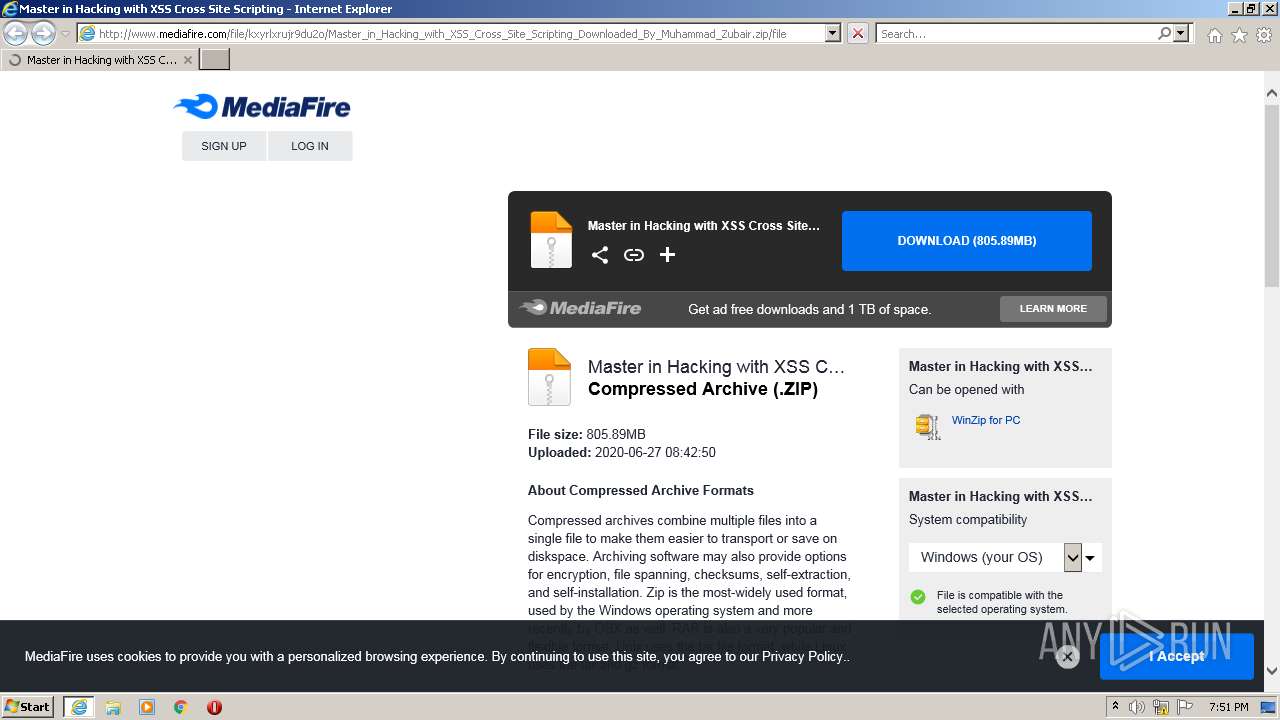
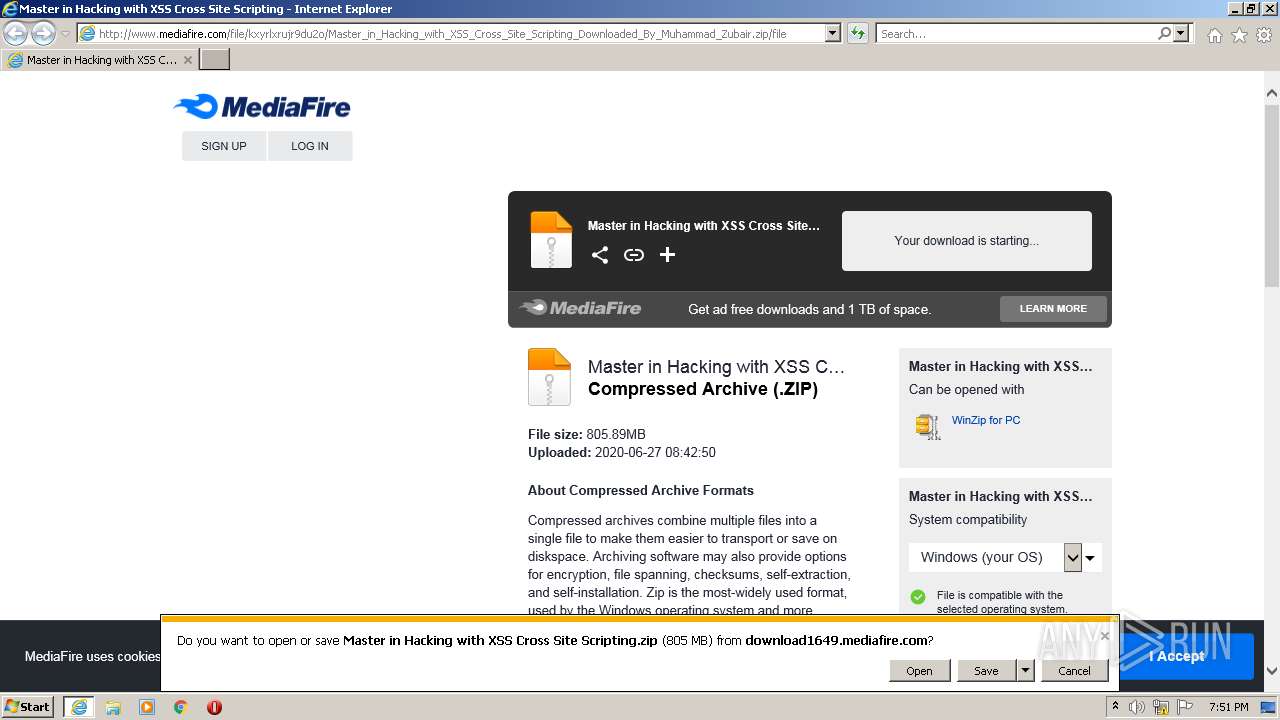
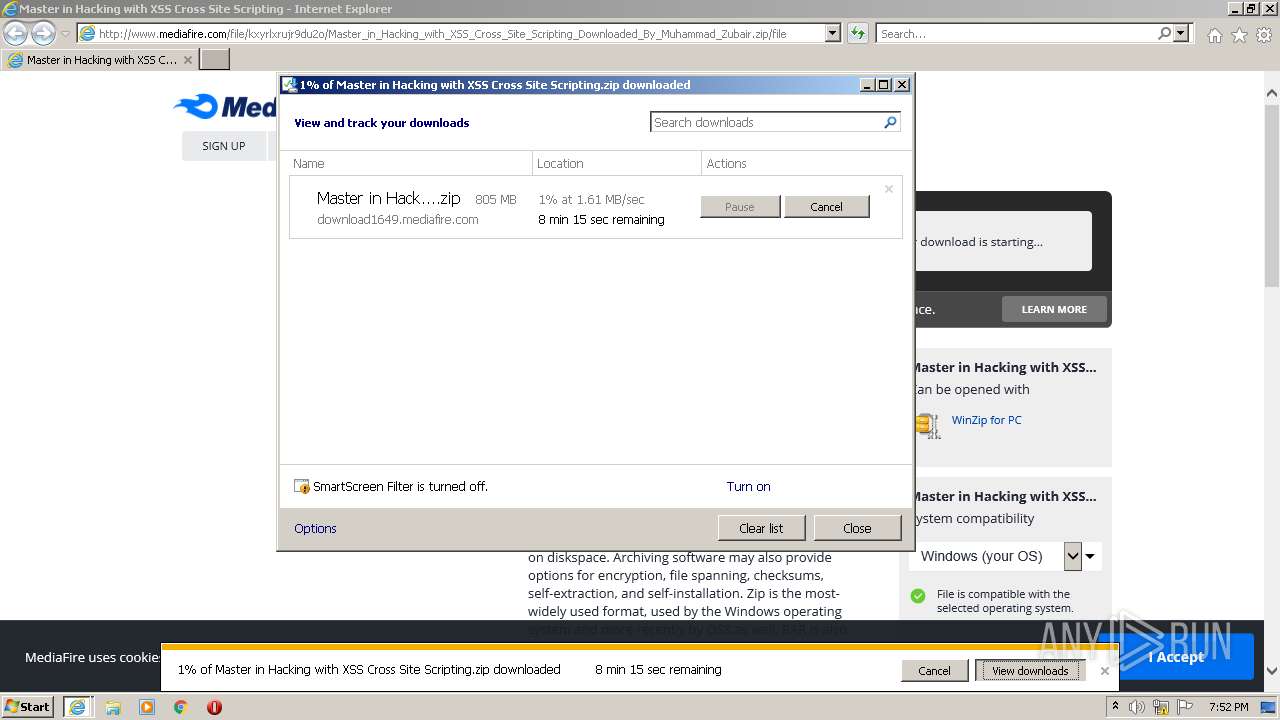
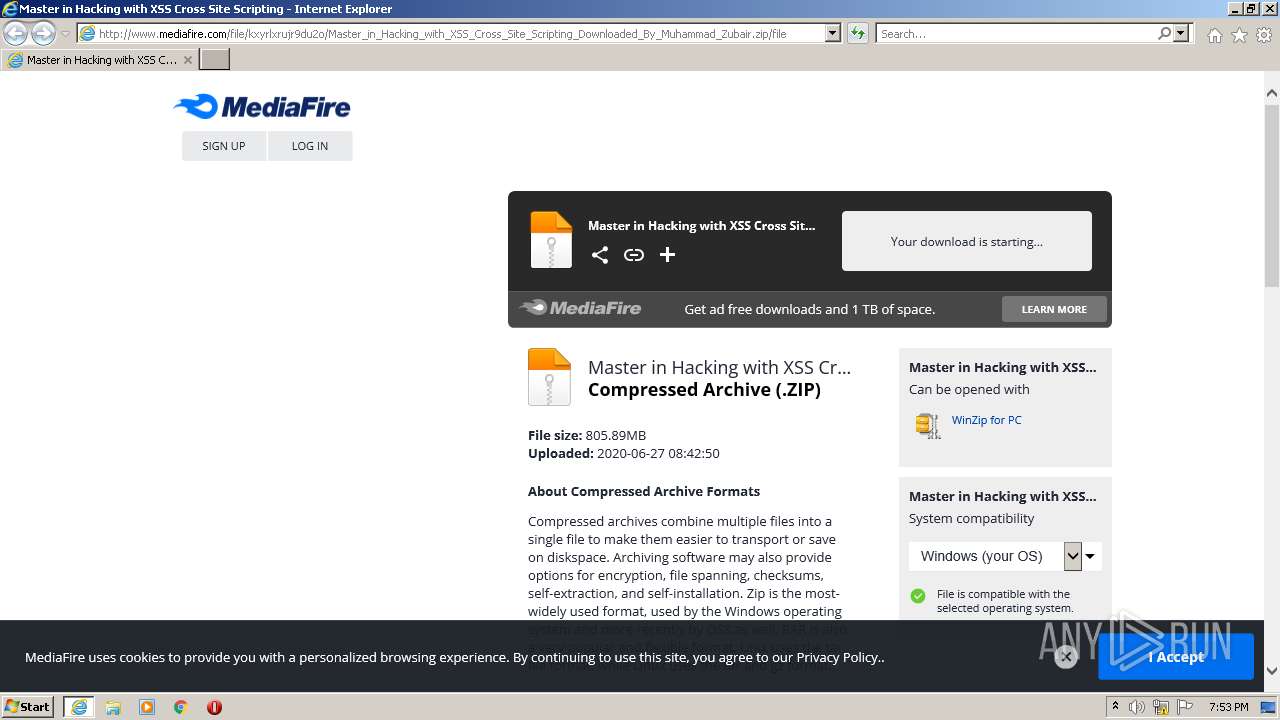
| URL: | http://www.mediafire.com/file/kxyrlxrujr9du2o/Master_in_Hacking_with_XSS_Cross_Site_Scripting_Downloaded_By_Muhammad_Zubair.zip/file |
| Full analysis: | https://app.any.run/tasks/d34a66b8-f09b-4be1-8223-f6cbe1d3510d |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 19:51:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EA6F6A3080EEB488914807B2D6DFEC82 |
| SHA1: | 71E1BBACBD964F505FD50188ECE1C8DF54C87604 |
| SHA256: | C190FBECAEF081BD6768486E99C69D37EFE2583F6B1091162A7075FA6BE0744F |
| SSDEEP: | 3:N1KJS4w3eGUoPXJV8Bhmy5QgcuWdV66kz2BdDYEaHlIVY9:Cc4w3eGDJgP5idVzkzWFM7 |
MALICIOUS
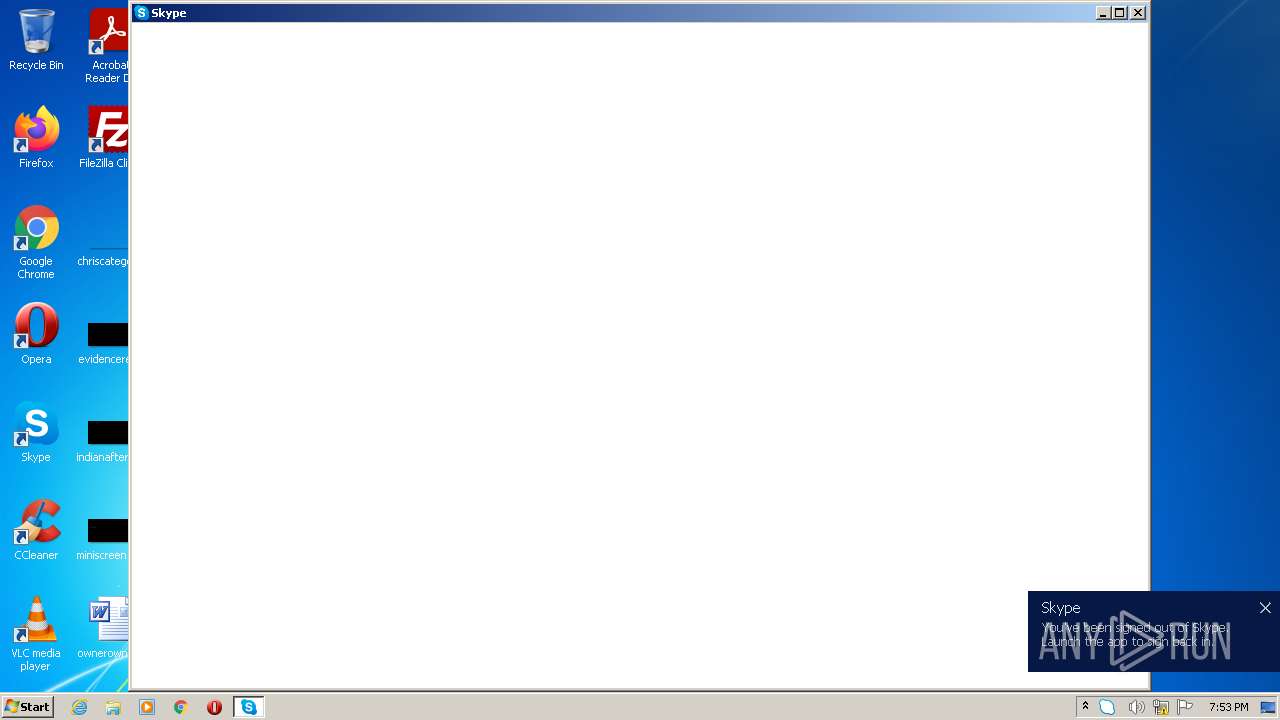
Changes the autorun value in the registry
- reg.exe (PID: 3144)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1108)
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2944)
Checks supported languages
- Skype.exe (PID: 2768)
- Skype.exe (PID: 3016)
- Skype.exe (PID: 2112)
- Skype.exe (PID: 404)
- Skype.exe (PID: 3488)
- Skype.exe (PID: 4044)
Reads CPU info
- Skype.exe (PID: 2768)
Reads the computer name
- Skype.exe (PID: 3016)
- Skype.exe (PID: 2768)
- Skype.exe (PID: 2112)
- Skype.exe (PID: 404)
- Skype.exe (PID: 3488)
- Skype.exe (PID: 4044)
Application launched itself
- Skype.exe (PID: 2768)
- Skype.exe (PID: 2112)
- Skype.exe (PID: 3488)
Creates files in the user directory
- Skype.exe (PID: 2768)
- Skype.exe (PID: 3488)
- Skype.exe (PID: 2112)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2768)
Changes default file association
- Skype.exe (PID: 2768)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2944)
Checks supported languages
- iexplore.exe (PID: 1108)
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 3792)
- reg.exe (PID: 3144)
- reg.exe (PID: 508)
Reads the computer name
- iexplore.exe (PID: 1108)
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2944)
Checks Windows Trust Settings
- iexplore.exe (PID: 1108)
- iexplore.exe (PID: 3792)
Creates files in the user directory
- iexplore.exe (PID: 1108)
- iexplore.exe (PID: 3792)
Application launched itself
- iexplore.exe (PID: 1108)
Changes internet zones settings
- iexplore.exe (PID: 1108)
Reads settings of System Certificates
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 1108)
- Skype.exe (PID: 2768)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1108)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1108)
- Skype.exe (PID: 2768)
Changes settings of System certificates
- iexplore.exe (PID: 1108)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1108)
Reads the date of Windows installation
- iexplore.exe (PID: 1108)
Manual execution by user
- Skype.exe (PID: 2768)
Reads the hosts file
- Skype.exe (PID: 2768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 508 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\system32\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.mediafire.com/file/kxyrlxrujr9du2o/Master_in_Hacking_with_XSS_Cross_Site_Scripting_Downloaded_By_Muhammad_Zubair.zip/file" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=53EF93F6A8EA3A3AA542A2260114670C --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=53EF93F6A8EA3A3AA542A2260114670C --renderer-client-id=3 --mojo-platform-channel-handle=1584 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Explorer.EXE | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1108 CREDAT:660759 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3144 | C:\Windows\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\system32\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=3A1AFD1DB57441F7952D2527D5323993 --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=3A1AFD1DB57441F7952D2527D5323993 --renderer-client-id=4 --mojo-platform-channel-handle=2672 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1108 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 054
Read events
20 870
Write events
181
Delete events
3
Modification events
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937435 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937435 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
41
Text files
42
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KYV1IV0W.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\71N18K88.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\file-zip-v3[1].png | image | |
MD5:A23B8B7059E953FC1B74BF87A77EBB0C | SHA256:4448E430D3C53BAD548A5D135E1C7E2F9593E806BA47892640D430EA752E979E | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\apps_list_sprite-v6[1].png | image | |
MD5:D3DF203853C4482E8753A856E13B0B07 | SHA256:DC54B817820F14CE6395BA2A037F37D4BB0AF75D5B017336140793FBE2F7F738 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SWM7Z8K5.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SFFSR29N.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\fb_16x16[1].png | image | |
MD5:78226526732869ADD09512E9B4BE3090 | SHA256:720671166AC43ABA99E3952B0B9341AB4E0FEE1FD891DB54E2A07F05DB653142 | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\footerIcons[1].png | image | |
MD5:E0ABC4FEA89D2C5153B73CD02AC5BA13 | SHA256:F917A9105C311331B1D40F4D2BDBF11233C1C465616C1A9C46232F451463B061 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
108
DNS requests
44
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
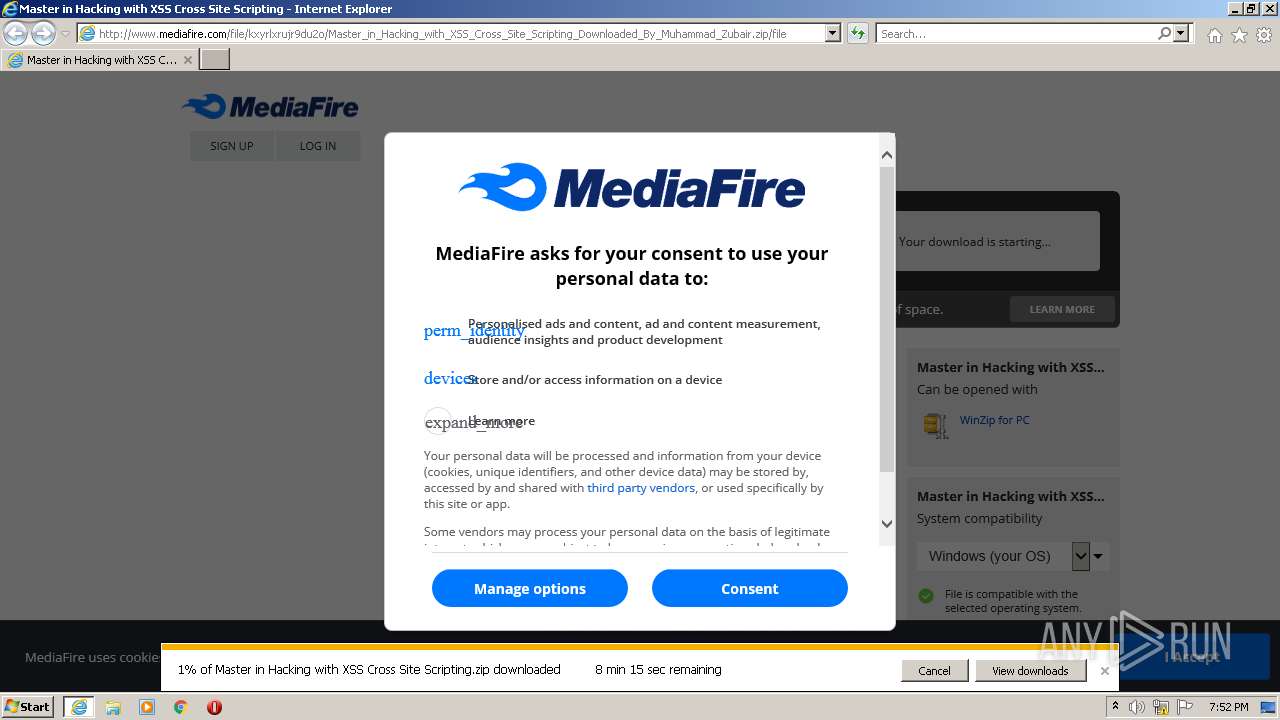
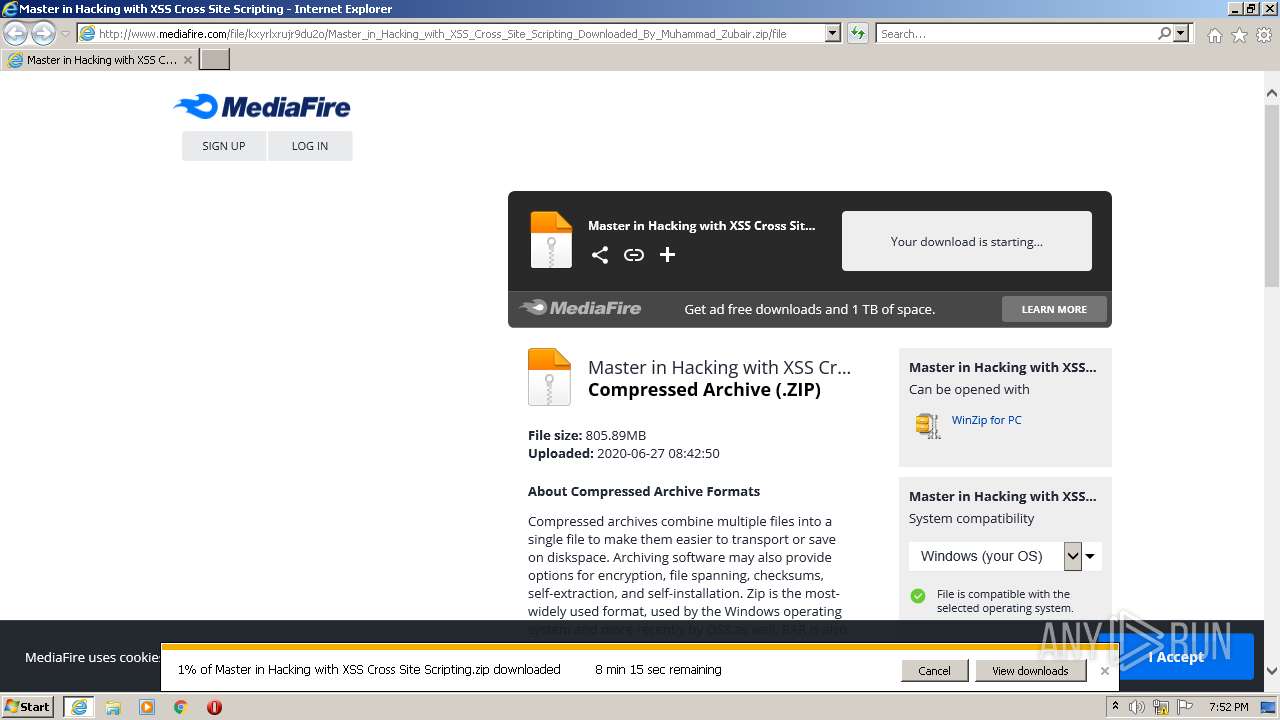
3792 | iexplore.exe | GET | — | 199.91.152.149:80 | http://download1649.mediafire.com/7rut71m98yug/kxyrlxrujr9du2o/Master+in+Hacking+with+XSS+Cross+Site+Scripting.zip | US | — | — | suspicious |
3792 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/file/kxyrlxrujr9du2o/Master_in_Hacking_with_XSS_Cross_Site_Scripting_Downloaded_By_Muhammad_Zubair.zip/file | US | html | 83.5 Kb | shared |
3792 | iexplore.exe | GET | 200 | 52.222.206.35:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 18.66.242.45:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3792 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAEC9RywYwyihLibdTfI1sk%3D | US | der | 280 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/filetype/file-zip-v3.png | US | image | 1.83 Kb | shared |
3792 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_dark/arrow_dropdown.svg | US | image | 255 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 142.250.185.206:80 | translate.google.com | Google Inc. | US | whitelisted |
3792 | iexplore.exe | 104.16.95.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
3792 | iexplore.exe | 142.250.185.206:443 | translate.google.com | Google Inc. | US | whitelisted |
3792 | iexplore.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3792 | iexplore.exe | 104.19.215.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
3792 | iexplore.exe | 52.222.206.214:443 | cdn.amplitude.com | Amazon.com, Inc. | US | suspicious |
3792 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3792 | iexplore.exe | 18.66.242.45:80 | ocsp.rootca1.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
3792 | iexplore.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3792 | iexplore.exe | 199.91.152.149:80 | download1649.mediafire.com | MediaFire, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
btloader.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
cdn.amplitude.com |
| whitelisted |
cdn.otnolatrnup.com |
| whitelisted |
static.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
Skype.exe | [3016:3300:0124/195332.366:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3016:3300:0124/195332.366:VERBOSE1:crash_service.cc(145)] window handle is 00020192
|
Skype.exe | [3016:3300:0124/195332.366:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [3016:3300:0124/195332.366:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [3016:3300:0124/195332.366:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [3016:2632:0124/195332.366:VERBOSE1:crash_service.cc(333)] client start. pid = 2768
|
Skype.exe | [3016:2632:0124/195334.841:VERBOSE1:crash_service.cc(333)] client start. pid = 2112
|
Skype.exe | [404:1408:0124/195334.919:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [404:1408:0124/195334.919:VERBOSE1:crash_service.cc(145)] window handle is 0002019C
|
Skype.exe | [404:1408:0124/195334.919:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|