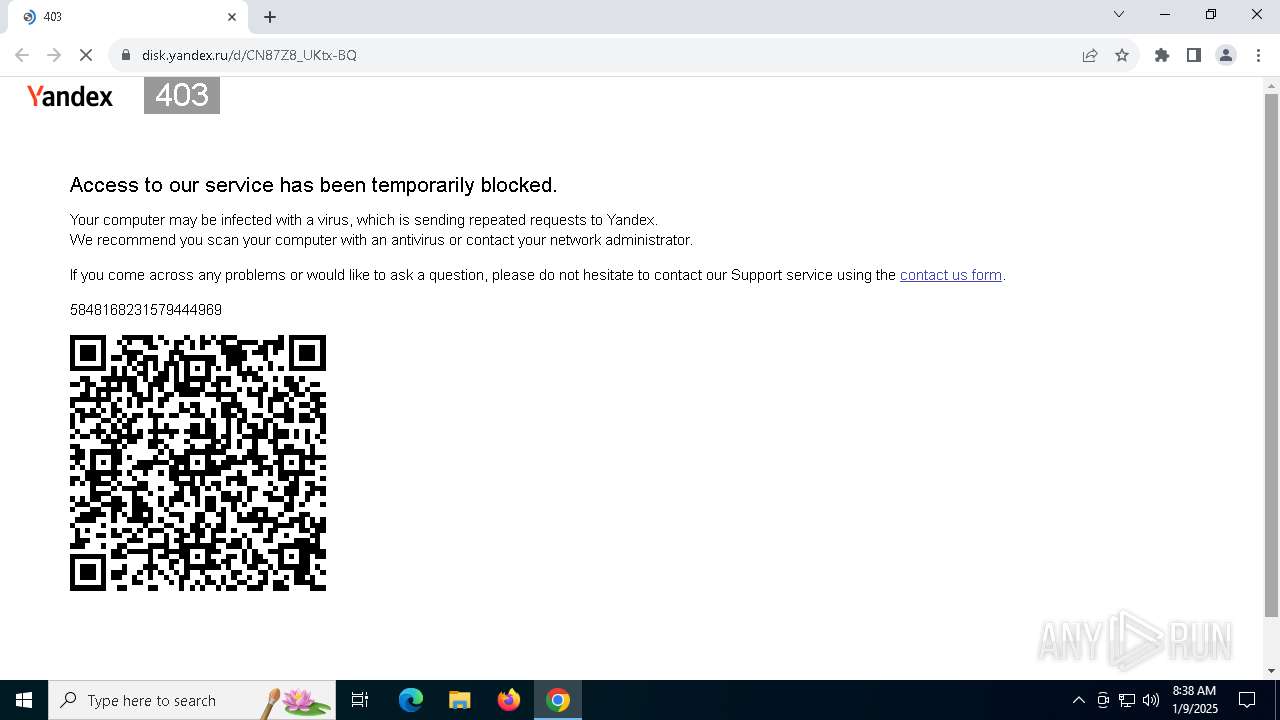
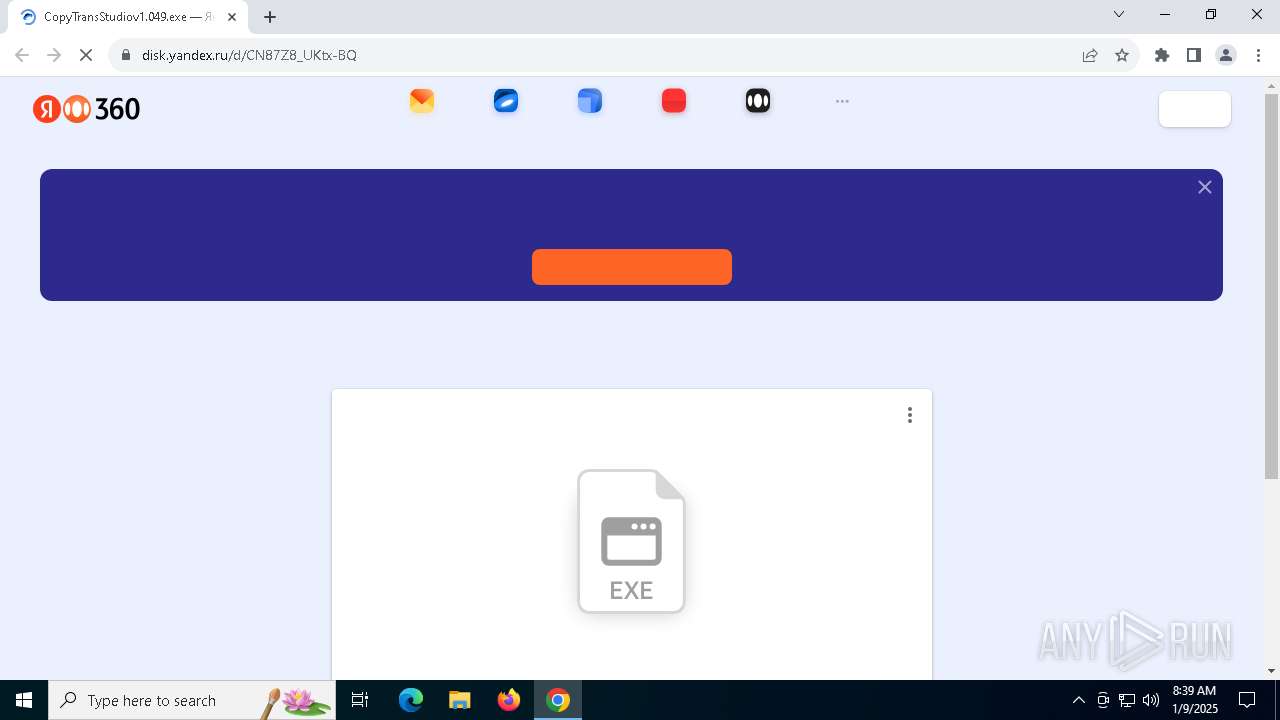
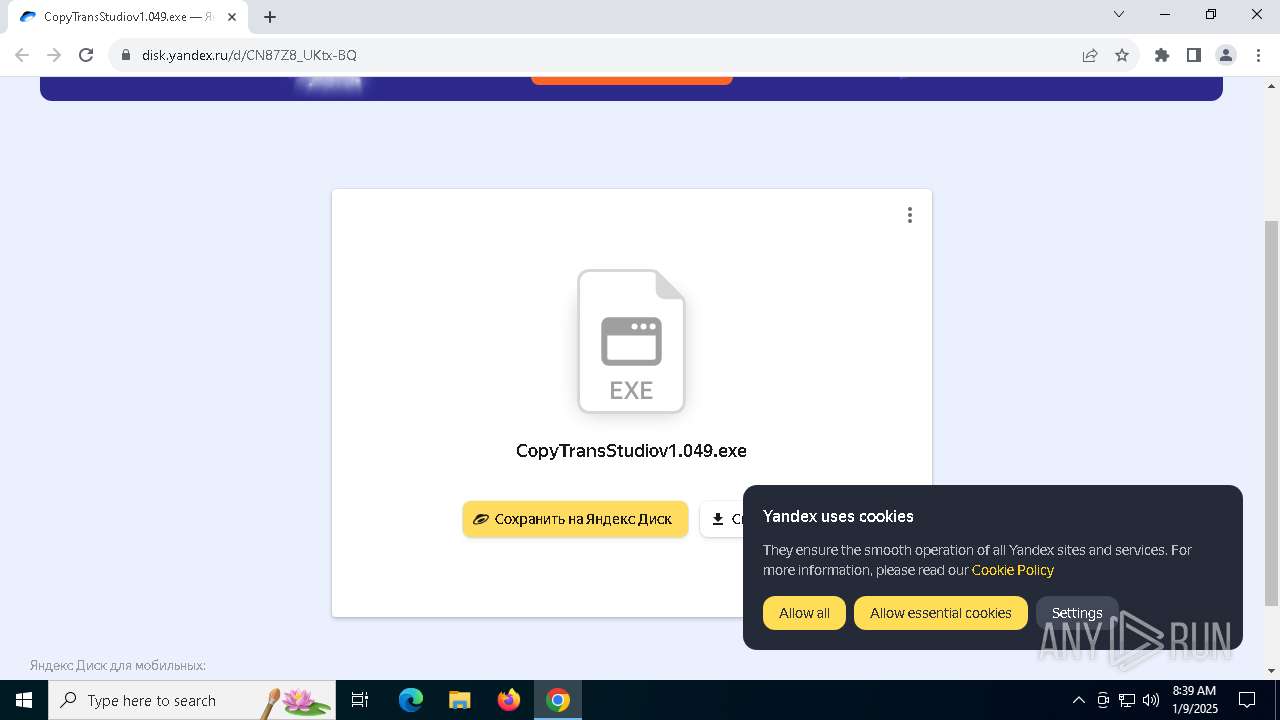
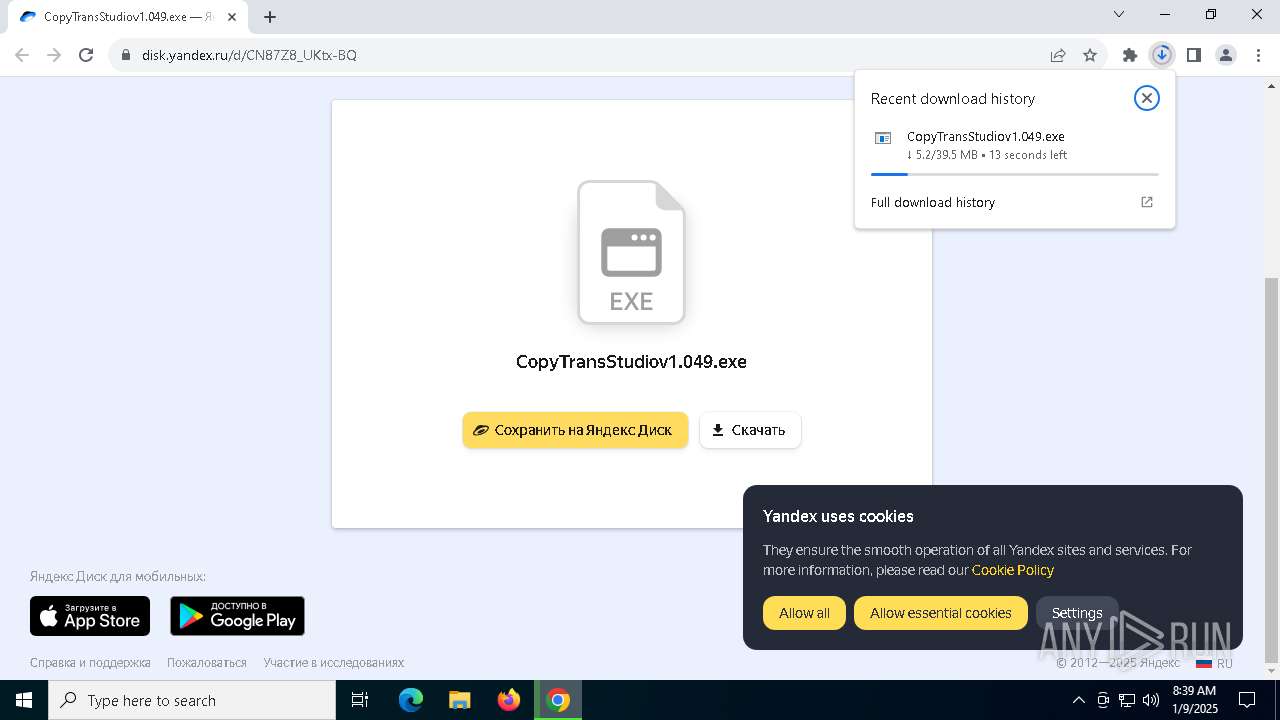
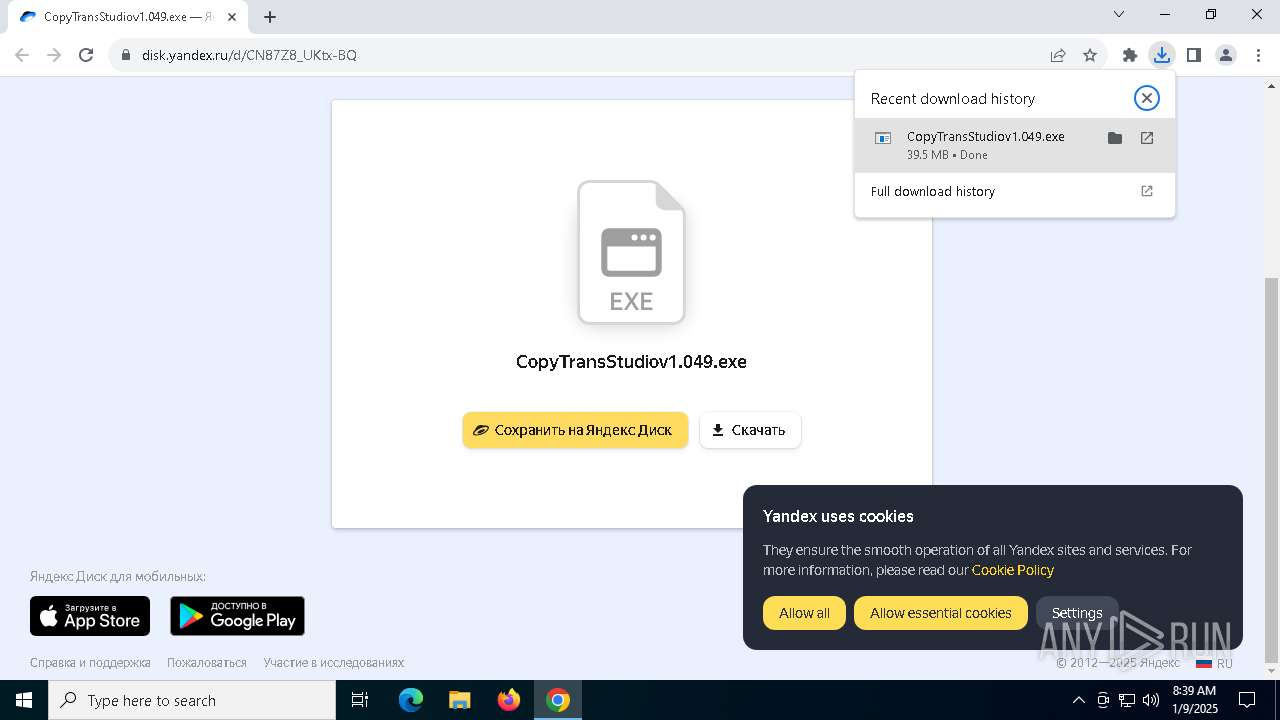
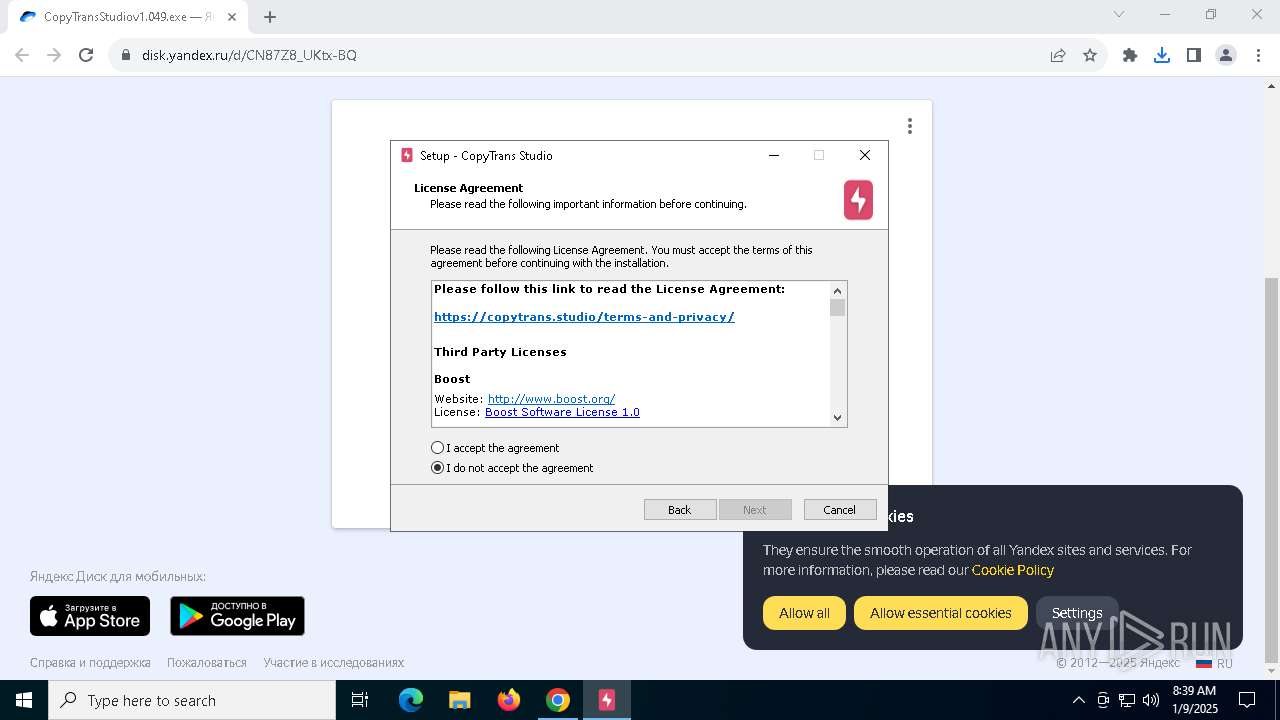
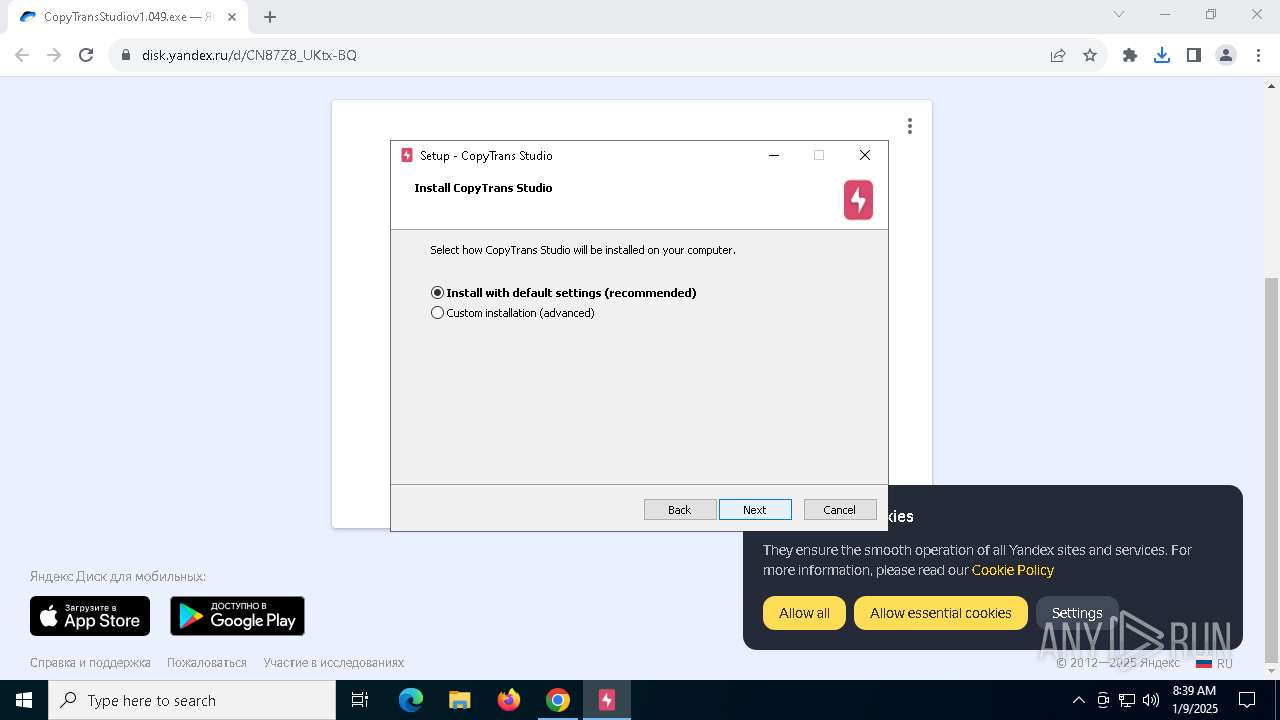
| URL: | https://disk.yandex.ru/d/CN87Z8_UKtx-BQ |
| Full analysis: | https://app.any.run/tasks/bef950a8-5c40-4d6d-8434-e189915607b0 |
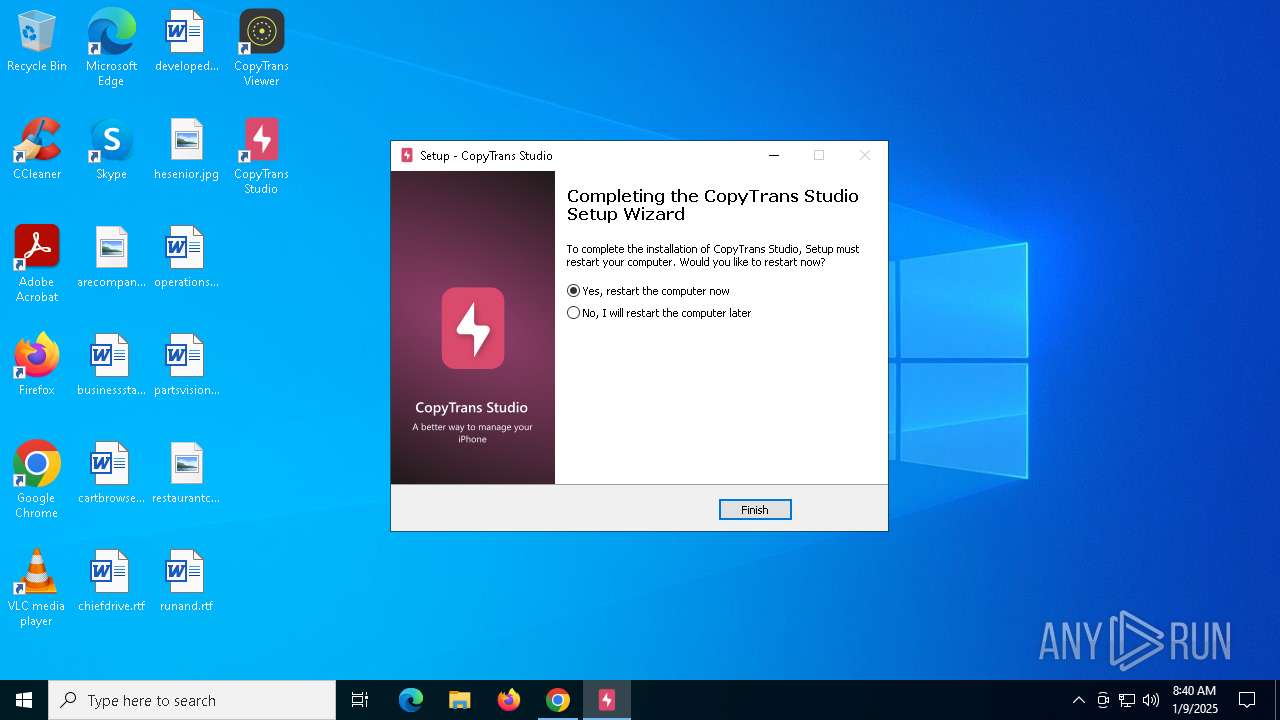
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2025, 08:38:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 35019124D4CCACD09607DF057E6E71A1 |
| SHA1: | 9DB6727150543A8267CF07DA3CAD552F2E28170C |
| SHA256: | C177CF4A7B38AA1DCBA73FA7936D95B27200B2C14786FC1A64F297CB108F675B |
| SSDEEP: | 3:N8U25S/dMn:2U2iM |
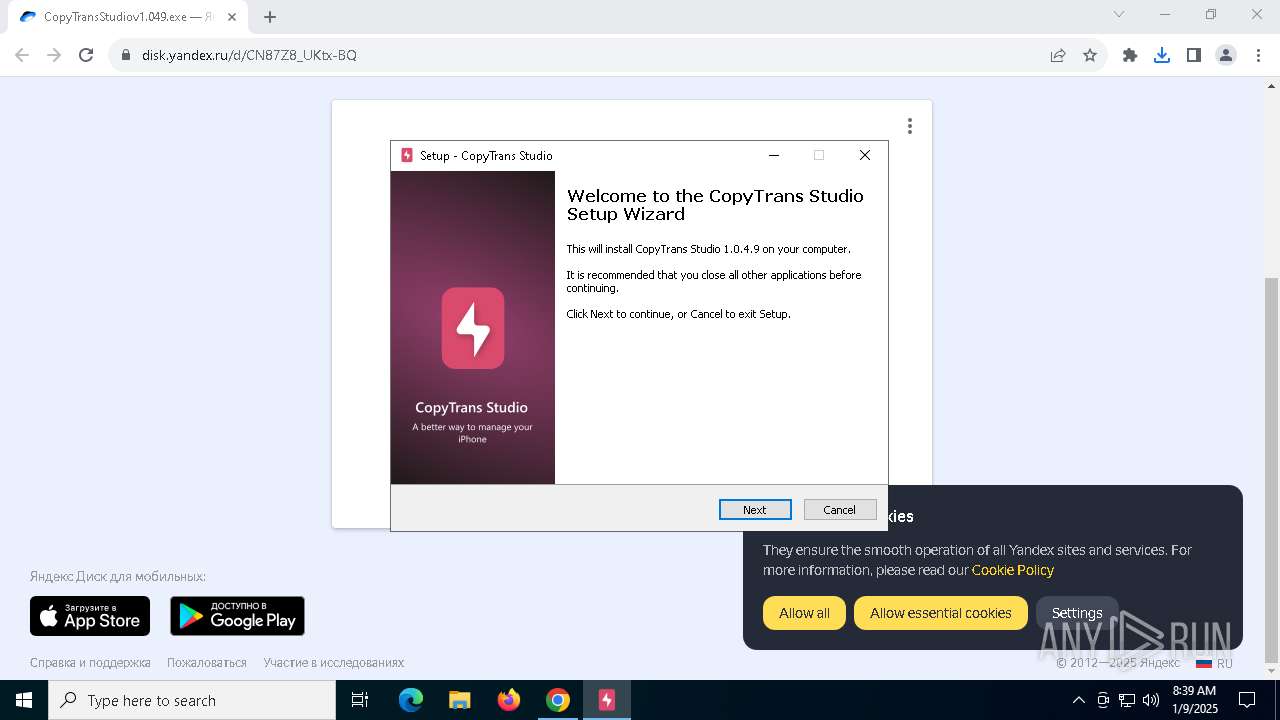
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- CopyTransHEICforWindows.tmp (PID: 4012)
- CopyTransStudiov1.049.tmp (PID: 3532)
SUSPICIOUS
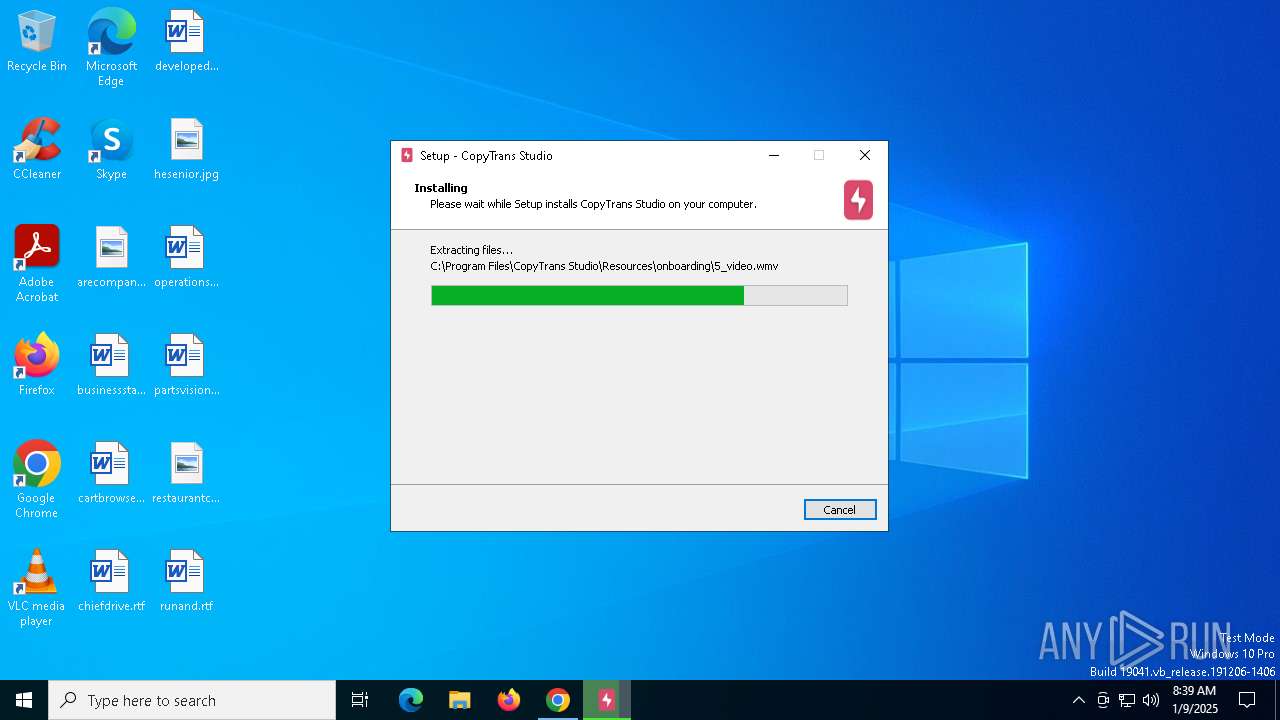
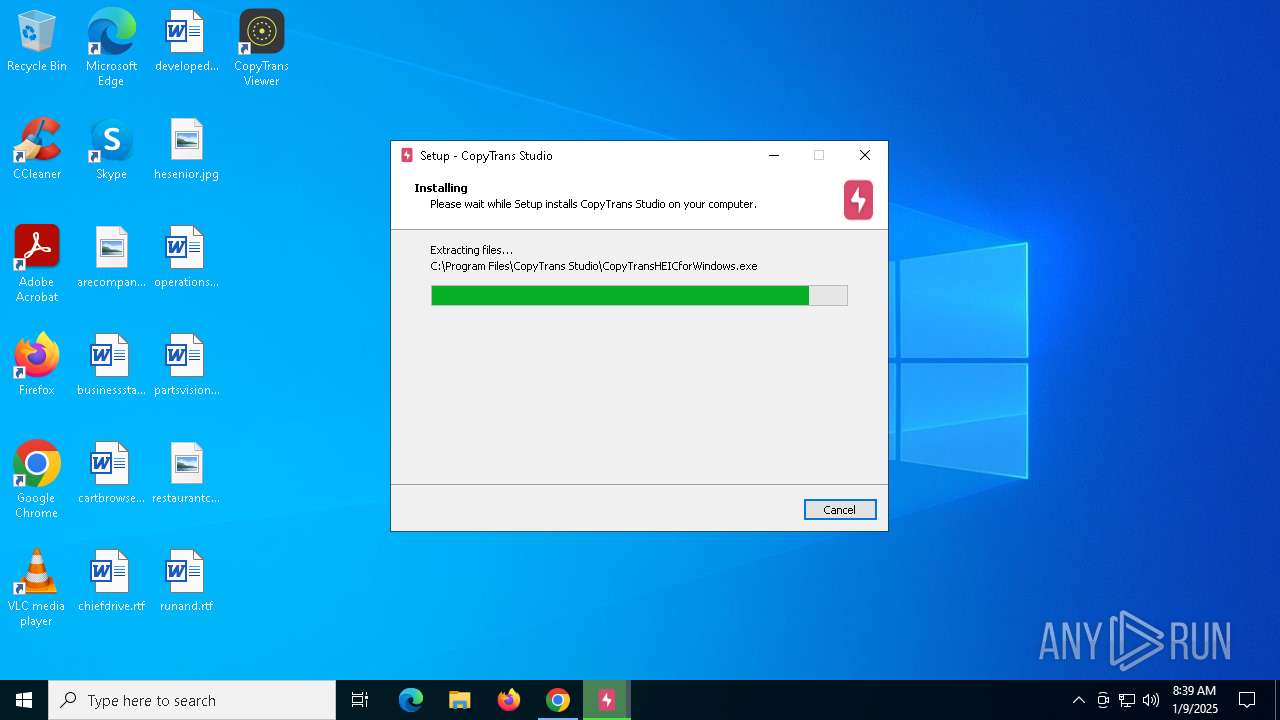
Executable content was dropped or overwritten
- CopyTransStudiov1.049.exe (PID: 6952)
- CopyTransStudiov1.049.exe (PID: 5836)
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransHEICforWindows.exe (PID: 1416)
- CopyTransViewerInstaller.tmp (PID: 4300)
- CopyTransHEICforWindows.exe (PID: 4308)
- CopyTransHEICforWindows.tmp (PID: 4012)
- CopyTransViewerInstaller.exe (PID: 5544)
Reads security settings of Internet Explorer
- CopyTransStudiov1.049.tmp (PID: 7132)
- CopyTransHEICforWindows.tmp (PID: 3988)
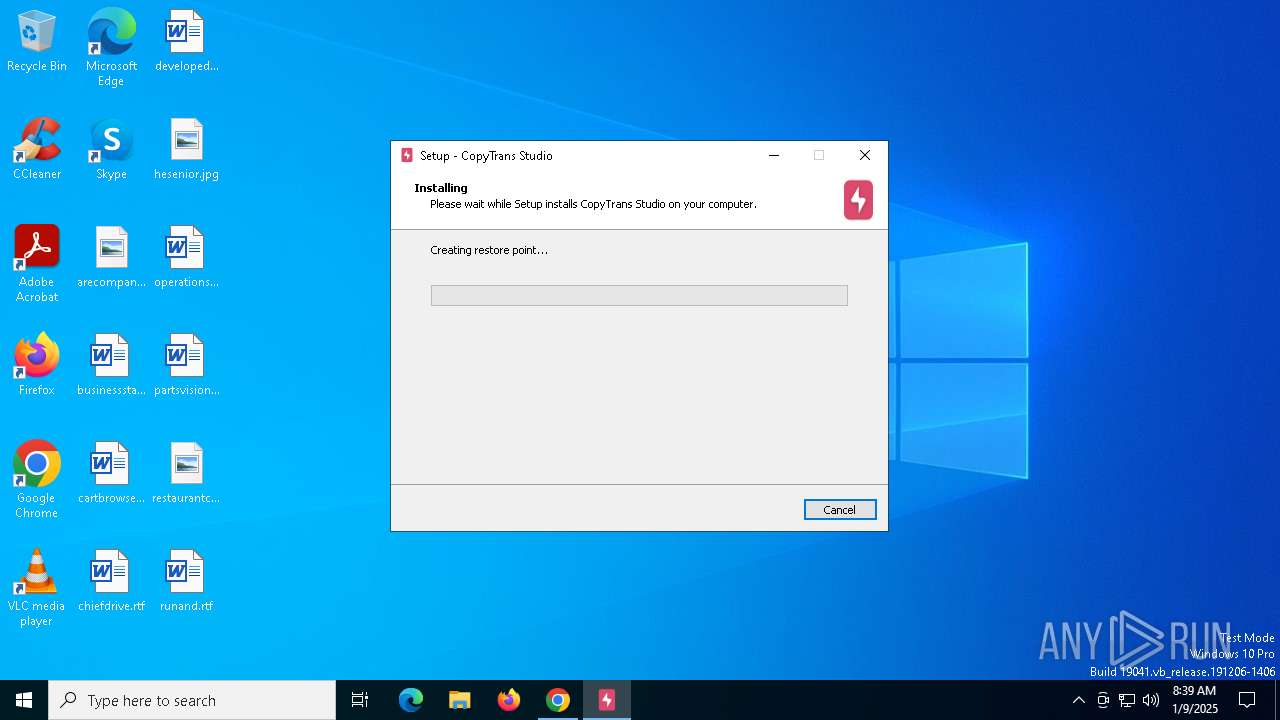
Executes as Windows Service
- VSSVC.exe (PID: 6736)
Searches for installed software
- dllhost.exe (PID: 2992)
- CopyTransHEICforWindows.tmp (PID: 4012)
Changes default file association
- CopyTransViewerInstaller.tmp (PID: 4300)
Reads the Windows owner or organization settings
- CopyTransHEICforWindows.tmp (PID: 4012)
Starts POWERSHELL.EXE for commands execution
- CopyTransHEICforWindows.tmp (PID: 3988)
- CopyTransStudio.exe (PID: 3640)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 624)
- CopyTransStudiov1.049.tmp (PID: 3532)
Uses REG/REGEDIT.EXE to modify registry
- CopyTransStudiov1.049.tmp (PID: 7132)
INFO
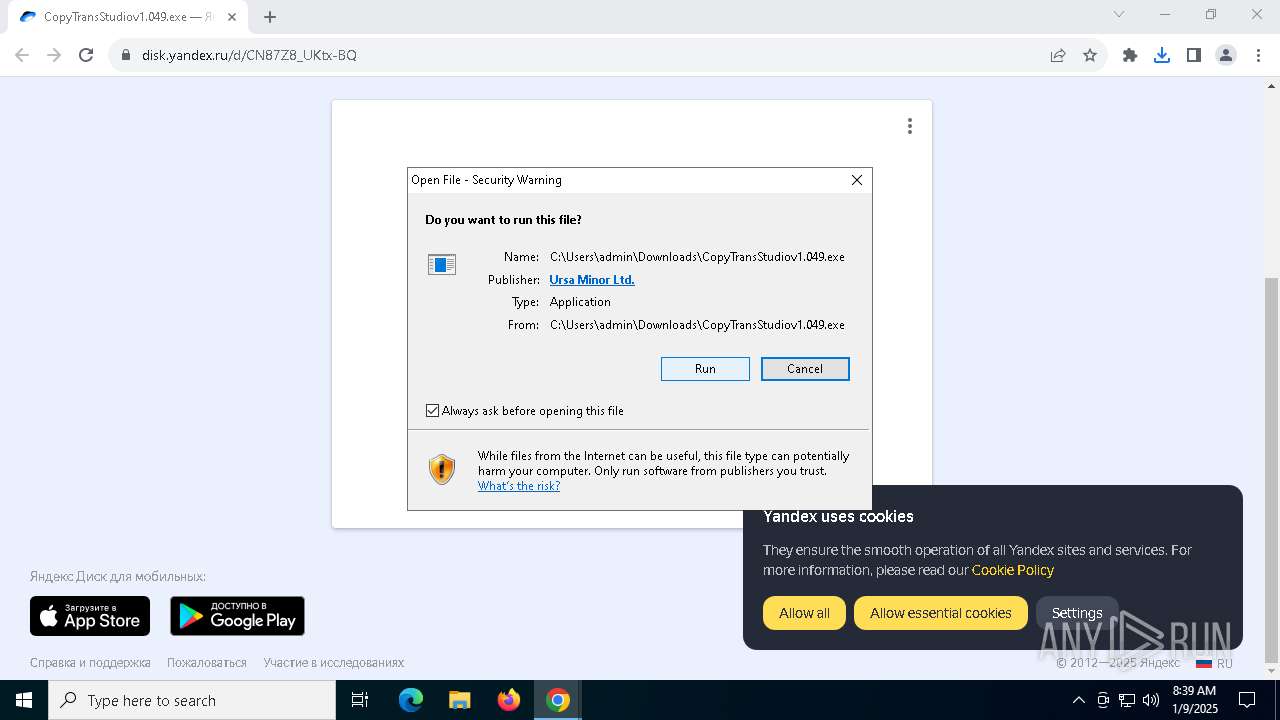
The process uses the downloaded file
- chrome.exe (PID: 6696)
- chrome.exe (PID: 4716)
Executable content was dropped or overwritten
- chrome.exe (PID: 4716)
- chrome.exe (PID: 6836)
Application launched itself
- chrome.exe (PID: 4716)
Checks supported languages
- CopyTransStudiov1.049.tmp (PID: 7132)
- CopyTransStudiov1.049.exe (PID: 5836)
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransViewerInstaller.tmp (PID: 4300)
- CopyTransHEICforWindows.exe (PID: 4308)
- CopyTransHEICforWindows.tmp (PID: 3988)
- CopyTransHEICforWindows.exe (PID: 1416)
- CopyTransHEICSparsePackageReg.exe (PID: 4704)
- CopyTransStudio.exe (PID: 3640)
Create files in a temporary directory
- CopyTransStudiov1.049.exe (PID: 5836)
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransViewerInstaller.tmp (PID: 4300)
Reads the computer name
- CopyTransStudiov1.049.tmp (PID: 7132)
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransHEICforWindows.tmp (PID: 4012)
- CopyTransHEICforWindows.tmp (PID: 3988)
Reads the software policy settings
- CopyTransStudiov1.049.tmp (PID: 3532)
Creates files in the program directory
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransViewerInstaller.tmp (PID: 4300)
- CopyTransHEICforWindows.tmp (PID: 4012)
- regsvr32.exe (PID: 624)
- powershell.exe (PID: 6600)
Manages system restore points
- SrTasks.exe (PID: 6916)
The sample compiled with english language support
- CopyTransStudiov1.049.tmp (PID: 3532)
- CopyTransHEICforWindows.tmp (PID: 4012)
- chrome.exe (PID: 6836)
Creates a software uninstall entry
- CopyTransViewerInstaller.tmp (PID: 4300)
- CopyTransHEICforWindows.tmp (PID: 4012)
- CopyTransStudiov1.049.tmp (PID: 3532)
Process checks computer location settings
- CopyTransHEICforWindows.tmp (PID: 3988)
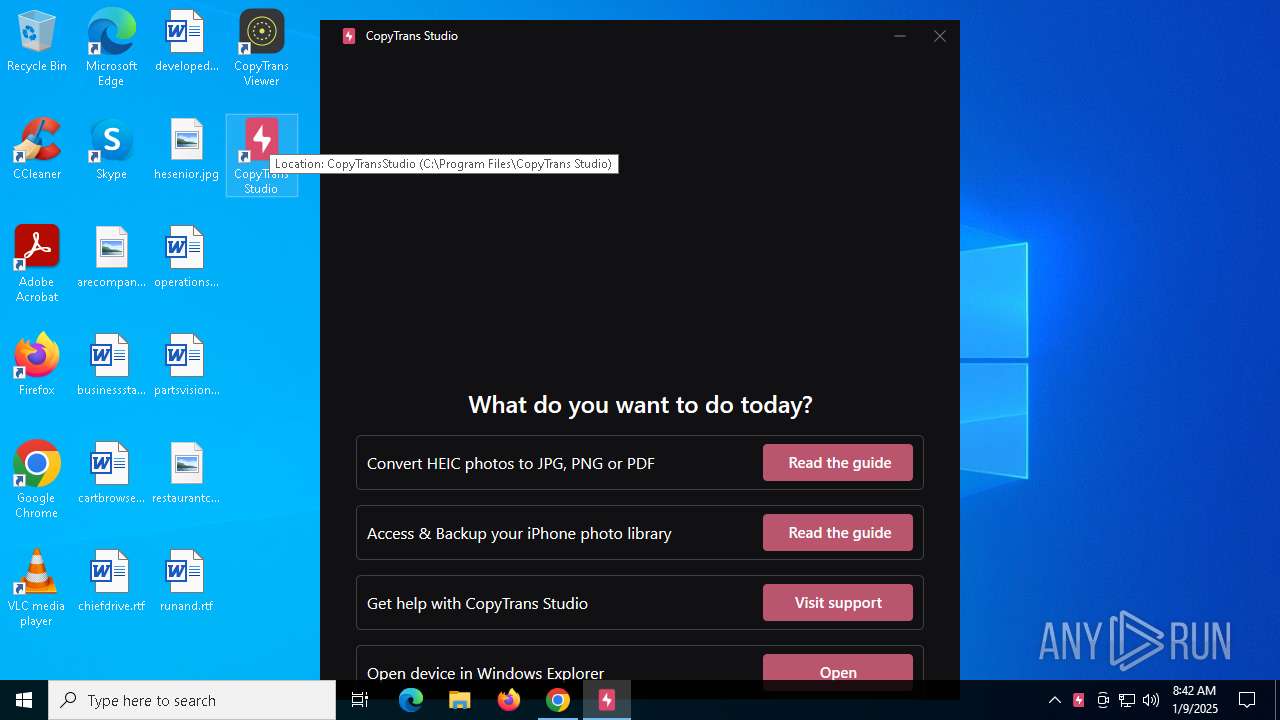
Manual execution by a user
- CopyTransStudio.exe (PID: 3640)
Reads CPU info
- CopyTransStudio.exe (PID: 3640)
Checks proxy server information
- CopyTransStudio.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
58
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | /s "C:\Program Files (x86)\CopyTrans HEIC for Windows\CopyTransHEICforWindows.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | "C:\Program Files\CopyTrans Studio\CopyTransHEICforWindows.exe" /SPAWNWND=$30226 /NOTIFYWND=$F02B6 /verysilent /norestart | C:\Program Files\CopyTrans Studio\CopyTransHEICforWindows.exe | CopyTransHEICforWindows.tmp | ||||||||||||
User: admin Company: Ursa Minor Ltd Integrity Level: HIGH Description: CopyTrans HEIC for Windows Setup Exit code: 0 Version: 2.0.2.0 Modules
| |||||||||||||||
| 1740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4188 --field-trial-handle=1240,i,12522776930094700934,5550043307113356327,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2088 | "reg.exe" DELETE "HKCU\SOFTWARE\CopyTrans\CopyTrans Studio" /v UpdateAvailable /f /reg:64 | C:\Windows\System32\reg.exe | — | CopyTransStudiov1.049.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | powershell.exe Get-AppxPackage -Name AppleInc.iCloud | Out-String -width 4096 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CopyTransStudio.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4992 --field-trial-handle=1240,i,12522776930094700934,5550043307113356327,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 177
Read events
38 623
Write events
518
Delete events
36
Modification events
| (PID) Process: | (4716) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4716) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4716) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4716) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4716) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6696) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EC1633FA7162DB01 | |||
| (PID) Process: | (3532) CopyTransStudiov1.049.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CopyTrans |
| Operation: | write | Name: | Mix |
Value: $device:587b16f4480076-f52bd40a9ad88b-2eea017b63b326-fb8b67a9c02269 | |||
| (PID) Process: | (3532) CopyTransStudiov1.049.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\CopyTrans\CopyTrans Studio |
| Operation: | write | Name: | Uc_ctst |
Value: 1 | |||
| (PID) Process: | (3532) CopyTransStudiov1.049.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\CopyTrans\CopyTrans Studio |
| Operation: | write | Name: | Fud_ctst |
Value: | |||
| (PID) Process: | (3532) CopyTransStudiov1.049.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\CopyTrans |
| Operation: | write | Name: | Faaud |
Value: | |||
Executable files
92
Suspicious files
419
Text files
164
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF136f09.TMP | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136f19.TMP | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF136f19.TMP | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136f28.TMP | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136f28.TMP | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136f28.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
75
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4716 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
4716 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
4716 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQC2XJ3xvLx7DdV%2B%2Bed2Ax4G | unknown | — | — | whitelisted |
7052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6444 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4864 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | — | Ooredoo Q.S.C. | QA | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4716 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6264 | chrome.exe | 87.250.250.50:443 | disk.yandex.ru | YANDEX LLC | RU | shared |
6264 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
disk.yandex.ru |
| shared |
accounts.google.com |
| whitelisted |
cdnrhkgfkkpupuotntfj.svc.cdn.yandex.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
mc.yandex.com |
| whitelisted |
yastatic.net |
| whitelisted |