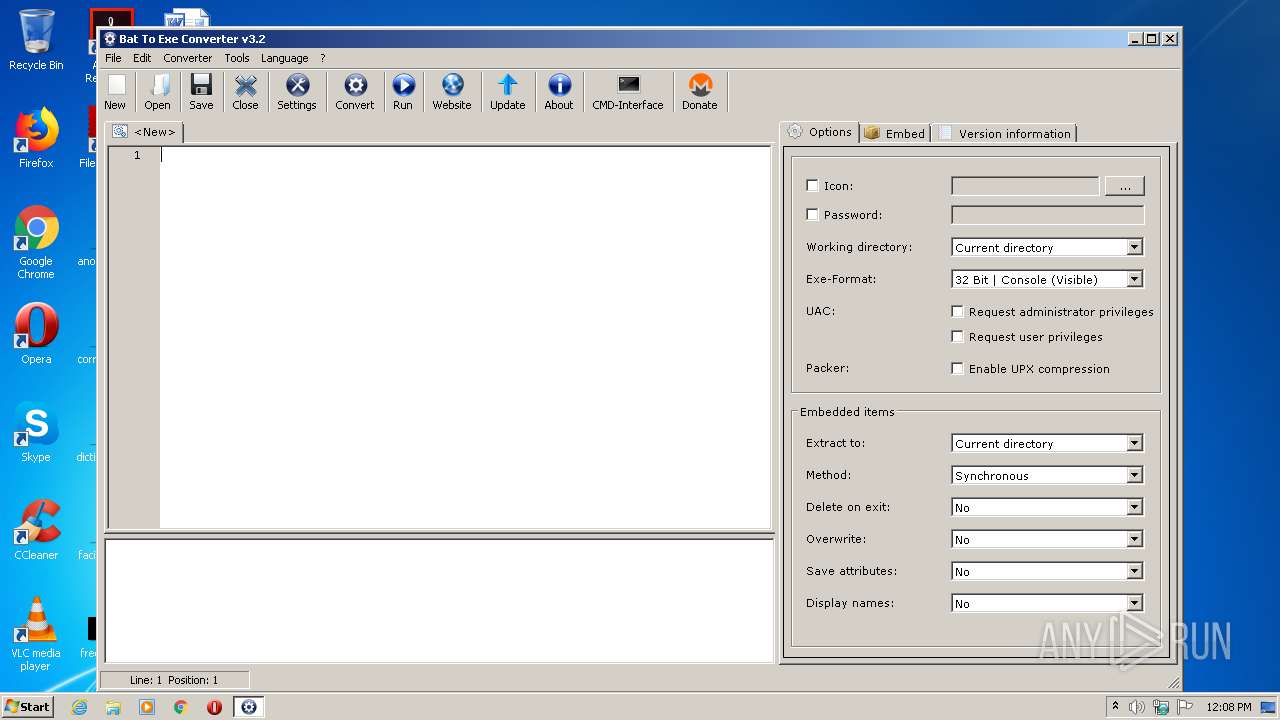
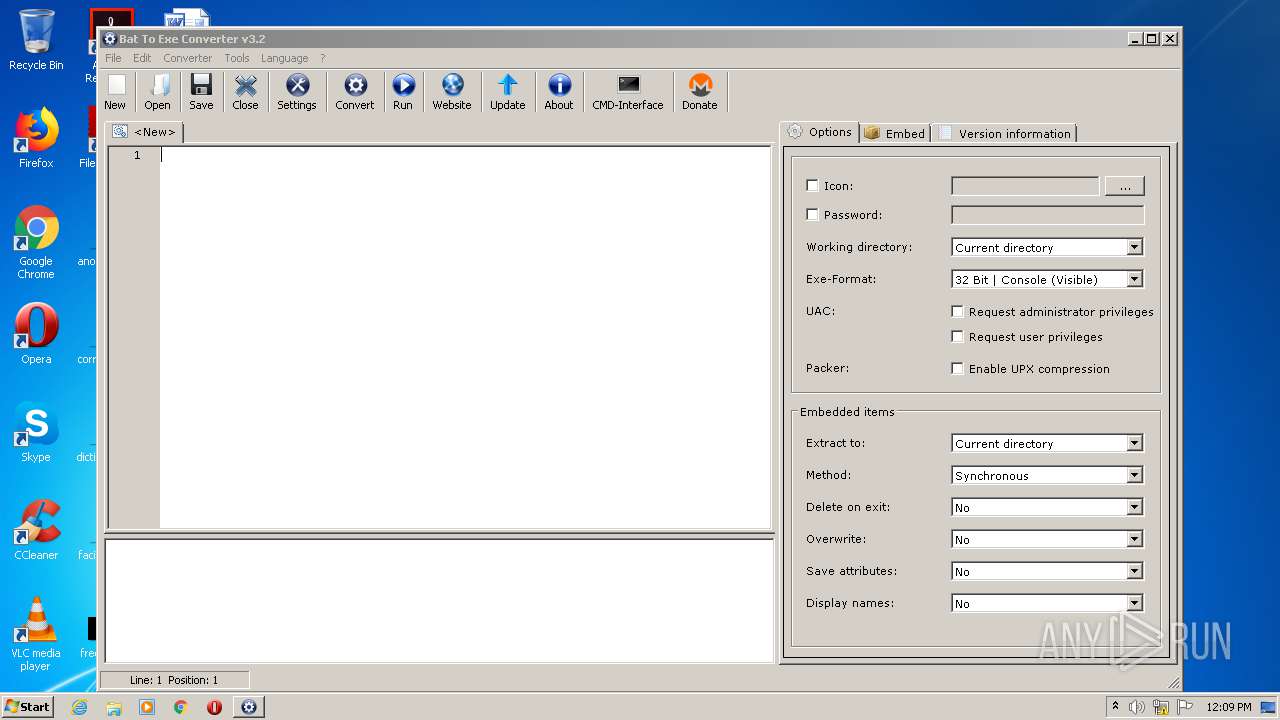
| File name: | Bat_To_Exe_Converter.exe |
| Full analysis: | https://app.any.run/tasks/2038a9ce-fb8e-4f33-9c09-f55ff12d04f5 |
| Verdict: | No threats detected |
| Analysis date: | August 22, 2020, 11:08:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 26FFE682B08C40C670D804DFED55B626 |
| SHA1: | A07D6372BF6DB8C75390797BCB3BA807C9FB41B8 |
| SHA256: | C1B41613A6DF623C253EA32C66C0253B20D18EB5BE53659B7F0C1707B4166B7A |
| SSDEEP: | 49152:juqeFfoAaZpyLY3NSNV80Lkcddb2lQwmnIV+9ugs:DeFfoAaZaYYNF4B9eugs |
MALICIOUS
Loads dropped or rewritten executable
- Bat_To_Exe_Converter.exe (PID: 2888)
SUSPICIOUS
Executable content was dropped or overwritten
- Bat_To_Exe_Converter.exe (PID: 2888)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 2916)
INFO
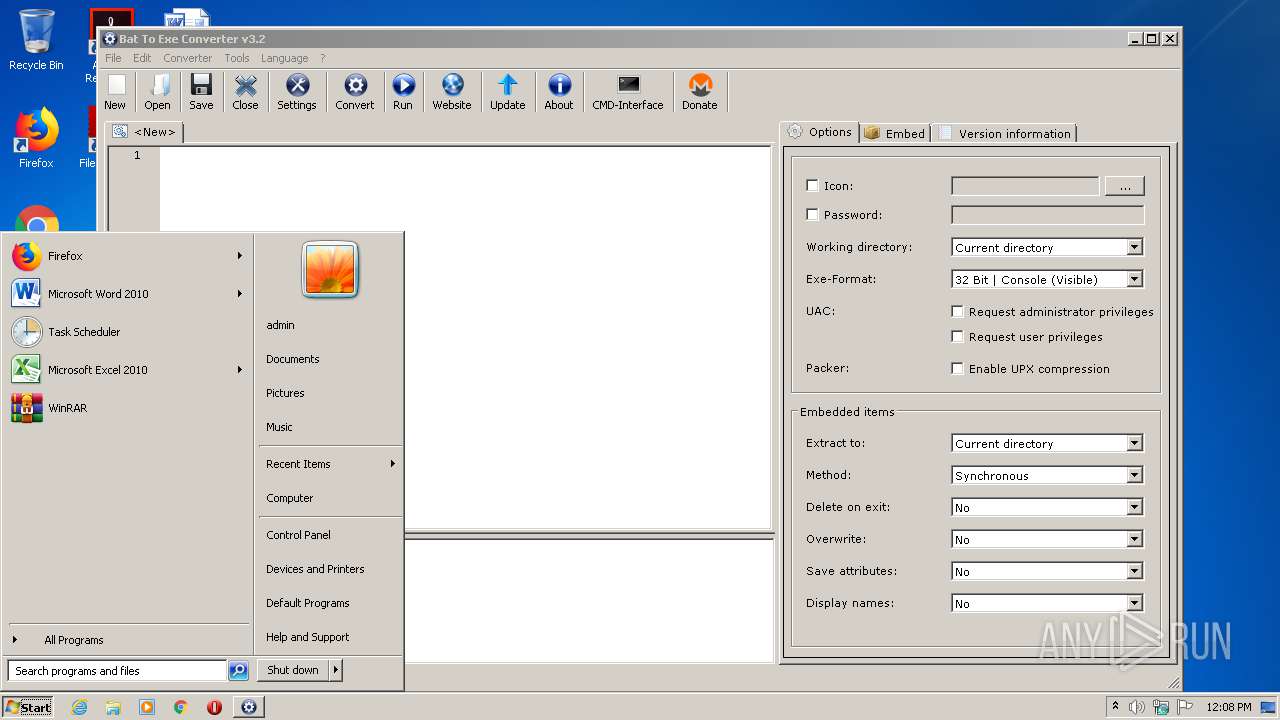
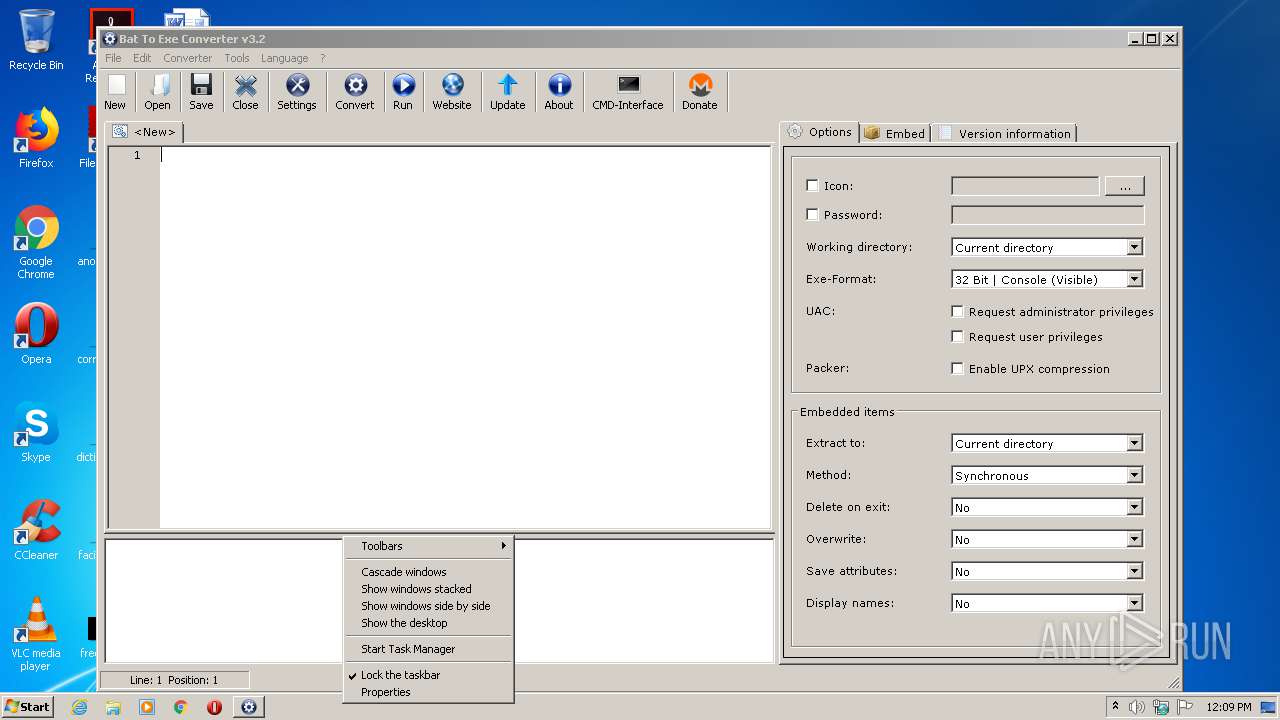
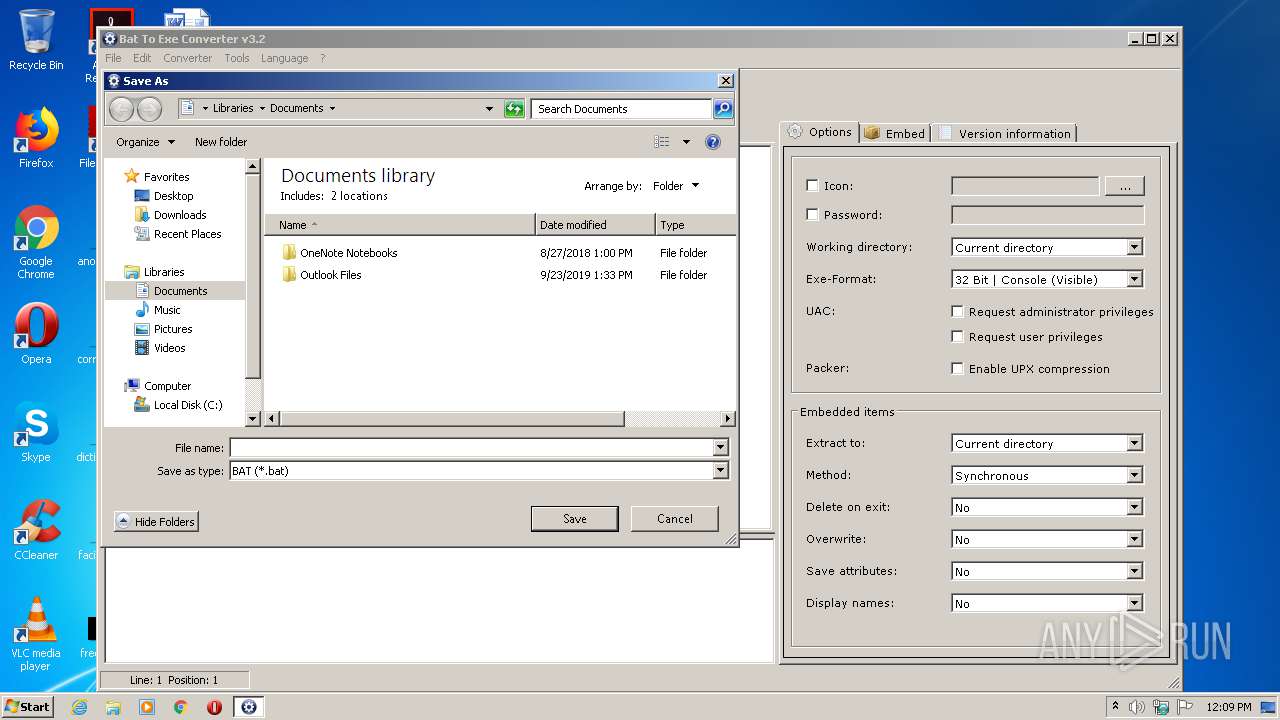
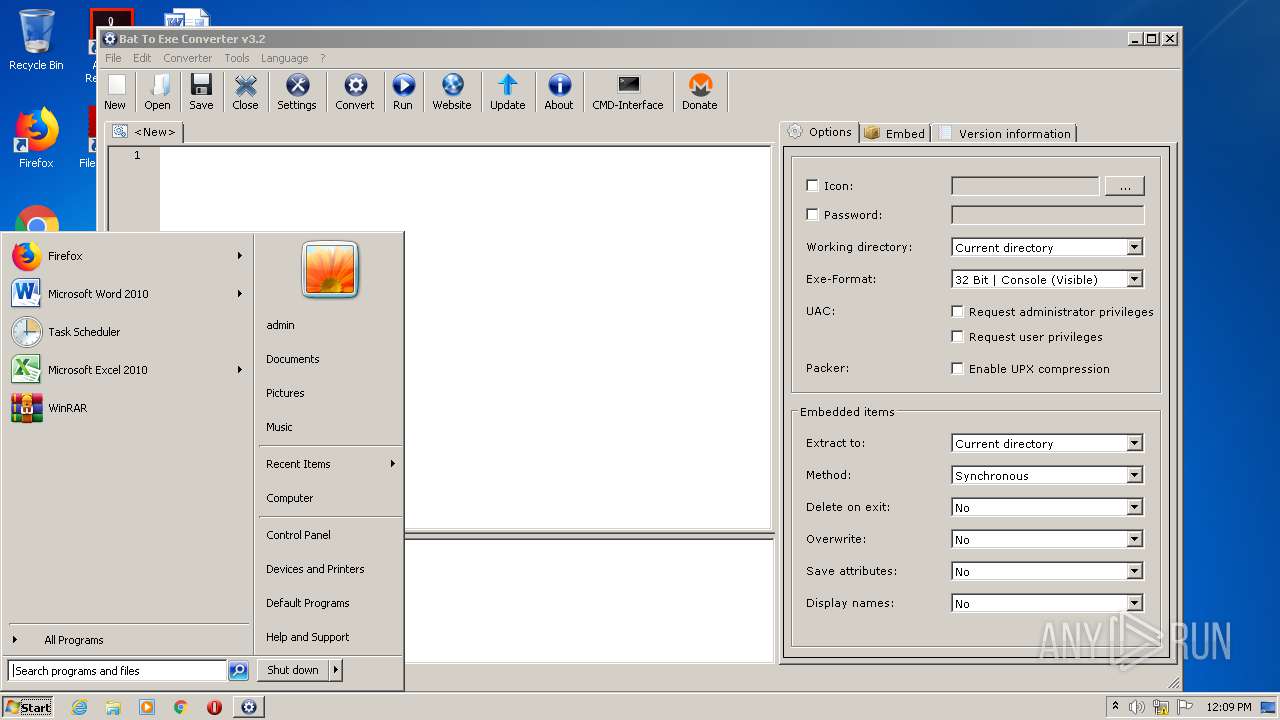
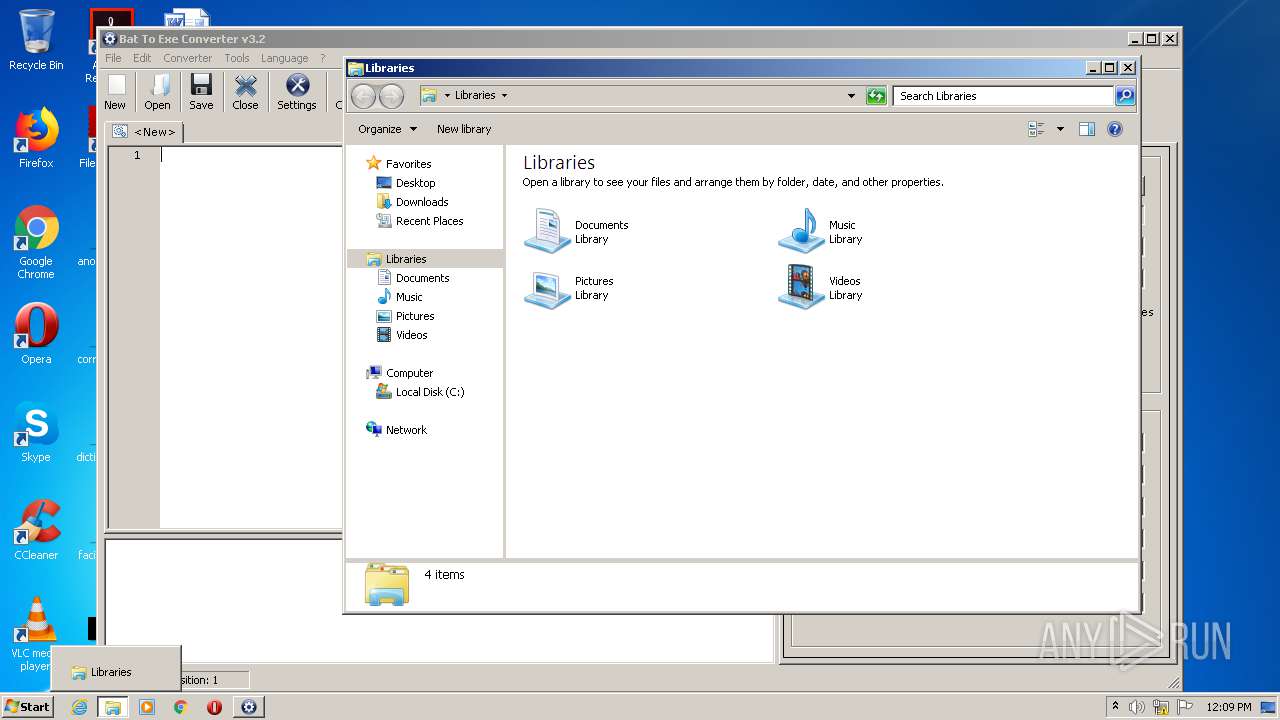
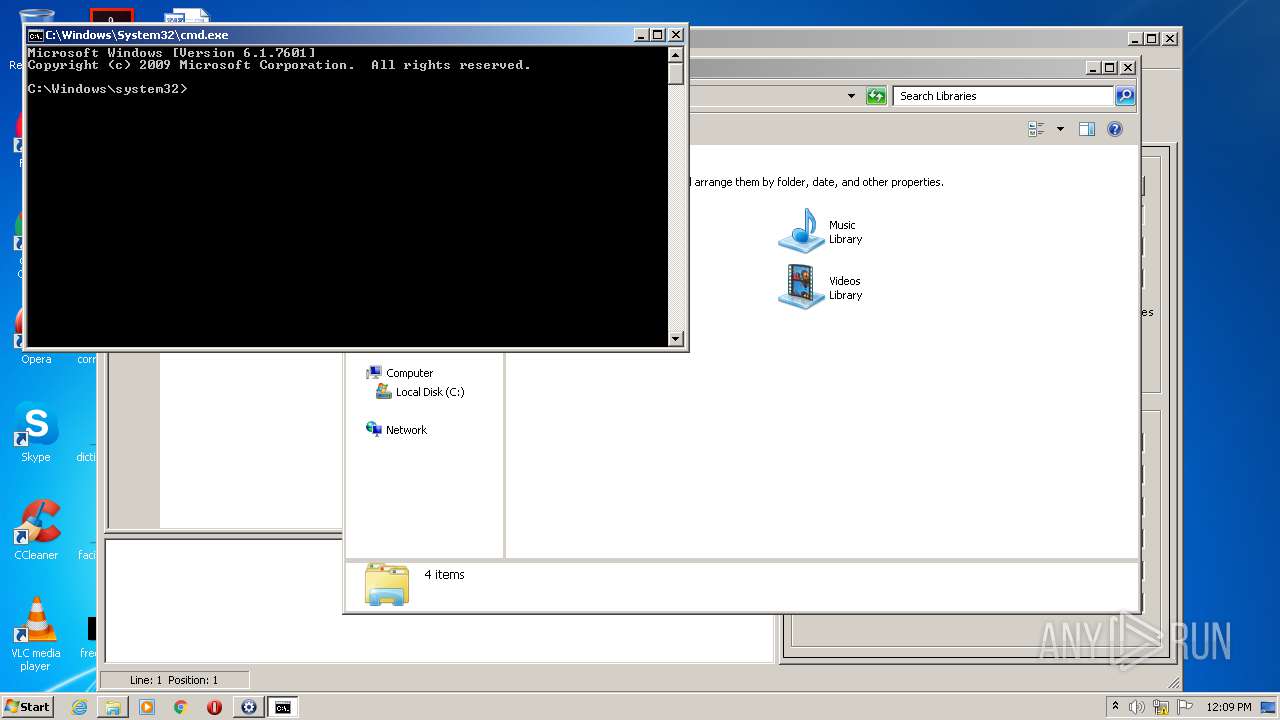
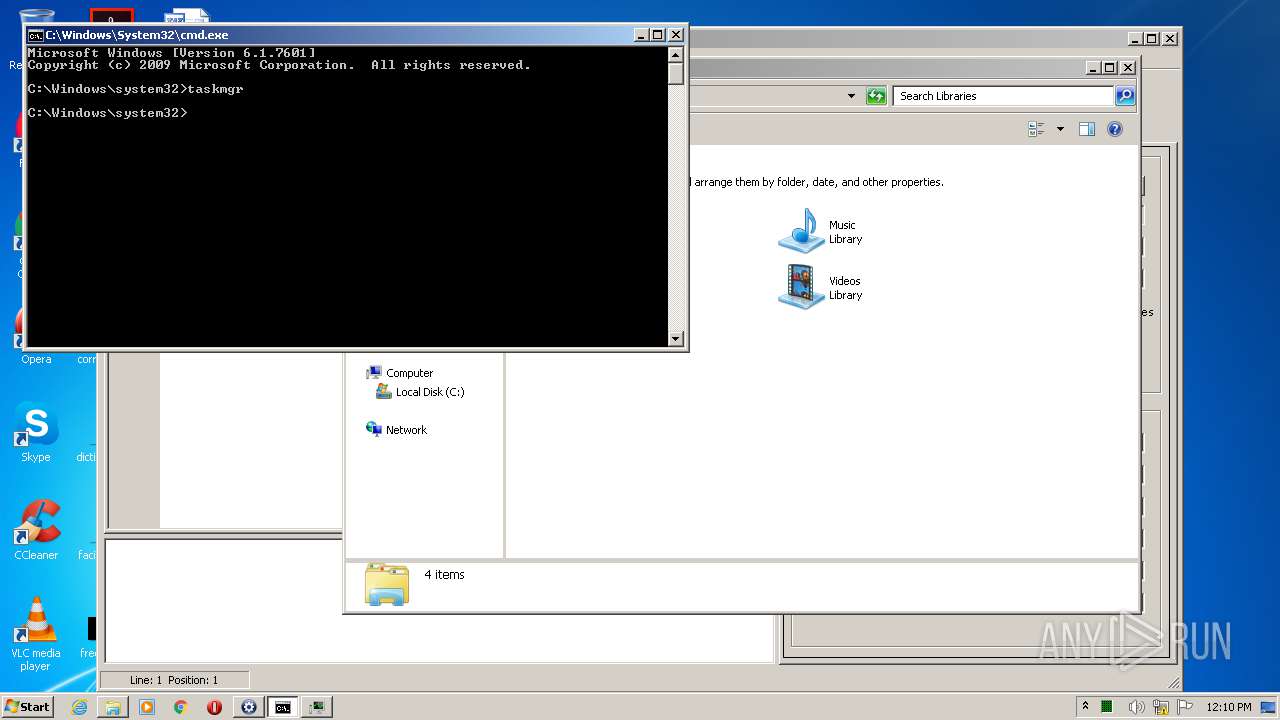
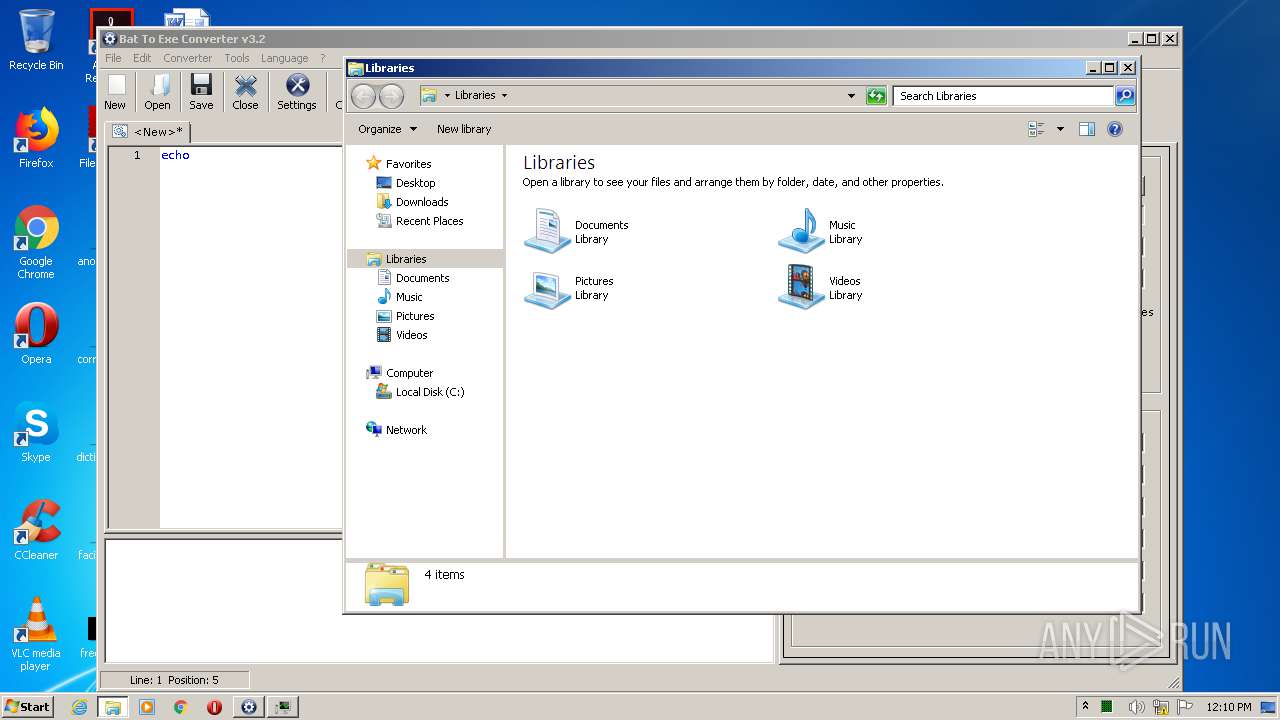
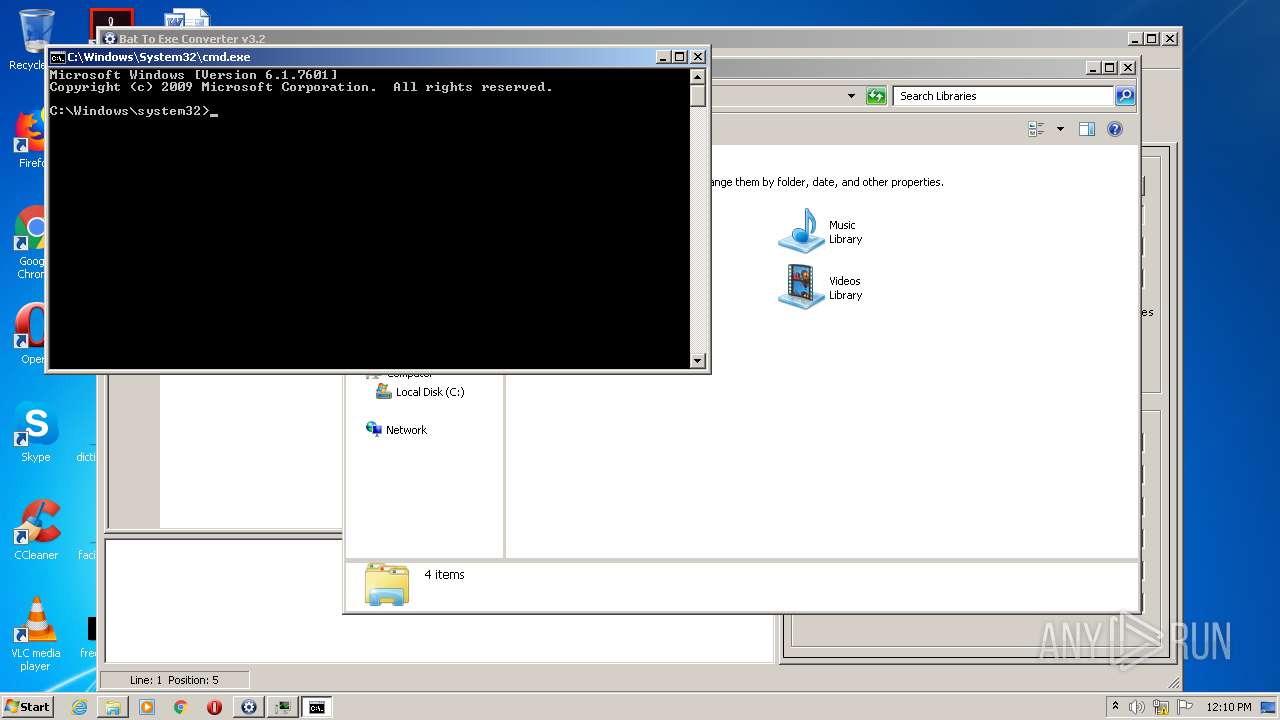
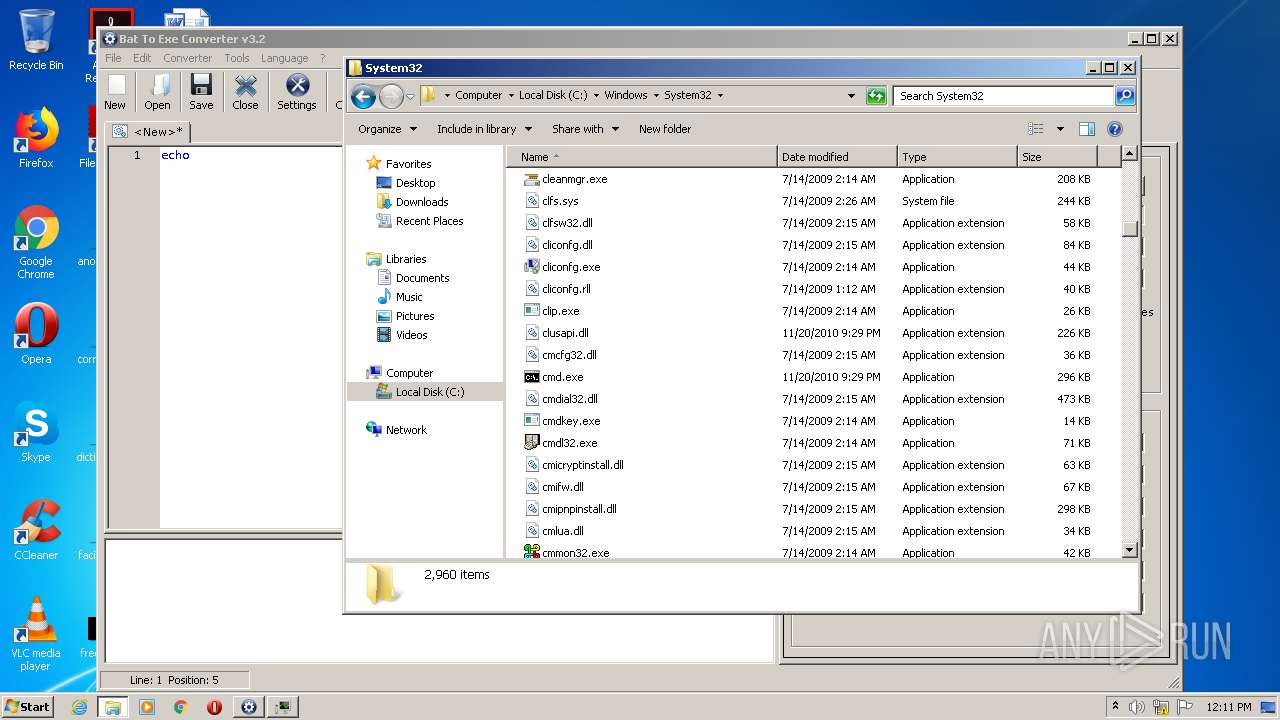
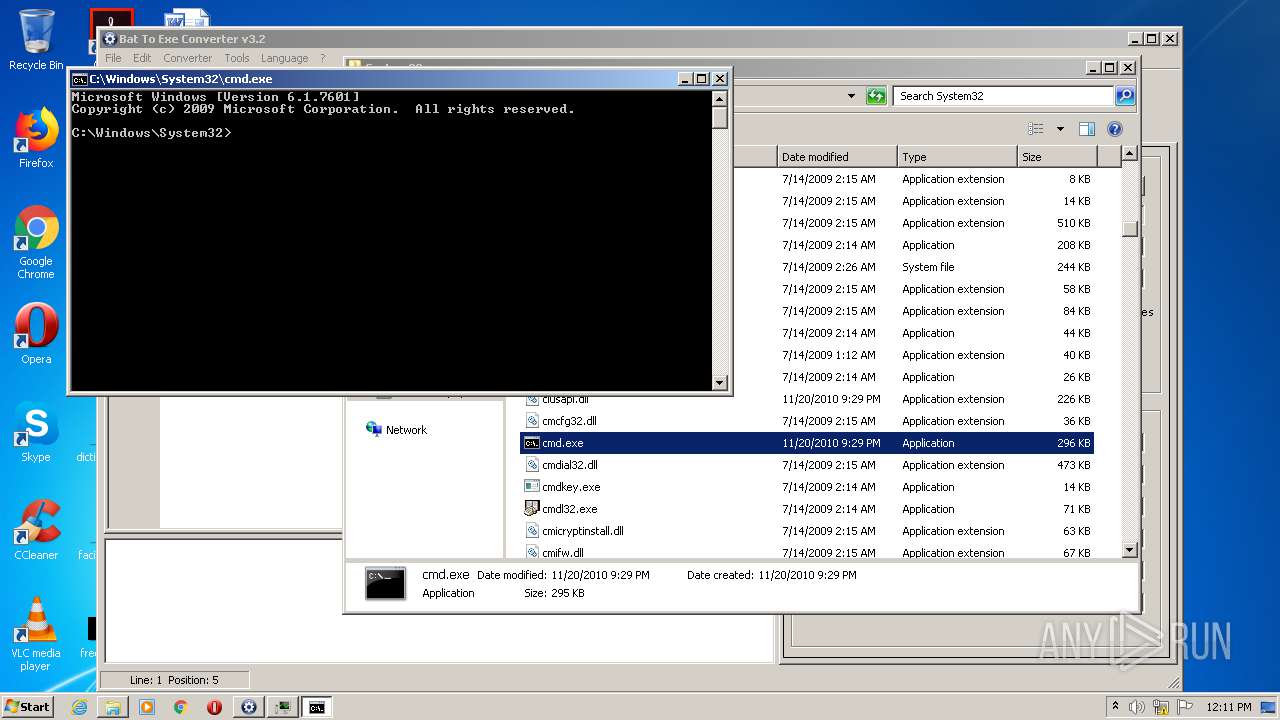
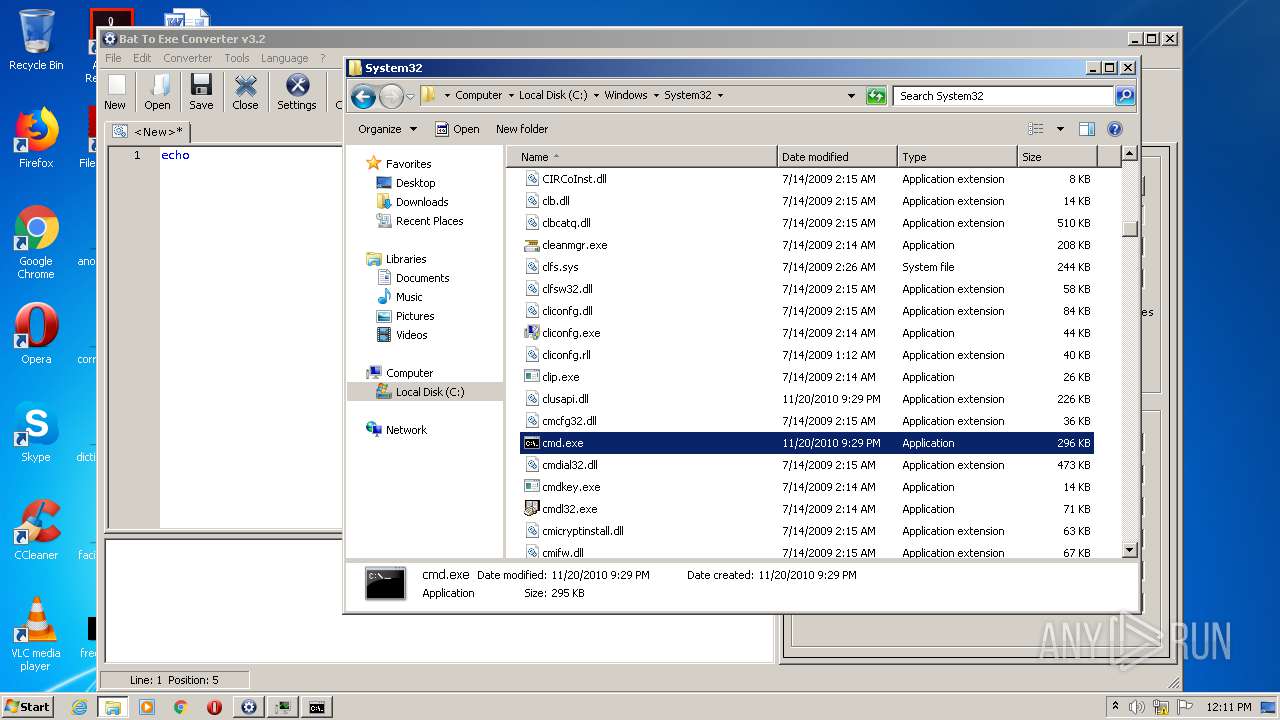
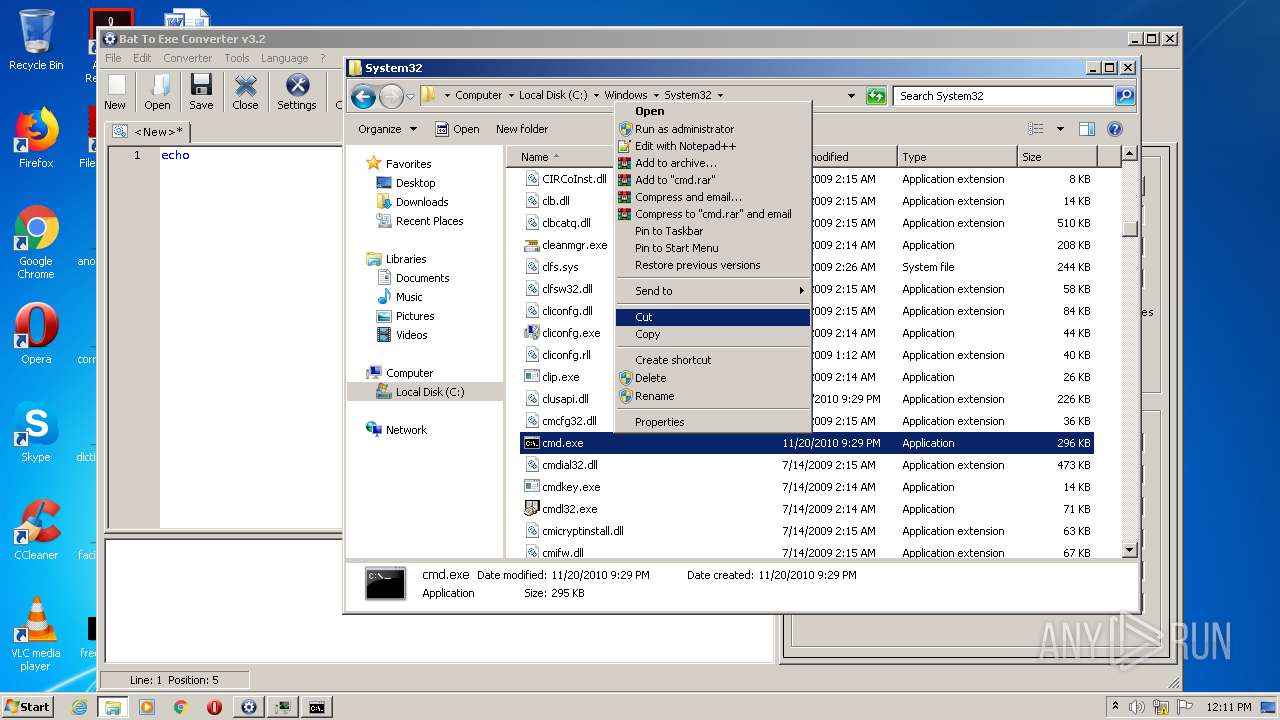
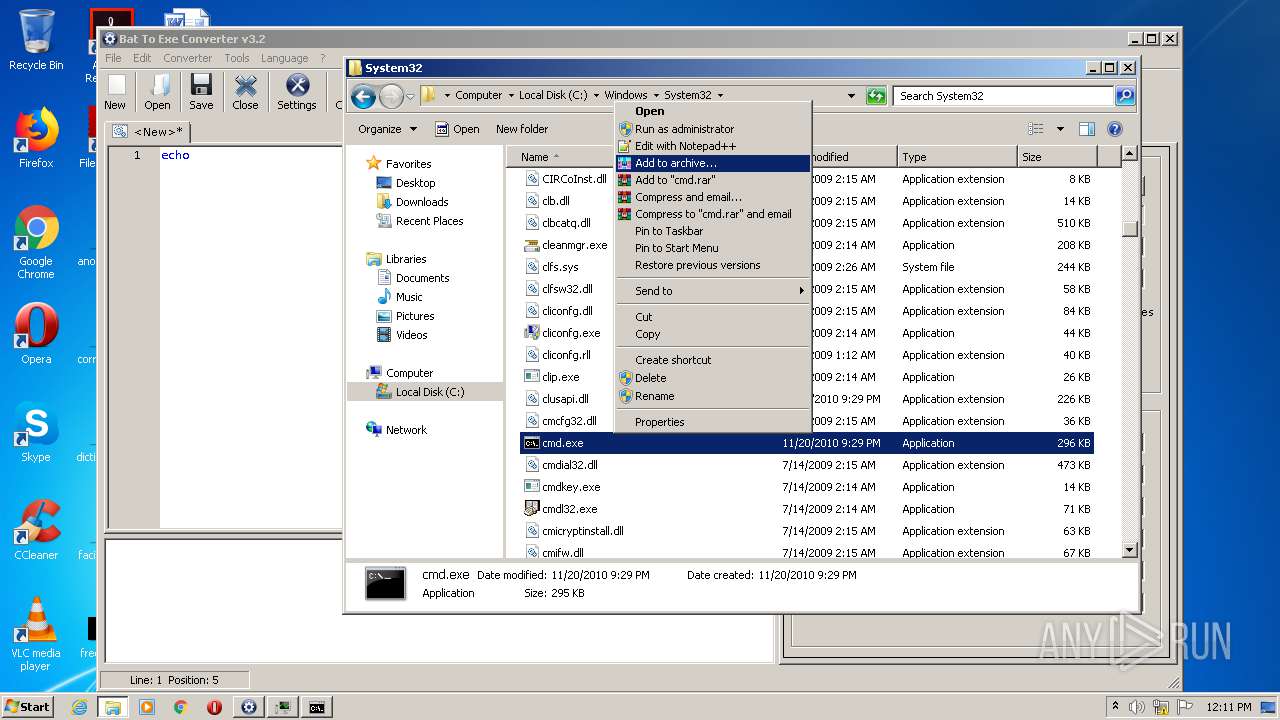
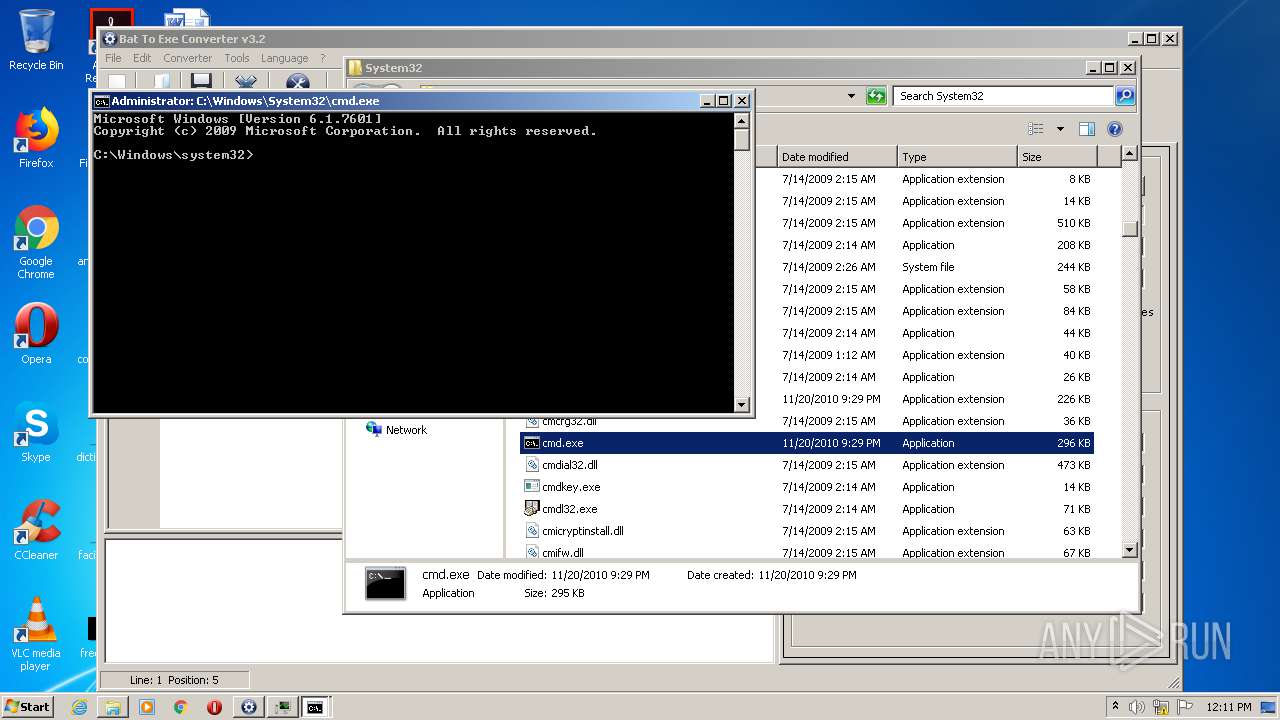
Manual execution by user
- cmd.exe (PID: 2916)
- explorer.exe (PID: 672)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 12:06:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1826816 |
| InitializedDataSize: | 147456 |
| UninitializedDataSize: | 1581056 |
| EntryPoint: | 0x33ff30 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.0.0 |
| ProductVersionNumber: | 3.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Fatih Kodak |
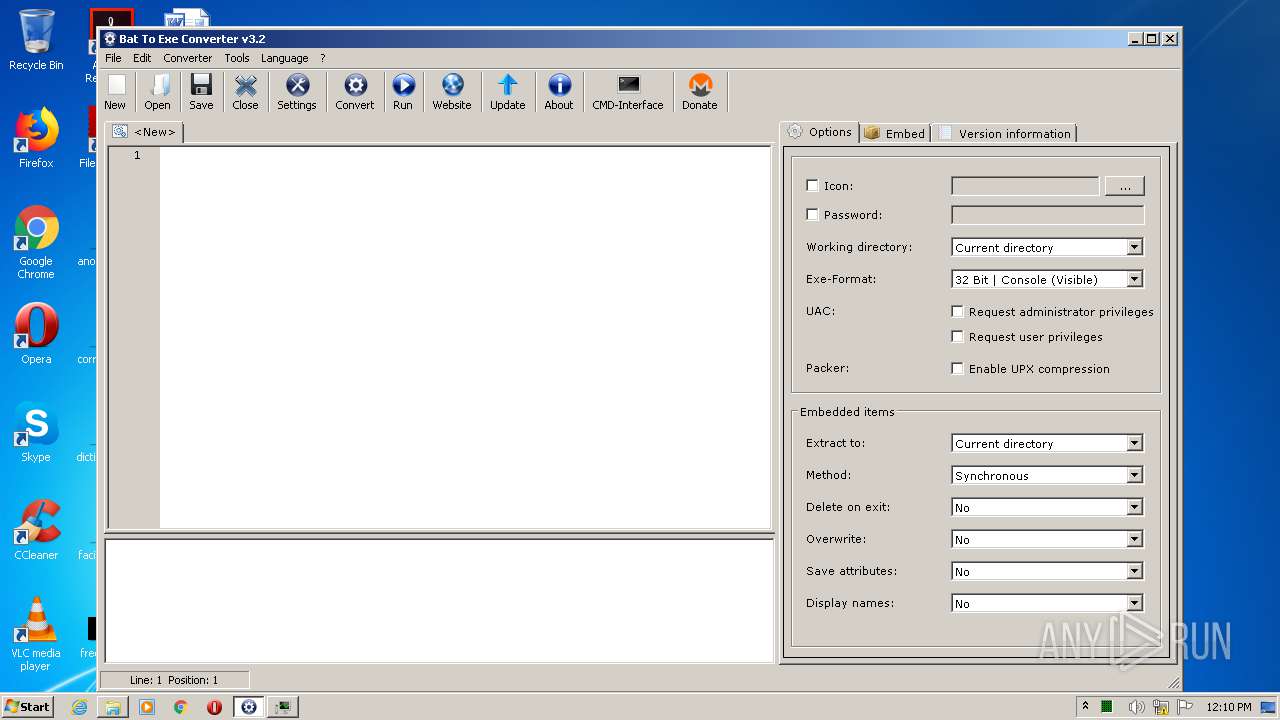
| ProductName: | Bat To Exe Converter |
| ProductVersion: | 3.2 |
| FileVersion: | 3.2 |
| FileDescription: | Bat To Exe Converter |
| InternalName: | Bat To Exe Converter |
| OriginalFileName: | Bat To Exe Converter |
| Website: | http://www.f2ko.de |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jul-2019 10:06:15 |
| Detected languages: |
|
| CompanyName: | Fatih Kodak |
| ProductName: | Bat To Exe Converter |
| ProductVersion: | 3.2 |
| FileVersion: | 3.2 |
| FileDescription: | Bat To Exe Converter |
| InternalName: | Bat To Exe Converter |
| OriginalFilename: | Bat To Exe Converter |
| Website: | http://www.f2ko.de |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Jul-2019 10:06:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00182000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00183000 | 0x001BE000 | 0x001BDC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99988 |
.rsrc | 0x00341000 | 0x00024000 | 0x00023C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.56919 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.72897 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 5.71122 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 5.68138 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.92516 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.98264 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 5.99869 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
OLEAUT32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
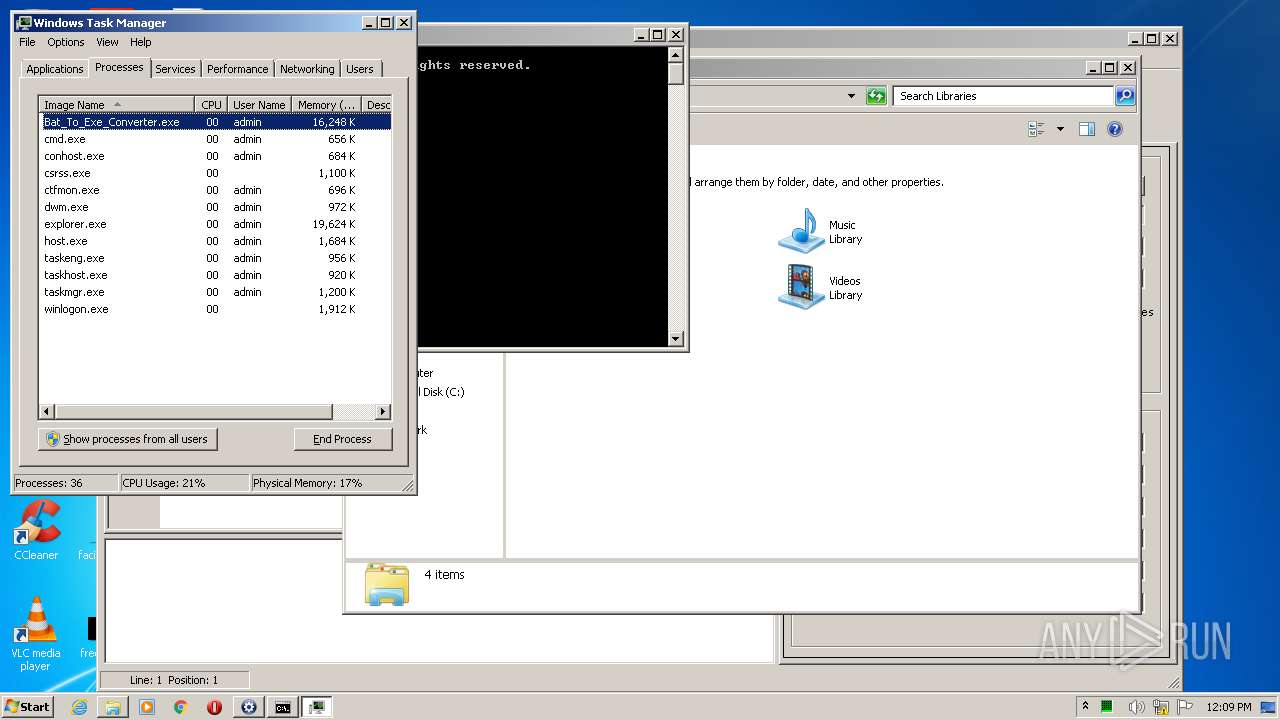
Total processes
53
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | whoami | C:\Windows\system32\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1632 | taskmgr | C:\Windows\system32\taskmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2860 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
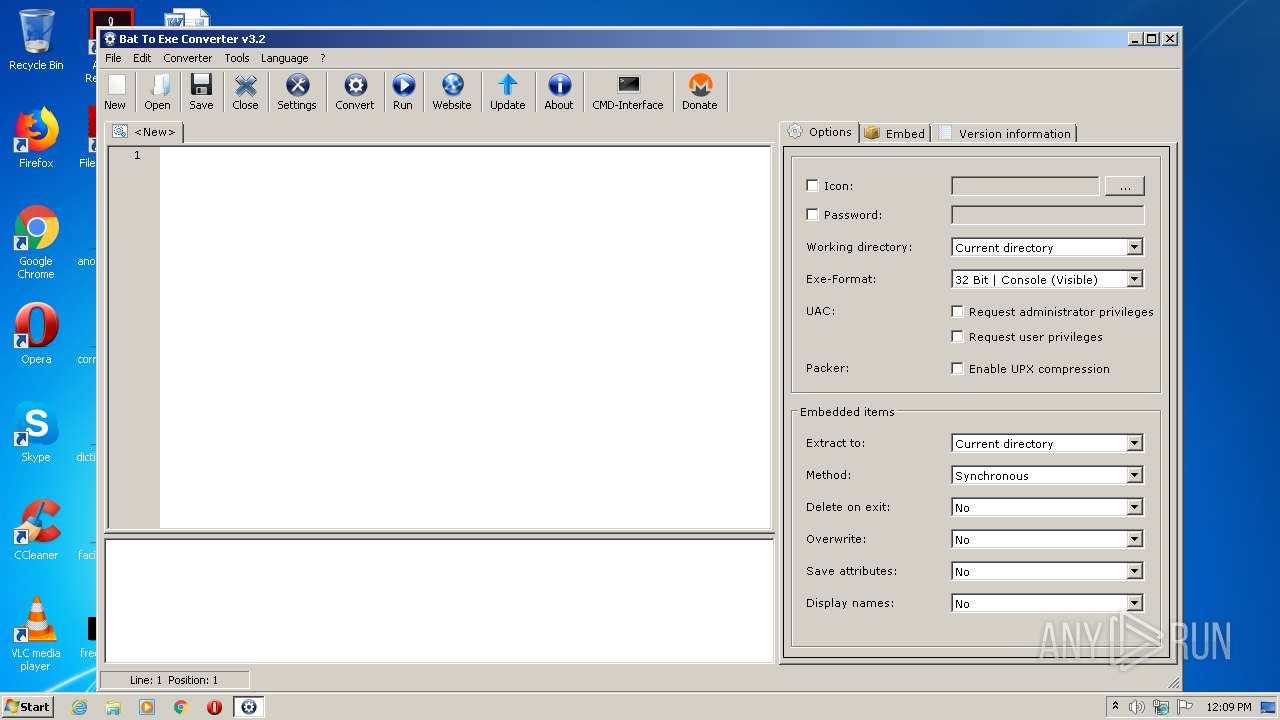
| 2888 | "C:\Users\admin\AppData\Local\Temp\Bat_To_Exe_Converter.exe" | C:\Users\admin\AppData\Local\Temp\Bat_To_Exe_Converter.exe | explorer.exe | ||||||||||||
User: admin Company: Fatih Kodak Integrity Level: MEDIUM Description: Bat To Exe Converter Exit code: 0 Version: 3.2 Modules
| |||||||||||||||
| 2916 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
563
Read events
532
Write events
29
Delete events
2
Modification events
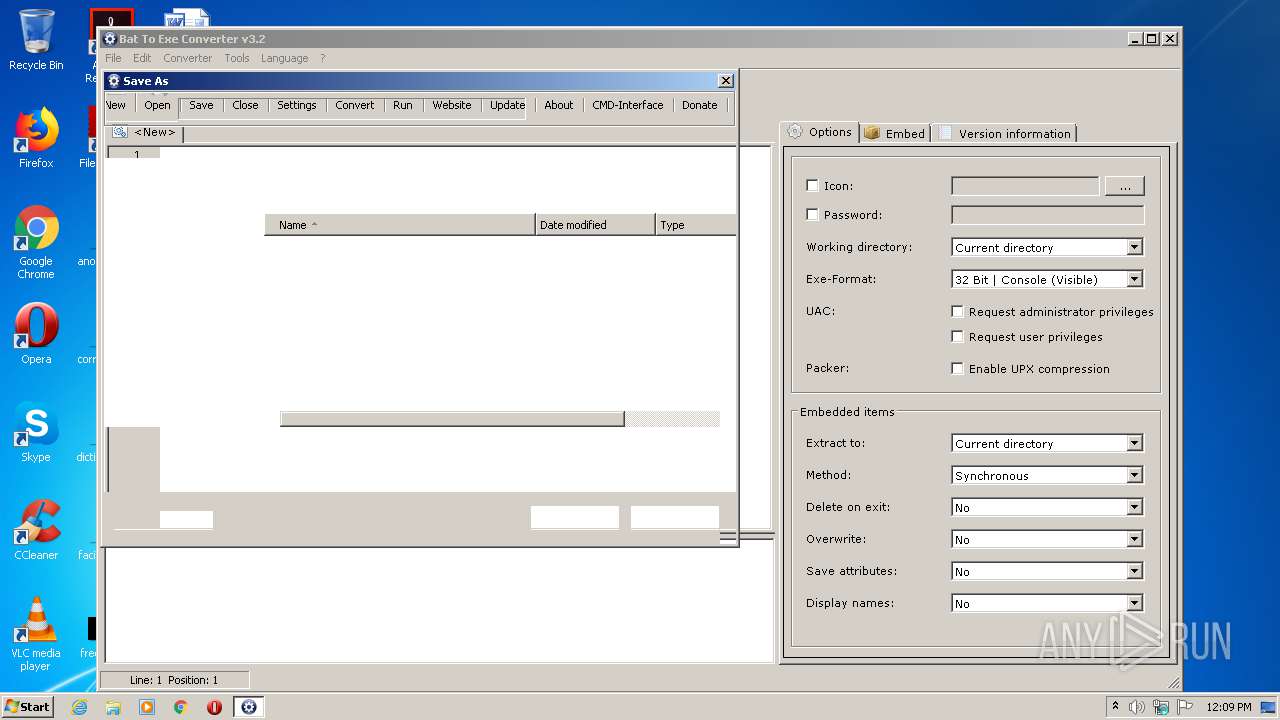
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000B0000000100000000000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 4200610074005F0054006F005F004500780065005F0043006F006E007600650072007400650072002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 2 |
Value: 4200610074005F0054006F005F004500780065005F0043006F006E007600650072007400650072002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2888) Bat_To_Exe_Converter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 4200610074005F0054006F005F004500780065005F0043006F006E007600650072007400650072002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006400000044000000E402000024020000000000000000000000000000000000000100000000000000 | |||
Executable files
4
Suspicious files
0
Text files
16
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\842836092.bat | — | |
MD5:— | SHA256:— | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\38680036.cmd | — | |
MD5:— | SHA256:— | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\日本語 (Japanese).lng | text | |
MD5:2125B2D9BFDA91CECA3ED41F4C861B4C | SHA256:876D4162596D4EFA962D5E214A3A801EAE4C8BFD36439D20880D5098F602321B | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\extd.chm | chi | |
MD5:D4FC8C71A167383B2CEA62137B12F63D | SHA256:2786F9B9CDF8A73396405CE59CB6D00FAD9D51E5136183999D14A5CB9F5D80FB | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\Português Brasileiro (Portuguese Brazilian).lng | text | |
MD5:71F0183E192E34D375F0735210E97C4A | SHA256:130764E3A2E43B78EE632C0372BC5630BD62ABF74AA825865FE5B4C14F4D7A27 | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\GoLink.exe | executable | |
MD5:CAFC4EEC8A4F05B8DFEE4067FB5B9076 | SHA256:1FA554D18490CB5E56D624CD97069F42E63800688136C6CF3C521E4EF6E83E28 | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\Ελληνικά (Greek).lng | text | |
MD5:CE7919F5607F6852962AFEE414CF143C | SHA256:CDA6F61CB33194B48B9764BC9E1D704197454DA7967BB7B6F0F87122D033E767 | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\한국어 (Korean).lng | text | |
MD5:CFC7FC230EA20DC8E11BB17389FA57B2 | SHA256:63D5C6772D8998FBD0331092E96151CA31662A6A7AC7B11AF4F5E2FD30ED77F4 | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\Русский (Russian).lng | text | |
MD5:E85F3E236272739458070F2AD0FD8AEA | SHA256:EFA8B1029530AA46FF21F704F6EFE59A69FE59D6B96E2370EDC32FAB62A2FD29 | |||
| 2888 | Bat_To_Exe_Converter.exe | C:\Users\admin\AppData\Local\Temp\32F2.tmp\lng\简化中国 (Chinese Simplified).lng | text | |
MD5:8AB06A4B804350D0A232E65B82E992E1 | SHA256:5A5FBE8998D1AA2C6CB7E16FA50861910C806AC3DF99E2026E8B577175B36133 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report