| File name: | ophack.exe |
| Full analysis: | https://app.any.run/tasks/f443640d-cc9a-418c-bdc4-bae82a67d493 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2020, 16:20:20 |
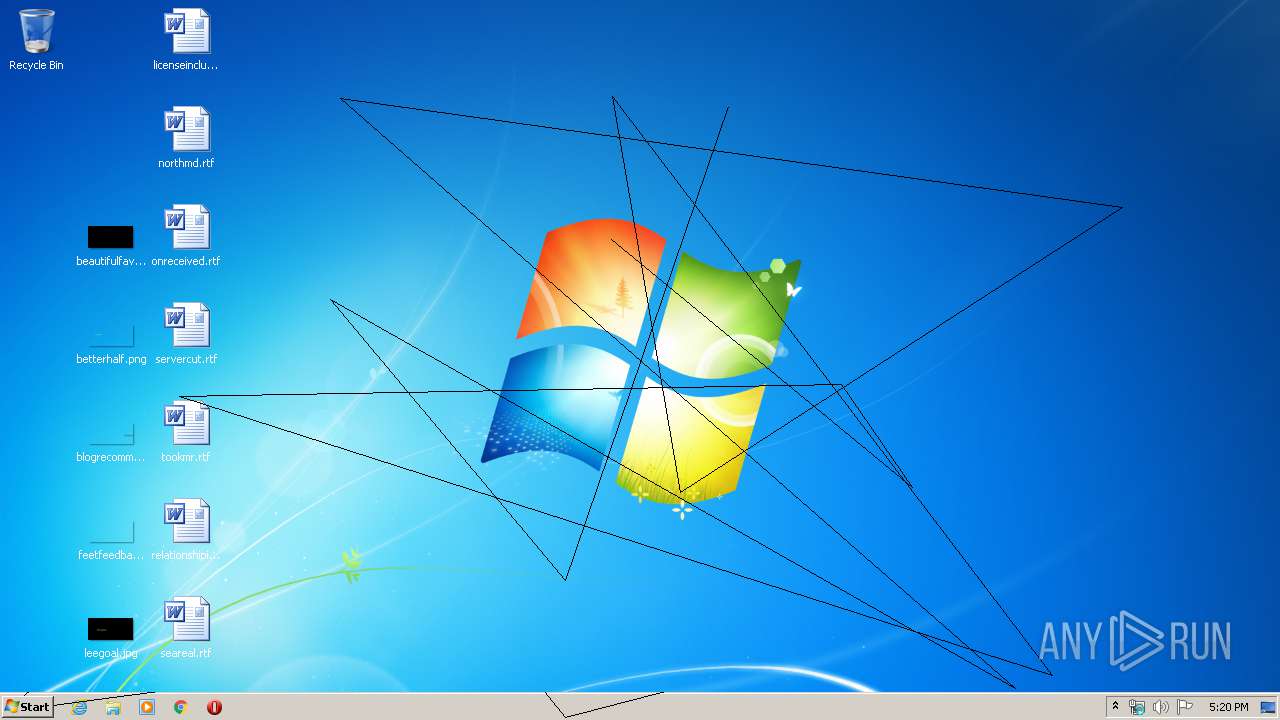
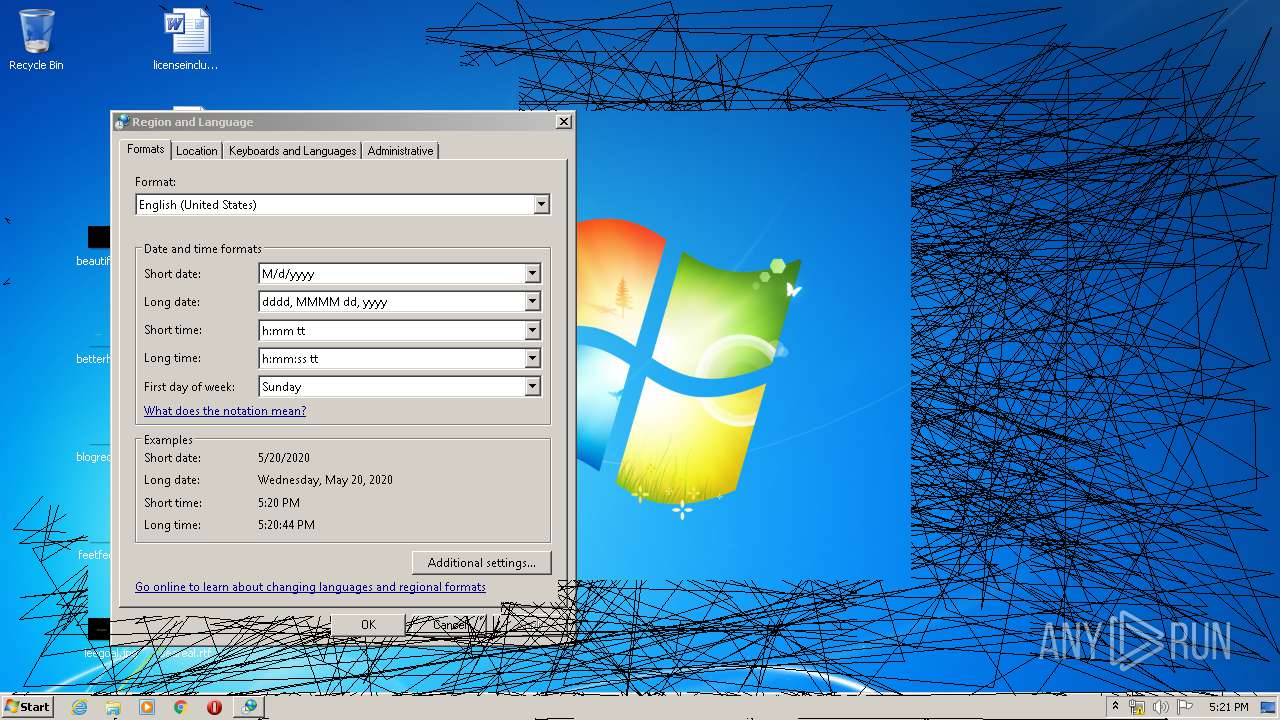
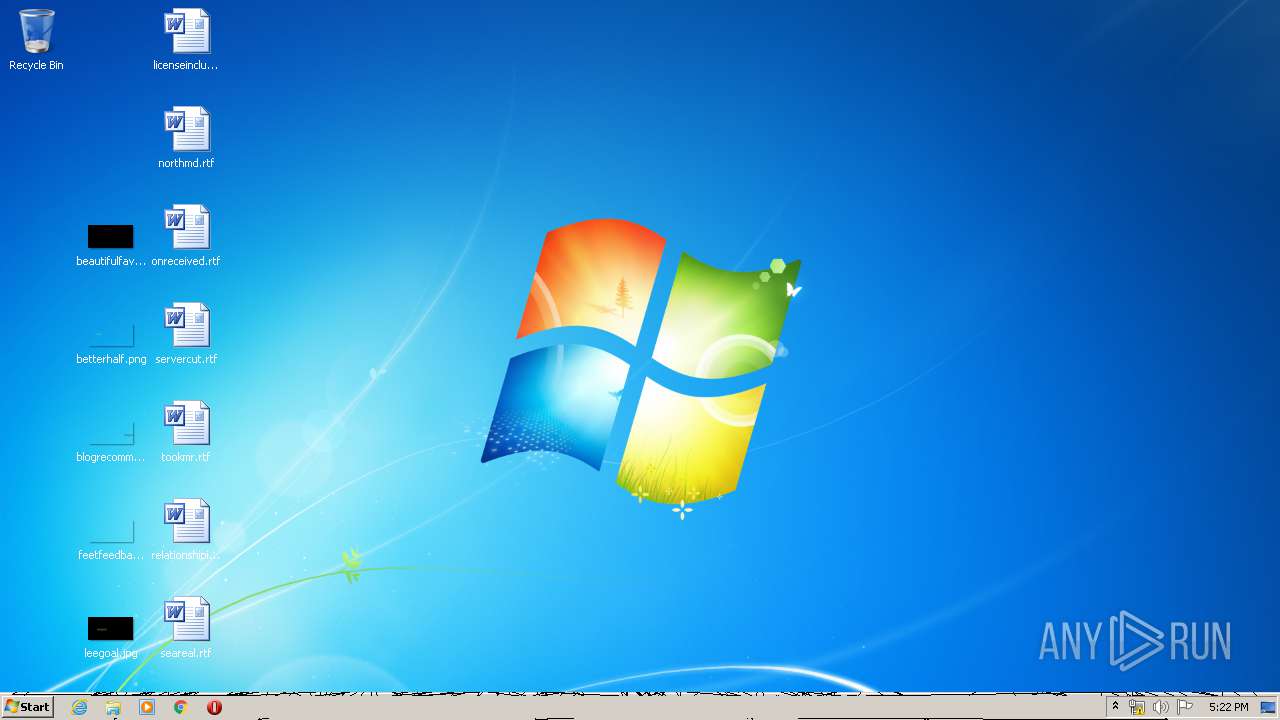
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 48FE89C566FB4544F49676F68CF9CE0C |
| SHA1: | 3BC353705D69267BBE078FED3DADE909F042D496 |
| SHA256: | C1AA786D7B9A5020F01D2674F9D5202D5459606AB07A52A118B64FFD6AA9649C |
| SSDEEP: | 384:8LipZl447piqb/lUYf5uH3w59AMRG5qUIjFgOrjFymqAeO8W8xbMRtWaArbjlzh2:dmiiqTfk2AMRGwlFgOrjsbbM9wjlzhZs |
MALICIOUS
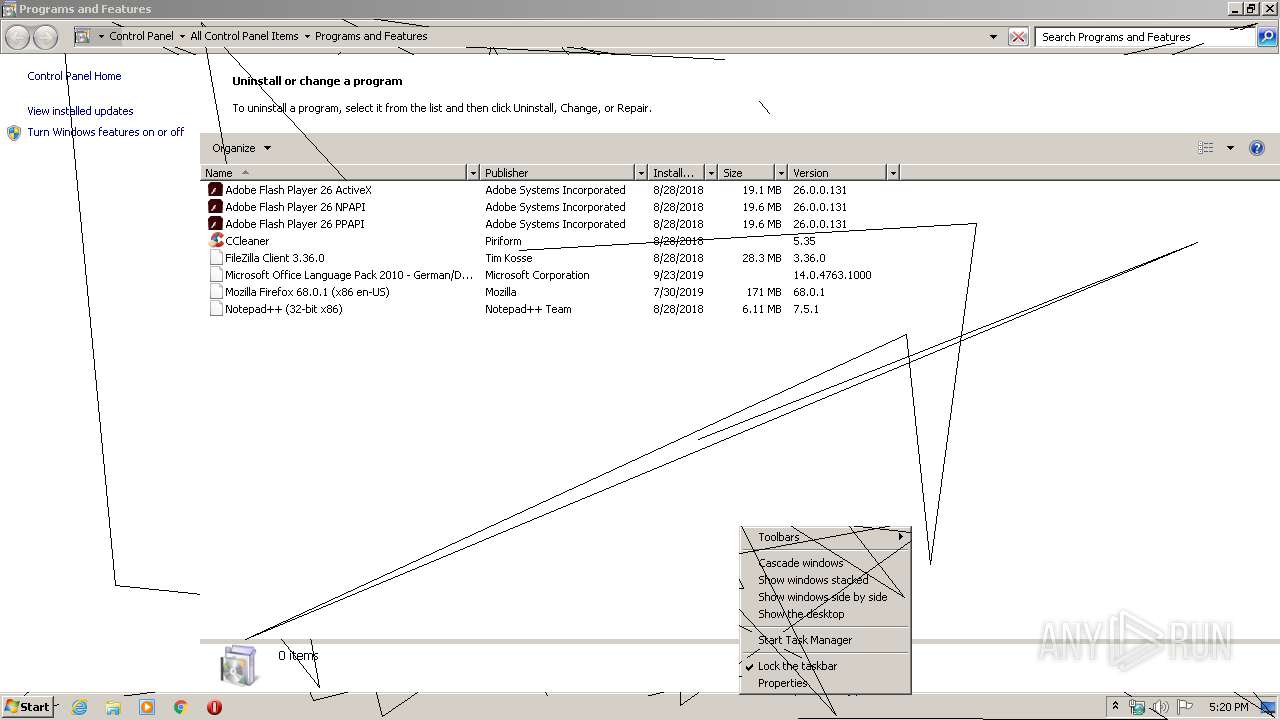
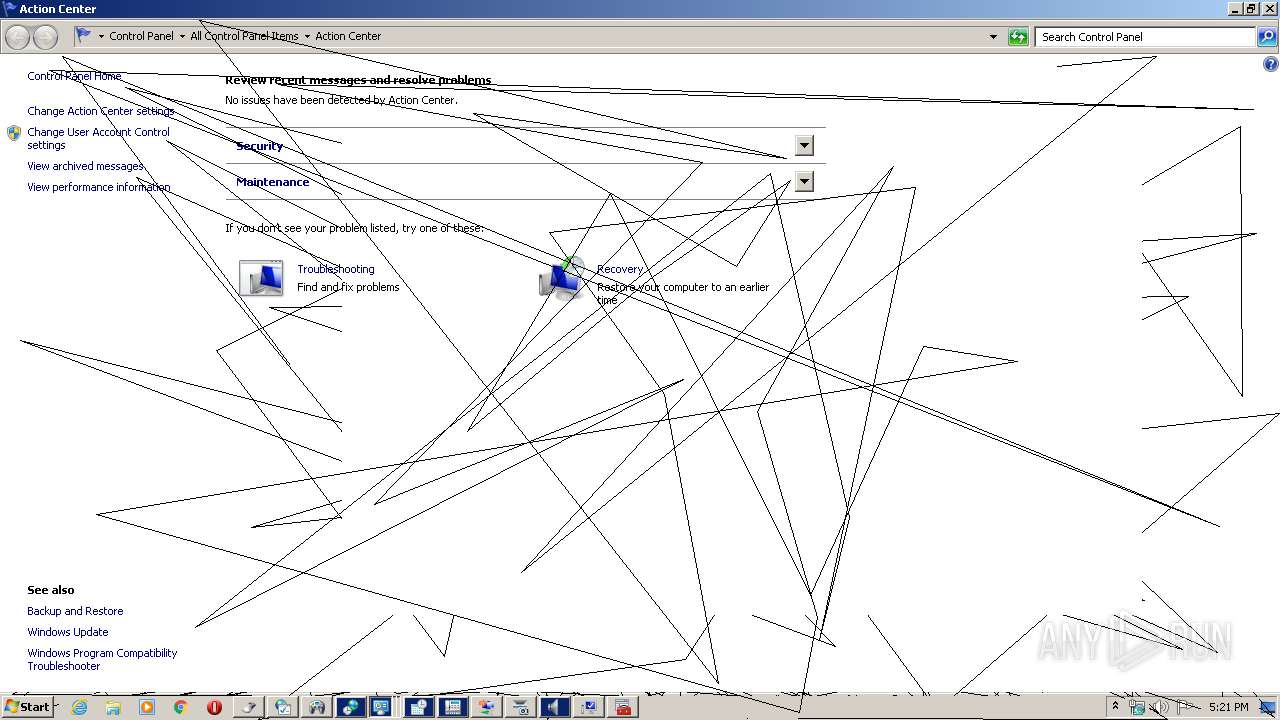
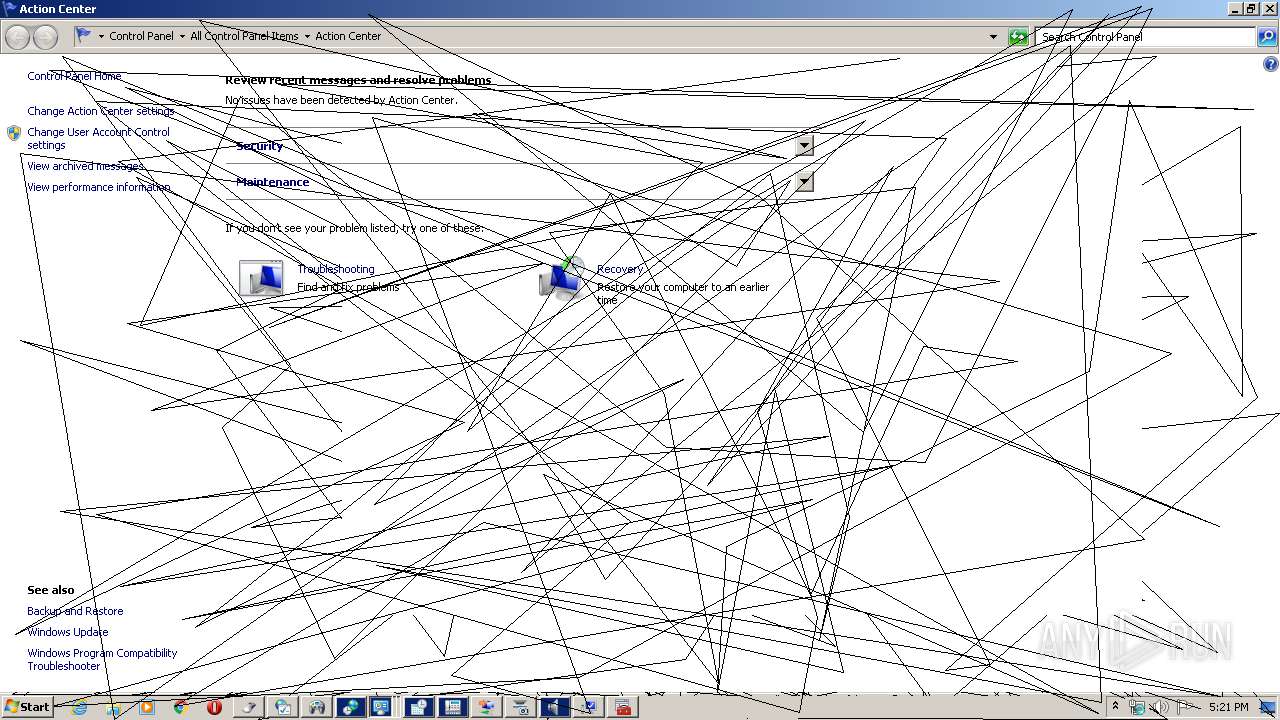
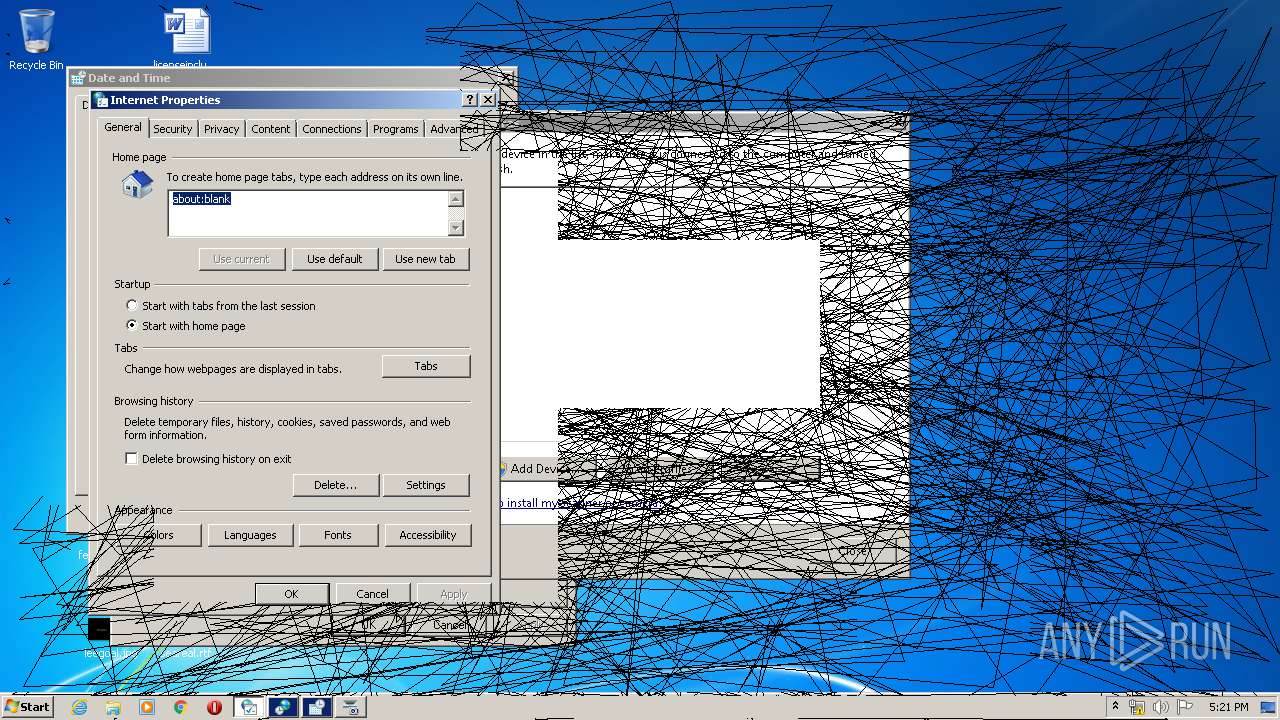
Disables Windows System Restore
- ophack.exe (PID: 2424)
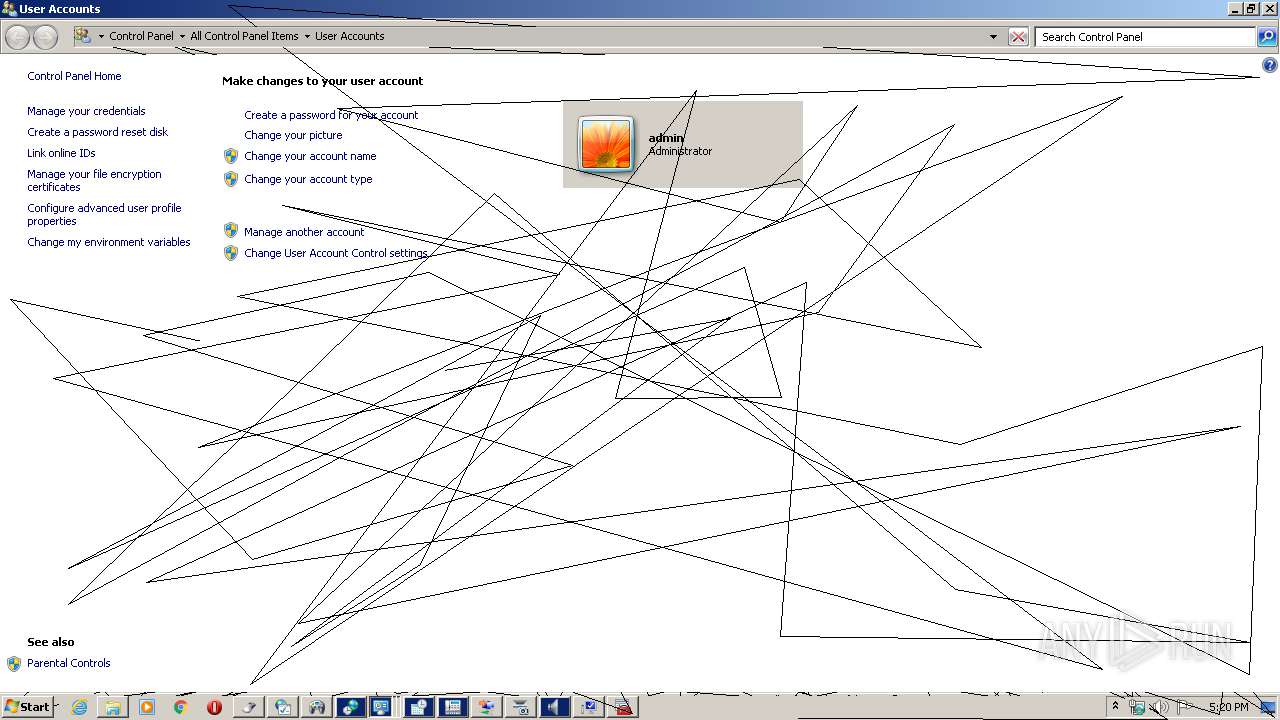
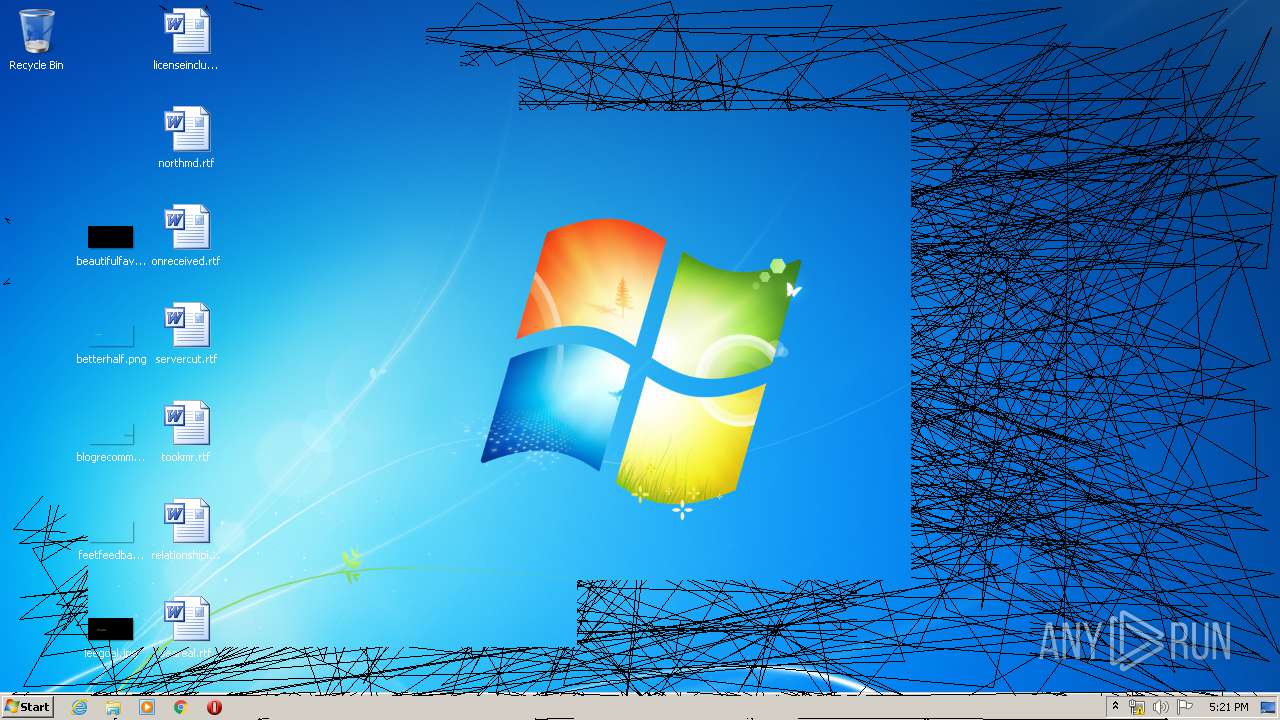
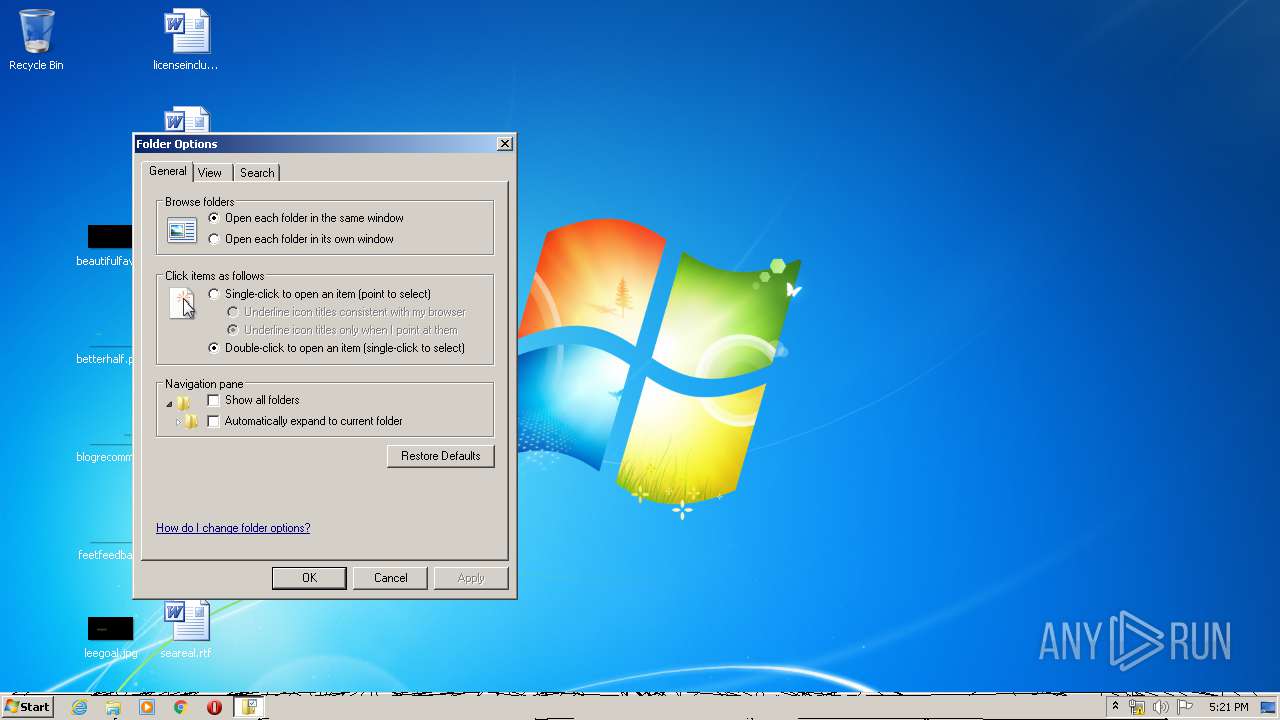
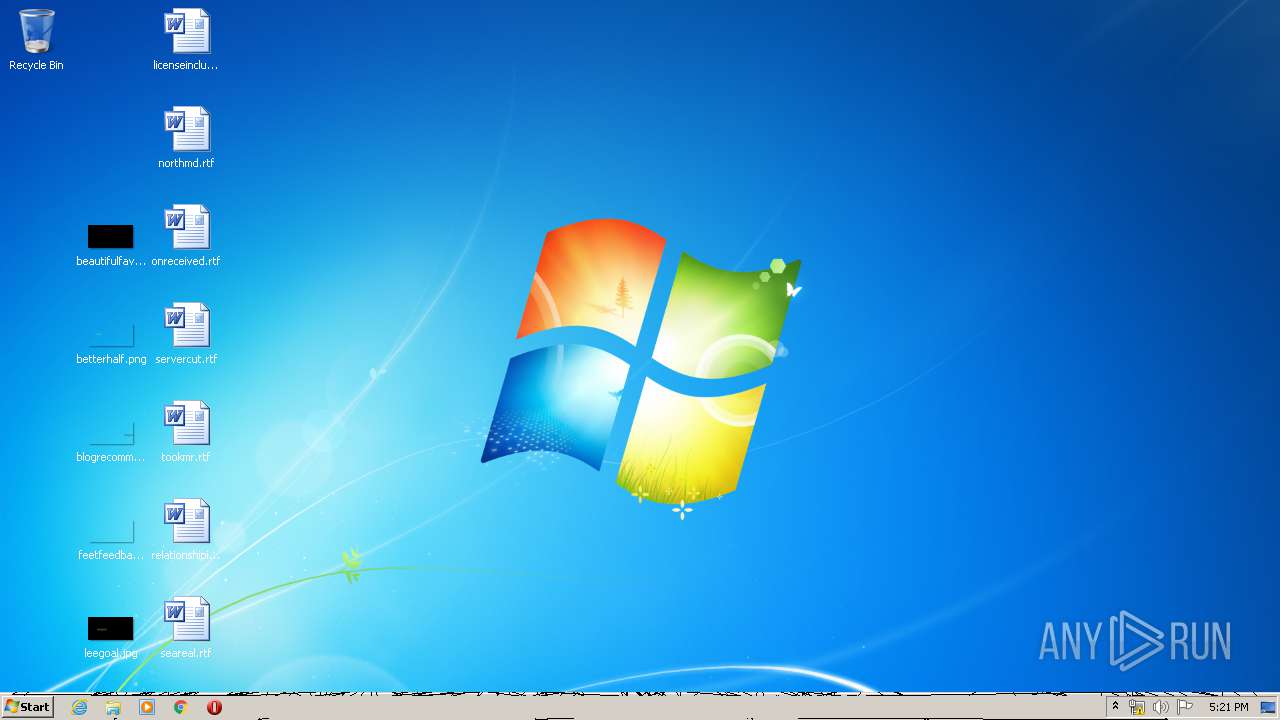
Actions looks like stealing of personal data
- ophack.exe (PID: 2424)
SUSPICIOUS
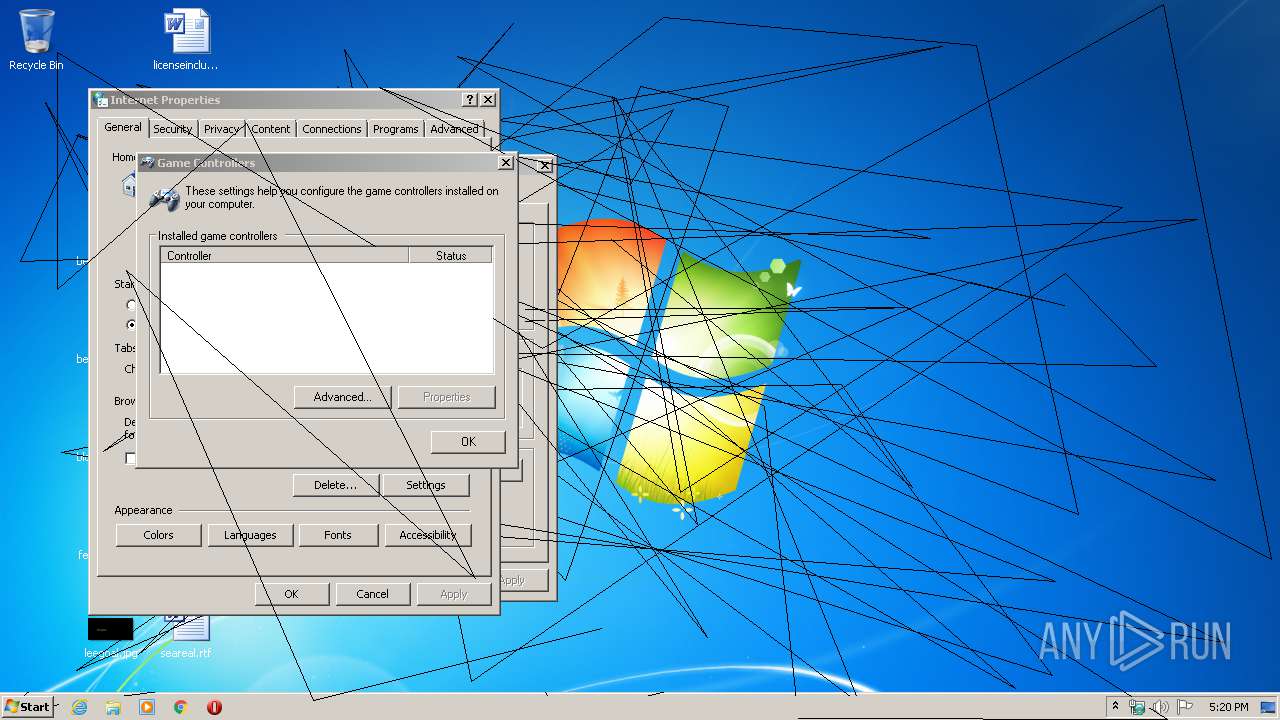
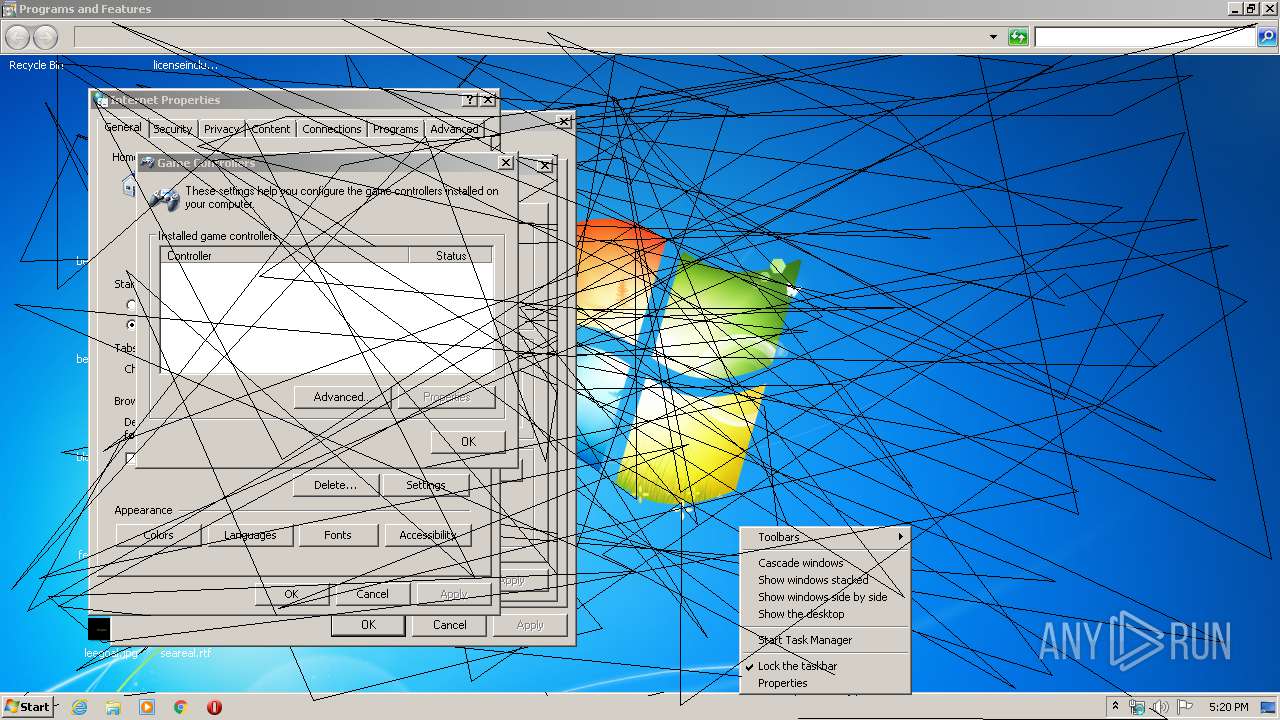
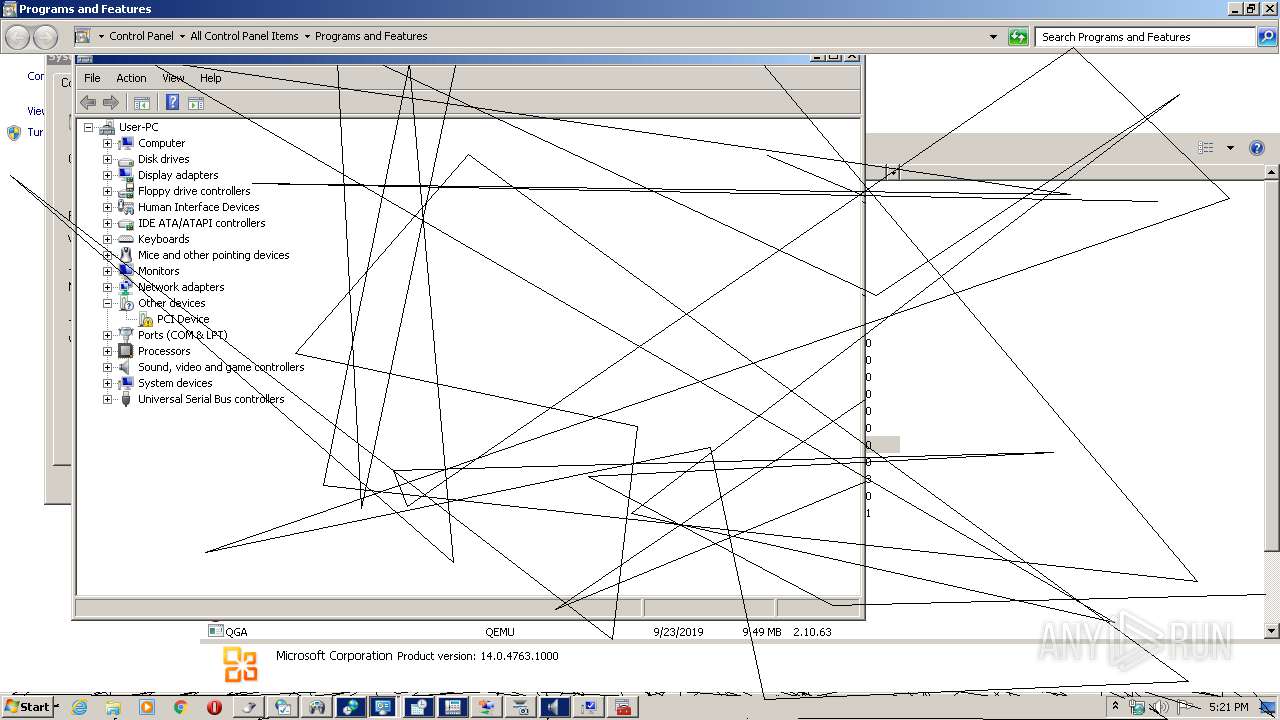
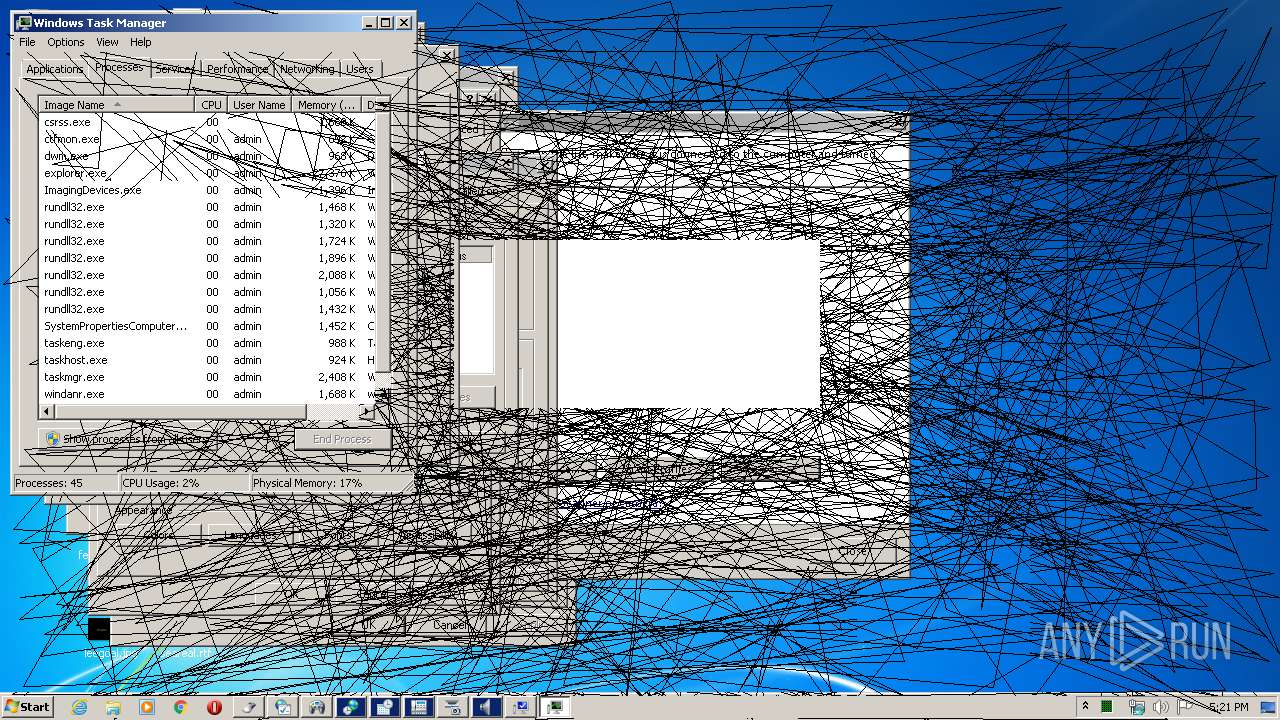
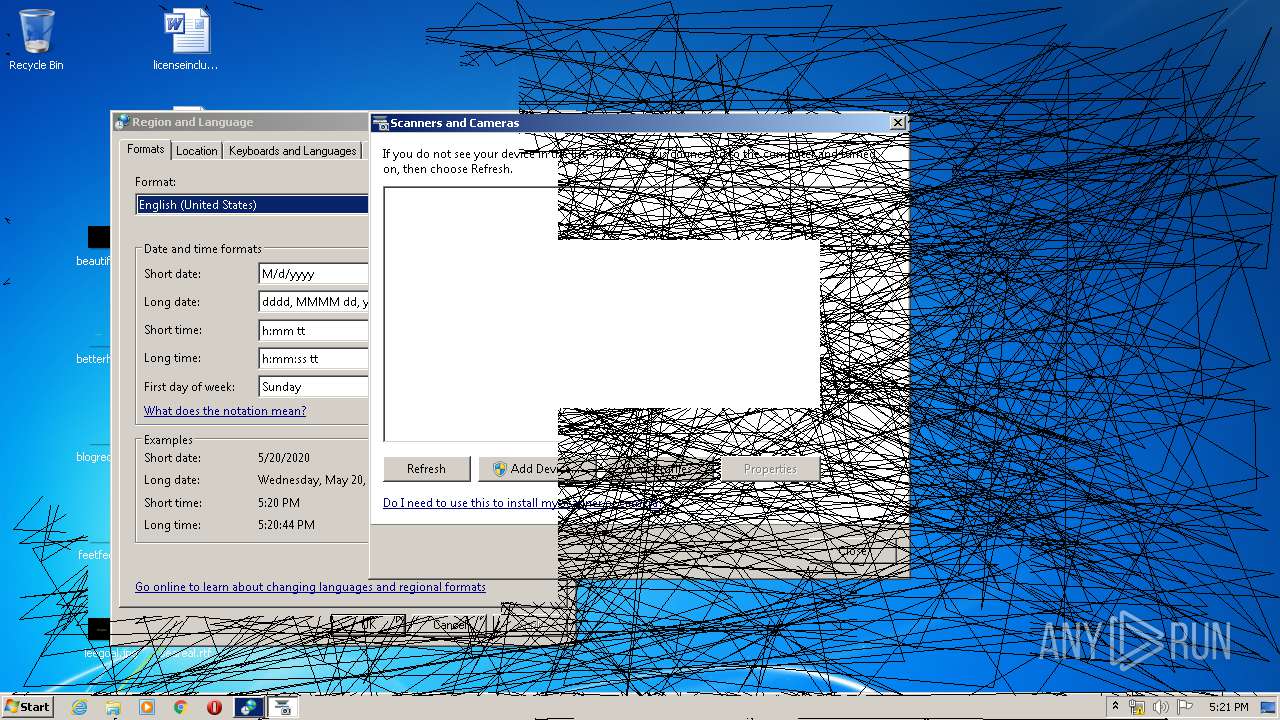
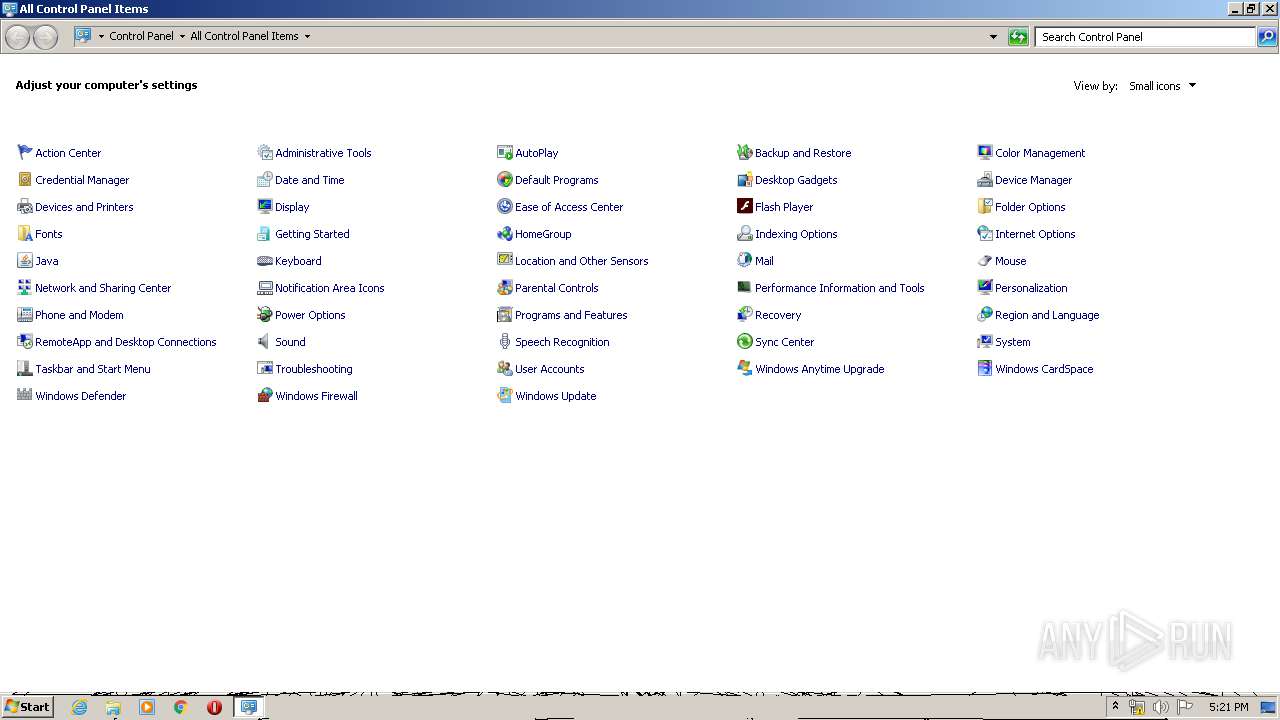
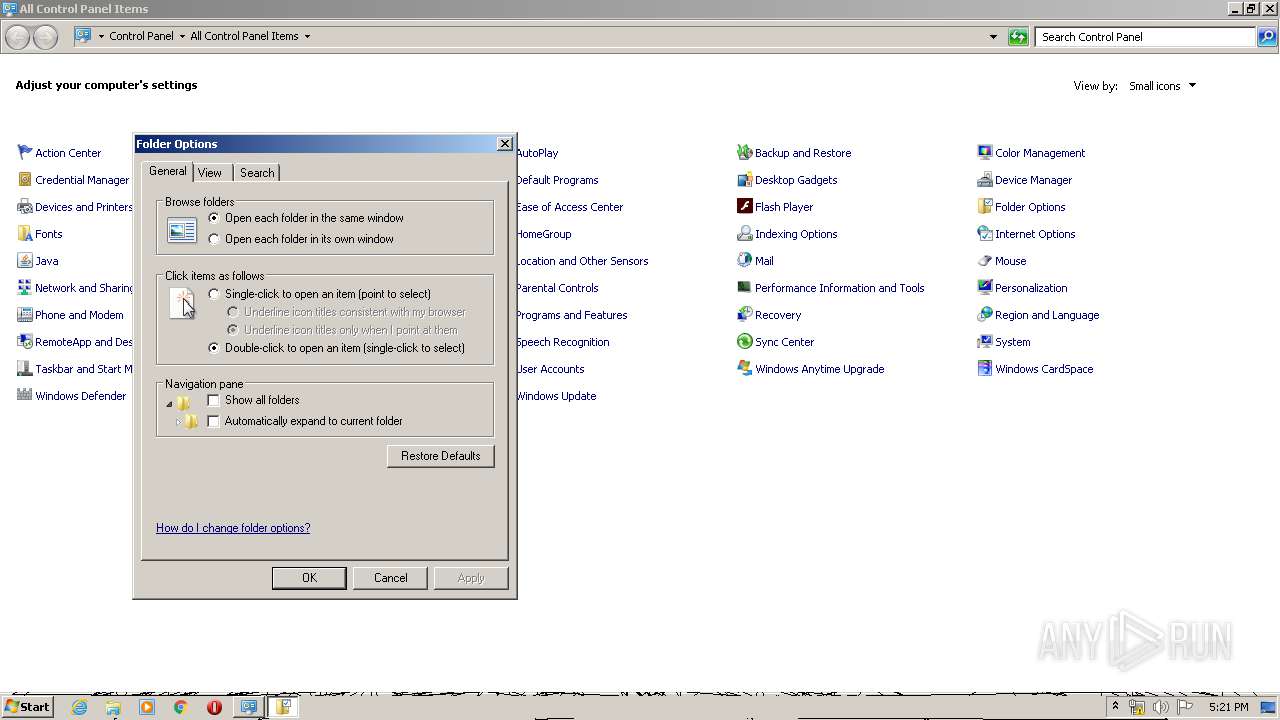
Uses RUNDLL32.EXE to load library
- control.exe (PID: 3628)
- rundll32.exe (PID: 724)
- ophack.exe (PID: 2424)
Modifies the open verb of a shell class
- ophack.exe (PID: 2424)
Application launched itself
- rundll32.exe (PID: 724)
- taskmgr.exe (PID: 3308)
Starts CMD.EXE for commands execution
- ophack.exe (PID: 2424)
INFO
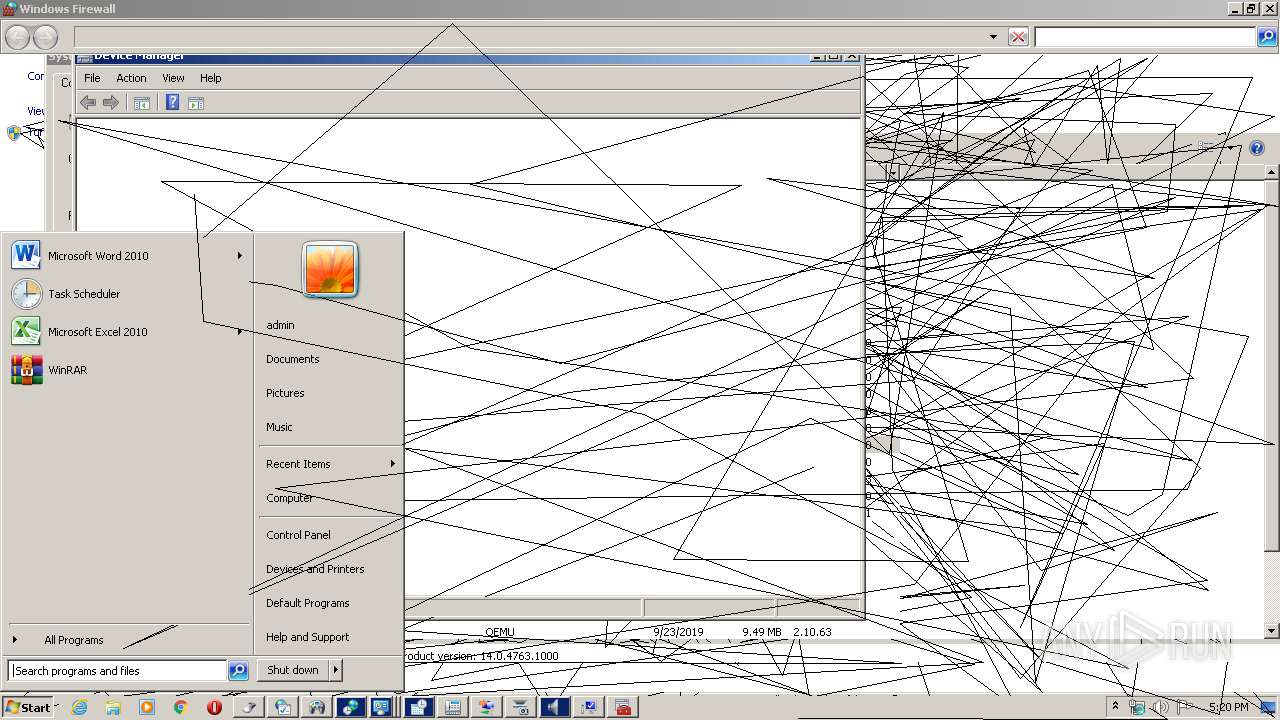
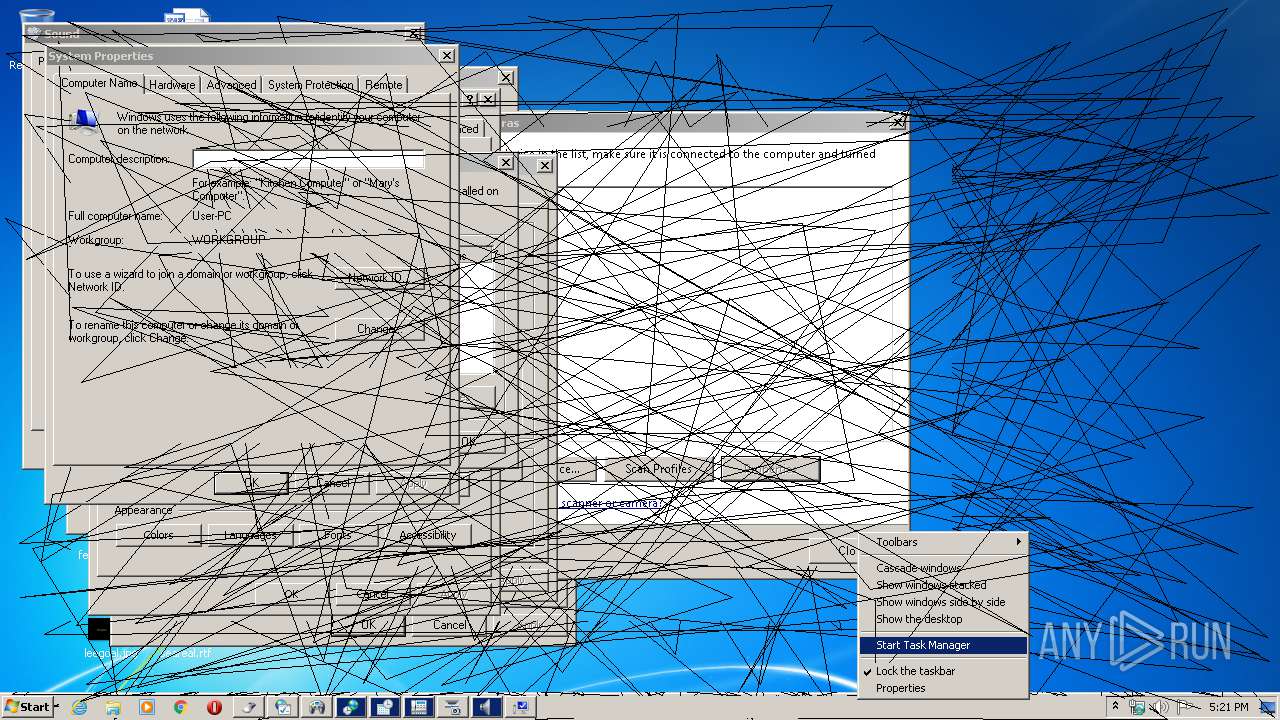
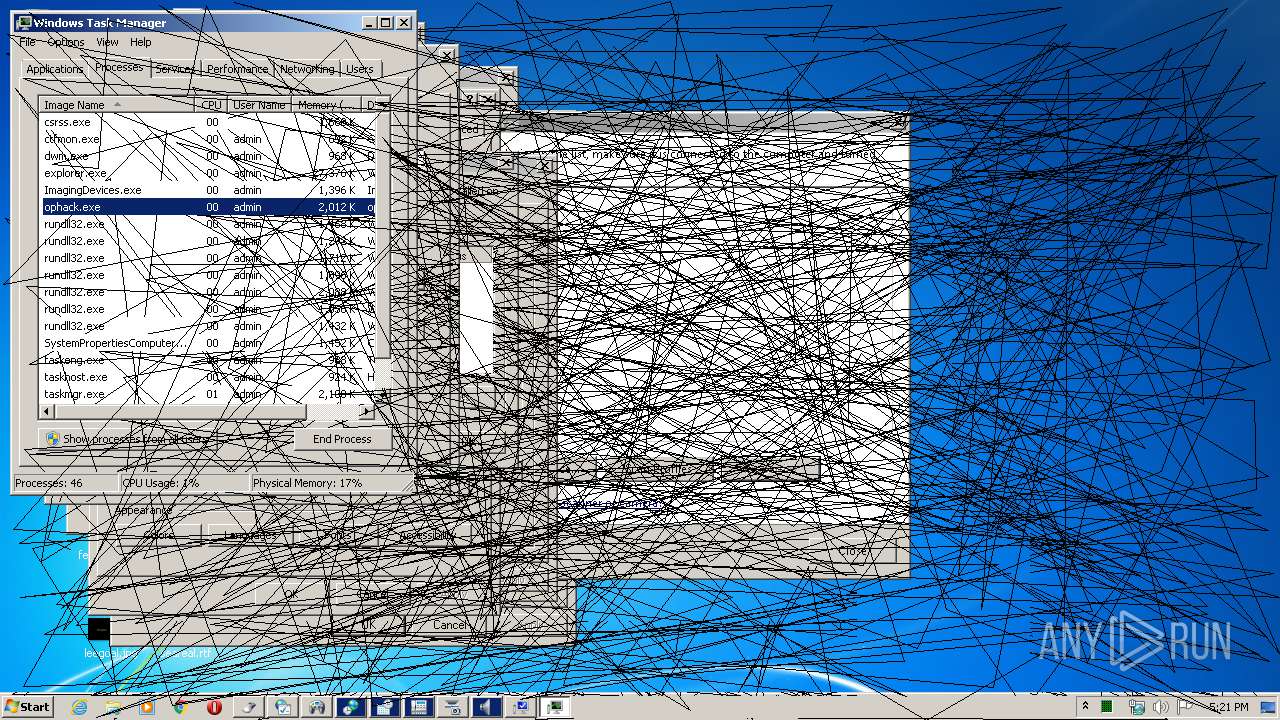
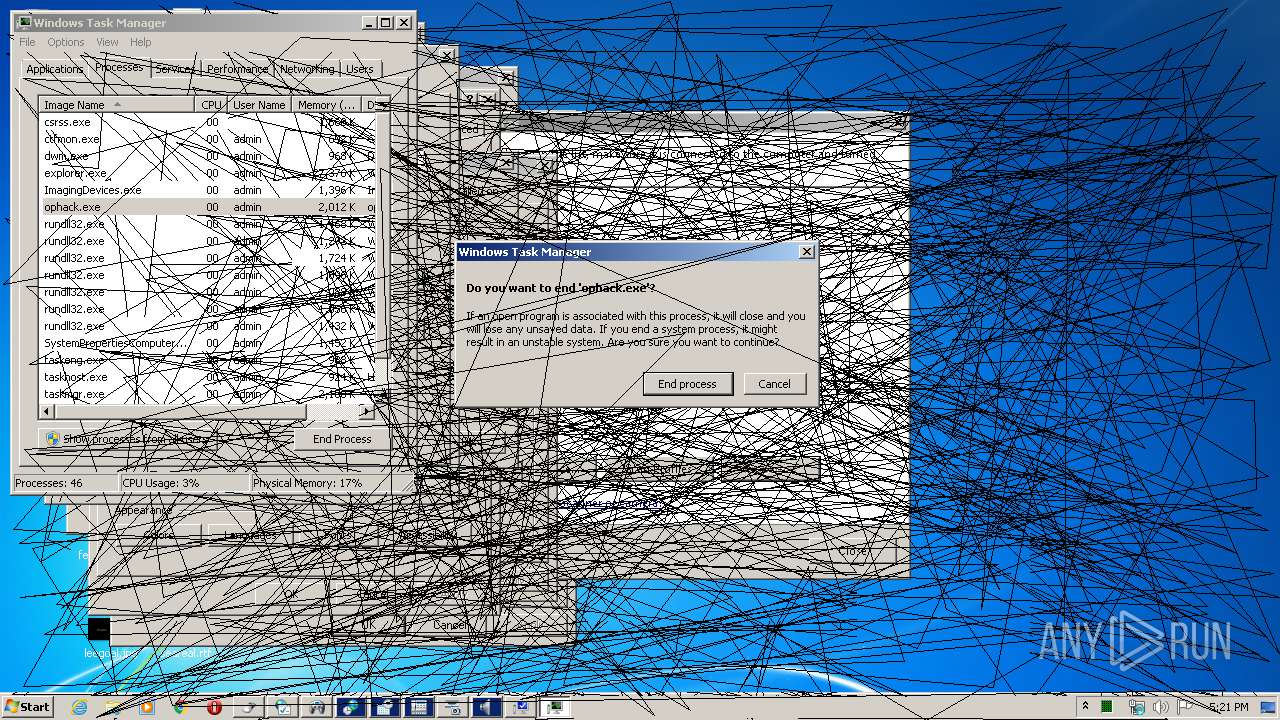
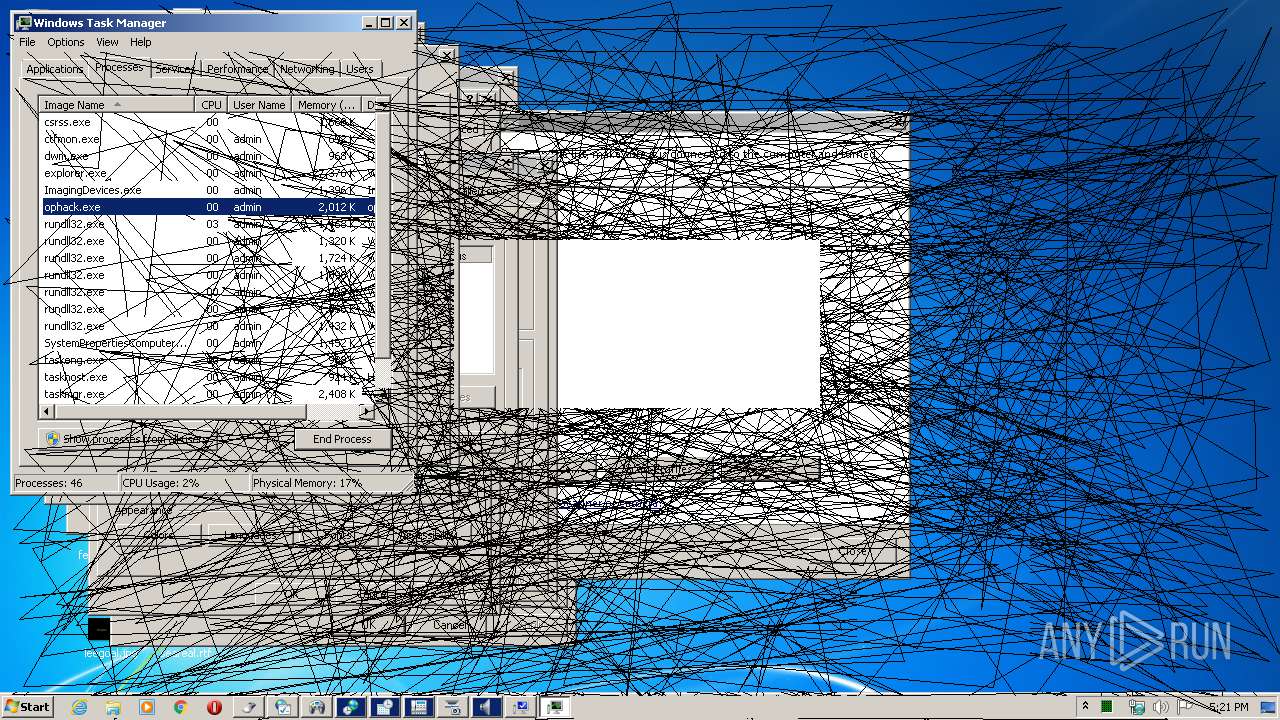
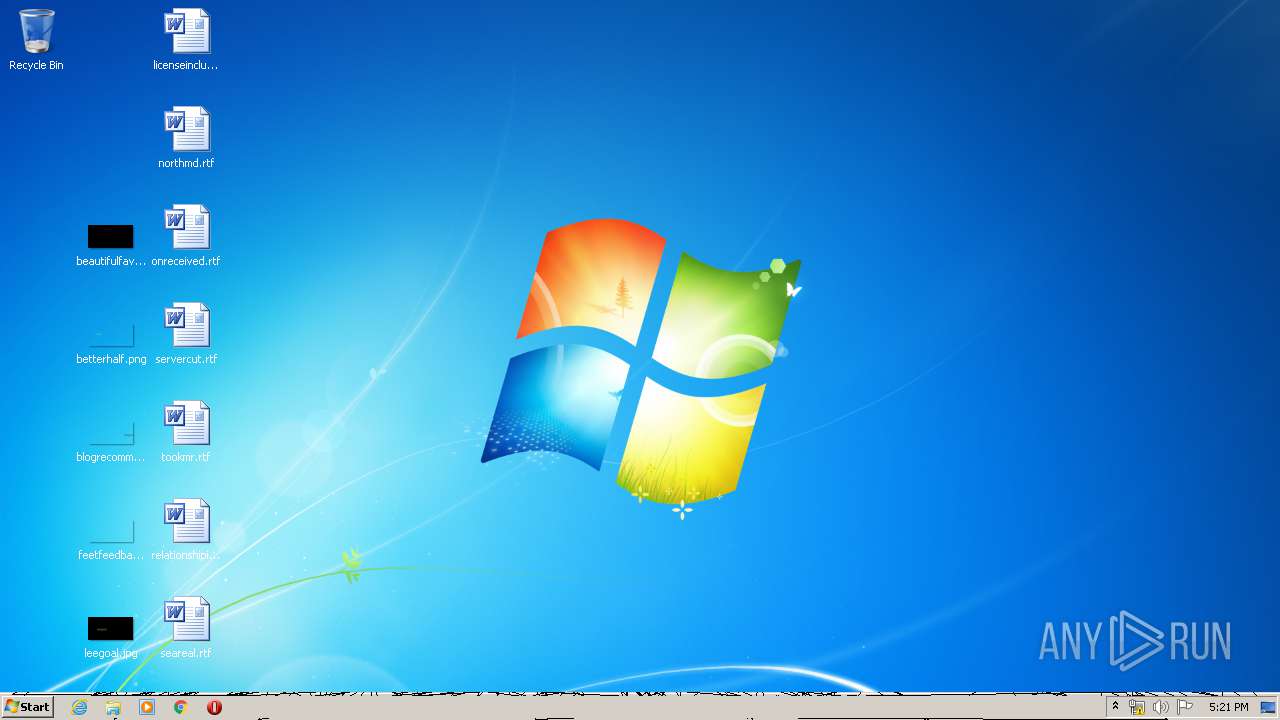
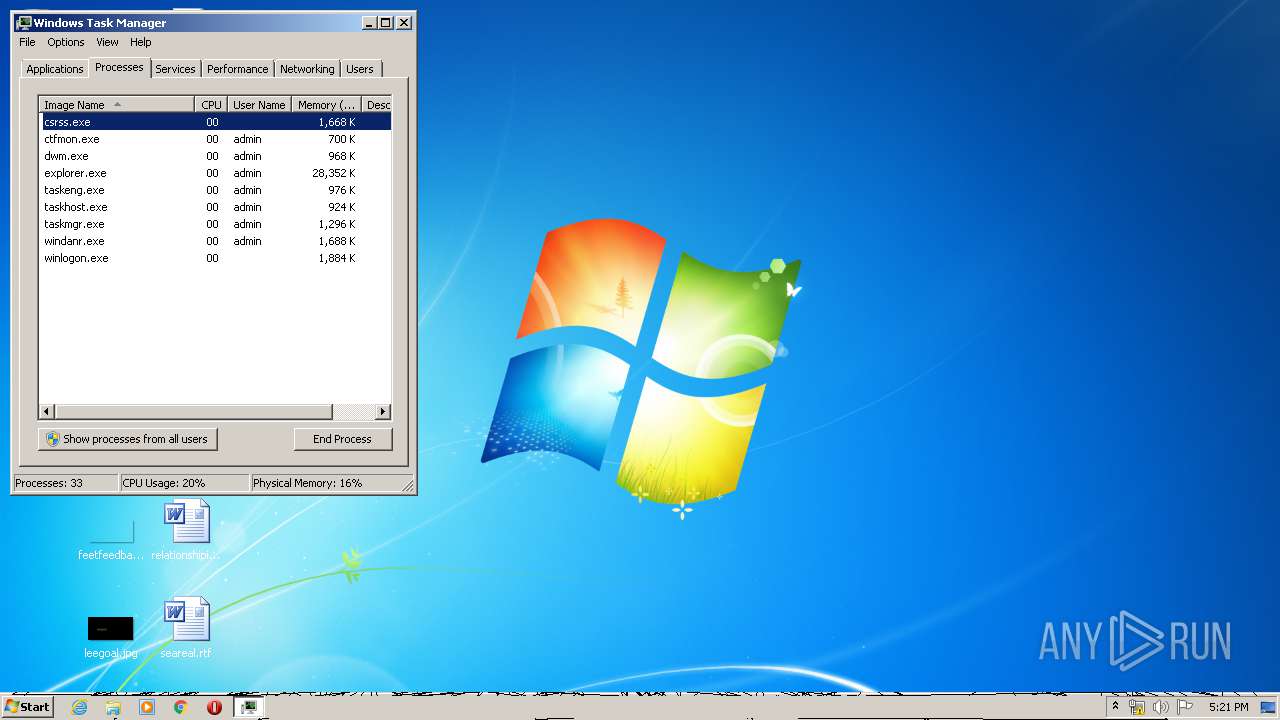
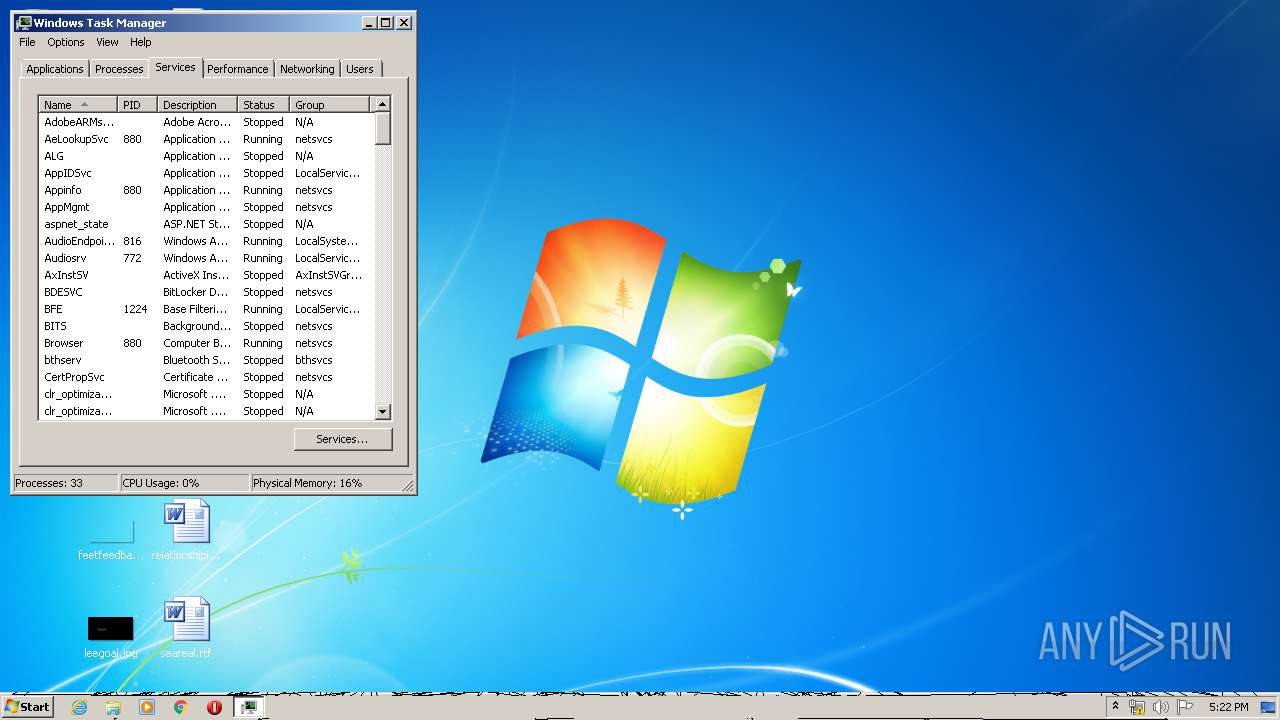
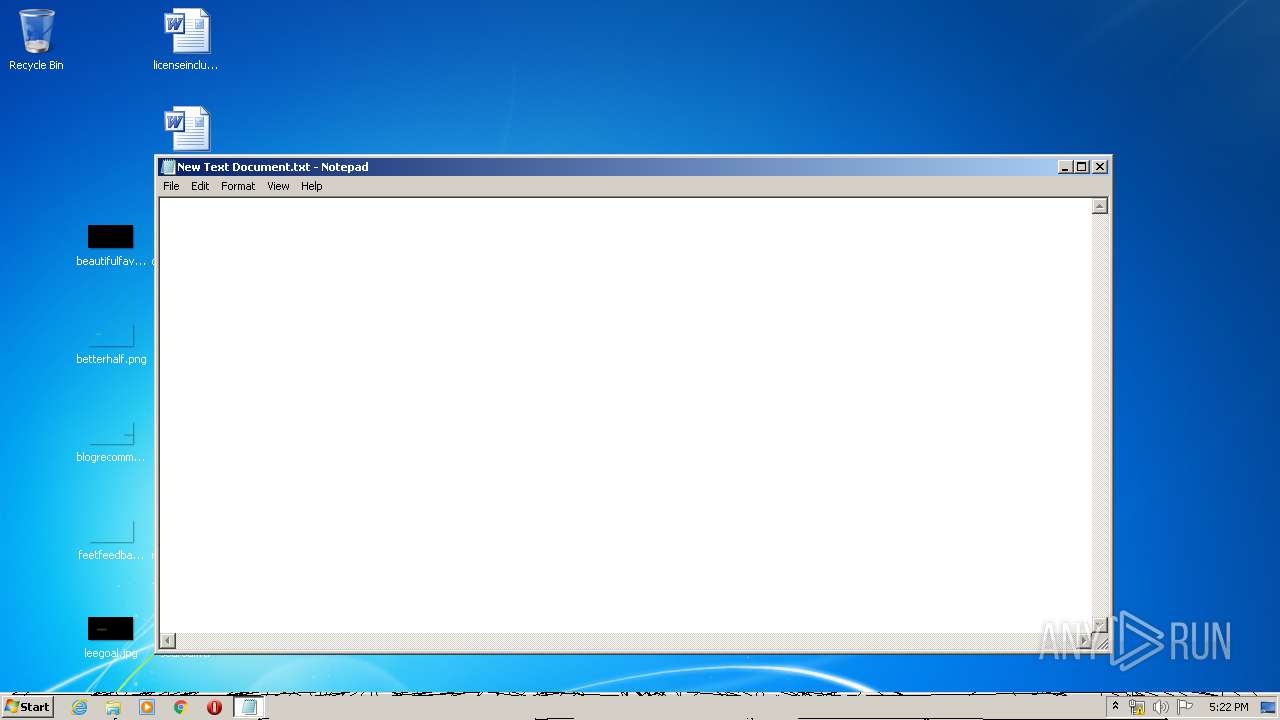
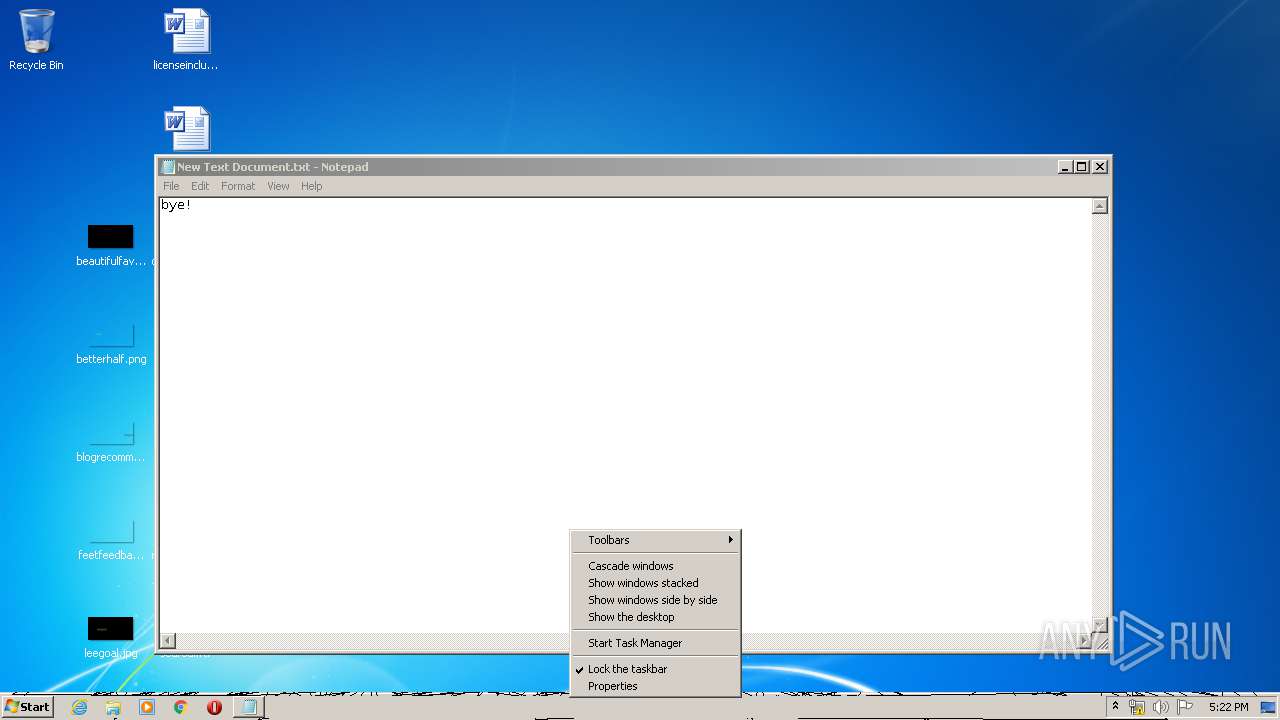
Manual execution by user
- taskmgr.exe (PID: 2852)
- rundll32.exe (PID: 2296)
- NOTEPAD.EXE (PID: 2848)
- taskmgr.exe (PID: 3308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (90.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:03:19 16:16:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Mar-2008 15:16:58 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Mar-2008 15:16:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005DEC | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.00937 |
.data | 0x00007000 | 0x00000B88 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00008000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.29004 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.83659 | 36 | Unicode (UTF 16LE) | UNKNOWN | RT_GROUP_ICON |
30001 | 2.67657 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 2.32506 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
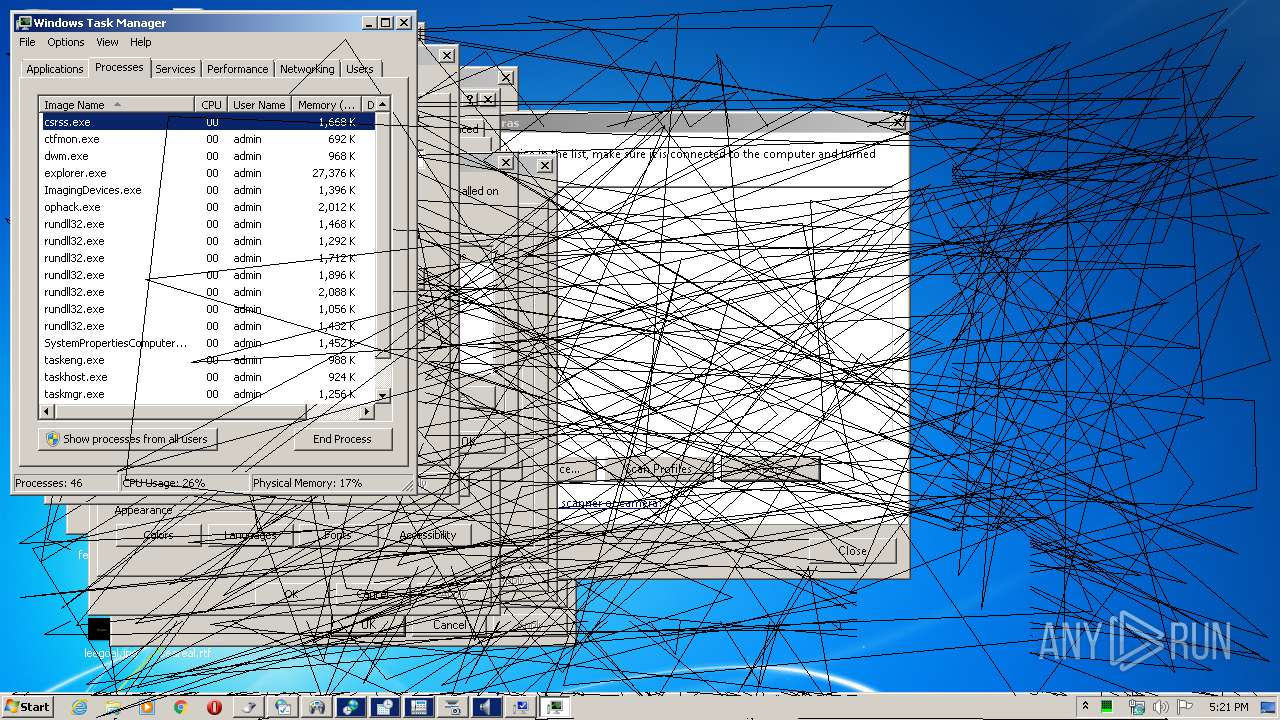
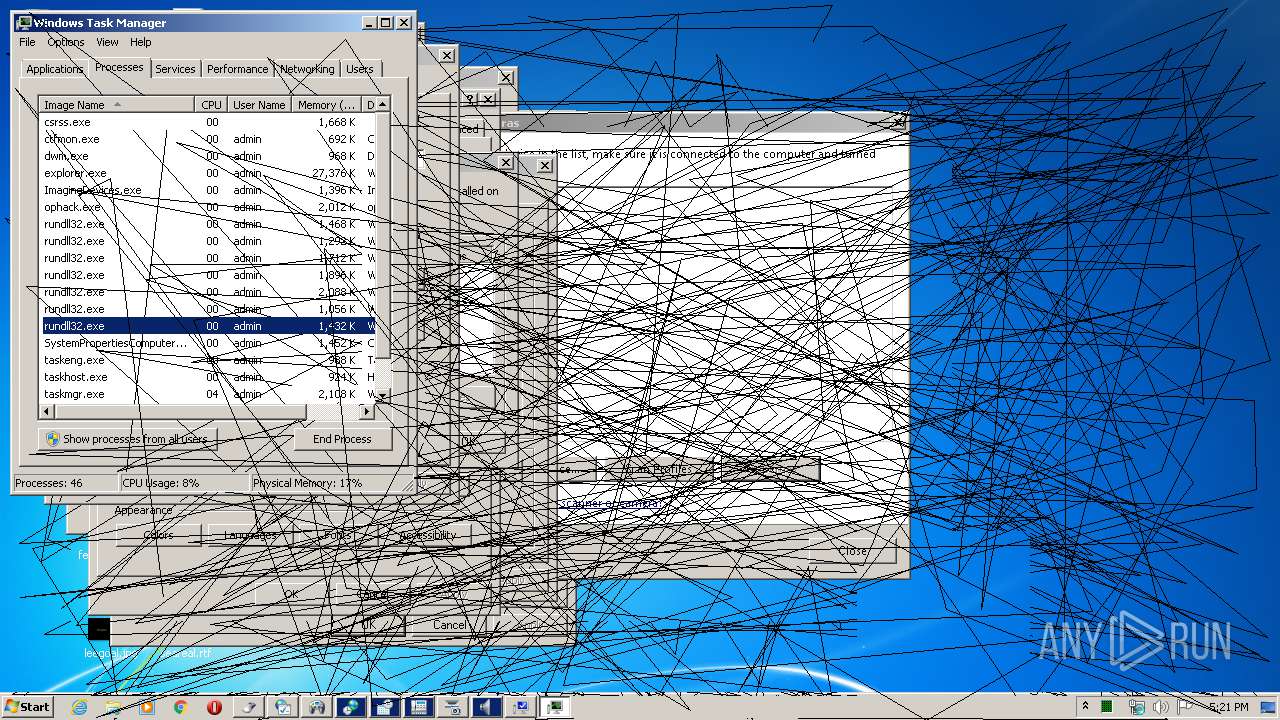
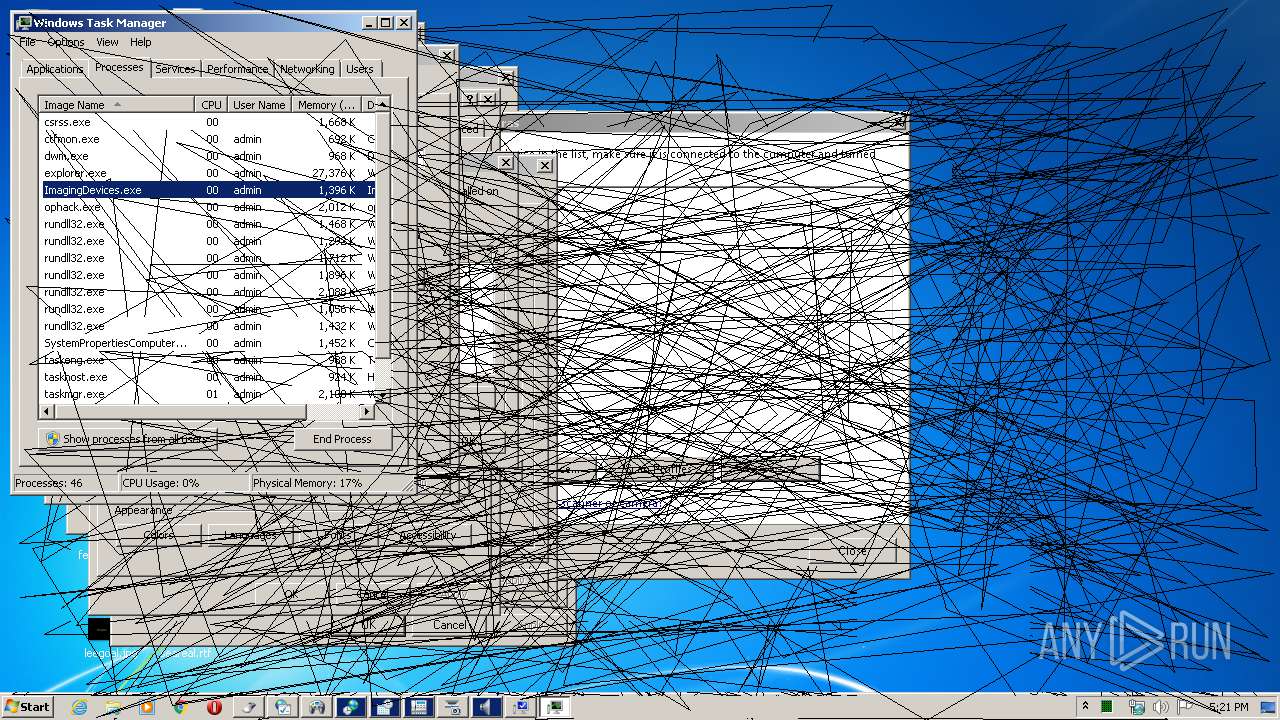
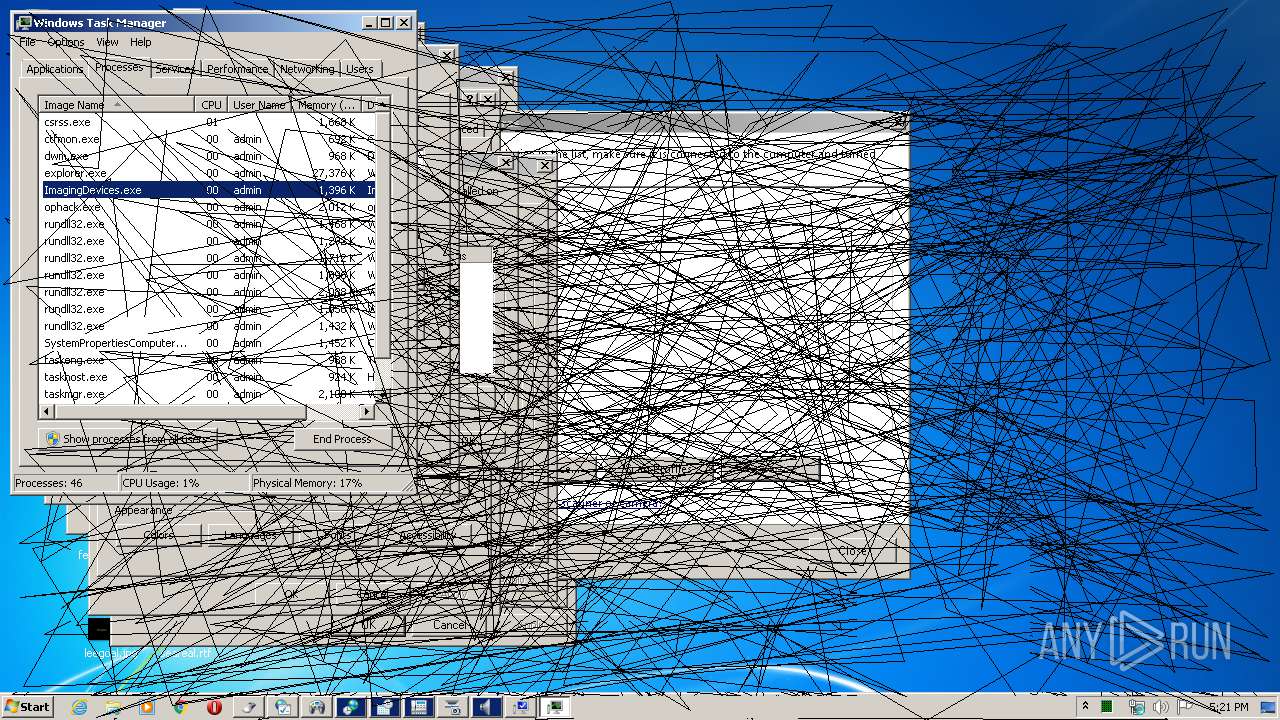
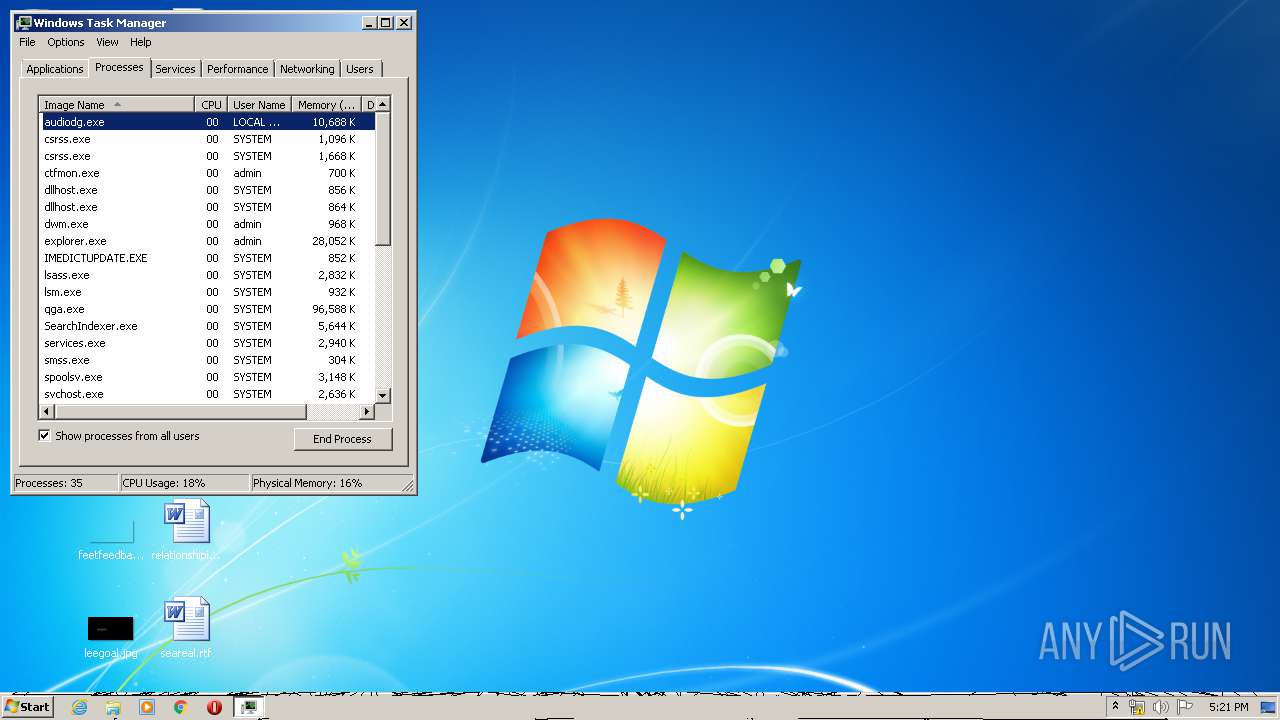
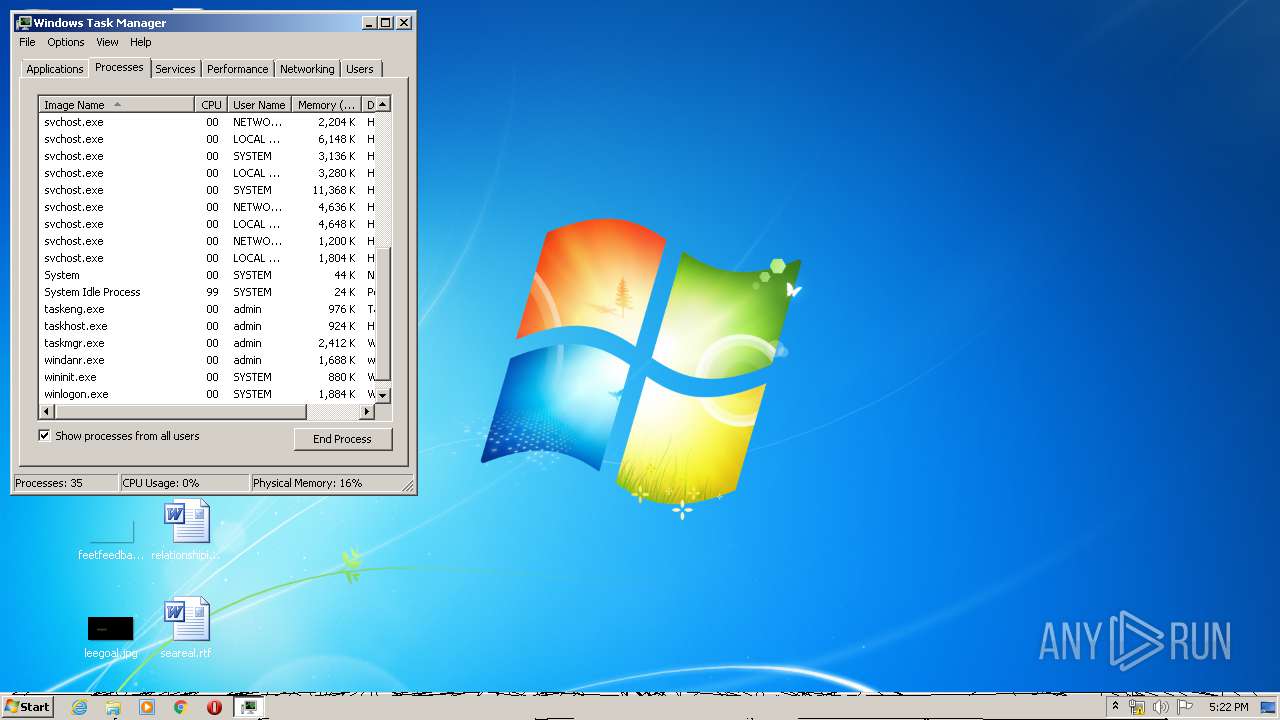
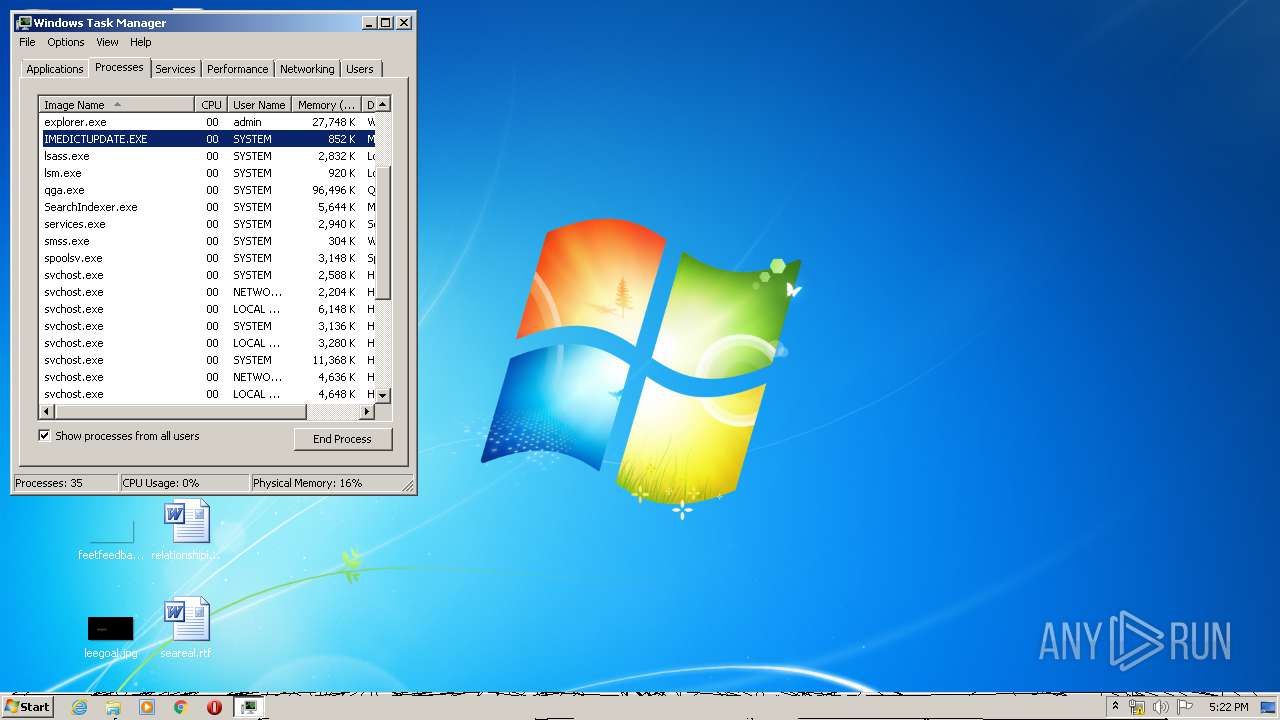
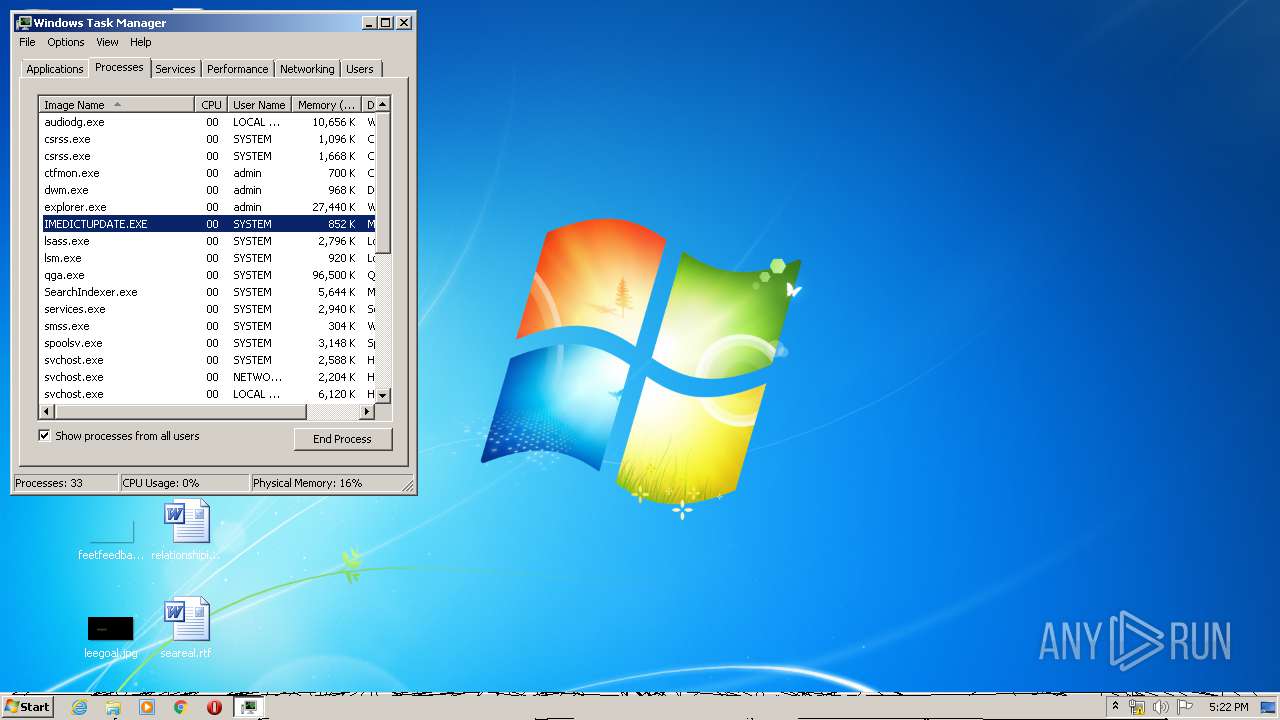
Total processes
84
Monitored processes
35
Malicious processes
1
Suspicious processes
0
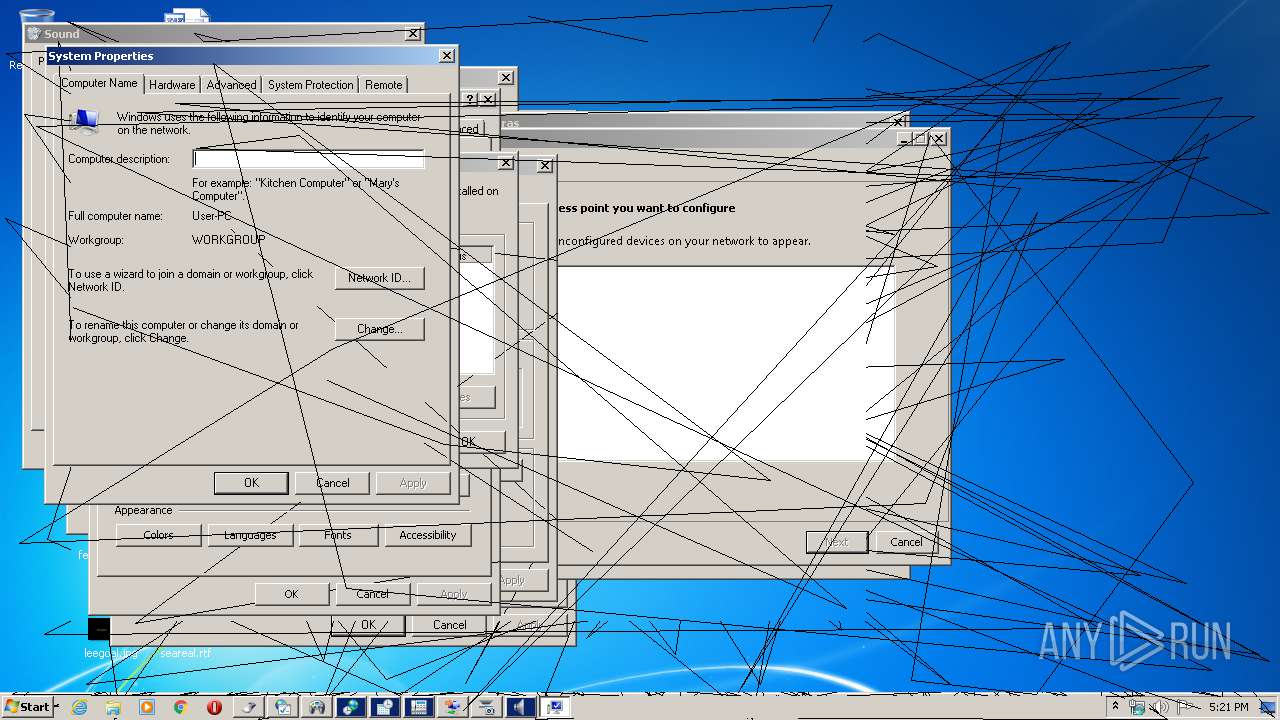
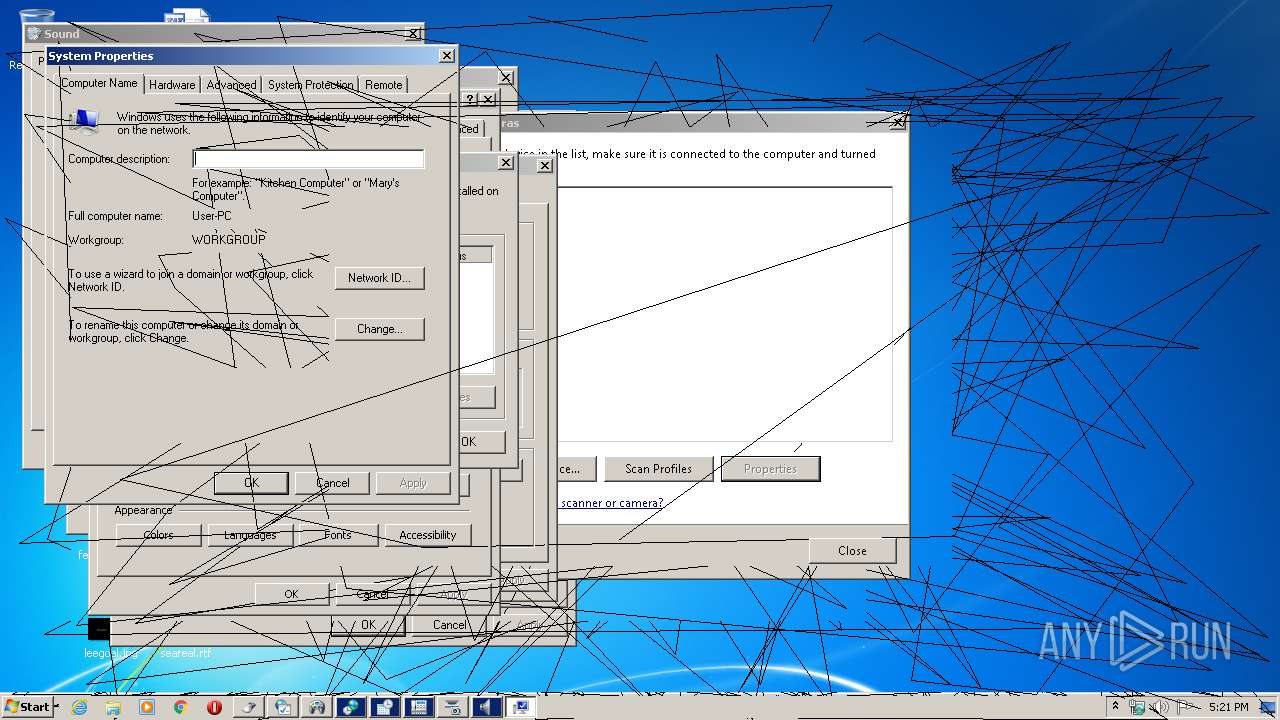
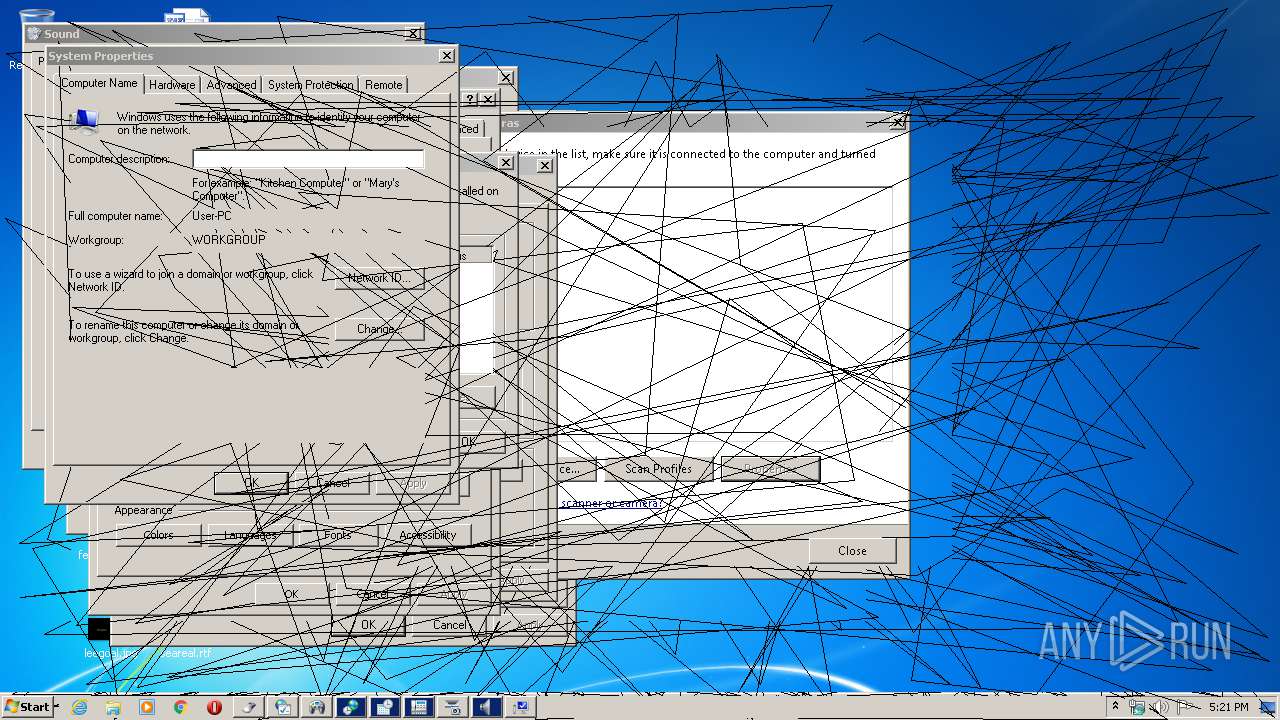
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
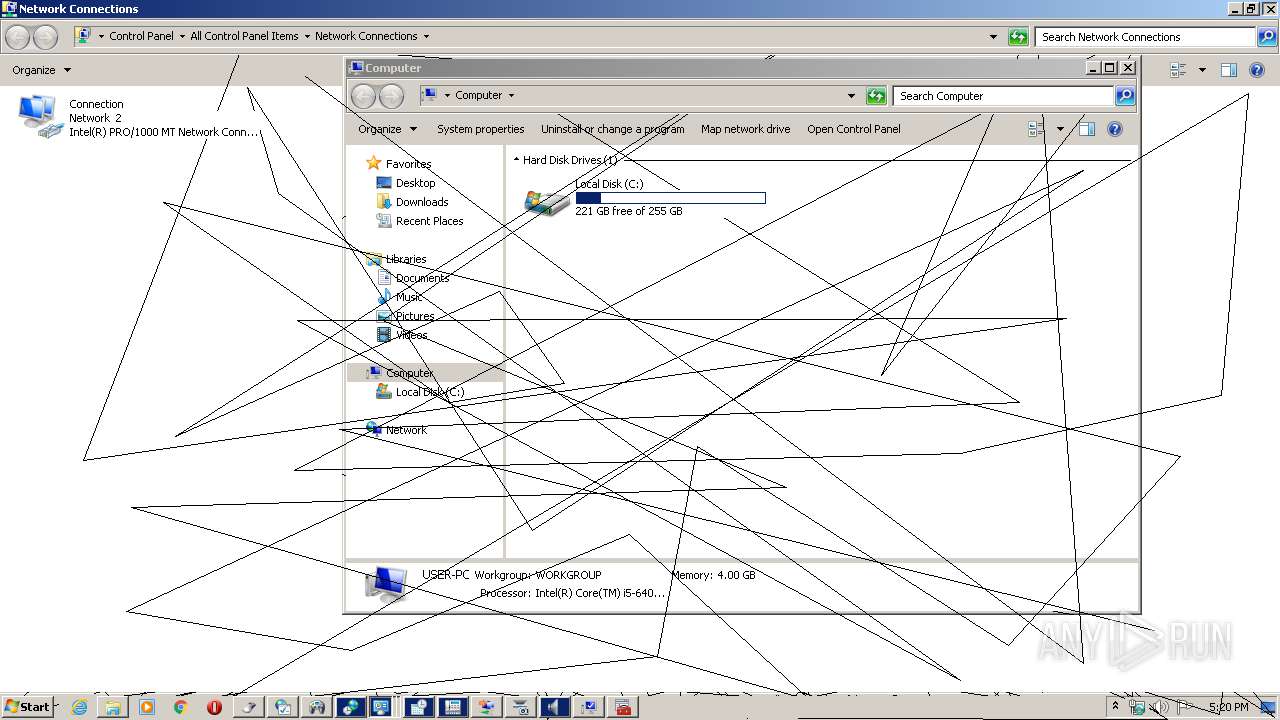
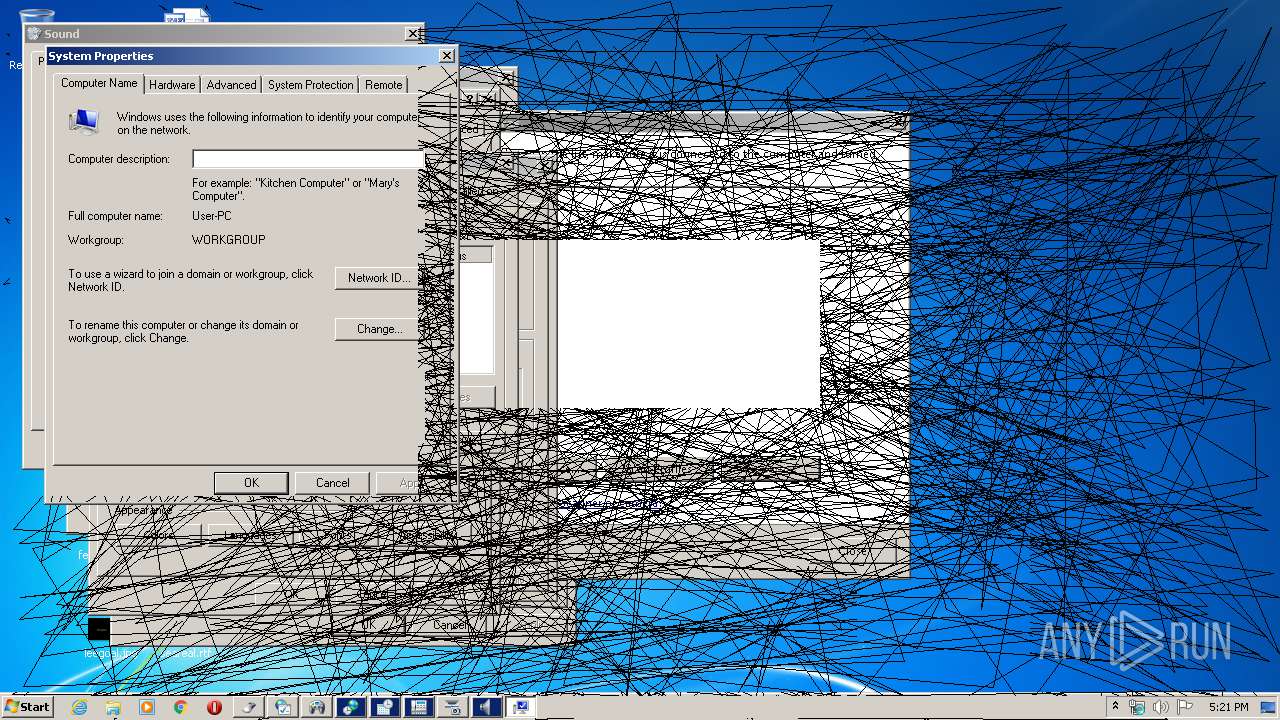
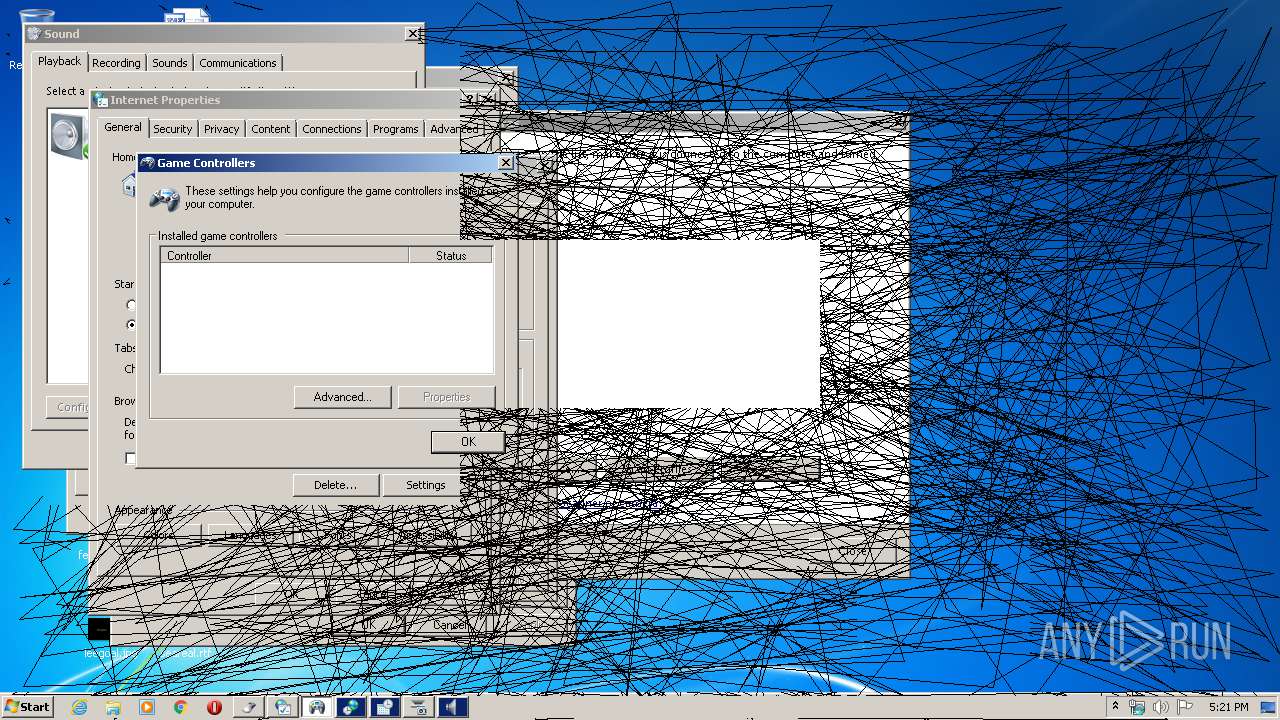
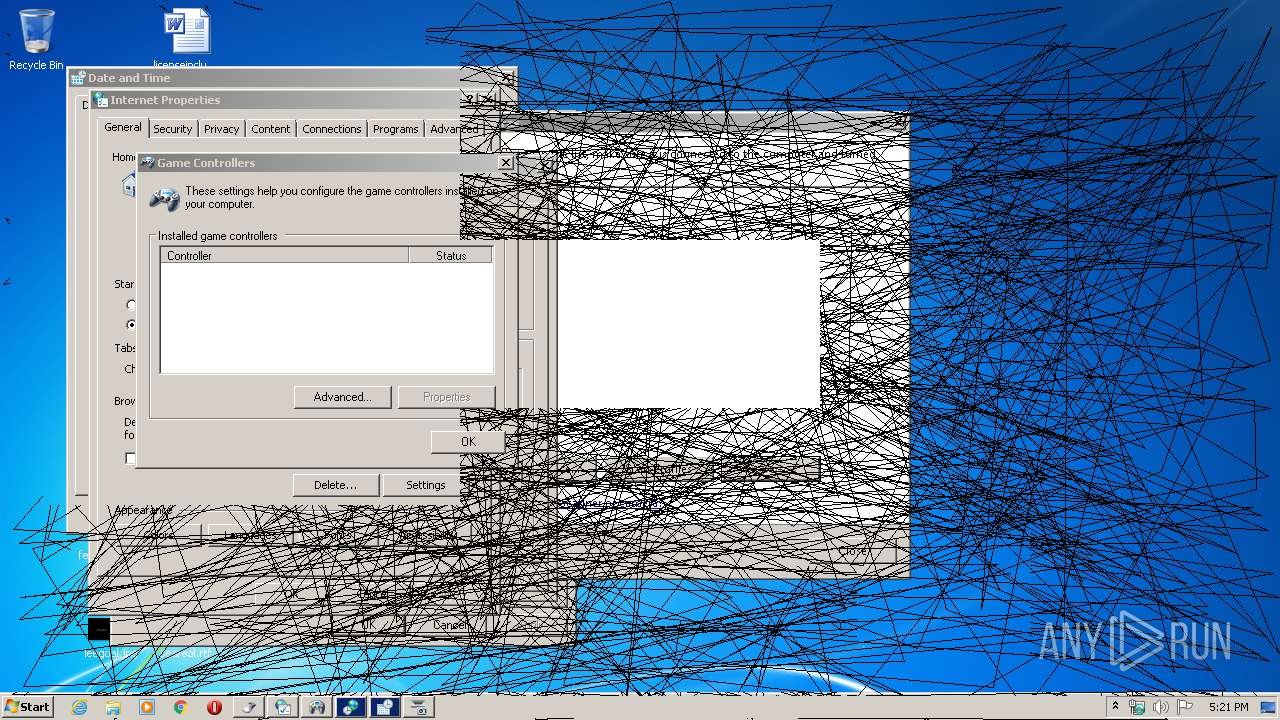
| 116 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL joy.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
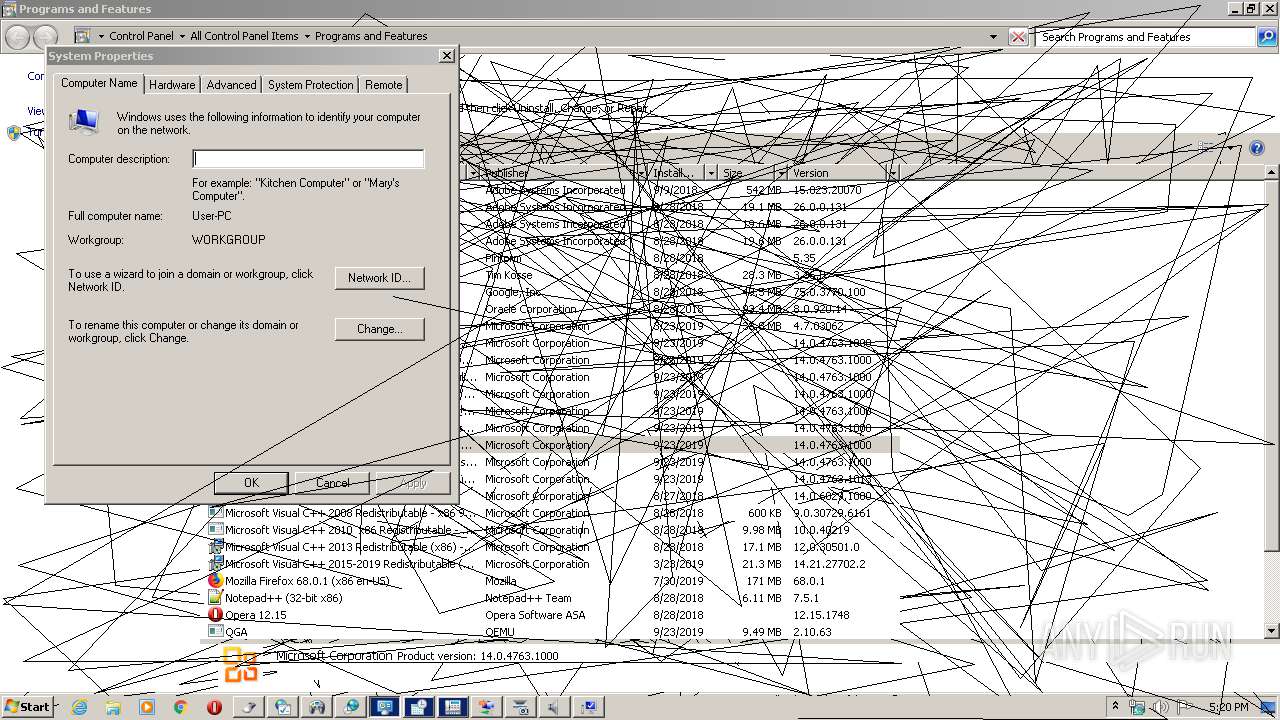
| 640 | "C:\Windows\System32\SystemPropertiesComputerName.exe" | C:\Windows\System32\SystemPropertiesComputerName.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change Computer Settings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
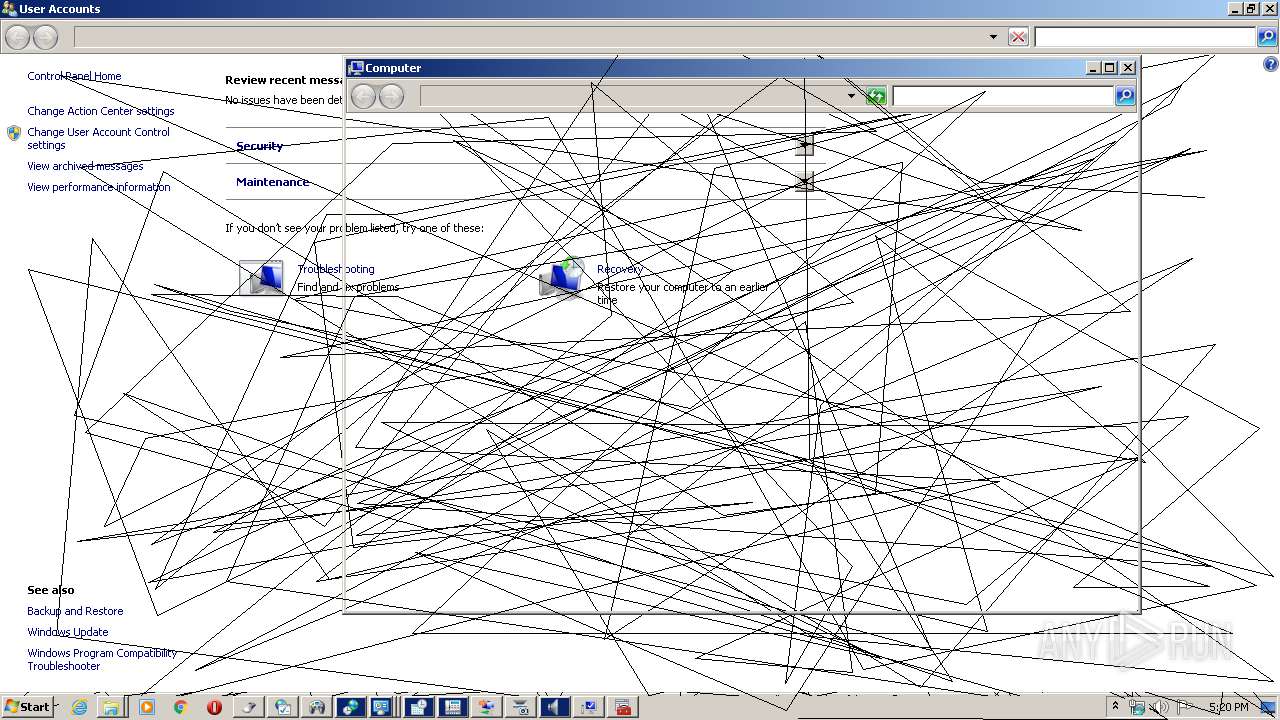
| 724 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL netsetup.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
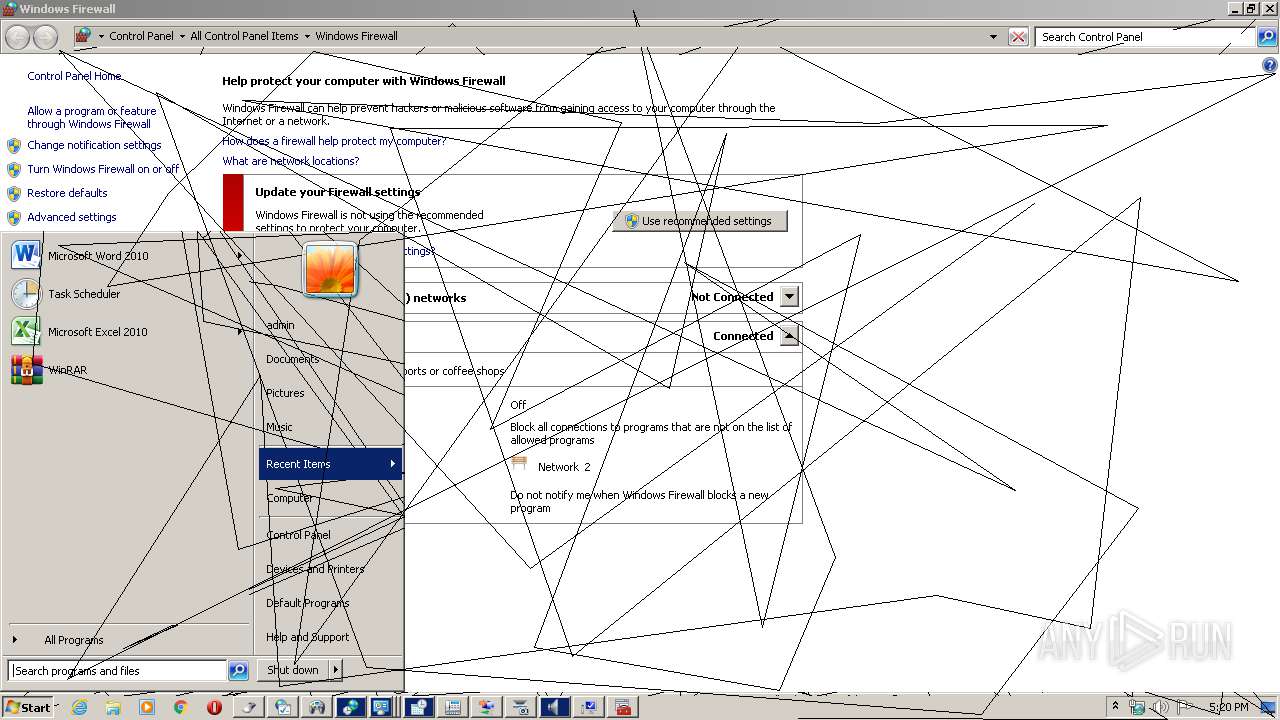
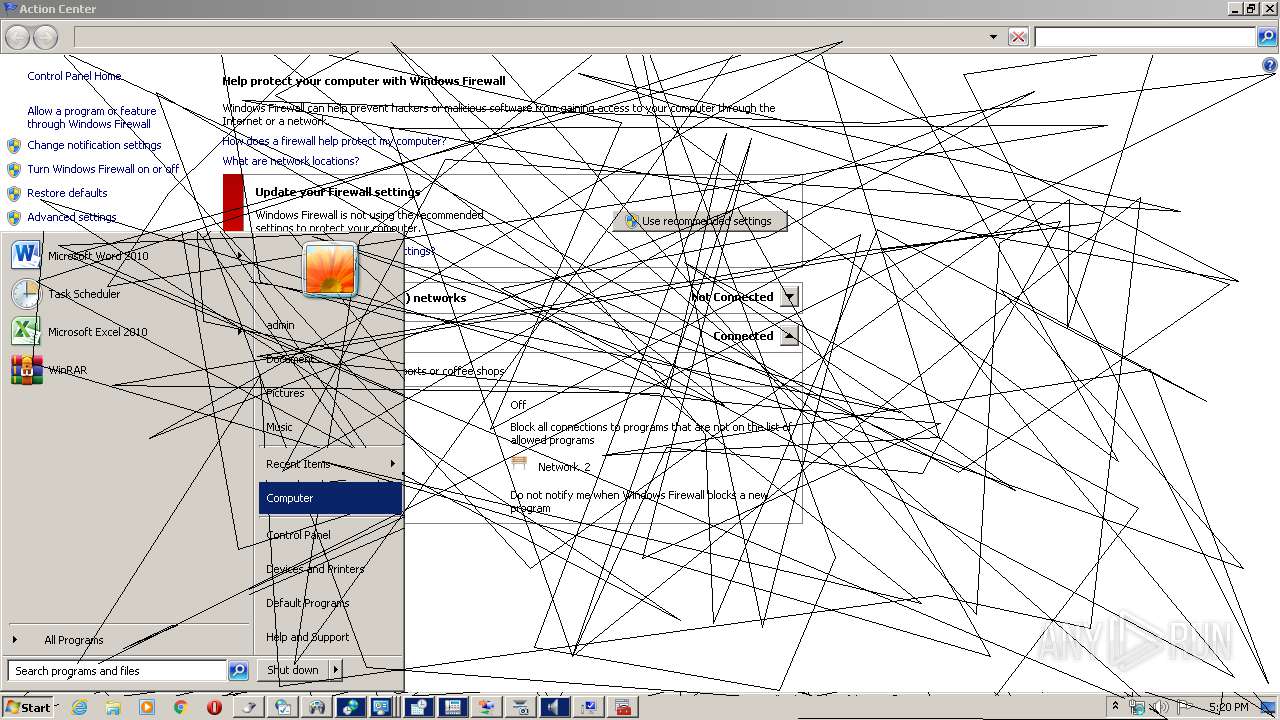
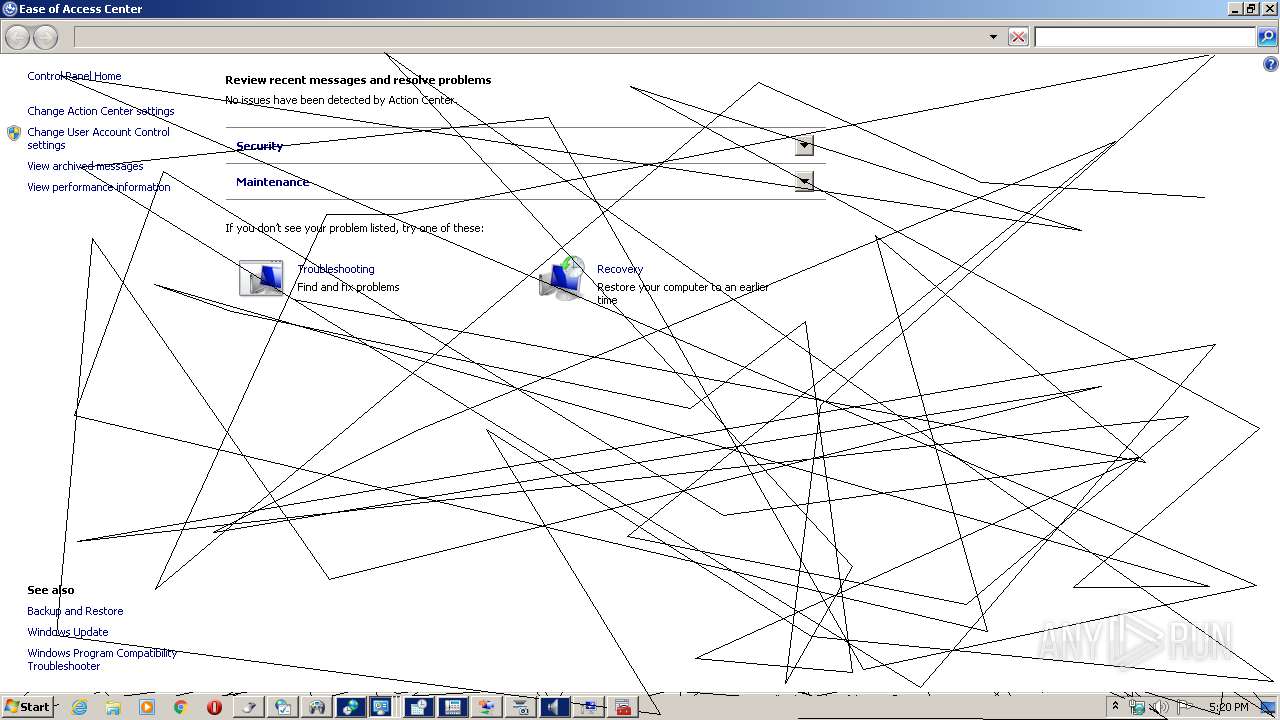
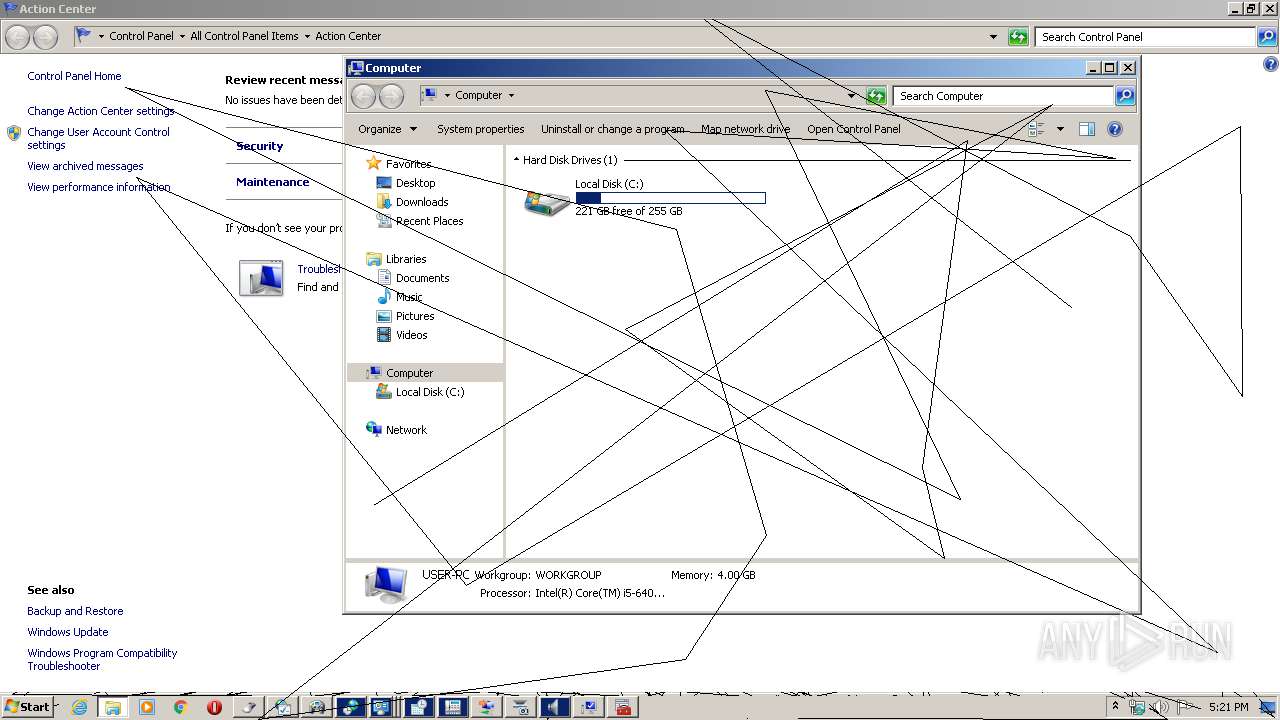
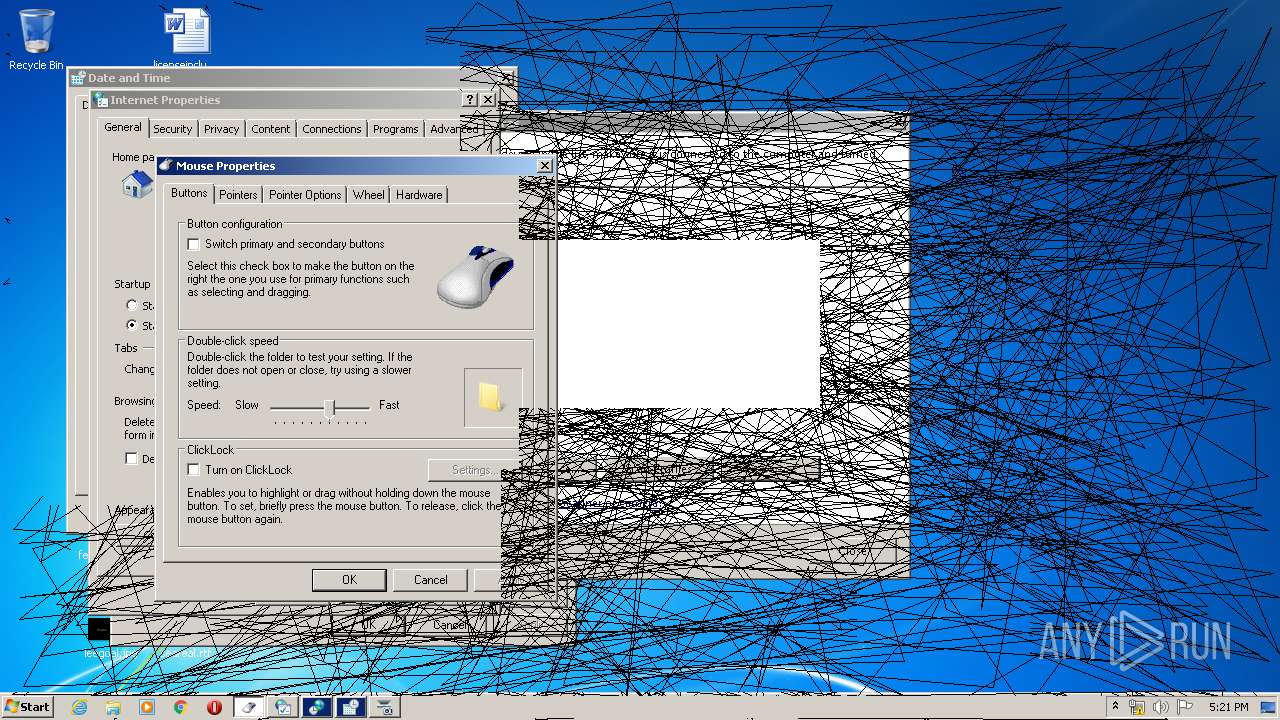
| 872 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL wscui.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
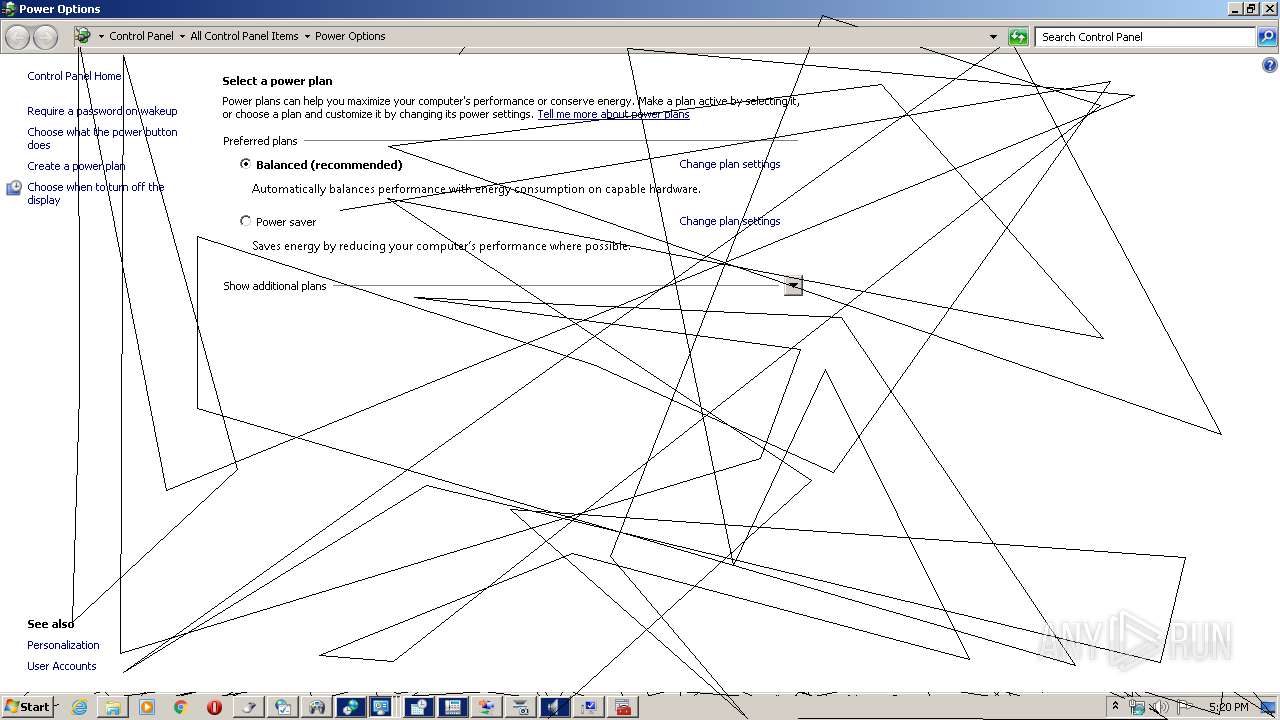
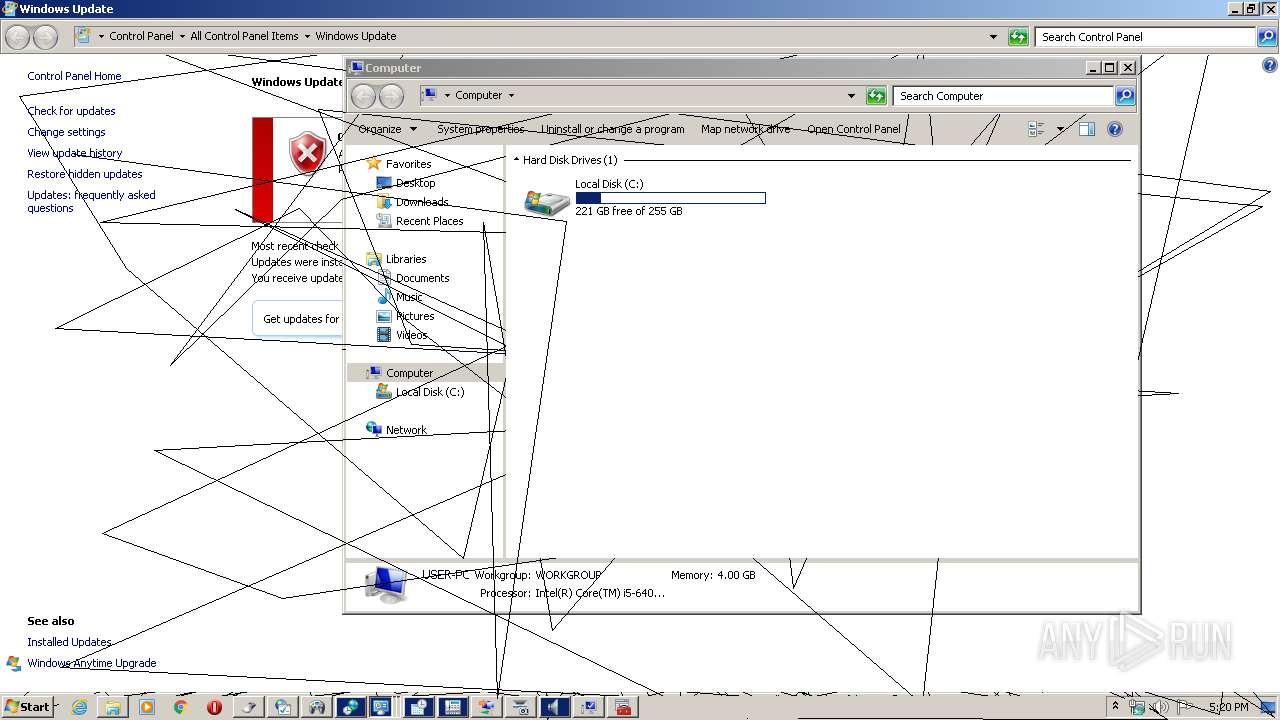
| 1084 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL wuaucpl.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\devmgmt.msc | C:\Windows\system32\mmc.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL telephon.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL access.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "C:\Windows\System32\rundll32.exe" Shell32.dll,Control_RunDLL hdwwiz.cpl | C:\Windows\System32\rundll32.exe | — | ophack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\devmgmt.msc | C:\Windows\system32\mmc.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 030
Read events
966
Write events
62
Delete events
2
Modification events
| (PID) Process: | (2424) ophack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\lnkfile |
| Operation: | delete value | Name: | IsShortcut |
Value: | |||
| (PID) Process: | (2424) ophack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open\command |
| Operation: | write | Name: | |
Value: RunDll32.exe | |||
| (PID) Process: | (2424) ophack.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\MAIN\FeatureControl\FEATURE_LOCALMACHINE_LOCKDOWN |
| Operation: | write | Name: | IExplorer |
Value: 0 | |||
| (PID) Process: | (1868) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2424) ophack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2424) ophack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1868) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {D555645E-D4F8-4C29-A827-D93C859C4F2A} {000214E6-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000006ACAA79BC22ED601 | |||
| (PID) Process: | (2892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @Display.dll,-1 |
Value: Display | |||
| (PID) Process: | (2892) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @Display.dll,-300 |
Value: Screen Resolution | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | ophack.exe | C:\Users\admin\AppData\Local\Temp\~DF09501DF2B36DF6E2.TMP | binary | |
MD5:2C887583160B6B5FA4FA0C954A41E559 | SHA256:4BEB5B2C63DC903C9ADBE828F09E6D360B03B68A9622170B059068A769C74F8B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report