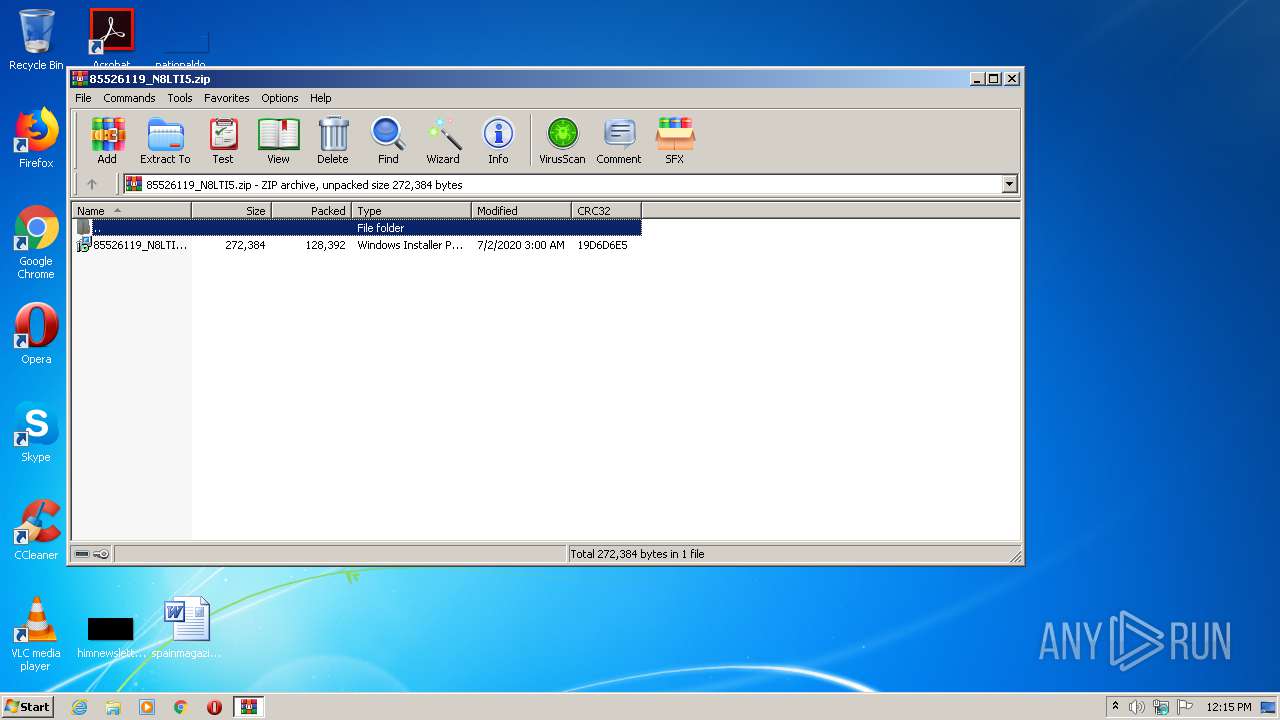
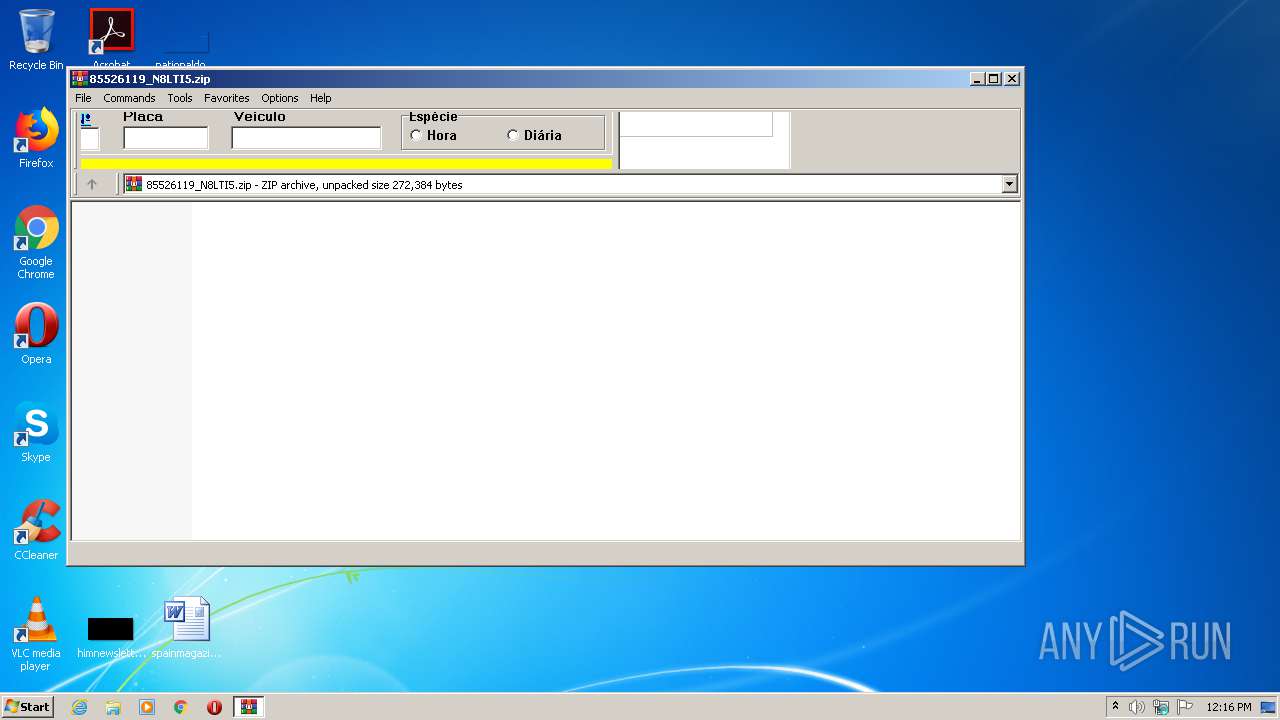
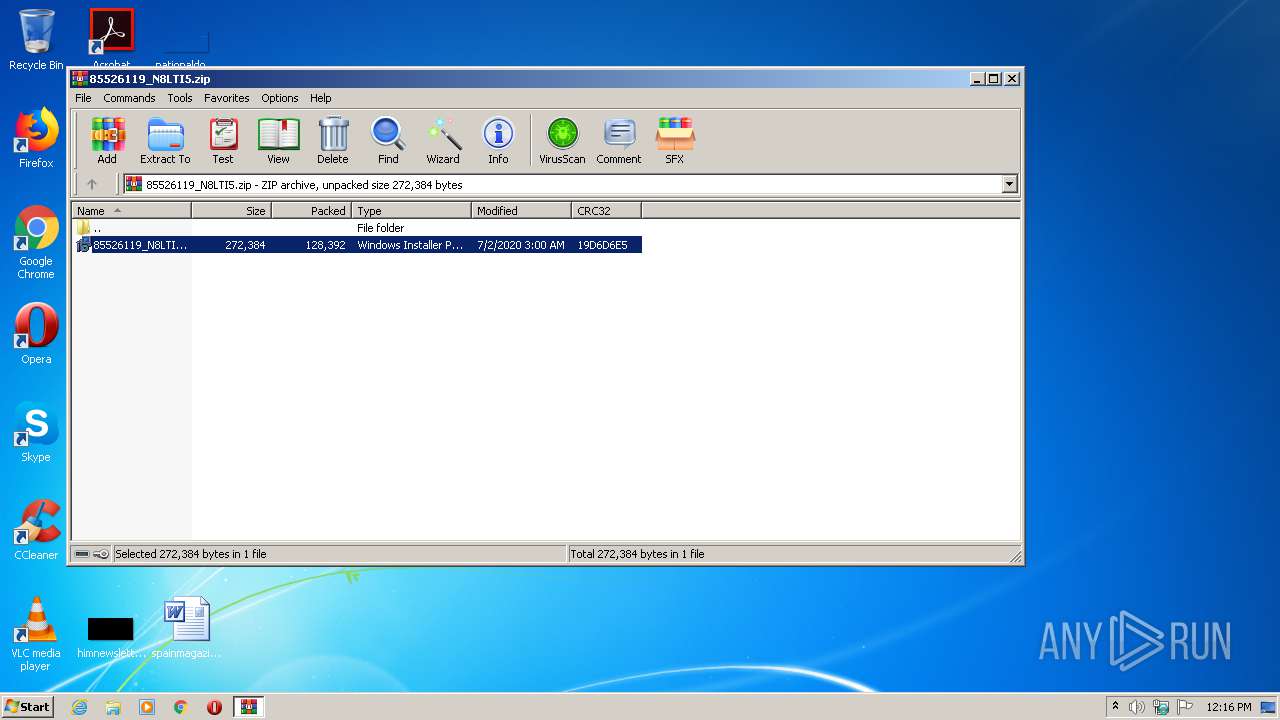
| File name: | 85526119_N8LTI5.zip |
| Full analysis: | https://app.any.run/tasks/5c210c13-817e-4377-beaf-50c2d6ca51d8 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 11:15:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | DC63384E8E107BA63DF99067EF0F852E |
| SHA1: | ABDC6983330B0D662557E0553AA8189691FB9AC6 |
| SHA256: | C1C052BA7A08751751BE4206A6DFCA6EF1DE8B11E2937233E11CC1A8EFB07C99 |
| SSDEEP: | 3072:MQts5LoHHFnK1EWaF/QC7eQeAjtsLYjv8HVHoIkIEaNBtxAS:M/+niEdZRe749jvs5kIZpxD |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3448)
- Host12_admin.exe (PID: 3992)
Changes the autorun value in the registry
- Host12_admin.exe (PID: 3992)
Application was dropped or rewritten from another process
- Host12_admin.exe (PID: 3992)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2016)
- msiexec.exe (PID: 2888)
- MsiExec.exe (PID: 1872)
Reads Internet Cache Settings
- MsiExec.exe (PID: 1872)
- Host12_admin.exe (PID: 3992)
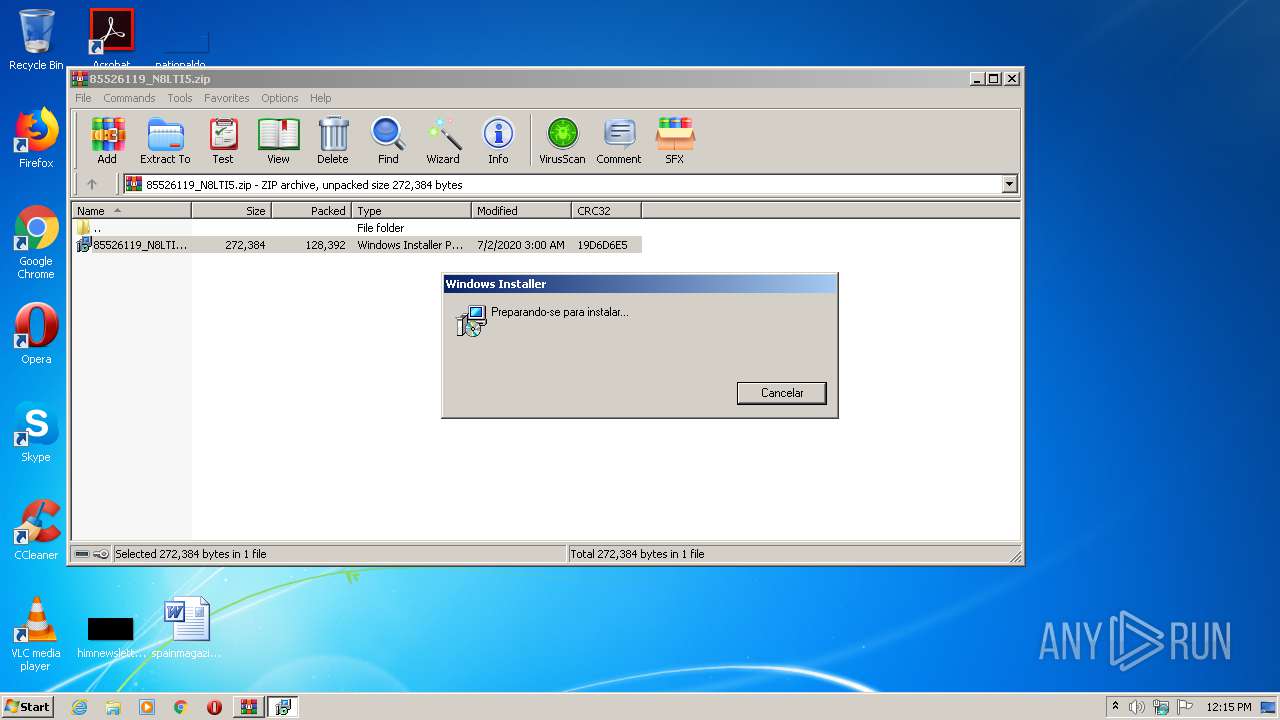
Starts Microsoft Installer
- WinRAR.exe (PID: 2016)
- cmd.exe (PID: 1516)
Creates files in the user directory
- Host12_admin.exe (PID: 3992)
Reads internet explorer settings
- Host12_admin.exe (PID: 3992)
Starts CMD.EXE for commands execution
- Host12_admin.exe (PID: 3992)
INFO
Application launched itself
- msiexec.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:02 03:00:13 |
| ZipCRC: | 0x19d6d6e5 |
| ZipCompressedSize: | 128392 |
| ZipUncompressedSize: | 272384 |
| ZipFileName: | 85526119_N8LTI5.msi |
Total processes
41
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa2016.38682\85526119_N8LTI5.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | C:\Windows\system32\MsiExec.exe -Embedding A122F55C6358D78174A781ABB6C0AA47 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Windows\System32\cmd.exe" /c msiexec.exe /i "C:\Users\admin\Videos\Gravacoes Ao Vivo\PURIP.msi" /qn | C:\Windows\System32\cmd.exe | — | Host12_admin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1872 | C:\Windows\system32\MsiExec.exe -Embedding CF4D4E15FC341C00A7242943D0B25251 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\85526119_N8LTI5.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2580 | msiexec.exe /i "C:\Users\admin\Videos\Gravacoes Ao Vivo\PURIP.msi" /qn | C:\Windows\system32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\Links\Origin Games\Host12_admin.exe" | C:\Users\admin\Links\Origin Games\Host12_admin.exe | MsiExec.exe | ||||||||||||
User: admin Company: Disc Soft Ltd Integrity Level: MEDIUM Description: Disc Soft Bus Service Pro Exit code: 0 Version: 8.3.0.0749 Modules
| |||||||||||||||
Total events
2 004
Read events
1 899
Write events
91
Delete events
14
Modification events
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\85526119_N8LTI5.zip | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2016) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
Executable files
7
Suspicious files
19
Text files
6
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | msiexec.exe | C:\Windows\Installer\MSI9378.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | msiexec.exe | C:\Windows\Installer\MSI93E6.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFFC92BF43EA1EF0AF.TMP | — | |
MD5:— | SHA256:— | |||
| 1872 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\Cab98E6.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\Tar98E7.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | msiexec.exe | C:\Windows\Installer\MSI9474.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | msiexec.exe | C:\Config.Msi\1092cf.rbs | — | |
MD5:— | SHA256:— | |||
| 2888 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFCFE5D07297556746.TMP | — | |
MD5:— | SHA256:— | |||
| 3992 | Host12_admin.exe | C:\Users\admin\AppData\Local\Temp\Cab2642.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | Host12_admin.exe | C:\Users\admin\AppData\Local\Temp\Tar2643.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3992 | Host12_admin.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDRWV%2BNyD7WkwIAAAAAbwew | US | der | 472 b | whitelisted |
3992 | Host12_admin.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3992 | Host12_admin.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDCBDbuX62tRAgAAAABvB68%3D | US | der | 471 b | whitelisted |
1872 | MsiExec.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEAeZSeYF37F3vDcS5eHtepU%3D | US | der | 471 b | whitelisted |
1872 | MsiExec.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3992 | Host12_admin.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEH4Q2QH3rAPNCAAAAABH744%3D | US | der | 471 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
3992 | Host12_admin.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDRWV%2BNyD7WkwIAAAAAbwew | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | MsiExec.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1872 | MsiExec.exe | 52.219.120.153:443 | 098093u369.s3-us-west-1.amazonaws.com | — | US | unknown |
3992 | Host12_admin.exe | 172.217.18.110:443 | sites.google.com | Google Inc. | US | whitelisted |
3992 | Host12_admin.exe | 52.219.120.201:443 | m309809369.s3-us-west-1.amazonaws.com | — | US | unknown |
3992 | Host12_admin.exe | 172.217.18.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3992 | Host12_admin.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3992 | Host12_admin.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
098093u369.s3-us-west-1.amazonaws.com |
| shared |
ocsp.digicert.com |
| whitelisted |
sites.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
claroweb.worse-than.tv |
| unknown |
m309809369.s3-us-west-1.amazonaws.com |
| unknown |