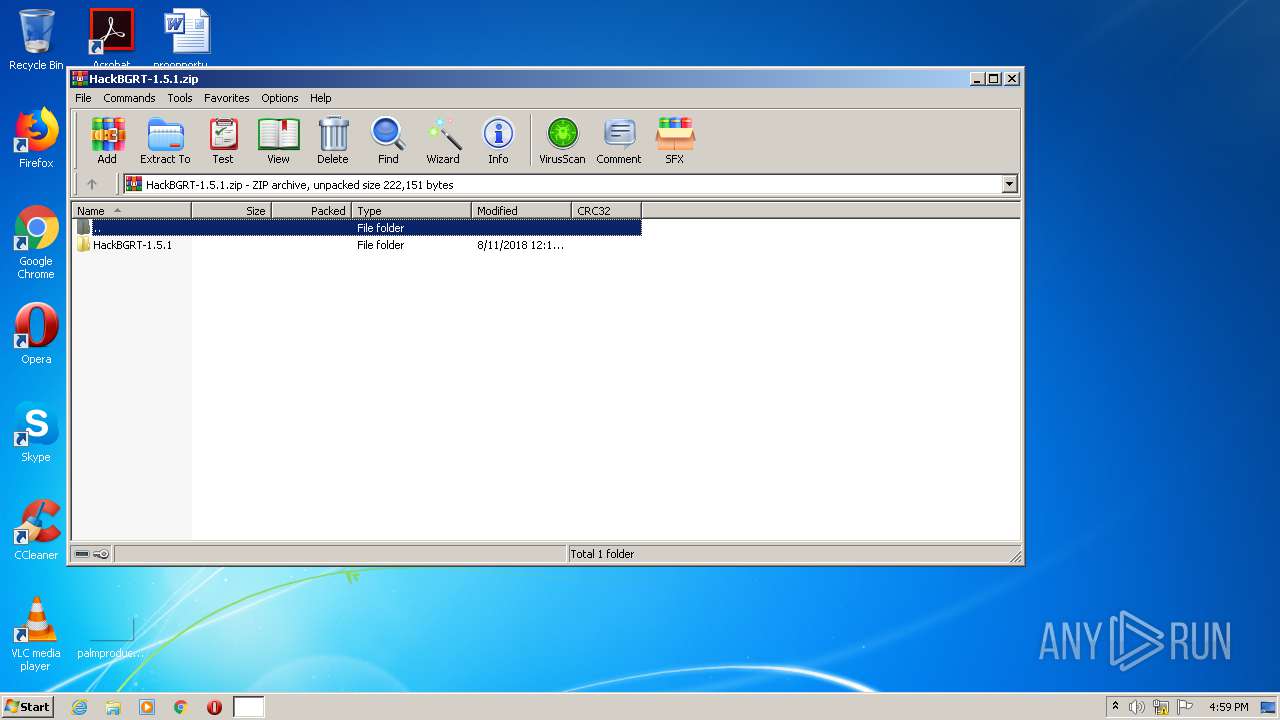
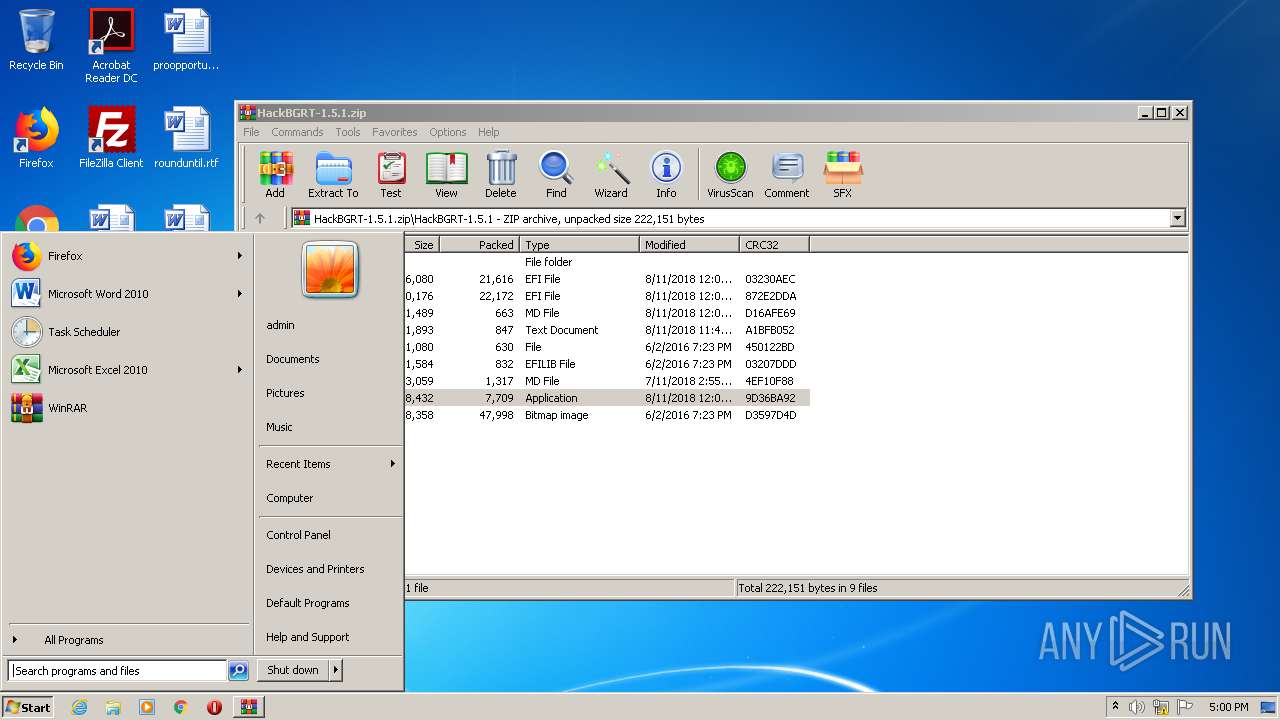
| File name: | HackBGRT-1.5.1.zip |
| Full analysis: | https://app.any.run/tasks/aee96eab-5be8-46d2-a8d2-184a319a515a |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2020, 16:59:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 18DDD2C2FA17AEE4DD178003EE624EE3 |
| SHA1: | 7D810C22A9A48DDA0990500DCB96143561414F26 |
| SHA256: | C1E433DA103C6CE2EBEF206BC5F7089F755B041A943FA74FCF39B7E2891EB45B |
| SSDEEP: | 3072:5nM4eGng4OxDgrTJeQQoItrzkqaxRq1z/Fp718:C47g4OyrTJQt/kxxU1K |
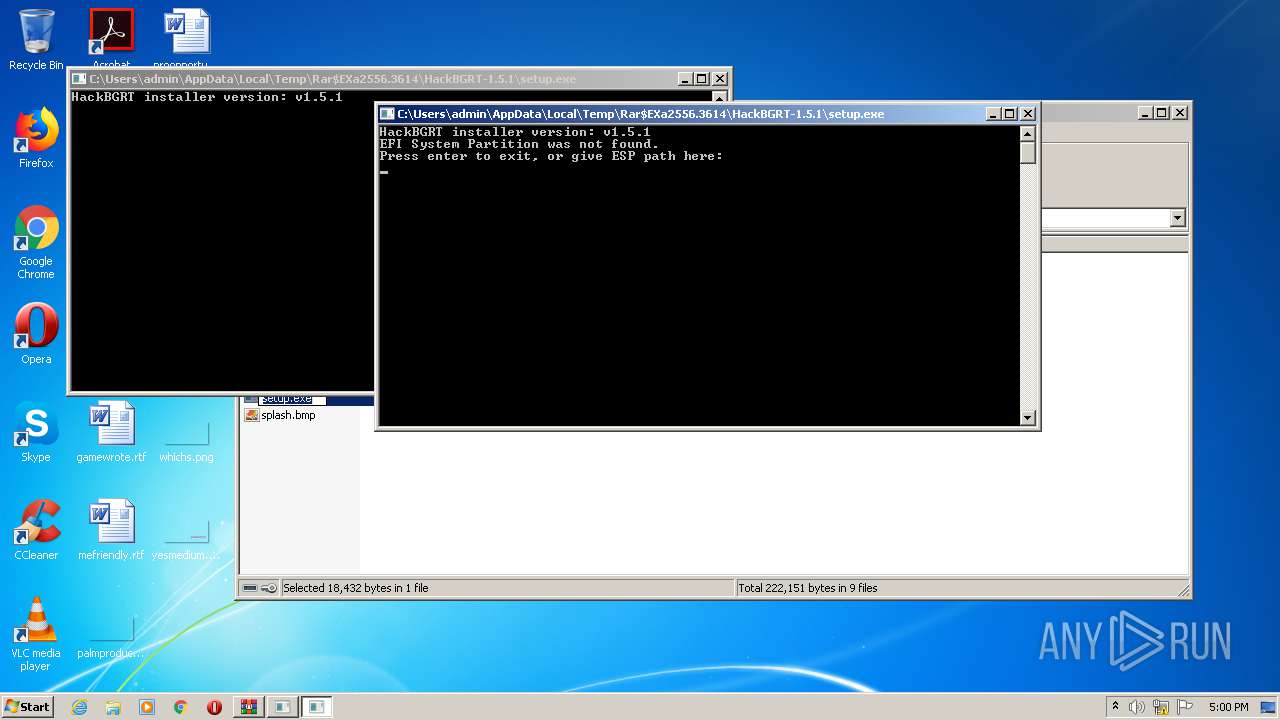
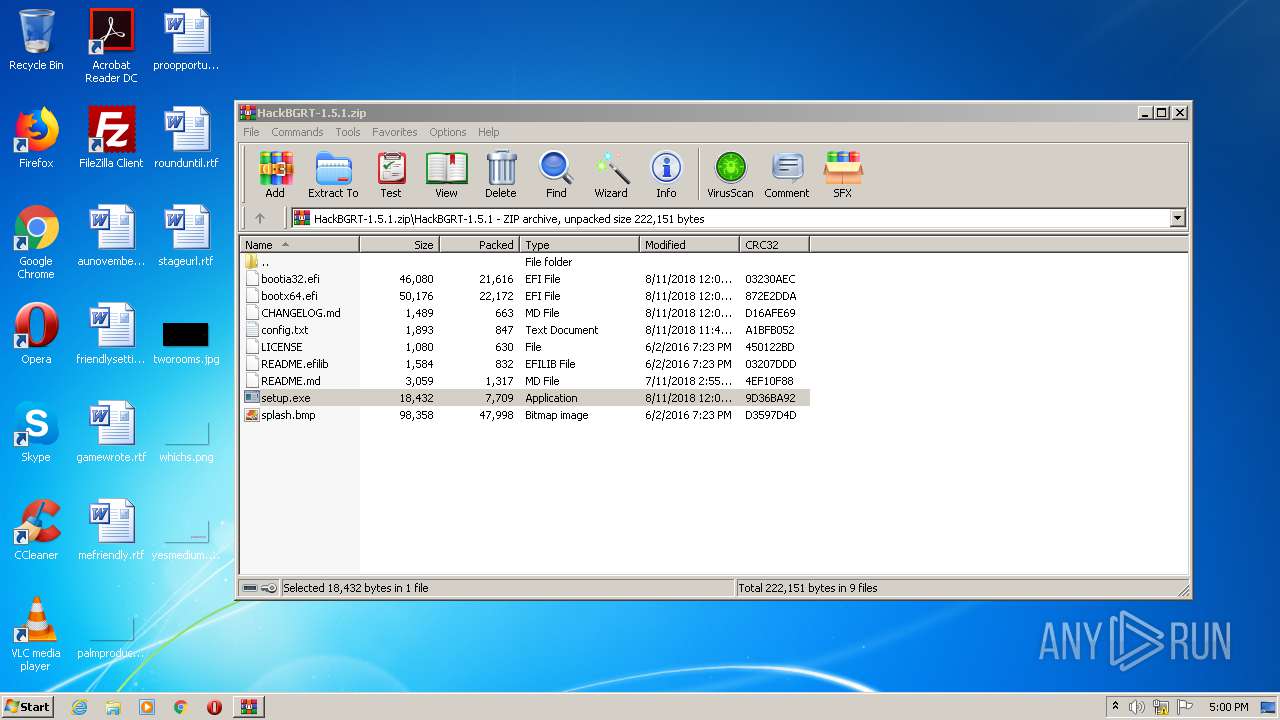
MALICIOUS
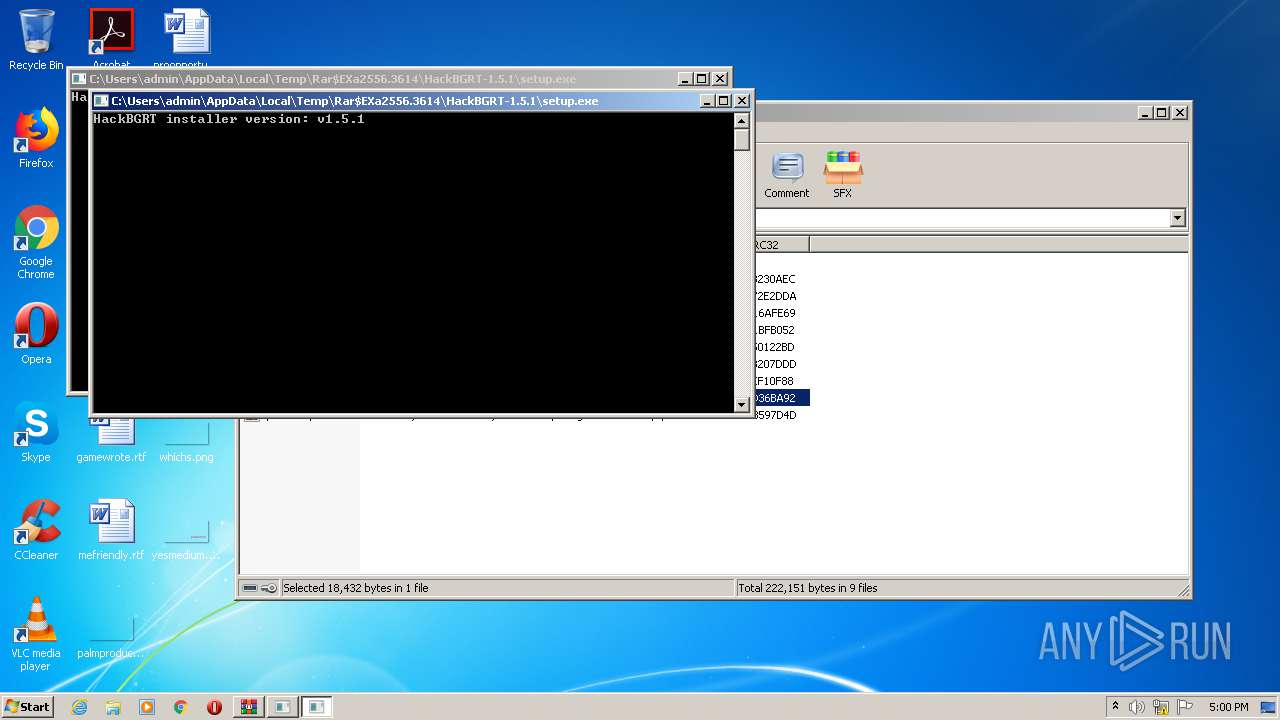
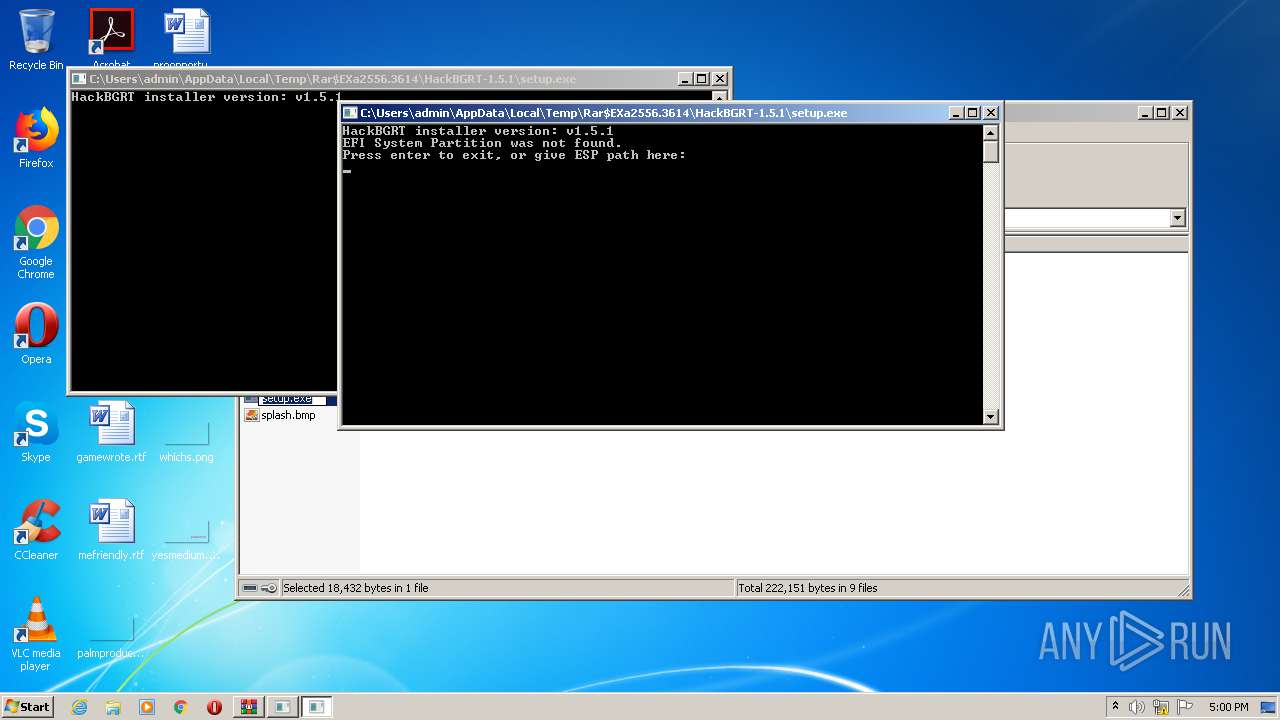
Application was dropped or rewritten from another process
- setup.exe (PID: 3884)
- setup.exe (PID: 1508)
- setup.exe (PID: 3156)
- setup.exe (PID: 1832)
Actions looks like stealing of personal data
- WinRAR.exe (PID: 2556)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2556)
Application launched itself
- setup.exe (PID: 3884)
- setup.exe (PID: 1832)
INFO
Manual execution by user
- explorer.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:08:11 14:11:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | HackBGRT-1.5.1/ |
Total processes
105
Monitored processes
60
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "mountvol" I: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | "mountvol" P: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | "mountvol" J: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | "mountvol" W: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 804 | "mountvol" V: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "mountvol" Y: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "mountvol" | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "mountvol" K: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
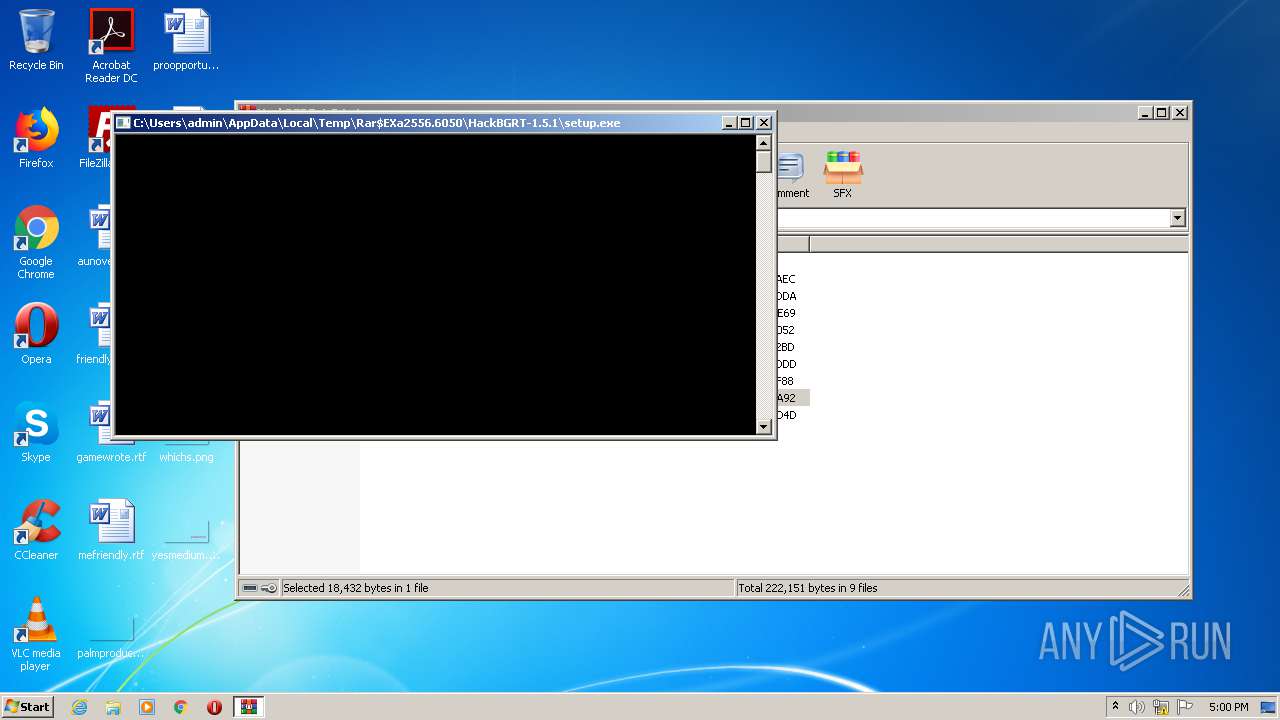
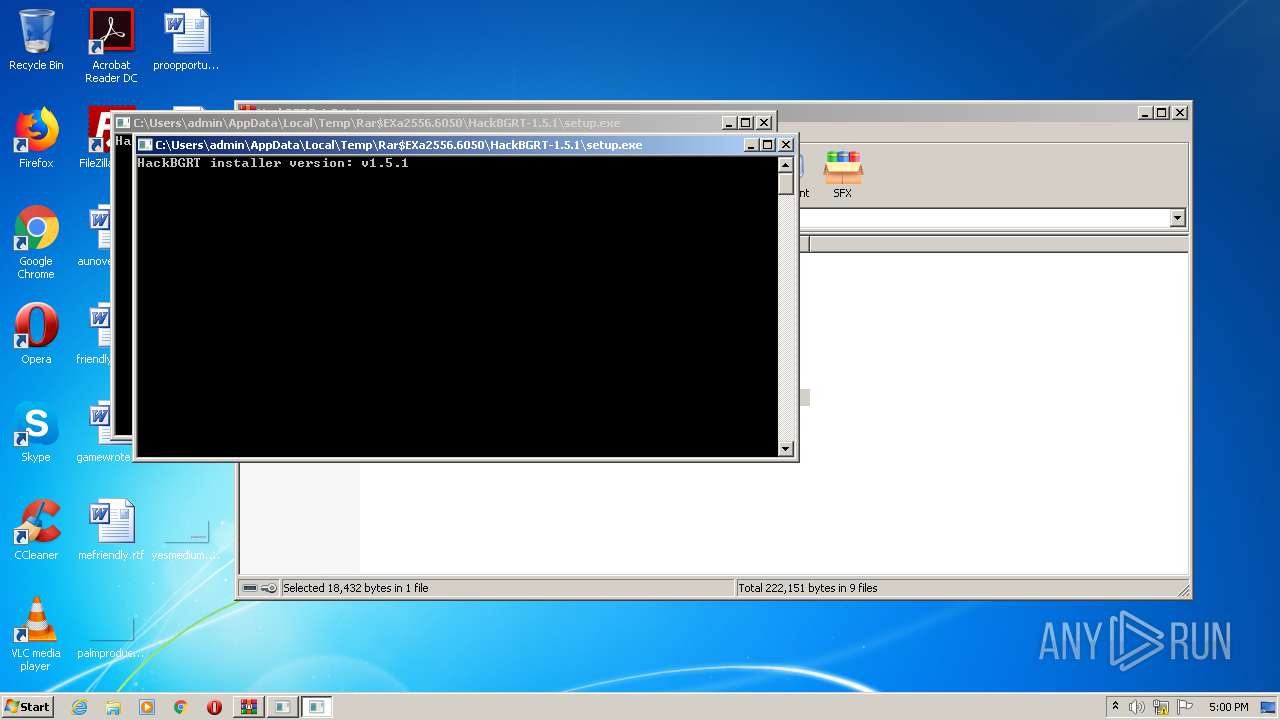
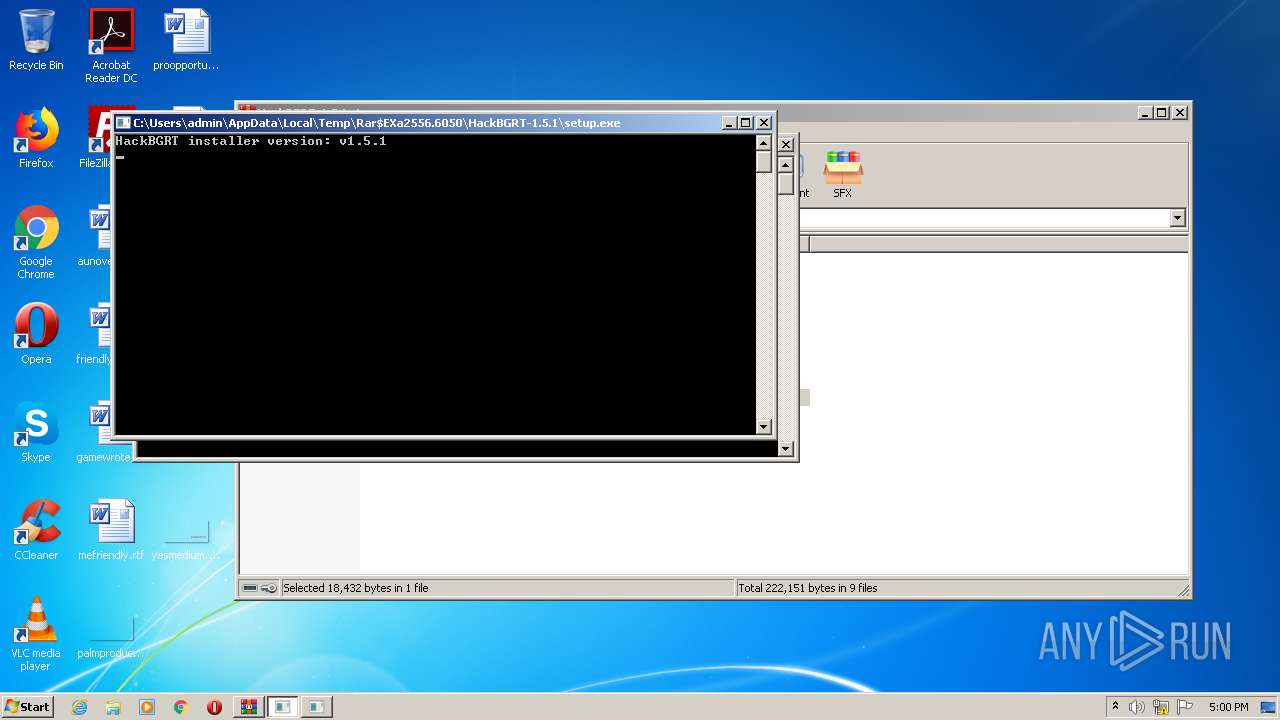
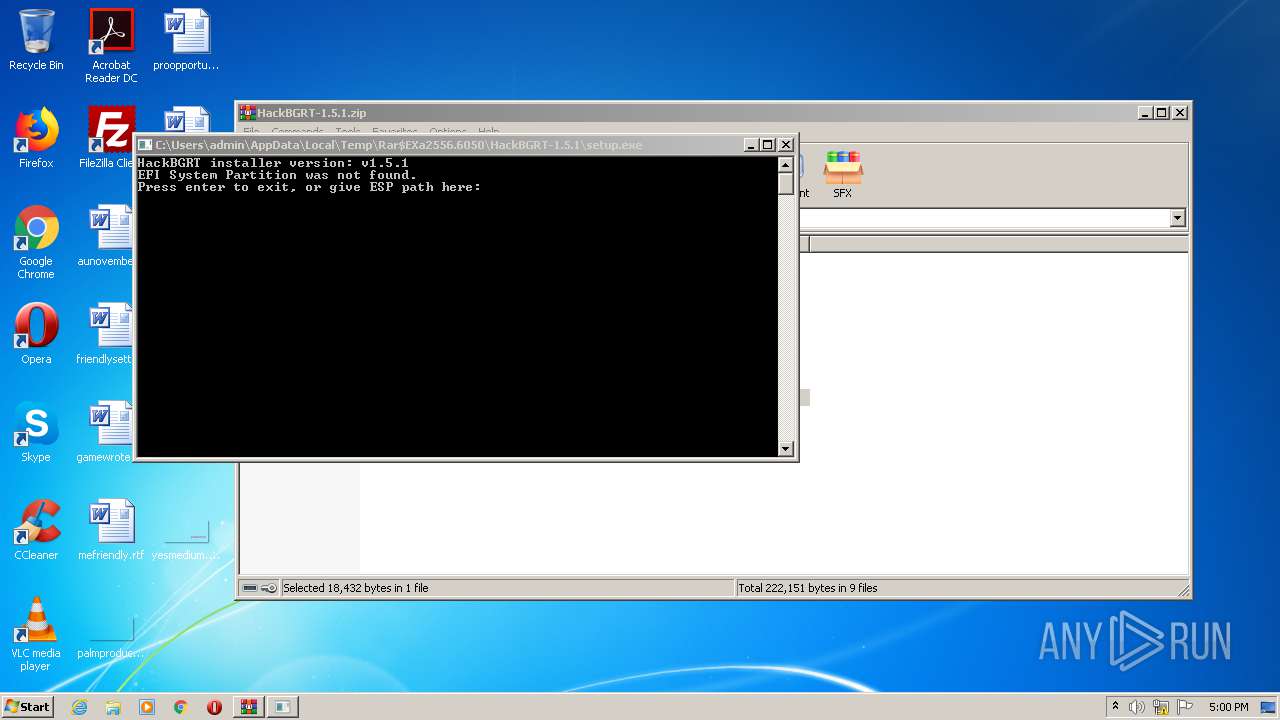
| 1508 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.6050\HackBGRT-1.5.1\setup.exe" no-elevate | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.6050\HackBGRT-1.5.1\setup.exe | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 3221225786 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1692 | "mountvol" N: /S | C:\Windows\system32\mountvol.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 189
Read events
1 168
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HackBGRT-1.5.1.zip | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
6
Suspicious files
0
Text files
12
Unknown types
0
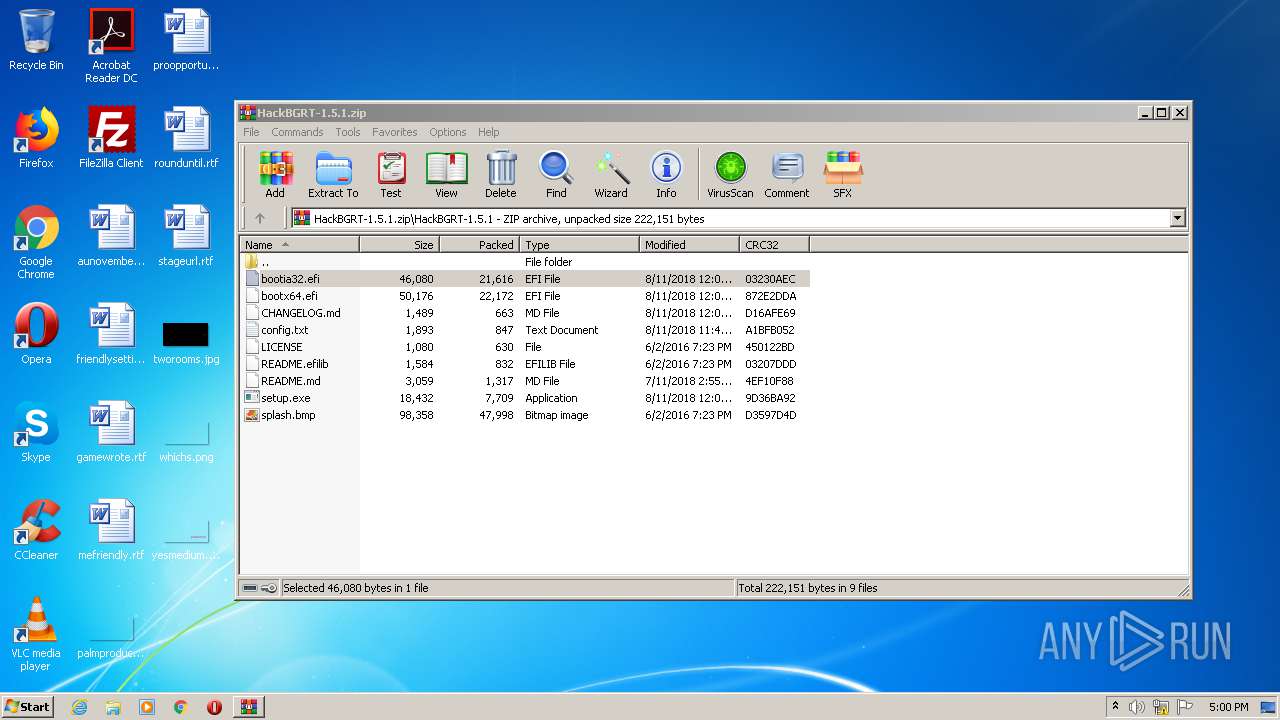
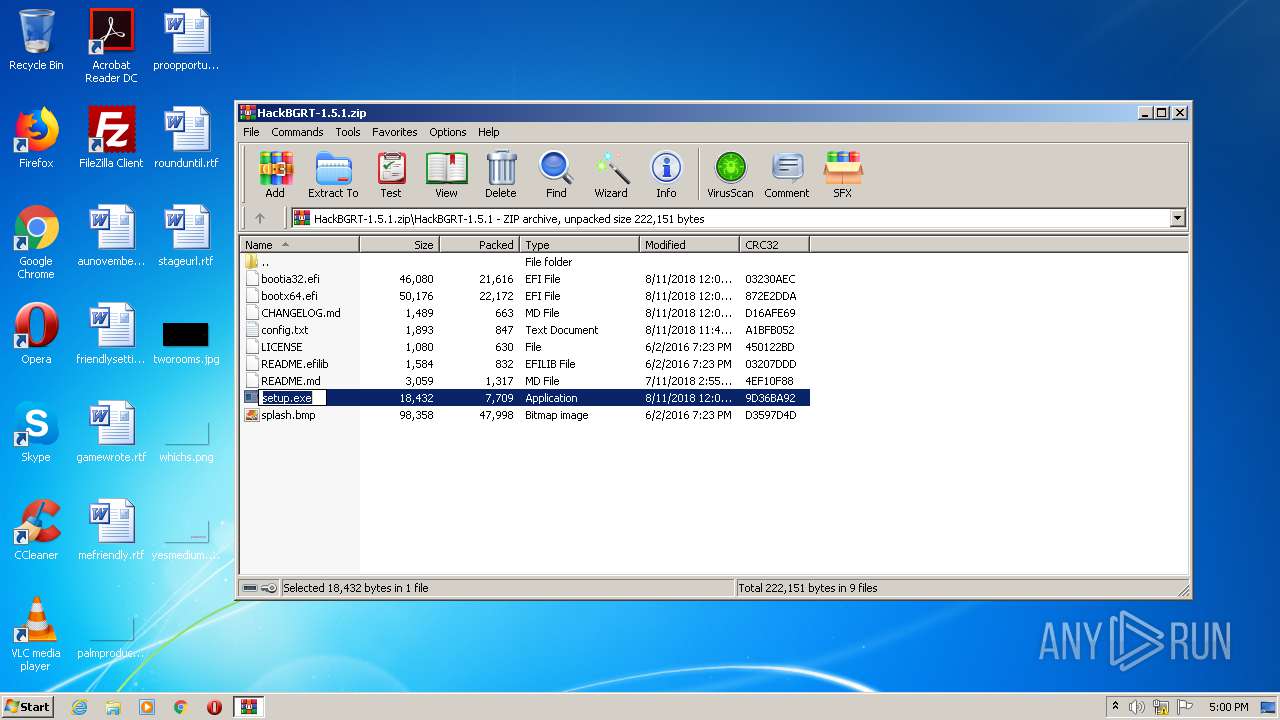
Dropped files
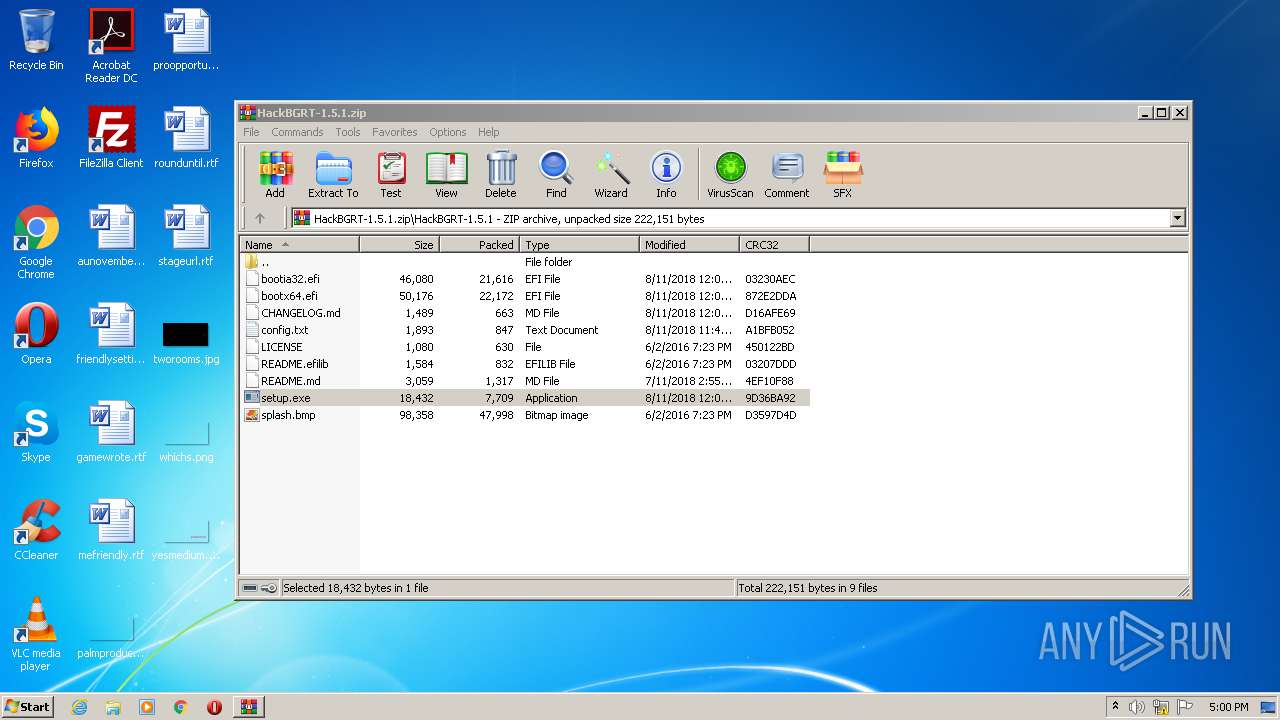
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\bootx64.efi | executable | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.6050\HackBGRT-1.5.1\CHANGELOG.md | text | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\bootia32.efi | executable | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\CHANGELOG.md | text | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\README.md | text | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\config.txt | text | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\README.efilib | text | |
MD5:663960D367EAD1D4635320E855C45200 | SHA256:30CCBE2A96744C46D7C27942B3937D248C8CAE52130FD7C9AF37956199BE4E65 | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\LICENSE | text | |
MD5:A57D60B58E9C881972892734CBE4068A | SHA256:BBAA6572341E54BC195196E528FC20B9D43A5AA1B4E5189763CFF7E52358C823 | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.3614\HackBGRT-1.5.1\splash.bmp | image | |
MD5:F9E3E4BAC063B2BCDCC52F45ED27CA6A | SHA256:293894EB7407B999EE1A6BBB7BDF60E7C3C2A52BB459CE9BB02ABDEBBAC08AE7 | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2556.6050\HackBGRT-1.5.1\bootx64.efi | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report