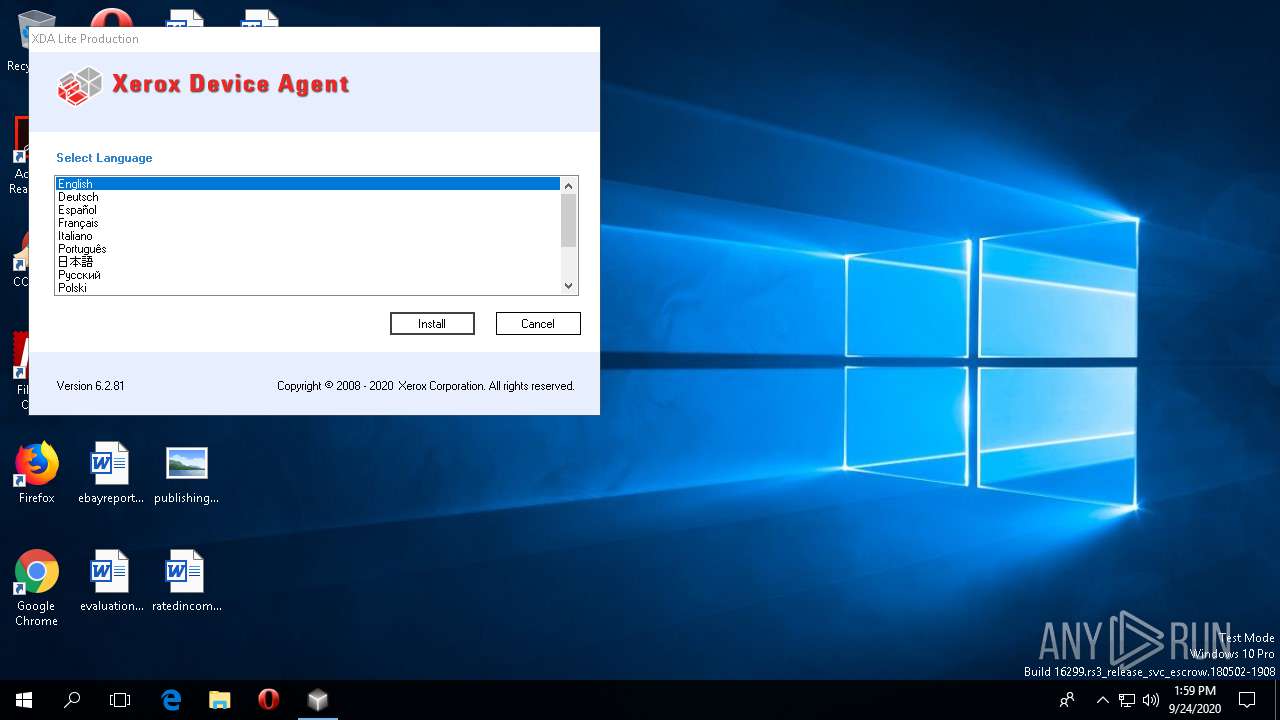
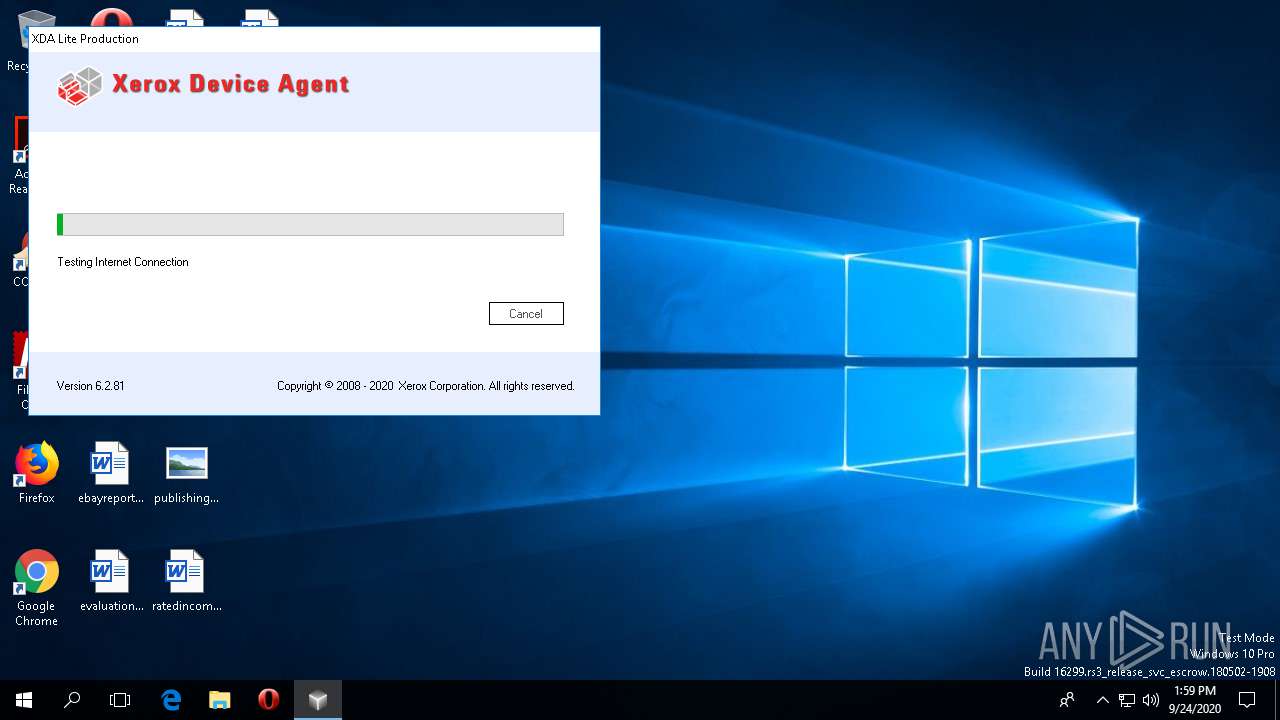
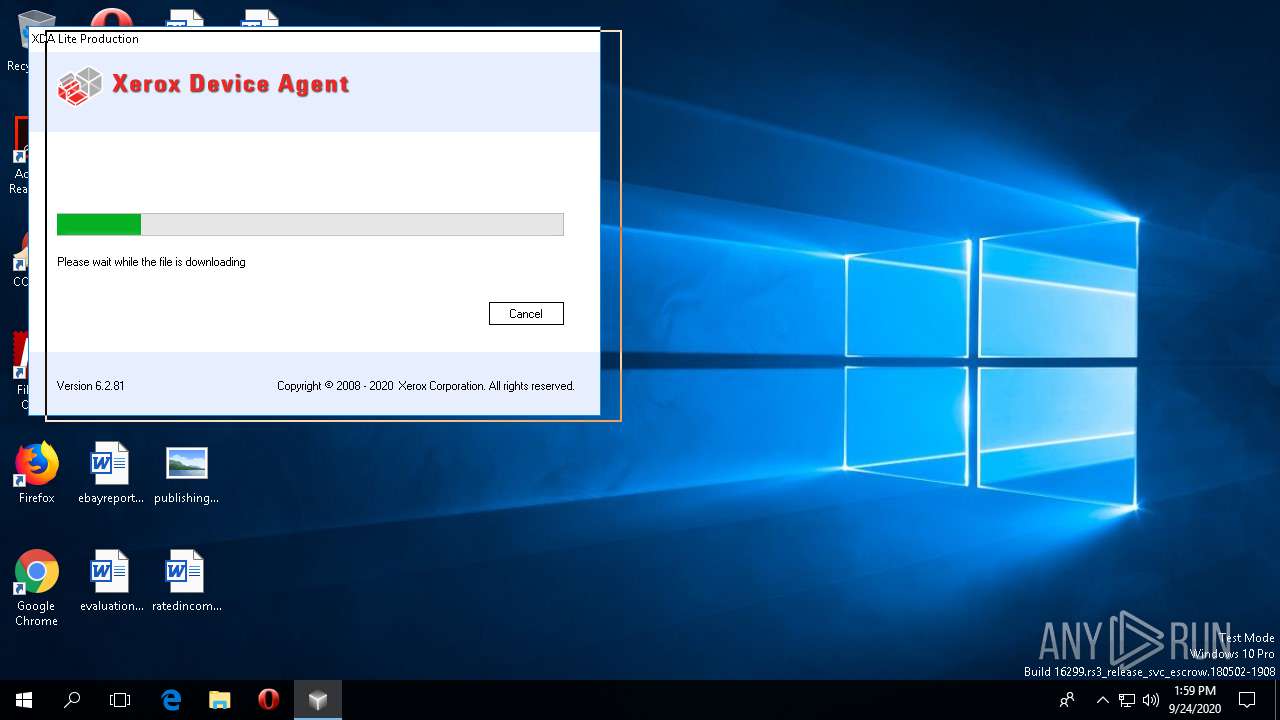
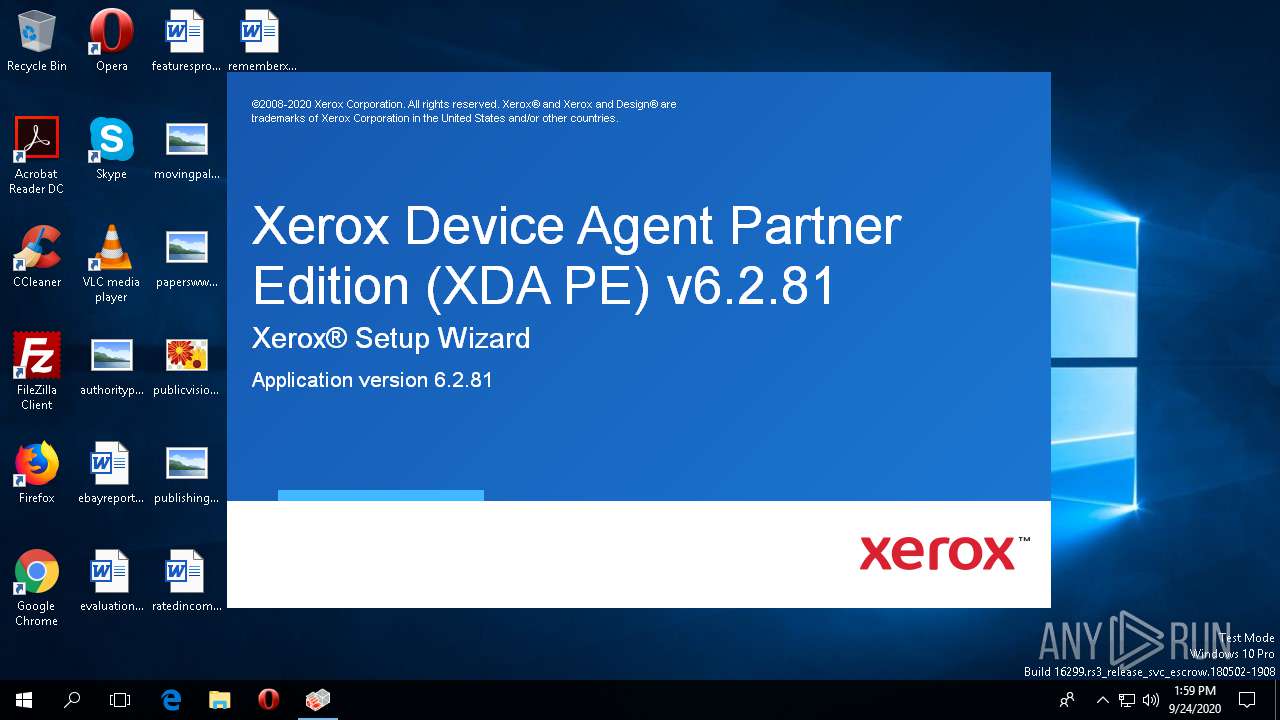
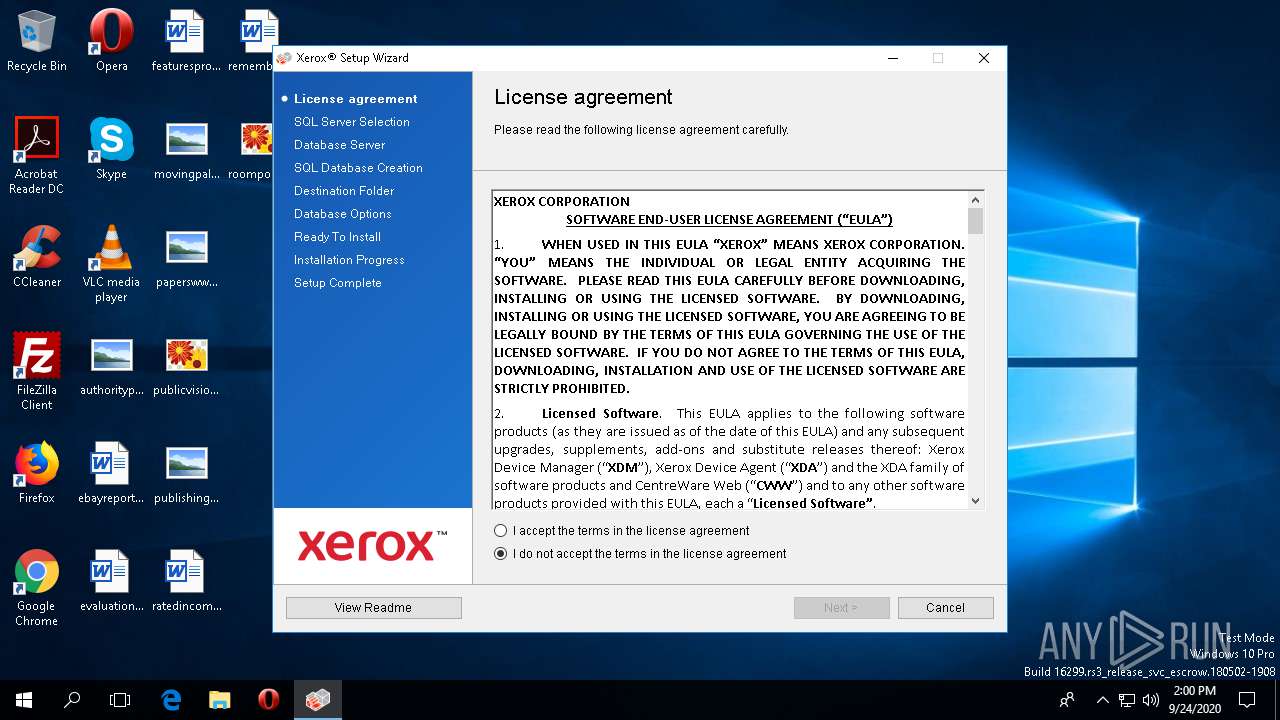
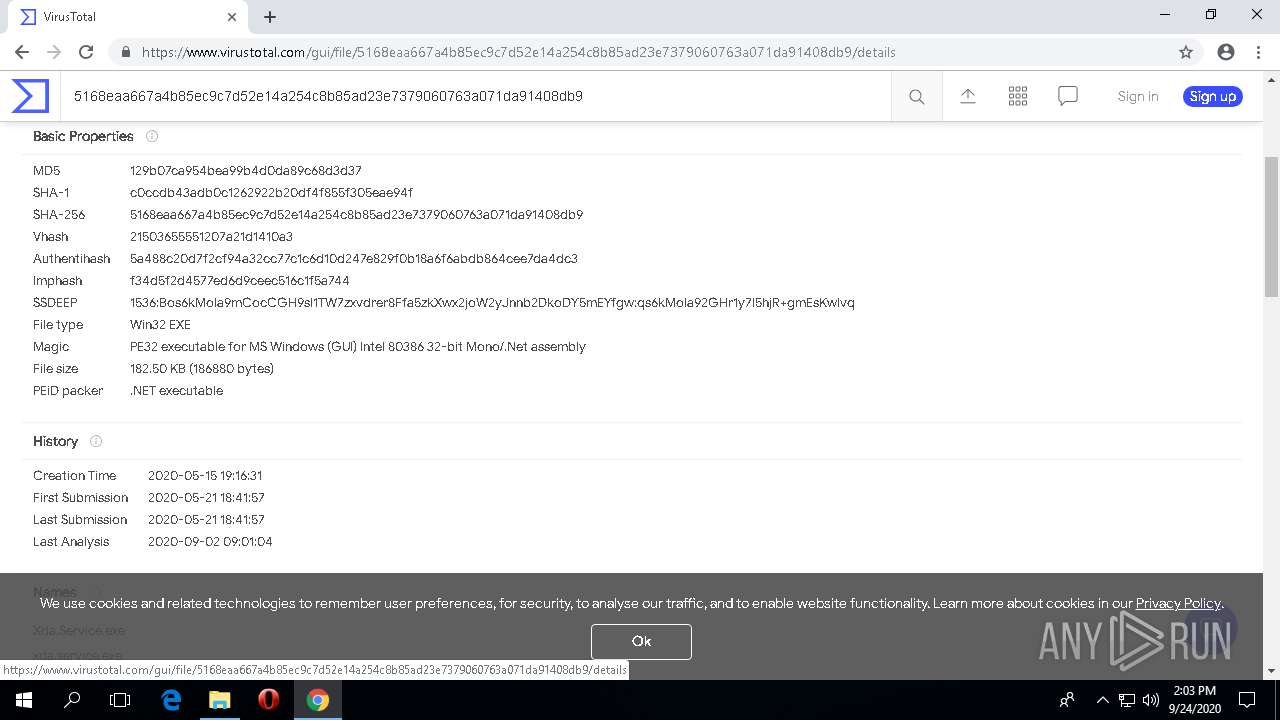
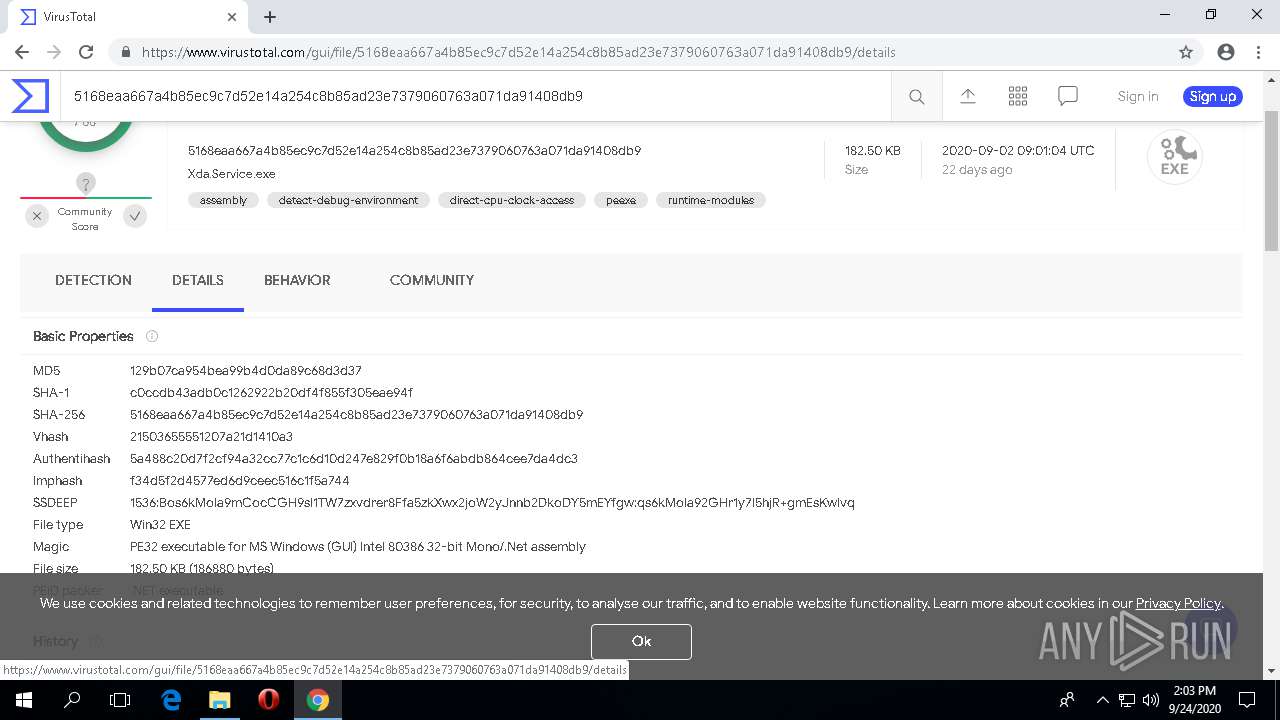
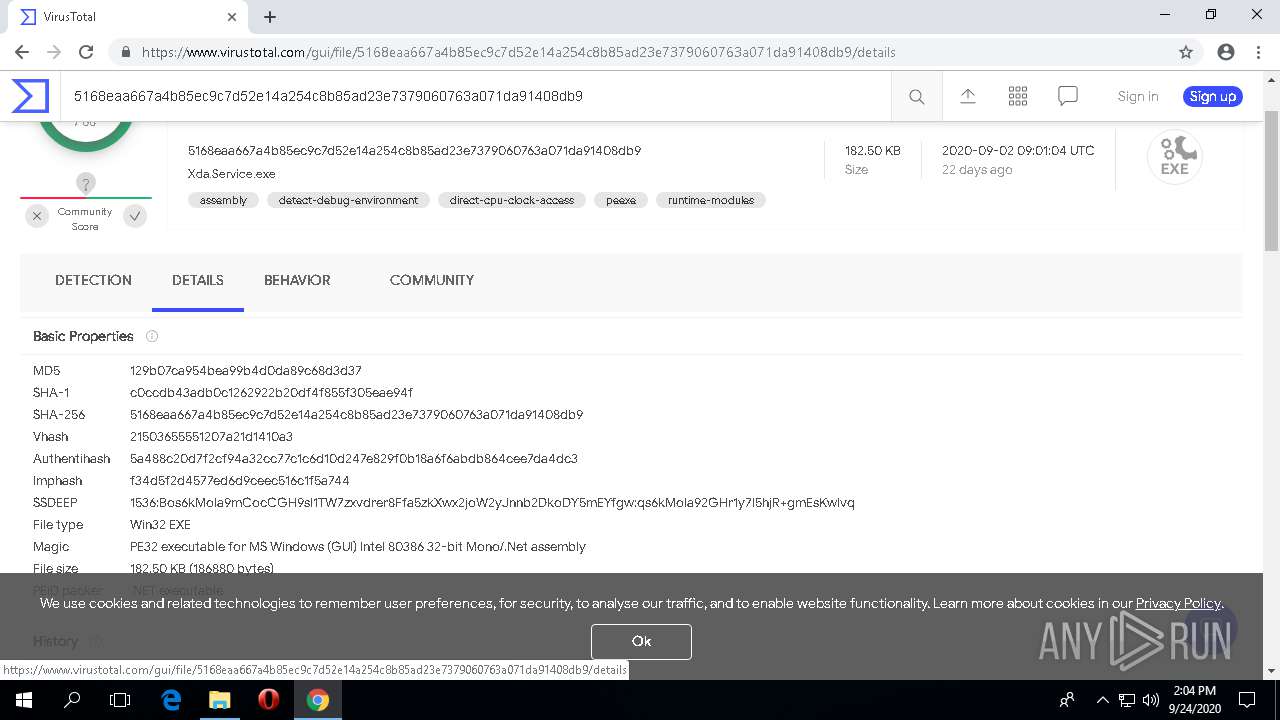
| File name: | XDA Lite Production v6.2.81.exe |
| Full analysis: | https://app.any.run/tasks/87f481fc-e0e1-46f3-9ae4-63f81d1e3017 |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2020, 13:58:27 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 70B9FD7686B820A6949420EED72F1817 |
| SHA1: | CD37155D73F52FC19C3119D099EB9E9A2E4BFBA5 |
| SHA256: | C13029B7052FD06B789A9735FD60D35DEA376F3FE161F2A52C6124D80BD5ADC3 |
| SSDEEP: | 12288:kR8IT3gy1wa9m1MBm1Mvy3cfhAm1Mxm1Mpm1MHbvLxcujjuHCyRd/QFltlAmPYv6:dyOLlUZ99ovVcuj6Hp/QFxra7m |
MALICIOUS
Application was dropped or rewritten from another process
- dbVersionDetect.exe (PID: 252)
- BrandingTask.exe (PID: 796)
- DBCreate.exe (PID: 3364)
- xda.service.exe (PID: 3712)
- Xerox.XDAMonitorService.exe (PID: 3636)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1620)
- rundll32.exe (PID: 2060)
- rundll32.exe (PID: 1668)
- rundll32.exe (PID: 3820)
- DBCreate.exe (PID: 3364)
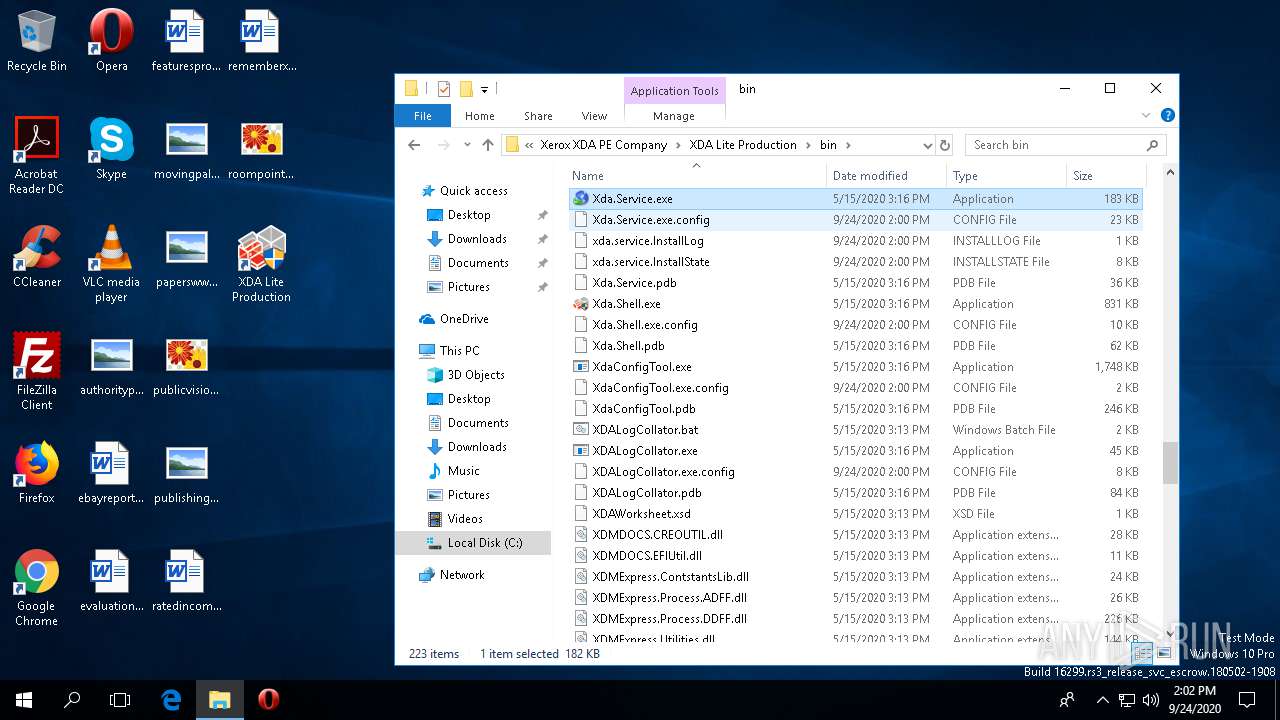
- xda.service.exe (PID: 3712)
- rundll32.exe (PID: 176)
Adds new firewall rule via NETSH.EXE
- xda.service.exe (PID: 3712)
SUSPICIOUS
Reads the machine GUID from the registry
- XDA Lite Production v6.2.81.exe (PID: 664)
- Setup.exe (PID: 1040)
- Setup.exe (PID: 864)
- dbVersionDetect.exe (PID: 252)
- msiexec.exe (PID: 3928)
- rundll32.exe (PID: 1668)
- rundll32.exe (PID: 3820)
- rundll32.exe (PID: 2060)
- rundll32.exe (PID: 1620)
- BrandingTask.exe (PID: 796)
- DBCreate.exe (PID: 3364)
- rundll32.exe (PID: 176)
- Xerox.XDAMonitorService.exe (PID: 3636)
- xda.service.exe (PID: 3712)
Reads Environment values
- XDA Lite Production v6.2.81.exe (PID: 664)
- xda.service.exe (PID: 3712)
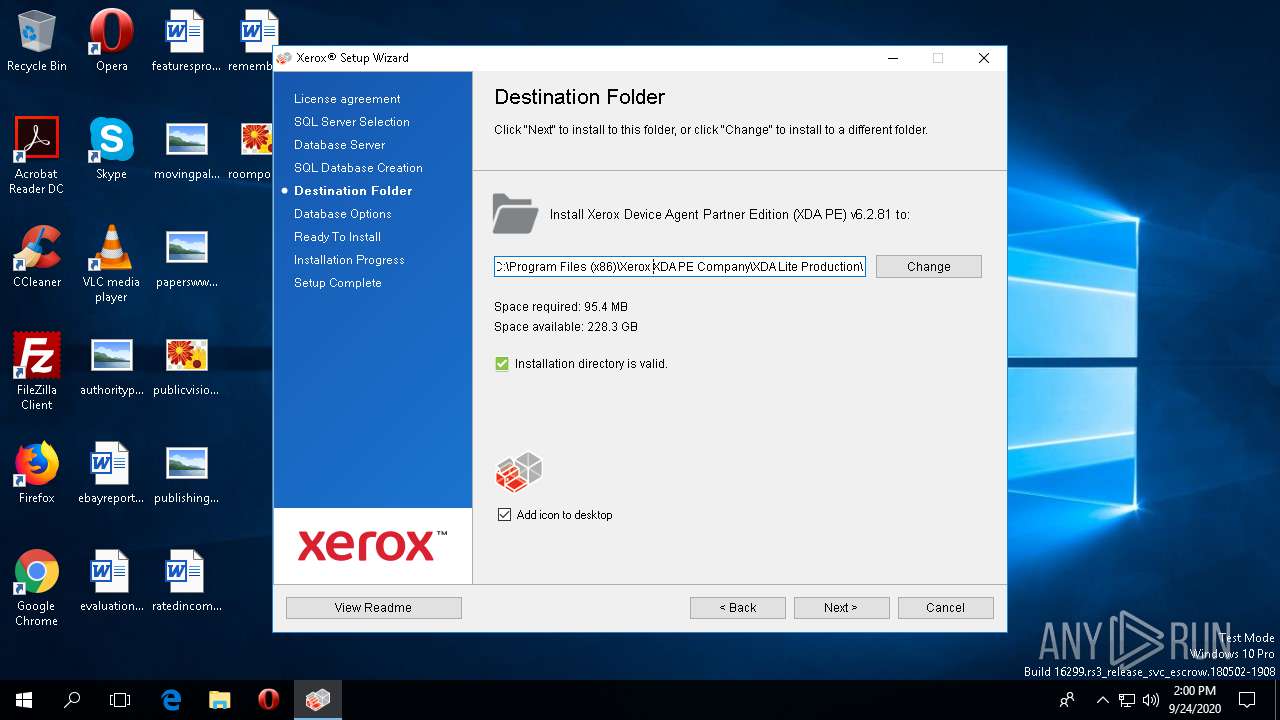
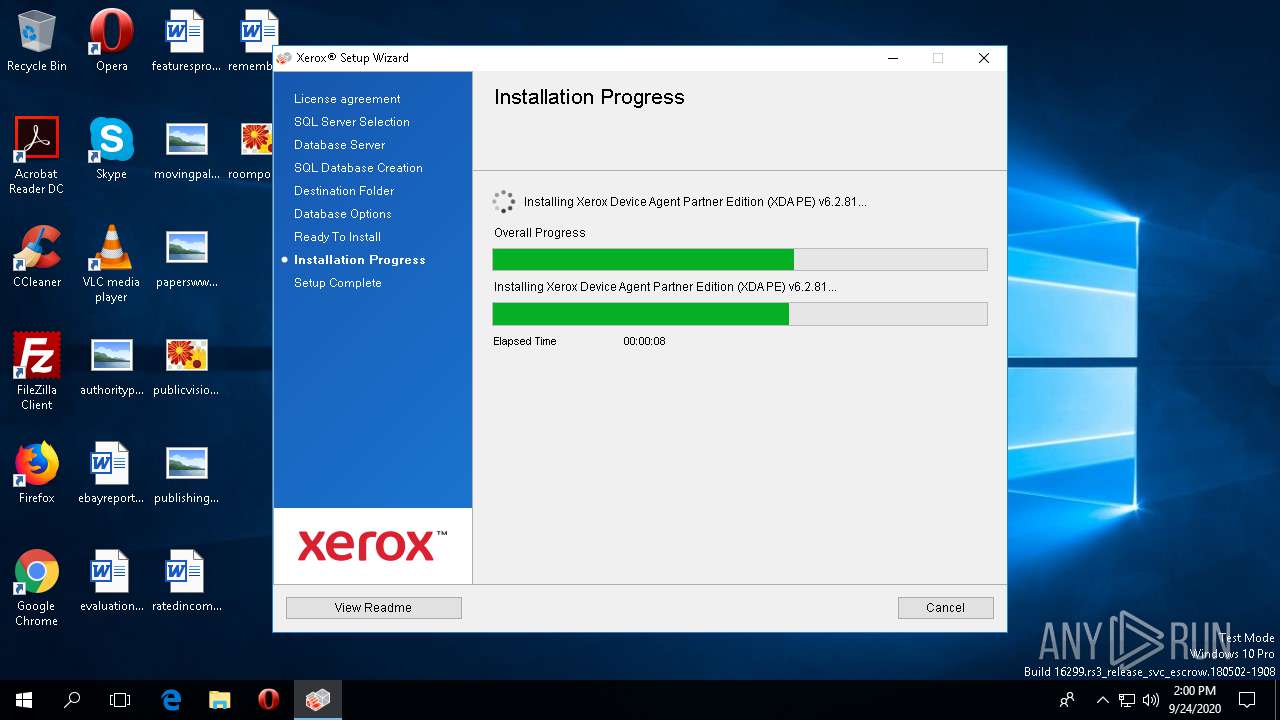
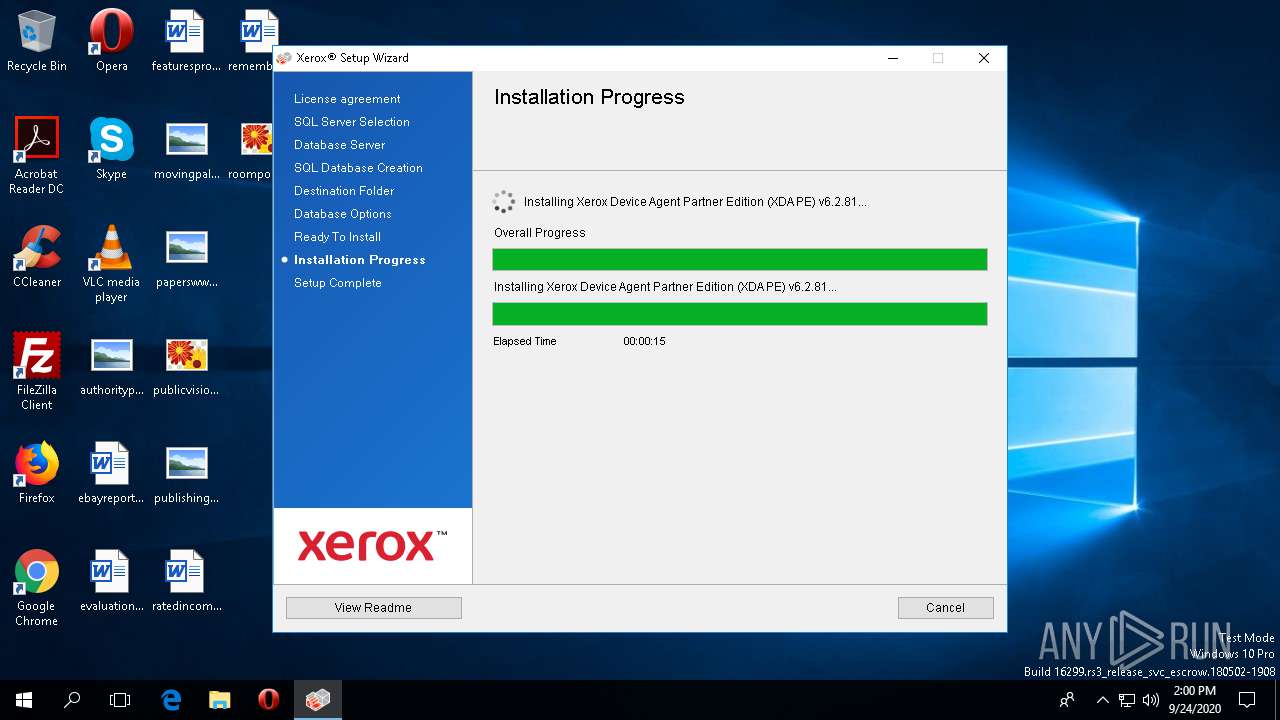
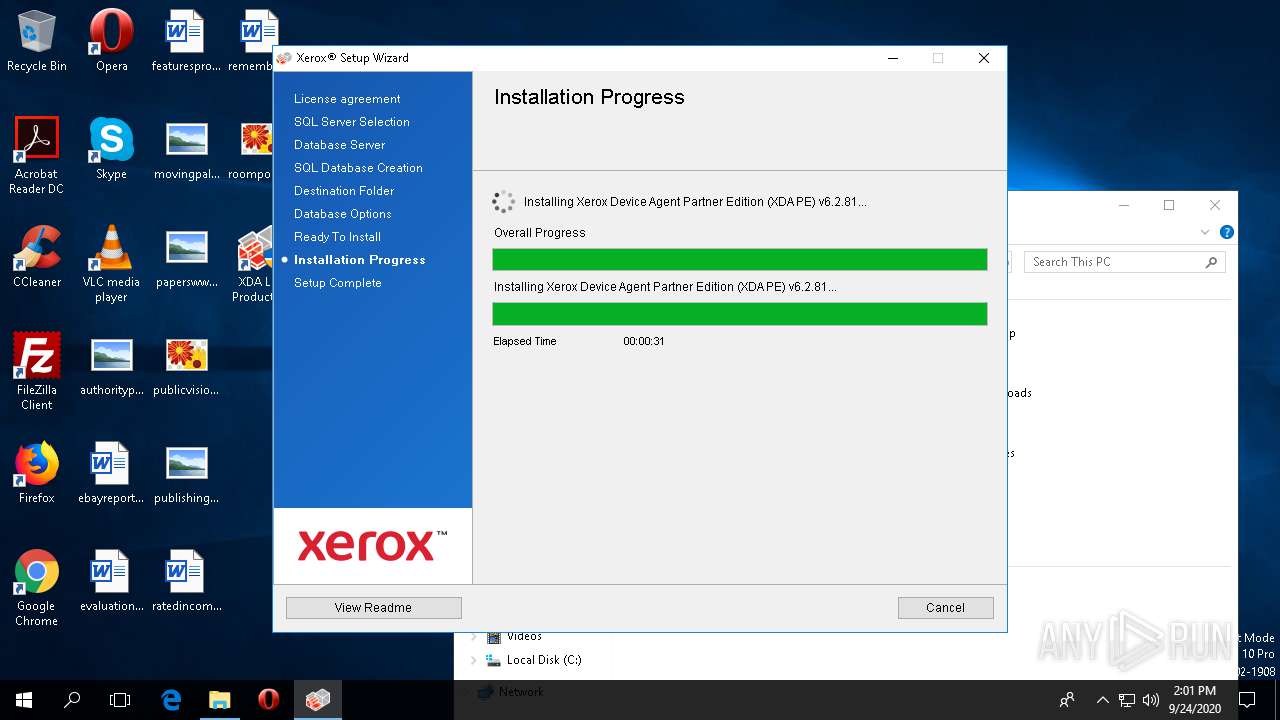
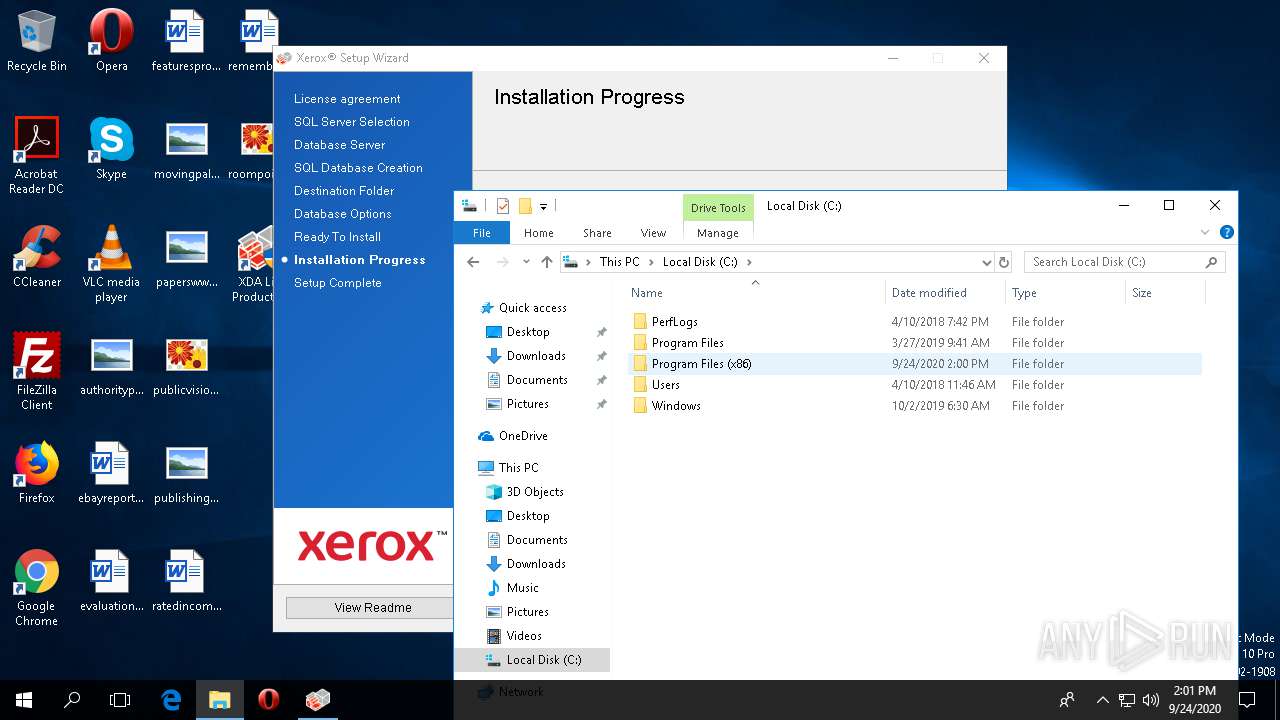
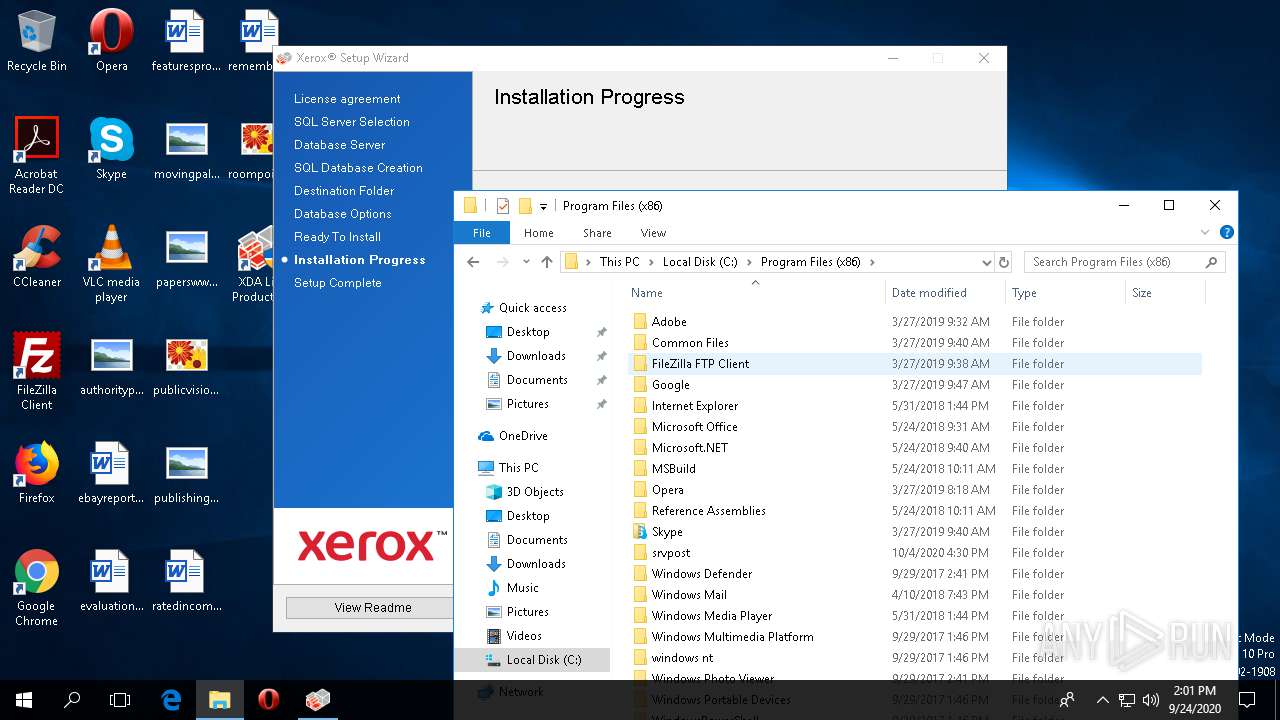
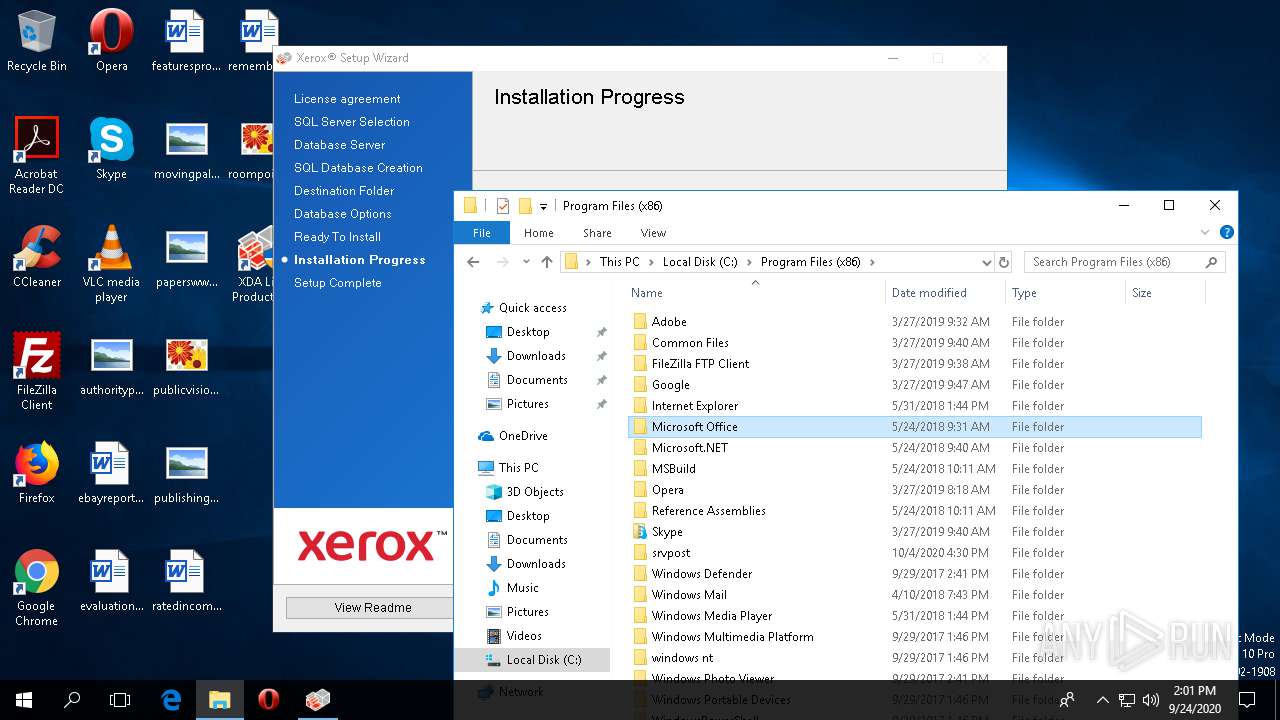
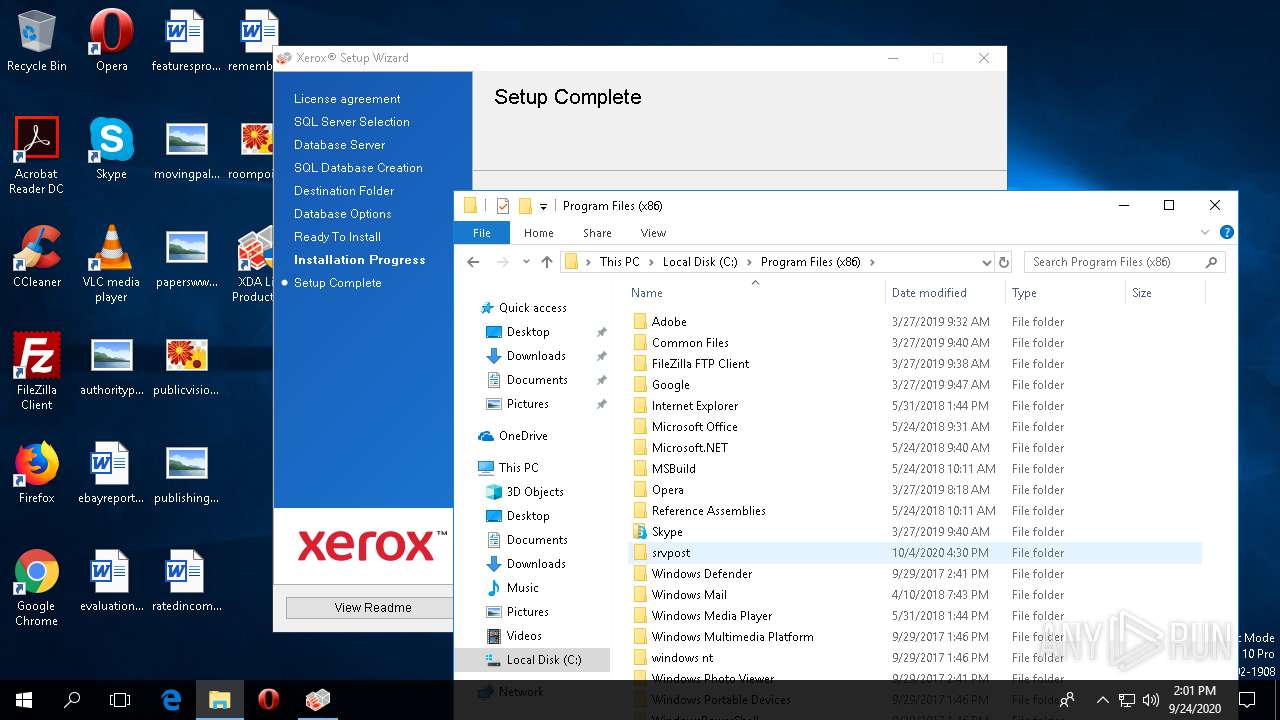
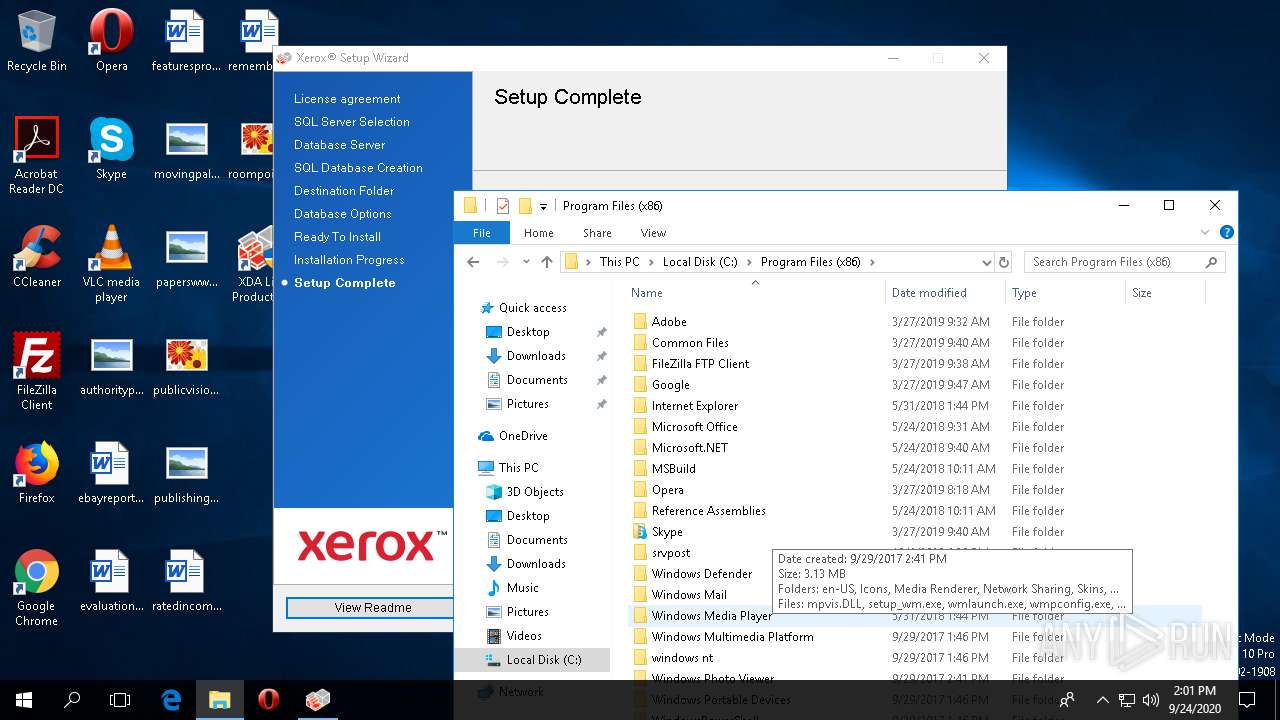
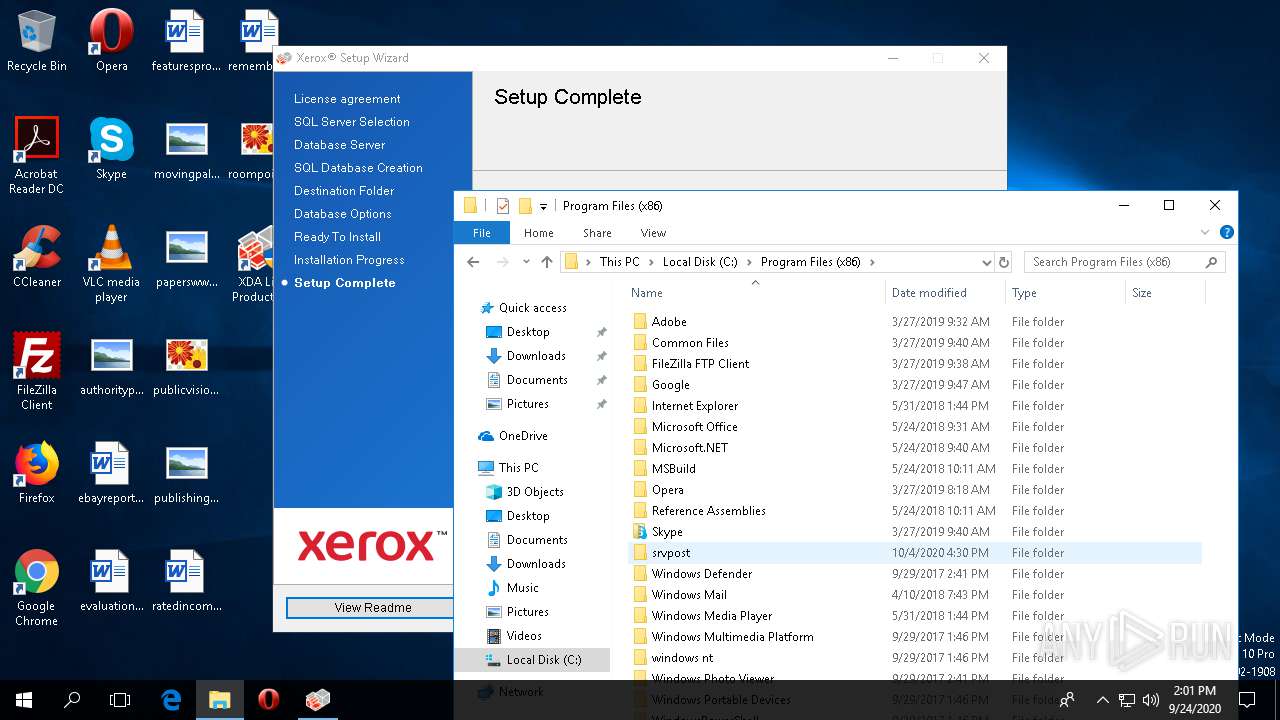
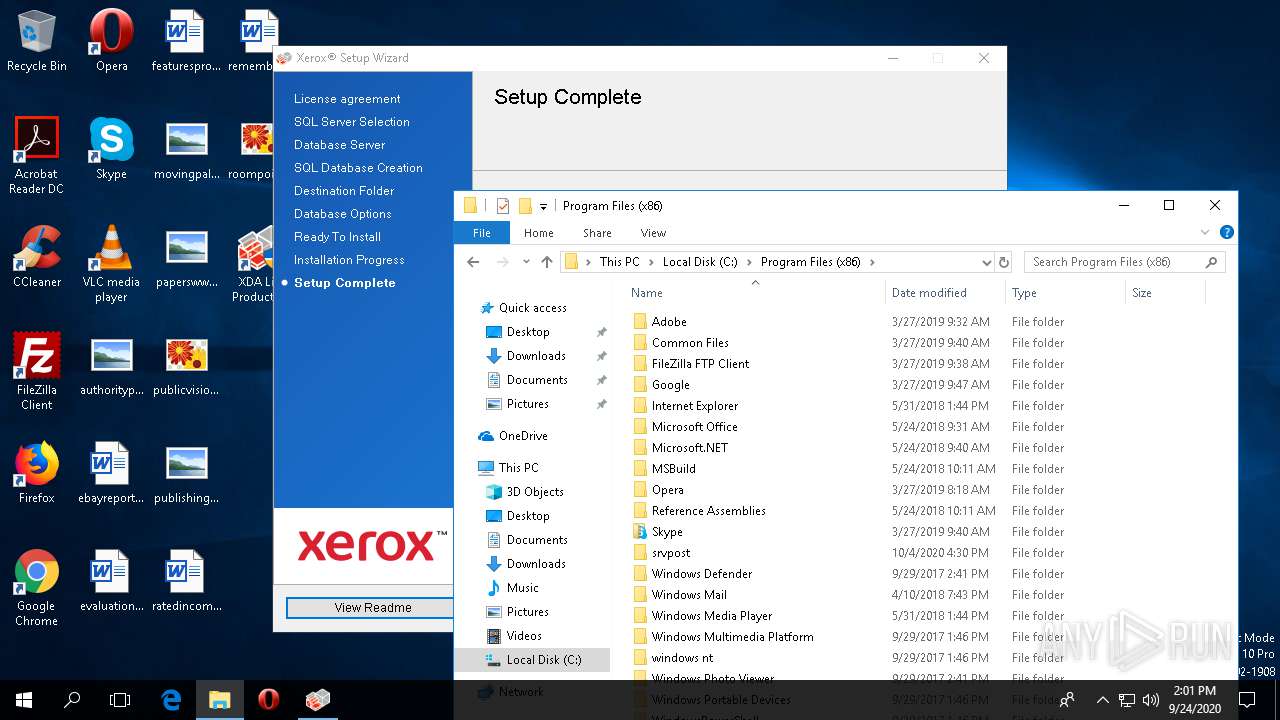
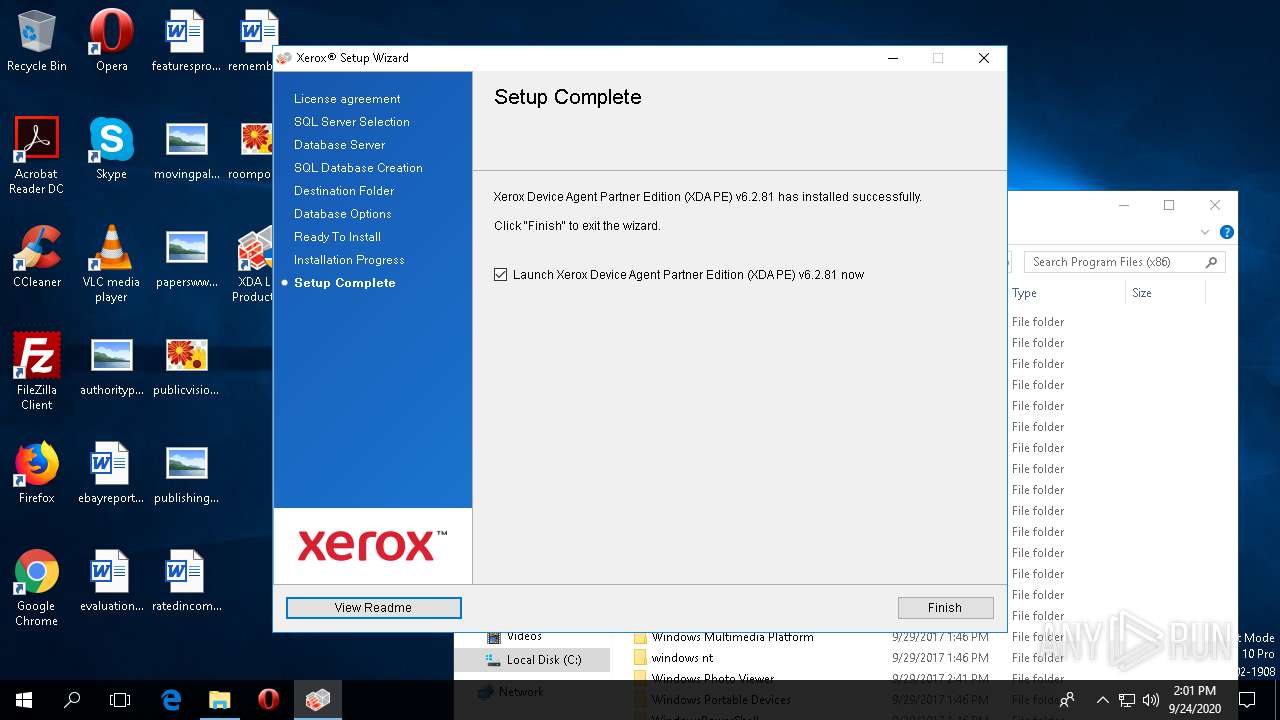
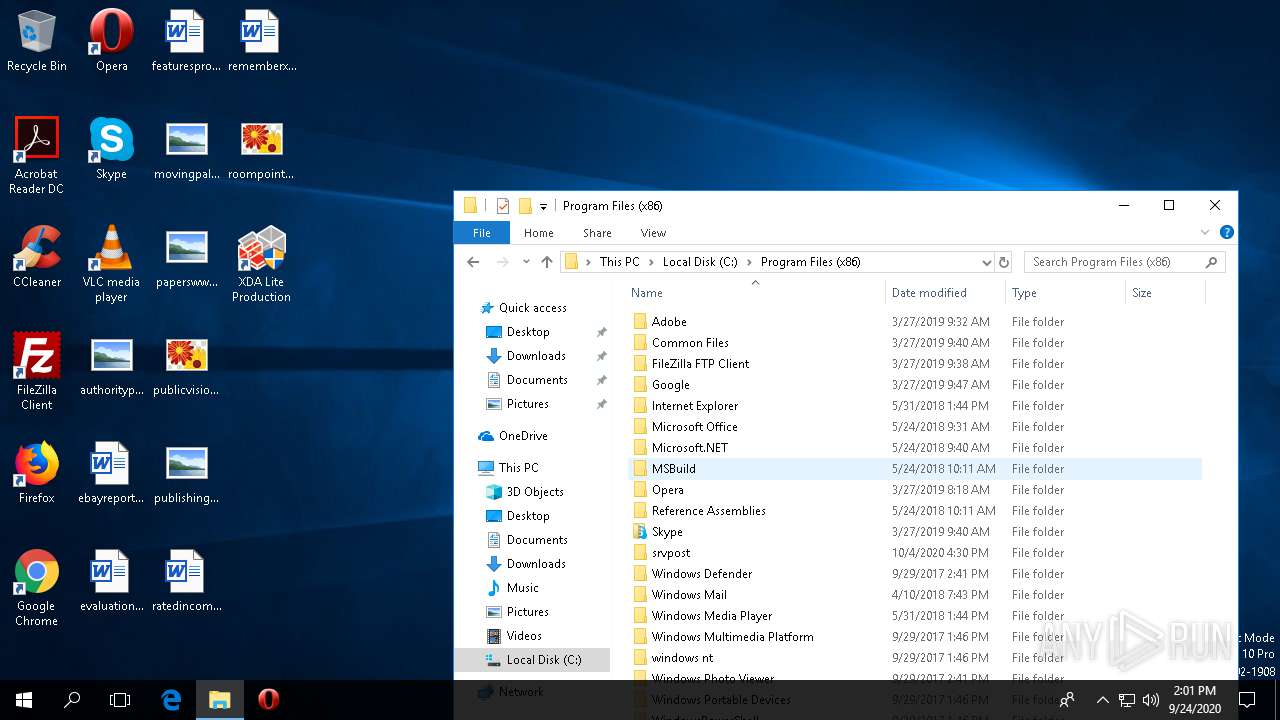
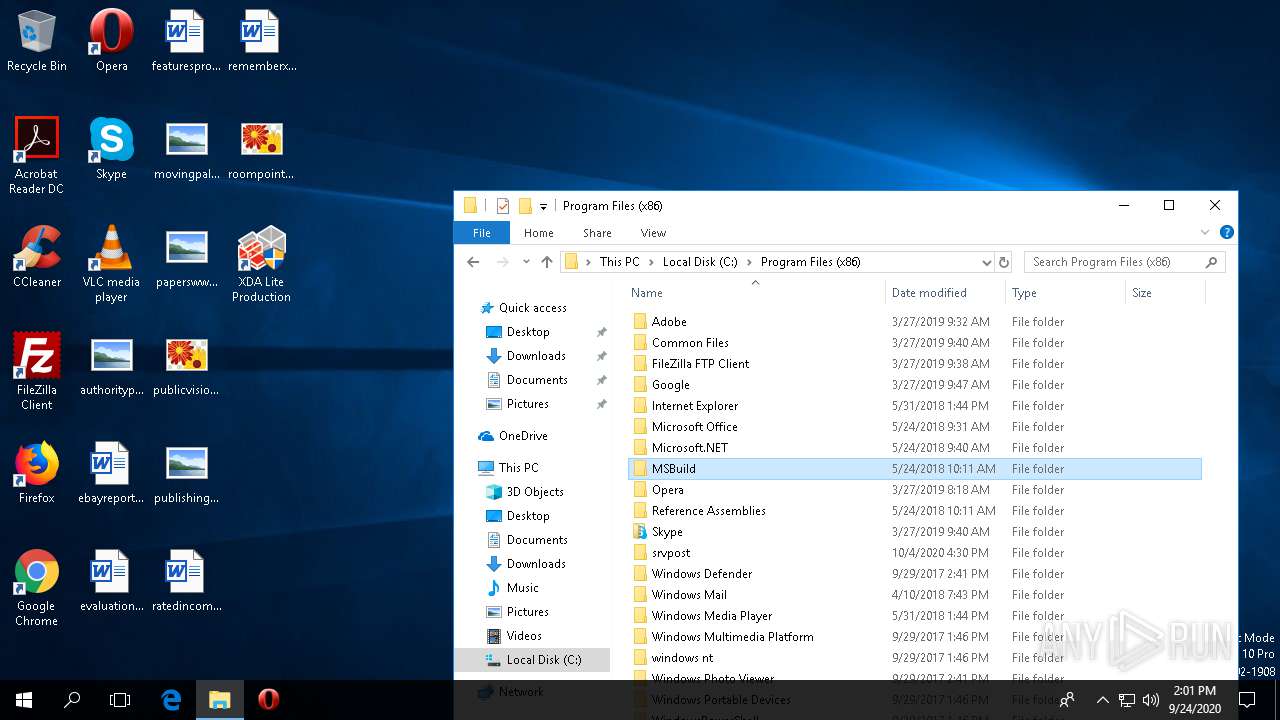
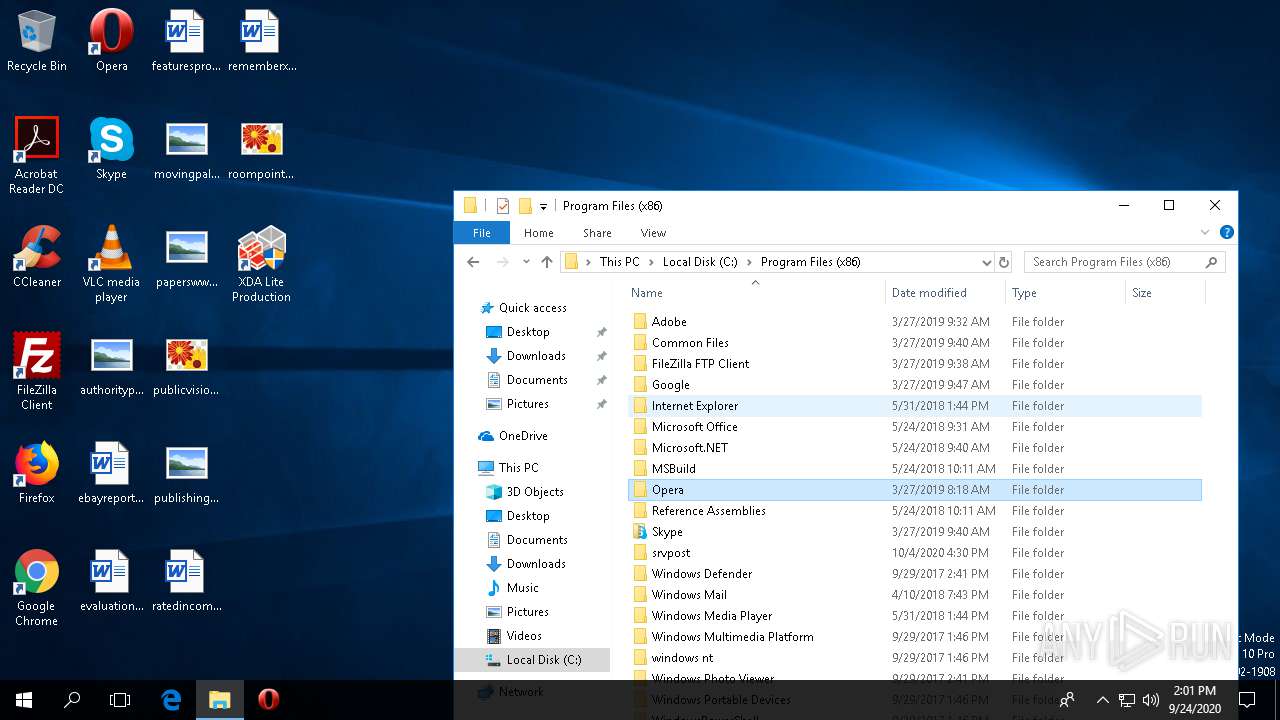
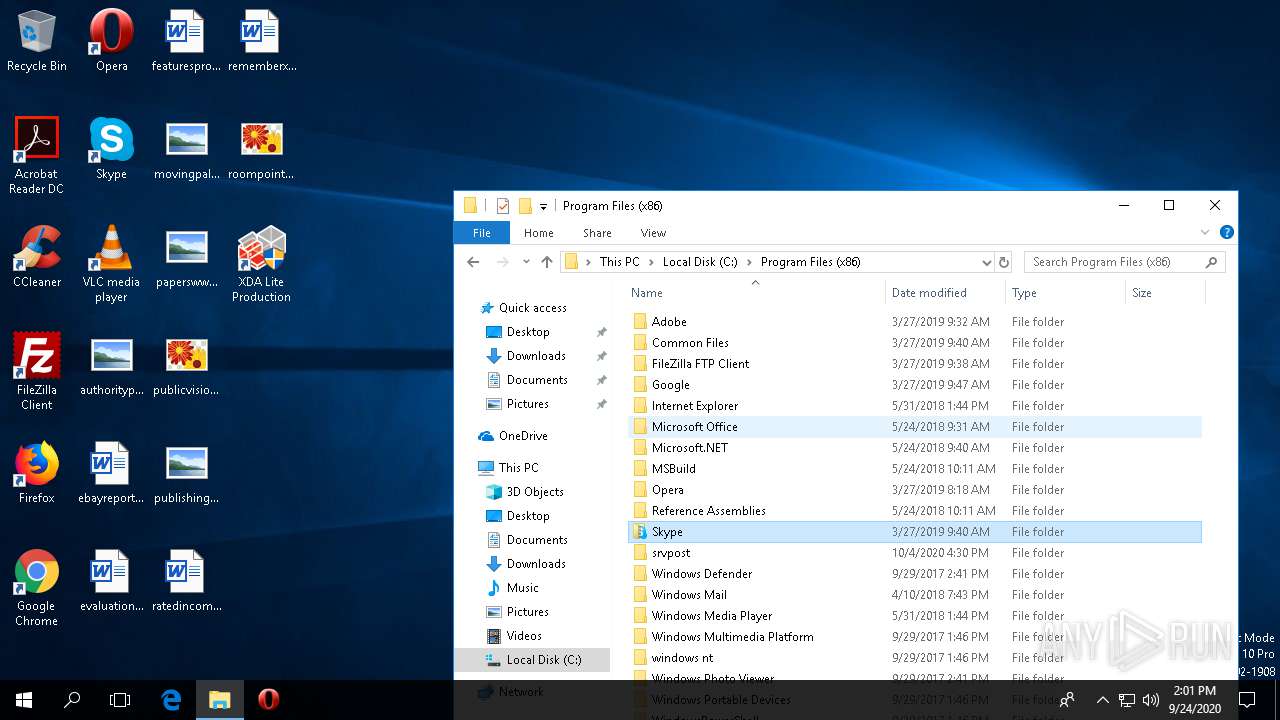
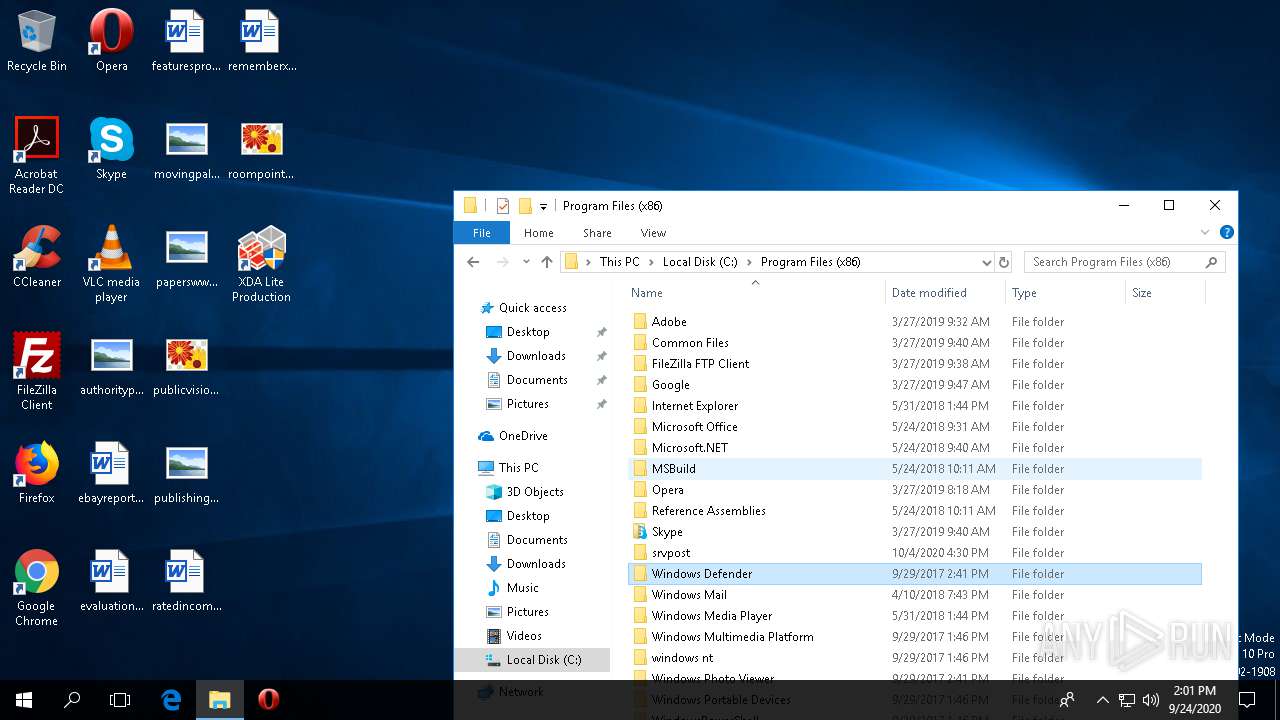
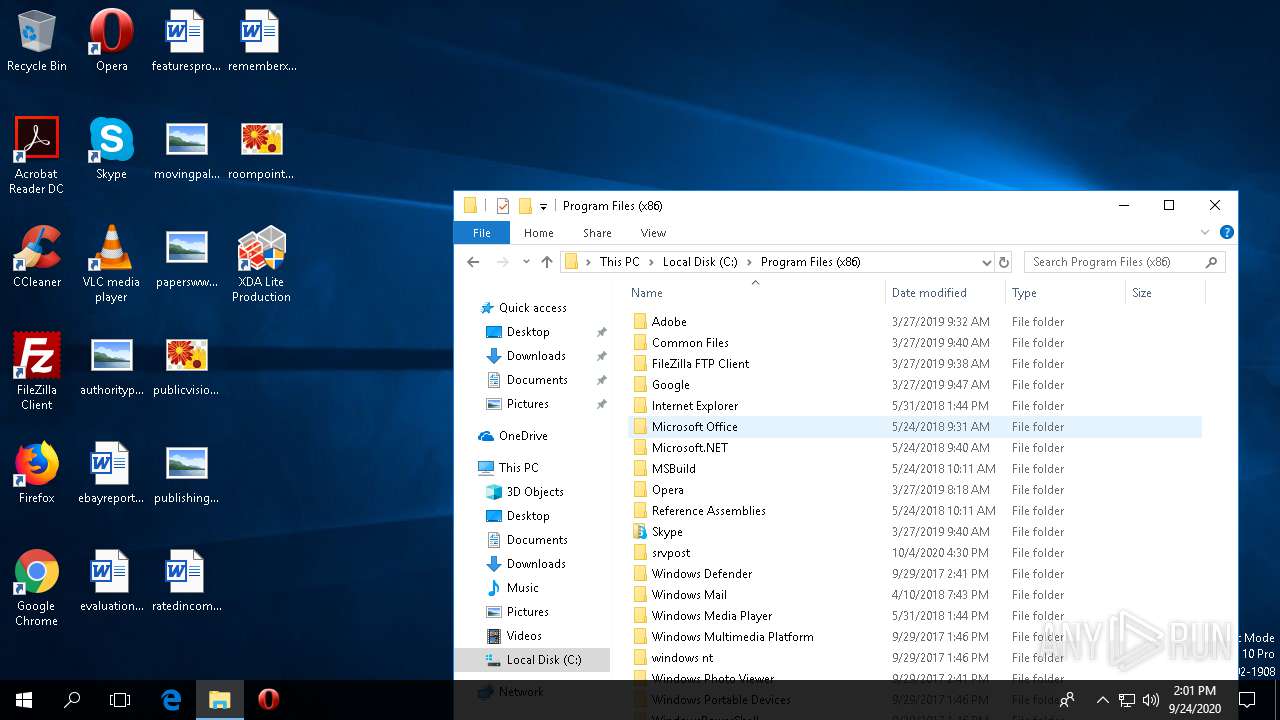
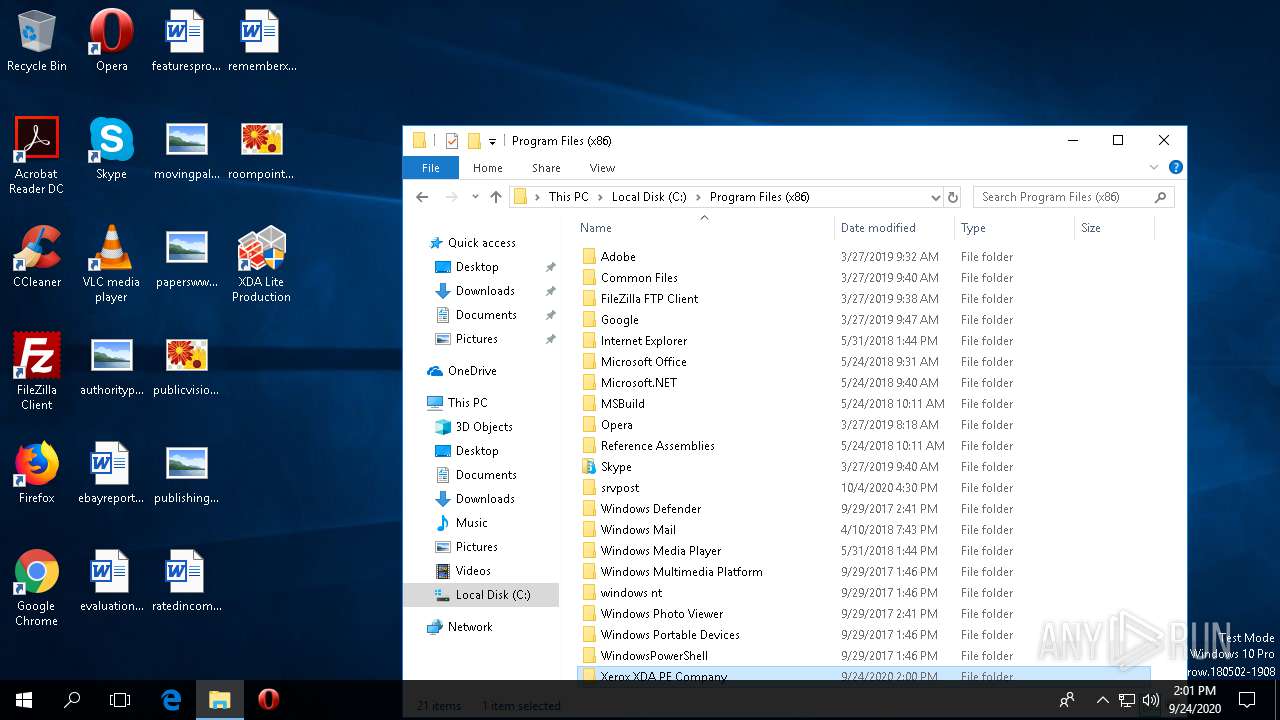
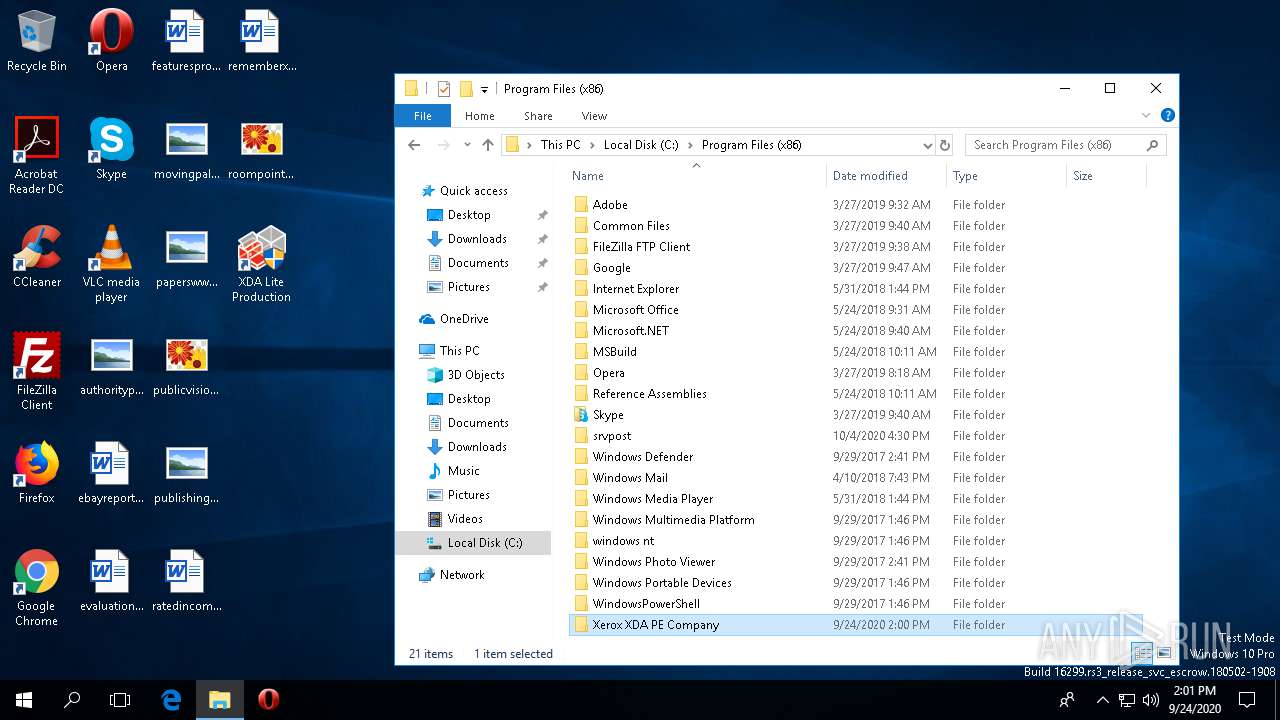
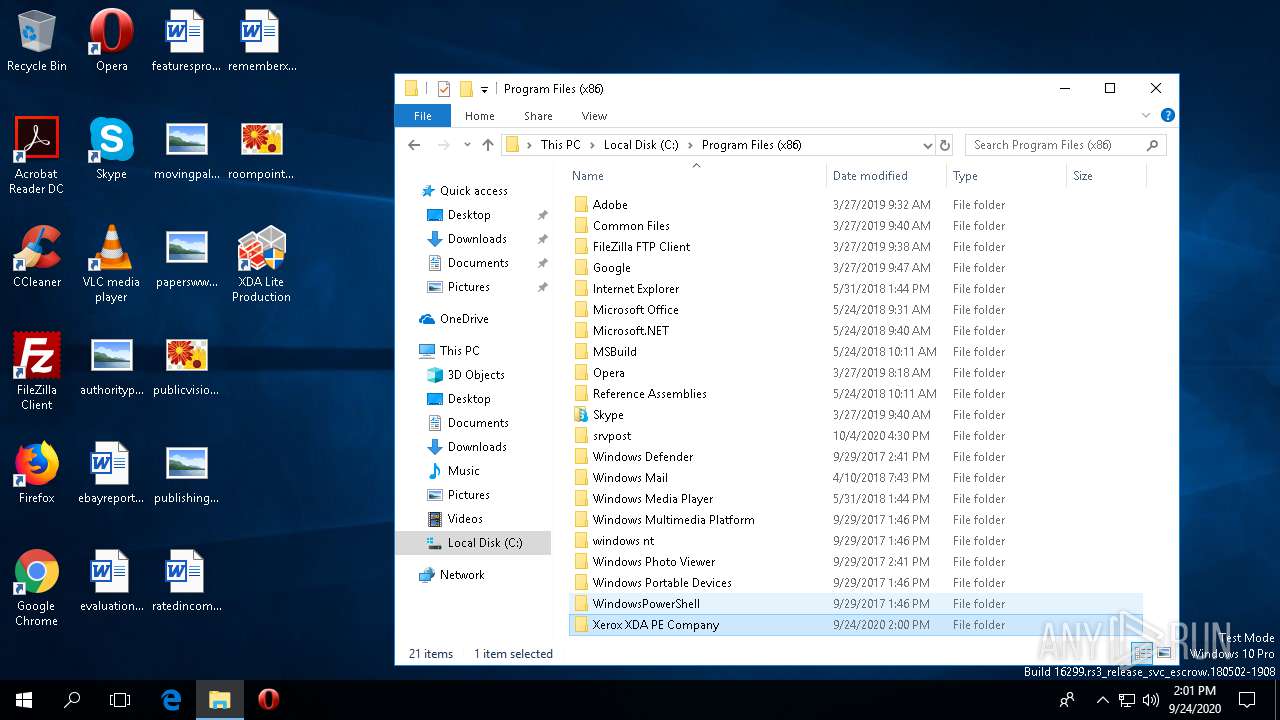
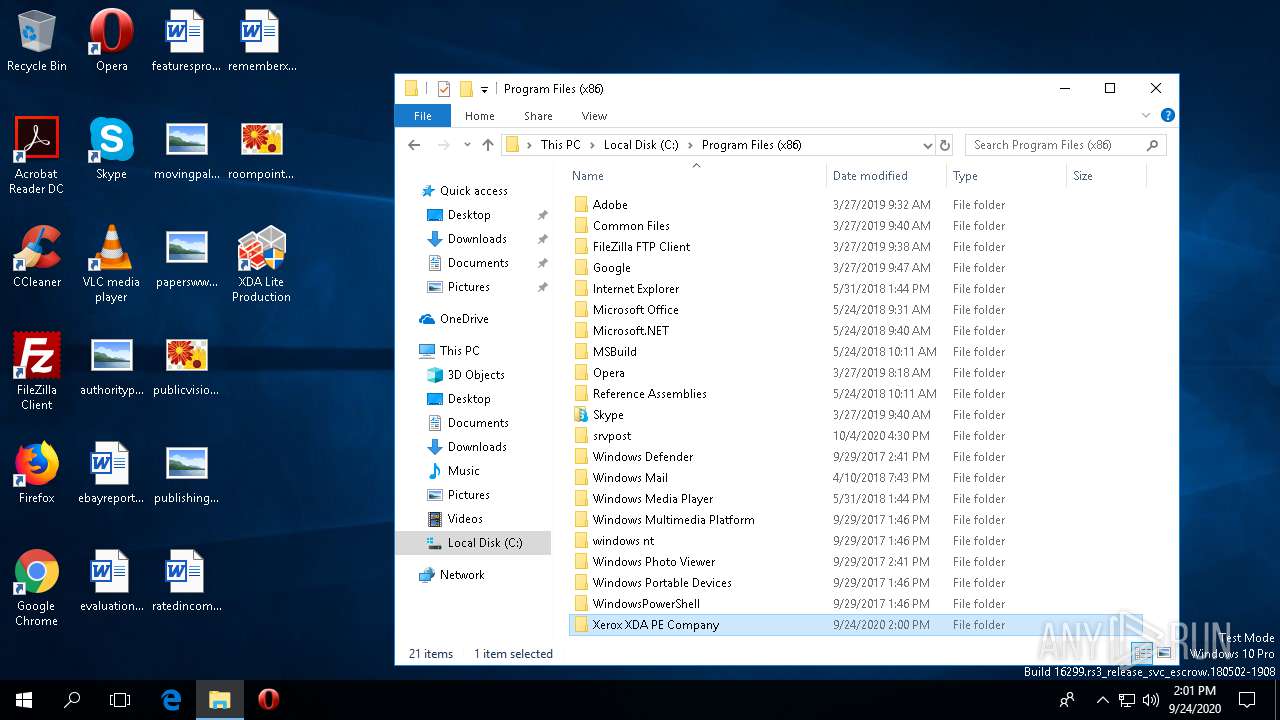
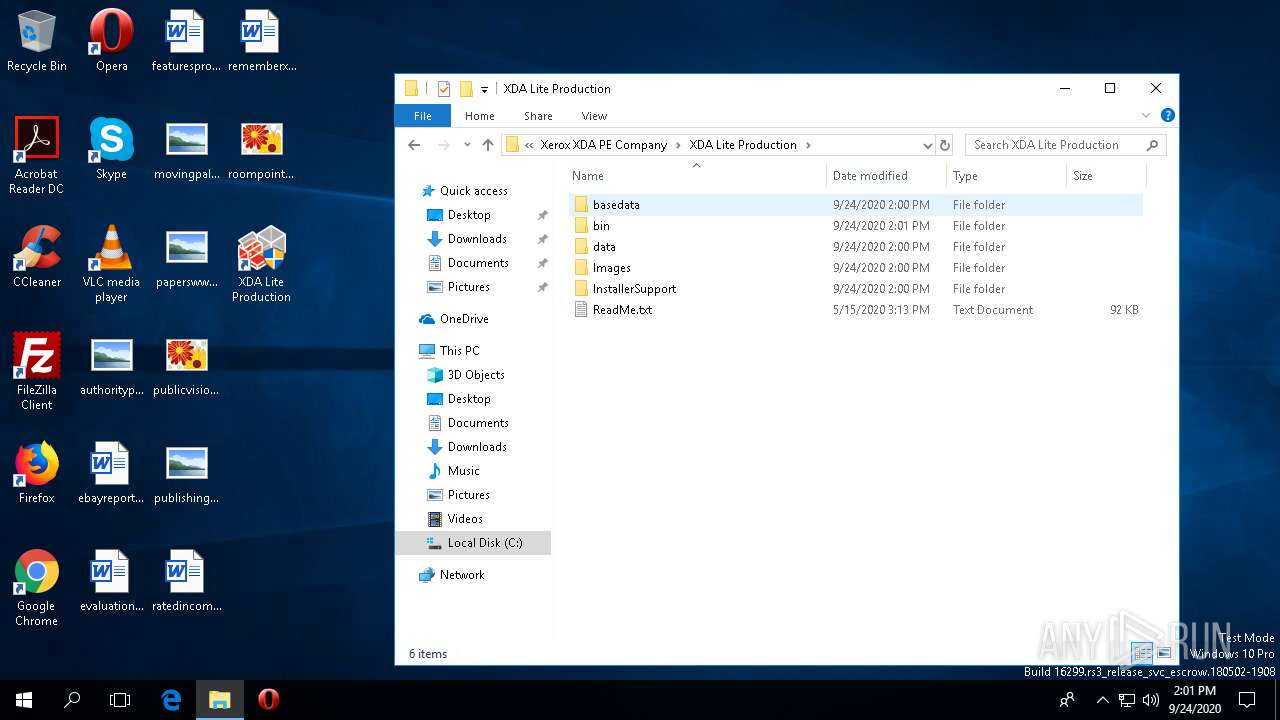
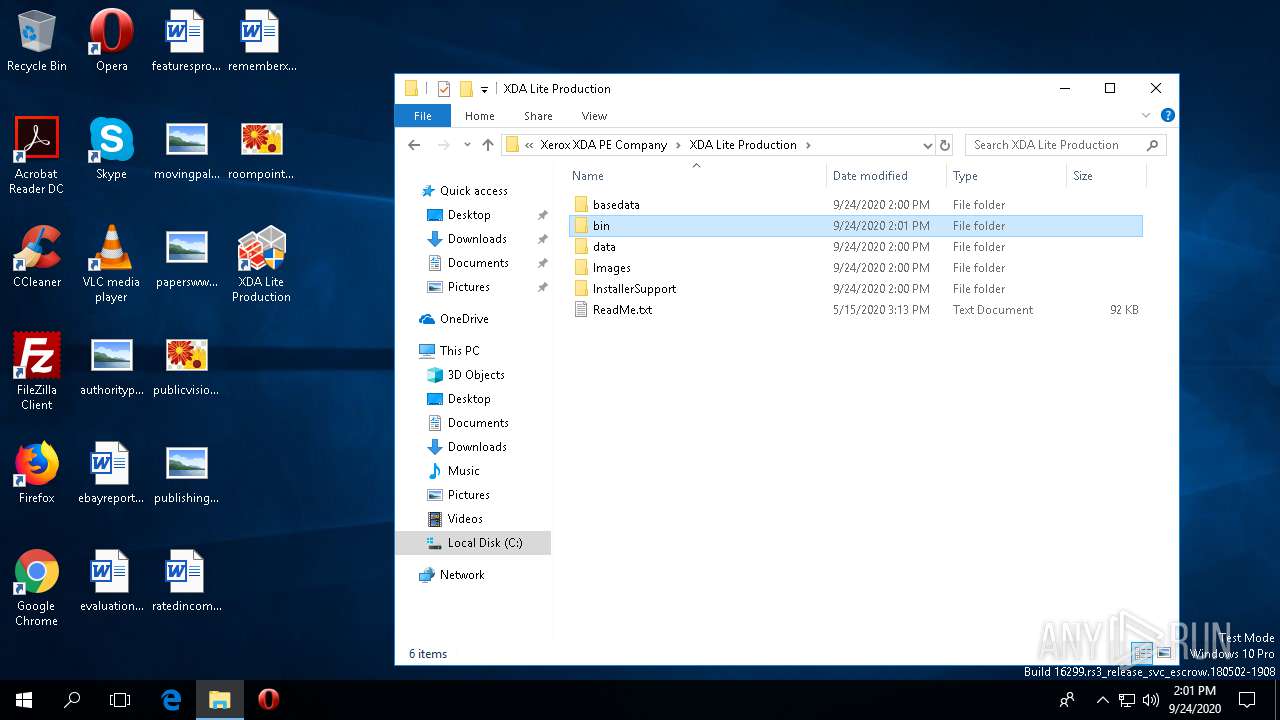
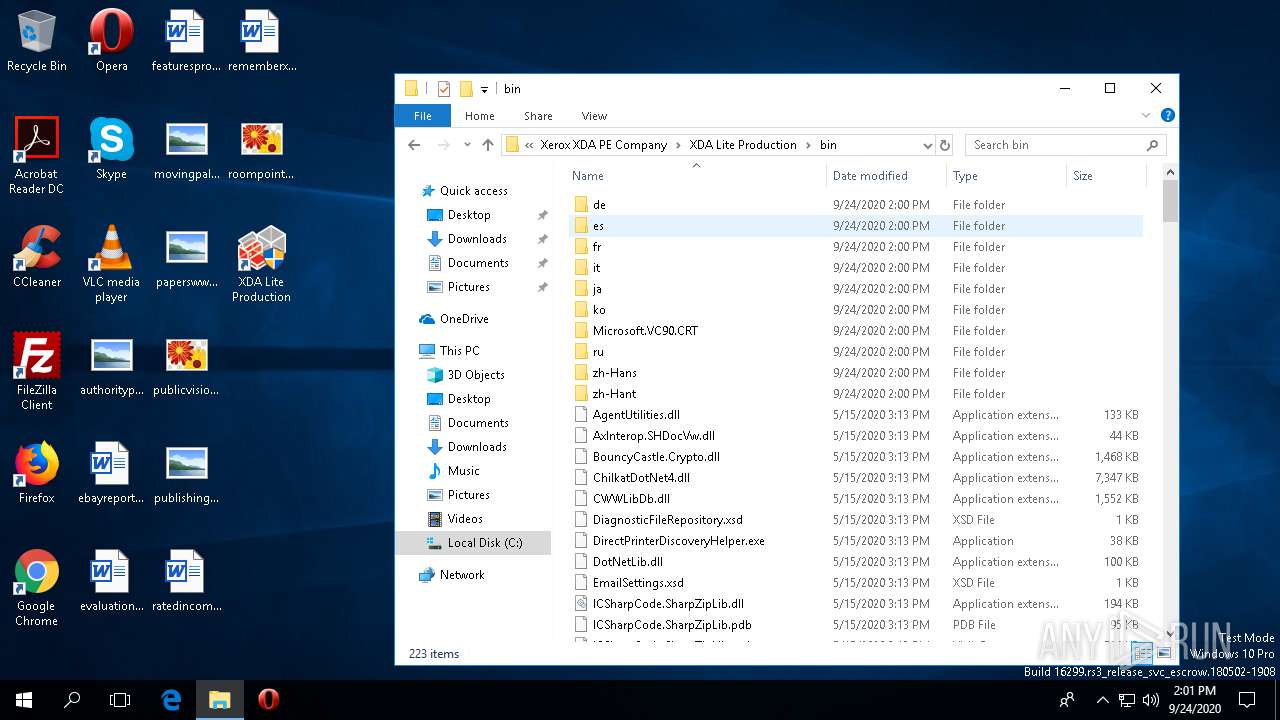
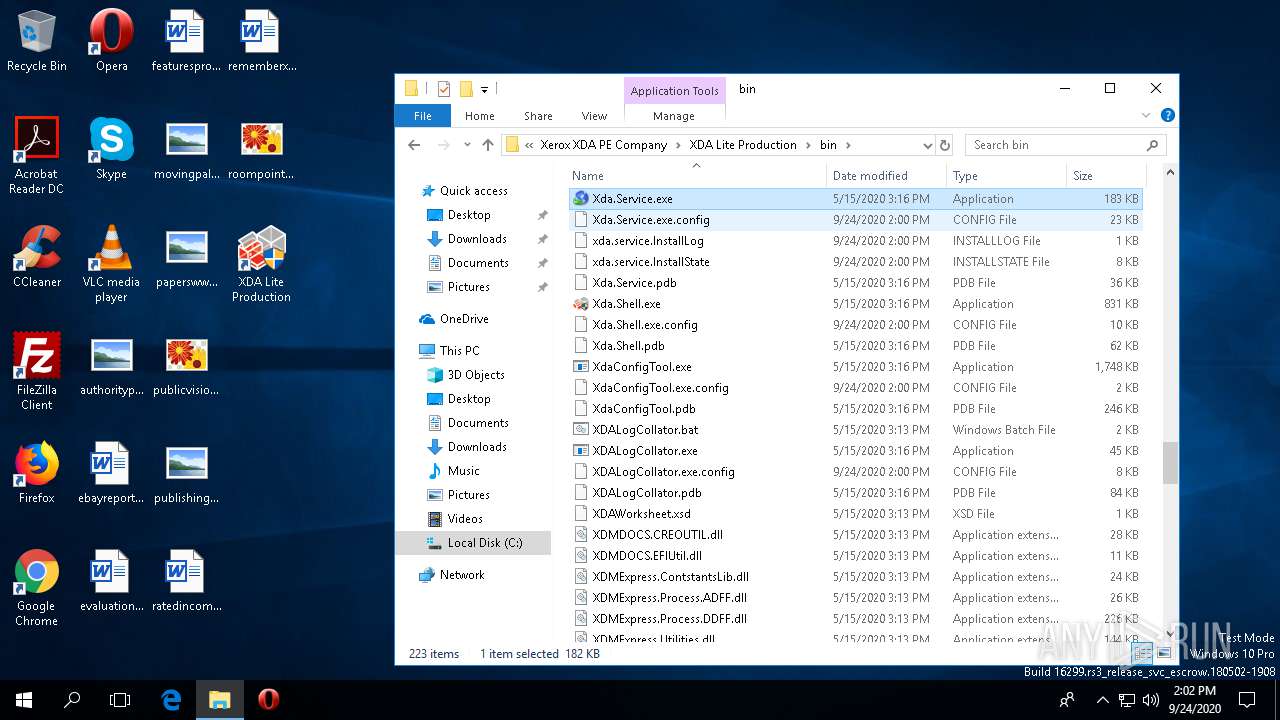
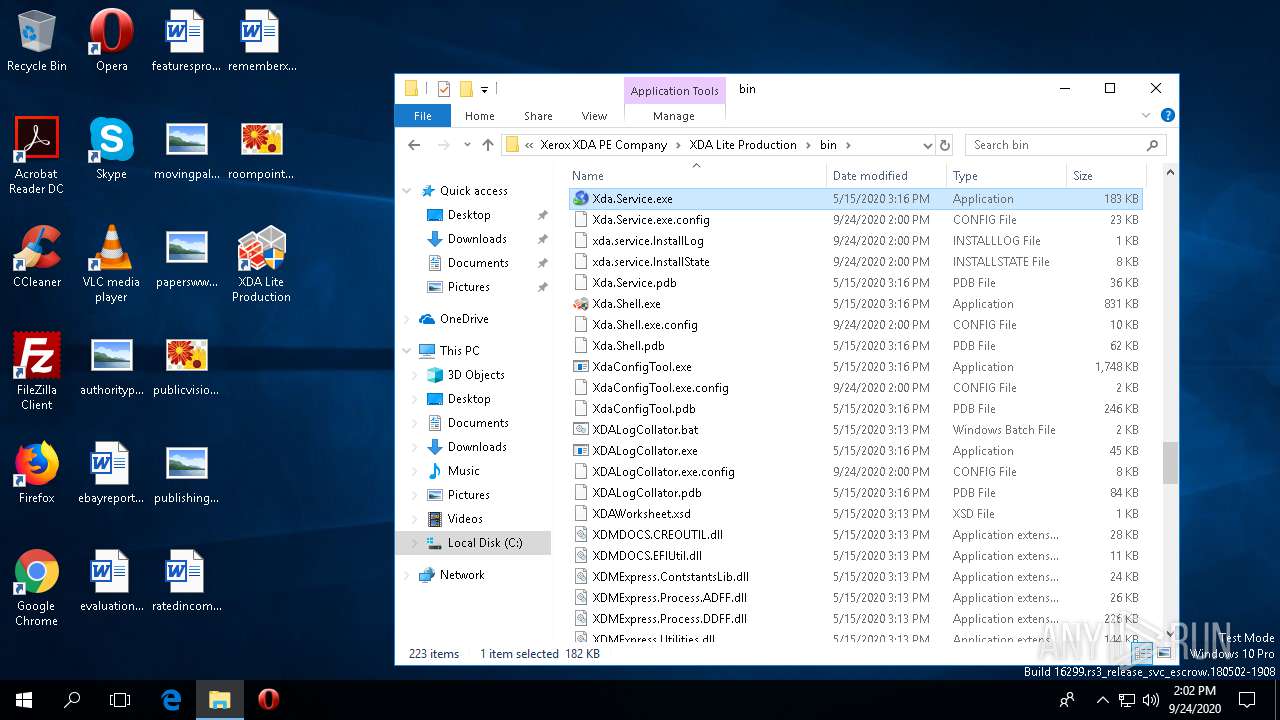
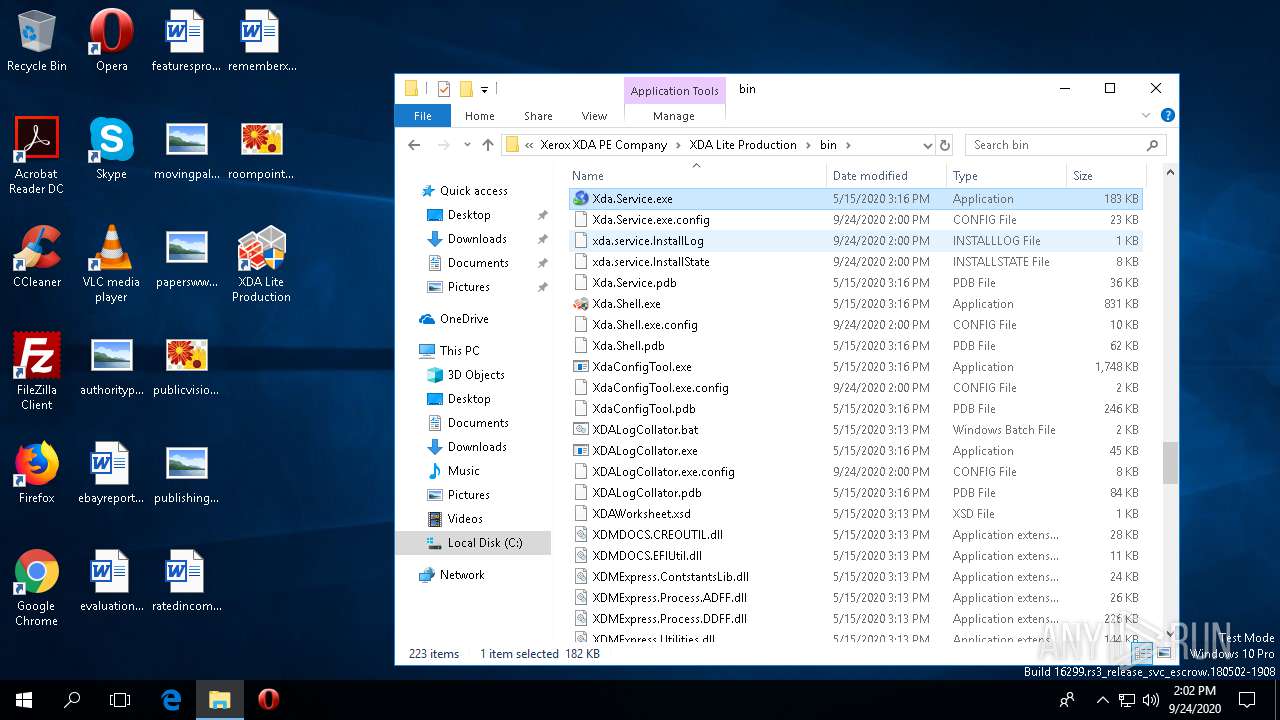
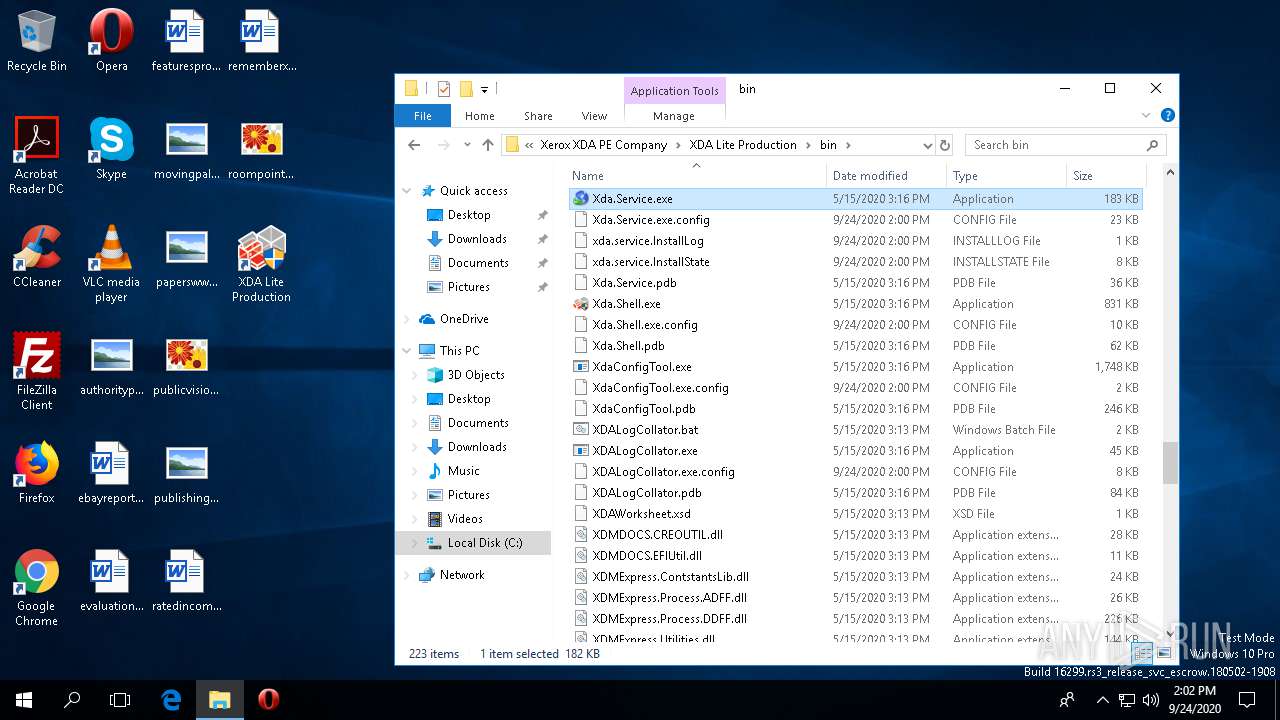
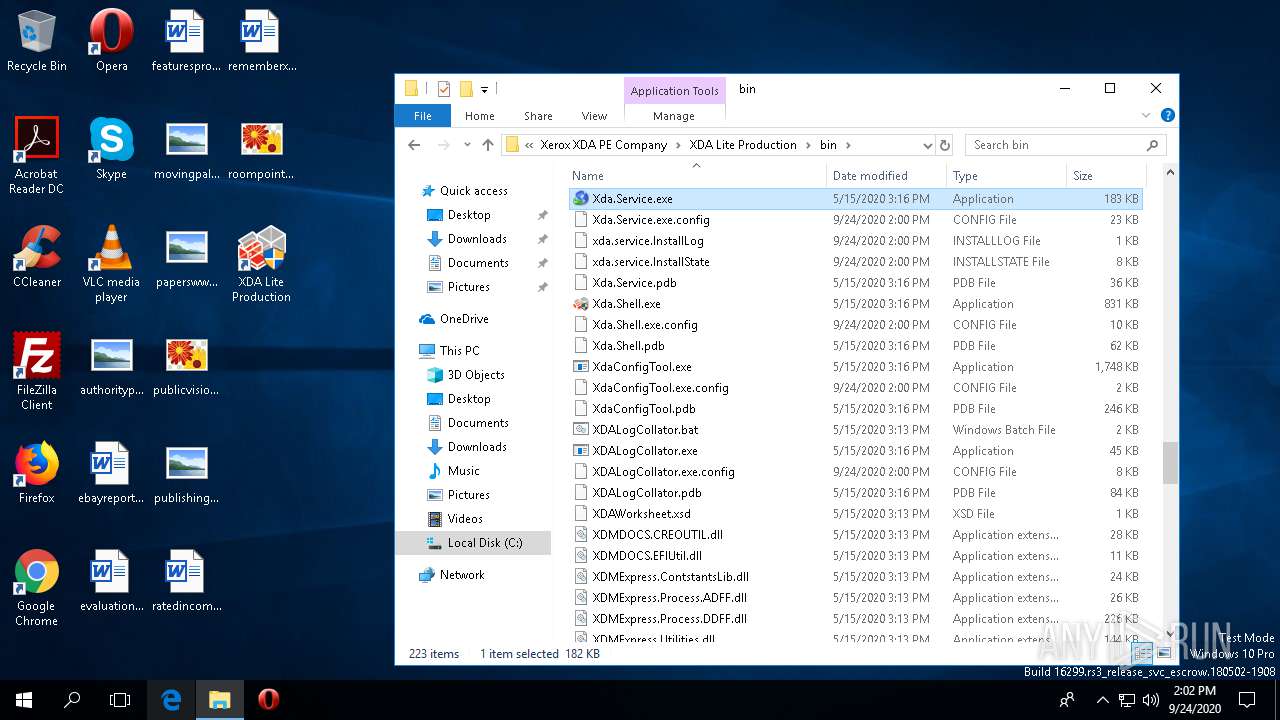
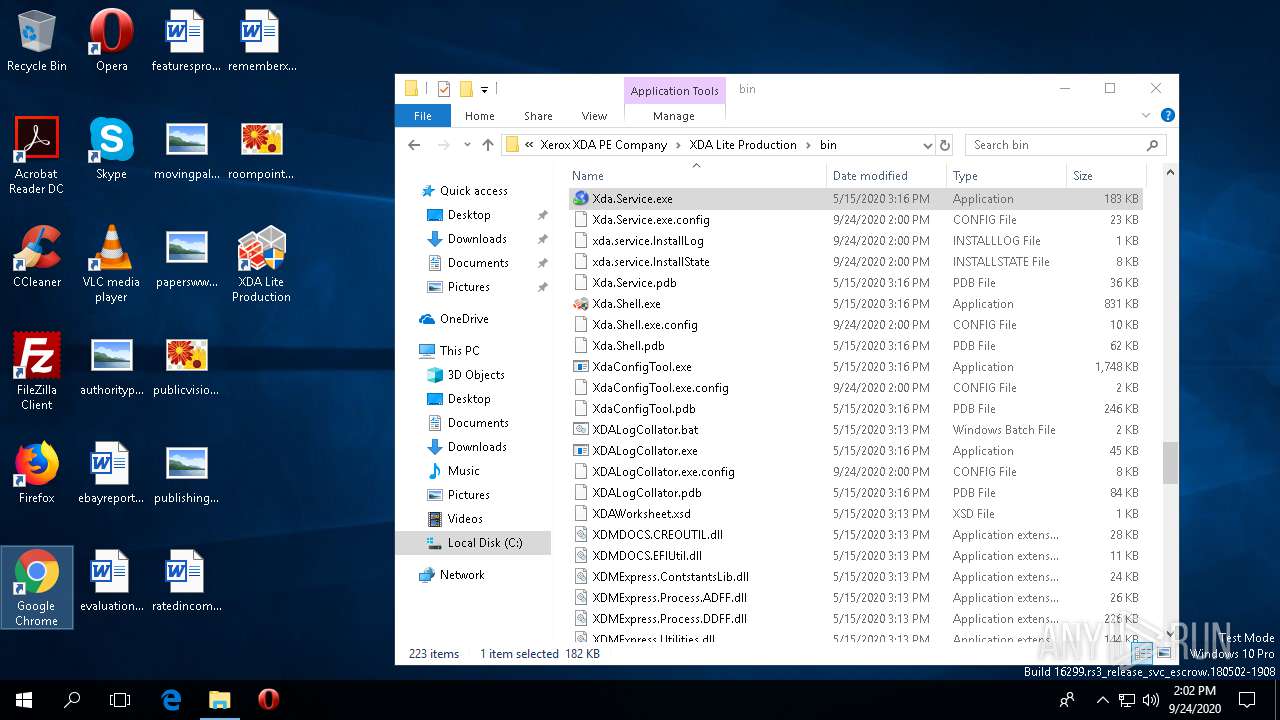
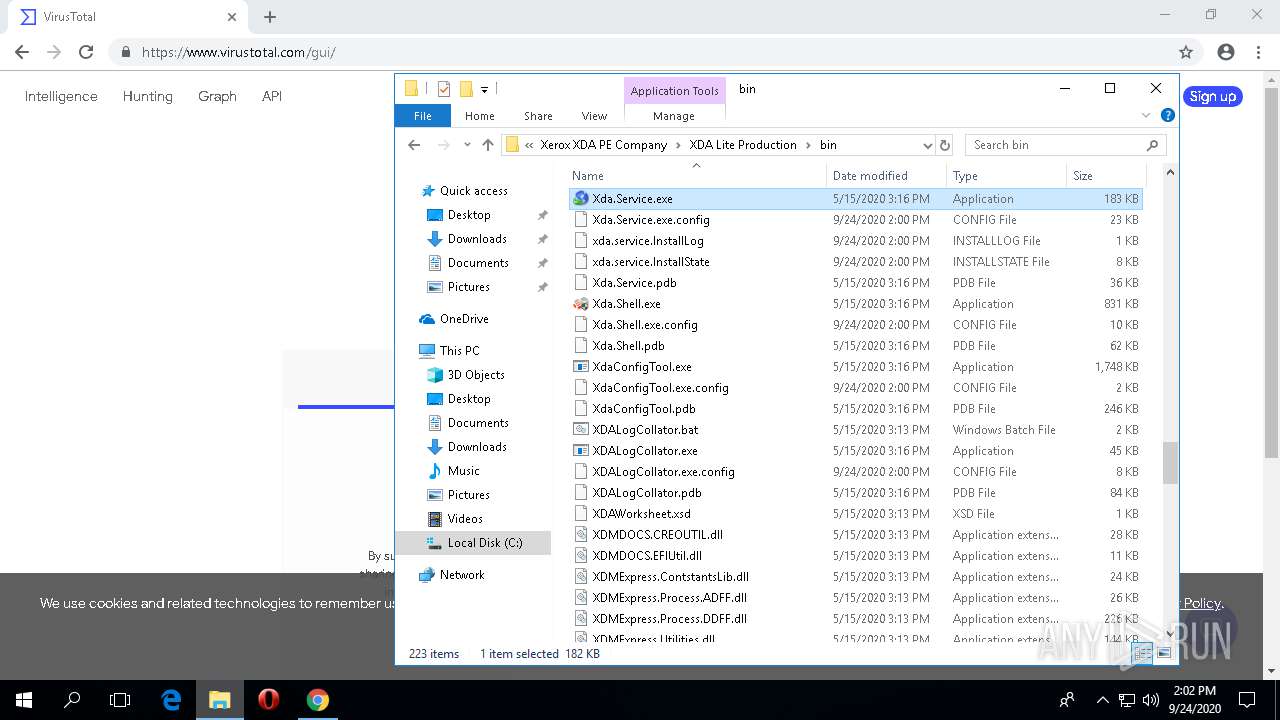
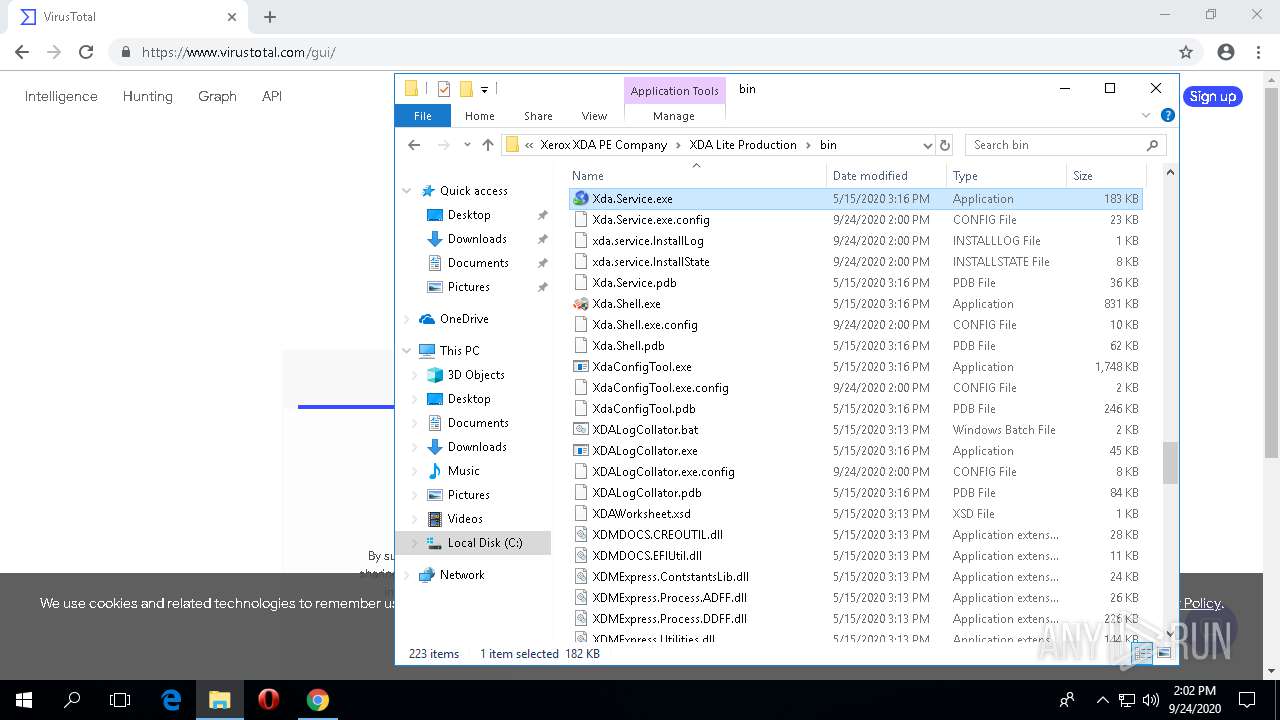
Creates files in the program directory
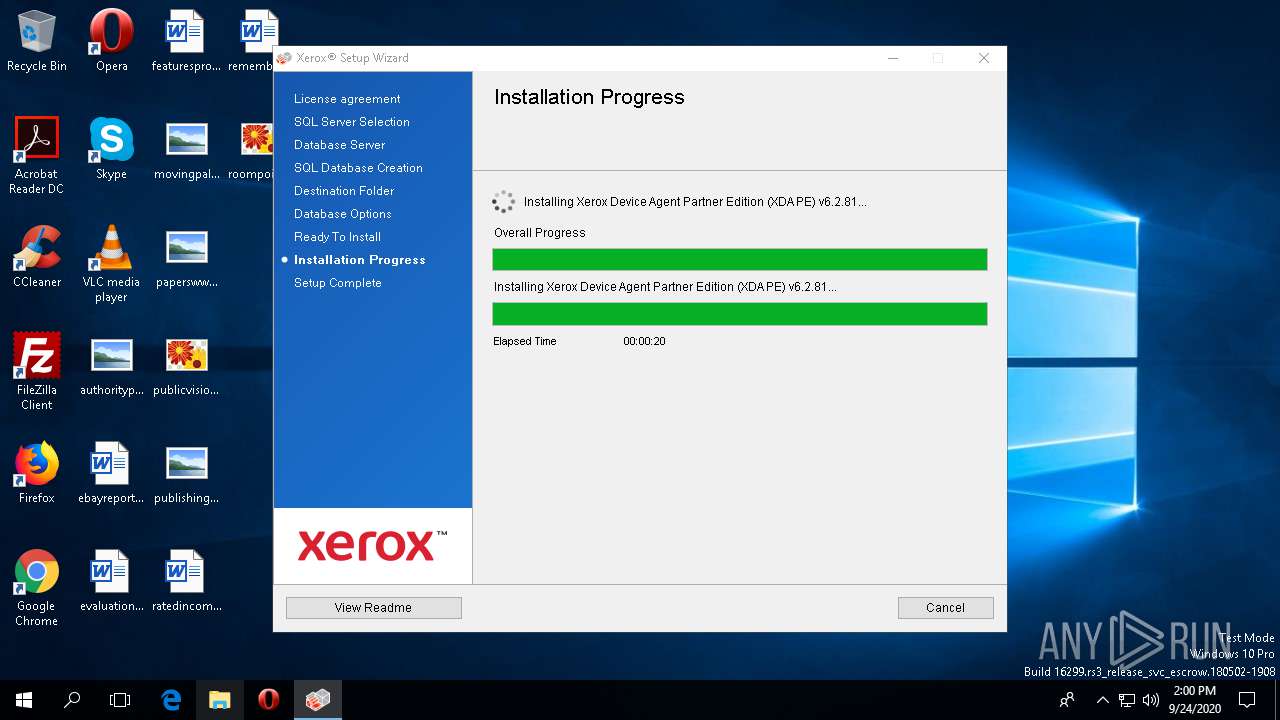
- Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe (PID: 780)
- Setup.exe (PID: 864)
- rundll32.exe (PID: 2060)
- rundll32.exe (PID: 1668)
- rundll32.exe (PID: 3820)
- BrandingTask.exe (PID: 796)
- DBCreate.exe (PID: 3364)
- rundll32.exe (PID: 176)
- xda.service.exe (PID: 3712)
Executable content was dropped or overwritten
- Setup.exe (PID: 864)
- rundll32.exe (PID: 1668)
- rundll32.exe (PID: 3820)
- DBCreate.exe (PID: 3364)
- msiexec.exe (PID: 3928)
- rundll32.exe (PID: 1620)
- rundll32.exe (PID: 176)
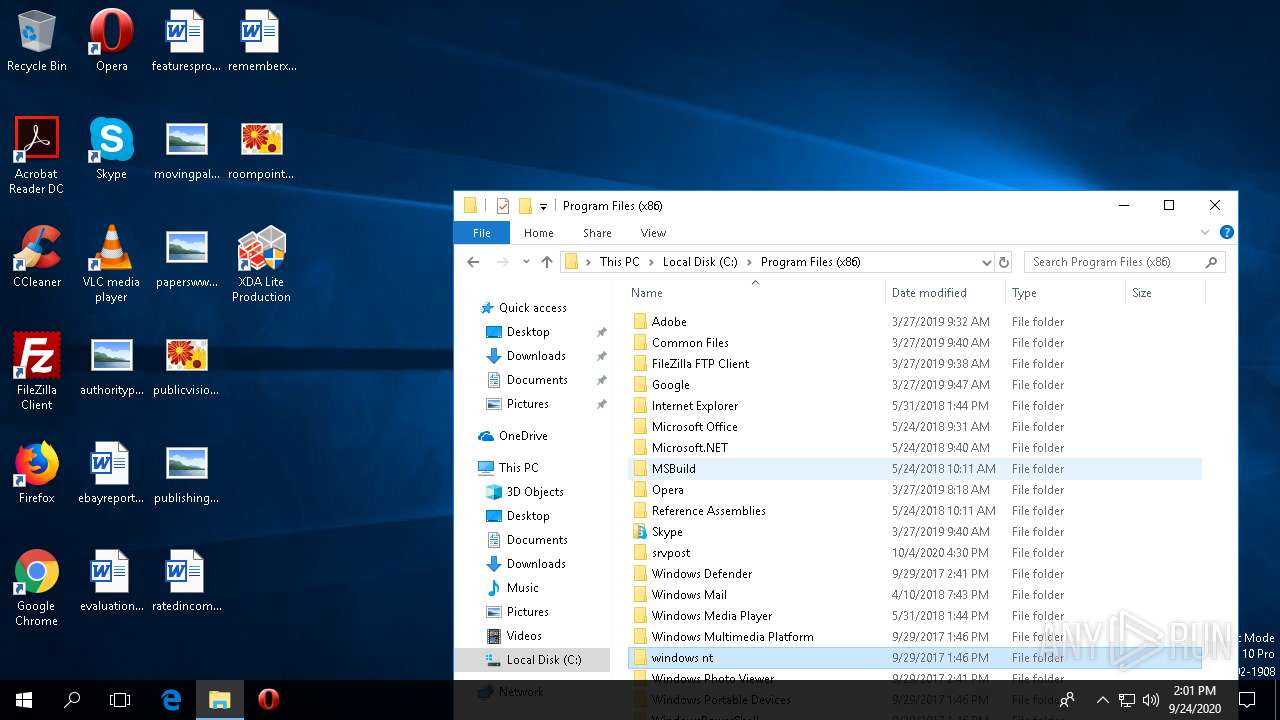
Creates files in the Windows directory
- msiexec.exe (PID: 3928)
- xda.service.exe (PID: 3712)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 1660)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 3820)
Uses NETSH.EXE for network configuration
- xda.service.exe (PID: 3712)
Executed as Windows Service
- xda.service.exe (PID: 3712)
- Xerox.XDAMonitorService.exe (PID: 3636)
Starts SC.EXE for service management
- cmd.exe (PID: 4100)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1080)
INFO
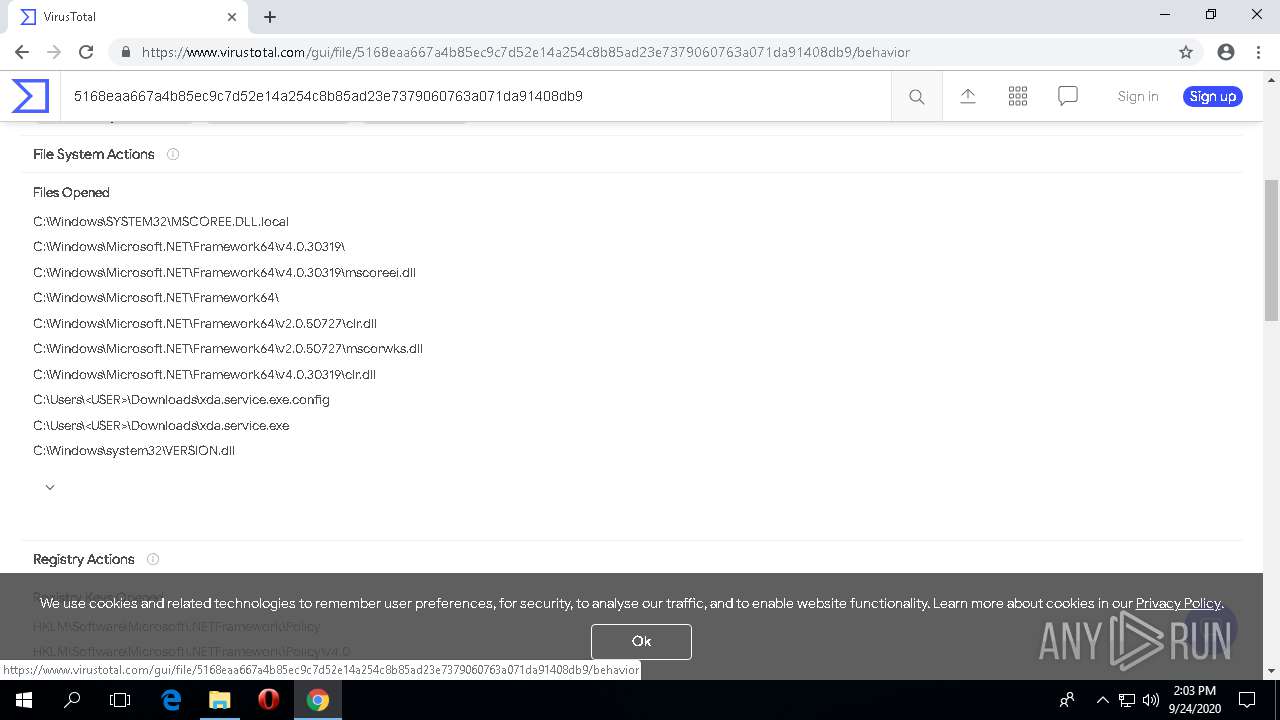
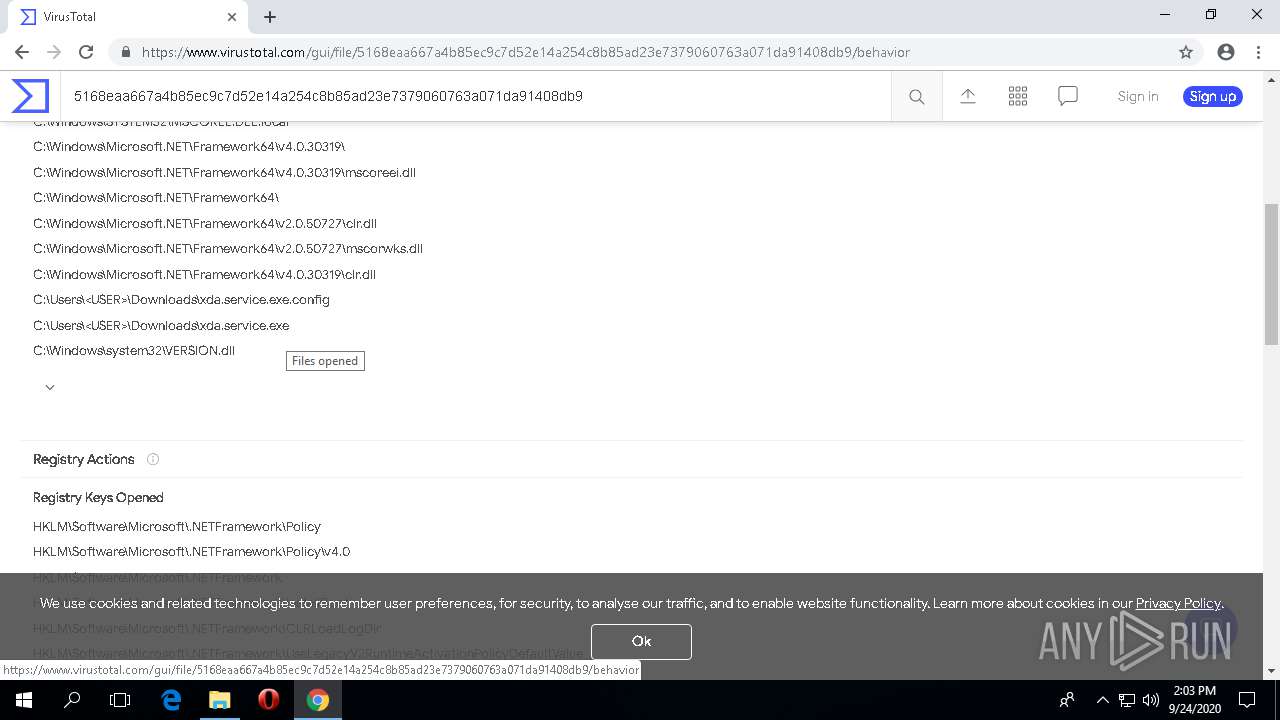
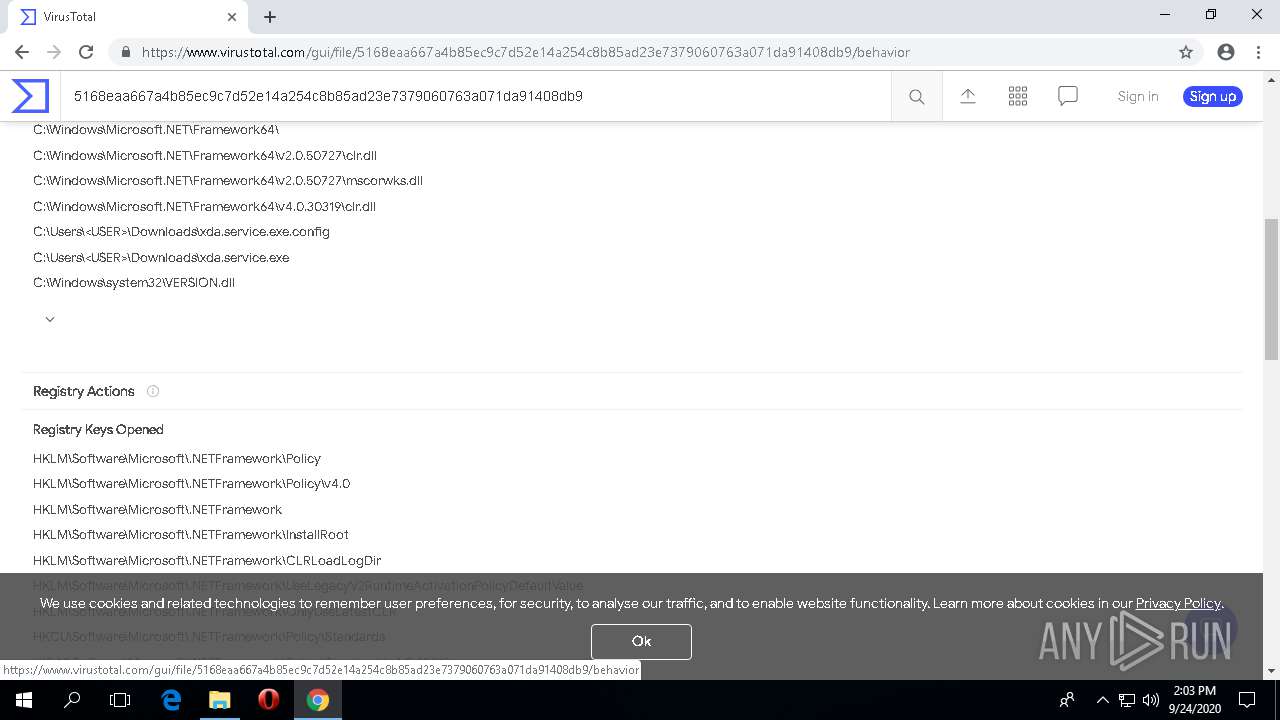
Reads the software policy settings
- msiexec.exe (PID: 3928)
- DBCreate.exe (PID: 3364)
- xda.service.exe (PID: 3712)
- chrome.exe (PID: 1080)
Reads settings of System Certificates
- msiexec.exe (PID: 3928)
- DBCreate.exe (PID: 3364)
- xda.service.exe (PID: 3712)
- chrome.exe (PID: 1080)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1660)
Creates a software uninstall entry
- msiexec.exe (PID: 3928)
Creates files in the program directory
- msiexec.exe (PID: 3928)
Application launched itself
- chrome.exe (PID: 1080)
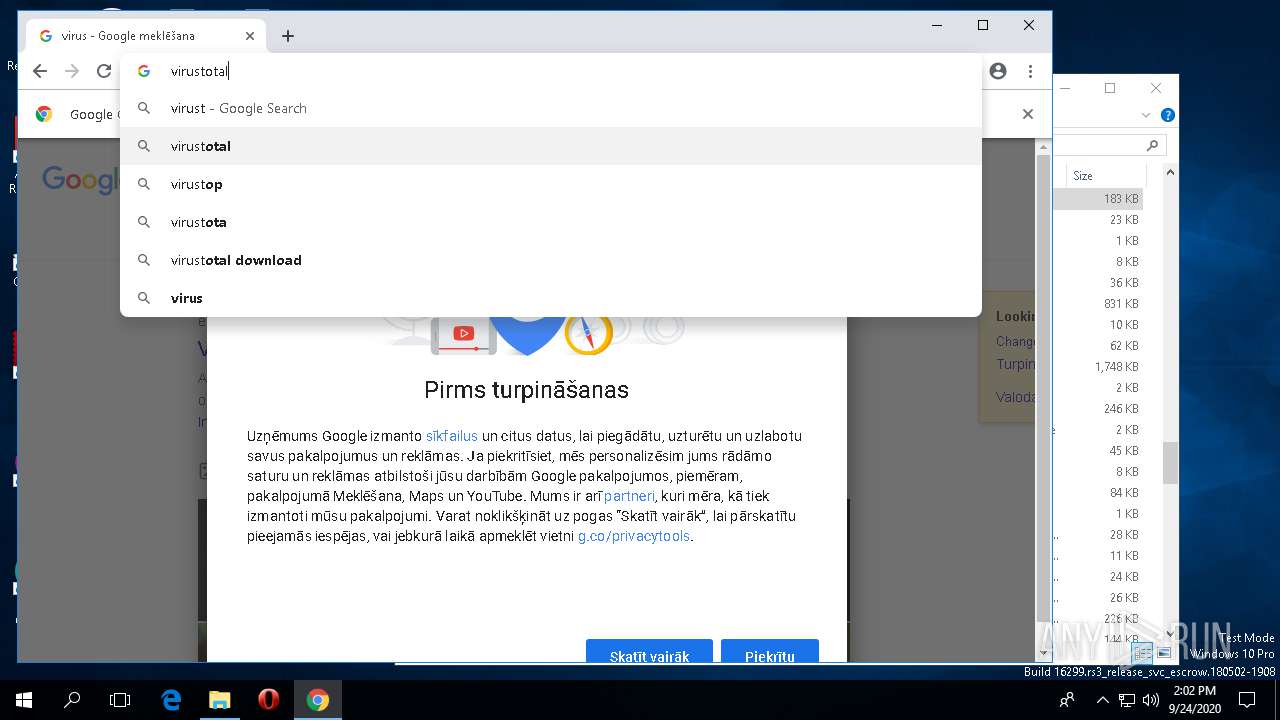
Manual execution by user
- chrome.exe (PID: 1080)
Reads the hosts file
- chrome.exe (PID: 1080)
Reads the machine GUID from the registry
- chrome.exe (PID: 1080)
Searches for installed software
- chrome.exe (PID: 1080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
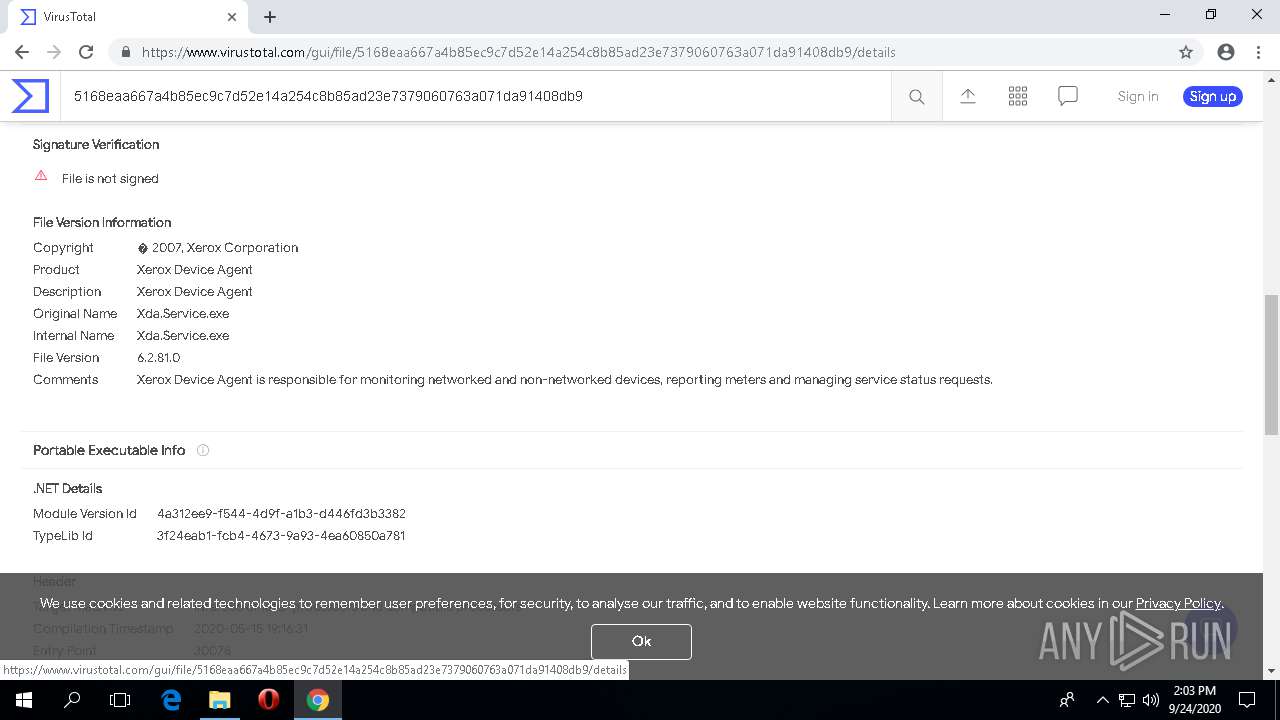
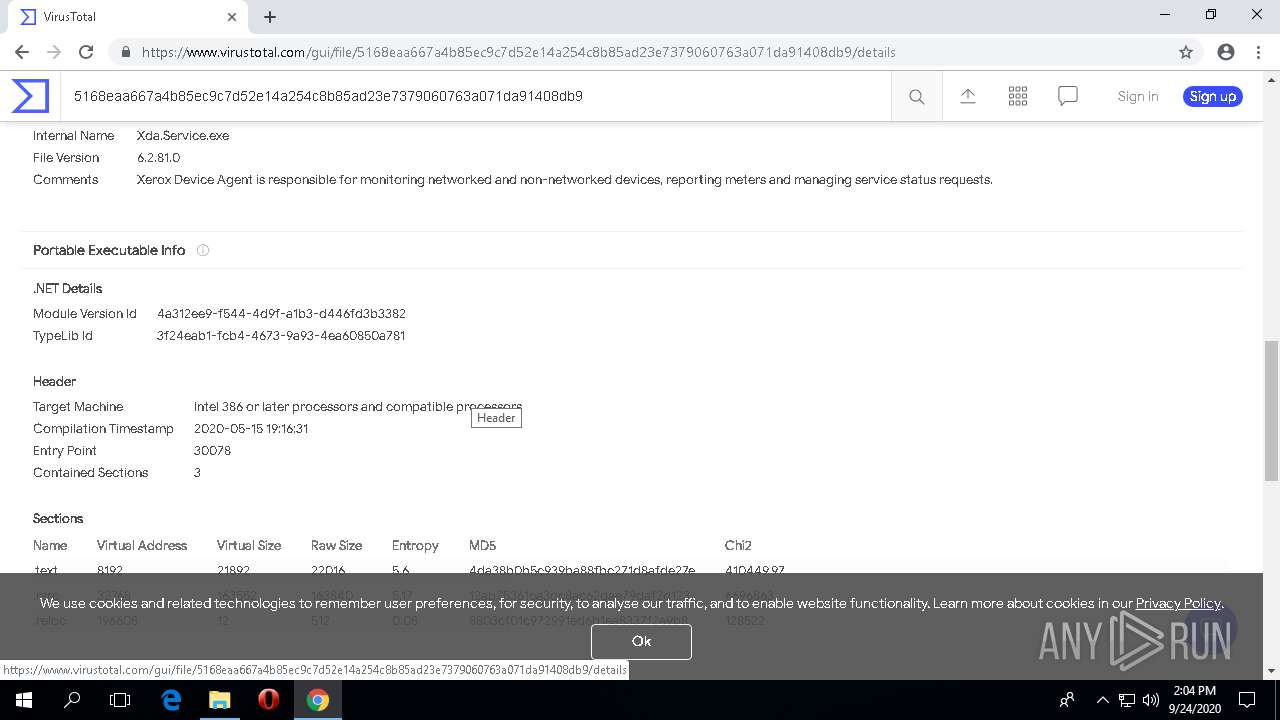
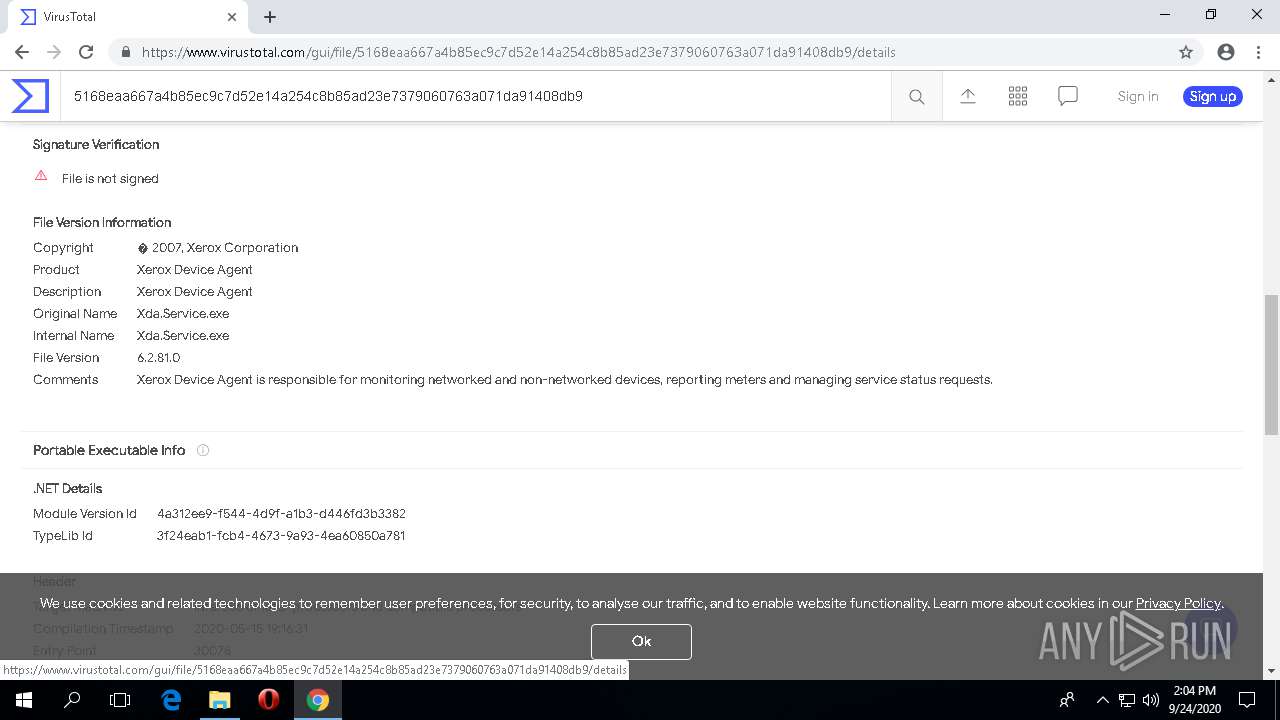
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:18 23:30:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 852992 |
| InitializedDataSize: | 56320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd22c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.11.56.0 |
| ProductVersionNumber: | 6.2.81.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Xerox Corporation |
| FileDescription: | Download Manager For Xerox XDA PE Company |
| FileVersion: | 2.11.56.0 |
| InternalName: | DownloadManager.exe |
| LegalCopyright: | Copyright © Xerox Corporation 2009 - 2015 |
| OriginalFileName: | DownloadManager.exe |
| ProductName: | XDA Lite Production |
| ProductVersion: | 6.2.81.0 |
| AssemblyVersion: | 2.11.56.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-May-2020 21:30:43 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 18-May-2020 21:30:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
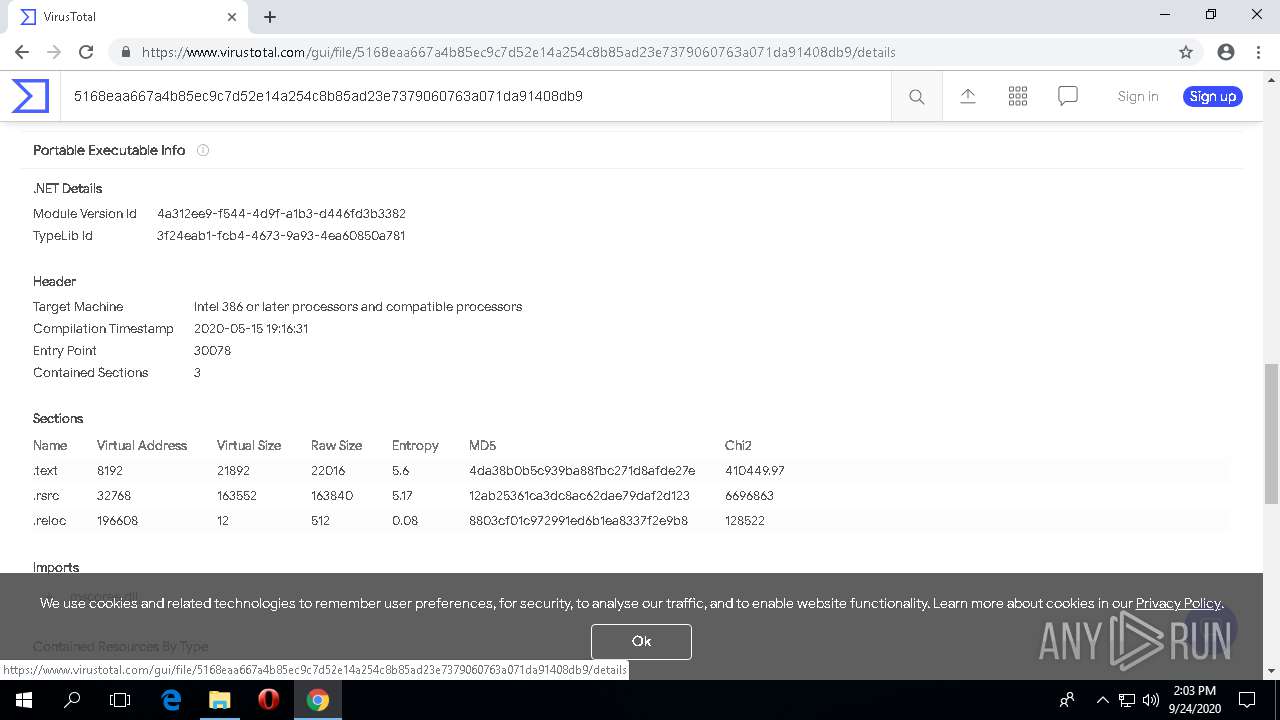
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000D0376 | 0x000D0400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56964 |
.rsrc | 0x000D4000 | 0x0000D9AF | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.71522 |
.reloc | 0x000E2000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23503 | 896 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.02277 | 4956 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.36827 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.50056 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.27211 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 7.80524 | 8244 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.0022 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.26509 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.34657 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 7.89145 | 14637 | UNKNOWN | UNKNOWN | RT_ICON |
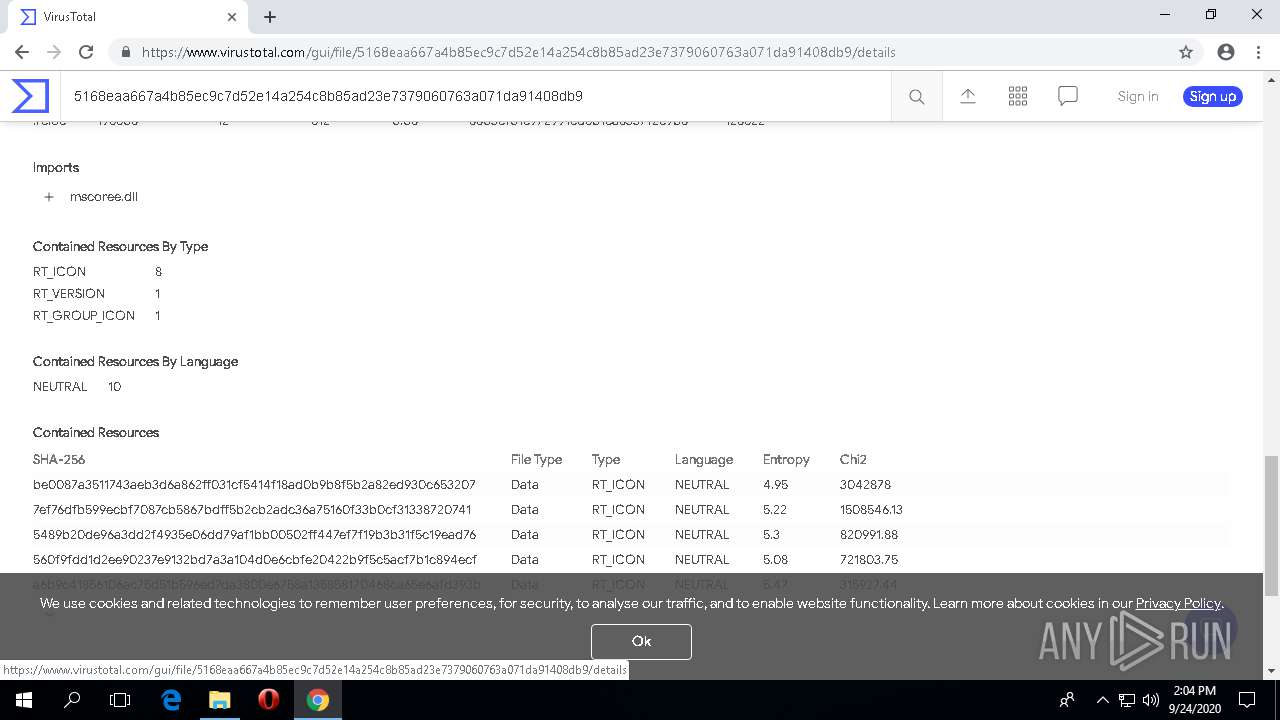
Imports
mscoree.dll |
Total processes
153
Monitored processes
58
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 176 | rundll32.exe "C:\WINDOWS\Installer\MSIF791.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_-1380386921 27 CustomAction!CustomActionsShared.ExecuteSequence.PostInstallFinalize | C:\WINDOWS\SysWOW64\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 212 | "C:\Windows\System32\netsh.exe" advfirewall firewall Delete rule name = XDA-Service | C:\Windows\System32\netsh.exe | — | xda.service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 252 | "C:\Users\admin\AppData\Local\Temp\ueoy5ytr.dl3\133ifhhd.pbe\dbVersionDetect.exe" SQLCE | C:\Users\admin\AppData\Local\Temp\ueoy5ytr.dl3\133ifhhd.pbe\dbVersionDetect.exe | — | Setup.exe | |||||||||||
User: admin Company: Xerox Corporation Integrity Level: HIGH Description: dbVersionDetect Exit code: 1 Version: 1.0.0.3 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\XDA Lite Production v6.2.81.exe" | C:\Users\admin\AppData\Local\Temp\XDA Lite Production v6.2.81.exe | explorer.exe | ||||||||||||
User: admin Company: Xerox Corporation Integrity Level: HIGH Description: Download Manager For Xerox XDA PE Company Exit code: 0 Version: 2.11.56.0 Modules
| |||||||||||||||
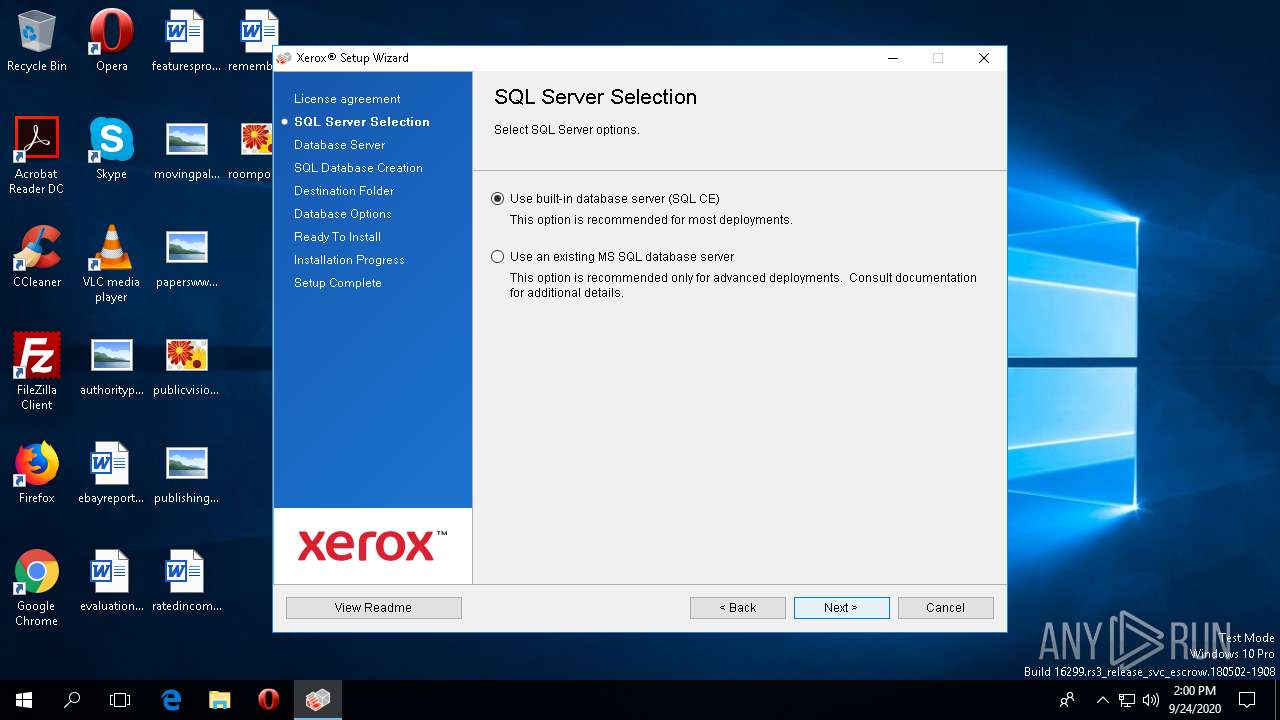
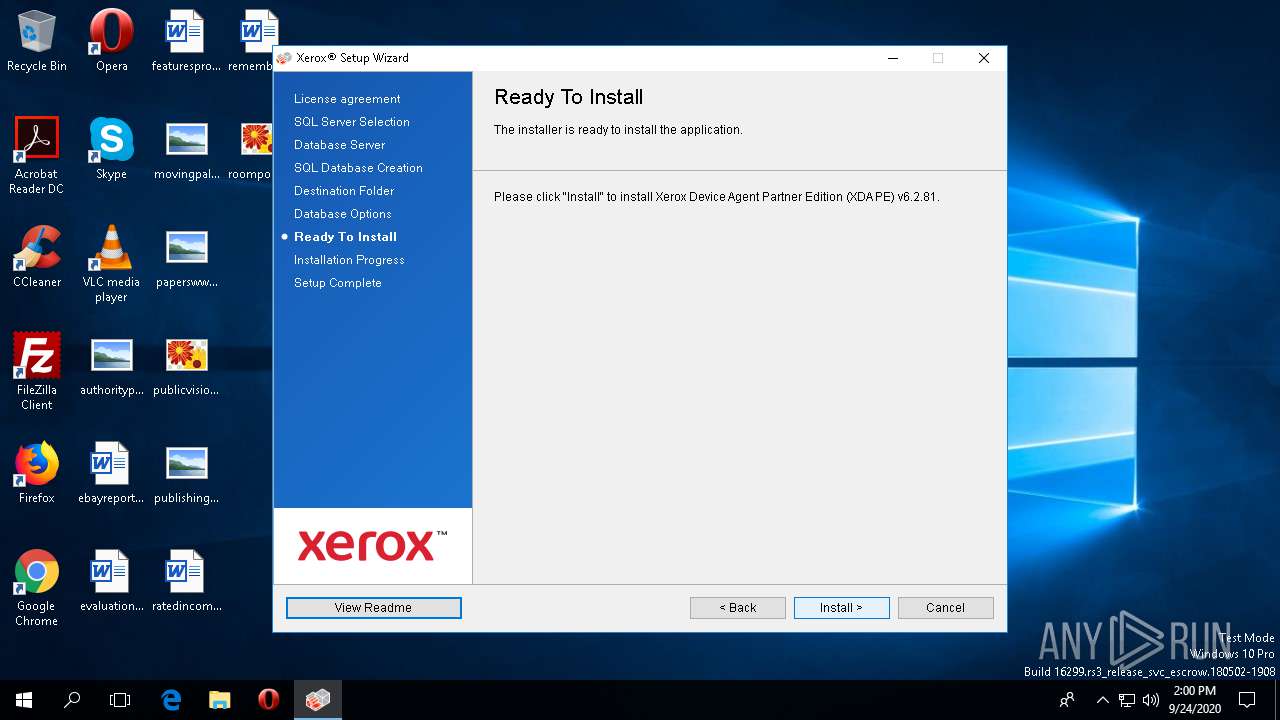
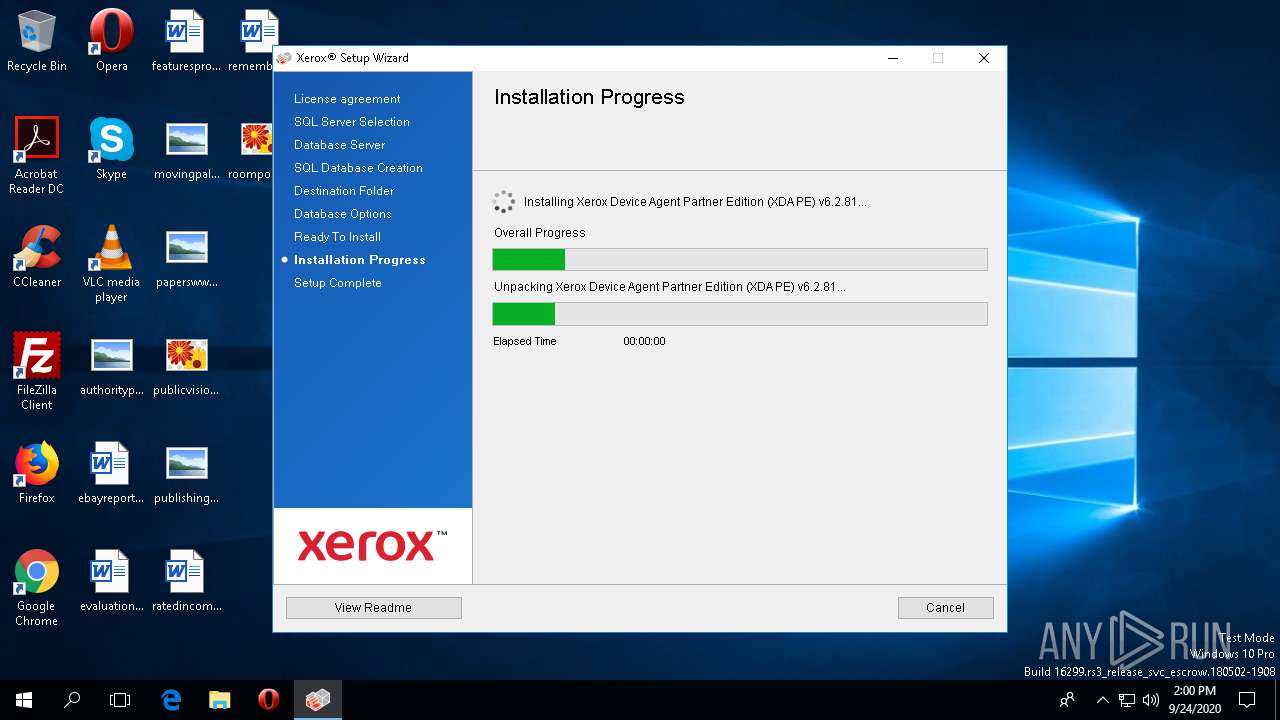
| 780 | "C:\Users\admin\AppData\Local\Temp\DSC\Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe" /L1033 /v"XMLLocation=\"C:\Users\admin\AppData\Local\Temp\DSC\xrs.val\"" SKIPLC=true | C:\Users\admin\AppData\Local\Temp\DSC\Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe | — | XDA Lite Production v6.2.81.exe | |||||||||||
User: admin Company: Xerox Corporation Integrity Level: HIGH Description: Xerox Device Agent Partner Edition (XDA PE) v6.2.81 Exit code: 4294967295 Version: 6.2.81 Modules
| |||||||||||||||
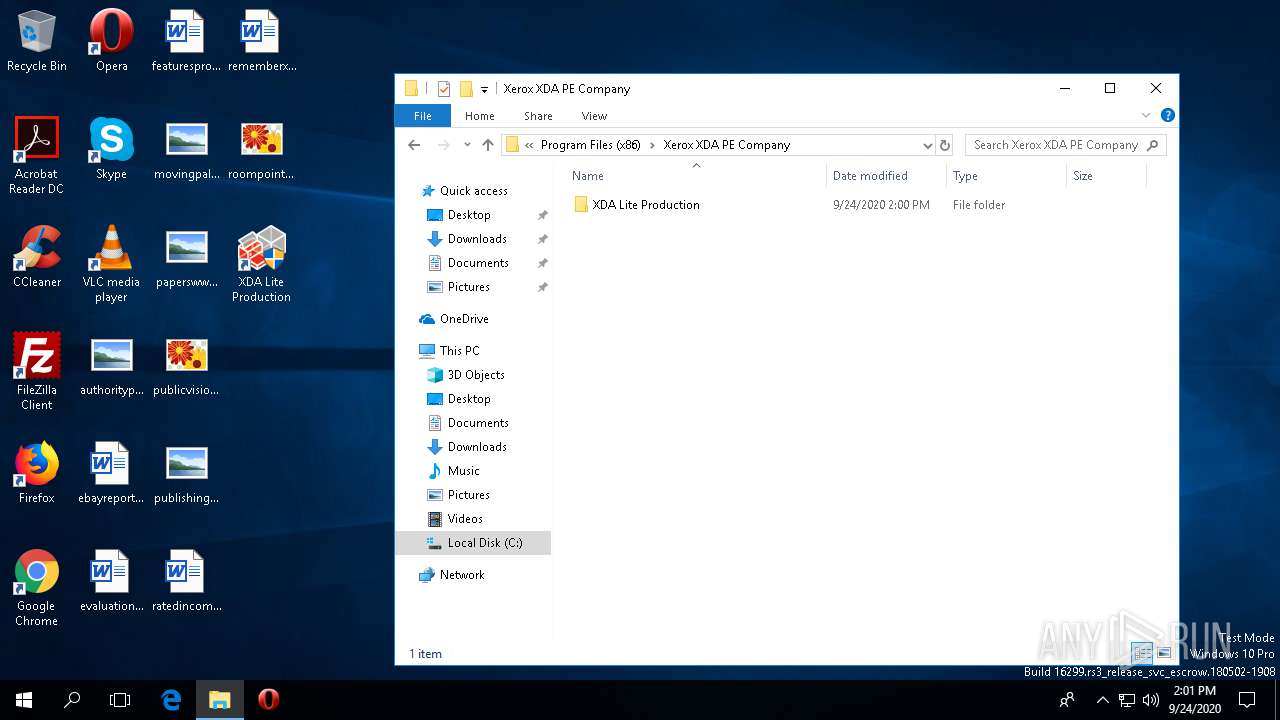
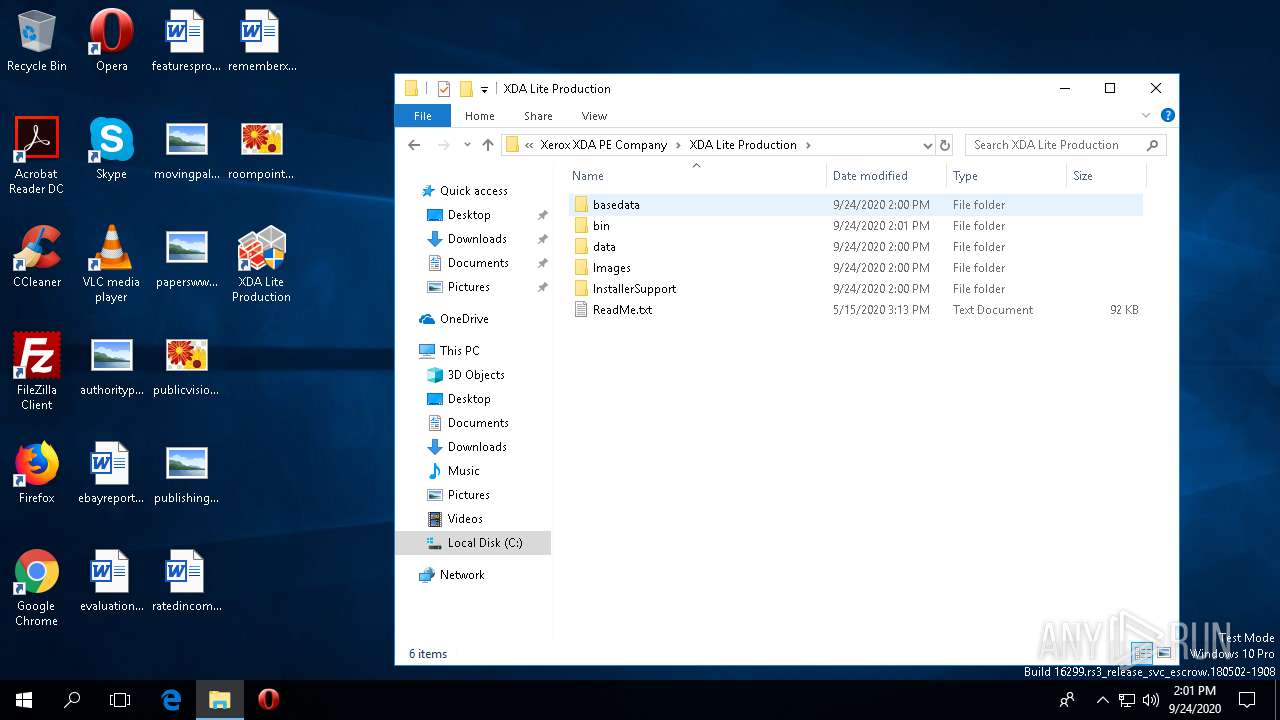
| 796 | "C:\Program Files (x86)\Xerox XDA PE Company\XDA Lite Production\InstallerSupport\database\BrandingTask.exe" | C:\Program Files (x86)\Xerox XDA PE Company\XDA Lite Production\InstallerSupport\database\BrandingTask.exe | — | rundll32.exe | |||||||||||
User: admin Company: Xerox Integrity Level: HIGH Description: Xerox DSC Packager Helper Exit code: 0 Version: 2.0.22.4 Modules
| |||||||||||||||
| 864 | /v"XMLLocation=\"C:\Users\admin\AppData\Local\Temp\DSC\xrs.val\"" SKIPLC=true /L1033 LOG="C:\ProgramData\Xerox\InstallLogs\Xerox_XDA_6.2.81_24_09_2020_1600955998.txt" /bootstrapped | C:\Users\admin\AppData\Local\Temp\DB3F24EE-DCEC-4C70-A5EA-4442DF5F3BCD\Setup.exe | Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Controller Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 912 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2596 --on-initialized-event-handle=692 --parent-handle=696 /prefetch:6 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 1040 | /prereqcheck /L1033 LOG="C:\ProgramData\Xerox\InstallLogs\Xerox_XDA_6.2.81_24_09_2020_1600955998.txt" /bootstrapped | C:\Users\admin\AppData\Local\Temp\DB3F24EE-DCEC-4C70-A5EA-4442DF5F3BCD\Setup.exe | — | Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Controller Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
Total events
7 620
Read events
7 091
Write events
501
Delete events
28
Modification events
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\Xerox DM (Device Management) |
| Operation: | write | Name: | MaxSize |
Value: 524288 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\Xerox DM (Device Management) |
| Operation: | write | Name: | AutoBackupLogFiles |
Value: 0 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\Xerox DM (Device Management)\Xerox DM (Device Management) |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework64\v4.0.30319\EventLogMessages.dll | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\Xerox DM (Device Management)\DSC Download Manager Log |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework64\v4.0.30319\EventLogMessages.dll | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (664) XDA Lite Production v6.2.81.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XDA Lite Production v6_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
275
Suspicious files
194
Text files
496
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 664 | XDA Lite Production v6.2.81.exe | C:\Users\admin\AppData\Local\Temp\c6445a86-074a-4241-8667-602b952f000b.exe | — | |
MD5:— | SHA256:— | |||
| 664 | XDA Lite Production v6.2.81.exe | C:\Users\admin\AppData\Local\Temp\DSC\Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe | — | |
MD5:— | SHA256:— | |||
| 664 | XDA Lite Production v6.2.81.exe | C:\Users\admin\AppData\Local\Temp\DSC\0f70538d-120a-4f64-bc52-79805328ff84.zip | compressed | |
MD5:— | SHA256:— | |||
| 664 | XDA Lite Production v6.2.81.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\XDA Lite Production v6.2.81.exe.log | text | |
MD5:— | SHA256:— | |||
| 664 | XDA Lite Production v6.2.81.exe | C:\Users\admin\AppData\Local\Temp\DSC\xrs.val | xml | |
MD5:— | SHA256:— | |||
| 780 | Xerox Device Agent Partner Edition (XDA PE) v6.2.81.exe | C:\ProgramData\Xerox\InstallLogs\Xerox_XDA_6.2.81_24_09_2020_1600955998.txt | text | |
MD5:— | SHA256:— | |||
| 1040 | Setup.exe | C:\ProgramData\Xerox\InstallLogs\Xerox_XDA_6.2.81_24_09_2020_1600955998.txt | text | |
MD5:— | SHA256:— | |||
| 864 | Setup.exe | C:\Users\admin\AppData\Local\Temp\ueoy5ytr.dl3\133ifhhd.pbe\DotNetZip-anj04ysf.tmp | — | |
MD5:— | SHA256:— | |||
| 864 | Setup.exe | C:\Users\admin\AppData\Local\Temp\ueoy5ytr.dl3\133ifhhd.pbe\DotNetZip-2cq4tn1l.tmp | — | |
MD5:— | SHA256:— | |||
| 864 | Setup.exe | C:\Users\admin\AppData\Local\Temp\ueoy5ytr.dl3\133ifhhd.pbe\DotNetZip-olv1oghg.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
48
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2876 | svchost.exe | HEAD | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956377&mv=m&mvi=2&pl=24&shardbypass=yes | LV | — | — | whitelisted |
1080 | chrome.exe | GET | 200 | 159.148.69.140:80 | http://r1---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956077&mv=m&mvi=1&pl=24&shardbypass=yes | LV | crx | 834 Kb | whitelisted |
2876 | svchost.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g | US | html | 499 b | whitelisted |
2876 | svchost.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g | US | html | 483 b | whitelisted |
1080 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
2876 | svchost.exe | GET | 206 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956438&mv=m&mvi=2&pcm2cms=yes&pl=24&shardbypass=yes | LV | binary | 41.1 Kb | whitelisted |
2876 | svchost.exe | GET | 206 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956377&mv=m&mvi=2&pl=24&shardbypass=yes | LV | binary | 9.04 Kb | whitelisted |
2876 | svchost.exe | GET | 206 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956377&mv=m&mvi=2&pl=24&shardbypass=yes | LV | binary | 10.3 Kb | whitelisted |
2876 | svchost.exe | GET | 206 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956377&mv=m&mvi=2&pcm2cms=yes&pl=24&shardbypass=yes | LV | binary | 1.85 Kb | whitelisted |
2876 | svchost.exe | GET | 206 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/release2/chrome_component/IPe0DW--vyzNNx0NkxLNjw_32.0.0.433/AKz8Q2rhuXOOMWYXiBLhv-g?cms_redirect=yes&mh=87&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1600956377&mv=m&mvi=2&pl=24&shardbypass=yes | LV | binary | 19.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
664 | XDA Lite Production v6.2.81.exe | 13.14.0.17:443 | transactions.services.xerox.com | XEROX CORPORATION | US | suspicious |
3712 | xda.service.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3712 | xda.service.exe | 13.14.0.10:443 | office.services.xerox.com | XEROX CORPORATION | US | unknown |
3712 | xda.service.exe | 13.13.56.126:443 | remserv00.support.xerox.com | XEROX CORPORATION | US | suspicious |
1080 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1080 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1080 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
1080 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1080 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1080 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
transactions.services.xerox.com |
| suspicious |
crl.microsoft.com |
| whitelisted |
office.services.xerox.com |
| unknown |
remserv00.support.xerox.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |