| download: | update.dll |
| Full analysis: | https://app.any.run/tasks/8f0e0ce5-1397-4f2d-a0f4-fc3082673c2d |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2020, 01:15:12 |
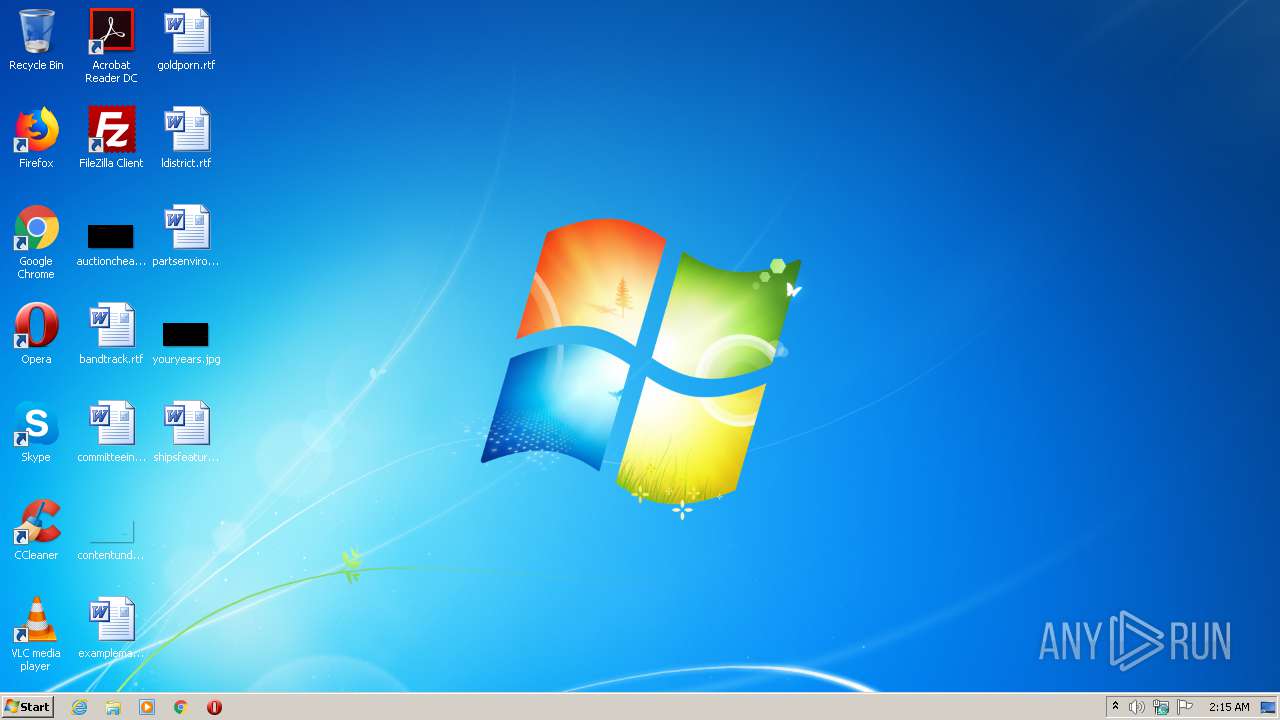
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 23607DF83A8C417844CE536D300D07D9 |
| SHA1: | 555999085969F600E30E379AE982762B6C319B0B |
| SHA256: | C15A16ACAAB7B12A7BC24416A36C5F7DC04F6512AC278F1877C231B0A03C76C0 |
| SSDEEP: | 12288:hcm8hkw56GHhTNgDo4ugUcfmN+/tRbcDyyaIJekGB:hc15cihTNfMU/+/tRbcMRrB |
MALICIOUS
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2572)
Actions looks like stealing of personal data
- rundll32.exe (PID: 2572)
Application was dropped or rewritten from another process
- rundll32.exe (PID: 2572)
SUSPICIOUS
Creates files in the user directory
- rundll32.exe (PID: 2572)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2572)
INFO
Loads main object executable
- rundll32.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:01 14:23:29+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 360960 |
| InitializedDataSize: | 356864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29b32 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.9200.20789 |
| ProductVersionNumber: | 6.2.9200.20789 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Windows (R) Win 7 DDK provider |
| FileDescription: | File comparison utility |
| FileVersion: | 6.2.9200.20789 |
| InternalName: | SDKDIFF.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | SDKDIFF.EXE |
| ProductName: | Windows (R) Win 7 DDK driver |
| ProductVersion: | 6.2.9200.20789 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jul-2020 12:23:29 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Windows (R) Win 7 DDK provider |
| FileDescription: | File comparison utility |
| FileVersion: | 6.2.9200.20789 |
| InternalName: | SDKDIFF.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | SDKDIFF.EXE |
| ProductName: | Windows (R) Win 7 DDK driver |
| ProductVersion: | 6.2.9200.20789 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-Jul-2020 12:23:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00058183 | 0x00058200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.78399 |
.rdata | 0x0005A000 | 0x0000CB40 | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.87483 |
.data | 0x00067000 | 0x00038B40 | 0x00035200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.20043 |
.idata | 0x000A0000 | 0x00001E8B | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78134 |
.tls | 0x000A2000 | 0x00004FD5 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000A7000 | 0x00005C99 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.14653 |
.reloc | 0x000AD000 | 0x00004B88 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.25726 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.58382 | 876 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
3 | 2.03848 | 308 | UNKNOWN | English - United States | RT_CURSOR |
26 | 2.75401 | 144 | UNKNOWN | English - United States | RT_STRING |
41 | 2.90062 | 210 | UNKNOWN | English - United States | RT_STRING |
42 | 3.36264 | 656 | UNKNOWN | English - United States | RT_STRING |
43 | 2.34548 | 88 | UNKNOWN | English - United States | RT_STRING |
44 | 3.40221 | 408 | UNKNOWN | English - United States | RT_STRING |
45 | 3.36387 | 878 | UNKNOWN | English - United States | RT_STRING |
46 | 3.46803 | 1184 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
DllRegisterServer | 1 | 0x0000150F |
Total processes
33
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2572 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Local\Temp\update.dll,DllRegisterServer | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | rundll32.exe | C:\Users\admin\AppData\Roaming\ArtPress\compatibility.ini | text | |
MD5:ED8B36407FE2C0E117F4DB829CEA9F98 | SHA256:7C8EAC3BE2840A538137351708E21B608BE9793241040DC4CDA18240DE55108C | |||
| 2572 | rundll32.exe | C:\Users\admin\AppData\Roaming\ArtPress\nvrundll32dn.mgb | executable | |
MD5:51138BEEA3E2C21EC44D0932C71762A8 | SHA256:5AD3C37E6F2B9DB3EE8B5AEEDC474645DE90C66E3D95F8620C48102F1EBA4124 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
0
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | rundll32.exe | 134.119.191.11:443 | — | velia.net Internetdienste GmbH | FR | malicious |
2572 | rundll32.exe | 185.14.31.104:443 | — | ITL Company | NL | malicious |
— | — | 185.14.31.104:443 | — | ITL Company | NL | malicious |
2572 | rundll32.exe | 185.99.2.65:443 | — | Globalhost d.o.o. | BA | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2572 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2572 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2572 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |