
| 2812 | "regsvr32" /s "C:\Program Files\BandiMPEG1\bdfilters64.dll" | C:\Windows\system32\regsvr32.exe | — | BDMPEG1SETUP.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | explorer.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 36, 0, 0 Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\BDMPEG1SETUP.EXE" /S | C:\Users\admin\AppData\Local\Temp\BDMPEG1SETUP.EXE | bdcamsetup.exe | ||||||||||||
User: admin Company: Bandicam Company Integrity Level: HIGH Description: Bandicam MPEG-1 Decoder Setup File Exit code: 0 Version: V1.0.5.17 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\Documents\Bandicam\bandicam 2020-02-21 20-21-09-392.avi" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\Desktop\bdcamsetup.exe" | C:\Users\admin\Desktop\bdcamsetup.exe | explorer.exe | ||||||||||||
User: admin Company: Bandicam Company Integrity Level: HIGH Description: Bandicam Setup File Exit code: 0 Version: 4.5.6.1647 Modules
| |||||||||||||||
Total events
4 672
Read events
2 187
Write events
2 481
Delete events
4
Modification events
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{89C4B786-A490-4A3E-AA70-E6A8C61D3689} |
| Operation: | write | Name: | |
Value: Bandicam MPEG-1 Video Decoder | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{89C4B786-A490-4A3E-AA70-E6A8C61D3689}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\BandiMPEG1\bdfilters.dll | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{89C4B786-A490-4A3E-AA70-E6A8C61D3689}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{A1C6833E-A3EC-4397-9FA9-151792F3408F} |
| Operation: | write | Name: | |
Value: Bandicam MPEG-1 Video Property | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{A1C6833E-A3EC-4397-9FA9-151792F3408F}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\BandiMPEG1\bdfilters.dll | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{A1C6833E-A3EC-4397-9FA9-151792F3408F}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E2E7539A-CECF-4A6A-B187-939943ECEF05} |
| Operation: | write | Name: | |
Value: Bandicam MPEG-1 Audio Decoder | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E2E7539A-CECF-4A6A-B187-939943ECEF05}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\BandiMPEG1\bdfilters.dll | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E2E7539A-CECF-4A6A-B187-939943ECEF05}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2976) BDMPEG1SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F4F5C9E9-CFCC-4C65-A8BD-0423A338F188} |
| Operation: | write | Name: | |
Value: Bandicam MPEG-1 Audio Property | |||
Executable files
25
Suspicious files
12
Text files
144
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | BDMPEG1SETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsiB466.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsbB138.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | bdcamsetup.exe | C:\Users\admin\AppData\Local\Temp\nsb8B22.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 3296 | bdcamsetup.exe | C:\Program Files\Bandicam\bdcam.exe | executable | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 2976 | BDMPEG1SETUP.EXE | C:\Windows\system32\bdmpega.acm | executable | |
MD5:9B3C54A9C49CA00F5A9DA7C7F84A57F9 | SHA256:940CFE50336B7865787EE94A7292AA9E38F4EC8714AE06E2969B76B473834CC2 | |||
| 3296 | bdcamsetup.exe | C:\Users\admin\AppData\Local\Temp\nsb8B22.tmp\LangDLL.dll | executable | |
MD5:F1E9EED02DB3A822A7DDEF0C724E5F1F | SHA256:6DFF504C6759C418C6635C9B25B8C91D0D9EF7787A3A93610D7670BB563C09DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | bdcam.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
3308 | bdcam.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
3188 | vlc.exe | GET | 206 | 88.191.250.2:80 | http://update.videolan.org/vlc/status-win-x86 | FR | text | 287 b | malicious |
3188 | vlc.exe | GET | 206 | 88.191.250.2:80 | http://update.videolan.org/vlc/status-win-x86.asc | FR | asc | 195 b | malicious |
3308 | bdcam.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3308 | bdcam.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | bdcam.exe | 151.101.2.217:443 | www.bandicam.com | Fastly | US | suspicious |
3308 | bdcam.exe | 151.101.2.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
3308 | bdcam.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3308 | bdcam.exe | 172.217.16.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3188 | vlc.exe | 88.191.250.2:80 | update.videolan.org | Free SAS | FR | malicious |
3828 | iexplore.exe | 151.101.2.217:443 | www.bandicam.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bandicam.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
update.videolan.org |
| unknown |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | core libvlc: Status file authenticated
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|