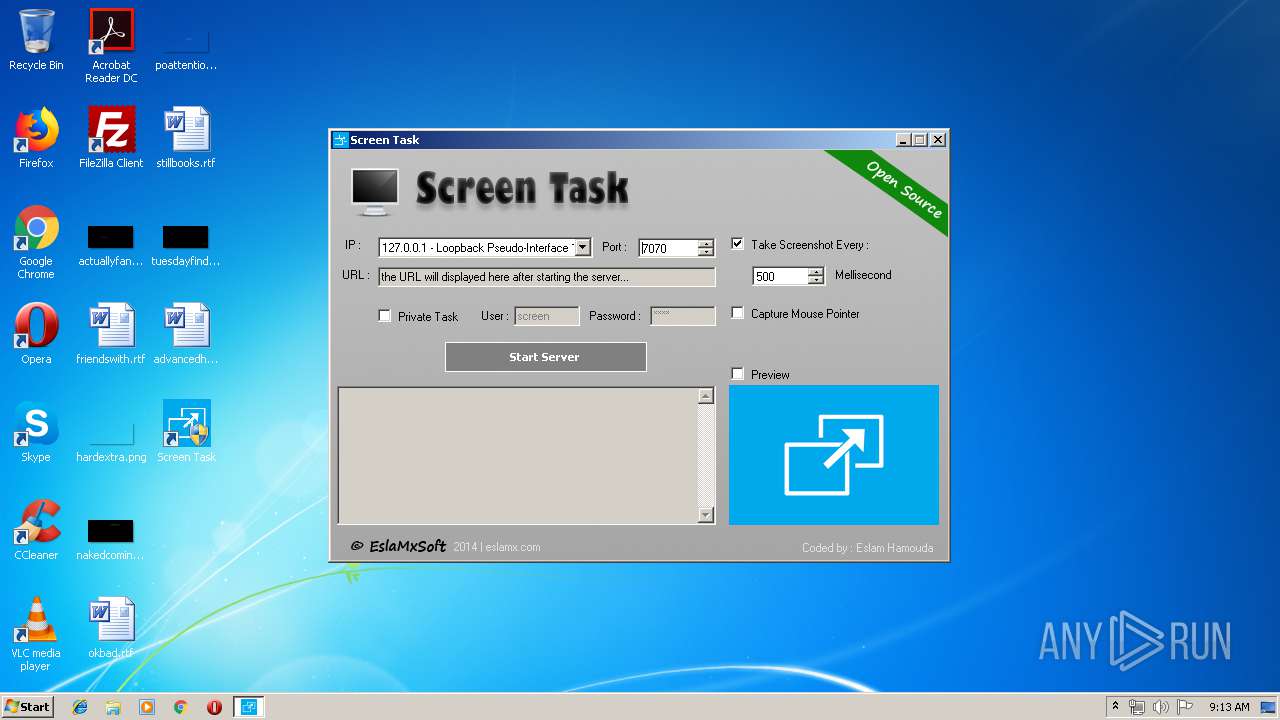
| File name: | ScreenTaskInstaller.exe |
| Full analysis: | https://app.any.run/tasks/7cb6a40a-fe8a-46cc-8aa3-8ce22ee7acc4 |
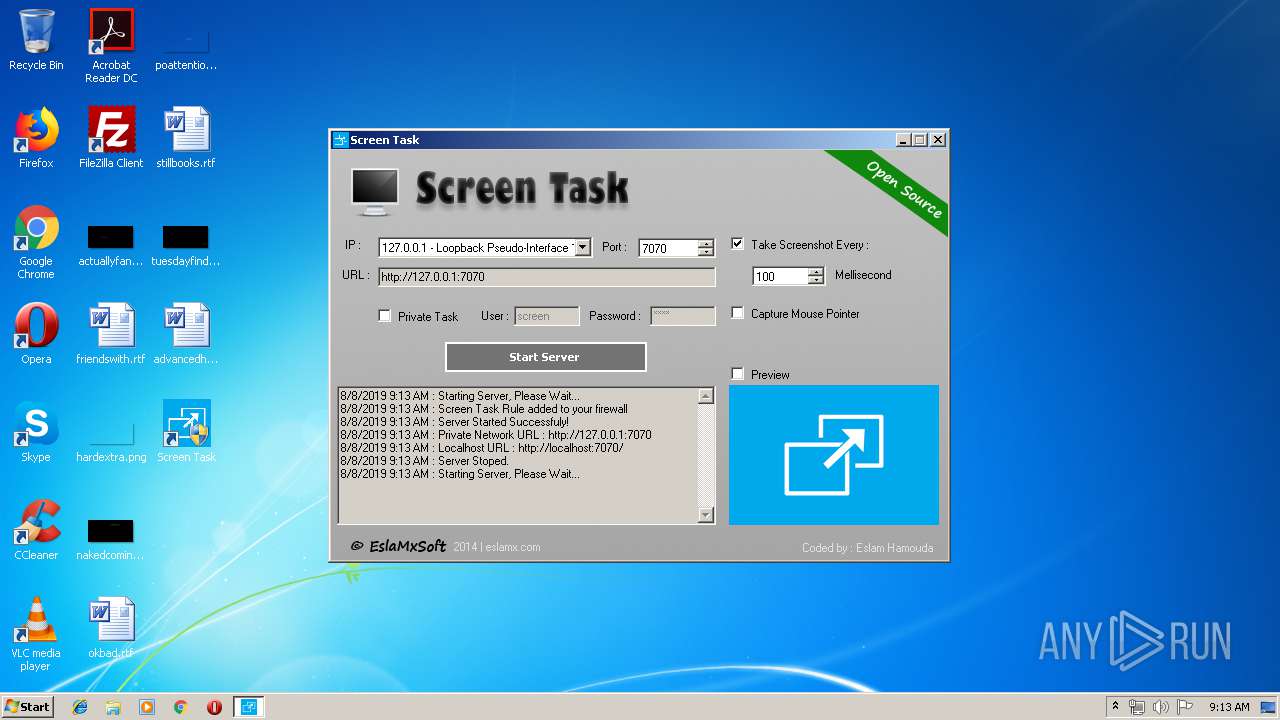
| Verdict: | Suspicious activity |
| Analysis date: | August 08, 2019, 08:12:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BE8582EC2A60E27994CB04252477A3D2 |
| SHA1: | CF6E27D45354300197B00CBC084E83D3014138B2 |
| SHA256: | C1B706B2E4E5CB978B157FFB6912A13ECA842EA019B84C64CA55C1DCB95CED00 |
| SSDEEP: | 6144:rif5xWIalUaE5rmyq/YJbrfGHZbn0KVMIni/7:s5xWIag5BAkbrWb7A7 |
MALICIOUS
Application was dropped or rewritten from another process
- ScreenTask.exe (PID: 3572)
SUSPICIOUS
Creates files in the program directory
- ScreenTaskInstaller.exe (PID: 1672)
- ScreenTask.exe (PID: 3572)
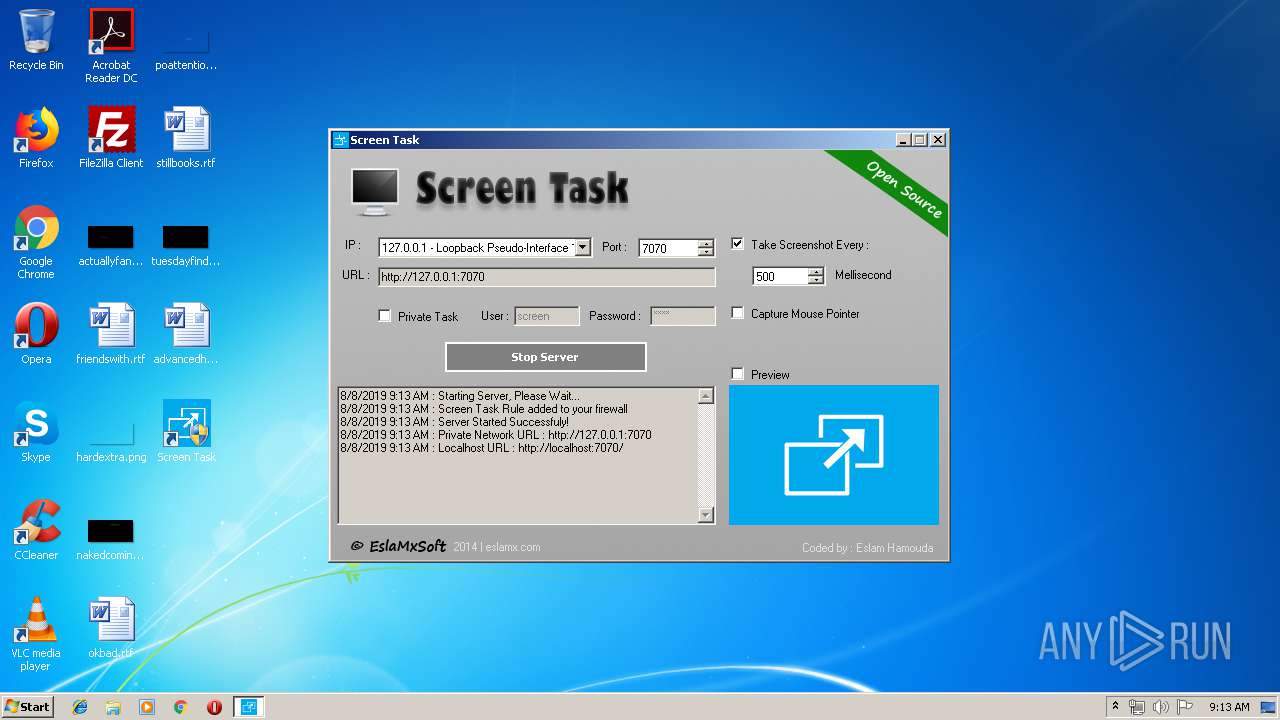
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 1928)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 3916)
Starts CMD.EXE for commands execution
- ScreenTask.exe (PID: 3572)
Application launched itself
- ScreenTaskInstaller.exe (PID: 2568)
Executable content was dropped or overwritten
- ScreenTaskInstaller.exe (PID: 1672)
Creates files in the user directory
- ScreenTaskInstaller.exe (PID: 1672)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:22 15:00:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 100352 |
| InitializedDataSize: | 102912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1085f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-2013 13:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Aug-2013 13:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001876A | 0x00018800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64352 |
.rdata | 0x0001A000 | 0x00004533 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.31676 |
.data | 0x0001F000 | 0x0002FE28 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.34267 |
.rsrc | 0x0004F000 | 0x0001399C | 0x00013A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.45858 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.18906 | 536 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 2.95673 | 288 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.77928 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.66523 | 162 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
13
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | netsh advfirewall firewall delete rule name="Screen Task" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\ScreenTaskInstaller.exe" -el -s2 "-dC:\Program Files\ScreenTask" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\ScreenTaskInstaller.exe | ScreenTaskInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1864 | netsh advfirewall firewall add rule name="Screen Task" dir=in action=allow remoteip=localsubnet protocol=tcp localport=7070 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "cmd.exe" /C netsh advfirewall firewall add rule name="Screen Task" dir=in action=allow remoteip=localsubnet protocol=tcp localport=7070 | C:\Windows\system32\cmd.exe | — | ScreenTask.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1928 | "cmd.exe" /C netsh advfirewall firewall show rule "Screen Task" | C:\Windows\system32\cmd.exe | — | ScreenTask.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2320 | "cmd.exe" /C netsh advfirewall firewall delete rule name="Screen Task" | C:\Windows\system32\cmd.exe | — | ScreenTask.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2376 | netsh advfirewall firewall add rule name="Screen Task" dir=in action=allow remoteip=localsubnet protocol=tcp localport=7070 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | netsh advfirewall firewall show rule "Screen Task" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\ScreenTaskInstaller.exe" | C:\Users\admin\AppData\Local\Temp\ScreenTaskInstaller.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2716 | "cmd.exe" /C netsh advfirewall firewall show rule "Screen Task" | C:\Windows\system32\cmd.exe | — | ScreenTask.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
805
Read events
571
Write events
234
Delete events
0
Modification events
| (PID) Process: | (2568) ScreenTaskInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2568) ScreenTaskInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1672) ScreenTaskInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1672) ScreenTaskInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1864) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2396) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2396) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2396) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2396) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2396) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
Executable files
1
Suspicious files
0
Text files
32
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1672 | ScreenTaskInstaller.exe | C:\Program Files\ScreenTask\ScreenTask.exe | executable | |
MD5:— | SHA256:— | |||
| 3572 | ScreenTask.exe | C:\Program Files\ScreenTask\WebServer\ScreenTask.jpg | image | |
MD5:— | SHA256:— | |||
| 1672 | ScreenTaskInstaller.exe | C:\Users\admin\Desktop\Screen Task.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1672 | ScreenTaskInstaller.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Screen Task.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1672 | ScreenTaskInstaller.exe | C:\Program Files\ScreenTask\WebServer\bootstrap.min.css | text | |
MD5:35FC838CE584C1EB81B3BEBE245442D6 | SHA256:46A2DE362F54E3C988CC8C9FBF68FE12018C8AE42FE11509A747F52F17834466 | |||
| 1672 | ScreenTaskInstaller.exe | C:\Program Files\ScreenTask\WebServer\index.html | html | |
MD5:B2C5198E847CC12C3A92E16249880FA0 | SHA256:6FDDB7D3A9797D1CE1CC38CDC6EEFF140601CC8D4D8AF526F7BD5BC91F206AFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report