| File name: | WPD.exe |
| Full analysis: | https://app.any.run/tasks/a2154d40-a9bc-4bbf-98be-699450d25f0b |
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2023, 02:39:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 65325F636AC238568A21F389387F0299 |
| SHA1: | ACF8022648F3EAB3B6DA50E0F90301EEFE64A3F7 |
| SHA256: | C21E9DE5B28DE8EDFB6B2264B33846E842F7954AD70FA07B3C652FEB5F0A09D7 |
| SSDEEP: | 6144:TRQucww8JJQLbRYX3XJ7Sjt52vljOwsxVDC5Mq7Zj2R7beOW2wmIyWk5QoBN6Z6l:1cwoQkl2JID |
MALICIOUS
No malicious indicators.SUSPICIOUS
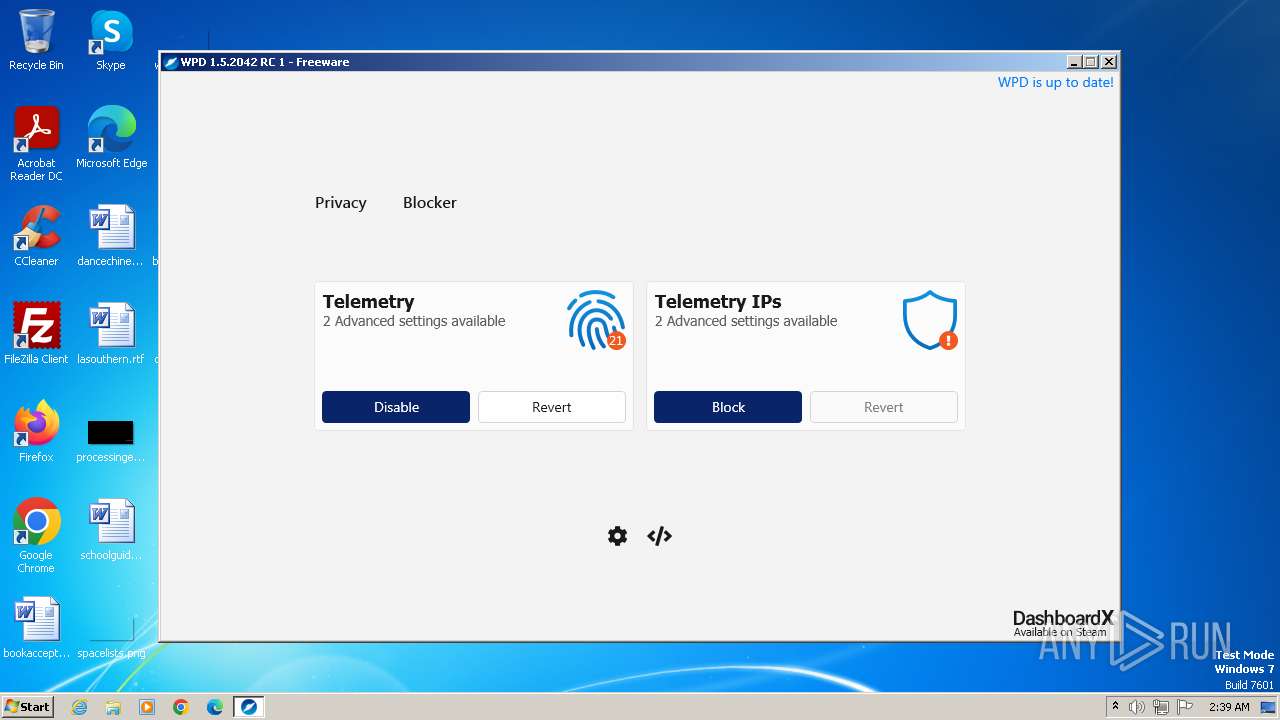
Reads settings of System Certificates
- WPD.exe (PID: 1668)
Reads the Internet Settings
- WPD.exe (PID: 1668)
Executes as Windows Service
- VSSVC.exe (PID: 2316)
INFO
Checks supported languages
- WPD.exe (PID: 1668)
- wmpnscfg.exe (PID: 2364)
Reads product name
- WPD.exe (PID: 1668)
Reads the computer name
- WPD.exe (PID: 1668)
- wmpnscfg.exe (PID: 2364)
Manual execution by a user
- wmpnscfg.exe (PID: 2364)
Reads the machine GUID from the registry
- WPD.exe (PID: 1668)
- wmpnscfg.exe (PID: 2364)
Reads Environment values
- WPD.exe (PID: 1668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:17 21:43:37+02:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 515584 |
| InitializedDataSize: | 74240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7fcd2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.2042.0 |
| ProductVersionNumber: | 1.5.2042.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Just the best privacy tweaker for Windows 10 |
| CompanyName: | https://wpd.app |
| FileDescription: | WPD |
| FileVersion: | 1.5.2042 |
| InternalName: | WPD.exe |
| LegalCopyright: | Copyright © 2021 Barnacle, Vegetorius |
| LegalTrademarks: | - |
| OriginalFileName: | WPD.exe |
| ProductName: | WPD |
| ProductVersion: | 1.5.2042 |
| AssemblyVersion: | 1.5.2042.0 |
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\AppData\Local\Temp\WPD.exe" | C:\Users\admin\AppData\Local\Temp\WPD.exe | — | explorer.exe | |||||||||||
User: admin Company: https://wpd.app Integrity Level: MEDIUM Description: WPD Exit code: 3221226540 Version: 1.5.2042 Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Local\Temp\WPD.exe" | C:\Users\admin\AppData\Local\Temp\WPD.exe | explorer.exe | ||||||||||||
User: admin Company: https://wpd.app Integrity Level: HIGH Description: WPD Exit code: 0 Version: 1.5.2042 Modules
| |||||||||||||||
| 1952 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 790
Read events
3 770
Write events
17
Delete events
3
Modification events
| (PID) Process: | (1668) WPD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (1668) WPD.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1952) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4000000000000000115B265700B2D301CC070000E40D0000D2070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1952) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4000000000000000115B265700B2D301CC070000E40D0000D2070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1952) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4000000000000000115B265700B2D301CC070000E40D0000D1070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1952) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4000000000000000115B265700B2D301CC070000E40D0000D1070000010000000000000001000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2364) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{979721F6-D374-4AE1-8E39-B013E7222227}\{E1C75640-6A89-47B3-A17F-E4C21F153AD0} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2364) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{979721F6-D374-4AE1-8E39-B013E7222227} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2364) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{C47F252A-B3FB-40AF-B19D-2756DB8D4DF1} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1668 | WPD.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:FED929AE34422010496B5B4A1827A501 | SHA256:2DDA40A266ECA9DDD736701EFA24C6FE186EDD6737DB7BF52BFFE32D614667ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1668 | WPD.exe | 104.21.94.155:443 | wpd.app | CLOUDFLARENET | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wpd.app |
| unknown |