| File name: | Gdi_trojan.exe |
| Full analysis: | https://app.any.run/tasks/5a15db68-4811-4707-a551-bd1f76a3401a |
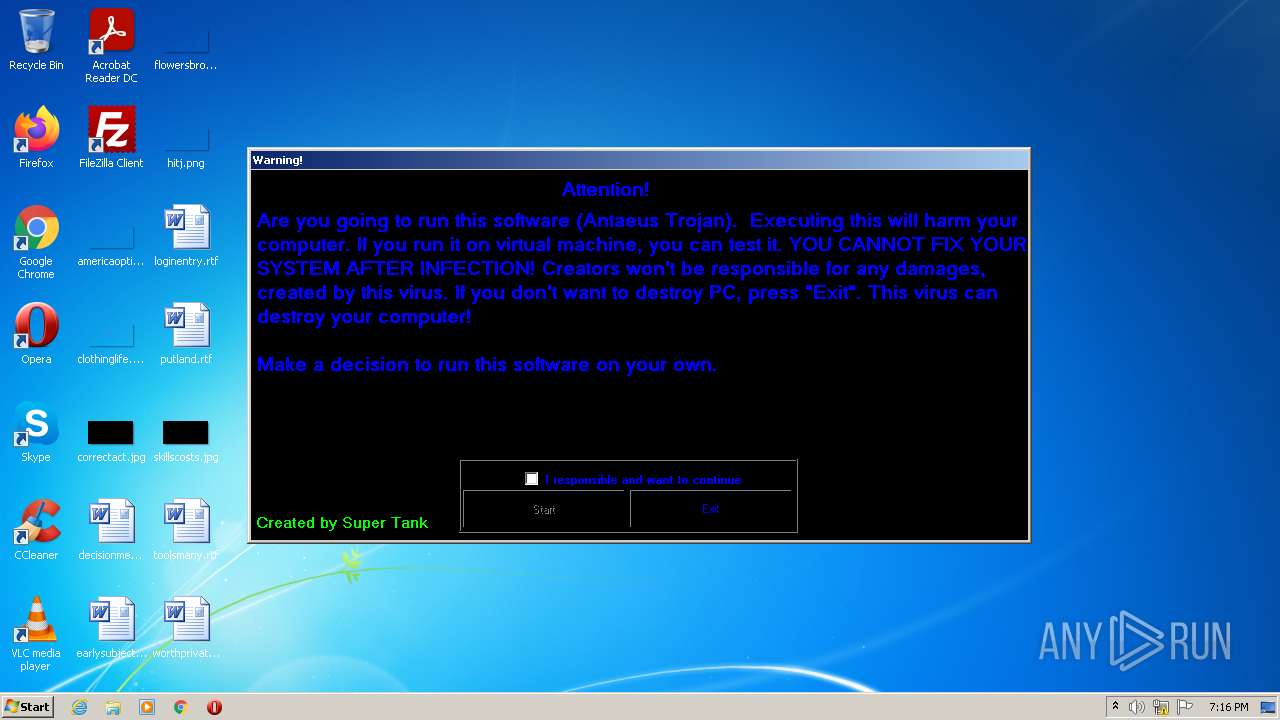
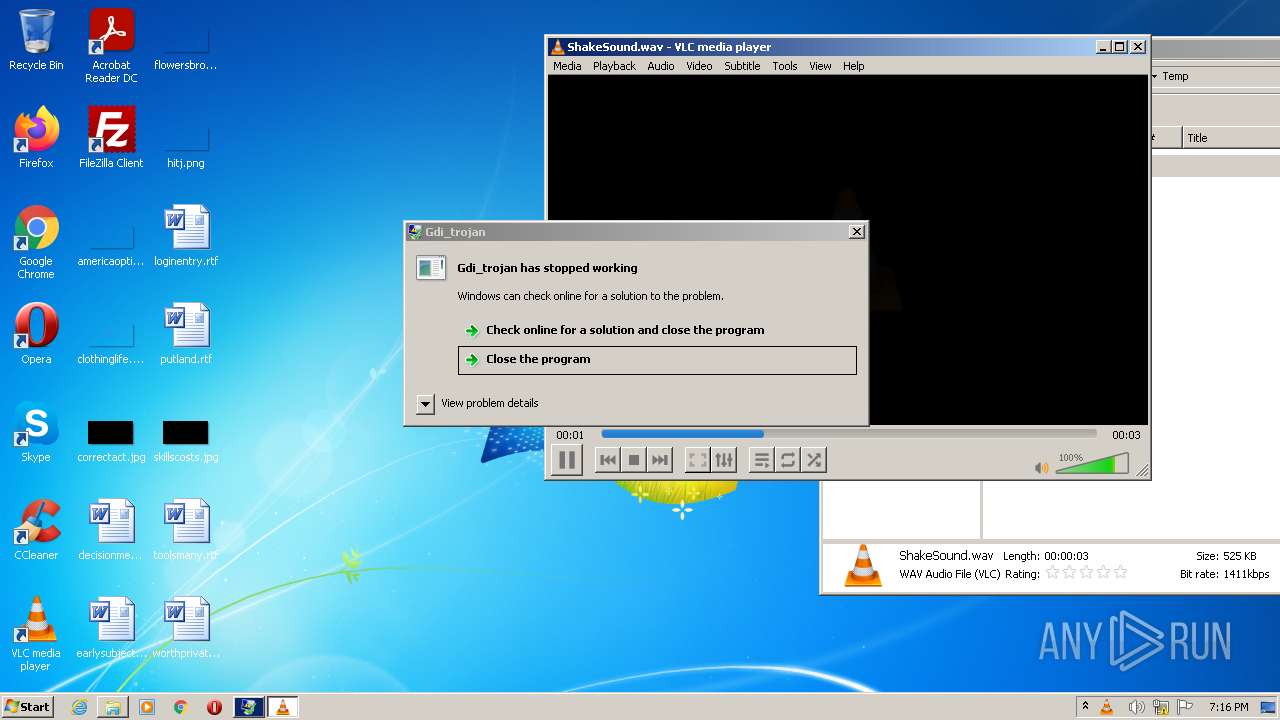
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 18:15:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4FCDE5315471C28FB56B903BEDA70DB3 |
| SHA1: | 8F9F84B114EA7B363513B3428FBDA2B4D0E86D87 |
| SHA256: | C1C14E3FF14BC873D7048889E7F8B25A054A2D650CD65B01131CDAFE290DB5A8 |
| SSDEEP: | 24576:+0ePxXP8c4ndIrymkvcWfJ90ePxXP8c4ndIrymkvcWfJ0:RexqlxzR6exqlxzR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- Gdi_trojan.exe (PID: 3532)
- vlc.exe (PID: 3164)
Checks supported languages
- Gdi_trojan.exe (PID: 3532)
- vlc.exe (PID: 3164)
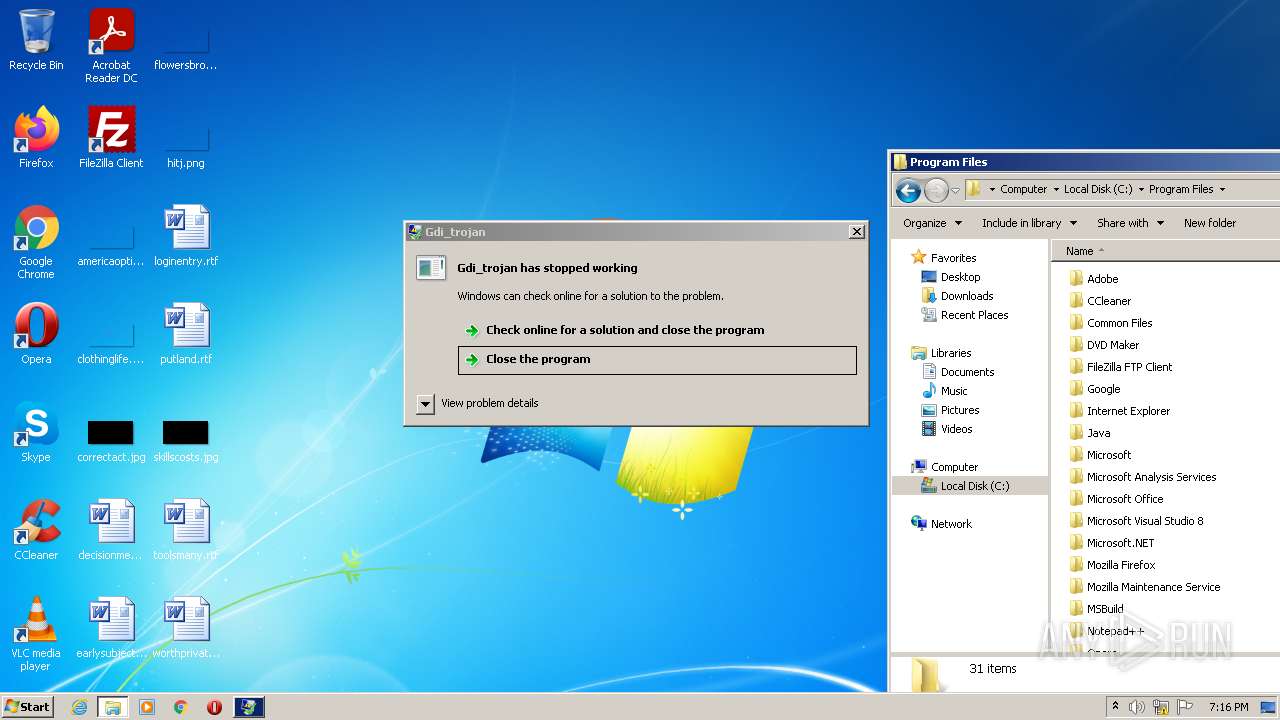
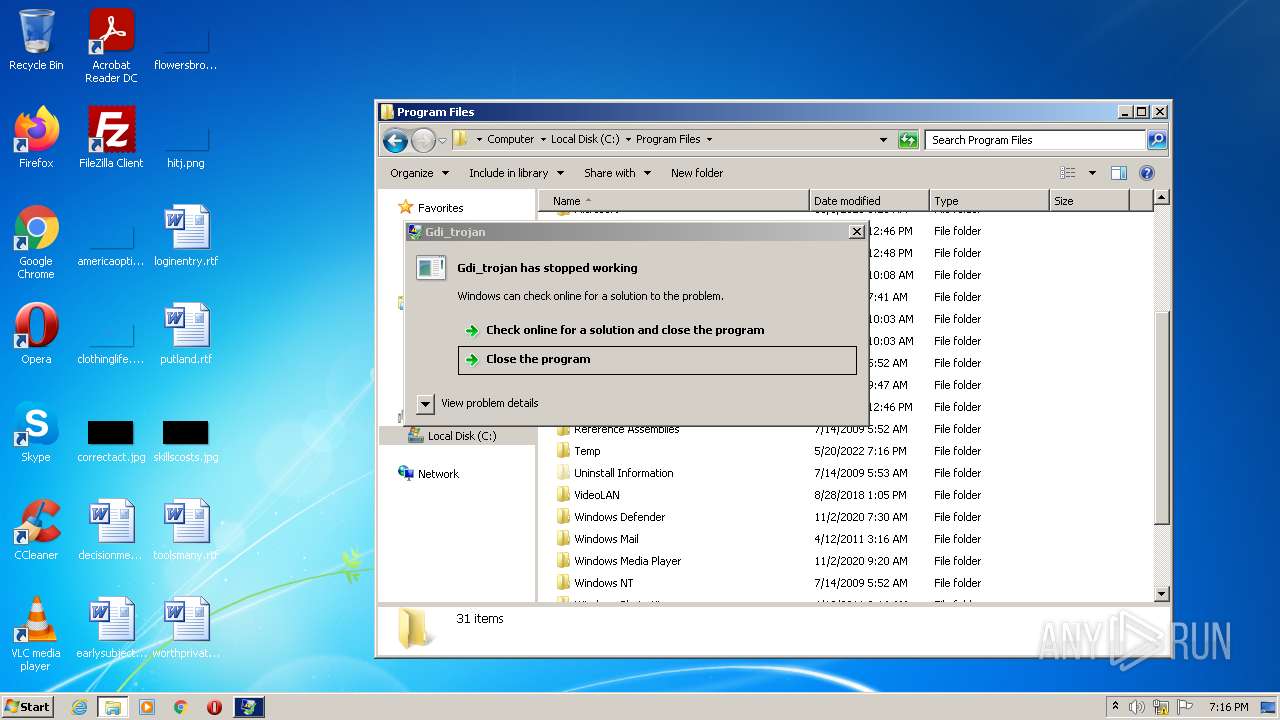
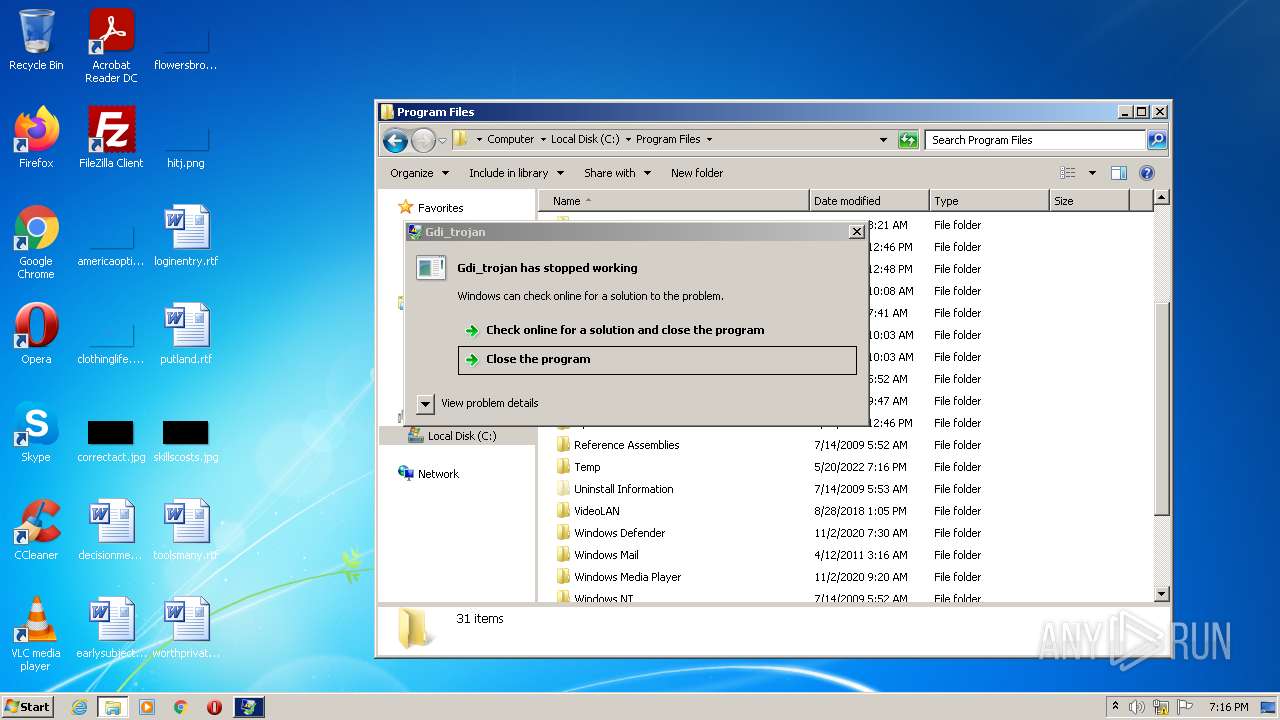
Creates files in the program directory
- Gdi_trojan.exe (PID: 3532)
Creates a directory in Program Files
- Gdi_trojan.exe (PID: 3532)
Creates files in the user directory
- vlc.exe (PID: 3164)
INFO
Checks supported languages
- explorer.exe (PID: 2492)
Reads the computer name
- explorer.exe (PID: 2492)
Manual execution by user
- vlc.exe (PID: 3164)
- explorer.exe (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Gdi_trojan |
| OriginalFileName: | Gdi_trojan.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © HP Inc. 2022 |
| InternalName: | Gdi_trojan.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Gdi_trojan |
| CompanyName: | HP Inc. |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x10d472 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 6144 |
| CodeSize: | 1095168 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2054:04:23 06:22:49+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Mar-1918 21:54:33 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | HP Inc. |
| FileDescription: | Gdi_trojan |
| FileVersion: | 1.0.0.0 |
| InternalName: | Gdi_trojan.exe |
| LegalCopyright: | Copyright © HP Inc. 2022 |
| LegalTrademarks: | - |
| OriginalFilename: | Gdi_trojan.exe |
| ProductName: | Gdi_trojan |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Mar-1918 21:54:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0010B478 | 0x0010B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37205 |
.rsrc | 0x0010E000 | 0x00001518 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38216 |
.reloc | 0x00110000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.44637 | 4394 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
45
Monitored processes
4
Malicious processes
0
Suspicious processes
1
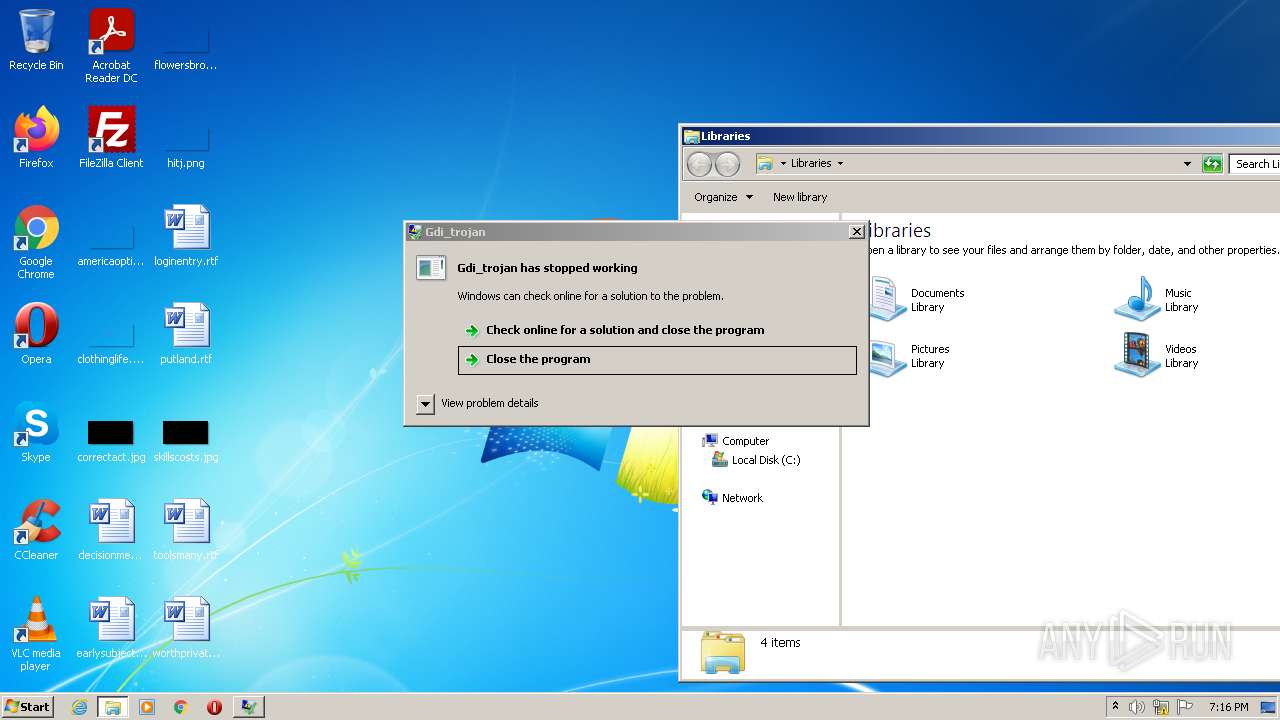
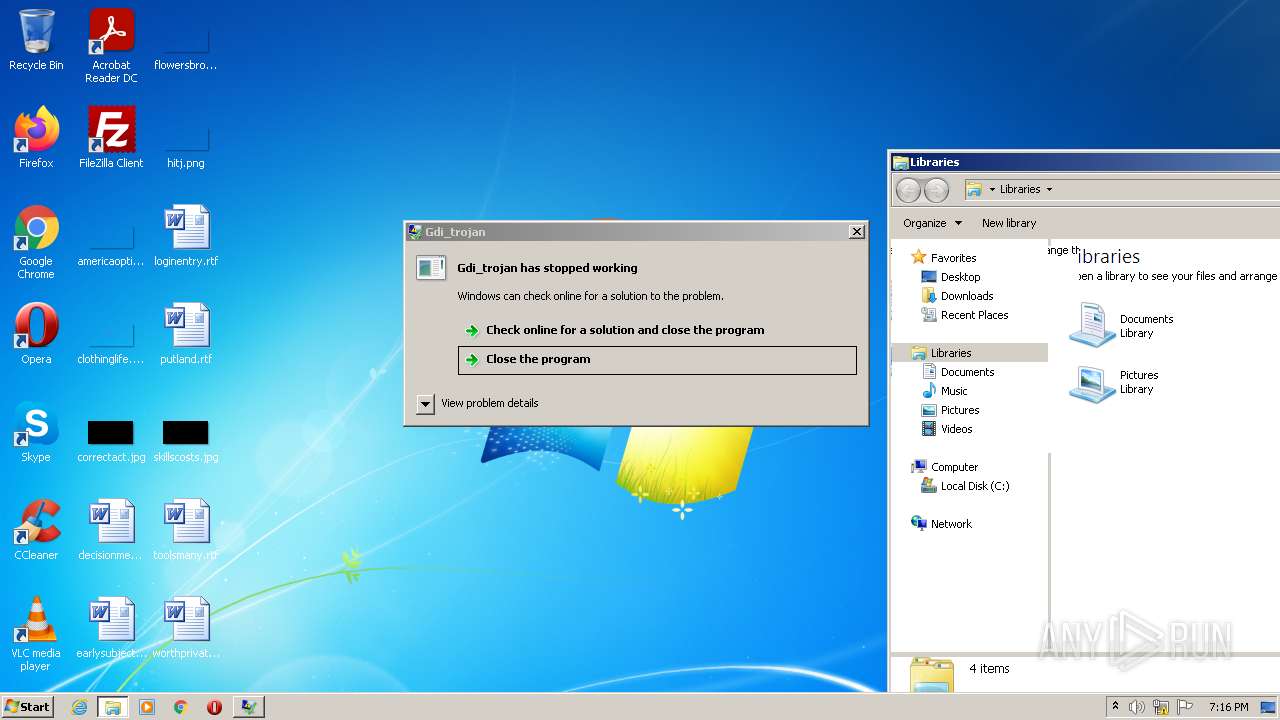
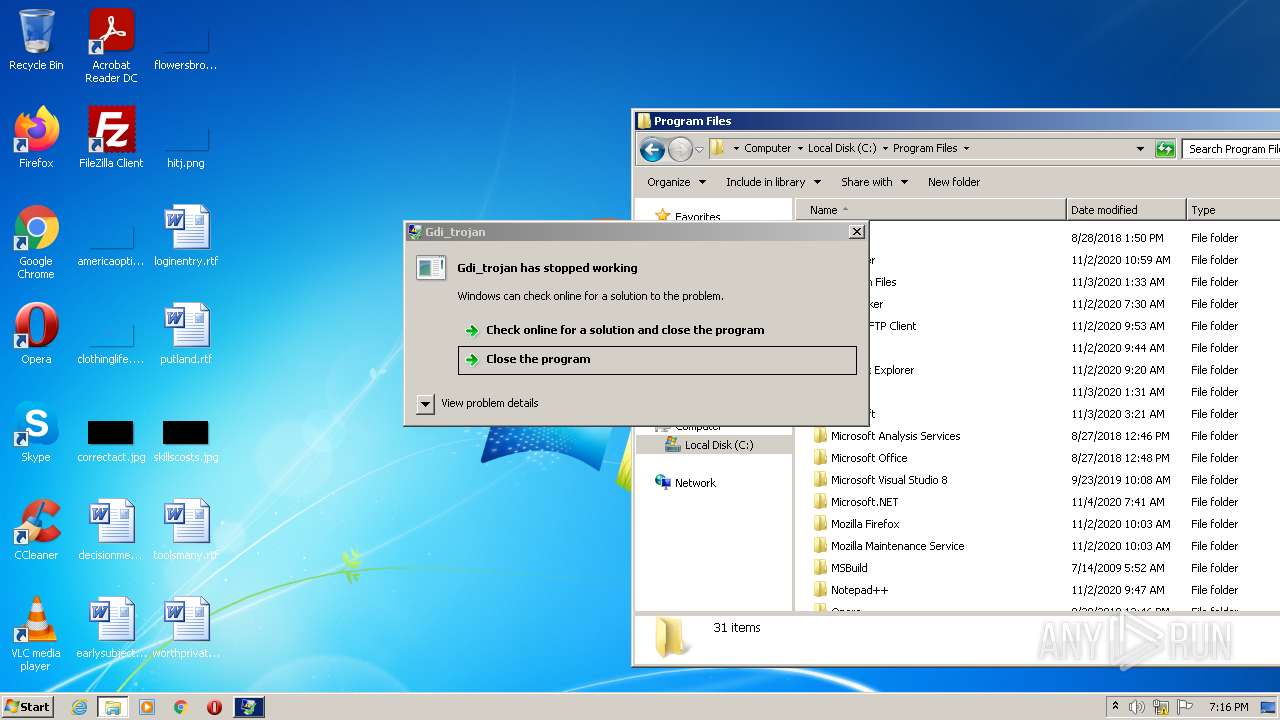
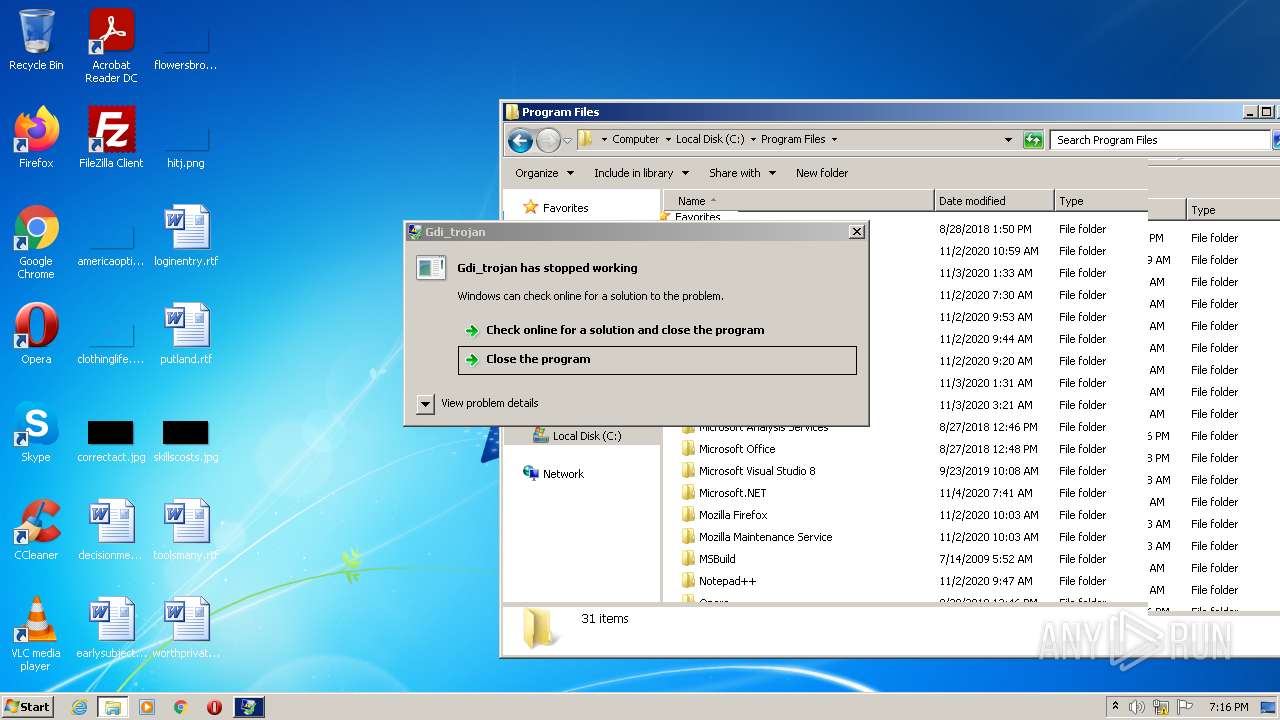
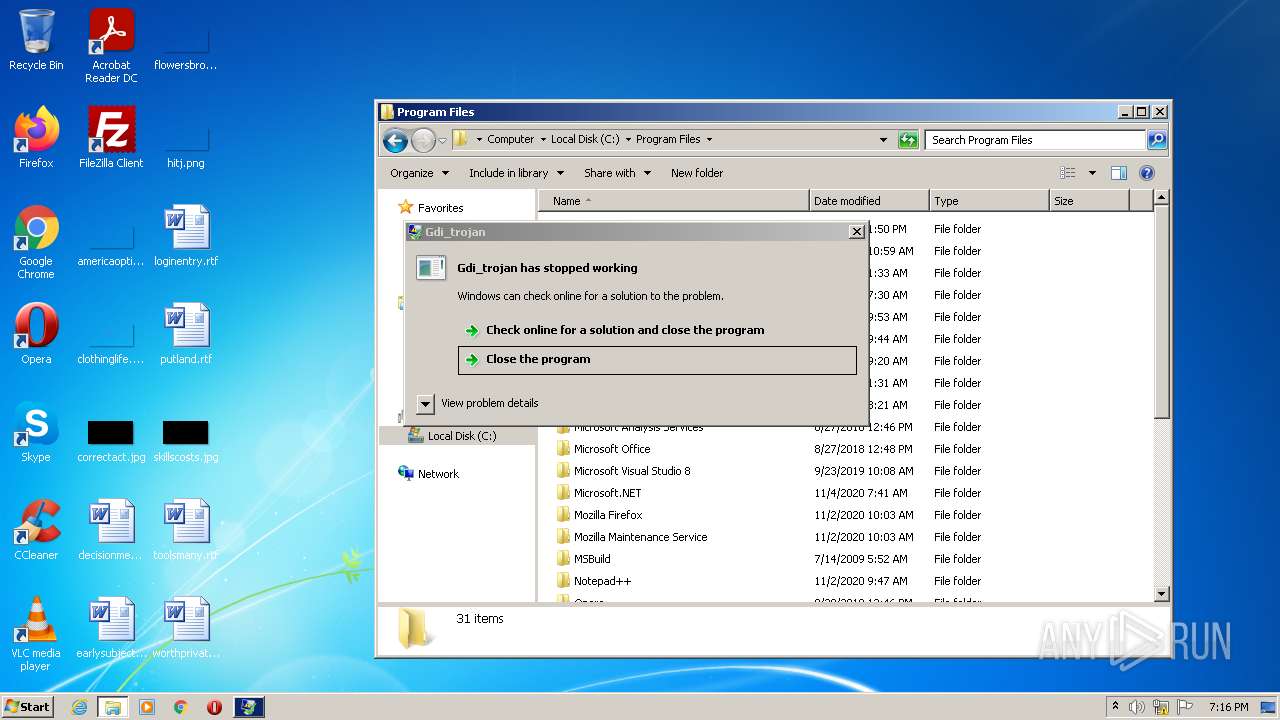
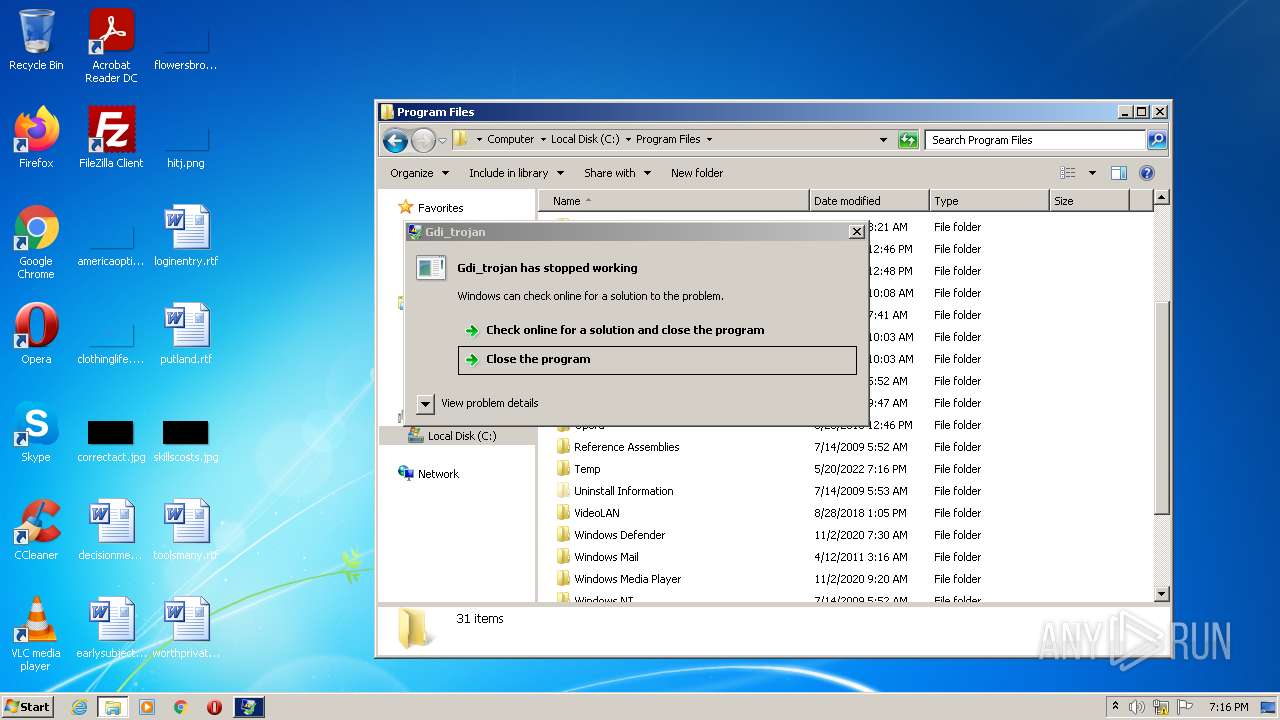
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Users\admin\AppData\Local\Temp\Gdi_trojan.exe" | C:\Users\admin\AppData\Local\Temp\Gdi_trojan.exe | — | Explorer.EXE | |||||||||||
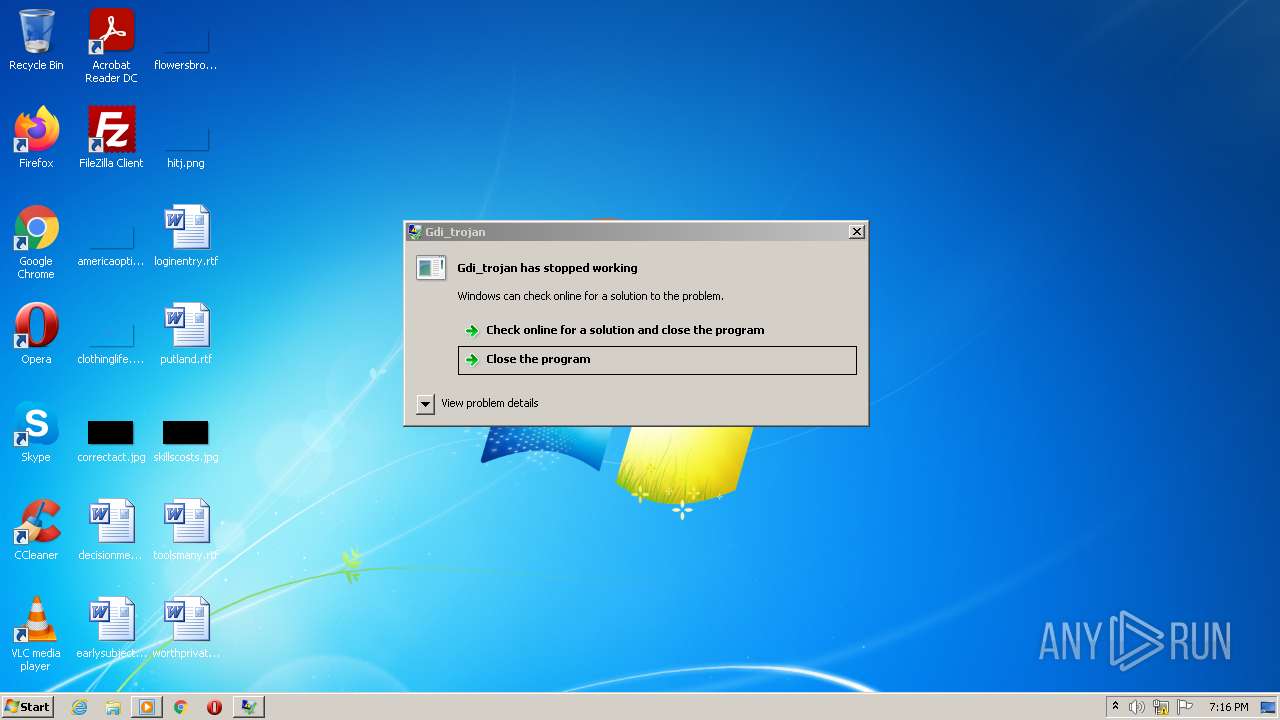
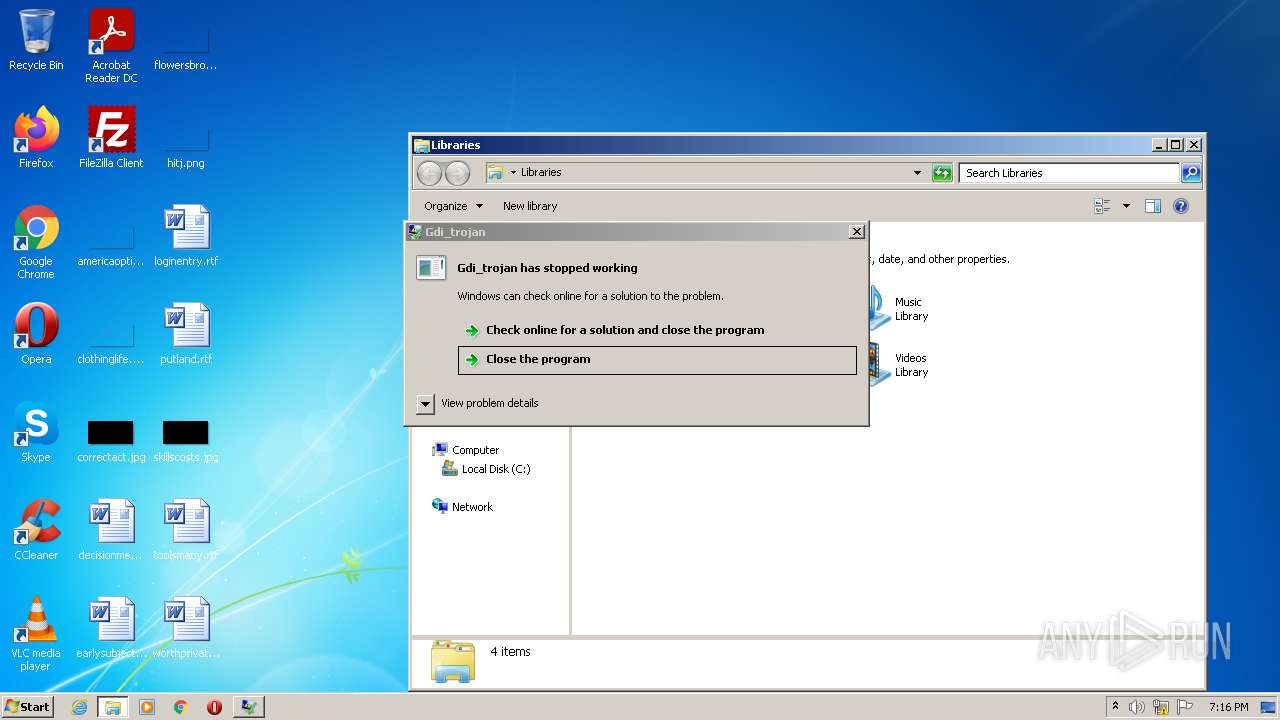
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: Gdi_trojan Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2492 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
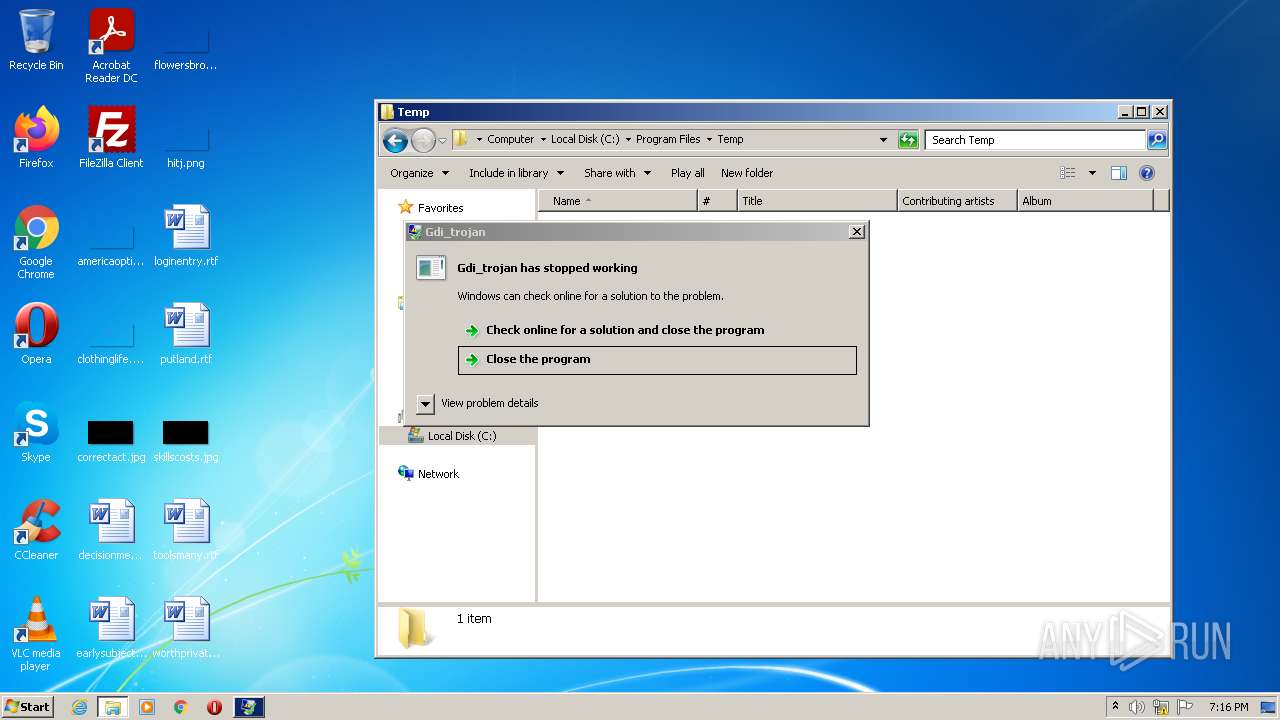
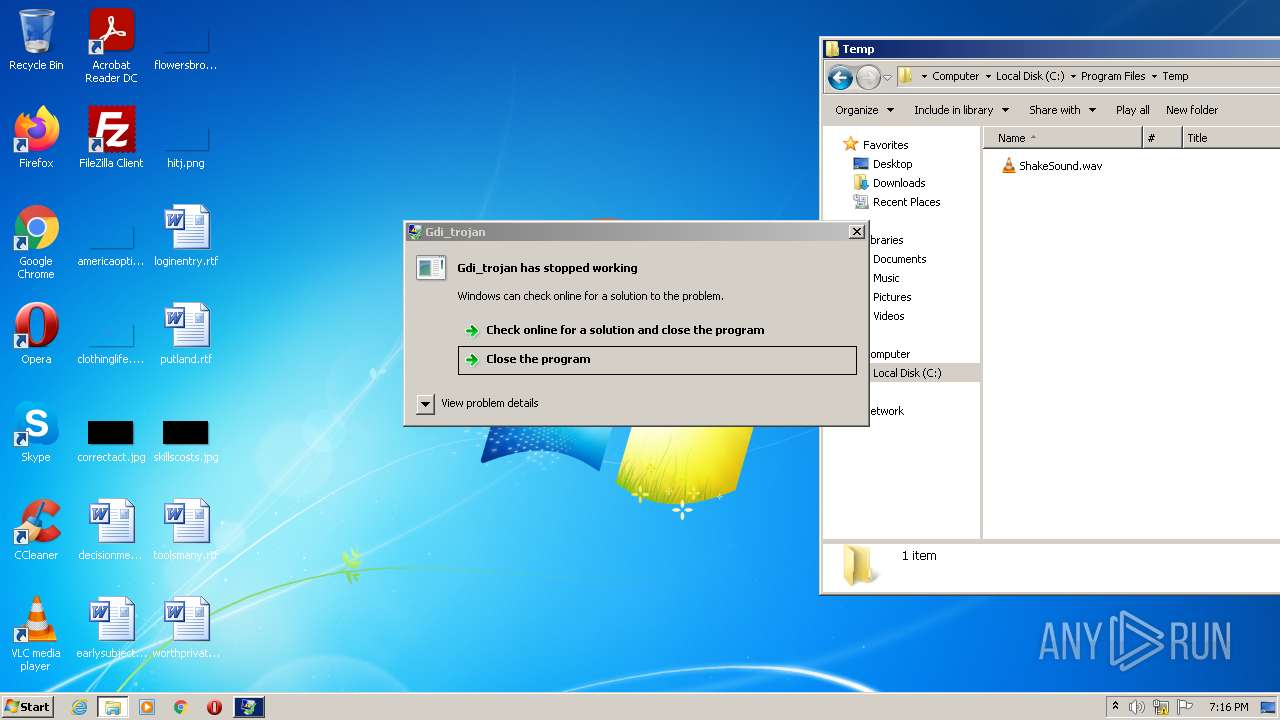
| 3164 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Program Files\Temp\ShakeSound.wav" | C:\Program Files\VideoLAN\VLC\vlc.exe | Explorer.EXE | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\Temp\Gdi_trojan.exe" | C:\Users\admin\AppData\Local\Temp\Gdi_trojan.exe | Explorer.EXE | ||||||||||||
User: admin Company: HP Inc. Integrity Level: HIGH Description: Gdi_trojan Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 146
Read events
5 146
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | Gdi_trojan.exe | C:\Program Files\Temp\ShakeSound.wav | wav | |
MD5:— | SHA256:— | |||
| 3164 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | ini | |
MD5:— | SHA256:— | |||
| 3164 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.Hp3164 | ini | |
MD5:— | SHA256:— | |||
| 3164 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:C045D870AD8B6D5AED597A7879735617 | SHA256:C63EC4412DEA506D3CA71885F9D8D637894BF5CDFB60401A59EF41E734088744 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|