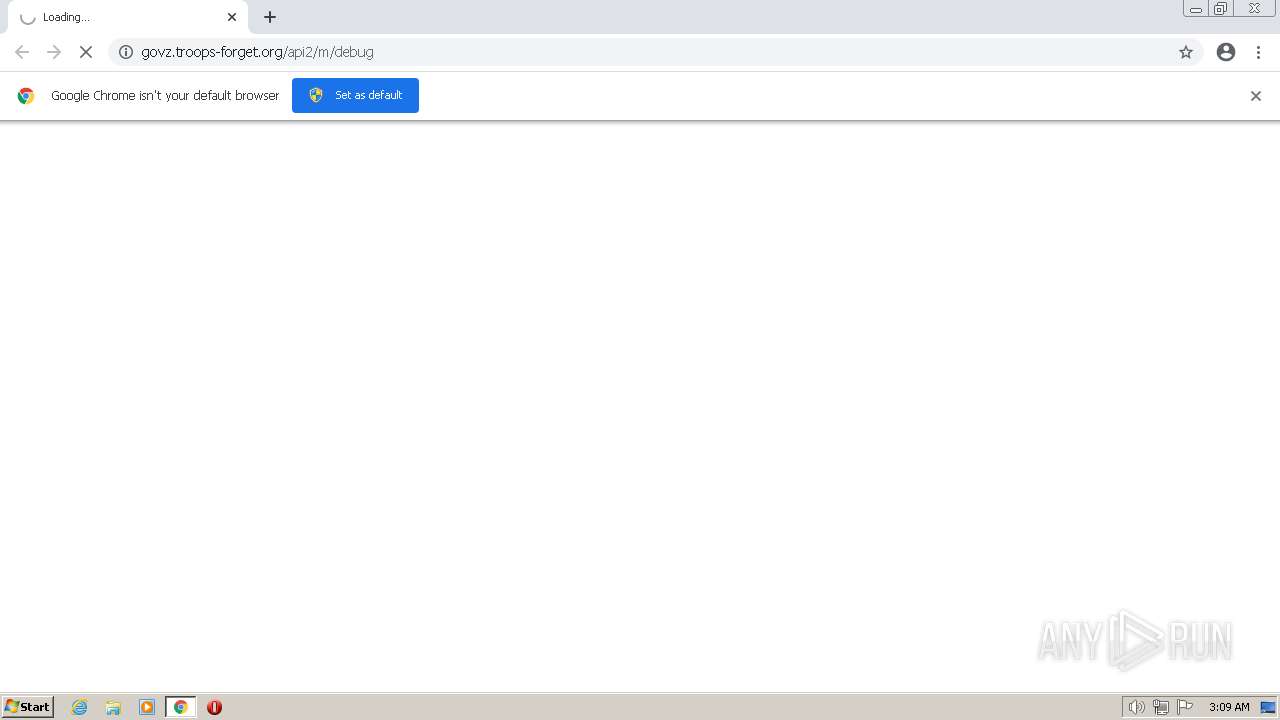
| URL: | https://govz.troops-forget.org/api2/m/debug |
| Full analysis: | https://app.any.run/tasks/6c9d0240-5139-4bd3-b519-d8fb558f9f89 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 03:09:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 09C1F5328E89487F1F19CDFBF8A66DE9 |
| SHA1: | 34FC778574393DDBBBCC7DFE16BCE4DBFC12CFAF |
| SHA256: | C16A0A70B545401313F5711923833EA19617F70A64E1651D8013B3E91CF8018F |
| SSDEEP: | 3:N8rHRXzP5D8Cn:2NXzPB |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://govz.troops-forget.org/api2/m/debug" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e95d988,0x6e95d998,0x6e95d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,11077785385747477754,17075805552332666212,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
11 785
Read events
11 681
Write events
99
Delete events
5
Modification events
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
24
Text files
85
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638EB277-808.pma | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b02174d7-d751-42c2-88ea-773374c3fe3e.tmp | text | |
MD5:— | SHA256:— | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF106eda1.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF106eeab.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b379ab28-5bc6-4e70-b797-c635e98e3889.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
58
DNS requests
40
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
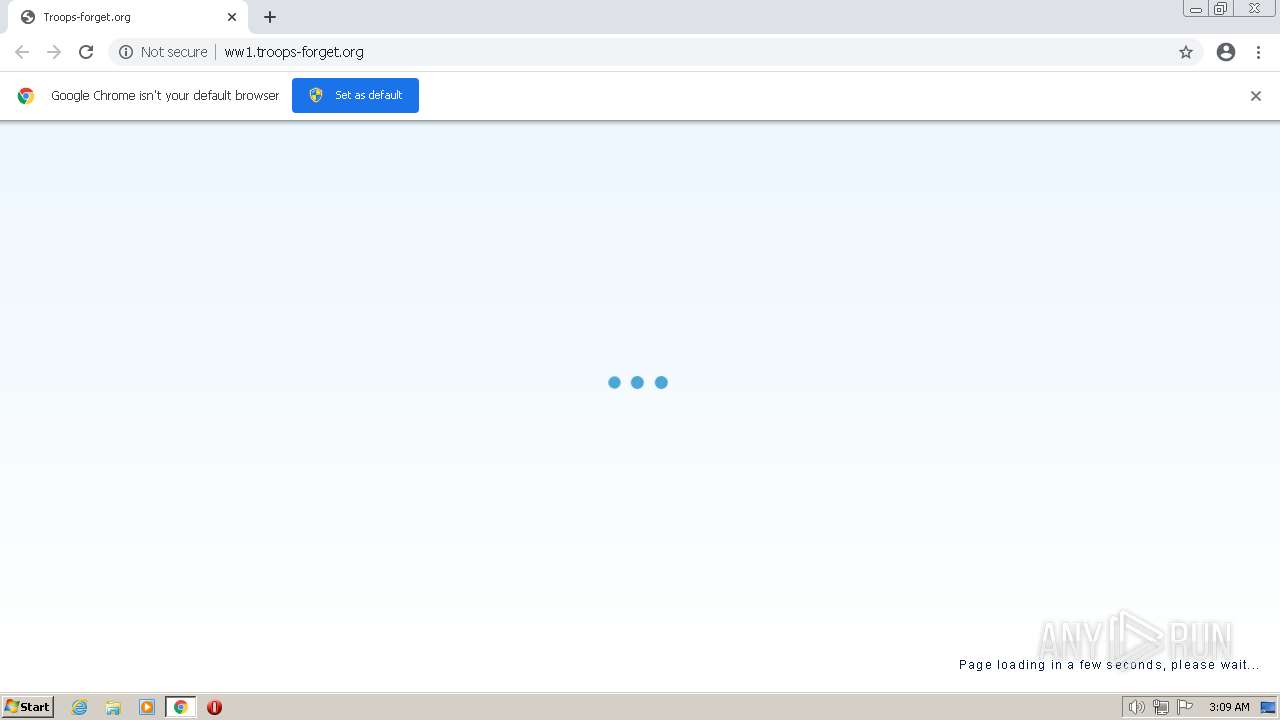
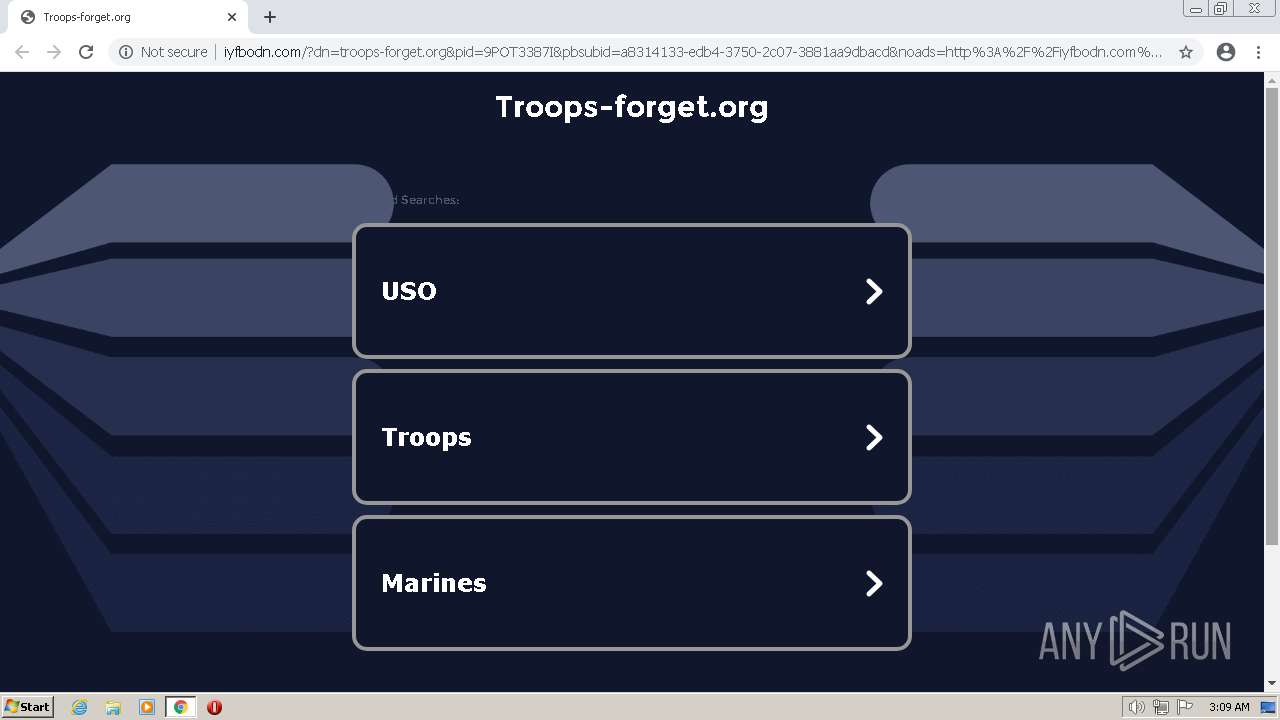
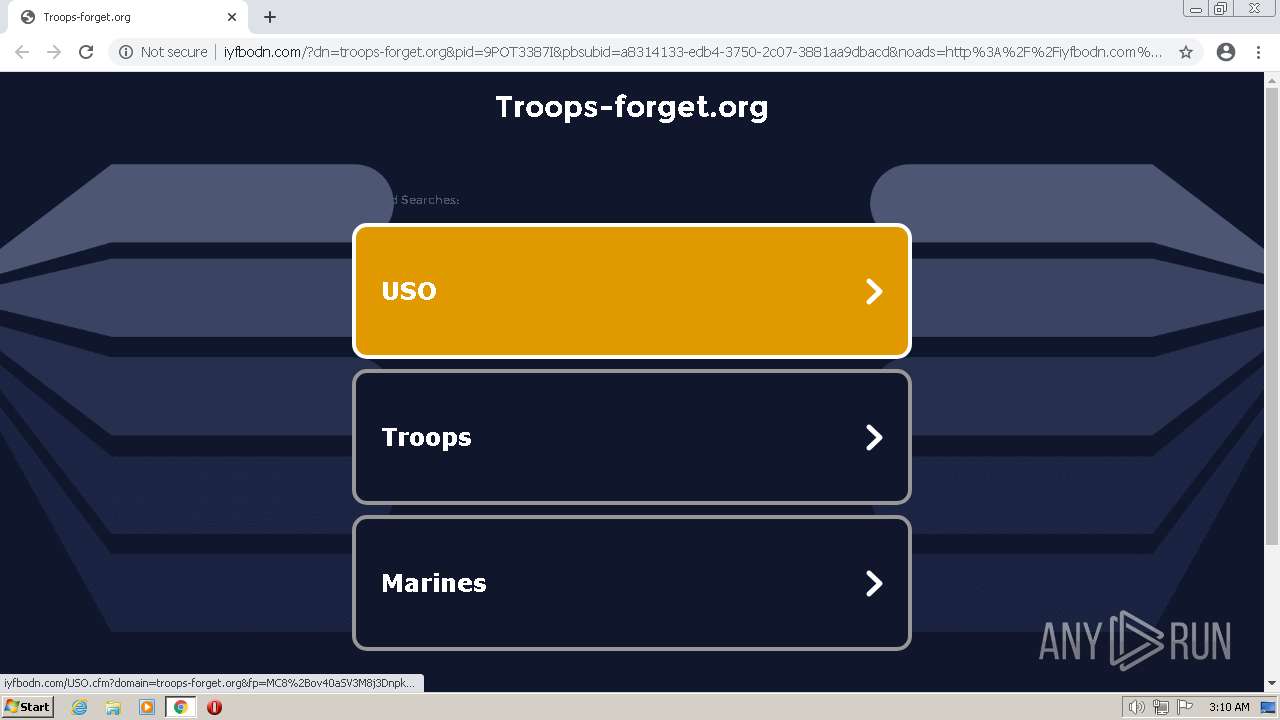
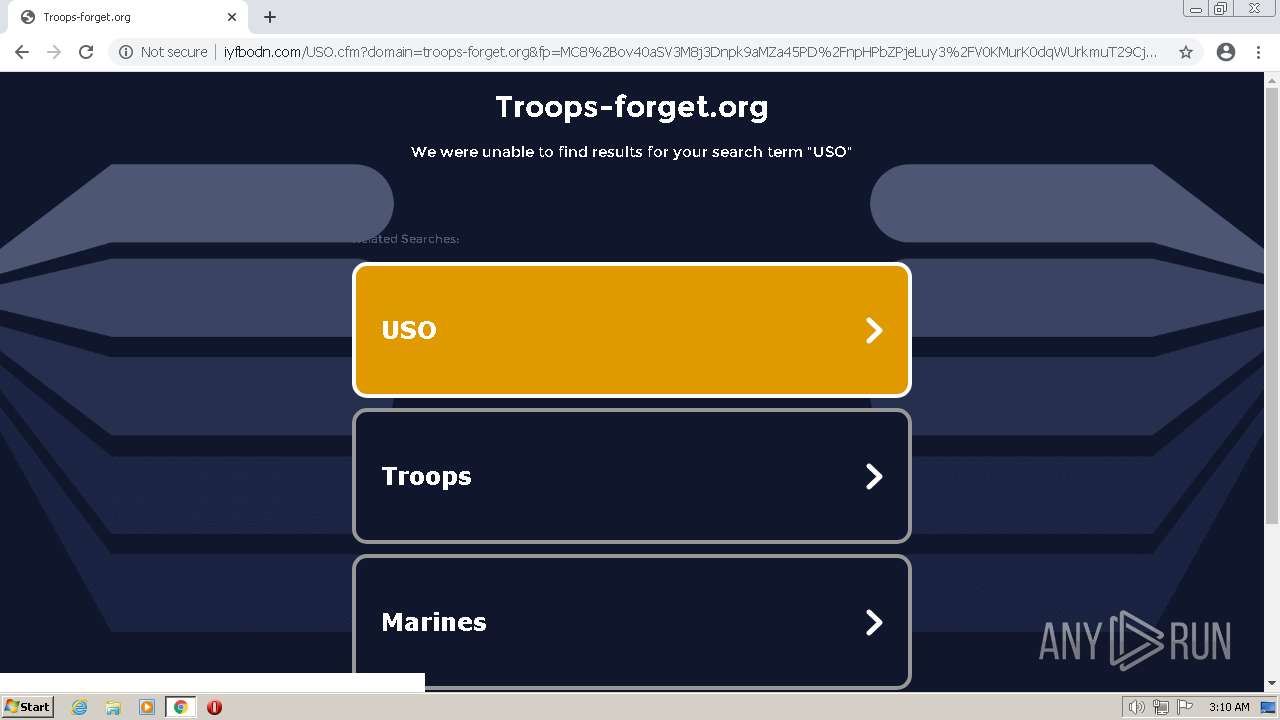
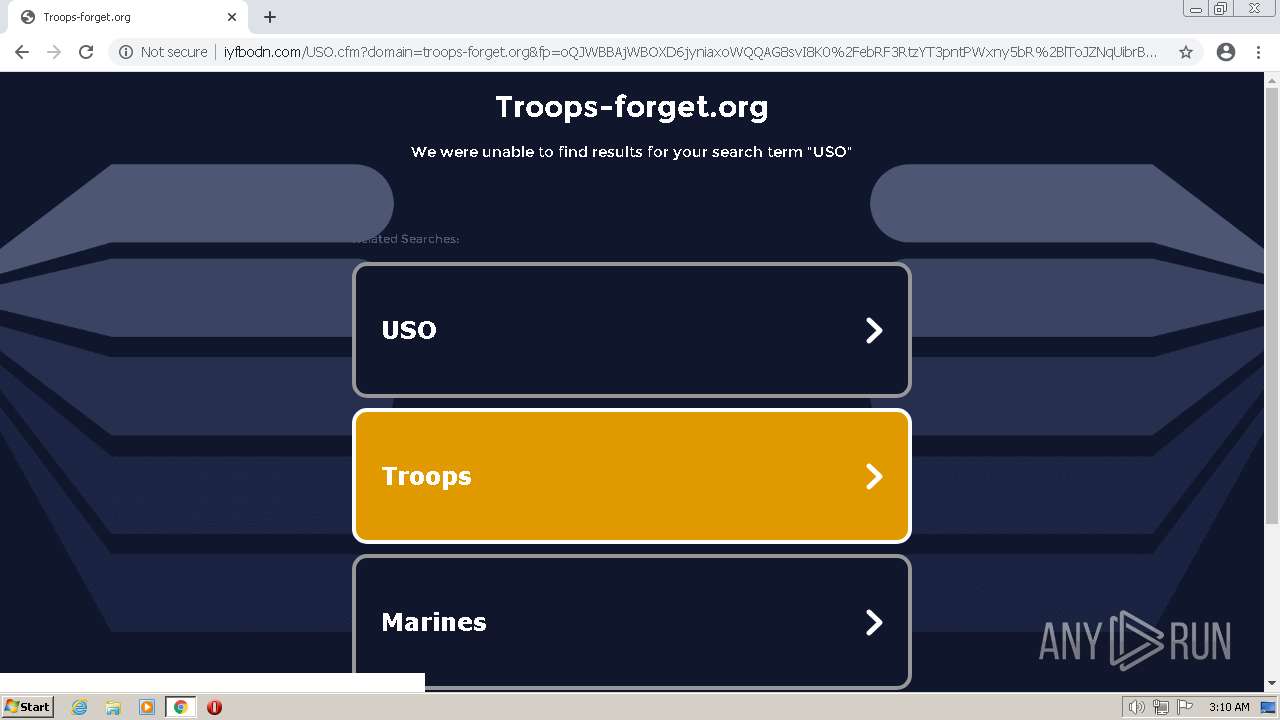
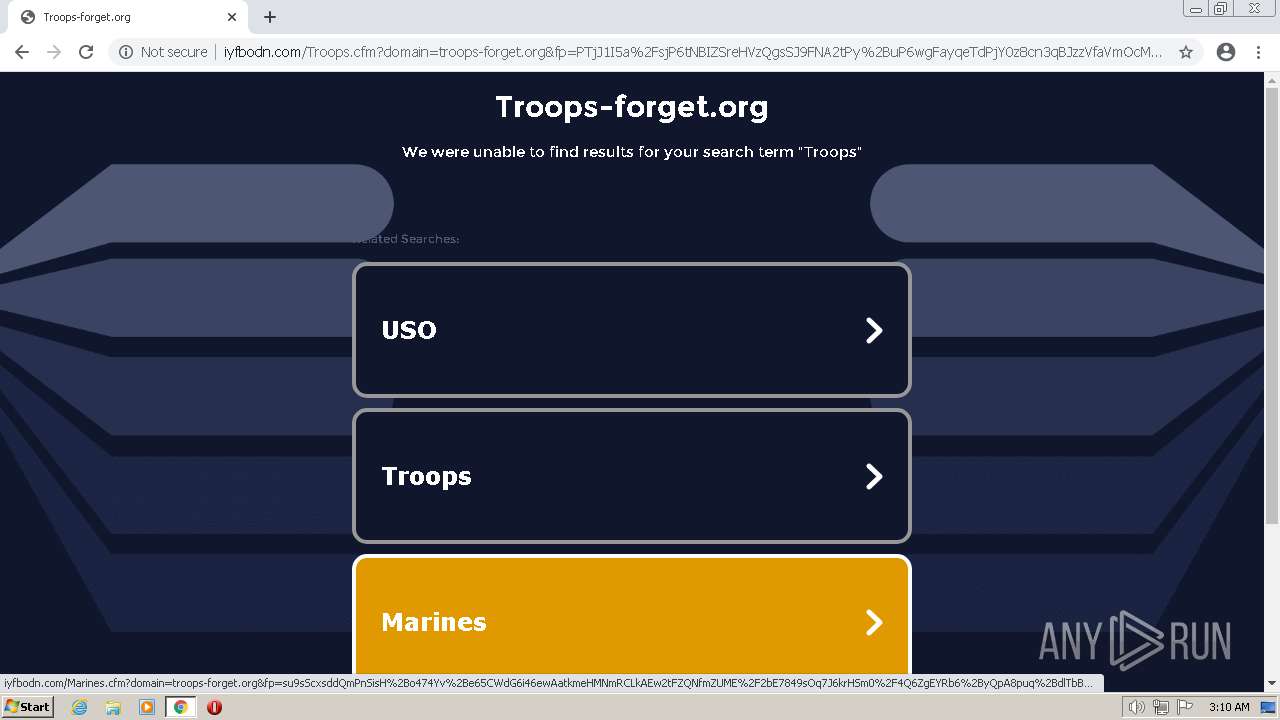
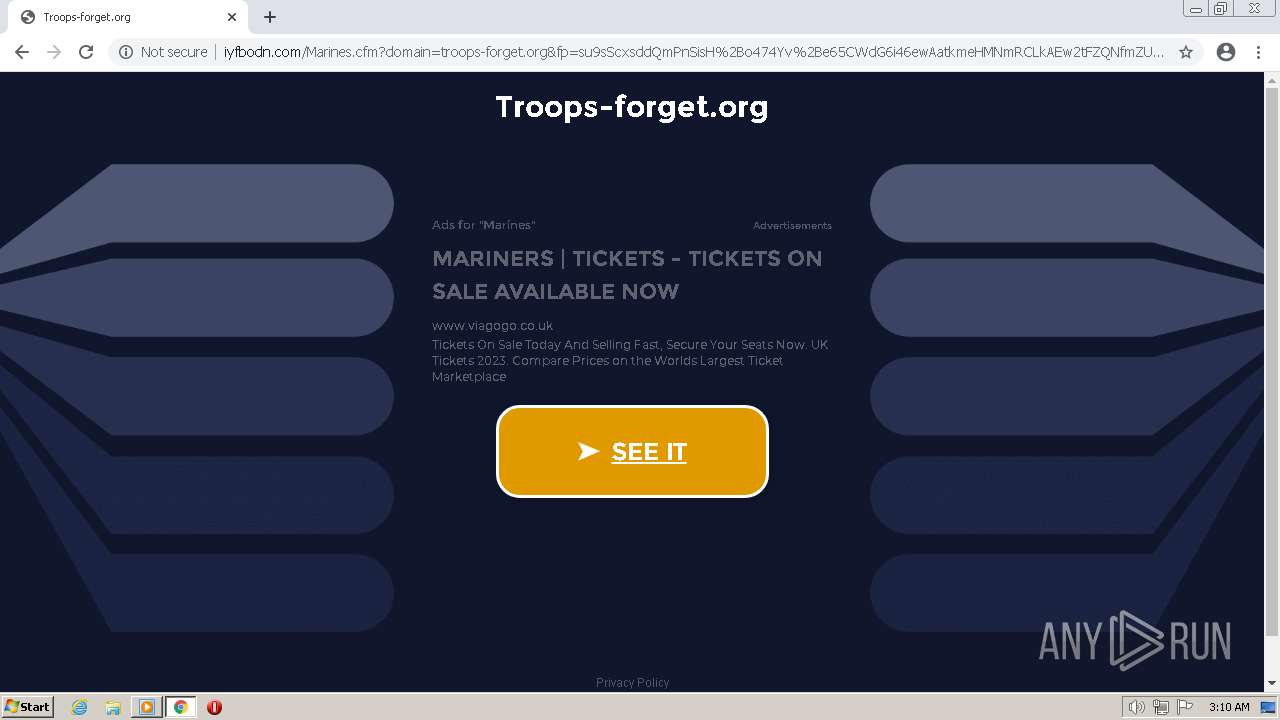
2020 | chrome.exe | GET | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/ | US | html | 1.03 Kb | malicious |
2020 | chrome.exe | GET | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/js/parking.2.100.2.js | US | html | 21.7 Kb | malicious |
2020 | chrome.exe | POST | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/_fd | US | text | 1.96 Kb | malicious |
2020 | chrome.exe | POST | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/_zc | US | text | 172 b | malicious |
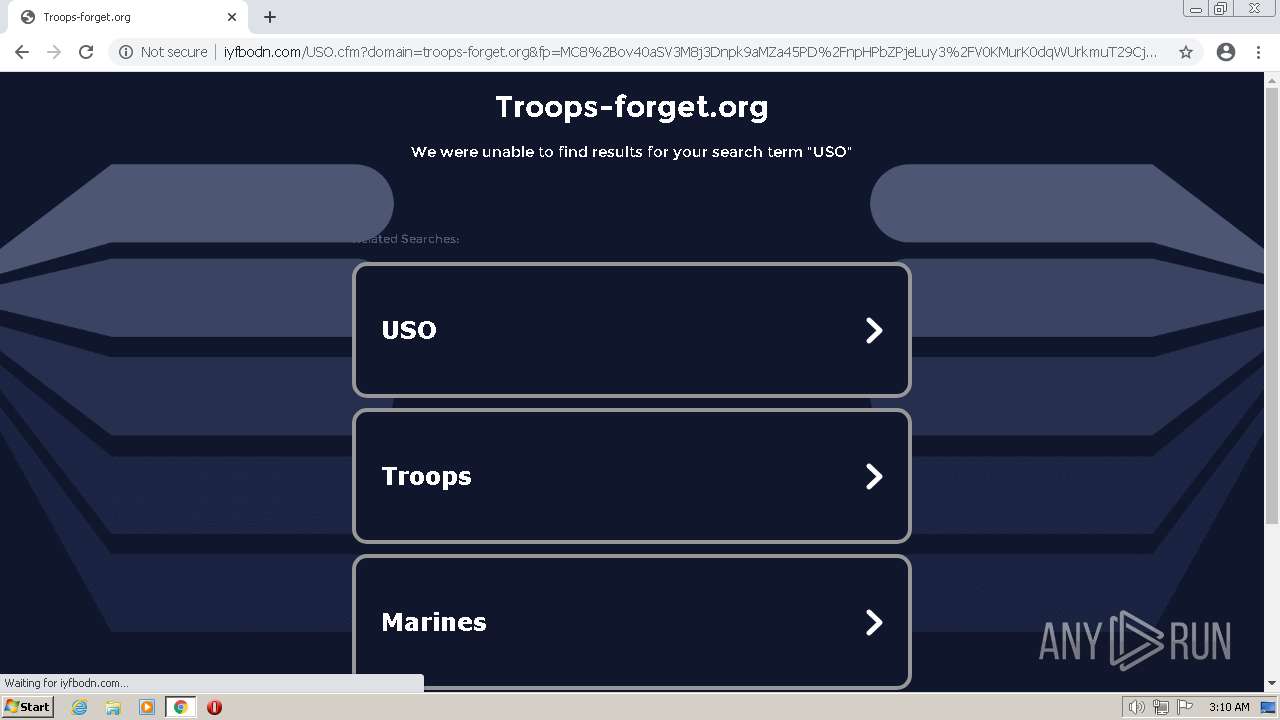
2020 | chrome.exe | GET | 200 | 208.91.196.46:80 | http://iyfbodn.com/USO.cfm?domain=troops-forget.org&fp=oQJWBBAjWBOXD6jyniaxoWQQAG8svI8K0%2FebRF3RtzYT3pntPWxny5bR%2BlToJZNqUibrBQBjWFwBtZt0T9q4A%2FjmTFP6f75Jm9kcSdsXueWbVIuzNYVaqhBEU8lftc27w4adyOSZCxO88JC4u9oxsCryVPGAF30rys0tfHIUhhcrgzk941DrJcIcHcbNVLW2Jdqjp1wg5c9EsdKzvl9u1g%3D%3D&yep=hxde5PmKz%2Fa0CTtOIOsyxAIE5AaBWxc53GNJwefAwiWmT34K2VYKM565xwl4zP0zVM%2Bpf9mq0%2F72swyyu7HGIwyvUUGhT%2B8avAdSCSa76lkrMKhlv9c31vZ%2BkUrr0iCftVwyWAkLjpgK1mDgzAct1p7pZSA33fRrMzhy1l61Xn87i%2FCWk1WcSGO0ZeuigbyBqgxwvt2N21Qh2GdUJyhtIqA5bFY4X%2BaPgRHpM63mS3rzPRLzlCZo5ut4hj5WC3D3uyfGO9fsya2RtoHBgXvHHaM%2BnWeuomYp9jMJCseghsUfHHbCtdgEOXO%2F%2F221VsSddoByVP8aVbL55NBllBaoStFCNrM3yAxPpXx3zR%2FvpEExbaikXx%2BFwKdrFReoAKVHR27kVIz1heBqG1r15ZojCYct2axypEQ%2FvR5aGQVmiiLVJl%2BkGYixKTyp%2BnlbnmNzv6vmvGY9NL88nMgf6hOKfxXnf%2F7%2F1TI6mWq7C6CcoLcXPFedzx%2Bls4ank59QXQbxS8aT4ufYJf5iUK1vHyw7Usi3VVzmVr%2Fo9xnO2kABpCirQ5RGkXl7e2xbuW82lEfpM4qP0RZGB%2FusfW28urVrL%2FbOEaKZWFmf8SREGd4DMvRojfi5KEVGLZLNI2ok3ZQNxdMr2RS1KYmY16sl2WScTBTre0xxo5bWODLAvW3tfgkkSwB4IWJi8OT6qC%2BGsIxadOOQu4cPkGQl1hwGkefKRDVxhwk%2B7byjwCqYCQzeT3rBkLy6BVs36hgeZ4mxF81fPZqWPOcGiF%2BA0C%2Bpg5snw46QCT%2Fy93ZsBo724PL6plM2edDaEeFlt14qNWoOLIZMpM5ugtvF0VJis7RLHodkOj%2F4eaaXhVsb33ZQq5QvFIWz%2FVxSdCK8kykb0eYYHAo%2BBFZu9jzTVVKQHzv13Js0mMsEUP7J27zv161yMRC3pzWeJ3eBIRvm9oi82zM1pf8v8FRNf%2Fu56NgHR73%2BKTrhmohQRVCnVxVRd08maF8xCwg%3D>np=0>pp=0&tp1=a8314133-edb4-3750-2c07-3881aa9dbacd&kbetu=1&maxads=0&kld=1003&yprpnd=2TUMFZMKvo%2F5mzblAyY9EILsZ6xAML6fKUrlfhQps%2F4%3D&prvtof=AOcN0GjIB96bA2aygtiof6GLbfGUV4sistVT1WFS7qlyAC0j57zjmsi%2FHUHLbLwm&pbsubid=a8314133-edb4-3750-2c07-3881aa9dbacd&noads=http%3A%2F%2Fiyfbodn.com%2F%3Fdn%3Dtroops-forget.org%26skipskenzo%3Dtrue>np=0>pp=0&kt=362&&kbc=troops&ki=29557307&ktd=0&kld=1003&kp=1&bd=0%23720%231280%231%230%23532%23277 | VG | html | 6.88 Kb | suspicious |
2020 | chrome.exe | GET | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/px.gif?ch=1&rn=4.191888759129753 | US | image | 42 b | malicious |
2020 | chrome.exe | GET | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/px.gif?ch=2&rn=4.191888759129753 | US | image | 42 b | malicious |
2020 | chrome.exe | GET | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/favicon.ico | US | image | 42 b | malicious |
2020 | chrome.exe | POST | 200 | 199.59.243.222:80 | http://ww1.troops-forget.org/_tr | US | text | 22 b | malicious |
2020 | chrome.exe | GET | 200 | 208.91.196.46:80 | http://iyfbodn.com/px.js?ch=1 | VG | text | 346 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2020 | chrome.exe | 212.82.100.137:443 | r.search.yahoo.com | Yahoo! UK Services Limited | IE | shared |
2020 | chrome.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2020 | chrome.exe | 172.217.18.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
2020 | chrome.exe | 23.82.12.35:443 | govz.troops-forget.org | LEASEWEB-USA-WDC | US | malicious |
2020 | chrome.exe | 142.250.184.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
2020 | chrome.exe | 8.241.78.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2020 | chrome.exe | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
2020 | chrome.exe | 199.59.243.222:80 | ww1.troops-forget.org | AMAZON-02 | US | malicious |
2020 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
2020 | chrome.exe | 142.250.184.194:443 | partner.googleadservices.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
govz.troops-forget.org |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ww1.troops-forget.org |
| malicious |
www.google.com |
| malicious |
parking.bodiscdn.com |
| whitelisted |
partner.googleadservices.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2020 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |