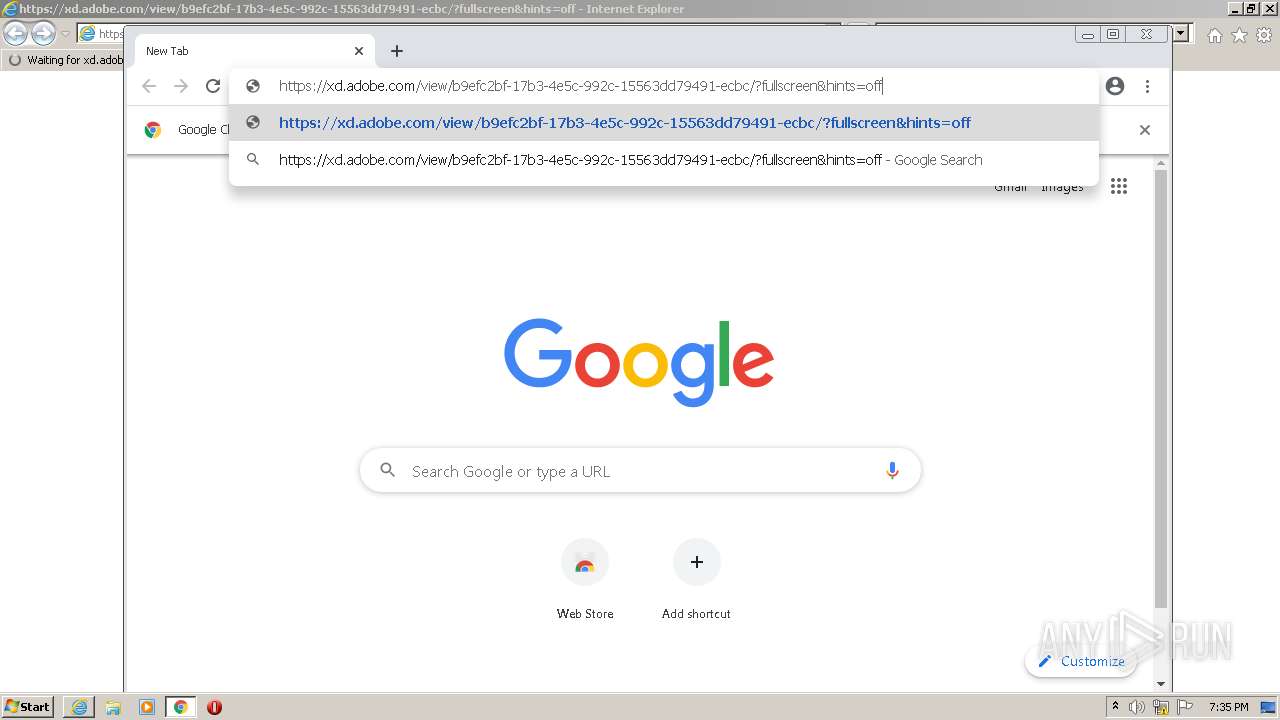
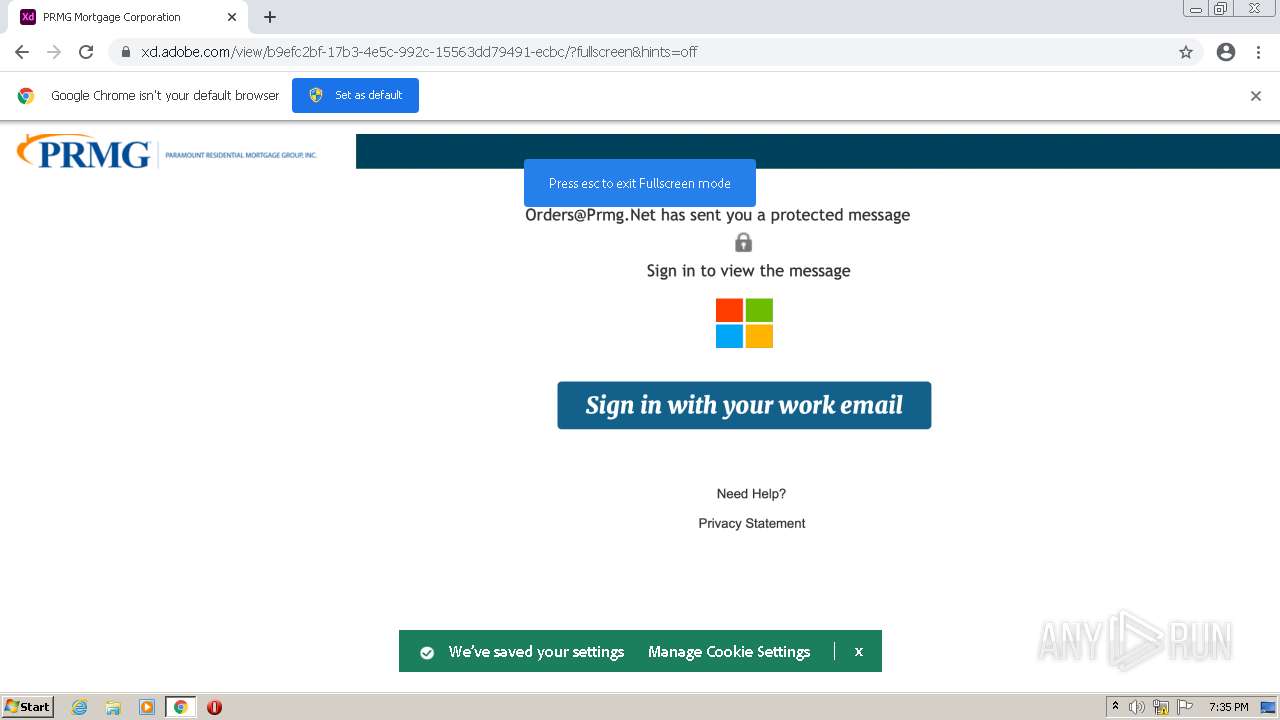
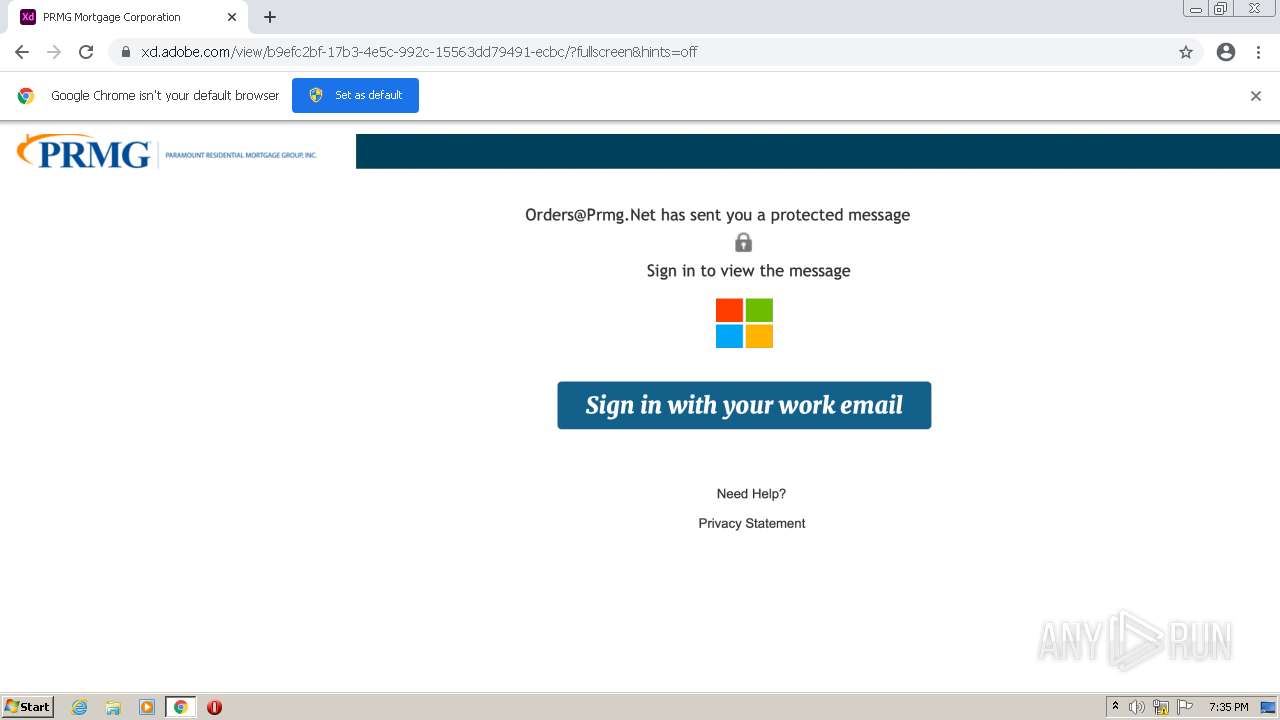
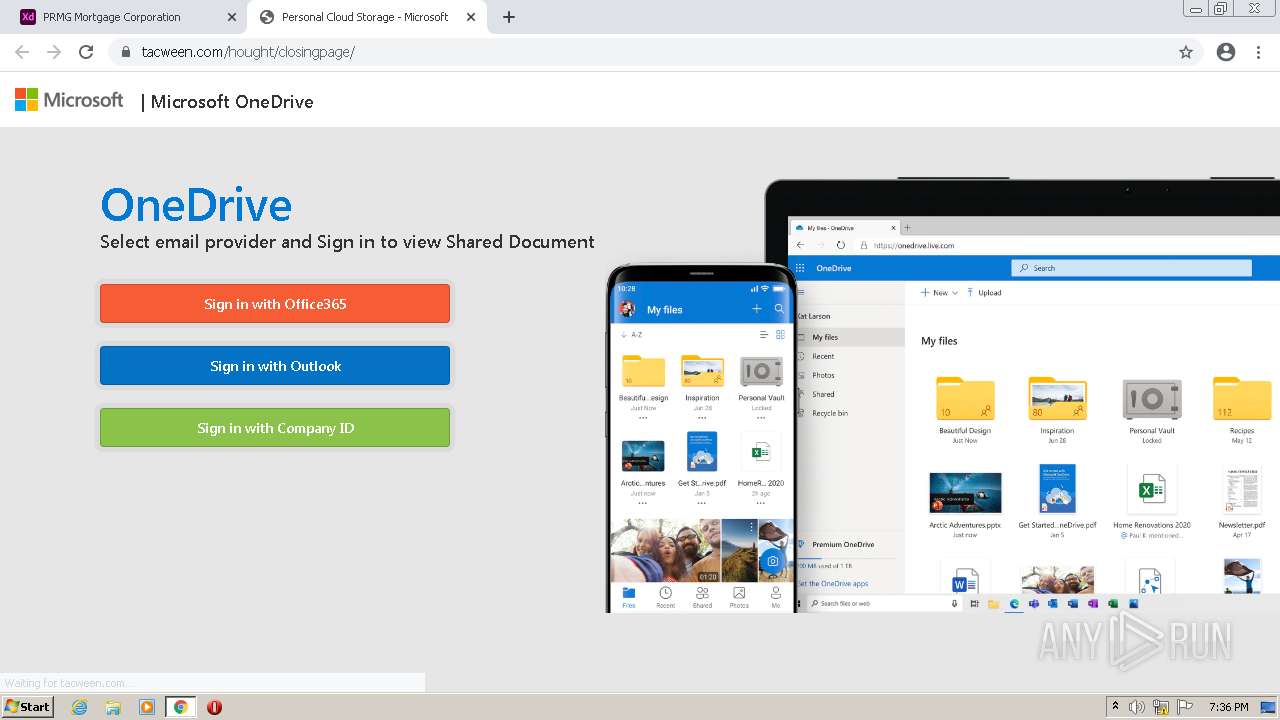
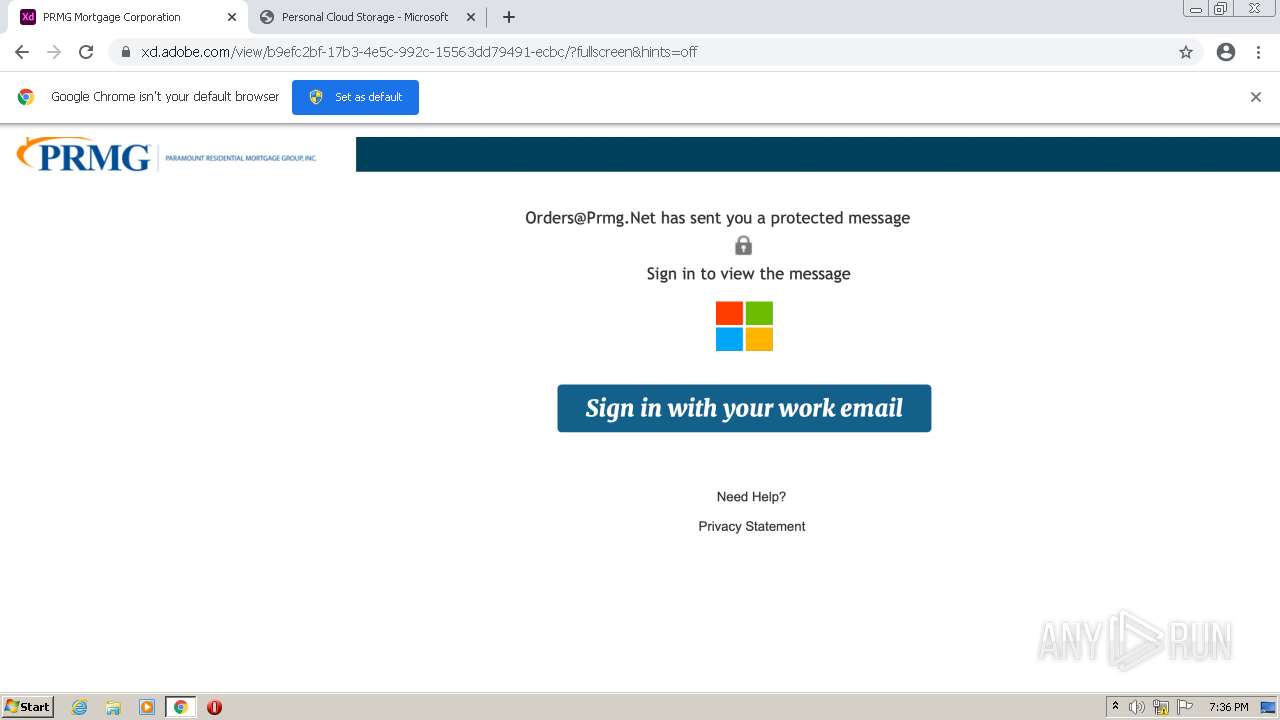
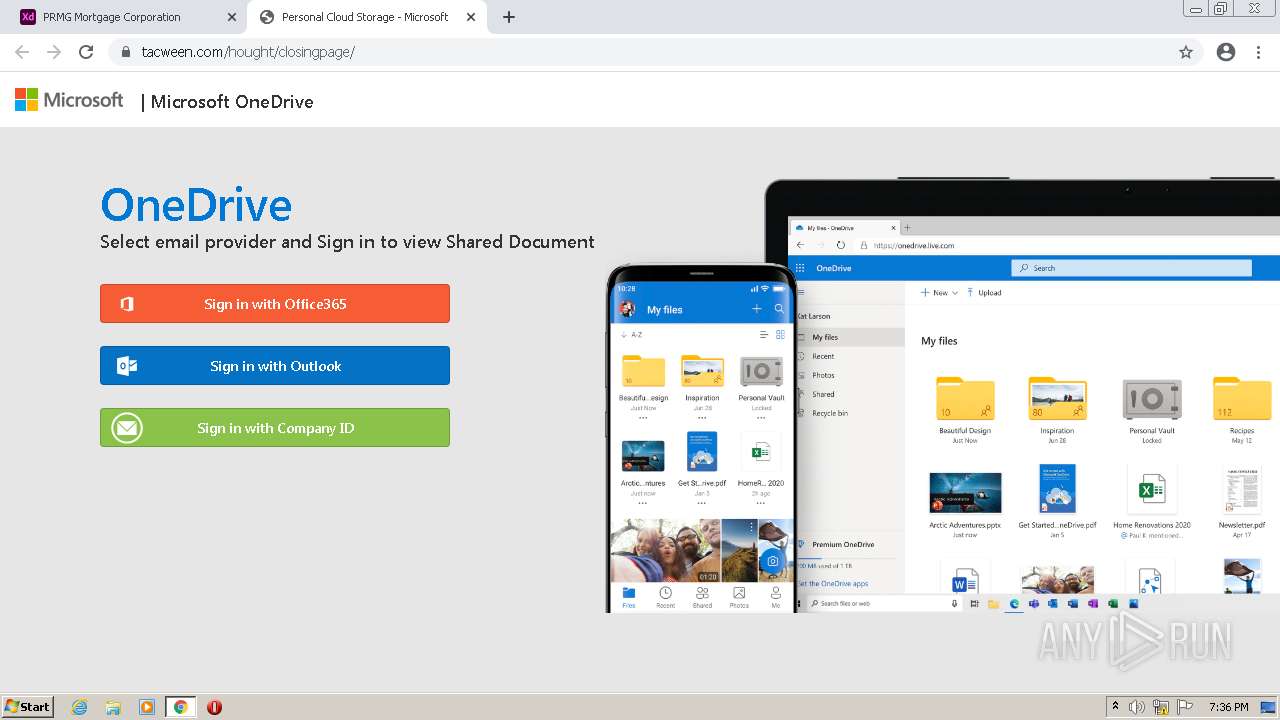
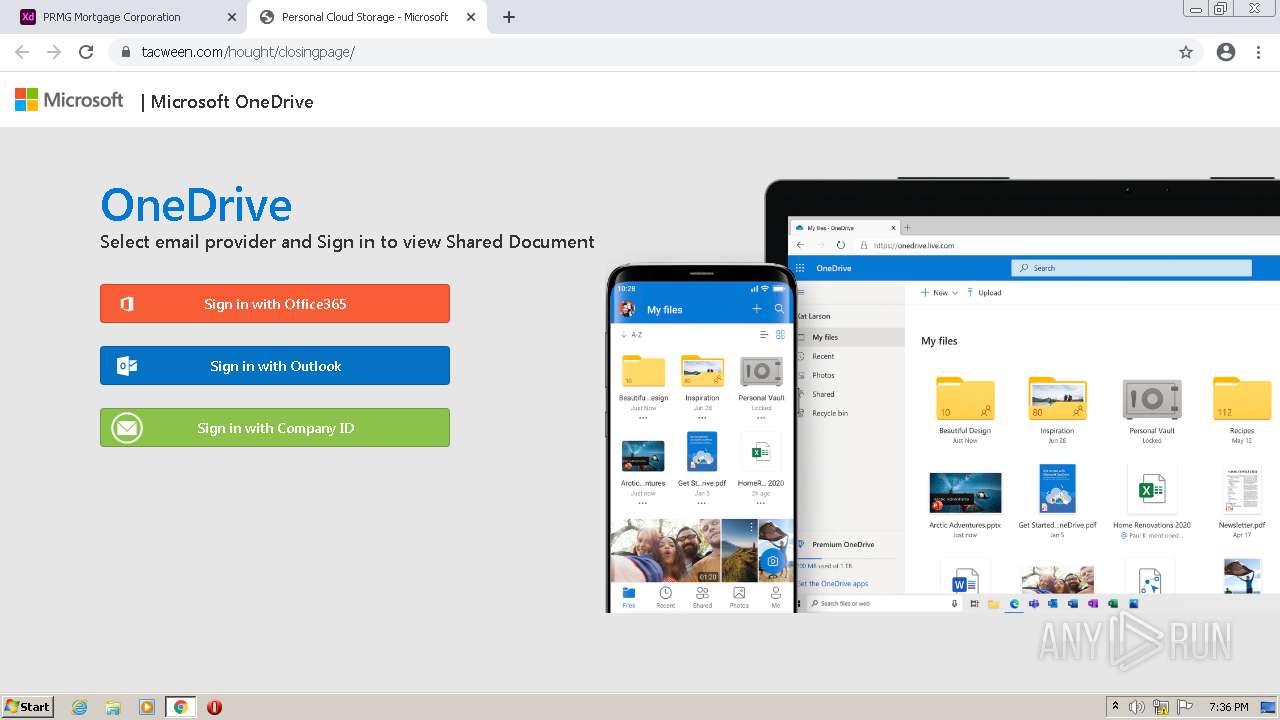
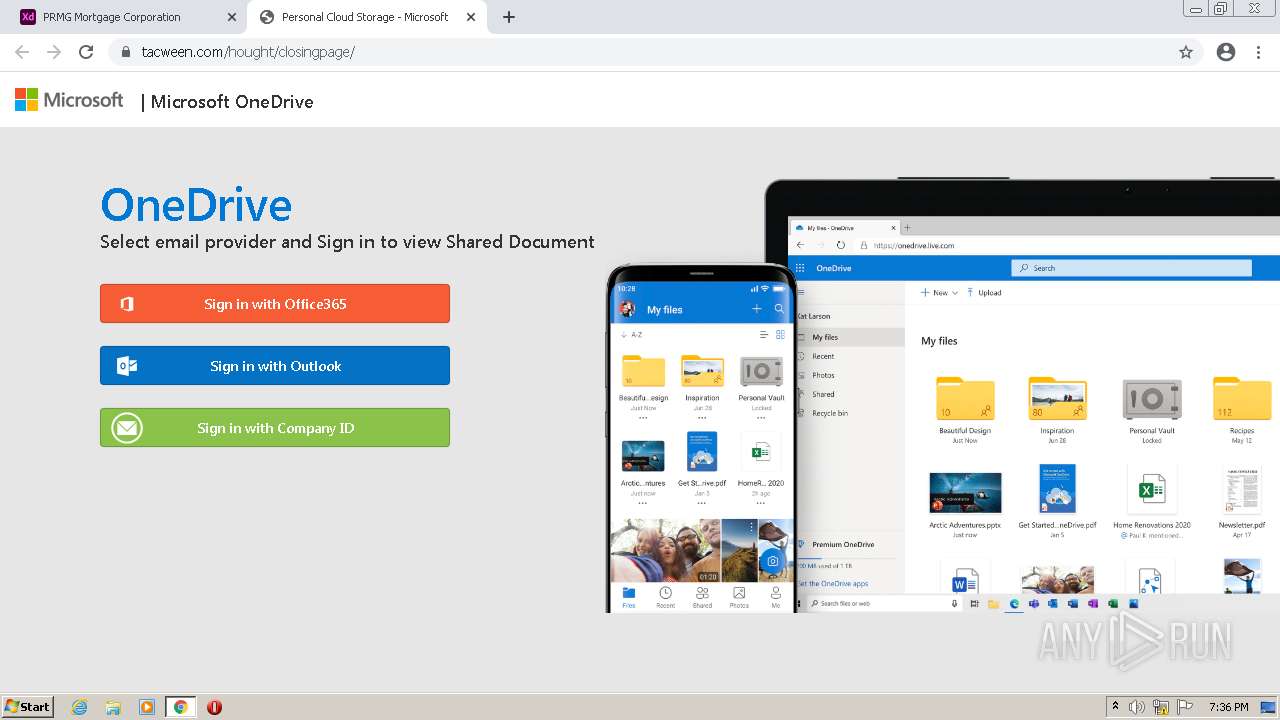
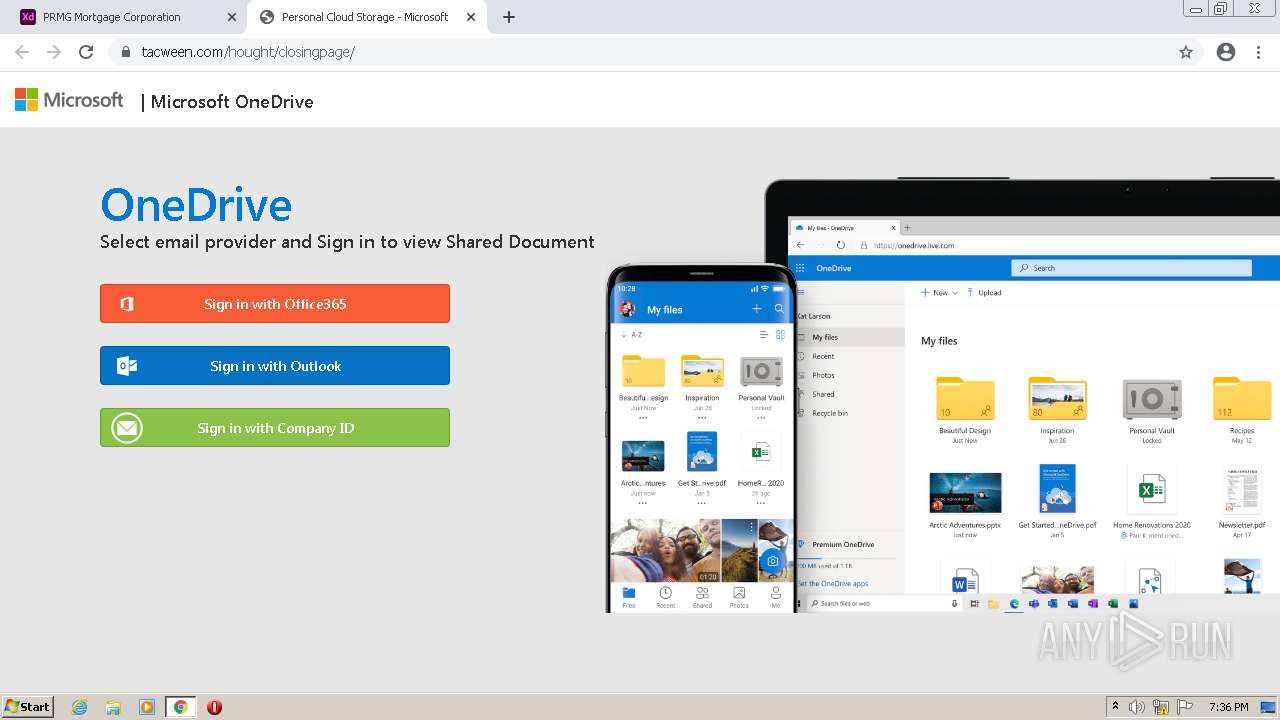
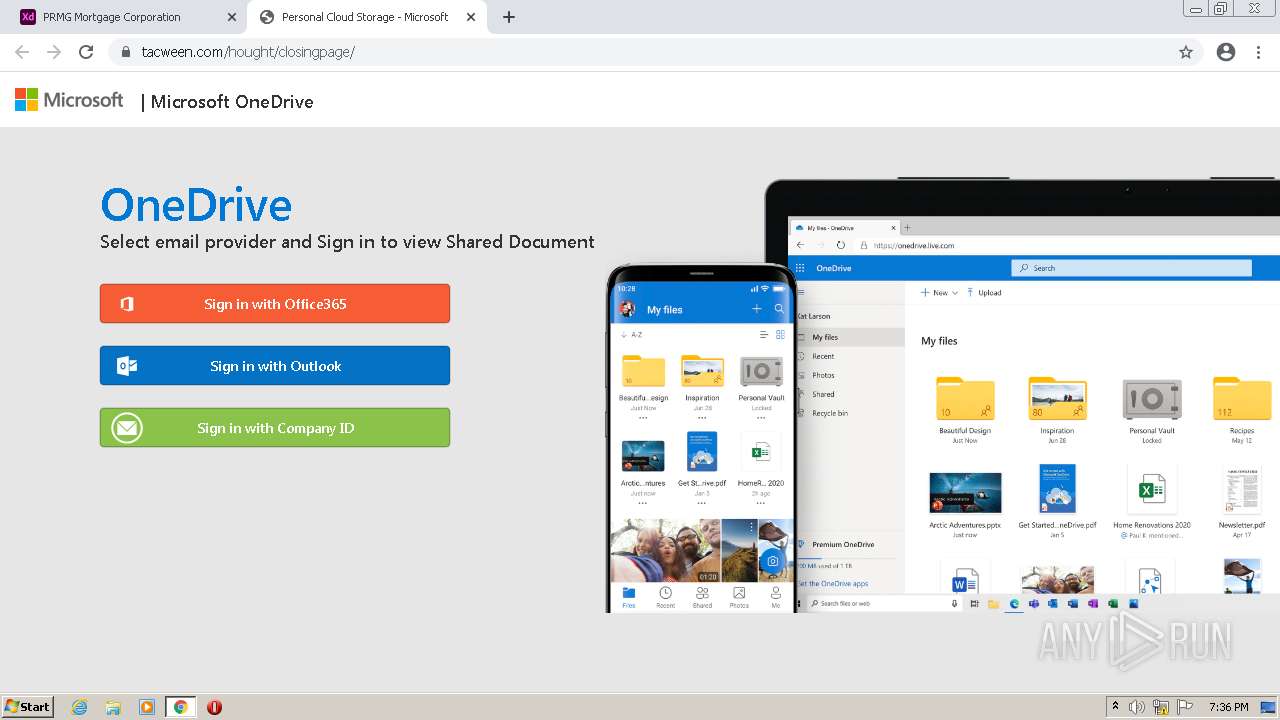
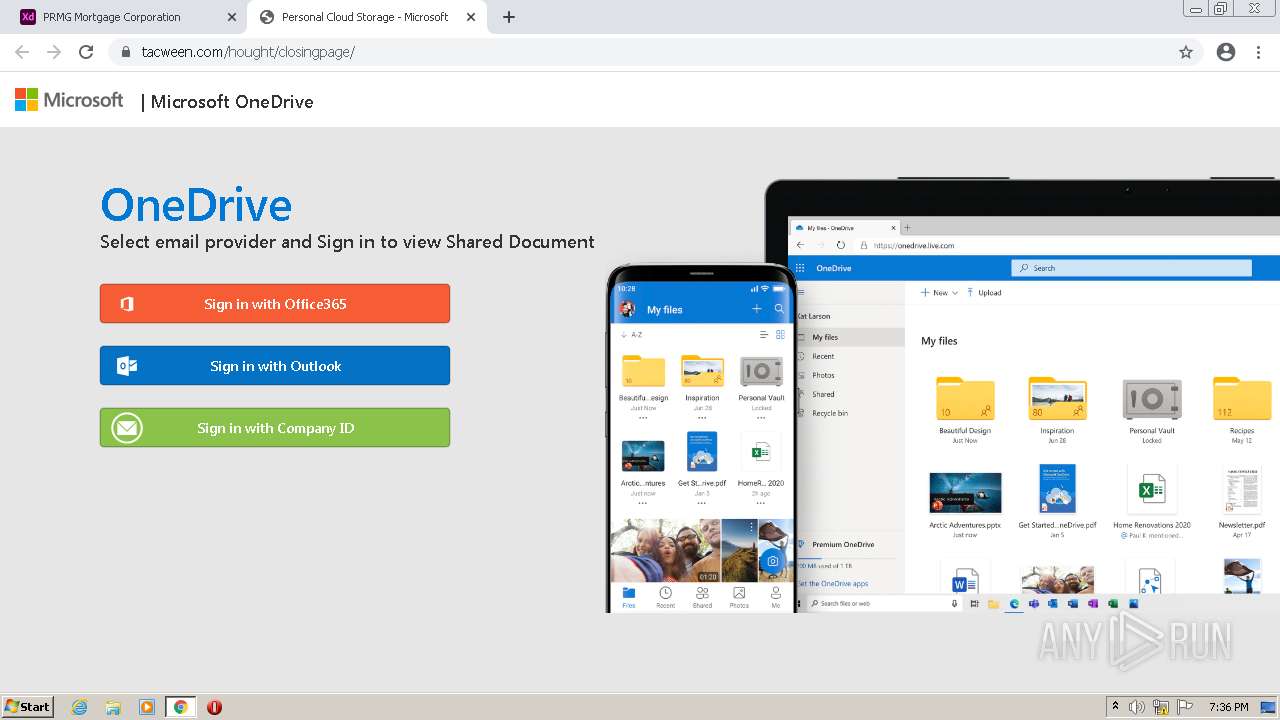
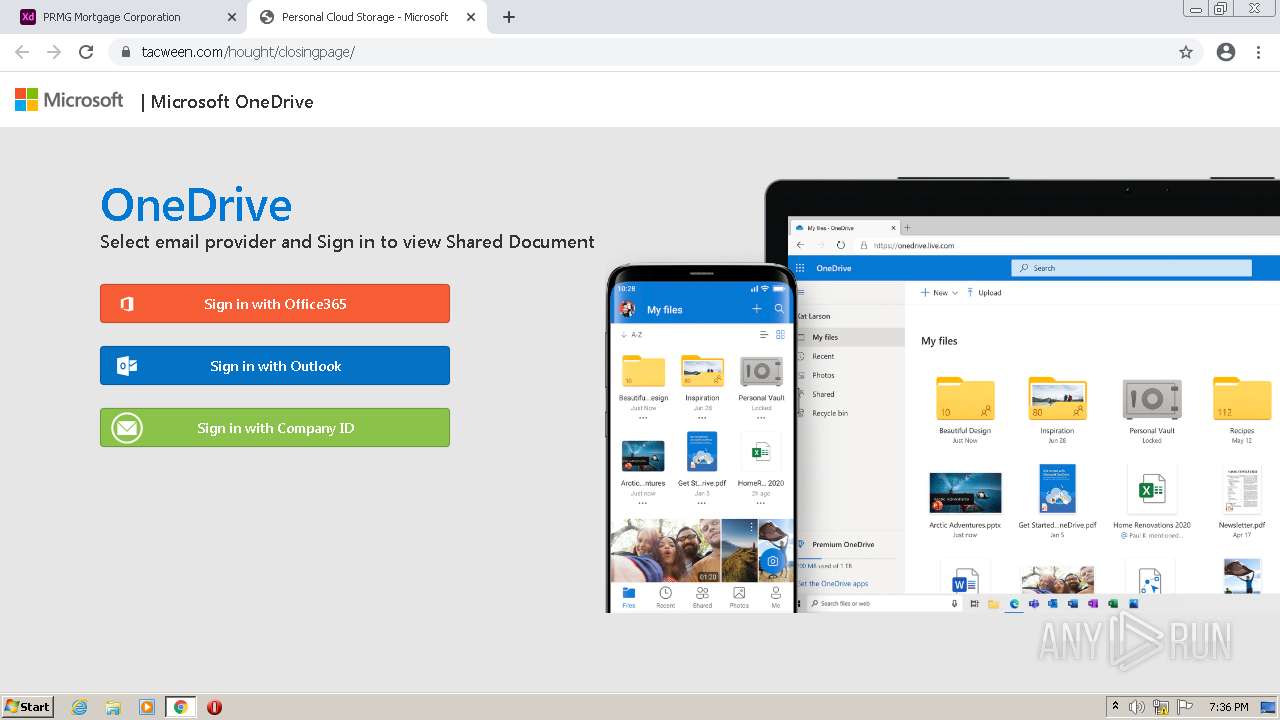
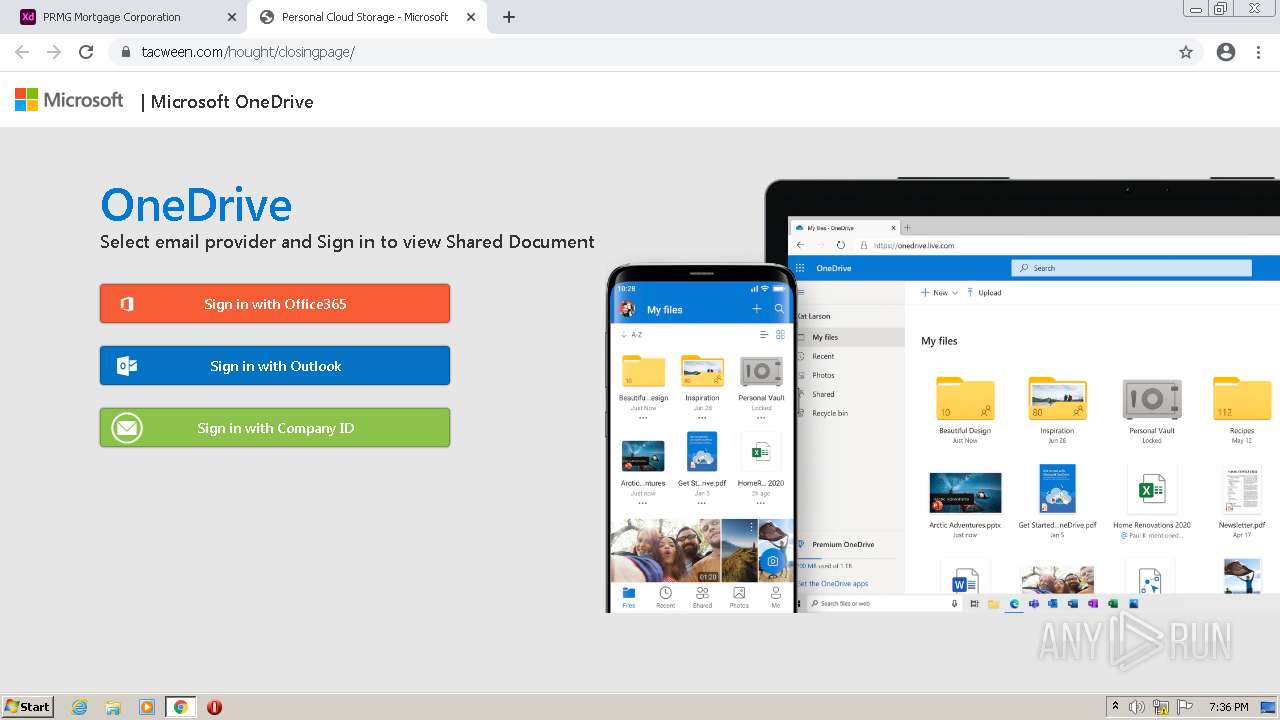
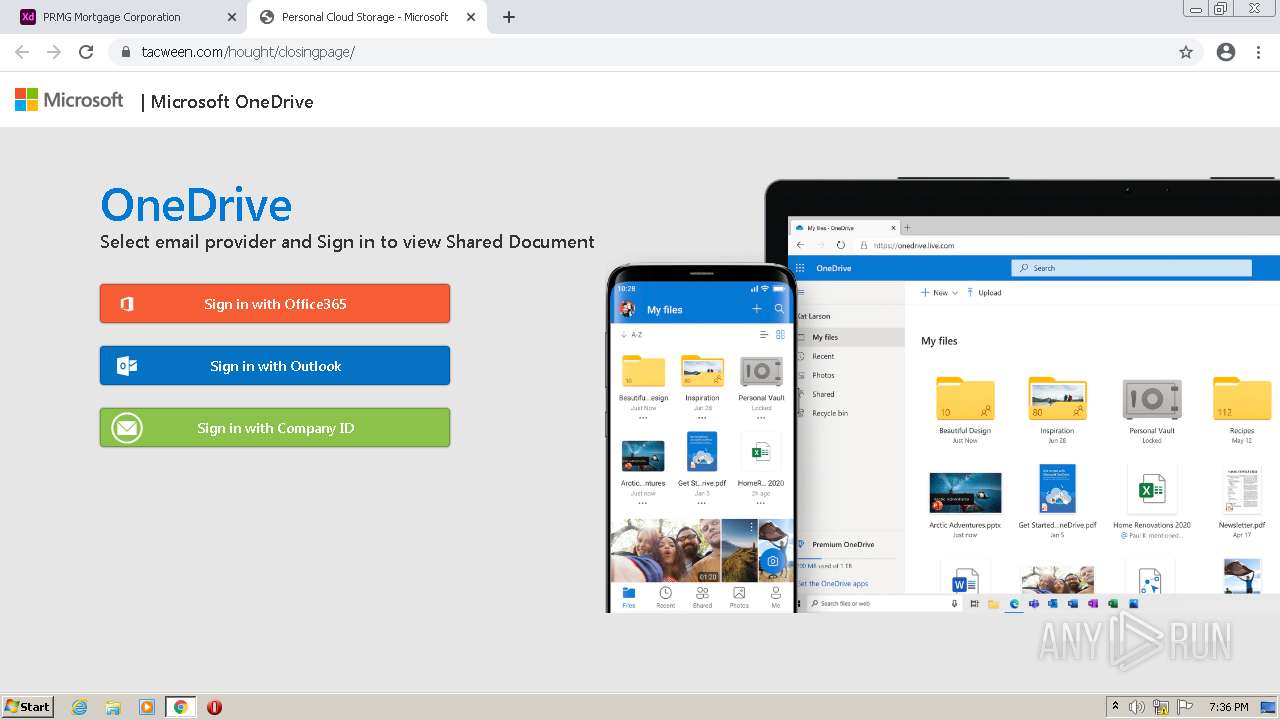
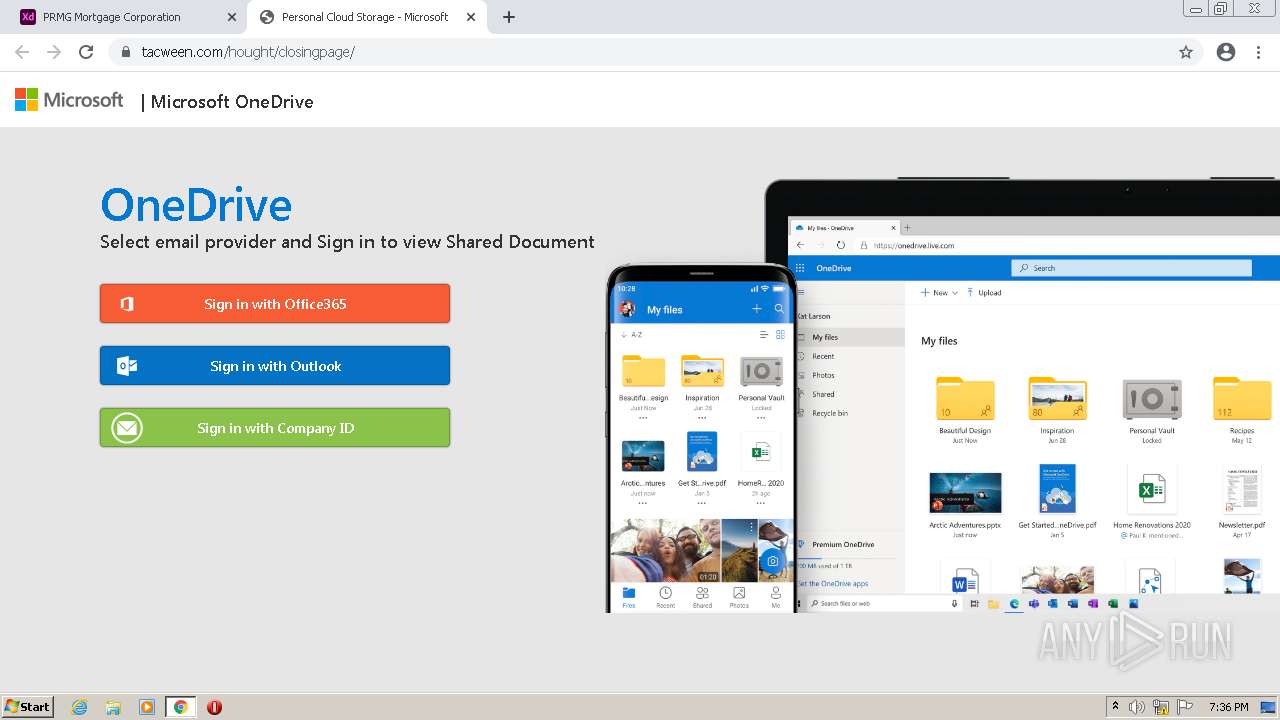
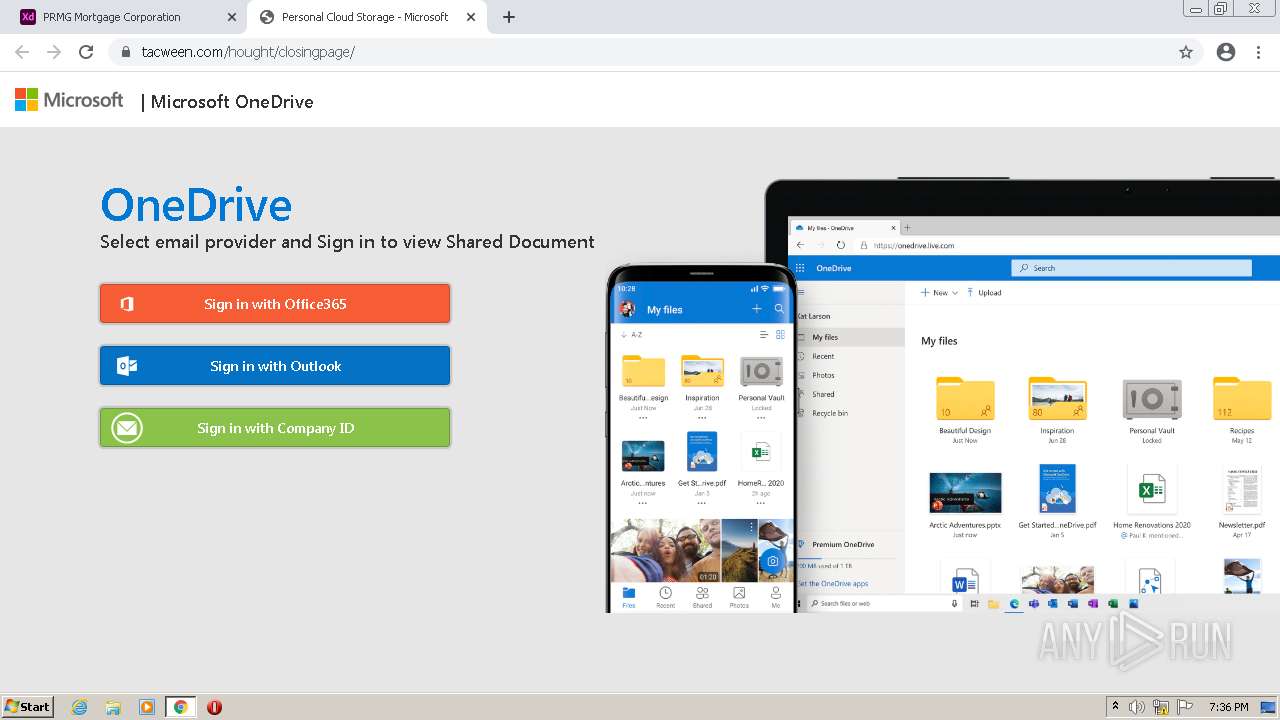
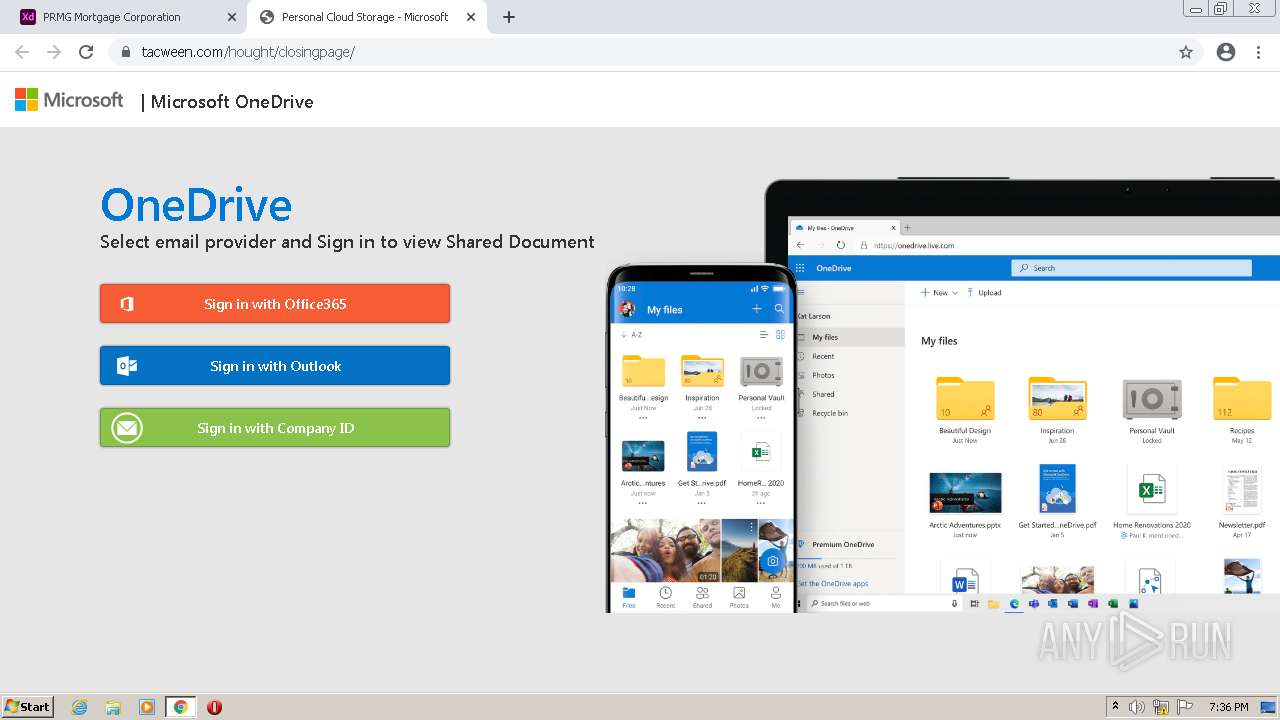
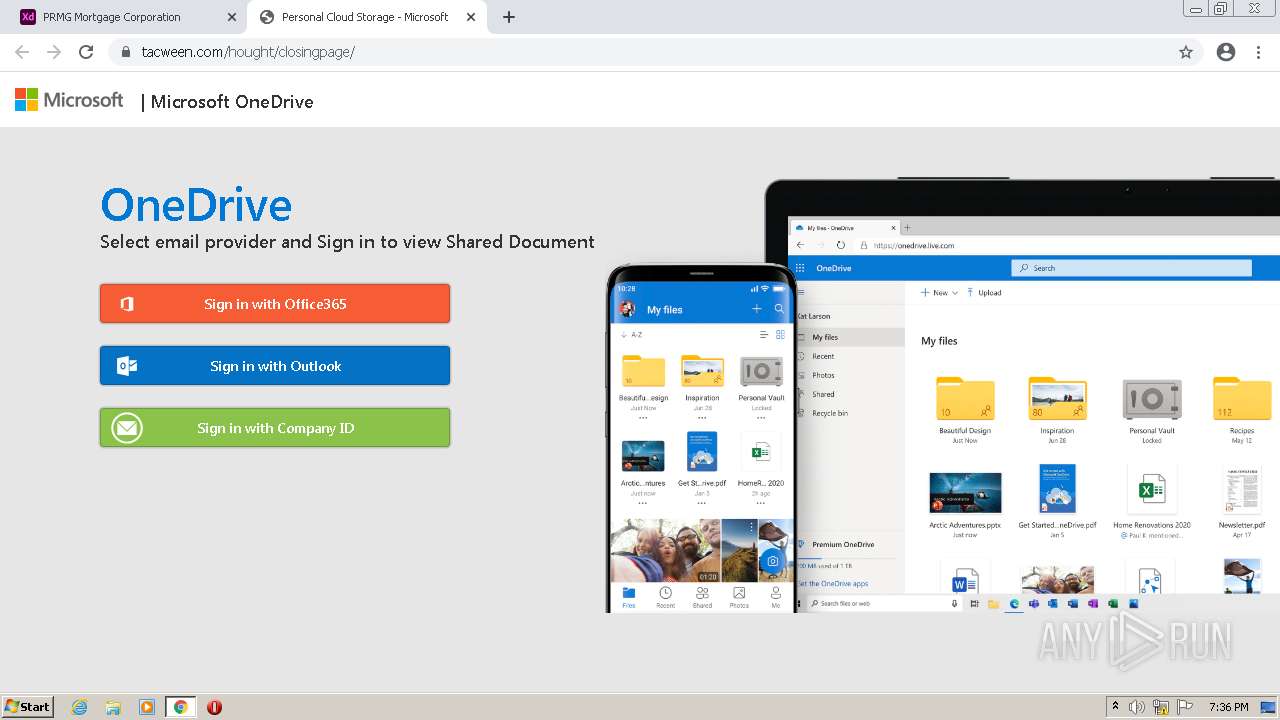
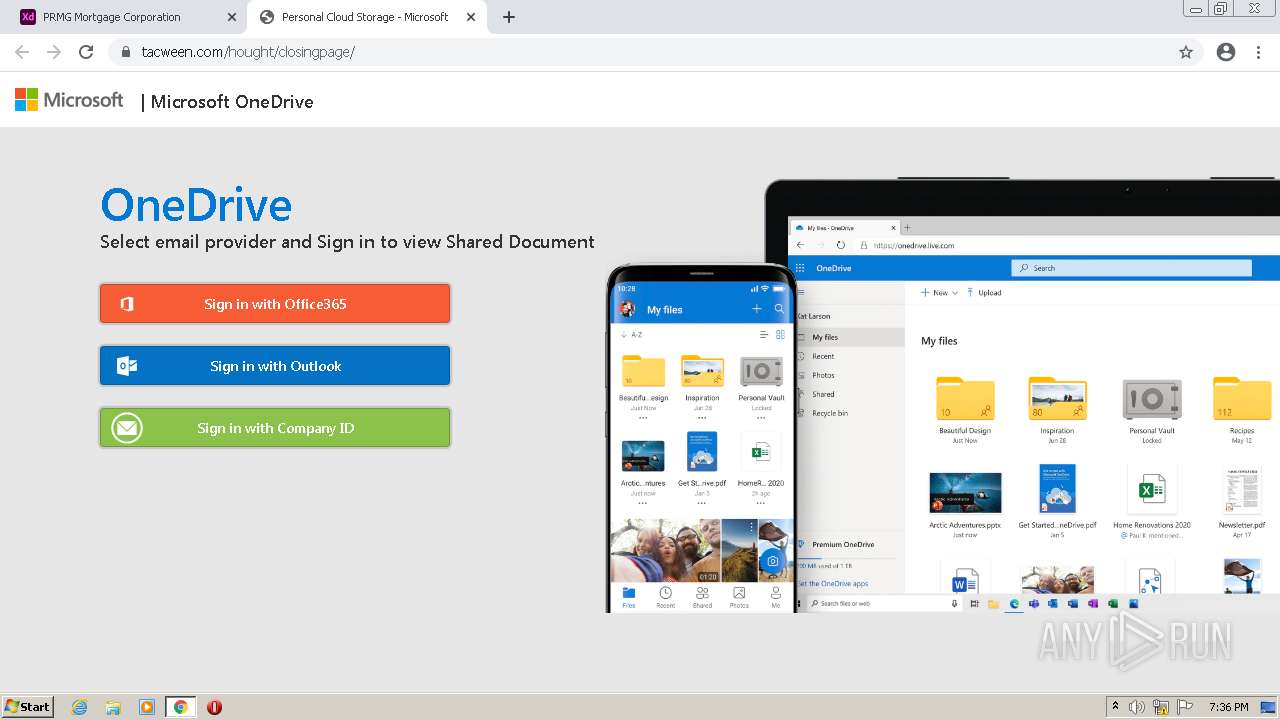
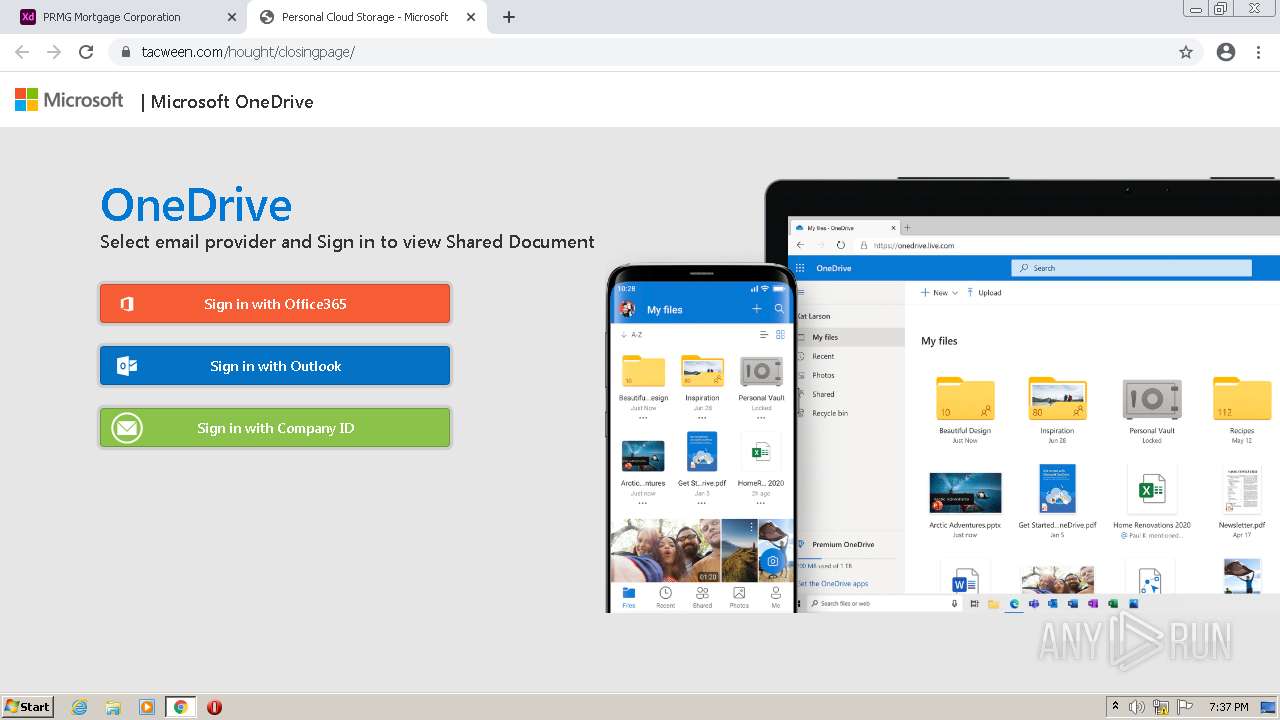
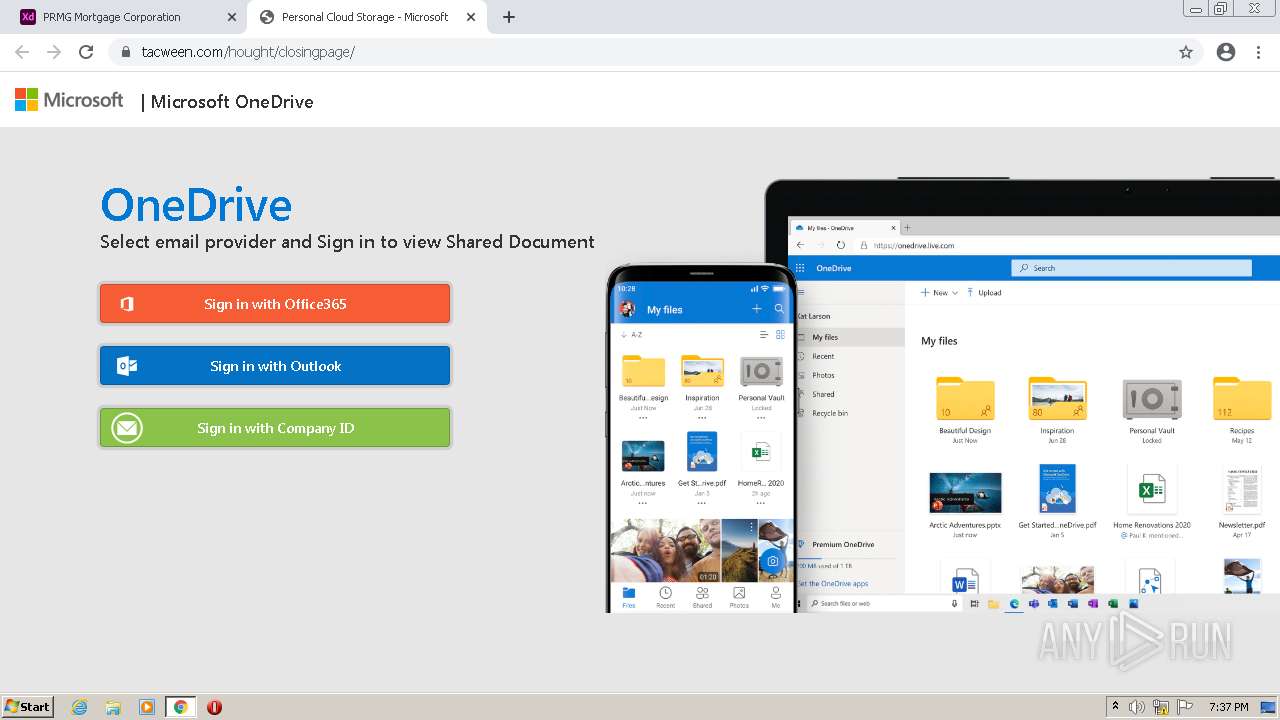
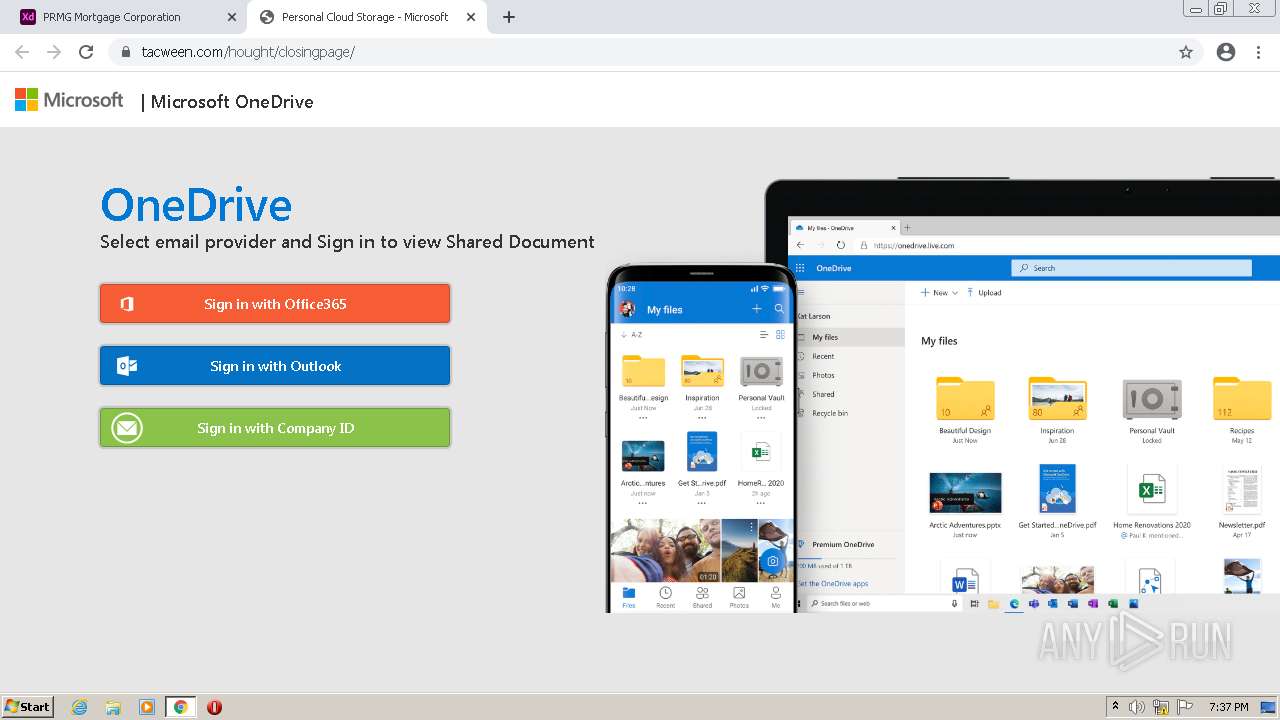
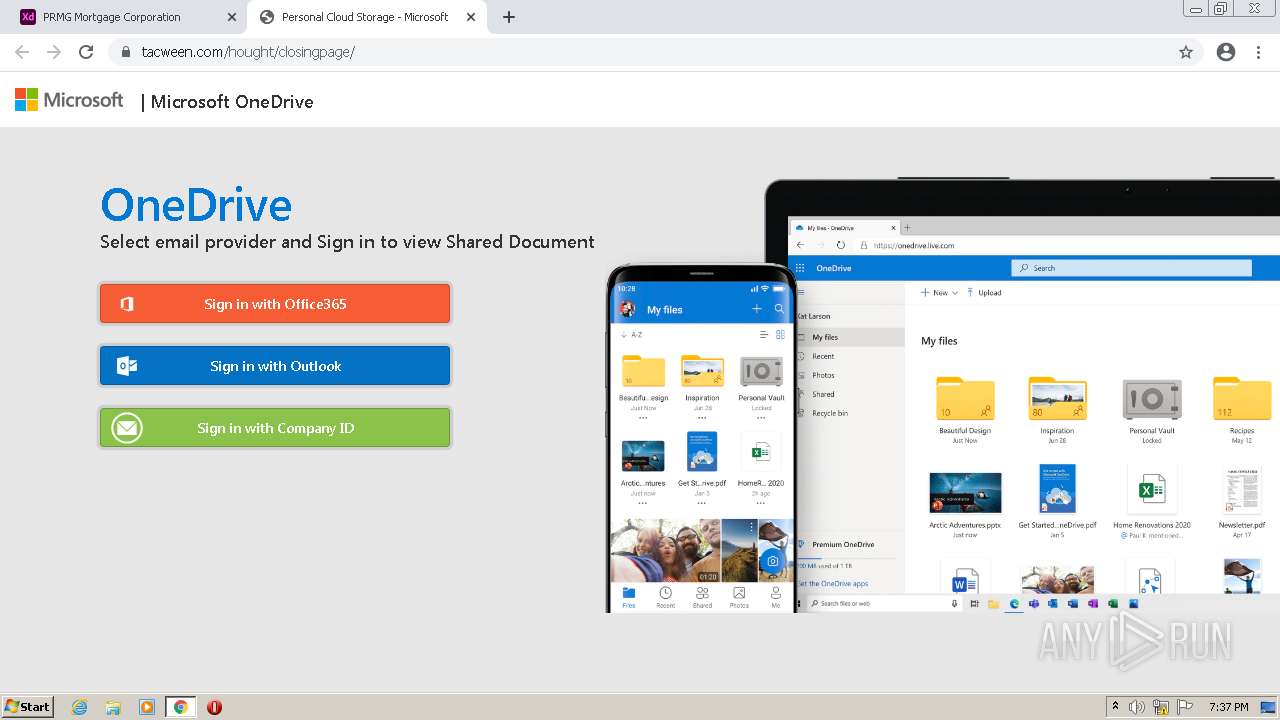
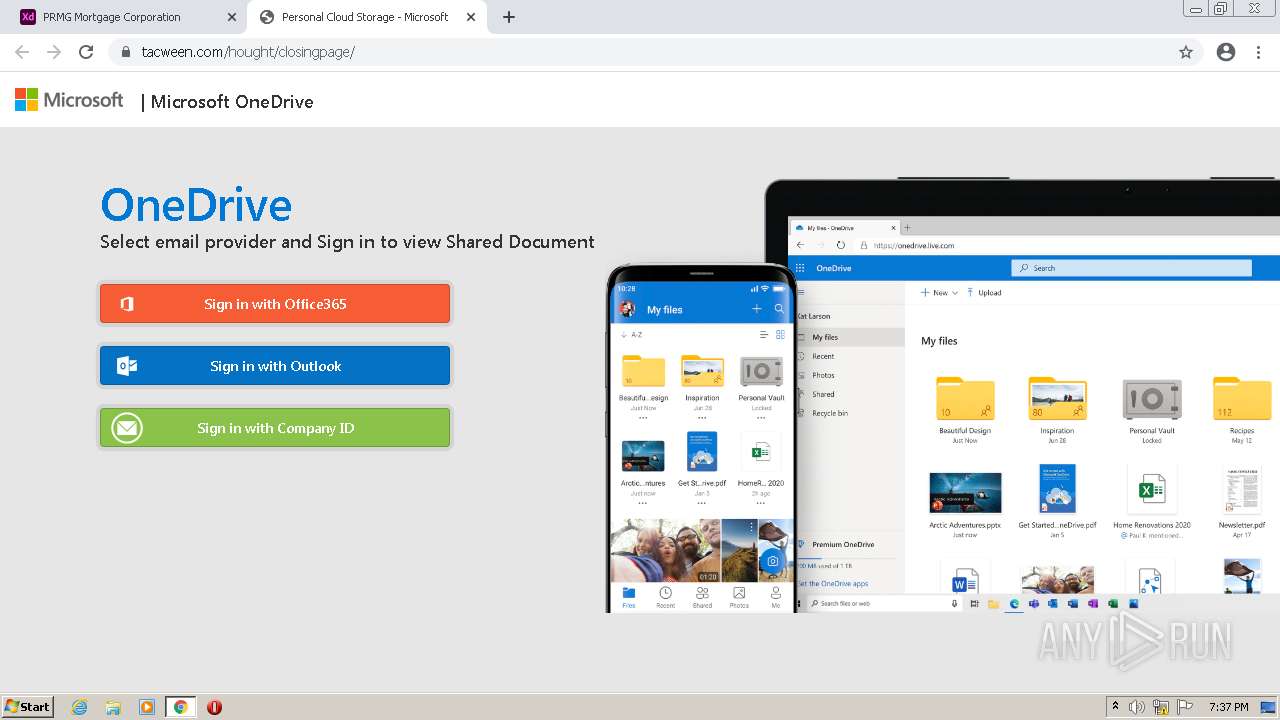
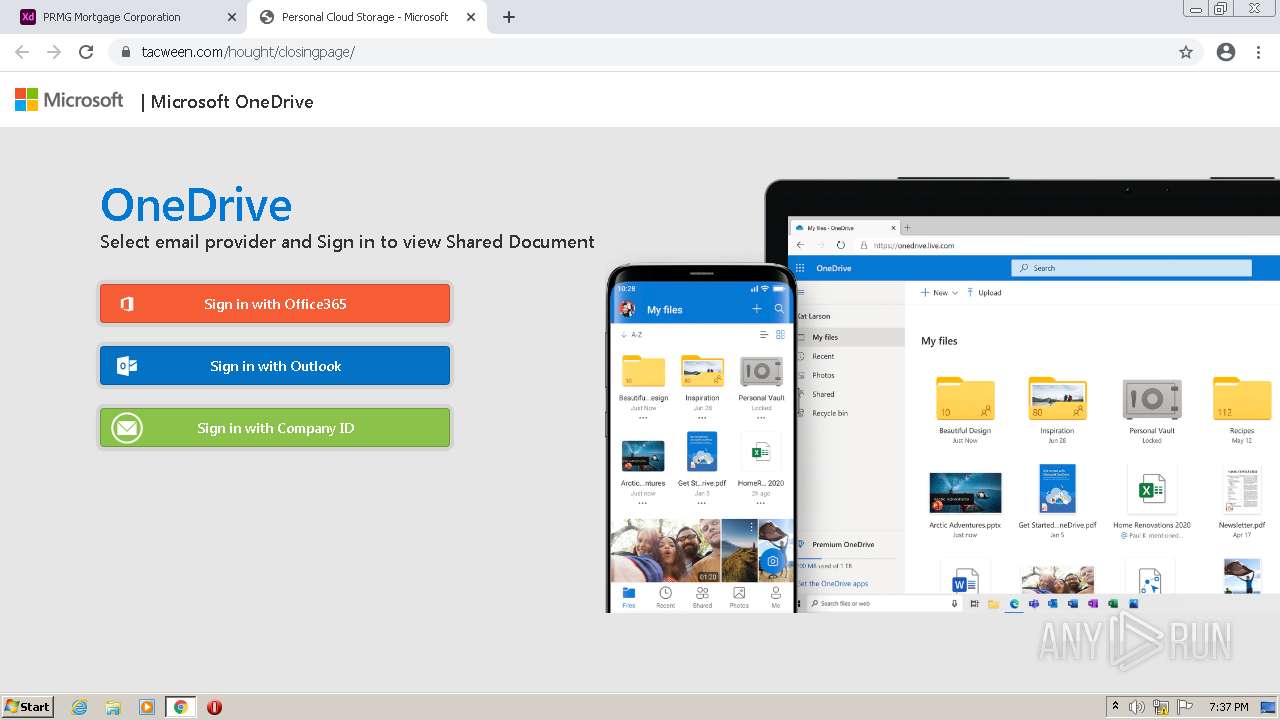
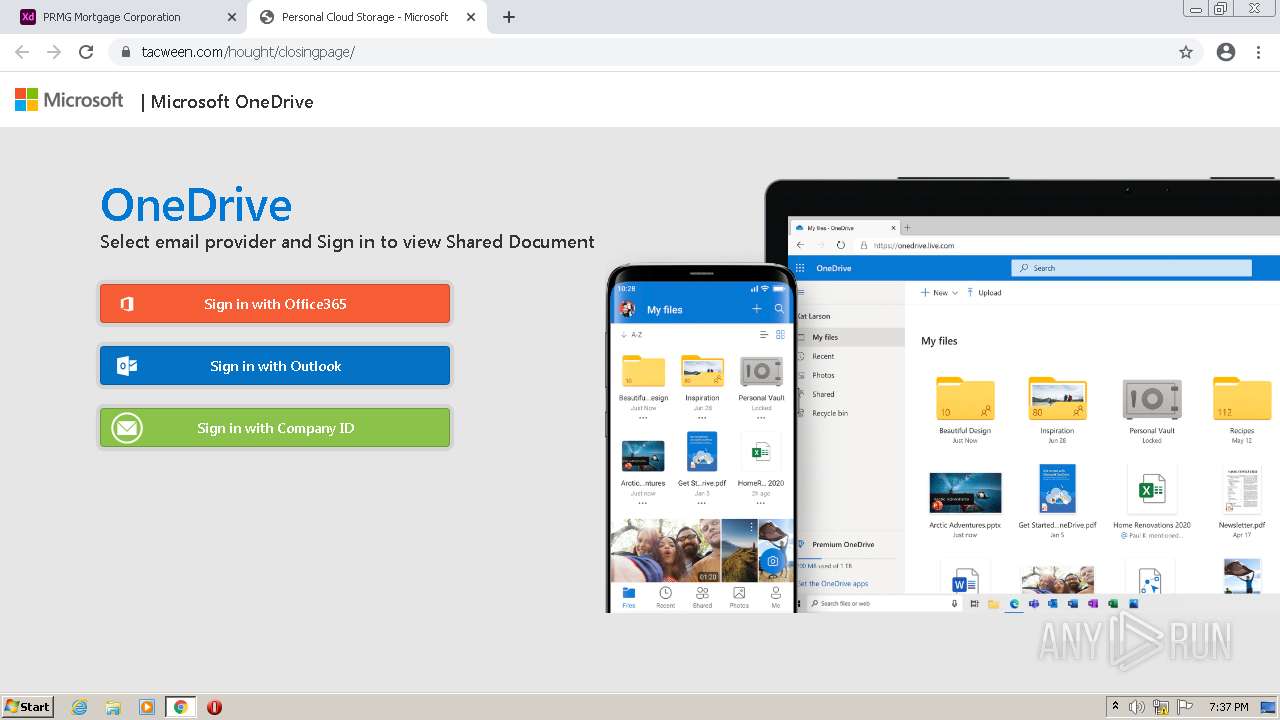
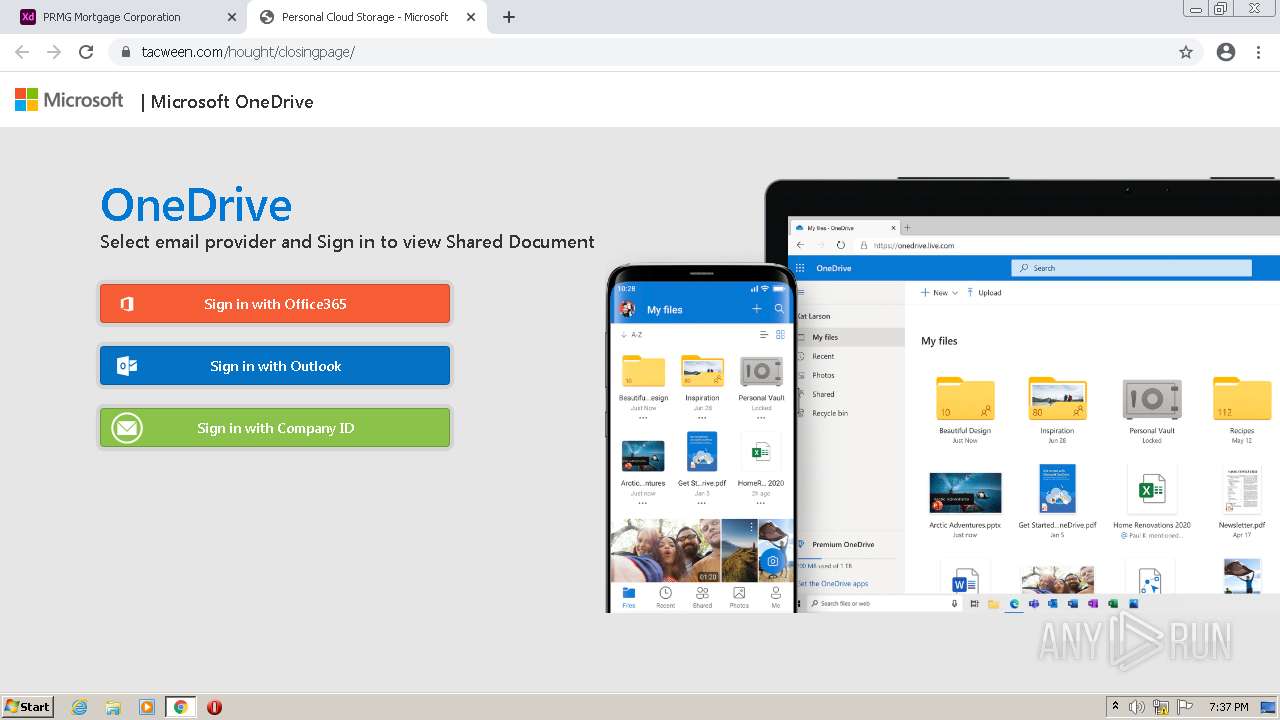
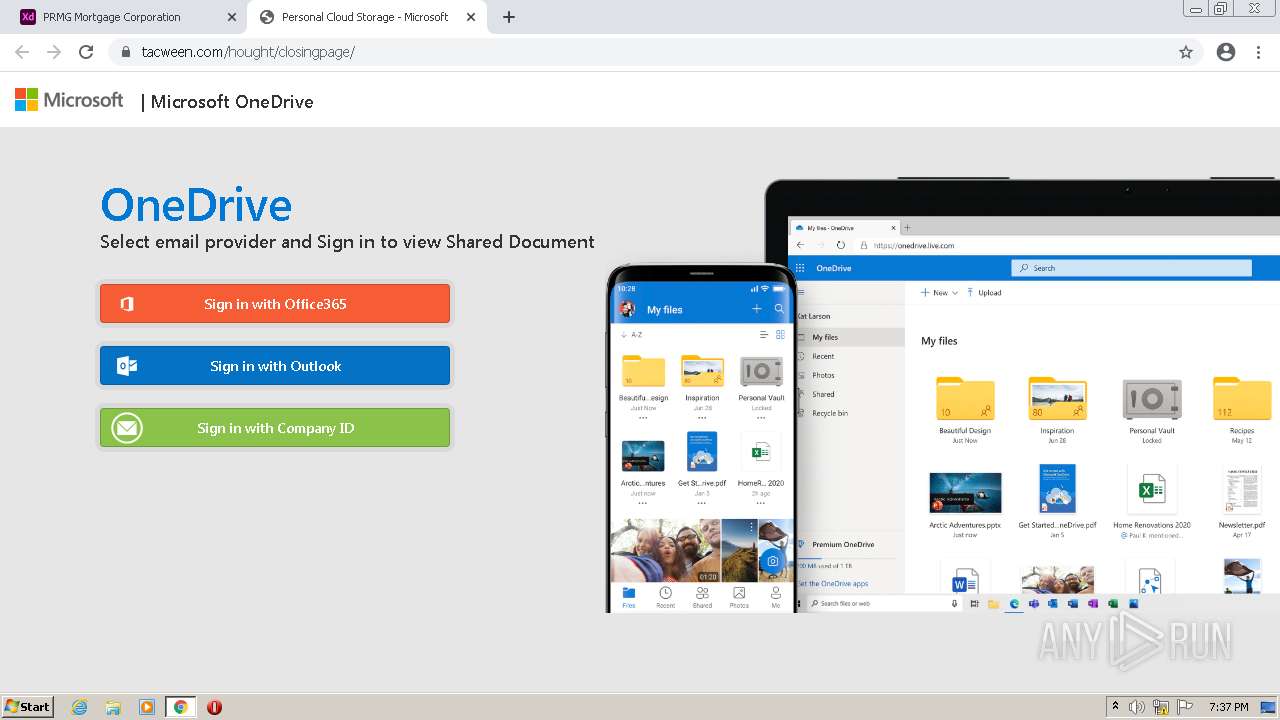
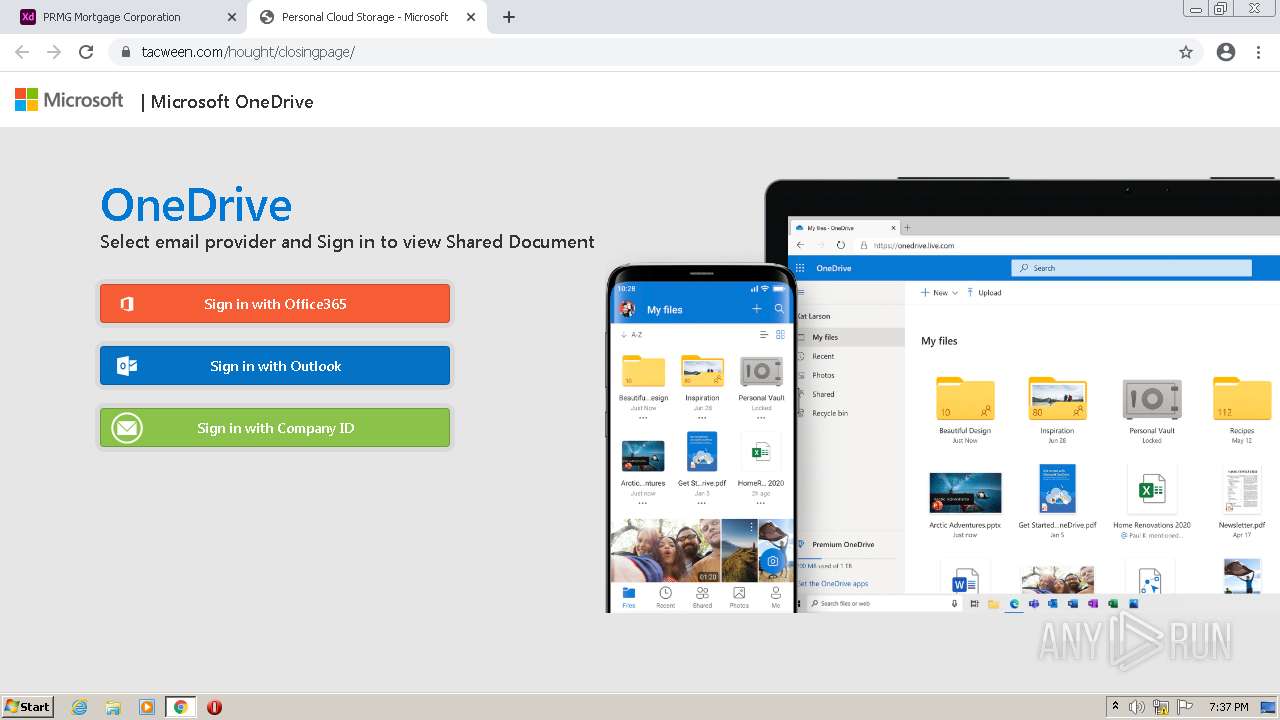
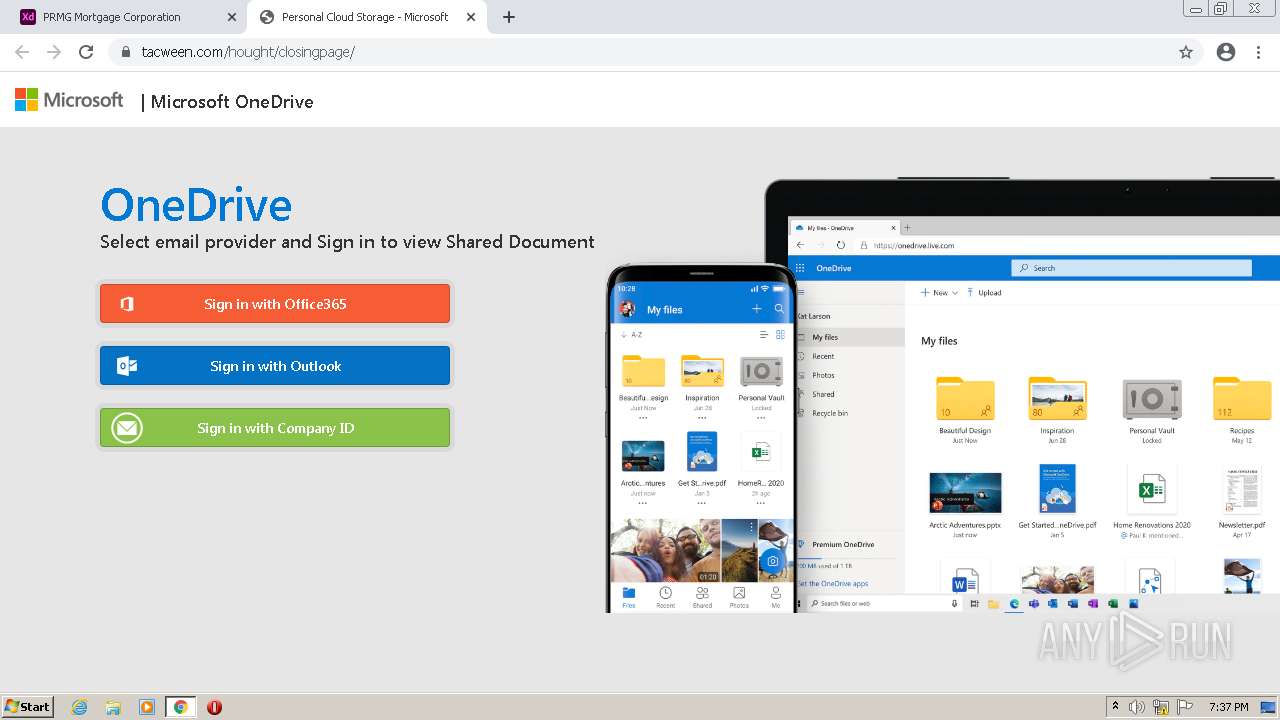
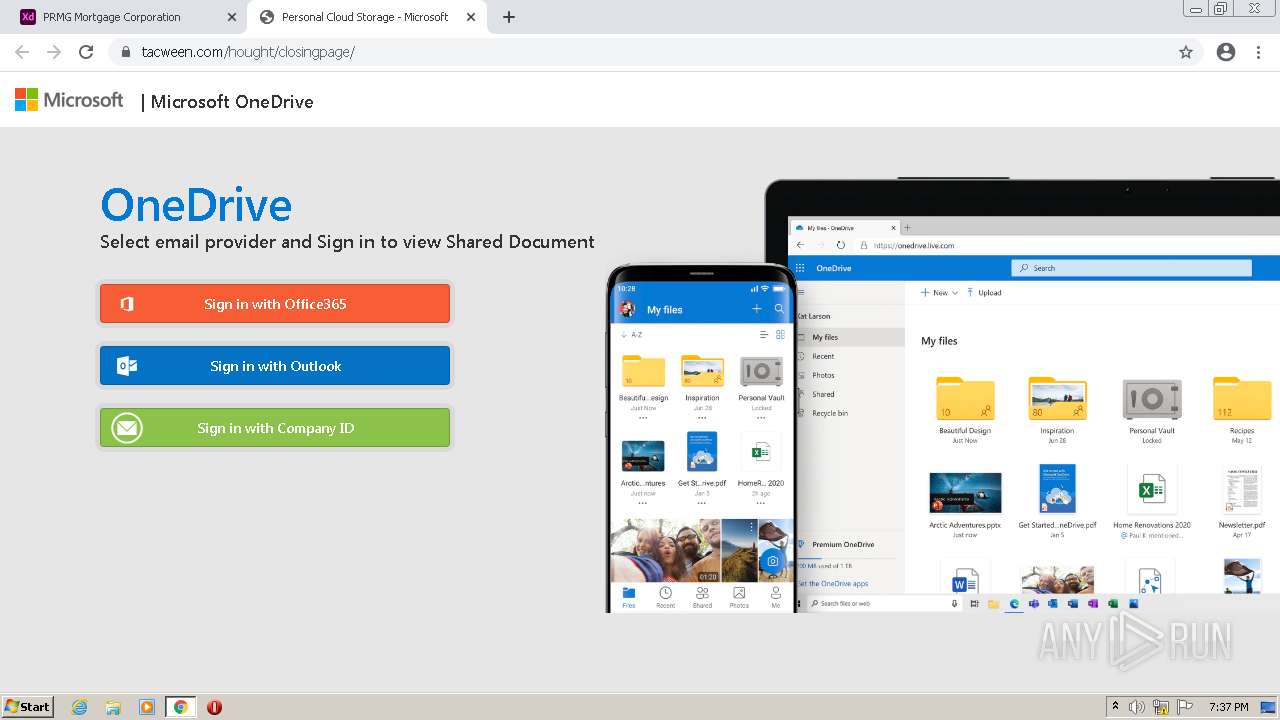
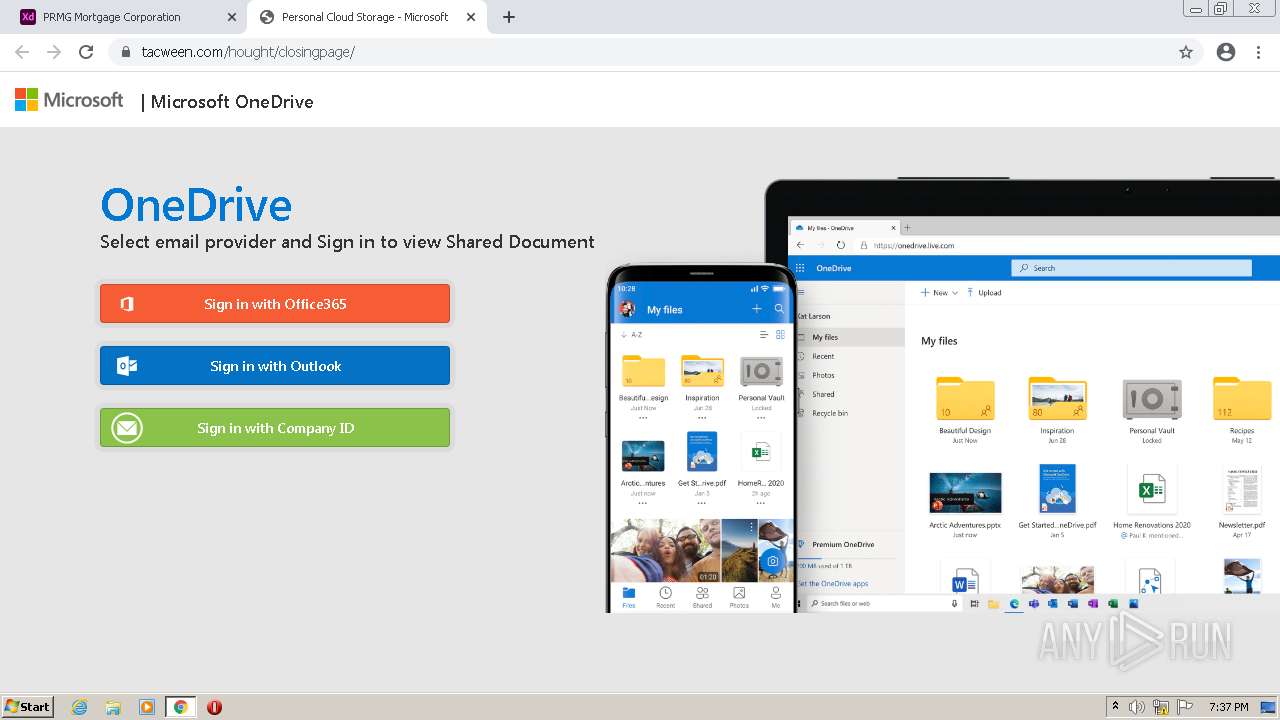
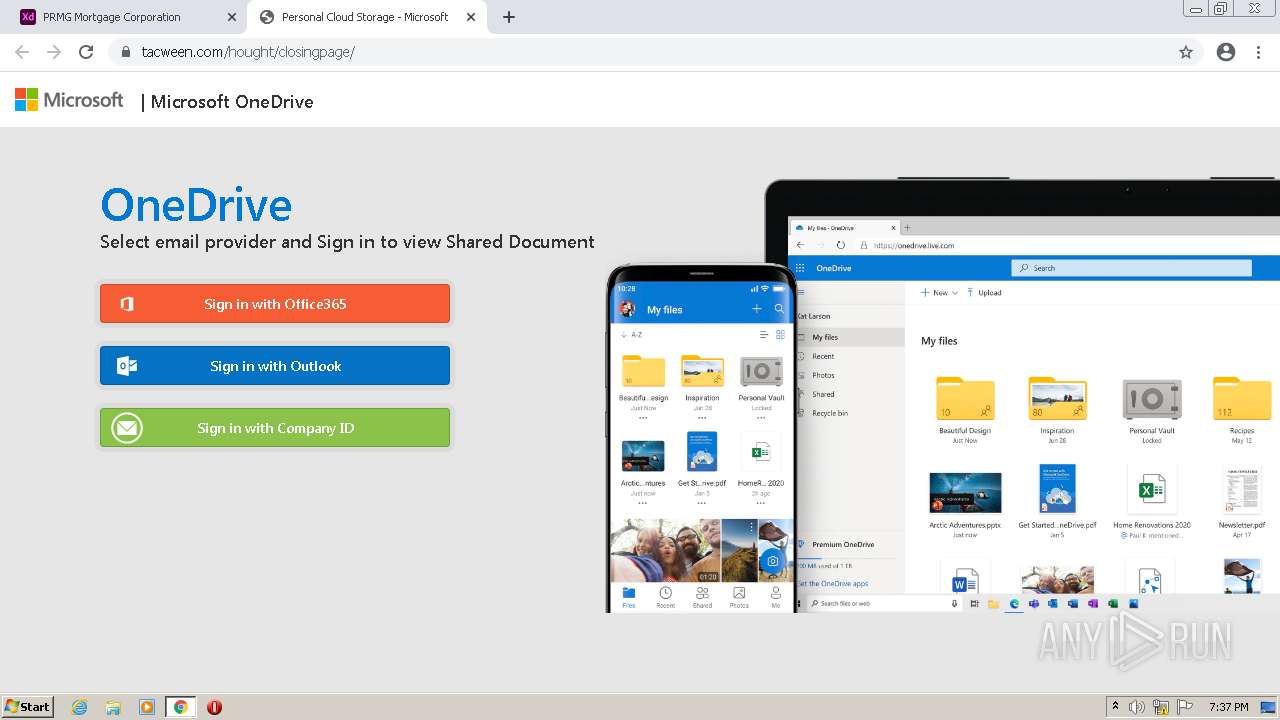
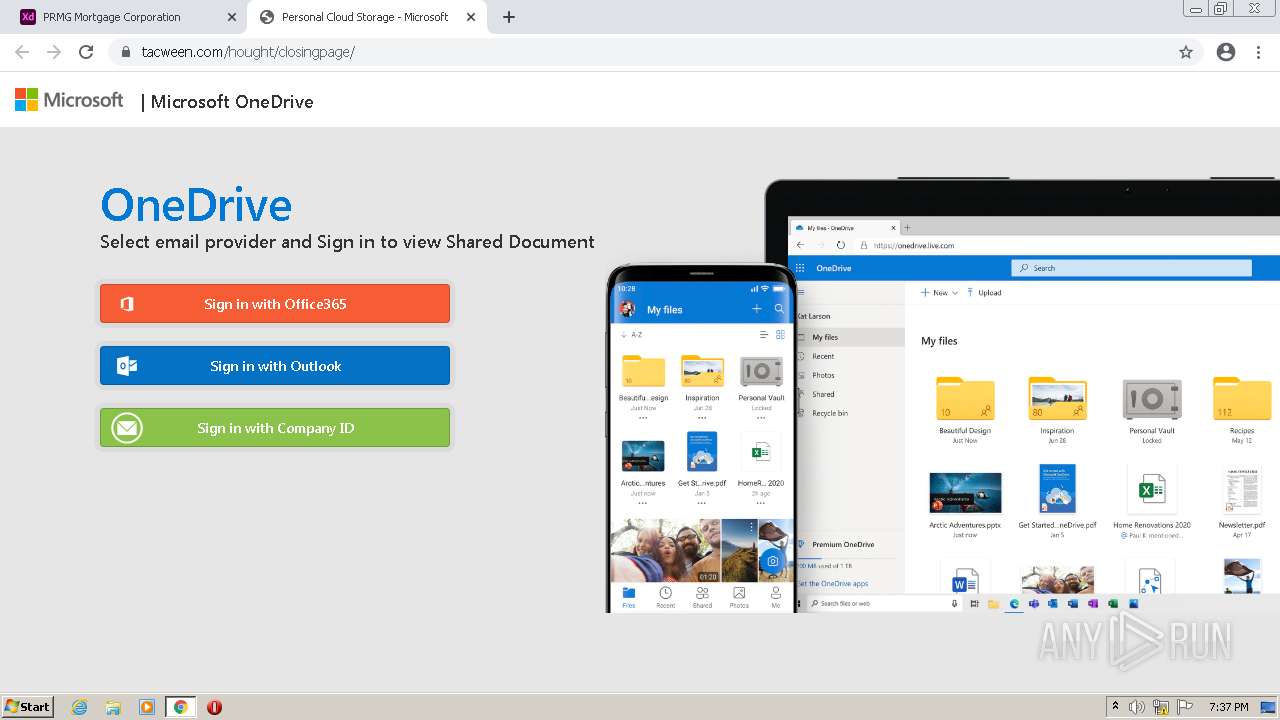
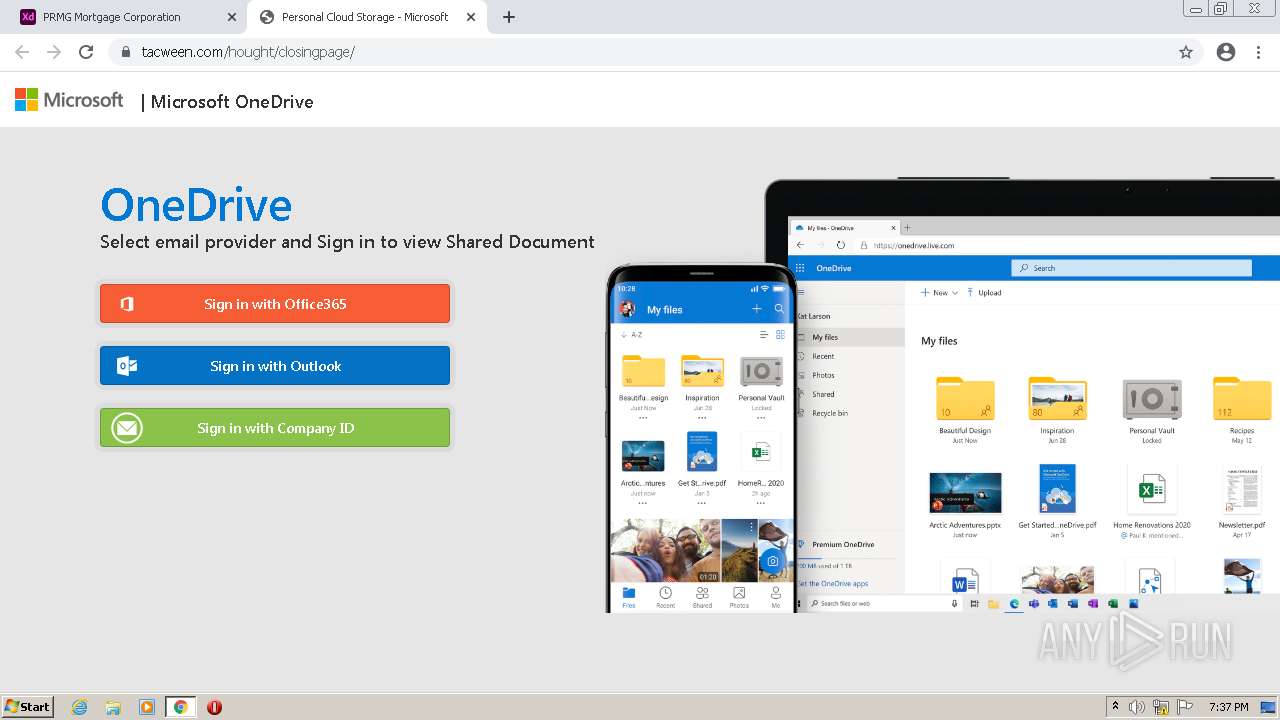
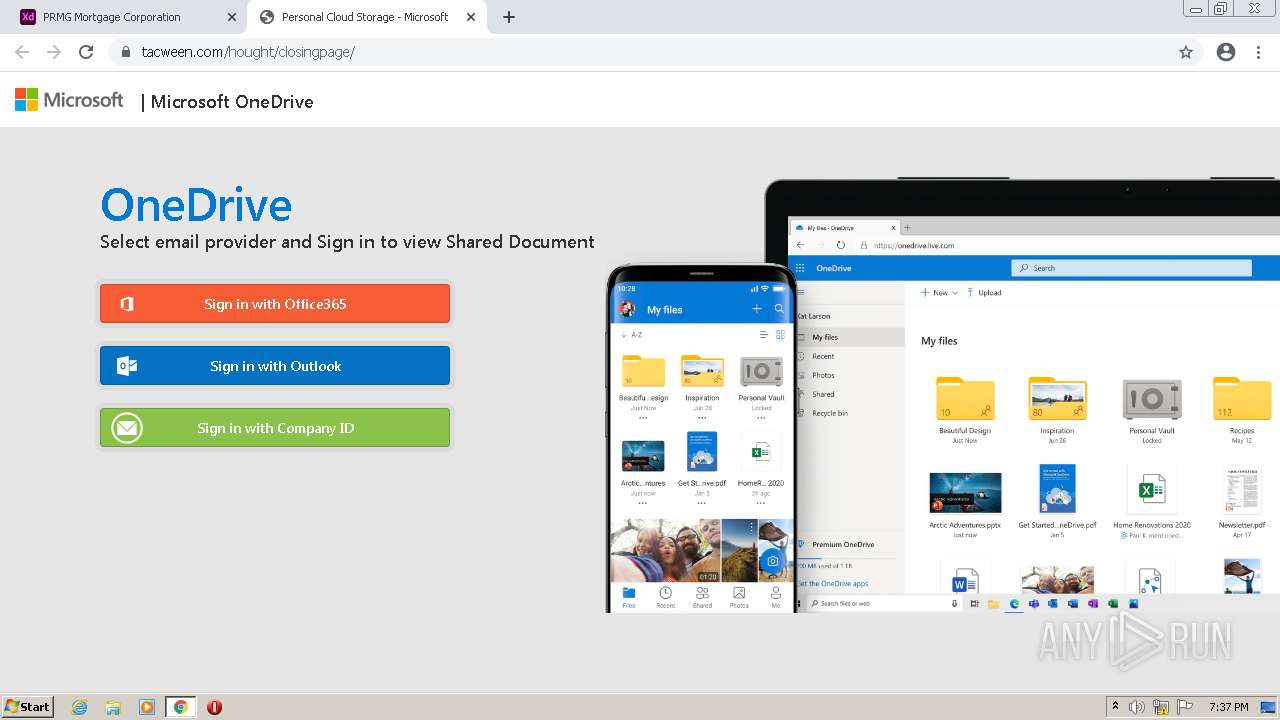
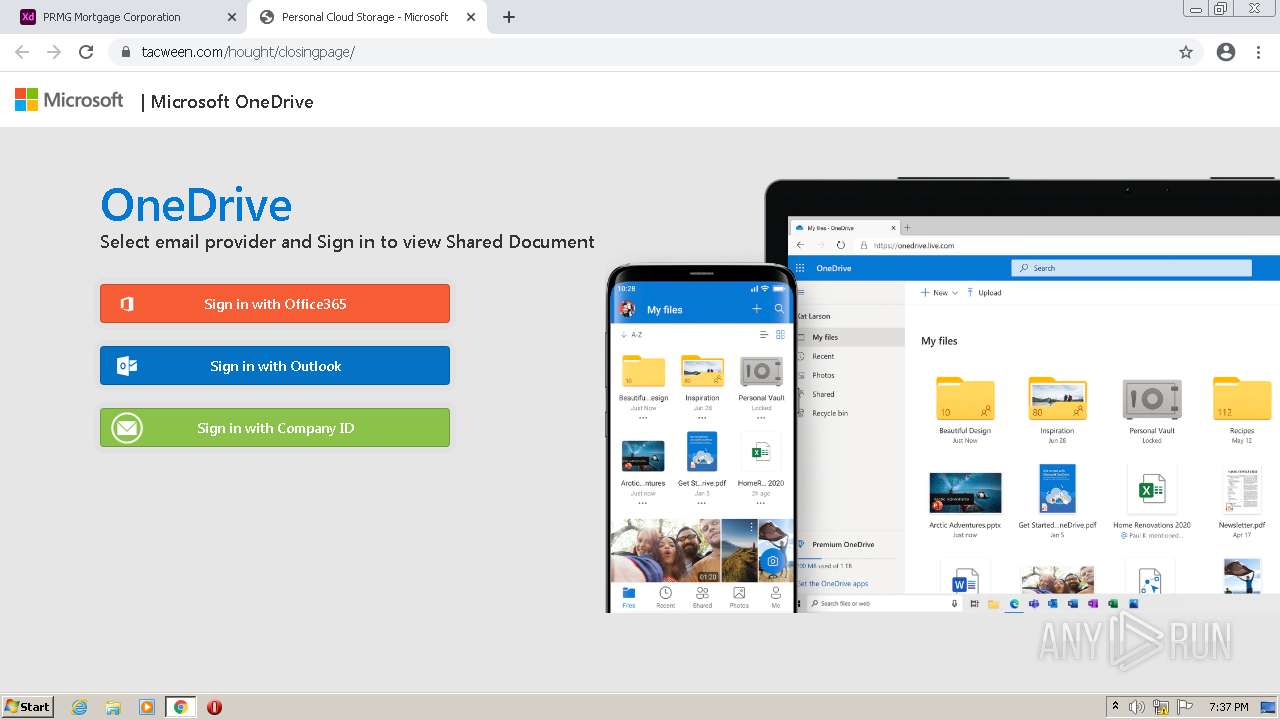
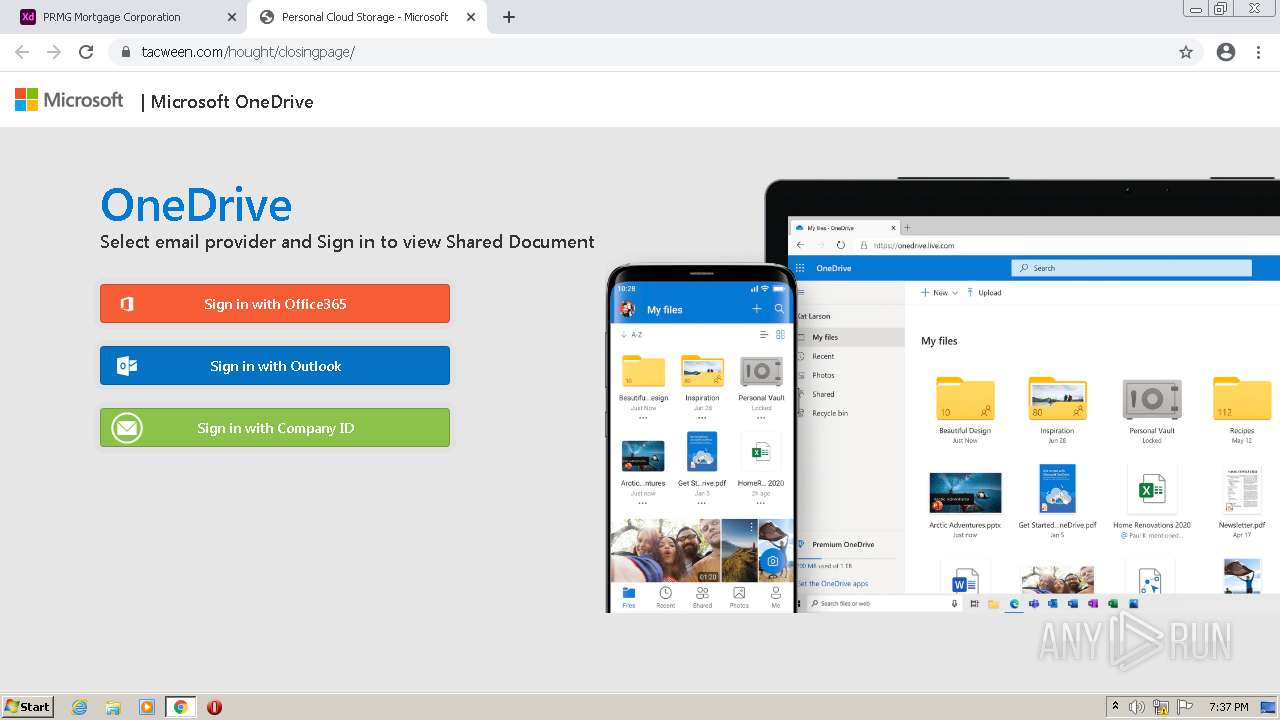
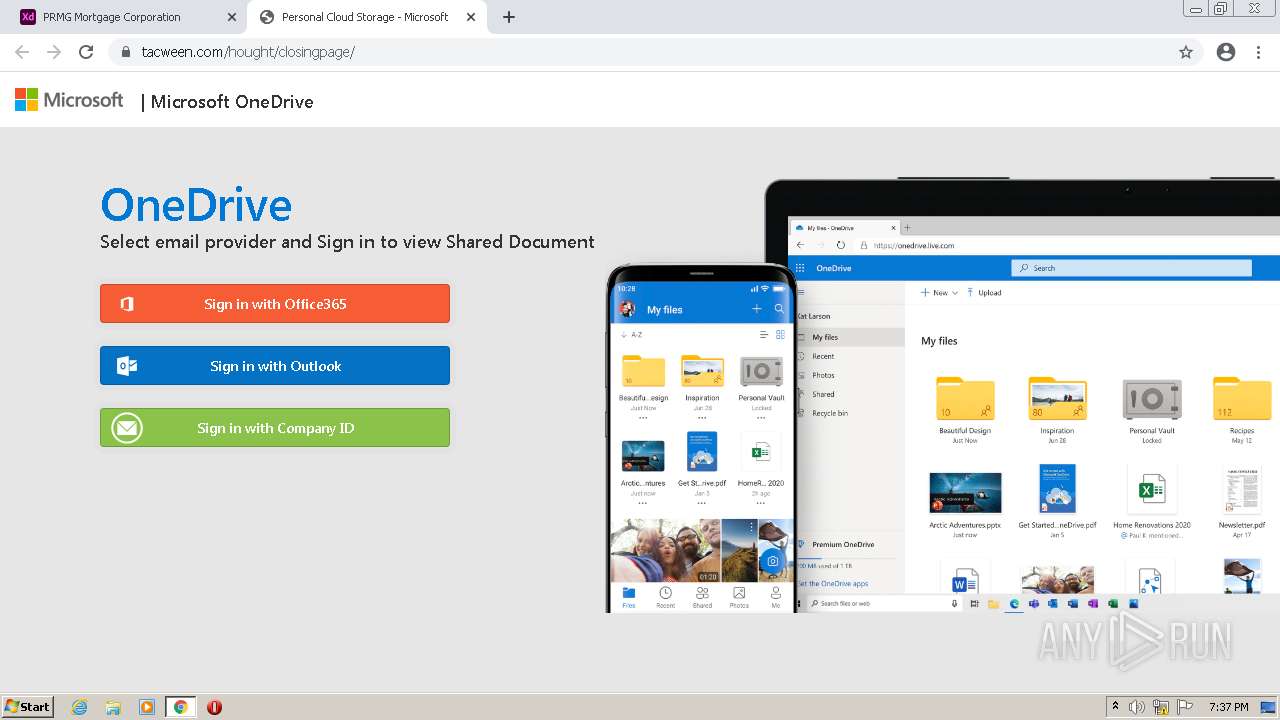
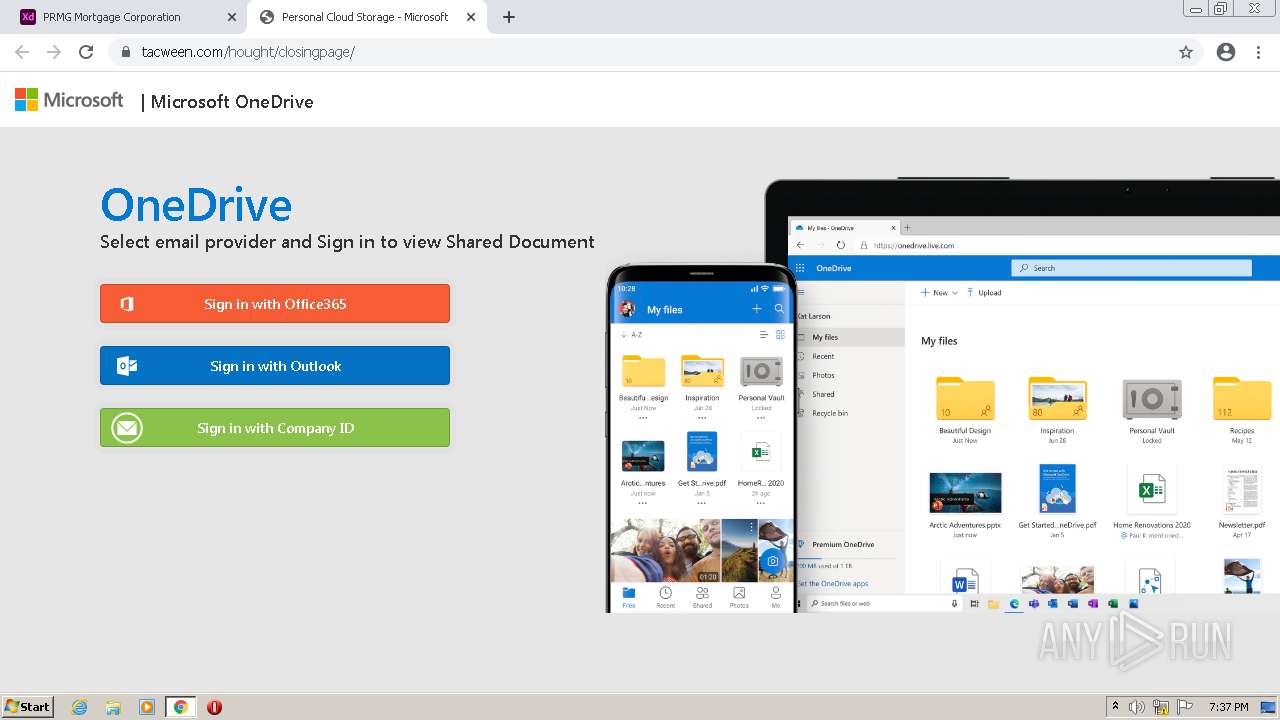
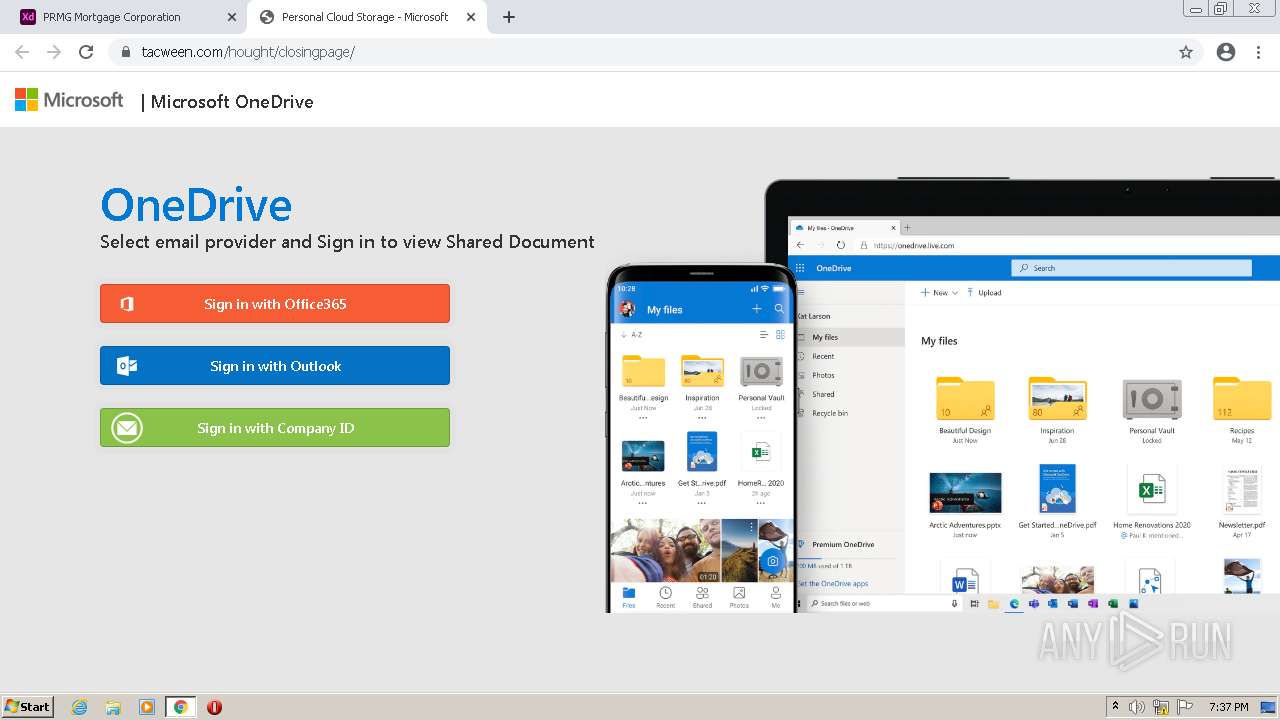
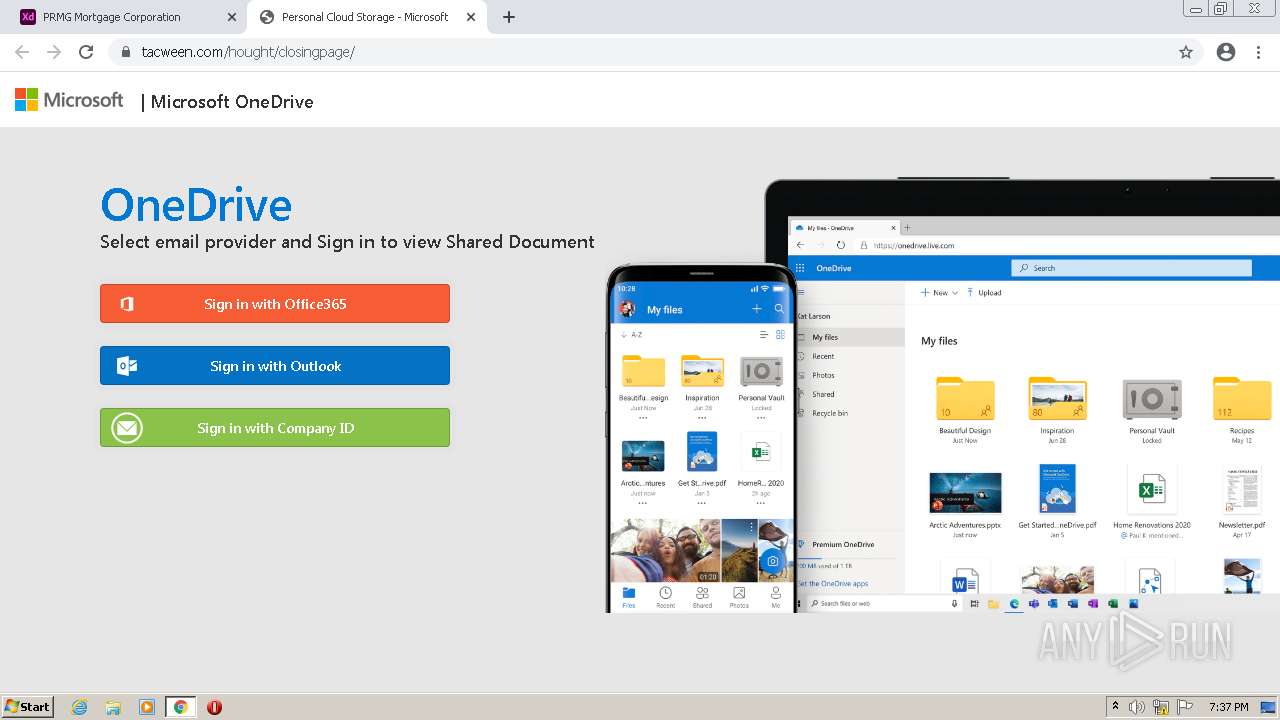
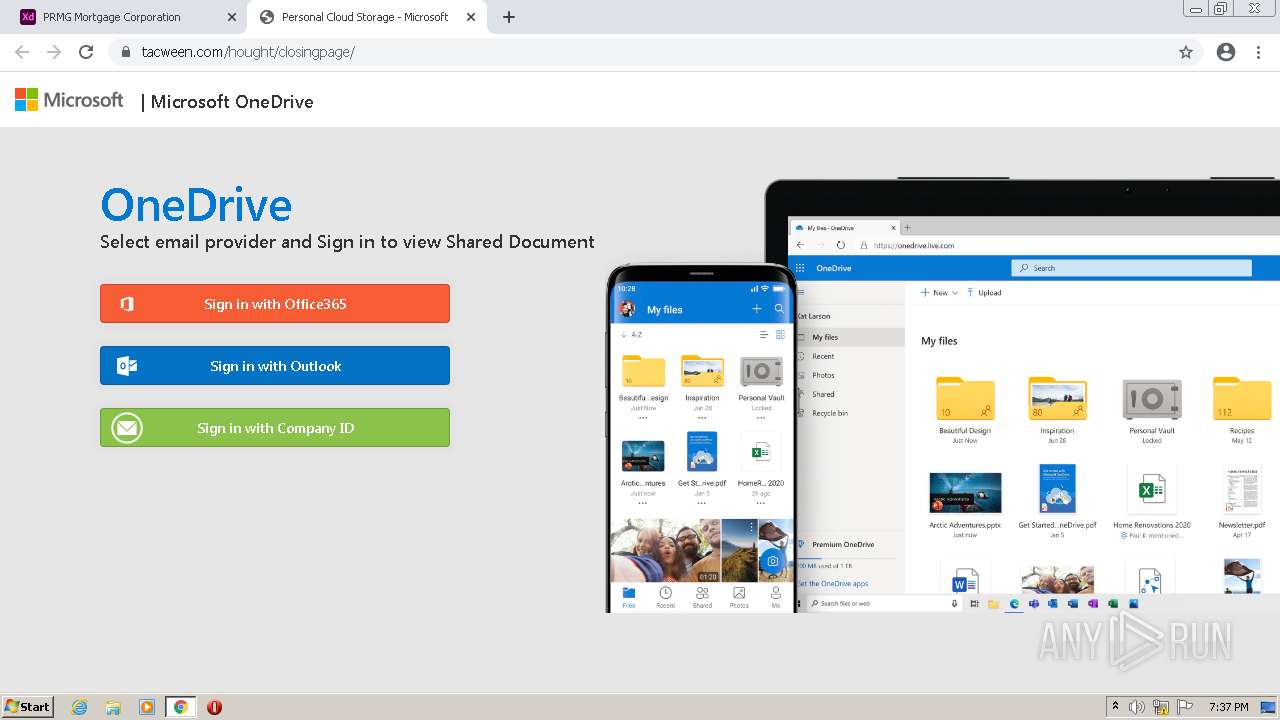
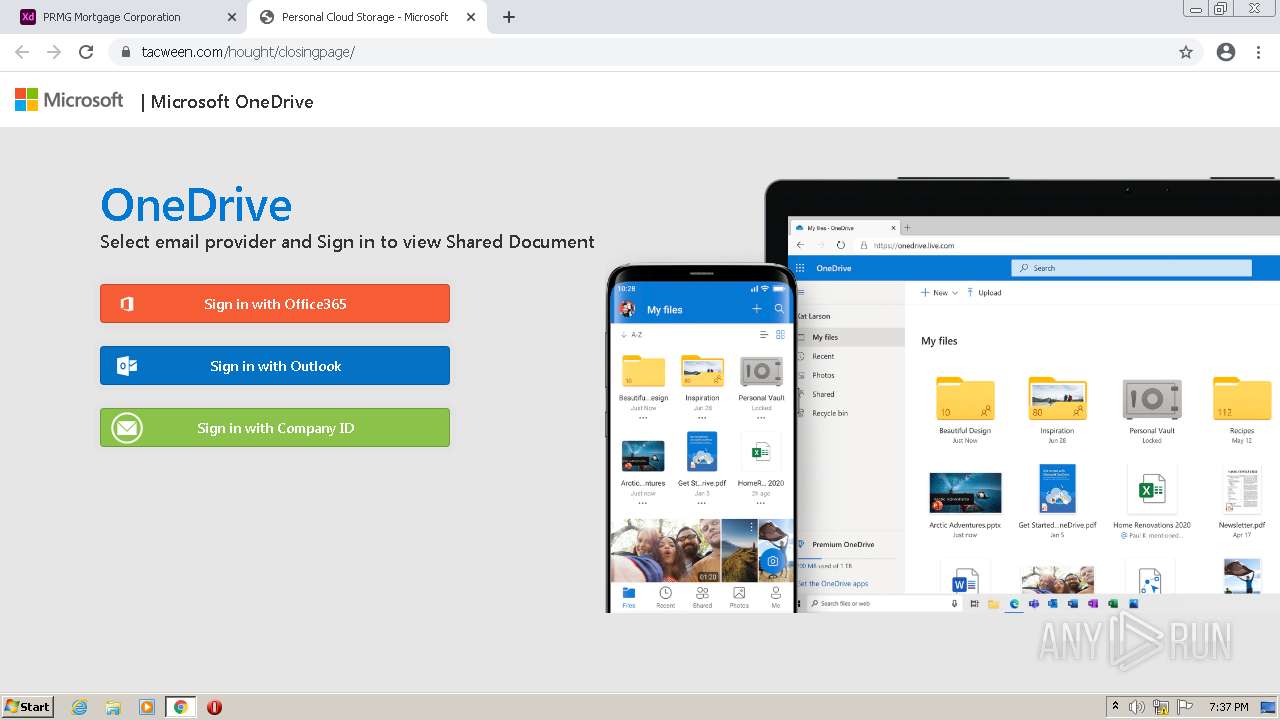
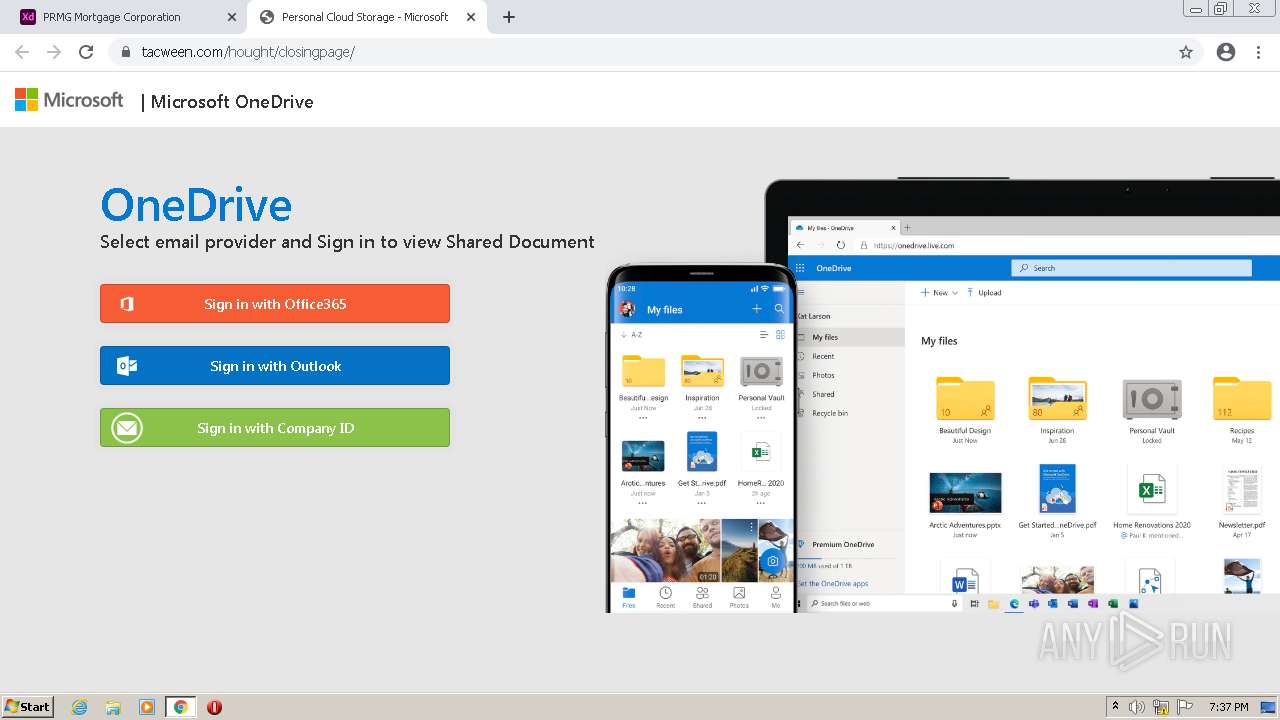
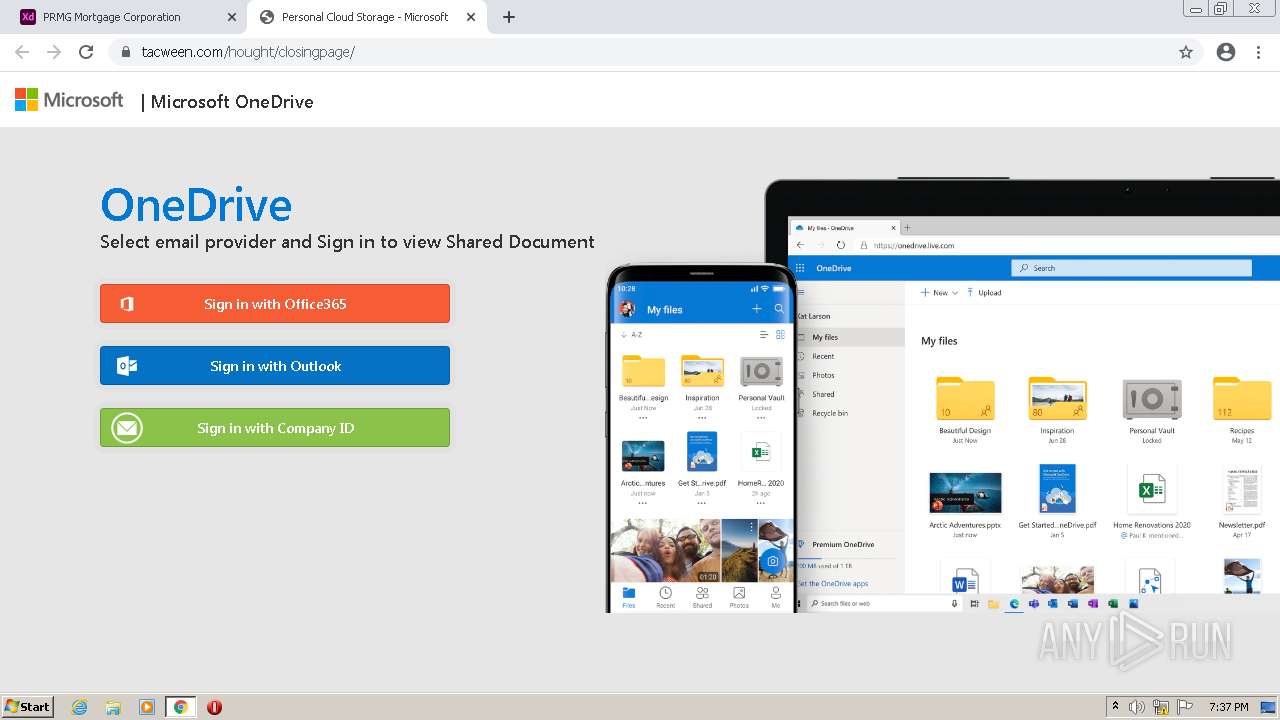
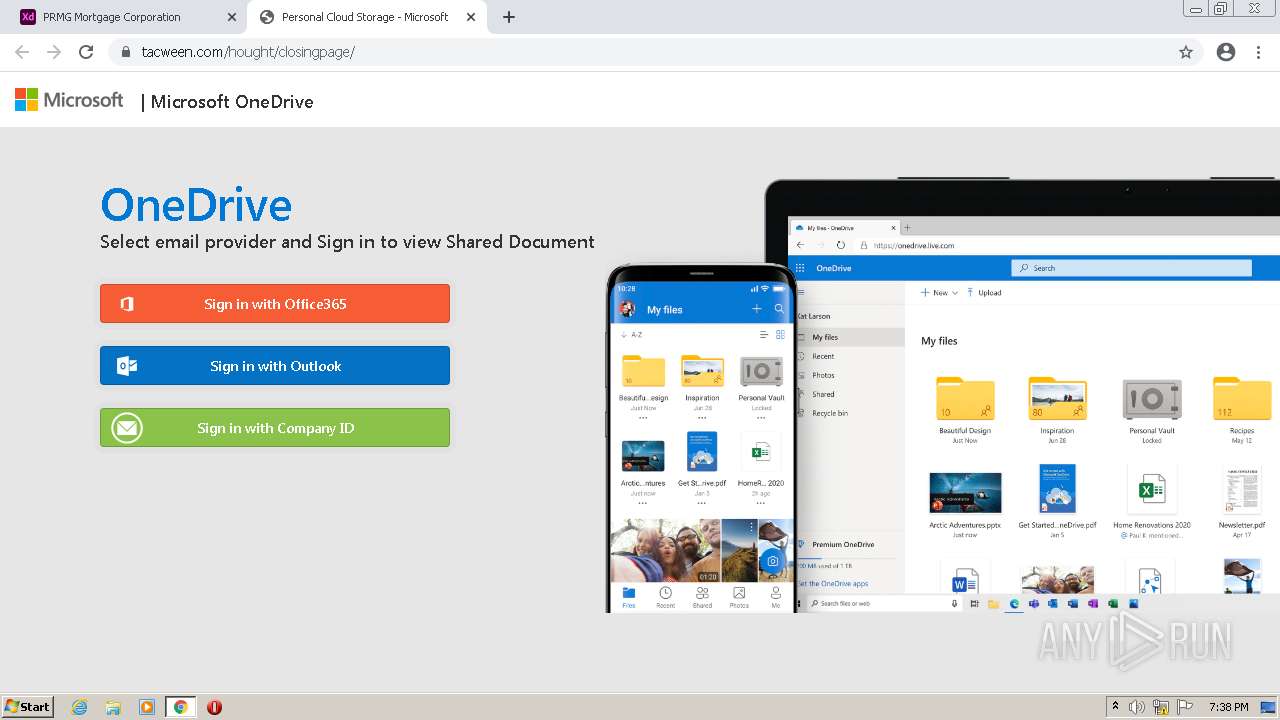
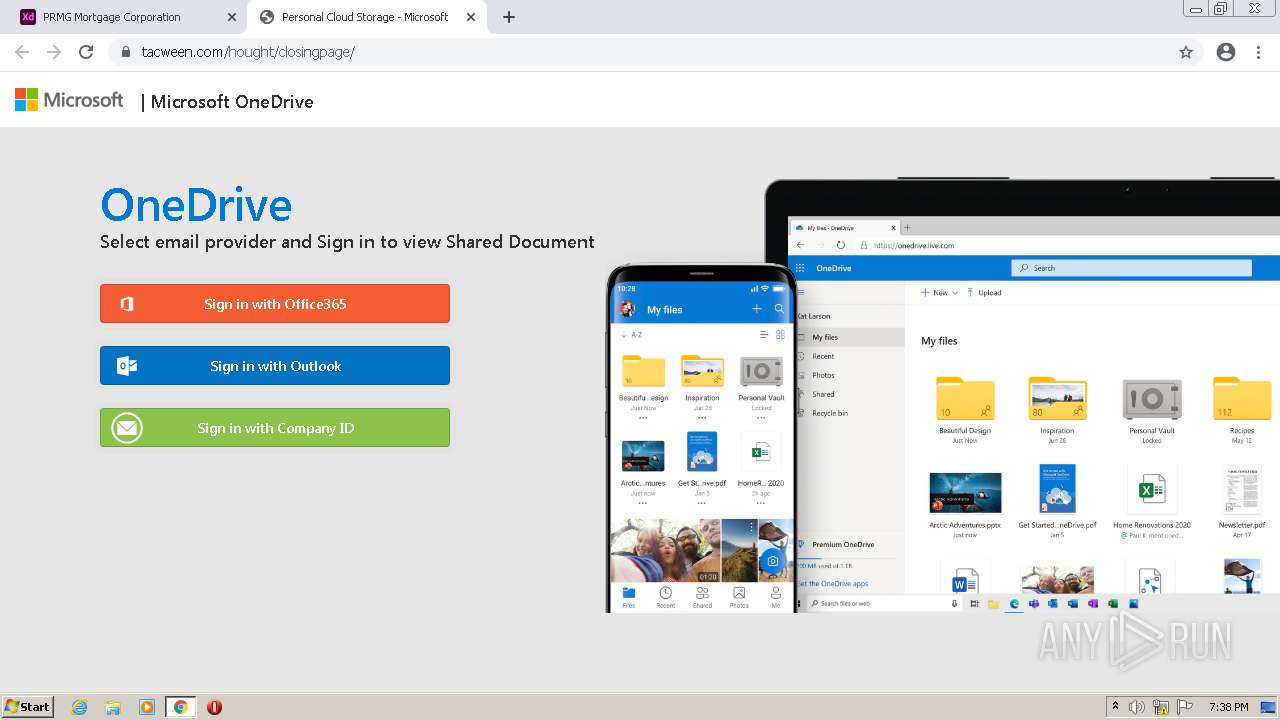
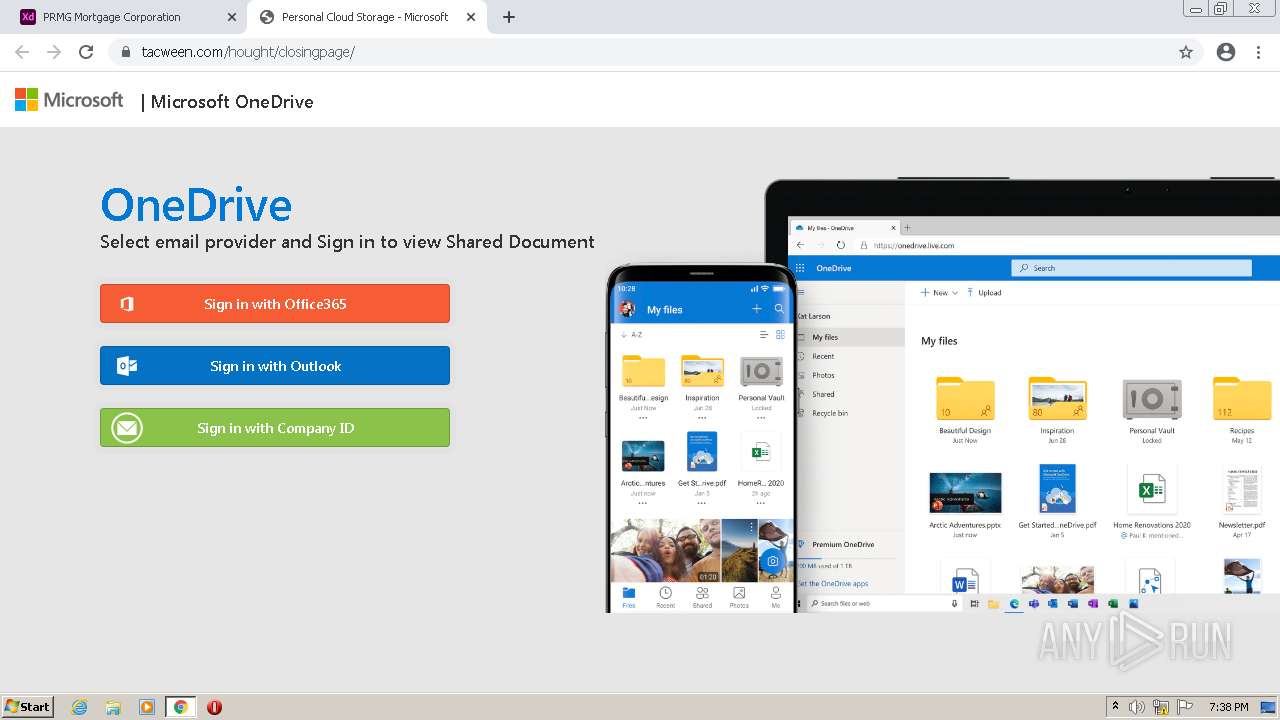
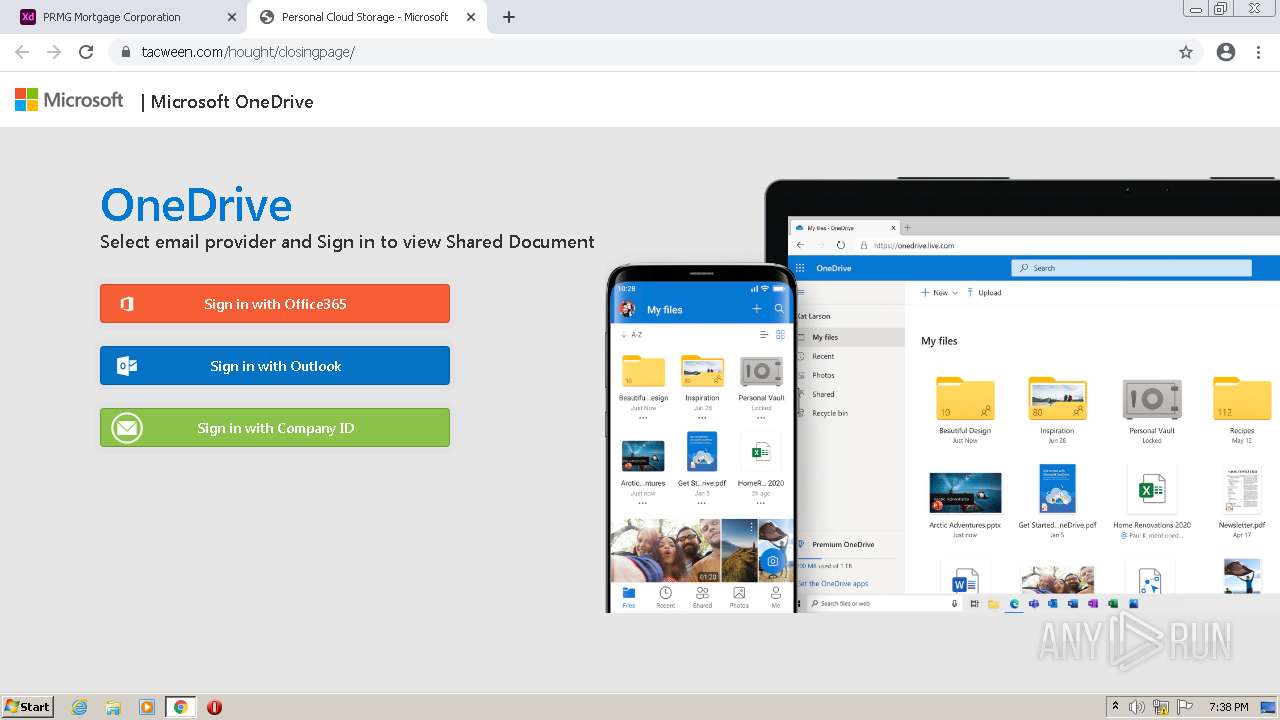
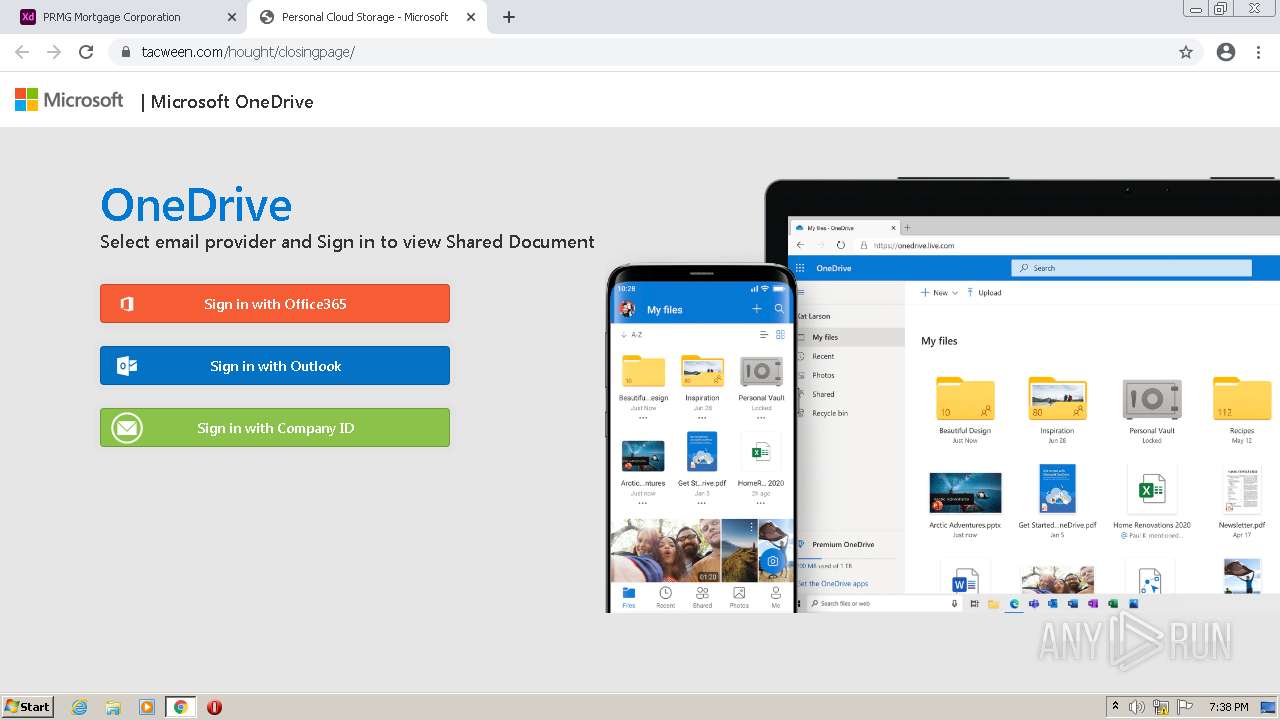
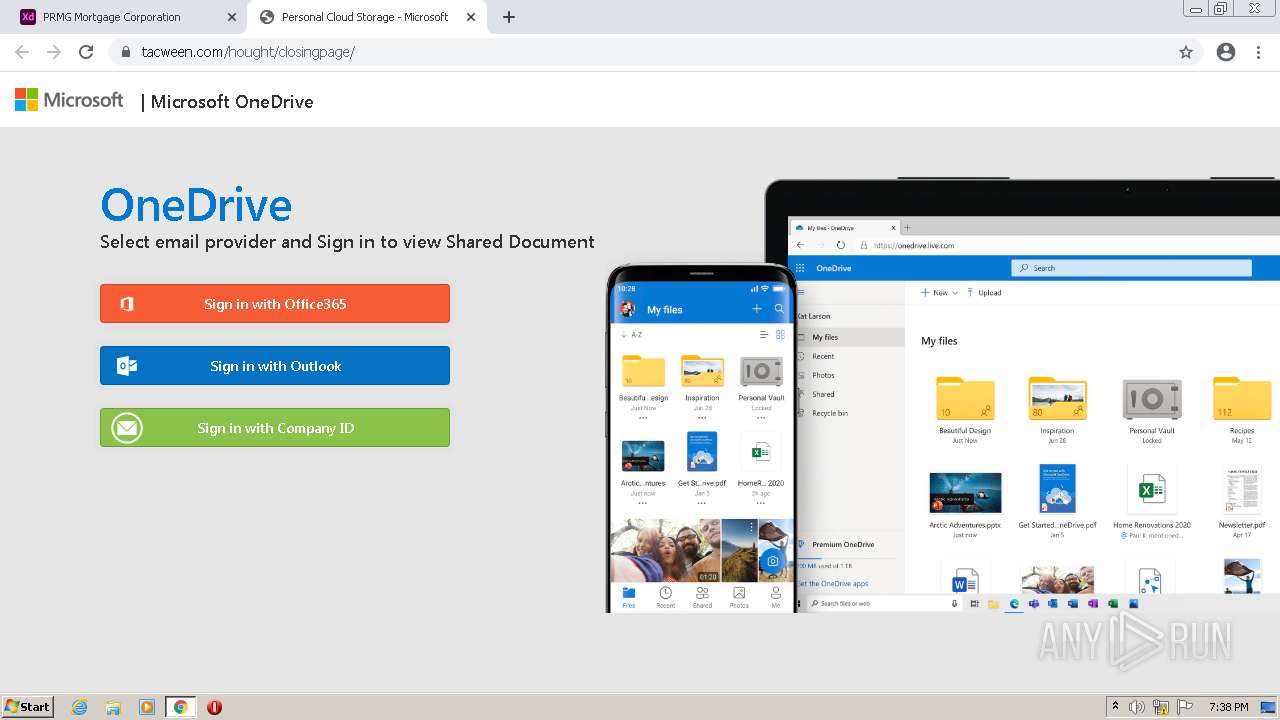
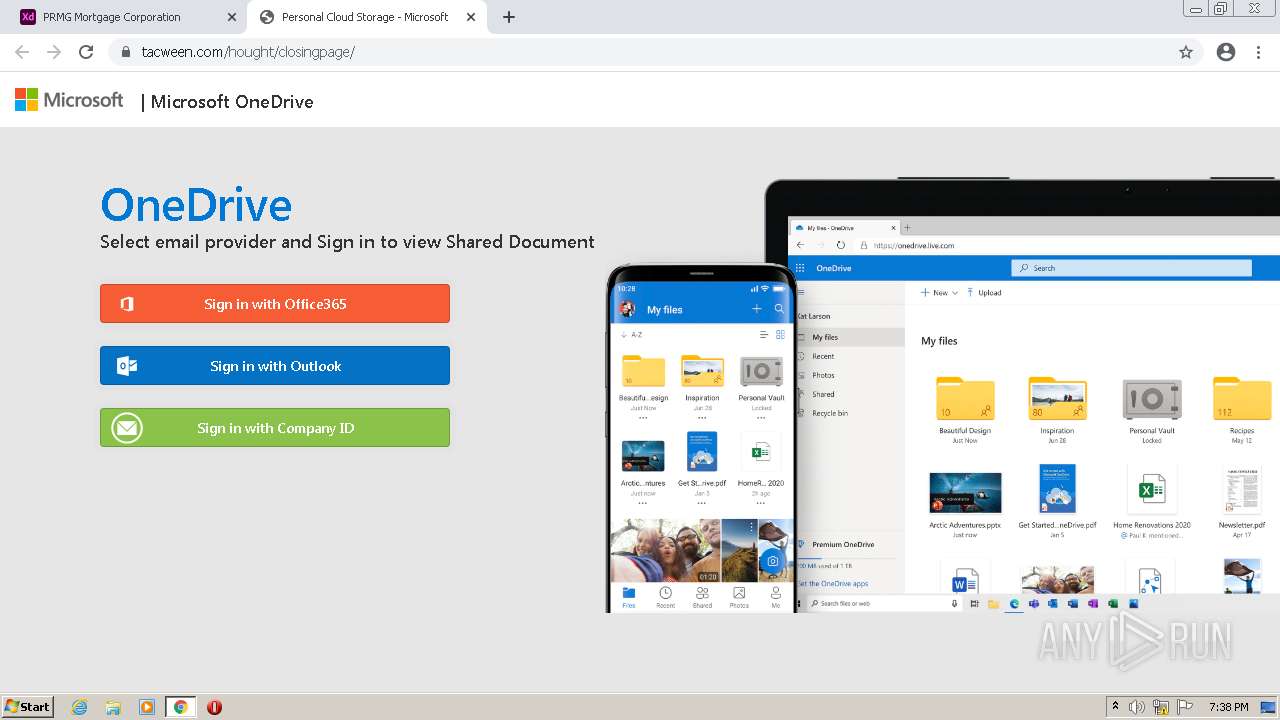
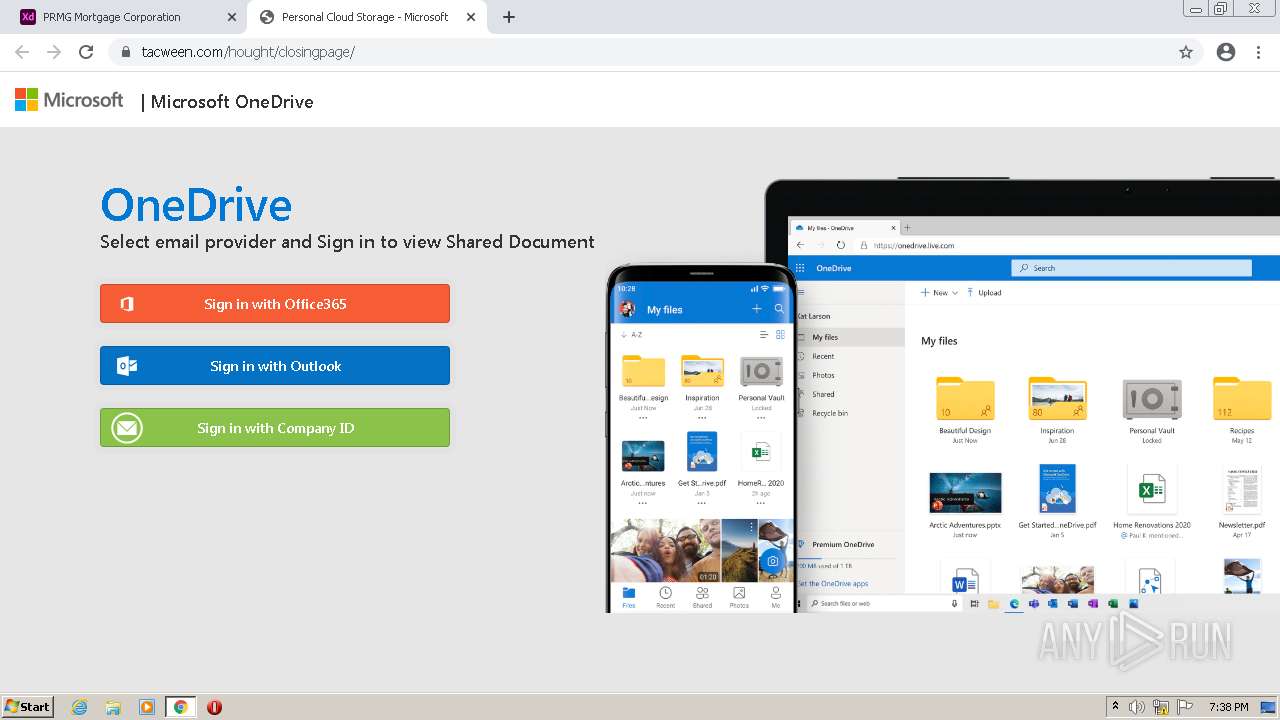
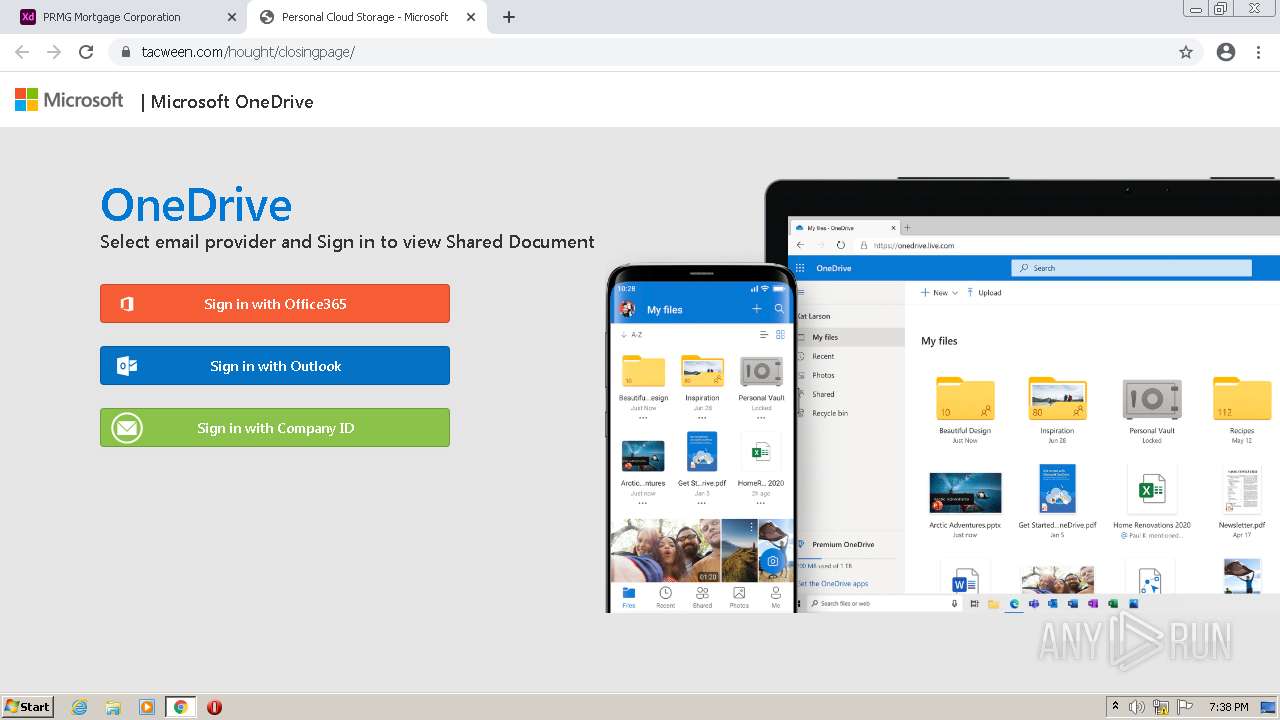
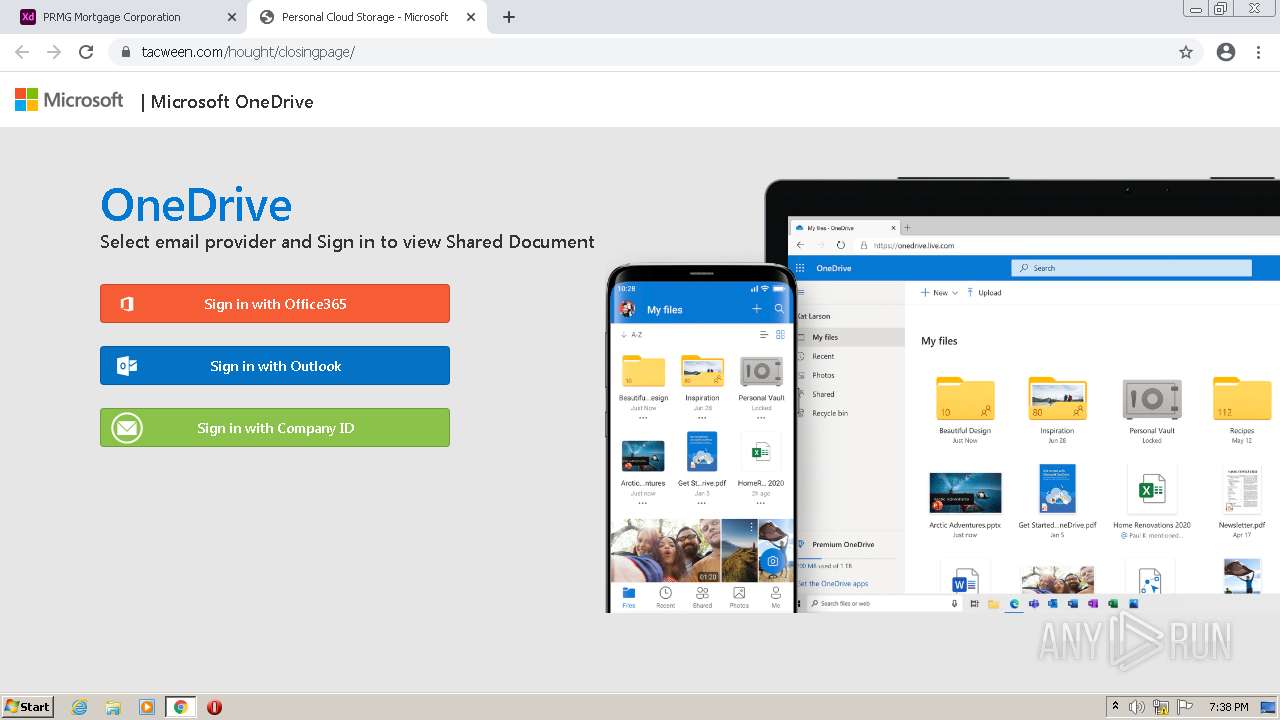
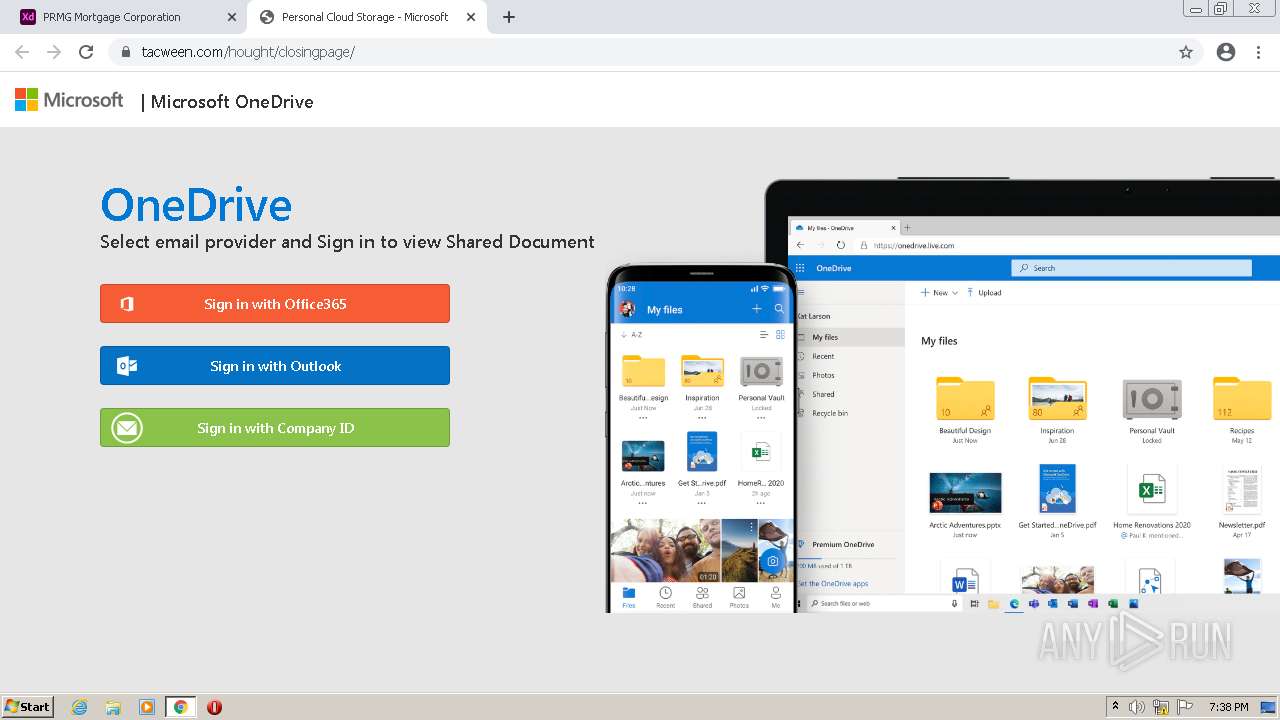
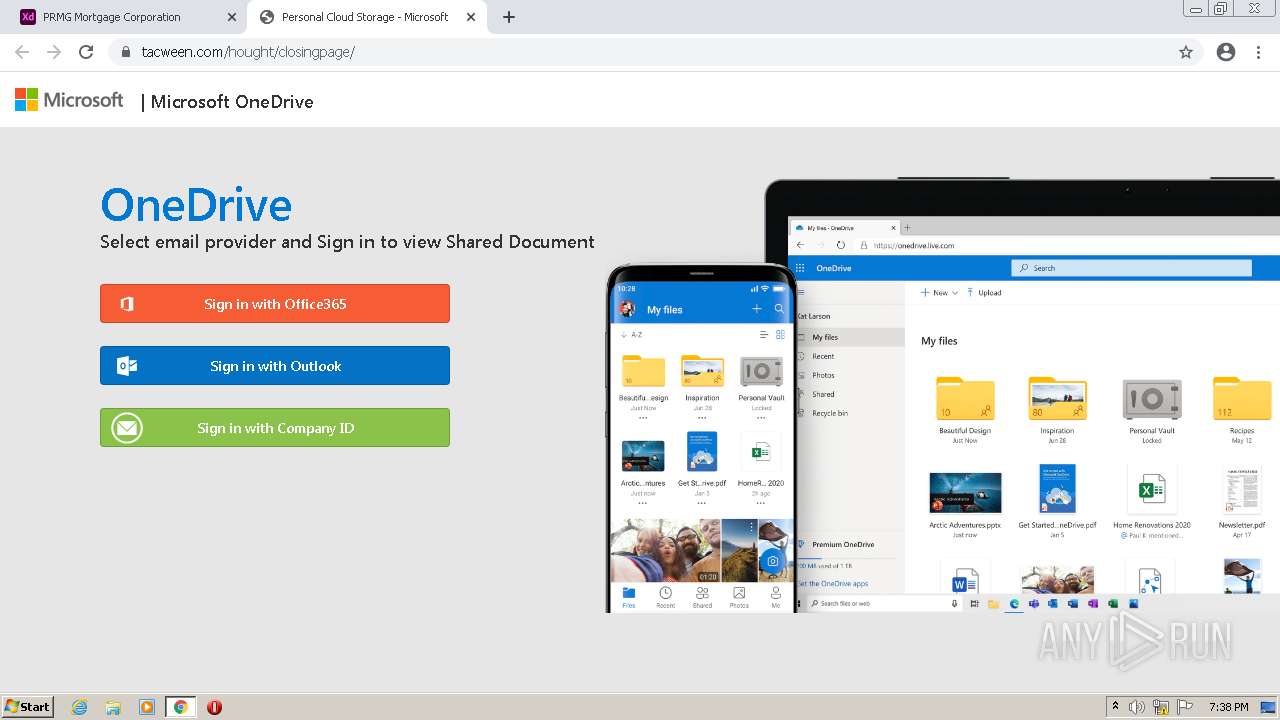
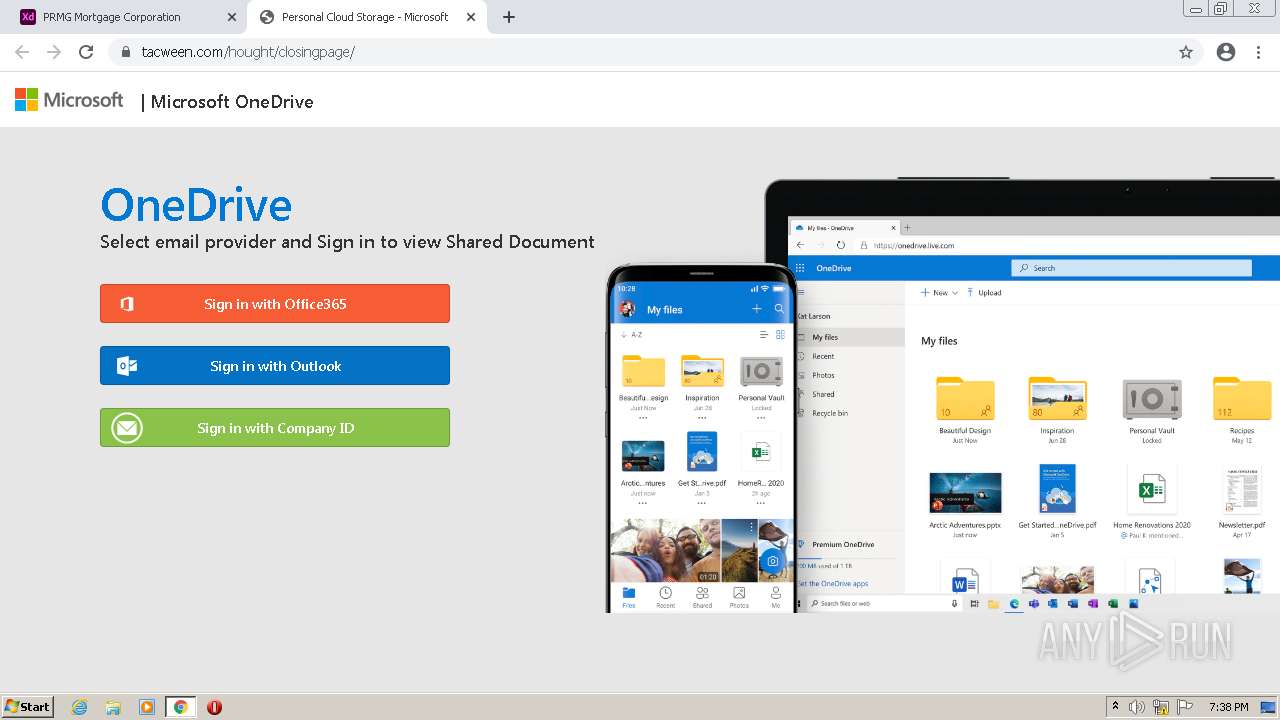
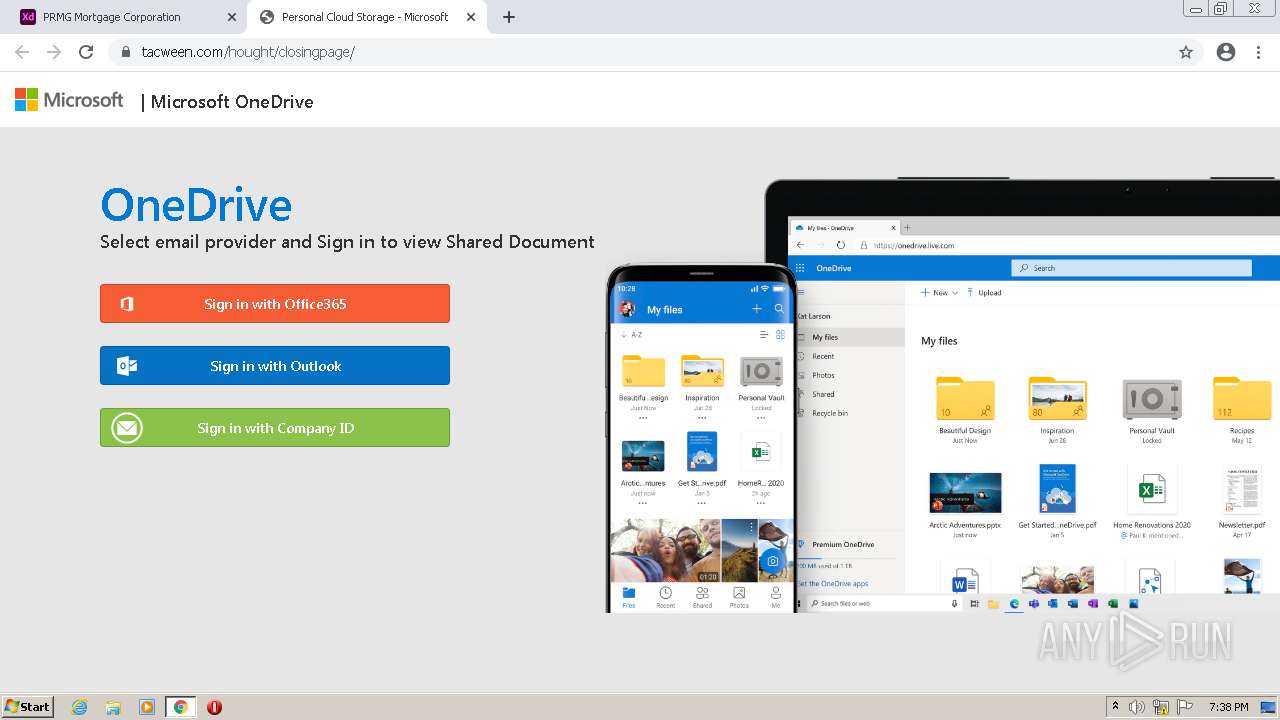
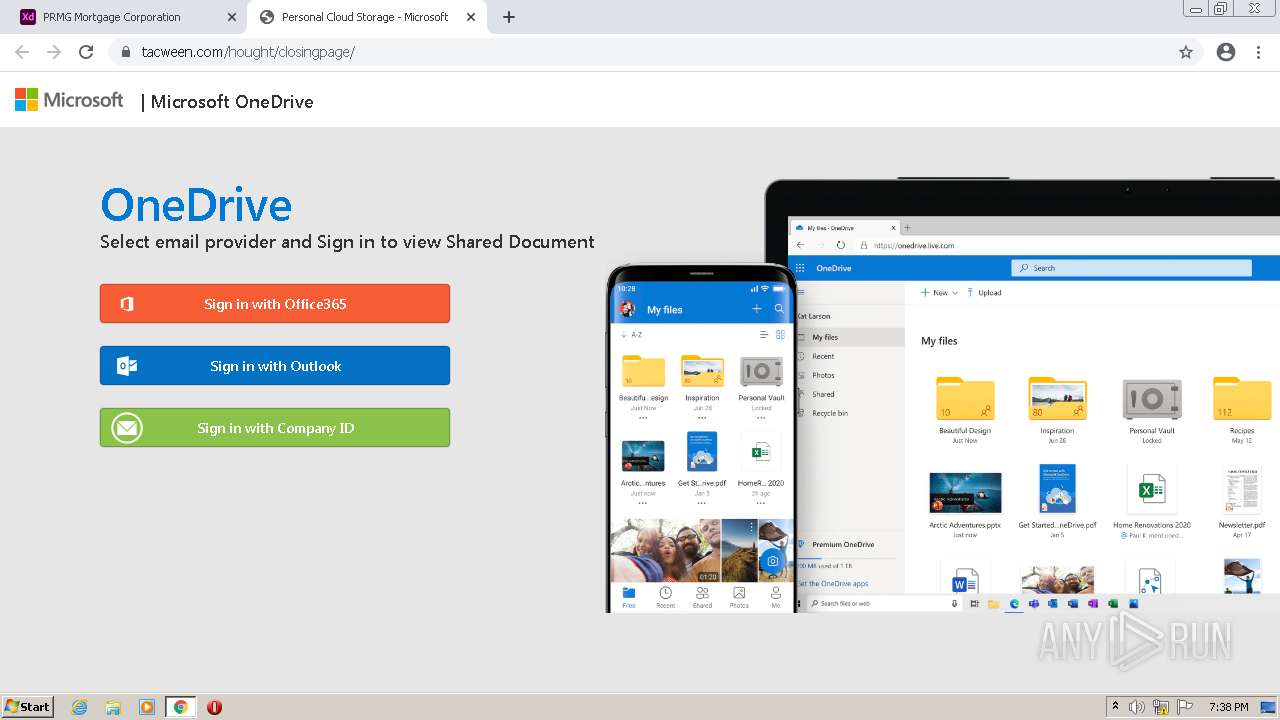
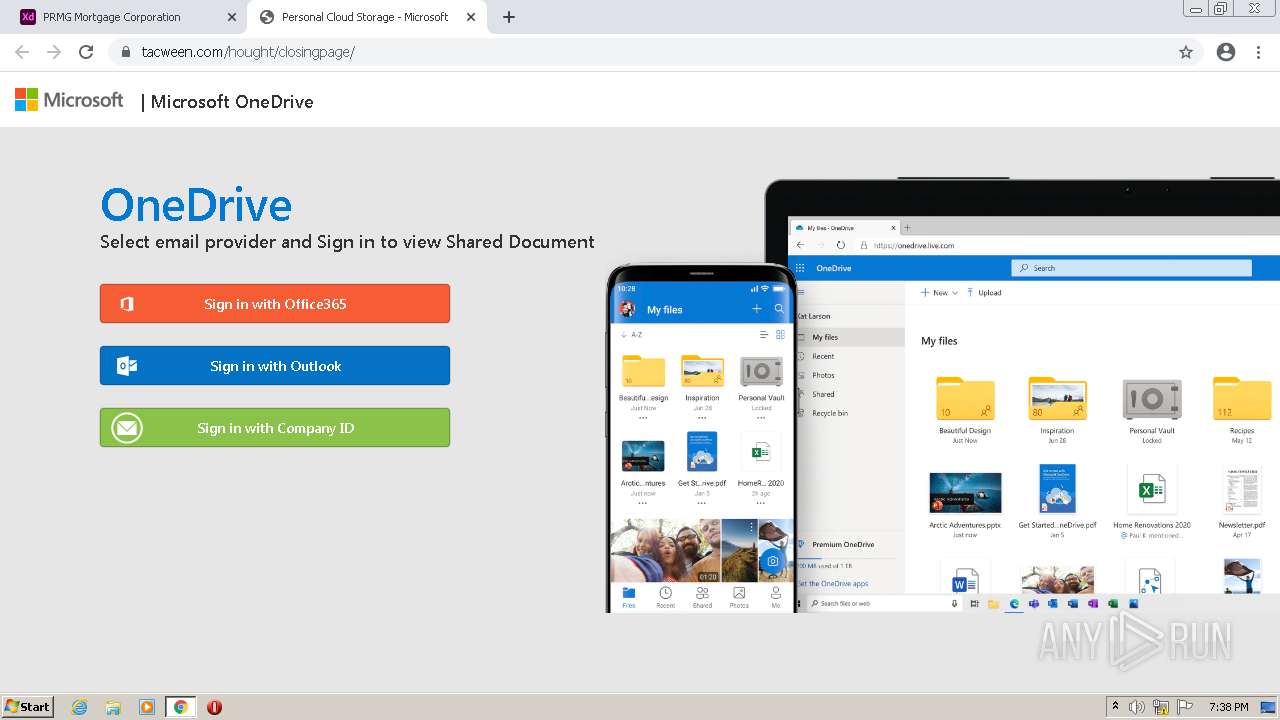
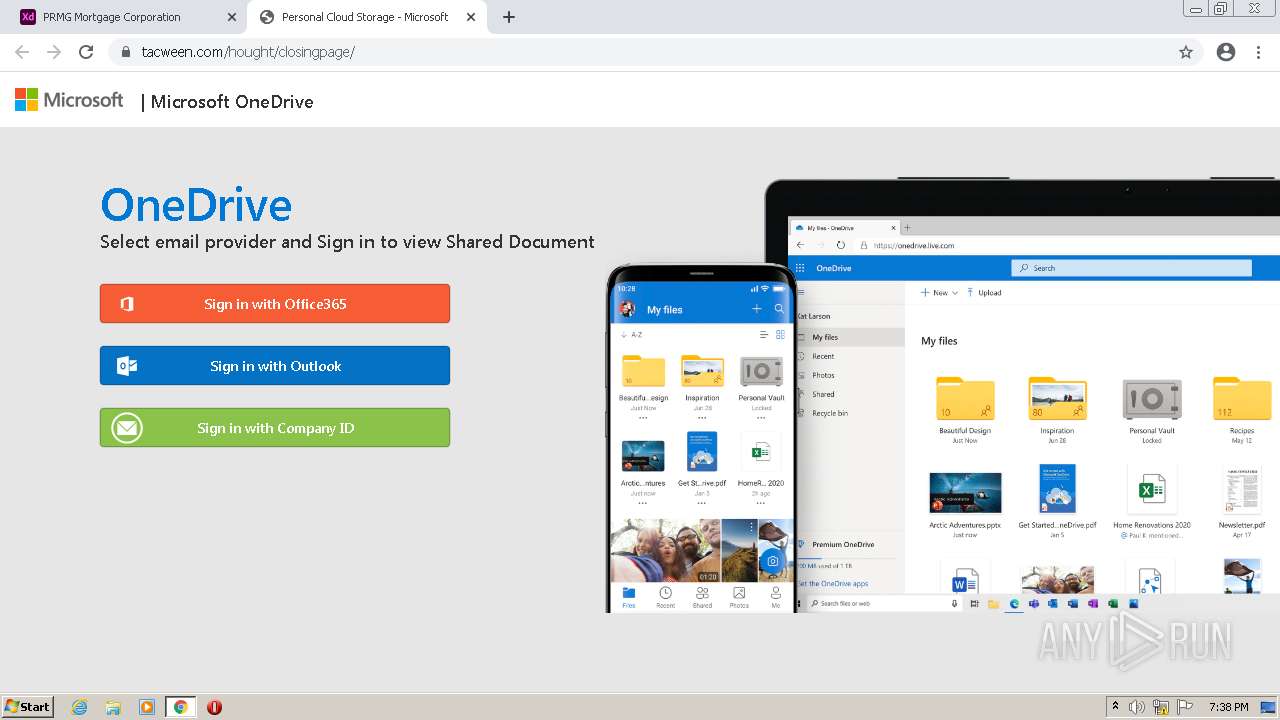
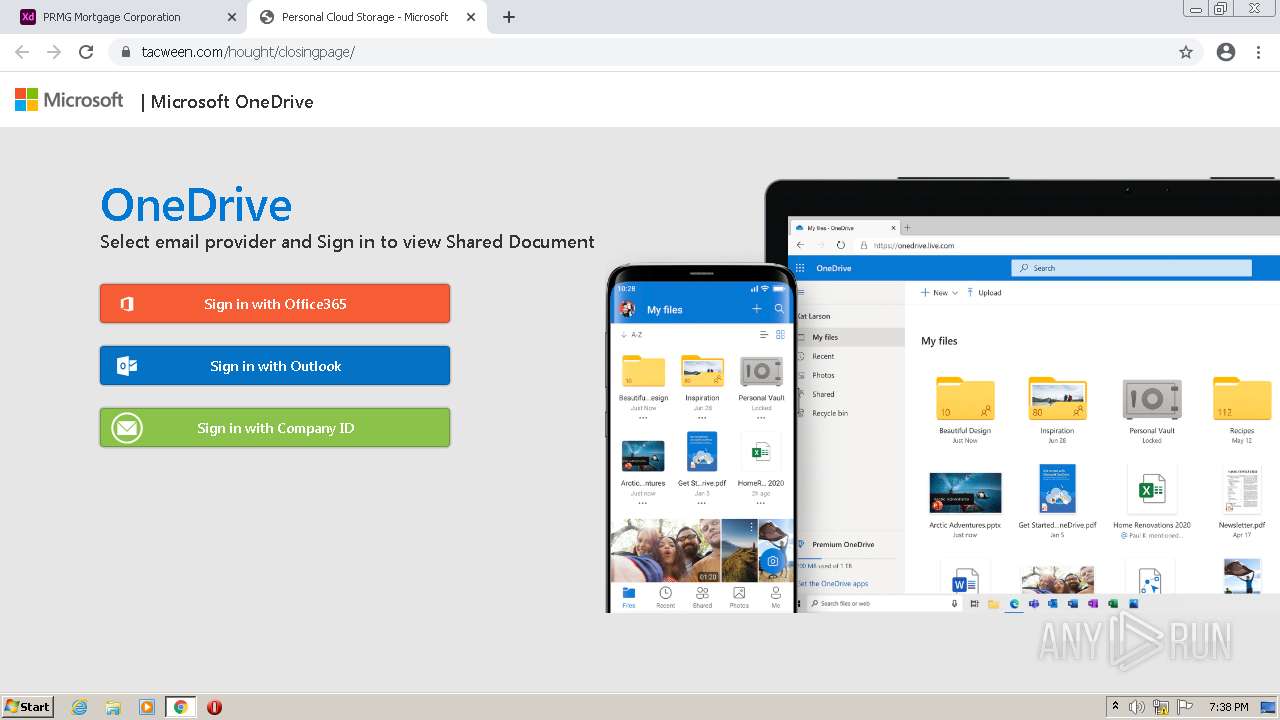
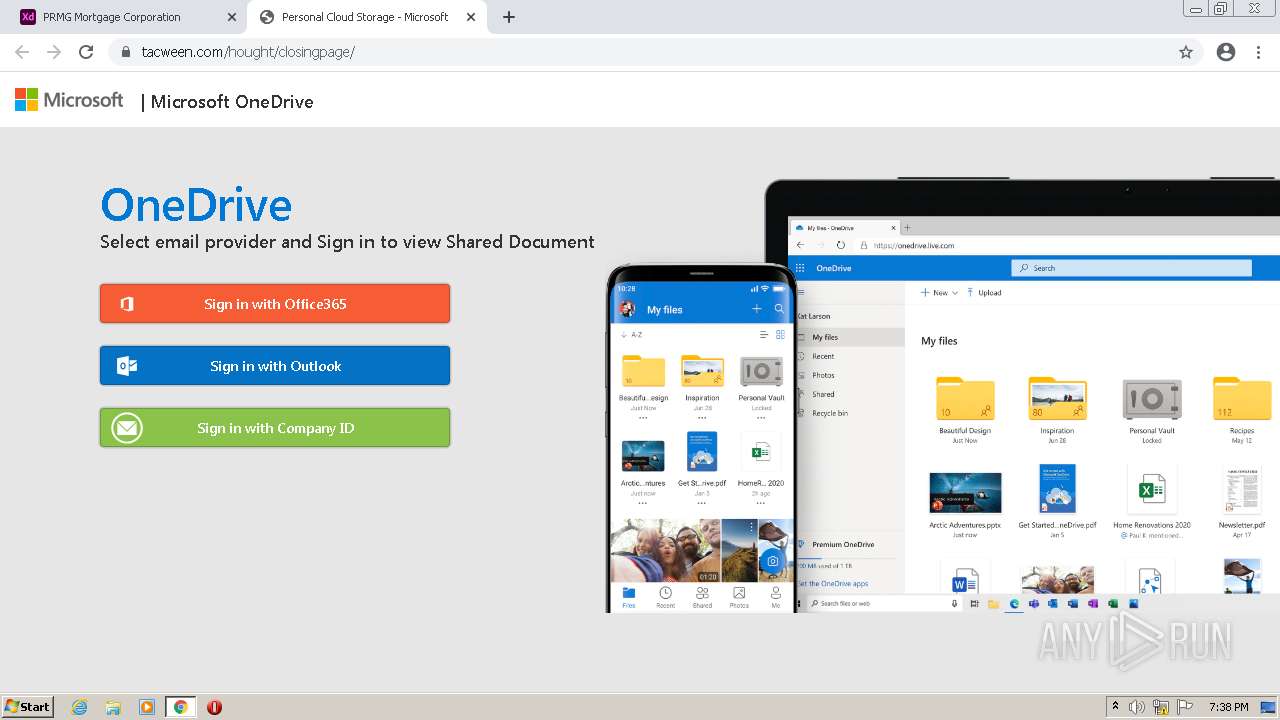
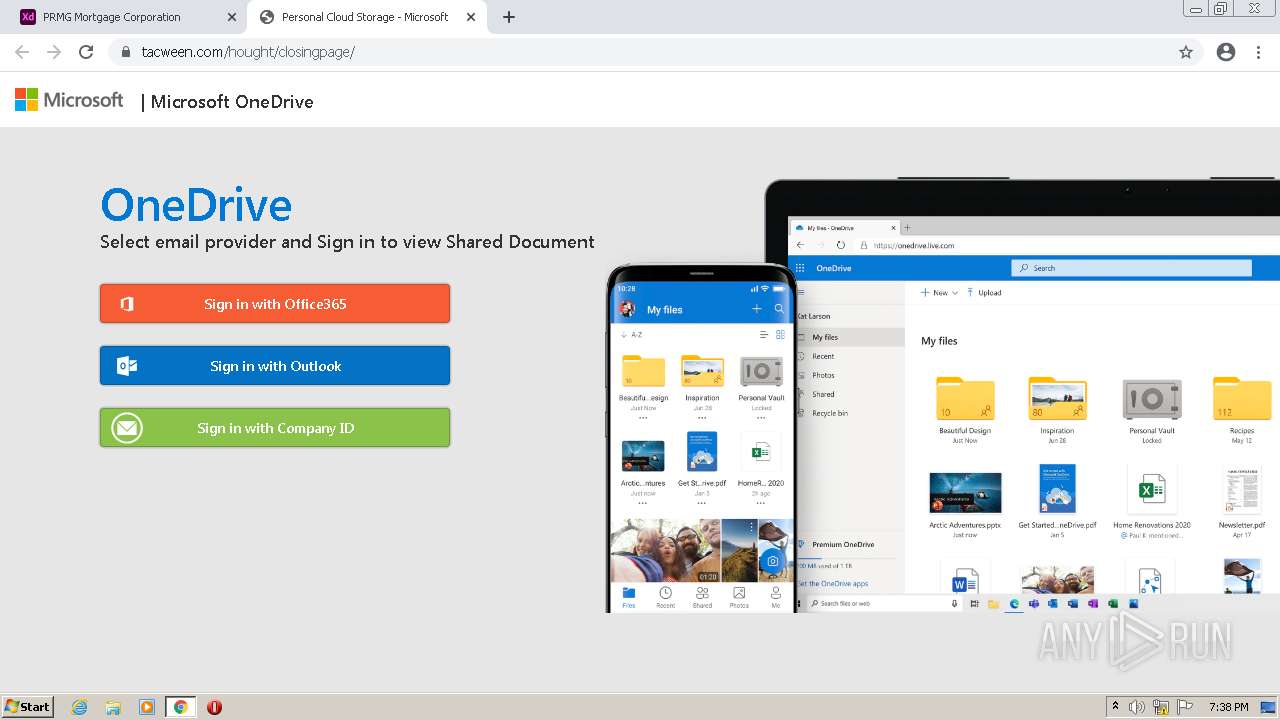
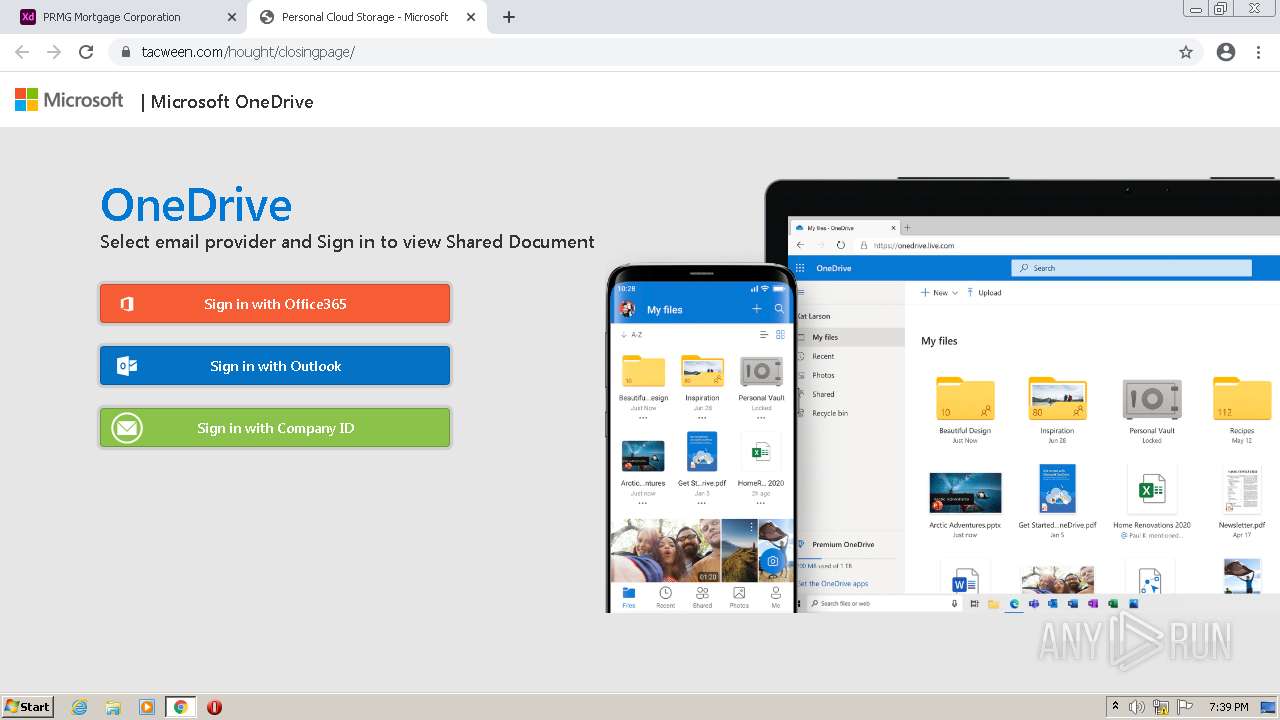
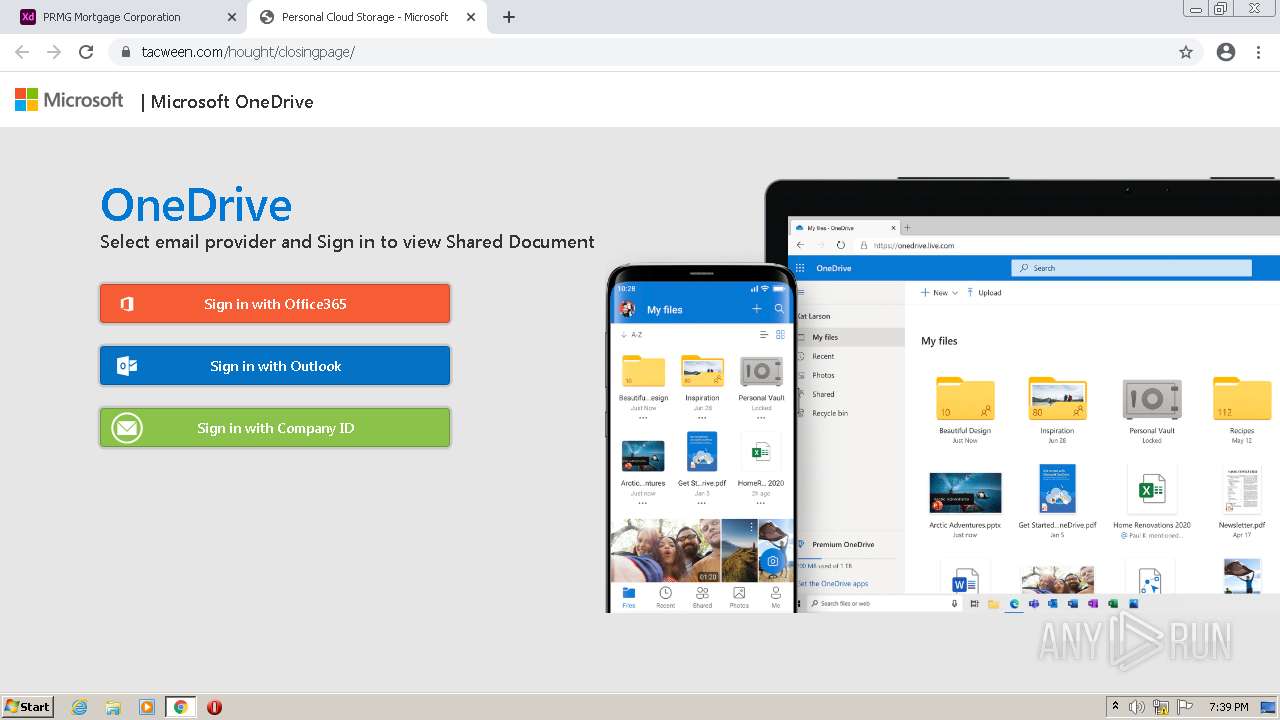
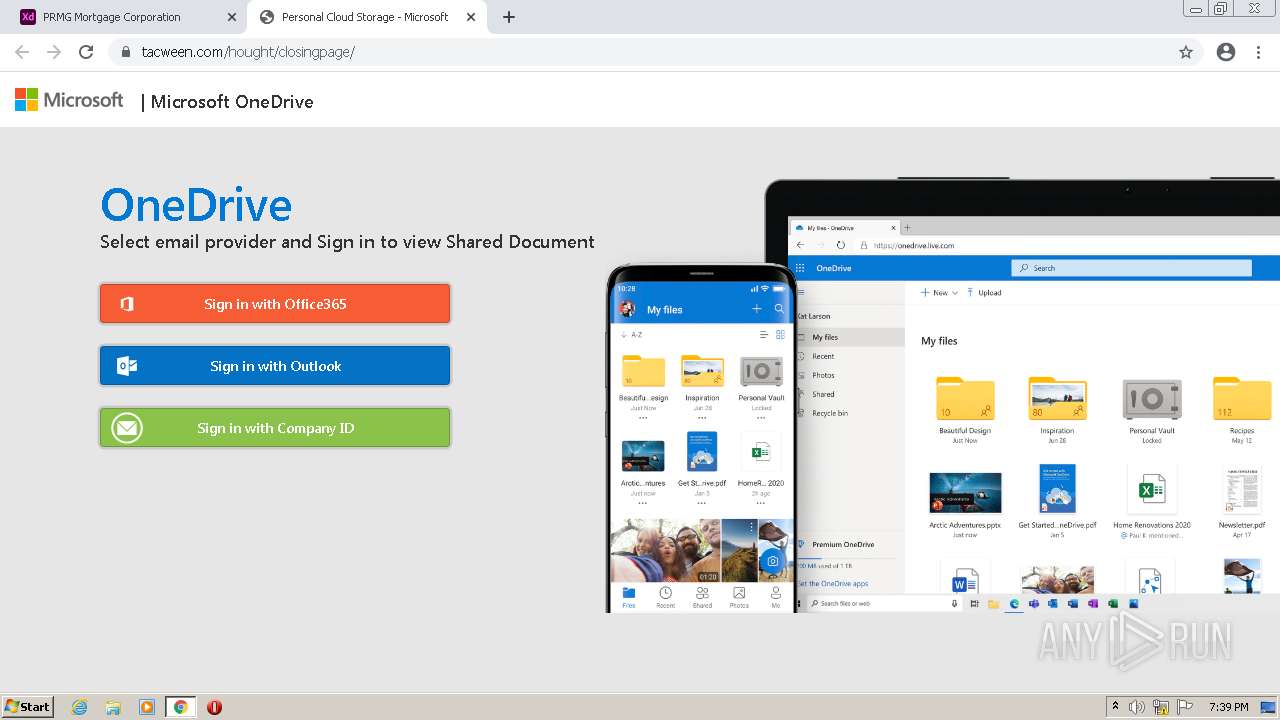
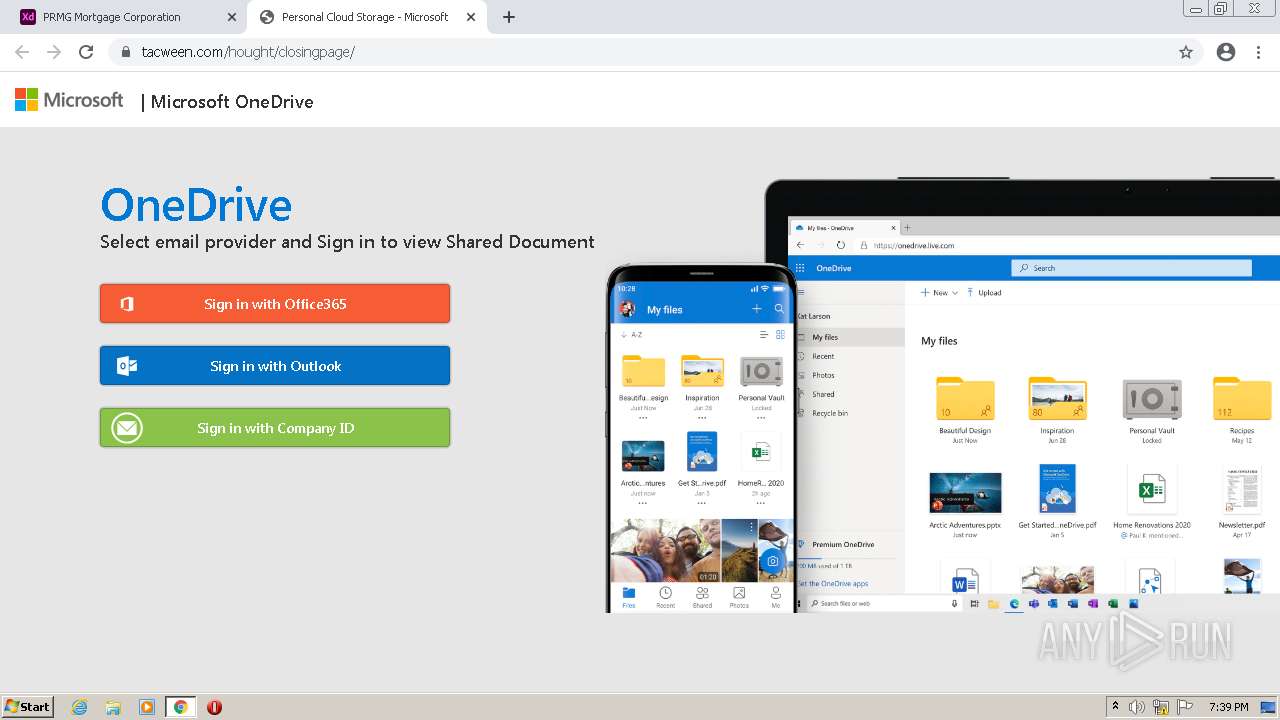
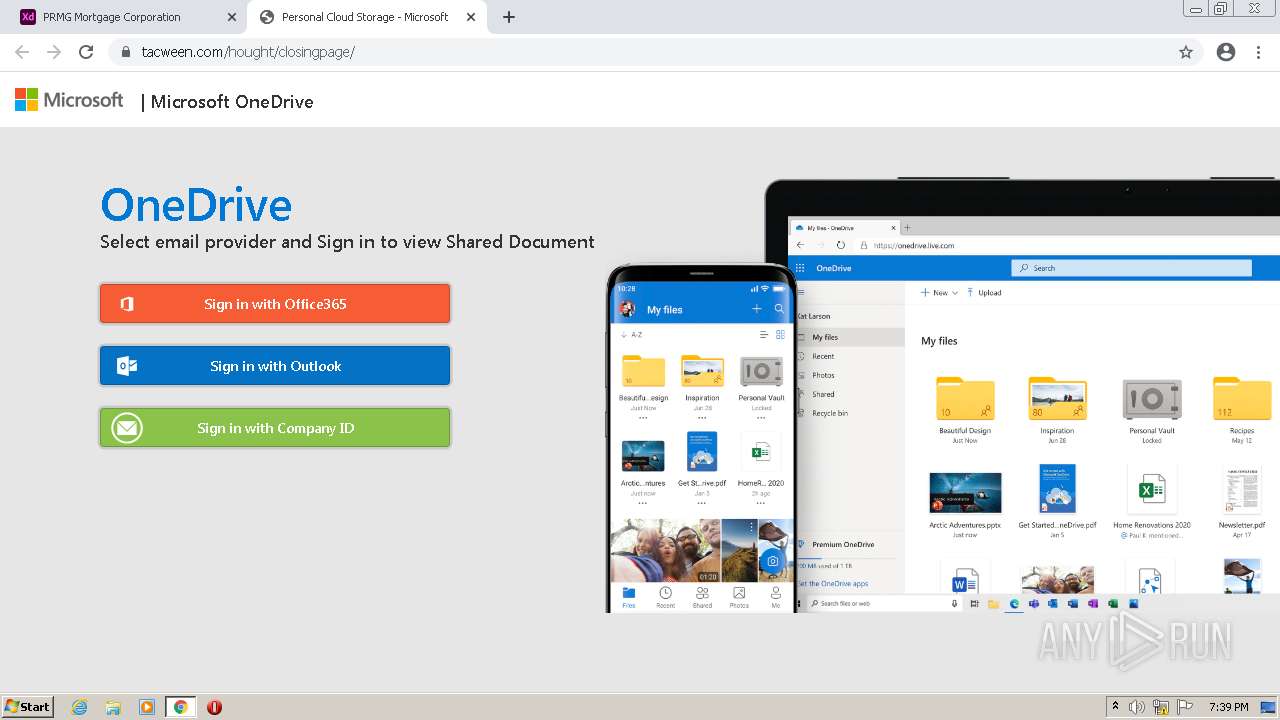
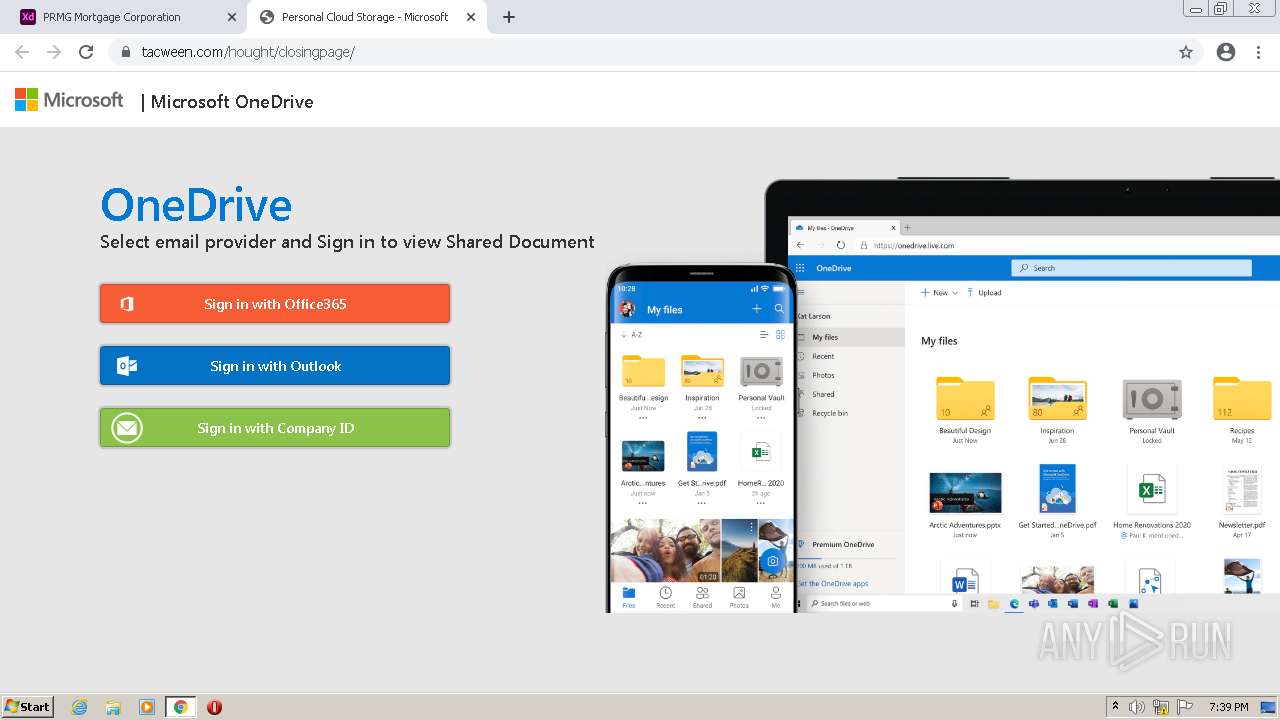
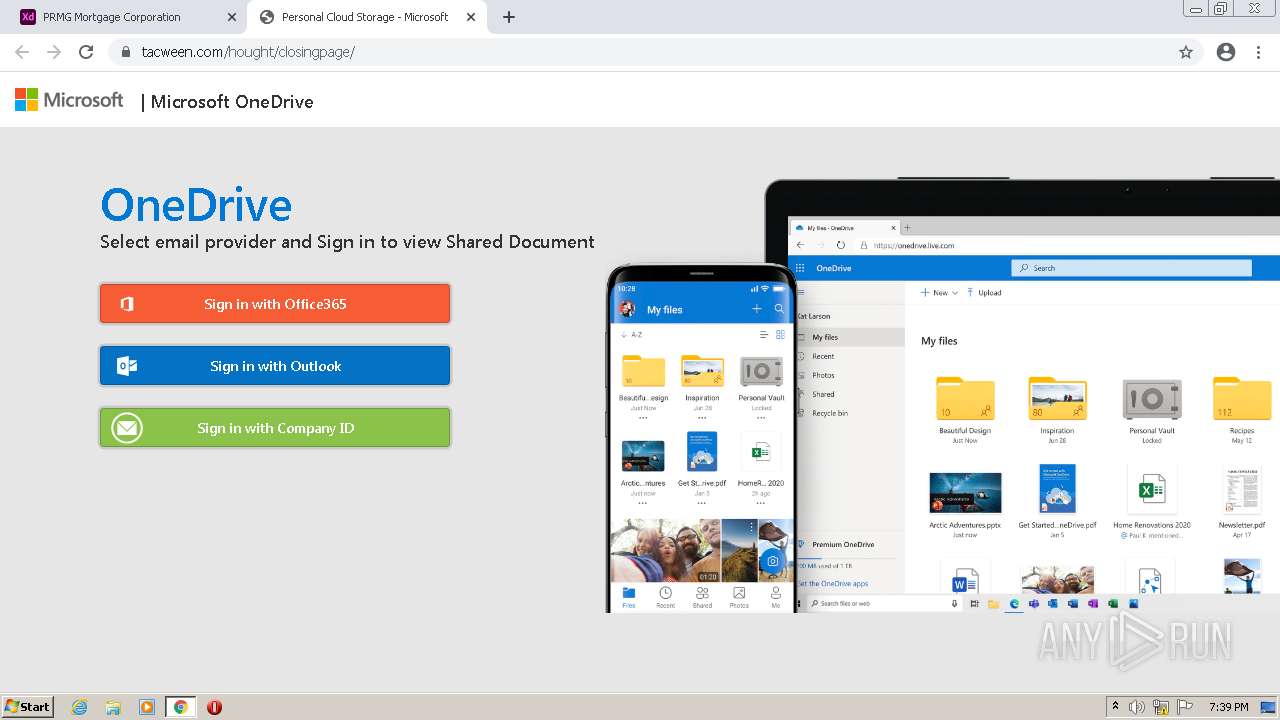
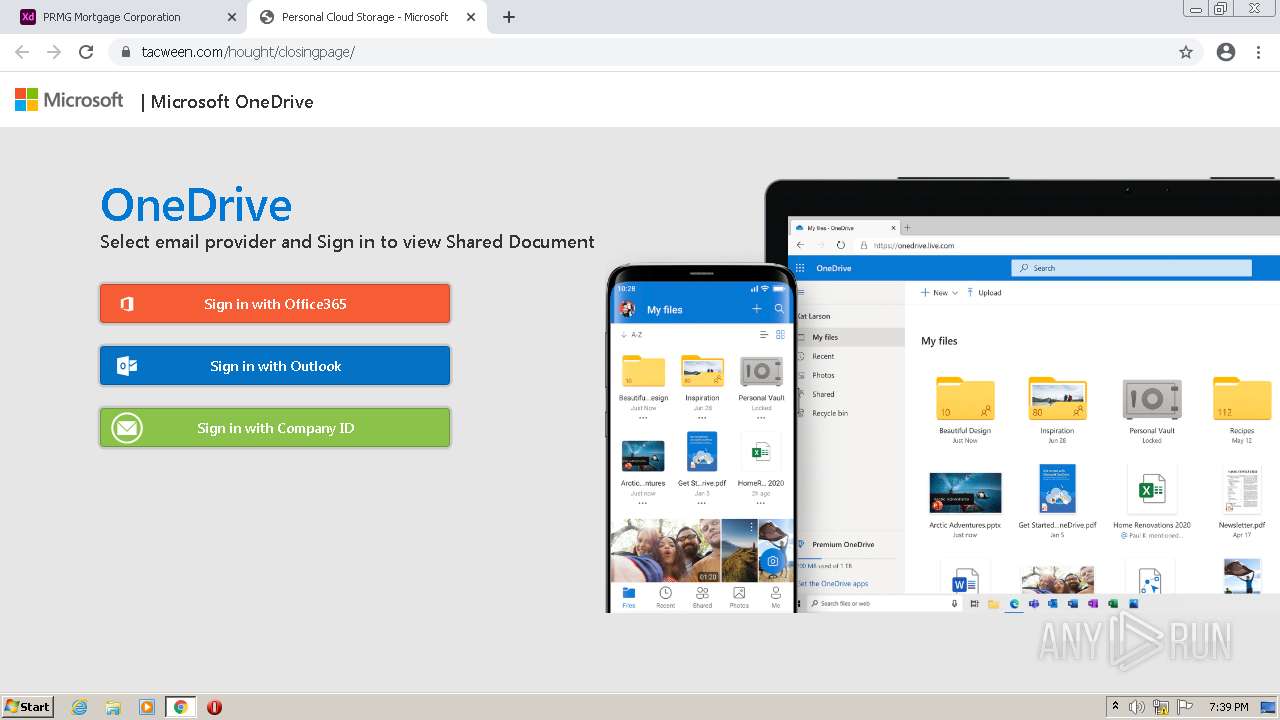
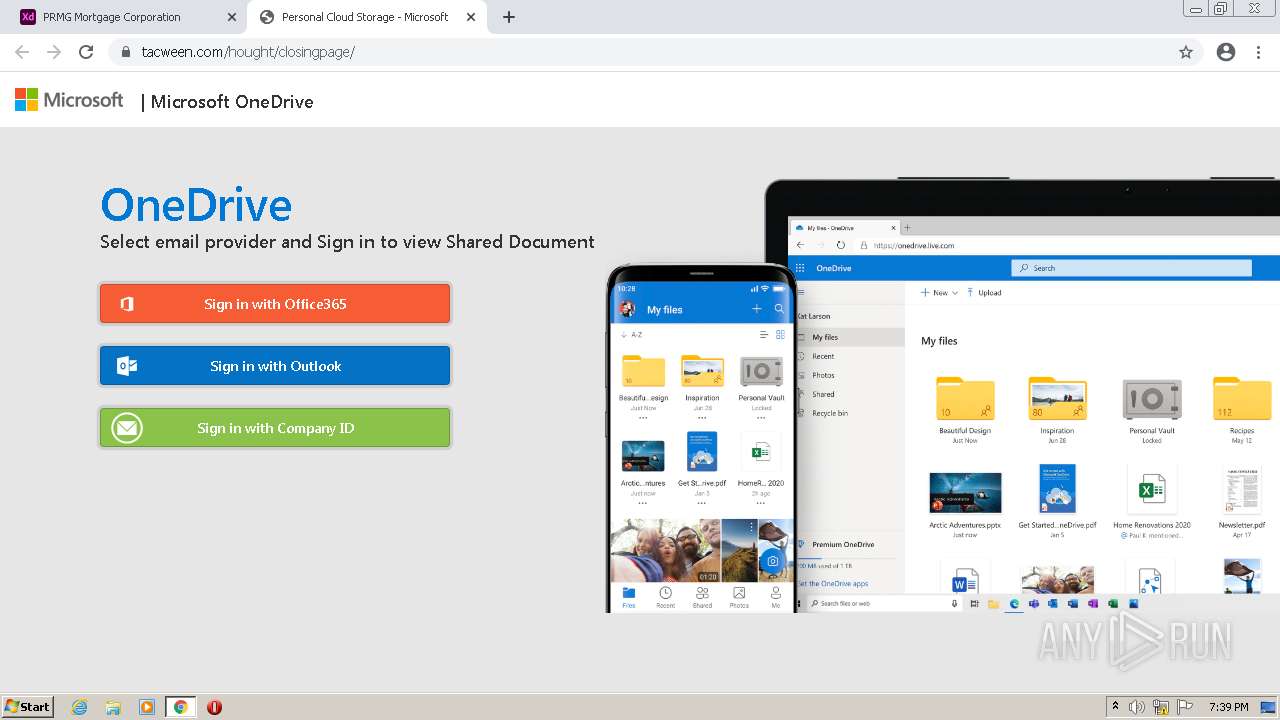
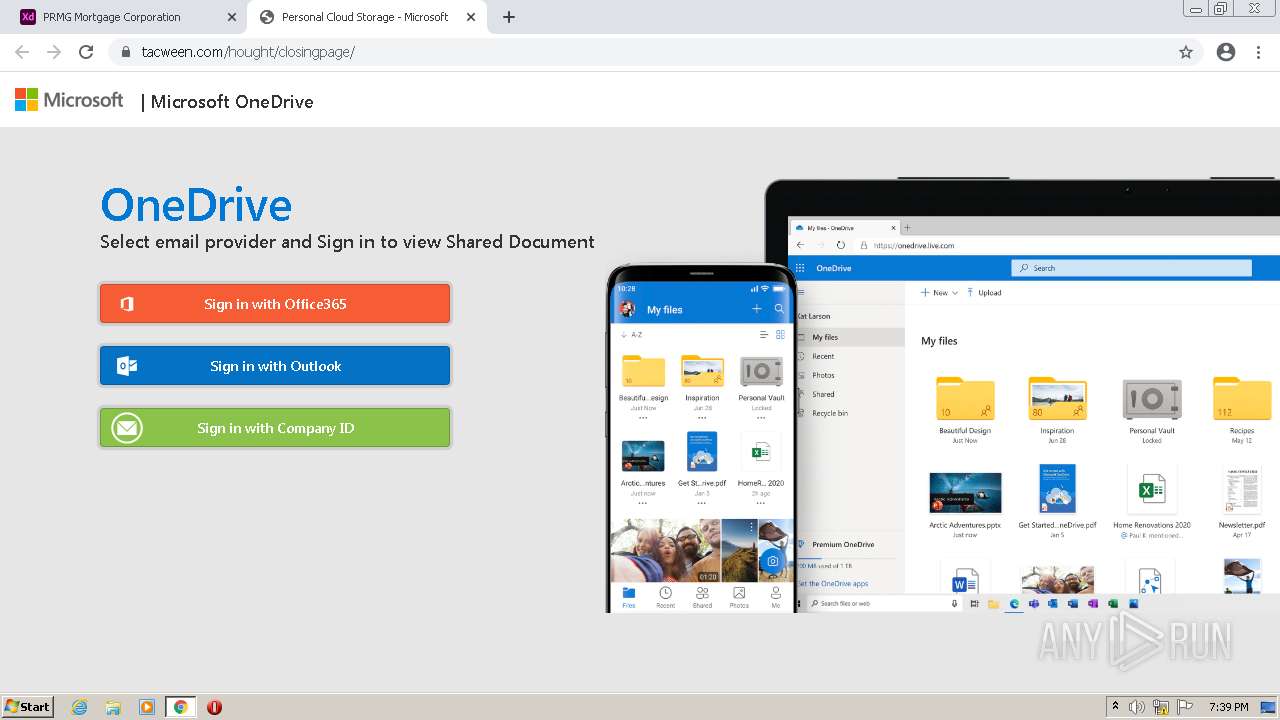
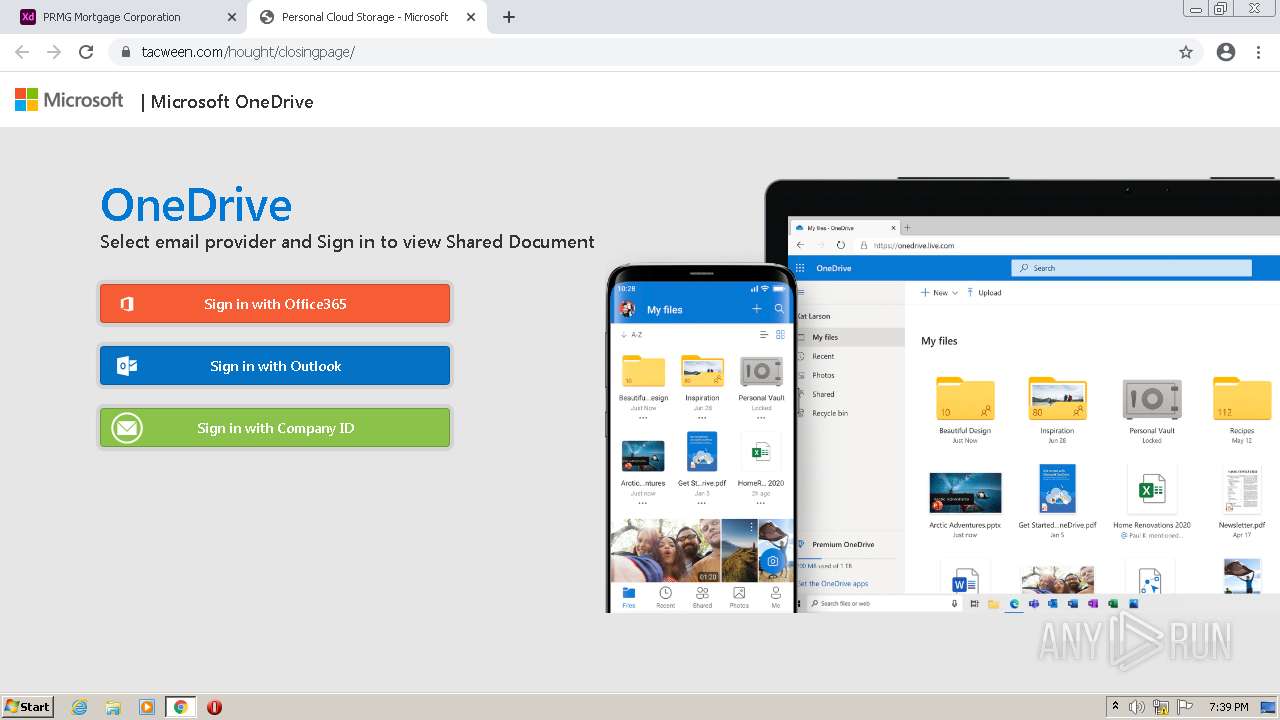
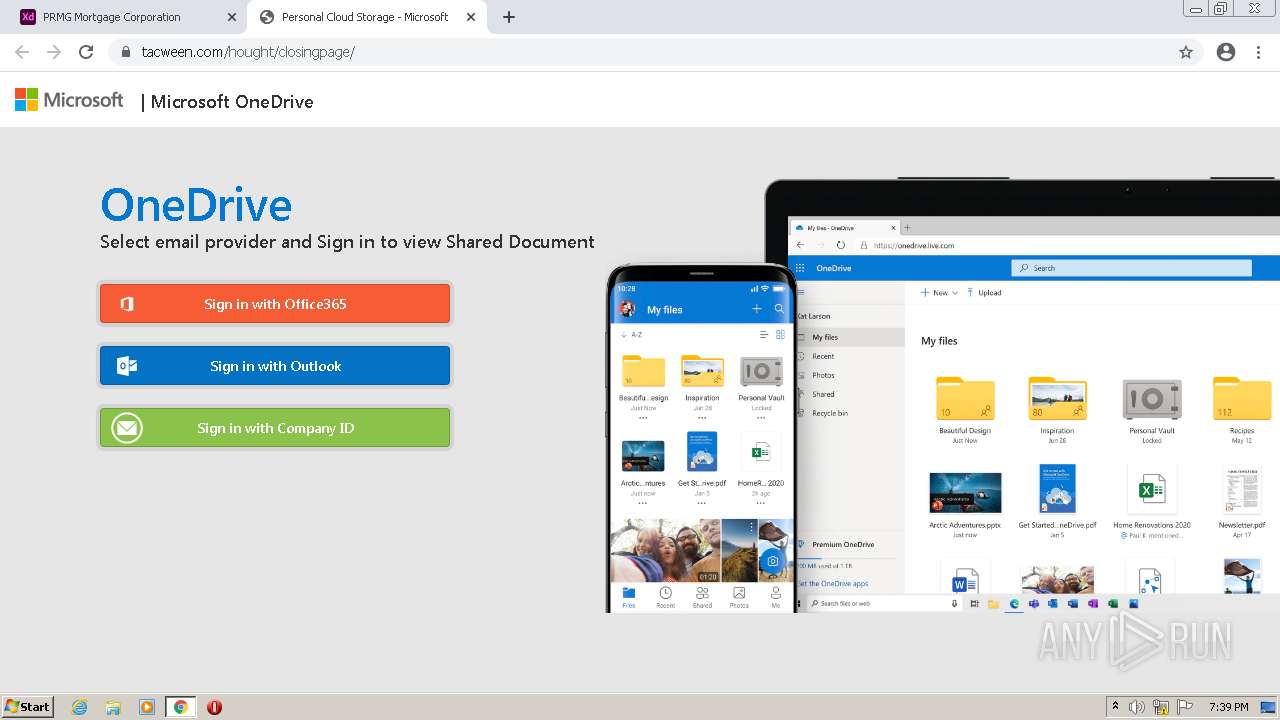
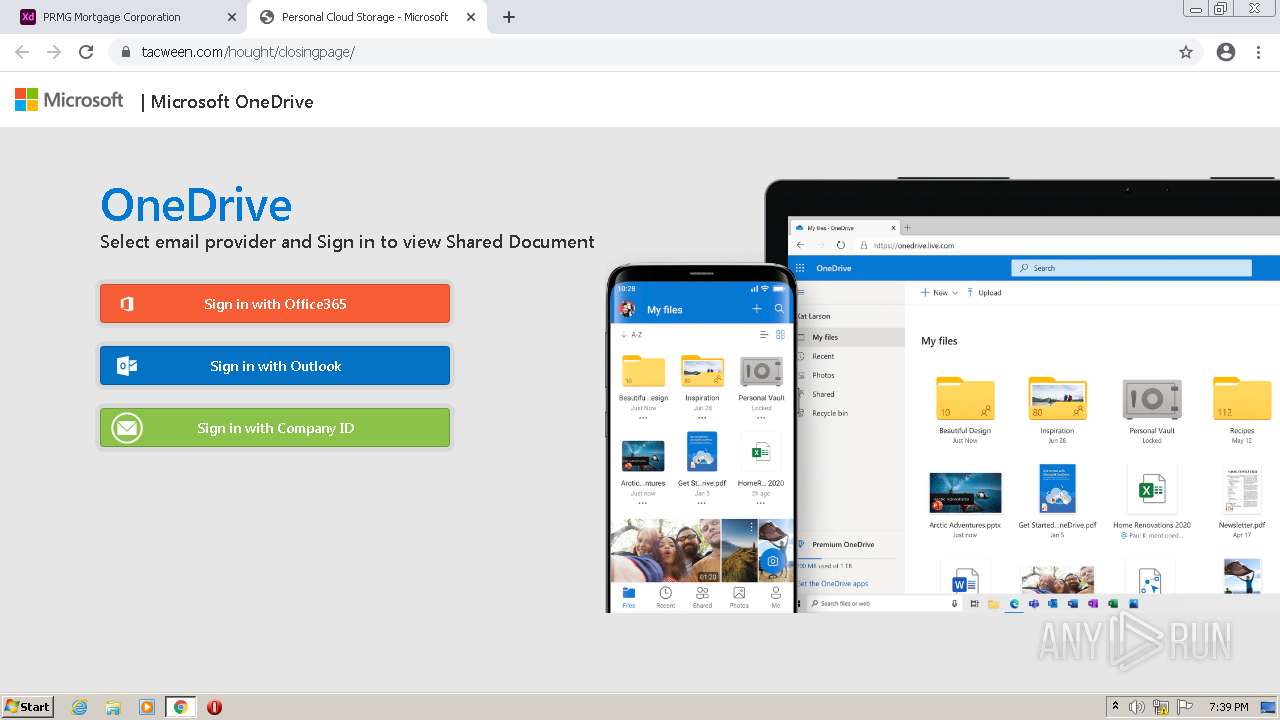
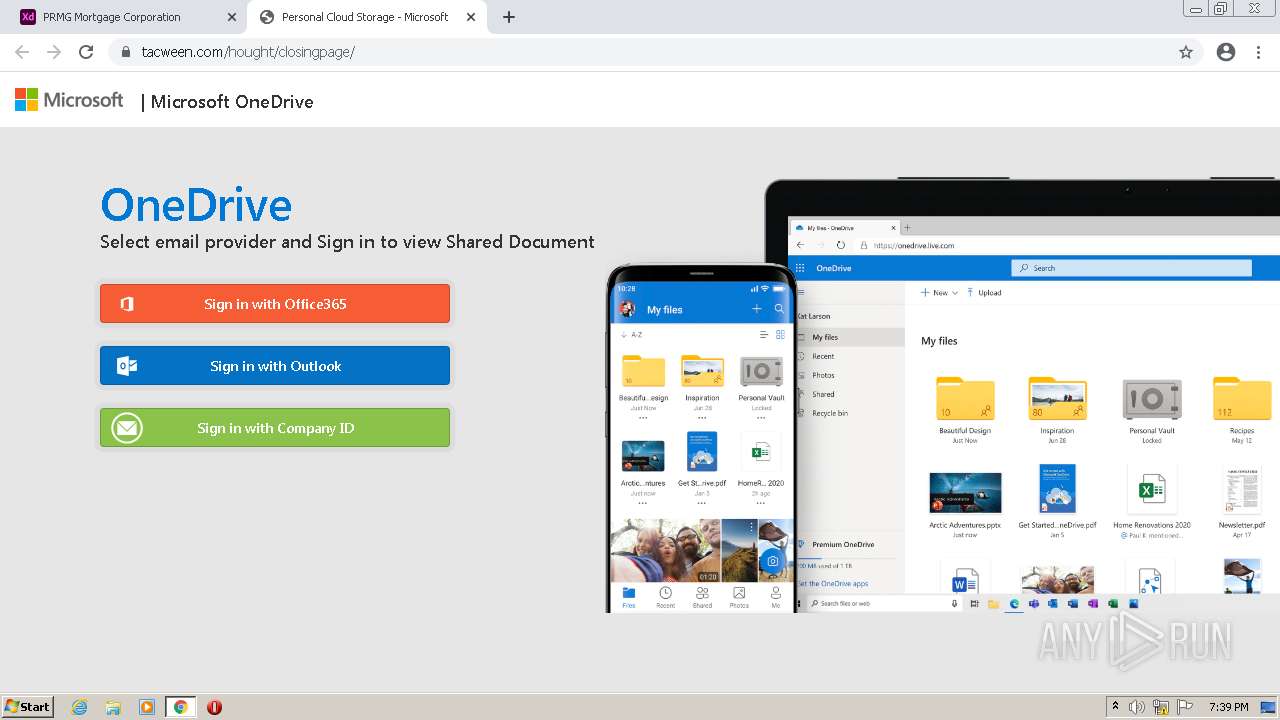
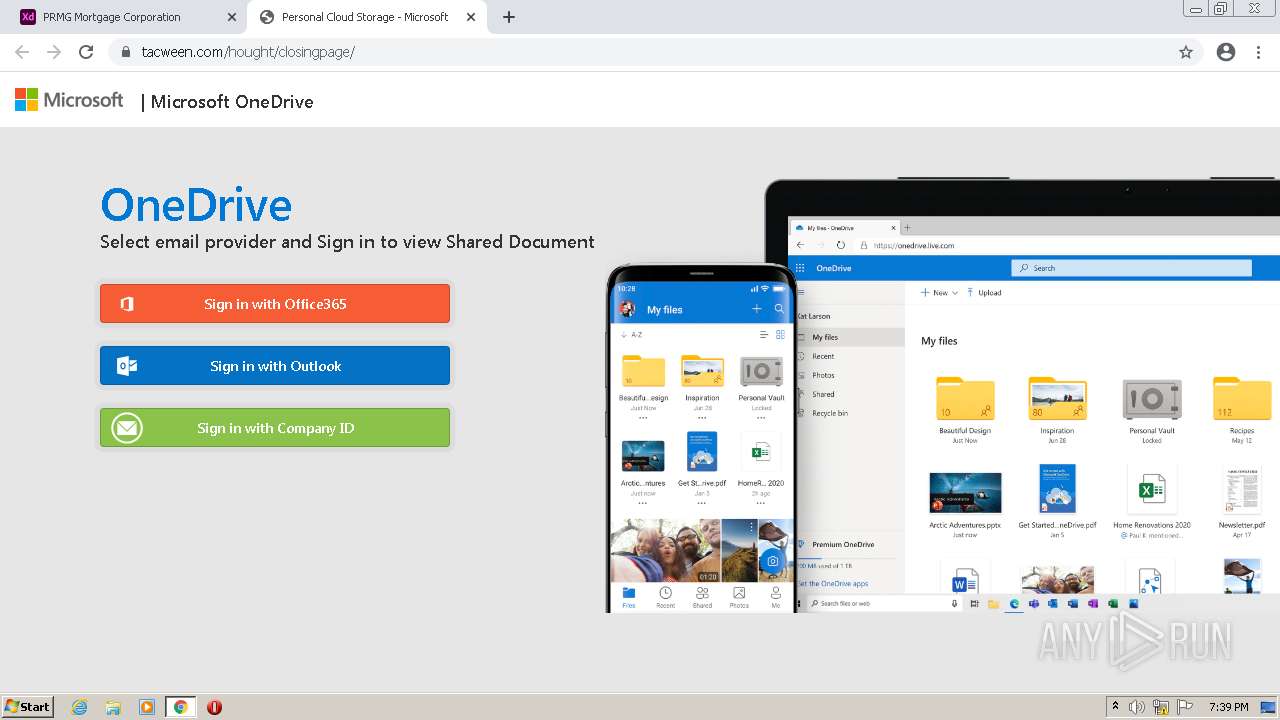
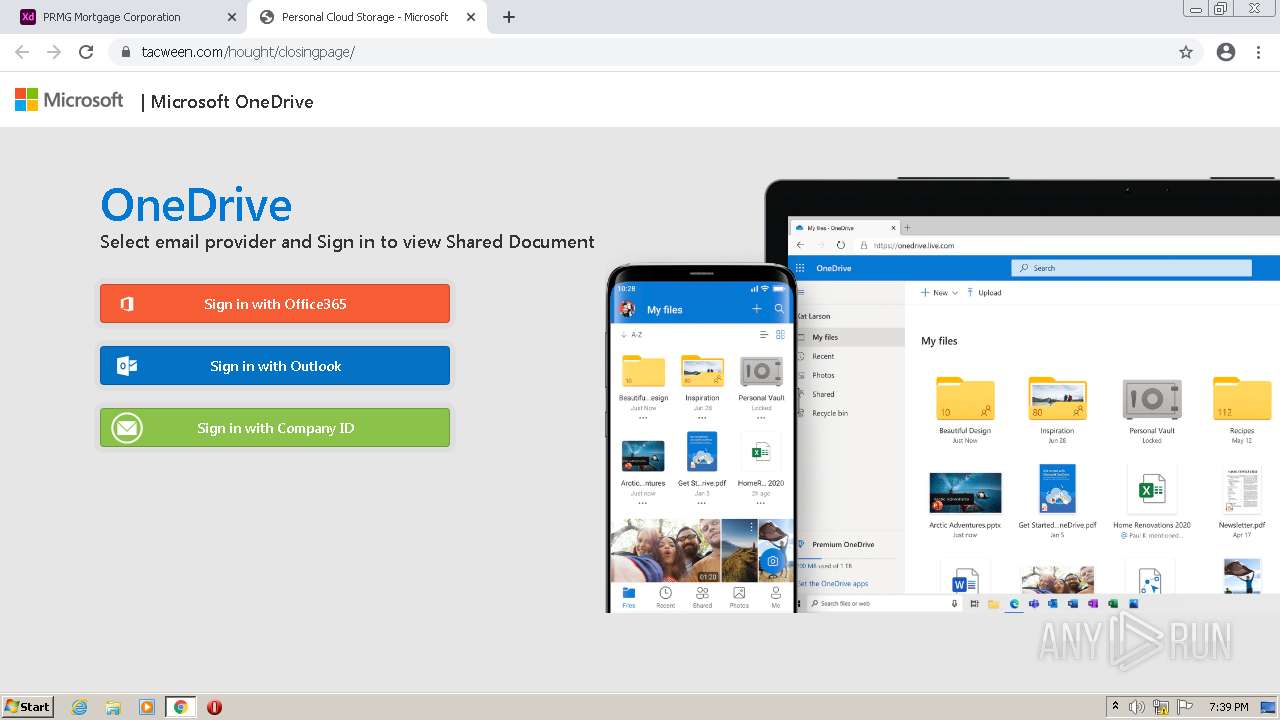
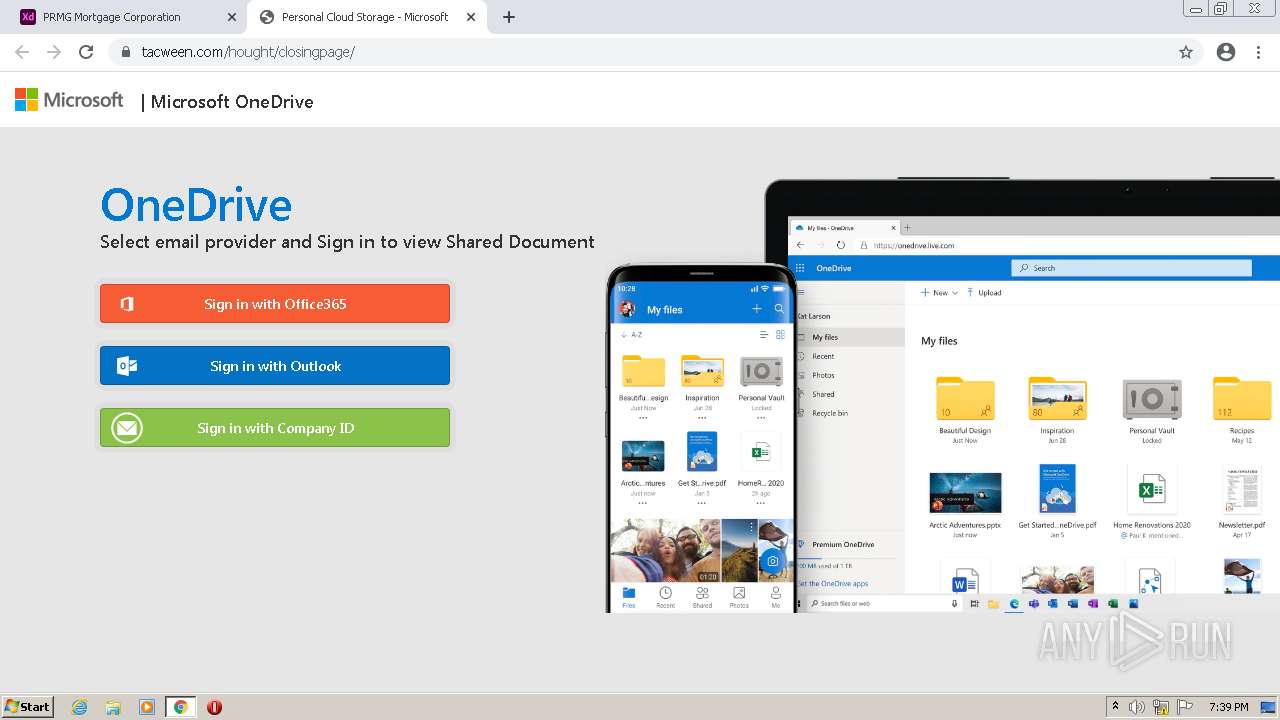
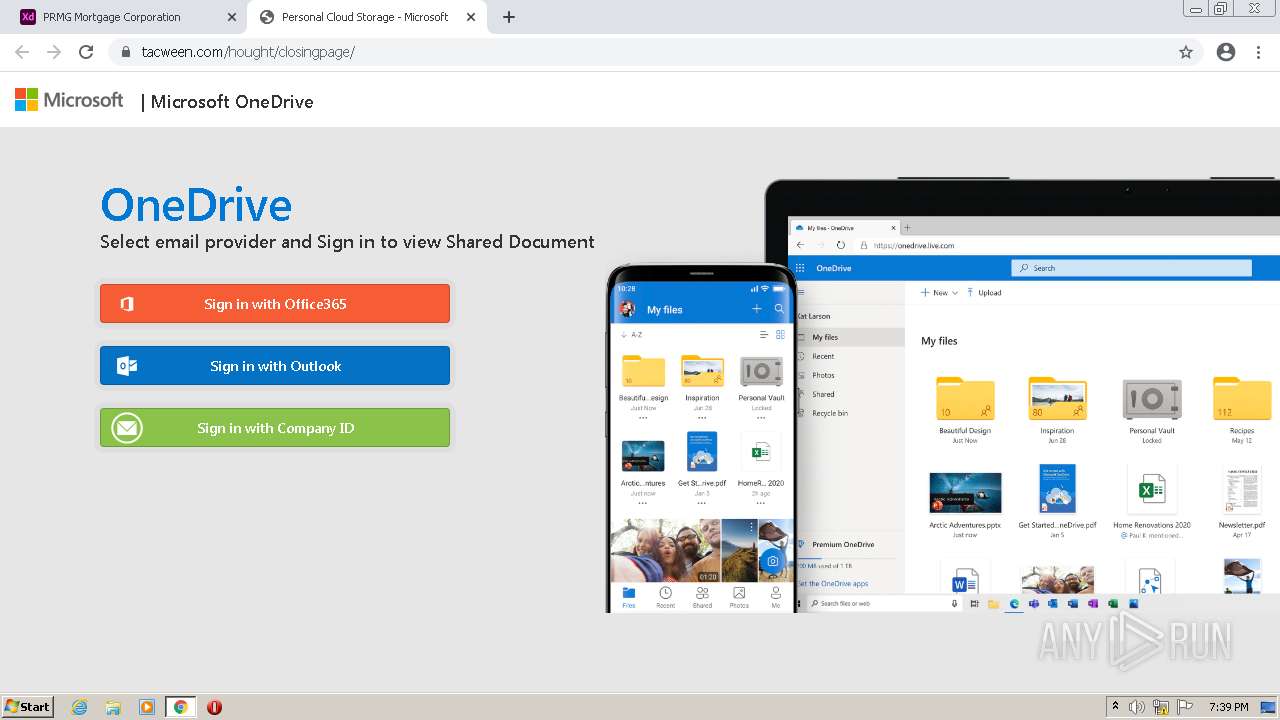
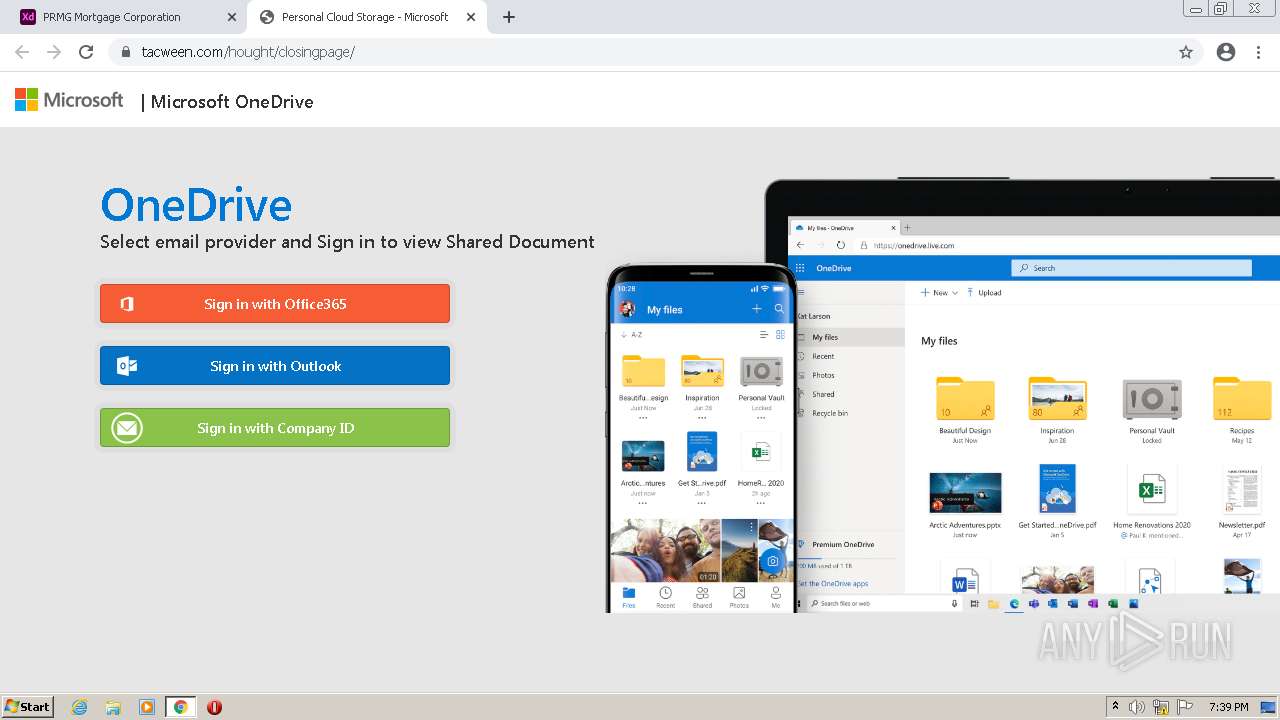
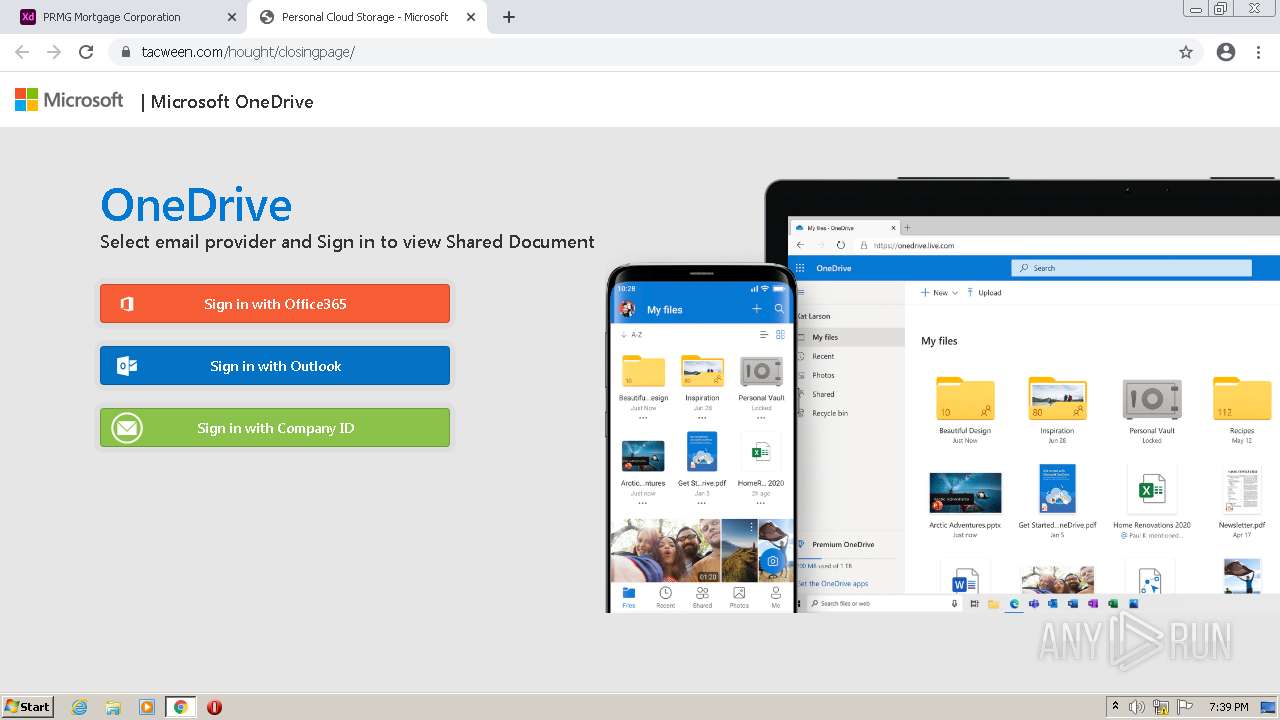
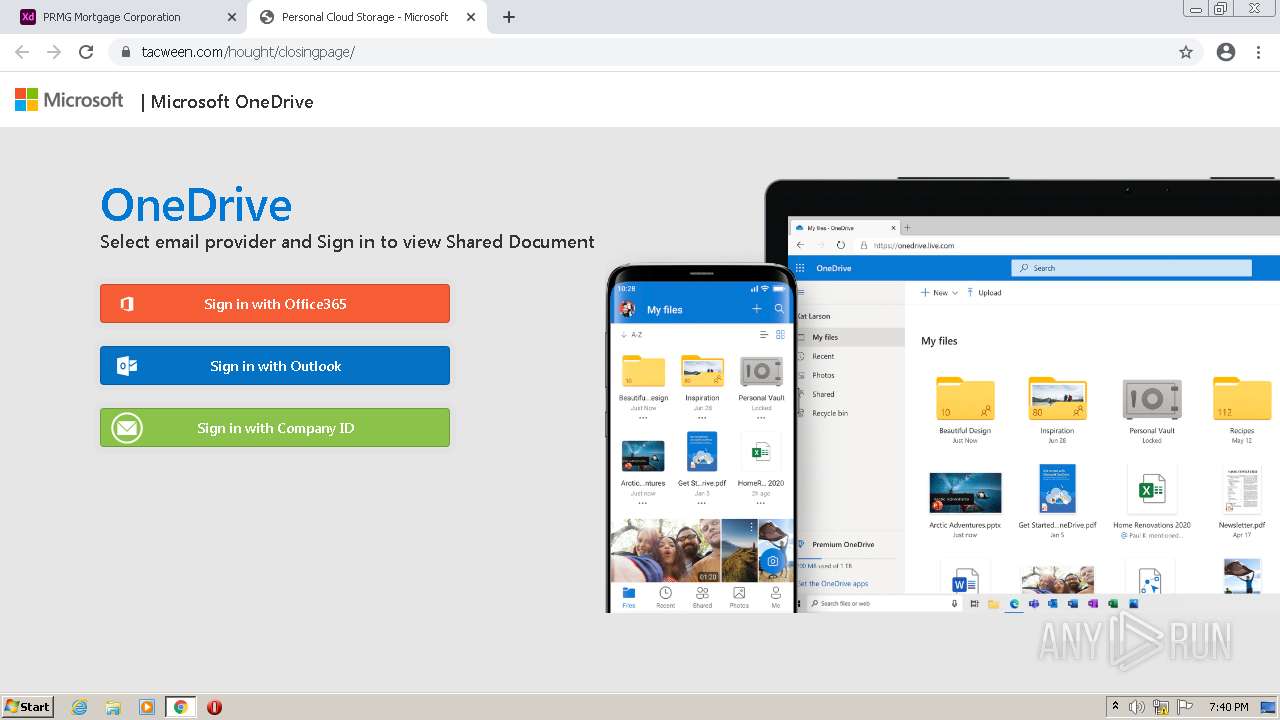
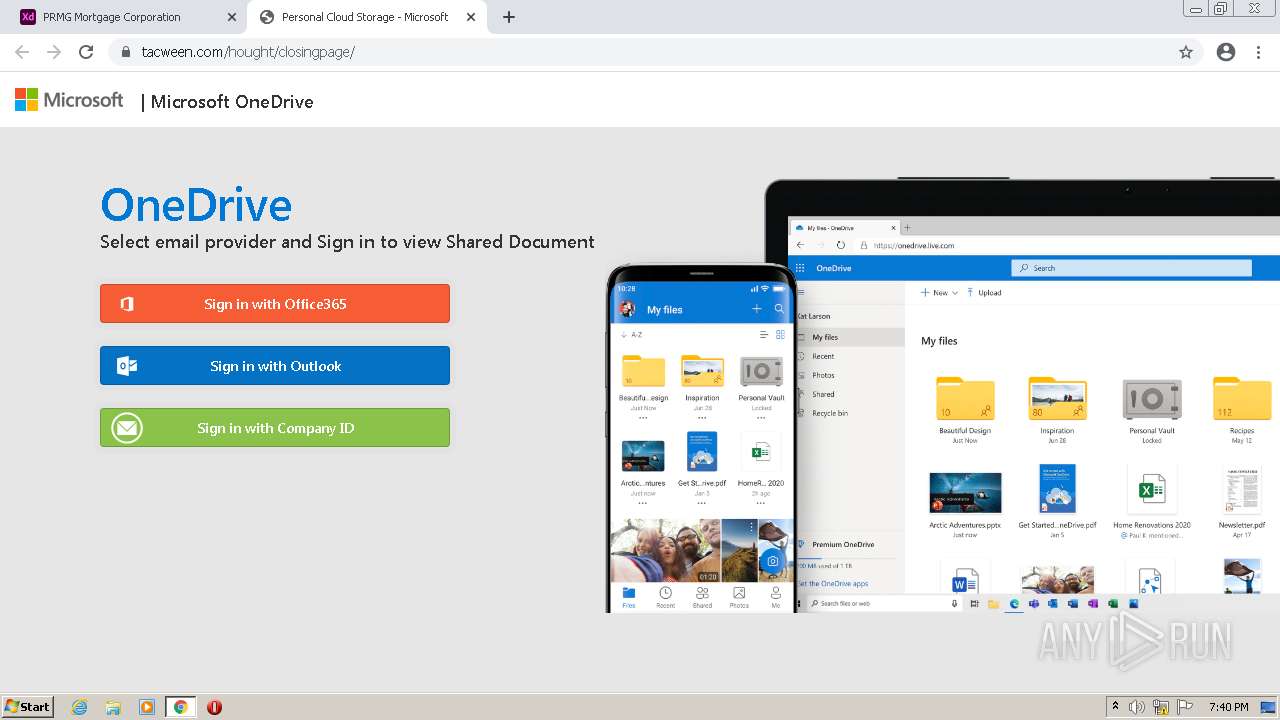
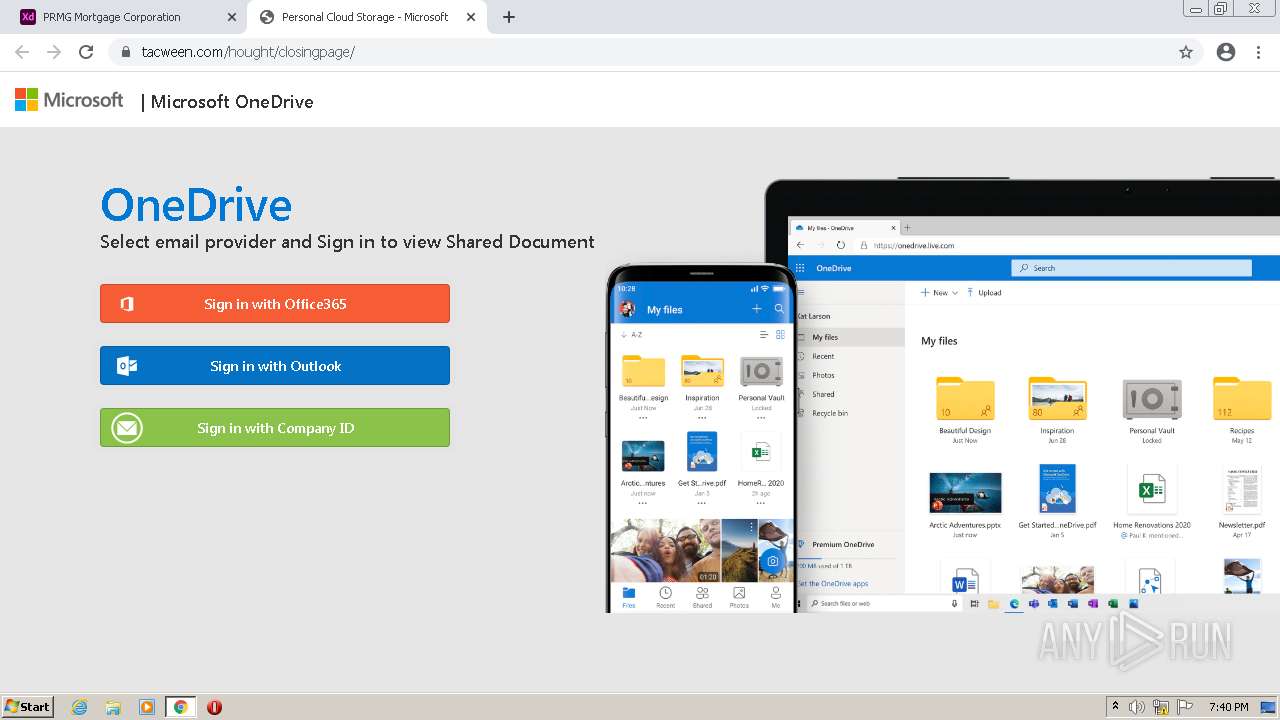
| URL: | https://xd.adobe.com/view/b9efc2bf-17b3-4e5c-992c-15563dd79491-ecbc/?fullscreen&hints=off |
| Full analysis: | https://app.any.run/tasks/d6c34f2f-5e7f-461f-a7b6-1dd95c7fba65 |
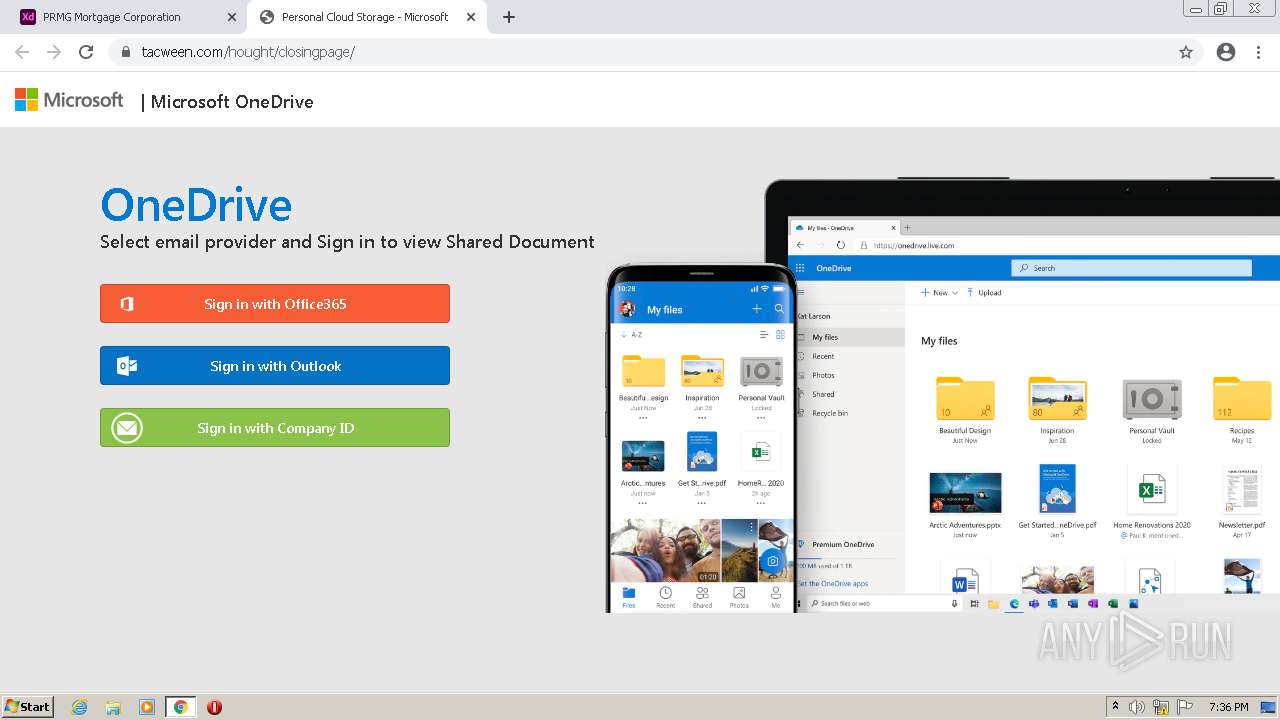
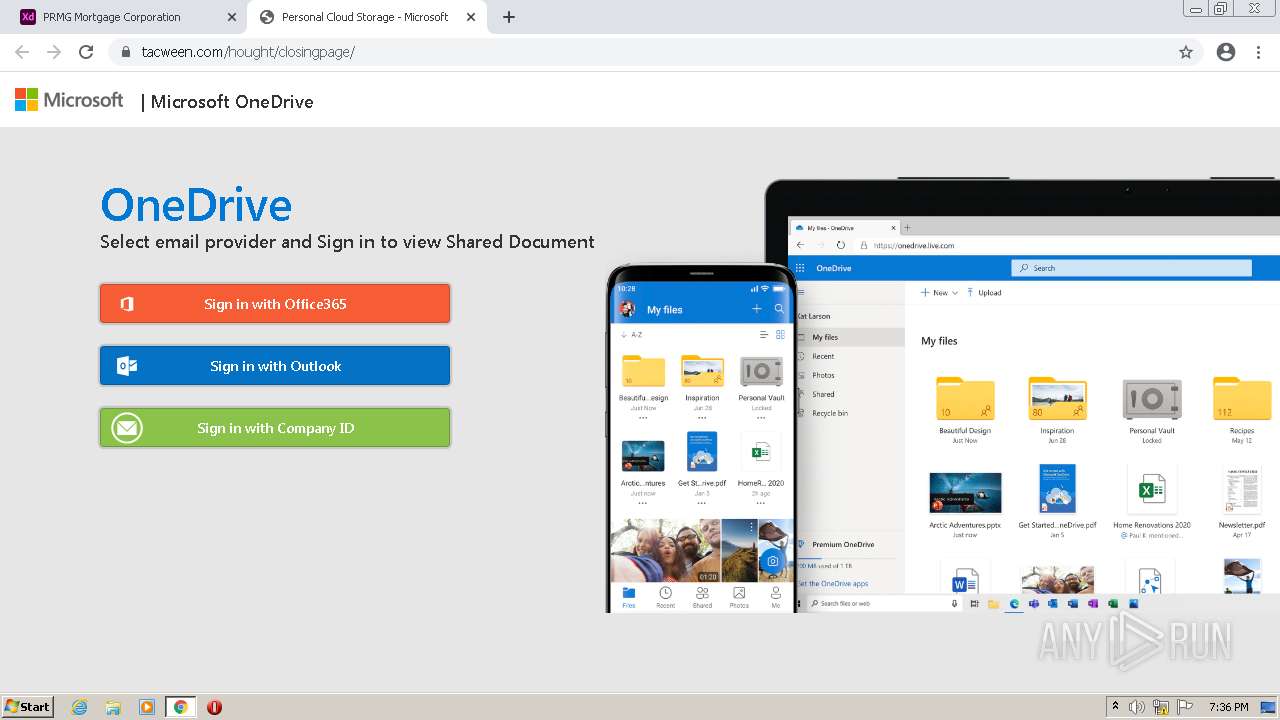
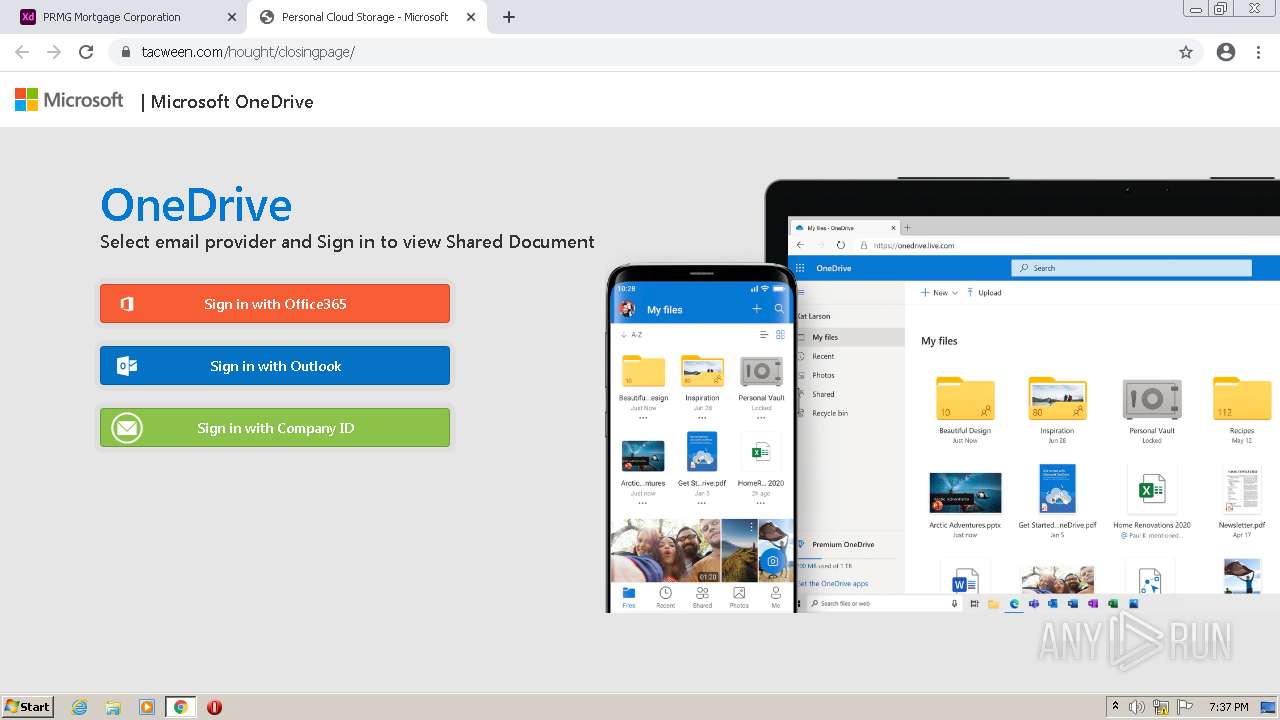
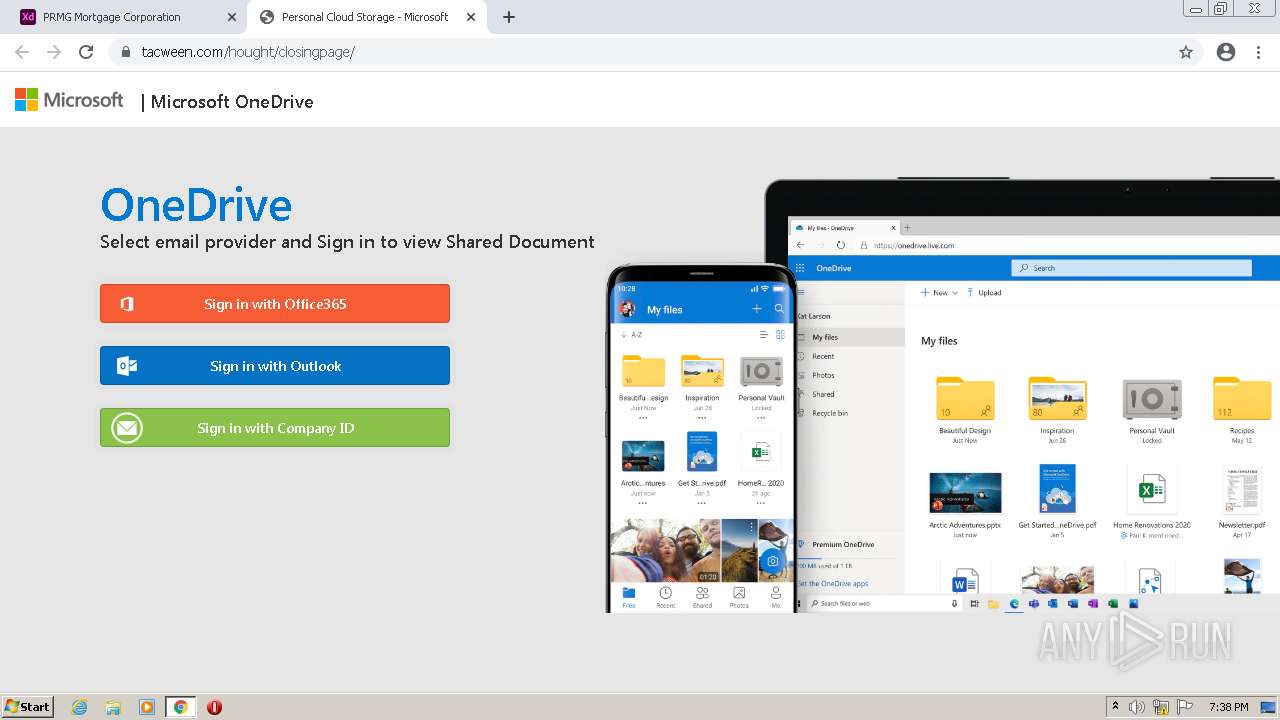
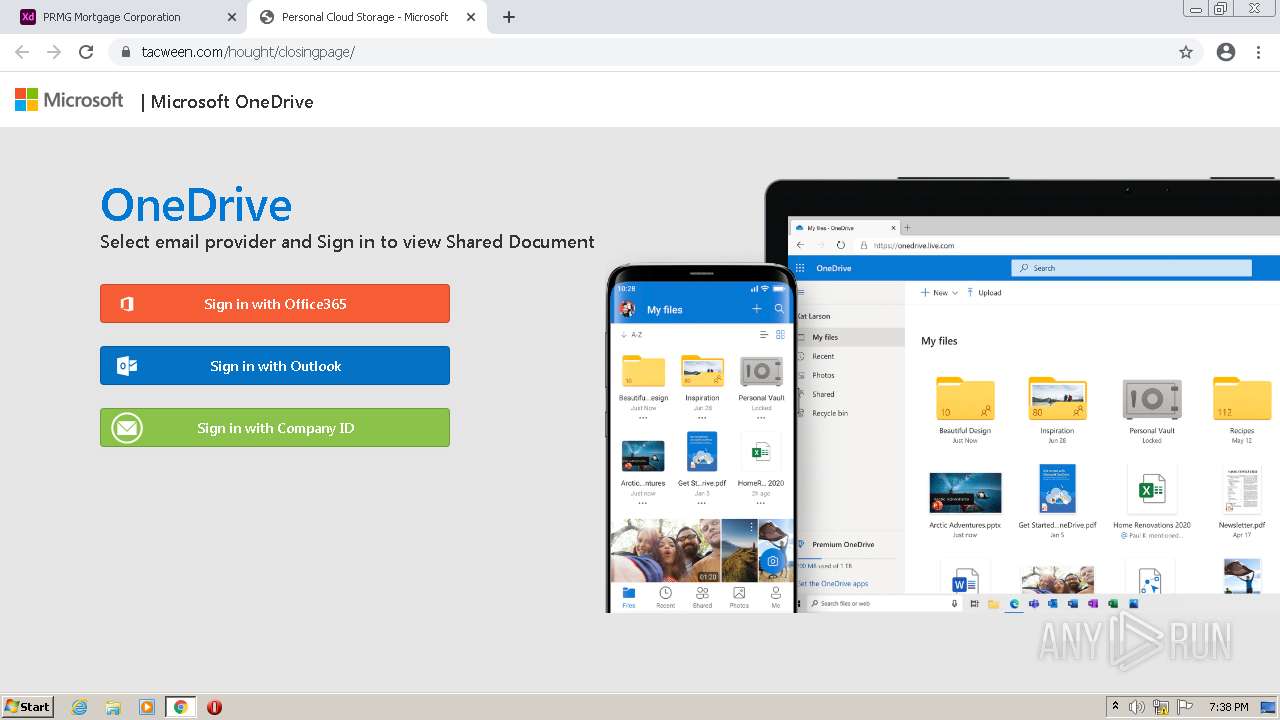
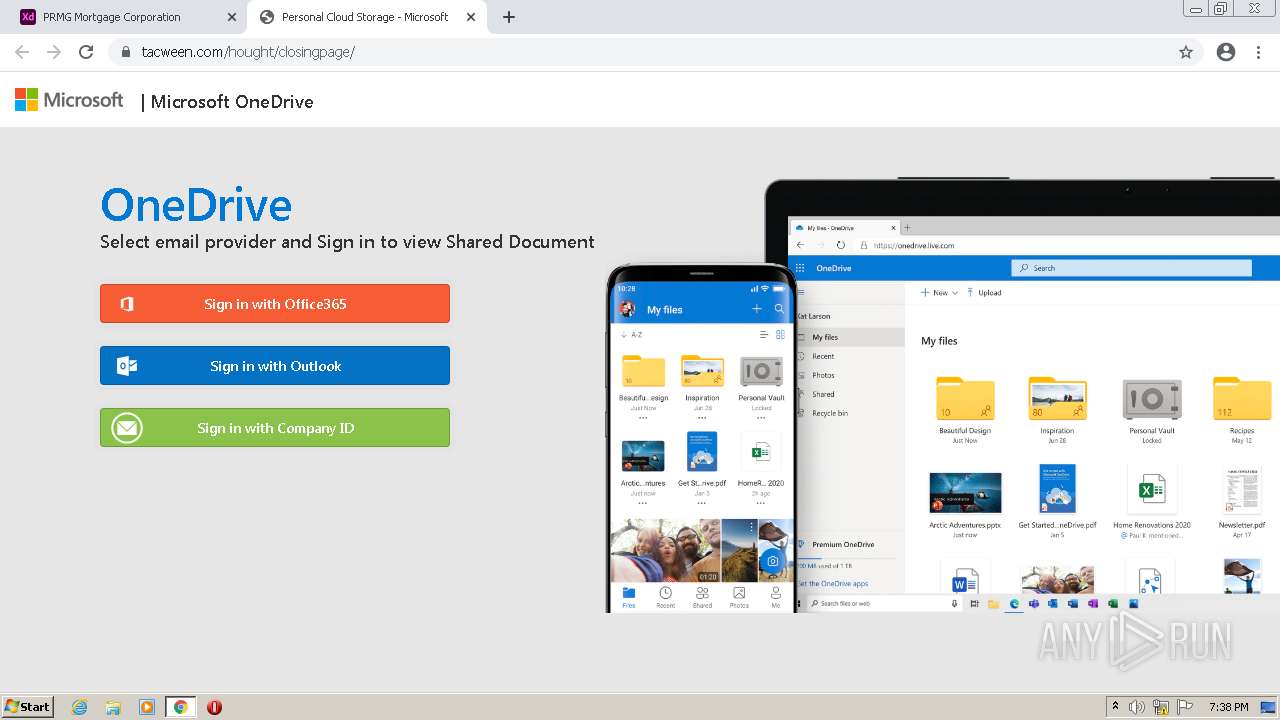
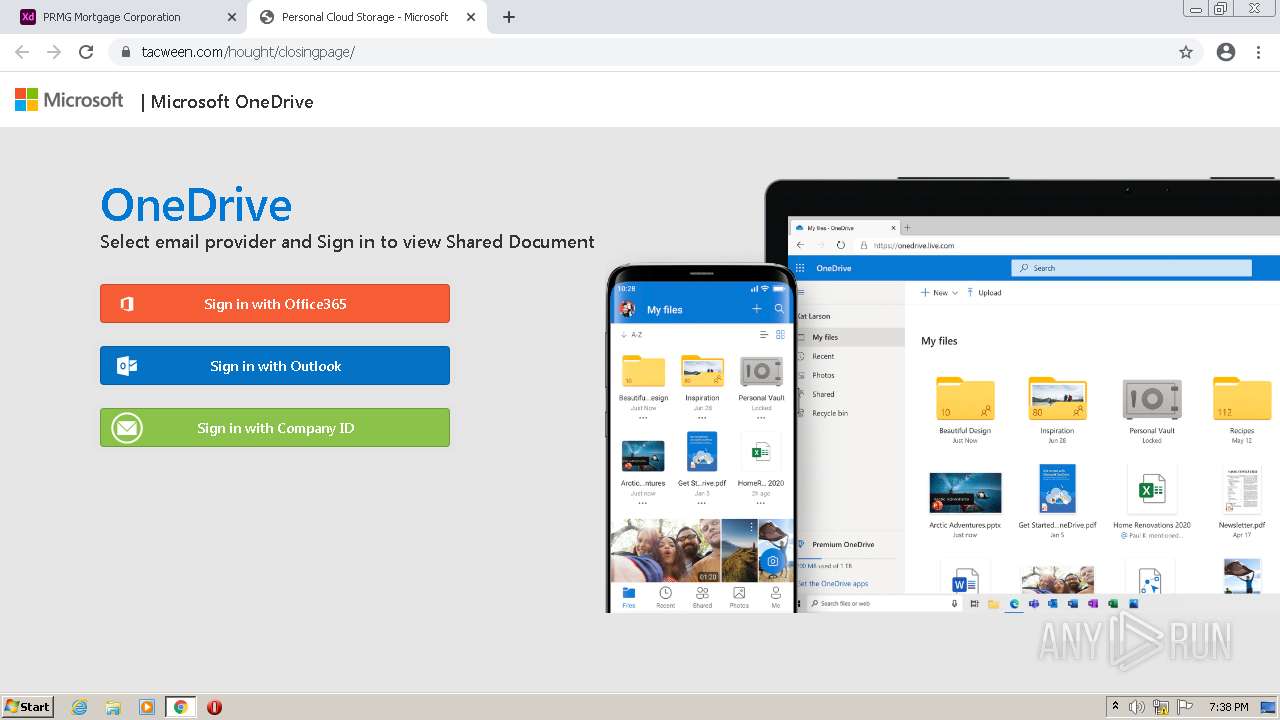
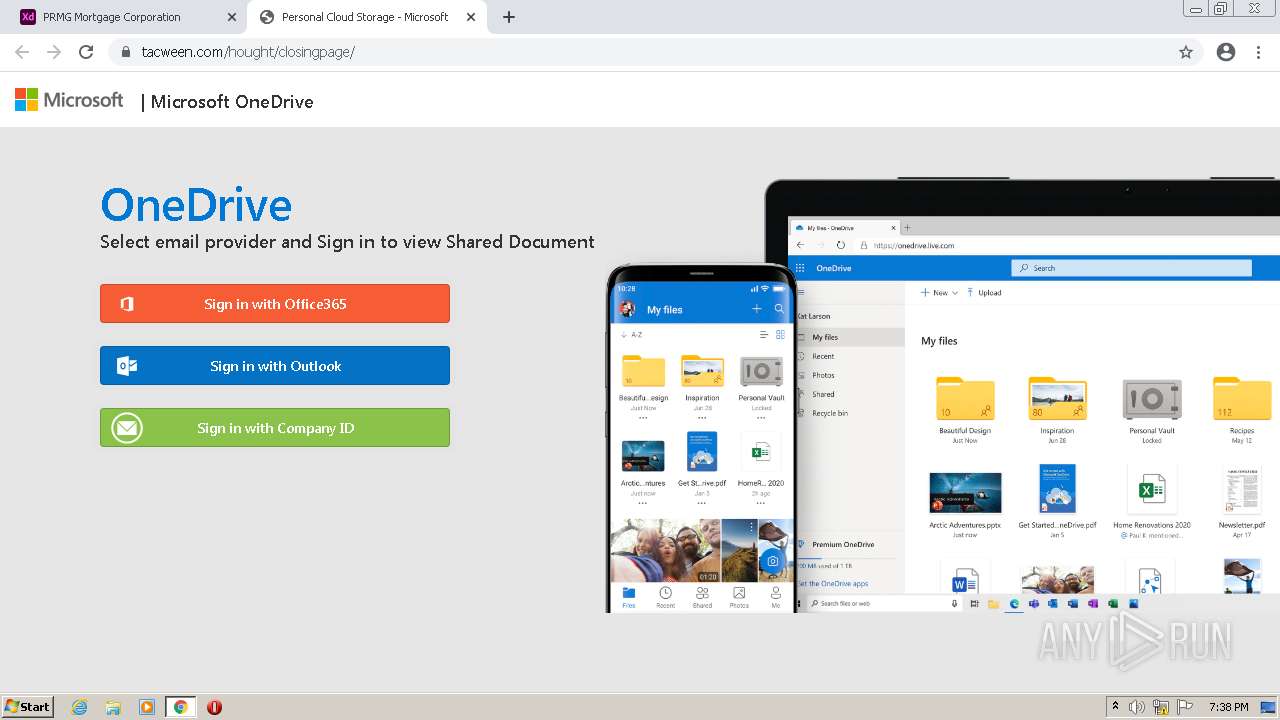
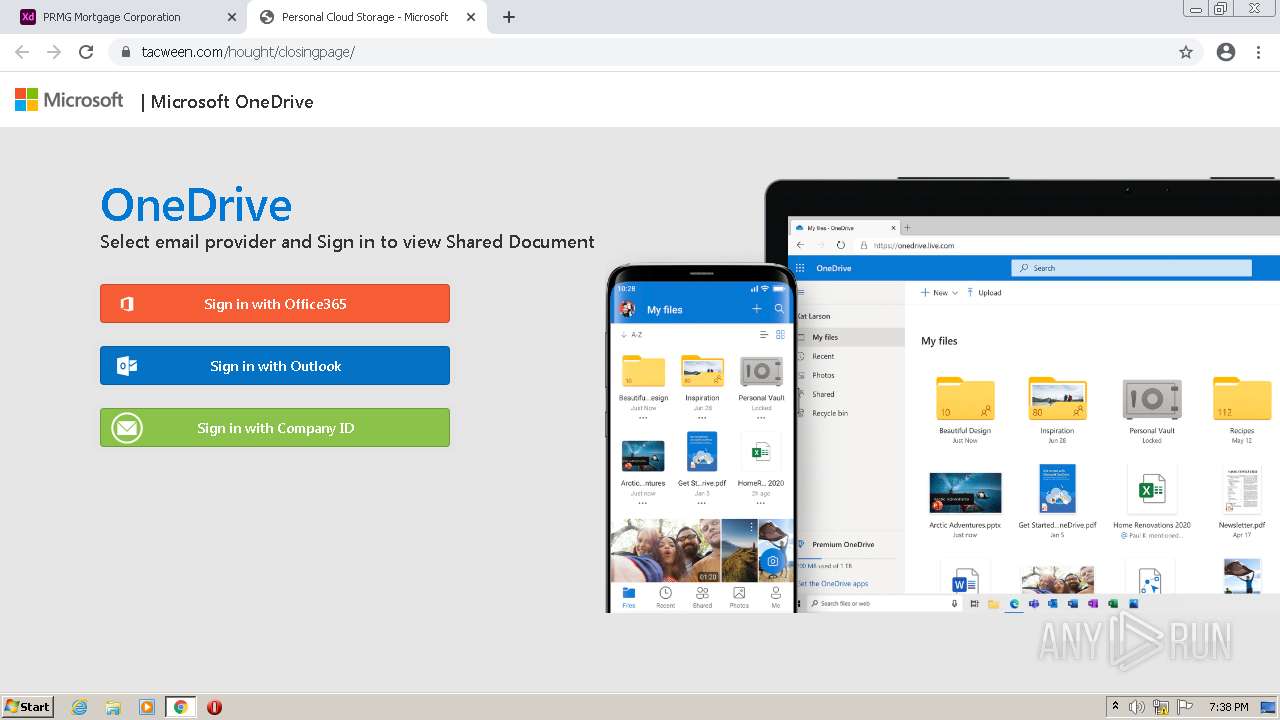
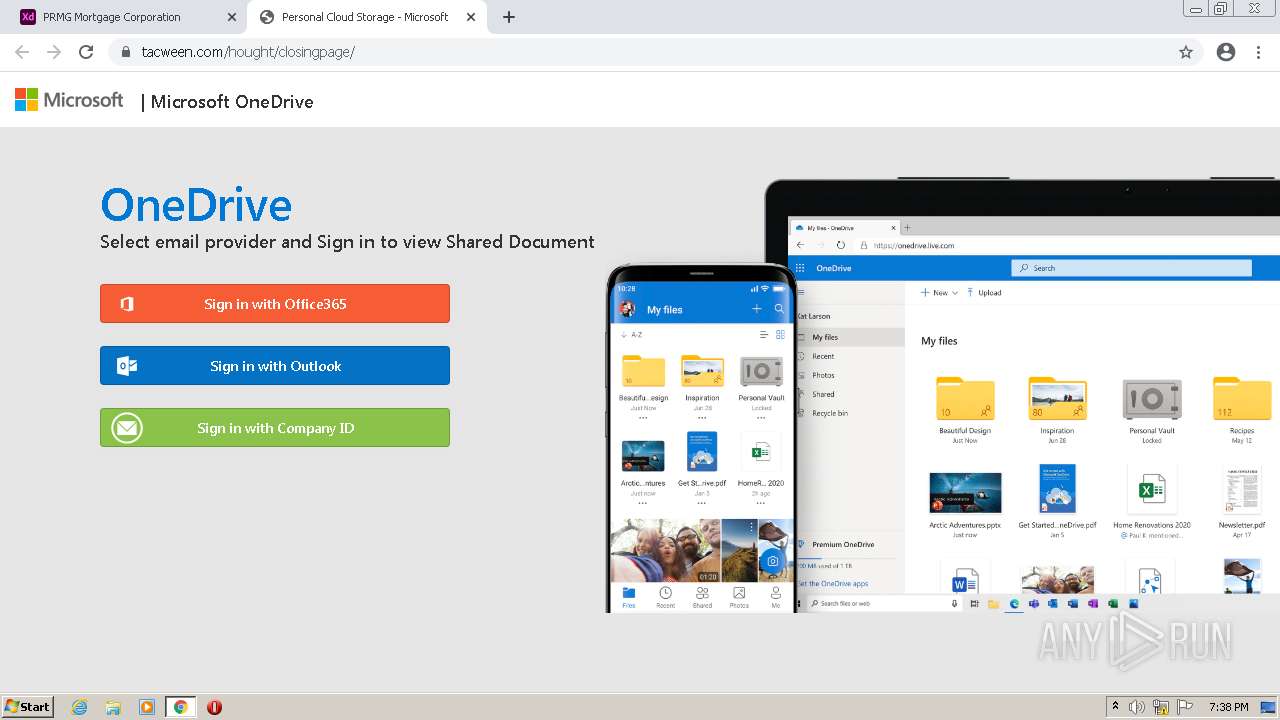
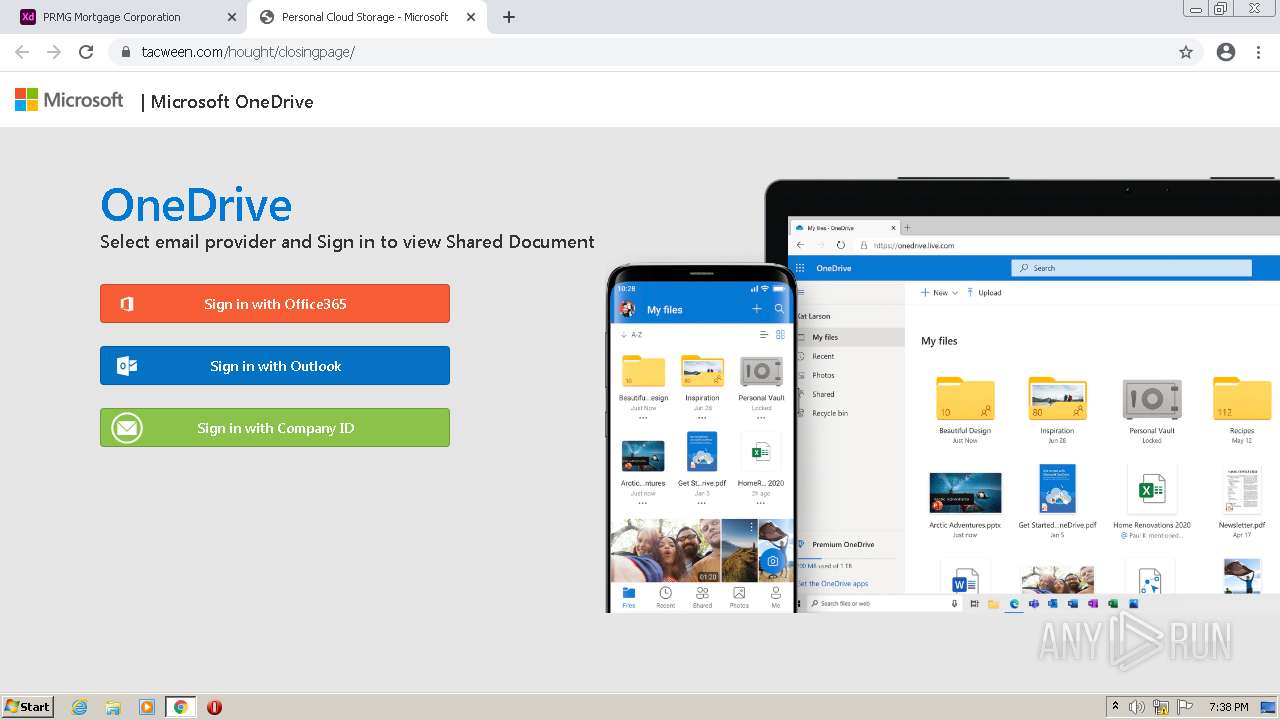
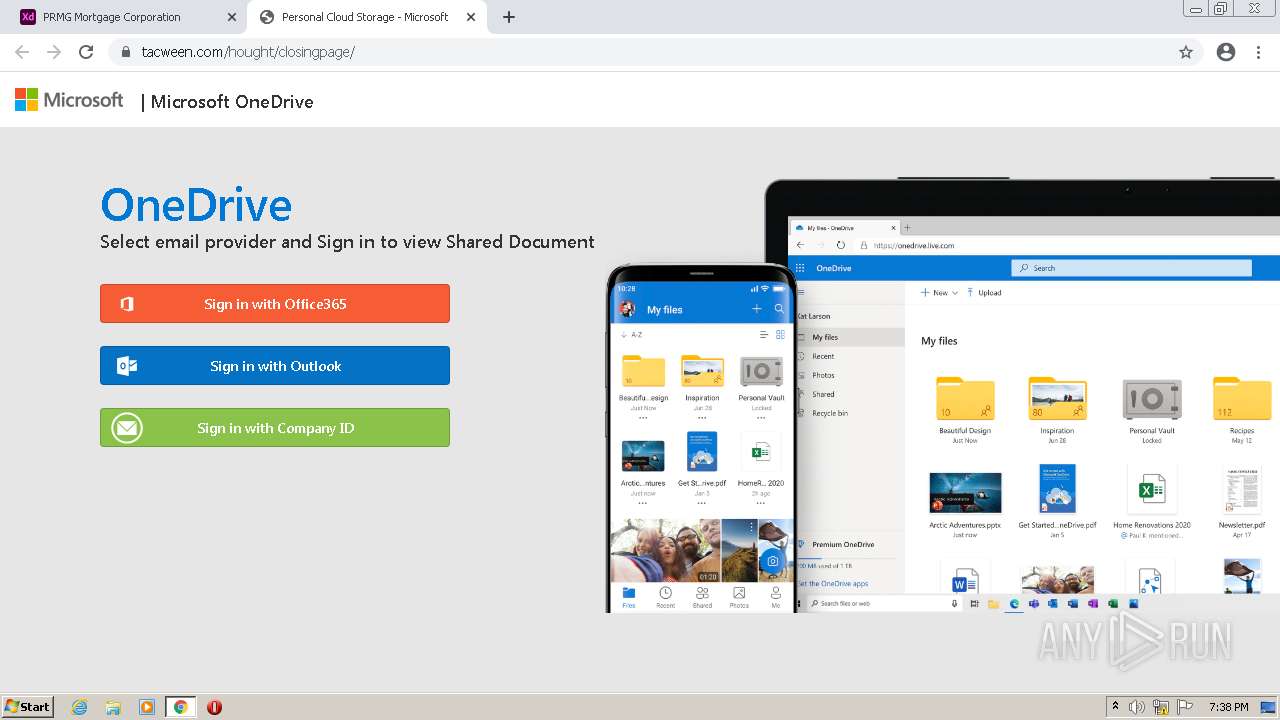
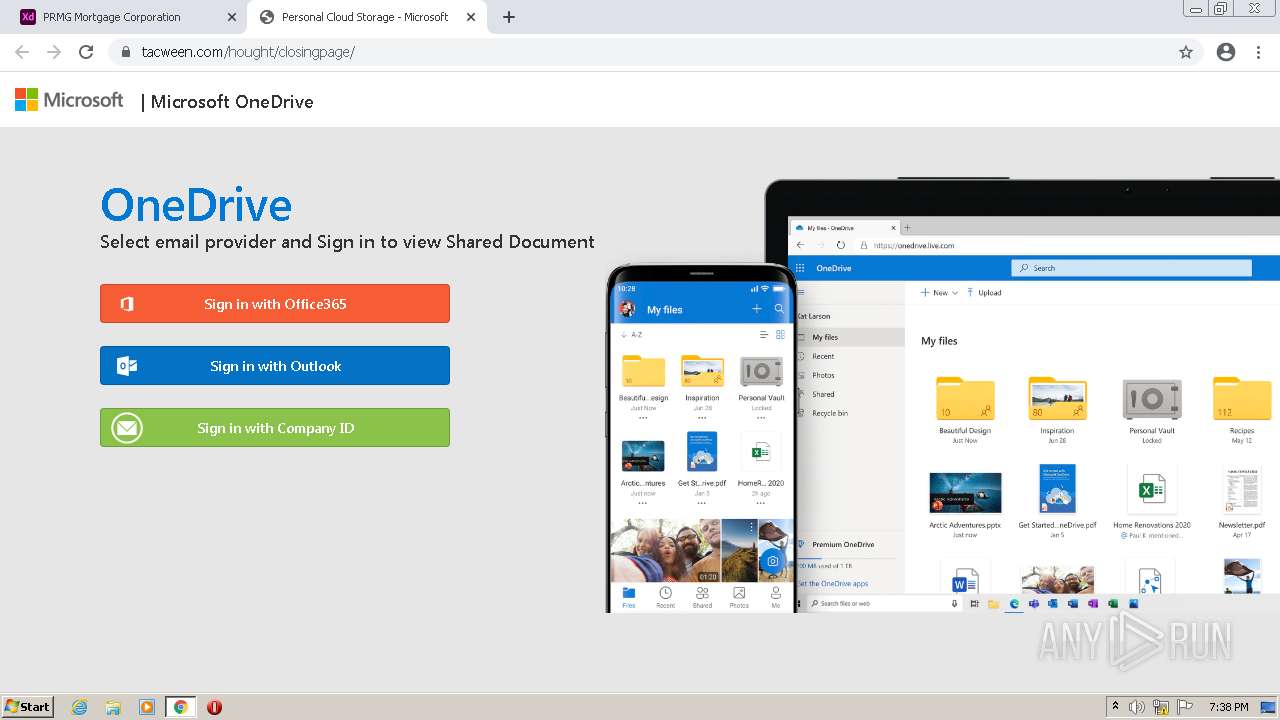
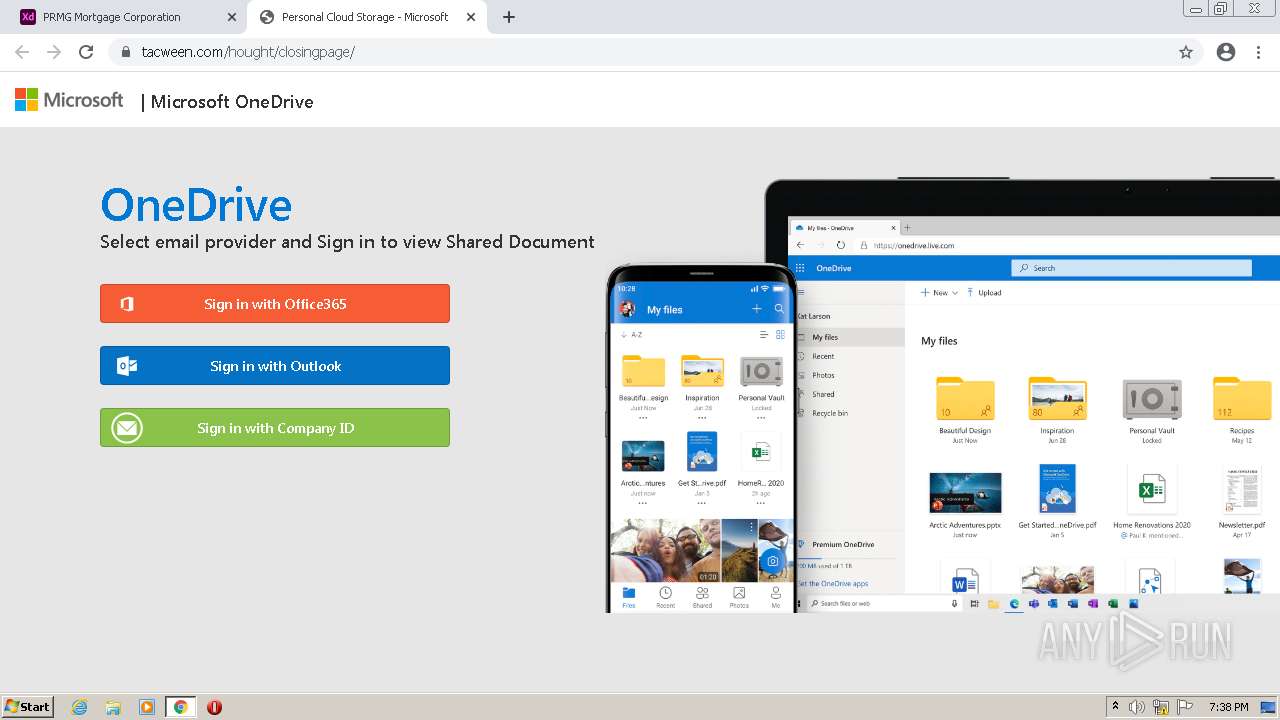
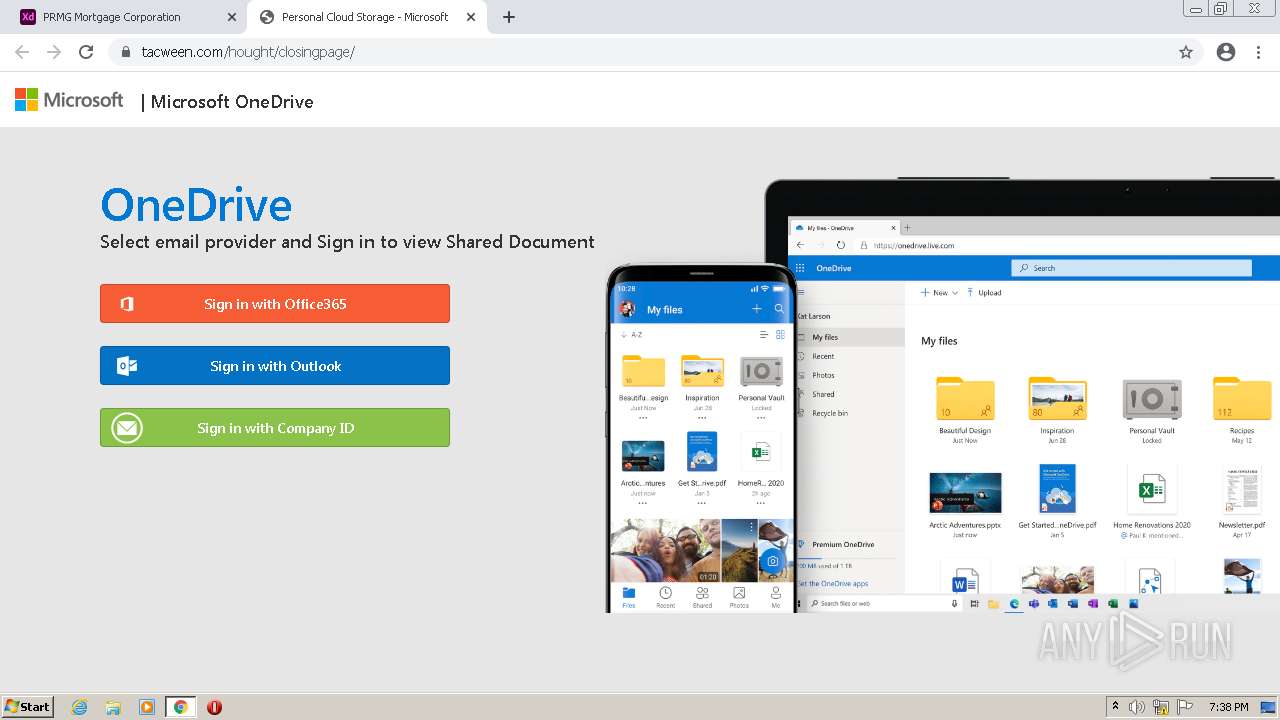
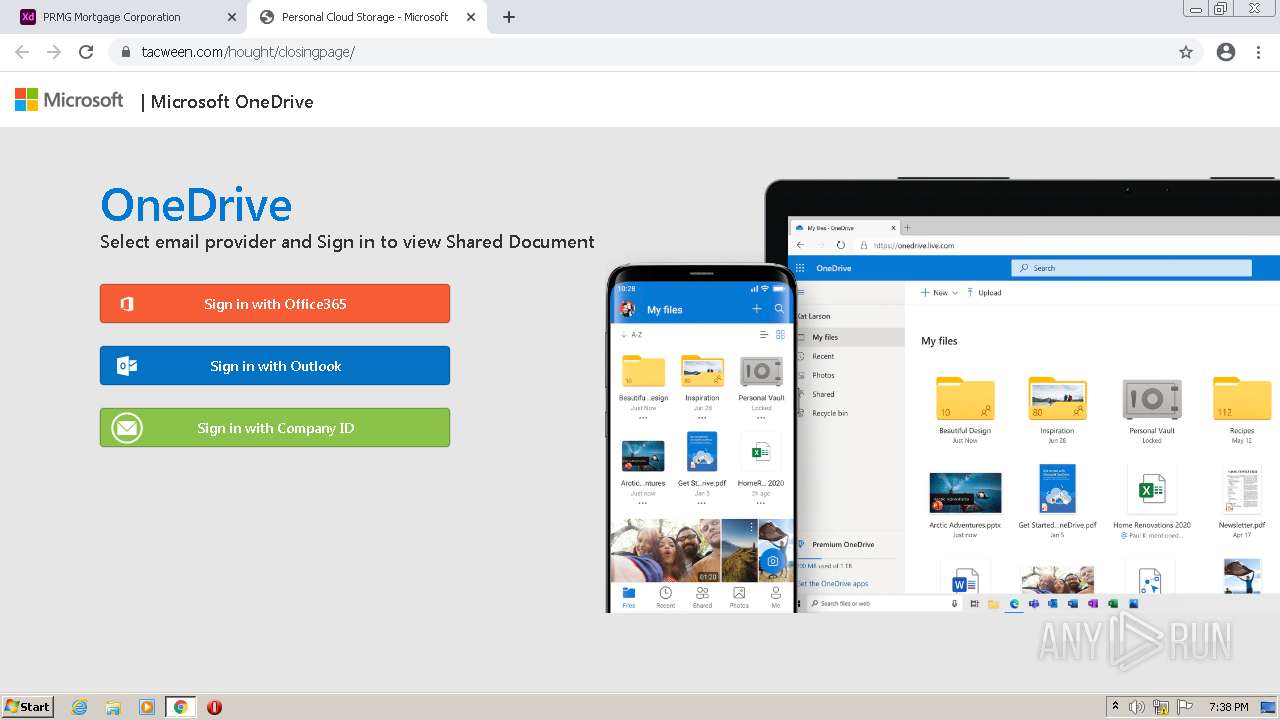
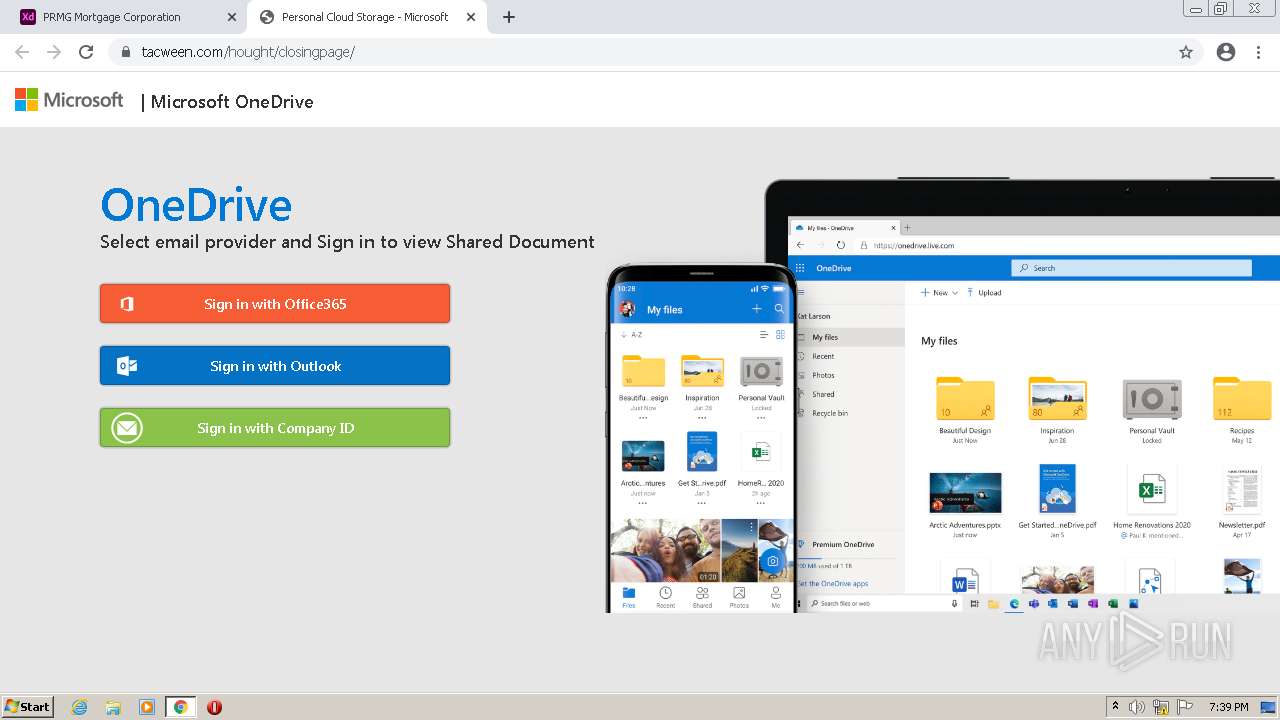
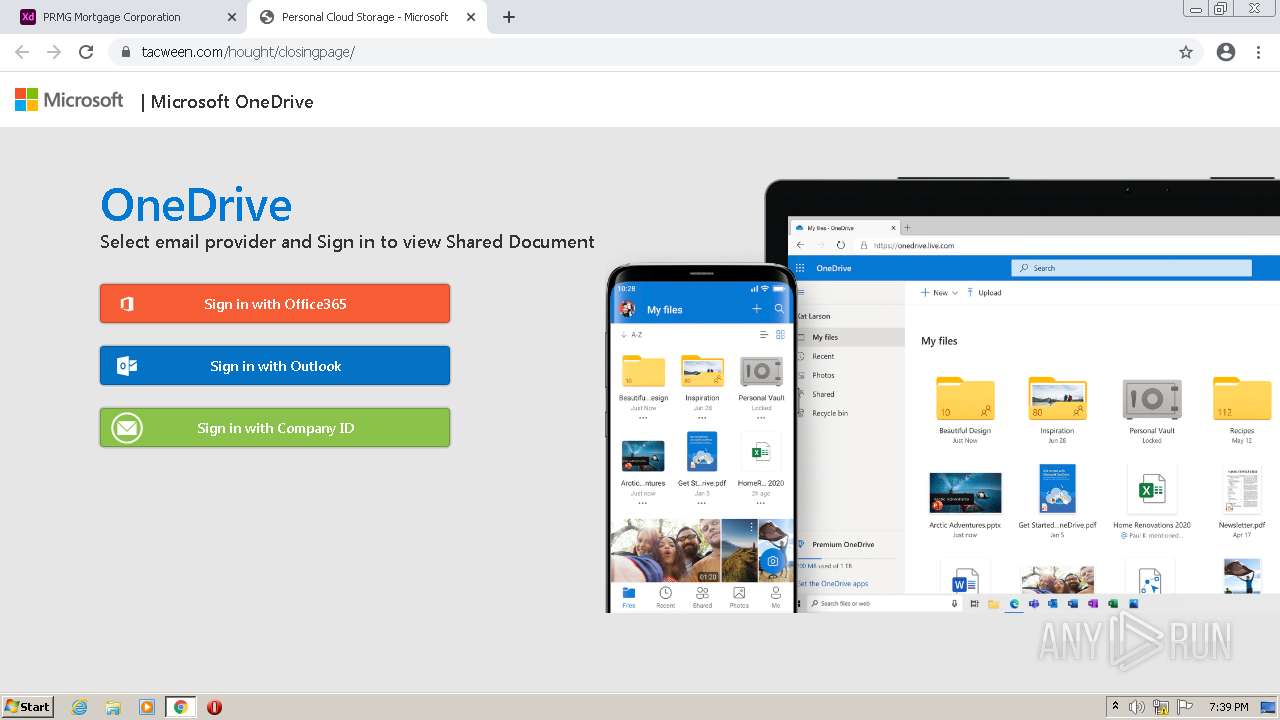
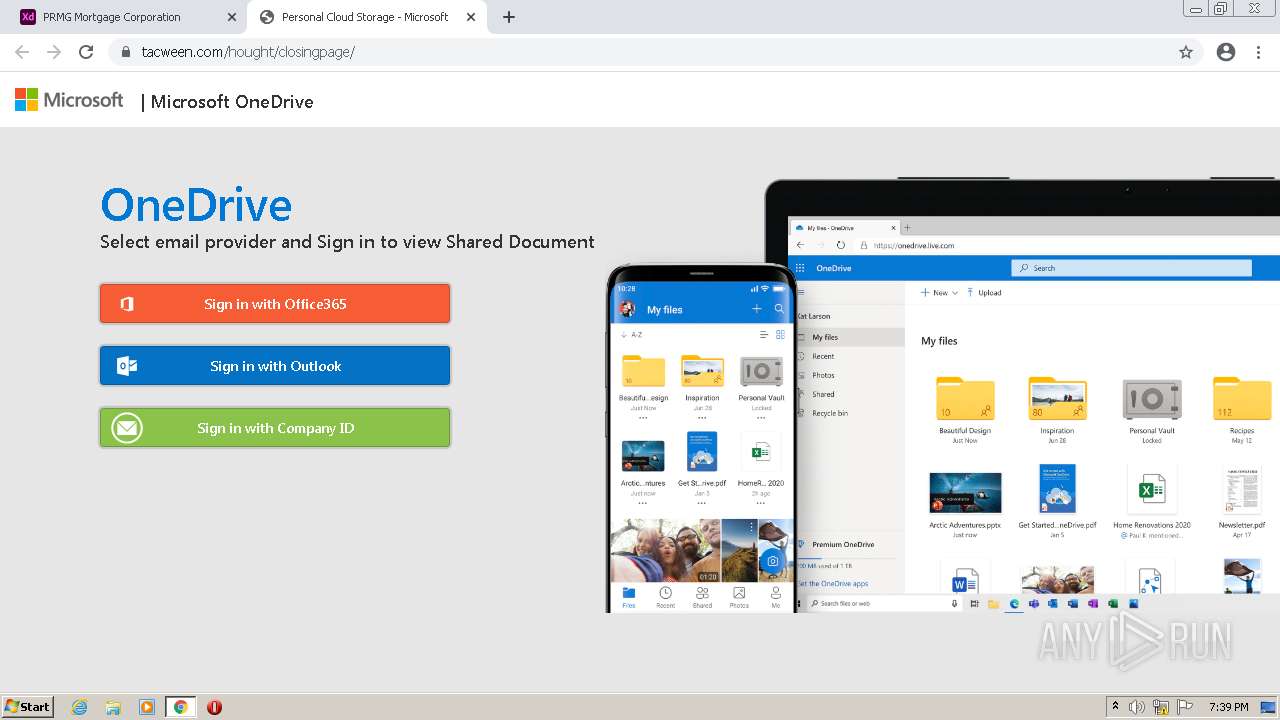
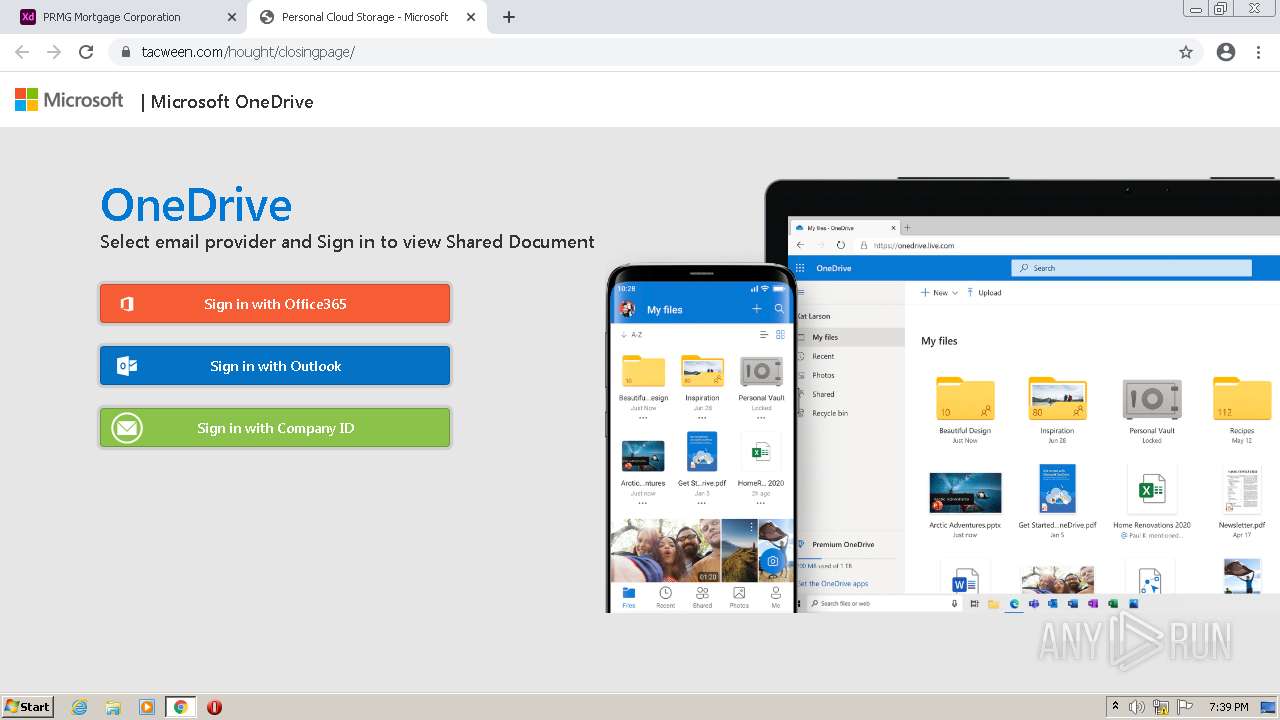
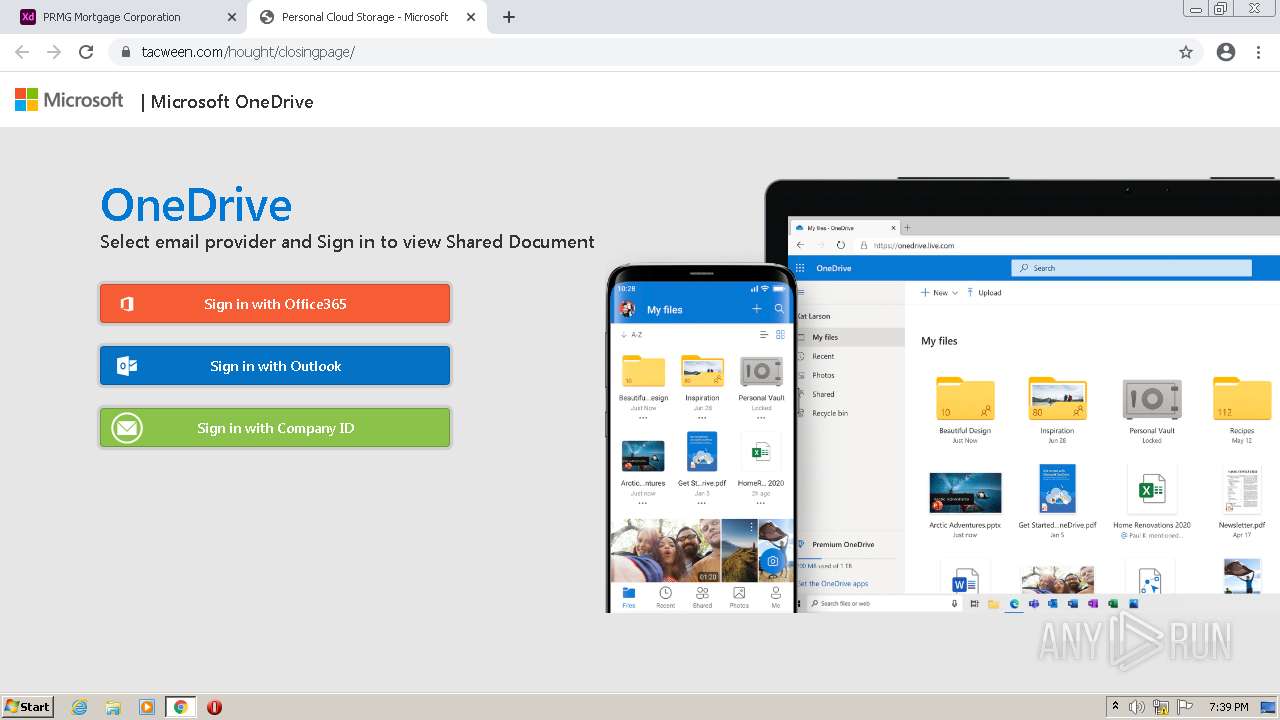
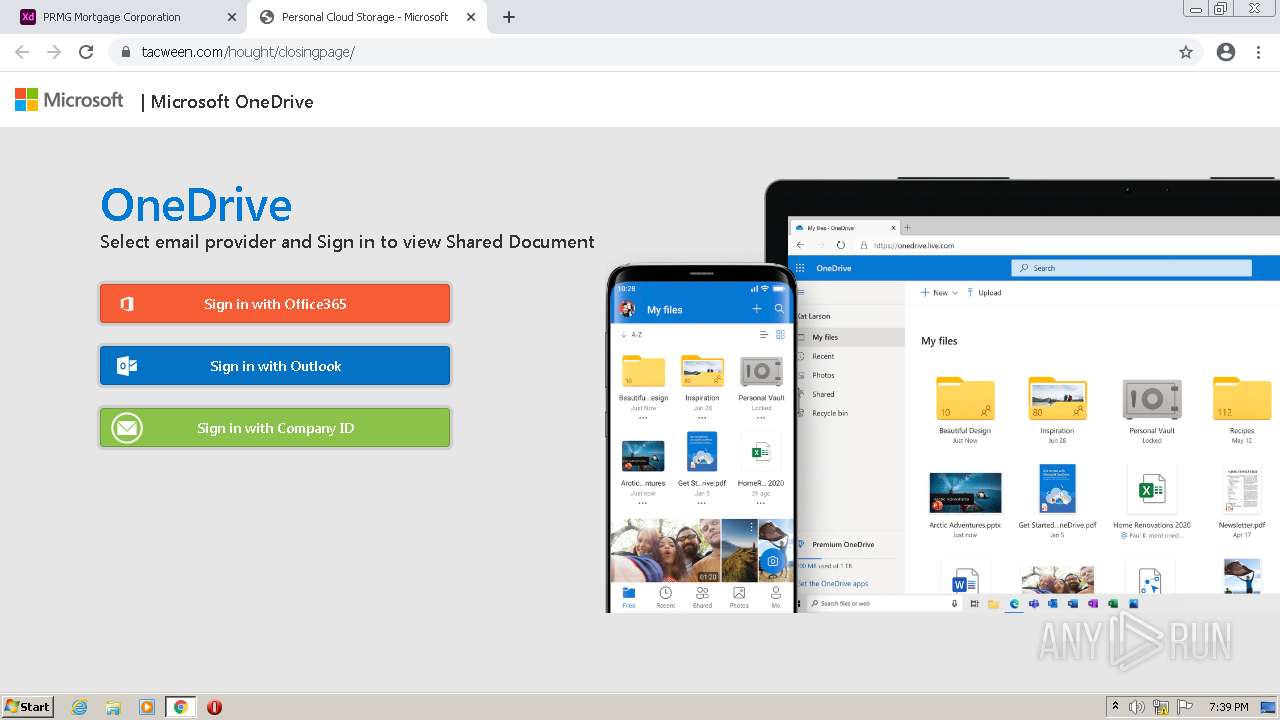
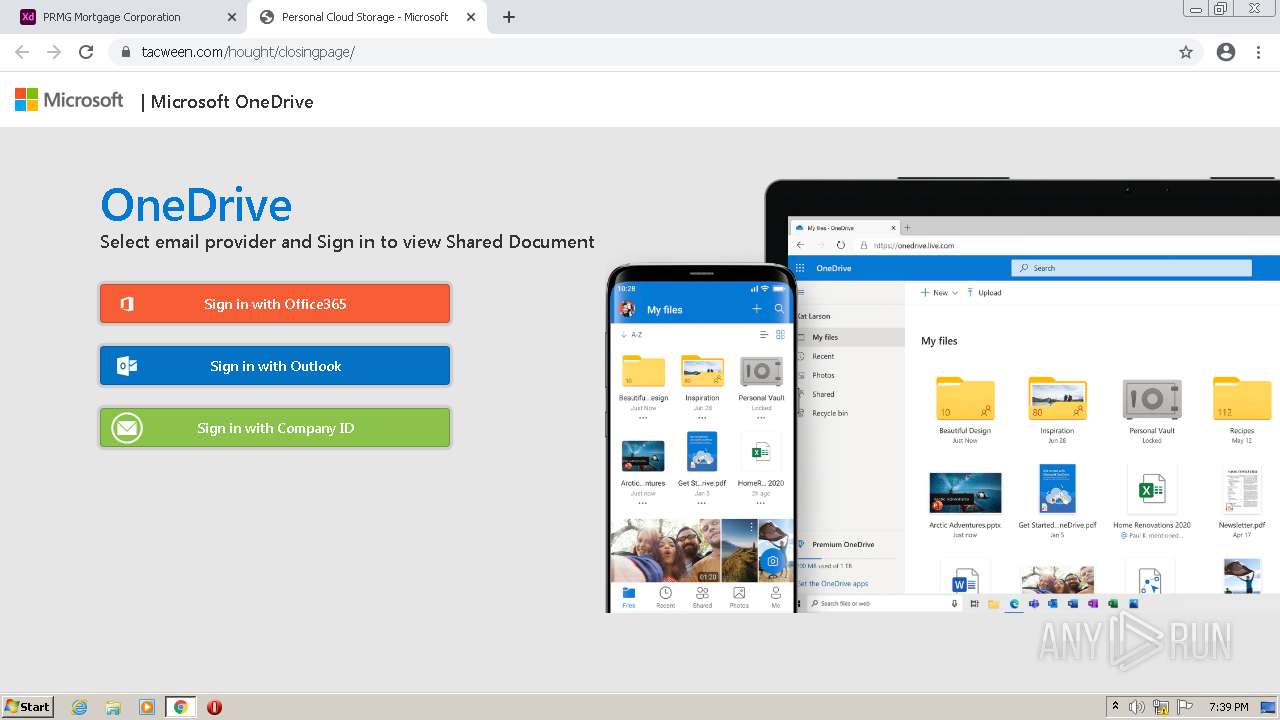
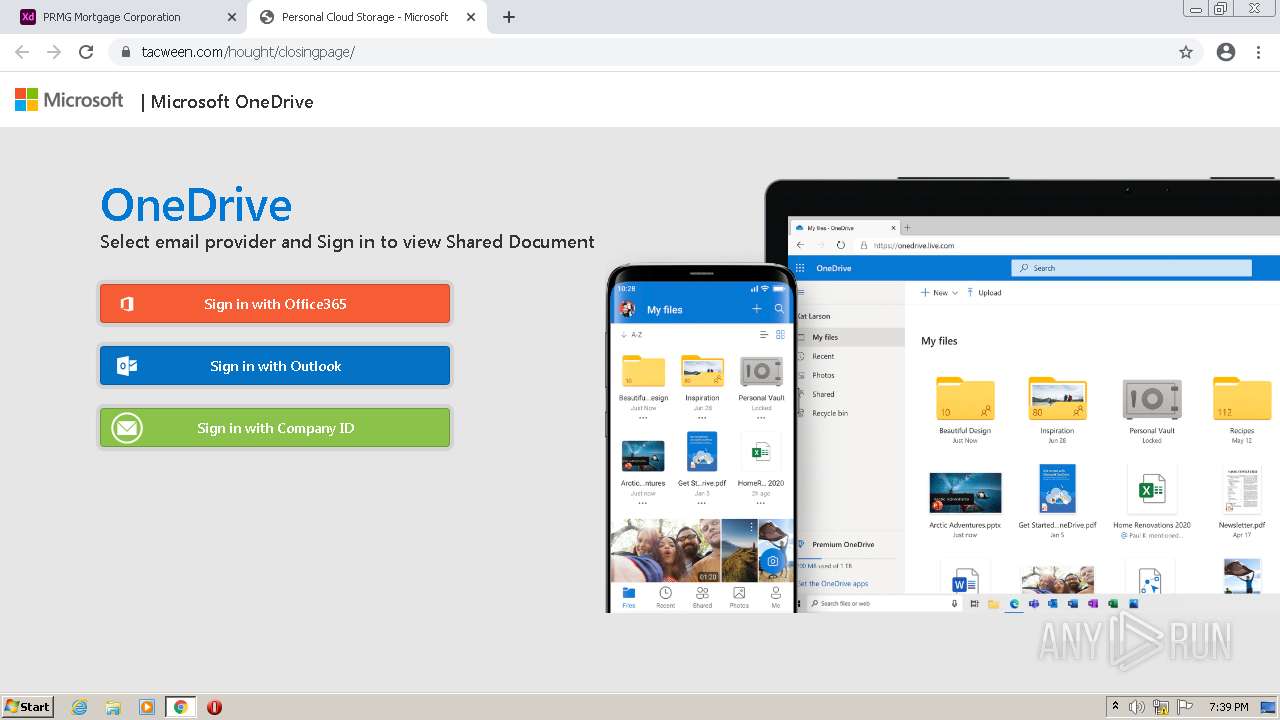
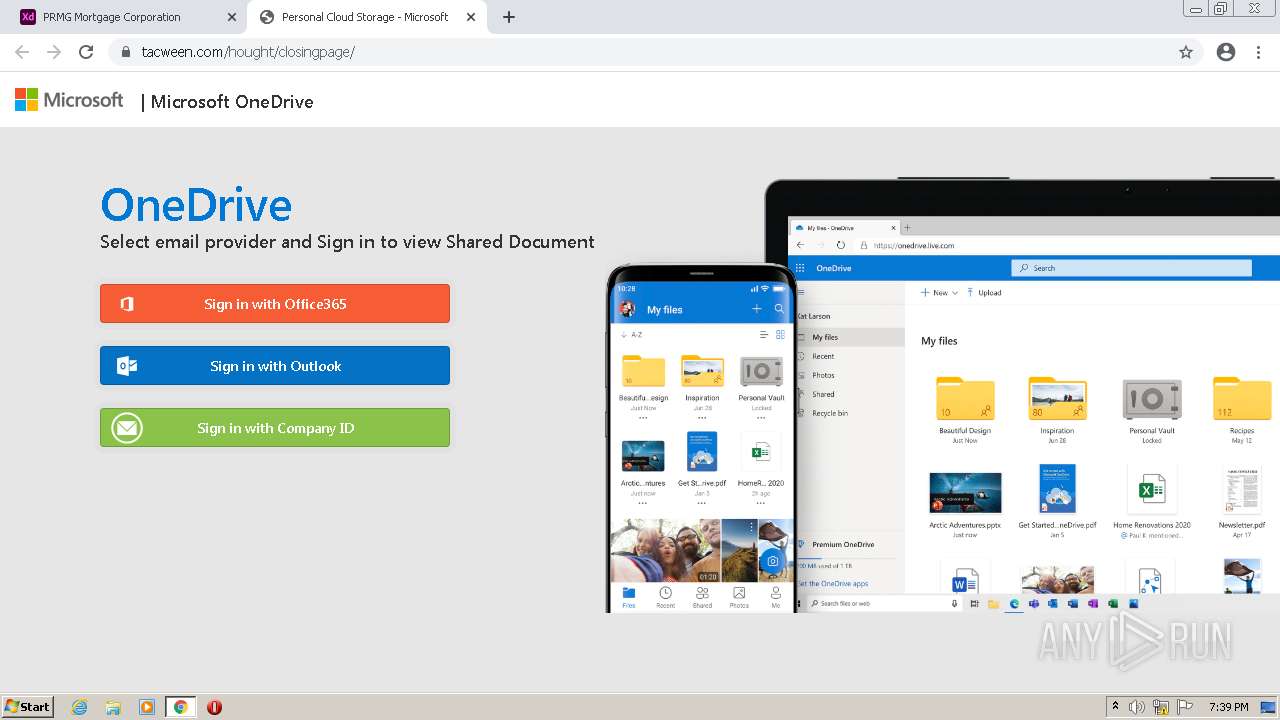
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 18:35:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4D363EF9FBA5D87C34134CFCDADD6CA3 |
| SHA1: | CC90DE44B82D8DB0FA566FAD8CE3FEDE892670EE |
| SHA256: | C1497E9FC90EF3E4CFCB09D2139D0CE28E3BEC0F4514220A776FD88AE0D64B22 |
| SSDEEP: | 3:N8t4TSjp0HKFPRj9aDQhhDURfu:2zfFpj4D0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1076)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2796)
INFO
Checks supported languages
- iexplore.exe (PID: 1300)
- iexplore.exe (PID: 1076)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3364)
- chrome.exe (PID: 1964)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 960)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 968)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 124)
- chrome.exe (PID: 2492)
Reads the computer name
- iexplore.exe (PID: 1300)
- iexplore.exe (PID: 1076)
- chrome.exe (PID: 3364)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 1264)
Reads settings of System Certificates
- iexplore.exe (PID: 1300)
- chrome.exe (PID: 3448)
Application launched itself
- iexplore.exe (PID: 1300)
- chrome.exe (PID: 2796)
Changes internet zones settings
- iexplore.exe (PID: 1300)
Checks Windows Trust Settings
- iexplore.exe (PID: 1300)
Reads the date of Windows installation
- iexplore.exe (PID: 1300)
- chrome.exe (PID: 1712)
Reads internet explorer settings
- iexplore.exe (PID: 1076)
Manual execution by user
- chrome.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1300 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://xd.adobe.com/view/b9efc2bf-17b3-4e5c-992c-15563dd79491-ecbc/?fullscreen&hints=off" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,11990276191749379223,16290586863826950818,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
16 797
Read events
16 567
Write events
221
Delete events
9
Modification events
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977658 | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977658 | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
195
Text files
143
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F69D67-AEC.pma | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b9795fda-3bbd-44b6-8b35-b7206d7d9b21.tmp | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFdb4d9.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdb4aa.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_1 | vxd | |
MD5:259E7ED5FB3C6C90533B963DA5B2FC1B | SHA256:35BB2F189C643DCF52ECF037603D104035ECDC490BF059B7736E58EF7D821A09 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cbfa0370-f35e-4278-ba0c-e1b0a9eecb9b.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_3 | vxd | |
MD5:41876349CB12D6DB992F1309F22DF3F0 | SHA256:E09F42C398D688DCE168570291F1F92D079987DEDA3099A34ADB9E8C0522B30C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
98
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
880 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcowylwzsylokyhi6kprflsy4la_52/khaoiebndkojlmppeemjhbpbandiljpe_52_win_admqwpf3f2g6ombninrvglq4im4q.crx3 | US | — | — | whitelisted |
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcowylwzsylokyhi6kprflsy4la_52/khaoiebndkojlmppeemjhbpbandiljpe_52_win_admqwpf3f2g6ombninrvglq4im4q.crx3 | US | — | — | whitelisted |
3448 | chrome.exe | GET | 200 | 192.124.249.31:80 | http://crl.godaddy.com/gdroot.crl | US | der | 429 b | whitelisted |
1300 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 45.9 Kb | whitelisted |
3448 | chrome.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 20.9 Kb | whitelisted |
880 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adcowylwzsylokyhi6kprflsy4la_52/khaoiebndkojlmppeemjhbpbandiljpe_52_win_admqwpf3f2g6ombninrvglq4im4q.crx3 | US | crx | 5.42 Kb | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1300 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3448 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3448 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 13.225.78.119:443 | xd.adobe.com | — | US | suspicious |
1300 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3448 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xd.adobe.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |