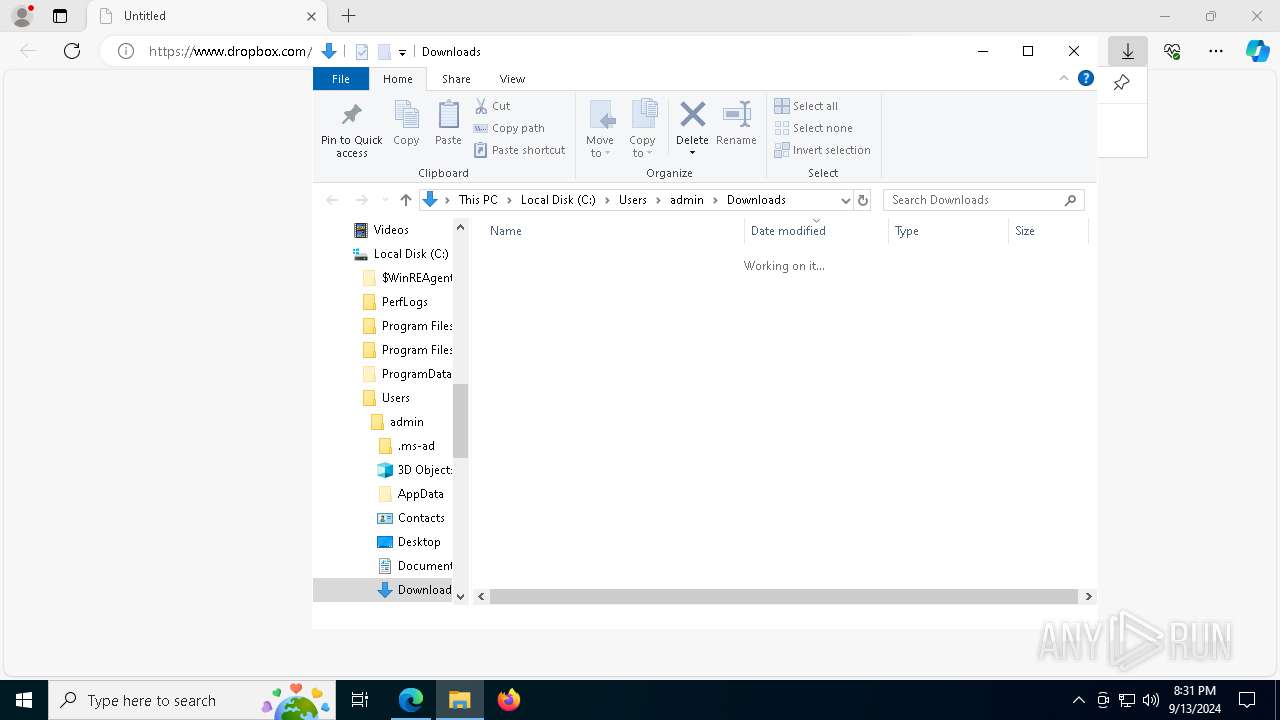
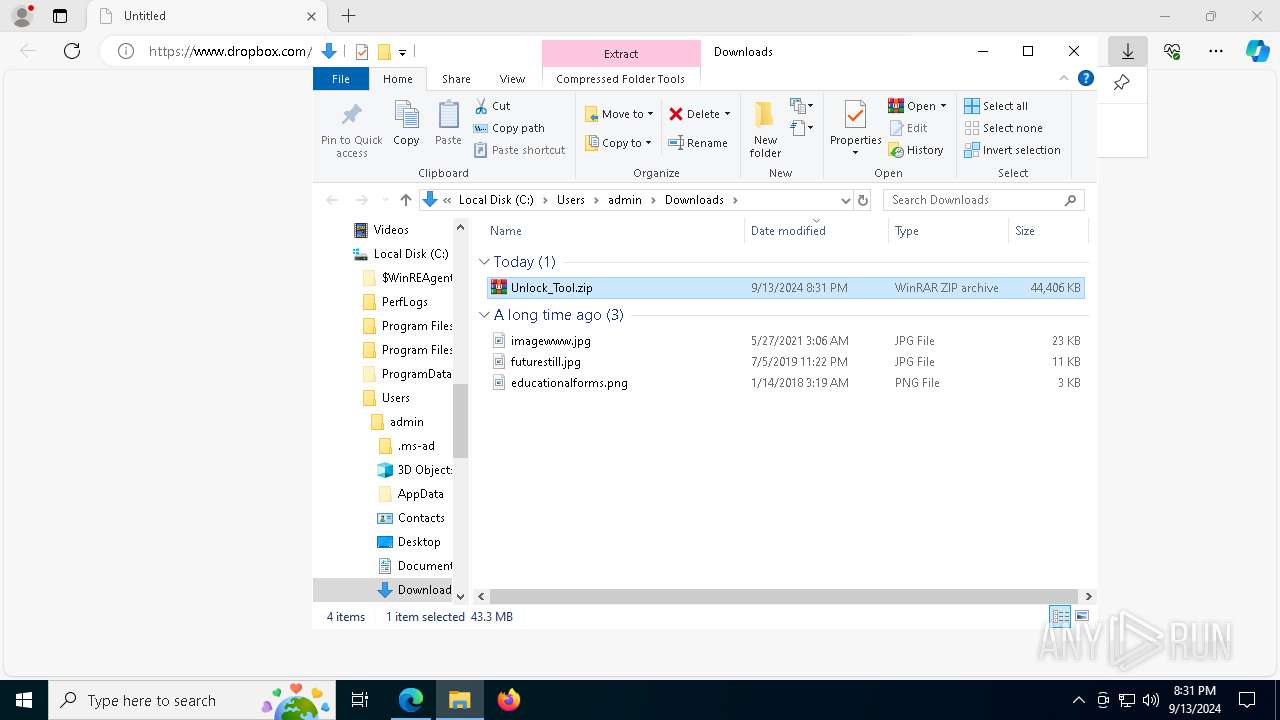
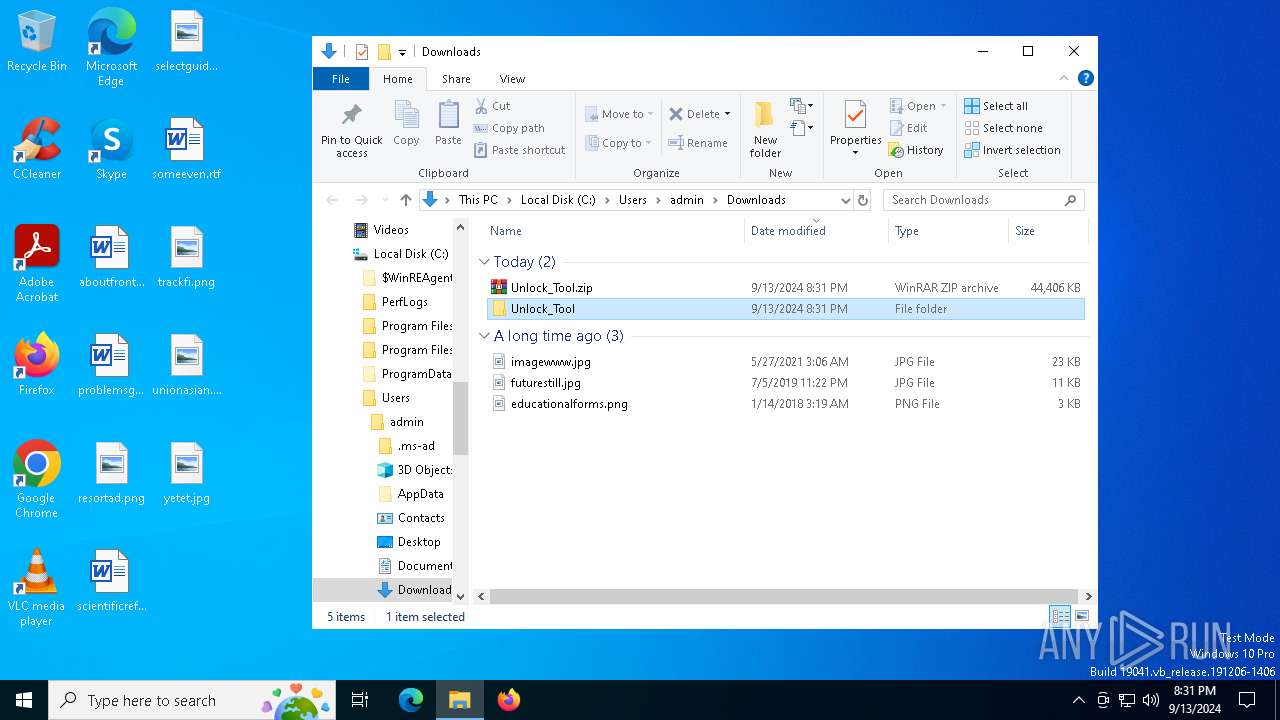
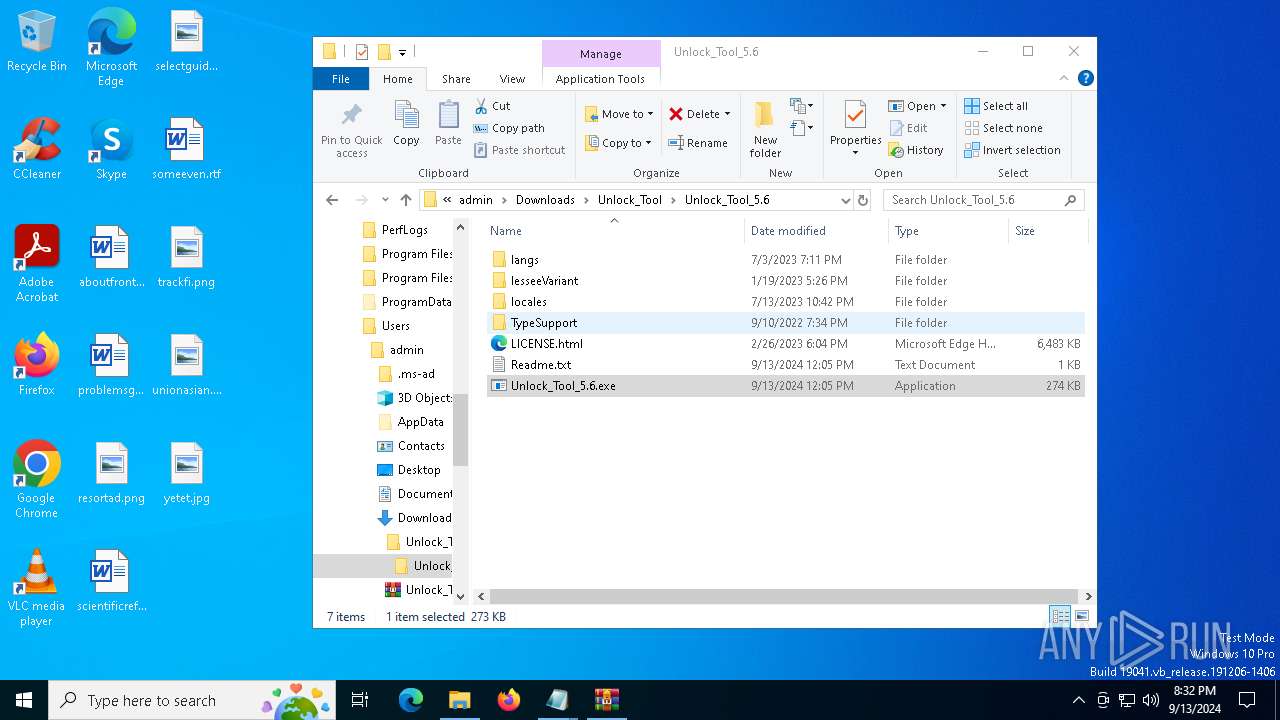
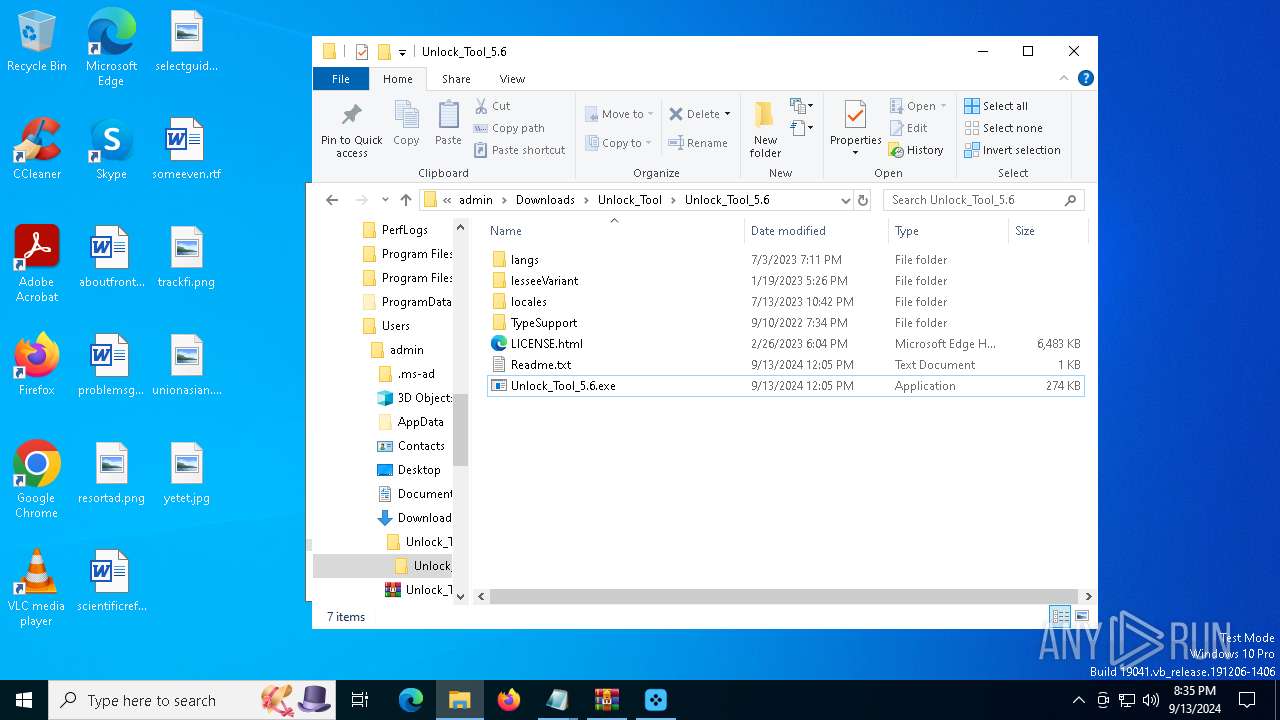
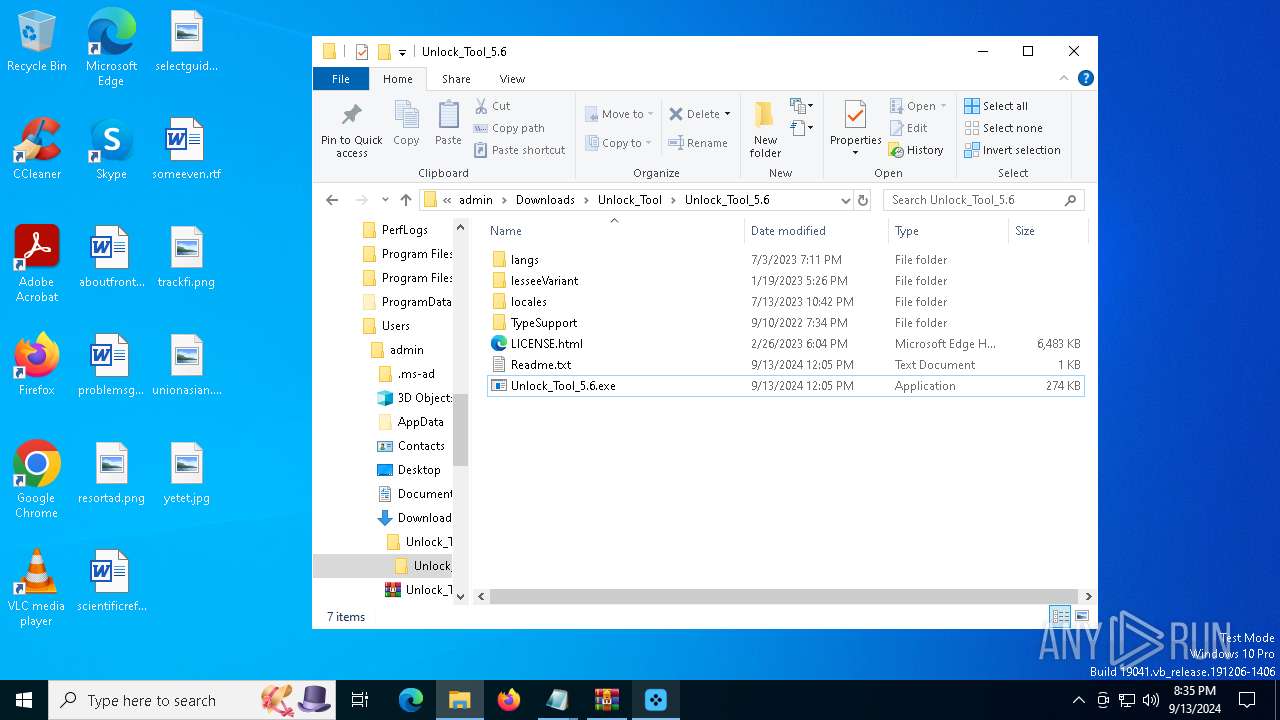
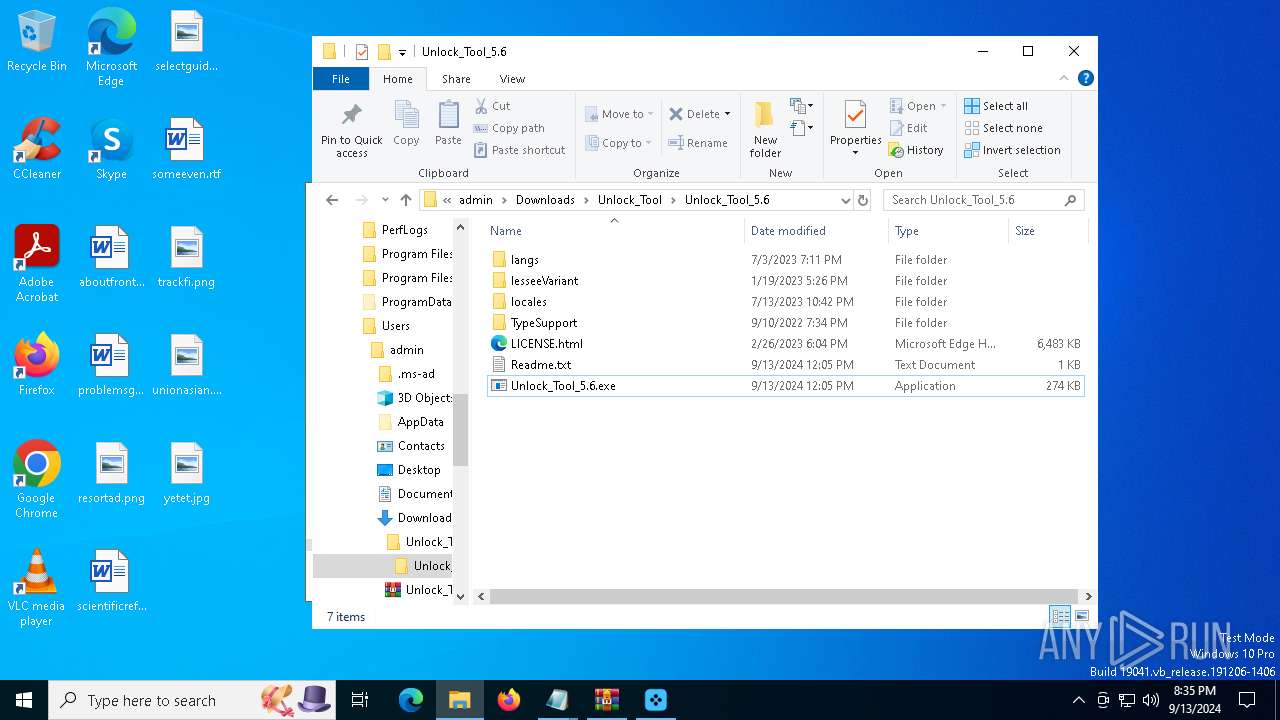
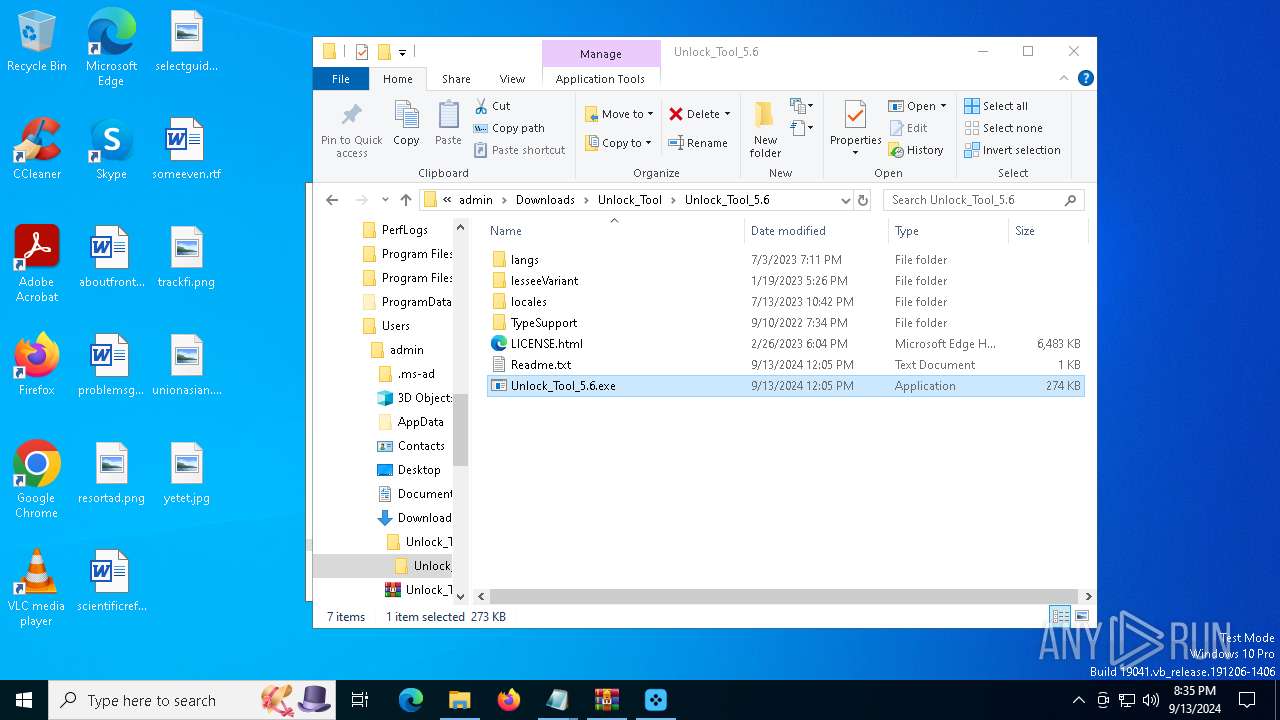
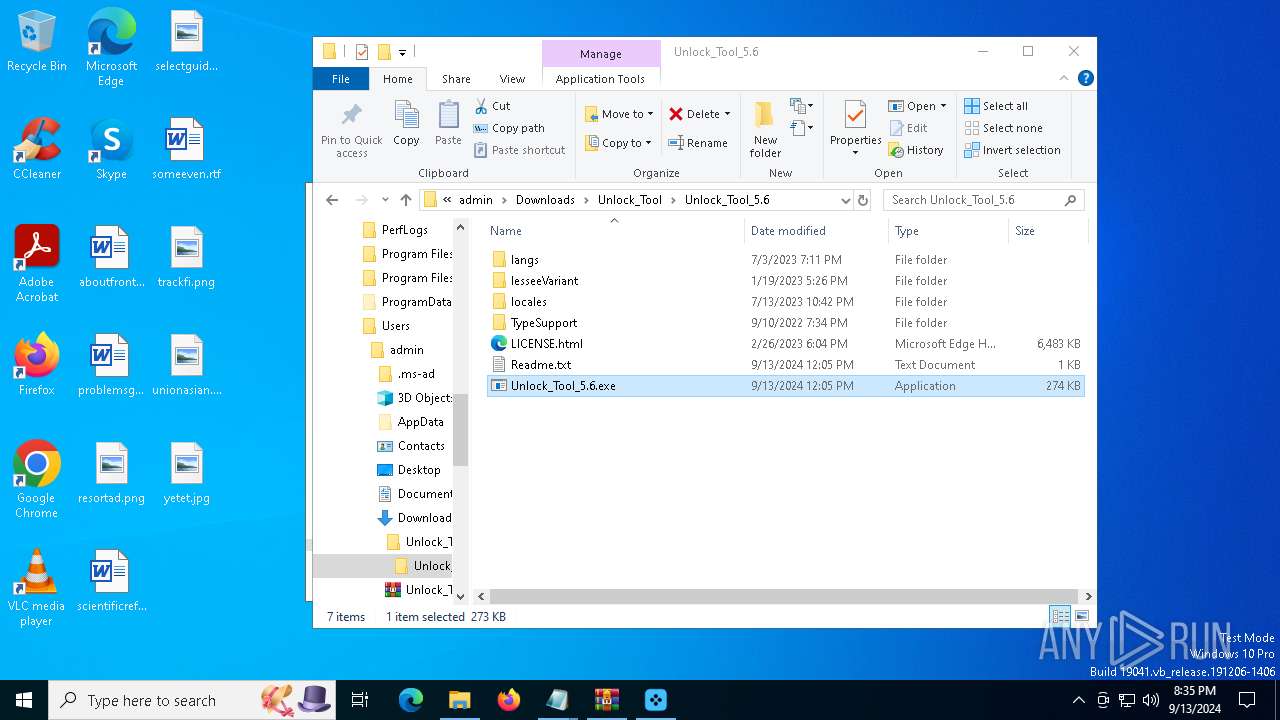
| URL: | https://www.dropbox.com/scl/fi/tplphzcb6uwop6ktsefrf/Unlock_Tool.zip?rlkey=zclwm6700czodjgtmop6b2fpq&st=b9fydq1m&dl=1 |
| Full analysis: | https://app.any.run/tasks/e60102d7-55b1-4dce-a3c7-674913dedb17 |
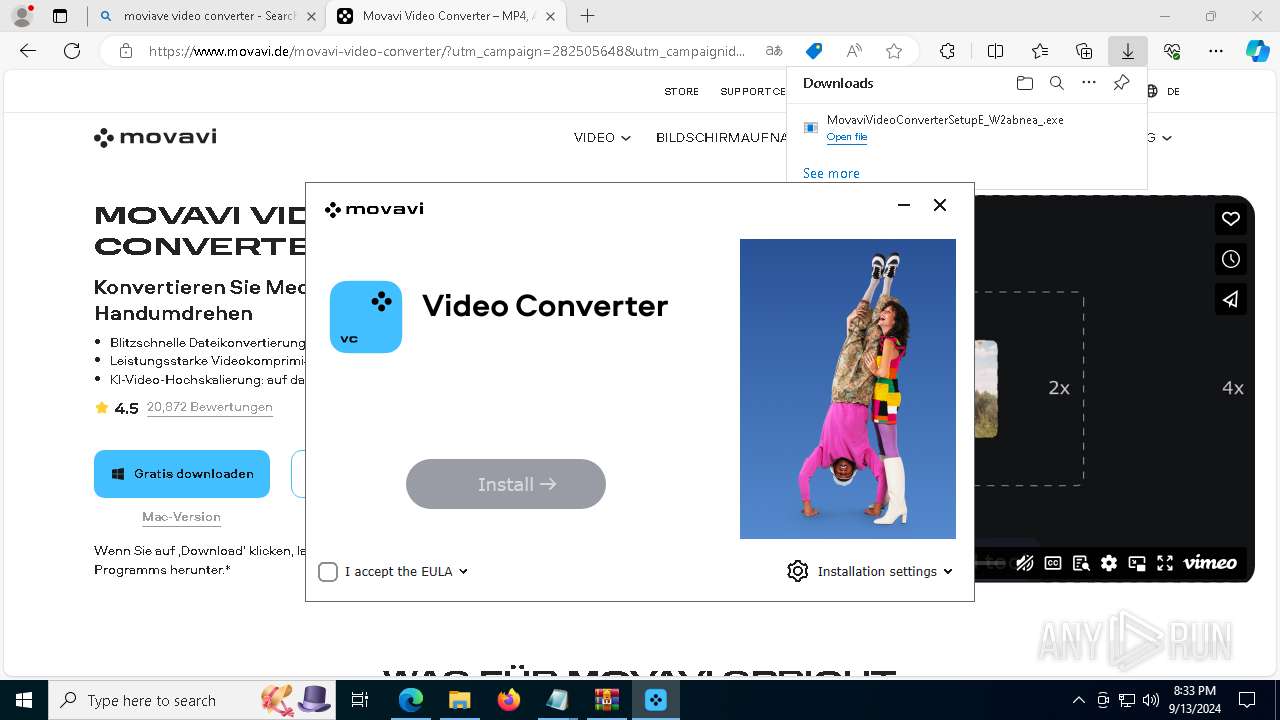
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | September 13, 2024, 20:30:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0AEE9EC1CD06789E139D92DD009853E6 |
| SHA1: | 2DA96FFF034CBD68A7DD468B93740F39BC823F80 |
| SHA256: | C20BCBD211FDB36FE0A173AE4F1F387A000BF9DD8CE13739F1FC791D3FD8BF1D |
| SSDEEP: | 3:N8DSLcVHGkG61fZILDK2KSLcaZOAcYG7pjFVLXJDFWUn:2OLHkbhI3hhw5YG1jFVLXVFTn |
MALICIOUS
VIDAR has been detected (YARA)
- RegAsm.exe (PID: 6168)
VIDAR has been detected (SURICATA)
- RegAsm.exe (PID: 6168)
Stealers network behavior
- RegAsm.exe (PID: 6168)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 6168)
Changes the autorun value in the registry
- InstallerGUI.exe (PID: 4644)
SUSPICIOUS
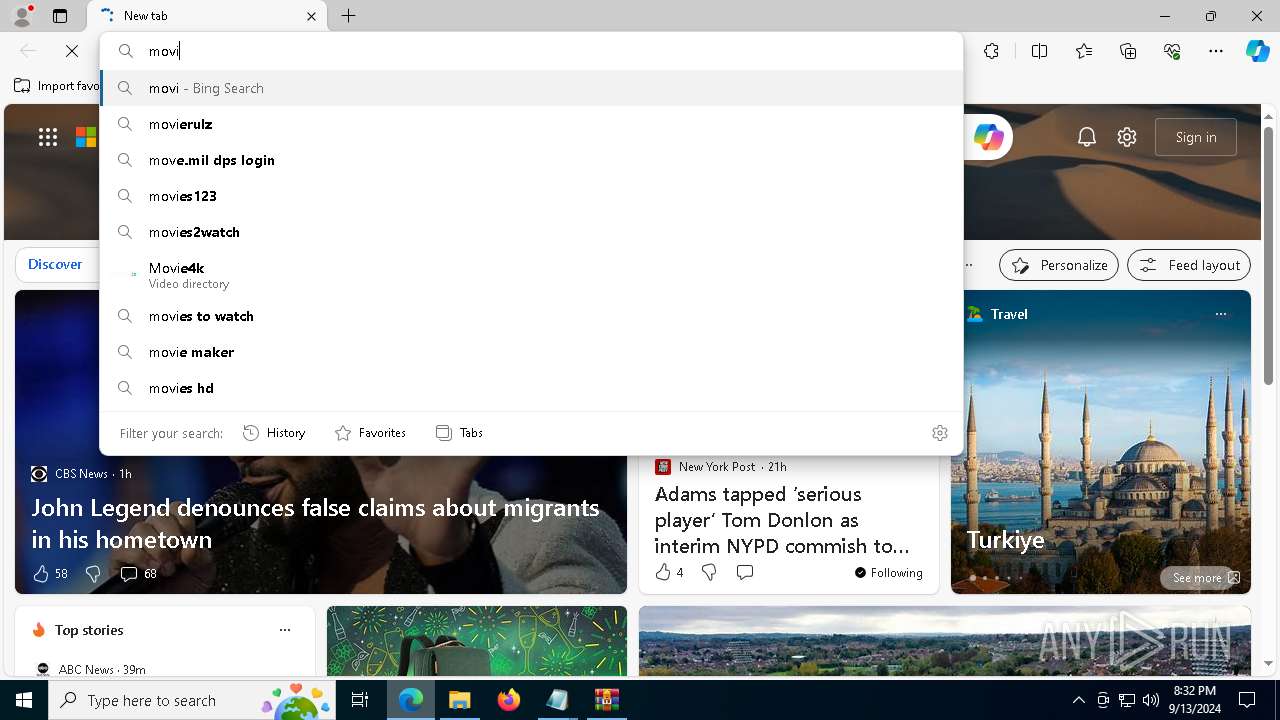
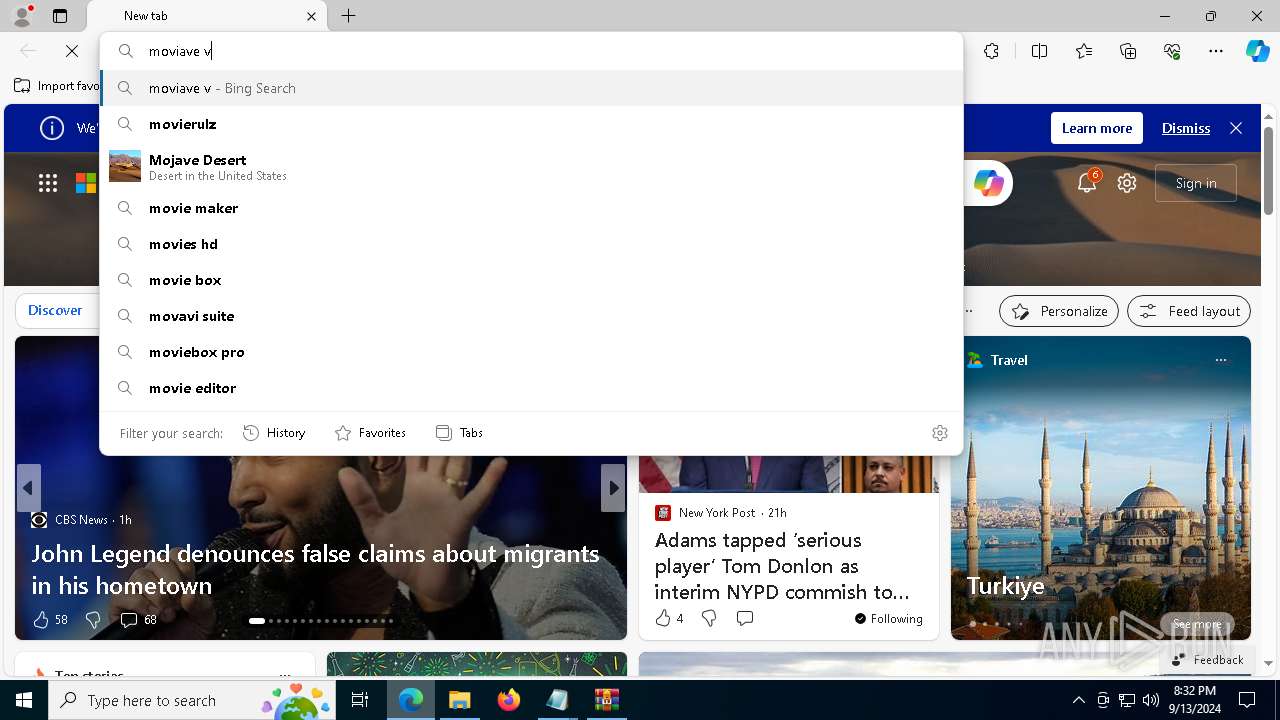
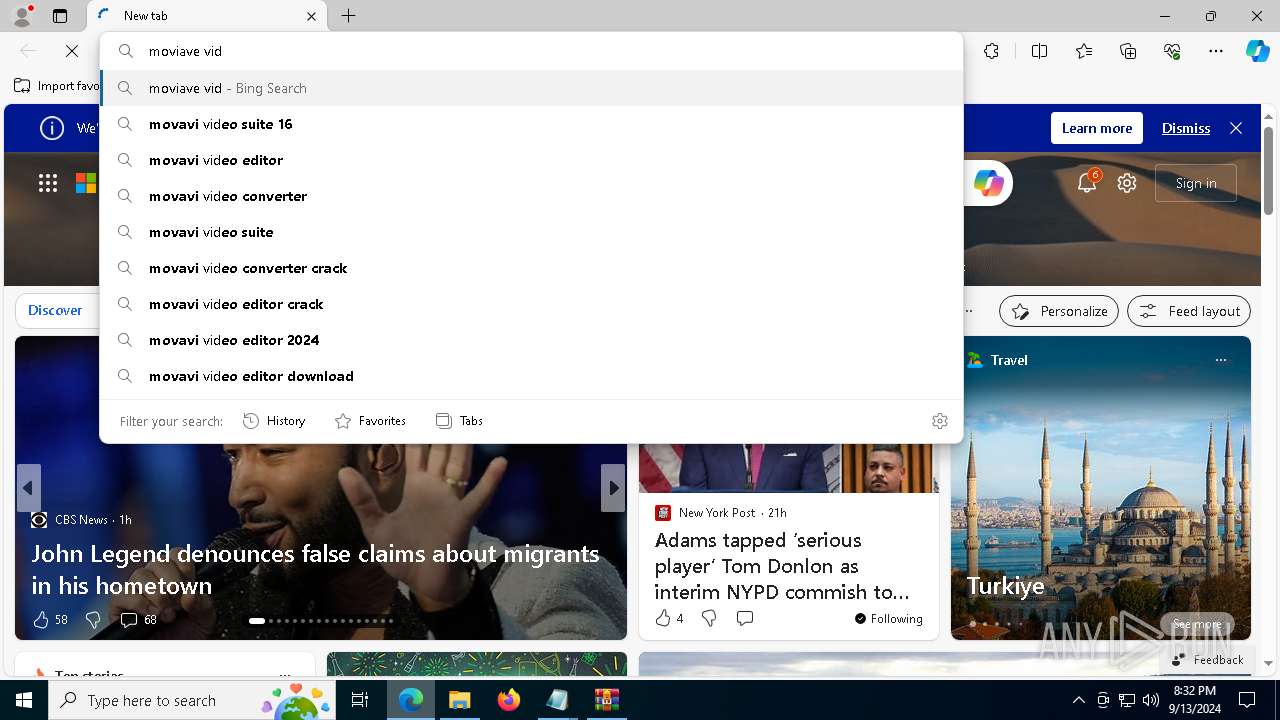
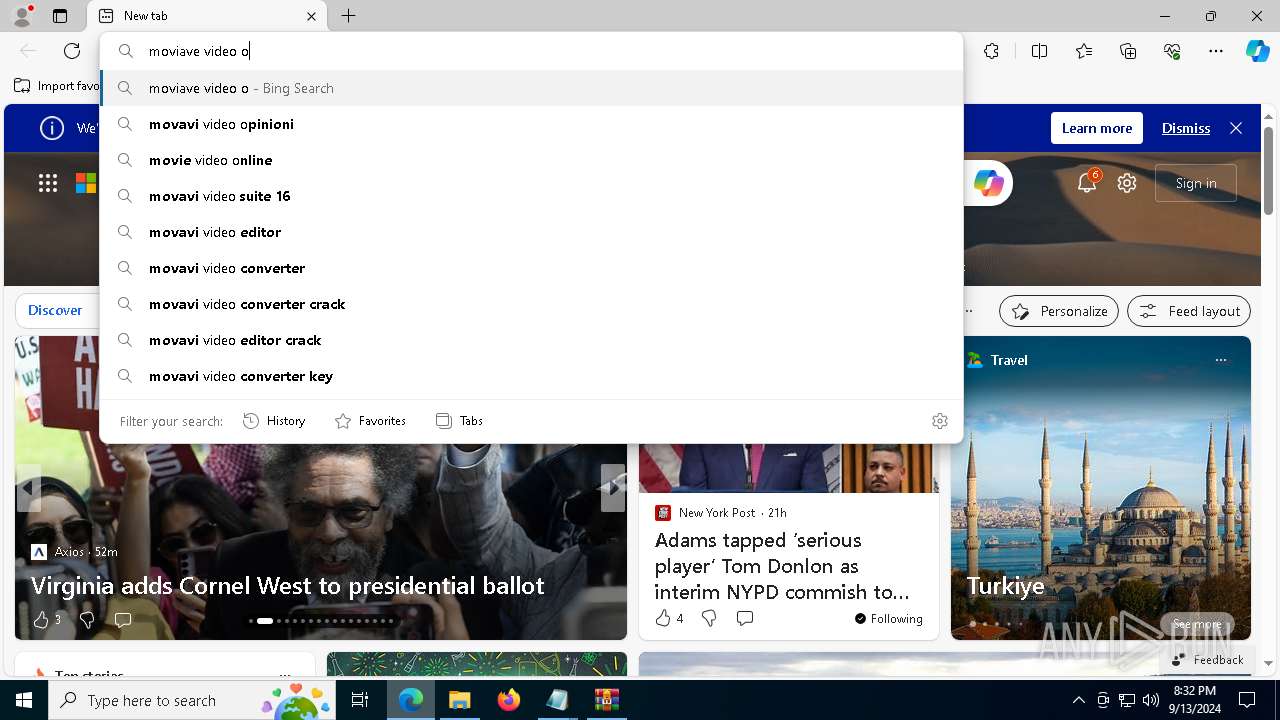
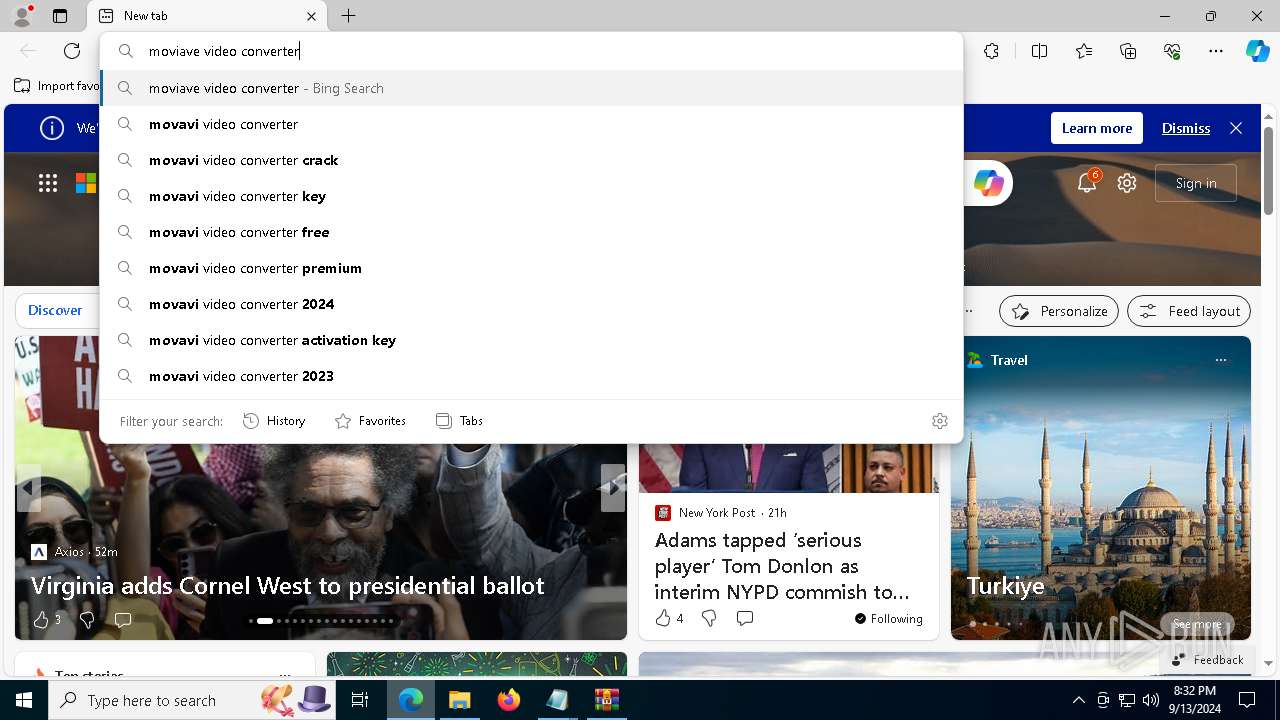
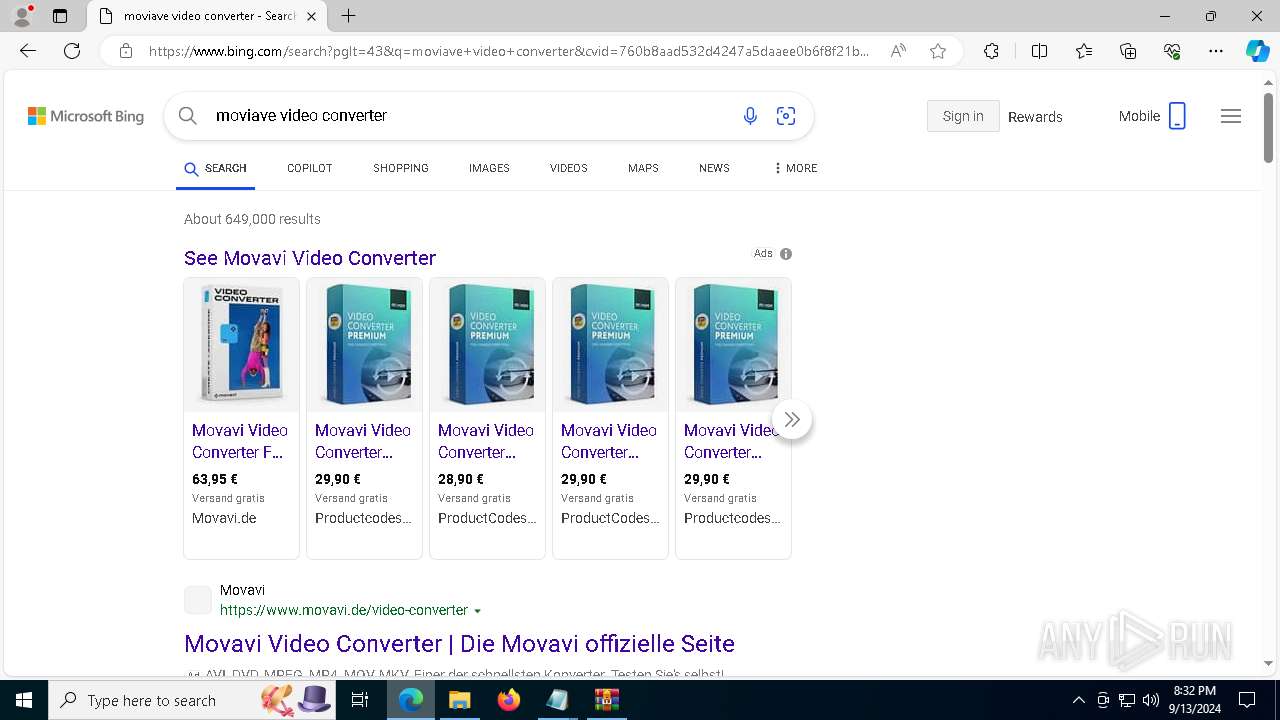
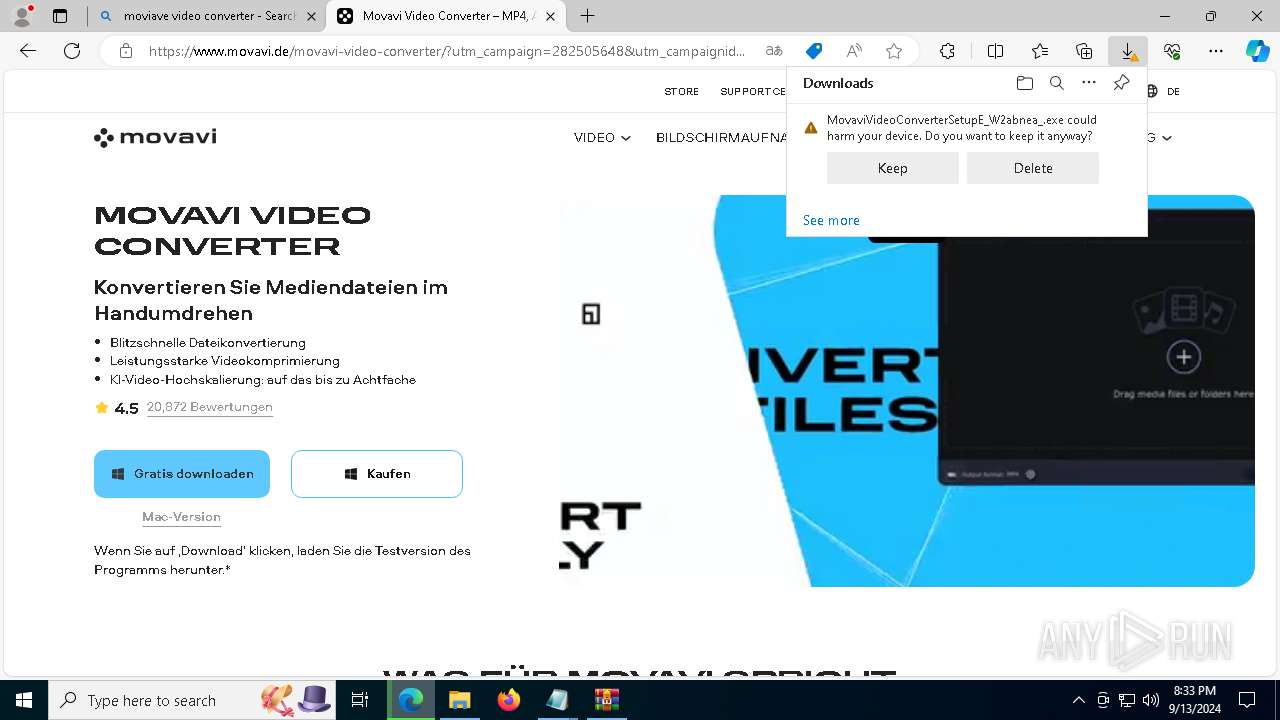
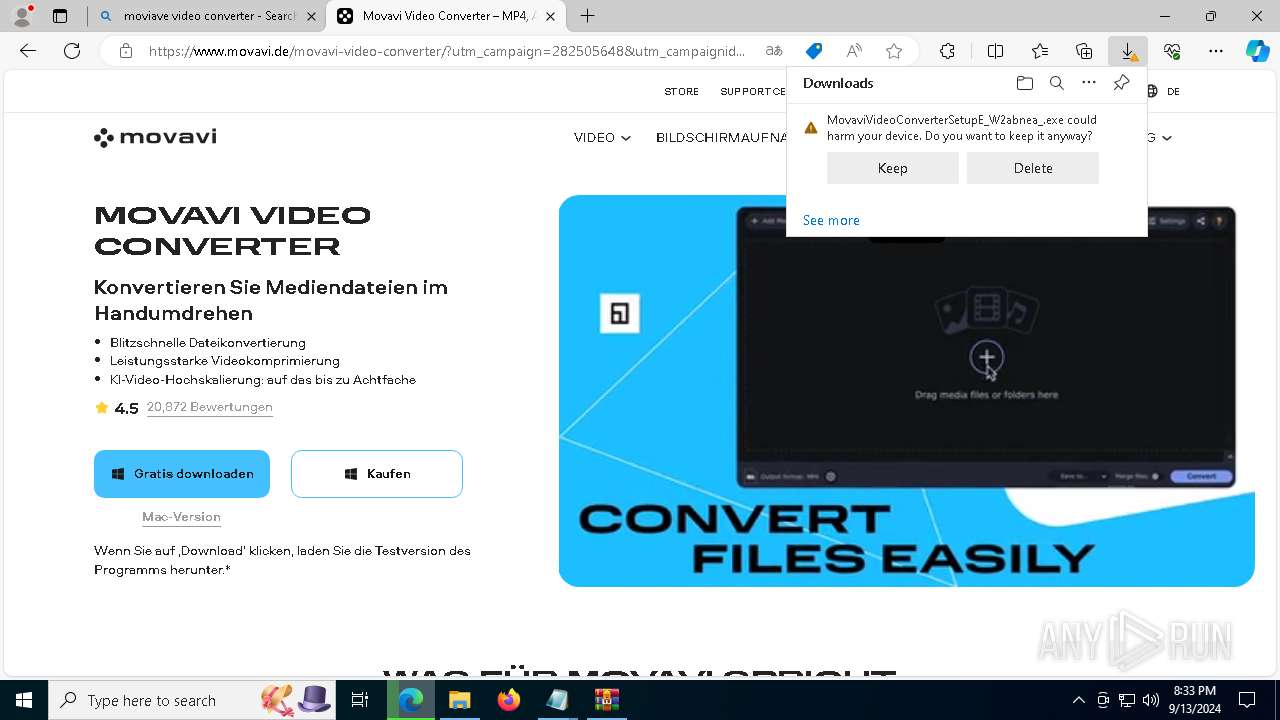
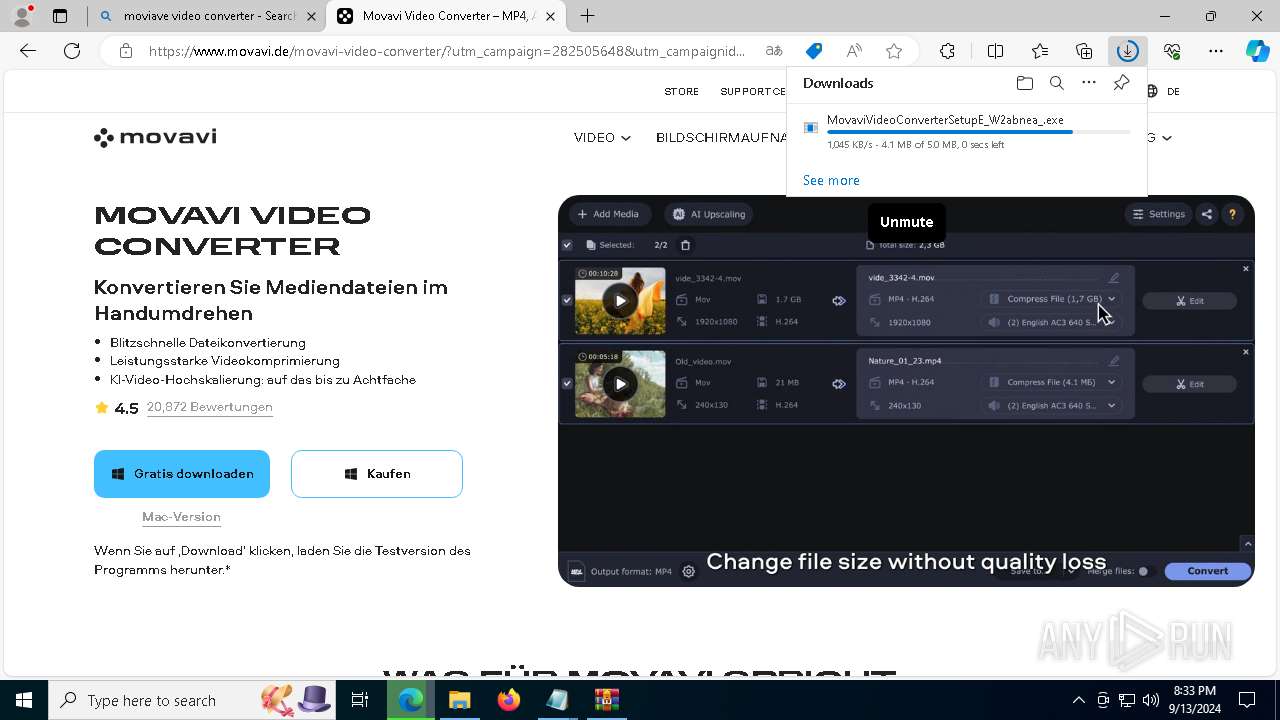
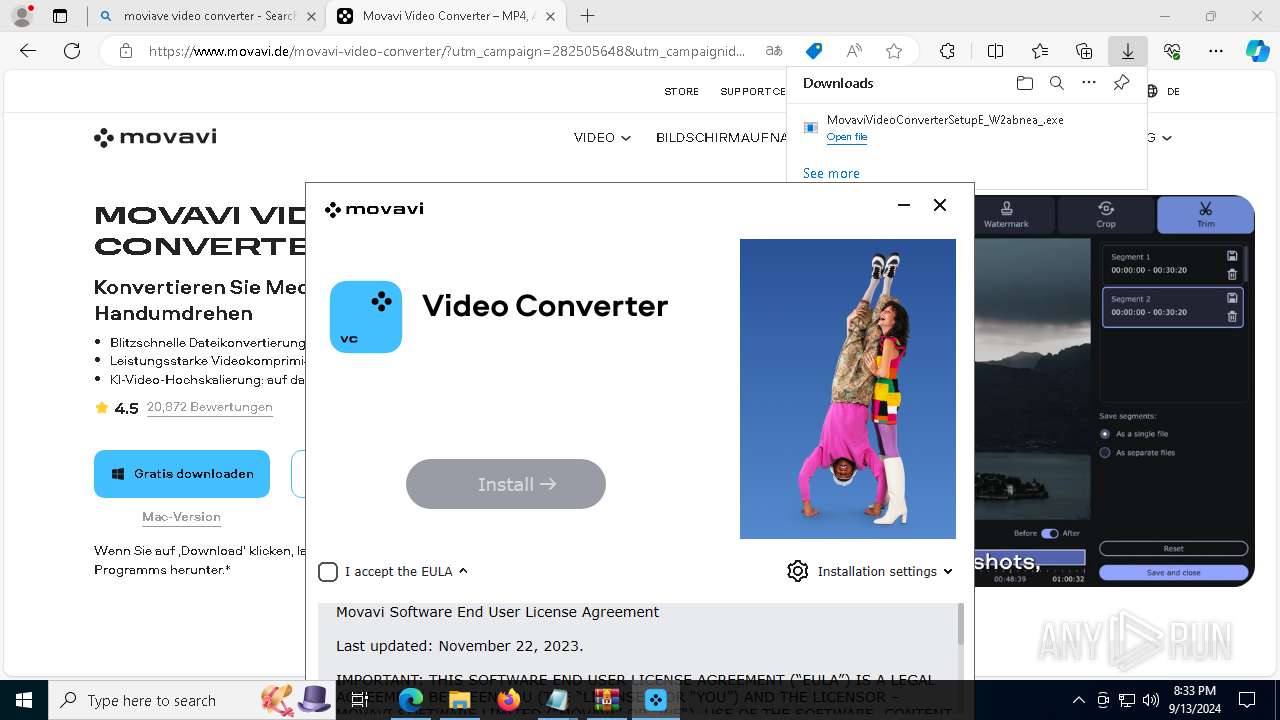
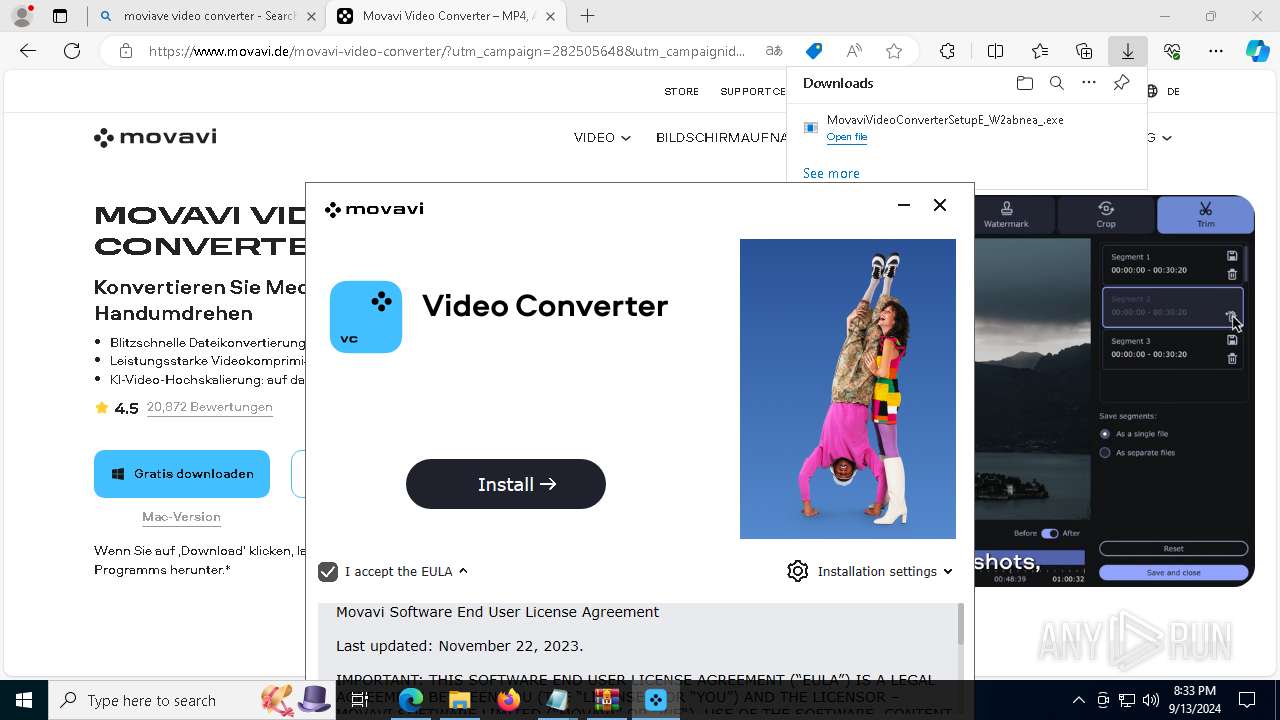
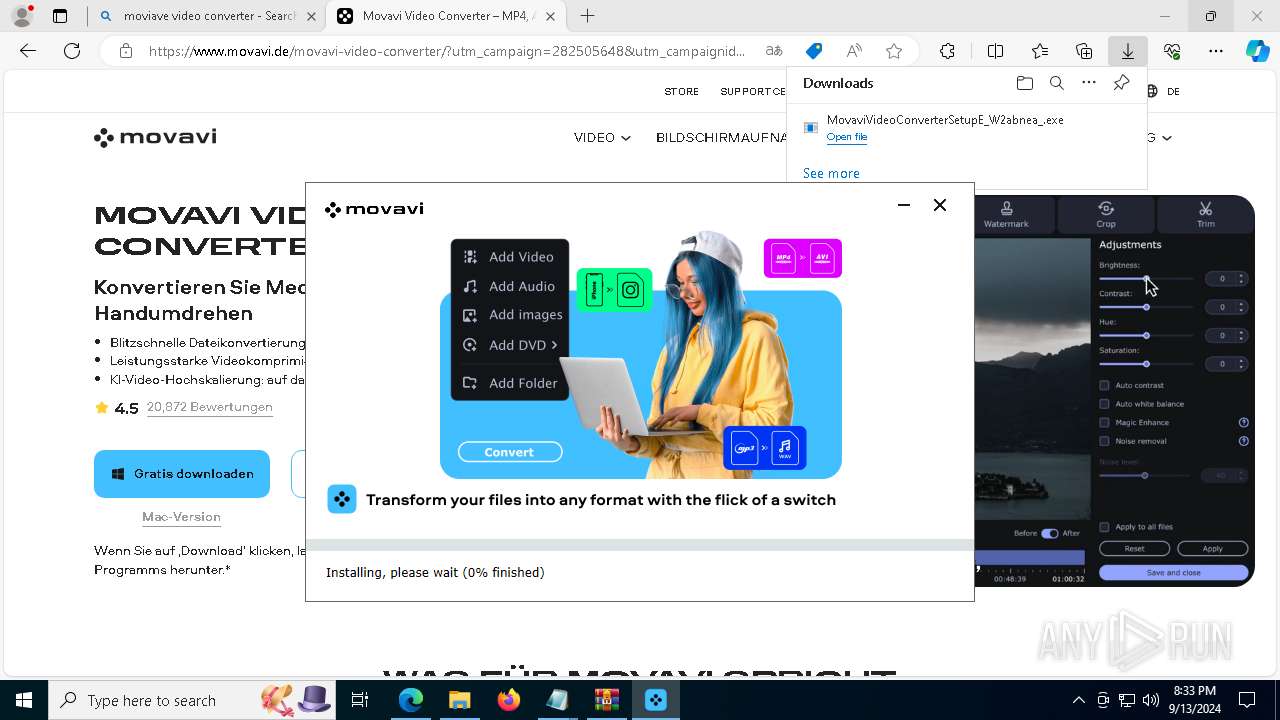
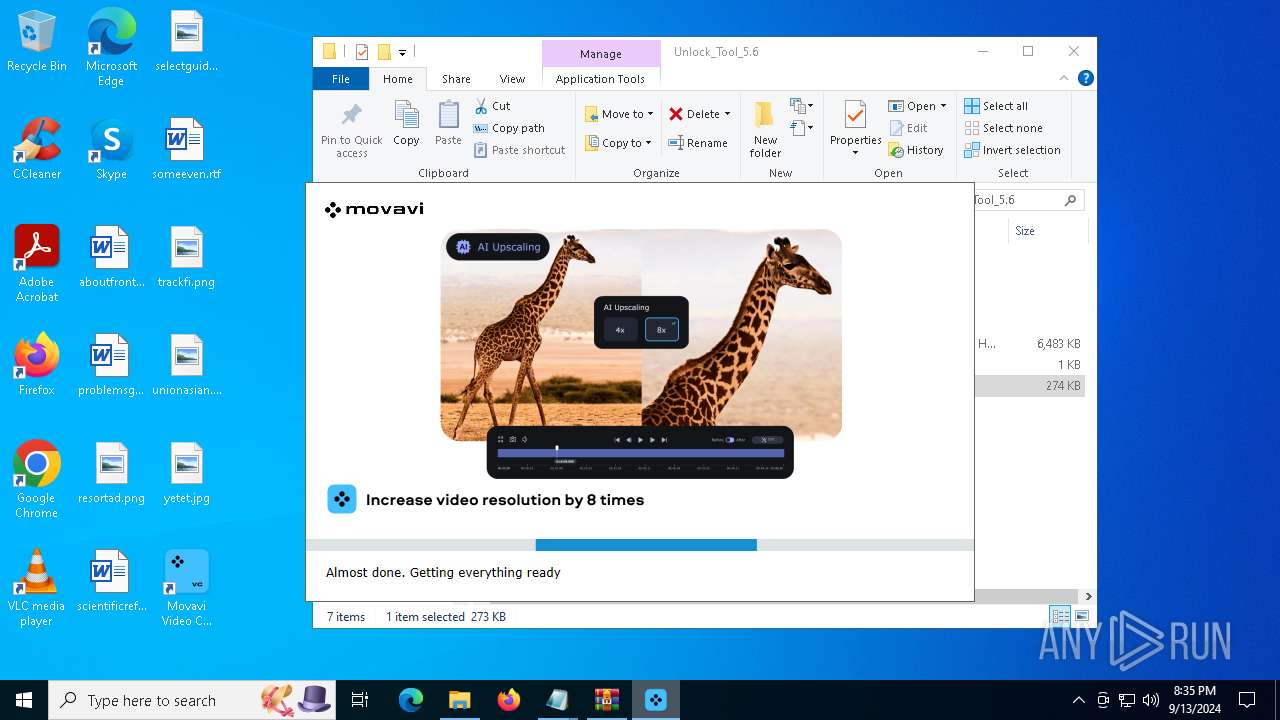
The process creates files with name similar to system file names
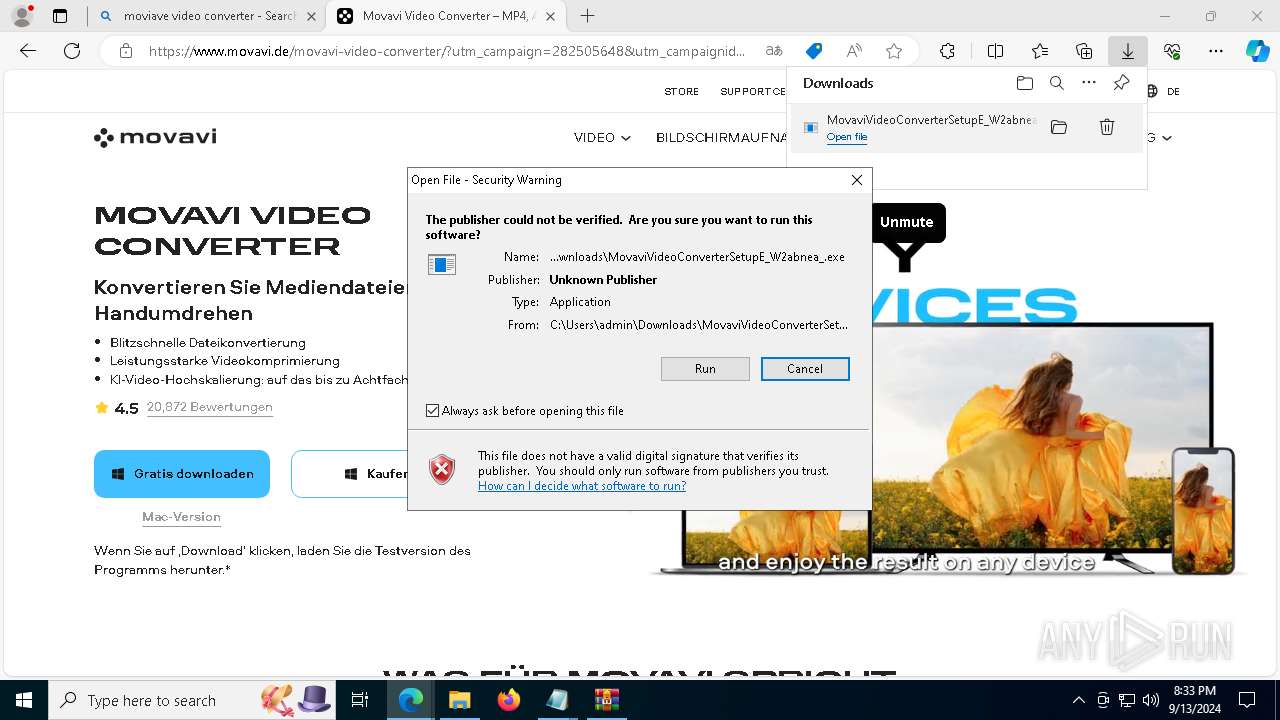
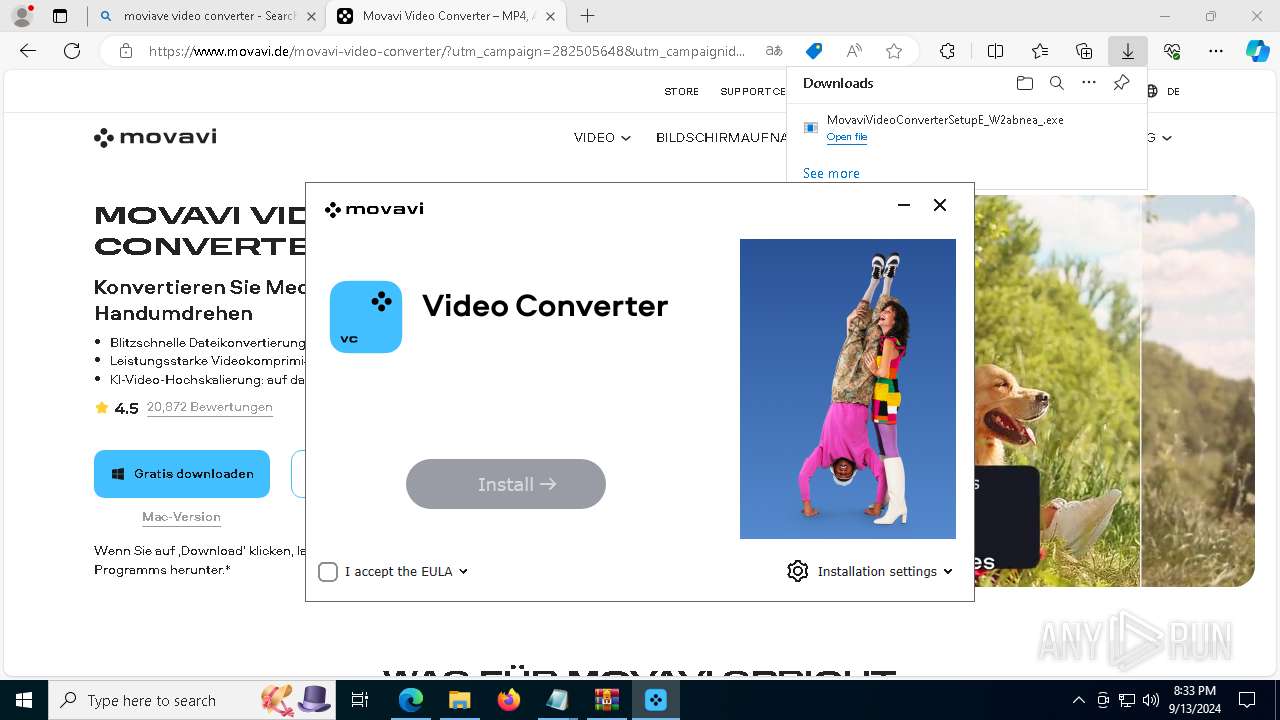
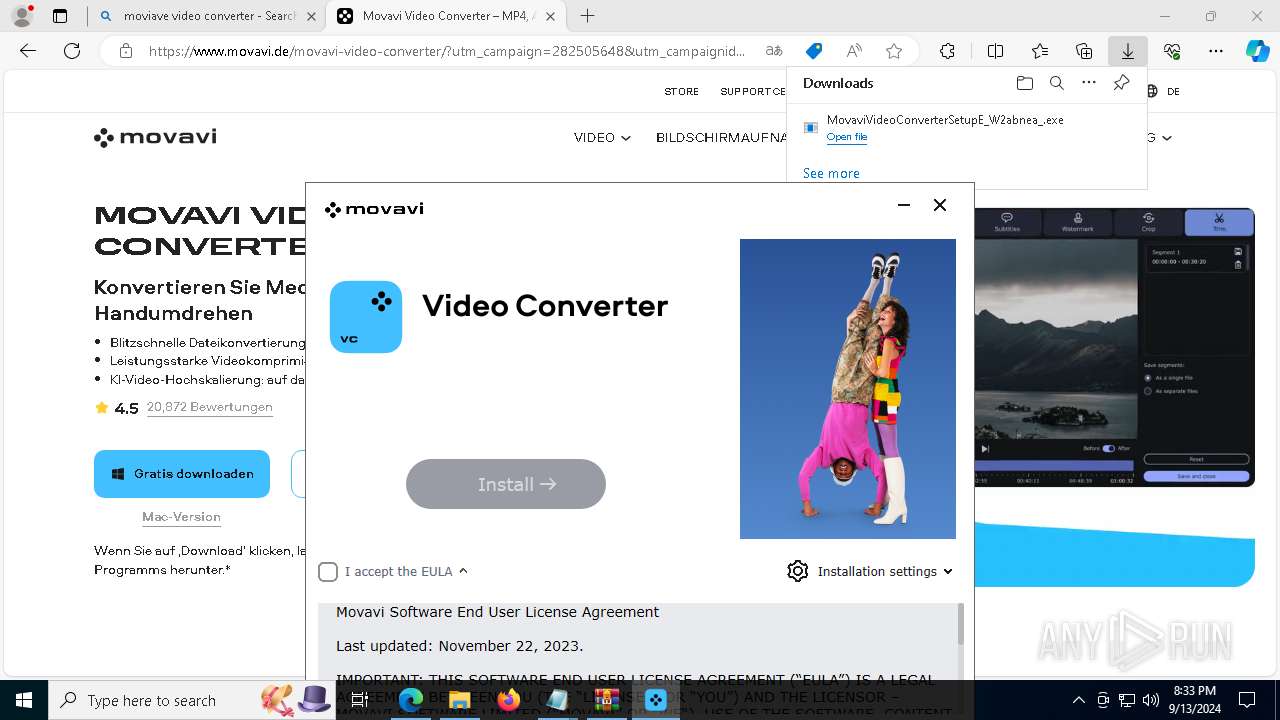
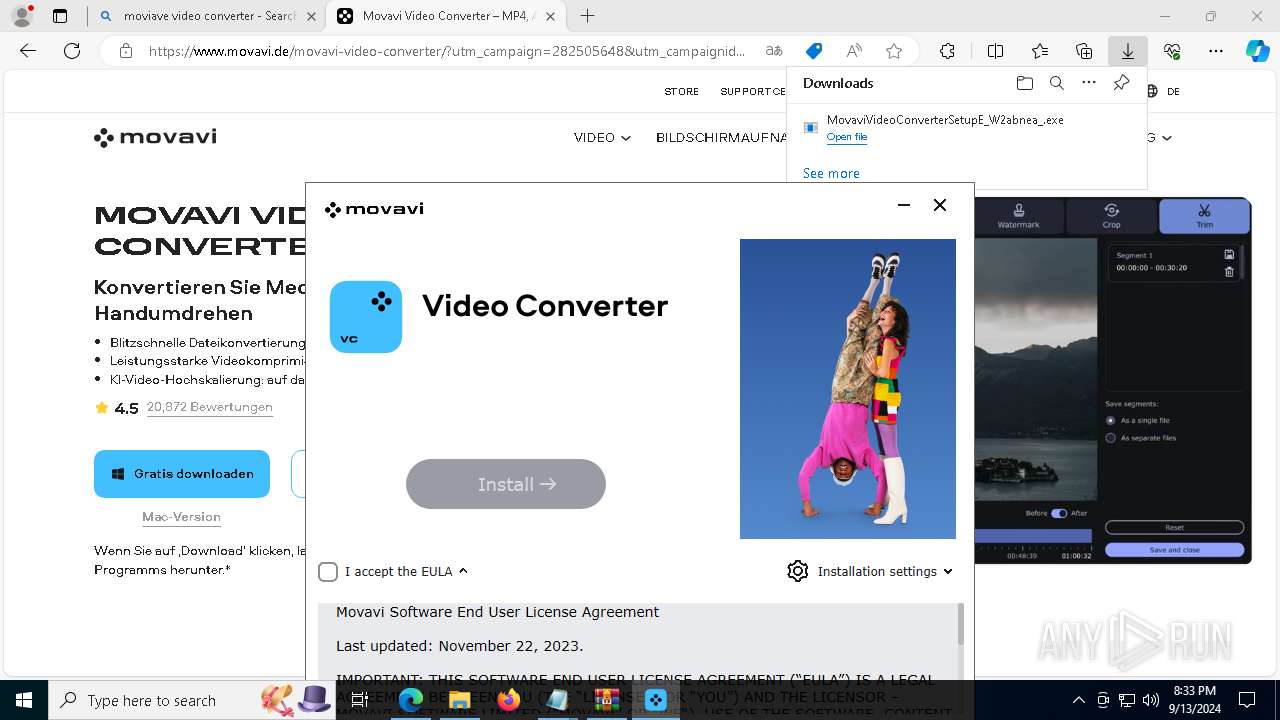
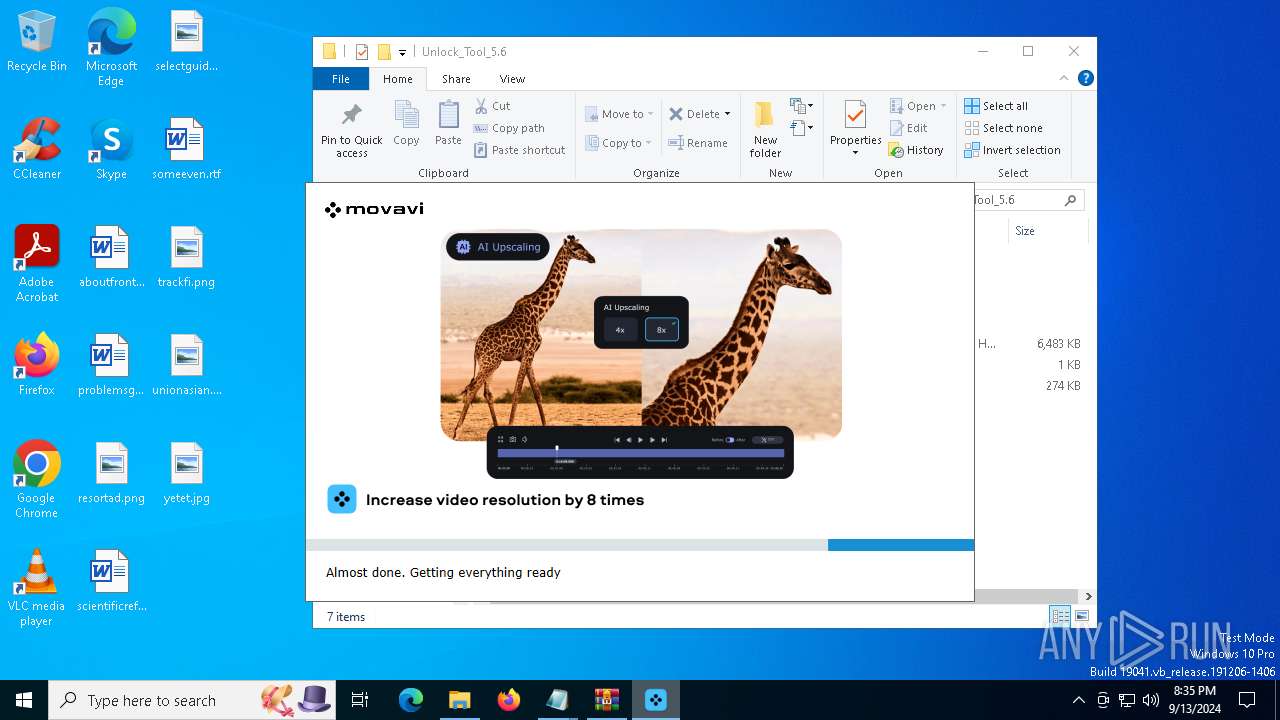
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
- 2029978299_W2abnea_.exe (PID: 8508)
- InstallerGUI.exe (PID: 4644)
Executable content was dropped or overwritten
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
- RegAsm.exe (PID: 6168)
- 2029978299_W2abnea_.exe (PID: 8508)
- InstallerGUI.exe (PID: 4644)
Reads the date of Windows installation
- installer.exe (PID: 6472)
Reads security settings of Internet Explorer
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
- ShellExperienceHost.exe (PID: 5084)
- RegAsm.exe (PID: 736)
- 2029978299_W2abnea_.exe (PID: 8508)
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
Get information on the list of running processes
- installer.exe (PID: 6472)
- cmd.exe (PID: 7236)
Starts CMD.EXE for commands execution
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
Hides command output
- cmd.exe (PID: 7236)
Checks Windows Trust Settings
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
Searches for installed software
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
- installer.exe (PID: 6472)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8404)
Reads the BIOS version
- InstallerGUI.exe (PID: 4644)
- ConverterAgent.exe (PID: 7688)
- WebConfigLoader.exe (PID: 7100)
- converter.exe (PID: 8116)
- WebConfigLoader.exe (PID: 7968)
Creates a software uninstall entry
- InstallerGUI.exe (PID: 4644)
INFO
Application launched itself
- msedge.exe (PID: 4668)
- msedge.exe (PID: 7708)
- msedge.exe (PID: 8776)
Checks supported languages
- identity_helper.exe (PID: 6552)
- identity_helper.exe (PID: 8020)
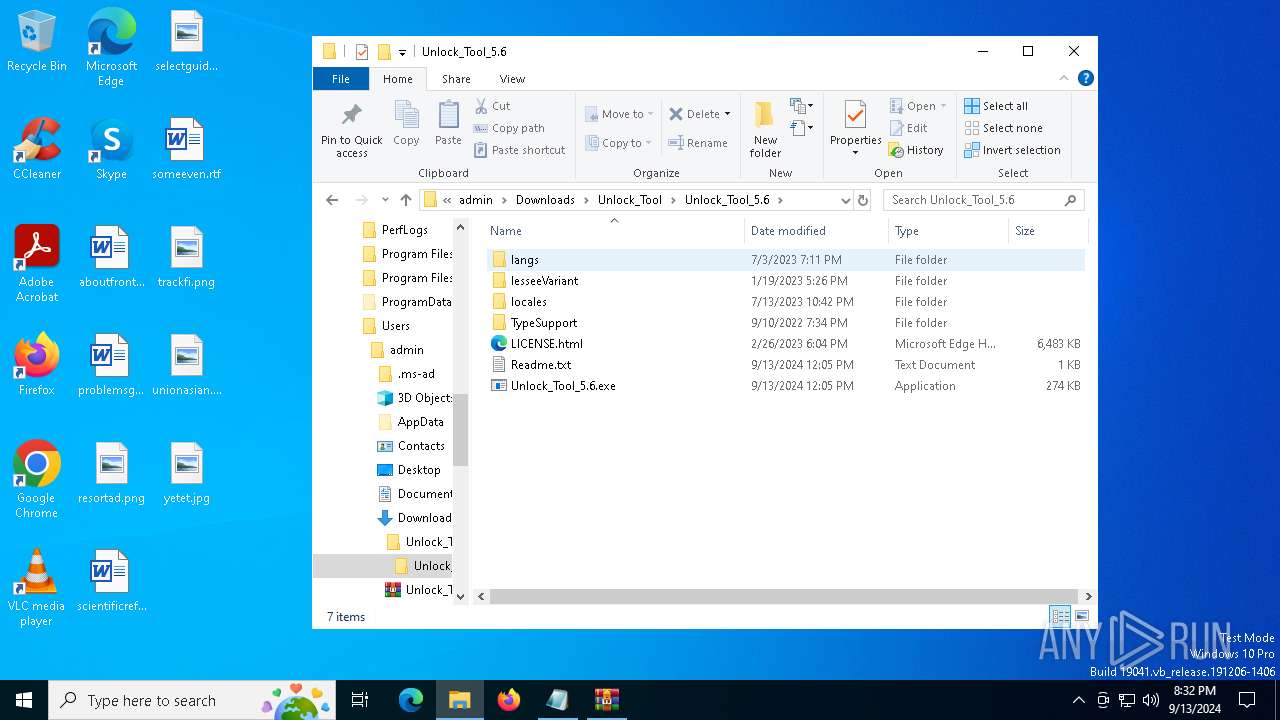
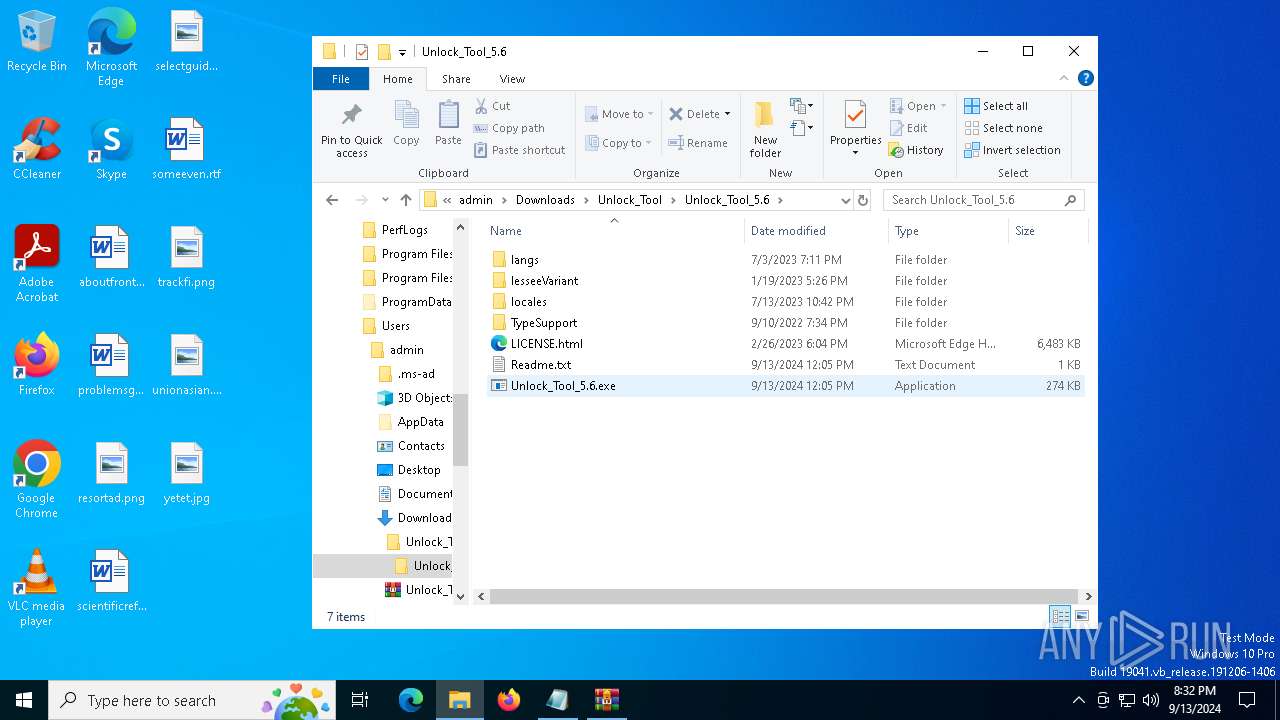
- Unlock_Tool_5.6.exe (PID: 4824)
- RegAsm.exe (PID: 6168)
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
- crashpad_handler.exe (PID: 5984)
- installer.exe (PID: 6472)
- identity_helper.exe (PID: 1156)
- 2029978299_W2abnea_.exe (PID: 8508)
- InstallerGUI.exe (PID: 4644)
- crashpad_handler.exe (PID: 8500)
- CoreChecker.exe (PID: 3492)
- PluginChecker.exe (PID: 7056)
- PluginChecker.exe (PID: 3028)
- PluginChecker.exe (PID: 8052)
- PluginChecker.exe (PID: 2460)
- PluginChecker.exe (PID: 6432)
- PluginChecker.exe (PID: 4020)
- PluginChecker.exe (PID: 788)
- PluginChecker.exe (PID: 6380)
- PluginChecker.exe (PID: 7380)
- PluginChecker.exe (PID: 9108)
- PluginChecker.exe (PID: 7876)
- PluginChecker.exe (PID: 4196)
- PluginChecker.exe (PID: 2144)
- PluginChecker.exe (PID: 7316)
- PluginChecker.exe (PID: 236)
- PluginChecker.exe (PID: 8360)
- PluginChecker.exe (PID: 9204)
- PluginChecker.exe (PID: 9200)
- PluginChecker.exe (PID: 7076)
- PluginChecker.exe (PID: 9180)
- PluginChecker.exe (PID: 1492)
- PluginChecker.exe (PID: 4880)
- PluginChecker.exe (PID: 608)
- PluginChecker.exe (PID: 7792)
- PluginChecker.exe (PID: 5908)
- PluginChecker.exe (PID: 5532)
- PluginChecker.exe (PID: 6888)
- PluginChecker.exe (PID: 2484)
- PluginChecker.exe (PID: 6548)
- CodecChecker.exe (PID: 7868)
- CodecChecker.exe (PID: 6252)
- CodecChecker.exe (PID: 6612)
- CodecChecker.exe (PID: 7428)
- CodecChecker.exe (PID: 8200)
- CodecChecker.exe (PID: 6148)
- CodecChecker.exe (PID: 8196)
- Unlock_Tool_5.6.exe (PID: 4544)
- RegAsm.exe (PID: 736)
- Unlock_Tool_5.6.exe (PID: 9064)
- RegAsm.exe (PID: 6772)
- ShellExperienceHost.exe (PID: 5084)
- WebConfigLoader.exe (PID: 7100)
- crashpad_handler.exe (PID: 6648)
- ConverterAgent.exe (PID: 7688)
- converter.exe (PID: 8116)
- WebConfigLoader.exe (PID: 7968)
- crashpad_handler.exe (PID: 3972)
- RouterApplication.exe (PID: 6132)
- RouterApplication.exe (PID: 6192)
- crashpad_handler.exe (PID: 7600)
Reads Environment values
- identity_helper.exe (PID: 6552)
- identity_helper.exe (PID: 8020)
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
- identity_helper.exe (PID: 1156)
- InstallerGUI.exe (PID: 4644)
- PluginChecker.exe (PID: 4020)
- PluginChecker.exe (PID: 4196)
- CoreChecker.exe (PID: 3492)
- CodecChecker.exe (PID: 6612)
- CodecChecker.exe (PID: 7868)
- CodecChecker.exe (PID: 6252)
- CodecChecker.exe (PID: 7428)
- CodecChecker.exe (PID: 8200)
- CodecChecker.exe (PID: 8196)
- CodecChecker.exe (PID: 6148)
- WebConfigLoader.exe (PID: 7100)
- RegAsm.exe (PID: 736)
- converter.exe (PID: 8116)
- WebConfigLoader.exe (PID: 7968)
Reads the computer name
- identity_helper.exe (PID: 6552)
- identity_helper.exe (PID: 8020)
- RegAsm.exe (PID: 6168)
- Unlock_Tool_5.6.exe (PID: 4824)
- installer.exe (PID: 6472)
- identity_helper.exe (PID: 1156)
- InstallerGUI.exe (PID: 4644)
- PluginChecker.exe (PID: 3028)
- PluginChecker.exe (PID: 7056)
- PluginChecker.exe (PID: 8052)
- PluginChecker.exe (PID: 2460)
- PluginChecker.exe (PID: 6432)
- PluginChecker.exe (PID: 4020)
- PluginChecker.exe (PID: 4196)
- PluginChecker.exe (PID: 788)
- PluginChecker.exe (PID: 6380)
- PluginChecker.exe (PID: 7380)
- PluginChecker.exe (PID: 9108)
- PluginChecker.exe (PID: 7876)
- PluginChecker.exe (PID: 2144)
- PluginChecker.exe (PID: 236)
- PluginChecker.exe (PID: 7316)
- PluginChecker.exe (PID: 9204)
- PluginChecker.exe (PID: 8360)
- PluginChecker.exe (PID: 7076)
- PluginChecker.exe (PID: 1492)
- PluginChecker.exe (PID: 9180)
- PluginChecker.exe (PID: 608)
- PluginChecker.exe (PID: 4880)
- PluginChecker.exe (PID: 9200)
- PluginChecker.exe (PID: 7792)
- PluginChecker.exe (PID: 5908)
- PluginChecker.exe (PID: 5532)
- PluginChecker.exe (PID: 2484)
- CoreChecker.exe (PID: 3492)
- PluginChecker.exe (PID: 6888)
- PluginChecker.exe (PID: 6548)
- CodecChecker.exe (PID: 7868)
- CodecChecker.exe (PID: 7428)
- CodecChecker.exe (PID: 6252)
- CodecChecker.exe (PID: 6612)
- CodecChecker.exe (PID: 8200)
- CodecChecker.exe (PID: 8196)
- CodecChecker.exe (PID: 6148)
- ShellExperienceHost.exe (PID: 5084)
- Unlock_Tool_5.6.exe (PID: 4544)
- RegAsm.exe (PID: 6772)
- RegAsm.exe (PID: 736)
- Unlock_Tool_5.6.exe (PID: 9064)
- WebConfigLoader.exe (PID: 7100)
- ConverterAgent.exe (PID: 7688)
- 2029978299_W2abnea_.exe (PID: 8508)
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
- WebConfigLoader.exe (PID: 7968)
- RouterApplication.exe (PID: 6132)
- converter.exe (PID: 8116)
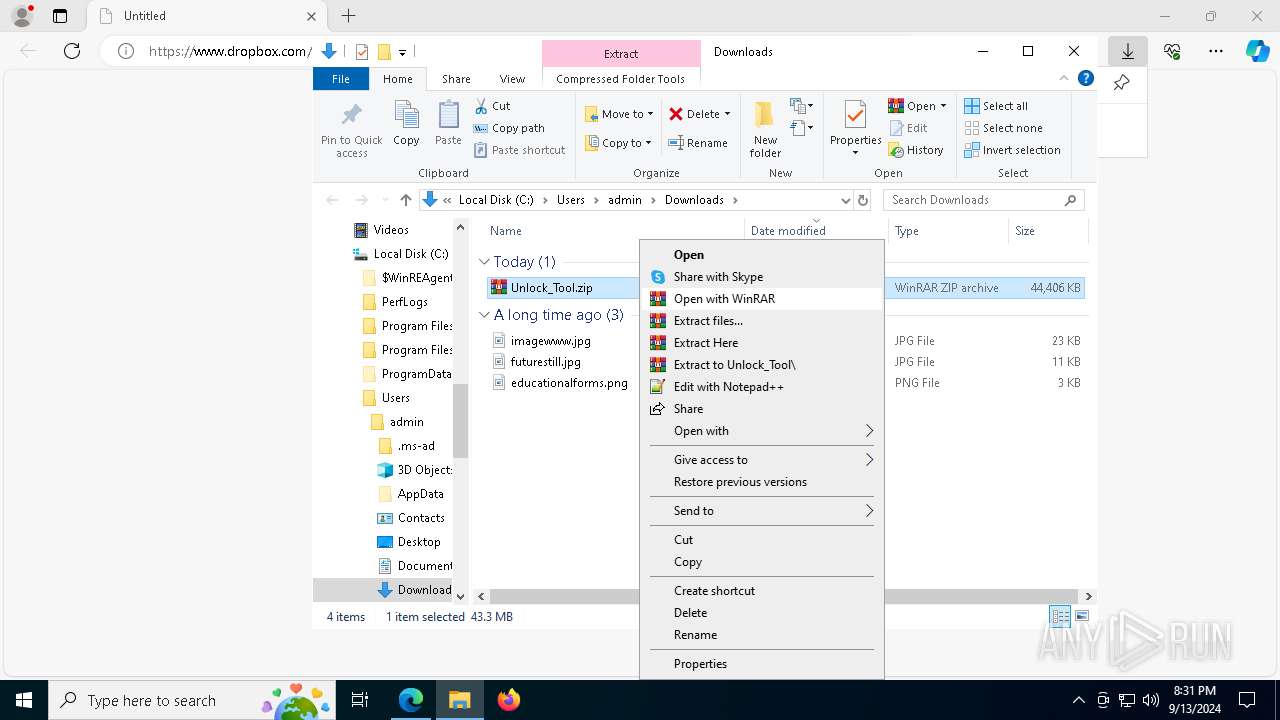
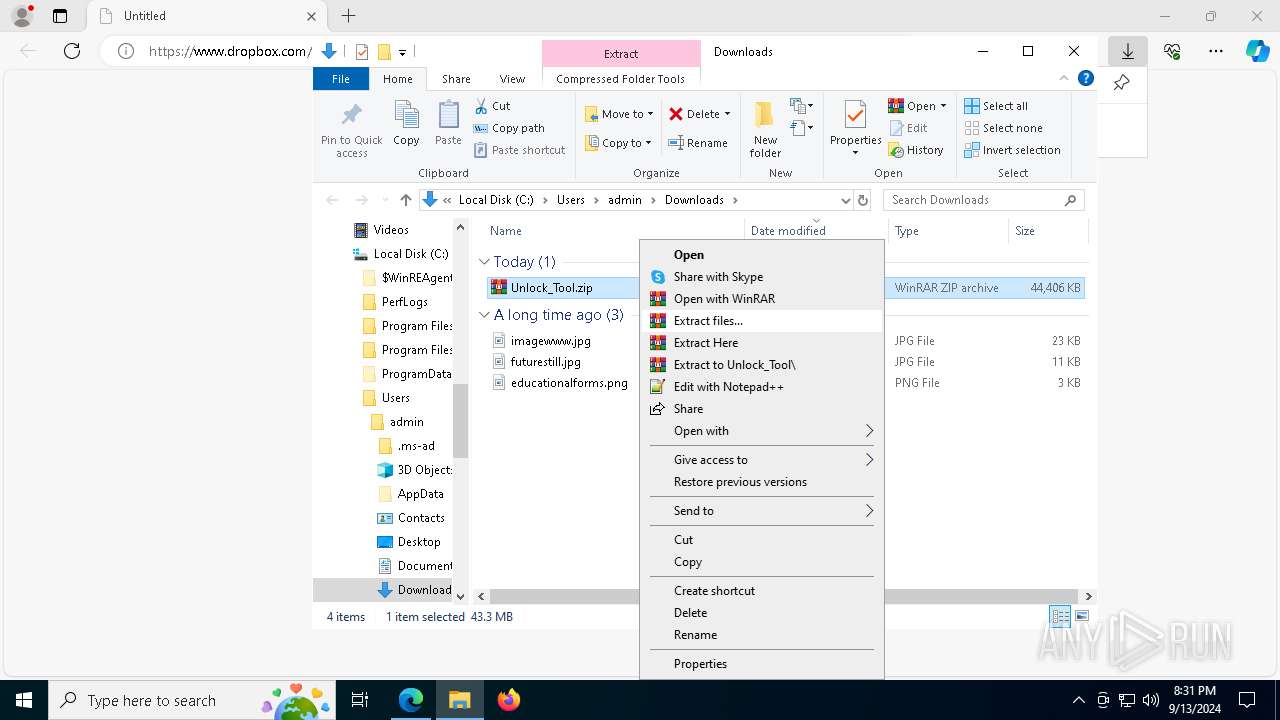
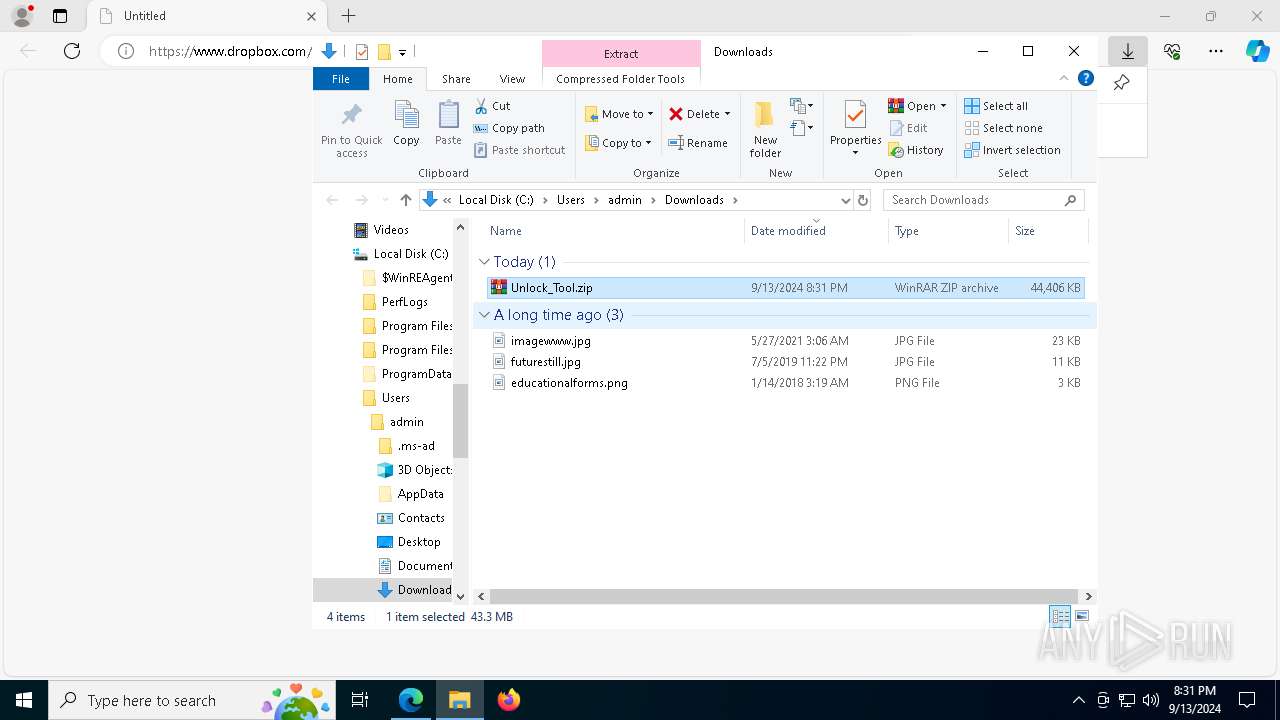
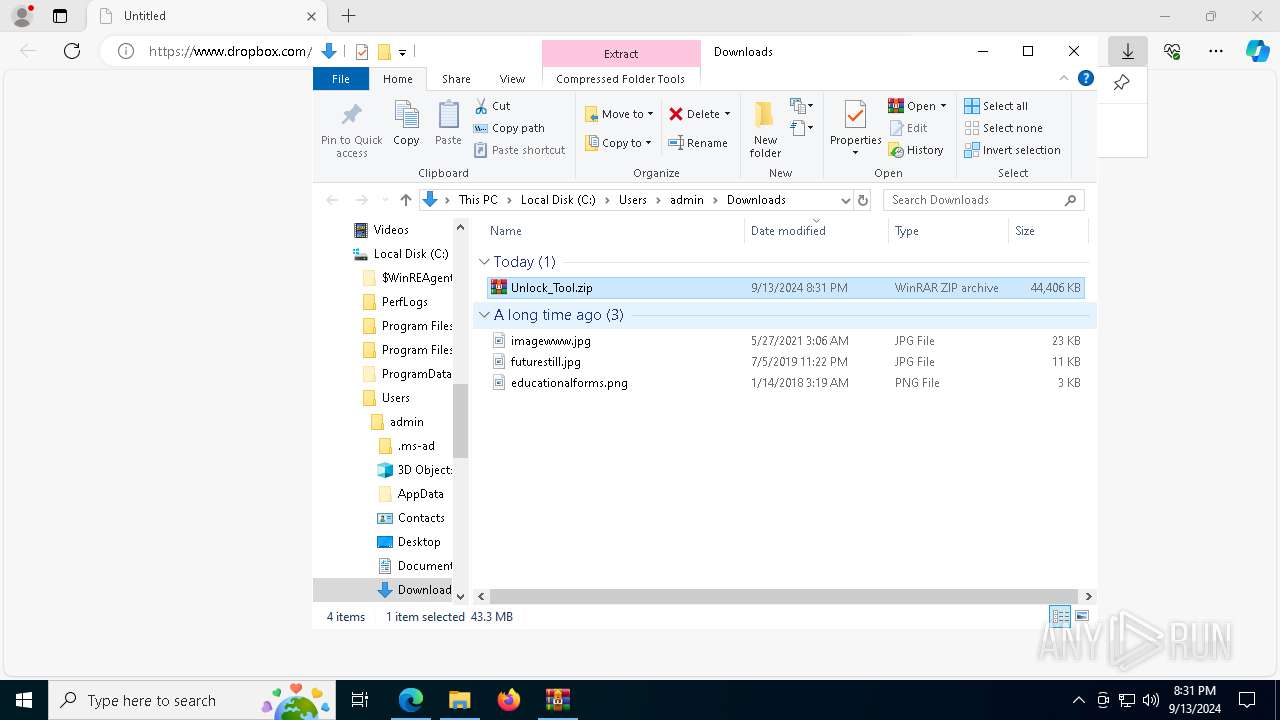
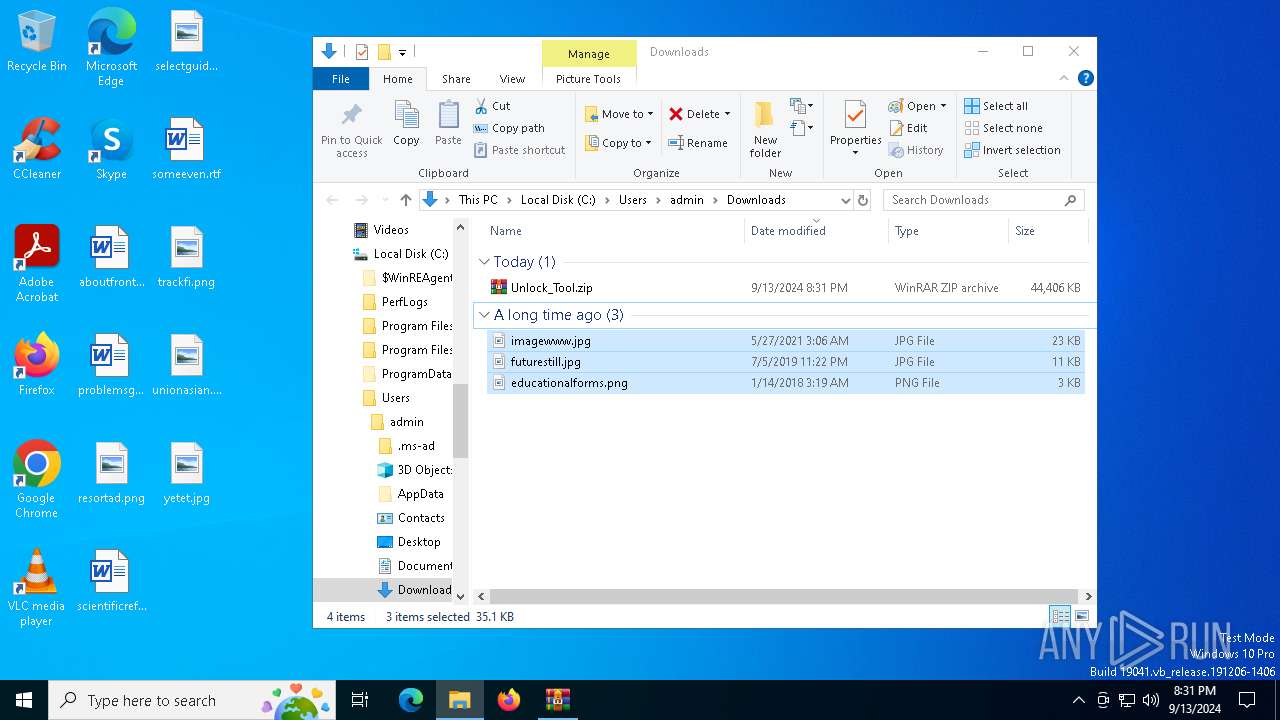
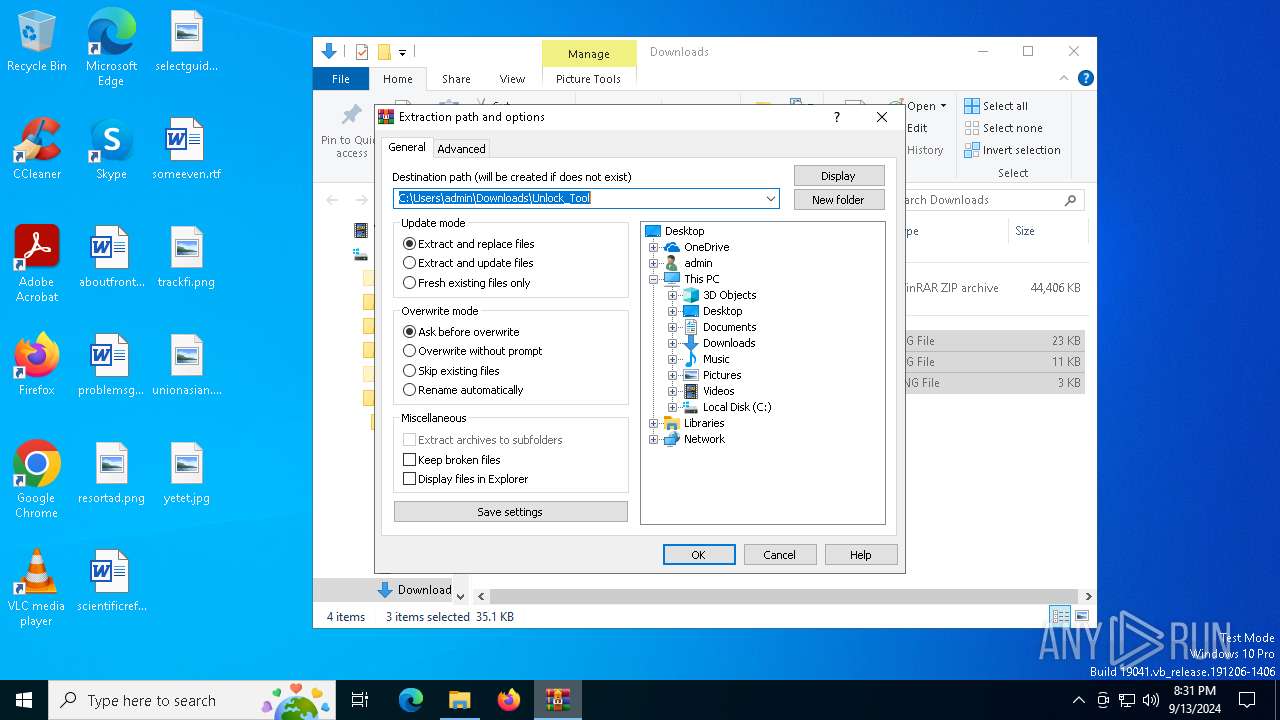
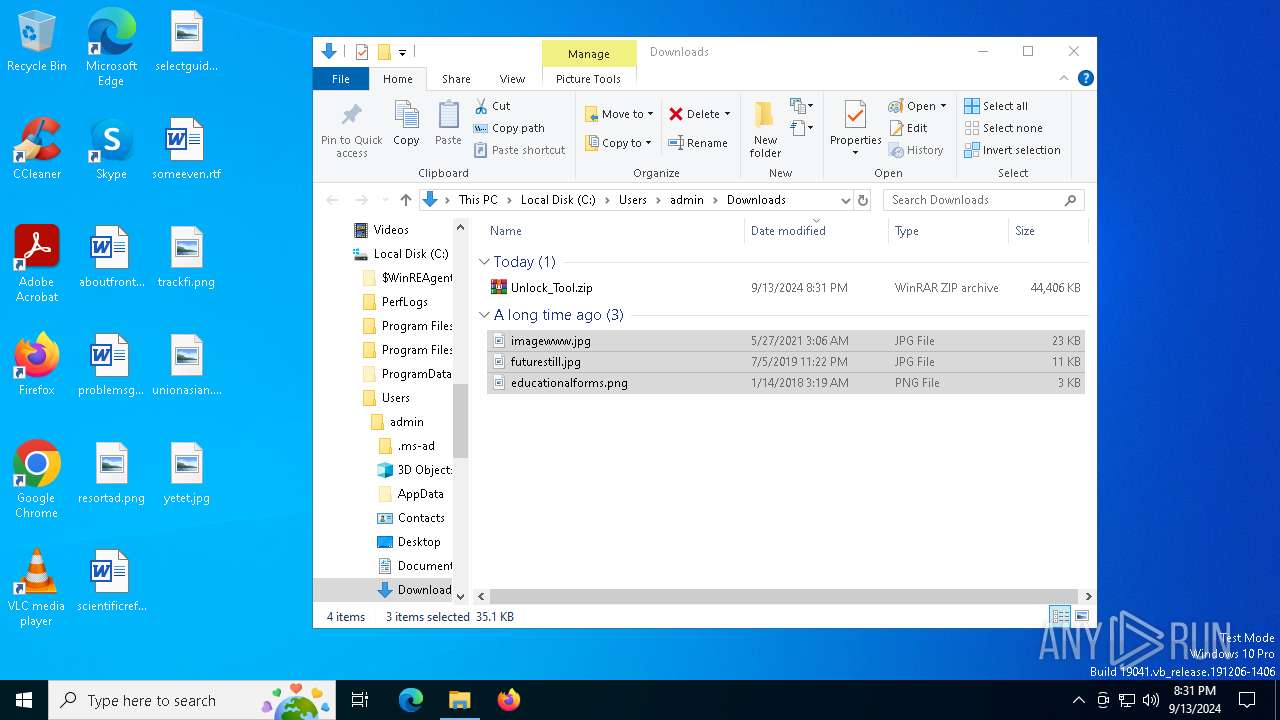
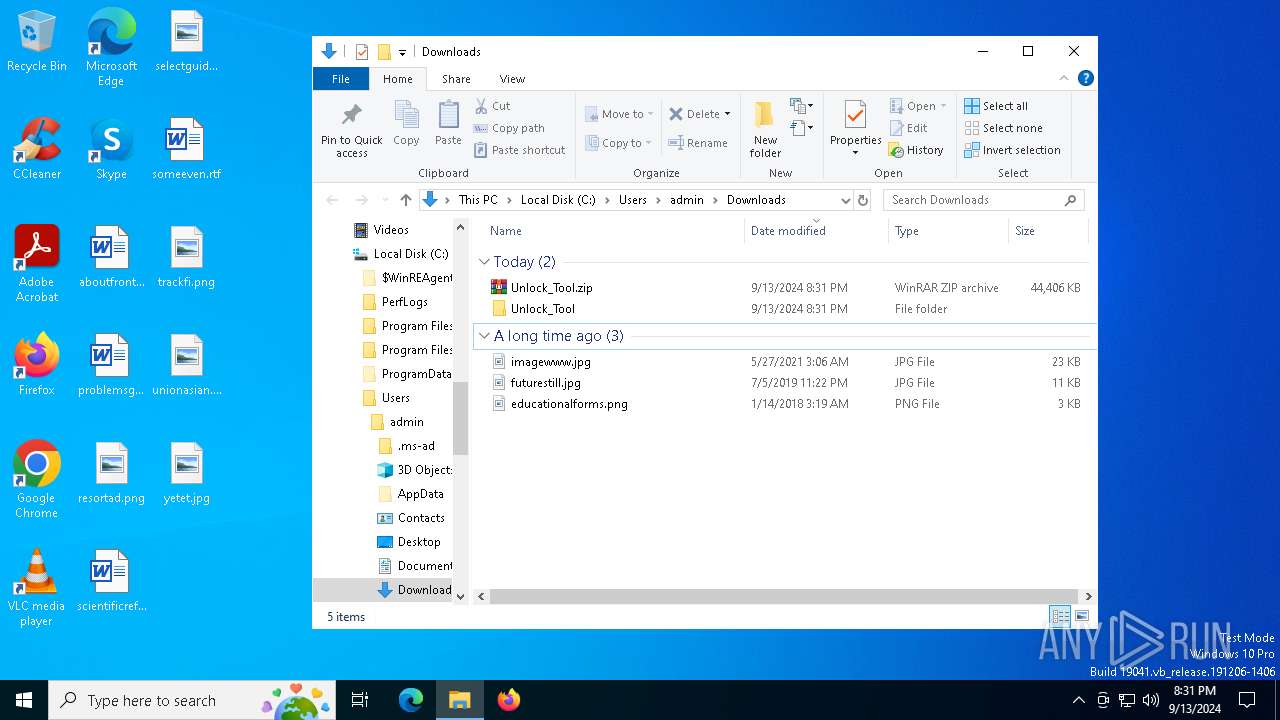
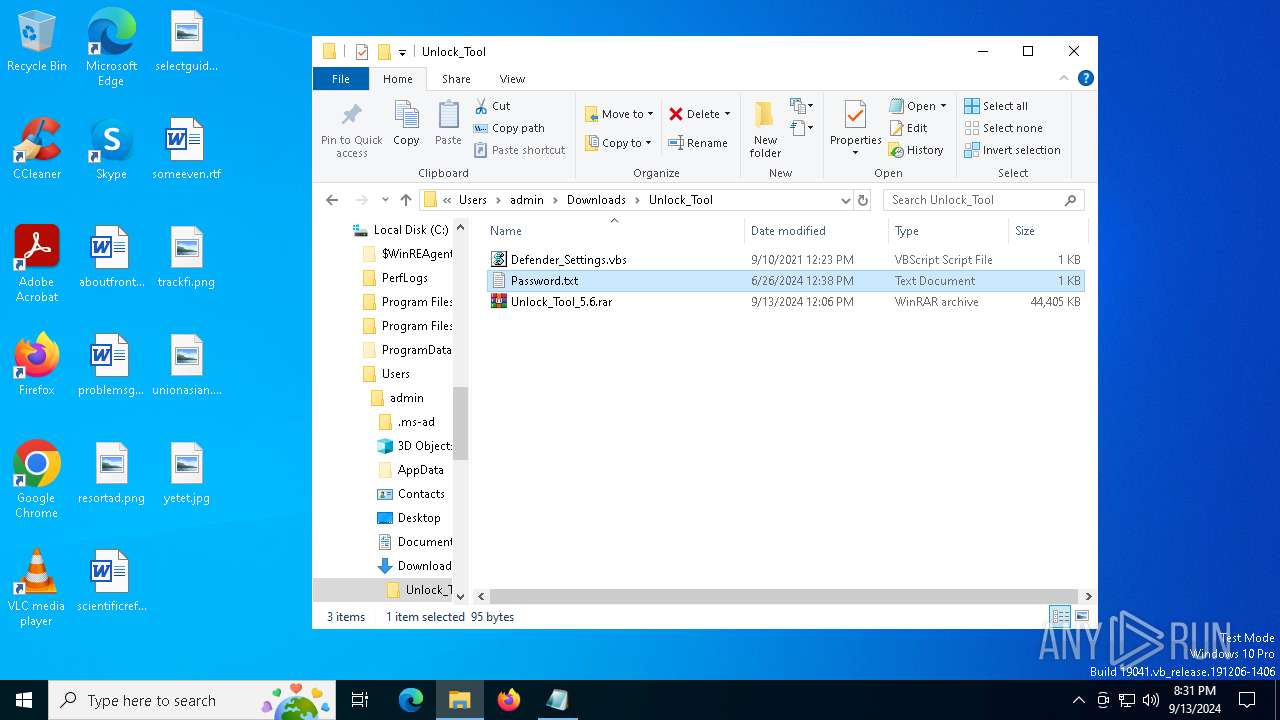
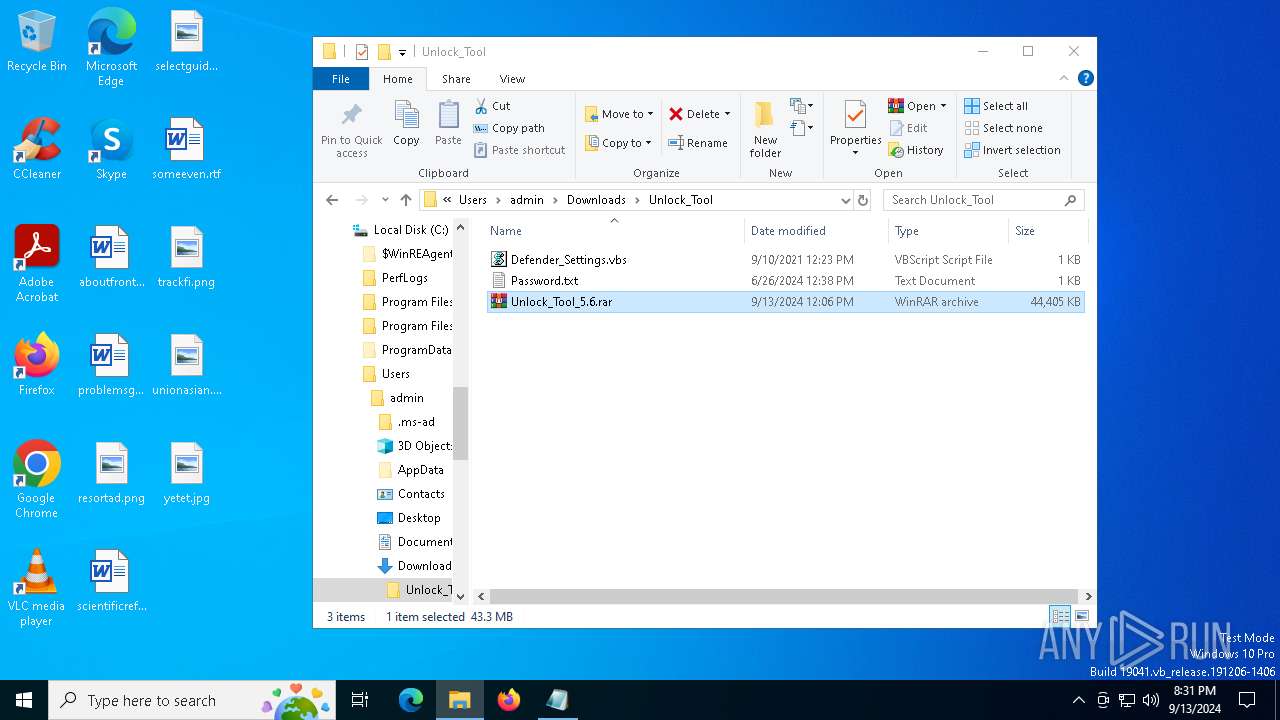
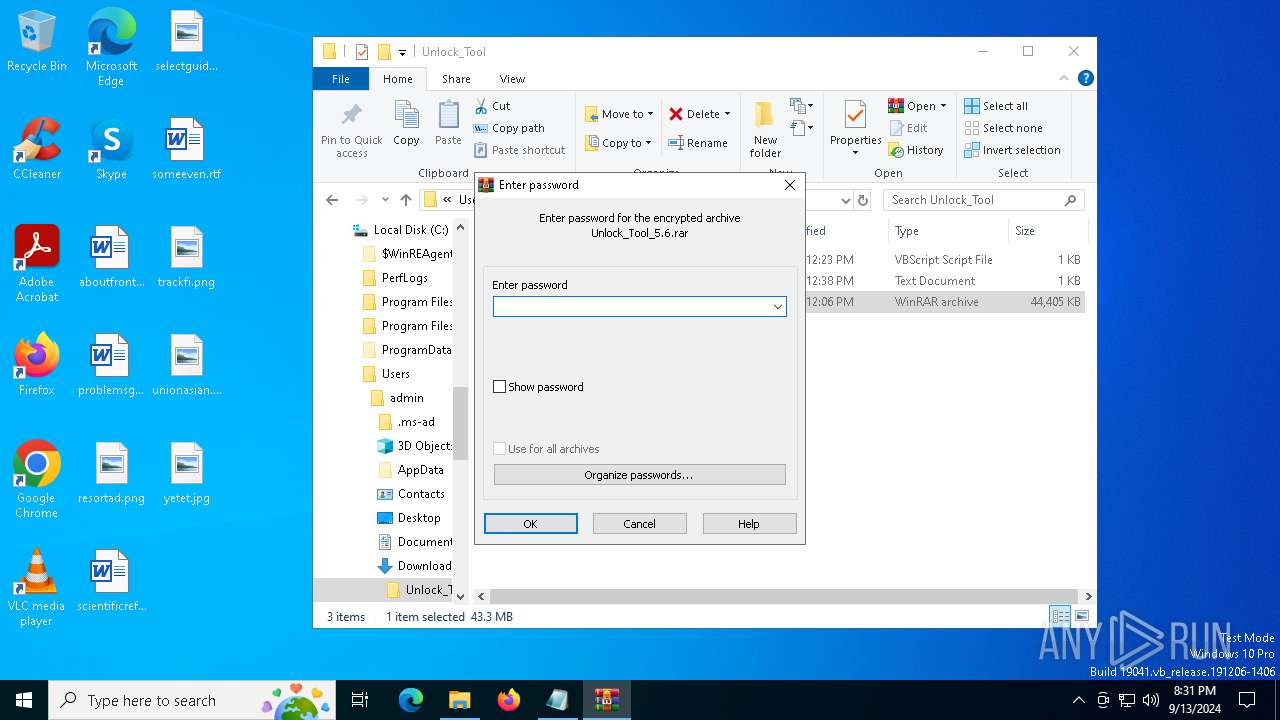
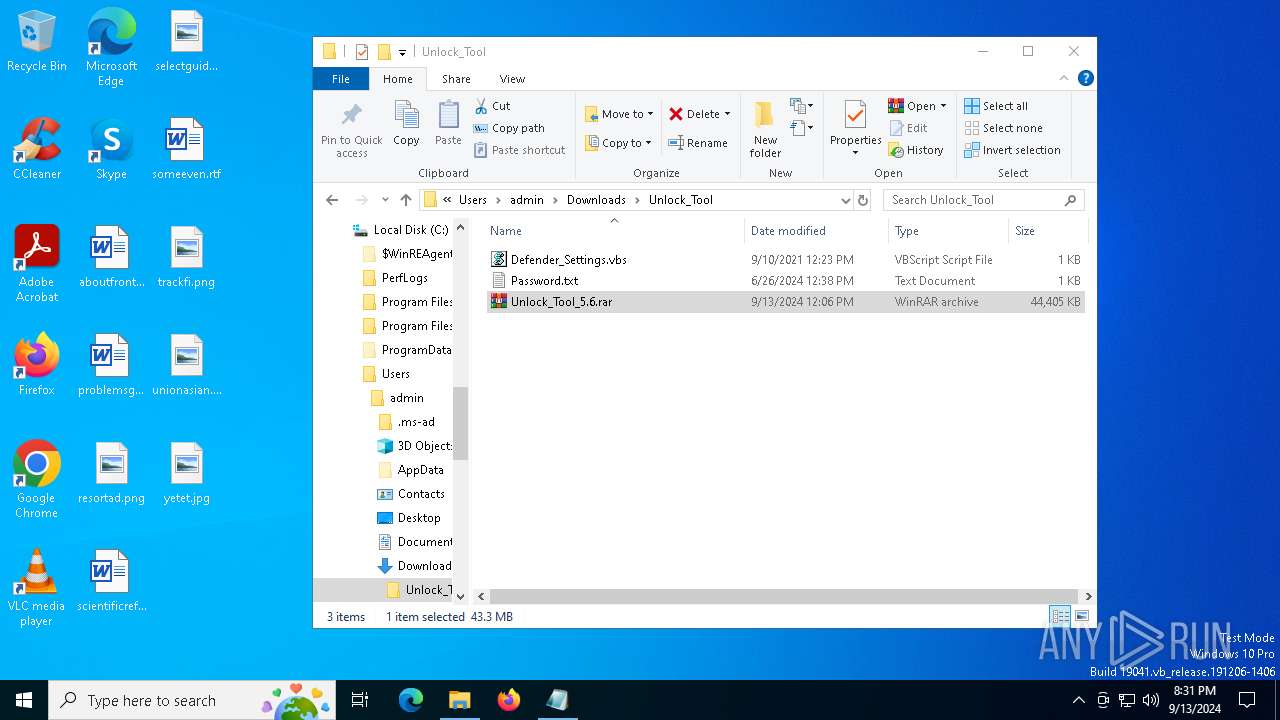
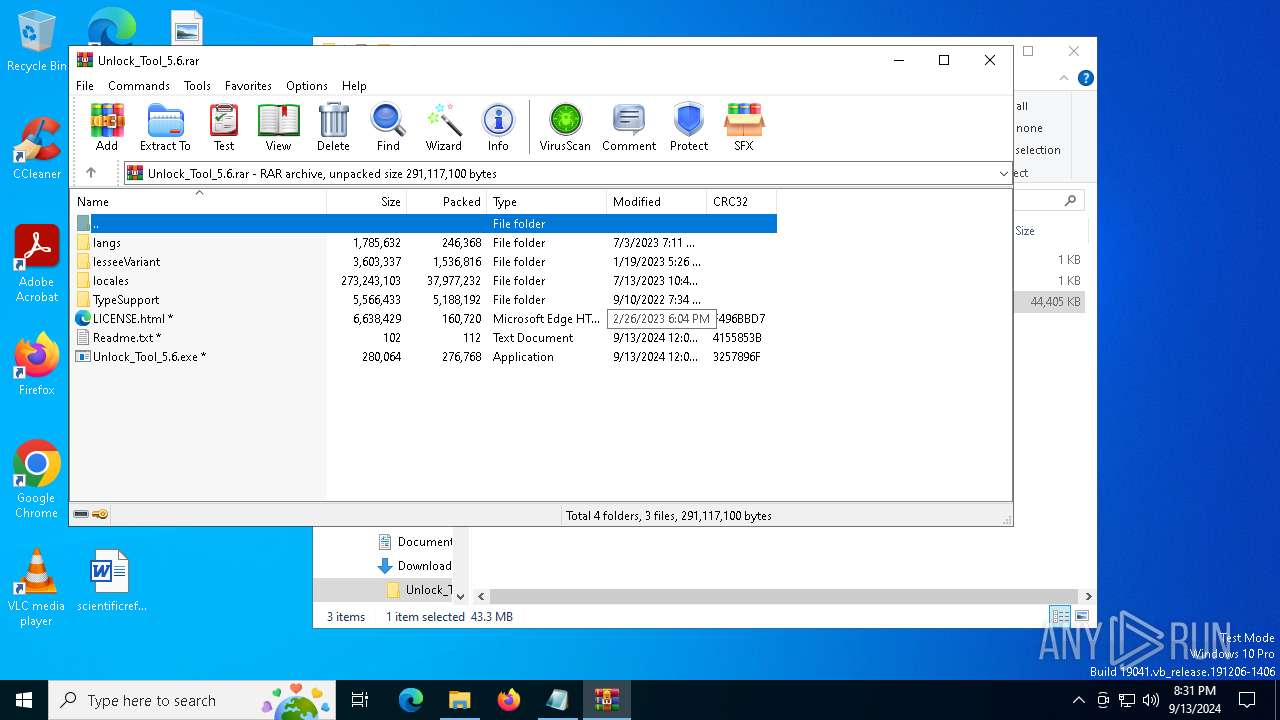
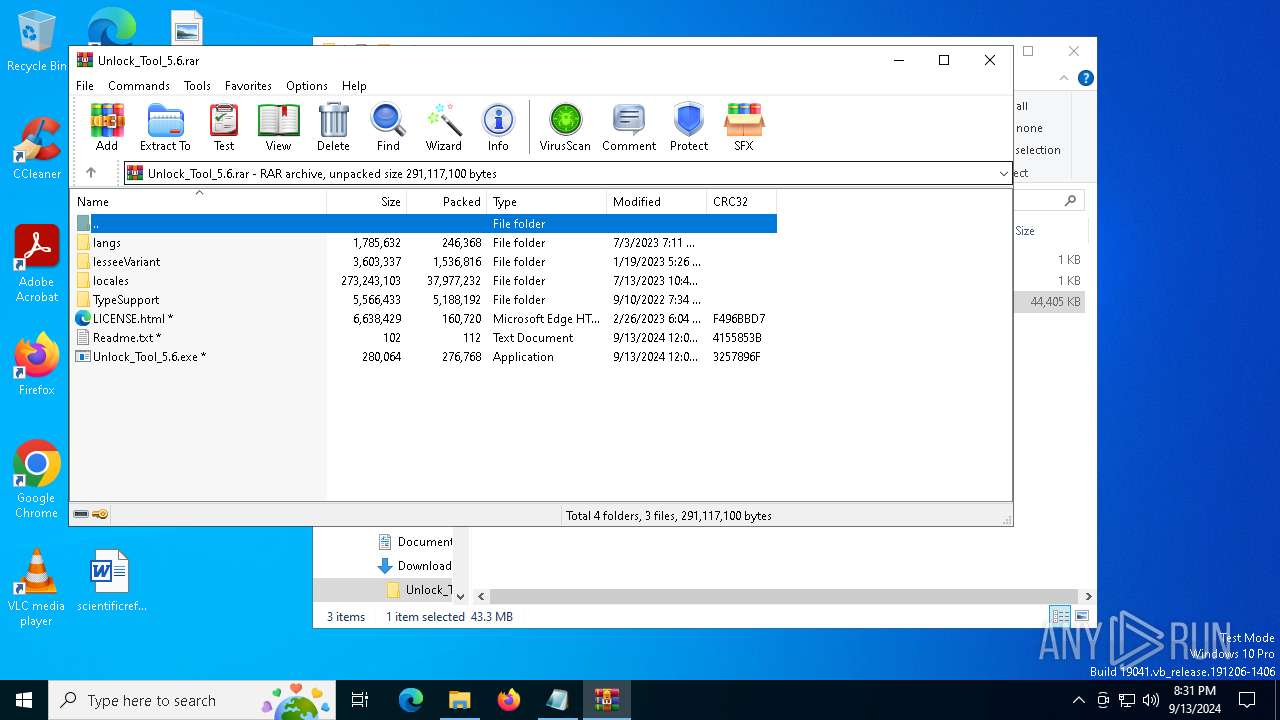
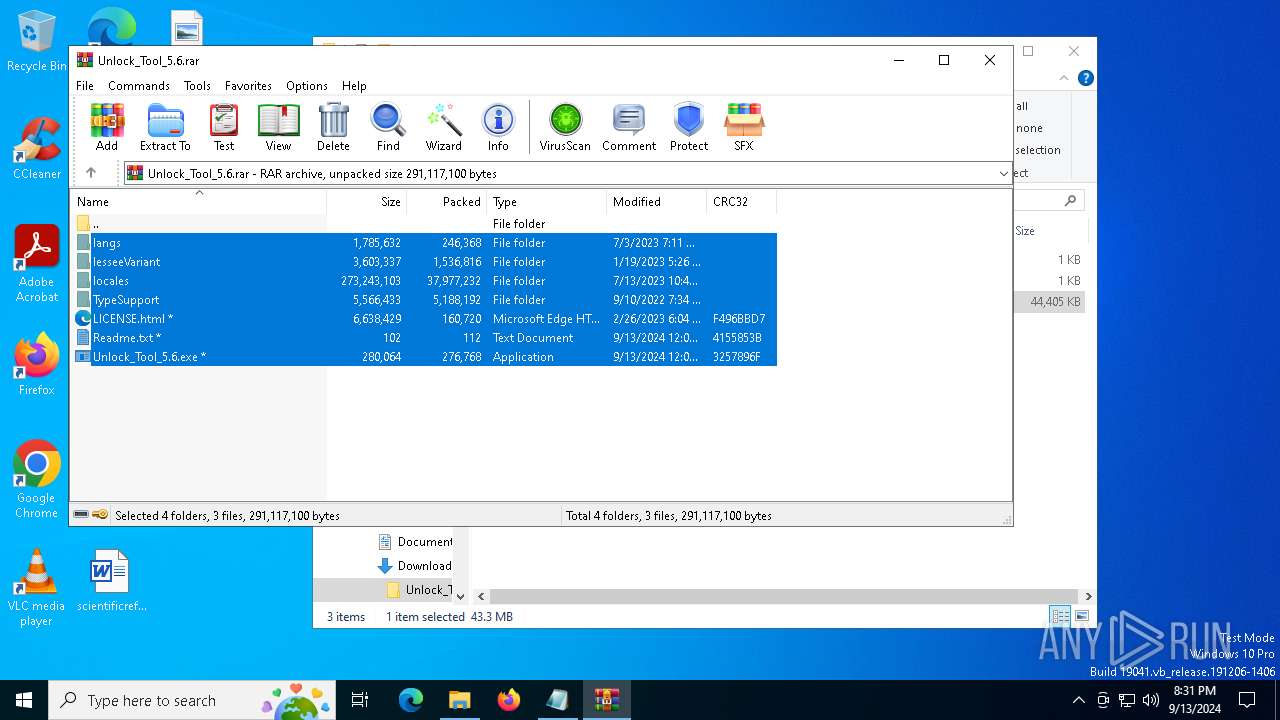
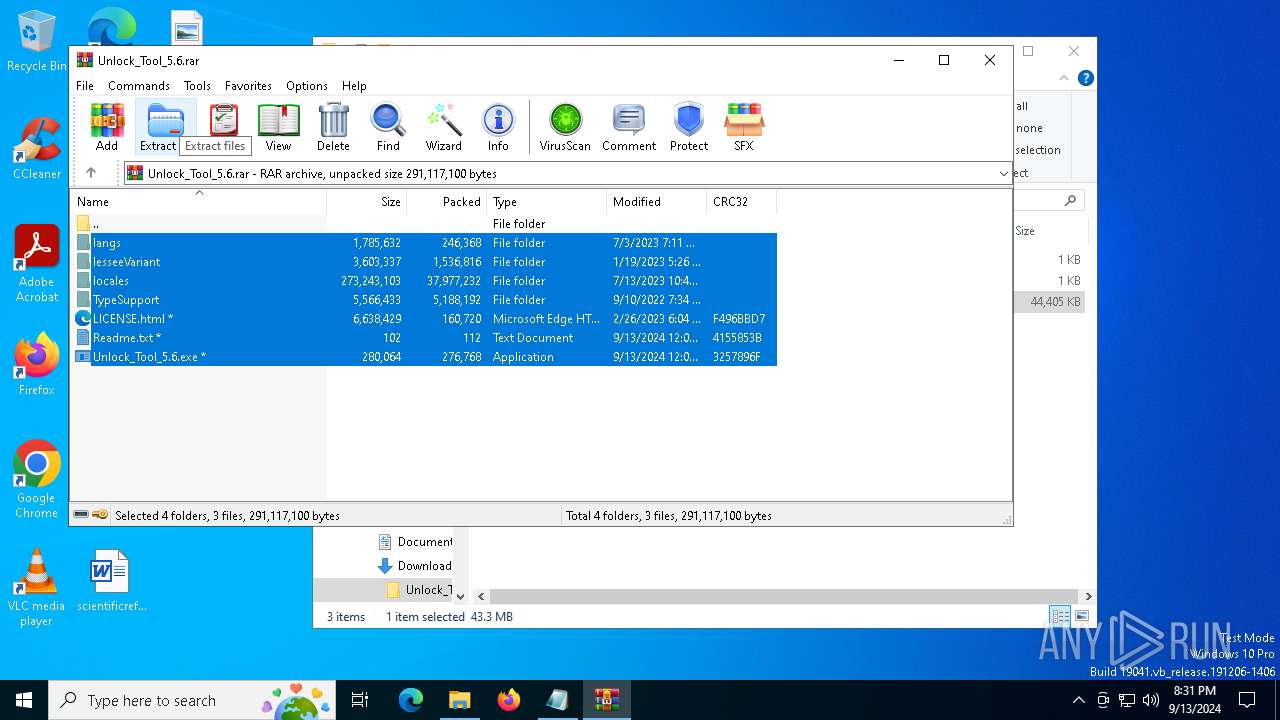
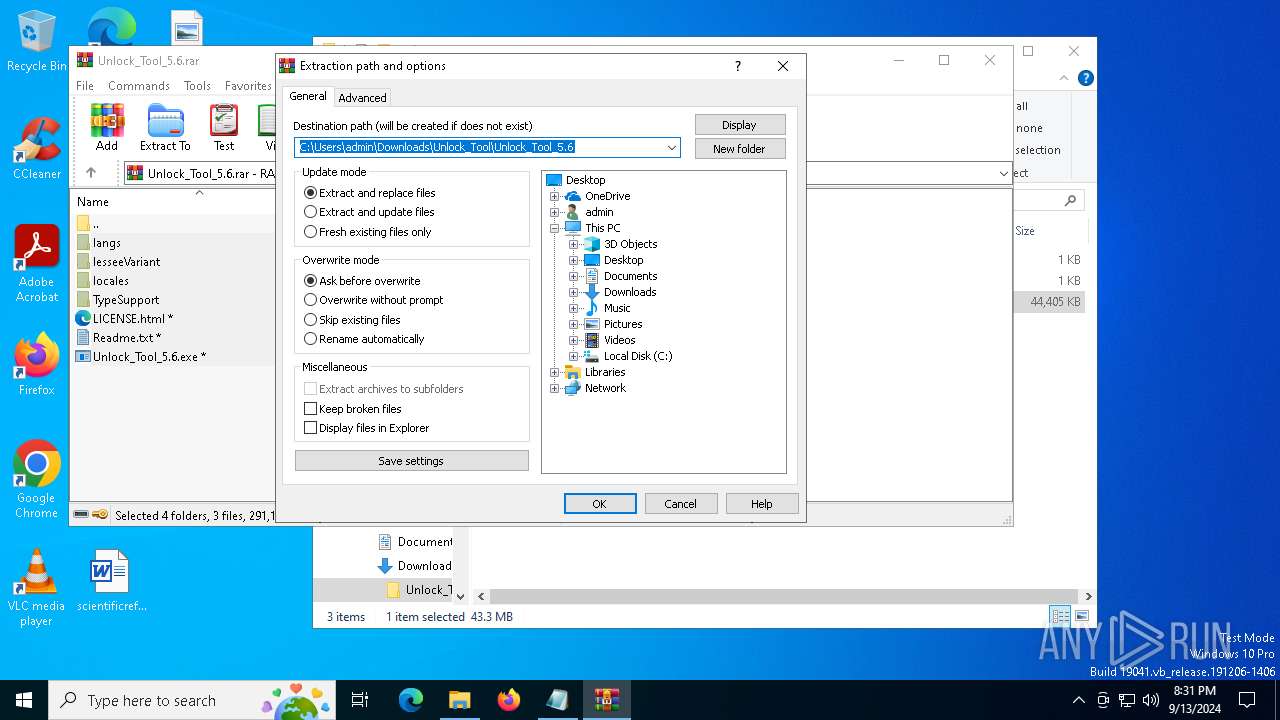
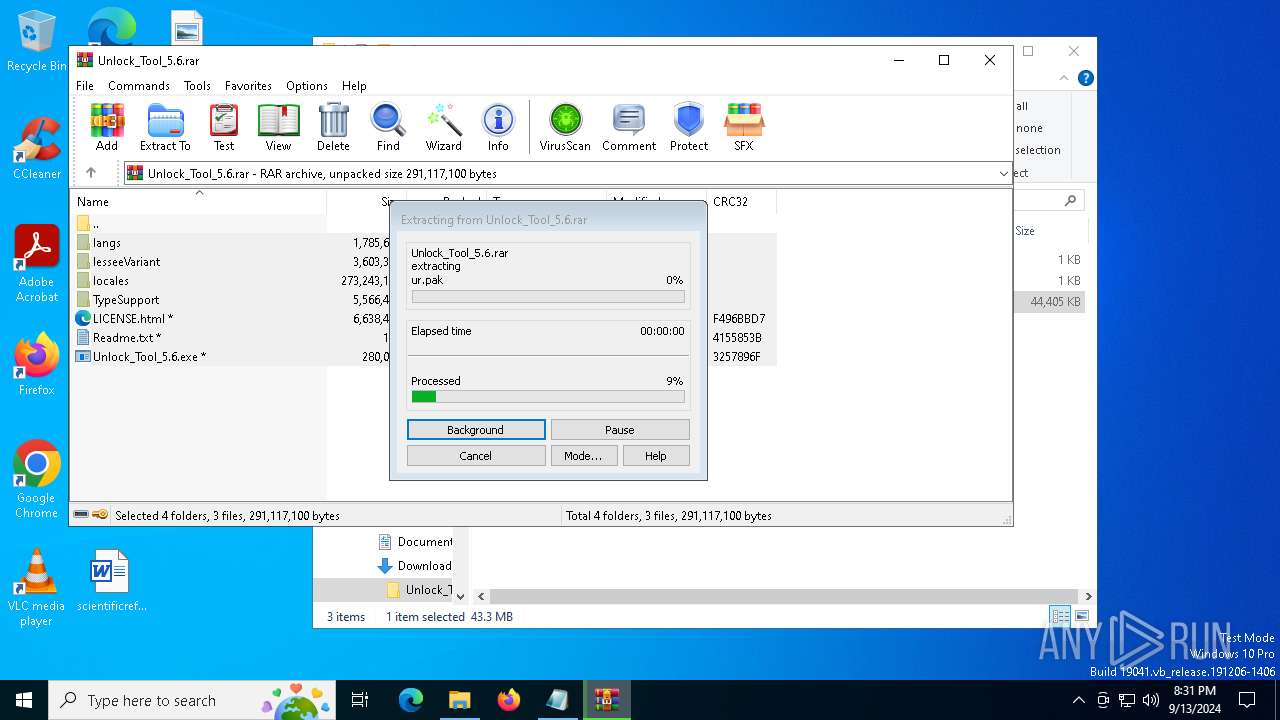
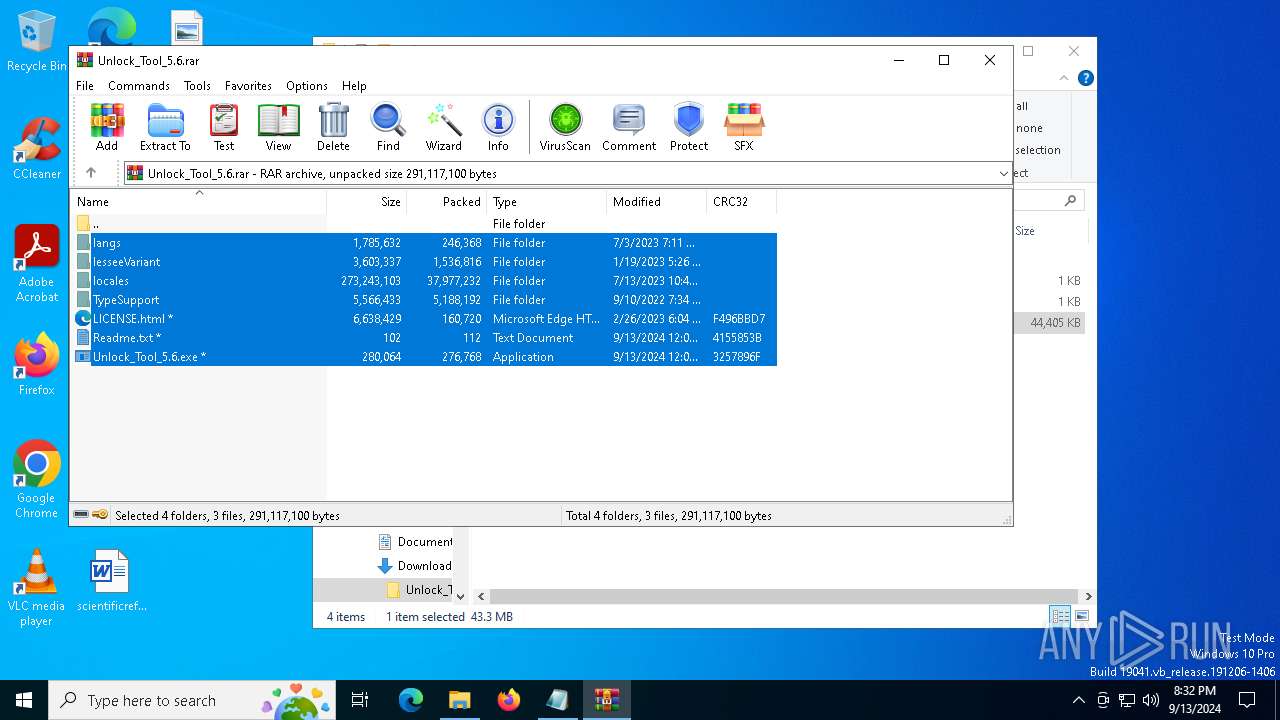
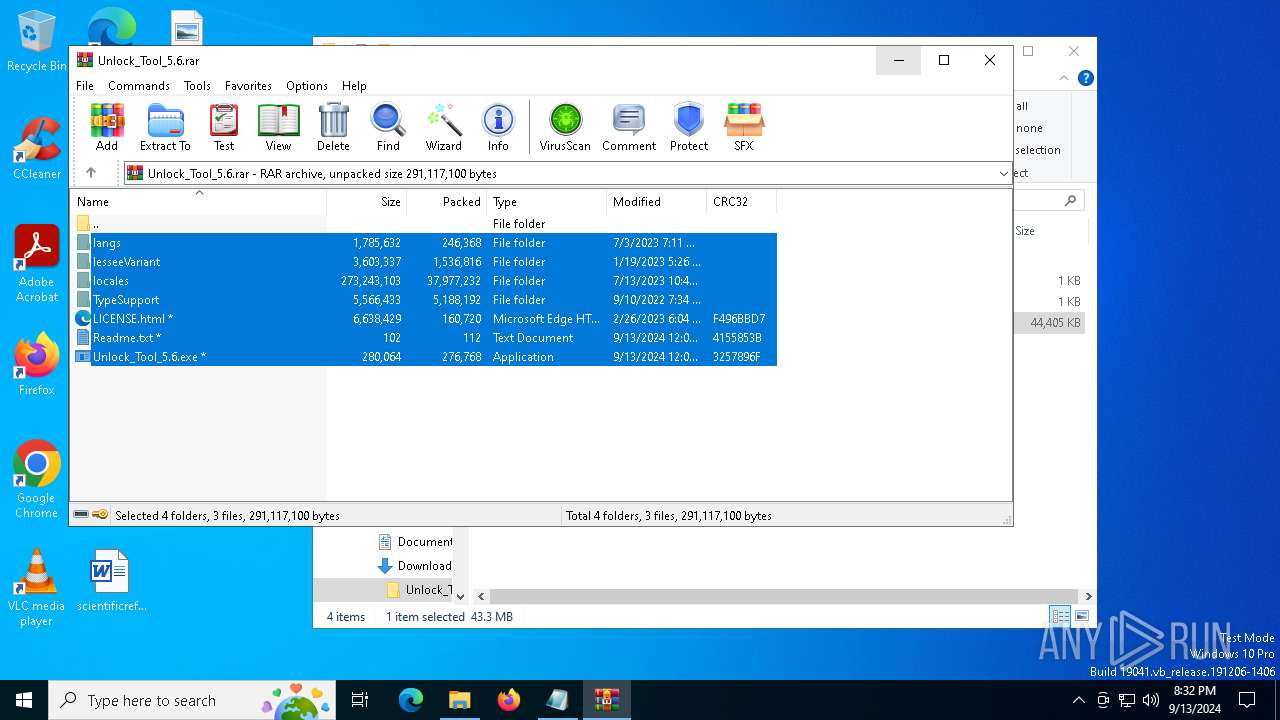
The process uses the downloaded file
- msedge.exe (PID: 8120)
- WinRAR.exe (PID: 7396)
- WinRAR.exe (PID: 2684)
- msedge.exe (PID: 5984)
- msedge.exe (PID: 7708)
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
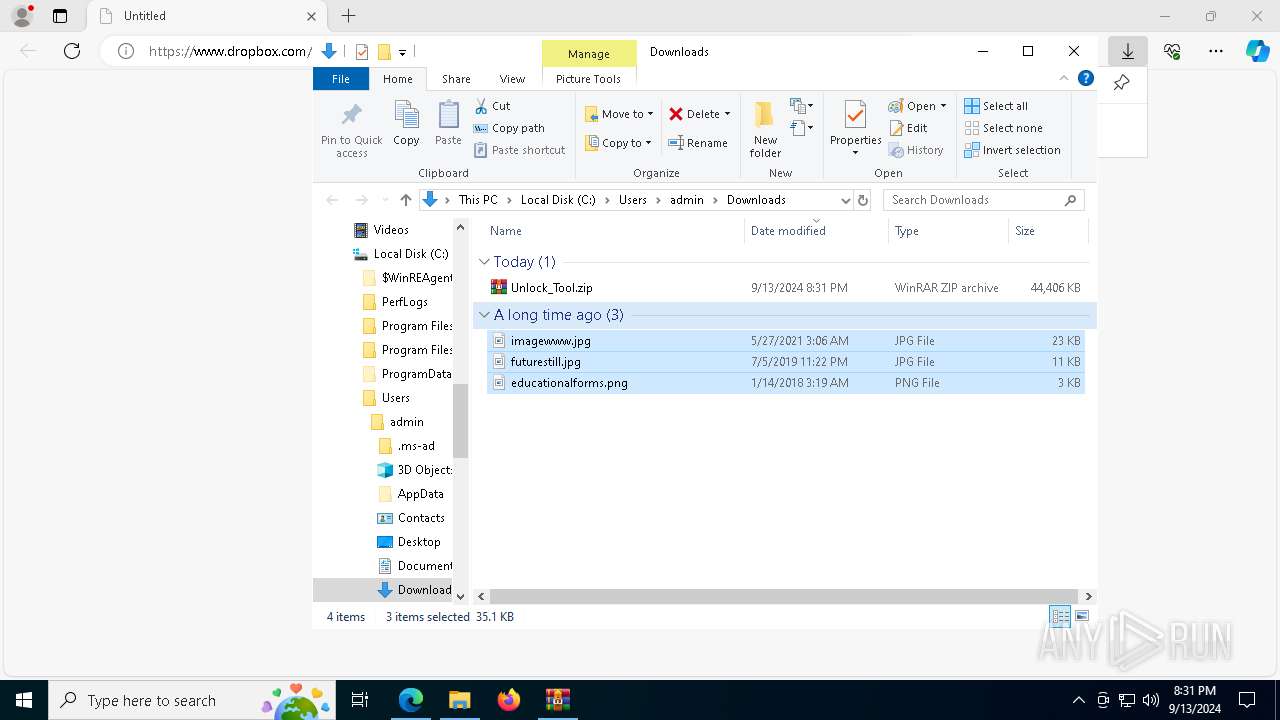
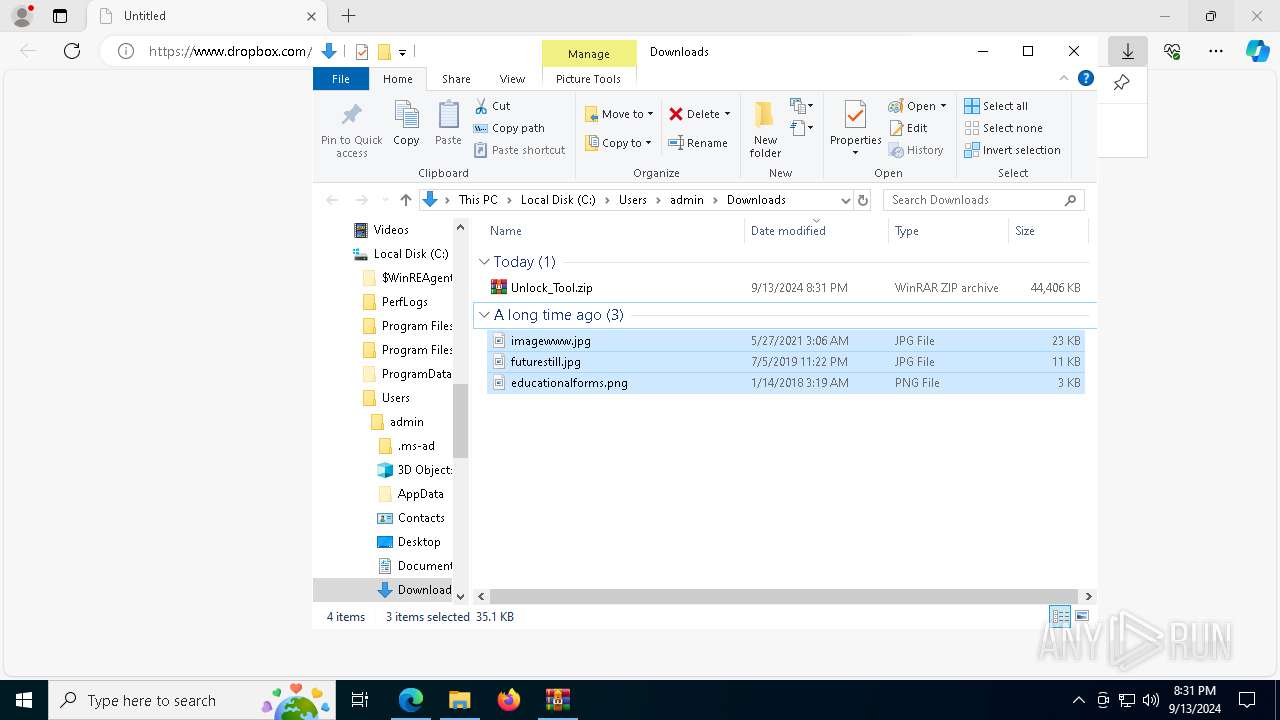
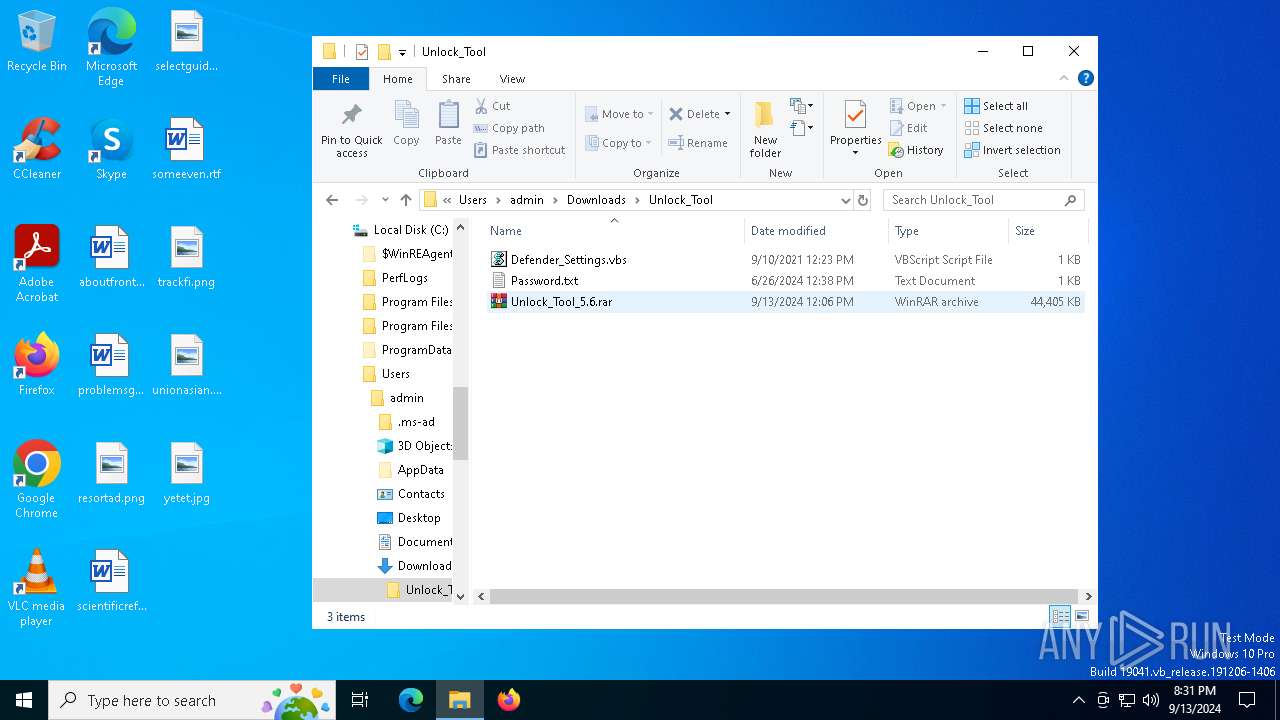
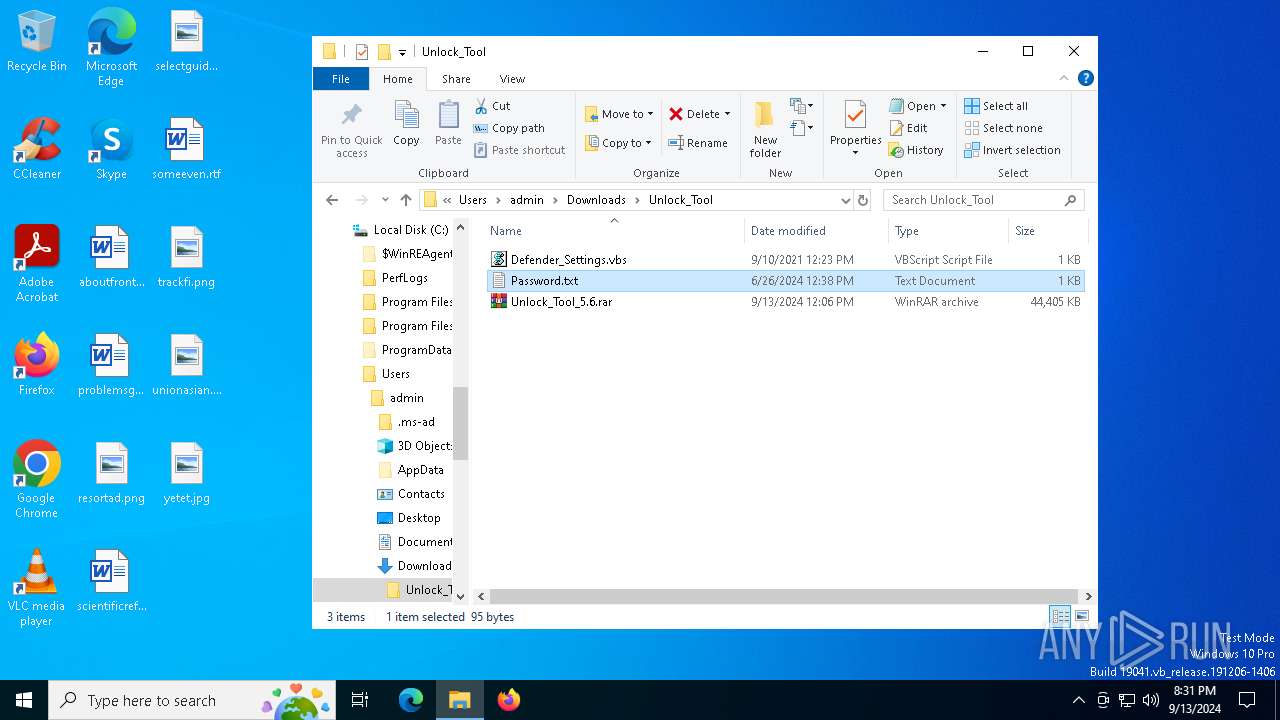
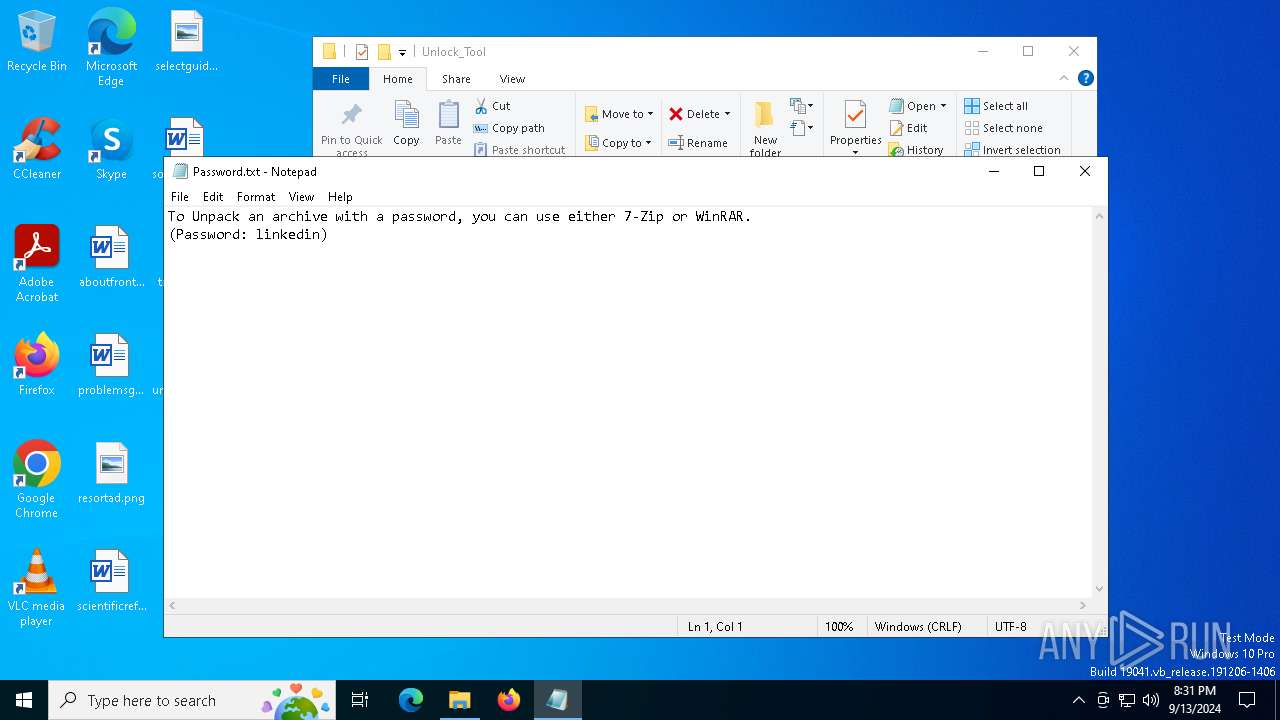
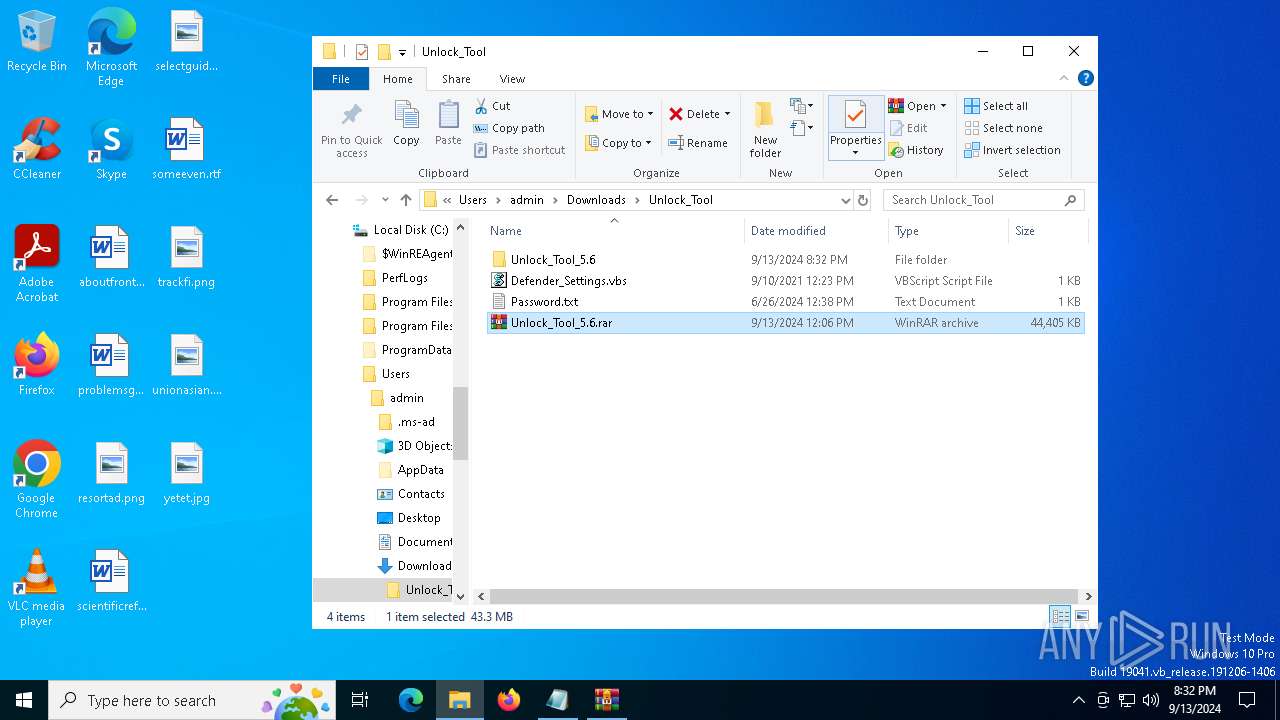
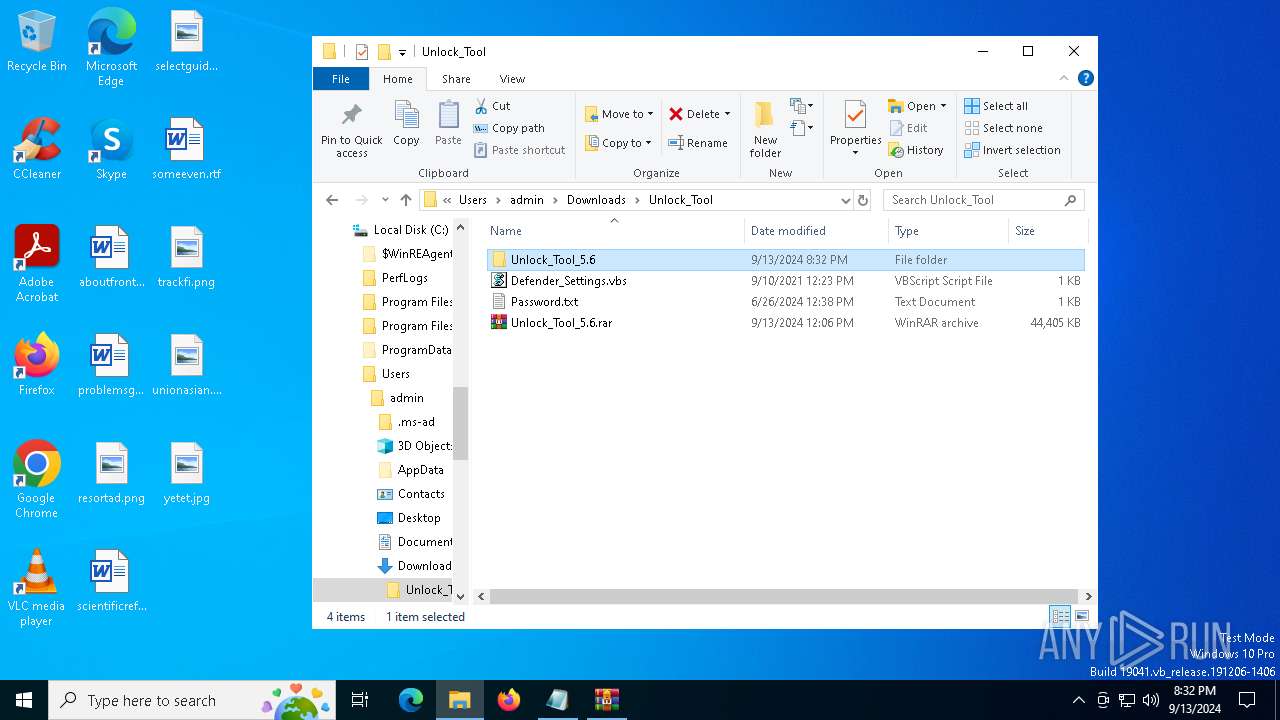
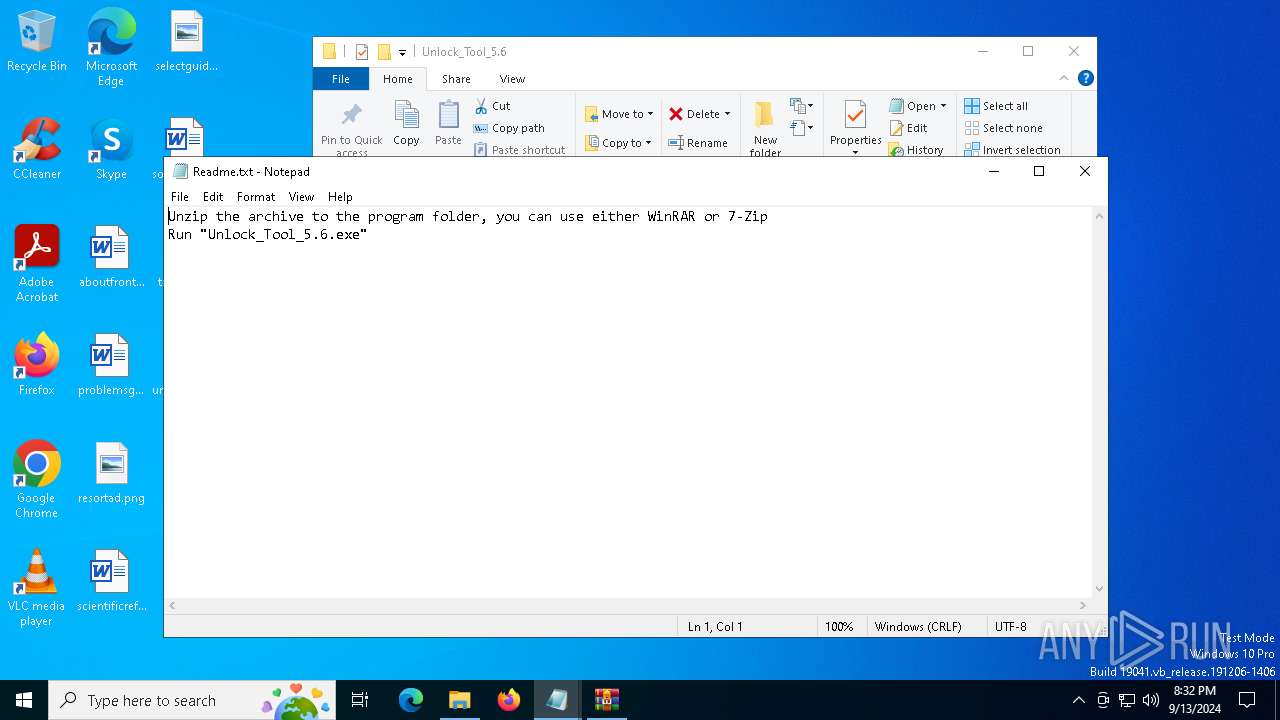
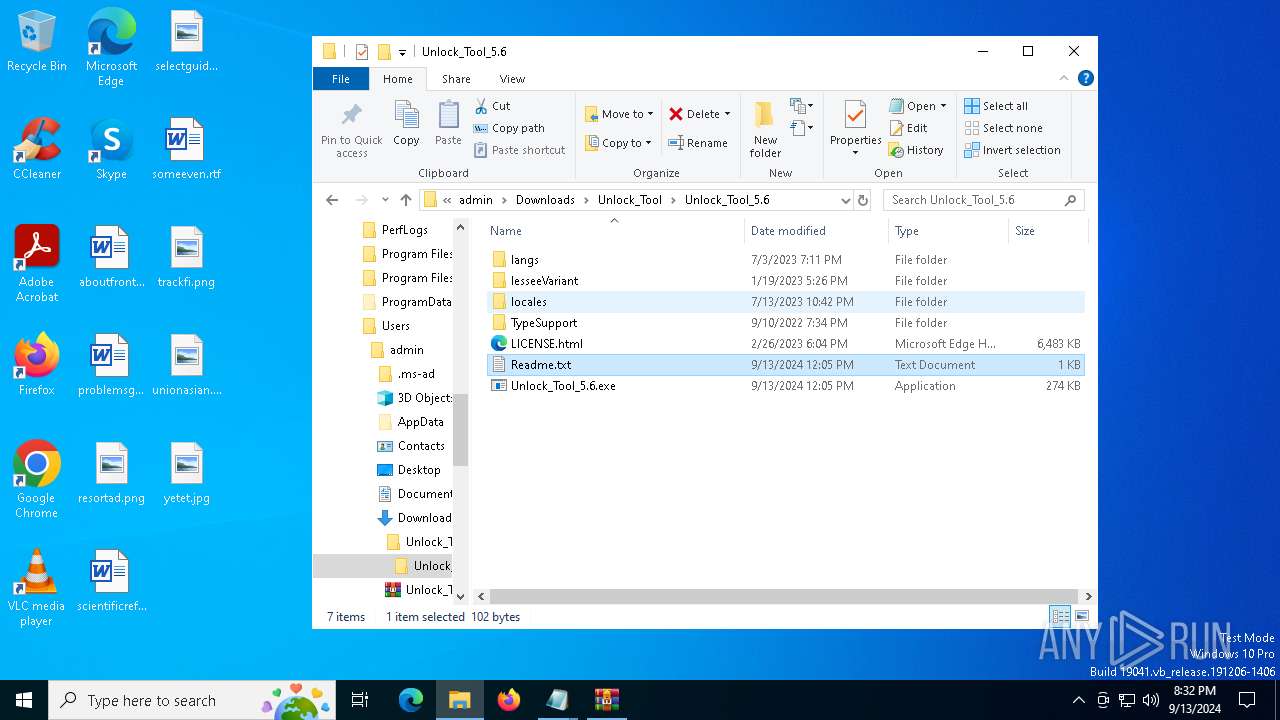
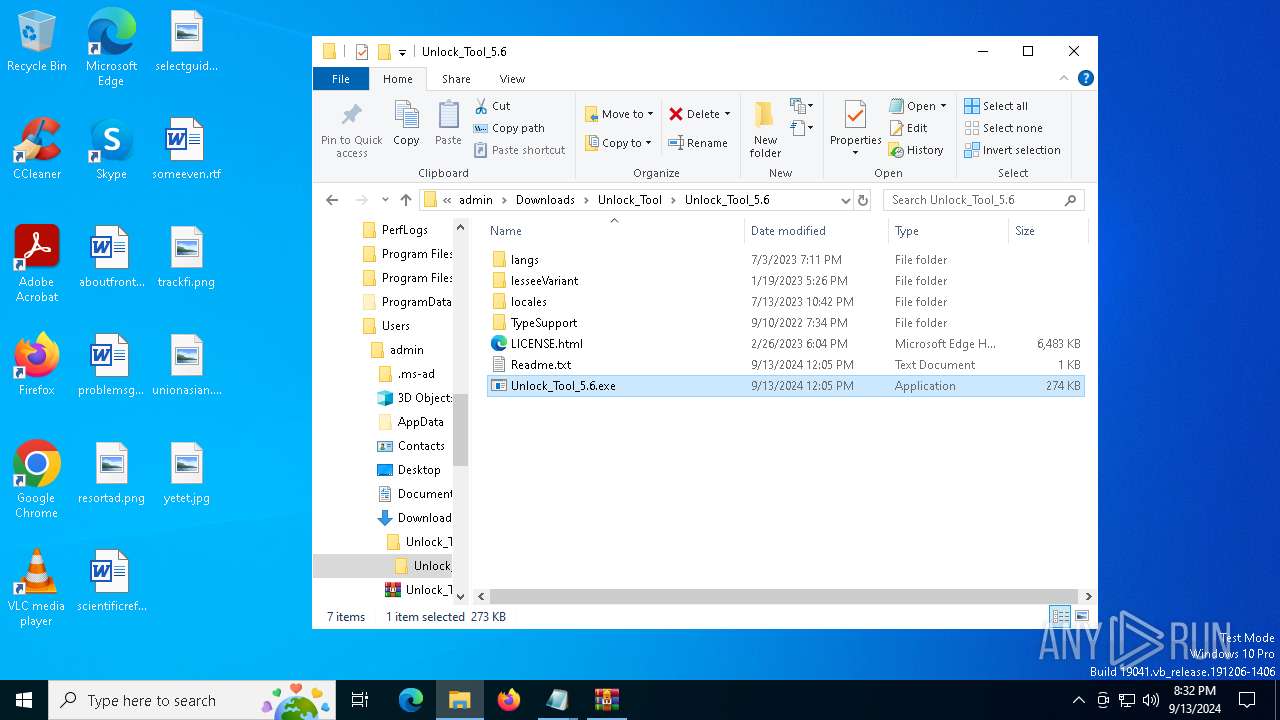
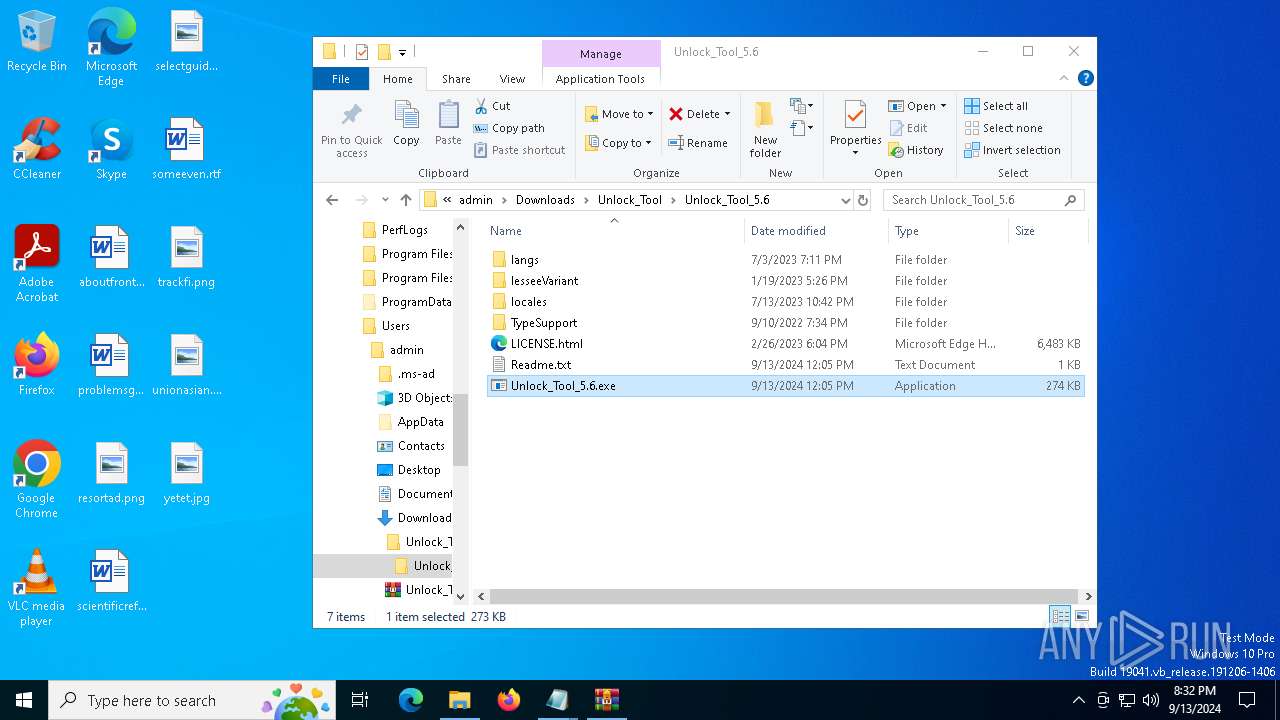
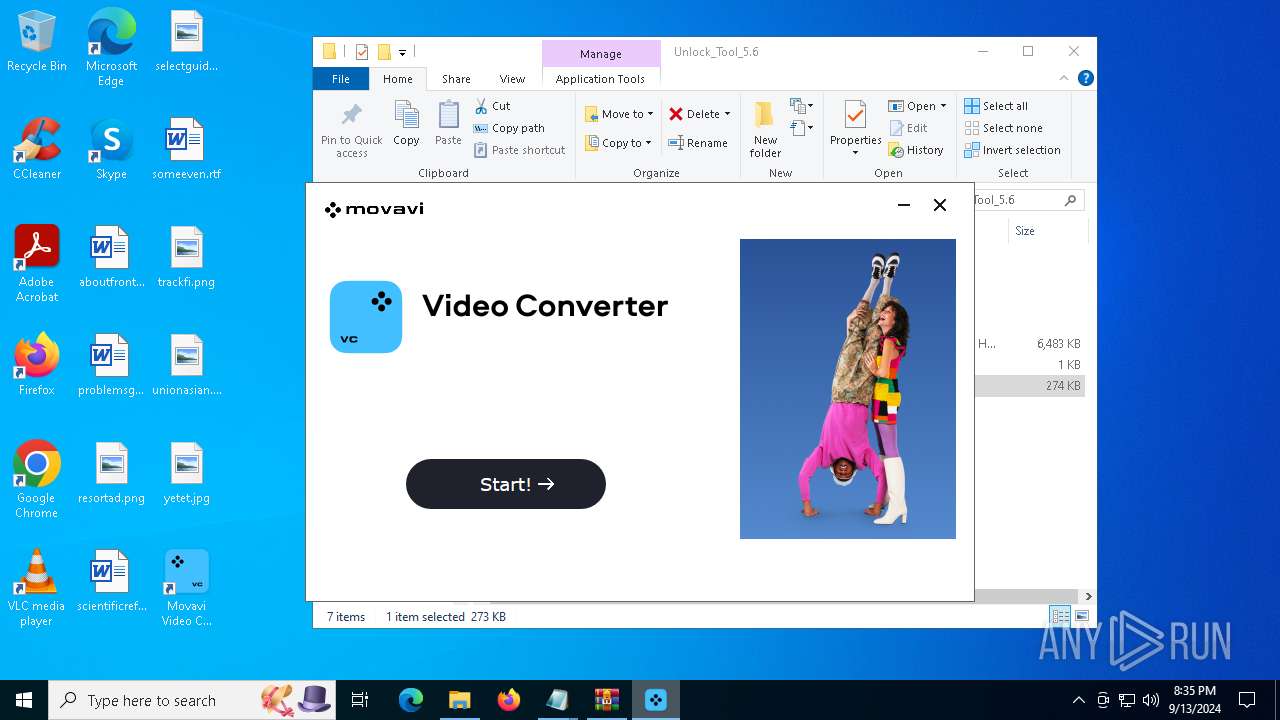
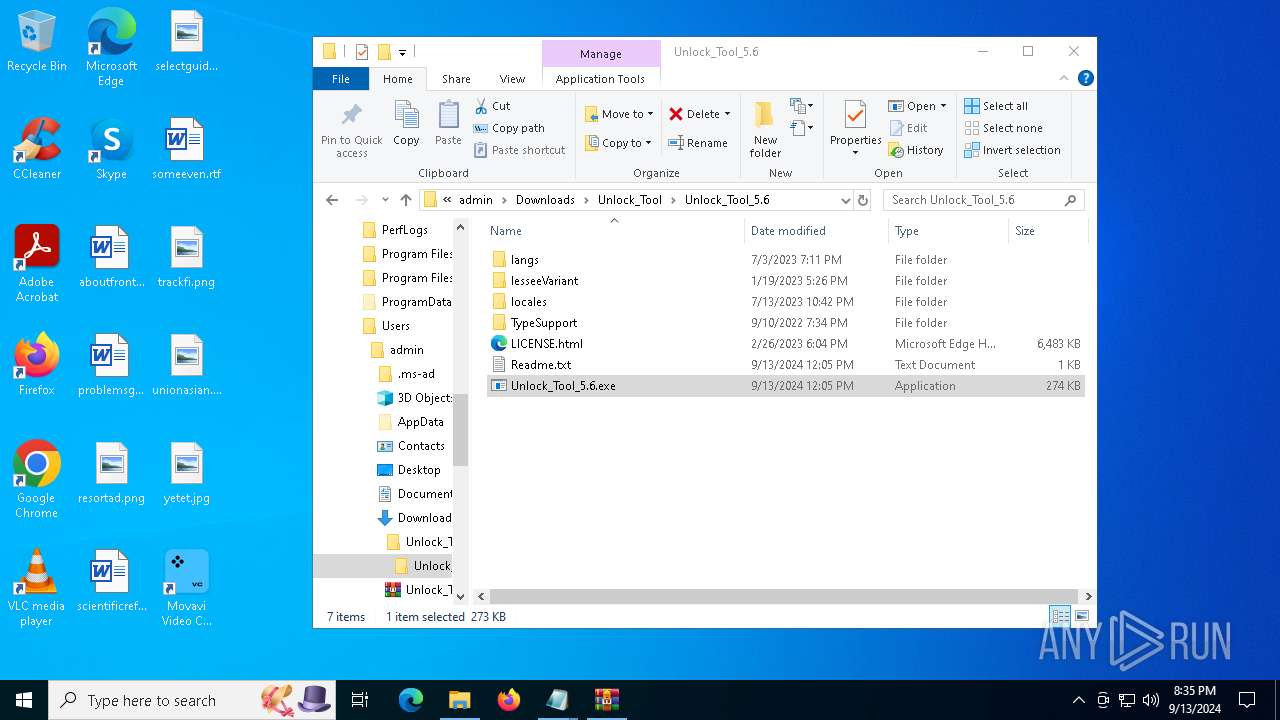
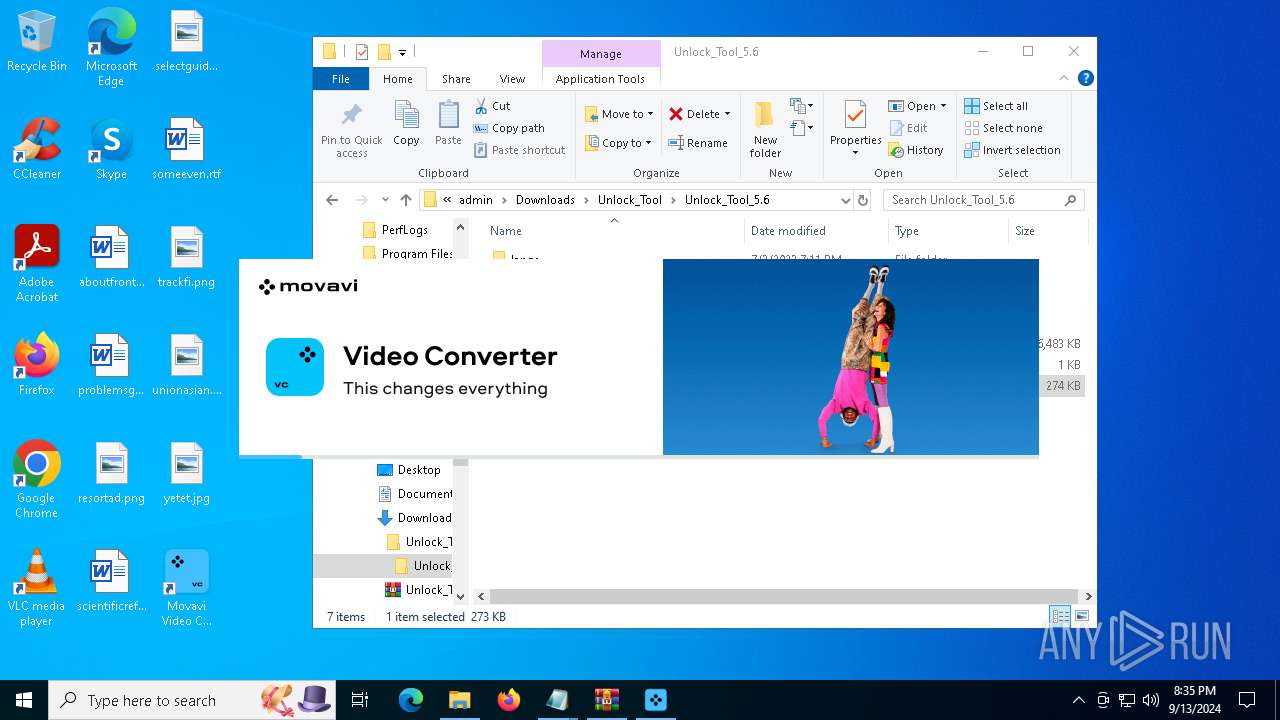
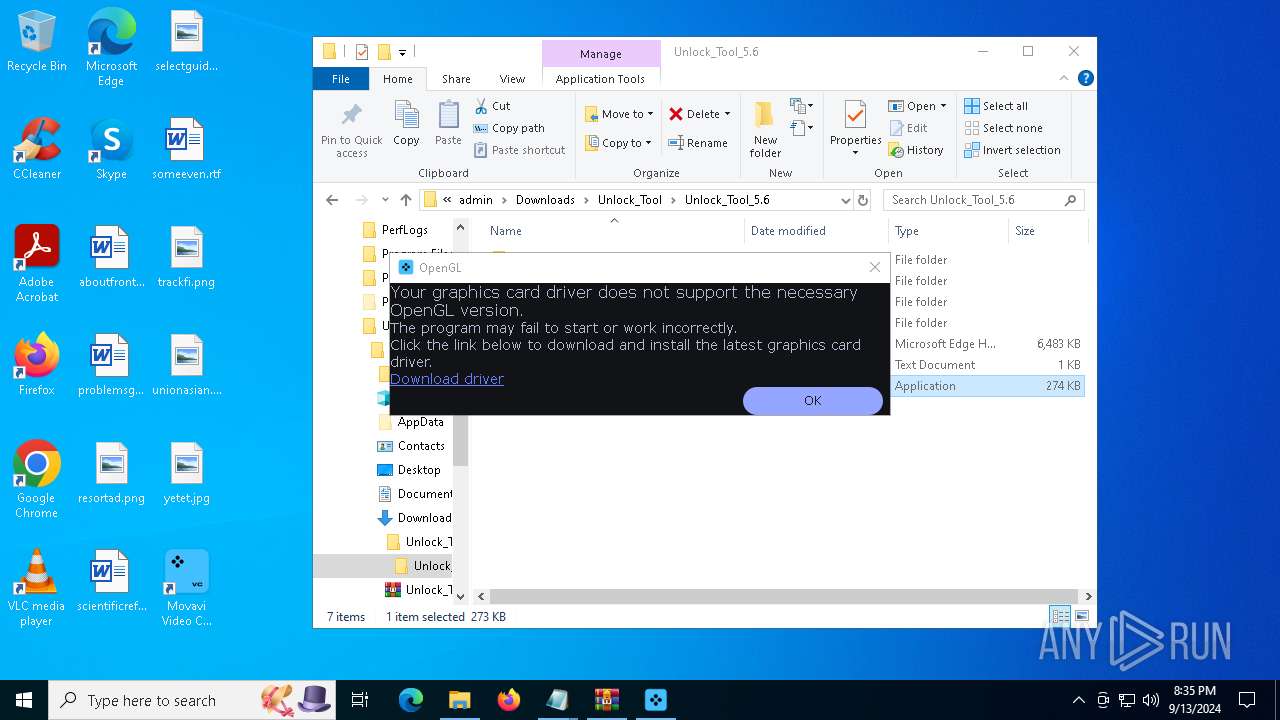
Manual execution by a user
- WinRAR.exe (PID: 7396)
- notepad.exe (PID: 4080)
- WinRAR.exe (PID: 2684)
- notepad.exe (PID: 6556)
- Unlock_Tool_5.6.exe (PID: 4824)
- msedge.exe (PID: 1156)
- Unlock_Tool_5.6.exe (PID: 4544)
- Unlock_Tool_5.6.exe (PID: 9064)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4080)
- notepad.exe (PID: 6556)
Reads the software policy settings
- slui.exe (PID: 7856)
- slui.exe (PID: 940)
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
- InstallerGUI.exe (PID: 4644)
- installer.exe (PID: 6472)
- WebConfigLoader.exe (PID: 7100)
- WebConfigLoader.exe (PID: 7968)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2684)
- msedge.exe (PID: 7708)
- msedge.exe (PID: 788)
- msedge.exe (PID: 7384)
Create files in a temporary directory
- RegAsm.exe (PID: 6168)
- MovaviVideoConverterSetupE_W2abnea_.exe (PID: 3844)
- installer.exe (PID: 6472)
- 2029978299_W2abnea_.exe (PID: 8508)
- InstallerGUI.exe (PID: 4644)
- RegAsm.exe (PID: 6772)
- ConverterAgent.exe (PID: 7688)
- converter.exe (PID: 8116)
- RouterApplication.exe (PID: 6132)
- RouterApplication.exe (PID: 6192)
Checks proxy server information
- slui.exe (PID: 940)
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
- InstallerGUI.exe (PID: 4644)
- RegAsm.exe (PID: 736)
- WebConfigLoader.exe (PID: 7100)
- converter.exe (PID: 8116)
- WebConfigLoader.exe (PID: 7968)
Sends debugging messages
- msedge.exe (PID: 7772)
- installer.exe (PID: 6472)
- msedge.exe (PID: 8820)
- PluginChecker.exe (PID: 7056)
- ConverterAgent.exe (PID: 7688)
- converter.exe (PID: 8116)
- ShellExperienceHost.exe (PID: 5084)
Creates files or folders in the user directory
- crashpad_handler.exe (PID: 5984)
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
- InstallerGUI.exe (PID: 4644)
- crashpad_handler.exe (PID: 8500)
- PluginChecker.exe (PID: 7056)
- PluginChecker.exe (PID: 3028)
- PluginChecker.exe (PID: 8052)
- PluginChecker.exe (PID: 2460)
- PluginChecker.exe (PID: 6432)
- PluginChecker.exe (PID: 4020)
- PluginChecker.exe (PID: 4196)
- PluginChecker.exe (PID: 788)
- PluginChecker.exe (PID: 6380)
- PluginChecker.exe (PID: 7380)
- PluginChecker.exe (PID: 9108)
- PluginChecker.exe (PID: 7876)
- PluginChecker.exe (PID: 2144)
- PluginChecker.exe (PID: 236)
- PluginChecker.exe (PID: 7316)
- PluginChecker.exe (PID: 8360)
- PluginChecker.exe (PID: 9204)
- PluginChecker.exe (PID: 7076)
- PluginChecker.exe (PID: 9180)
- PluginChecker.exe (PID: 1492)
- PluginChecker.exe (PID: 4880)
- PluginChecker.exe (PID: 9200)
- PluginChecker.exe (PID: 7792)
- PluginChecker.exe (PID: 5532)
- PluginChecker.exe (PID: 2484)
- PluginChecker.exe (PID: 6888)
- PluginChecker.exe (PID: 6548)
- CoreChecker.exe (PID: 3492)
- PluginChecker.exe (PID: 608)
- PluginChecker.exe (PID: 5908)
- CodecChecker.exe (PID: 7428)
- CodecChecker.exe (PID: 6252)
- CodecChecker.exe (PID: 7868)
- CodecChecker.exe (PID: 6612)
- CodecChecker.exe (PID: 6148)
- CodecChecker.exe (PID: 8196)
- CodecChecker.exe (PID: 8200)
- RegAsm.exe (PID: 736)
- WebConfigLoader.exe (PID: 7100)
- crashpad_handler.exe (PID: 6648)
- ConverterAgent.exe (PID: 7688)
- converter.exe (PID: 8116)
- WebConfigLoader.exe (PID: 7968)
- RouterApplication.exe (PID: 6132)
Process checks computer location settings
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
Creates files in the program directory
- RegAsm.exe (PID: 6168)
- InstallerGUI.exe (PID: 4644)
- RegAsm.exe (PID: 736)
Reads the machine GUID from the registry
- installer.exe (PID: 6472)
- RegAsm.exe (PID: 6168)
- PluginChecker.exe (PID: 7876)
- CoreChecker.exe (PID: 3492)
- CodecChecker.exe (PID: 7868)
- CodecChecker.exe (PID: 7428)
- CodecChecker.exe (PID: 8200)
- CodecChecker.exe (PID: 6148)
- CodecChecker.exe (PID: 8196)
- CodecChecker.exe (PID: 6612)
- CodecChecker.exe (PID: 6252)
- RegAsm.exe (PID: 736)
- converter.exe (PID: 8116)
Attempting to use instant messaging service
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
Reads CPU info
- RegAsm.exe (PID: 6168)
- CodecChecker.exe (PID: 6612)
- RegAsm.exe (PID: 736)
Reads product name
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 736)
Themida protector has been detected
- InstallerGUI.exe (PID: 4644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Vidar
(PID) Process(6168) RegAsm.exe
C2https://t.me/edm0d
URLhttps://steamcommunity.com/profiles/
RC40123456789ABCDEF
Total processes
385
Monitored processes
248
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6004 --field-trial-handle=2428,i,9104317460254115978,14051852028199183887,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe" Effects EffectFactory | C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe | — | CoreChecker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 608 | "C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe" MuxerHEIF MuxerFactory | C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe | — | CoreChecker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 736 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | Unlock_Tool_5.6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2536 --field-trial-handle=2412,i,15565015475588057848,16958013596220586390,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | "C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe" EncoderAMF CodecFactory | C:\Users\admin\AppData\Local\Temp\Movavi-installer-538bff92-8b9d-4088-ada3-a66cad99770c\PluginChecker.exe | — | CoreChecker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PluginChecker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5372 --field-trial-handle=2428,i,9104317460254115978,14051852028199183887,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 940 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CodecChecker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
81 434
Read events
81 158
Write events
261
Delete events
15
Modification events
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A8954B619C802F00 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 33A652619C802F00 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459590 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CFE710AC-D0E9-4A1A-B164-0B2270F821BA} | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459590 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B82F4B31-4276-466B-A1C7-69C5753E4E89} | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
752
Suspicious files
1 662
Text files
1 448
Unknown types
136
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129ec8.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129ec8.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129ef7.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129ef7.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129f07.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
361
DNS requests
363
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6192 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5284 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726551334&P2=404&P3=2&P4=BRpRZVyJMXWh7f82BhmK%2bv%2bCKTa9ukLx4VWNdMkpNPogsgQ8OM9igtWHP8P7FoE9qhpqqpcEQ0yHMFgeGHuELA%3d%3d | unknown | — | — | whitelisted |
788 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
5284 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726551334&P2=404&P3=2&P4=BRpRZVyJMXWh7f82BhmK%2bv%2bCKTa9ukLx4VWNdMkpNPogsgQ8OM9igtWHP8P7FoE9qhpqqpcEQ0yHMFgeGHuELA%3d%3d | unknown | — | — | whitelisted |
788 | msedge.exe | GET | 304 | 95.101.54.195:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
5284 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726551334&P2=404&P3=2&P4=BRpRZVyJMXWh7f82BhmK%2bv%2bCKTa9ukLx4VWNdMkpNPogsgQ8OM9igtWHP8P7FoE9qhpqqpcEQ0yHMFgeGHuELA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6880 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6020 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4668 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5244 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5244 | msedge.exe | 162.125.72.18:443 | www.dropbox.com | DROPBOX | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.dropbox.com |
| shared |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
788 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
788 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
788 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
788 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
6168 | RegAsm.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
6168 | RegAsm.exe | A Network Trojan was detected | STEALER [ANY.RUN] Vidar TLS Connection Attempt |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
msedge.exe | [0913/203306.049:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0913/203306.917:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0913/203306.917:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
|
msedge.exe | [0913/203306.917:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff85f0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0913/203306.917:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\SYSTEM32\ntdll.dll
|
msedge.exe | [0913/203306.917:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff6f10000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0913/203306.917:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNEL32.DLL
|
msedge.exe | [0913/203306.917:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff5da0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0913/203306.917:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNELBASE.dll
|
msedge.exe | [0913/203306.917:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7fffd3770000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|