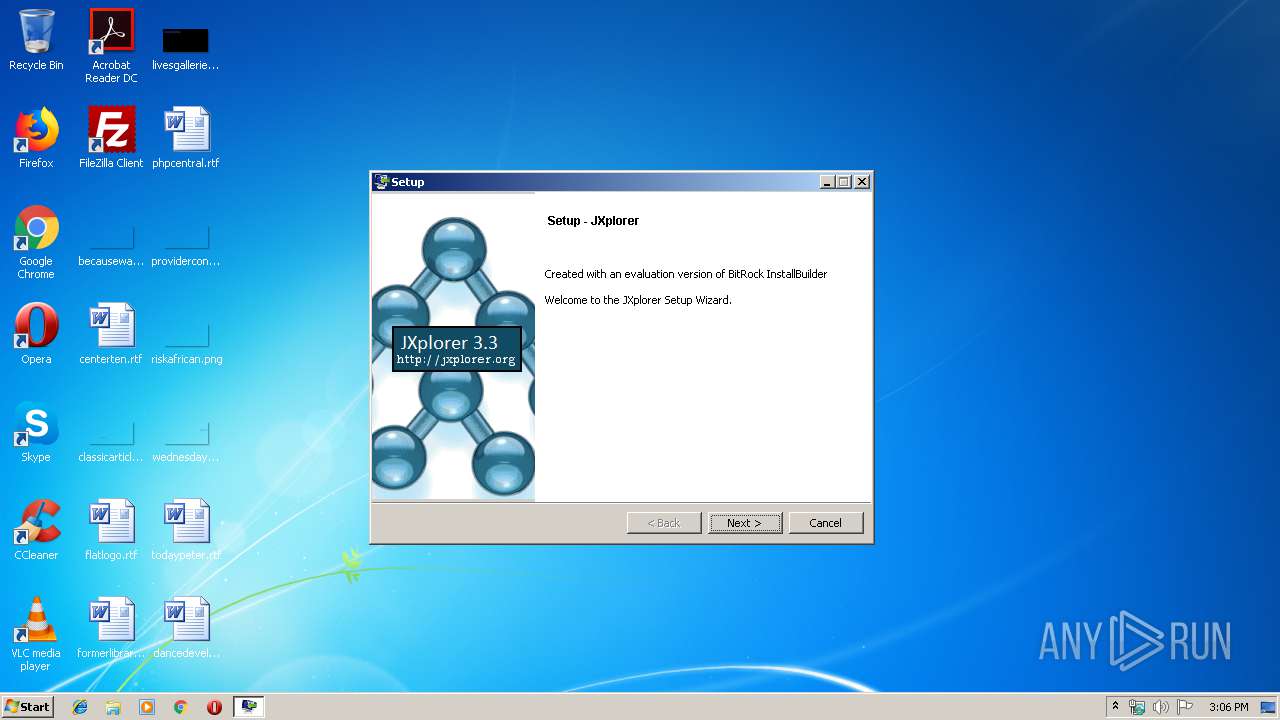
| download: | jxplorer-3.3.1.2-windows-installer.exe |
| Full analysis: | https://app.any.run/tasks/8901600f-bb50-49f2-9202-ad73cab19f15 |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2019, 14:05:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | C23A27B06281CFA93641FDBB611C33FF |
| SHA1: | CAC02AB7F94320FF7168AC30CA4DA44DF649DFA9 |
| SHA256: | C1FE14A60BC6AA909EA8C1D5F09EB7426722BDD90634B451C12D1A32D10FF67B |
| SSDEEP: | 196608:p5DOE1MFFH51Cetx3WxgzPp52ce3pYt3XqZ9sYg:p5v1MFFH51CWx3WOzPp5n1Xc4 |
MALICIOUS
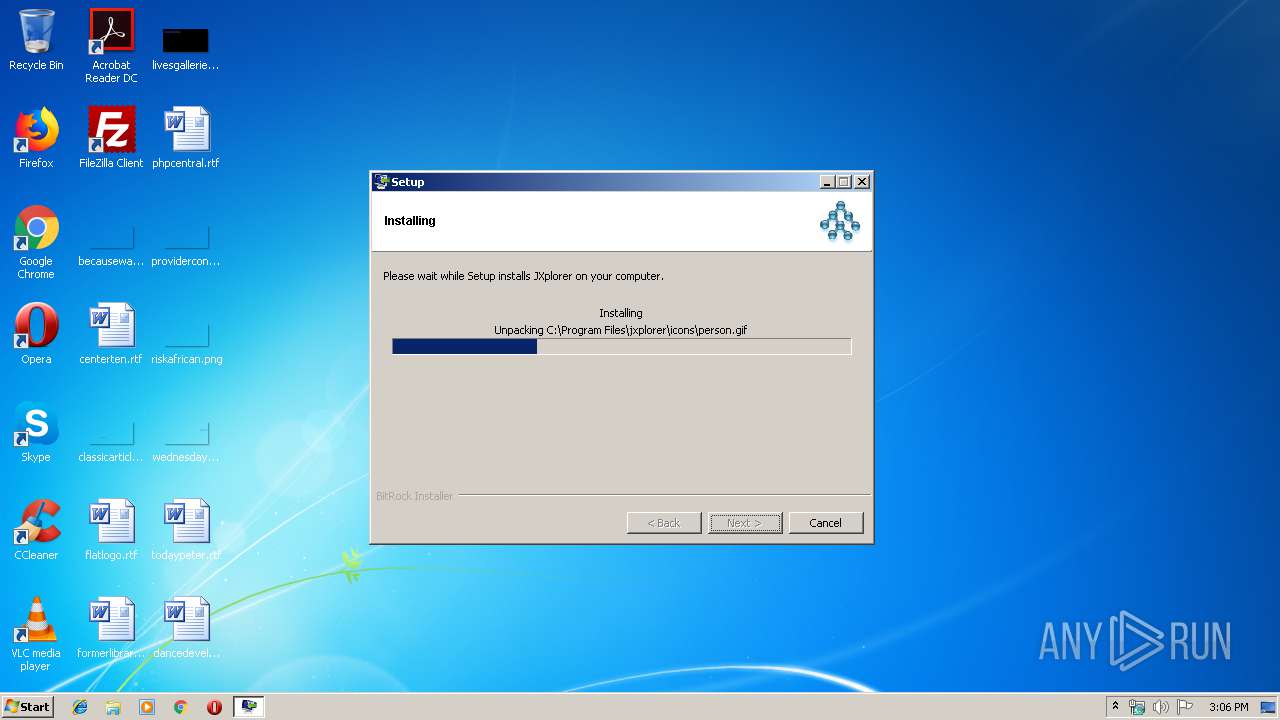
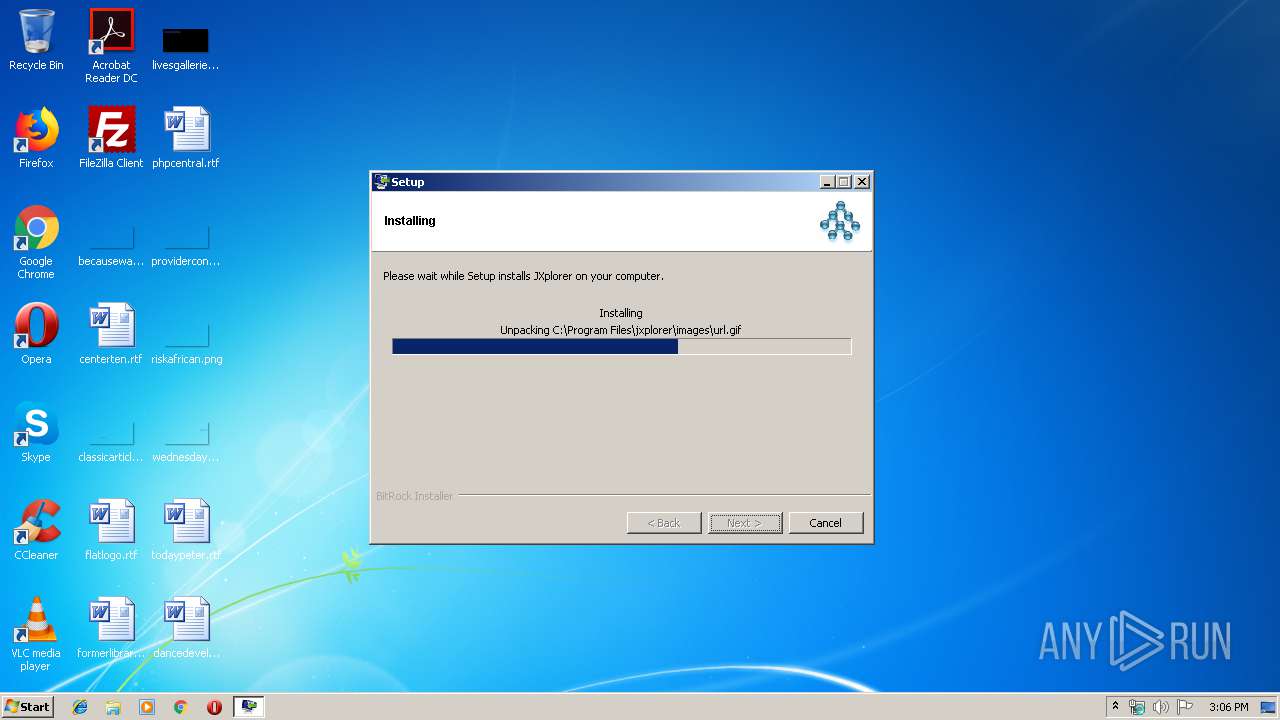
Loads dropped or rewritten executable
- jxplorer-3.3.1.2-windows-installer.exe (PID: 3904)
SUSPICIOUS
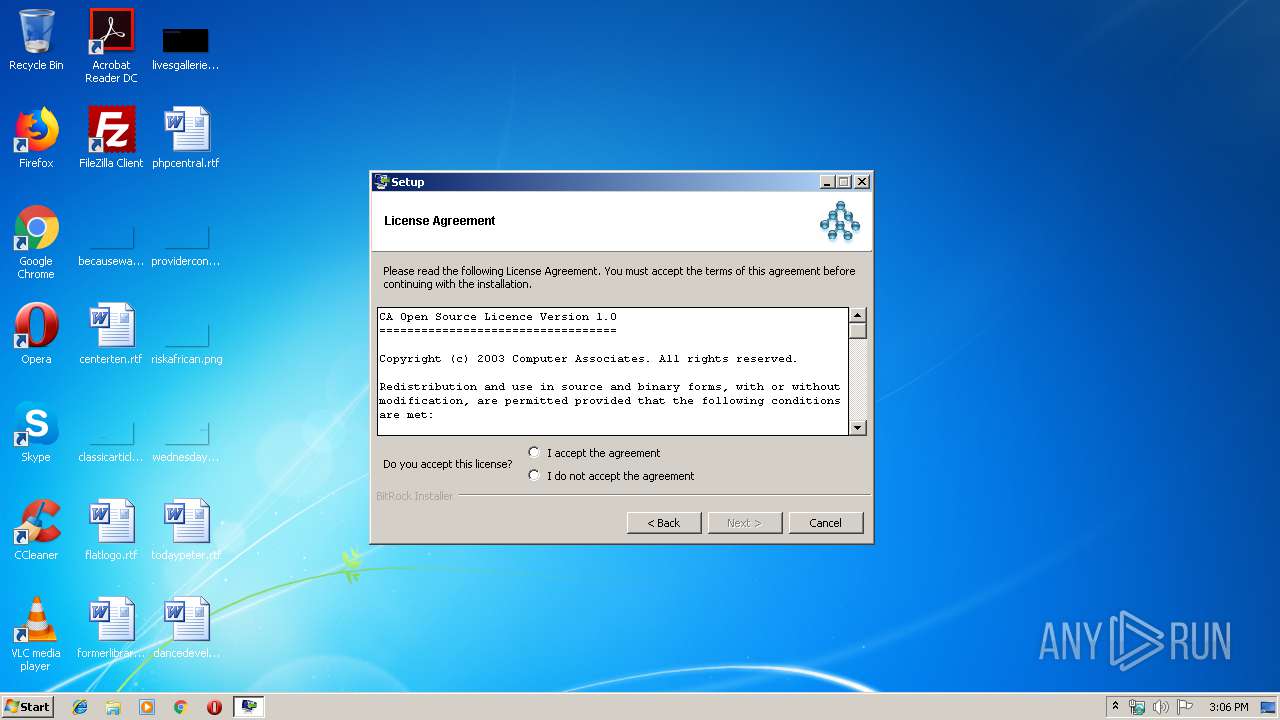
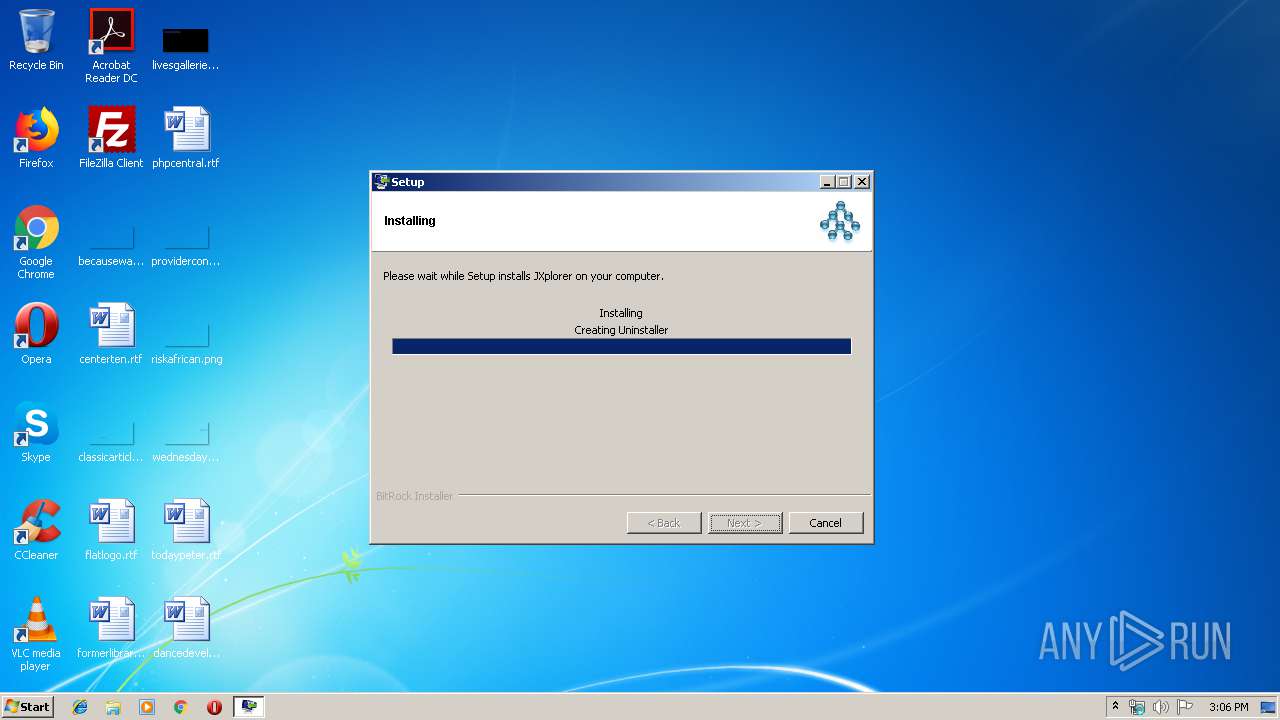
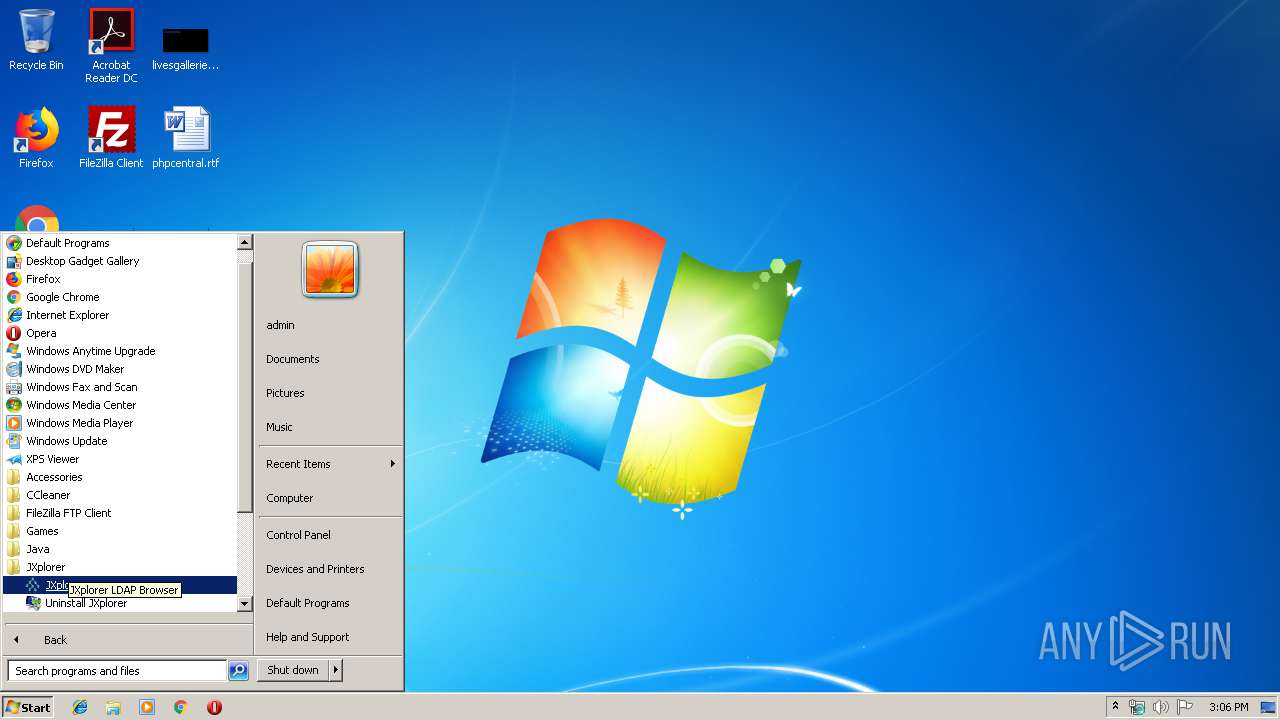
Creates a software uninstall entry
- jxplorer-3.3.1.2-windows-installer.exe (PID: 3904)
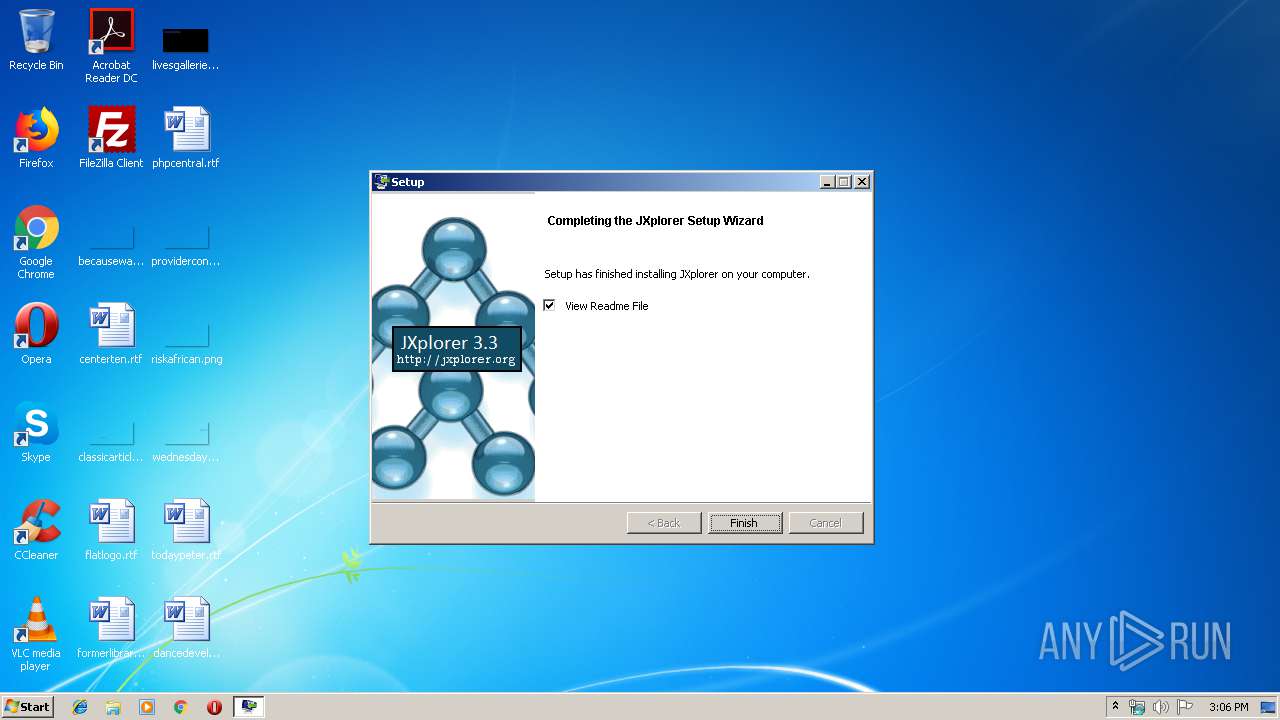
Executes JAVA applets
- jxplorer-3.3.1.2-windows-installer.exe (PID: 3904)
Executable content was dropped or overwritten
- jxplorer-3.3.1.2-windows-installer.exe (PID: 3904)
Creates files in the user directory
- javaw.exe (PID: 2900)
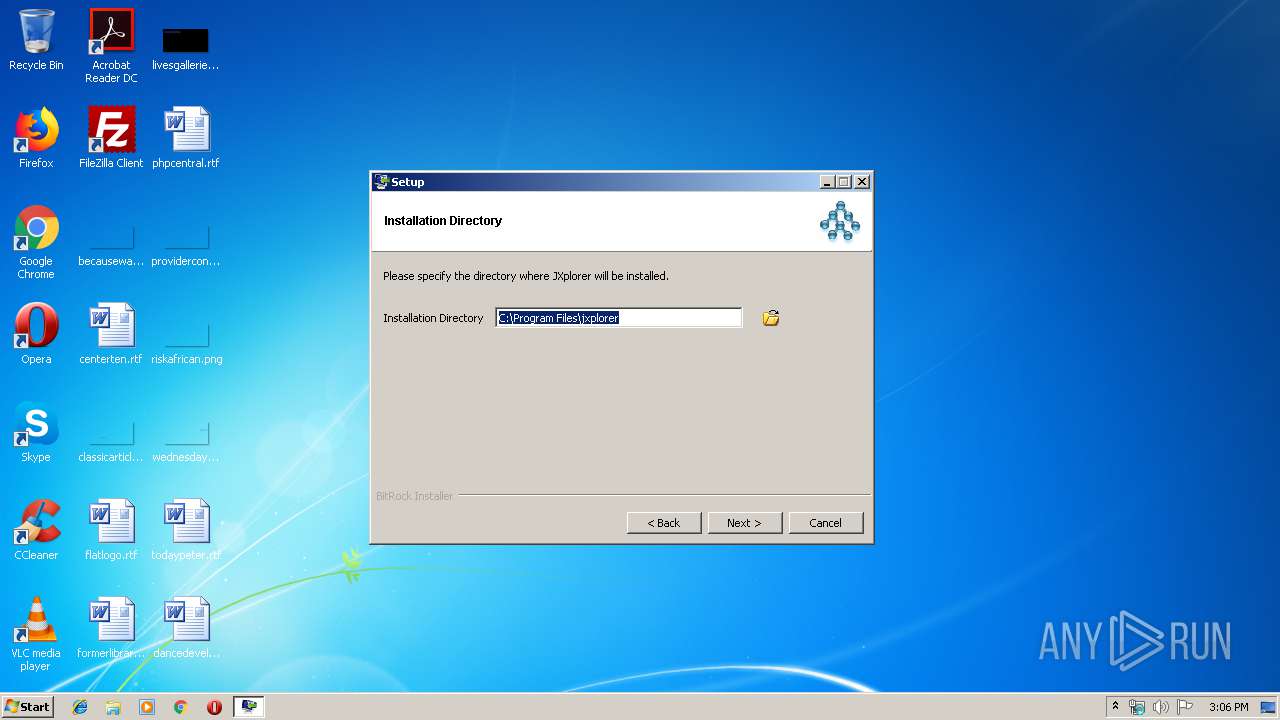
Creates files in the program directory
- jxplorer-3.3.1.2-windows-installer.exe (PID: 3904)
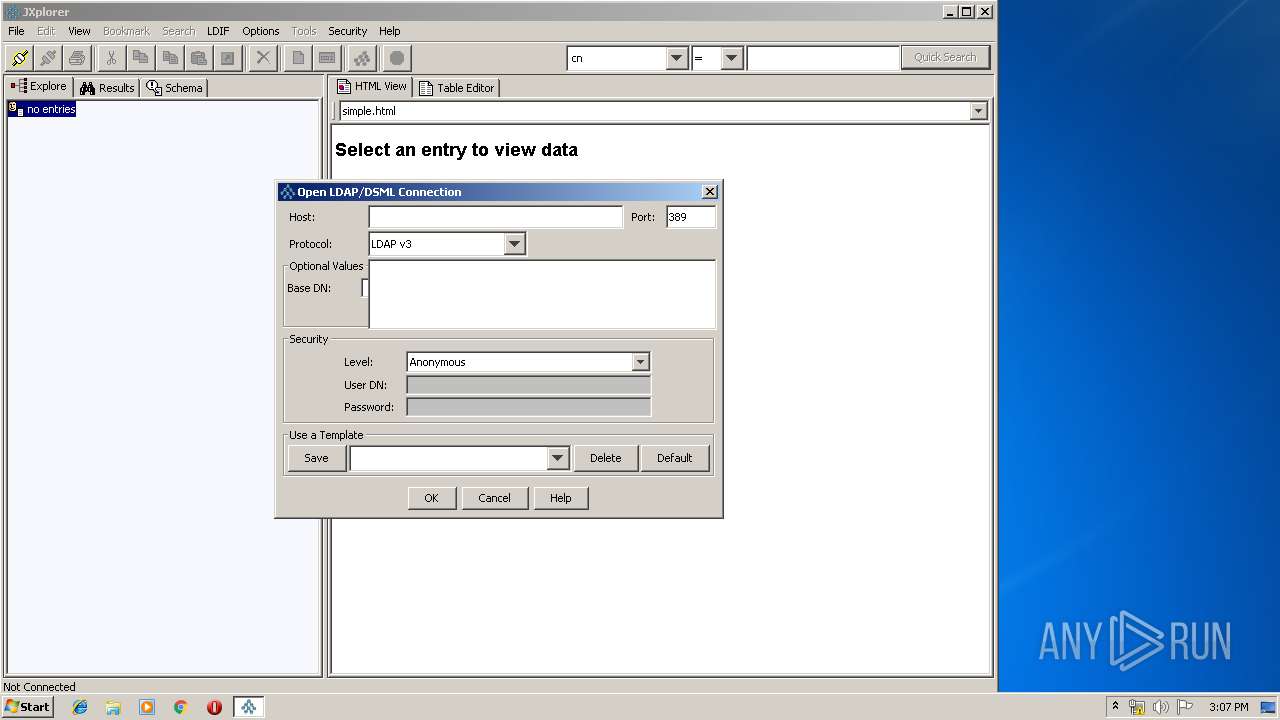
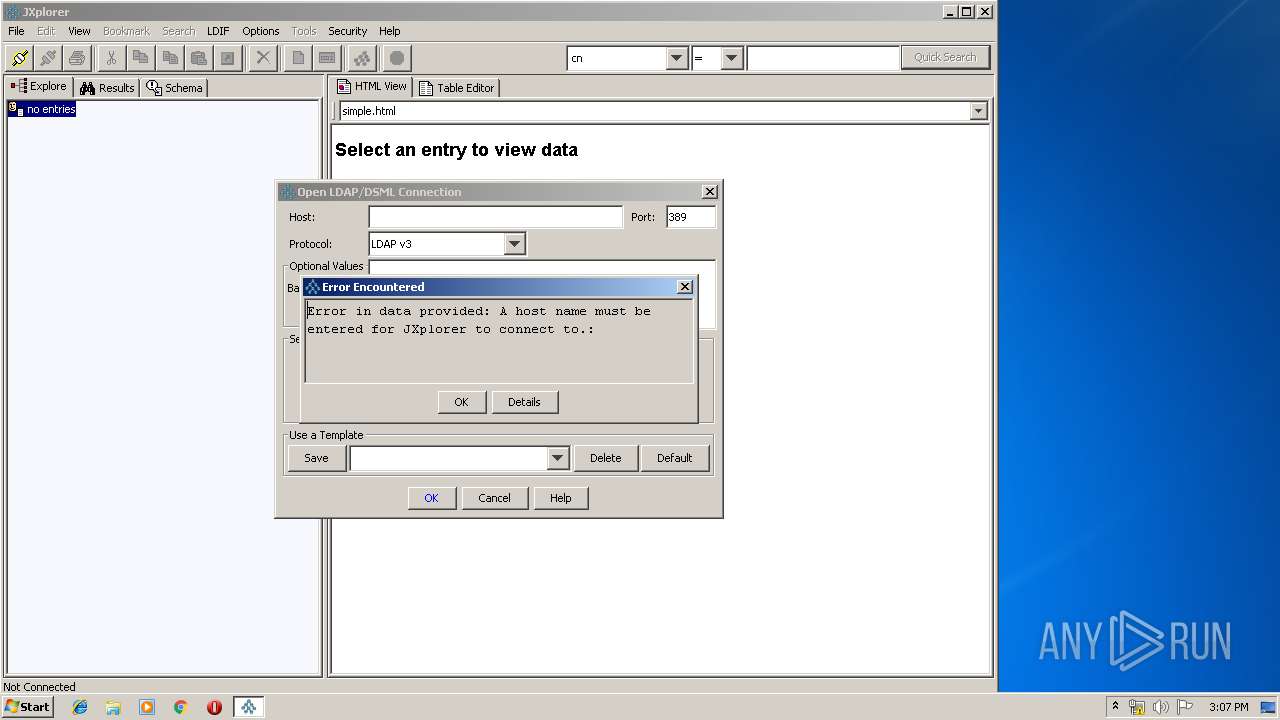
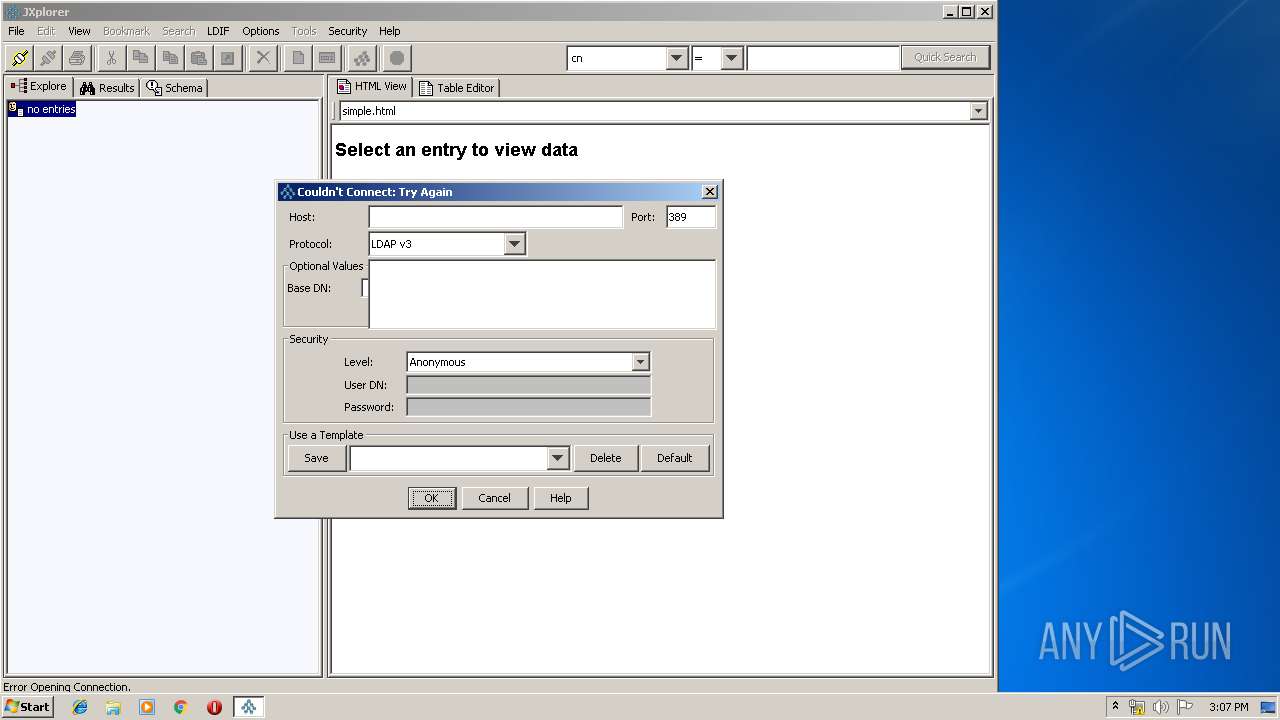
INFO
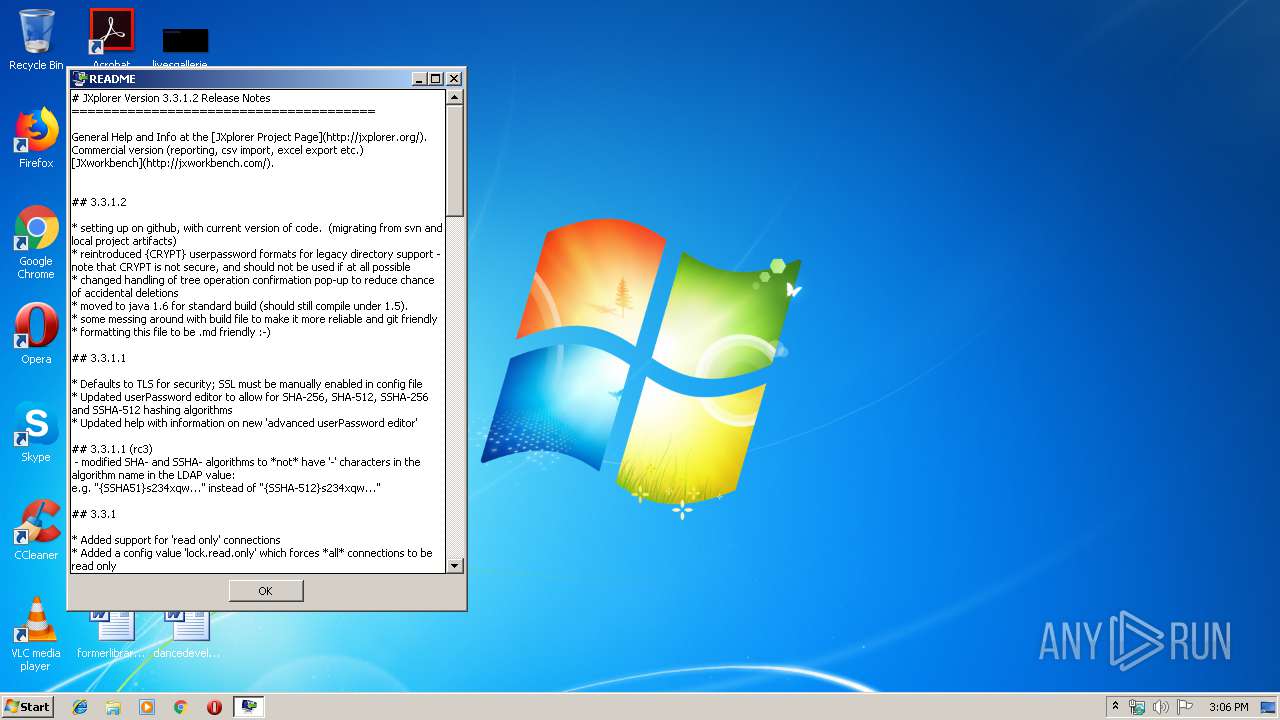
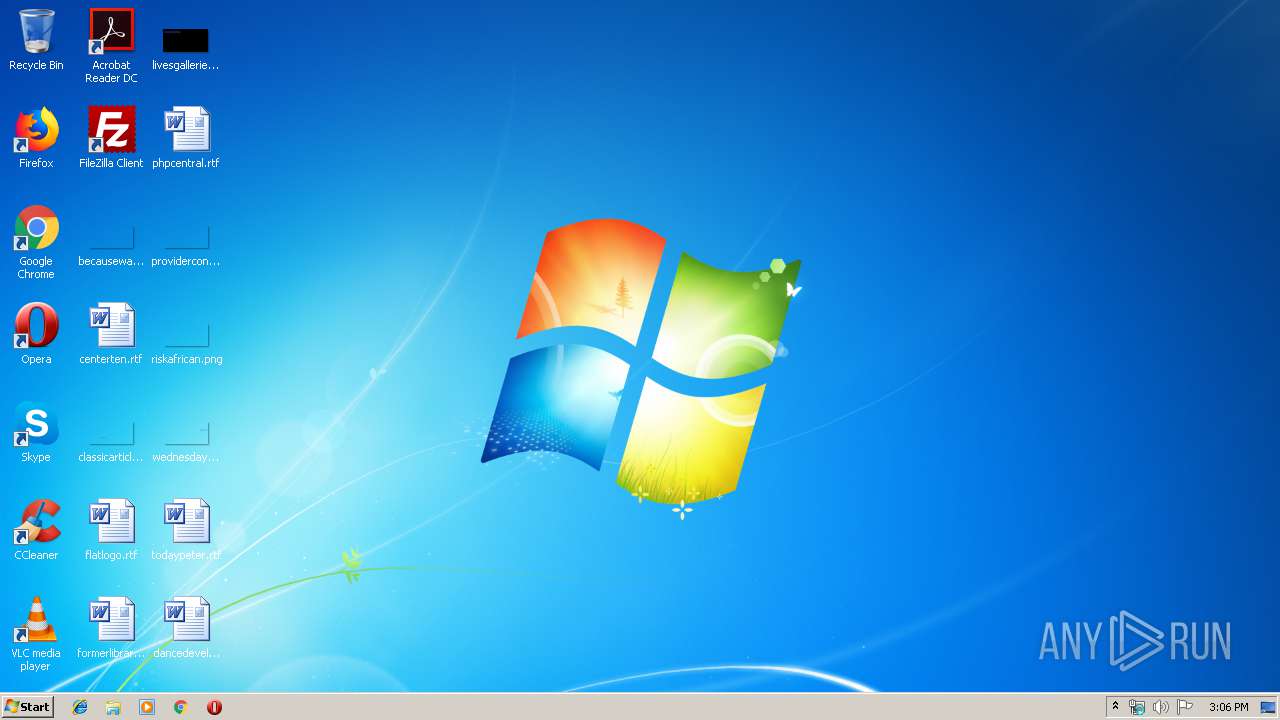
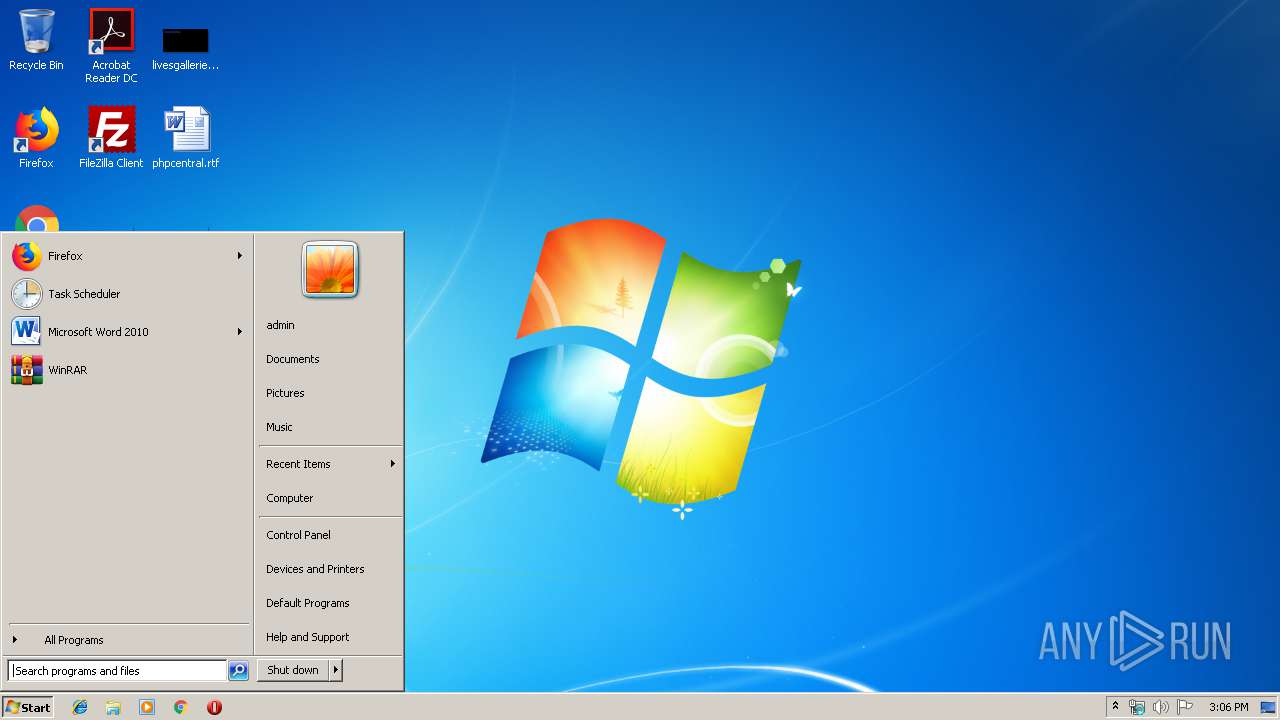
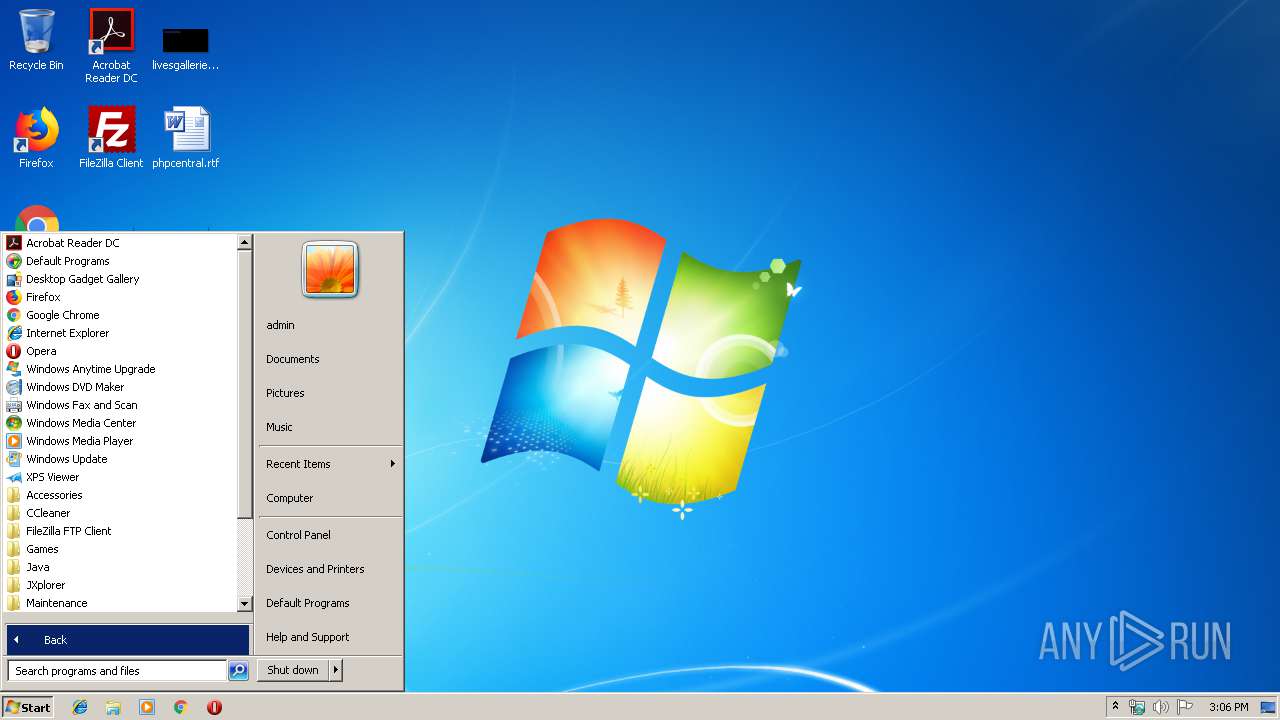
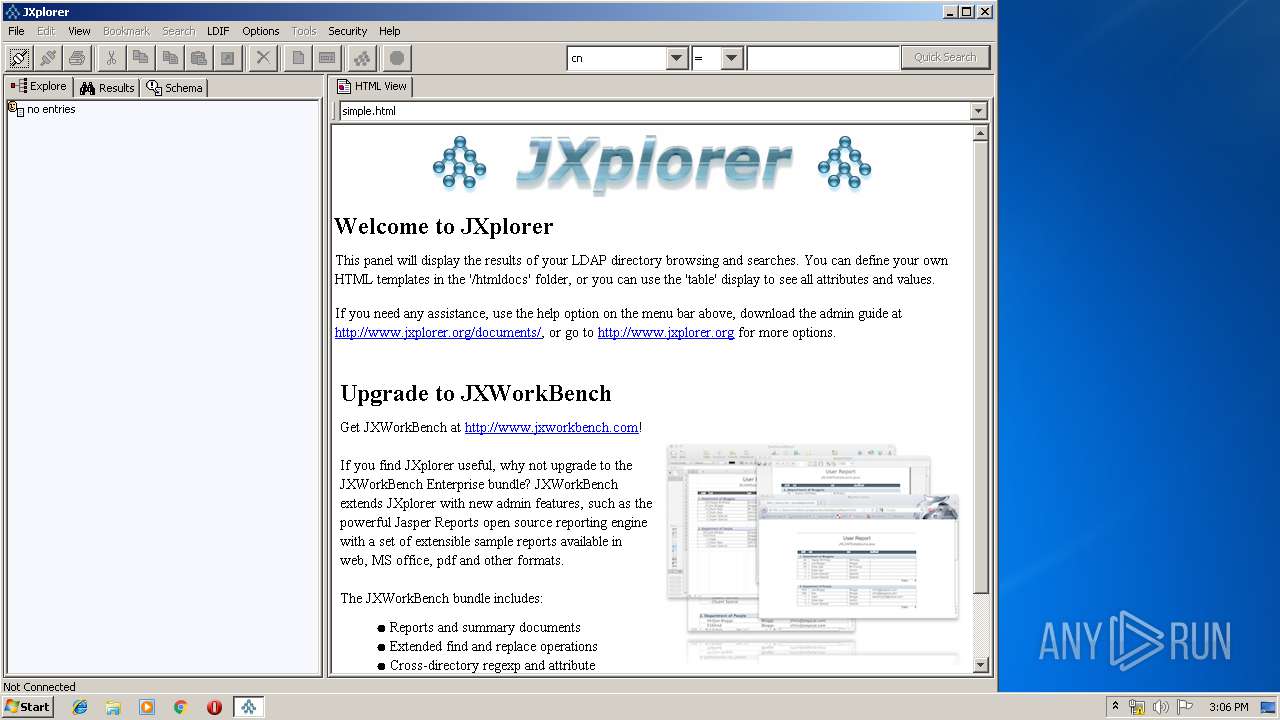
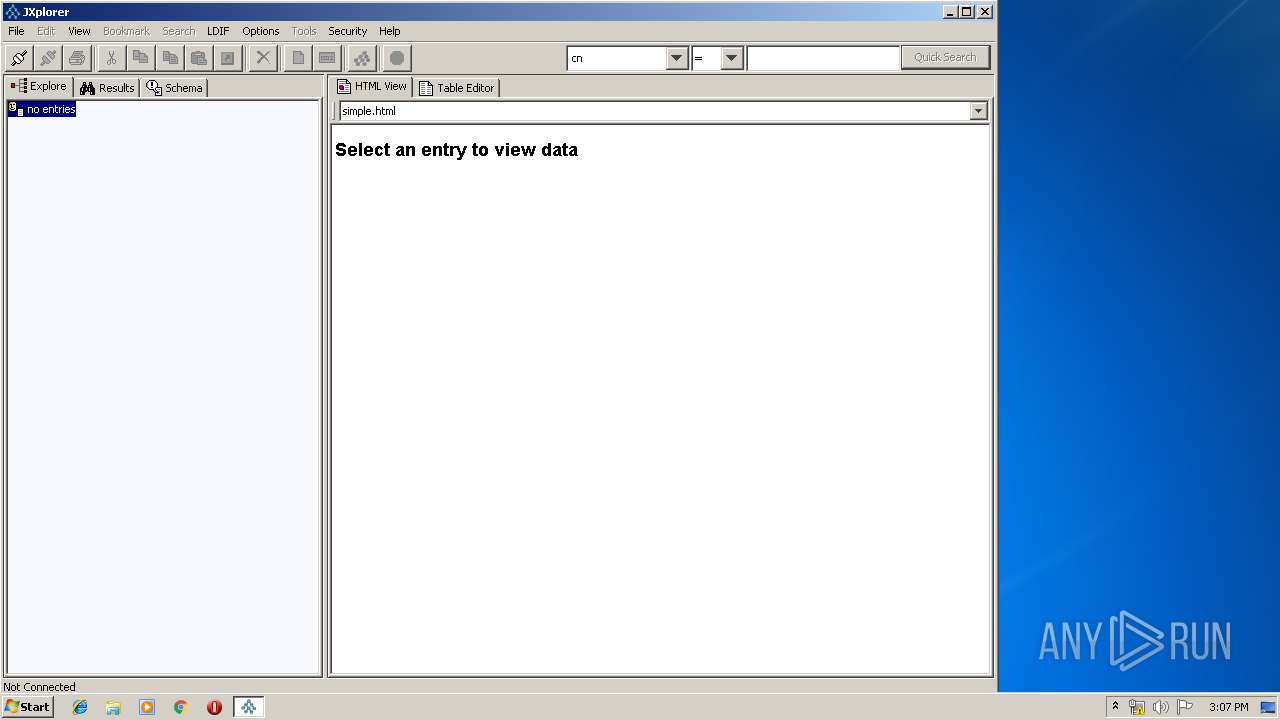
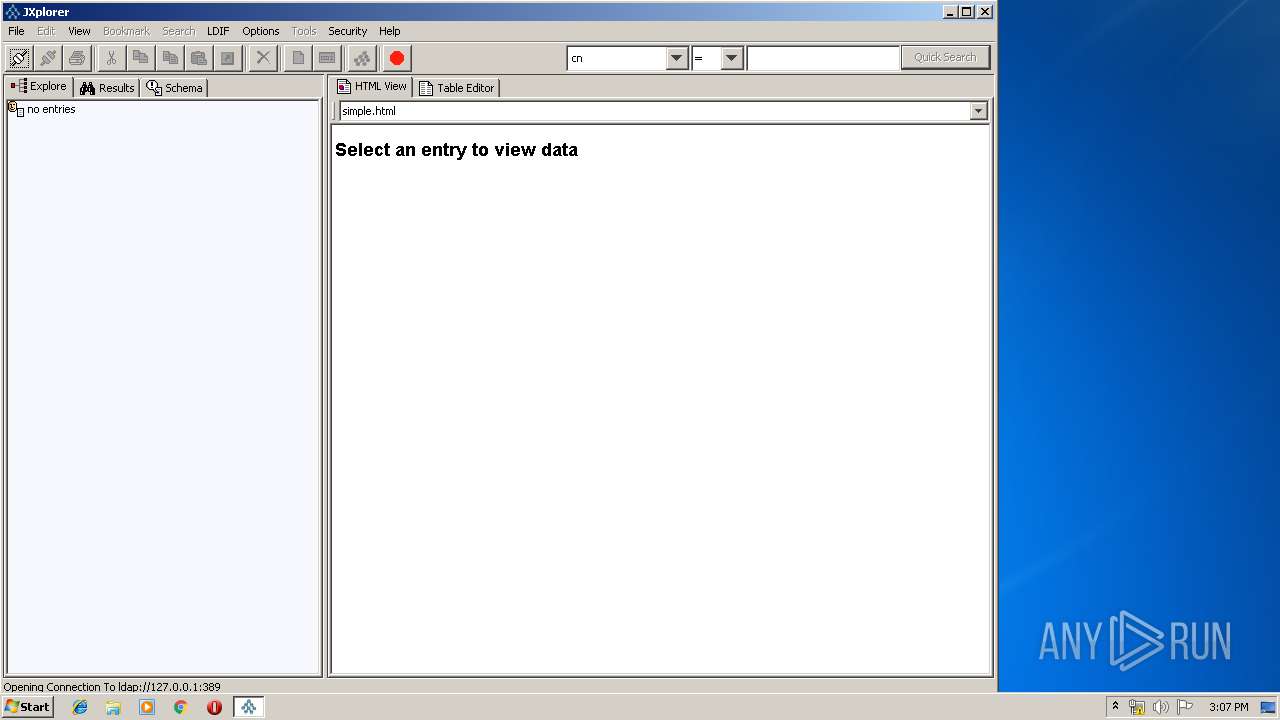
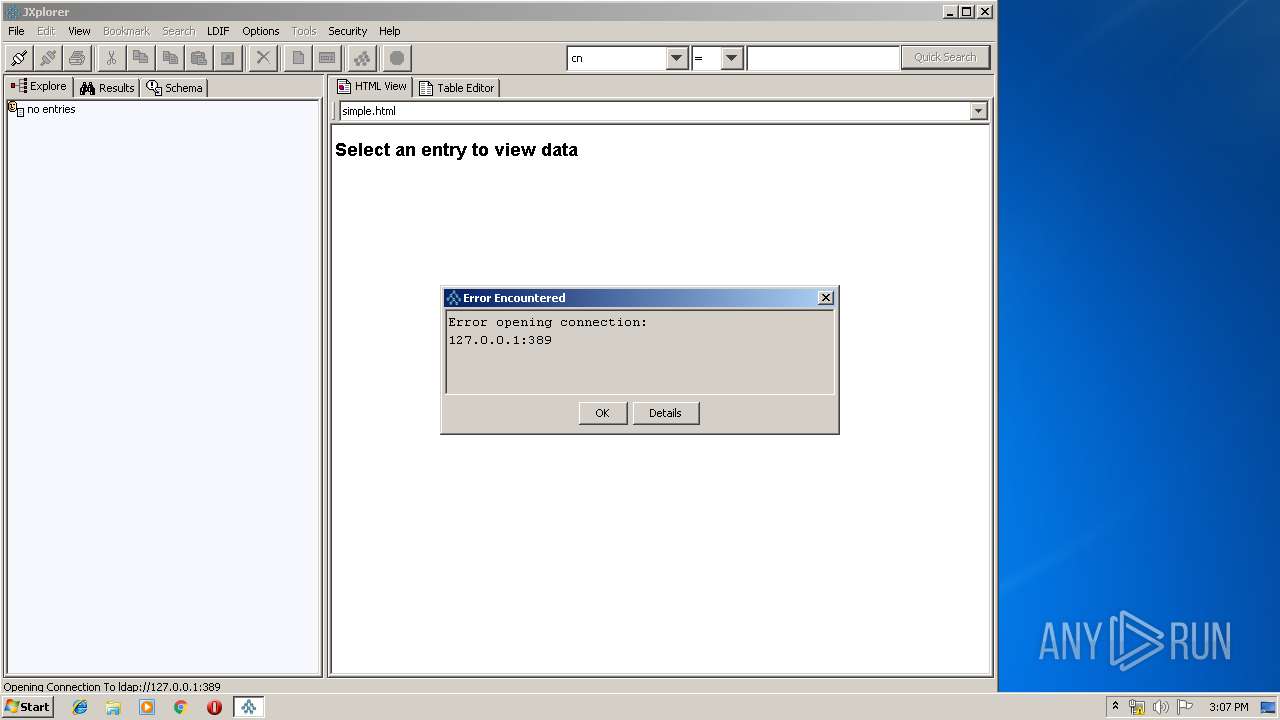
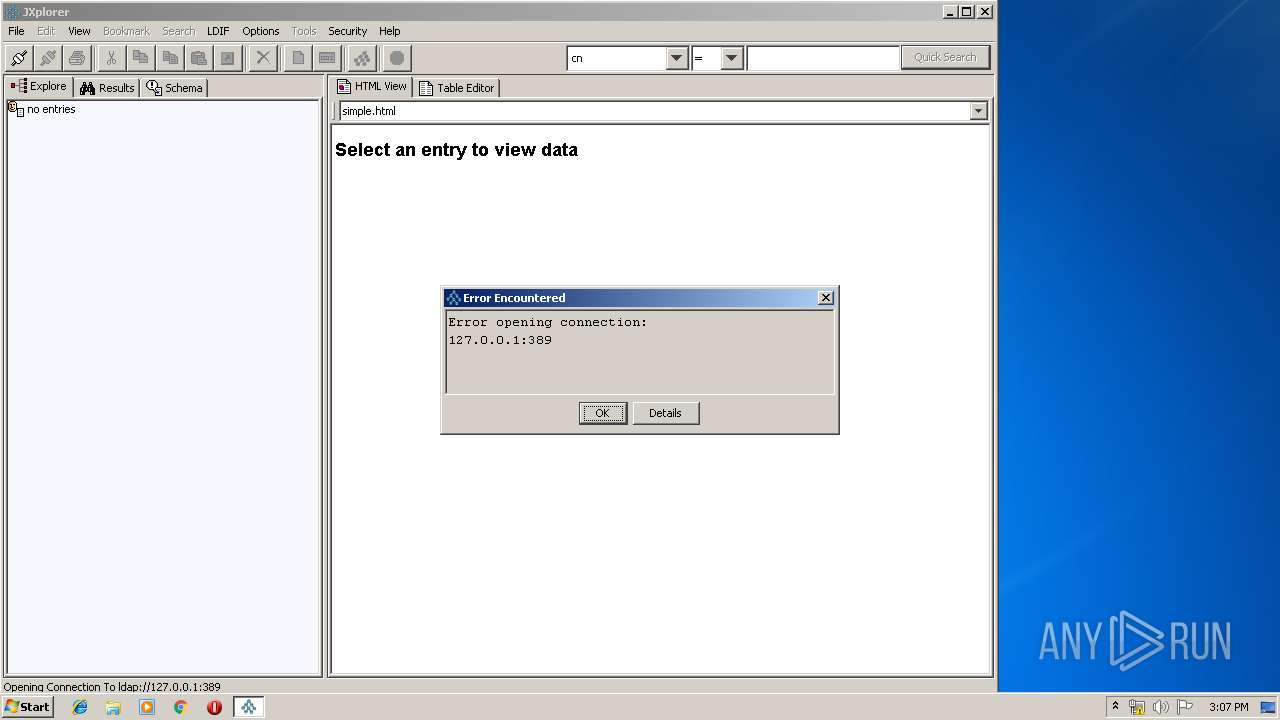
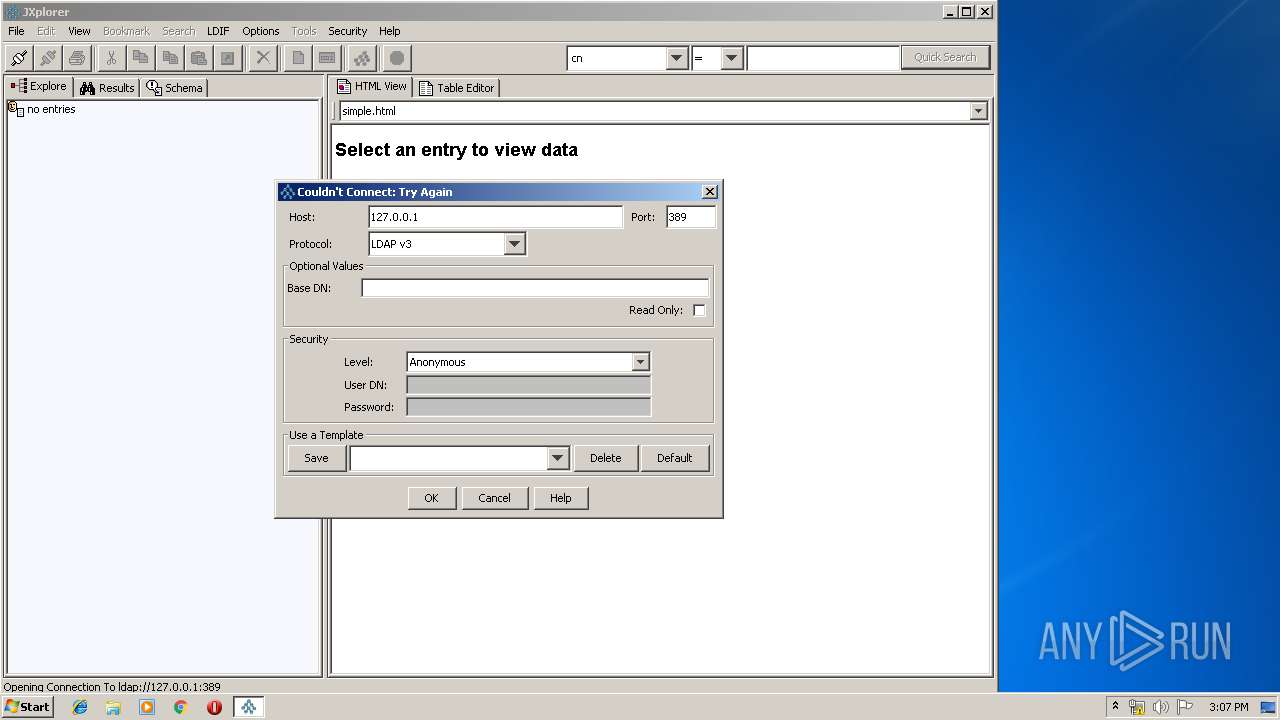
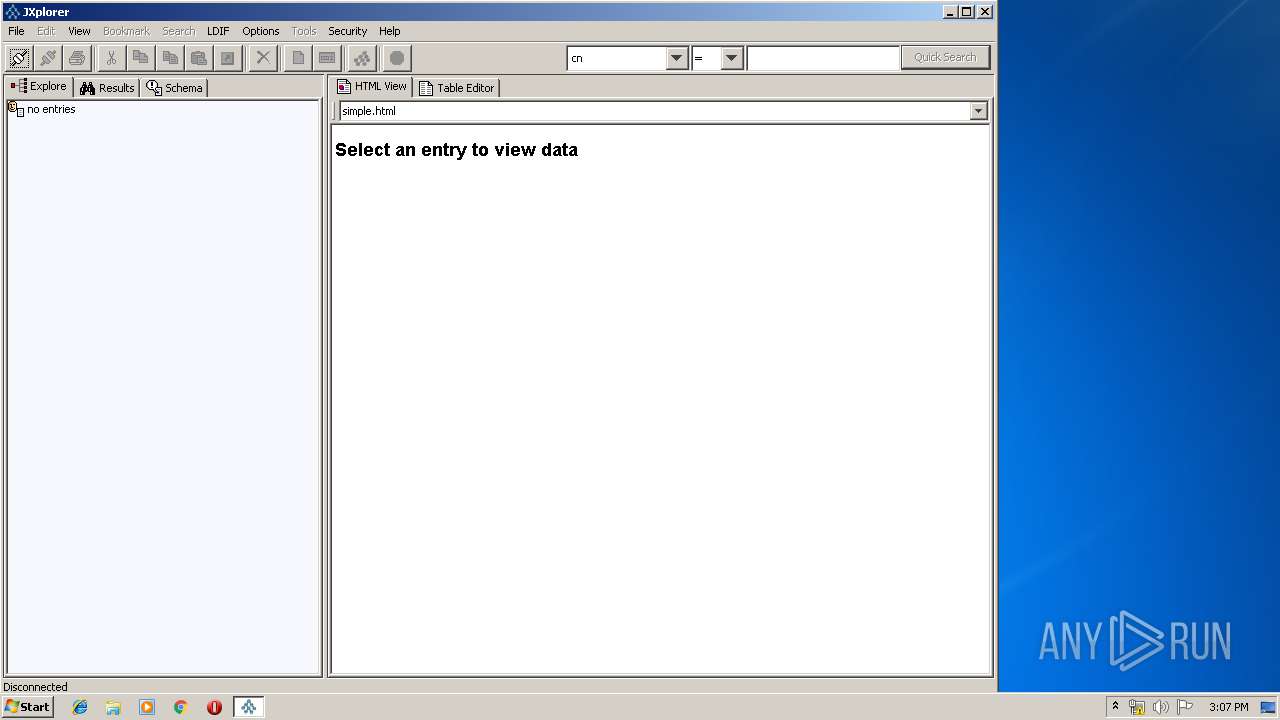
Manual execution by user
- javaw.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:09:07 11:39:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.2 |
| CodeSize: | 864256 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | 1785856 |
| EntryPoint: | 0x287150 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.1.2 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | JXplorer |
| LegalTrademarks: | - |
| FileDescription: | - |
| InternalName: | - |
| CompanyName: | JXplorer Open Source Project |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Copyright JXplorer Open Source Project |
| OriginalFileName: | setup.exe |
| Comments: | - |
| ProductVersion: | 3.3.1.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Sep-2012 09:39:15 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| ProductName: | JXplorer |
| LegalTrademarks: | - |
| FileDescription: | - |
| InternalName: | - |
| CompanyName: | JXplorer Open Source Project |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Copyright JXplorer Open Source Project |
| OriginalFilename: | setup.exe |
| Comments: | - |
| ProductVersion: | 3.3.1.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Sep-2012 09:39:15 |
| Pointer to Symbol Table: | 0x00270400 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001B4000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001B5000 | 0x000D3000 | 0x000D2E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9997 |
.rsrc | 0x00288000 | 0x00013000 | 0x00012800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.16139 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07731 | 1457 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.29217 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 4.33115 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.30424 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.5642 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 2.29164 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.17695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.18099 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.15567 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 1.88729 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.dll |
IMM32.DLL |
KERNEL32.DLL |
OLE32.dll |
OLEAUT32.DLL |
SHELL32.DLL |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TclKit_AppInit | 1 | 0x00002344 |
TclKit_SetKitPath | 2 | 0x00002720 |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1884 | C:\ProgramData\Oracle\Java\javapath\java.exe -d64 -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | jxplorer-3.3.1.2-windows-installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | jxplorer-3.3.1.2-windows-installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2232 | C:\ProgramData\Oracle\Java\javapath\java.exe -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | jxplorer-3.3.1.2-windows-installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -d64 -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | jxplorer-3.3.1.2-windows-installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -classpath .;jars/jxplorer.jar;jars/help.jar;jars/jhall.jar;jars/jxworkbench.jar;jars/junit.jar; -Dfile.encoding=utf-8 com.ca.directory.jxplorer.JXplorer | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3584 | "C:\Users\admin\AppData\Local\Temp\jxplorer-3.3.1.2-windows-installer.exe" | C:\Users\admin\AppData\Local\Temp\jxplorer-3.3.1.2-windows-installer.exe | — | explorer.exe | |||||||||||
User: admin Company: JXplorer Open Source Project Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3904 | "C:\Users\admin\AppData\Local\Temp\jxplorer-3.3.1.2-windows-installer.exe" | C:\Users\admin\AppData\Local\Temp\jxplorer-3.3.1.2-windows-installer.exe | explorer.exe | ||||||||||||
User: admin Company: JXplorer Open Source Project Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
231
Read events
212
Write events
18
Delete events
1
Modification events
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | BitRock |
Value: 1 | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | delete value | Name: | BitRock |
Value: 1 | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | DisplayVersion |
Value: 3.3.1.2 | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | Publisher |
Value: JXplorer Open Source Project | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | DisplayName |
Value: JXplorer | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | UrlInfoAbout |
Value: | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | HelpLink |
Value: | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | Comments |
Value: | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | Contact |
Value: | |||
| (PID) Process: | (3904) jxplorer-3.3.1.2-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JXplorer 3.3.1.2 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\jxplorer\uninstall.exe | |||
Executable files
20
Suspicious files
5
Text files
189
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR2BD0.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR2C8C.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR2CCC.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR2D3A.tmp | — | |
MD5:— | SHA256:— | |||
| 2228 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:7CC8DEB834B63678937D384FC6C83AB8 | SHA256:B3223A67E8B367BC8D6B49BCC31F19923797926FD9606B81B8EC1901DB7C3E02 | |||
| 2232 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:7CC8DEB834B63678937D384FC6C83AB8 | SHA256:B3223A67E8B367BC8D6B49BCC31F19923797926FD9606B81B8EC1901DB7C3E02 | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR1C94.tmp | executable | |
MD5:D33EE6D856350F321189138134745388 | SHA256:9EB5405449BE0D43FEE145B5B6D5FE01799C6F635389A44F58A0AF2793A1B737 | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Program Files\jxplorer\example.ldif | text | |
MD5:F8D49361D0B51FC017666355DFD2E0DE | SHA256:948A2515DD0DF718EC39009C71DBC96C8CAAAF28D48B97883F4A0FA2EC945268 | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\BR21AD.tmp | executable | |
MD5:145D5C49FE34A44662BEAFFE641D58C7 | SHA256:59182F092B59A3005ADA6B2F2855C7E860E53E8ADF6E41CD8CD515578AE7815A | |||
| 3904 | jxplorer-3.3.1.2-windows-installer.exe | C:\Program Files\jxplorer\images\JX.icns | image | |
MD5:D049F6F6CDD75AFB4C868178C6F8B4B6 | SHA256:37F3122A7CA2FFAF629F94E85DFFEAB4A77B562A8DCEB9E210111725ACBC2C0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report