| download: | index.html |
| Full analysis: | https://app.any.run/tasks/2271128e-8ae6-49fe-90a0-bb681a4743d9 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2018, 16:04:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 2C3A42B8EF09AEE4913EE7A61E8E3972 |
| SHA1: | CF17E92909C7FC34E780E2C44732884CAD7E459A |
| SHA256: | C1C2FA7E8BDDDA36E98A960F2E79E7B82F0A45090EAB1437E5272F157A7B3EB5 |
| SSDEEP: | 1536:geBn6g6dZhOr/ztqmXY8ekQpPCWrlXBuPWoi8rJPI4T8Vya+dYdLEvw0nOqkQz76:gUn6gzWoi8rJPI4T8Vya+dYdLEvw0nOz |
MALICIOUS
Changes internet zones settings
- iexplore.exe (PID: 2780)
Changes settings of System certificates
- iexplore.exe (PID: 3184)
SUSPICIOUS
Application launched itself
- iexplore.exe (PID: 2780)
Starts Internet Explorer
- iexplore.exe (PID: 2780)
Reads internet explorer settings
- iexplore.exe (PID: 3184)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 2780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3184)
Creates files in the user directory
- iexplore.exe (PID: 3184)
INFO
Dropped object may contain URL's
- iexplore.exe (PID: 3184)
Reads settings of System Certificates
- iexplore.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
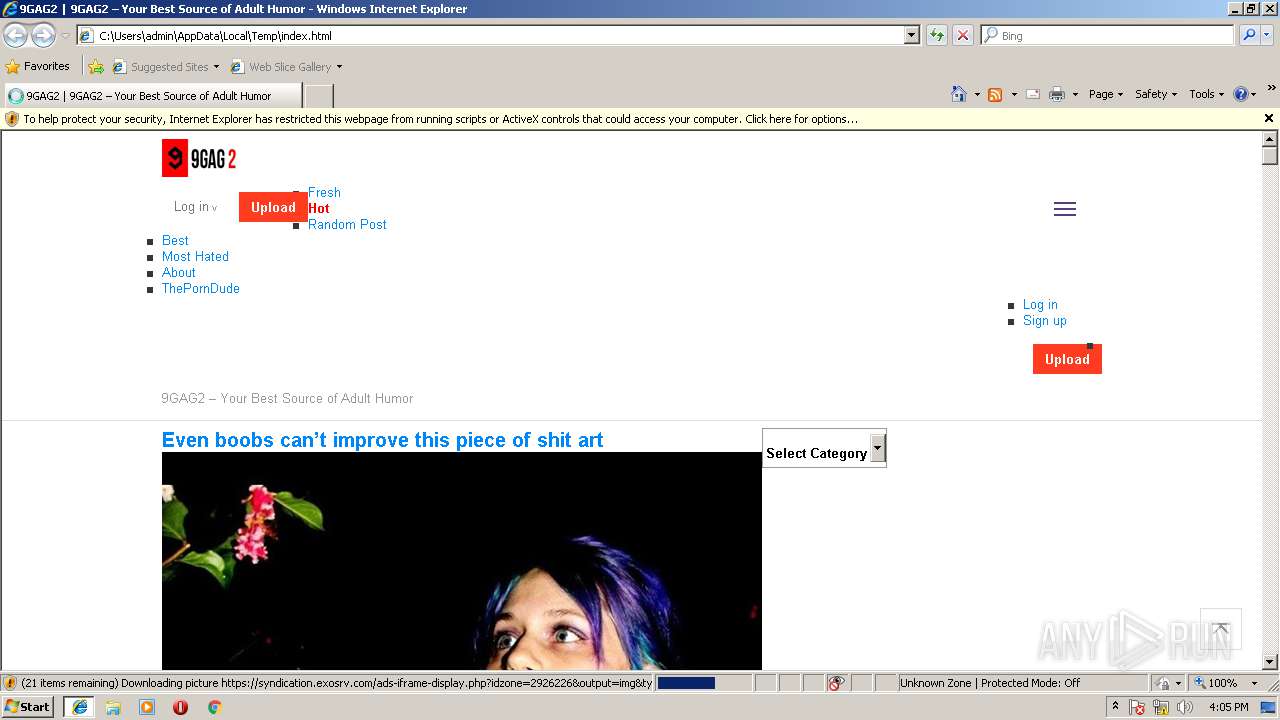
| Description: | Funny porn for adults. Your best source of adult humor, porn fails, bloopers, weird fetishes and shockers. |
|---|---|
| viewport: | width=device-width |
| Title: | 9GAG2 | 9GAG2 – Your Best Source of Adult Humor |
| Generator: | WordPress 4.9.4 |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2780 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2780 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
452
Read events
349
Write events
101
Delete events
2
Modification events
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B000000090000000000000000000000000000000400000000000000108E82C8479FD301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A8640B0000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {CC0D8873-2933-11E8-943E-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E207030005001000100005000900C801 | |||
Executable files
0
Suspicious files
39
Text files
74
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\O0BRTIYI\bootstrap.min[1].js | text | |
MD5:7BCDD2AD3F1FF109E72E71C53B7DFA37 | SHA256:27FB5F00A5B79FF72F273B209EED6398353E764E230E6109820D436D923F3A6B | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\O0BRTIYI\jquery.fancybox[1].css | text | |
MD5:BBD3C7F1D579D0AC140DF5B7FFAE411D | SHA256:21BF87572A91C47B98F9B38E73650205001EC20C401519852AE01ACA618B0D8B | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\X1H3Z3B0\9gag2LOGOU3[1].jpg | image | |
MD5:54DB0000D105FA1595863653C5EC32DF | SHA256:A8C9C46C509D3ABA069A2B944878AEBFD6400EE04E5DCDA2B6B9055F8A8EF44F | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\media[1].css | text | |
MD5:583A29C81AE07D8574770A8F3FCE28BD | SHA256:C848AB0C4AA154AC2C86E5E9FCCB2C96A61E194DD93D2784364CE3CF7C4E5F1D | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\5B8XX9S5\9gag2-Adult-Humor-Funny-Porn-Joke-Hilarious-8649[1].jpg | image | |
MD5:3783BE4667173750CDB7B18A8AF68832 | SHA256:07BCF32DA6AB27F3CB5C7E5E0B9B8708934FCF45F2B1CE602602222A0D01F0B2 | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\5B8XX9S5\9gag2-Adult-Humor-Funny-Porn-Joke-Hilarious-8650[1].jpg | image | |
MD5:38E806B06EAE200092EB717F9562500F | SHA256:1A19BAE9B98797985BC2E645711D131423D4F86DCFA7FA01A328964733EDFCBB | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\main[1].css | text | |
MD5:872C94D9C9DF90E22F2C25C674FBAA22 | SHA256:75760A35C7B344BE9FC85737CC86580269427EBEA76E45ED510DEDBC41D47B35 | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\5B8XX9S5\style[1].css | text | |
MD5:10BED7B87D383A0D586CF79D9FF090F5 | SHA256:C60132D6FC85DC8A9D1717EAE65A5778EEF33F713442C0F6A552336227BA0327 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
63
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/uploads/2018/02/9gag2-Adult-Humor-Funny-Porn-Joke-Hilarious-8646.jpg | US | image | 122 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/uploads/2018/02/9gag2-Adult-Humor-Funny-Porn-Joke-Hilarious-8644.jpg | US | image | 32.4 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/uploads/2018/02/9gag2-Adult-Humor-Funny-Porn-Joke-Hilarious-8643.jpg | US | image | 132 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/themes/9gag/style.css | US | text | 8.93 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/themes/9gag/js/html5.js | US | html | 1.22 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/themes/9gag/main.css?ver=20140426 | US | text | 13.8 Kb | malicious |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/themes/9gag/media.css?ver=20140728 | US | text | 931 b | malicious |
— | — | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | 200 | 104.25.146.38:80 | http://www.9gag2.com/wp-content/themes/9gag/inc/fancybox/jquery.fancybox.css?ver=4.9.4 | US | text | 1.17 Kb | malicious |
— | — | GET | 200 | 172.217.22.10:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.10.2/jquery.min.js?ver=4.9.4 | US | text | 32.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 2.21.246.17:80 | www.download.windowsupdate.com | Akamai International B.V. | AT | whitelisted |
— | — | 205.185.216.10:443 | ads.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
— | — | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 172.217.22.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.25.146.38:80 | www.9gag2.com | Cloudflare Inc | US | shared |
— | — | 104.19.193.102:443 | ajax.cloudflare.com | Cloudflare Inc | US | shared |
— | — | 205.185.216.42:443 | ads.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.9gag2.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
ads.exosrv.com |
| whitelisted |
syndication.exosrv.com |
| whitelisted |
apps.identrust.com |
| shared |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |