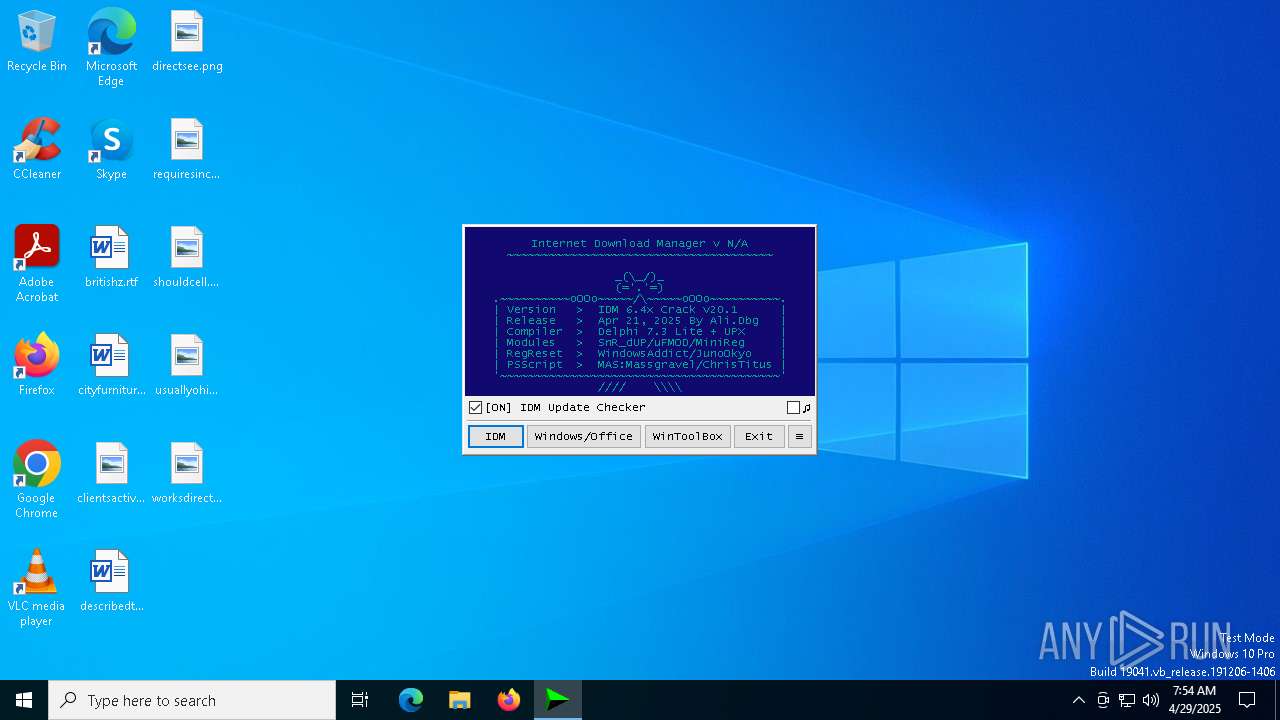
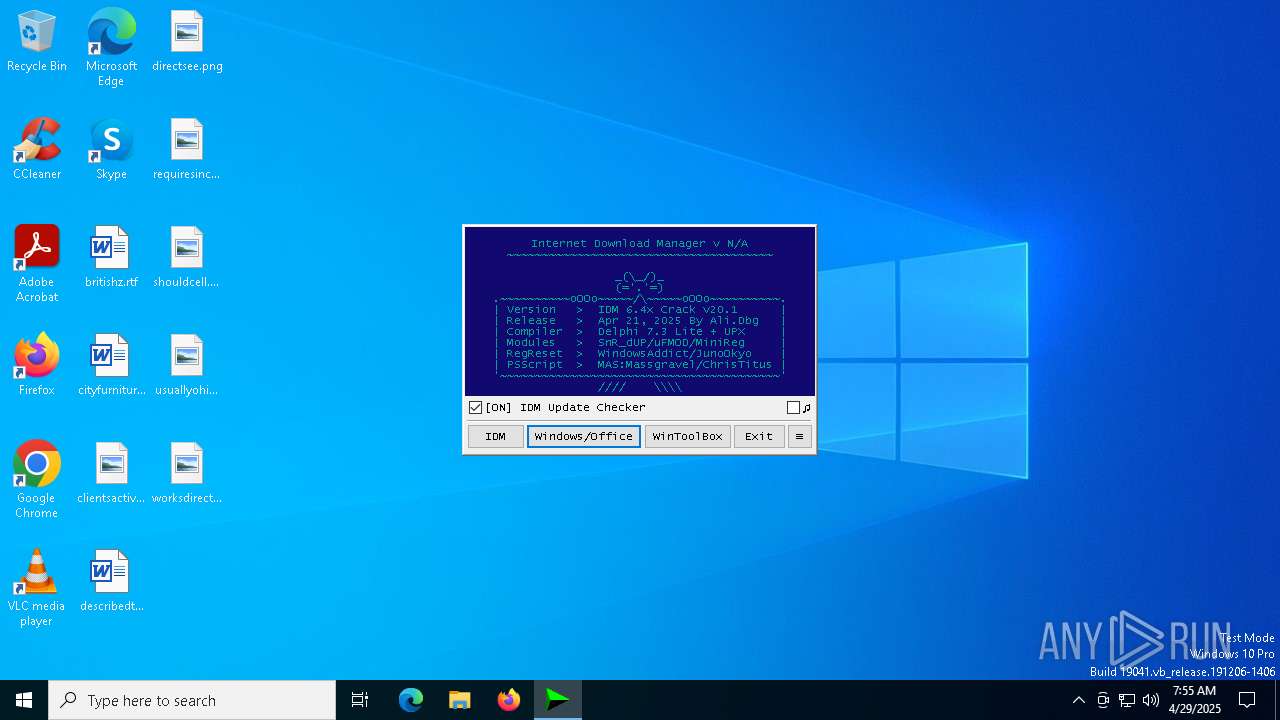
| File name: | IDM_6.4x_Crack_v20.1.exe |
| Full analysis: | https://app.any.run/tasks/0288bb2f-a11b-40af-90df-e7d5e2e6b0ca |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 07:54:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 832EAC4526E3E0C9A96EA29D90A5B521 |
| SHA1: | 8B89CC3C79310BCAEB3428A86C64AB609F1333F5 |
| SHA256: | C1BD821751C7F0ECD0741103EEF6888025F4509229E0C11F1CD436BF334AA240 |
| SSDEEP: | 1536:Se+j44X5OjRrmLlgOypw5JM8uaT3kDculsKdrX+UXaf+blAj:Se+04Xool46Lia/fKBXnq2blAj |
MALICIOUS
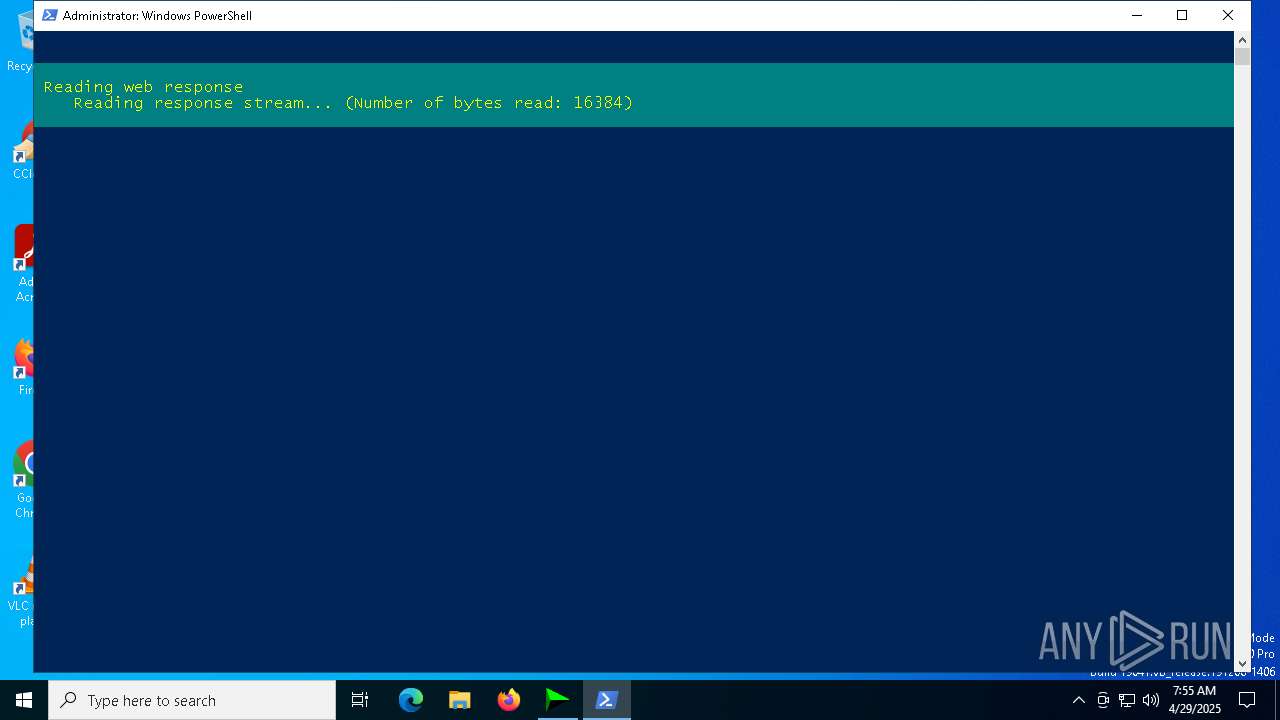
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1072)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1072)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1072)
Deletes a file (SCRIPT)
- wscript.exe (PID: 1072)
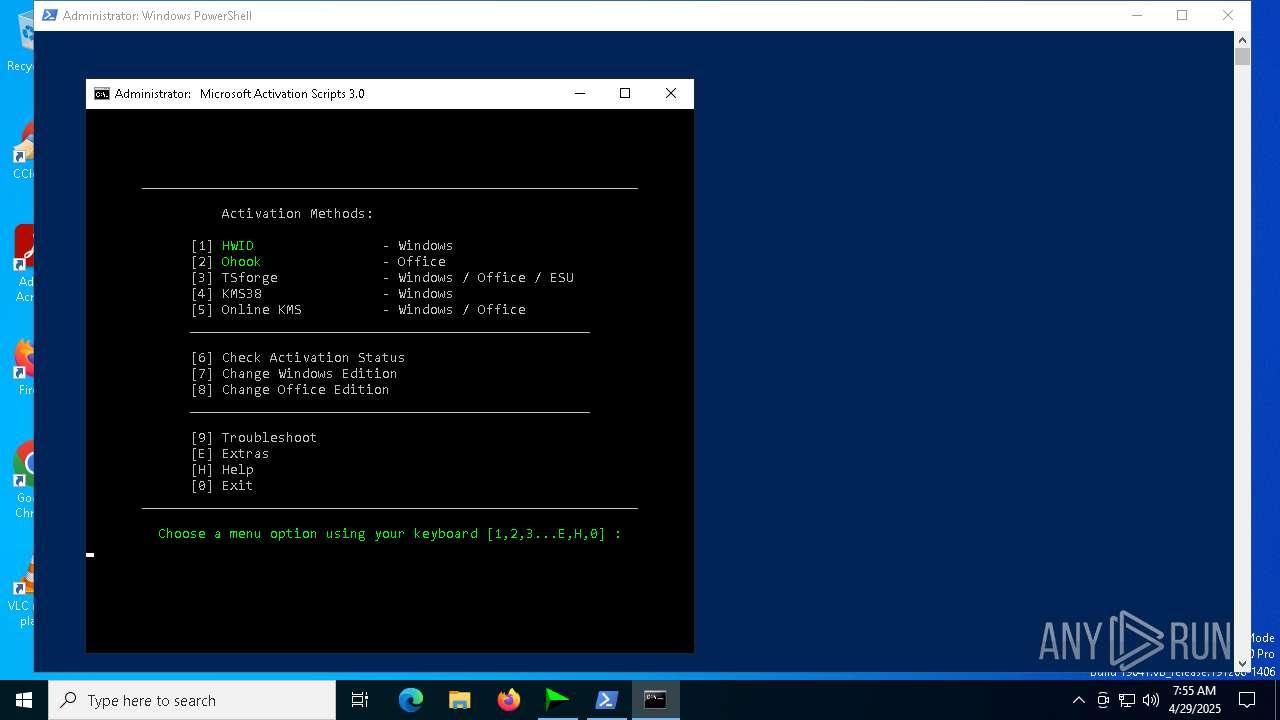
Bypass execution policy to execute commands
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5744)
Changes powershell execution policy (Bypass)
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 5744)
SUSPICIOUS
The process executes VB scripts
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1072)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 1072)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1072)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 1072)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 4756)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 4892)
- powershell.exe (PID: 4336)
- cmd.exe (PID: 664)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 6700)
- powershell.exe (PID: 6700)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 4728)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- cmd.exe (PID: 4756)
Application launched itself
- cmd.exe (PID: 4756)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 4728)
Hides command output
- cmd.exe (PID: 5352)
- cmd.exe (PID: 1348)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4756)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 1512)
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- cmd.exe (PID: 4652)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 4424)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4756)
- cmd.exe (PID: 4652)
- cmd.exe (PID: 2384)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4756)
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- cmd.exe (PID: 4652)
- cmd.exe (PID: 2384)
Starts application with an unusual extension
- cmd.exe (PID: 4756)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4336)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4336)
Executing commands from ".cmd" file
- powershell.exe (PID: 4336)
- cmd.exe (PID: 664)
- cmd.exe (PID: 6004)
- powershell.exe (PID: 6700)
- cmd.exe (PID: 4424)
Reads security settings of Internet Explorer
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Starts SC.EXE for service management
- cmd.exe (PID: 6004)
- cmd.exe (PID: 4424)
Windows service management via SC.EXE
- sc.exe (PID: 4424)
- sc.exe (PID: 1812)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6004)
- cmd.exe (PID: 4424)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 5744)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 5744)
INFO
Checks supported languages
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- chcp.com (PID: 5212)
- mode.com (PID: 5436)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
- reg.exe (PID: 856)
Reads the computer name
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Checks proxy server information
- wscript.exe (PID: 1072)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5744)
Checks operating system version
- cmd.exe (PID: 4756)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 4424)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 632)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Changes the display of characters in the console
- cmd.exe (PID: 4756)
Disables trace logs
- powershell.exe (PID: 4336)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 4464)
Process checks computer location settings
- IDM_6.4x_Crack_v20.1.exe (PID: 3300)
Starts MODE.COM to configure console settings
- mode.com (PID: 5436)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 61440 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 188416 |
| EntryPoint: | 0x3cf20 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
248
Monitored processes
121
Malicious processes
7
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\BATCLEN.bat') -split ':PowerShellTest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\WINDOWS\system32\cmd.exe" /c ""C:\WINDOWS\Temp\MAS_10581ed6-7d3b-44e8-8fc3-22b8b7e8af83.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | REG ADD "HKLM\Software\Internet Download Manager" /v "AdvIntDriverEnabled2" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Windows\Temp\MAS_10581ed6-7d3b-44e8-8fc3-22b8b7e8af83.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | reg export HKCU\Software\Classes\Wow6432Node\CLSID "C:\WINDOWS\Temp\_Backup_HKCU_CLSID_20250429-075515721.reg" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\CRK_UPDT.vbs" "https://idm.0dy.ir/" "Version" "Download_URL" "20.1" "Crack" "C:\Program Files\Google\Chrome\Application\chrome.exe" silent | C:\Windows\SysWOW64\wscript.exe | IDM_6.4x_Crack_v20.1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
59 149
Read events
59 090
Write events
44
Delete events
15
Modification events
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (3300) IDM_6.4x_Crack_v20.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
0
Suspicious files
11
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:F59D92D223CE737B95200A3D38C1EE3B | SHA256:A338479E0C1098B6FE3A807376157FD42FDE7427A8383C768846823AEC0CE892 | |||
| 3300 | IDM_6.4x_Crack_v20.1.exe | C:\Users\admin\AppData\Local\Temp\BATCLEN.bat | text | |
MD5:9FE22C4AD624881F8F0977CC7614346F | SHA256:12B47C1949CC555C2F68F9FD4677ED5266F25C4DA4630BEC36E303629B133225 | |||
| 856 | reg.exe | C:\Users\admin\AppData\Local\Temp\REG18D4.tmp | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
| 1072 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:1FBB37F79B317A9A248E7C4CE4F5BAC5 | SHA256:9BF639C595FE335B6F694EE35990BEFD2123F5E07FD1973FF619E3FC88F5F49F | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x21yra4a.qca.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1072 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4A90329071AE30B759D279CCA342B0A6 | SHA256:4F544379EDA8E2653F71472AB968AEFD6B5D1F4B3CE28A5EDB14196184ED3B60 | |||
| 1072 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\W52U2YQG.xml | text | |
MD5:21A5285AE43EDD57EB010DBAA5E01AD1 | SHA256:E2346FA47B5BE1883B01FA3764F618C2DCA0AC1765BAA75506433A7532C764A5 | |||
| 4880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n3ybip0f.hx4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_14sbq33b.fws.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 632 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4434896CEEE521CC551DF7725295C0CA | SHA256:904F0E10C2D80FF38B2936FBC558AC698AA0FB72E2FE3B93E66A76CF2B882EE1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
28
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
5228 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
1072 | wscript.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1072 | wscript.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
5228 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1072 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
1072 | wscript.exe | 142.250.184.195:80 | c.pki.goog | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
idm.0dy.ir |
| unknown |
c.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |