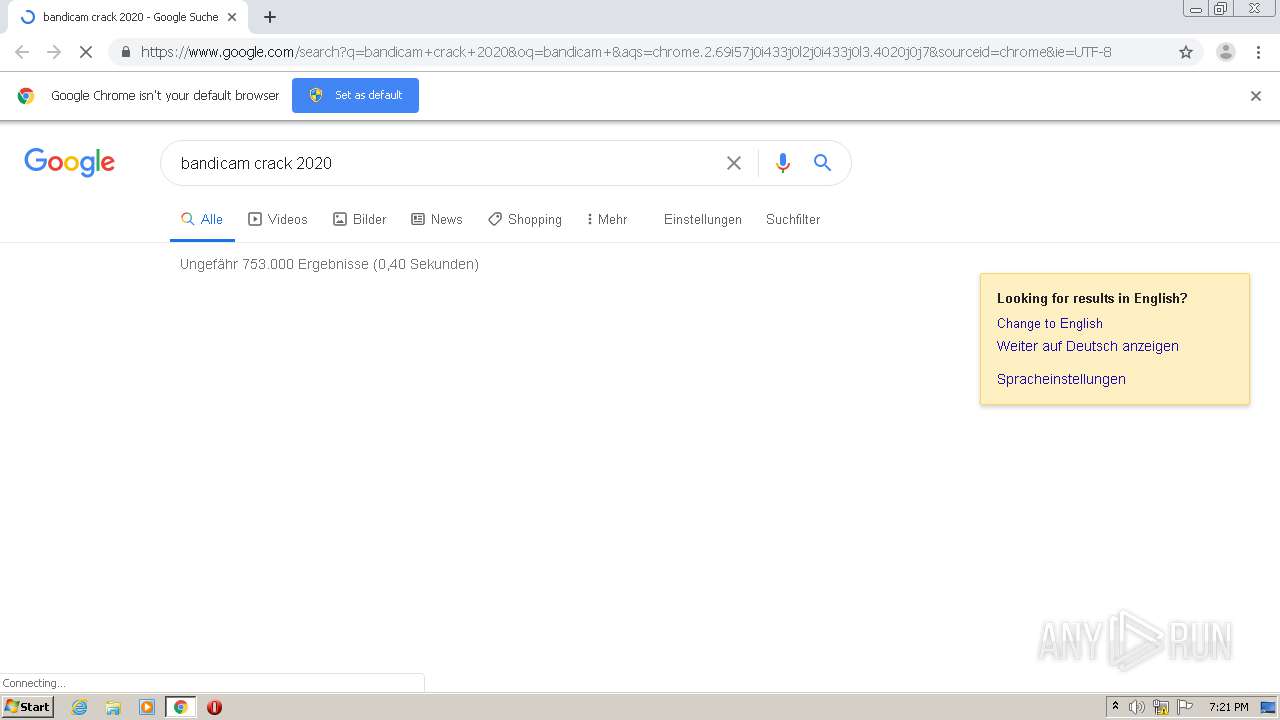
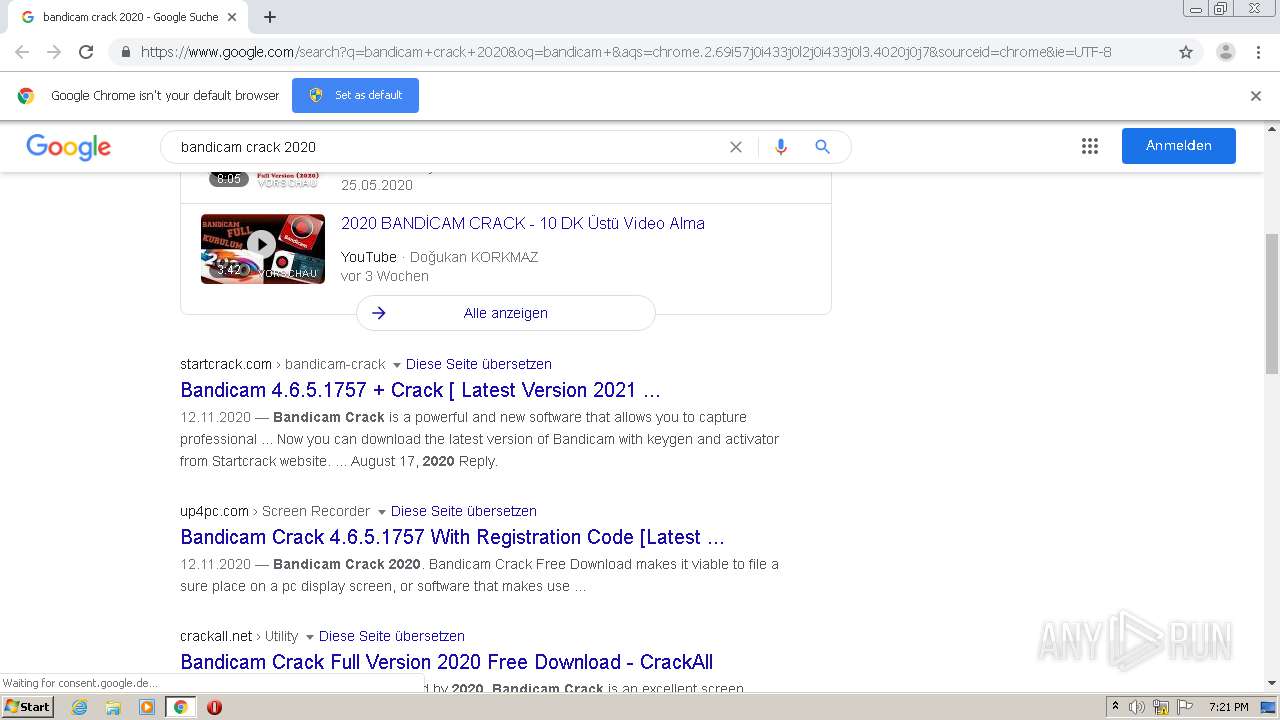
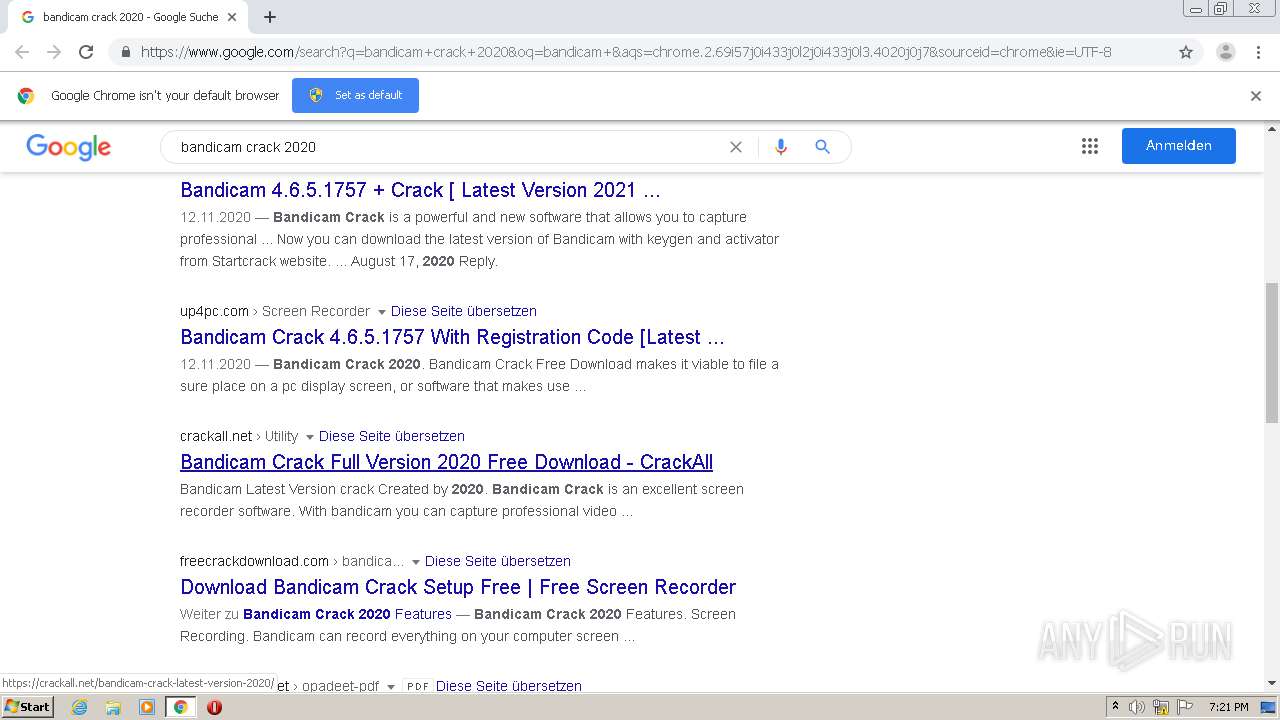
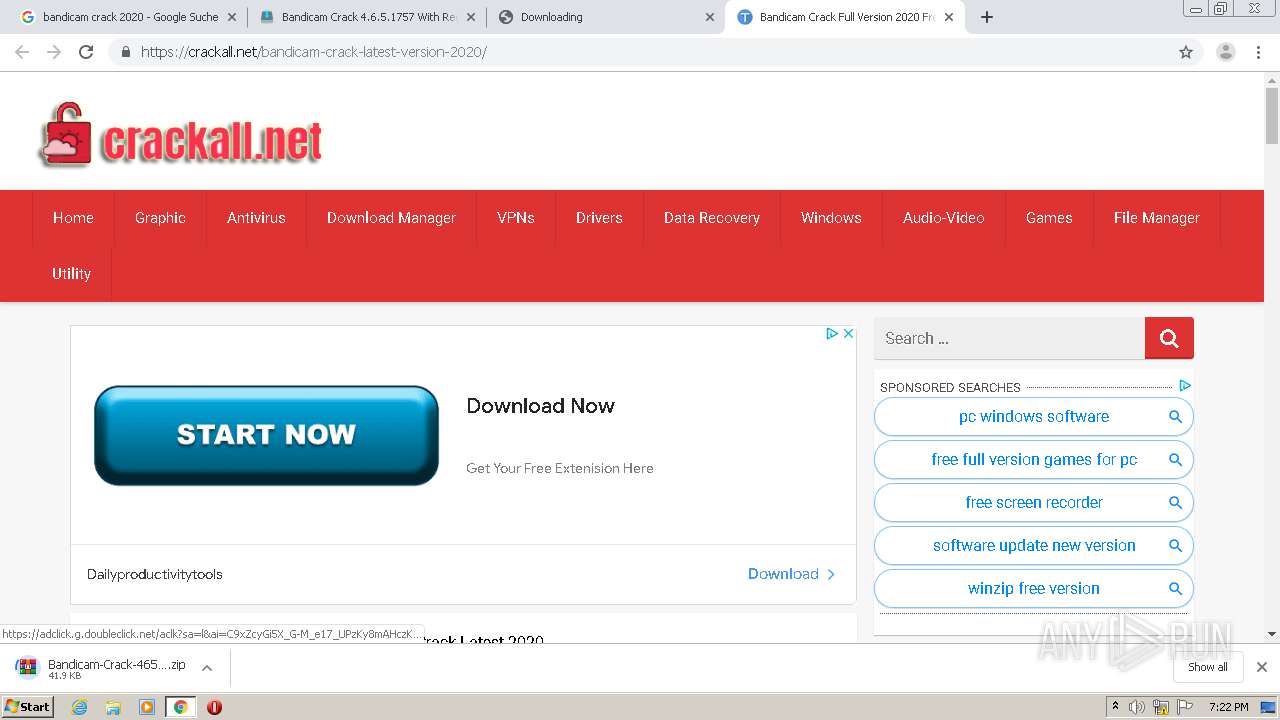
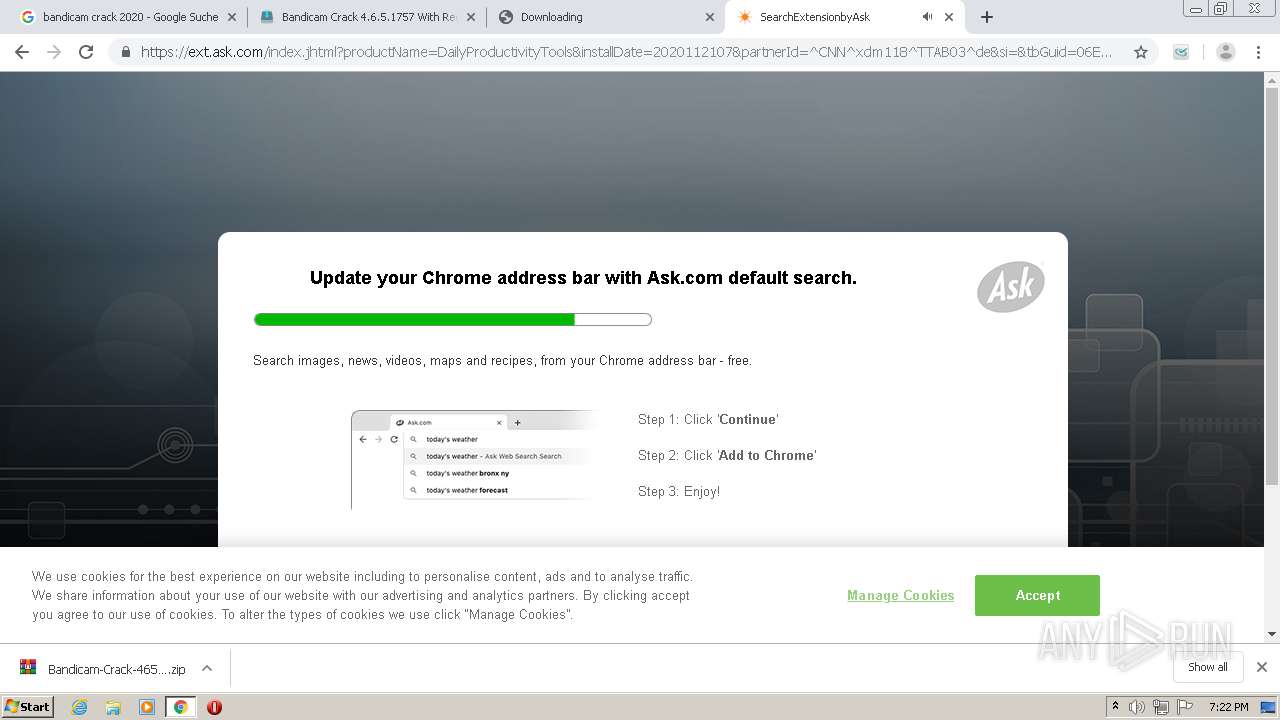
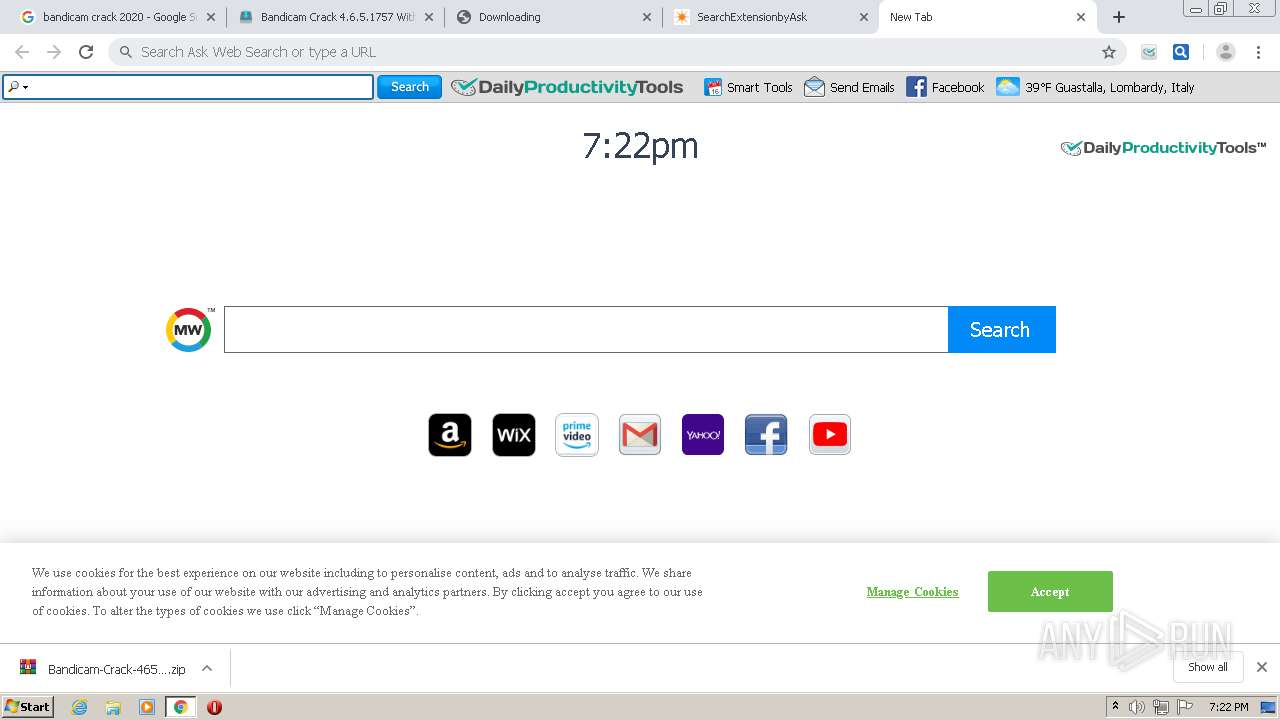
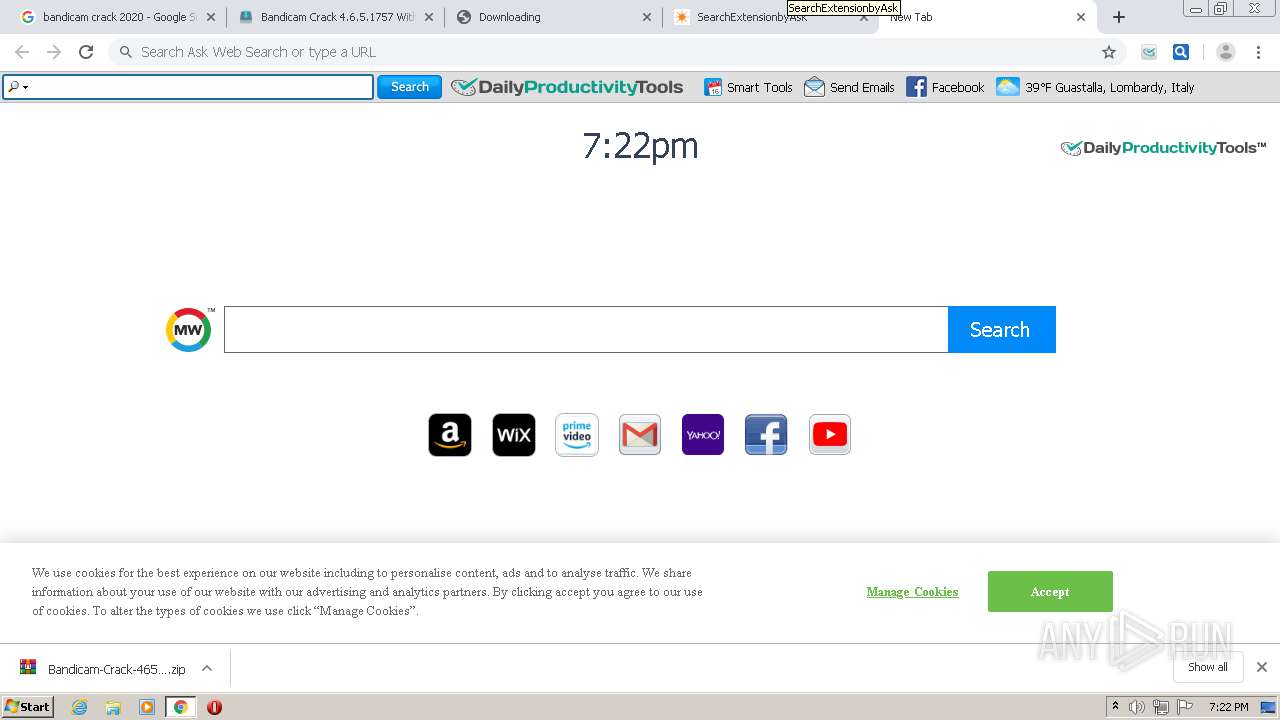
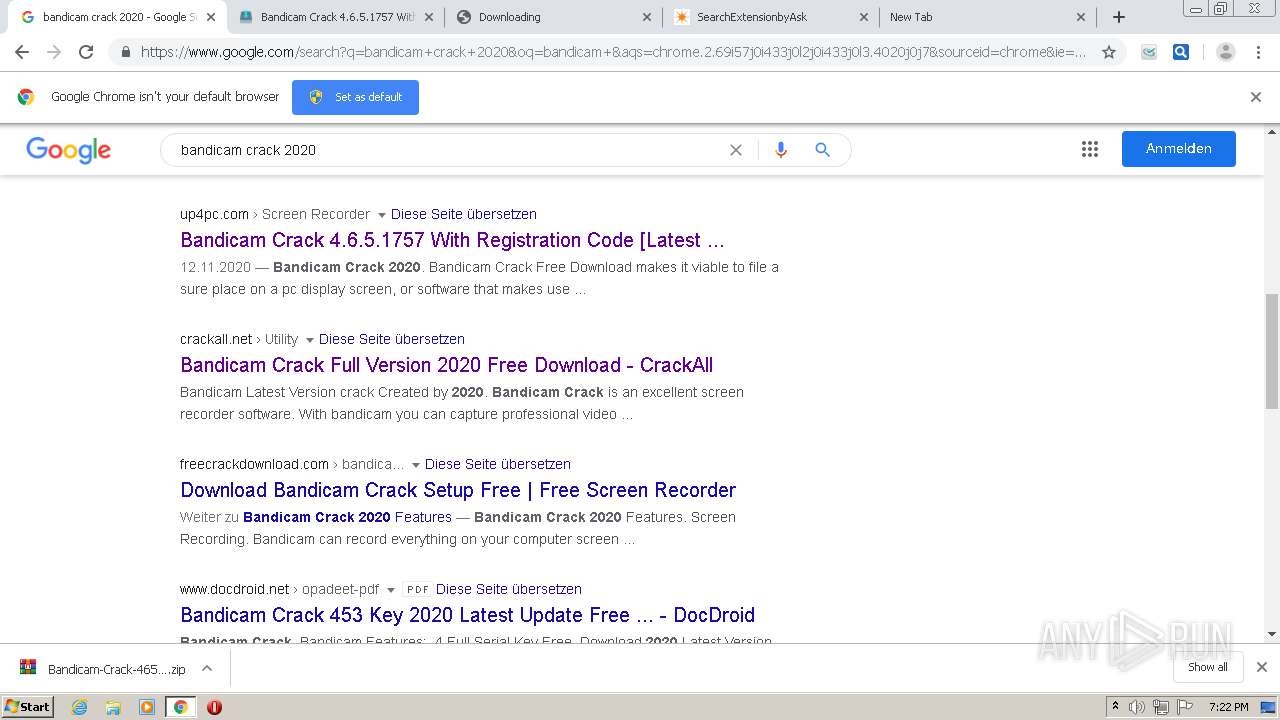
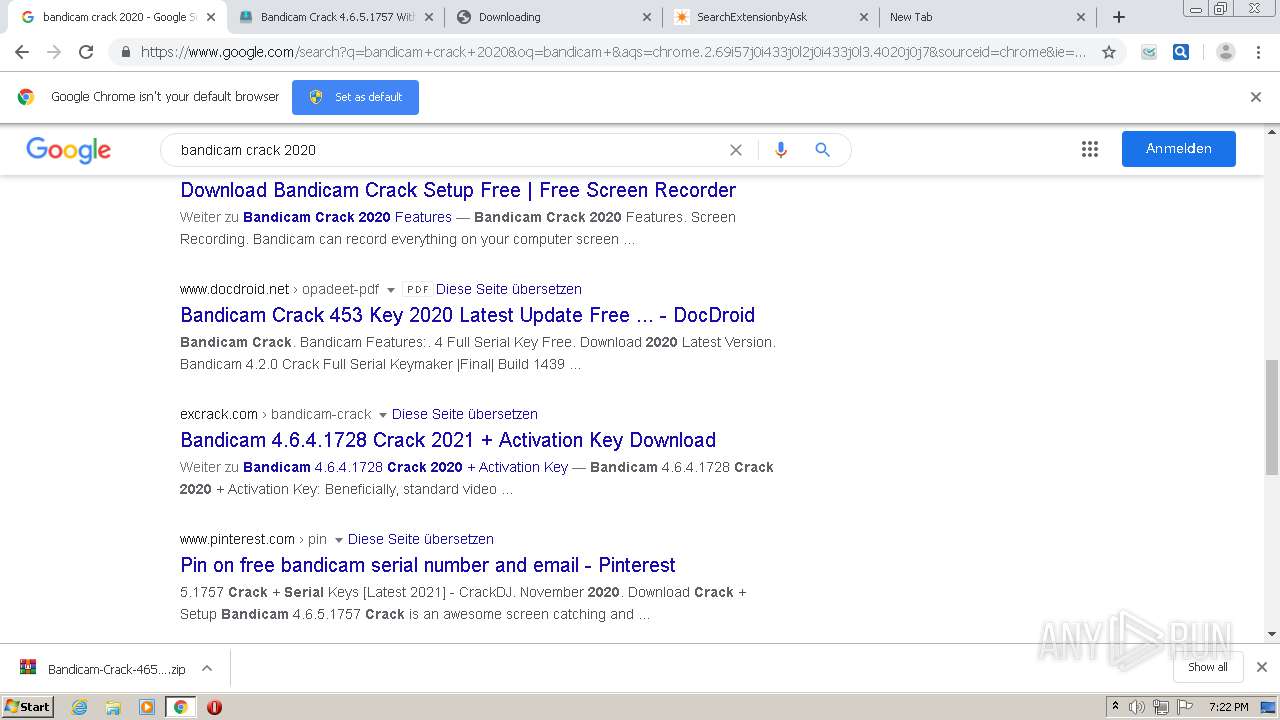
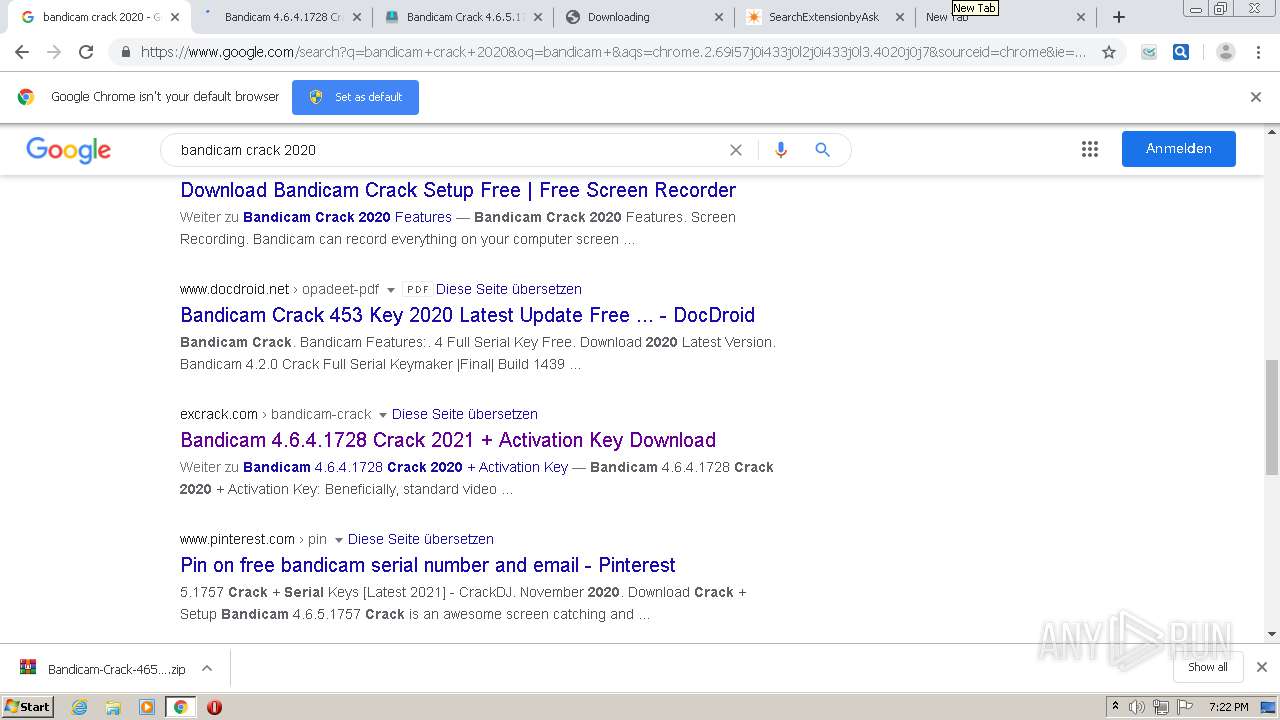
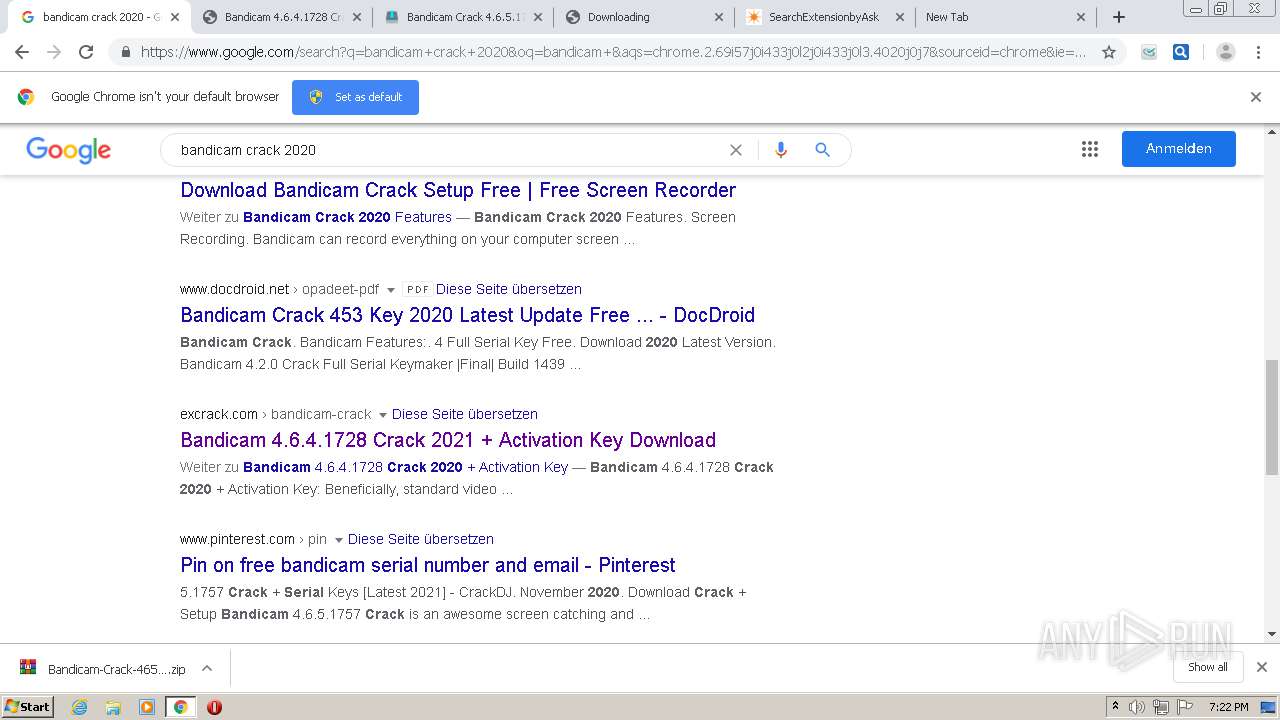
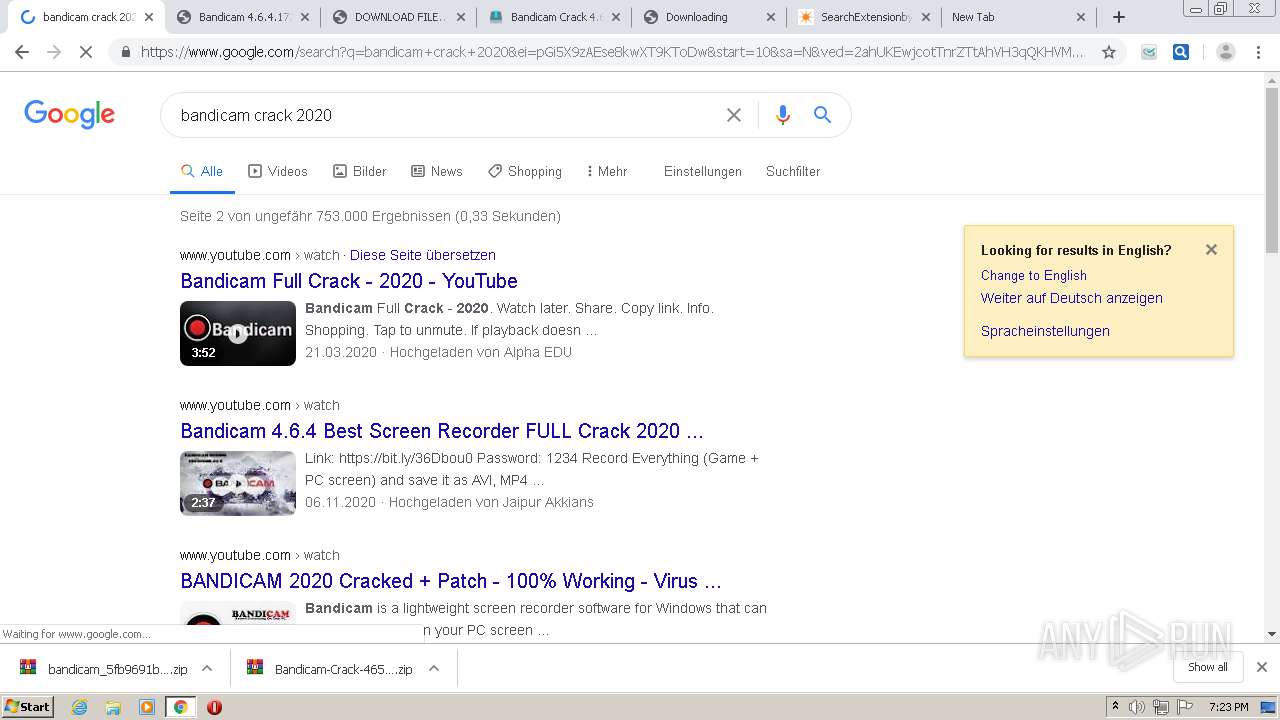
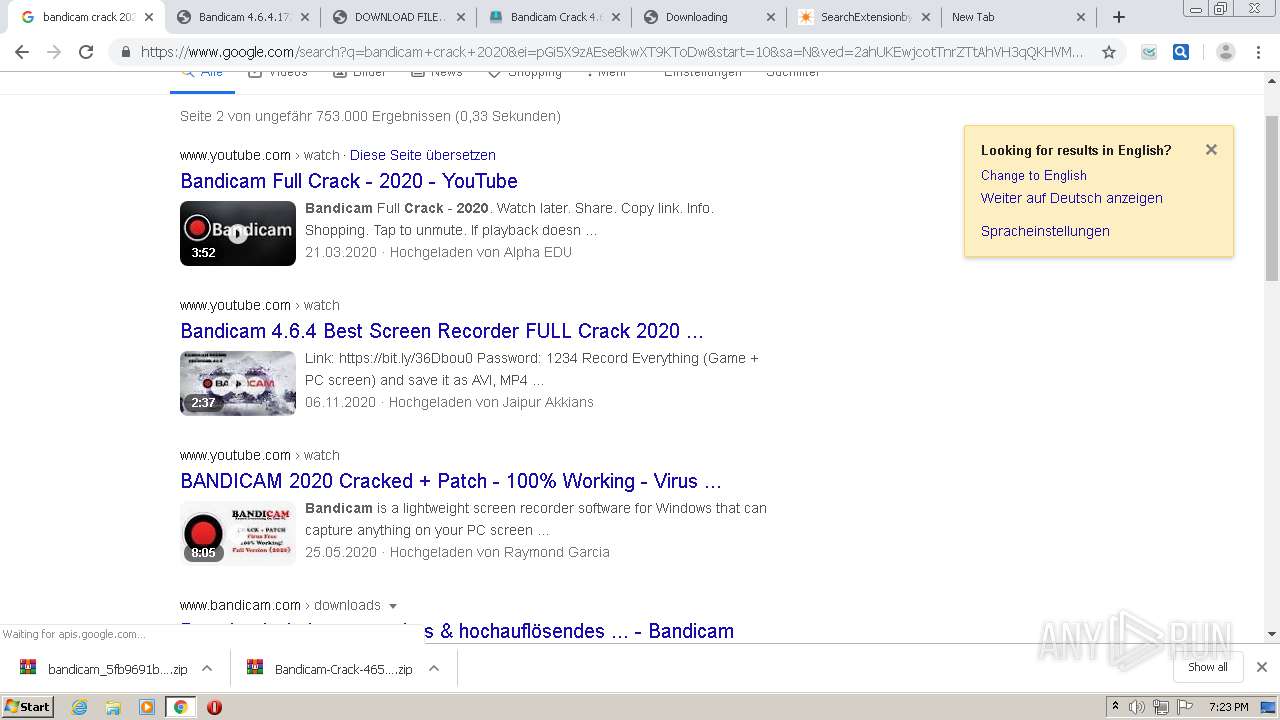
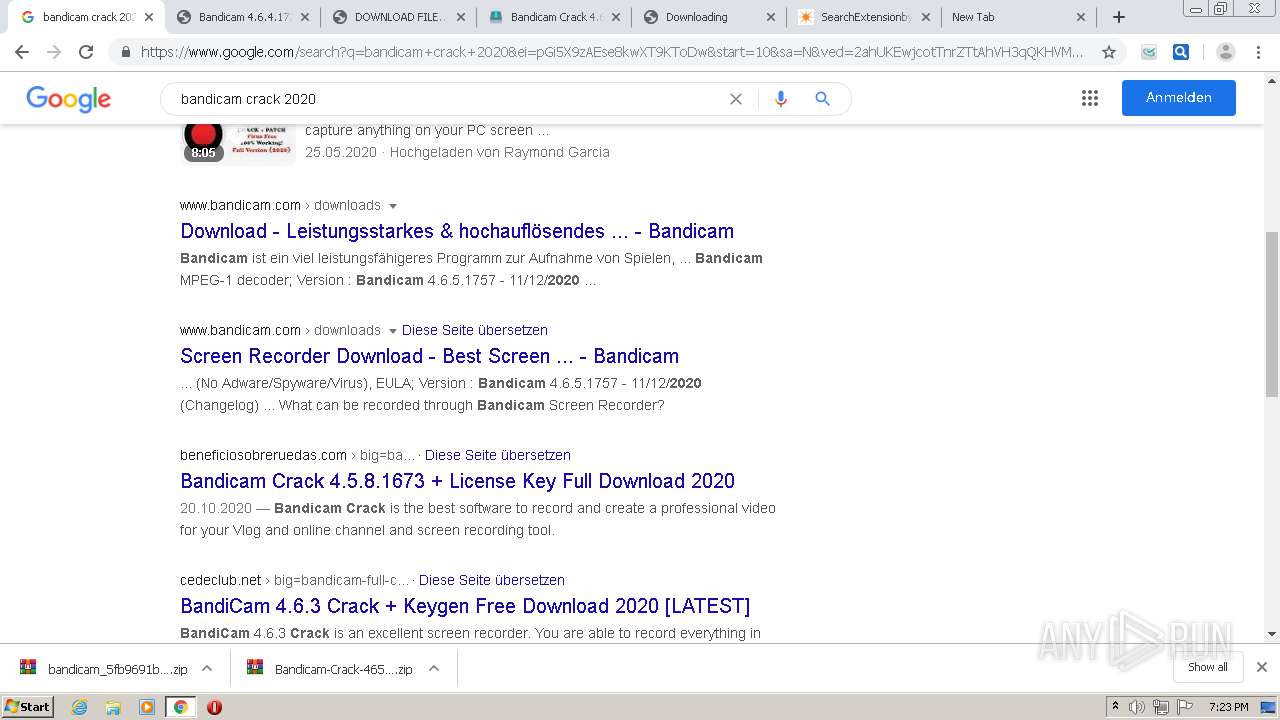
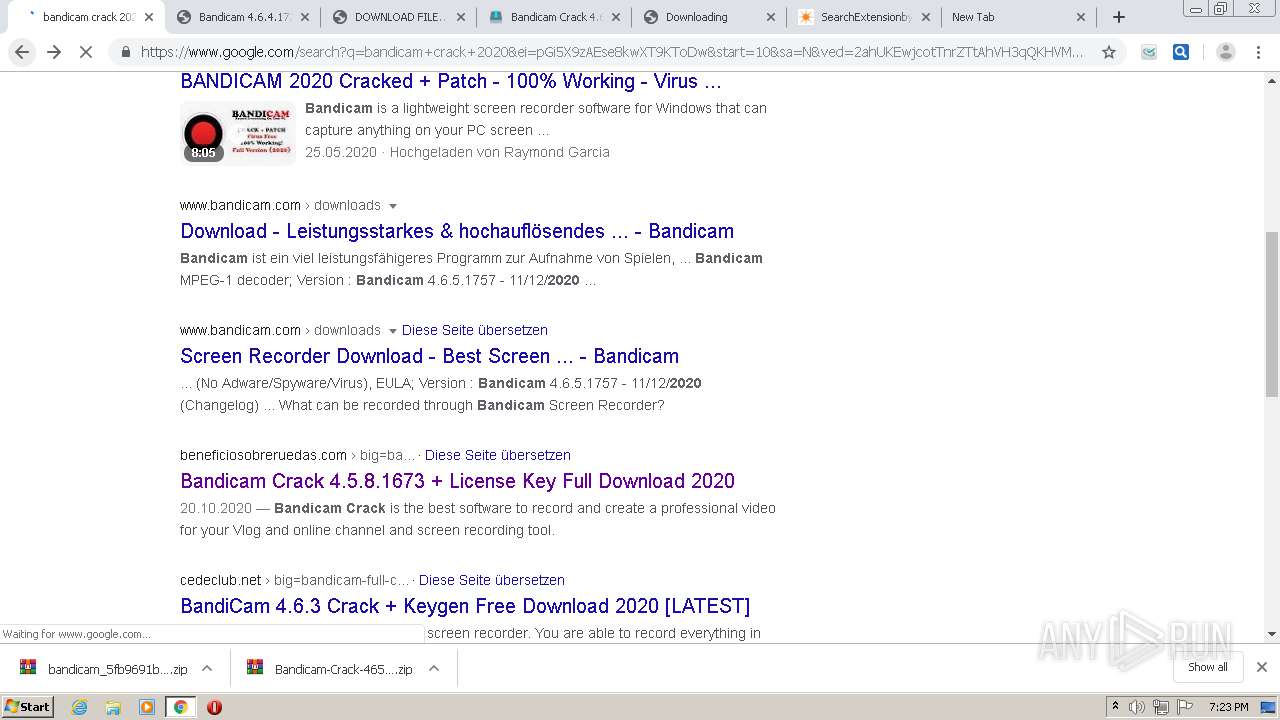
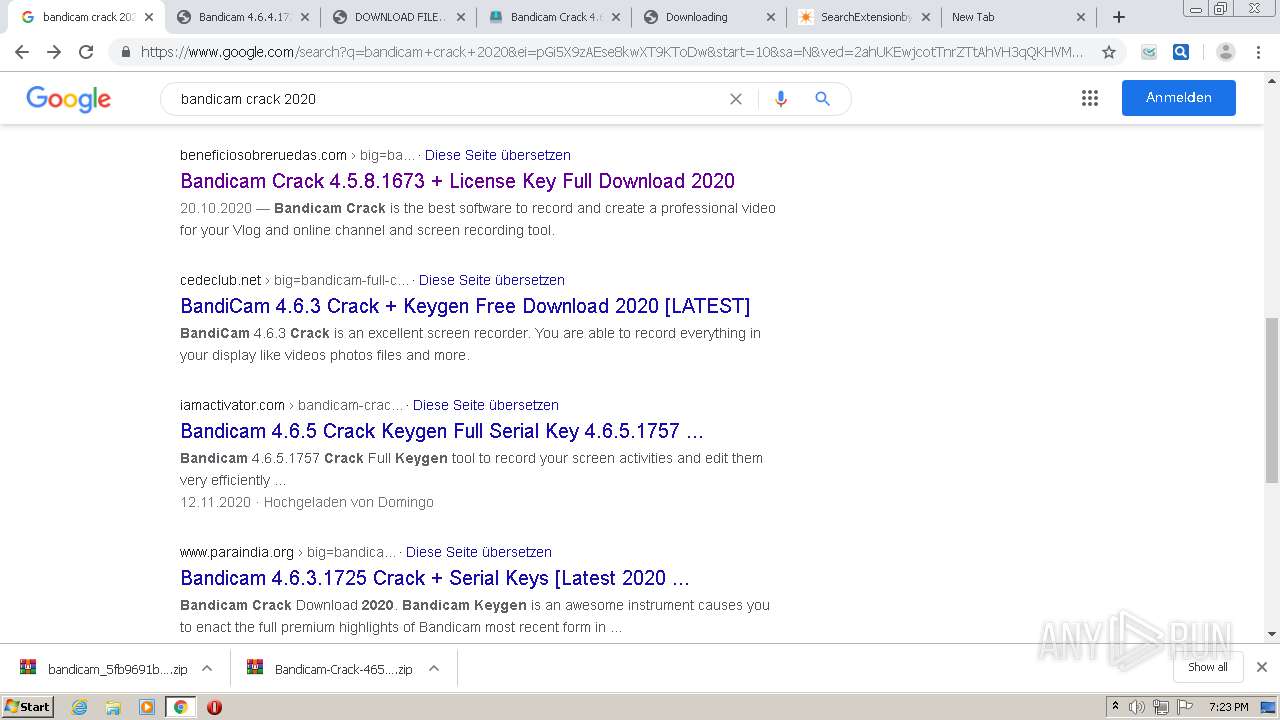
| URL: | https://www.google.com/search?q=bandicam+crack+2020&oq=bandicam+&aqs=chrome.2.69i57j0i433j0l2j0i433j0l3.4020j0j7&sourceid=chrome&ie=UTF-8 |
| Full analysis: | https://app.any.run/tasks/45acd09a-fd41-4446-83f5-9ad5fcb1de9f |
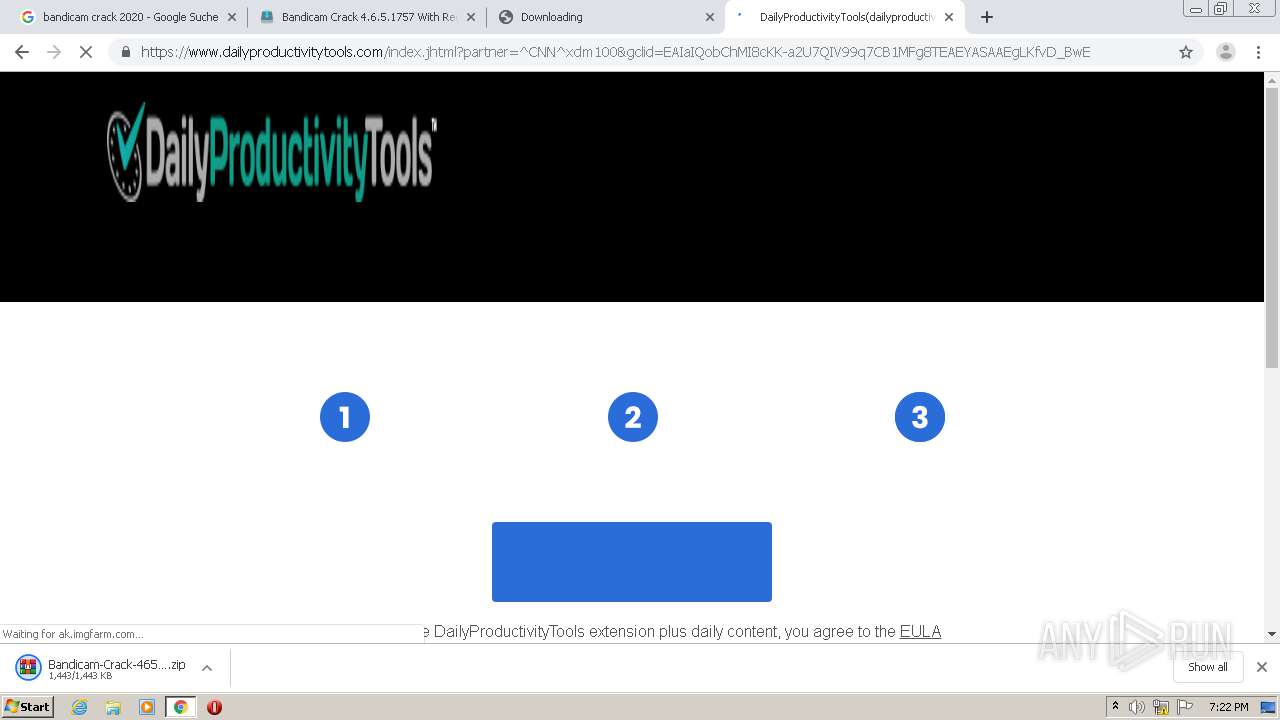
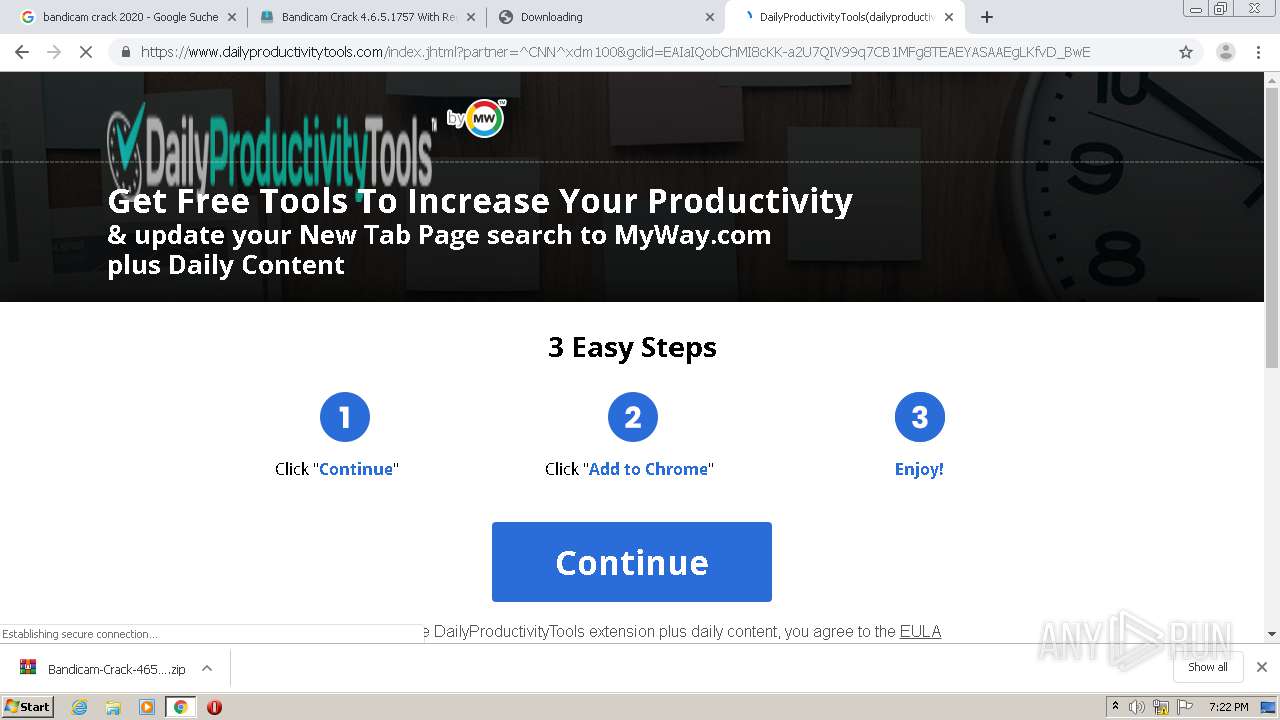
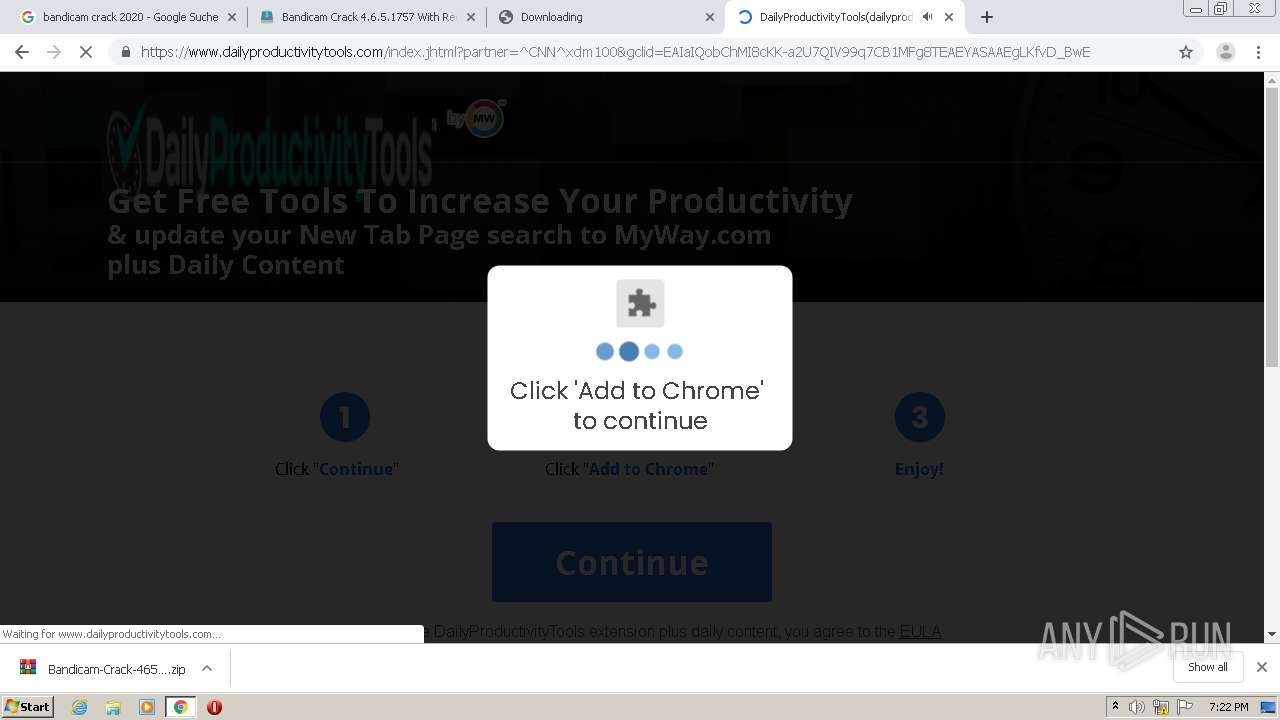
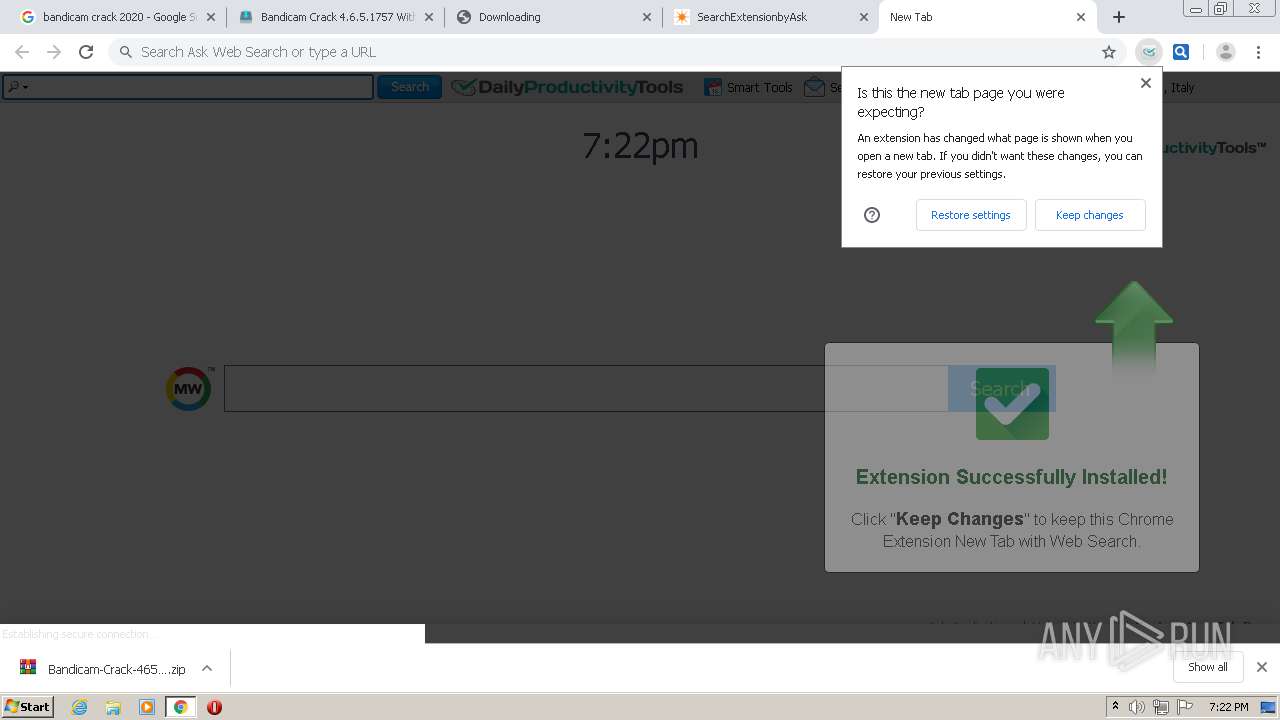
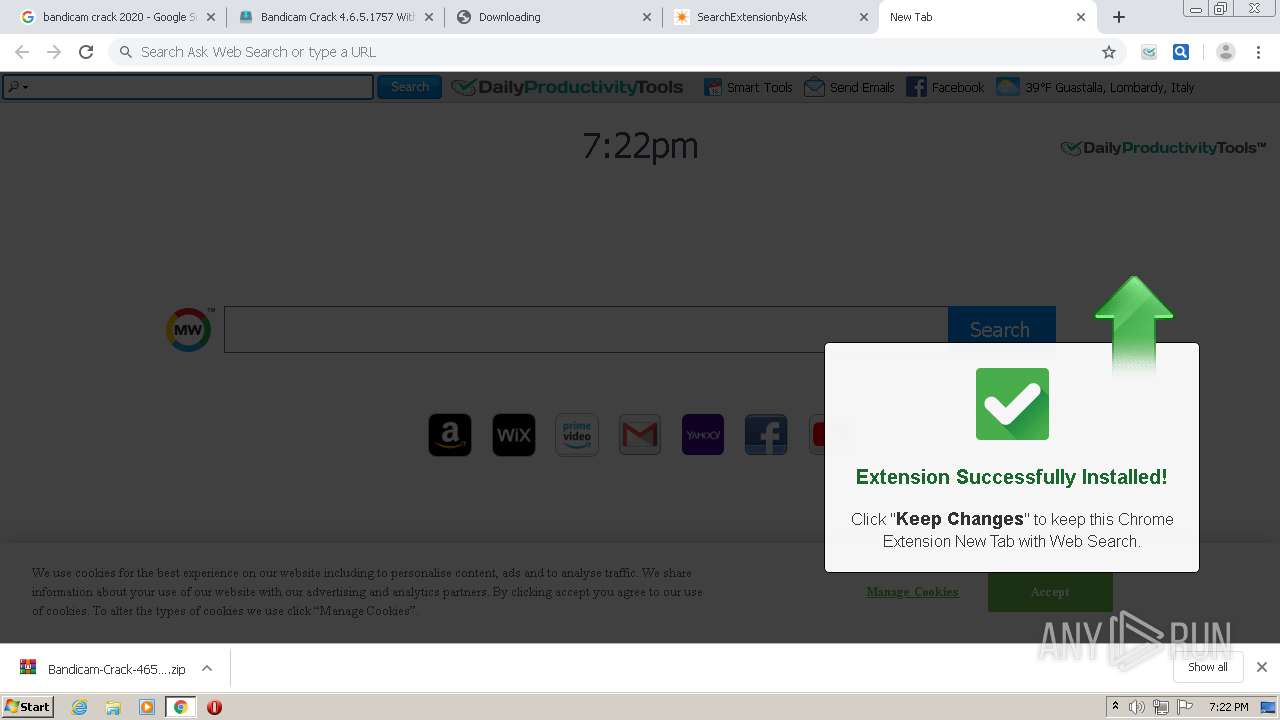
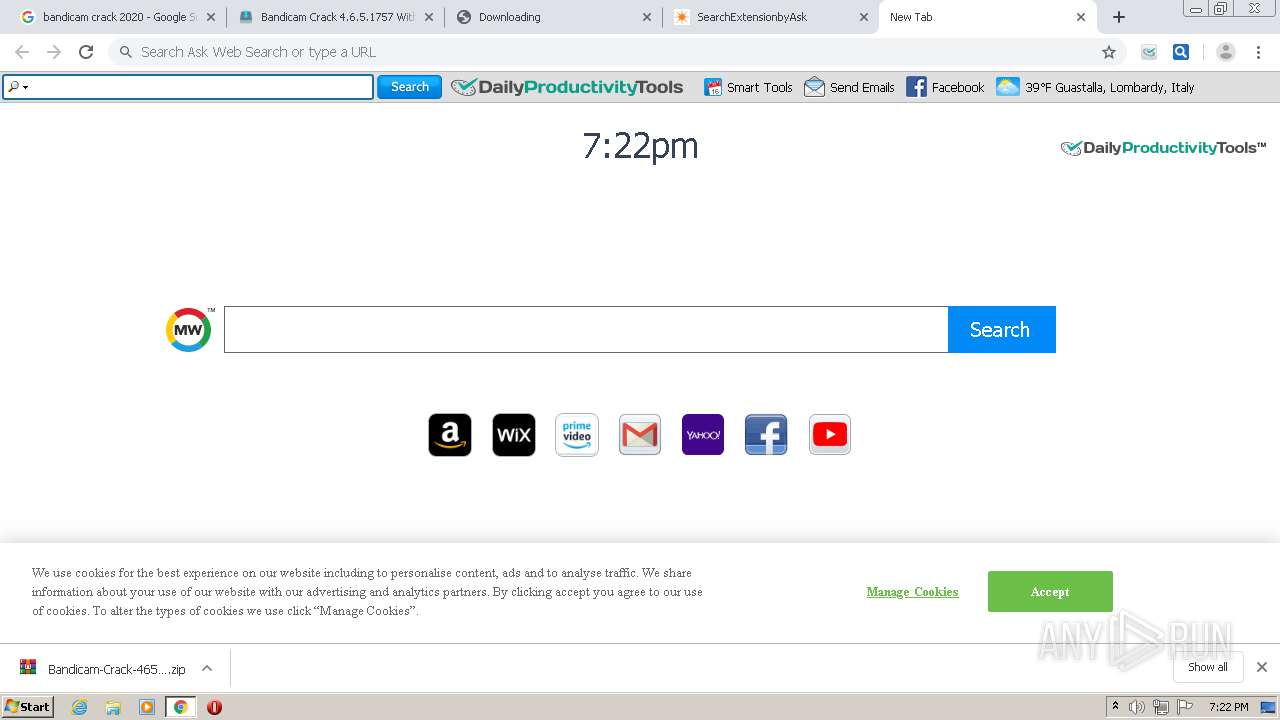
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2020, 19:20:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7A0E0B86331E3B075F75DA5F19723F40 |
| SHA1: | 6EA1E769ABA039C9B13BCFE952429BB3D18B09C6 |
| SHA256: | C16EF9F3A2DCA1B6C465479B1F80CAB091CAC9432324124E0E4243B899FA996E |
| SSDEEP: | 3:N8DSLIwAEXGp/GTcjXVTqvTvEJAj4wO+wPLRtqDUX9GiVzjId:2OLIwBGwT2yTvEJAj4H+wVwDUTOd |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.google.com/search?q=bandicam+crack+2020&oq=bandicam+&aqs=chrome.2.69i57j0i433j0l2j0i433j0l3.4020j0j7&sourceid=chrome&ie=UTF-8" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
192
DNS requests
123
Threats
196
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
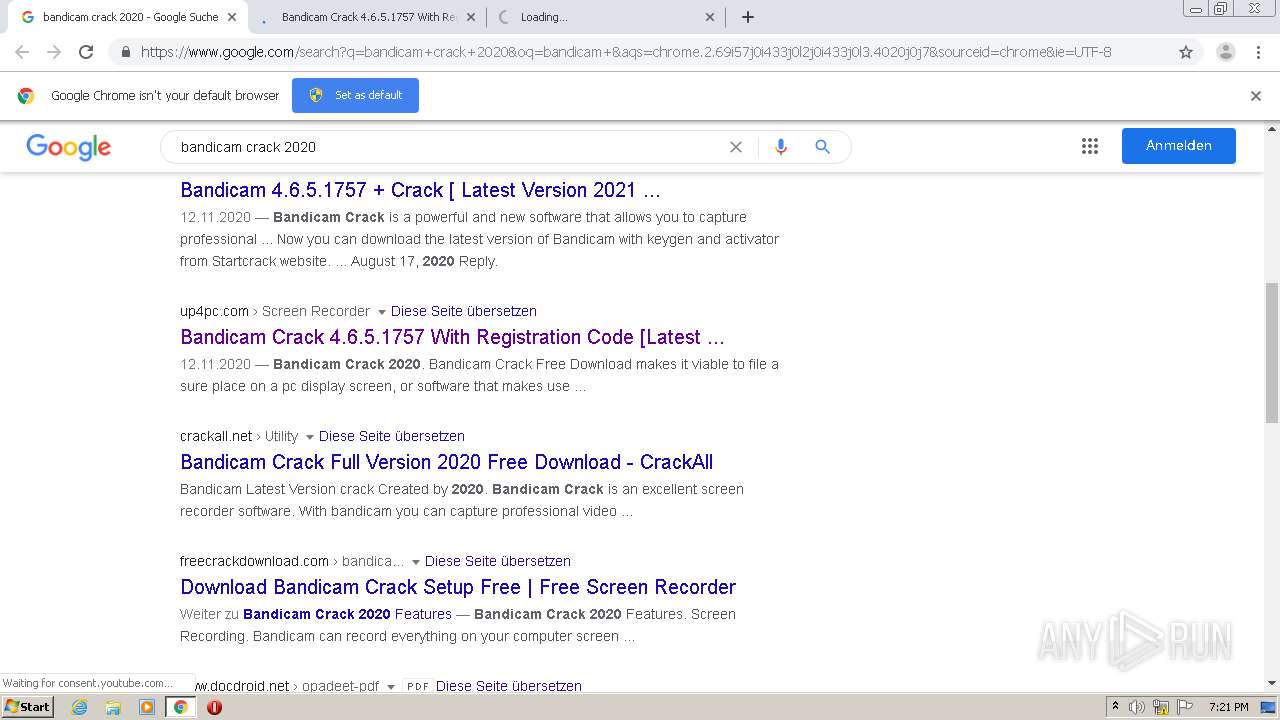
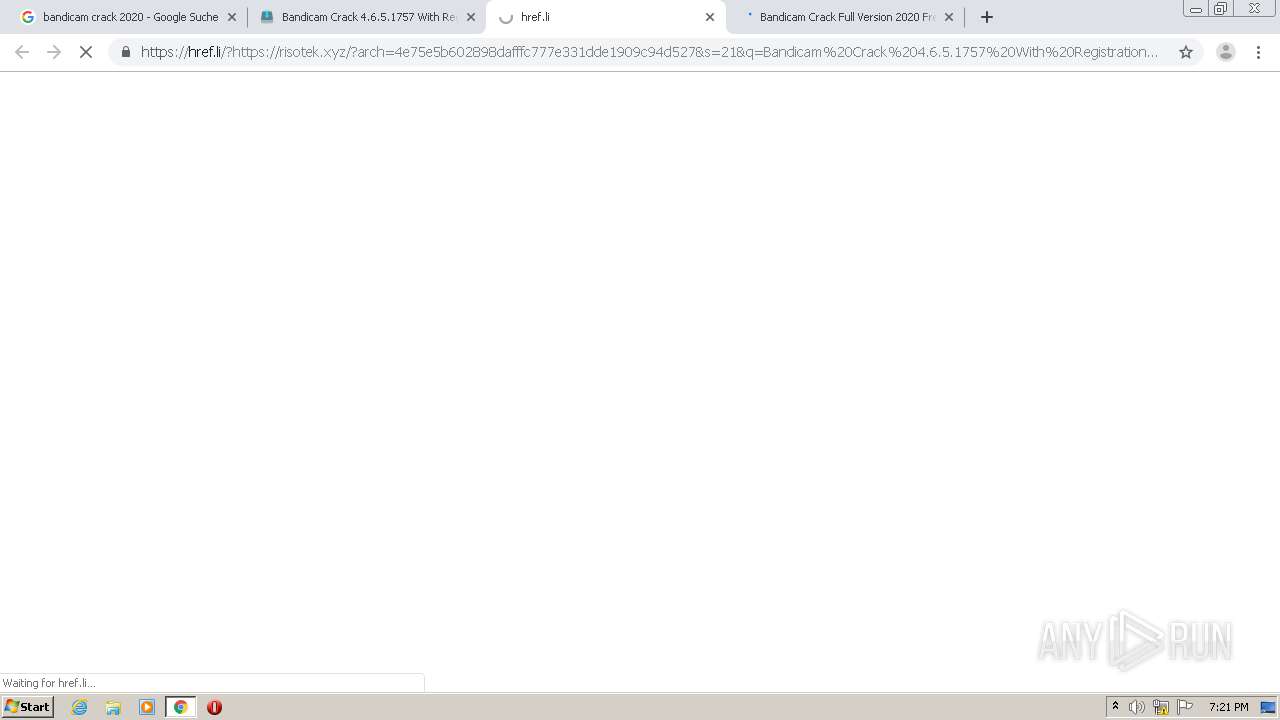
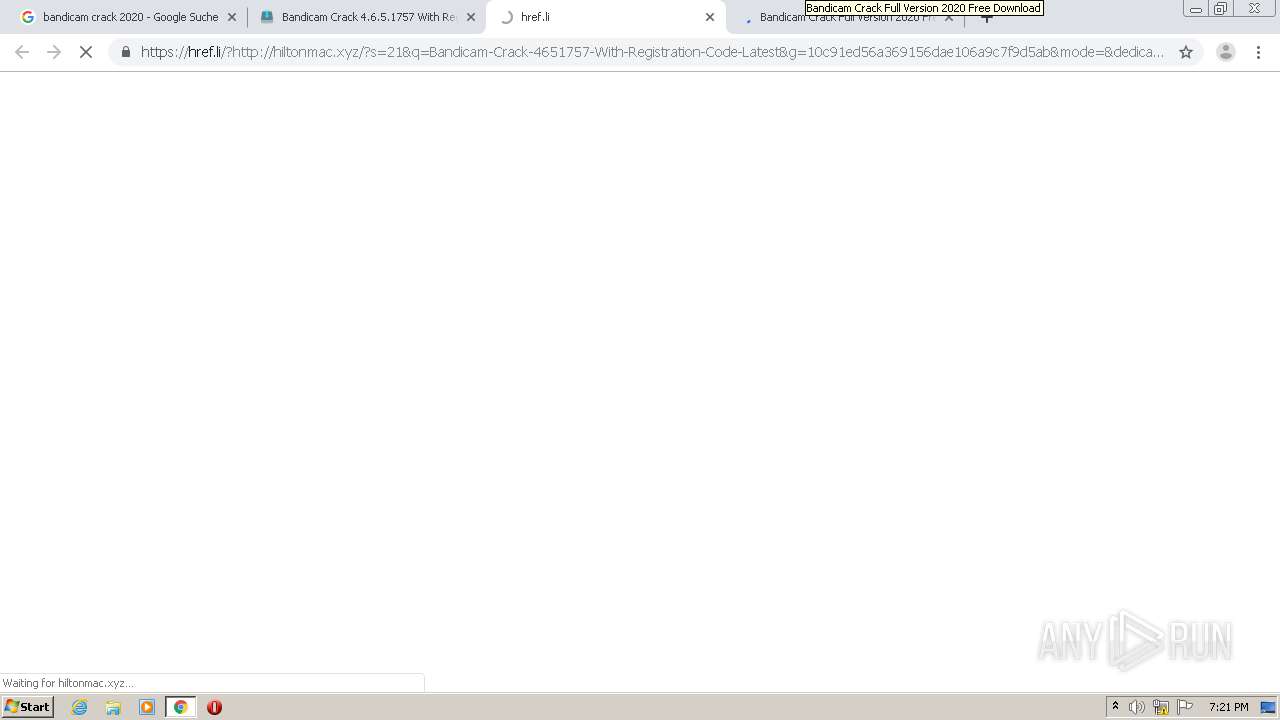
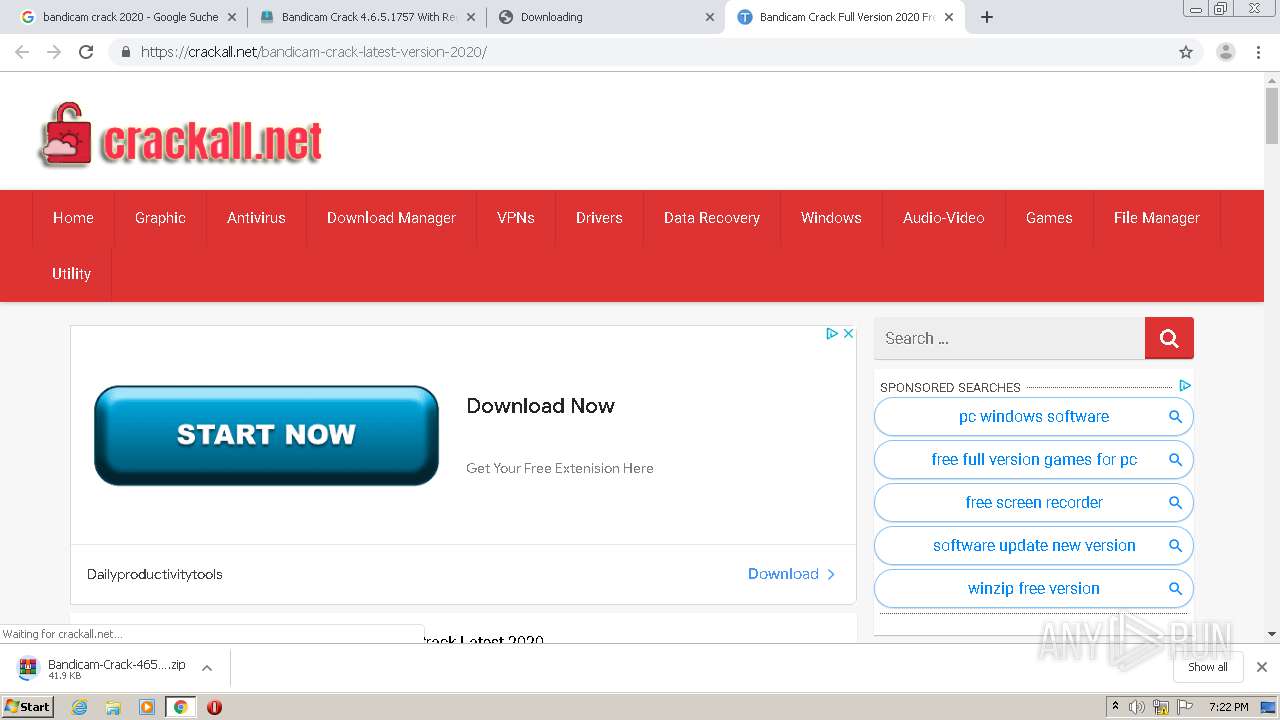
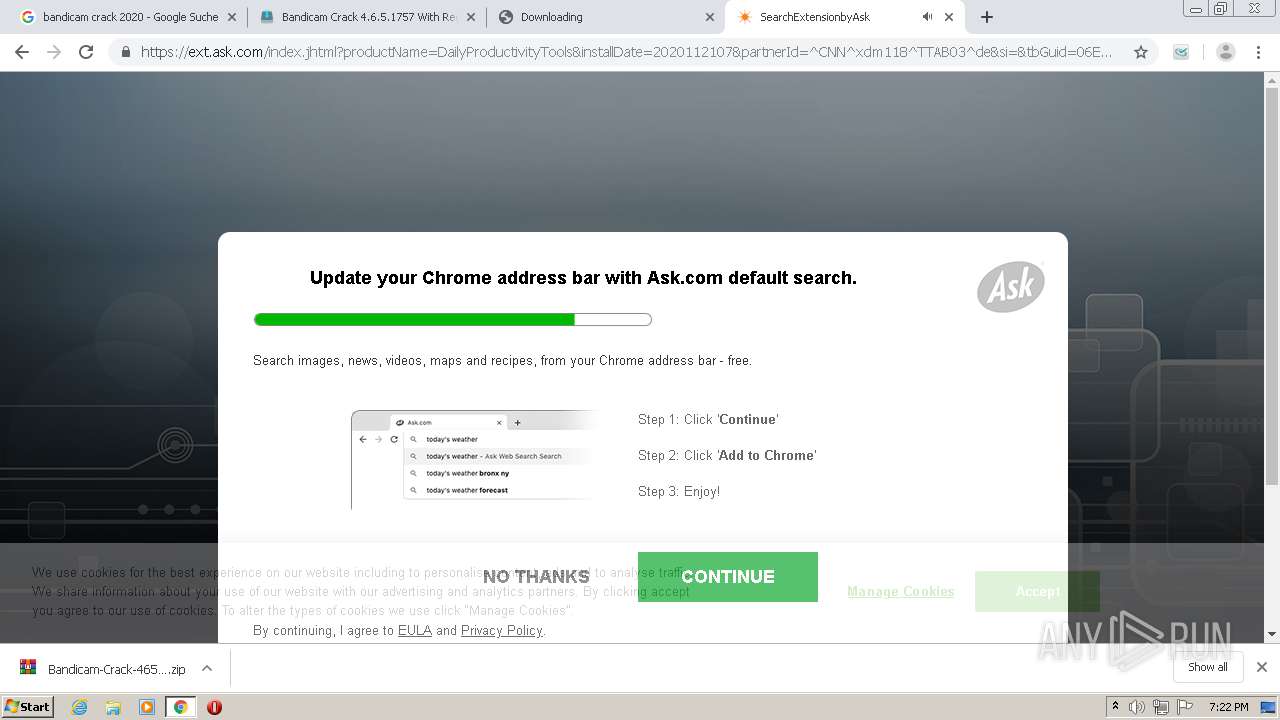
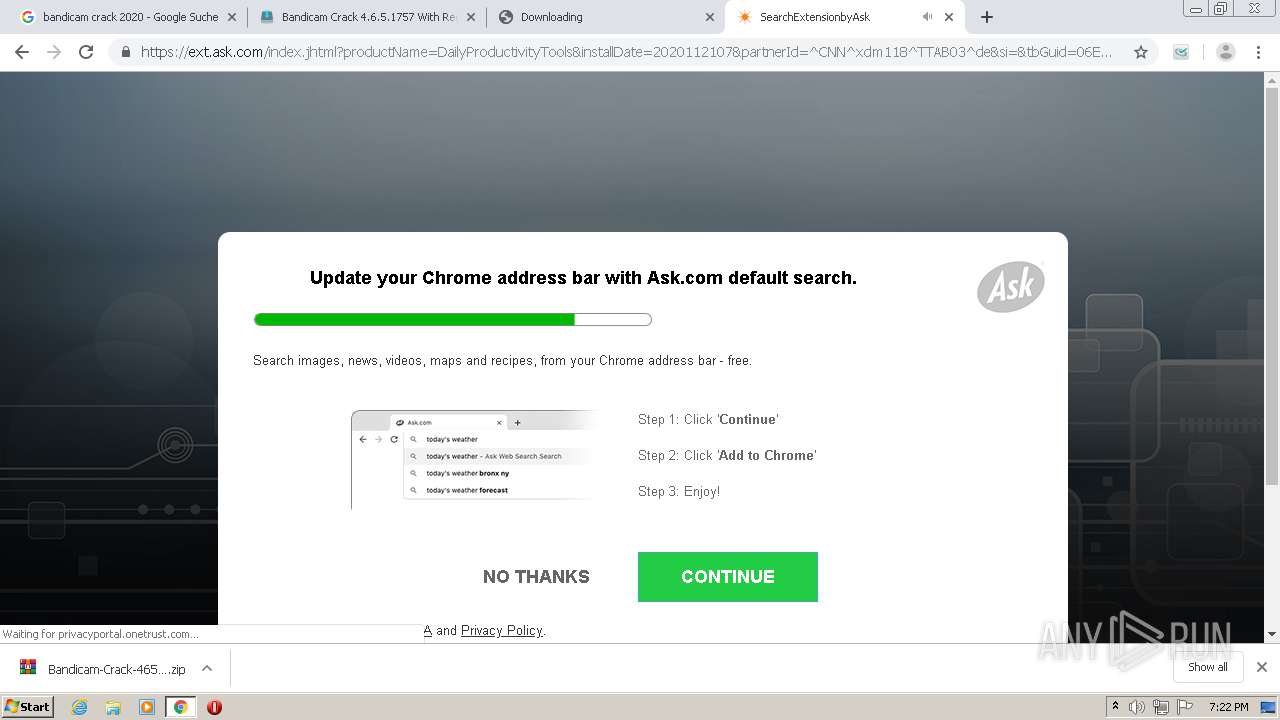
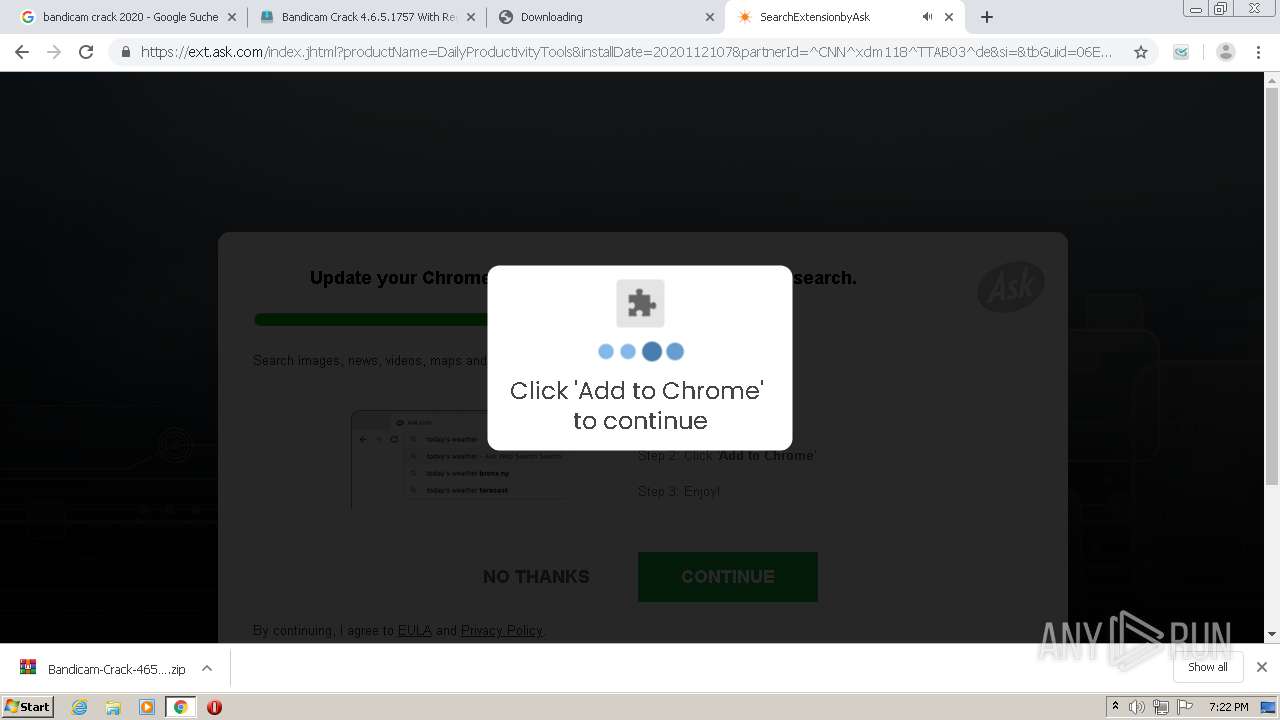
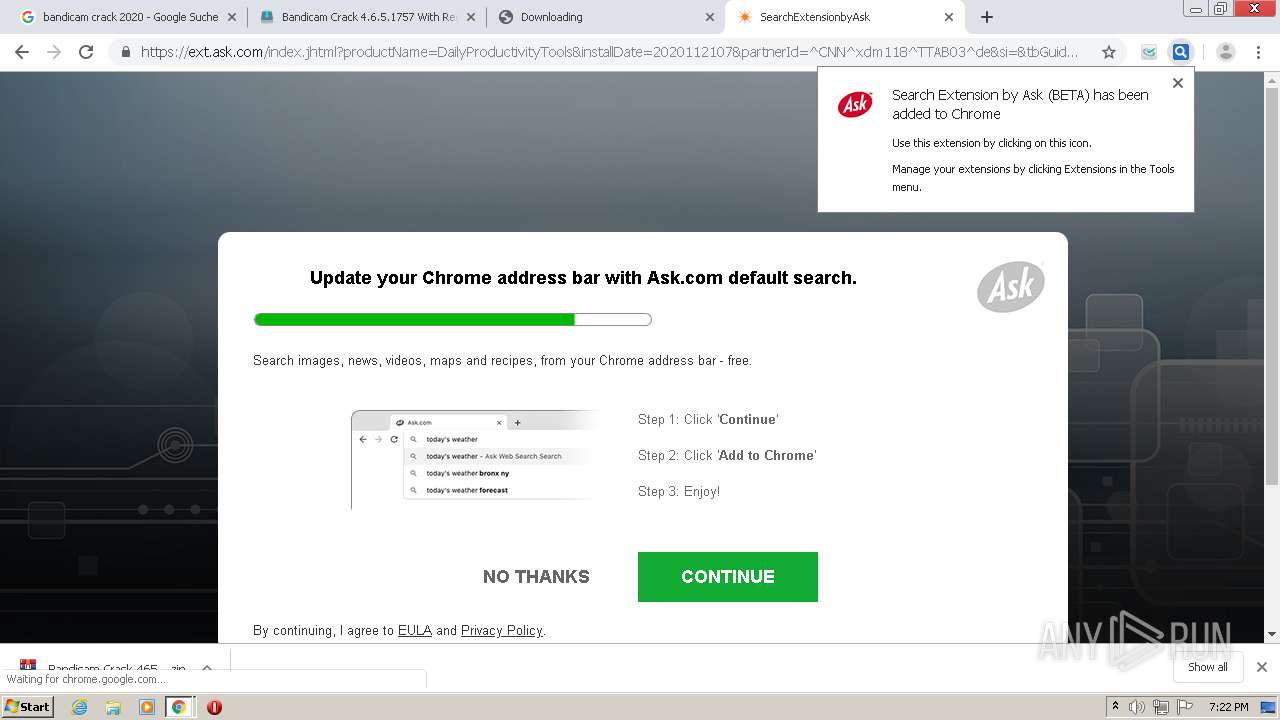
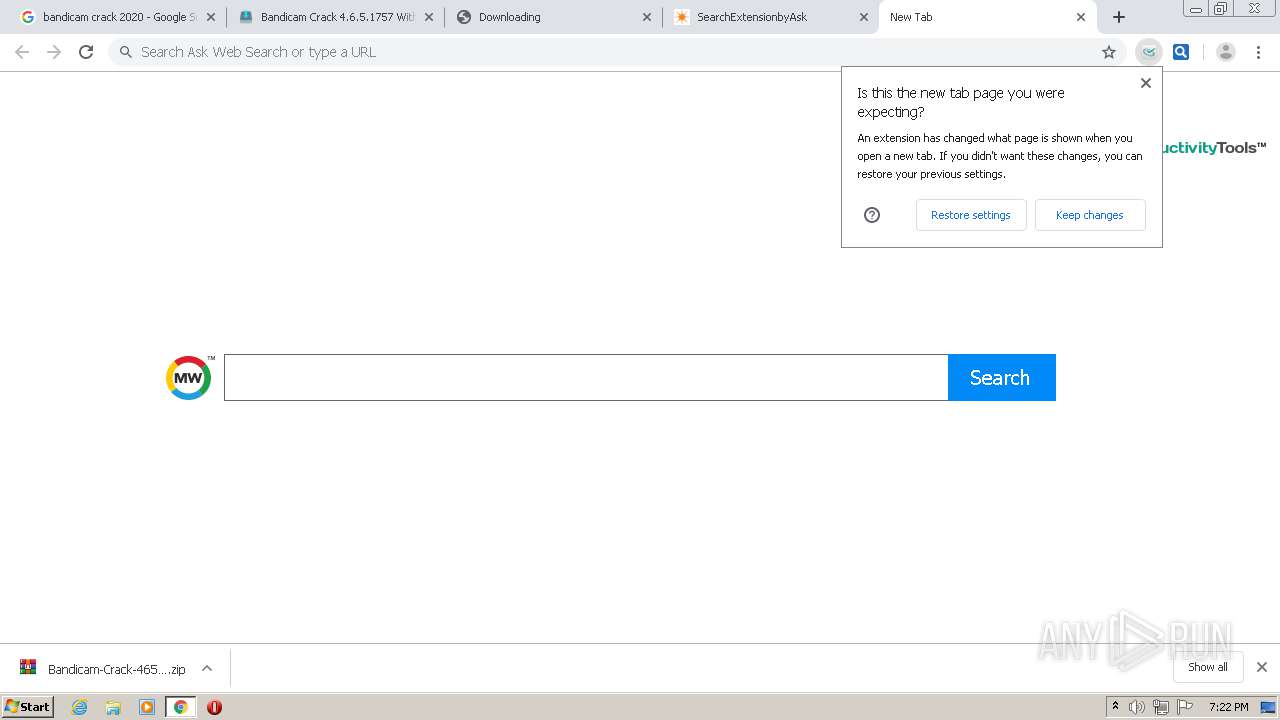
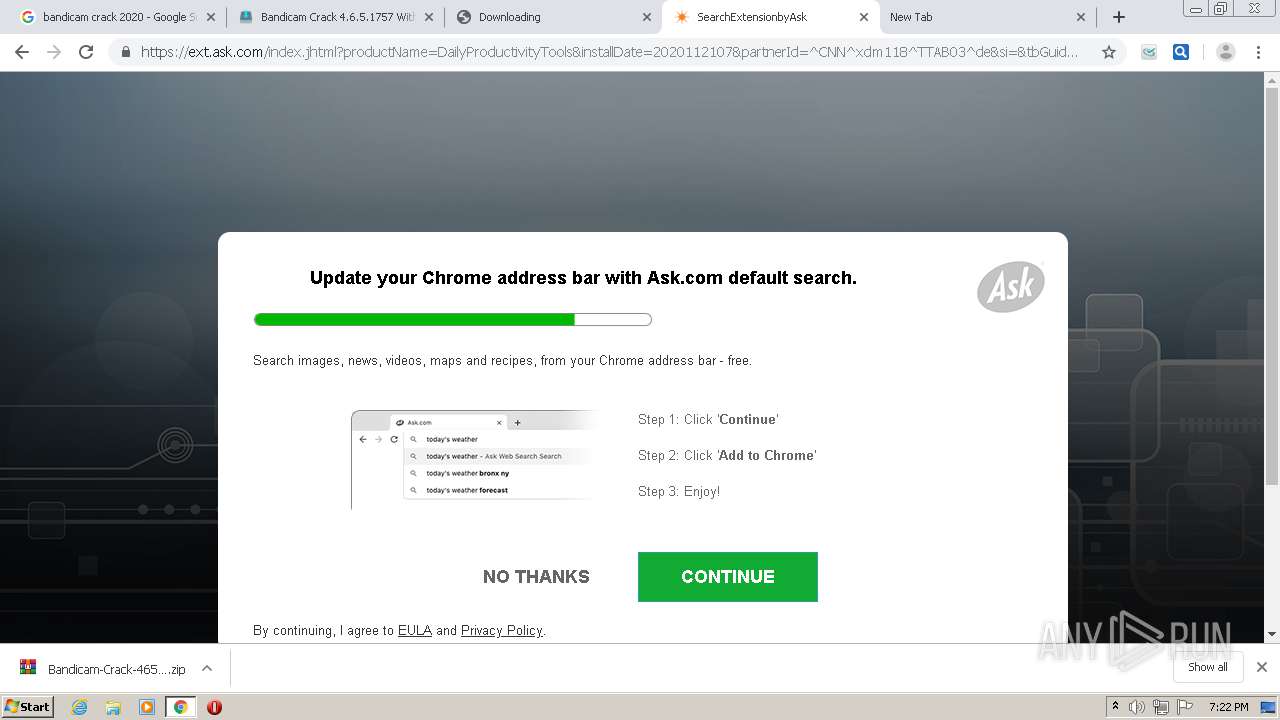
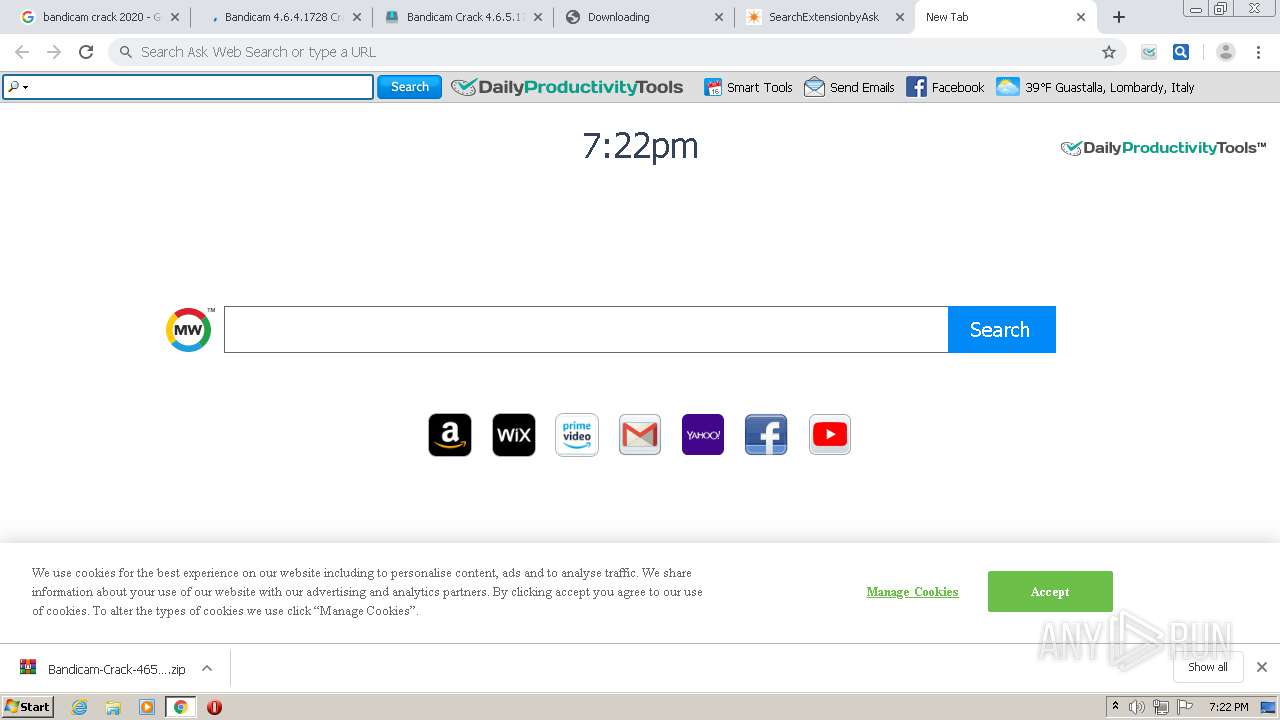
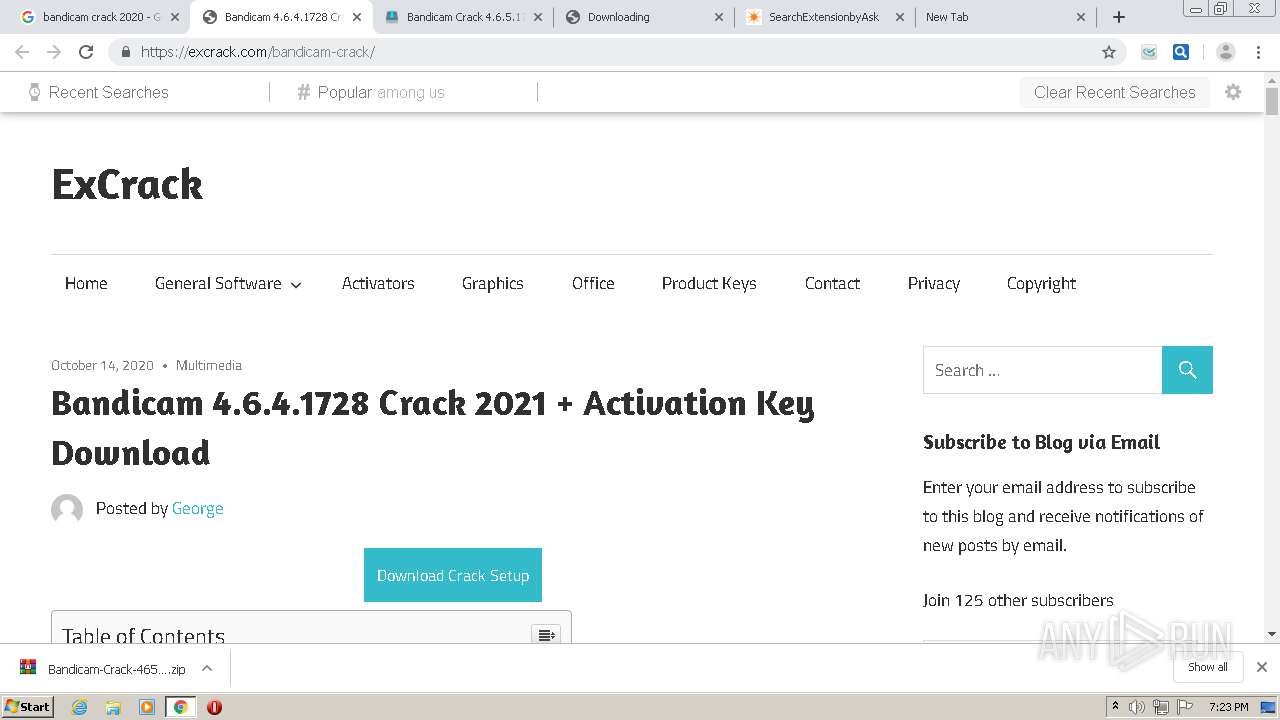
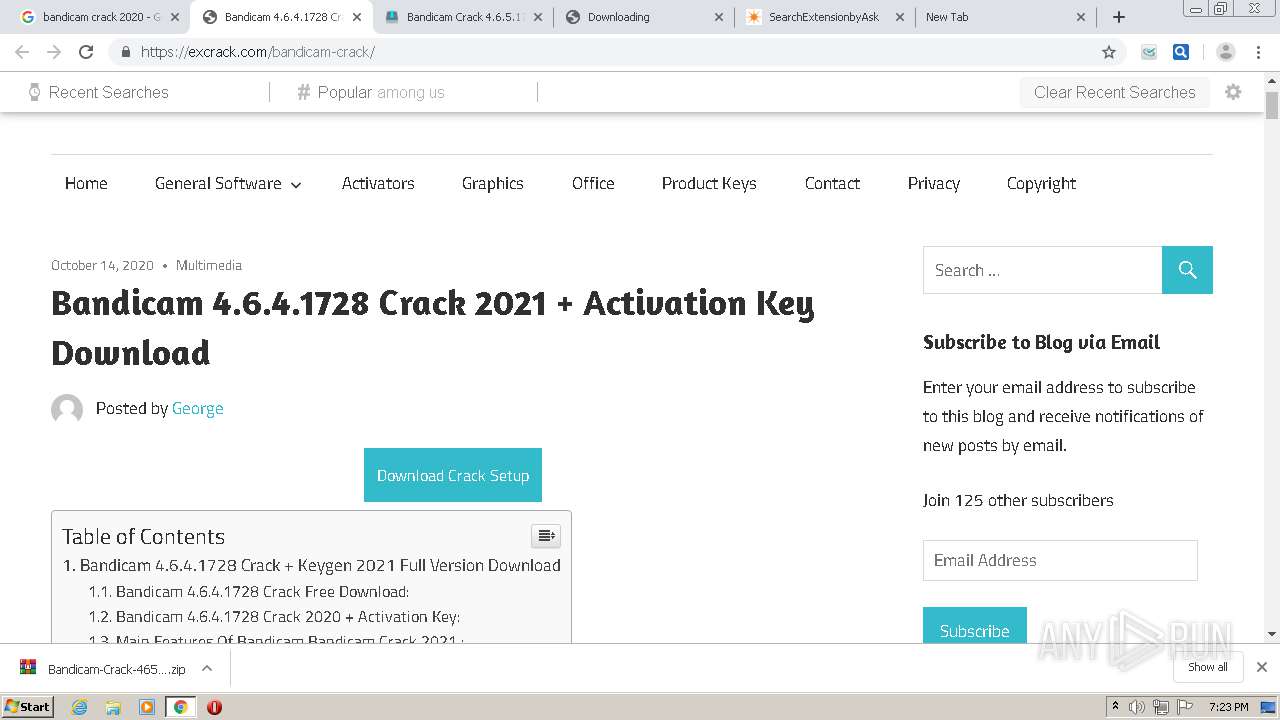
— | — | GET | 301 | 172.67.152.75:80 | http://hiltonmac.xyz/?s=21&q=Bandicam-Crack-4651757-With-Registration-Code-Latest&g=10c91ed56a369156dae106a9c7f9d5ab&mode=&dedica=10 | US | — | — | suspicious |
— | — | GET | — | 198.15.92.226:80 | http://www.paraindia.org/?big=bandicam-keygen-full-crack-download/ | US | — | — | malicious |
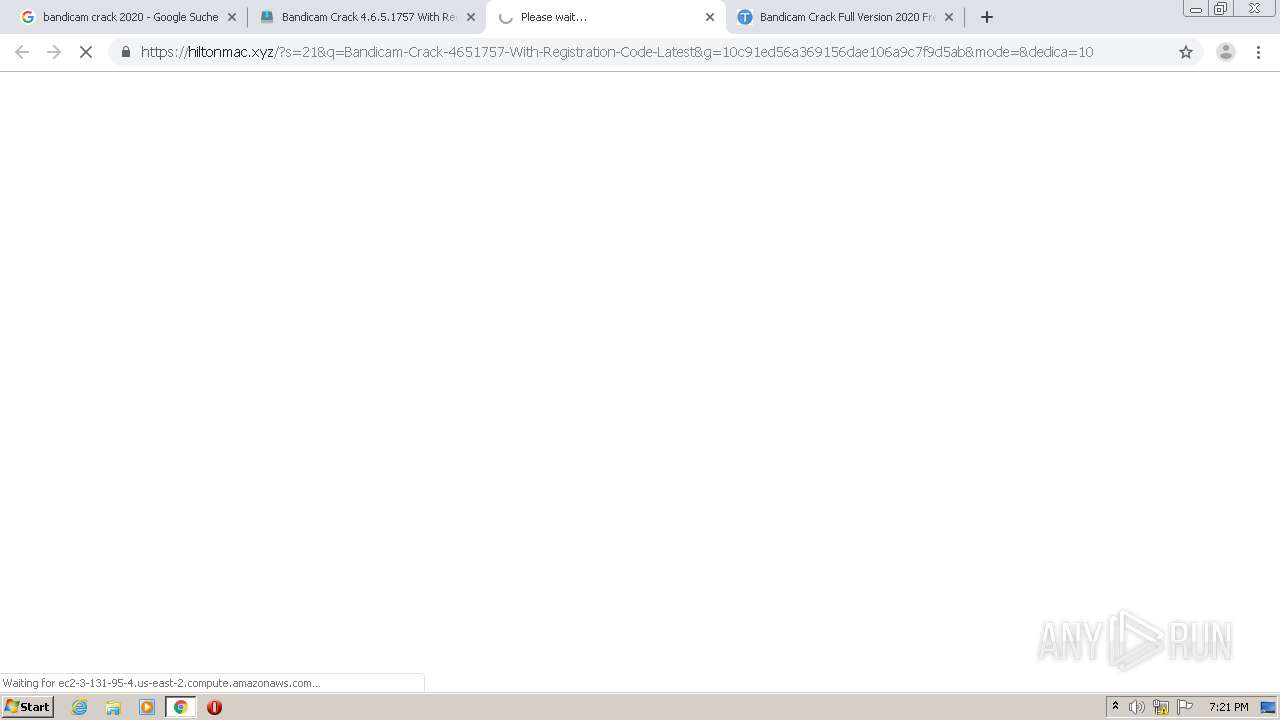
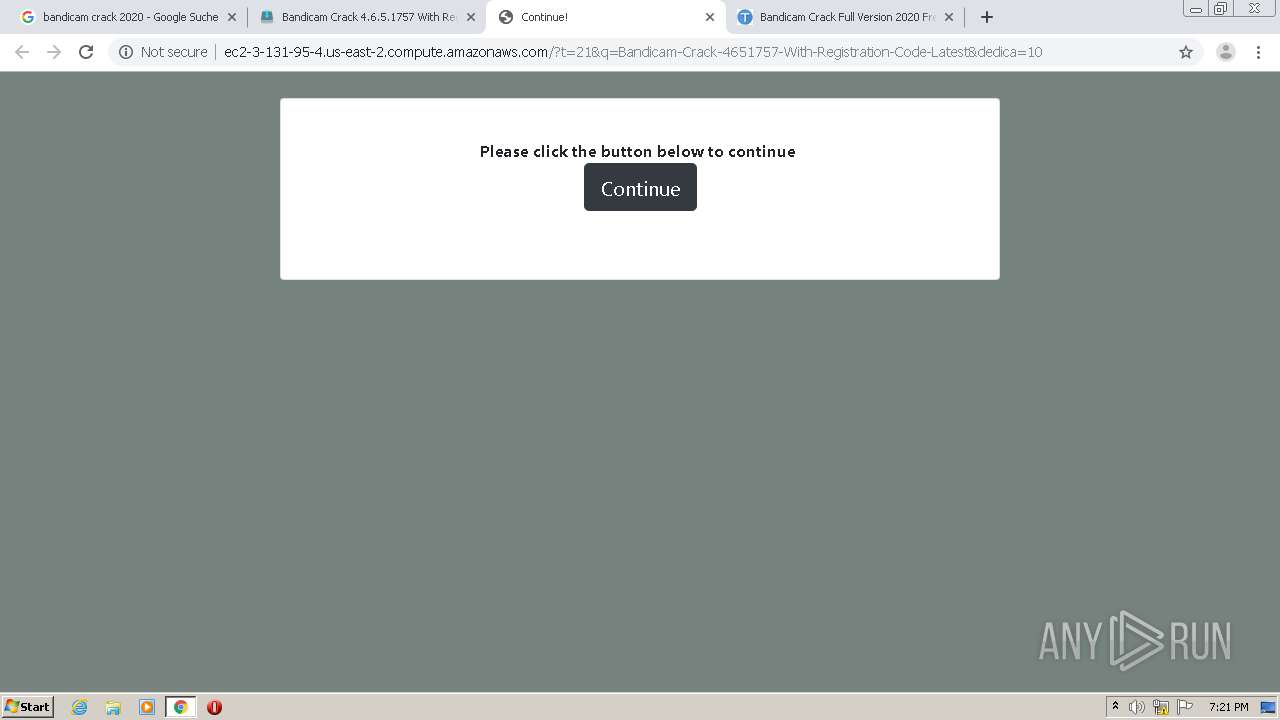
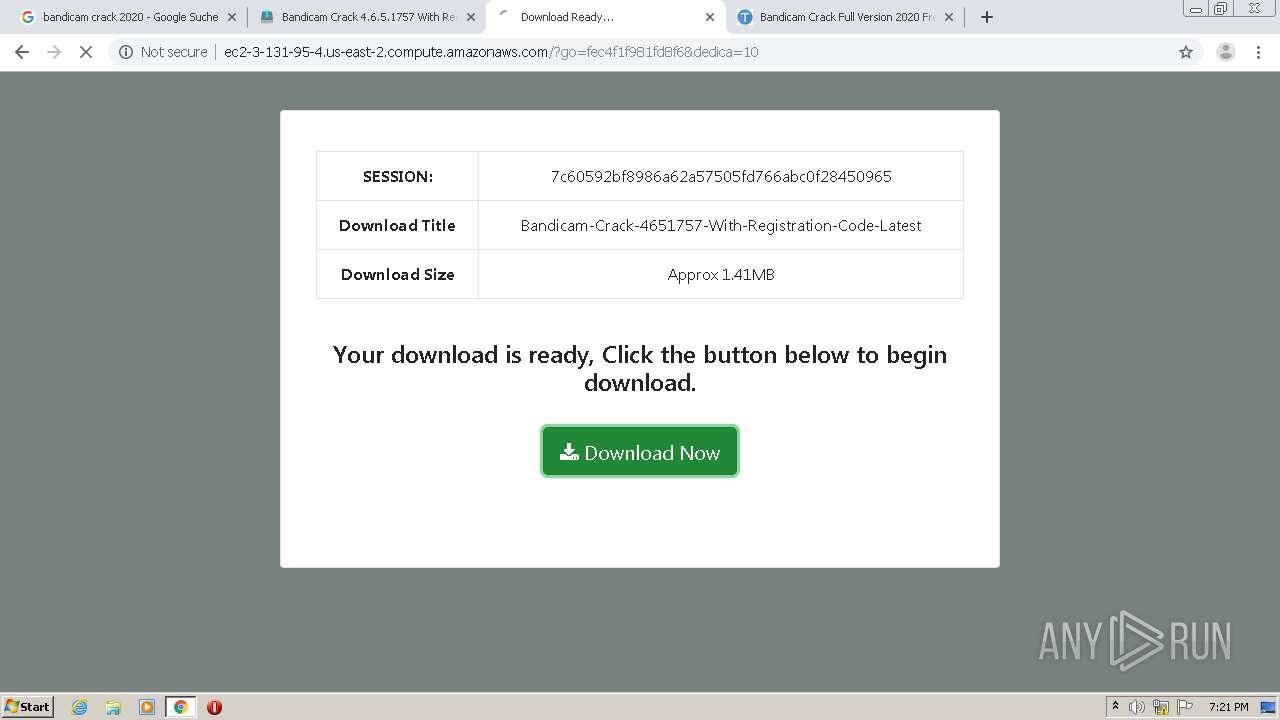
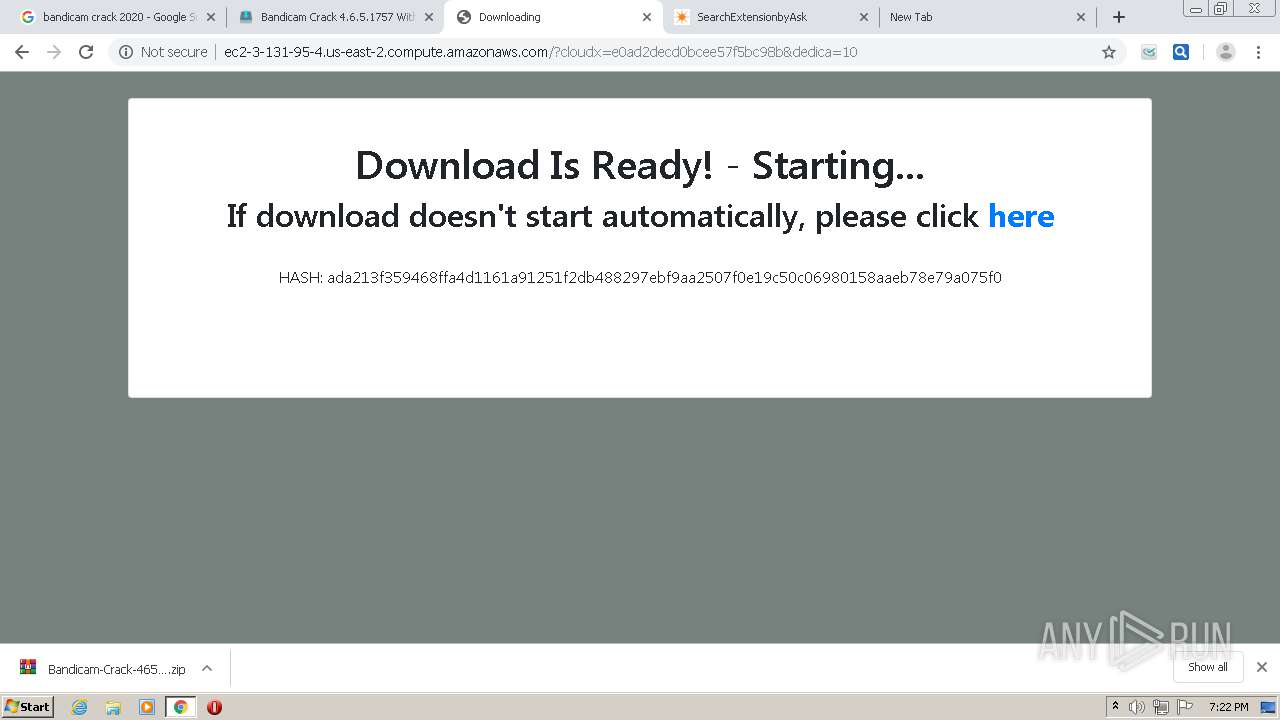
— | — | GET | 302 | 3.131.95.4:80 | http://ec2-3-131-95-4.us-east-2.compute.amazonaws.com/?t=21&q=Bandicam-Crack-4651757-With-Registration-Code-Latest&dedica=10 | US | html | 783 b | shared |
— | — | GET | 404 | 3.131.95.4:80 | http://ec2-3-131-95-4.us-east-2.compute.amazonaws.com/favicon.ico | US | html | 292 b | shared |
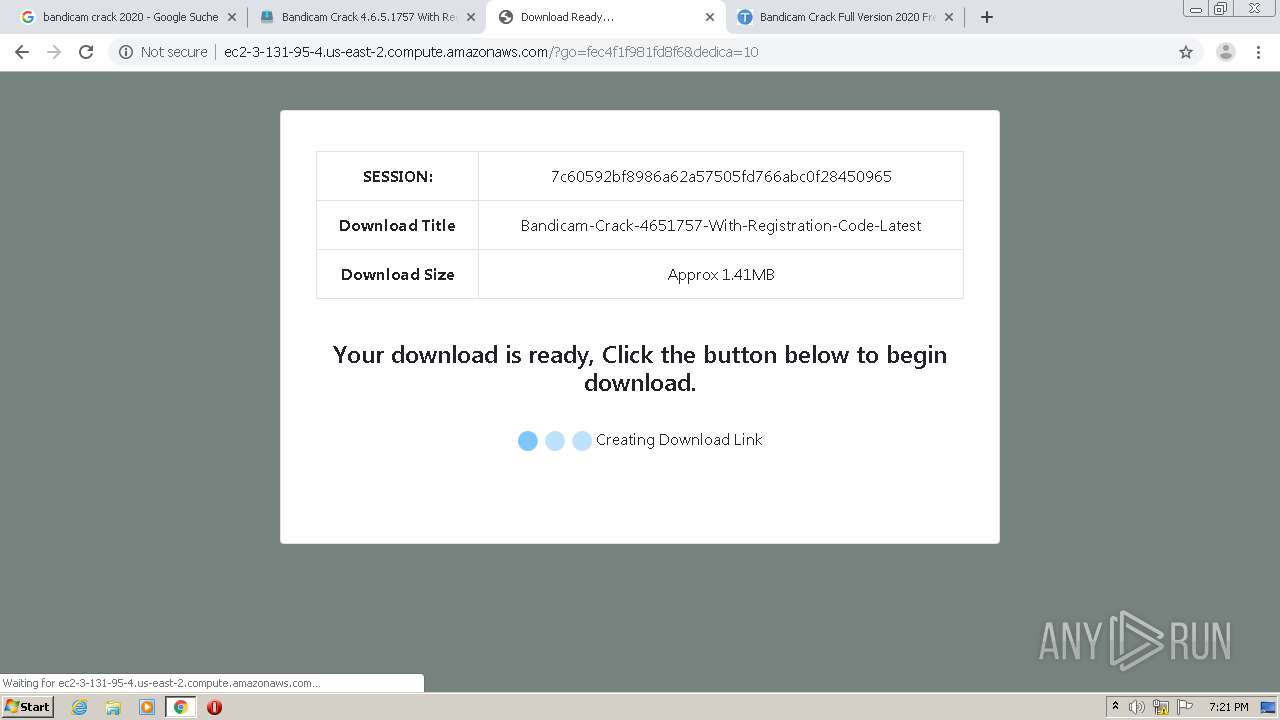
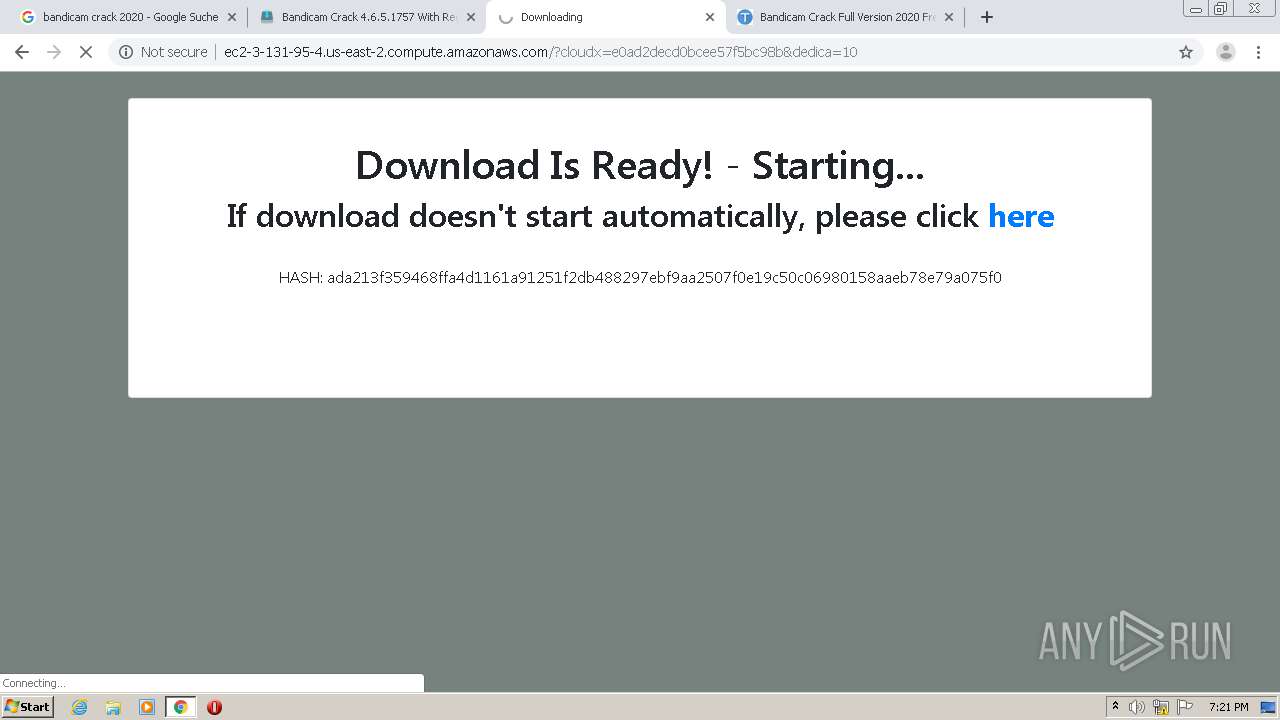
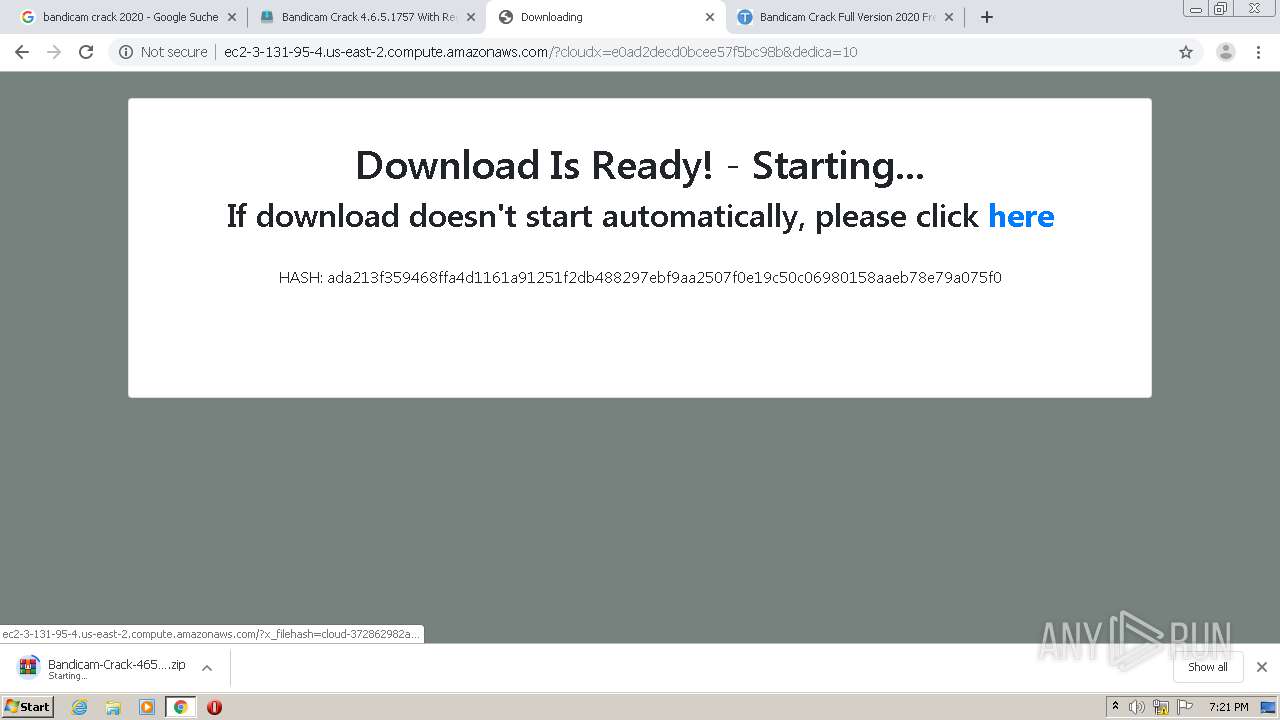
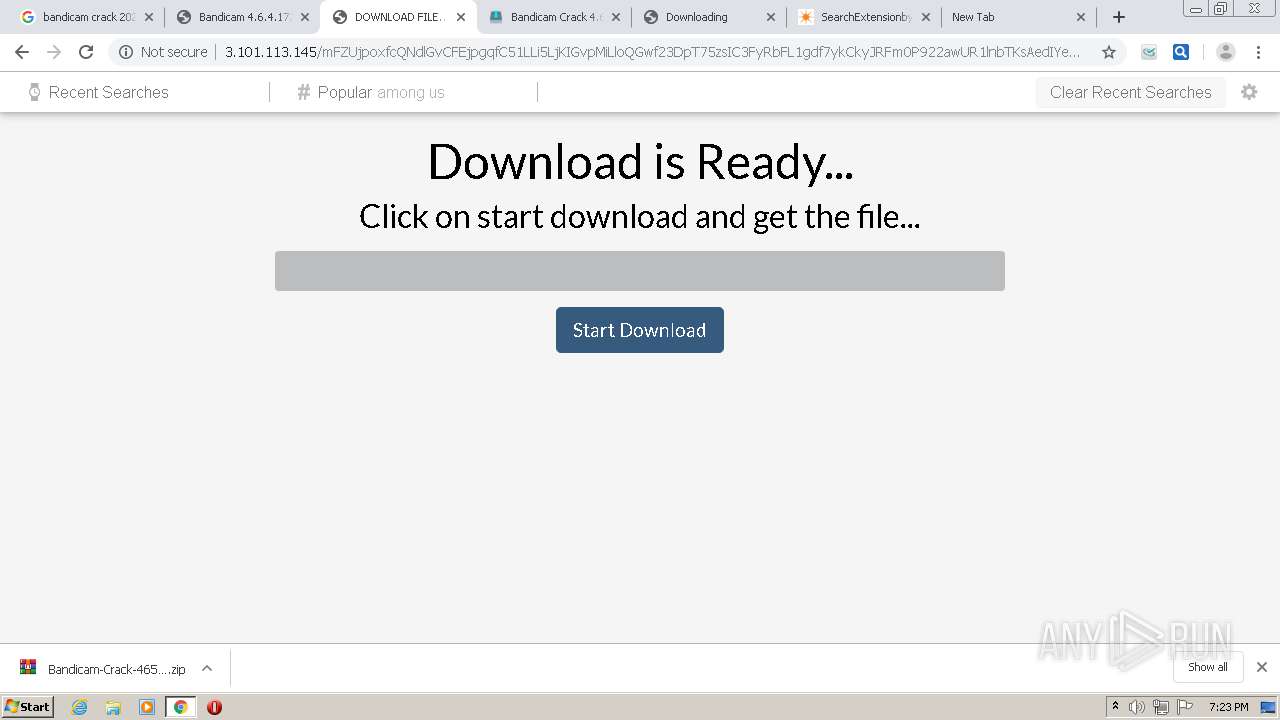
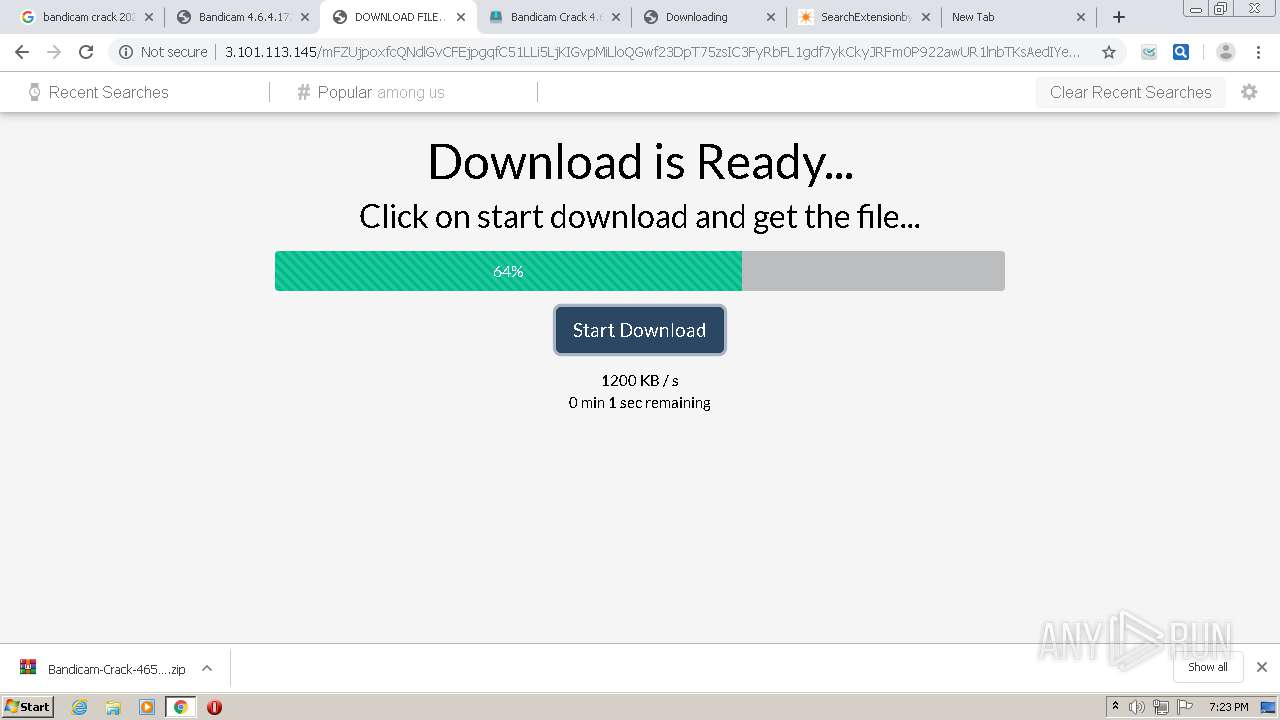
— | — | GET | 200 | 3.131.95.4:80 | http://ec2-3-131-95-4.us-east-2.compute.amazonaws.com/?x_filehash=cloud-372862982a38a361c0a3bf783e769666&c2778ecc2fac3ab9a1d1f639f9f38c3f98dcdc05=4495875d35f3a890eb9fe82f07f4c76a88514a62 | US | compressed | 1.41 Mb | shared |
— | — | POST | 200 | 3.131.95.4:80 | http://ec2-3-131-95-4.us-east-2.compute.amazonaws.com/?go=fec4f1f981fd8f6&dedica=10 | US | html | 1.32 Kb | shared |
— | — | GET | 200 | 3.131.95.4:80 | http://ec2-3-131-95-4.us-east-2.compute.amazonaws.com/loading.gif | US | image | 17.8 Kb | shared |
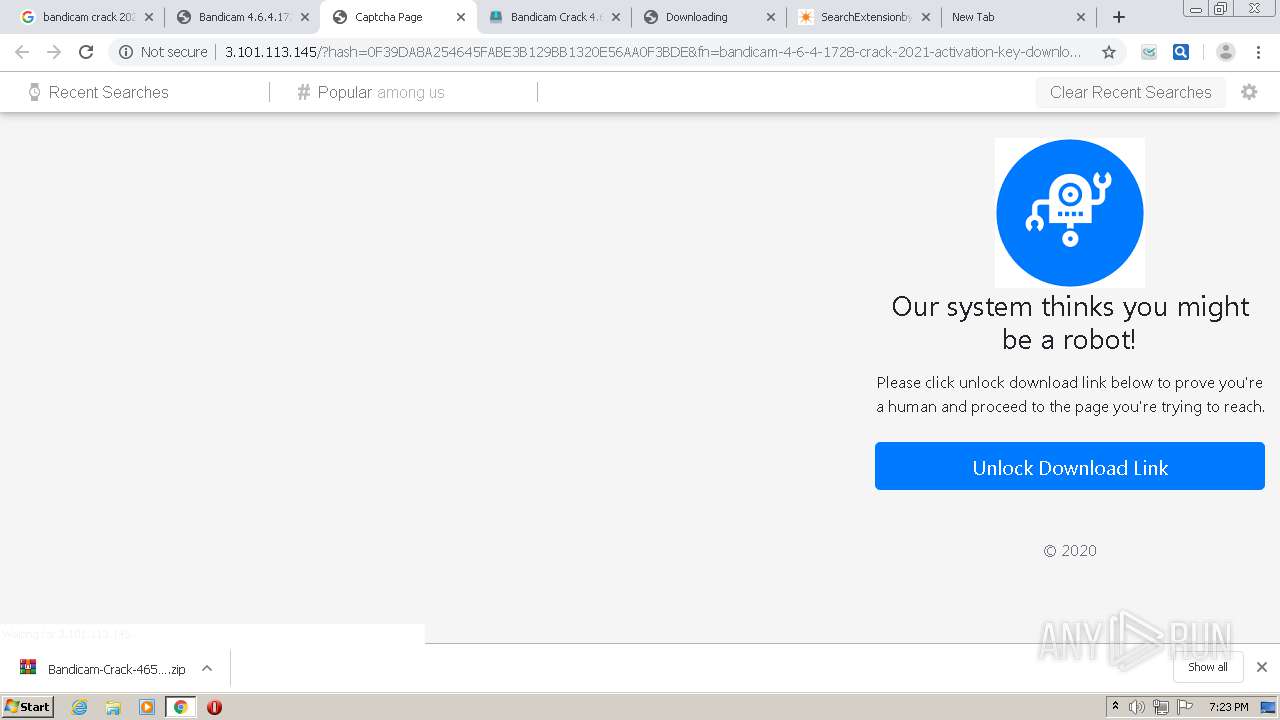
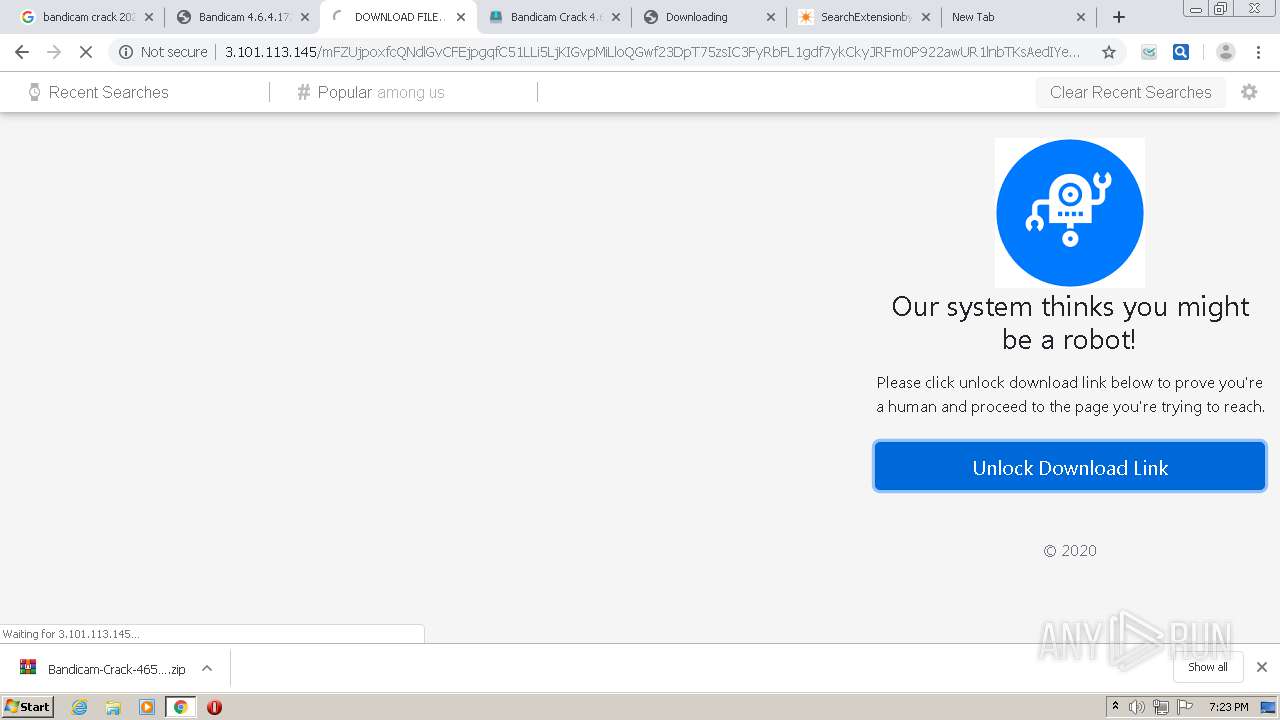
— | — | GET | 200 | 3.101.113.145:80 | http://3.101.113.145/?hash=0F39DA8A254645FABE3B129BB1320E56AA0F3BDE&fn=bandicam-4-6-4-1728-crack-2021-activation-key-download&file=2_bandicam4641728crack2021activationkeydownload.html | US | html | 8.38 Kb | unknown |
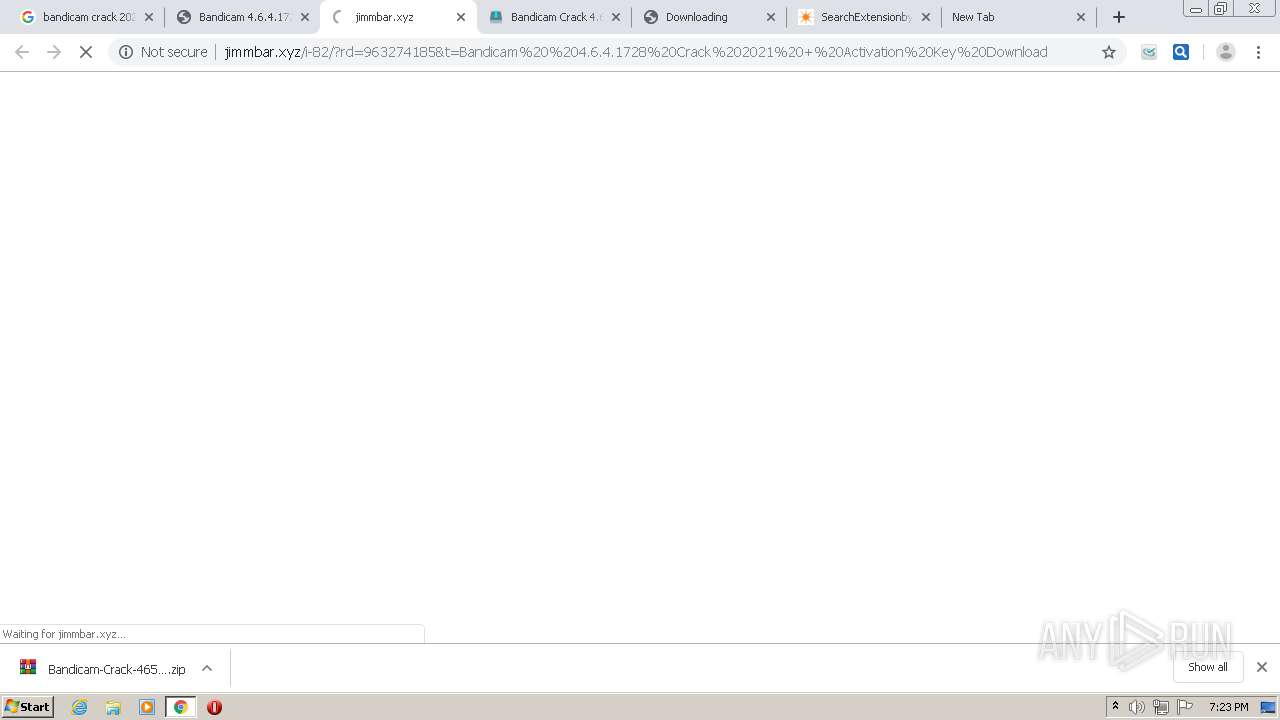
— | — | GET | 200 | 104.24.106.174:80 | http://jimmbar.xyz/i-82/?rd=963274185&t=Bandicam%20%204.6.4.1728%20Crack%202021%20+%20Activation%20Key%20Download | US | html | 367 b | malicious |
— | — | GET | 404 | 3.101.113.145:80 | http://3.101.113.145/favicon.ico | US | html | 275 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.58.210.14:443 | consent.google.com | Google Inc. | US | whitelisted |
— | — | 64.233.180.102:443 | apis.google.com | Google Inc. | US | unknown |
— | — | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.195.156:443 | adservice.google.com | Google Inc. | US | unknown |
— | — | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.110:443 | encrypted-vtbn3.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.164.174:443 | consent.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
play.google.com |
| whitelisted |
adservice.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |