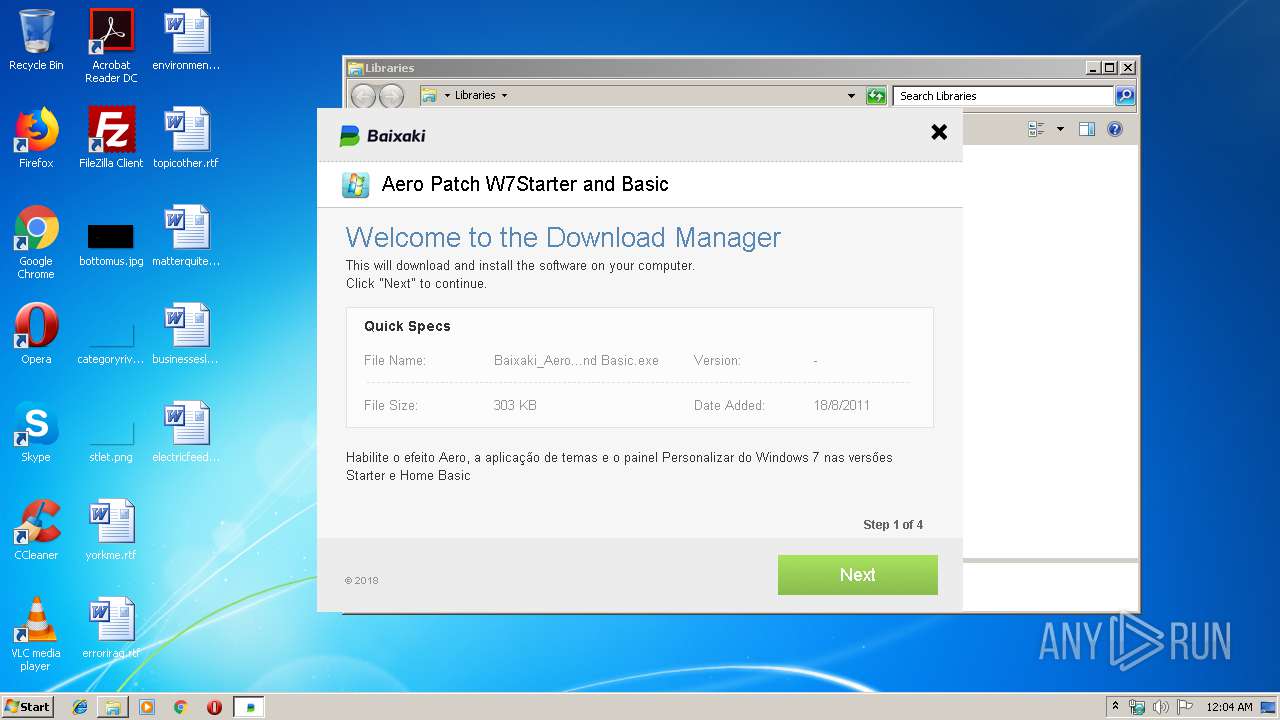
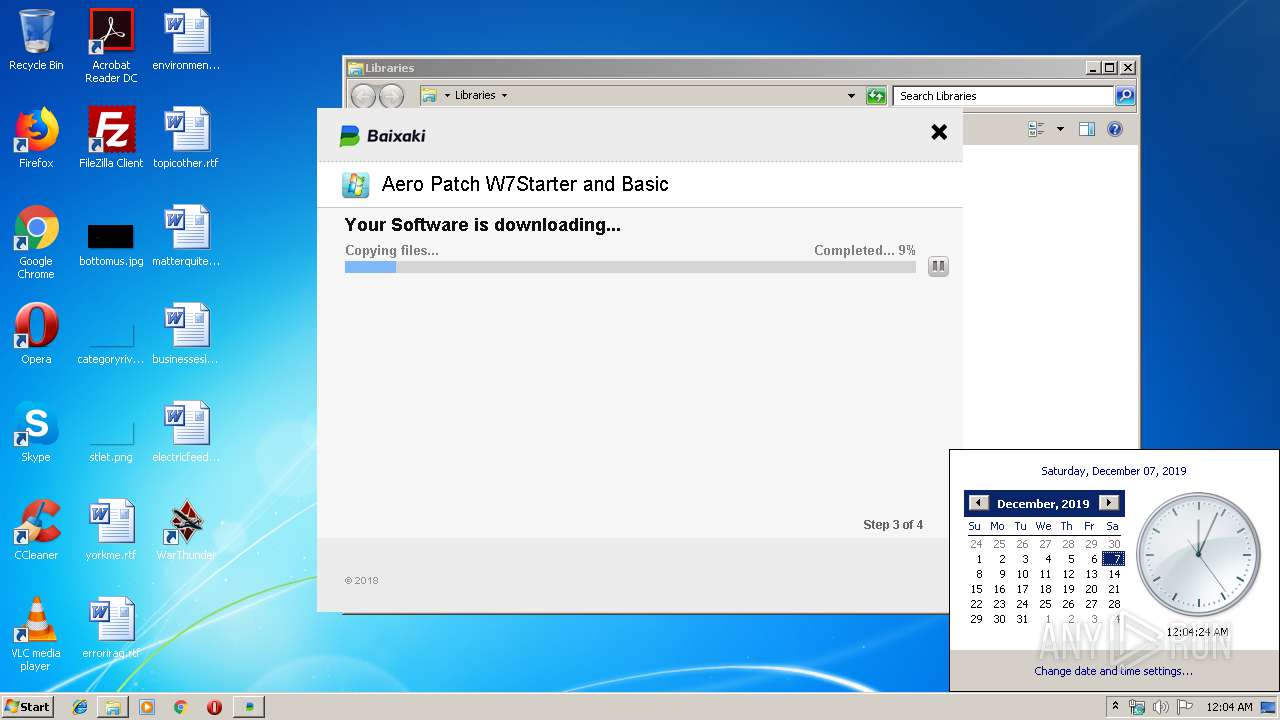
| File name: | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe |
| Full analysis: | https://app.any.run/tasks/4b35be8b-369e-448c-9a42-52c68633d3ab |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2019, 00:03:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5C6CF8272BDB8AC517F990630A7149A1 |
| SHA1: | 06EBD0730D852D25329D21BC6400D027F915D984 |
| SHA256: | C21F704455CCE6455B7011C047FFCF8A3FBB7A0E5D3E358133F2E0E562C07D76 |
| SSDEEP: | 49152:mmCh3EiithV3HppQTyQRnQs4e7kV6upG0b1k03A/R/YrJ:bC6i+zHLQRR+mmJQ/R |
MALICIOUS
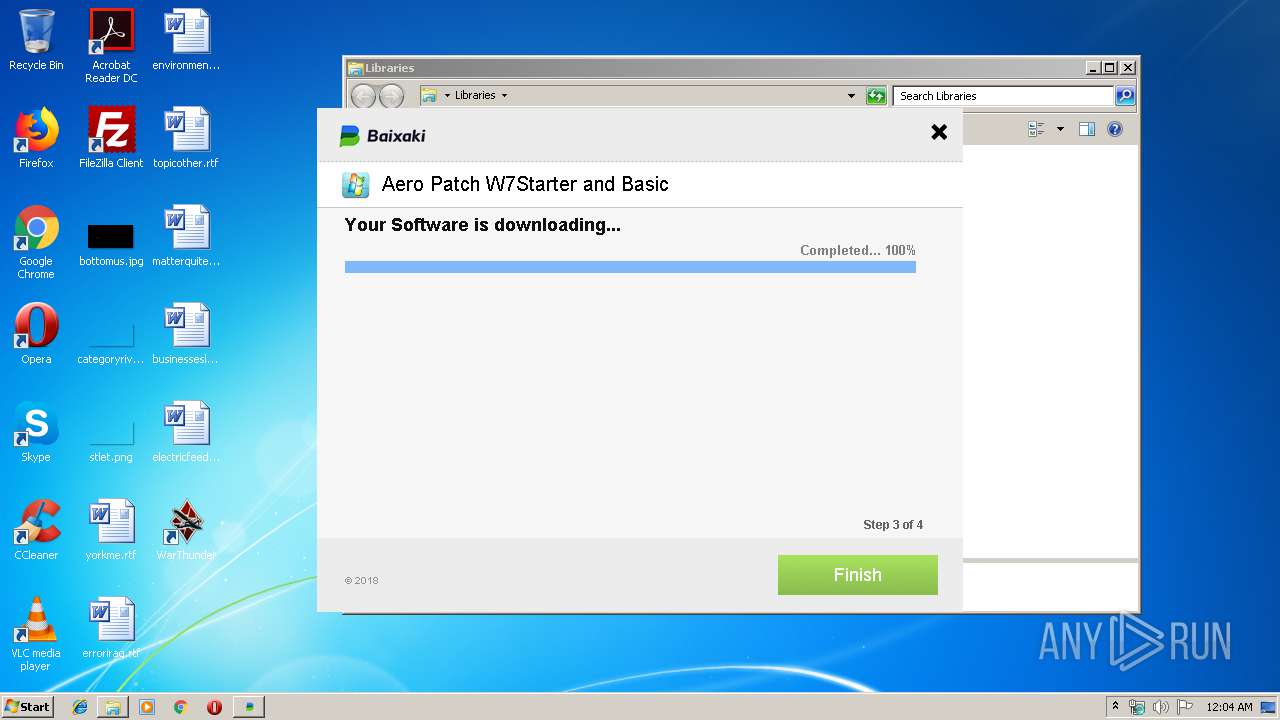
Loads dropped or rewritten executable
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
Loads the Task Scheduler COM API
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
SUSPICIOUS
Application launched itself
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2788)
Reads internet explorer settings
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
Executable content was dropped or overwritten
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
Reads Environment values
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
Creates files in the user directory
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
Creates a software uninstall entry
- Baixaki_Aero Patch W7Starter and Basic_1846101744.exe (PID: 2760)
INFO
Reads the hosts file
- chrome.exe (PID: 3624)
- chrome.exe (PID: 3984)
Manual execution by user
- explorer.exe (PID: 3744)
Changes settings of System certificates
- chrome.exe (PID: 3984)
Application launched itself
- chrome.exe (PID: 3624)
Adds / modifies Windows certificates
- chrome.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:08 07:01:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 87552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Web prog Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Web prog |
| ProductVersion: | 3.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2018 05:01:01 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Web prog Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Web prog |
| ProductVersion: | 3.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 08-Jun-2018 05:01:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38388 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.78081 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00013490 | 0x00013600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.90599 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.84163 | 6424 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.93418 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.95427 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
58
Monitored processes
20
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14115912570714665783 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13262631416361683438 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1506240923610846866 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14821489411487389471 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6450864976334498176 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9531498541686084180 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12719549866802914975 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\AppData\Local\Temp\Baixaki_Aero Patch W7Starter and Basic_1846101744.exe" /RSF /ppn:YyhwYgxaFRAiP211FM5W /mnl | C:\Users\admin\AppData\Local\Temp\Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Web prog Setup Exit code: 4294967295 Version: Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Local\Temp\Baixaki_Aero Patch W7Starter and Basic_1846101744.exe" | C:\Users\admin\AppData\Local\Temp\Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Web prog Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3172516202212938170,958102283234539710,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13638531708048714604 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
933
Read events
837
Write events
93
Delete events
3
Modification events
| (PID) Process: | (2788) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1528434061 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Baixaki_Aero Patch W7Starter and Basic_1846101744_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Baixaki_Aero Patch W7Starter and Basic_1846101744_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2760) Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Baixaki_Aero Patch W7Starter and Basic_1846101744_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
104
Text files
114
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\0039C965.log | — | |
MD5:— | SHA256:— | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\ie6_main.css | text | |
MD5:C628398EC07FE762971FC9ED90902340 | SHA256:46E335ECA724C6CB93334B15A793710FA2C0A544B7D887A2F63FF65185D07821 | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\sdk-ui\button.css | text | |
MD5:37E1FF96E084EC201F0D95FEEF4D5E94 | SHA256:8E806F5B94FC294E918503C8053EF1284E4F4B1E02C7DA4F4635E33EC33E0534 | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\sdk-ui\checkbox.css | text | |
MD5:64773C6B0E3413C81AEBC46CCE8C9318 | SHA256:B09504C1BF0486D3EC46500592B178A3A6C39284672AF8815C3687CC3D29560D | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\sdk-ui\images\progress-bg.png | image | |
MD5:E9F12F92A9EEB8EBE911080721446687 | SHA256:C1CF449536BC2778E27348E45F0F53D04C284109199FB7A9AF7A61016B91F8BC | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\sdk-ui\images\progress-bg-corner.png | image | |
MD5:608F1F20CD6CA9936EAA7E8C14F366BE | SHA256:86B6E6826BCDE2955D64D4600A4E01693522C1FDDF156CE31C4BA45B3653A7BD | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\css\main.css | text | |
MD5:EB40D3236AD8892F8603A10622DA1E63 | SHA256:D3EBE309B2F9A973C1F17505E432E546F00EE2594351BCA68C68193A6E418796 | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\inH378710917544\images\Button_Hover.png | image | |
MD5:795C6DC6CFE3049B93BDBB36DAAE209E | SHA256:18F462F4D6491D3B4318BC569206F44F9E35BF1B86B06998E4472D693D4FE62A | |||
| 2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | C:\Users\admin\AppData\Local\Temp\0039CC14.log | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
84
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | HEAD | 200 | 185.59.222.148:80 | http://bbs.tepit-muva.com/ofr/Solululadul/icut_v2_2 | NL | — | — | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | HEAD | 200 | 185.59.222.148:80 | http://bbs.tepit-muva.com/ofr/Webinebinec/Webinebinec_Links_13Oct15 | NL | — | — | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | HEAD | 200 | 185.59.222.148:80 | http://bbs.tepit-muva.com/ofr/Solululadul/osutils | NL | — | — | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | HEAD | 200 | 185.59.222.148:80 | http://bbs.tepit-muva.com/ofr/Niniwic/YL/Niniwic_yl_10Apr16 | NL | — | — | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | POST | 200 | 52.212.215.62:80 | http://vps.tepit-muva.com/ | IE | binary | 615 Kb | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | GET | 200 | 199.115.112.67:80 | http://ww1.tepit-muva.com/img/Sibarasawi/logo_comp.png | US | image | 12.4 Kb | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | GET | 200 | 199.115.112.67:80 | http://ww1.tepit-muva.com/img/Sibarasawi/bg_comp.png | US | image | 25.2 Kb | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | POST | 200 | 52.51.217.55:80 | http://cdn.tepit-muva.com/ | IE | — | — | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | HEAD | 200 | 199.115.112.67:80 | http://ww1.tepit-muva.com/ofr/Niniwic/YL/Niniwic_Tefenece_12Apr16 | US | image | 25.2 Kb | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | GET | 200 | 199.115.112.67:80 | http://ww1.tepit-muva.com/ofr/Niniwic/YL/Niniwic_yl_10Apr16 | US | binary | 8.93 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 54.246.196.116:80 | vpn.tepit-muva.com | Amazon.com, Inc. | IE | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 52.51.217.55:80 | cdn.tepit-muva.com | Amazon.com, Inc. | IE | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 52.212.215.62:80 | vps.tepit-muva.com | Amazon.com, Inc. | IE | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 151.80.204.60:443 | img.ibxk.com.br | OVH SAS | FR | unknown |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 199.115.112.67:80 | ww1.tepit-muva.com | Leaseweb USA, Inc. | US | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 185.59.222.148:80 | bbs.tepit-muva.com | Datacamp Limited | NL | malicious |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 54.148.202.127:80 | fc03.deviantart.net | Amazon.com, Inc. | US | unknown |
2760 | Baixaki_Aero Patch W7Starter and Basic_1846101744.exe | 52.34.182.205:80 | orig07.deviantart.net | Amazon.com, Inc. | US | unknown |
3984 | chrome.exe | 151.80.204.60:80 | img.ibxk.com.br | OVH SAS | FR | unknown |
3984 | chrome.exe | 151.80.204.60:443 | img.ibxk.com.br | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.tepit-muva.com |
| malicious |
vpn.tepit-muva.com |
| malicious |
vps.tepit-muva.com |
| malicious |
img.ibxk.com.br |
| suspicious |
ww1.tepit-muva.com |
| malicious |
bbs.tepit-muva.com |
| malicious |
fc03.deviantart.net |
| unknown |
orig07.deviantart.net |
| unknown |
clientservices.googleapis.com |
| whitelisted |
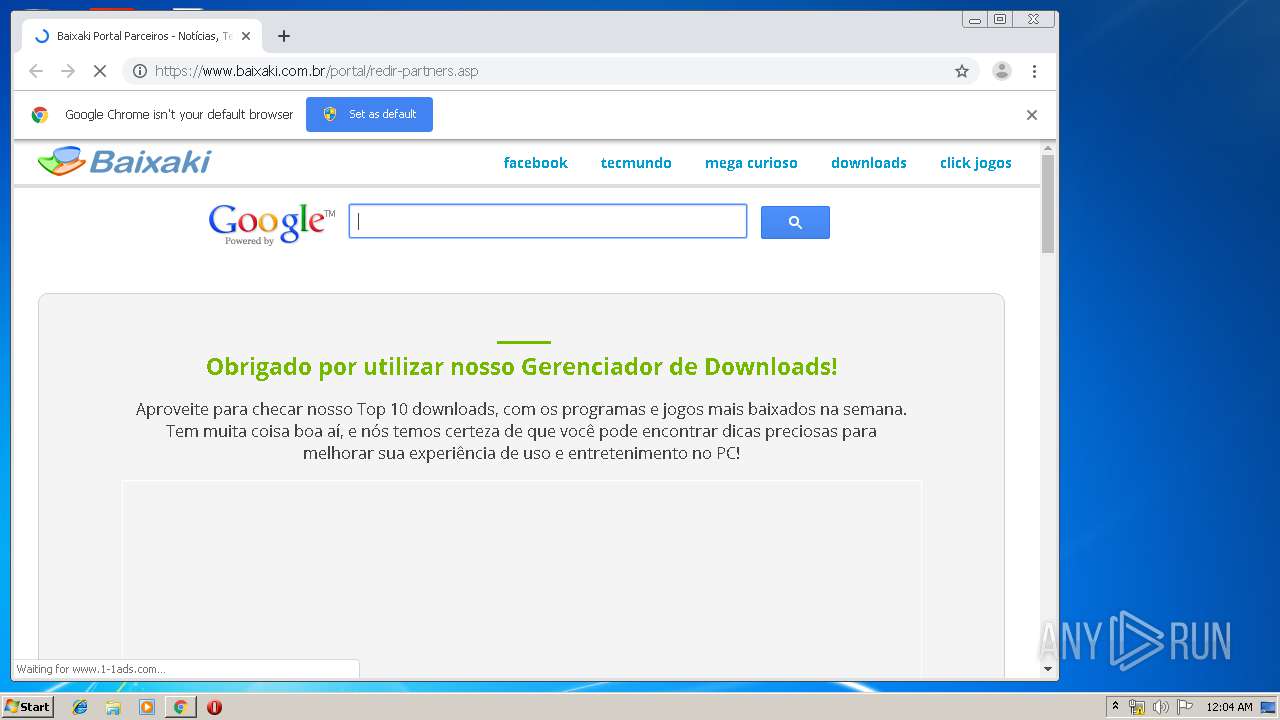
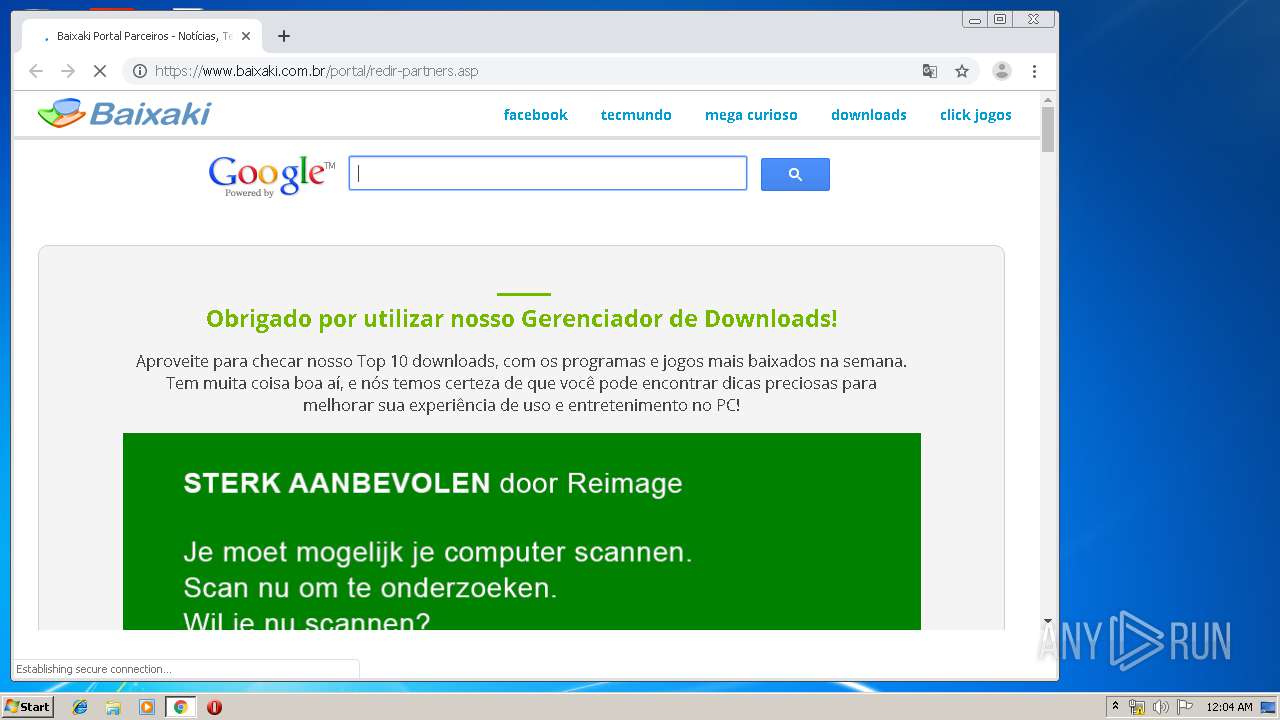
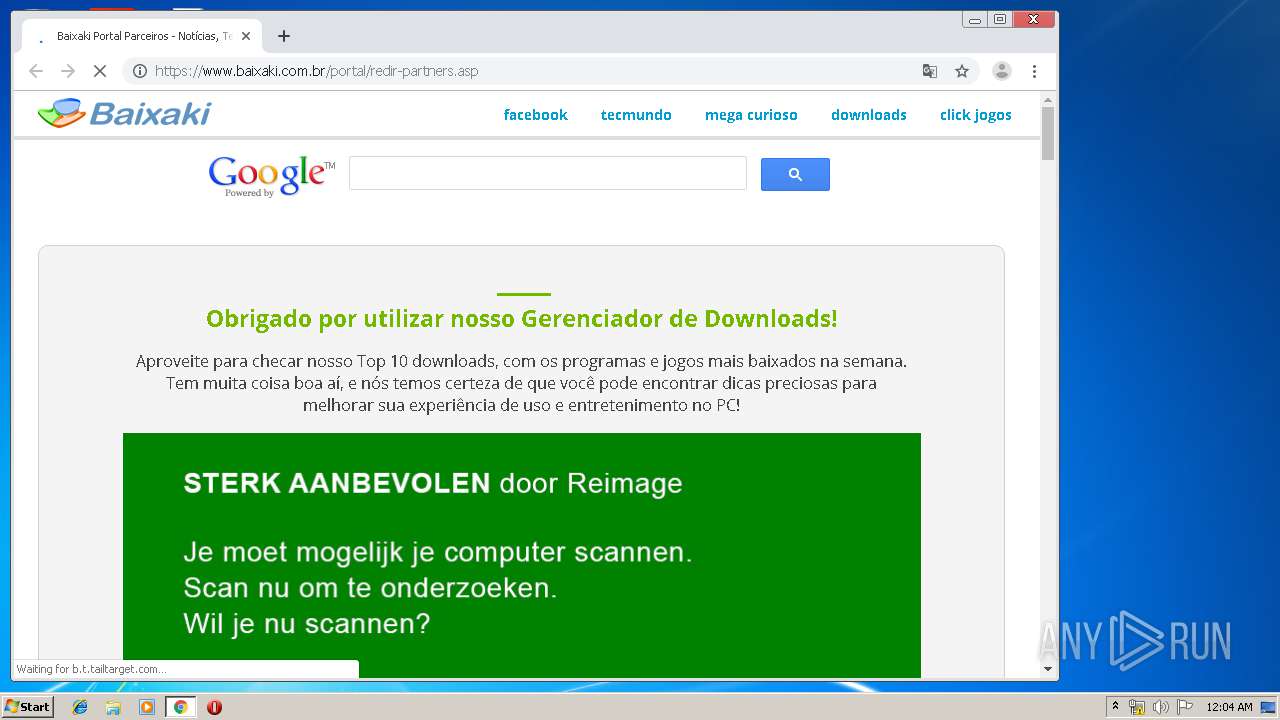
www.baixaki.com.br |
| suspicious |