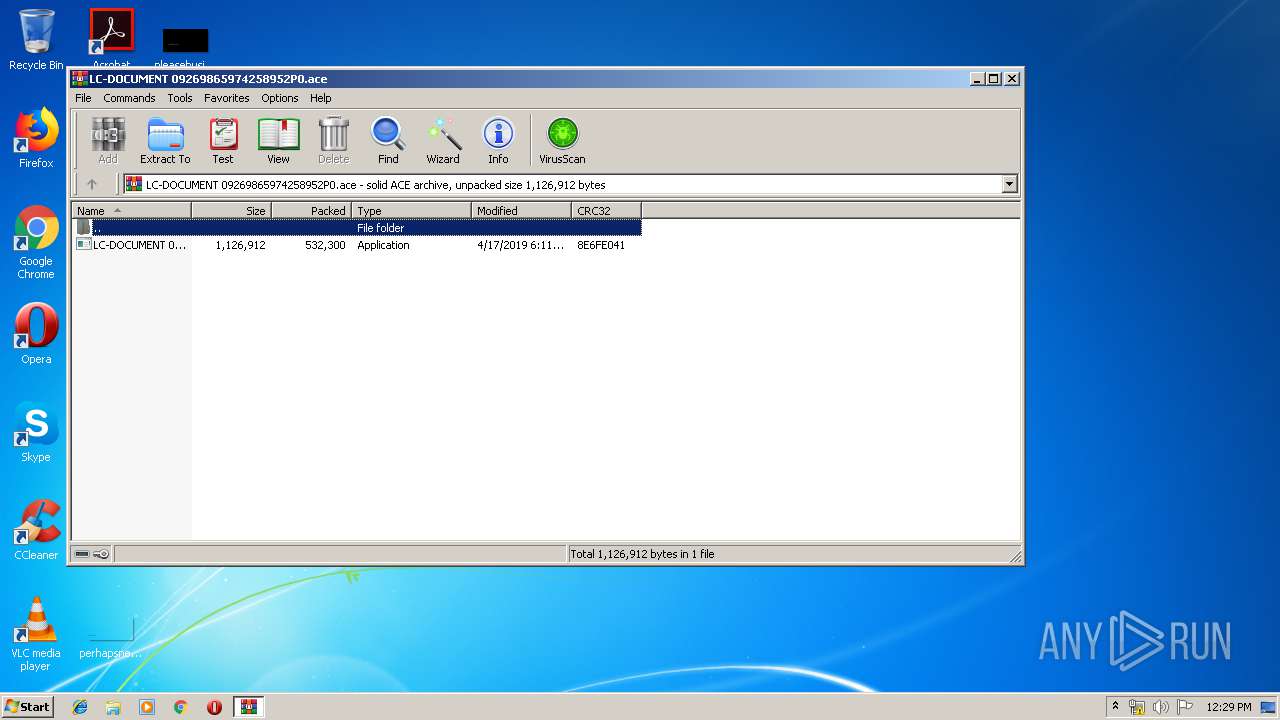
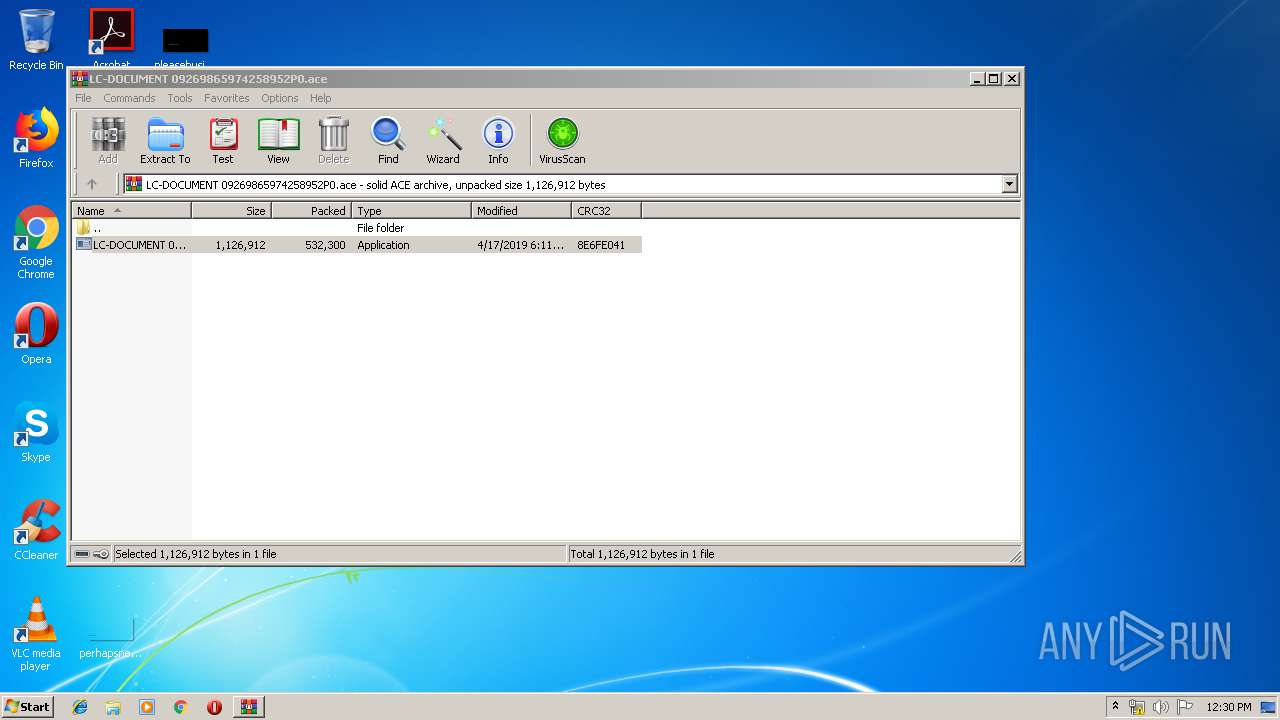
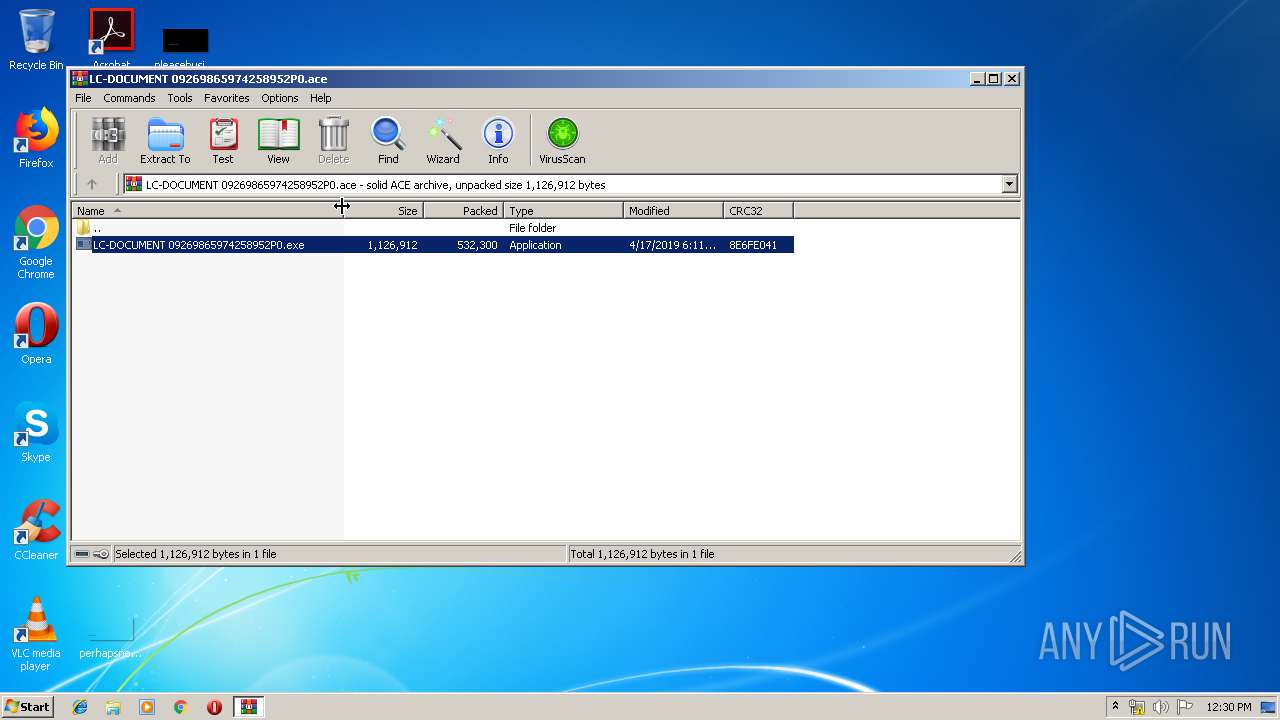
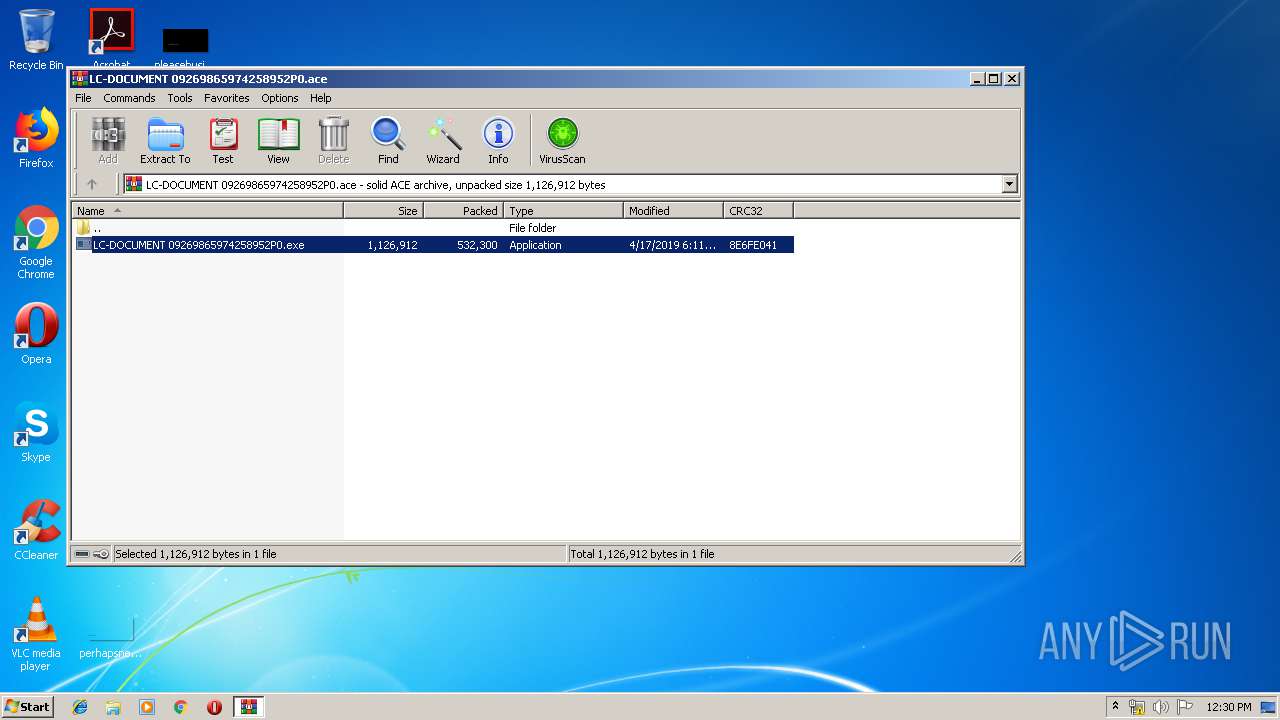
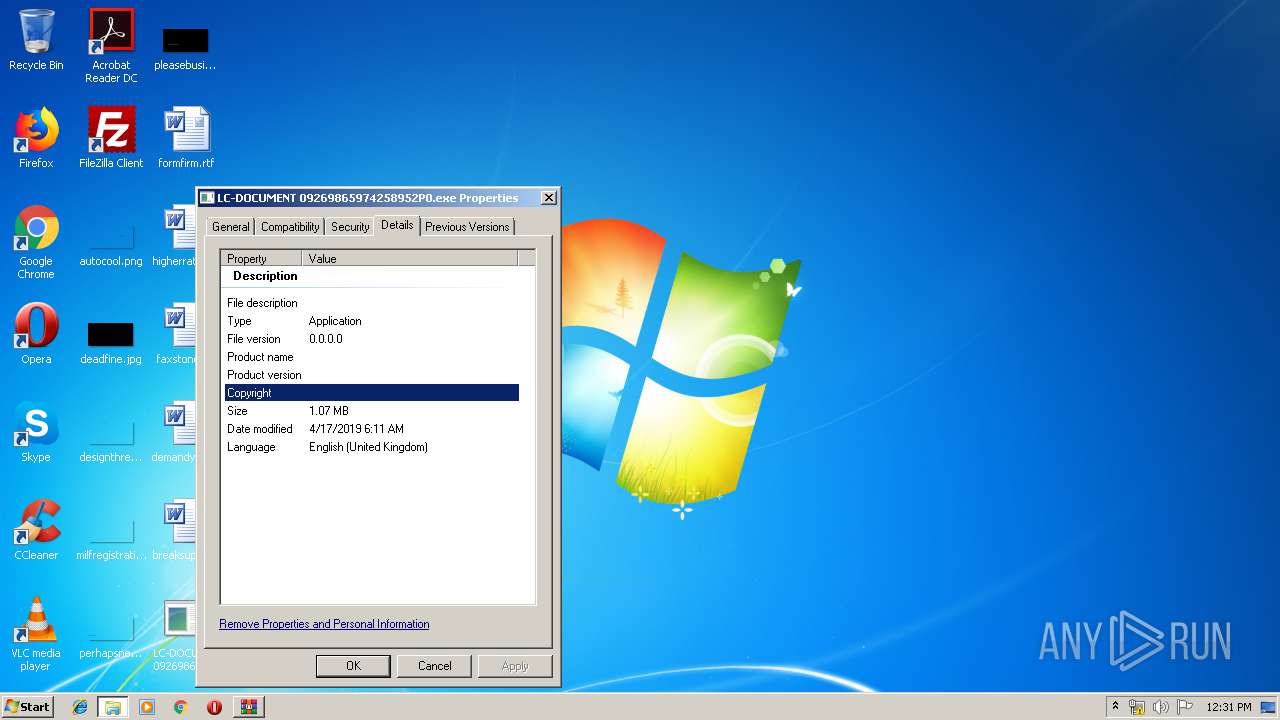
| File name: | LC-DOCUMENT 09269865974258952P0.ace |
| Full analysis: | https://app.any.run/tasks/013c963b-a849-442a-b477-2bf09281f025 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:29:21 |
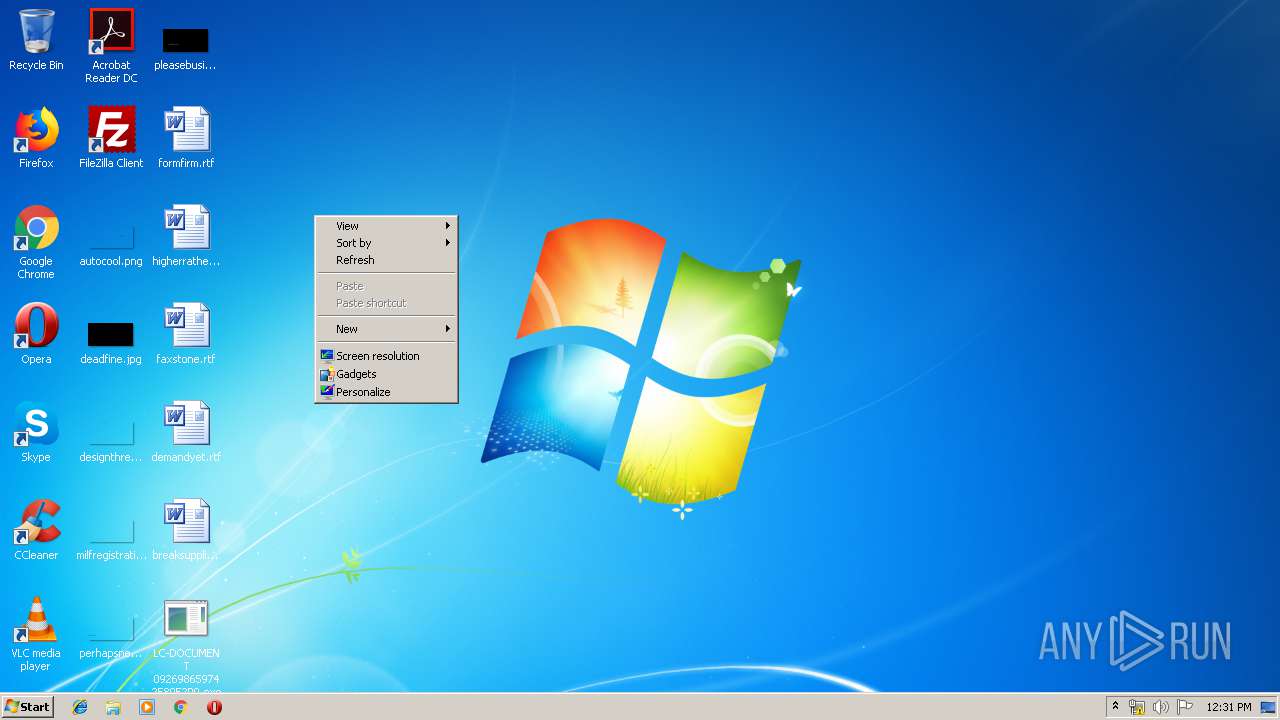
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | ACE archive data version 20, from Win/32, version 20 to extract, contains AV-String (unregistered), solid |
| MD5: | E140EA6A2DD435290BE7848185D11252 |
| SHA1: | CEC3BE312CB670E08BD8CB8D7BD16E8617AB9F96 |
| SHA256: | C1EE7A6393CB075073328719298BE1A6472C7A7B0736ED3D74E5C42271E23A30 |
| SSDEEP: | 12288:IxyprdEVM/ITLzZNoI55PuYwOA/OiEp8wUwMq:IxypZEji/CpRv |
MALICIOUS
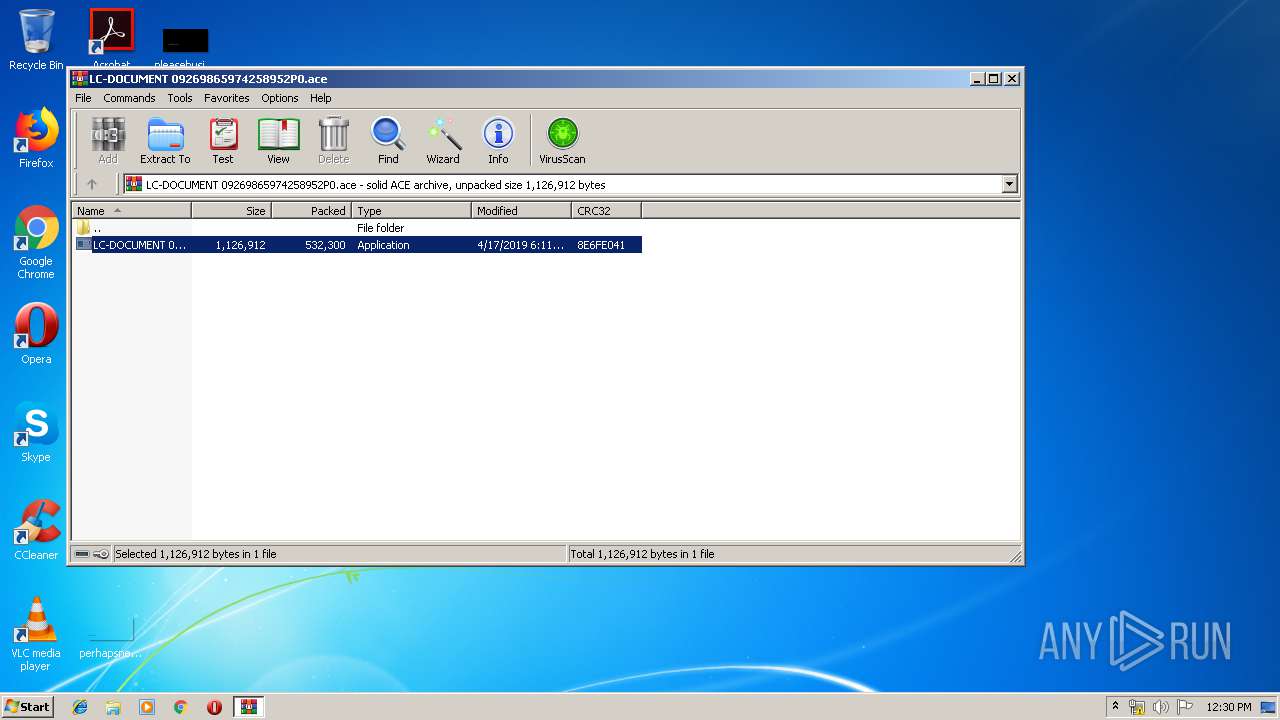
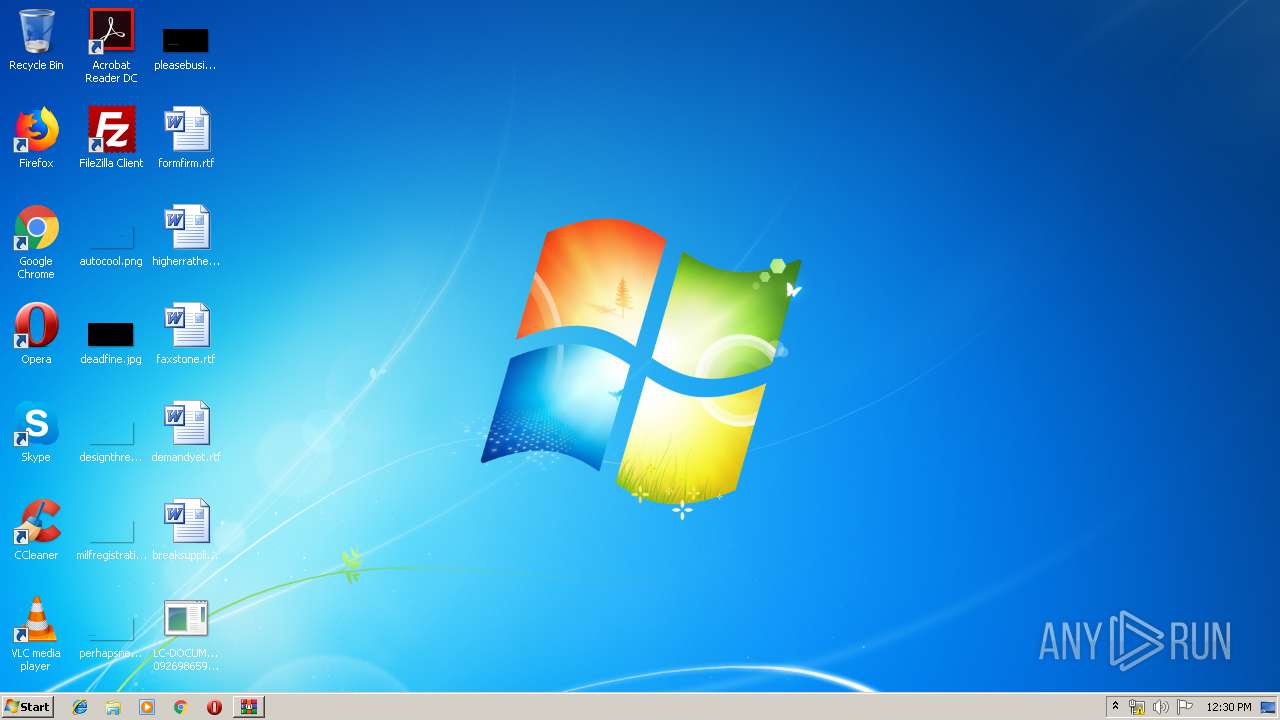
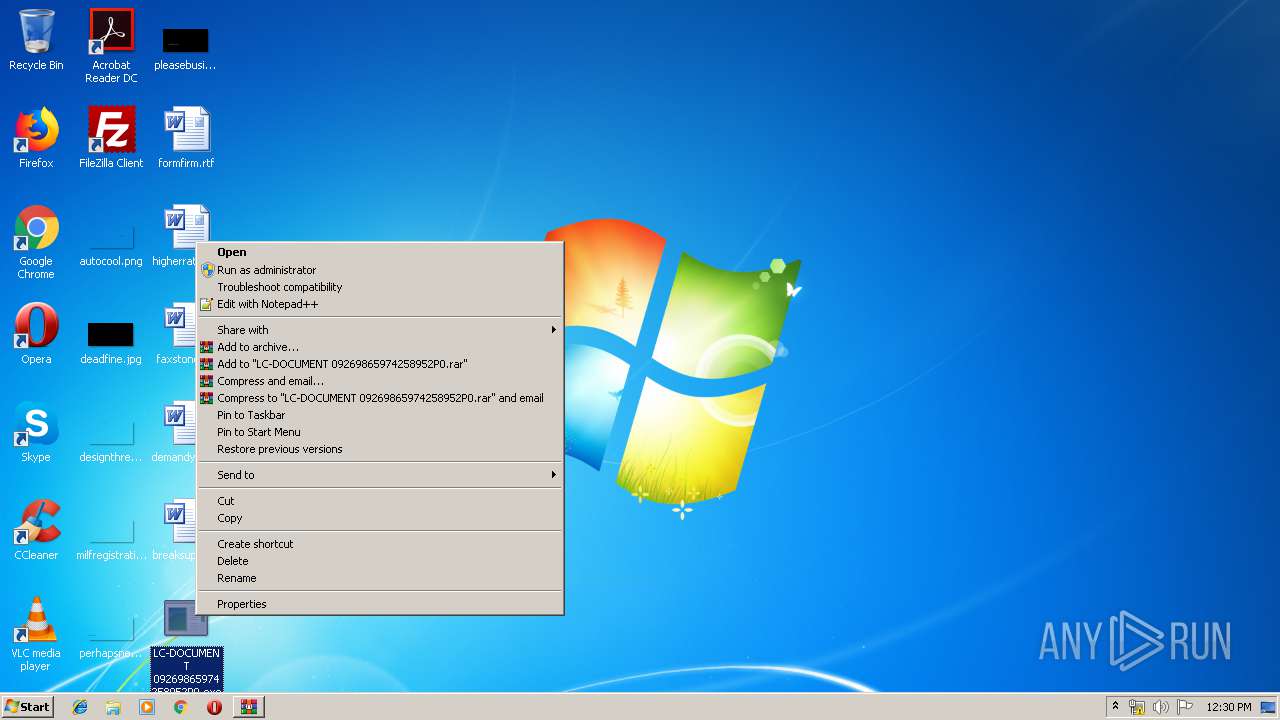
Application was dropped or rewritten from another process
- LC-DOCUMENT 09269865974258952P0.exe (PID: 1204)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 3092)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 3448)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 2152)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 3236)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 2712)
- LC-DOCUMENT 09269865974258952P0.exe (PID: 2704)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2484)
Application launched itself
- LC-DOCUMENT 09269865974258952P0.exe (PID: 1204)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ace | | | ACE compressed archive (100) |
|---|
Total processes
43
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
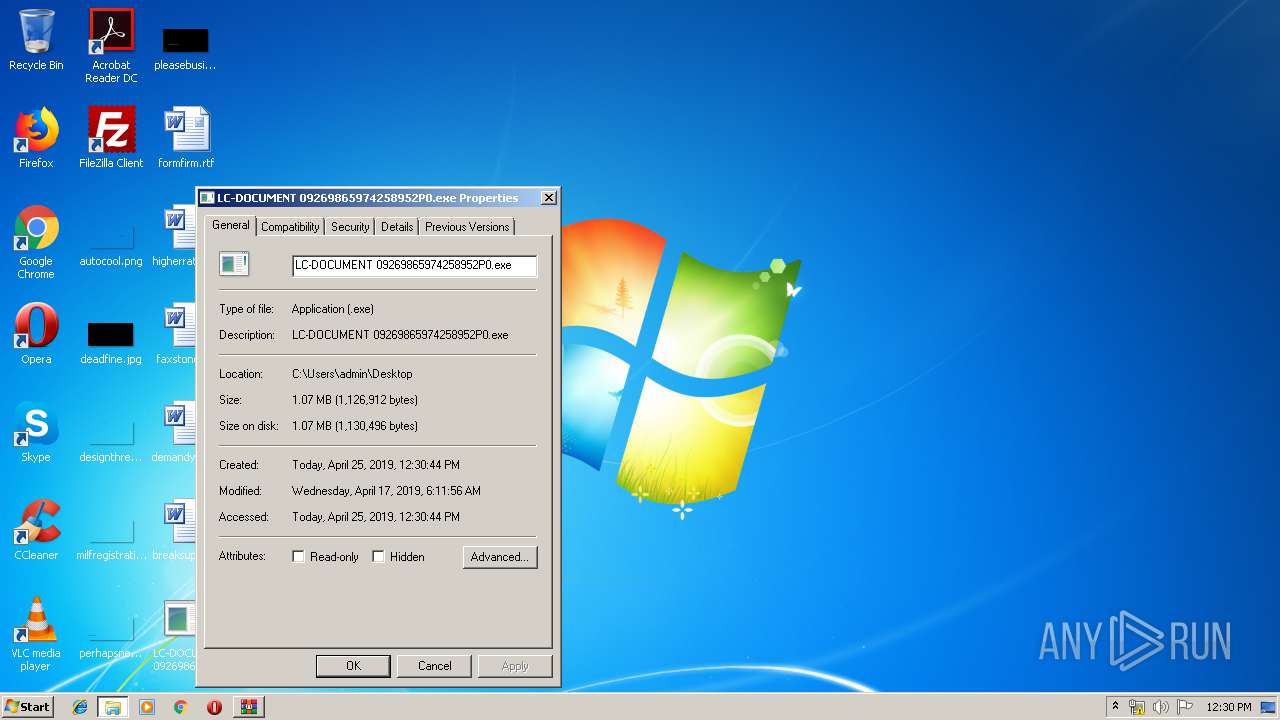
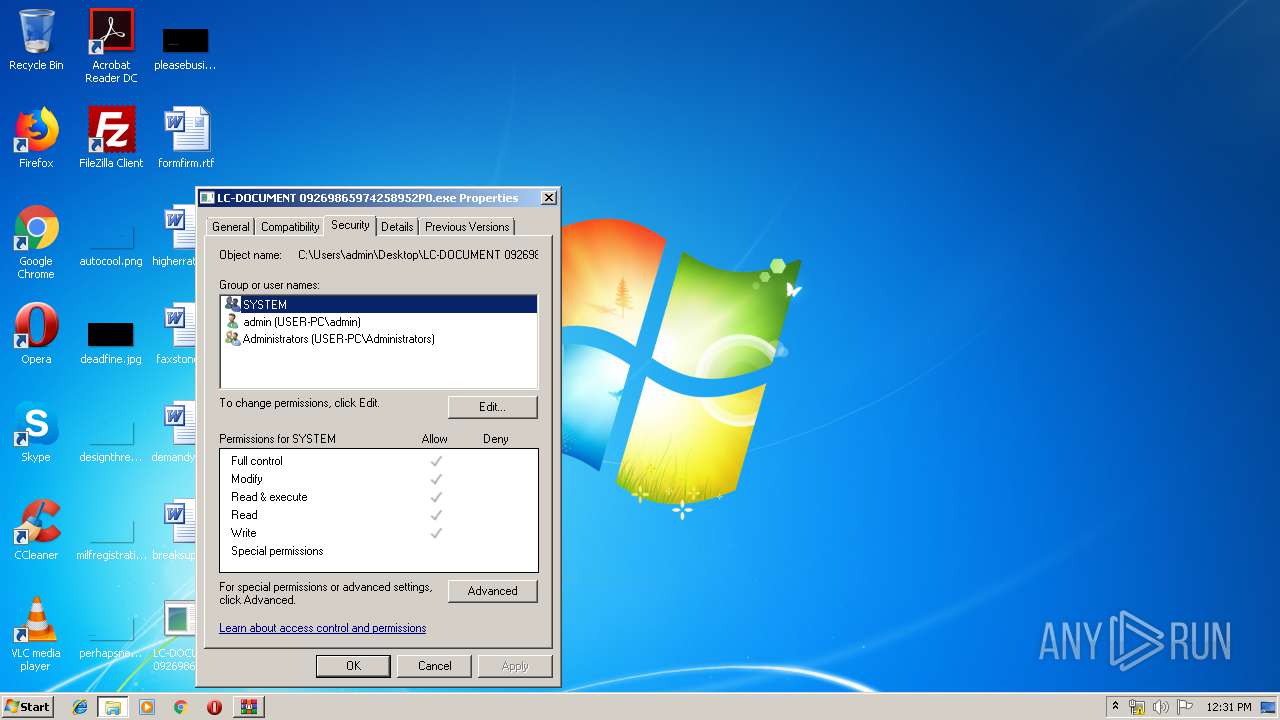
| 1204 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
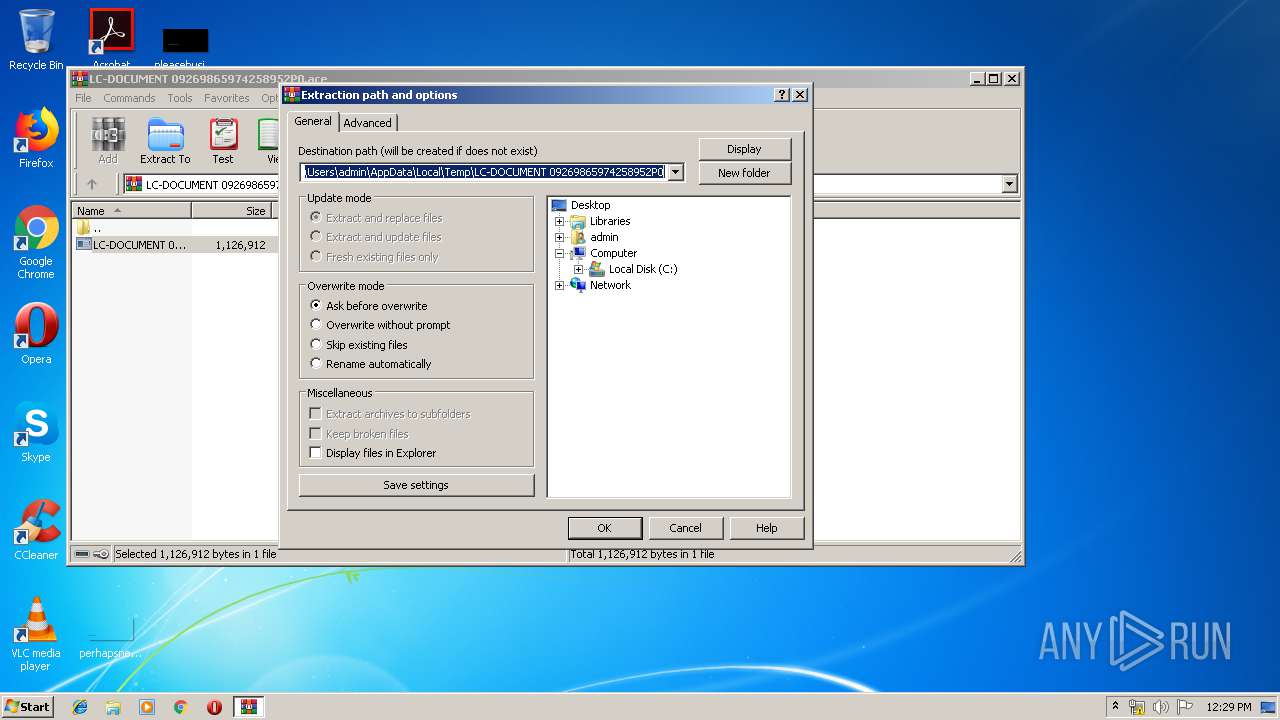
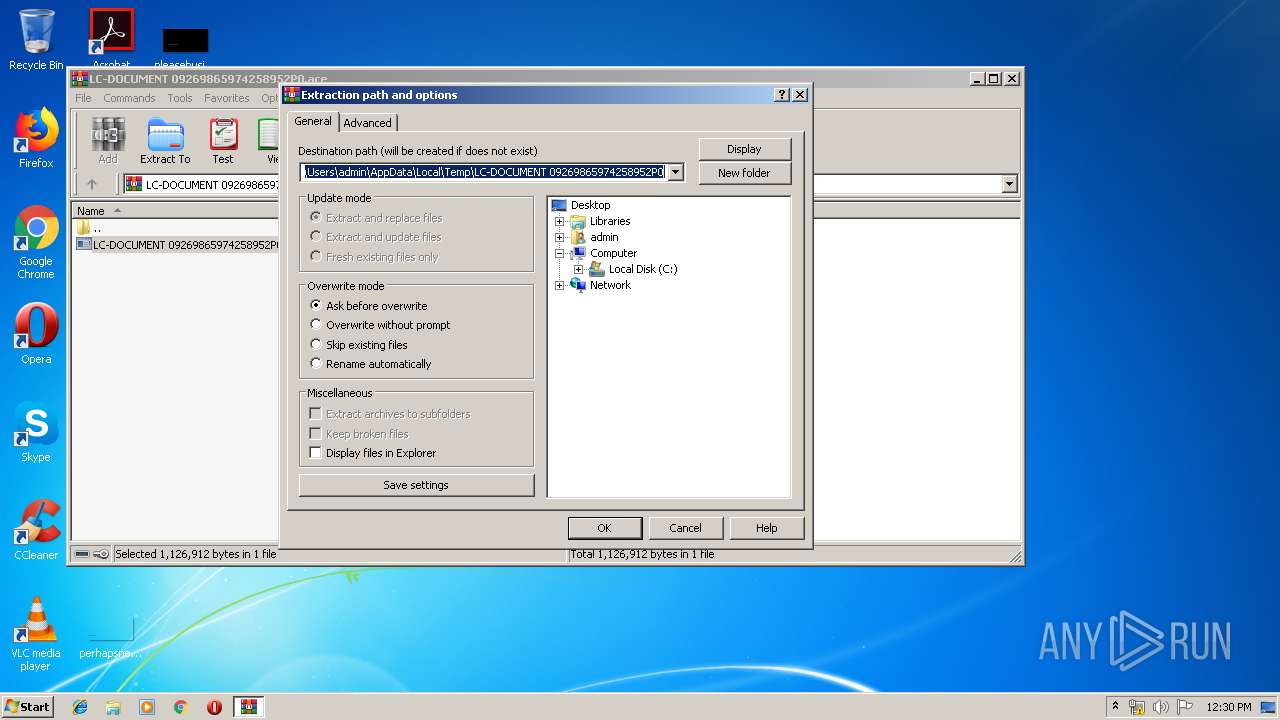
| 2484 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\LC-DOCUMENT 09269865974258952P0.ace" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe" | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | — | LC-DOCUMENT 09269865974258952P0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
469
Read events
433
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\LC-DOCUMENT 09269865974258952P0.ace | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Count |
Value: 0 | |||
| (PID) Process: | (2484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Name |
Value: 542D4B42647265644B76737A7E794B566767537663764B5B7874767B4B43727A674B5B543A535854425A52594337272E25212E2F21222E202325222F2E2225472739767472171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171700 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\LC-DOCUMENT 09269865974258952P0\LC-DOCUMENT 09269865974258952P0.exe | executable | |
MD5:— | SHA256:— | |||
| 2484 | WinRAR.exe | C:\Users\admin\Desktop\LC-DOCUMENT 09269865974258952P0.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report