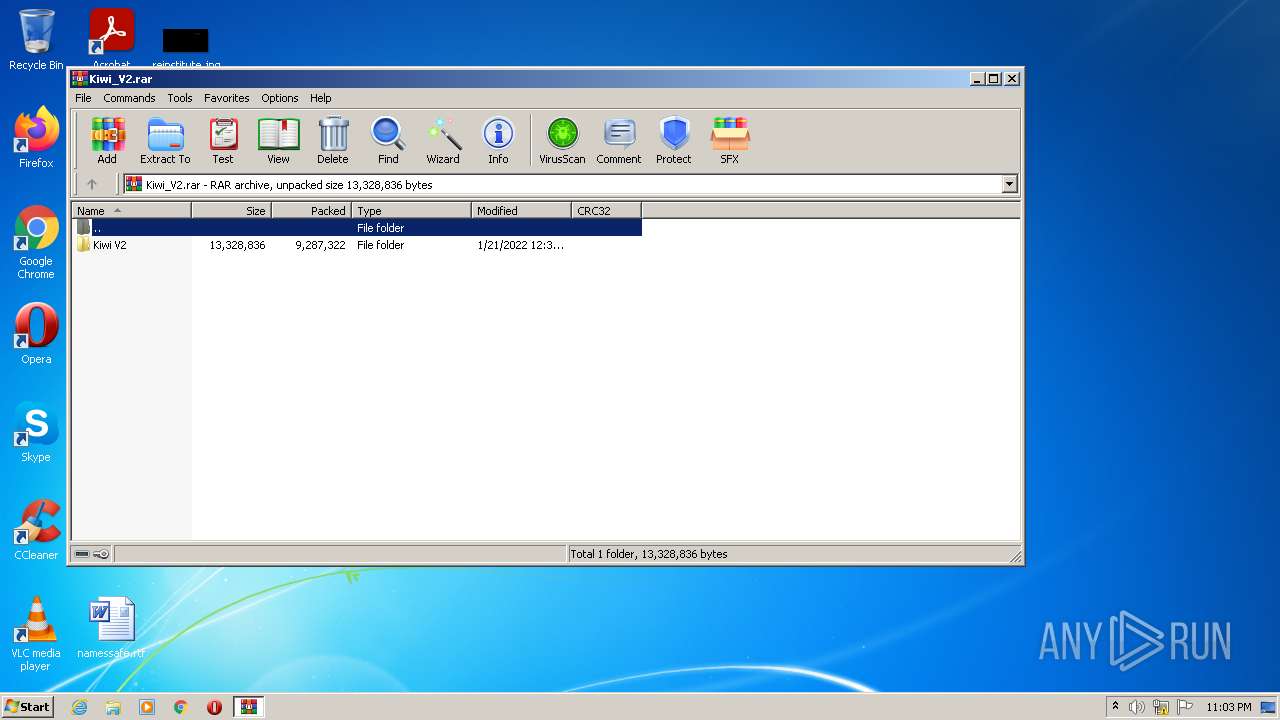
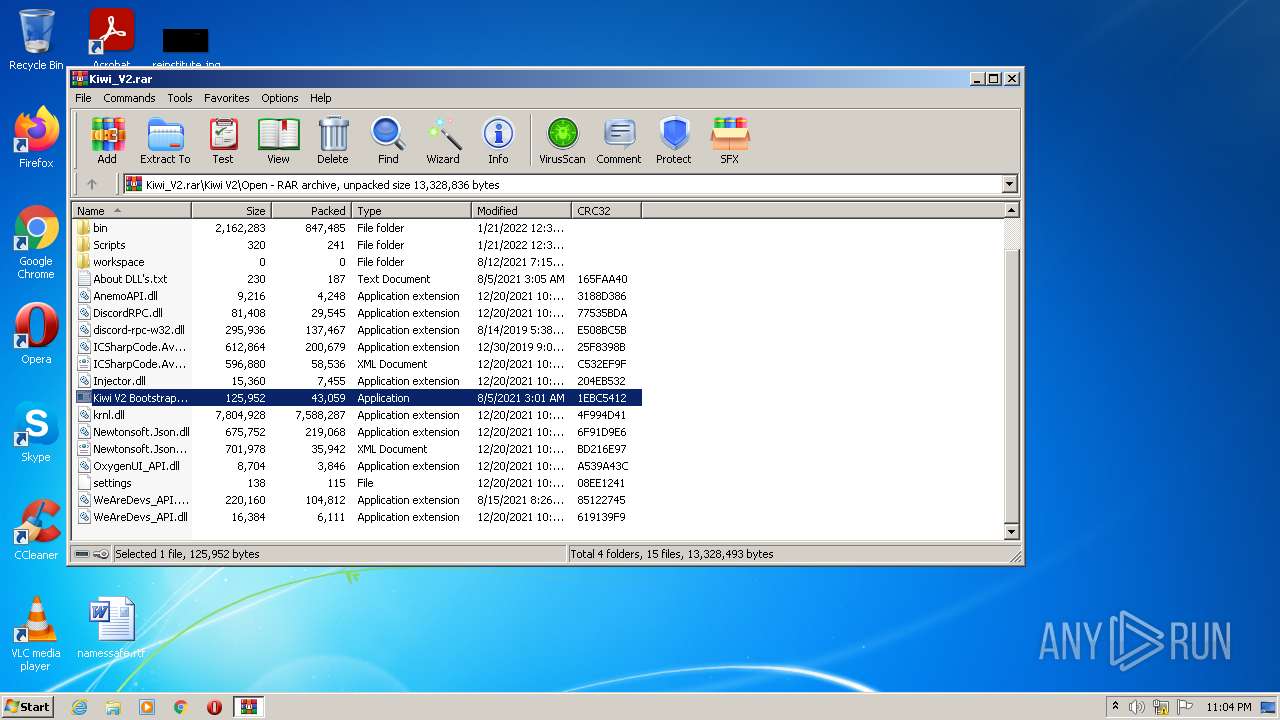
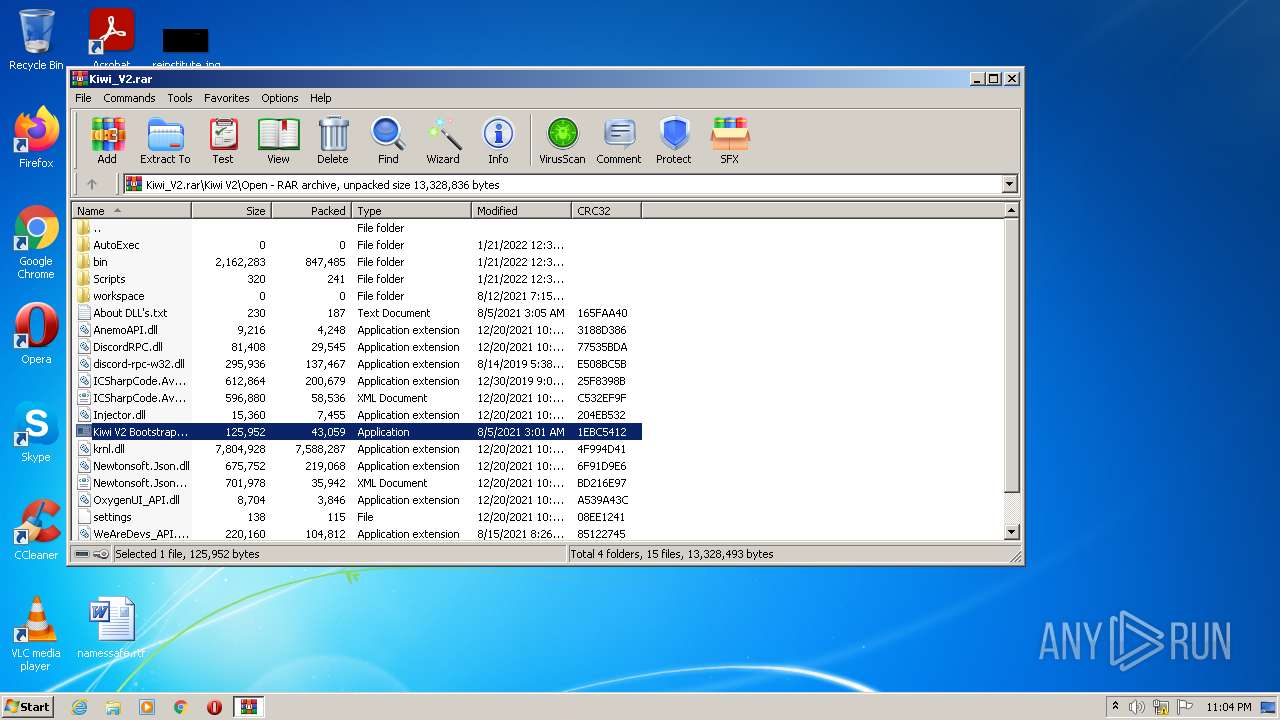
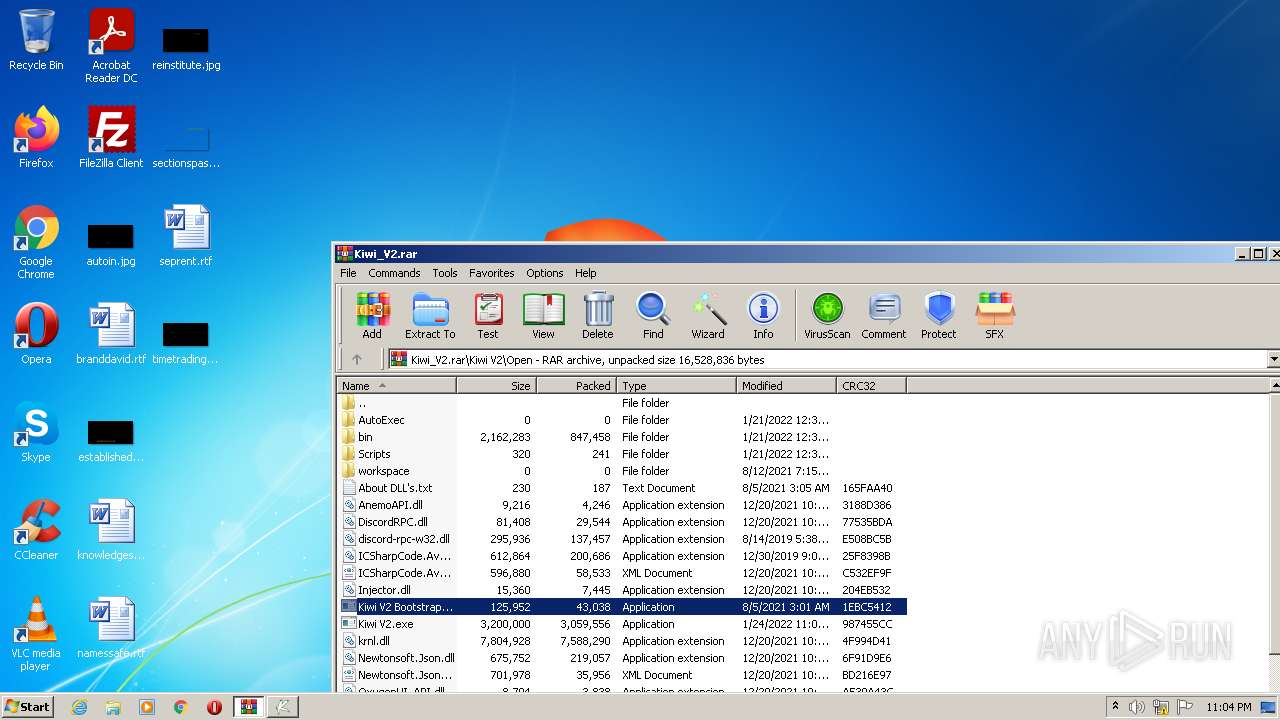
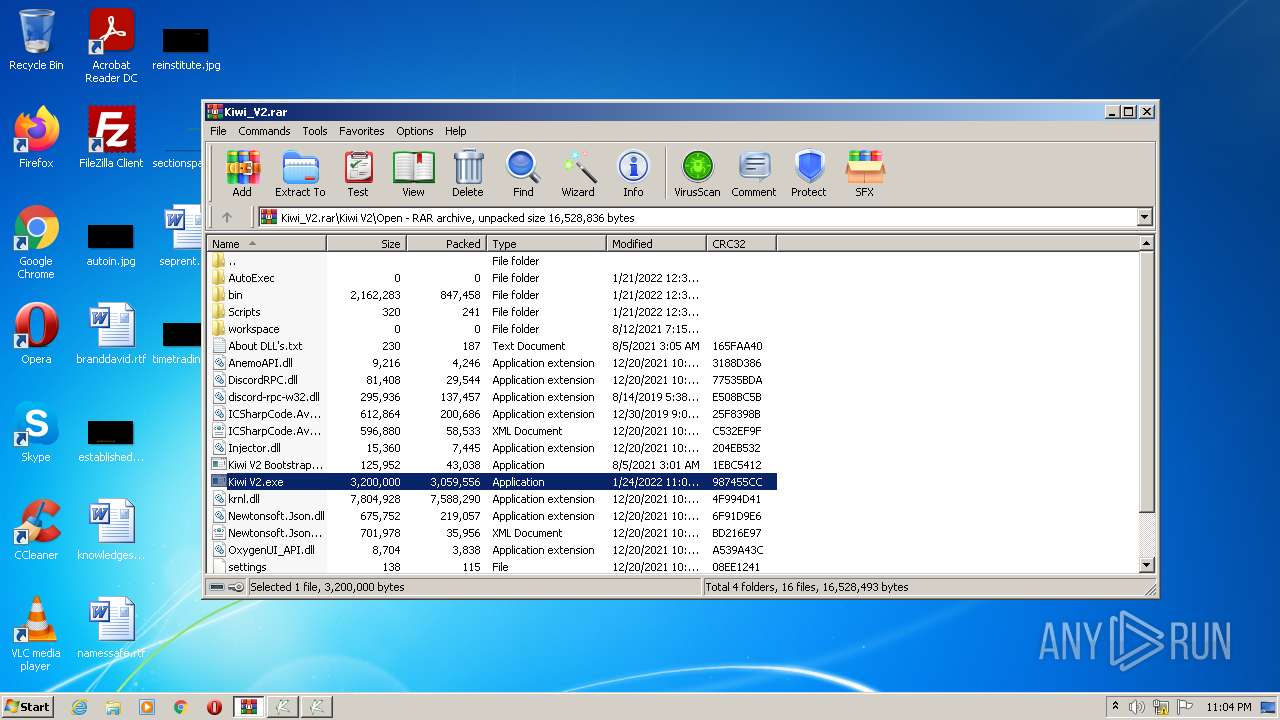
| File name: | Kiwi_V2.rar |
| Full analysis: | https://app.any.run/tasks/3bae2bab-f080-424d-be47-55ffcbc01127 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 23:03:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A81CB5ACD8C587C243A385BCBECBC59B |
| SHA1: | F38F40BD72848A6602186D4B87849CF930A3AFE9 |
| SHA256: | C1453AAEA6F6CABDE251F22B0DCE94ABD30A7AE68C8E3F7A41ACB8B320755DCE |
| SSDEEP: | 196608:Nk56GlddASZxkt8mv9JFKK++IFyyLgbVWP24WixtKzQ3:25xddZK8W9Wr8y8RWPWixtKzu |
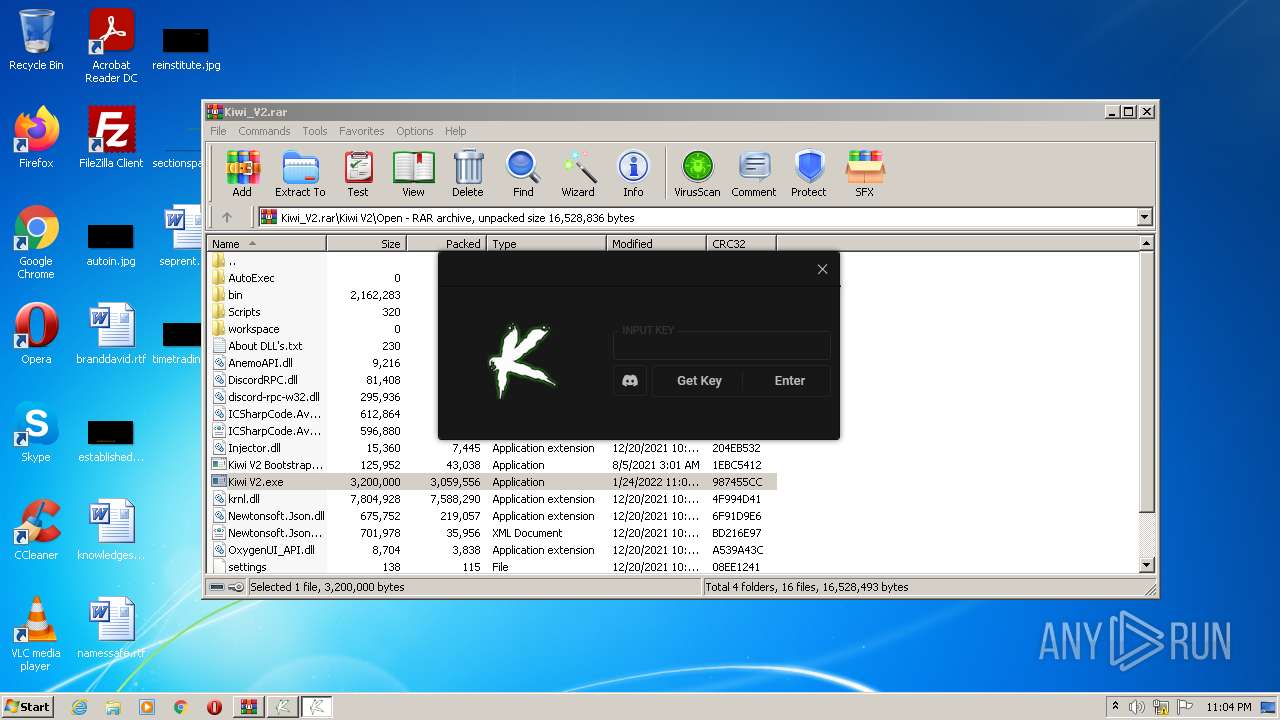
MALICIOUS
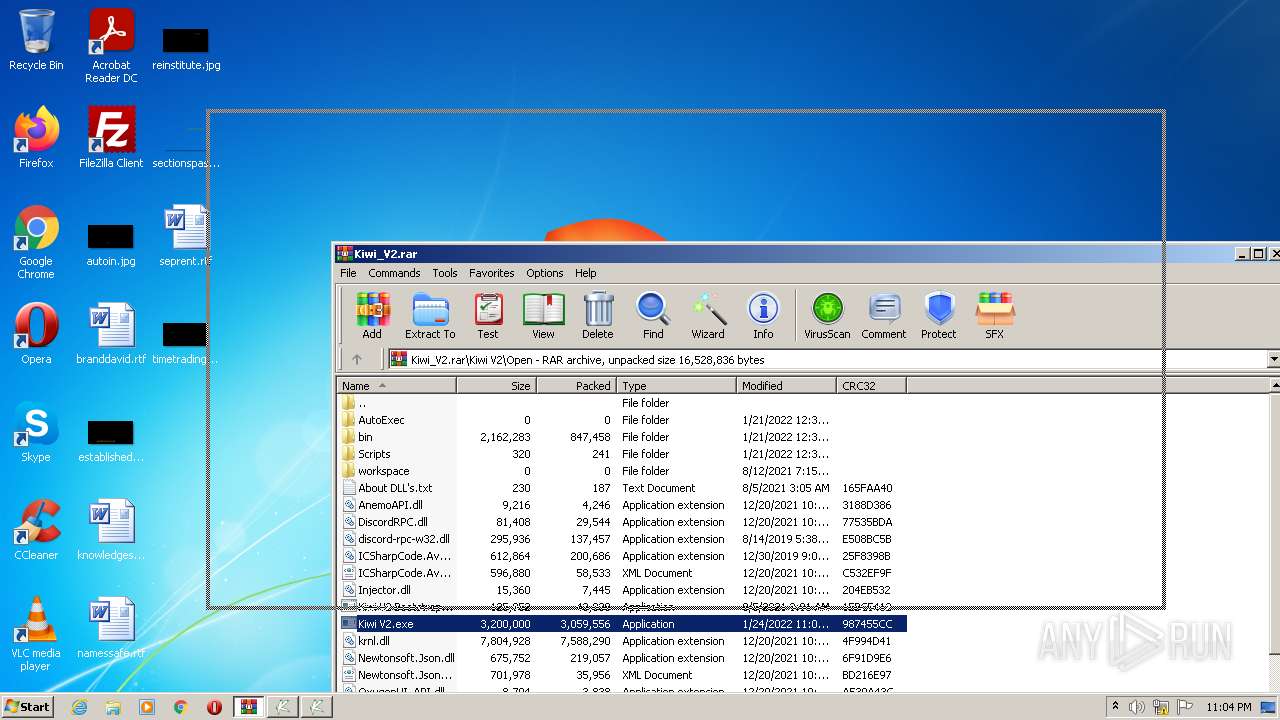
Application was dropped or rewritten from another process
- Kiwi V2.exe (PID: 3456)
- Kiwi V2.exe (PID: 2932)
- Kiwi V2 Bootstrapper.exe (PID: 3064)
Loads dropped or rewritten executable
- Kiwi V2.exe (PID: 2932)
SUSPICIOUS
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1076)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1076)
- Kiwi V2 Bootstrapper.exe (PID: 3064)
Reads the computer name
- WinRAR.exe (PID: 1076)
- Kiwi V2.exe (PID: 2932)
- Kiwi V2.exe (PID: 3456)
- Kiwi V2 Bootstrapper.exe (PID: 3064)
Drops a file that was compiled in debug mode
- Kiwi V2 Bootstrapper.exe (PID: 3064)
- WinRAR.exe (PID: 1076)
Checks supported languages
- Kiwi V2.exe (PID: 2932)
- Kiwi V2.exe (PID: 3456)
- WinRAR.exe (PID: 1076)
- Kiwi V2 Bootstrapper.exe (PID: 3064)
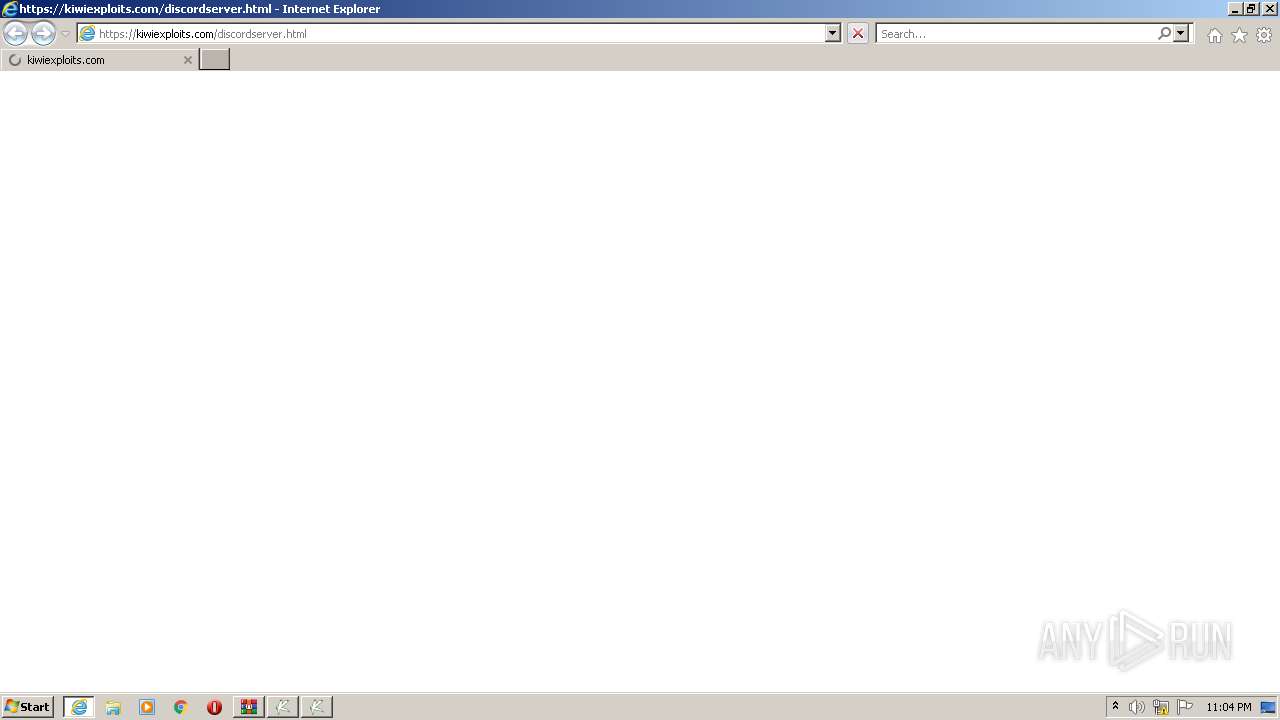
Starts Internet Explorer
- Kiwi V2.exe (PID: 2932)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3316)
Reads Environment values
- Kiwi V2 Bootstrapper.exe (PID: 3064)
INFO
Checks supported languages
- WISPTIS.EXE (PID: 2044)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 3316)
Reads the computer name
- WISPTIS.EXE (PID: 2044)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 3316)
Application launched itself
- iexplore.exe (PID: 1988)
Changes internet zones settings
- iexplore.exe (PID: 1988)
Reads settings of System Certificates
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 1988)
- Kiwi V2 Bootstrapper.exe (PID: 3064)
Checks Windows Trust Settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 1988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
44
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
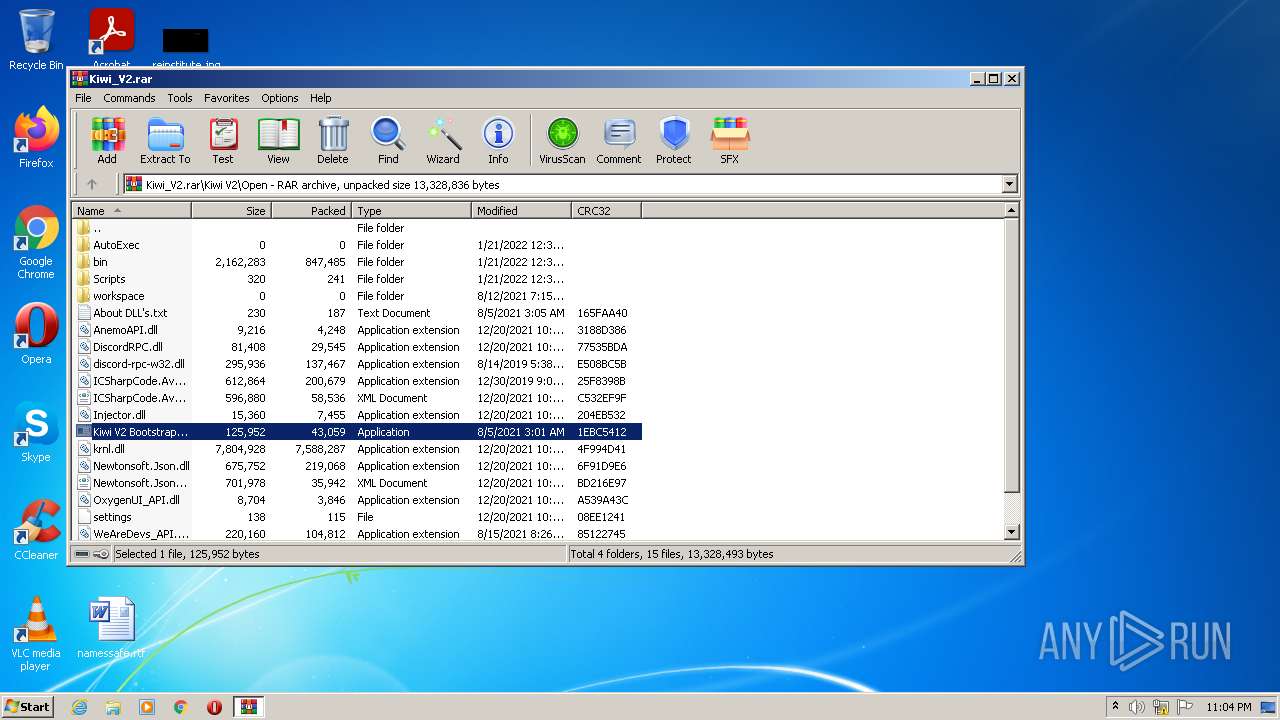
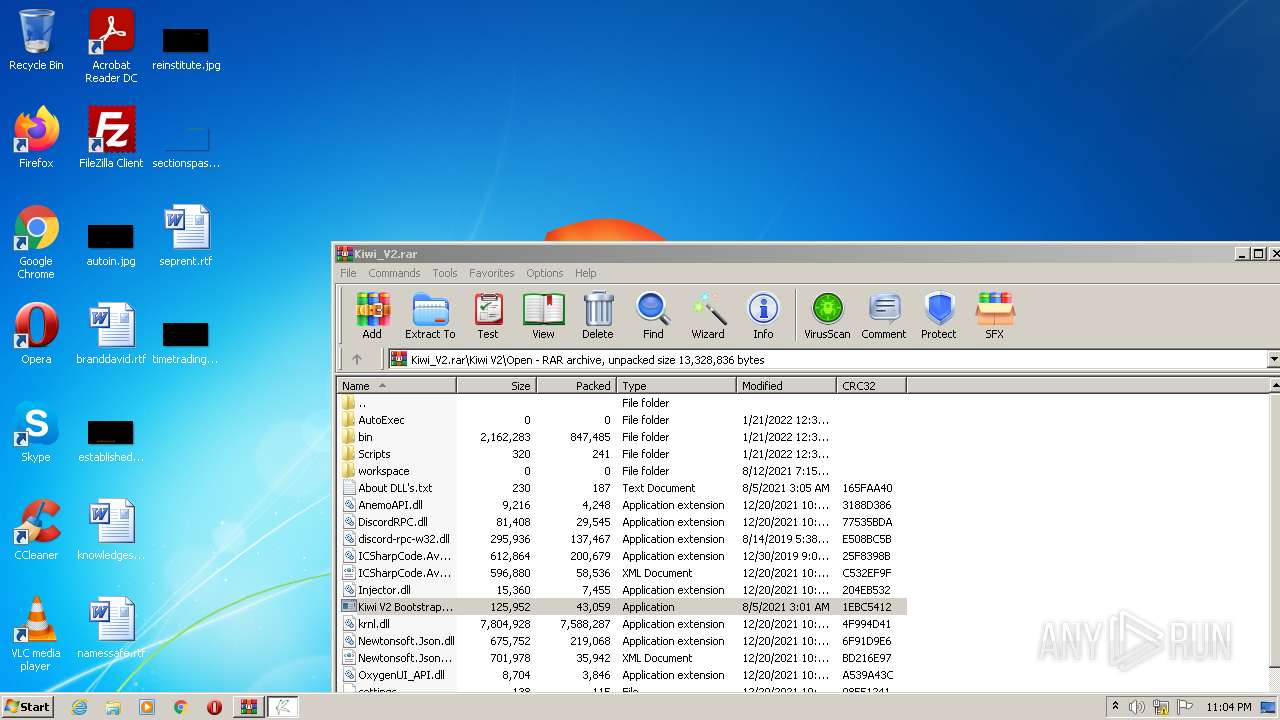
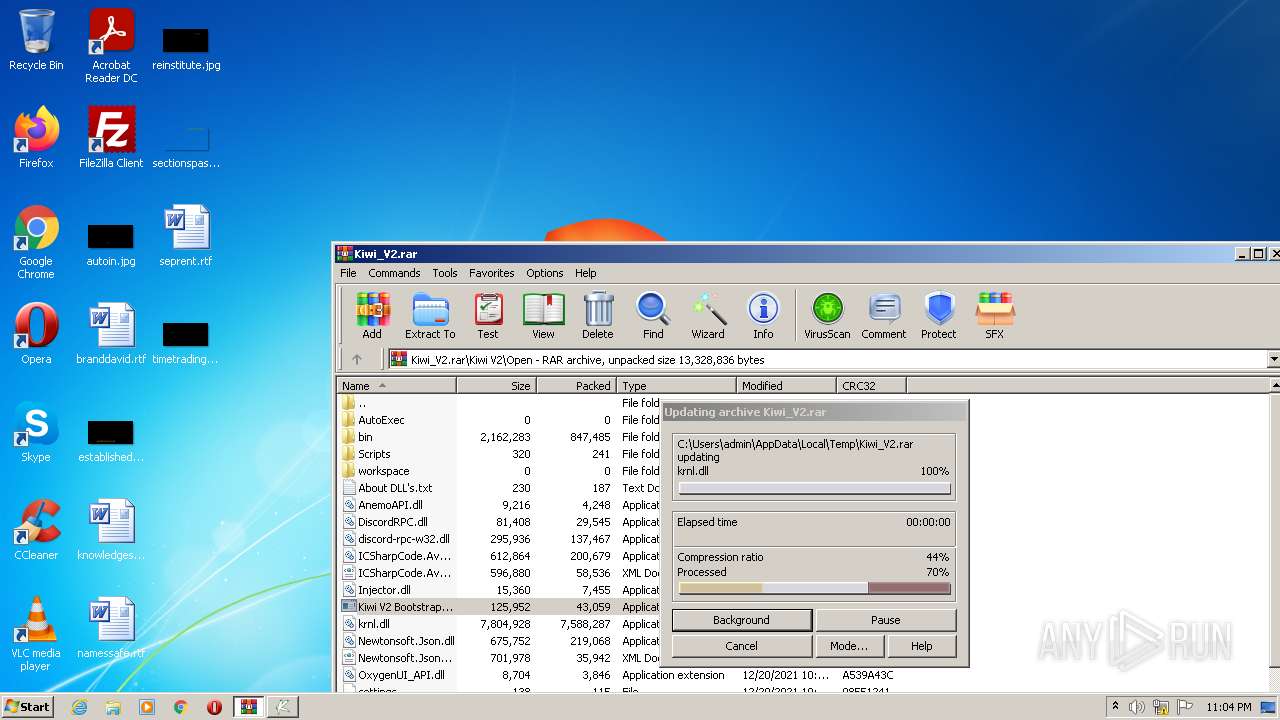
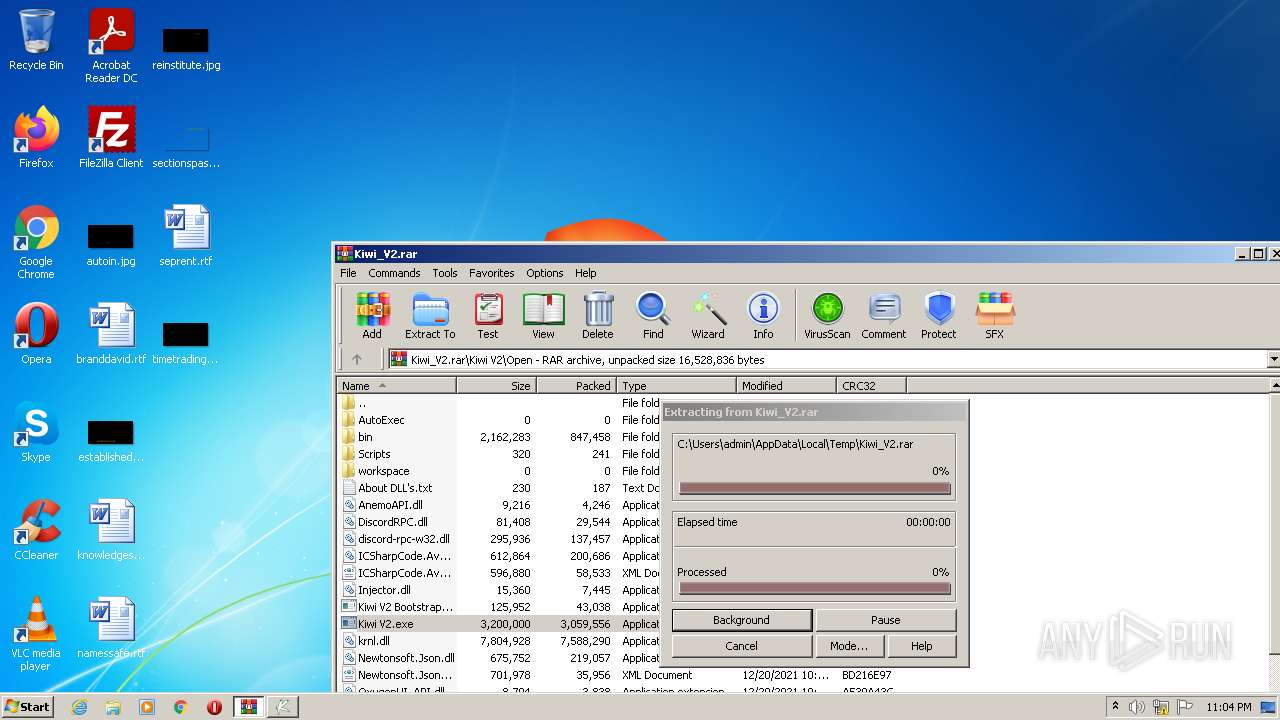
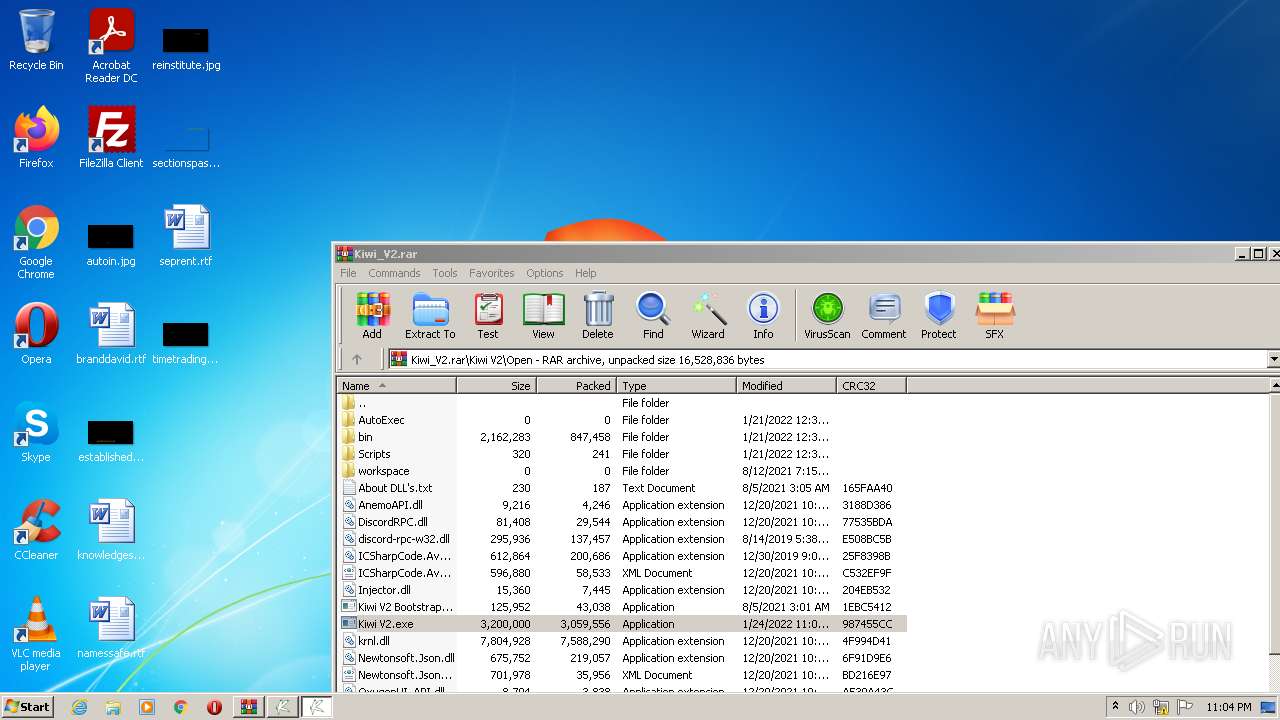
| 1076 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Kiwi_V2.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1596 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | Kiwi V2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Internet Explorer\iexplore.exe" https://kiwiexploits.com/discordserver.html | C:\Program Files\Internet Explorer\iexplore.exe | Kiwi V2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2044 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | Kiwi V2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.11673\Kiwi V2\Open\Kiwi V2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.11673\Kiwi V2\Open\Kiwi V2.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: KiwiV2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3064 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Kiwi V2 Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Kiwi V2 Bootstrapper.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Kichi Bootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1988 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Kiwi V2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Kiwi V2.exe | — | Kiwi V2 Bootstrapper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: KiwiV2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
10 687
Read events
10 515
Write events
172
Delete events
0
Modification events
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Kiwi_V2.rar | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
28
Suspicious files
0
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
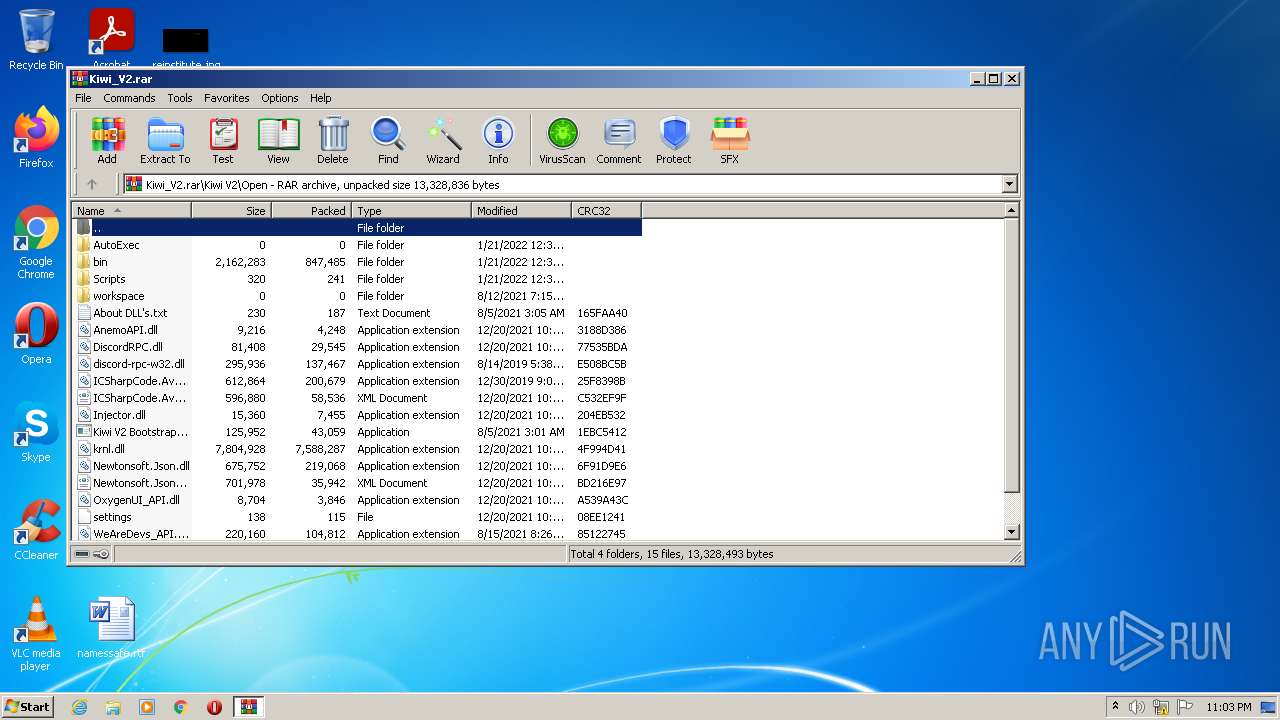
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\bin\lua.xshd | xml | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\bin\Api.txt | text | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\AnemoAPI.dll | executable | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rar_1076.11298 | — | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Kiwi_V2.bak1076.11413 | — | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Kiwi_V2.rar | — | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\About DLL's.txt | text | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Kiwi V2 Bootstrapper.exe | executable | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\Injector.dll | executable | |
MD5:— | SHA256:— | |||
| 1076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1076.9902\Kiwi V2\Open\bin\RobloxPlayerLauncher.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | iexplore.exe | GET | — | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | — | — | whitelisted |
1988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3316 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3316 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6e08f4cc202b8f1d | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3064 | Kiwi V2 Bootstrapper.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
3064 | Kiwi V2 Bootstrapper.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
1988 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3316 | iexplore.exe | 199.188.201.131:443 | kiwiexploits.com | Namecheap, Inc. | US | unknown |
3316 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1988 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3316 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
cdn.discordapp.com |
| shared |
kiwiexploits.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |