| URL: | http://ba41e084.amazzin.pw/iptv/HHBDAMMWAWBF84/522/index.m3u8 |
| Full analysis: | https://app.any.run/tasks/de34f1a0-8fa8-4f8f-aa8b-a0ce50e153b1 |
| Verdict: | No threats detected |
| Analysis date: | September 04, 2020, 05:51:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C501DC95E9840ECF2AE22601194A4057 |
| SHA1: | 81F4E1F2718BD490DB36B3C1BE3378B837F96996 |
| SHA256: | C1BE7F32C9869A8C9FD44D2742A895CF79A46C24F2EBD02BC194D219553877DB |
| SSDEEP: | 3:N1Kc4rd2BfKhSsyp0qUKMKd8WI:CcqeAzo0LXv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 2868)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2904)
Application launched itself
- chrome.exe (PID: 2984)
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Reads the hosts file
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x717fa9d0,0x717fa9e0,0x717fa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17699451879568151530 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14195421868897148656 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5831846267327758260 --mojo-platform-channel-handle=1180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15569432223452695860 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2992 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
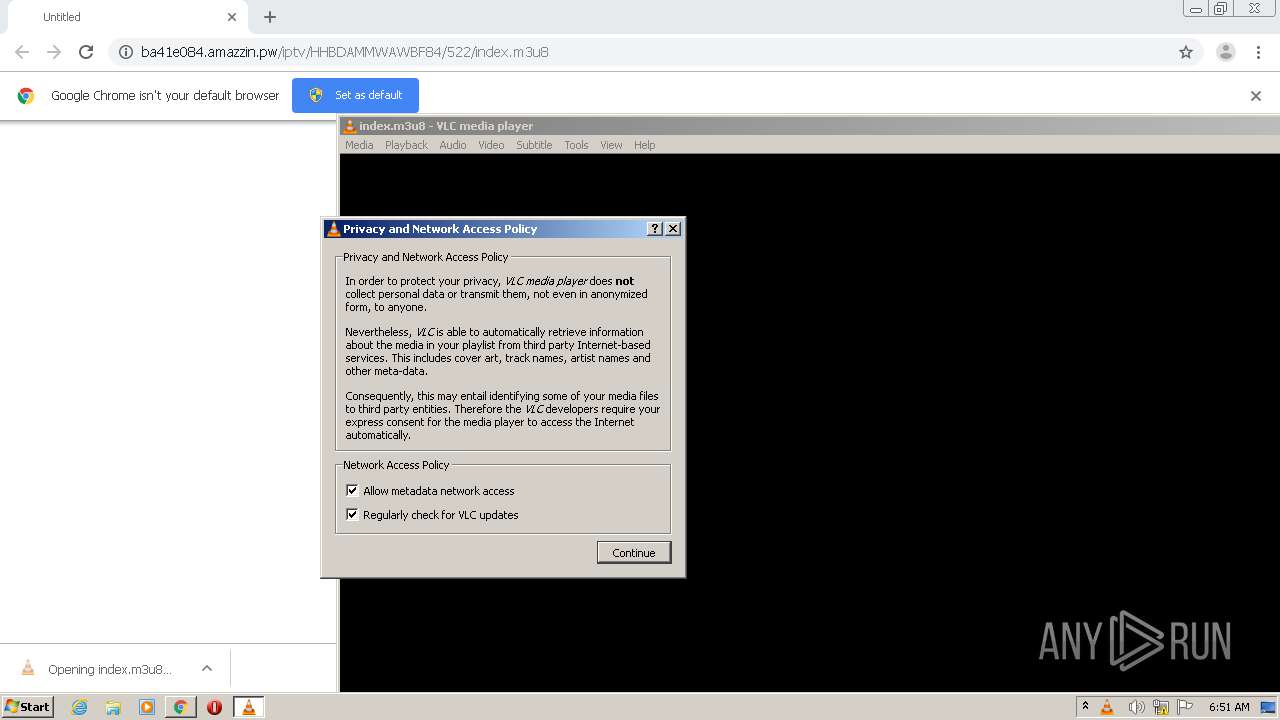
| 2868 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\Downloads\index.m3u8" | C:\Program Files\VideoLAN\VLC\vlc.exe | chrome.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13428229428292564157 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://ba41e084.amazzin.pw/iptv/HHBDAMMWAWBF84/522/index.m3u8" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4619344623571216825,10551964259328048694,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15069527166371044554 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 384
Read events
1 322
Write events
59
Delete events
3
Modification events
| (PID) Process: | (2828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13243672282140625 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
69
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e7737fcc-9f29-4e0b-bf4c-b5f8b007227f.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1934c2.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1934c2.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1936c5.TMP | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
10
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
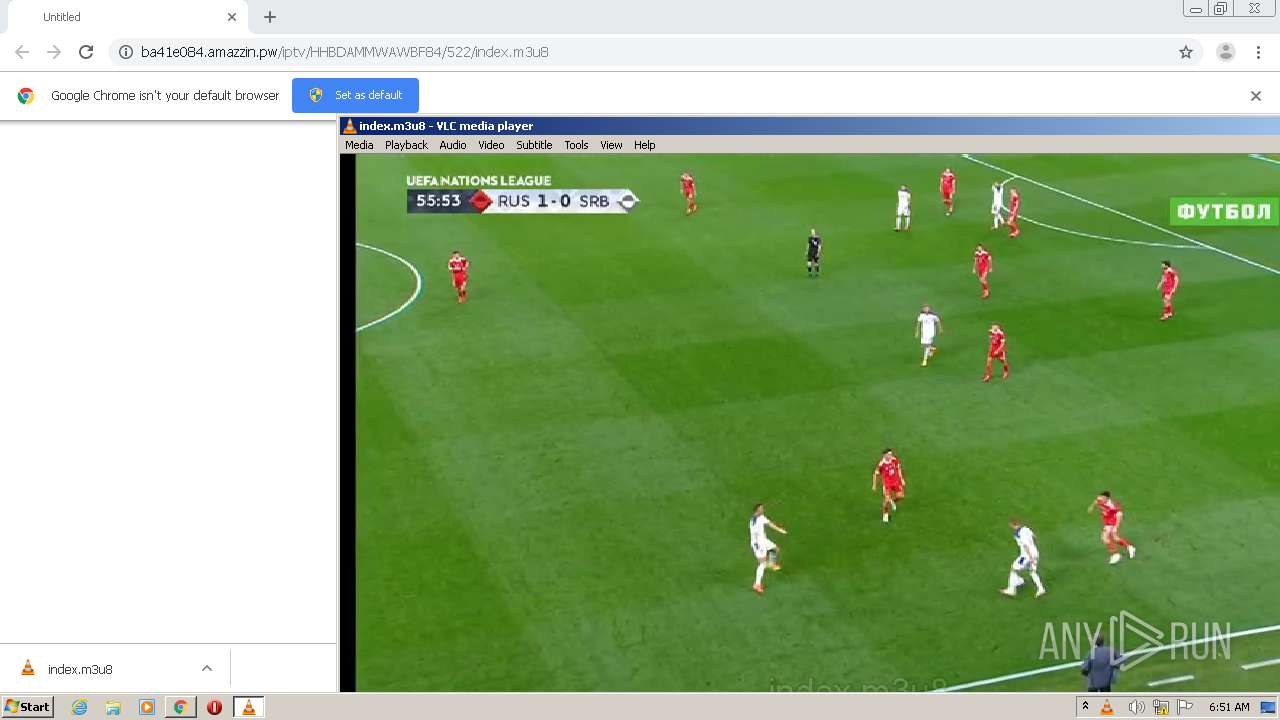
2868 | vlc.exe | GET | 206 | 213.226.69.82:80 | http://213.226.69.82/iptv/HHBDAMMWAWBF84/522/1599198563000.ts | unknown | ts | 2.09 Mb | unknown |
2904 | chrome.exe | GET | 200 | 51.15.191.15:80 | http://ba41e084.amazzin.pw/iptv/HHBDAMMWAWBF84/522/index.m3u8 | FR | text | 560 b | suspicious |
2868 | vlc.exe | GET | 206 | 93.189.60.90:80 | http://93.189.60.90/iptv/HHBDAMMWAWBF84/522/1599198543000.ts | DE | ts | 1.82 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 51.15.191.15:80 | ba41e084.amazzin.pw | Online S.a.s. | FR | suspicious |
2904 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2868 | vlc.exe | 93.189.60.90:80 | — | Melbikomas UAB | DE | unknown |
2868 | vlc.exe | 213.226.69.82:80 | — | — | — | unknown |
2868 | vlc.exe | 5.188.172.90:80 | — | Multiservice Networks Ltd. | RU | unknown |
— | — | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ba41e084.amazzin.pw |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2904 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2904 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | httplive stream: HTTP Live Streaming (/C:/Users/admin/Downloads/index.m3u8)
|
vlc.exe | ts demux: MPEG-4 descriptor not found for pid 0xdd type 0xf
|
vlc.exe | packetizer_mpeg4audio packetizer: AAC channels: 2 samplerate: 48000
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | httplive stream error: reloading playlist failed
|
vlc.exe | core stream error: cannot pre fill buffer
|
vlc.exe | core stream error: cannot pre fill buffer
|