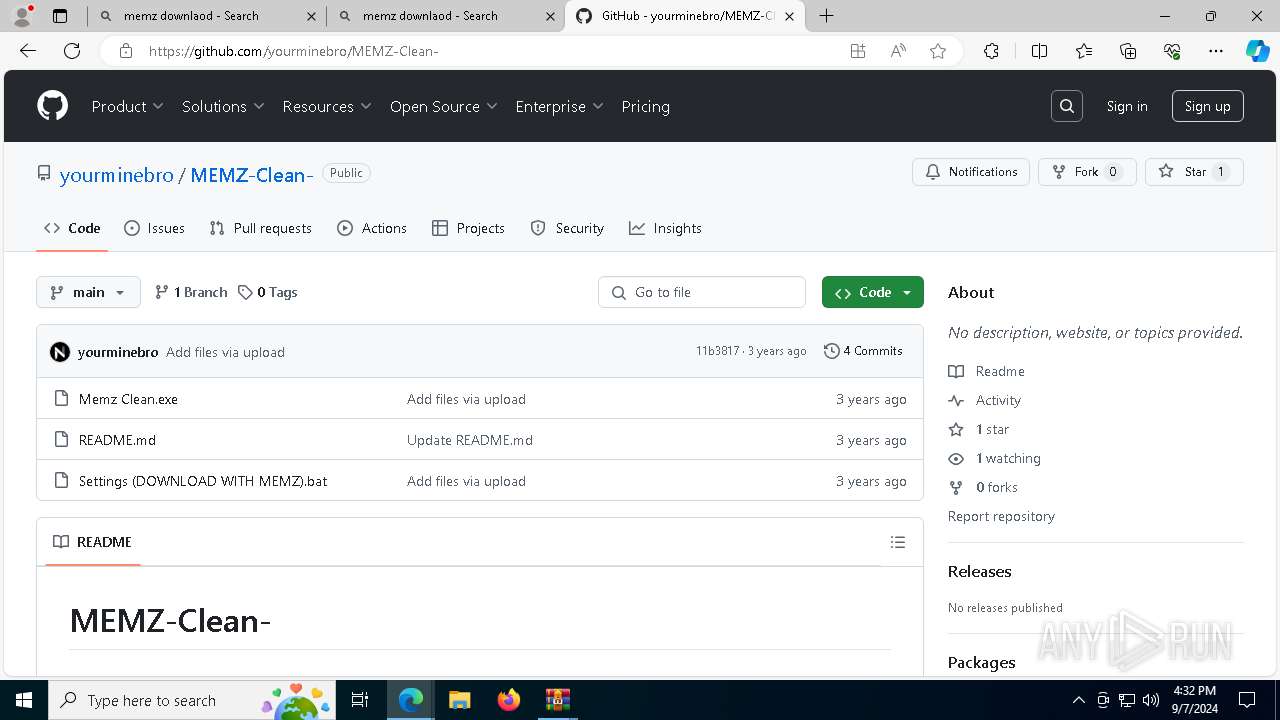
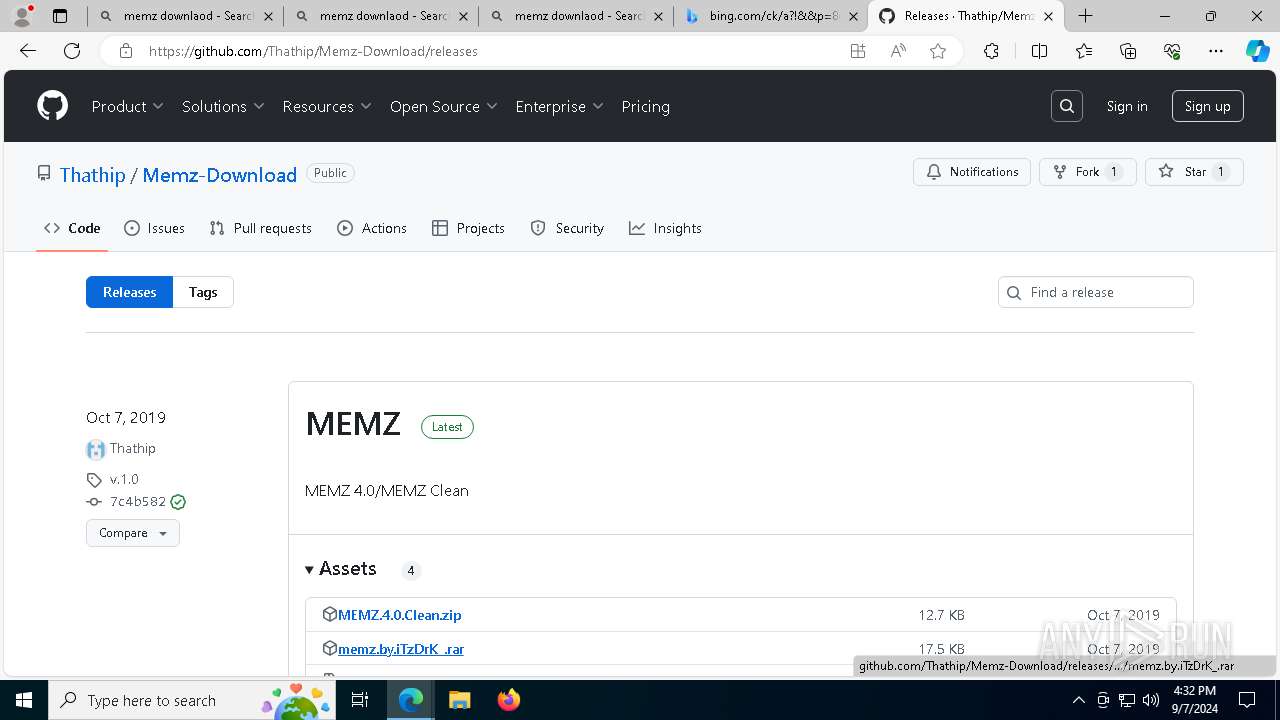
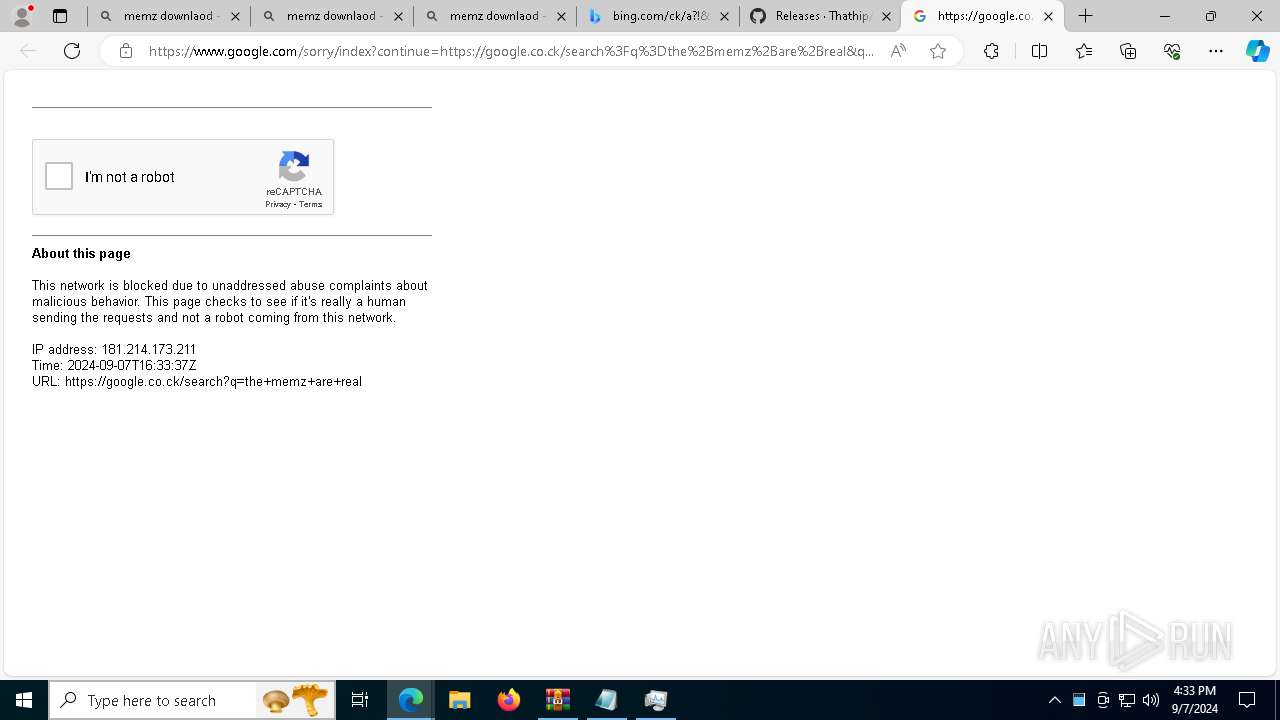
| URL: | roblox.com |
| Full analysis: | https://app.any.run/tasks/9606d5f7-3f22-4f6b-b41f-e9caddad8cfa |
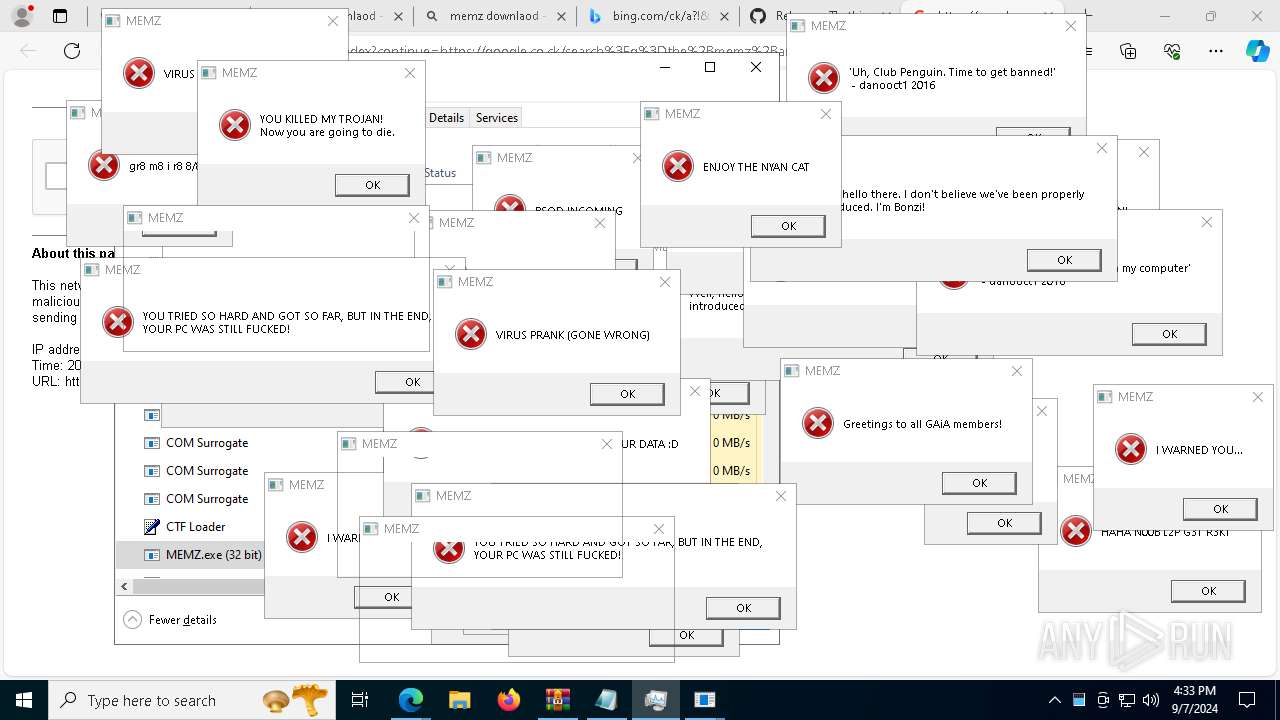
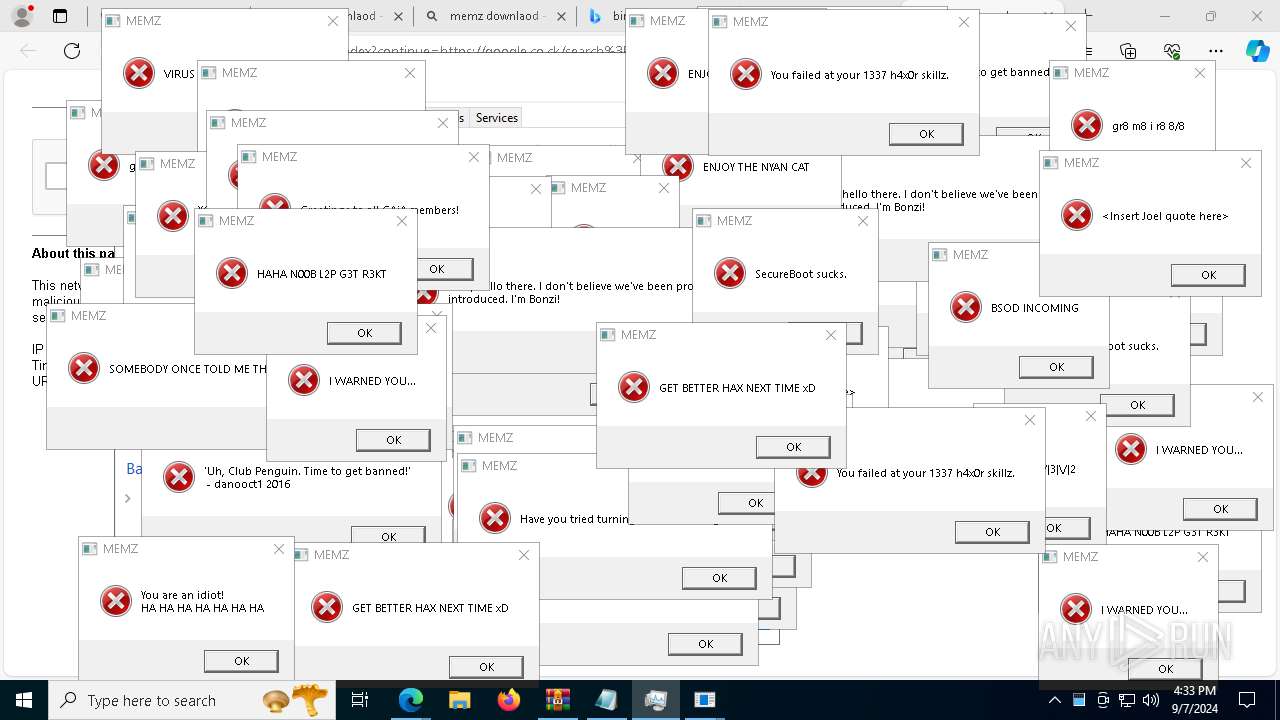
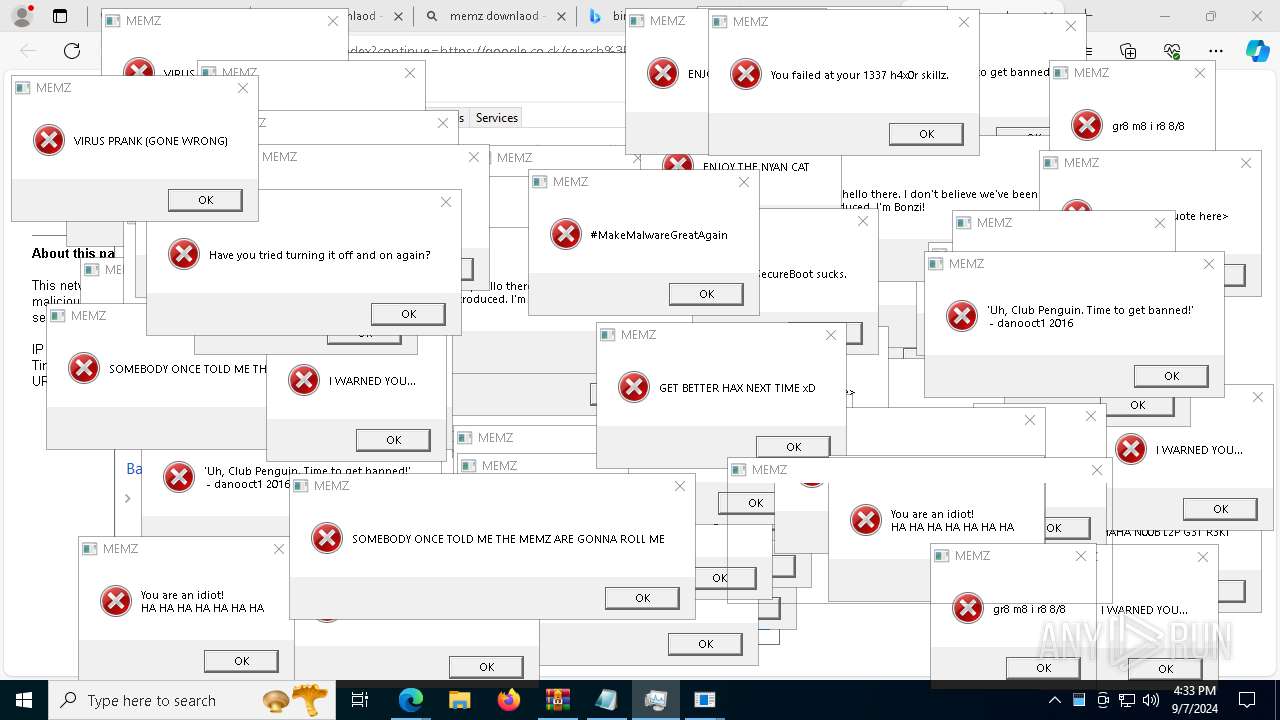
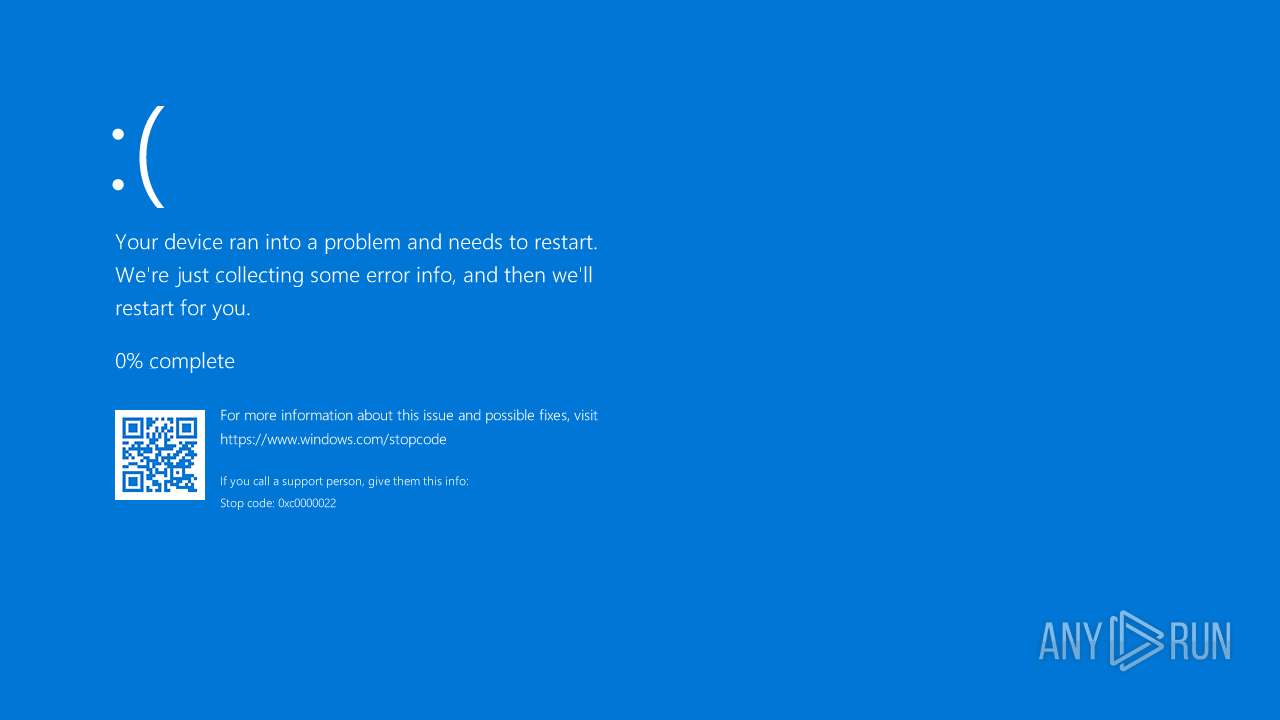
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2024, 16:29:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | C06012A24CBE7C52D0E0A9AD4A936C79 |
| SHA1: | FB22C4B259680F2301B90F8DD5FB40D975C17190 |
| SHA256: | C1688E9B4C7A1DC950E389DE2A104CCDC8C80648F9202D1CCA5F4289D5D43032 |
| SSDEEP: | 3:MJ6In:MNn |
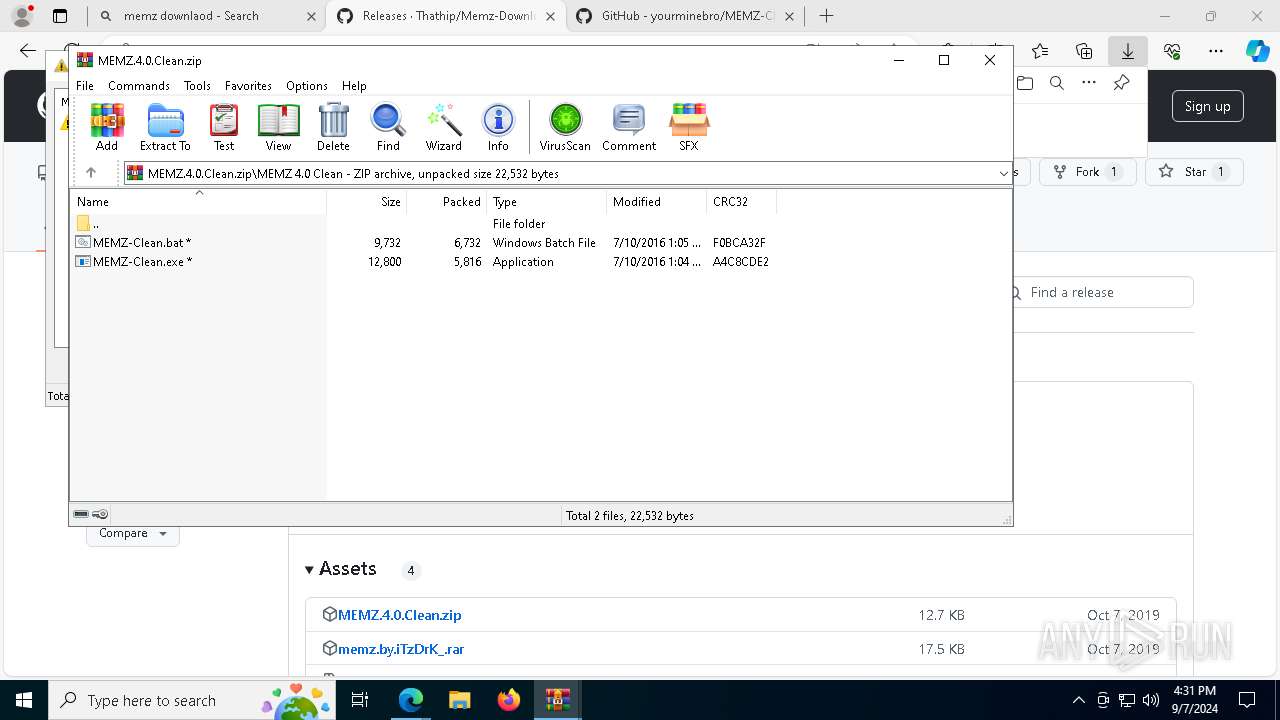
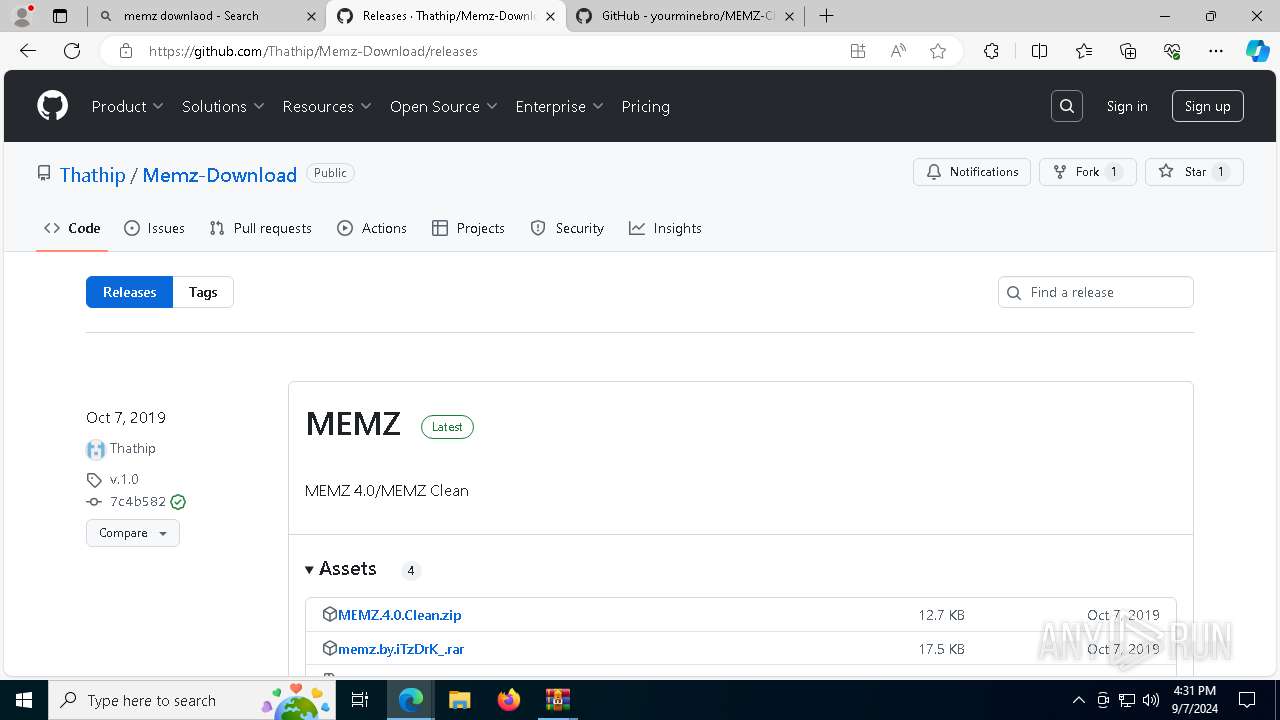
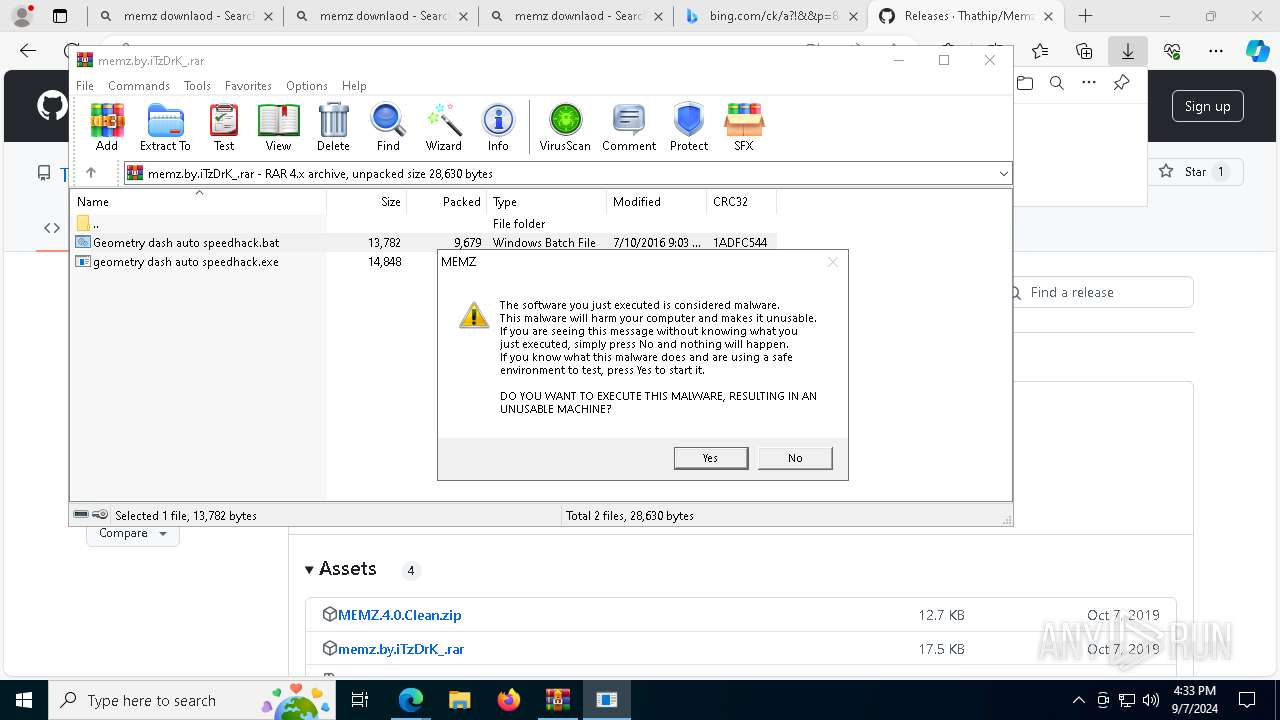
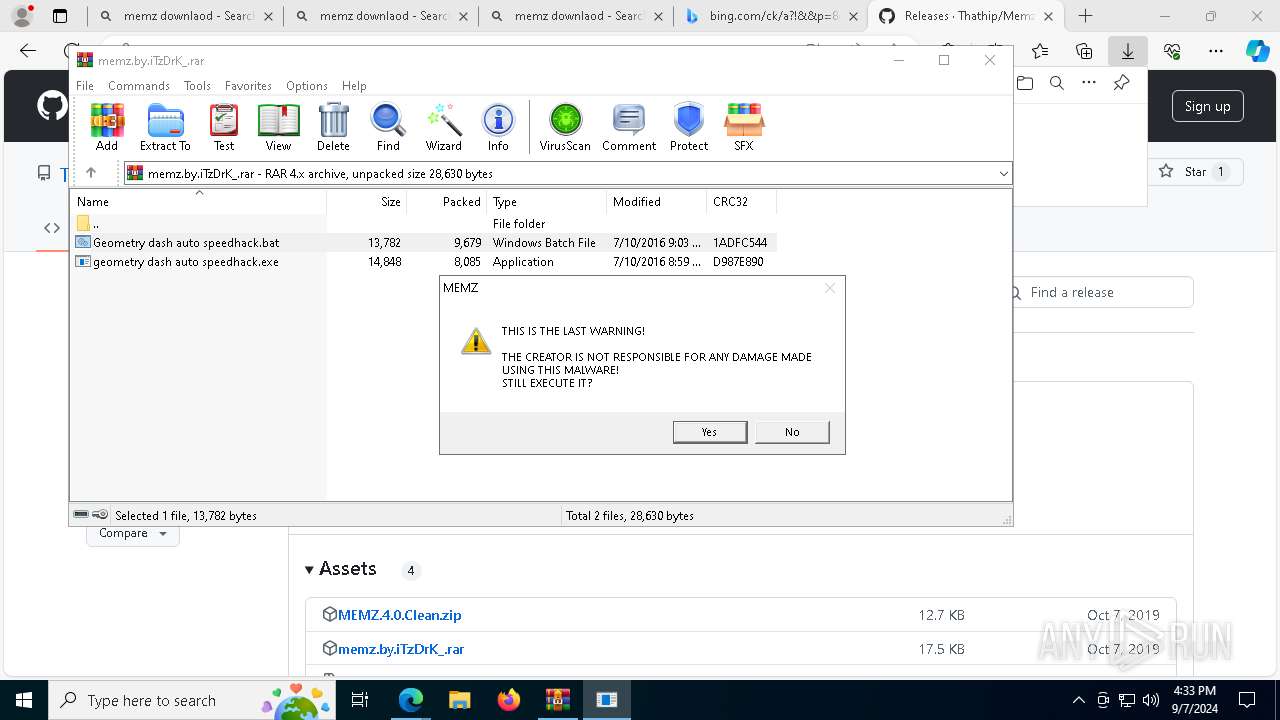
MALICIOUS
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 7876)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 7876)
SUSPICIOUS
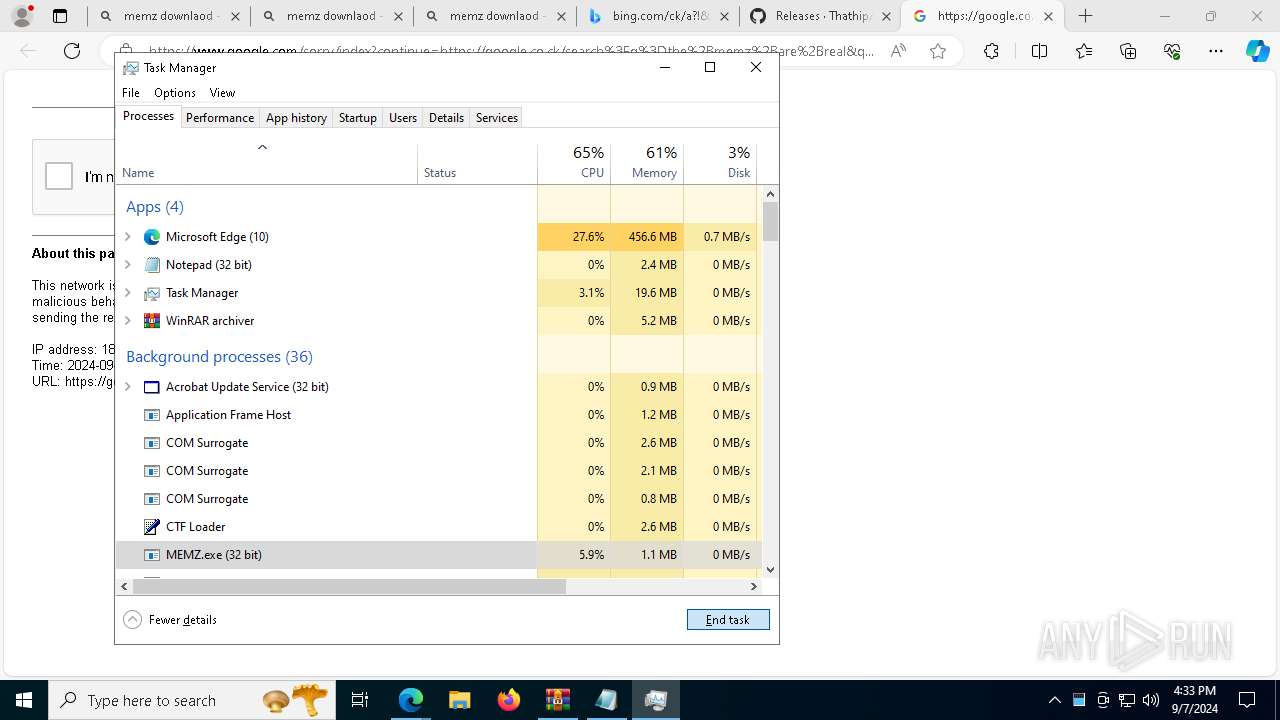
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7568)
- MEMZ.exe (PID: 7484)
- MEMZ.exe (PID: 300)
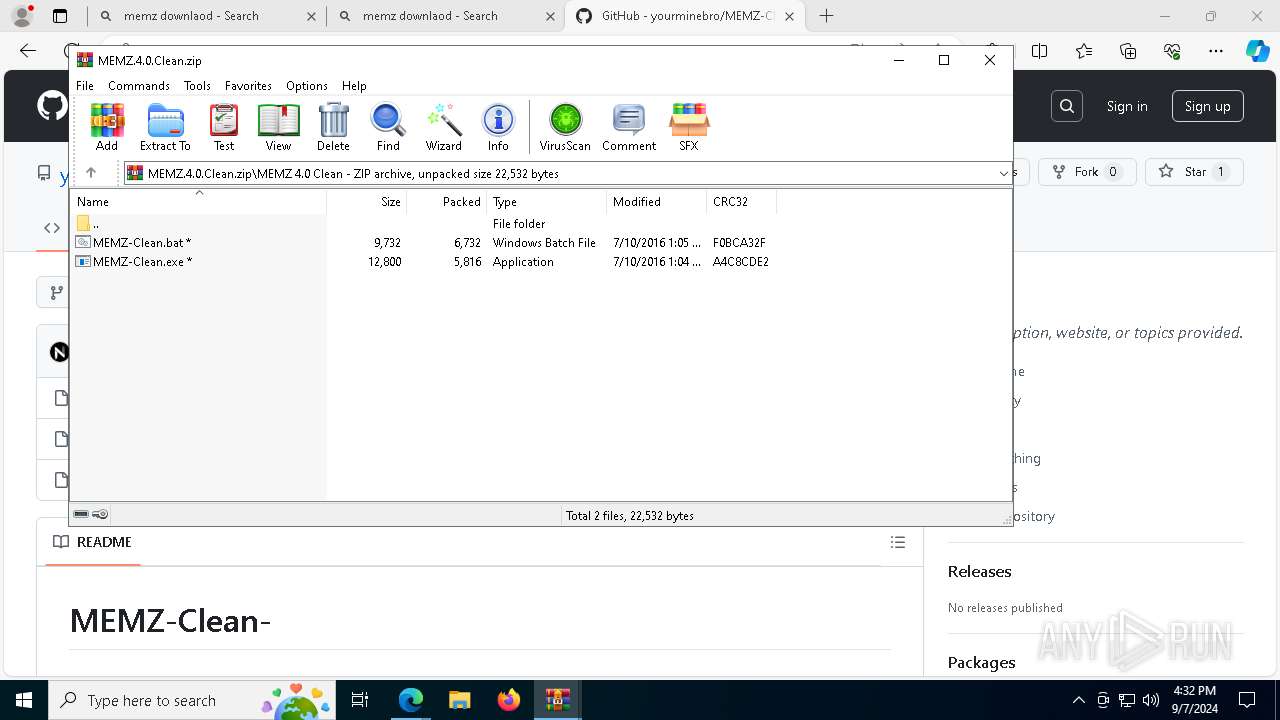
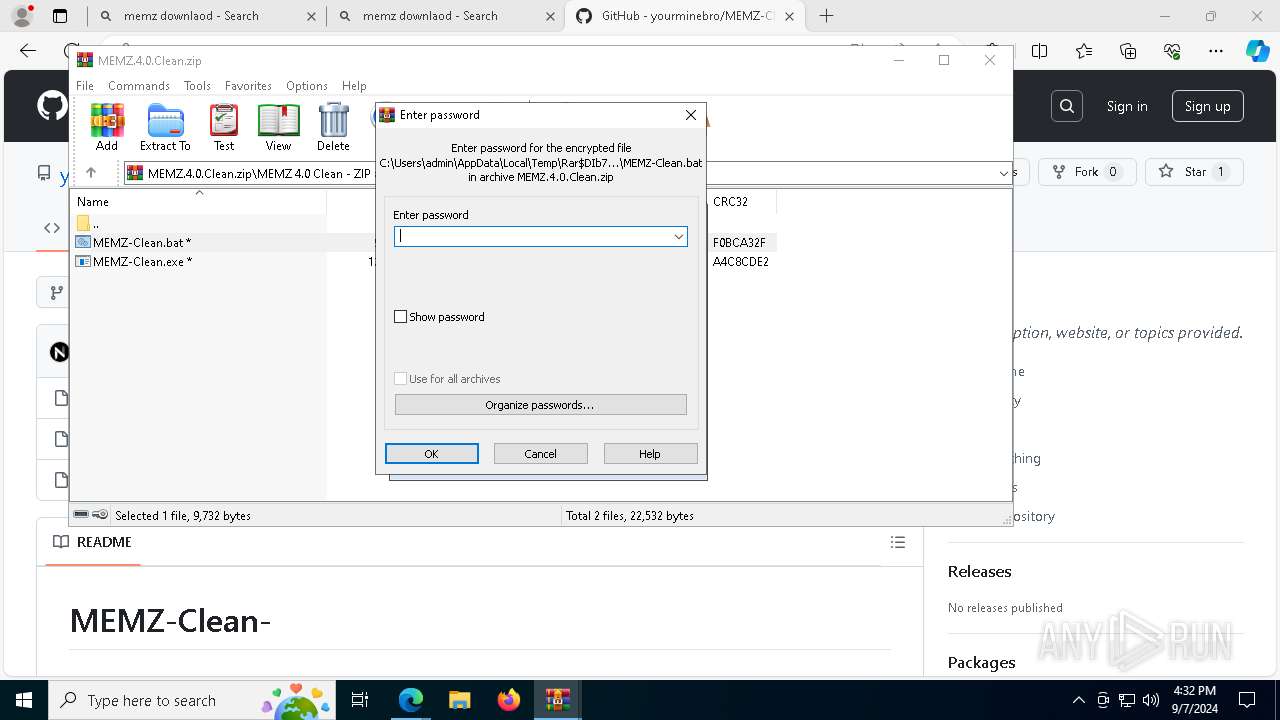
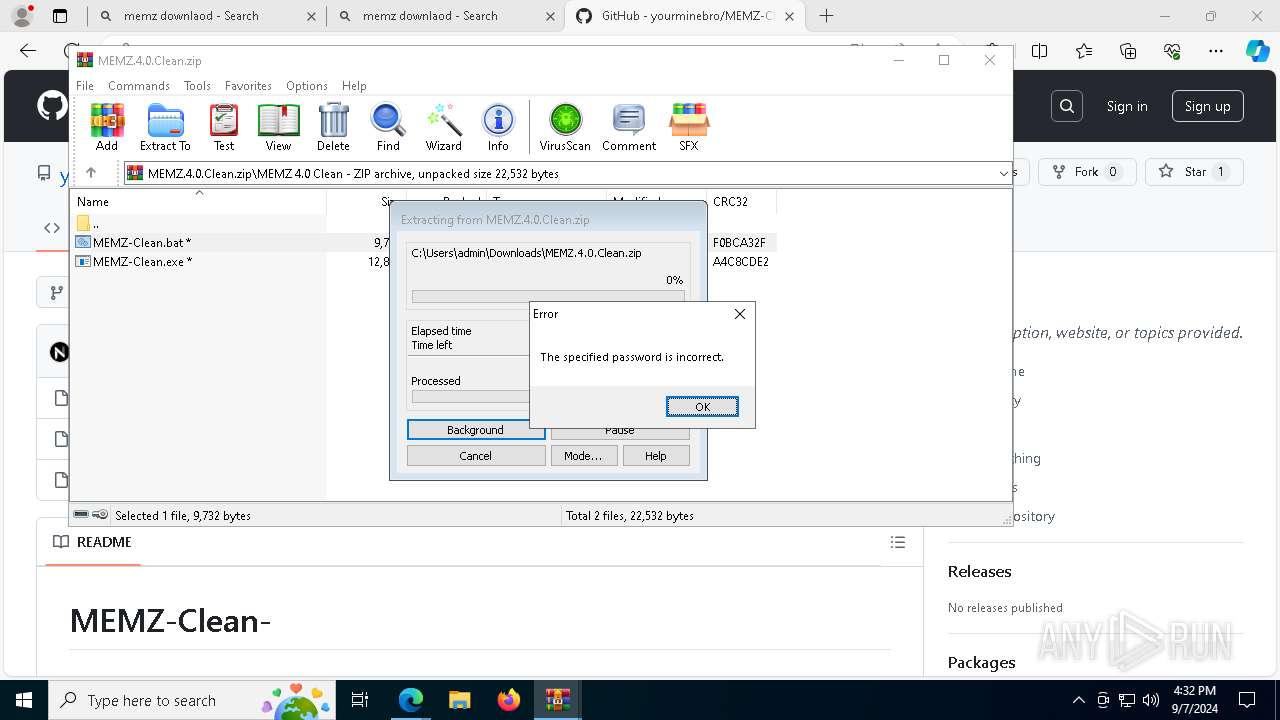
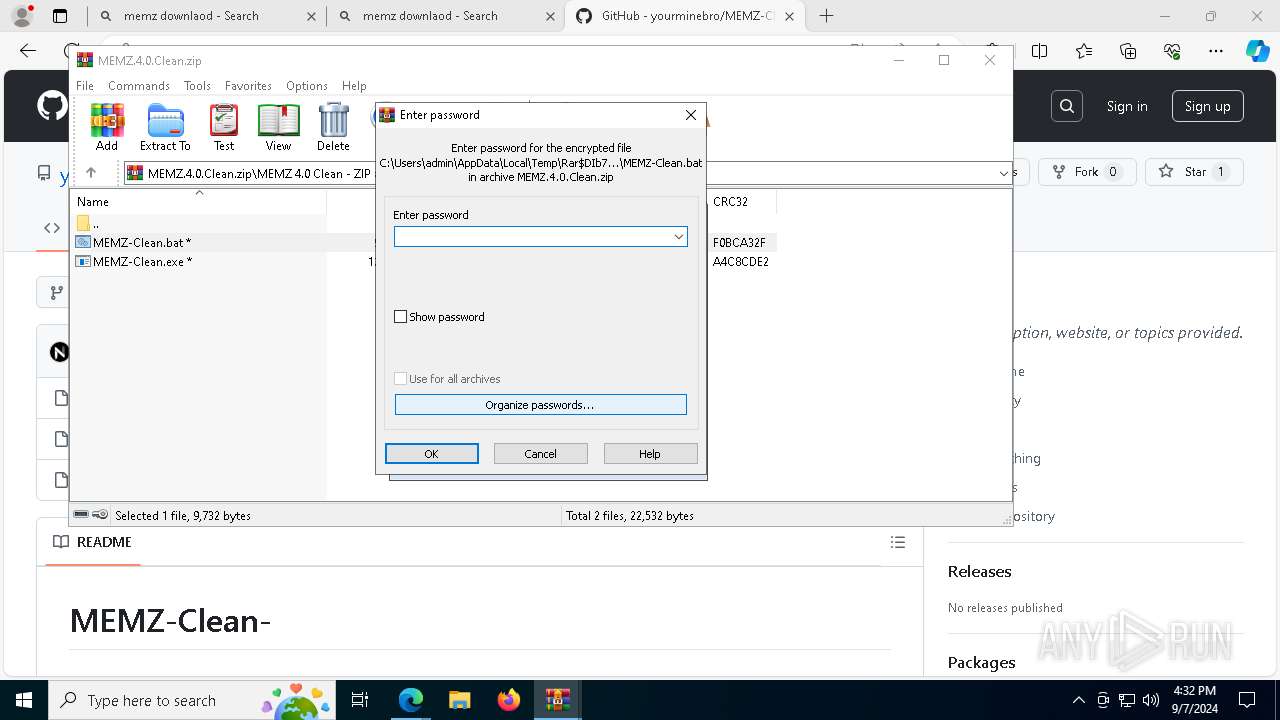
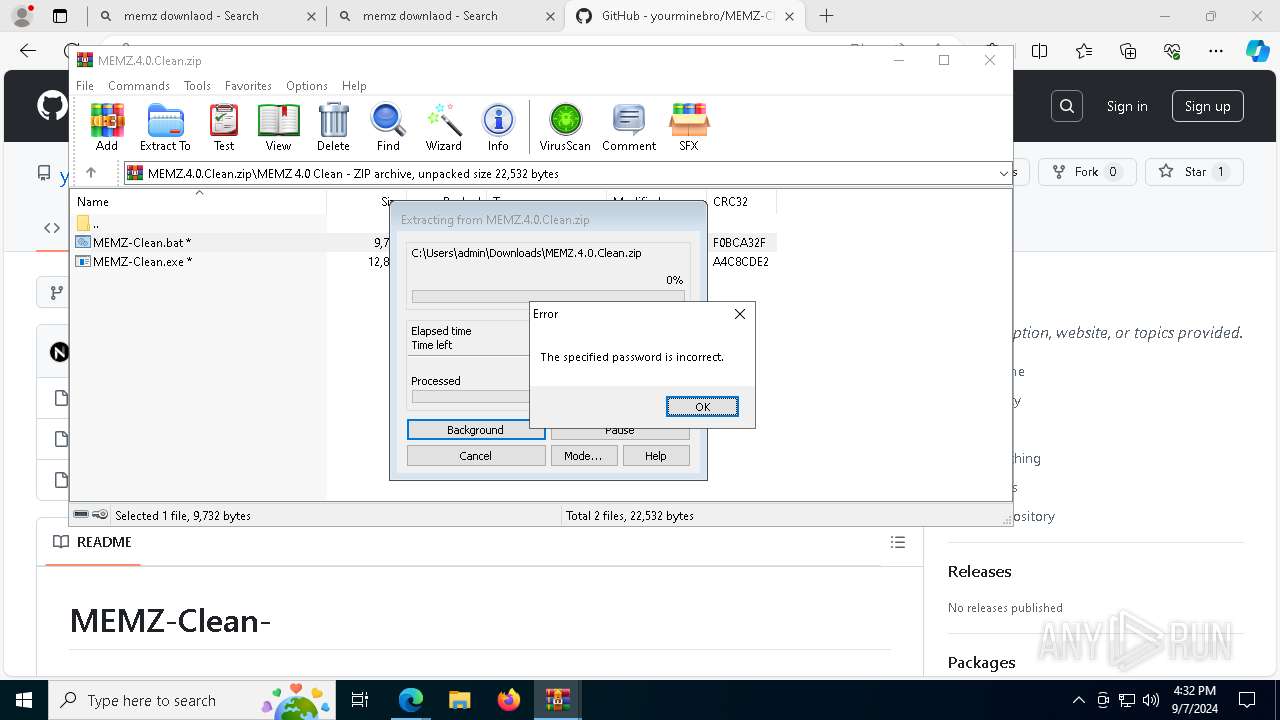
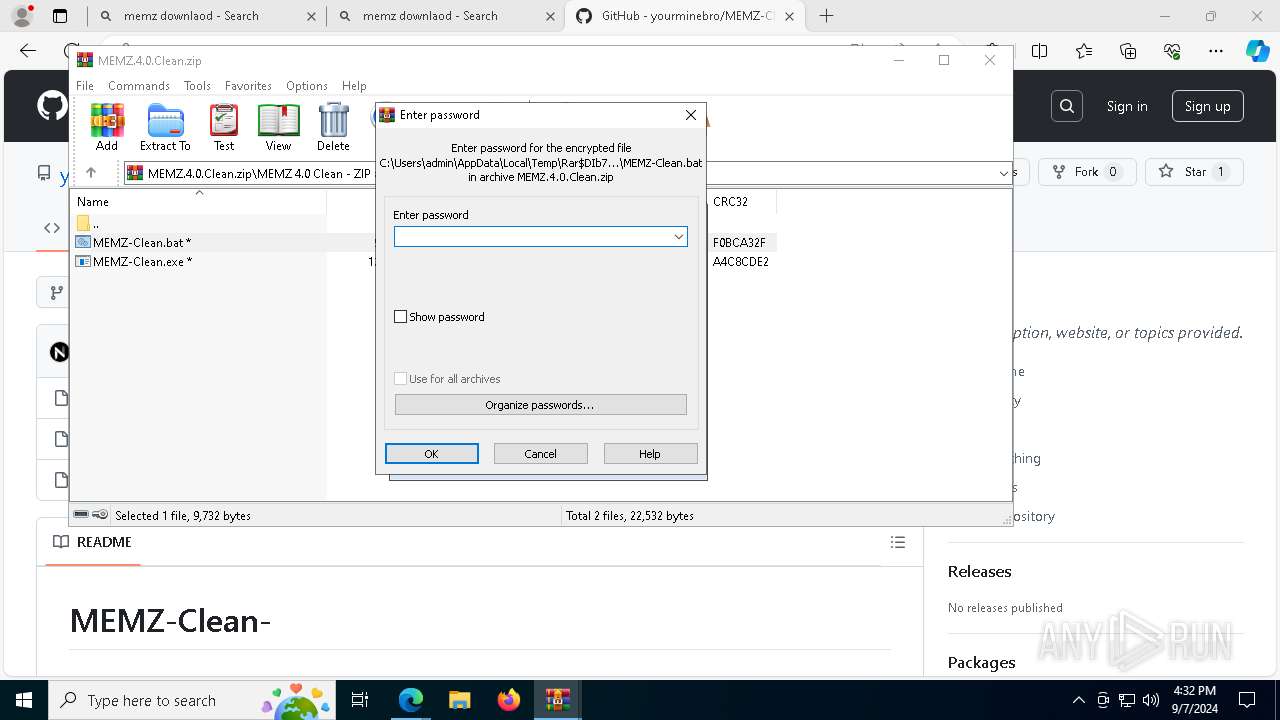
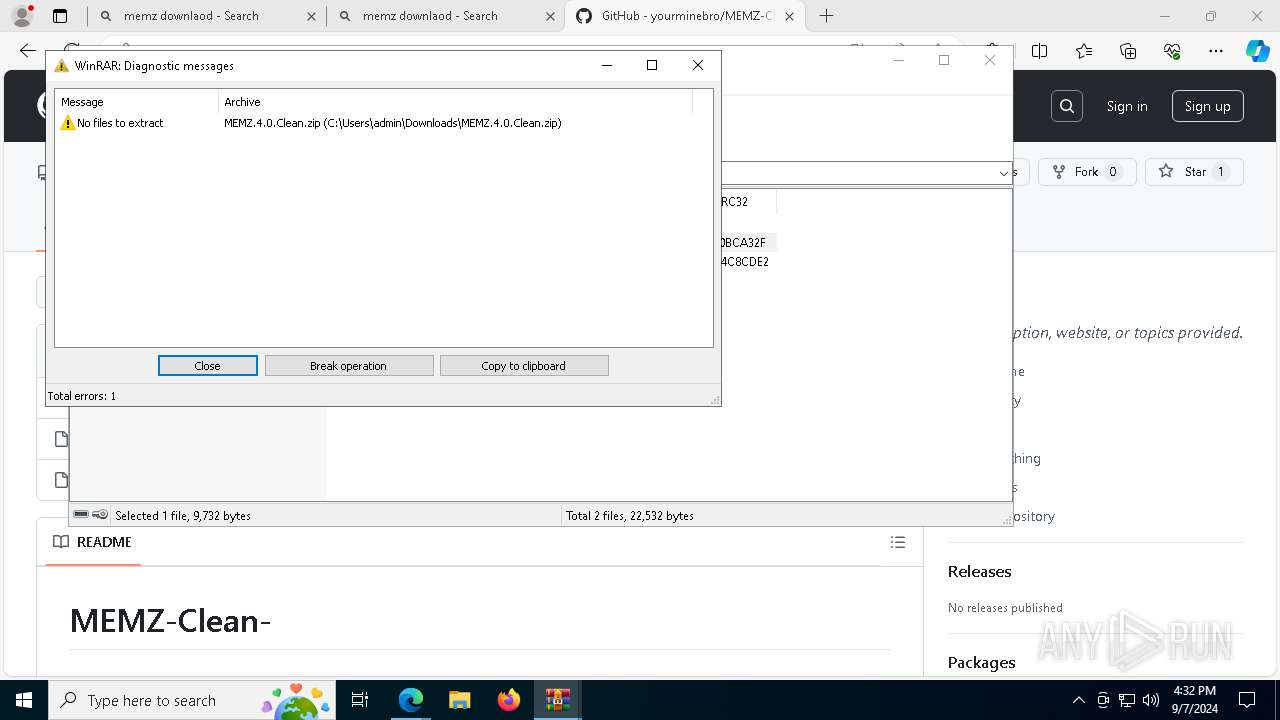
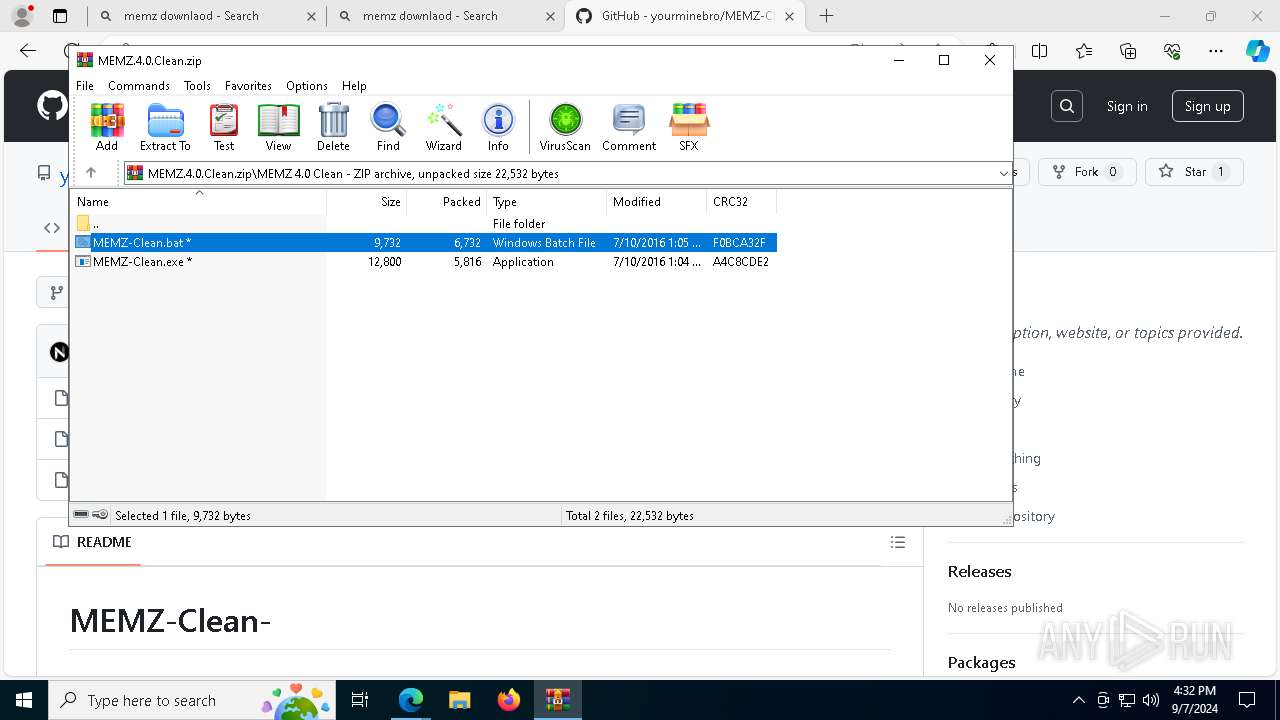
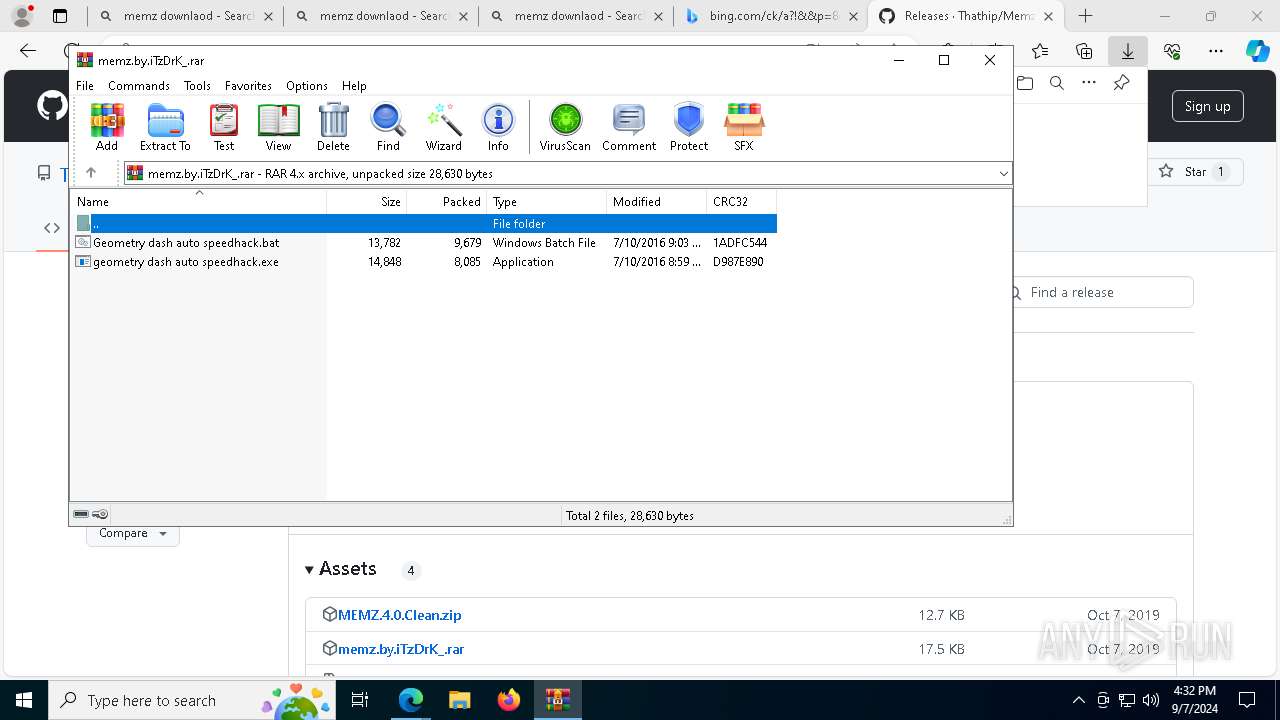
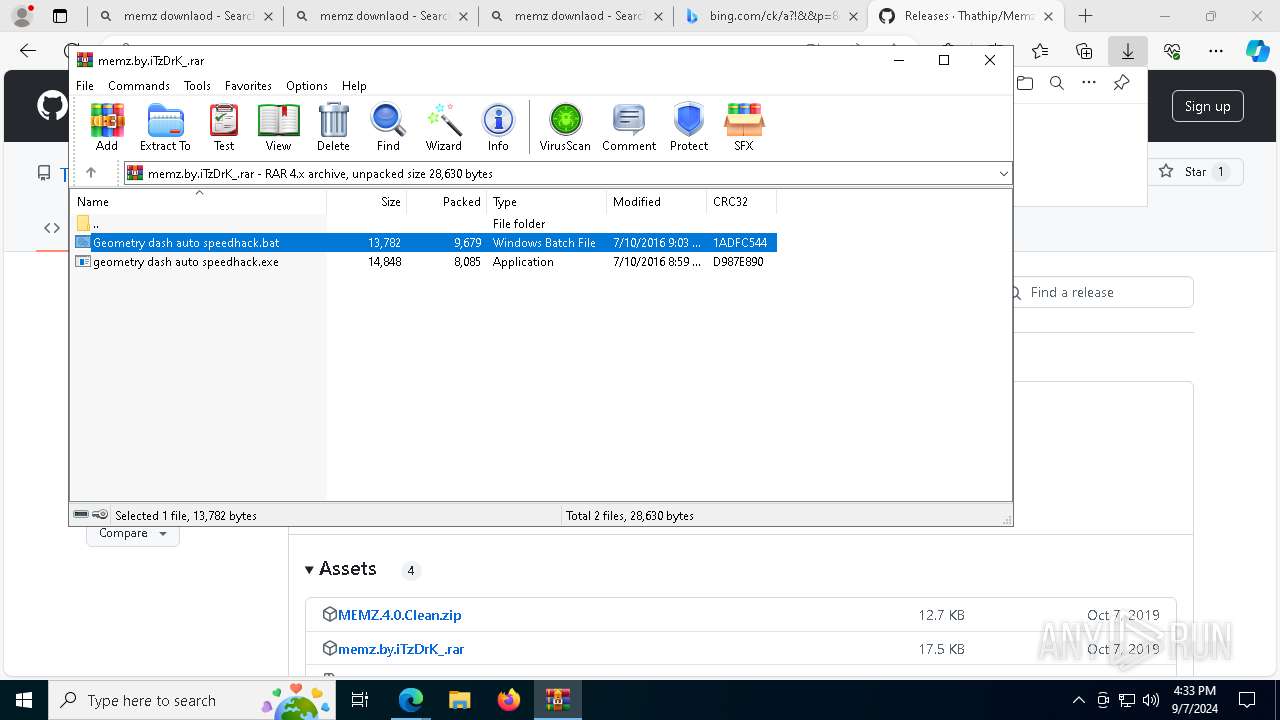
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7568)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7568)
The process executes JS scripts
- cmd.exe (PID: 5052)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 7876)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 7876)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7876)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 7876)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 7876)
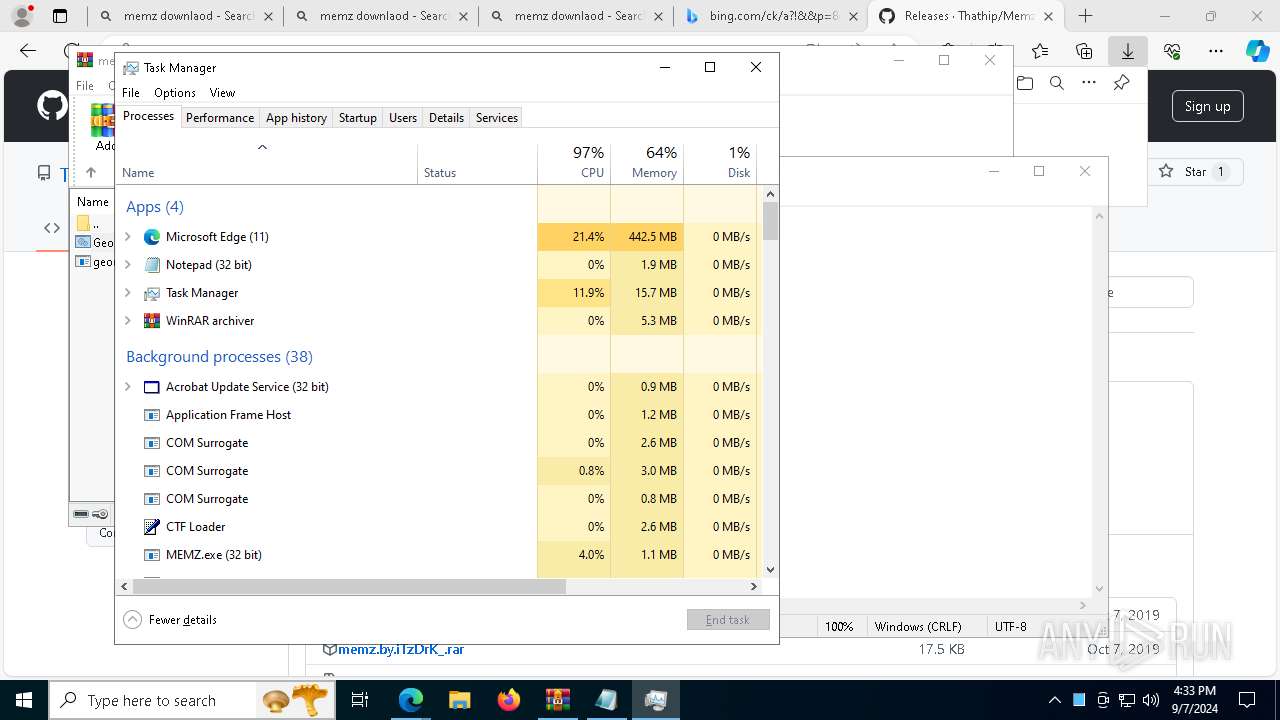
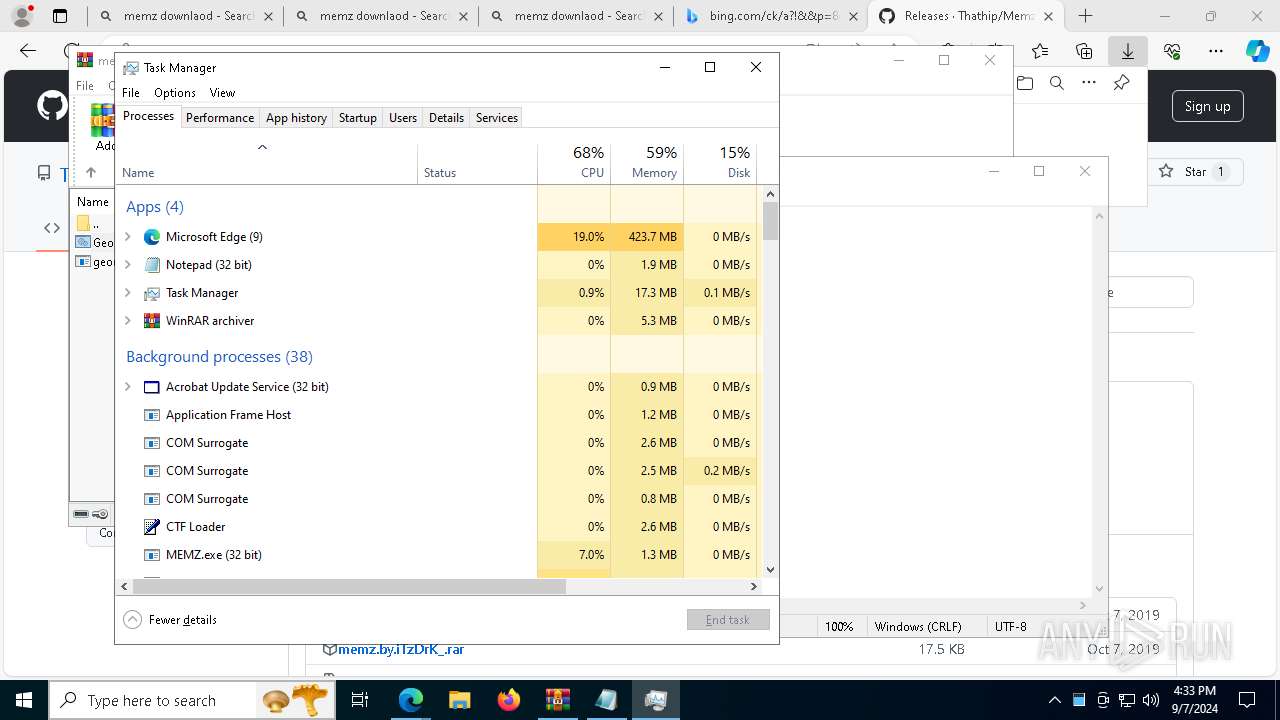
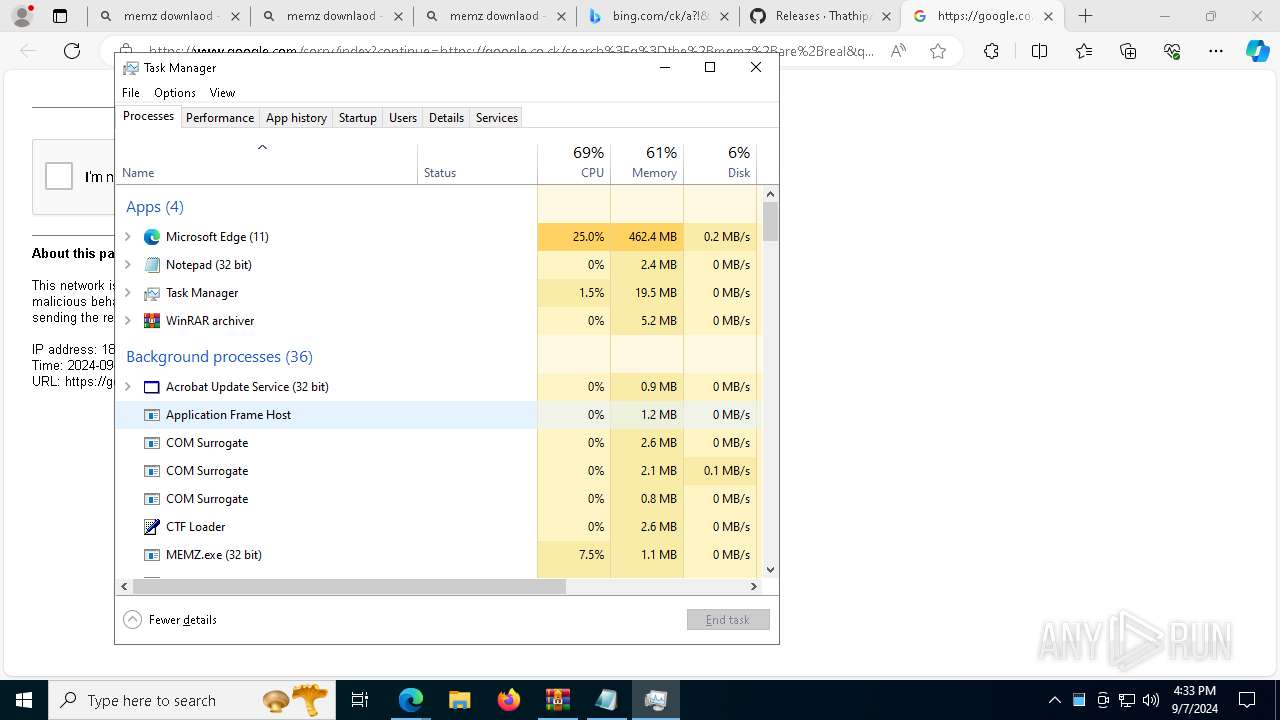
The executable file from the user directory is run by the CMD process
- MEMZ.exe (PID: 780)
- MEMZ.exe (PID: 7484)
- MEMZ.exe (PID: 7552)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 7876)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 7876)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 7876)
Executable content was dropped or overwritten
- cscript.exe (PID: 7876)
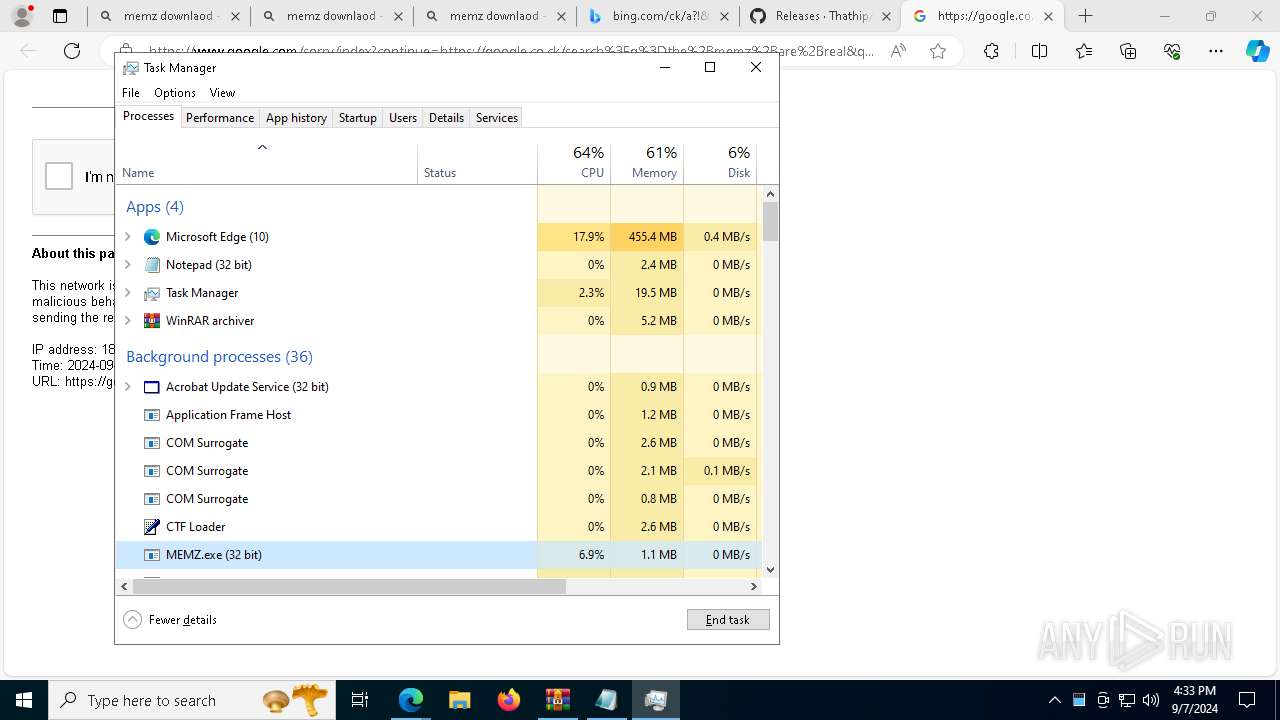
Creates file in the systems drive root
- MEMZ.exe (PID: 300)
- notepad.exe (PID: 4772)
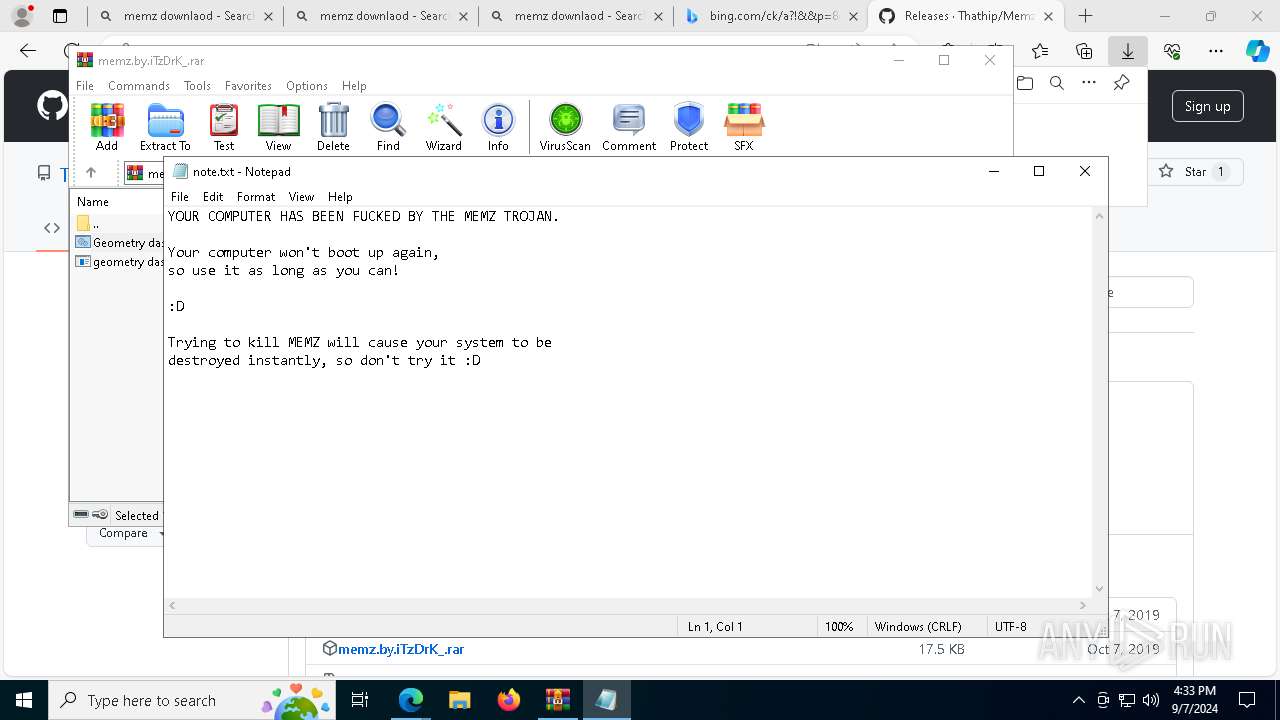
Start notepad (likely ransomware note)
- MEMZ.exe (PID: 300)
Application launched itself
- MEMZ.exe (PID: 7484)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 2820)
- WinRAR.exe (PID: 7684)
- msedge.exe (PID: 4920)
- msedge.exe (PID: 4876)
- msedge.exe (PID: 3672)
- WinRAR.exe (PID: 7568)
- cscript.exe (PID: 7876)
- cmd.exe (PID: 5052)
- MEMZ.exe (PID: 7484)
- MEMZ.exe (PID: 300)
Application launched itself
- msedge.exe (PID: 3672)
Checks supported languages
- identity_helper.exe (PID: 6292)
- MEMZ.exe (PID: 7484)
- MEMZ.exe (PID: 7700)
- MEMZ.exe (PID: 608)
- MEMZ.exe (PID: 1356)
- MEMZ.exe (PID: 6780)
- MEMZ.exe (PID: 300)
- MEMZ.exe (PID: 5148)
Reads Environment values
- identity_helper.exe (PID: 6292)
Reads the computer name
- identity_helper.exe (PID: 6292)
- MEMZ.exe (PID: 7484)
- MEMZ.exe (PID: 300)
- MEMZ.exe (PID: 7700)
- MEMZ.exe (PID: 608)
- MEMZ.exe (PID: 5148)
- MEMZ.exe (PID: 6780)
Reads the software policy settings
- slui.exe (PID: 7848)
- slui.exe (PID: 6856)
Sends debugging messages
- msedge.exe (PID: 3036)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3672)
Checks proxy server information
- slui.exe (PID: 6856)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7876)
- notepad.exe (PID: 4772)
- Taskmgr.exe (PID: 8400)
Creates files or folders in the user directory
- cscript.exe (PID: 7876)
Process checks computer location settings
- MEMZ.exe (PID: 300)
- MEMZ.exe (PID: 7484)
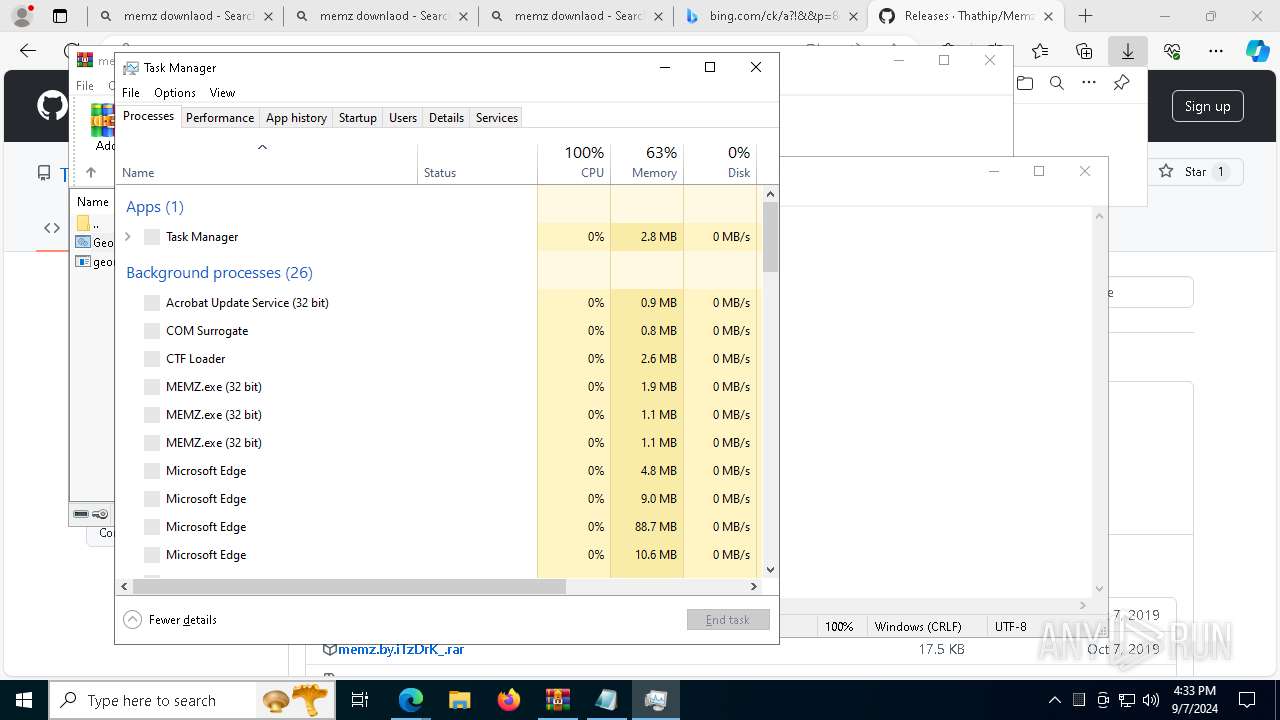
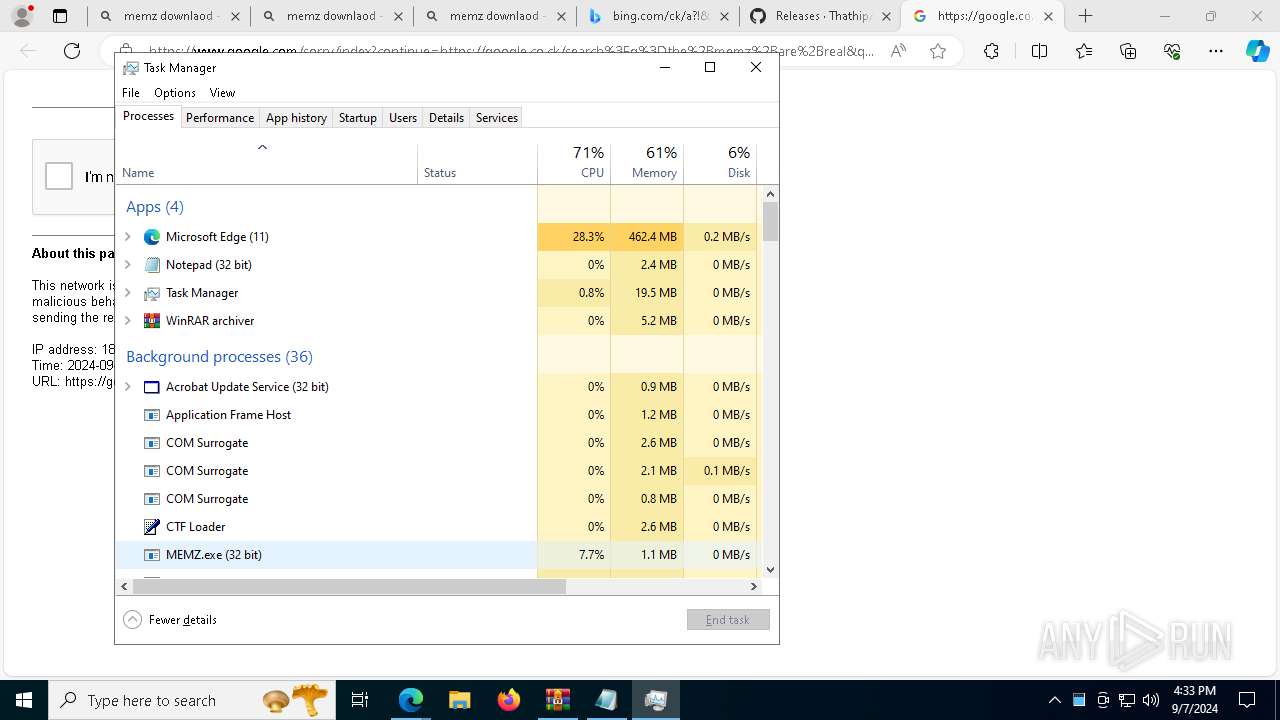
Manual execution by a user
- Taskmgr.exe (PID: 8400)
- Taskmgr.exe (PID: 8348)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 300)
- MEMZ.exe (PID: 5148)
- MEMZ.exe (PID: 7700)
- MEMZ.exe (PID: 608)
- MEMZ.exe (PID: 6780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
259
Monitored processes
119
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5300 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6180 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /main | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2748 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=9524 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 608 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 780 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=4496 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5768 --field-trial-handle=2336,i,4258747926528357838,541979618870688407,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 599
Read events
17 478
Write events
120
Delete events
1
Modification events
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (3672) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3672) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3672) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3672) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
10
Suspicious files
893
Text files
197
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129f94.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129fb3.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129fc2.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129fc2.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
218
DNS requests
211
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7496 | svchost.exe | HEAD | 200 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
1404 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 23.48.23.56:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1726022725&P2=404&P3=2&P4=gUh1%2fzVJmij9ViyKiG9zU5fwUJtGYPpKg5LczK3SFnYxzWfPsLzKiu6TtH%2fIwAr5mvHwWGZFXXepsWl2nHL35Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2248 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6364 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3964 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3672 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3964 | msedge.exe | 128.116.21.3:80 | roblox.com | ROBLOX-PRODUCTION | US | whitelisted |
3964 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3964 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3964 | msedge.exe | 128.116.21.3:443 | roblox.com | ROBLOX-PRODUCTION | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
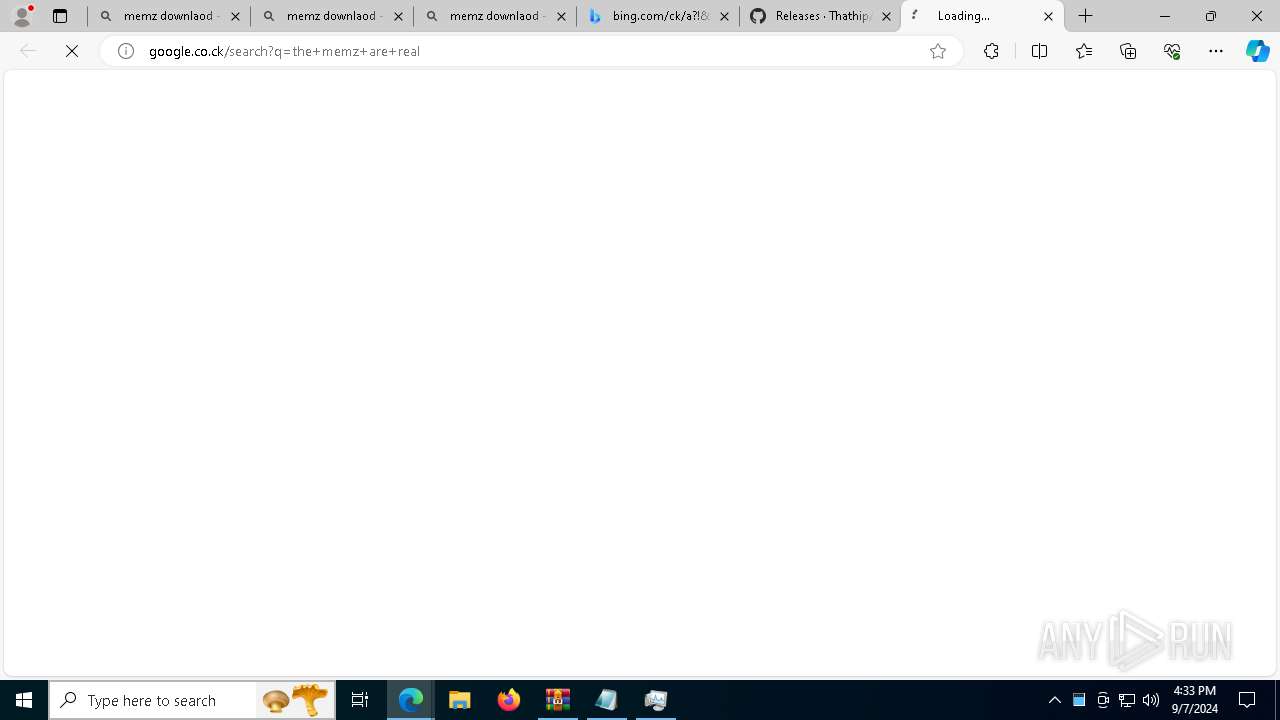
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
roblox.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.roblox.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
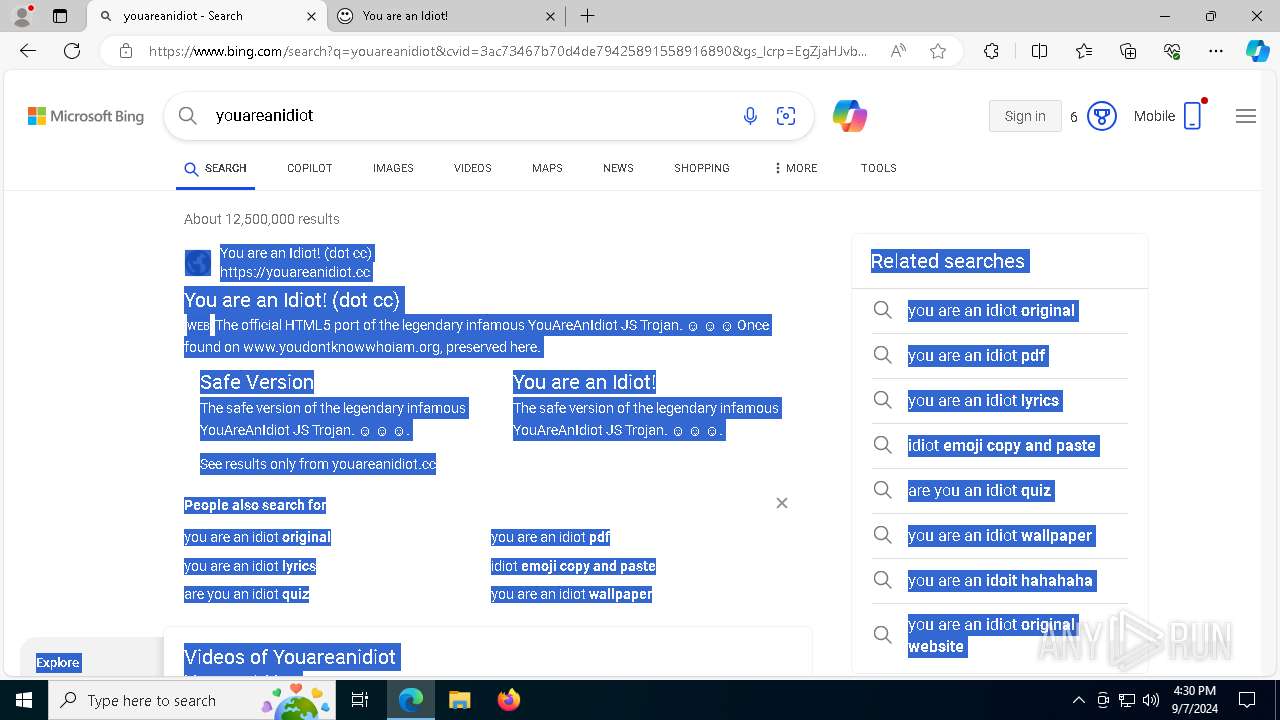
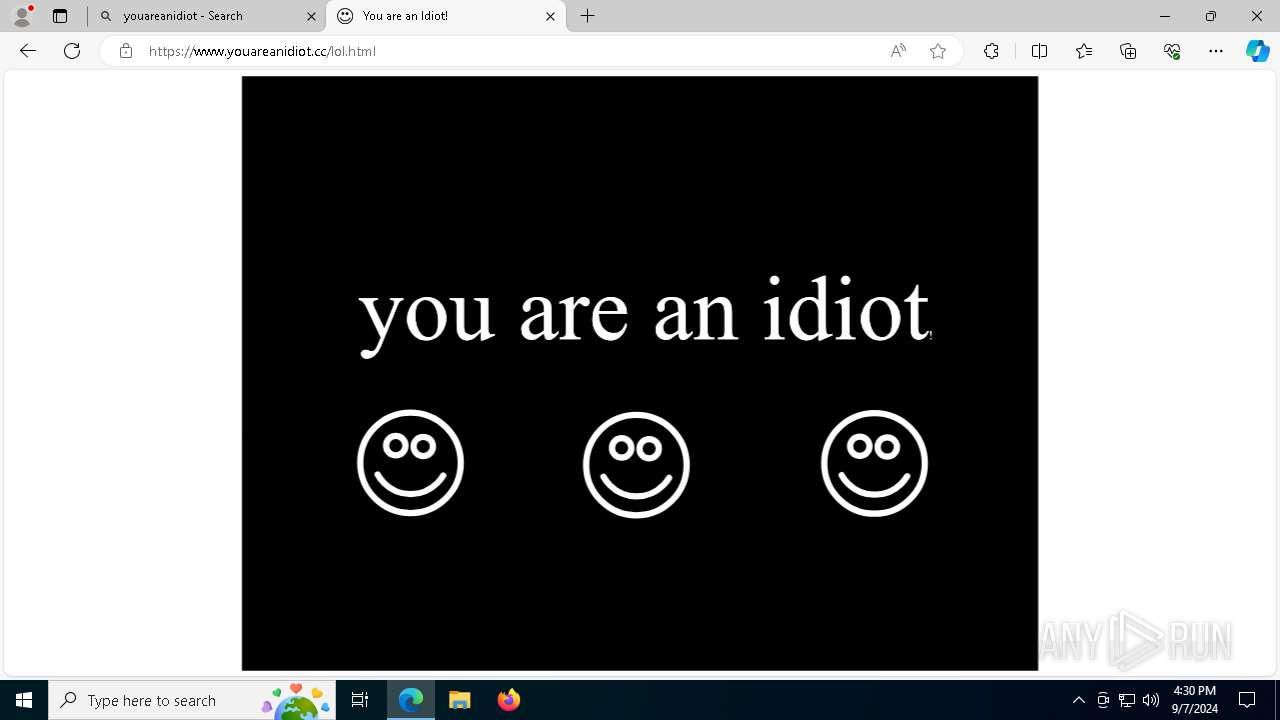
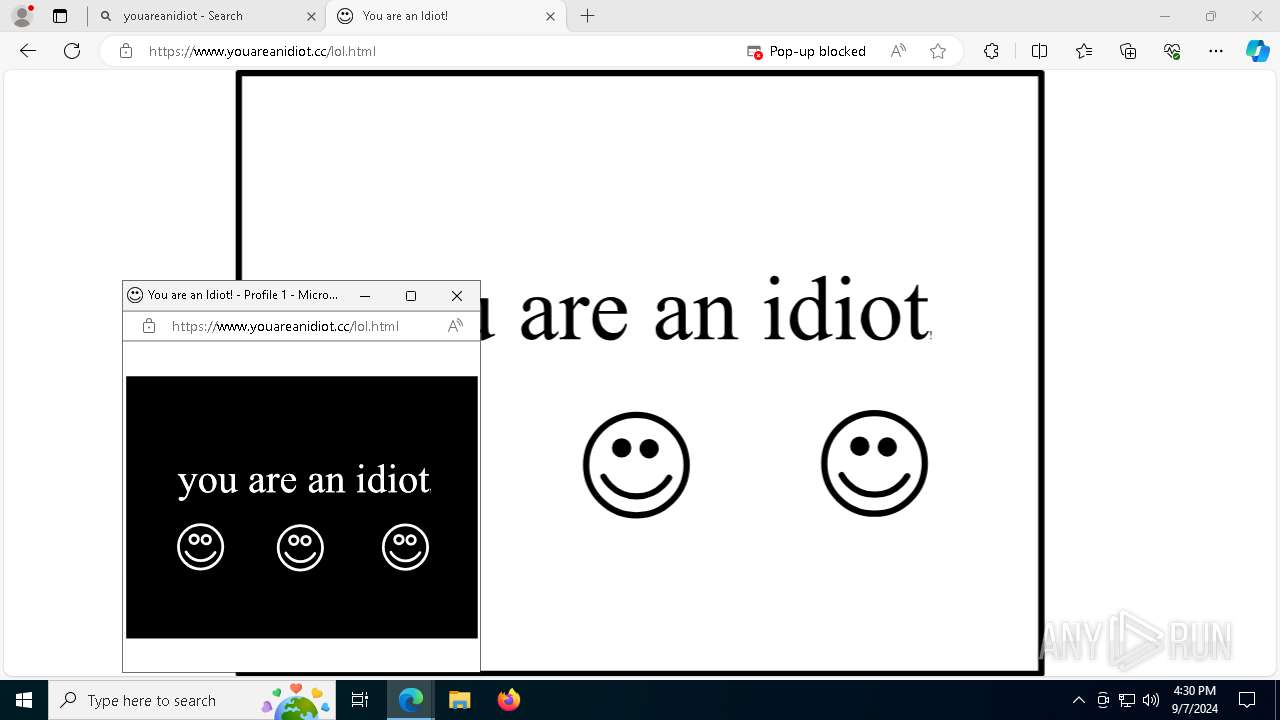
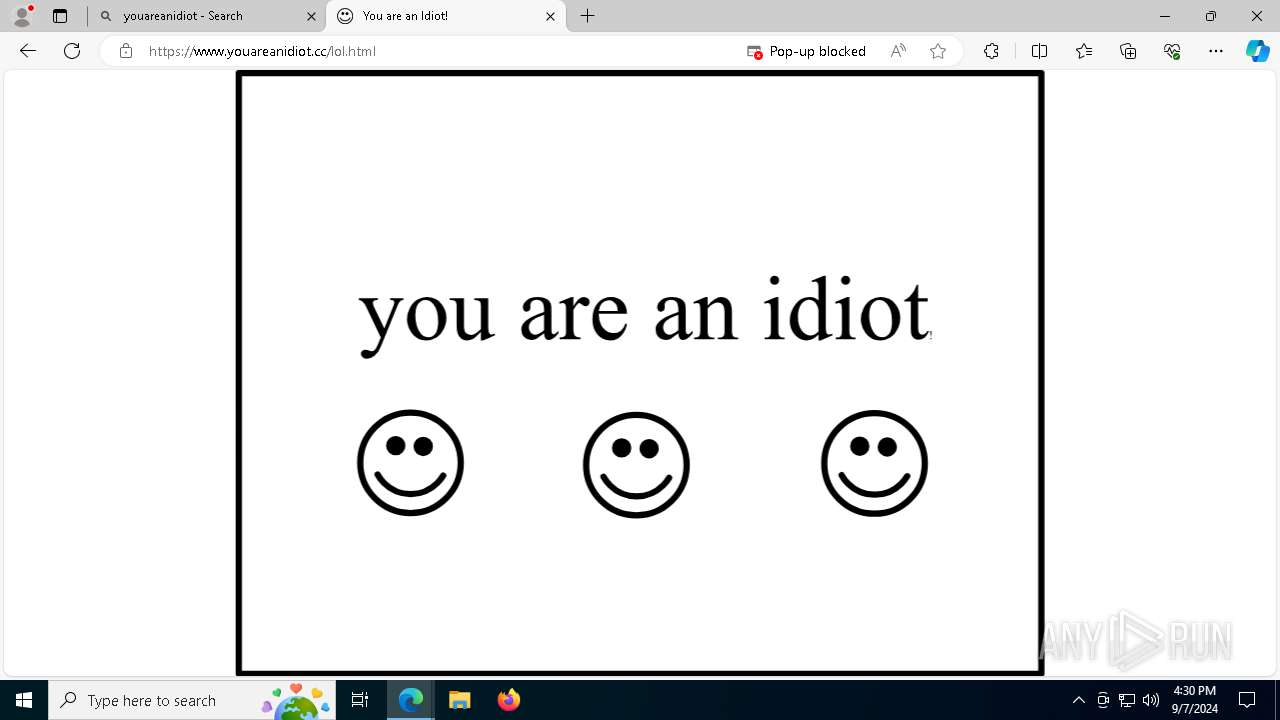
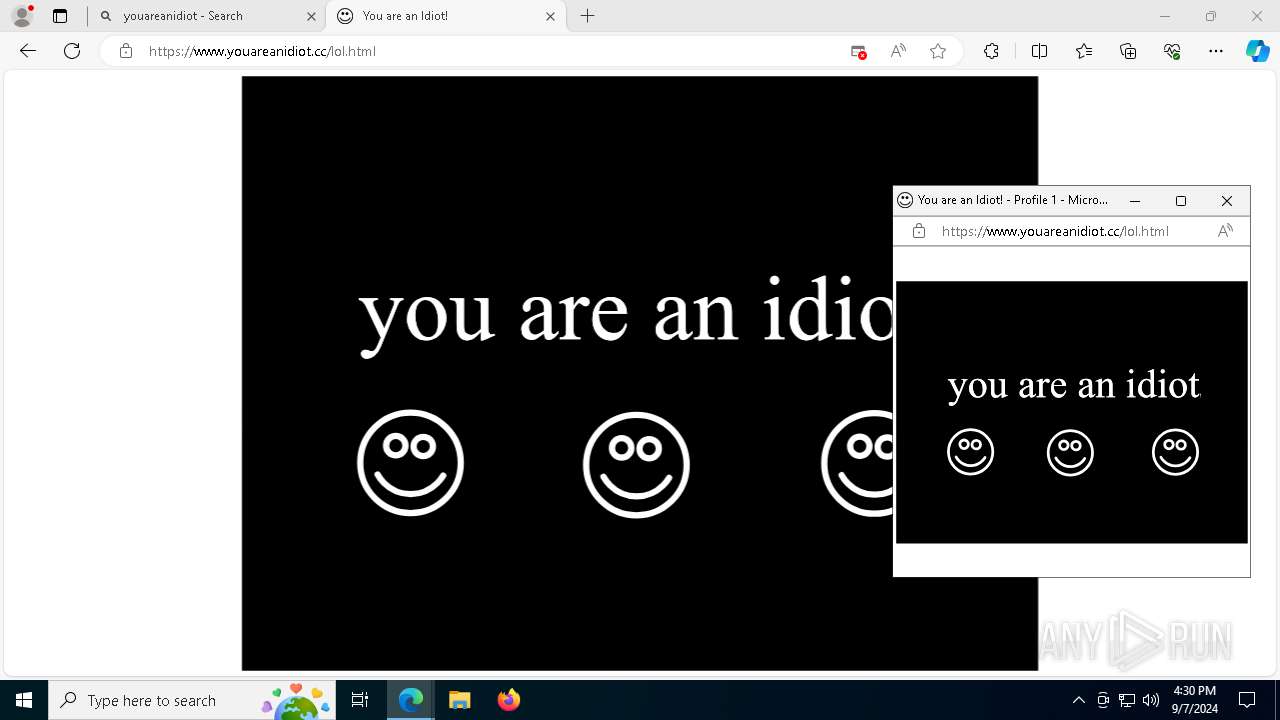
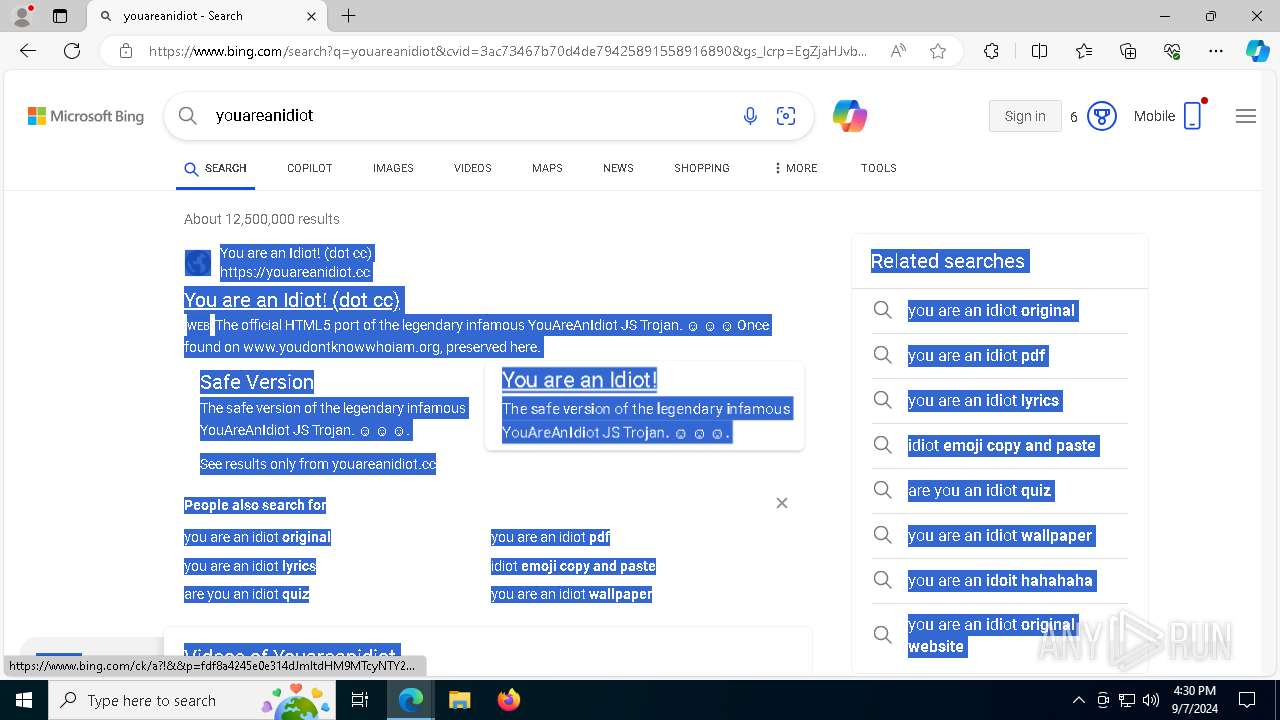
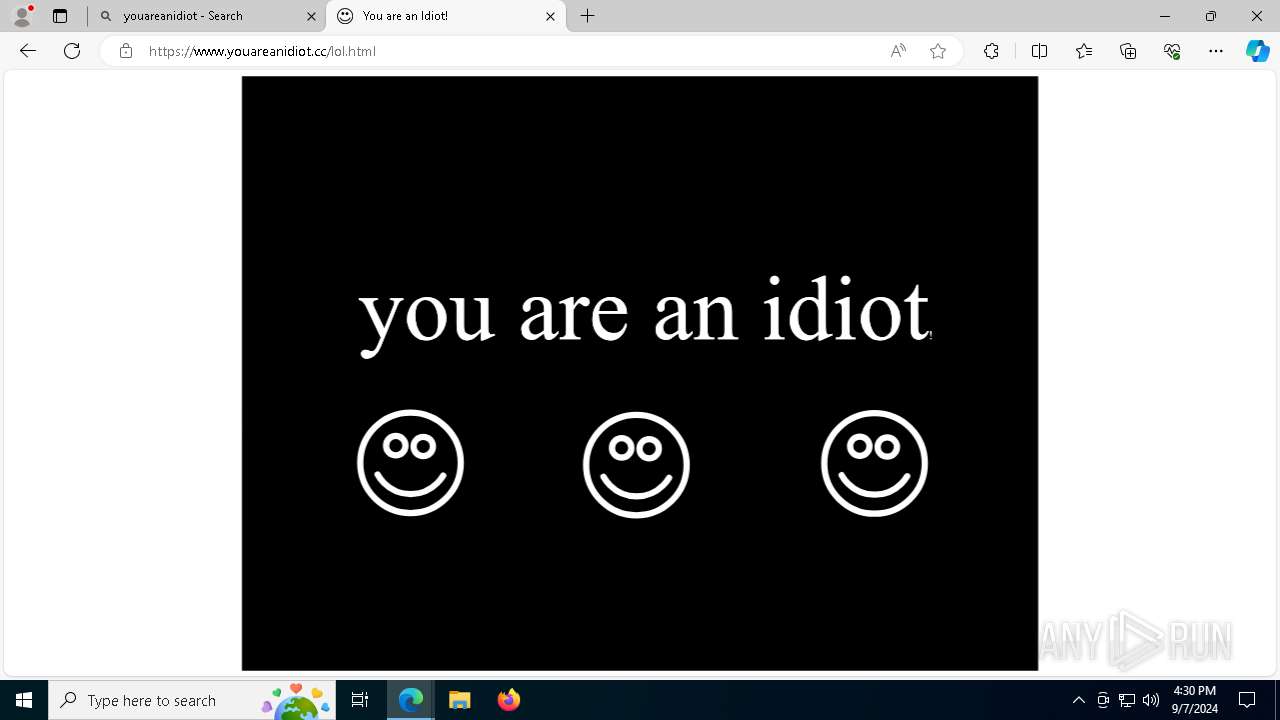
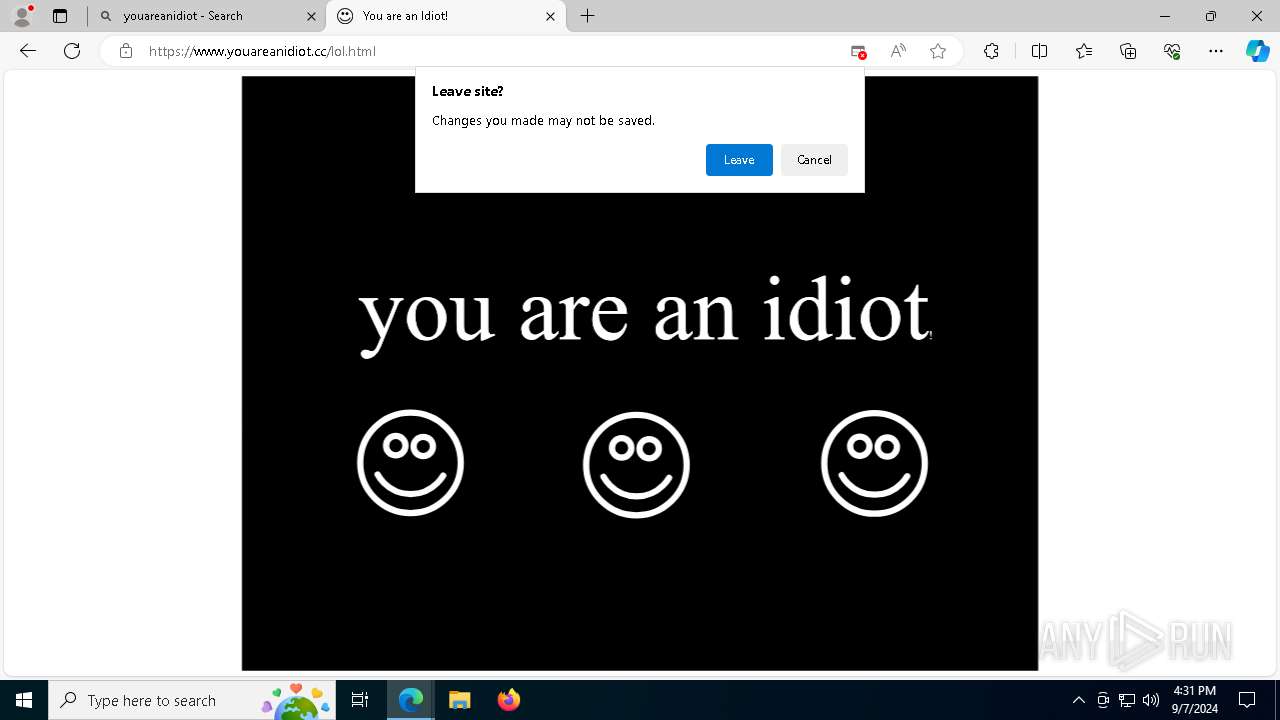
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3964 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
msedge.exe | [0907/163028.378:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0907/163029.007:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0907/163029.009:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
|
msedge.exe | [0907/163029.009:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff85f0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0907/163029.009:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\SYSTEM32\ntdll.dll
|
msedge.exe | [0907/163029.009:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff6f10000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0907/163029.010:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNEL32.DLL
|
msedge.exe | [0907/163029.010:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff5da0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0907/163029.010:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNELBASE.dll
|
msedge.exe | [0907/163029.010:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7fffd23c0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|