| File name: | runw.exe |
| Full analysis: | https://app.any.run/tasks/74347c25-a543-44d0-8ae9-5363f235c18c |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 10:57:44 |
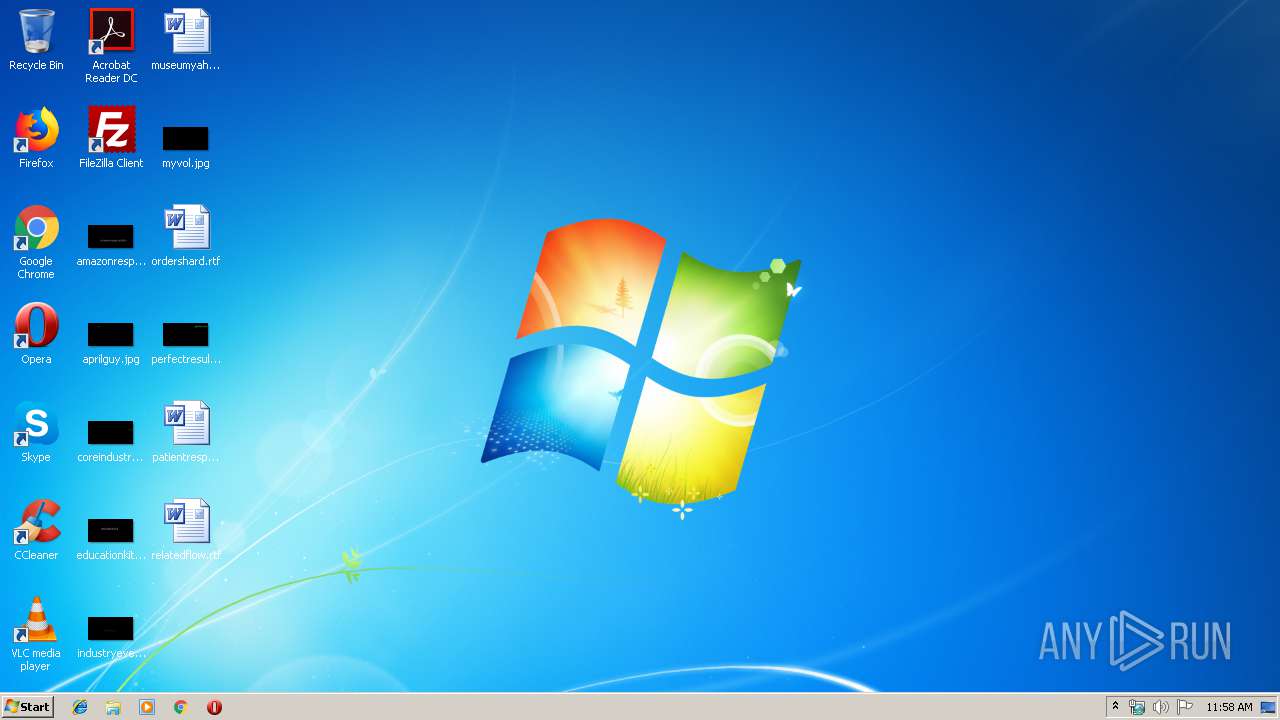
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3F71174DAA6EF5867707DEE3821CEDE0 |
| SHA1: | D16208C4F71E5132535A16E50A8EB492836FA5C6 |
| SHA256: | C1A739B7105704DBB94153F93C6D6588920D40385D65A973CA10A1B6682CE88E |
| SSDEEP: | 6144:bjkiMzx9uJSW/NbNTBZT3Zm5V0V3ZXti:vUzx9y/1NTLU5WVpdi |
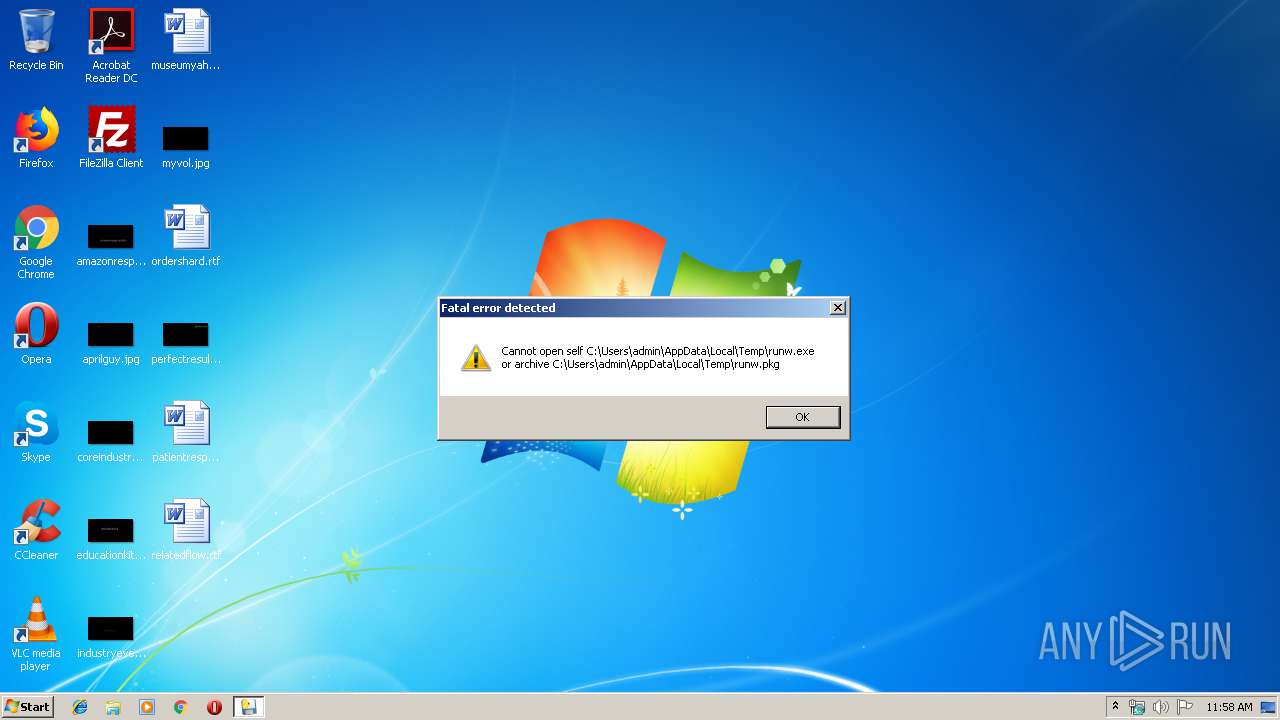
MALICIOUS
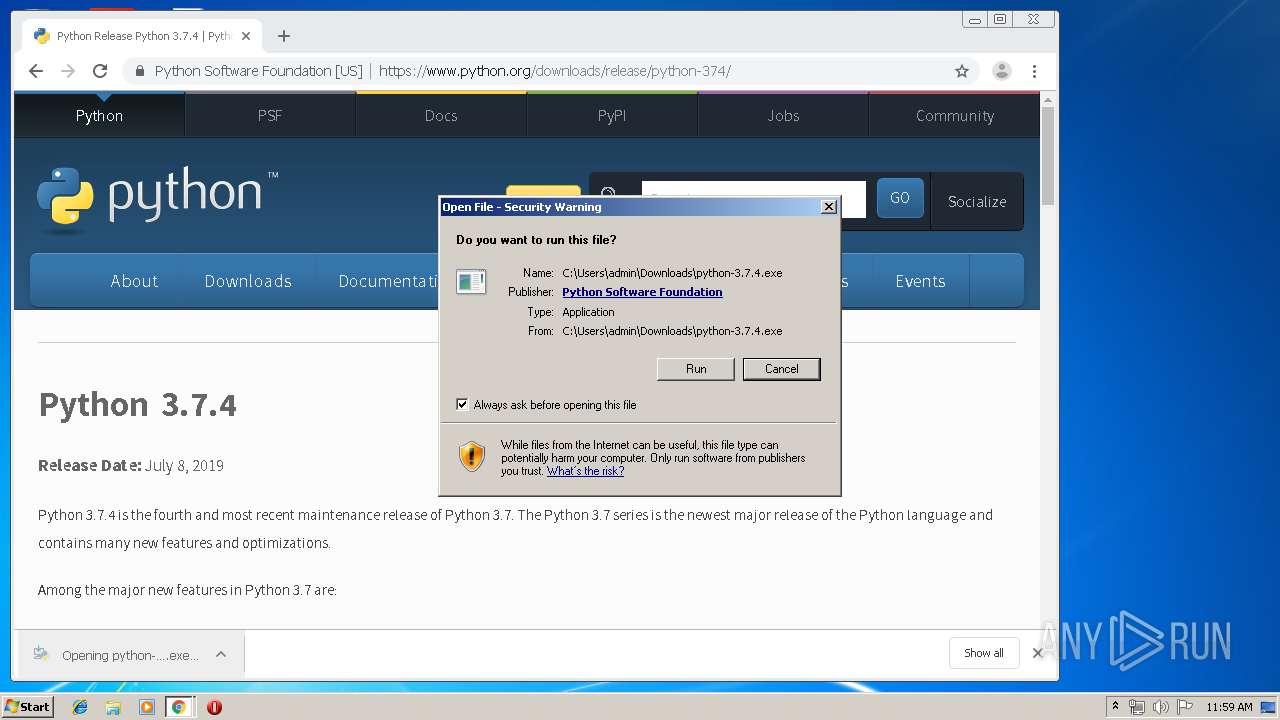
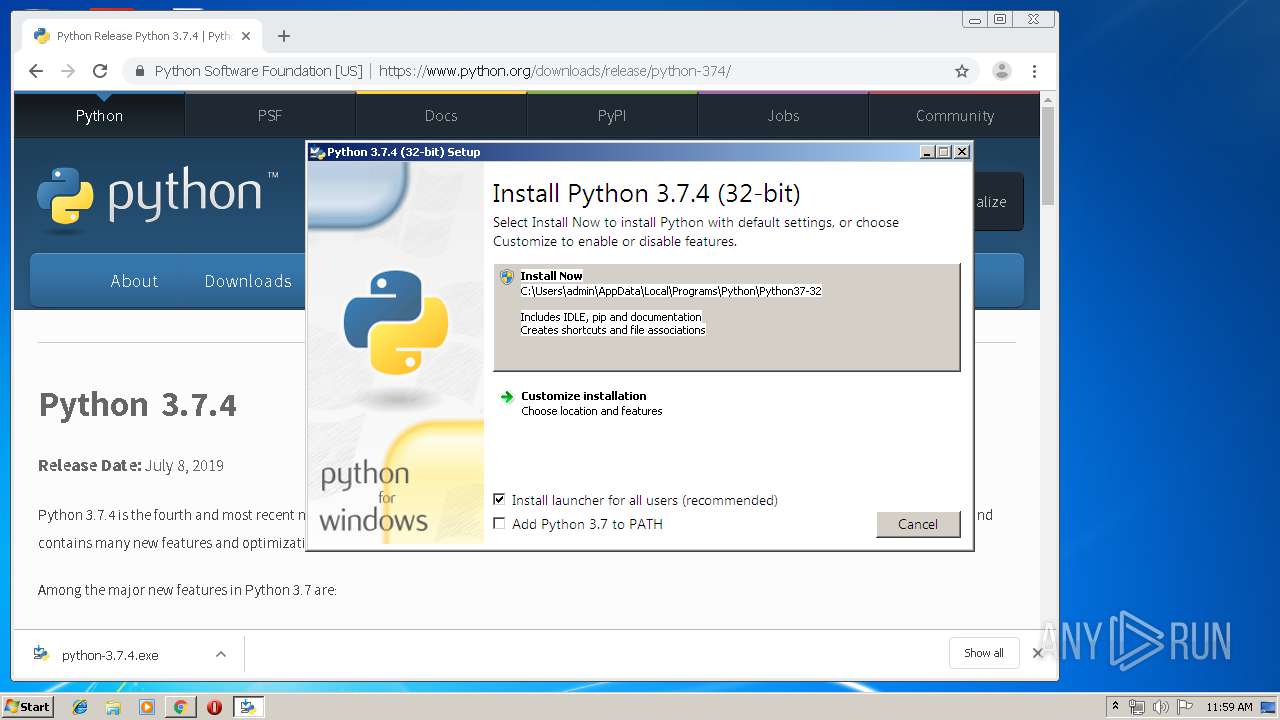
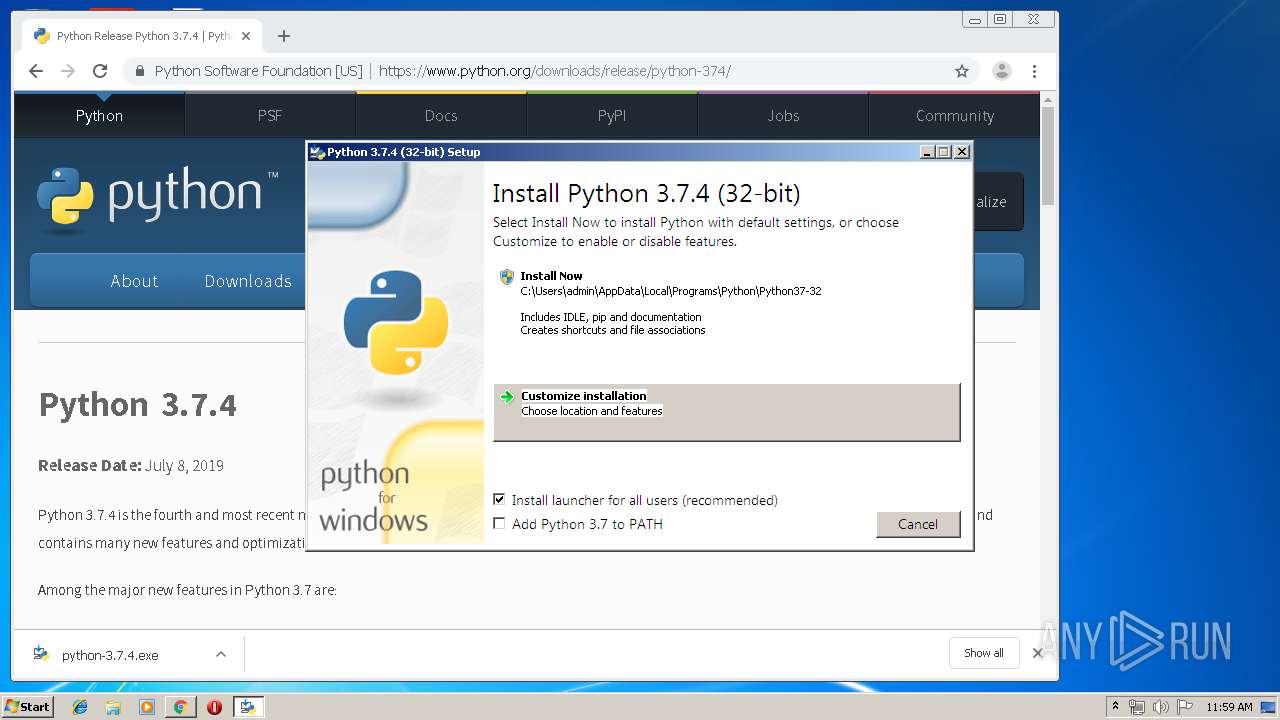
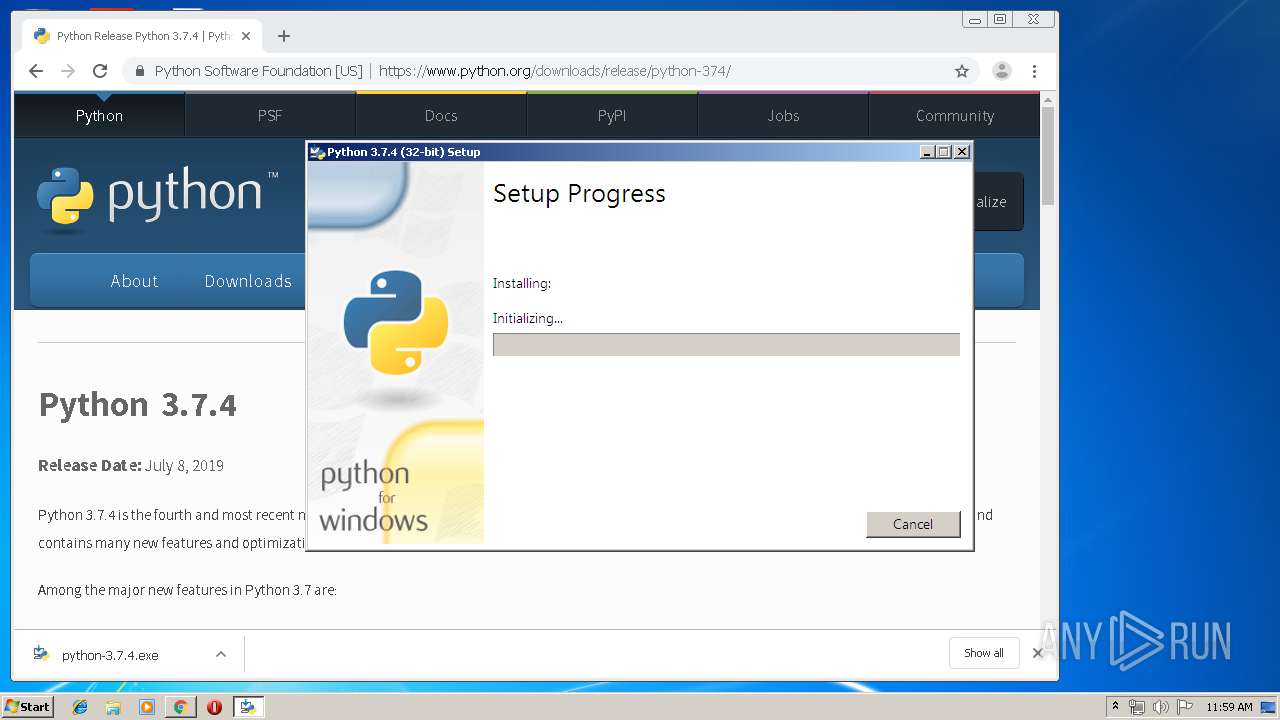
Application was dropped or rewritten from another process
- python-3.7.4.exe (PID: 2840)
- python-3.7.4.exe (PID: 3820)
- python-3.7.4.exe (PID: 3420)
- python.exe (PID: 2172)
Loads dropped or rewritten executable
- python-3.7.4.exe (PID: 3820)
- python.exe (PID: 2172)
Changes the autorun value in the registry
- python-3.7.4.exe (PID: 3820)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2252)
Executable content was dropped or overwritten
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2252)
- python-3.7.4.exe (PID: 2840)
- python-3.7.4.exe (PID: 3820)
- msiexec.exe (PID: 3756)
- python-3.7.4.exe (PID: 3420)
- python.exe (PID: 2172)
Starts itself from another location
- python-3.7.4.exe (PID: 3820)
Executed as Windows Service
- vssvc.exe (PID: 3736)
Searches for installed software
- python-3.7.4.exe (PID: 3420)
Executed via COM
- DrvInst.exe (PID: 3468)
Creates a software uninstall entry
- python-3.7.4.exe (PID: 3820)
Creates files in the user directory
- msiexec.exe (PID: 3756)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3756)
Creates COM task schedule object
- msiexec.exe (PID: 3756)
Creates files in the Windows directory
- msiexec.exe (PID: 3756)
Loads Python modules
- python.exe (PID: 2172)
INFO
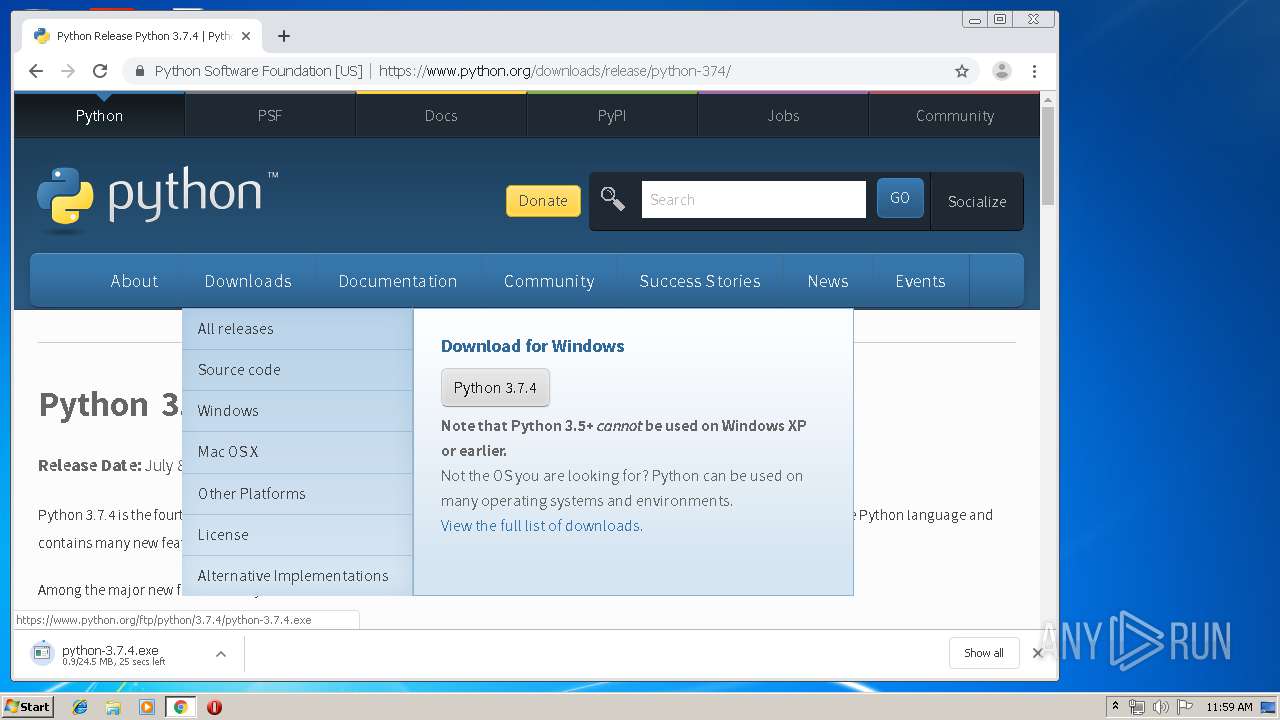
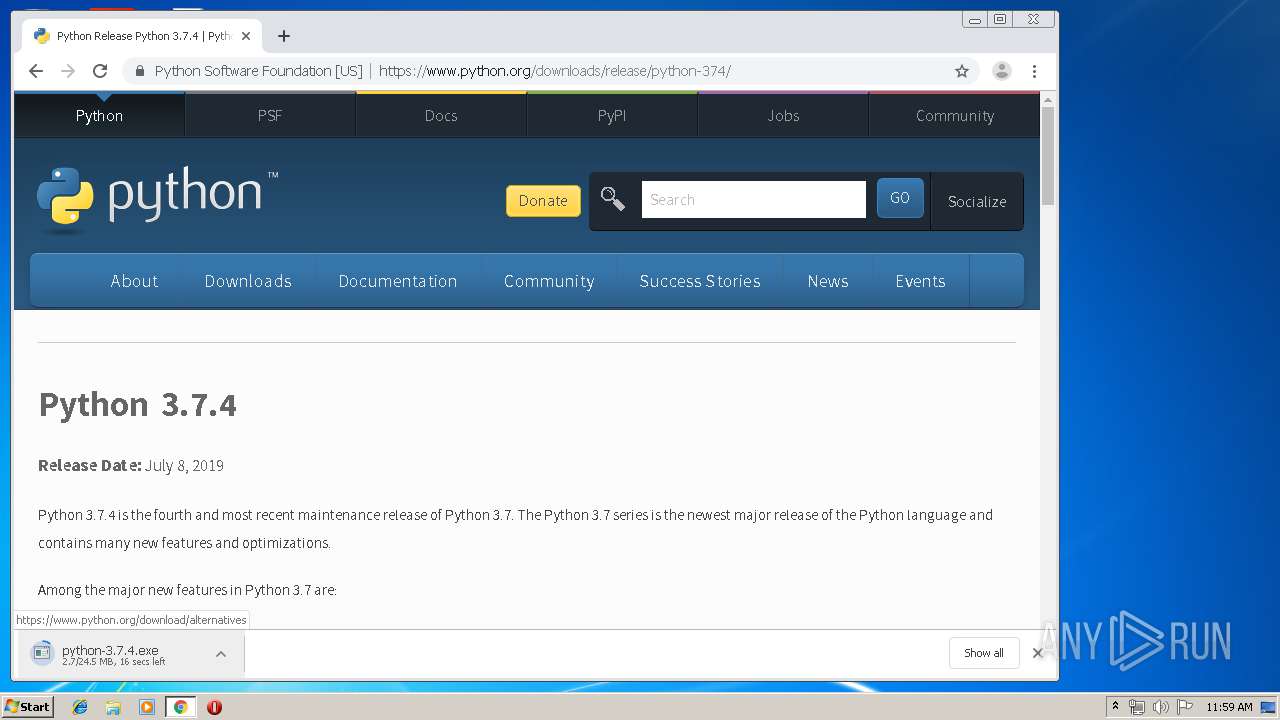
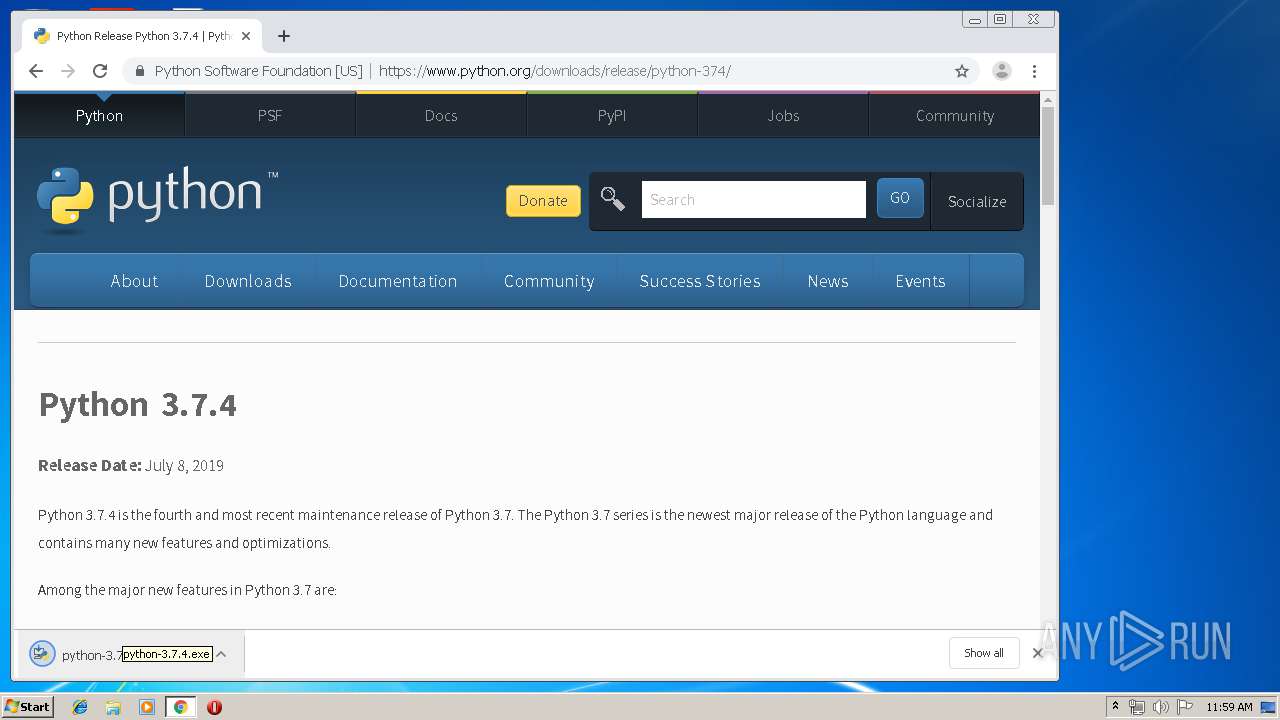
Manual execution by user
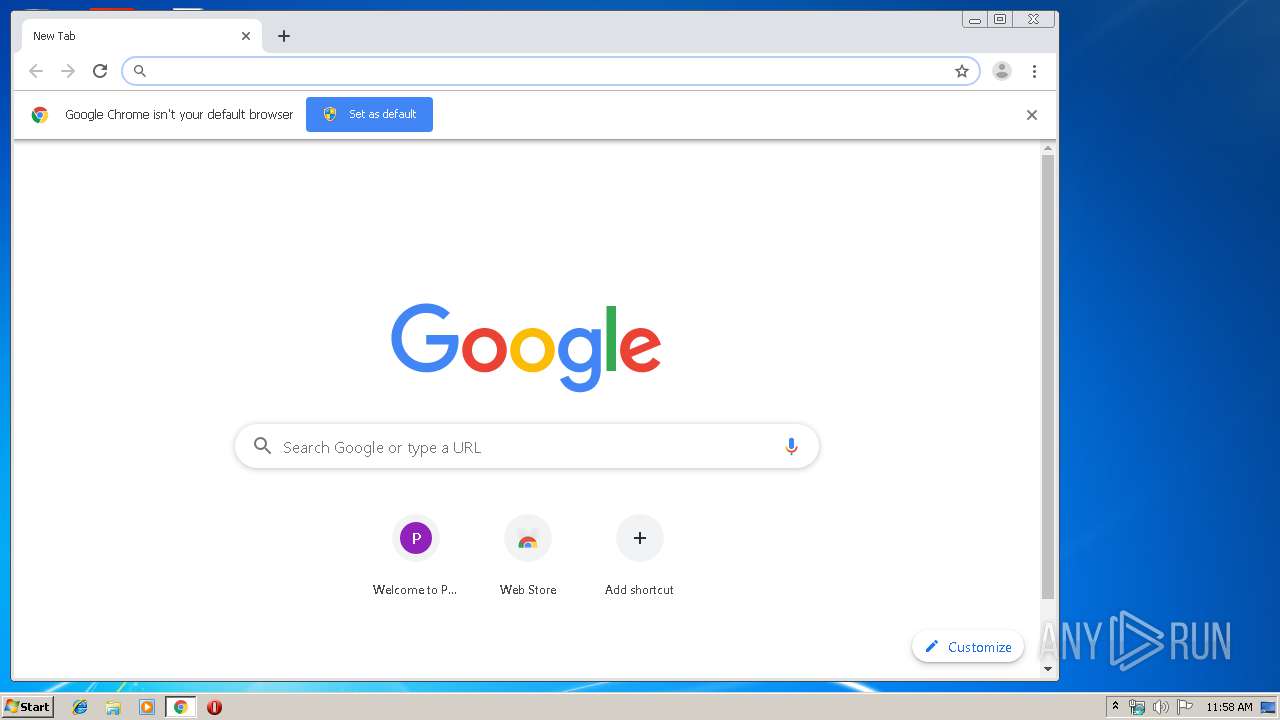
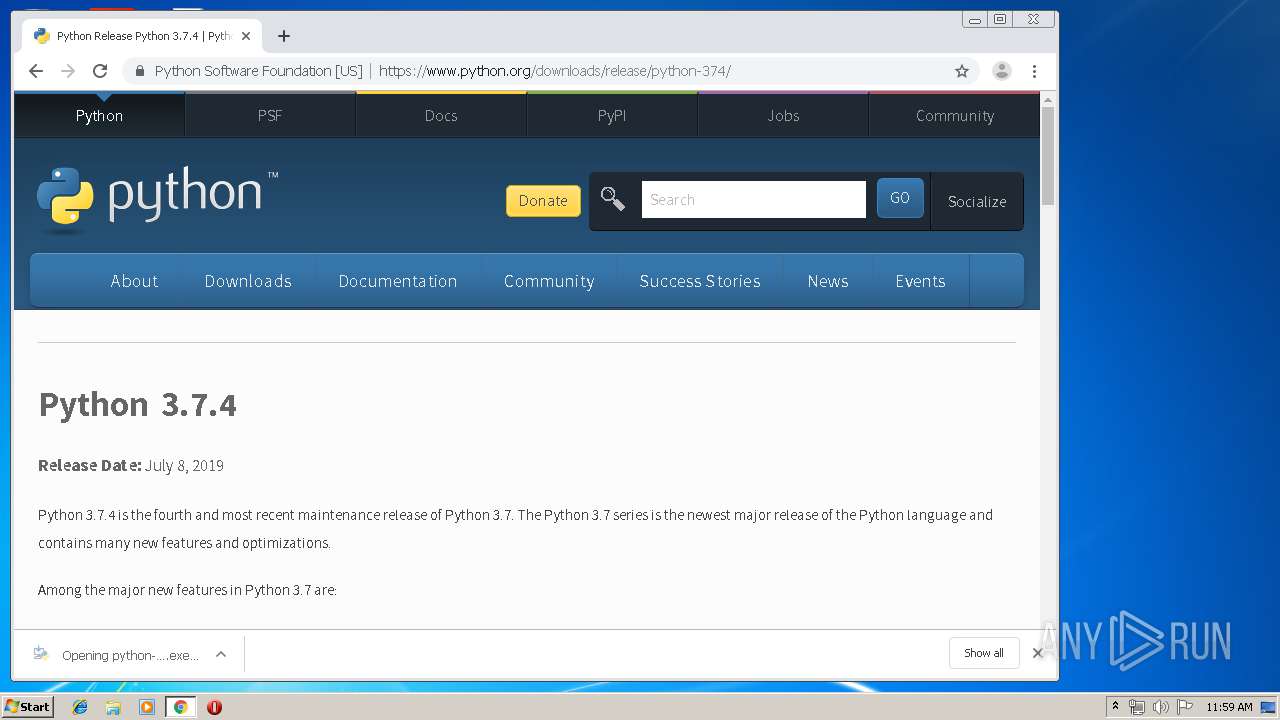
- chrome.exe (PID: 3660)
- chrome.exe (PID: 2252)
Application launched itself
- chrome.exe (PID: 3660)
- chrome.exe (PID: 2252)
- msiexec.exe (PID: 3756)
Reads settings of System Certificates
- chrome.exe (PID: 2844)
Reads Internet Cache Settings
- chrome.exe (PID: 2252)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3736)
Dropped object may contain Bitcoin addresses
- python.exe (PID: 2172)
- msiexec.exe (PID: 3756)
Creates a software uninstall entry
- msiexec.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:23:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 126464 |
| InitializedDataSize: | 173056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7b43 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jul-2019 14:23:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:23:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001ECA4 | 0x0001EE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64533 |
.rdata | 0x00020000 | 0x0000B164 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10043 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92387 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.85181 |
.rsrc | 0x0003C000 | 0x0000EEC8 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.51705 |
.reloc | 0x0004B000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65903 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.15653 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.44895 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
95
Monitored processes
54
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,16911434639137319771,13154736198687653299,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9621035114360744205 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,16911434639137319771,13154736198687653299,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8941298176453348466 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,16911434639137319771,13154736198687653299,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13082783527833794968 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10275112974821688631,5003446986000011917,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9162977029009948819 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,16911434639137319771,13154736198687653299,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16015052690788246996 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Programs\Python\Python37-32\python.exe" -E -s -m ensurepip -U --default-pip | C:\Users\admin\AppData\Local\Programs\Python\Python37-32\python.exe | MsiExec.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.4 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,10275112974821688631,5003446986000011917,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10515768950092496195 --mojo-platform-channel-handle=3356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | C:\Windows\system32\MsiExec.exe -Embedding 742781E92457465CC2C015CB24DBDB52 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,16911434639137319771,13154736198687653299,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17887216284434505413 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 670
Read events
2 395
Write events
5 149
Delete events
126
Modification events
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3660-13211290693677625 |
Value: 259 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
115
Suspicious files
1 066
Text files
4 508
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b4722dec-afb3-4fc6-9aed-2ec319d82024.tmp | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16d016.TMP | text | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF16d055.TMP | text | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
46
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
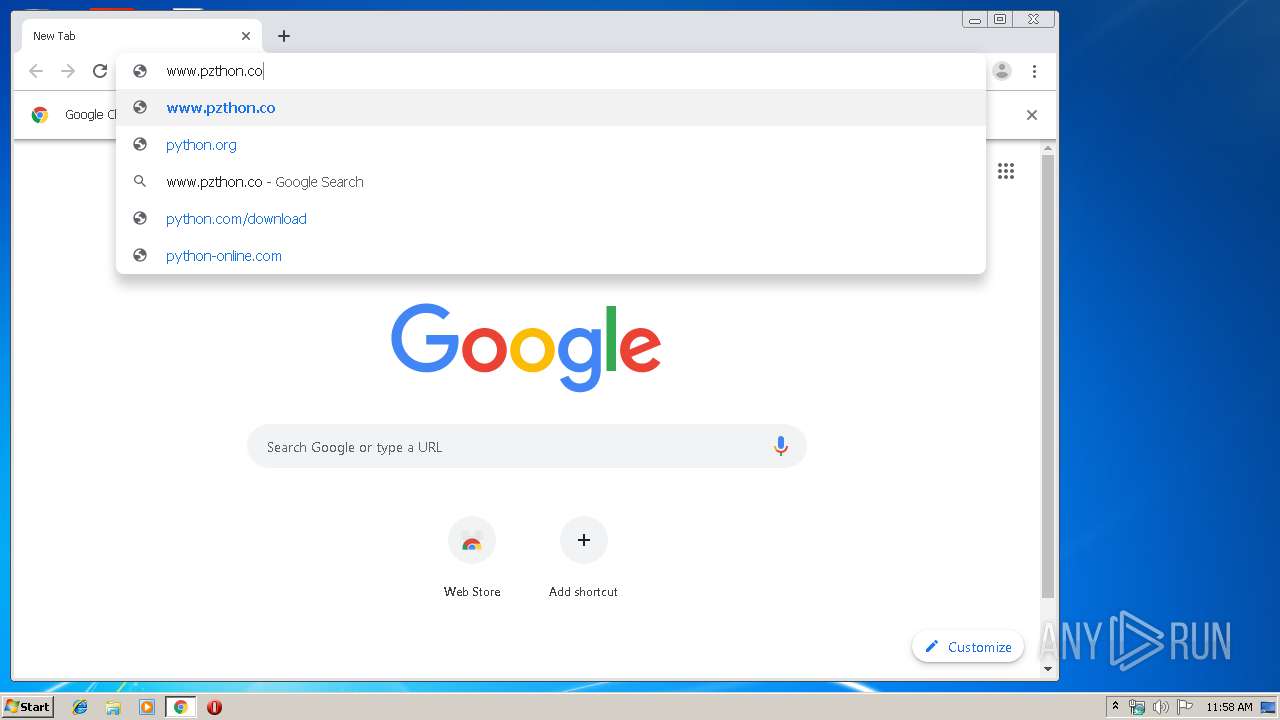
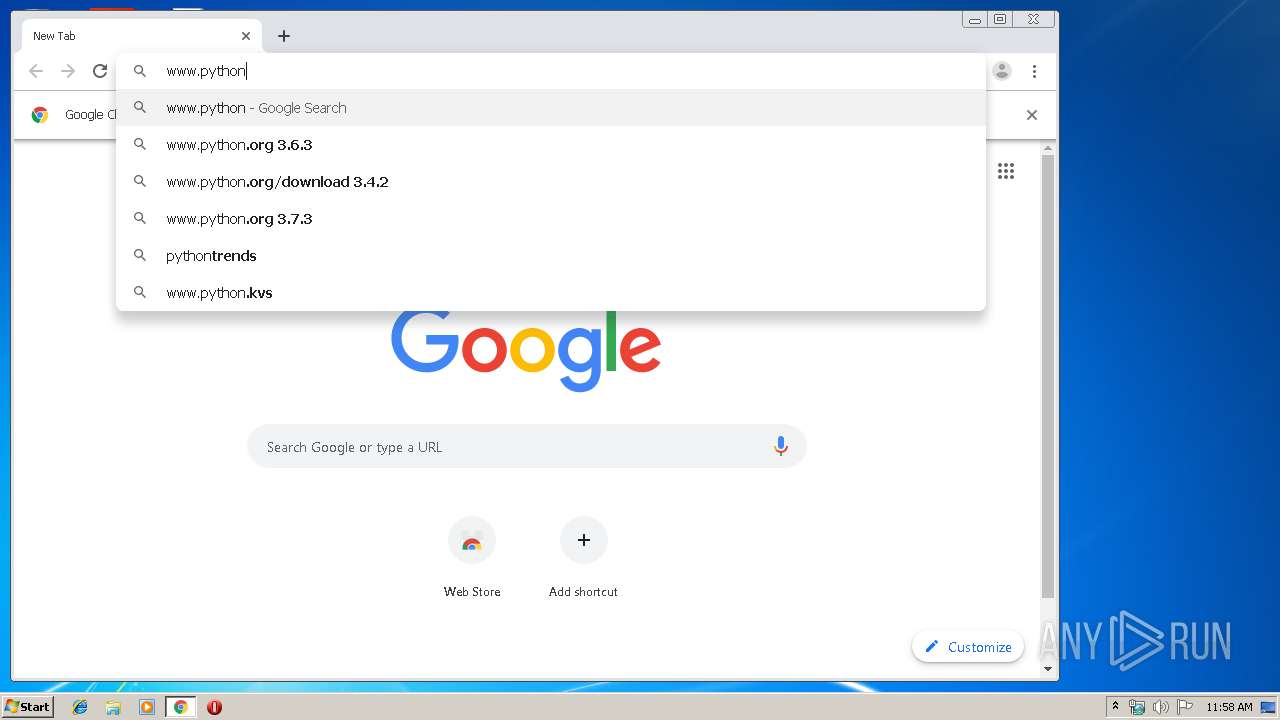
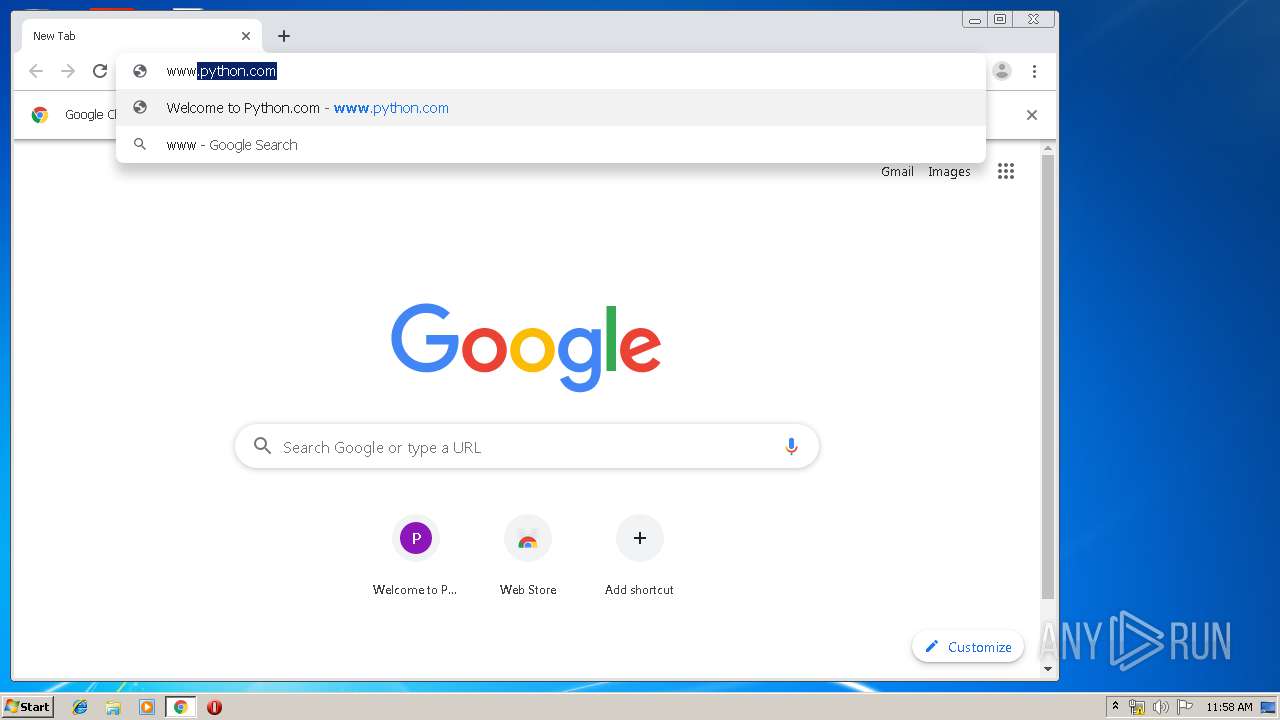
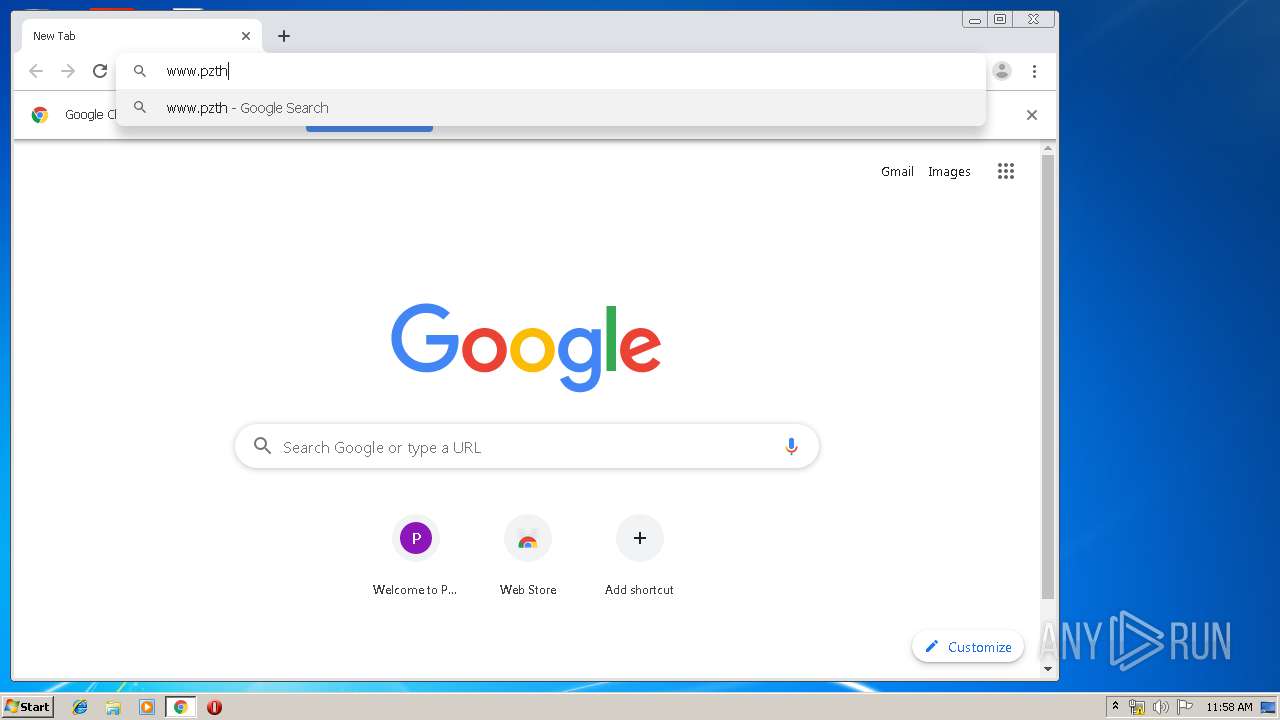
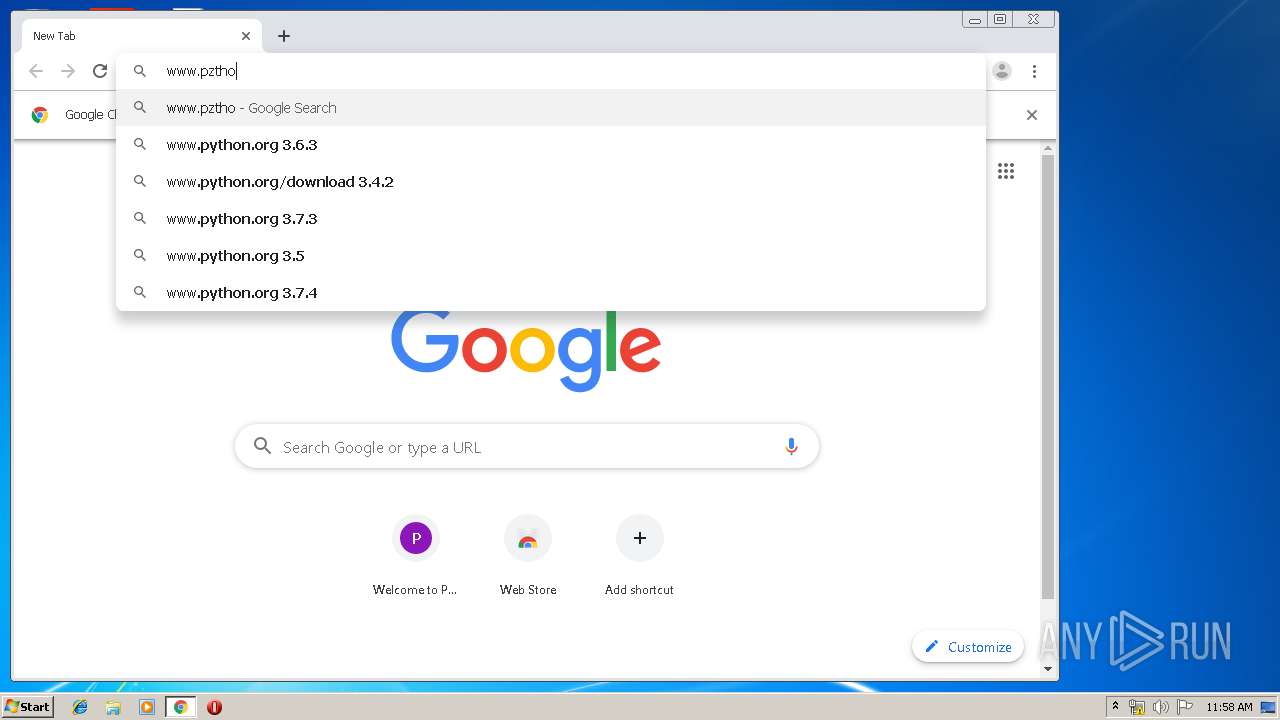
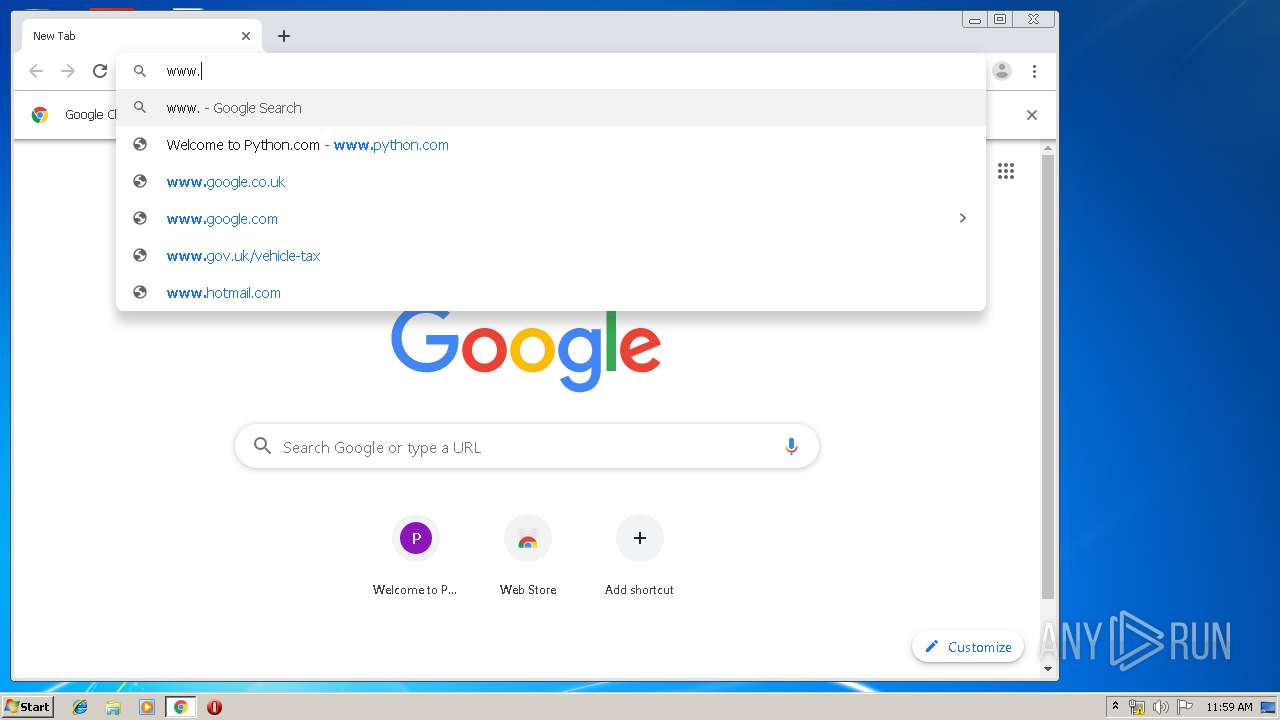
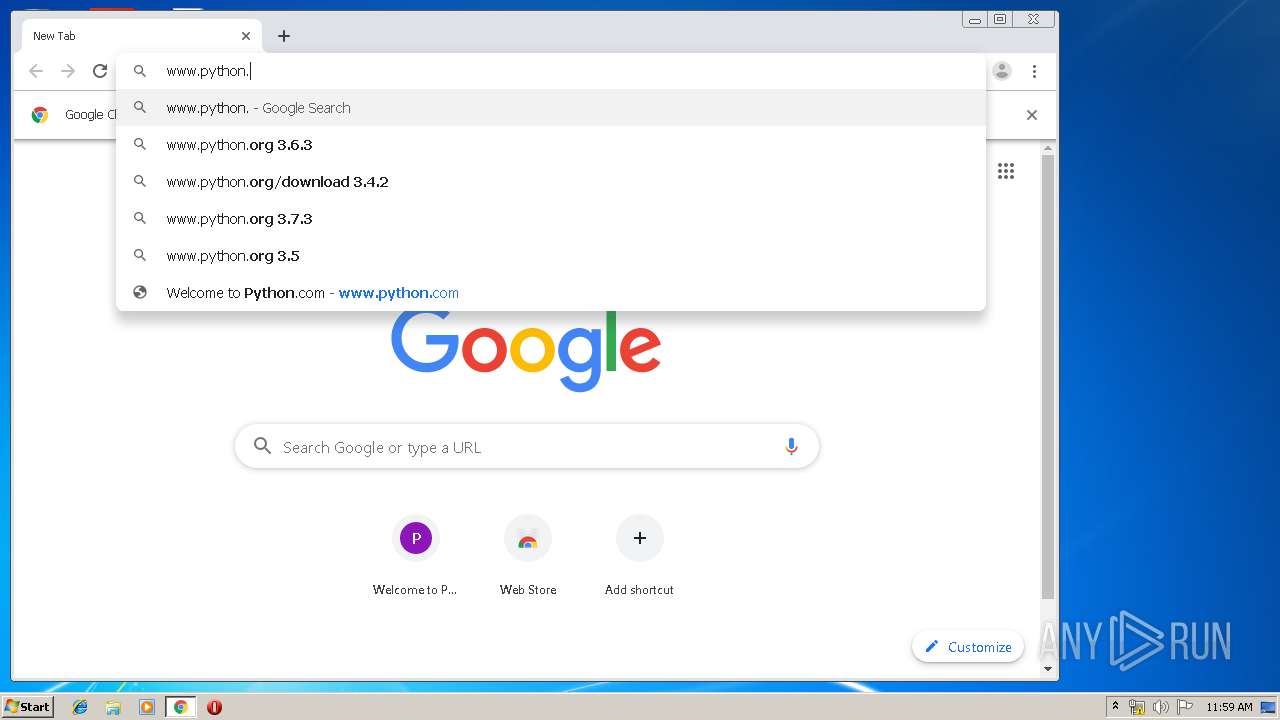
2844 | chrome.exe | GET | 301 | 151.101.0.223:80 | http://www.python.org/ | US | — | — | whitelisted |
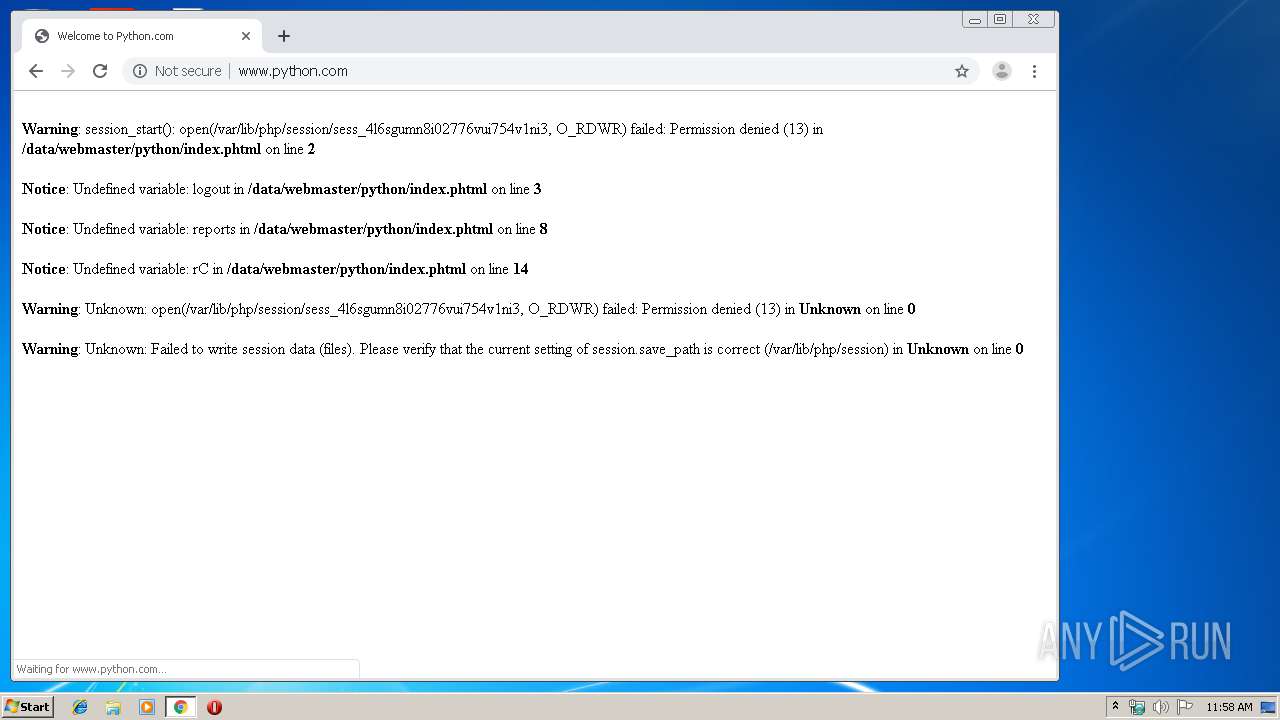
2924 | chrome.exe | GET | 200 | 199.59.88.81:80 | http://www.python.com/ | US | html | 492 b | malicious |
2844 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2924 | chrome.exe | GET | 200 | 74.125.4.167:80 | http://r2---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.117.157&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1566817038&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2924 | chrome.exe | GET | 404 | 199.59.88.81:80 | http://www.python.com/favicon.ico | US | html | 209 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 216.58.210.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 74.125.4.167:80 | r2---sn-aigzrne7.gvt1.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 199.59.88.81:80 | www.python.com | MOJOHOST | US | unknown |
2844 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |