| File name: | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe |
| Full analysis: | https://app.any.run/tasks/51f37b94-d551-4980-bb02-70bef99b79da |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 01:17:22 |
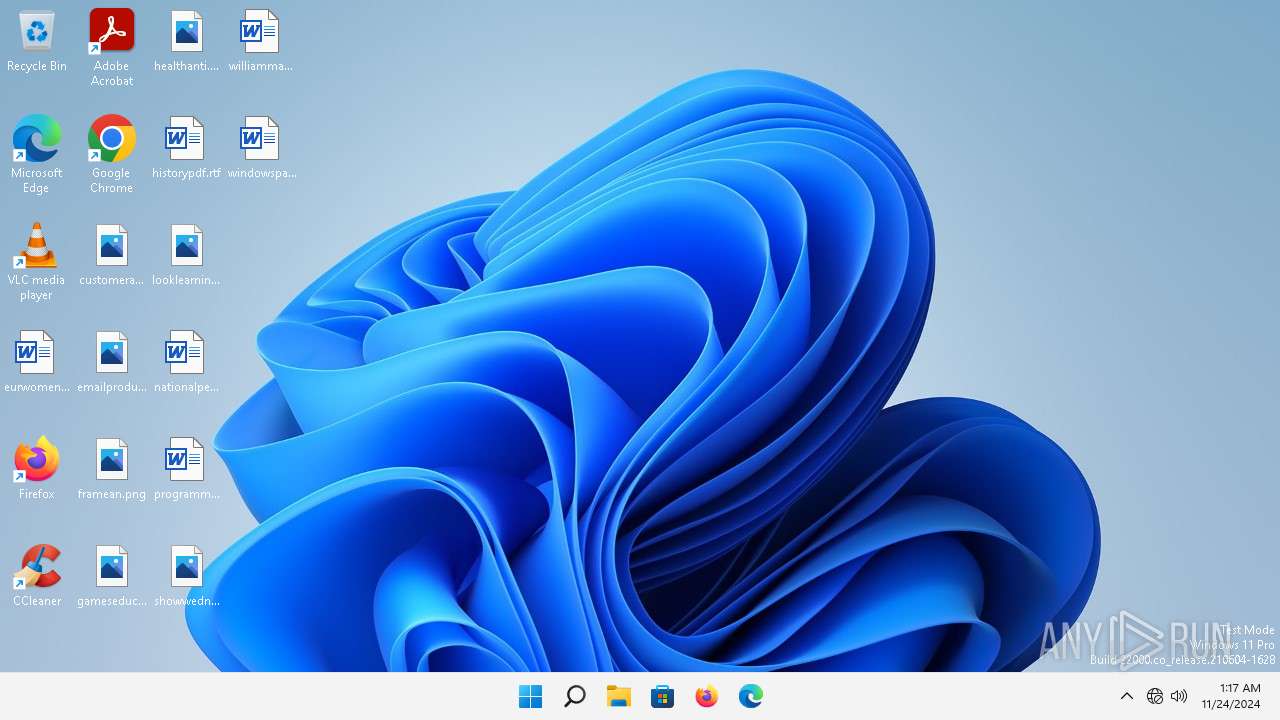
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed, 4 sections |
| MD5: | 23BD4BB28CD4E4C6C6BF99DBF42D717B |
| SHA1: | F07ED34A5D978880A78C9054DB9B11FABDCDFE01 |
| SHA256: | C219E1BF1F0E9A7538CFAE556EE942B829FA76770DD18339C1434543D863274C |
| SSDEEP: | 6144:CXqVs6VCP7VhRtCPoHDARle+RLl+Up5j+axi+qPB:CXMszVhaPG0leQLl+Up5j1i+aB |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 5960)
SUSPICIOUS
Reads security settings of Internet Explorer
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Starts CMD.EXE for commands execution
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Probably fake Windows Update
- reg.exe (PID: 5960)
Executing commands from a ".bat" file
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4796)
Probably fake Windows Update file has been dropped
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Reads the Internet Settings
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Executable content was dropped or overwritten
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
INFO
Create files in a temporary directory
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Reads the computer name
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Checks supported languages
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
The process uses the downloaded file
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Creates files or folders in the user directory
- c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe (PID: 5248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (56.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (19) |
| .exe | | | UPX compressed Win32 Executable (18.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Generic Win/DOS Executable (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:02:26 02:03:02+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 638976 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 991232 |
| EntryPoint: | 0x10c4 |
| OSVersion: | 4 |
| ImageVersion: | 31.9 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 31.9.0.7 |
| ProductVersionNumber: | 31.9.0.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | NYWZLFQEC |
| CompanyName: | CITIUPIBA |
| FileDescription: | VWTLUHEKD |
| ProductName: | ROMSBFGEA |
| FileVersion: | 31.09.0007 |
| ProductVersion: | 31.09.0007 |
| InternalName: | hyaogec |
| OriginalFileName: | hyaogec.exe |
Total processes
114
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1656 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2668 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4796 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\XVQPK.bat" " | C:\Windows\SysWOW64\cmd.exe | — | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5248 | "C:\Users\admin\Desktop\c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe" | C:\Users\admin\Desktop\c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | explorer.exe | ||||||||||||
User: admin Company: CITIUPIBA Integrity Level: MEDIUM Description: VWTLUHEKD Version: 31.09.0007 Modules
| |||||||||||||||
| 5960 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "Window Updates" /t REG_SZ /d "C:\Users\admin\AppData\Roaming\Windows Update\winupdt.exe" /f | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 903
Read events
1 894
Write events
9
Delete events
0
Modification events
| (PID) Process: | (5248) c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5248) c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5248) c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5248) c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5960) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Window Updates |
Value: C:\Users\admin\AppData\Roaming\Windows Update\winupdt.exe | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5248 | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | C:\Users\admin\AppData\Local\Temp\XVQPK.bat | text | |
MD5:7C0DA86D75FAC7AAA6A8B6739493B7BD | SHA256:3930401762D7F33C0170FC296A6AE3BAE549239FDDF048042E24A31C8987B2A4 | |||
| 5248 | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | C:\Users\admin\AppData\Roaming\Windows Update\winupdt.txt | executable | |
MD5:23BD4BB28CD4E4C6C6BF99DBF42D717B | SHA256:C219E1BF1F0E9A7538CFAE556EE942B829FA76770DD18339C1434543D863274C | |||
| 5248 | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | C:\Users\admin\AppData\Roaming\Windows Update\winupdt.exe | executable | |
MD5:64EFFAC64CFE8B9AD687F68A56DDC872 | SHA256:191CCDC94E8A76309A450A2B9FAE4F63B4018EEEB14B881C65E5CA33A69411CB | |||
| 5248 | c219e1bf1f0e9a7538cfae556ee942b829fa76770dd18339c1434543d863274c.exe | C:\Users\admin\AppData\Local\Temp\XVQPK.txt | text | |
MD5:7C0DA86D75FAC7AAA6A8B6739493B7BD | SHA256:3930401762D7F33C0170FC296A6AE3BAE549239FDDF048042E24A31C8987B2A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
25
DNS requests
39
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
436 | MoUsoCoreWorker.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?28f4436f070816ed | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.4:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3732 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3732 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3732 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 184.30.17.174:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
3732 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ca35b9155f2b6b6f | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?0811ccc60b3de69d | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?a32176130b135011 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
6136 | OfficeC2RClient.exe | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
— | — | 184.24.77.4:80 | — | Akamai International B.V. | DE | unknown |
3732 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
3732 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
436 | MoUsoCoreWorker.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
6136 | OfficeC2RClient.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2852 | OfficeClickToRun.exe | 52.109.89.117:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |
1656 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servequake .com |