| URL: | roblox.com |
| Full analysis: | https://app.any.run/tasks/08f00167-cc29-4313-93a8-393d29f28ffd |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 12:19:33 |
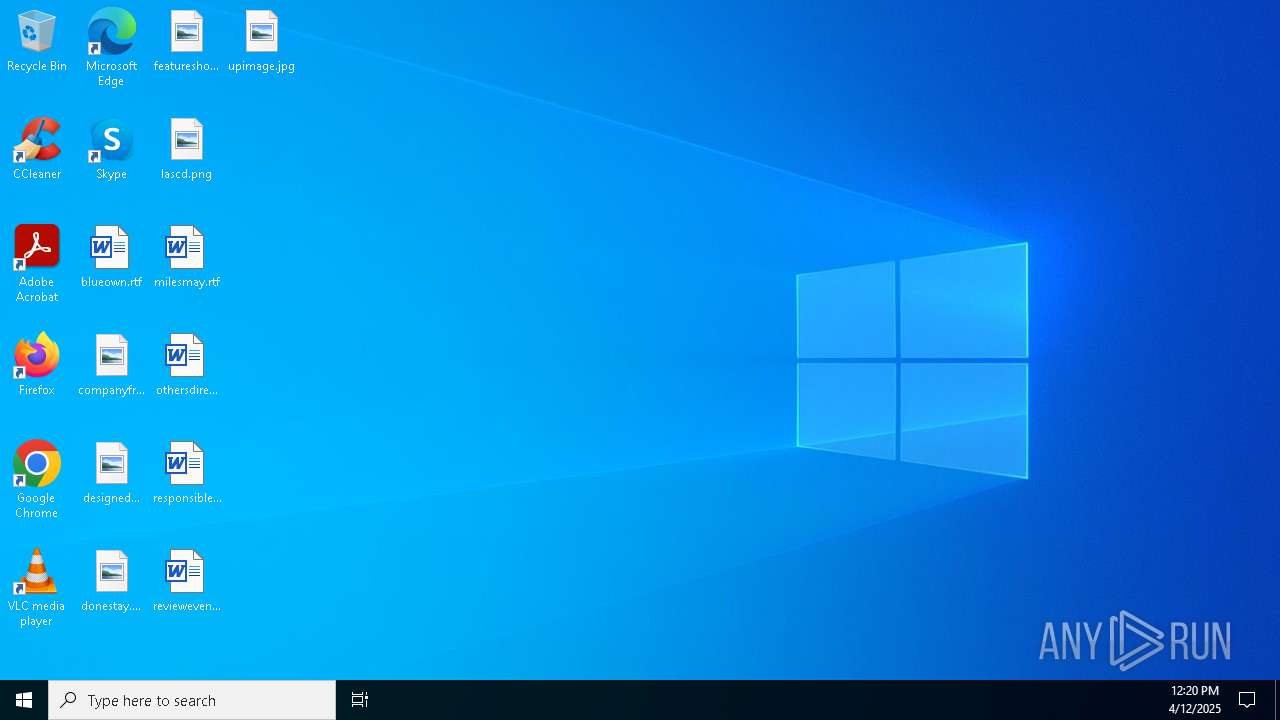
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C06012A24CBE7C52D0E0A9AD4A936C79 |
| SHA1: | FB22C4B259680F2301B90F8DD5FB40D975C17190 |
| SHA256: | C1688E9B4C7A1DC950E389DE2A104CCDC8C80648F9202D1CCA5F4289D5D43032 |
| SSDEEP: | 3:MJ6In:MNn |
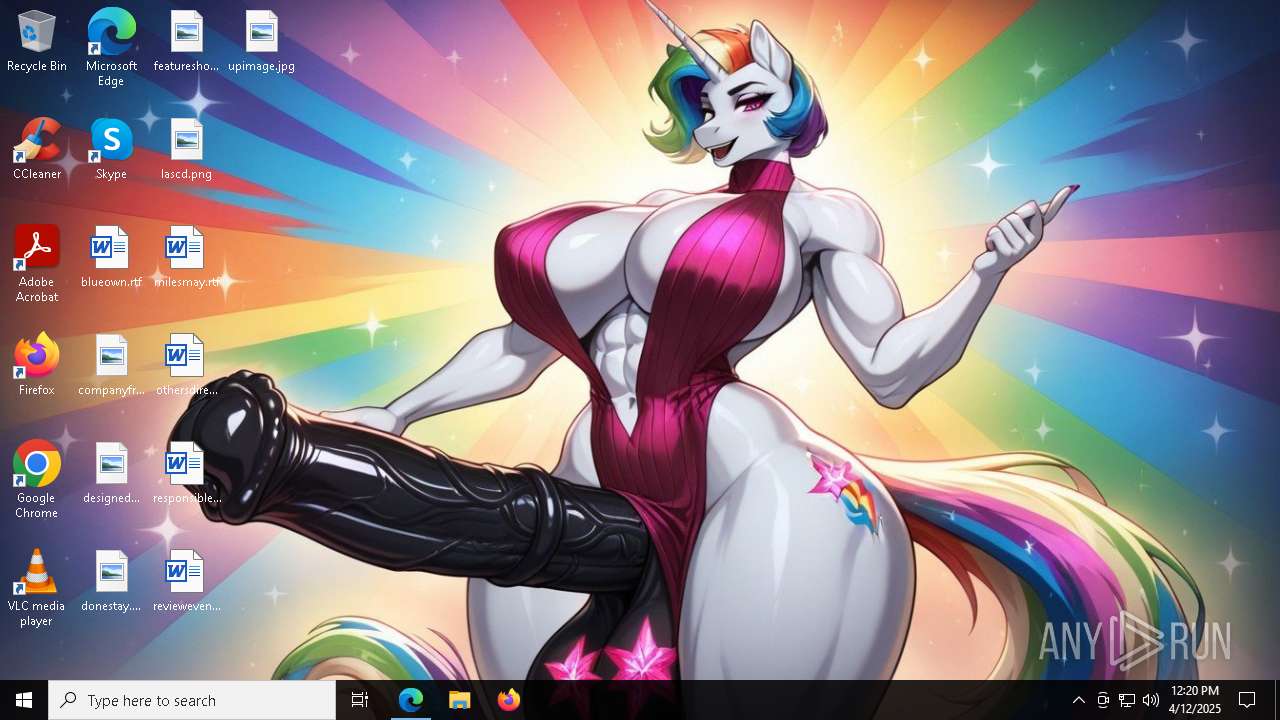
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 5048)
Disables task manager
- powershell.exe (PID: 8164)
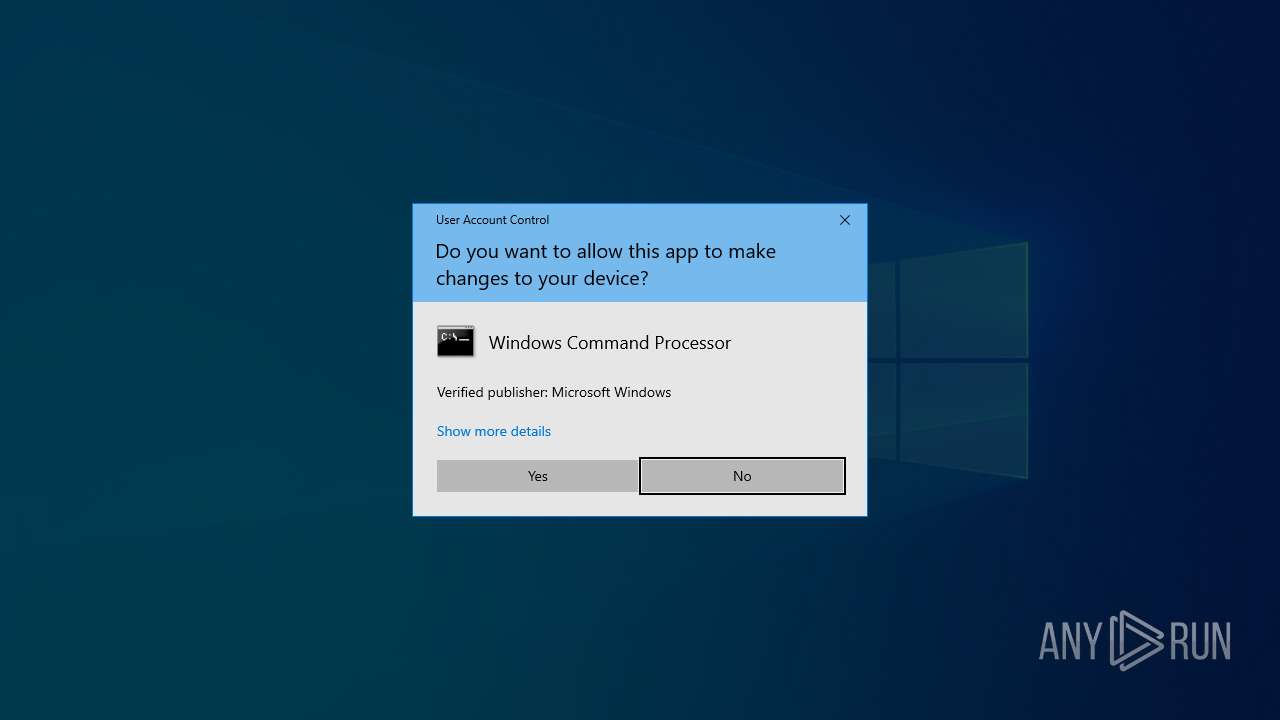
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7196)
Bypass execution policy to execute commands
- powershell.exe (PID: 8164)
- powershell.exe (PID: 1280)
Run PowerShell with an invisible window
- powershell.exe (PID: 1280)
SUSPICIOUS
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6652)
- net.exe (PID: 7344)
- cmd.exe (PID: 7508)
- net.exe (PID: 7588)
- cmd.exe (PID: 7196)
- net.exe (PID: 2416)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6652)
- cmd.exe (PID: 7196)
Starts process via Powershell
- powershell.exe (PID: 7364)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7364)
- cmd.exe (PID: 7508)
- wscript.exe (PID: 7304)
- cmd.exe (PID: 7196)
- wscript.exe (PID: 5596)
Application launched itself
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7196)
Executing commands from a ".bat" file
- wscript.exe (PID: 7304)
- wscript.exe (PID: 5596)
- powershell.exe (PID: 7364)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7304)
- wscript.exe (PID: 5596)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5048)
The process executes VB scripts
- cmd.exe (PID: 5048)
- cmd.exe (PID: 7508)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7508)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7196)
The process executes Powershell scripts
- cmd.exe (PID: 7196)
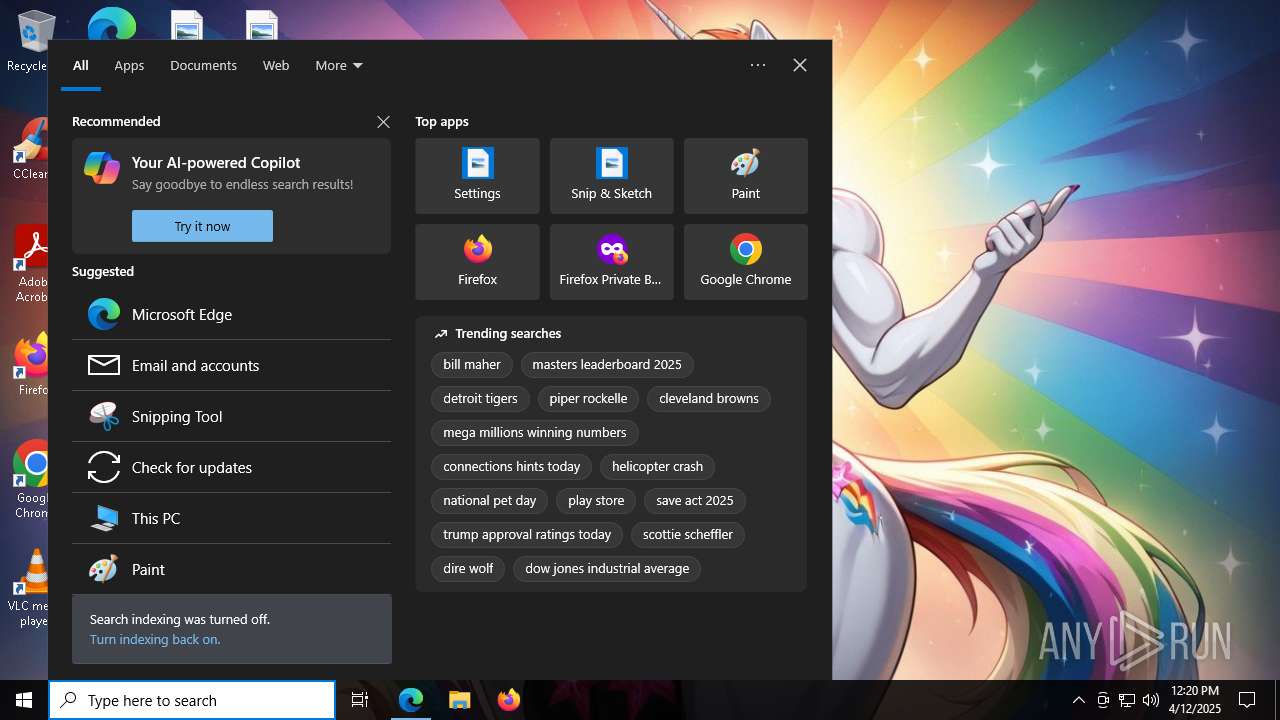
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 812)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 812)
- SearchApp.exe (PID: 4260)
CSC.EXE is used to compile C# code
- csc.exe (PID: 1388)
Executable content was dropped or overwritten
- csc.exe (PID: 1388)
INFO
Checks supported languages
- identity_helper.exe (PID: 5596)
- identity_helper.exe (PID: 5376)
- mode.com (PID: 7296)
- mode.com (PID: 6112)
- mode.com (PID: 2152)
- StartMenuExperienceHost.exe (PID: 812)
- SearchApp.exe (PID: 4260)
- cvtres.exe (PID: 7380)
- TextInputHost.exe (PID: 2904)
- csc.exe (PID: 1388)
Application launched itself
- msedge.exe (PID: 496)
- msedge.exe (PID: 7648)
Reads Environment values
- identity_helper.exe (PID: 5596)
- identity_helper.exe (PID: 5376)
- SearchApp.exe (PID: 4260)
Reads the computer name
- identity_helper.exe (PID: 5596)
- identity_helper.exe (PID: 5376)
- StartMenuExperienceHost.exe (PID: 812)
- SearchApp.exe (PID: 4260)
- TextInputHost.exe (PID: 2904)
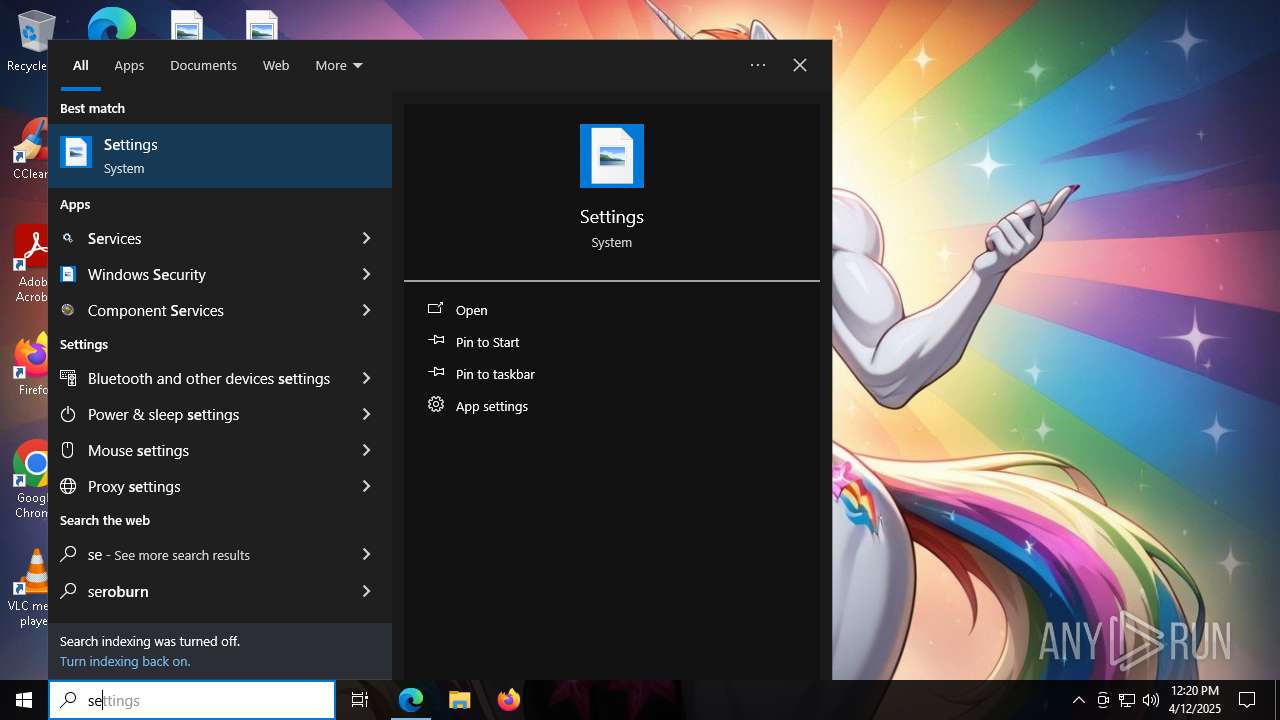
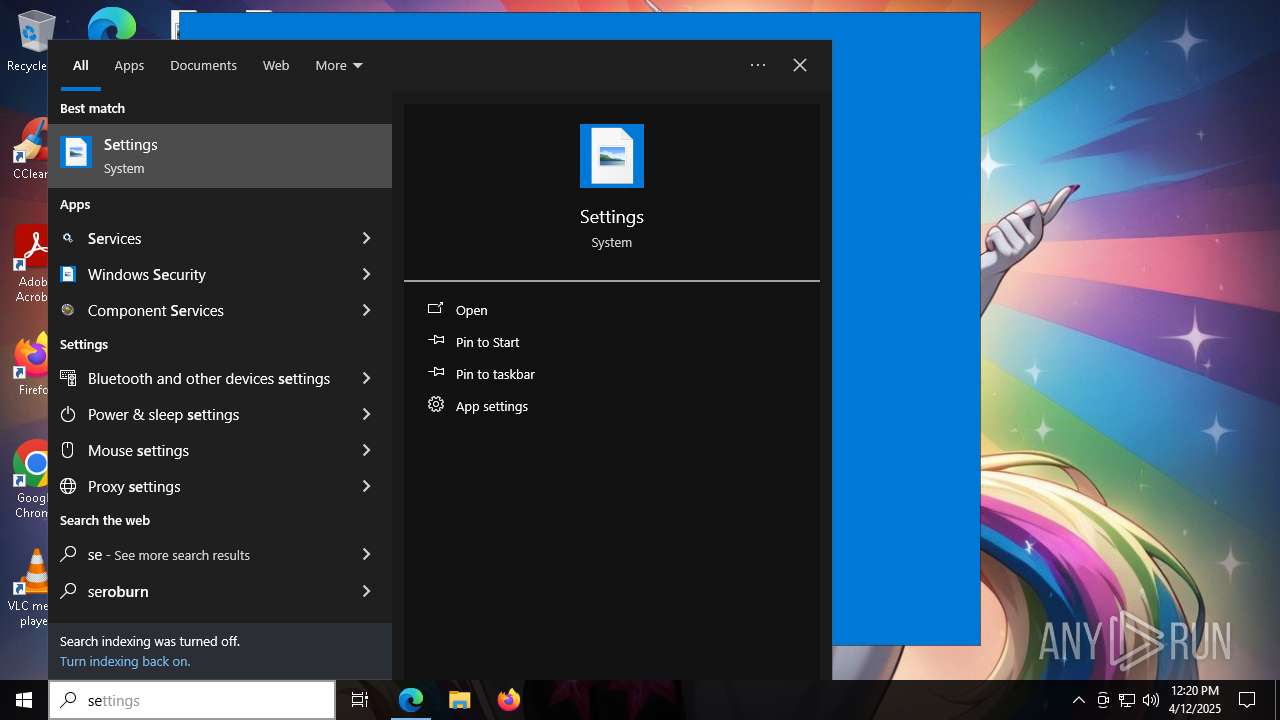
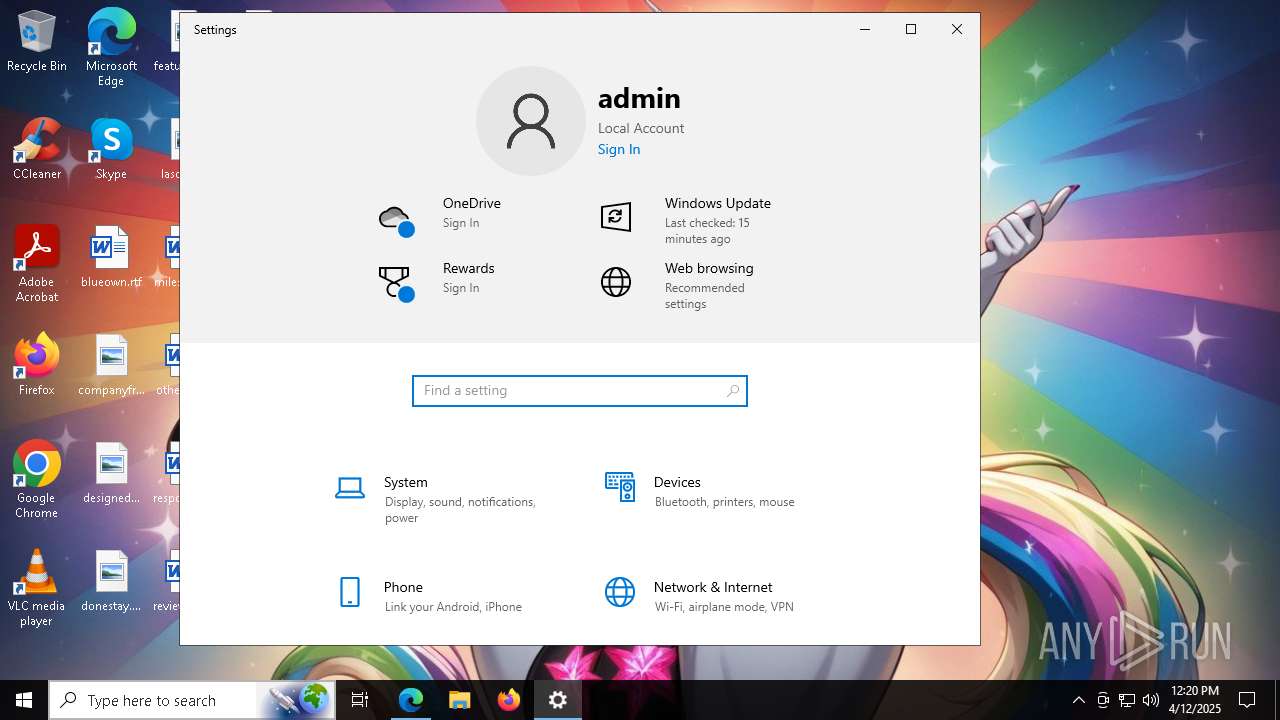
Manual execution by a user
- cmd.exe (PID: 6652)
Starts MODE.COM to configure console settings
- mode.com (PID: 7296)
- mode.com (PID: 6112)
- mode.com (PID: 2152)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8164)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8164)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8164)
Checks proxy server information
- powershell.exe (PID: 1280)
- SearchApp.exe (PID: 4260)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 812)
- SearchApp.exe (PID: 4260)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 4260)
- csc.exe (PID: 1388)
Disables trace logs
- powershell.exe (PID: 1280)
Reads the software policy settings
- SearchApp.exe (PID: 4260)
- slui.exe (PID: 1164)
Create files in a temporary directory
- cvtres.exe (PID: 7380)
- csc.exe (PID: 1388)
The sample compiled with english language support
- msedge.exe (PID: 6600)
Executable content was dropped or overwritten
- msedge.exe (PID: 6600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
237
Monitored processes
100
Malicious processes
5
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "roblox.com" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5920 --field-trial-handle=2428,i,8119223496790946795,2536044259325273627,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo C:\Users\admin\AppData\Roaming\appdiagnostics\ " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=5524 --field-trial-handle=2424,i,10806164745722519423,13438322996502380106,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File "C:\Users\admin\AppData\Local\Temp\payload.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6508 --field-trial-handle=2424,i,10806164745722519423,13438322996502380106,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\datuxmcs\datuxmcs.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6832 --field-trial-handle=2428,i,8119223496790946795,2536044259325273627,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 460
Read events
40 282
Write events
175
Delete events
3
Modification events
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A1CBB01D2A912F00 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F6D7B91D2A912F00 | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CE3EE11D-E0E0-4662-A076-145DCBEA4C4B} | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B221F7C9-04BB-4DD0-A137-A8E9BEF70DA5} | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3D887D46-82E8-49A9-B85B-D27D8D88BA9F} | |||
| (PID) Process: | (496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {326FA7BC-0972-4DCD-A436-A015E172E60E} | |||
Executable files
18
Suspicious files
507
Text files
214
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b306.TMP | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b306.TMP | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b306.TMP | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
119
DNS requests
123
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6960 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744955549&P2=404&P3=2&P4=nStB6QRzKbkkWmFsormpZVWEIyQTem5ld2SvOv91SxsBJIe1yDo%2fdSo7Nmp802jjj5f699SKqm%2bRPyuwdfAzjQ%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4260 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1348 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4260 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6960 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cd4e6fbf-c0e9-4dc2-9e3d-7f538bc7435a?P1=1744955549&P2=404&P3=2&P4=fUqgHtAEMA5voIdLGzfXPQEpMe77cVbv2eMLIHKZBOs0hStnQqRKdKegq%2b5W%2frc15lih4QbhtlvteJexaSpdrA%3d%3d | unknown | — | — | whitelisted |
1348 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4260 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4260 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.38:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7400 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7400 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7400 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
496 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7400 | msedge.exe | 128.116.21.3:80 | roblox.com | ROBLOX-PRODUCTION | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
roblox.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.roblox.com |
| whitelisted |