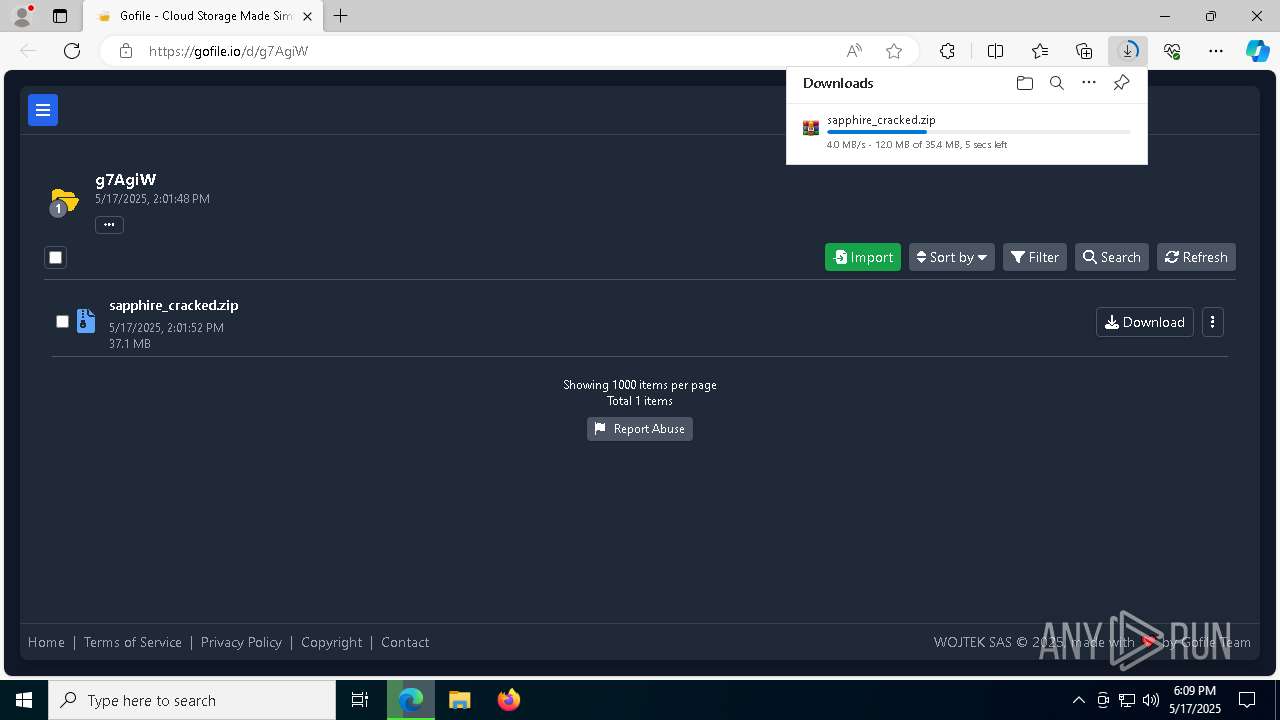
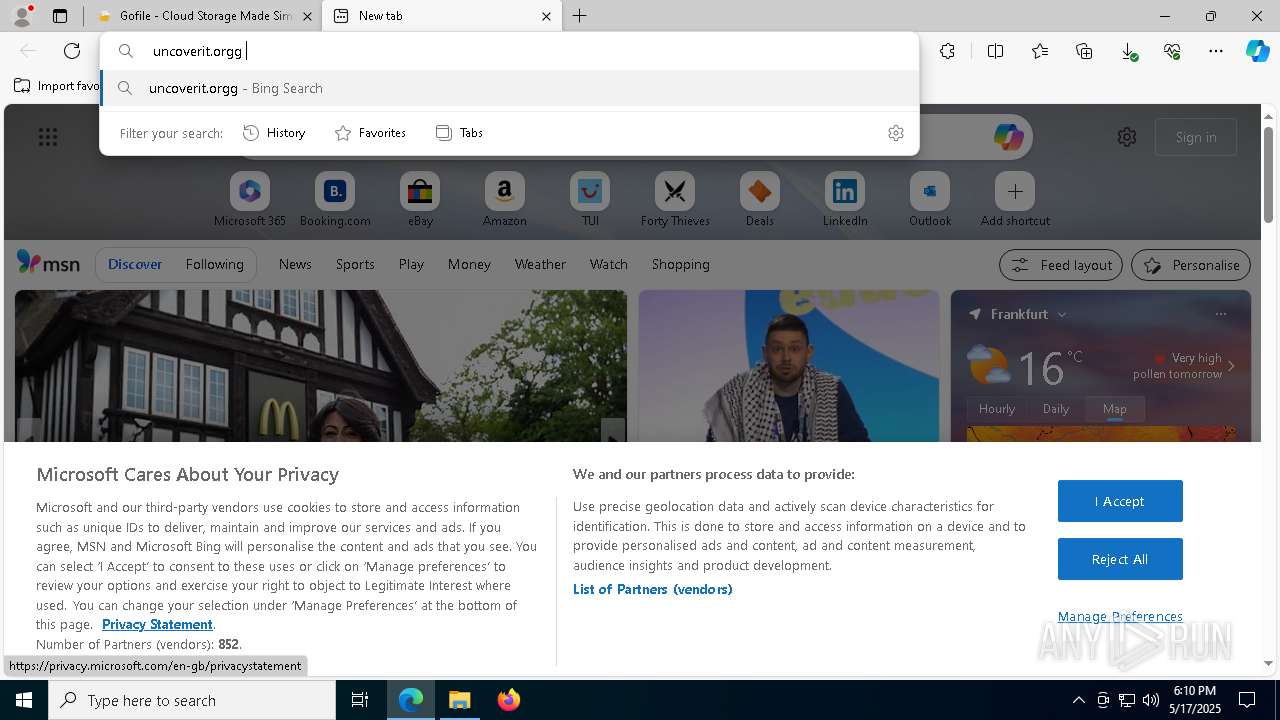
| URL: | https://gofile.io/d/g7AgiW |
| Full analysis: | https://app.any.run/tasks/025abe17-a0af-42ad-a755-5362b8e36806 |
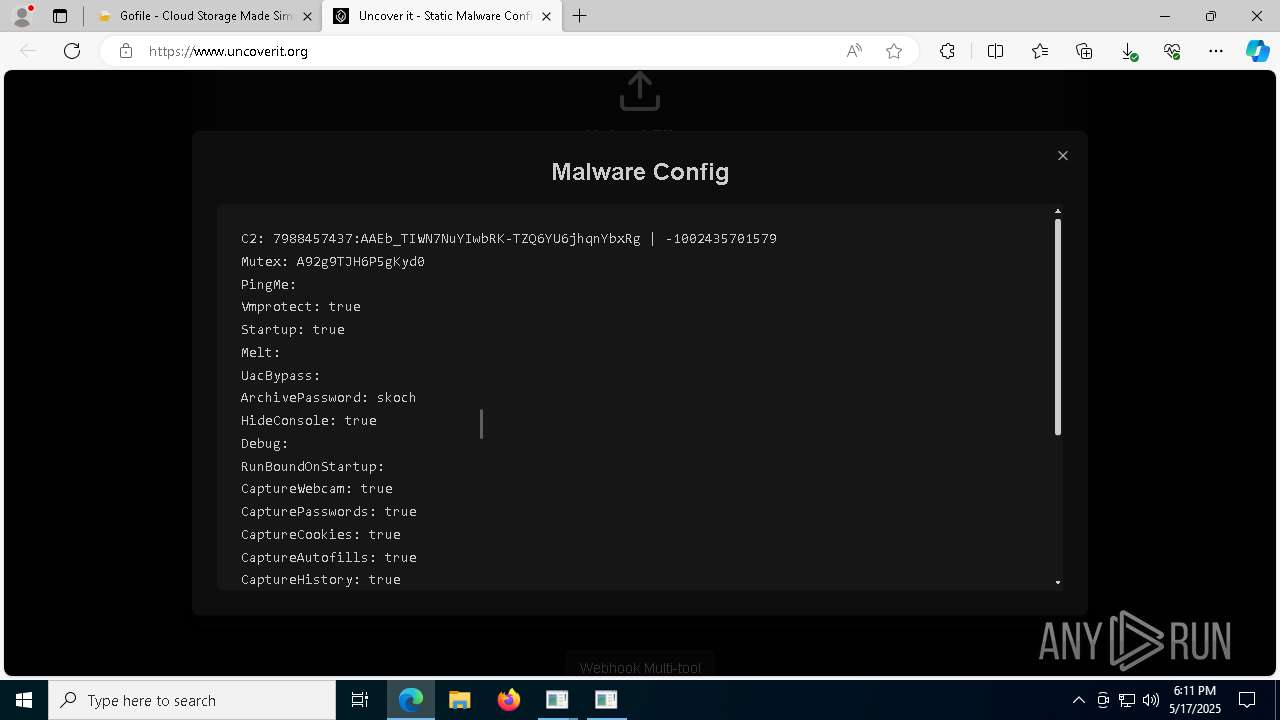
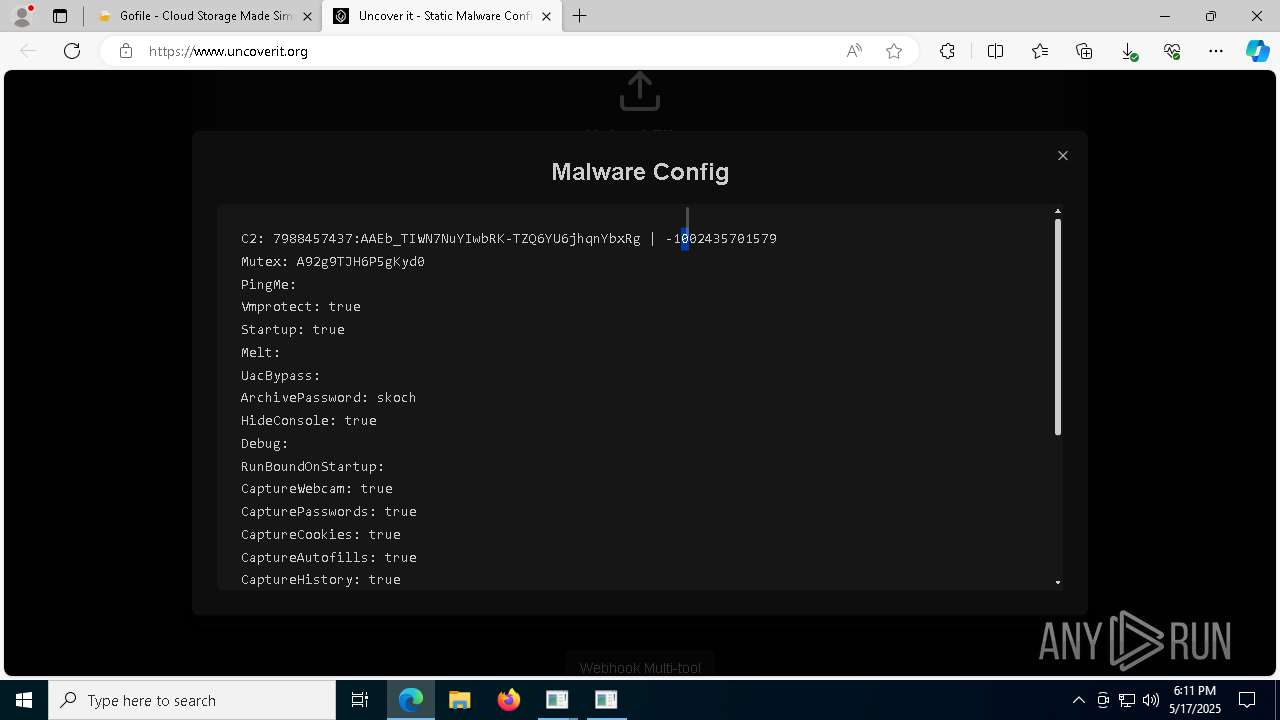
| Verdict: | Malicious activity |
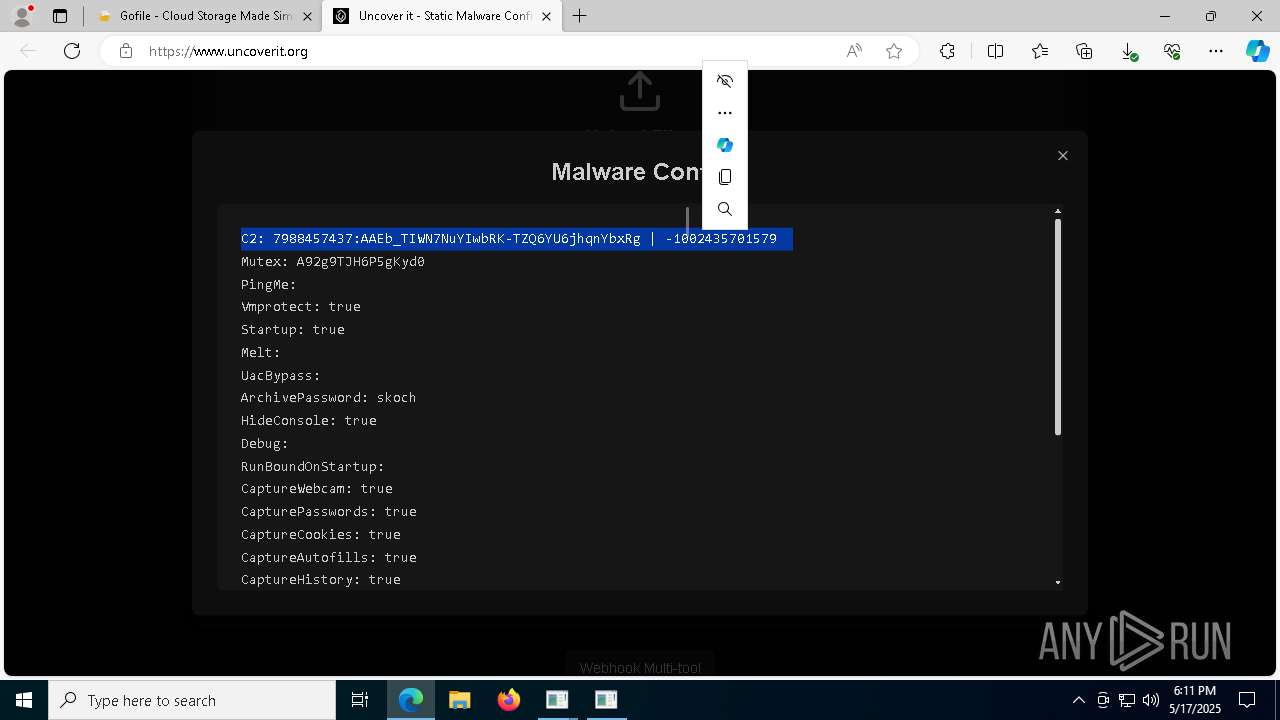
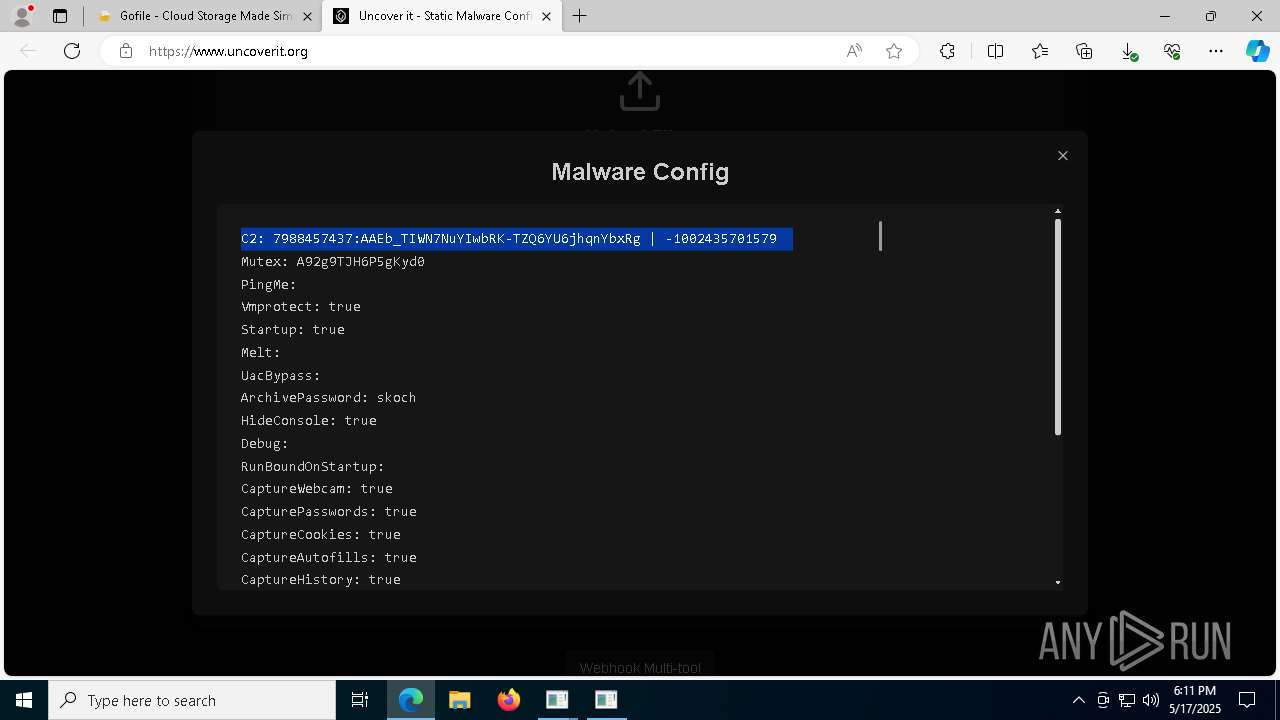
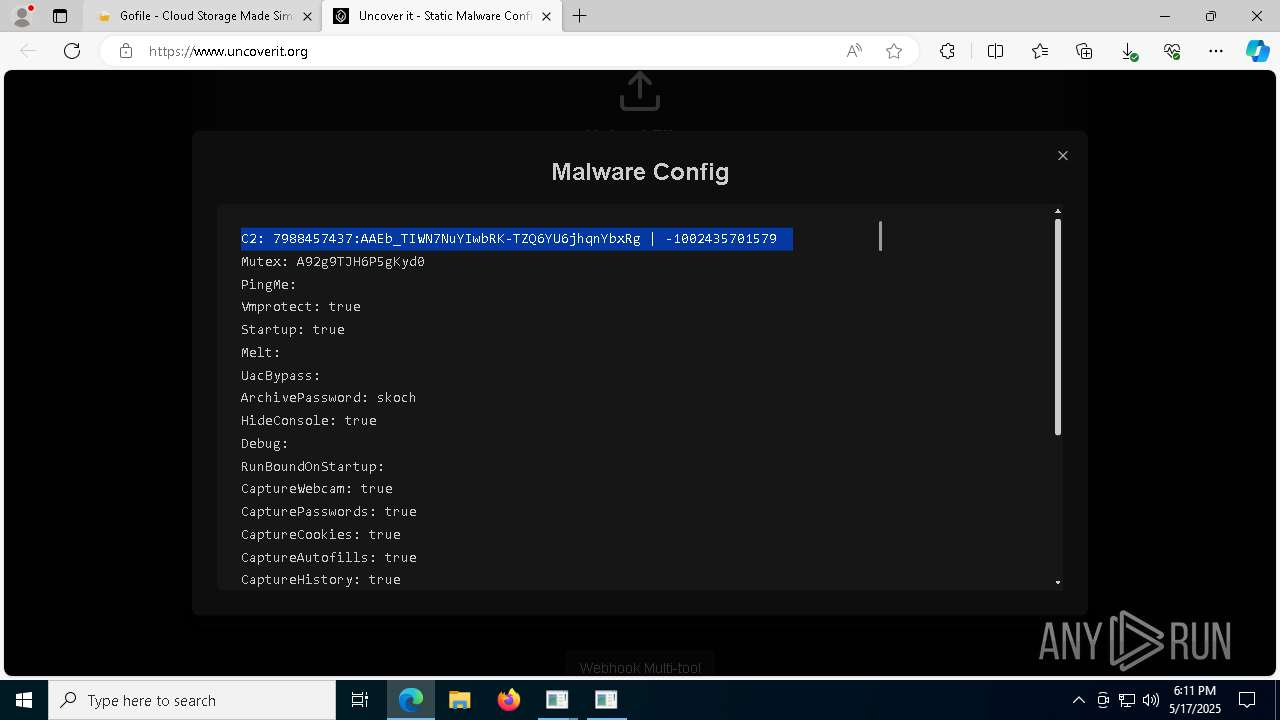
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | May 17, 2025, 18:09:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 209A7B0FAF516D74E1FAF1DADA066D9A |
| SHA1: | E5F178E72A284753F228D82AA92B78D4E73C9AAB |
| SHA256: | C1274945325BA1EAACC47951D5082F1F39A622A219061D2D4605DDCE29E761FC |
| SSDEEP: | 3:N8rxL16yn:2ZX |
MALICIOUS
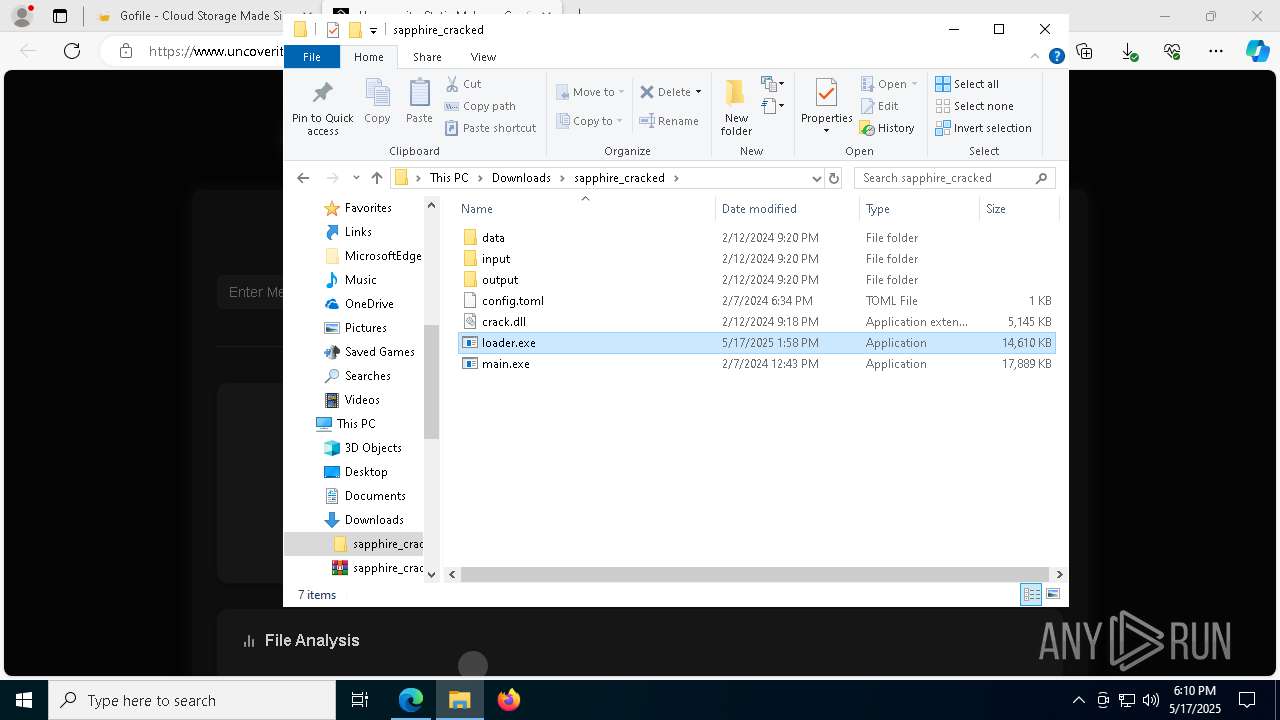
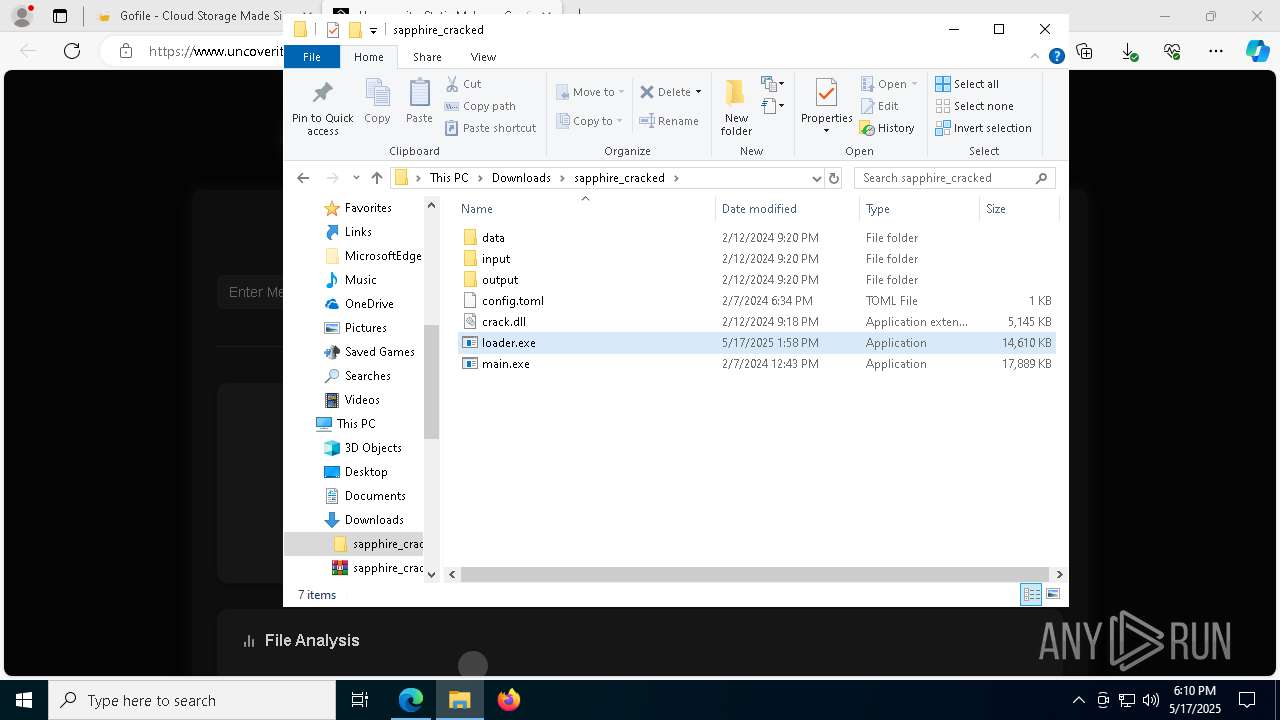
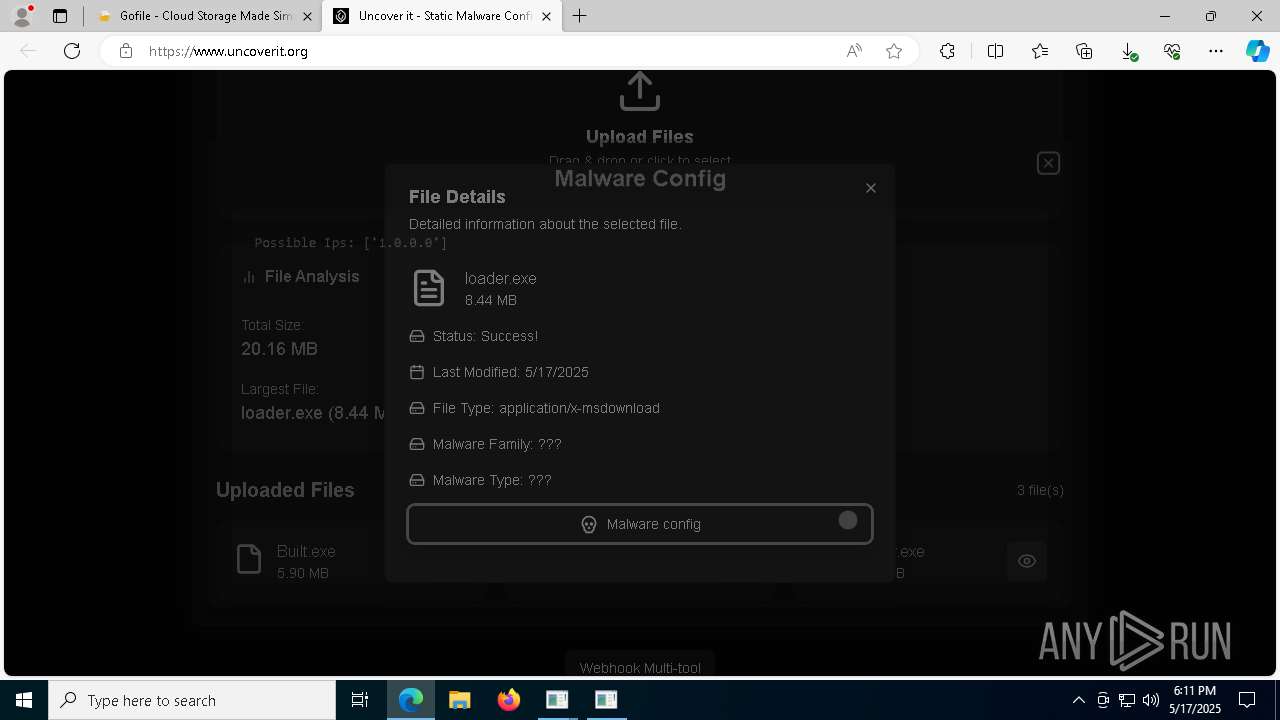
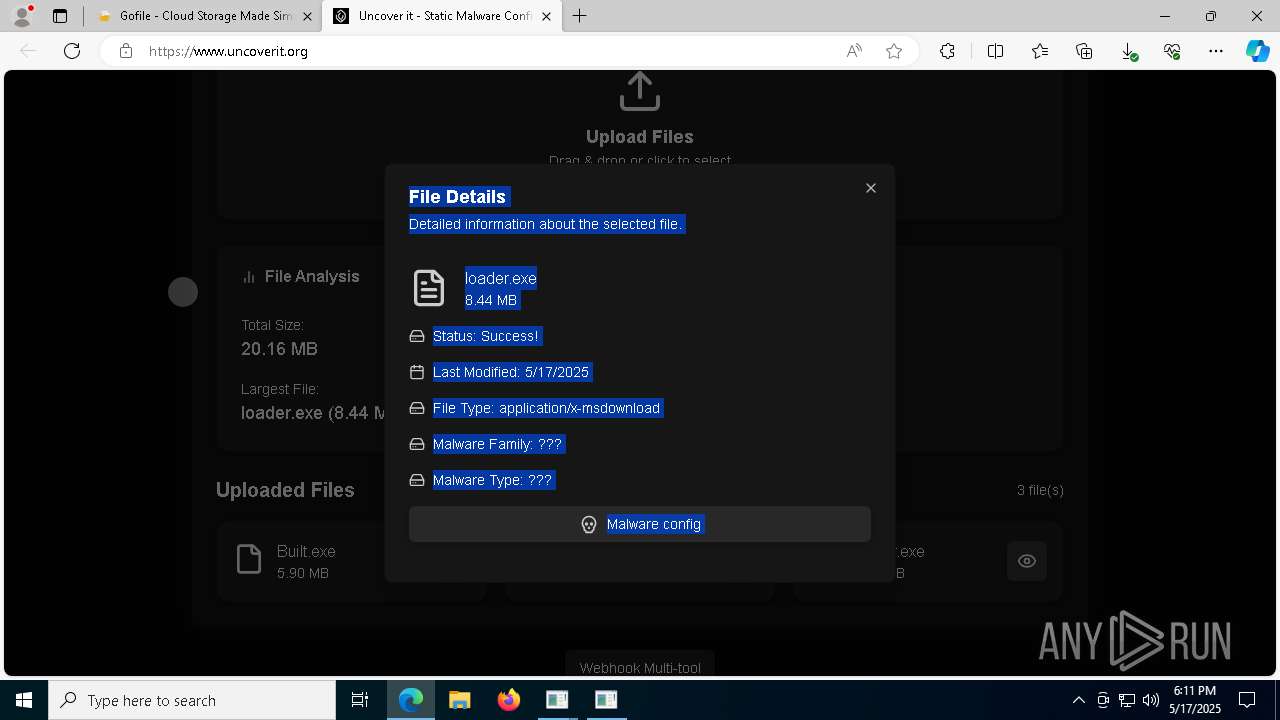
TROX has been detected
- main.exe (PID: 5352)
- loader.exe (PID: 5608)
- loader.exe (PID: 1748)
- main.exe (PID: 8328)
- main.exe (PID: 8368)
- main.exe (PID: 8816)
Known privilege escalation attack
- dllhost.exe (PID: 8060)
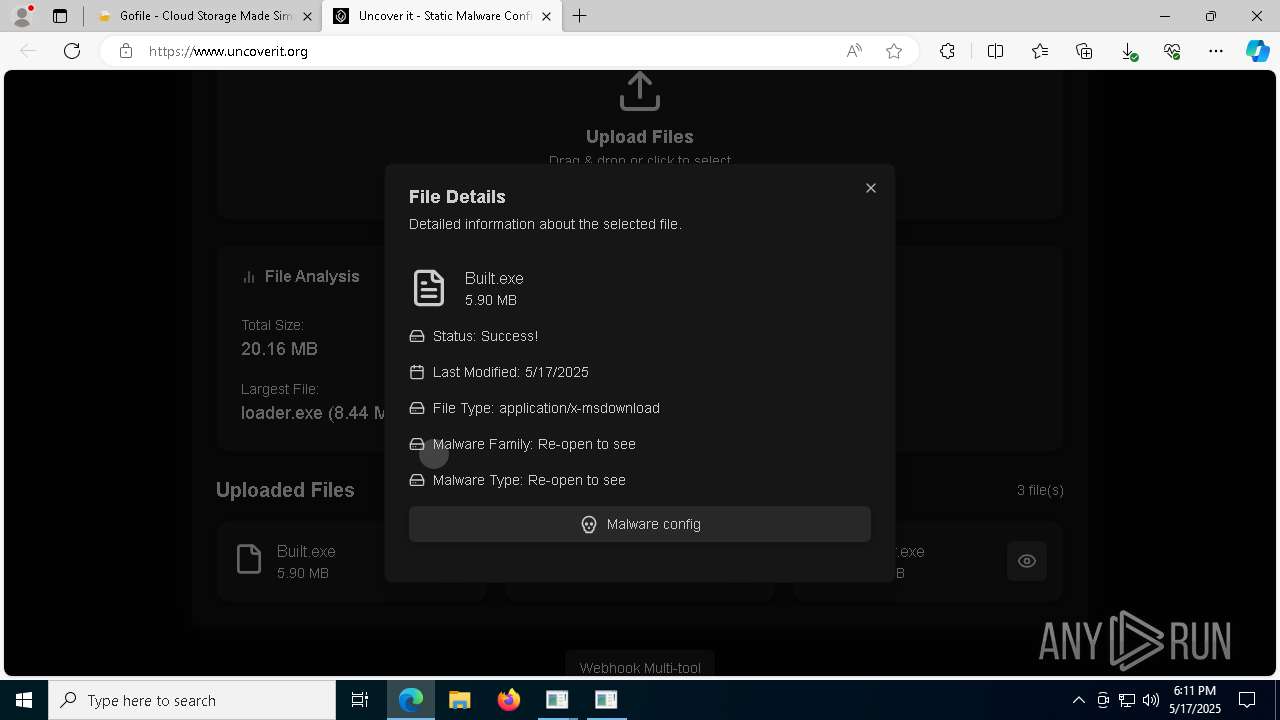
Executing a file with an untrusted certificate
- Built.exe (PID: 6584)
- Built.exe (PID: 1272)
- Built.exe (PID: 8444)
- Built.exe (PID: 8568)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 1272)
- cmd.exe (PID: 6252)
- Built.exe (PID: 8568)
- cmd.exe (PID: 8620)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 8632)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes Windows Defender settings
- cmd.exe (PID: 5204)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8632)
Changes Controlled Folder Access settings
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Changes settings for real-time protection
- powershell.exe (PID: 4692)
- powershell.exe (PID: 8900)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8576)
- MpCmdRun.exe (PID: 8808)
SUSPICIOUS
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- loader.exe (PID: 5048)
Process drops python dynamic module
- main.exe (PID: 5352)
- loader.exe (PID: 5608)
- Built.exe (PID: 6584)
- loader.exe (PID: 1748)
- Built.exe (PID: 8444)
- main.exe (PID: 8328)
- main.exe (PID: 8368)
- main.exe (PID: 8816)
The process drops C-runtime libraries
- main.exe (PID: 5352)
- loader.exe (PID: 5608)
- Built.exe (PID: 6584)
- loader.exe (PID: 1748)
- Built.exe (PID: 8444)
- main.exe (PID: 8328)
- main.exe (PID: 8368)
- main.exe (PID: 8816)
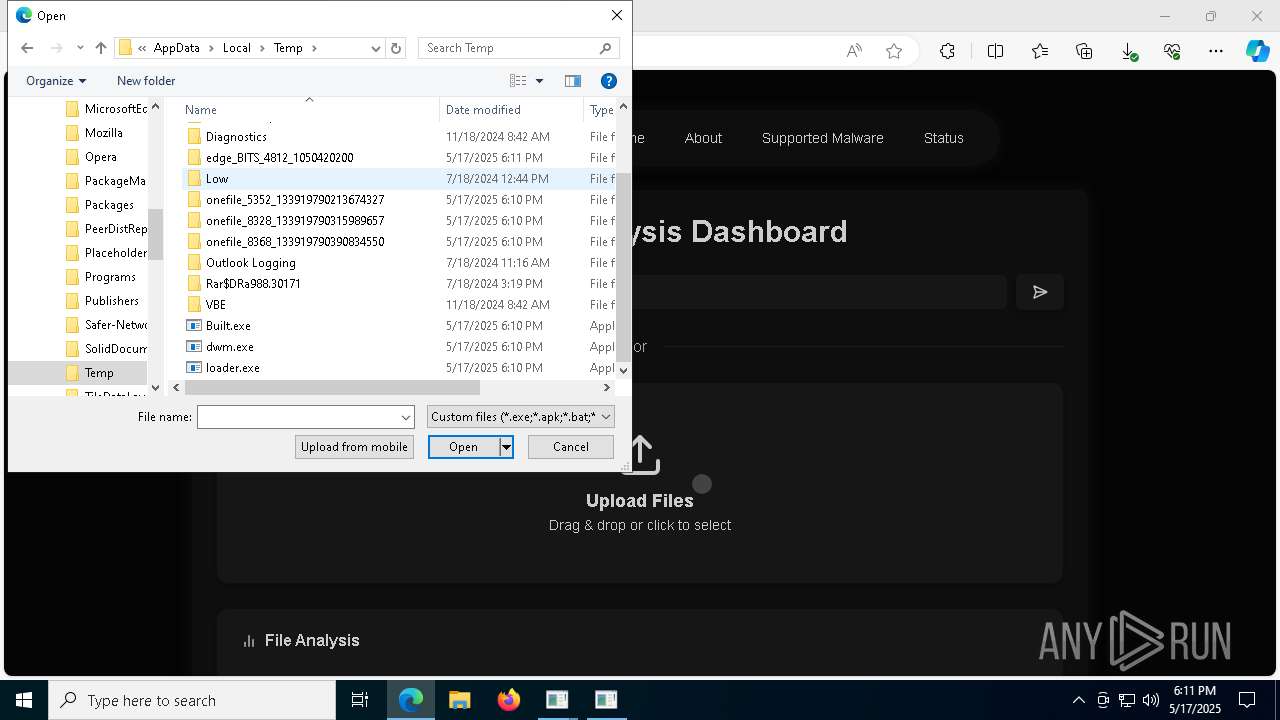
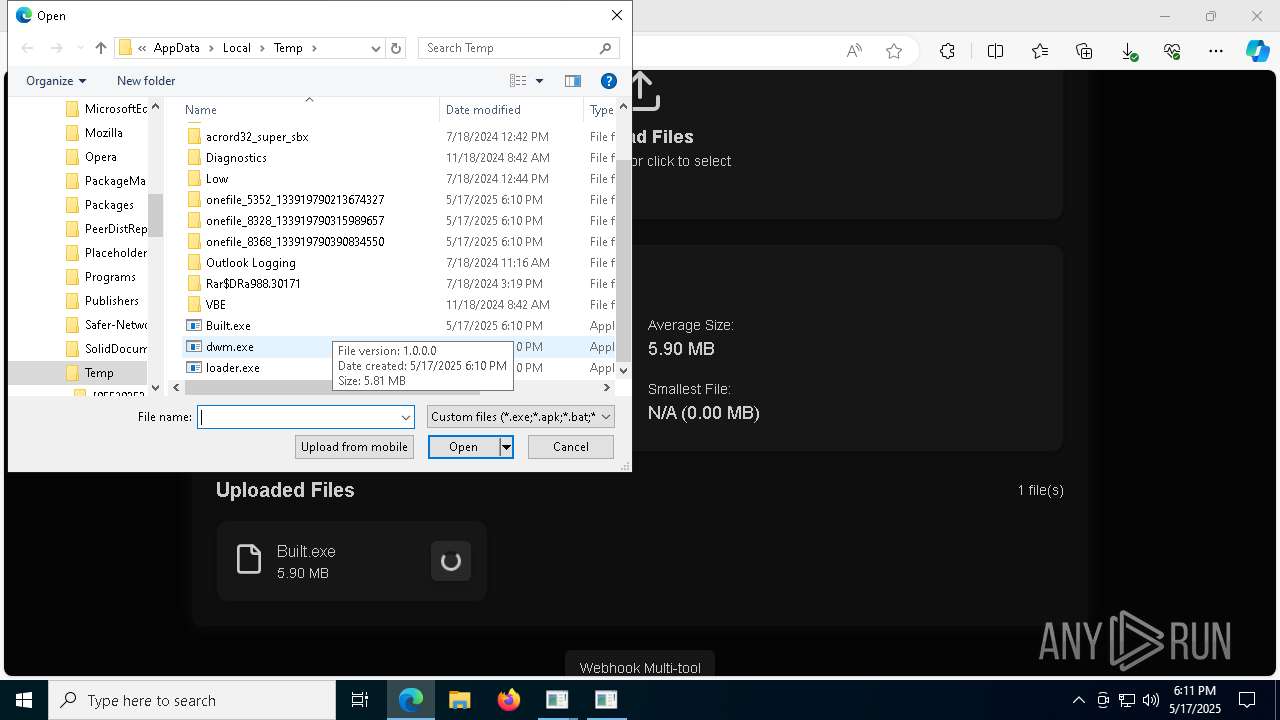
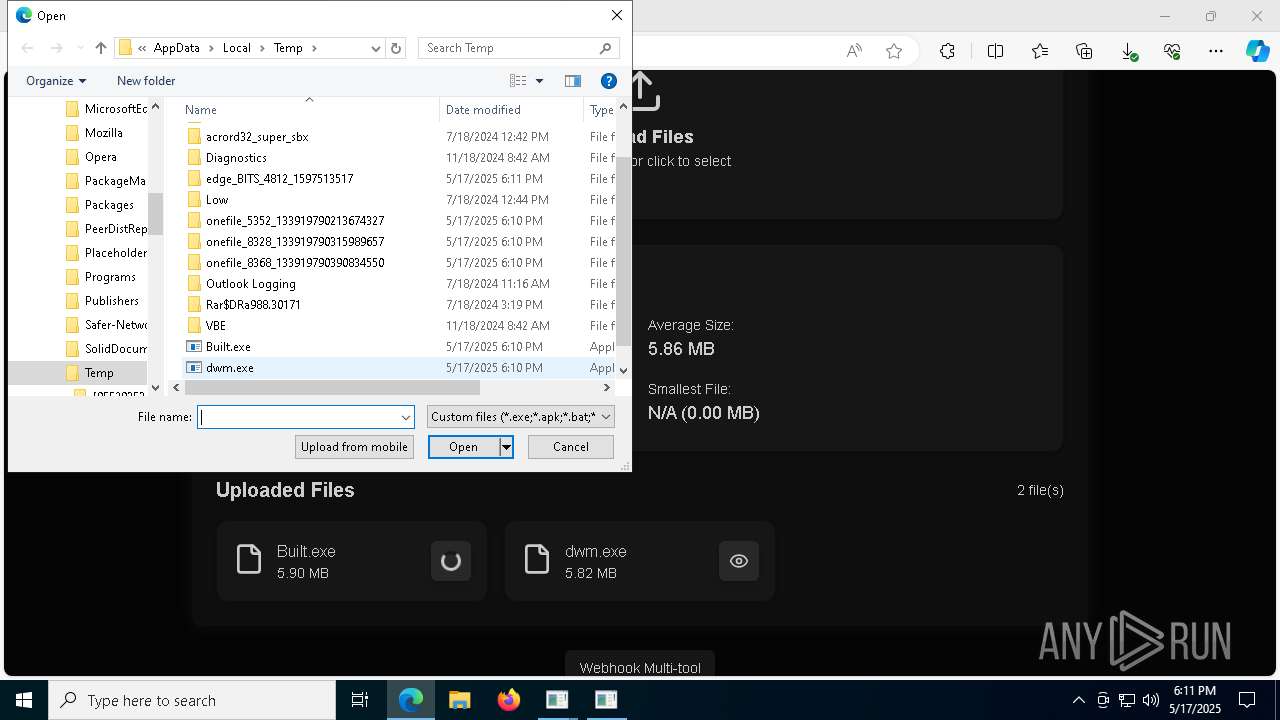
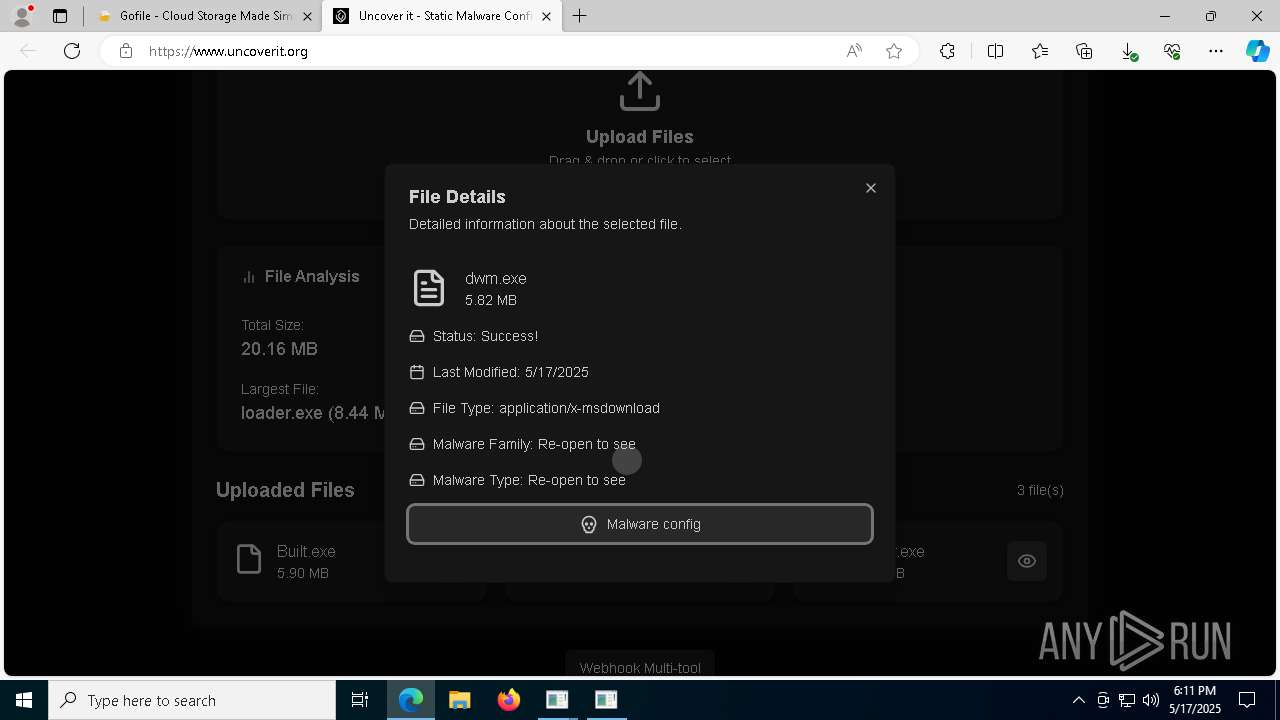
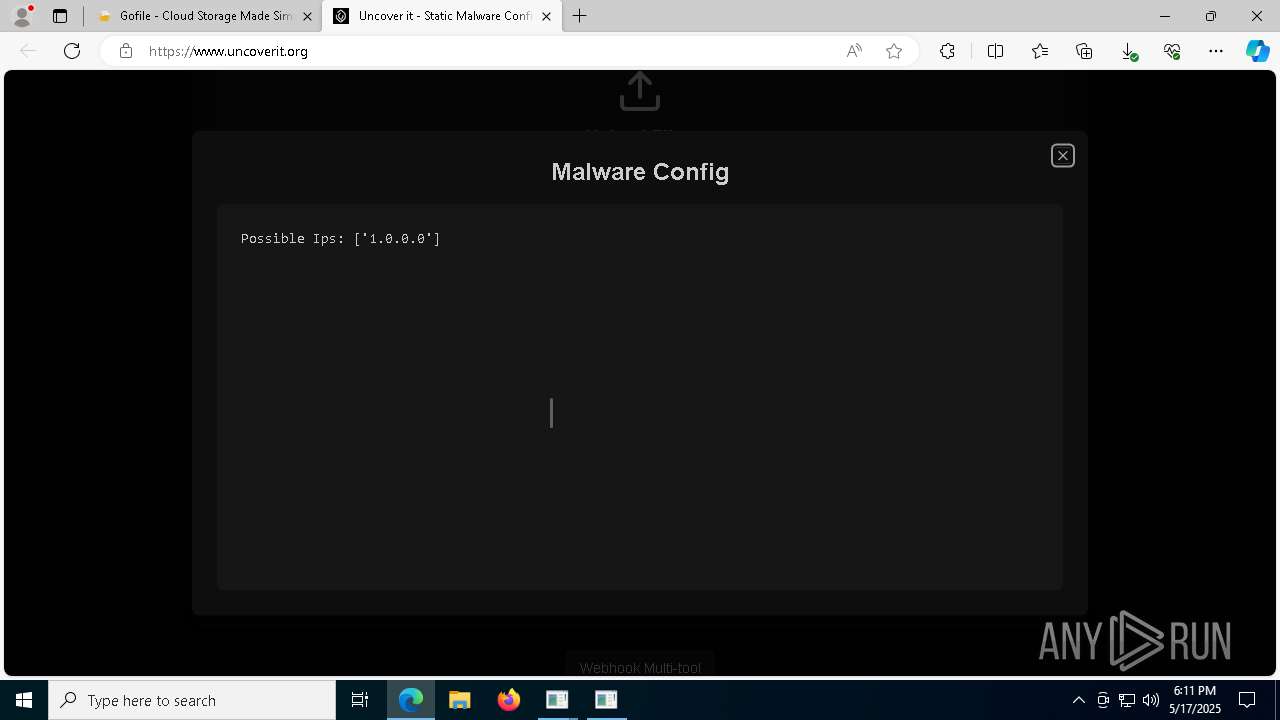
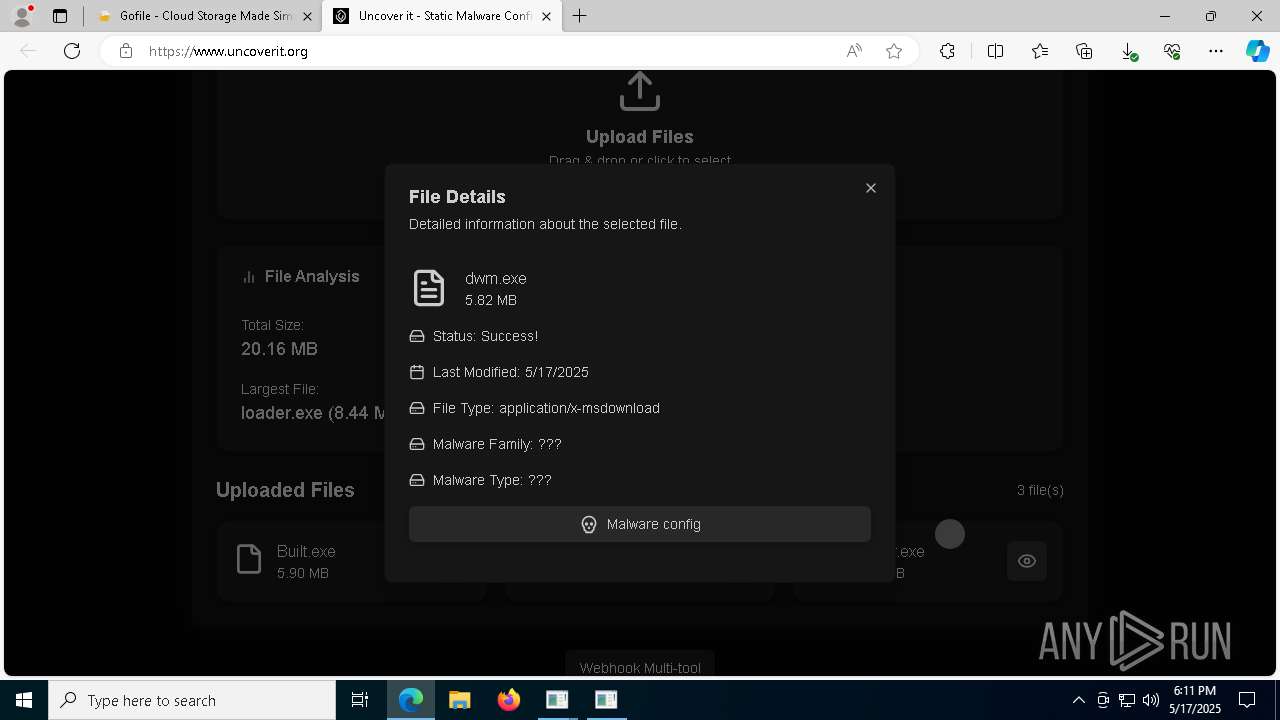
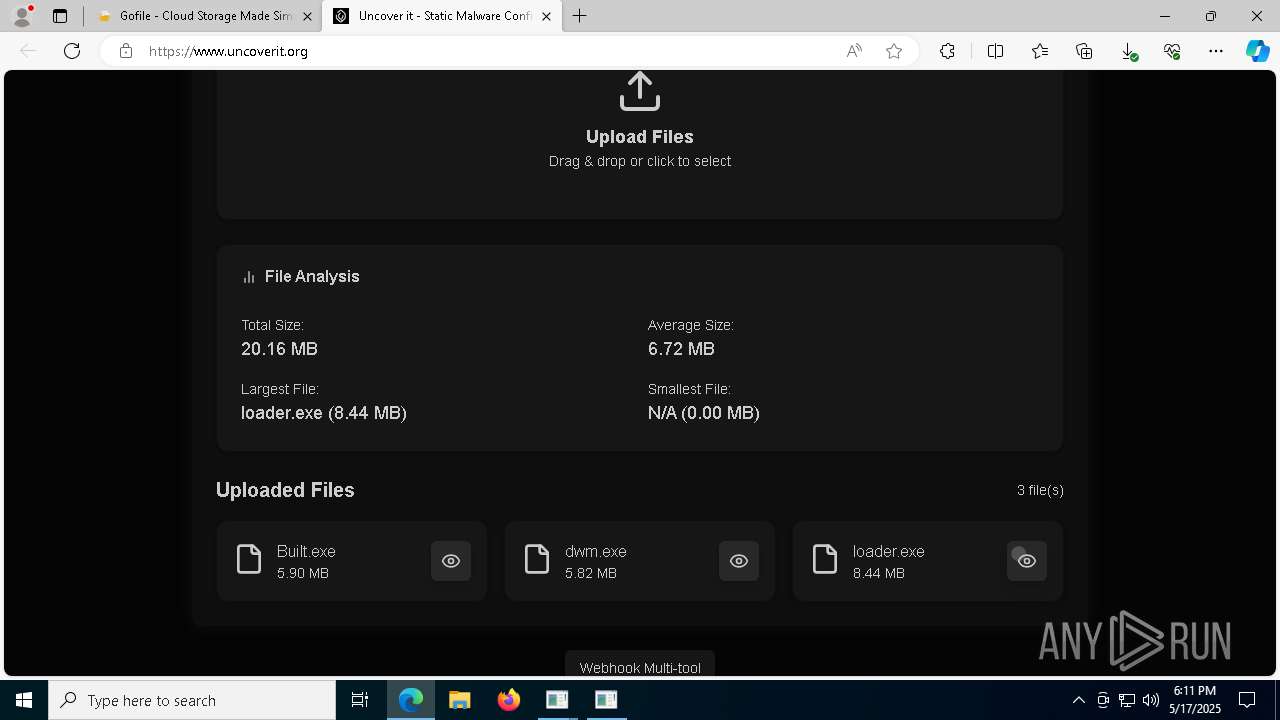
Executable content was dropped or overwritten
- main.exe (PID: 5352)
- loader.exe (PID: 6156)
- loader.exe (PID: 5608)
- Built.exe (PID: 6584)
- dwm.exe (PID: 4736)
- loader.exe (PID: 1748)
- Built.exe (PID: 8444)
- main.exe (PID: 8328)
- main.exe (PID: 8816)
- main.exe (PID: 8368)
Process drops legitimate windows executable
- main.exe (PID: 5352)
- loader.exe (PID: 5608)
- dwm.exe (PID: 4736)
- Built.exe (PID: 6584)
- loader.exe (PID: 1748)
- Built.exe (PID: 8444)
- main.exe (PID: 8328)
- main.exe (PID: 8368)
- main.exe (PID: 8816)
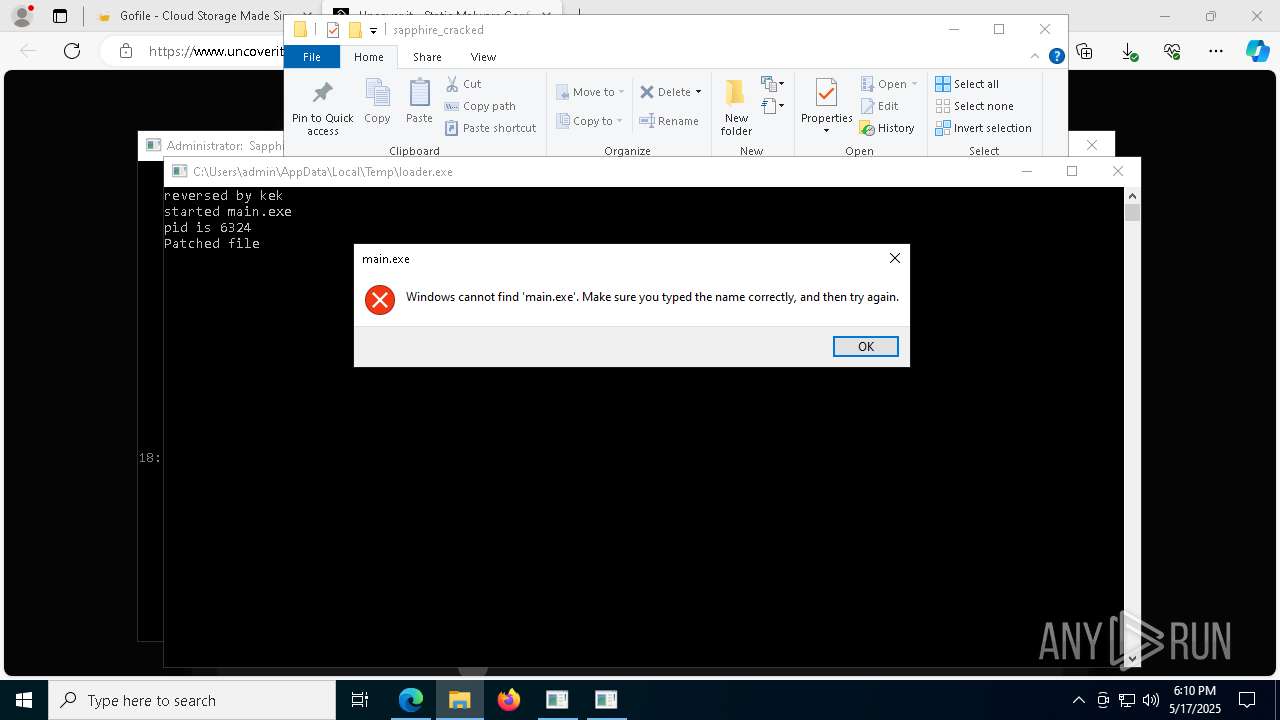
Starts CMD.EXE for commands execution
- main.exe (PID: 6324)
- loader.exe (PID: 7804)
- Built.exe (PID: 1272)
- loader.exe (PID: 8216)
- Built.exe (PID: 8568)
- main.exe (PID: 9112)
- main.exe (PID: 8540)
- main.exe (PID: 4448)
Starts a Microsoft application from unusual location
- Built.exe (PID: 6584)
- Built.exe (PID: 1272)
- Built.exe (PID: 8444)
- Built.exe (PID: 8568)
Application launched itself
- Built.exe (PID: 6584)
- Built.exe (PID: 8444)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 1116)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 1272)
- Built.exe (PID: 8568)
Get information on the list of running processes
- Built.exe (PID: 1272)
- cmd.exe (PID: 7584)
- Built.exe (PID: 8568)
- cmd.exe (PID: 8668)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 5204)
- cmd.exe (PID: 8632)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5204)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8632)
Script disables Windows Defender's IPS
- cmd.exe (PID: 5204)
- cmd.exe (PID: 8632)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7904)
- cmd.exe (PID: 8756)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6252)
- cmd.exe (PID: 8620)
Checks for external IP
- Built.exe (PID: 1272)
- svchost.exe (PID: 2196)
- Built.exe (PID: 8568)
The executable file from the user directory is run by the CMD process
- main.exe (PID: 8328)
INFO
Reads Environment values
- identity_helper.exe (PID: 4892)
Application launched itself
- msedge.exe (PID: 4812)
- msedge.exe (PID: 1748)
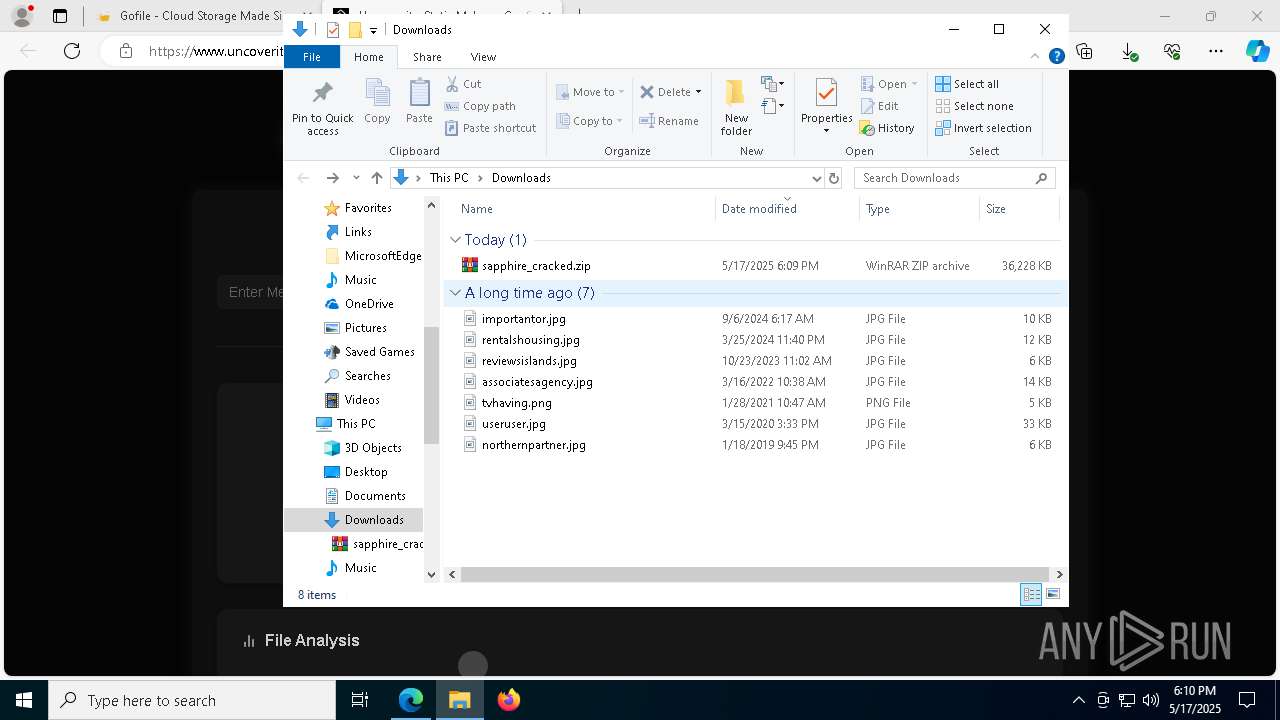
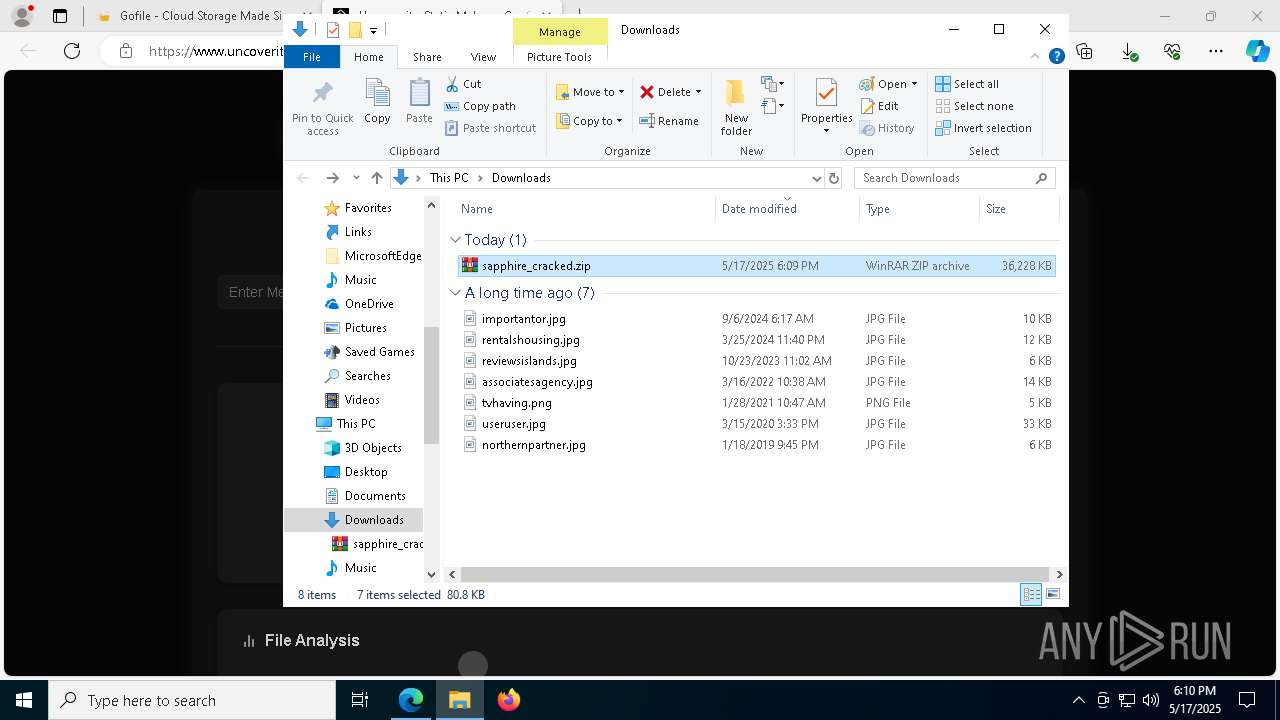
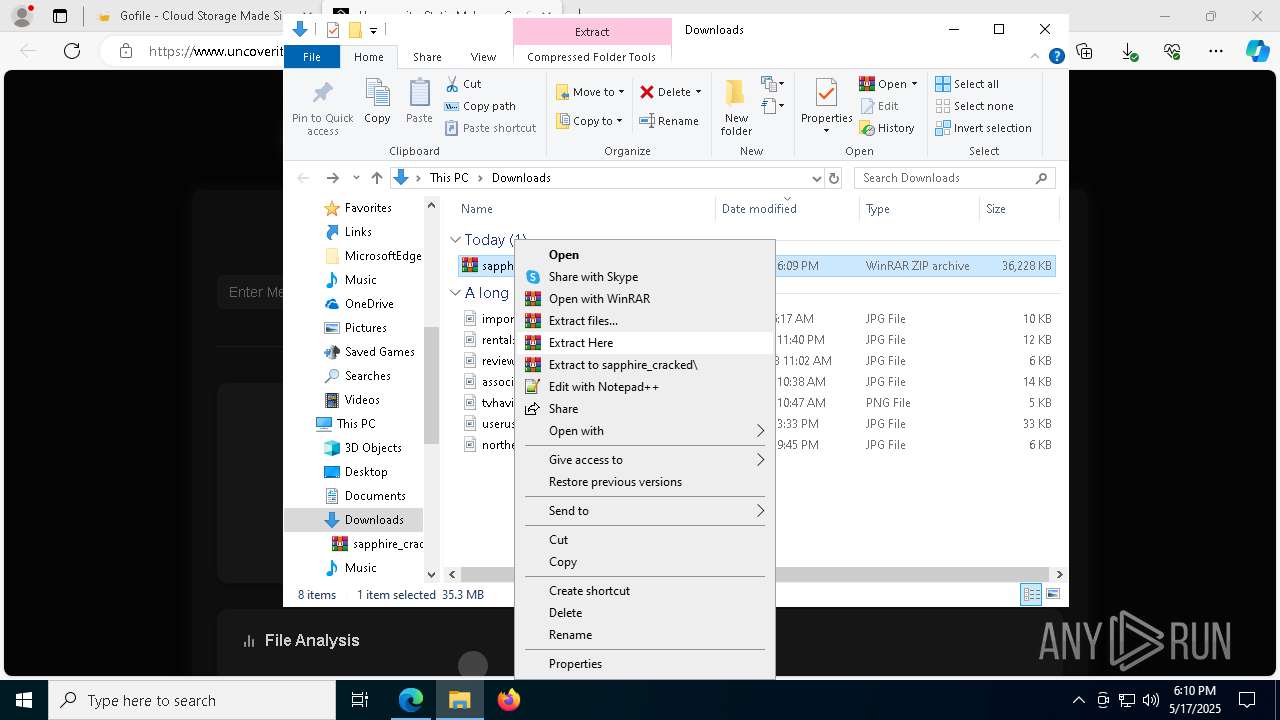
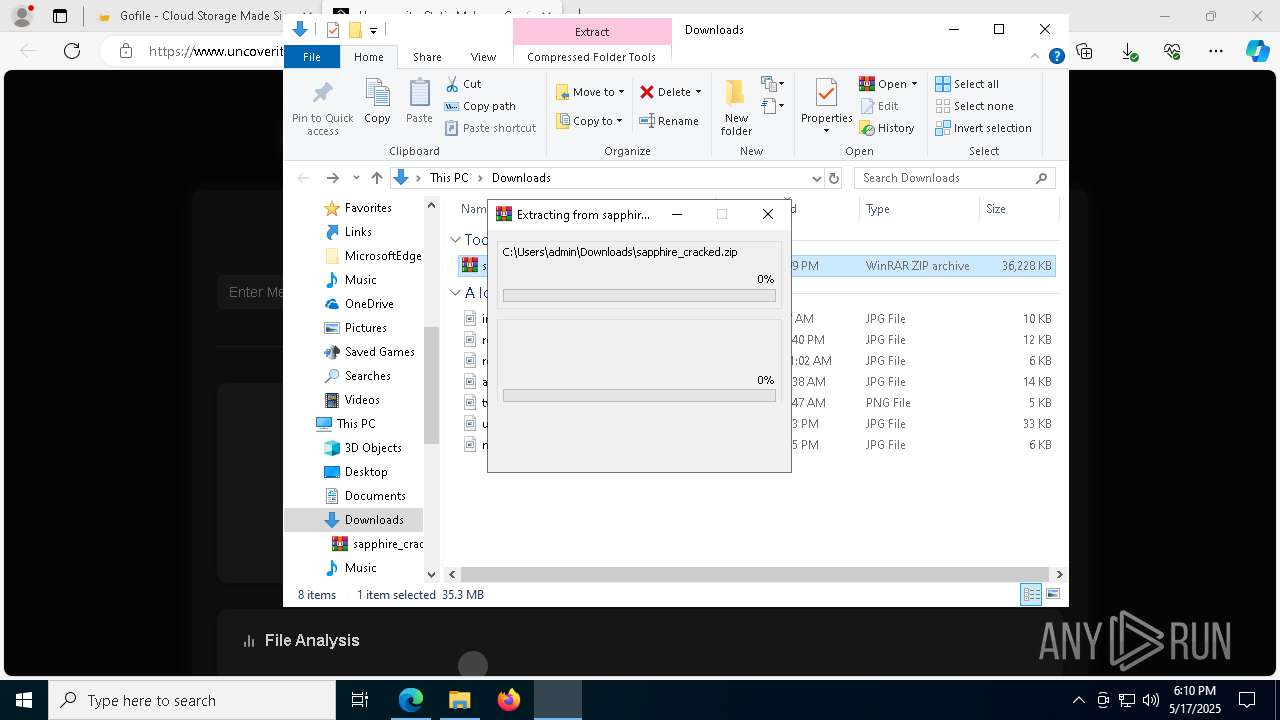
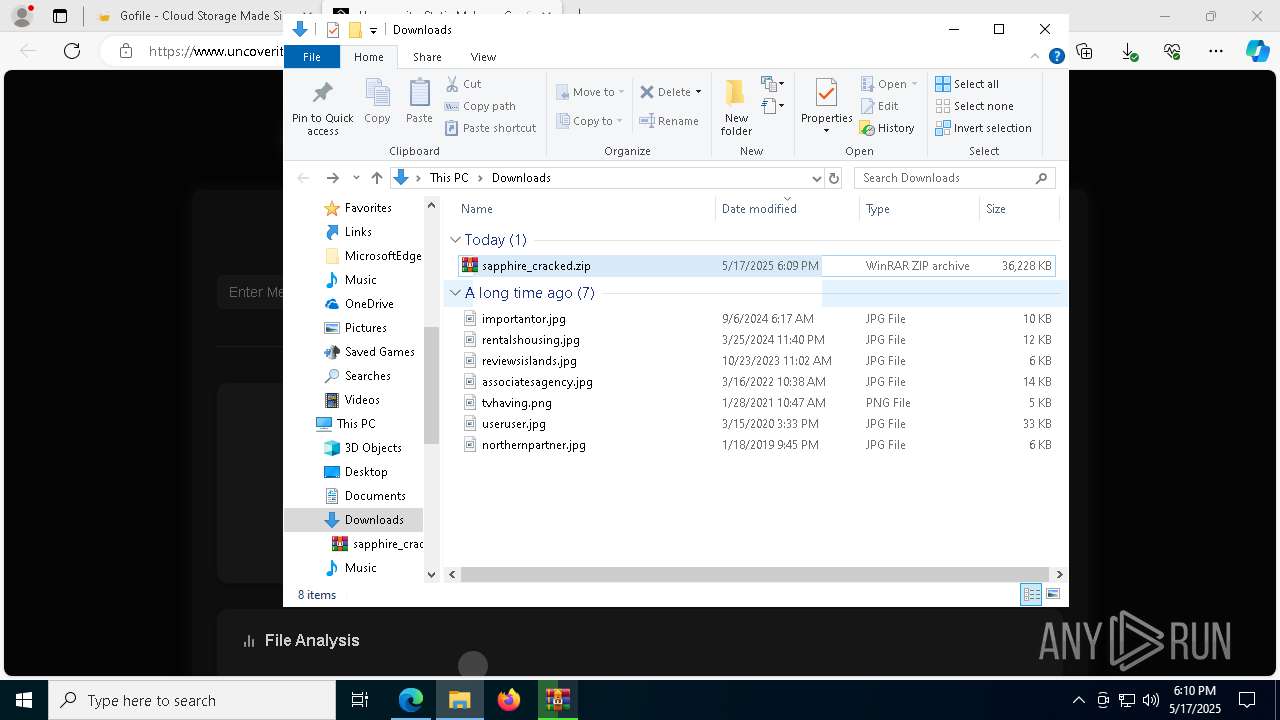
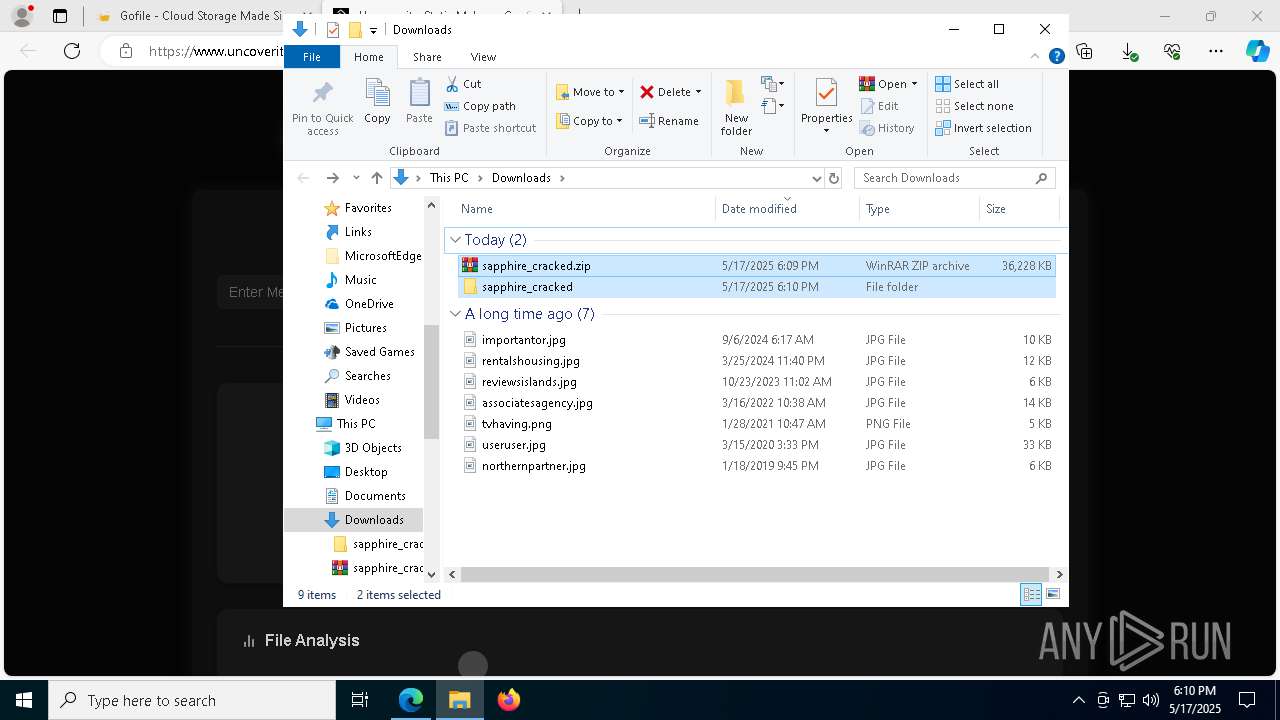
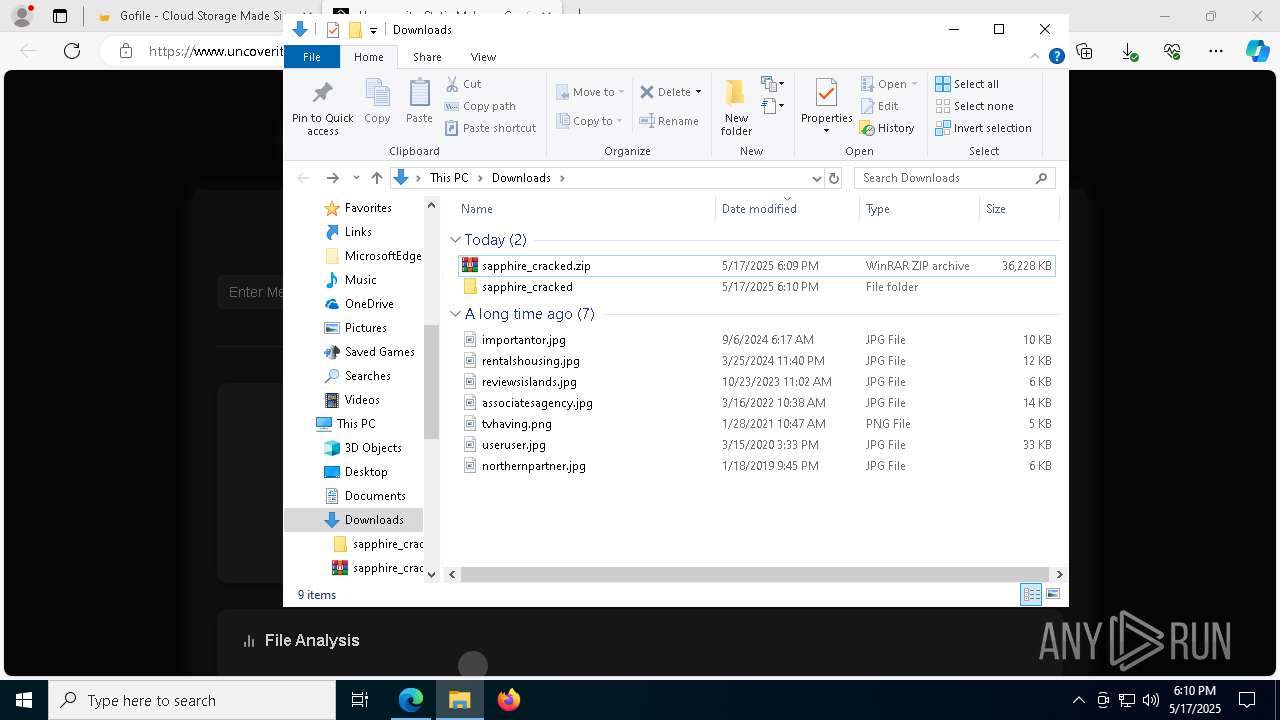
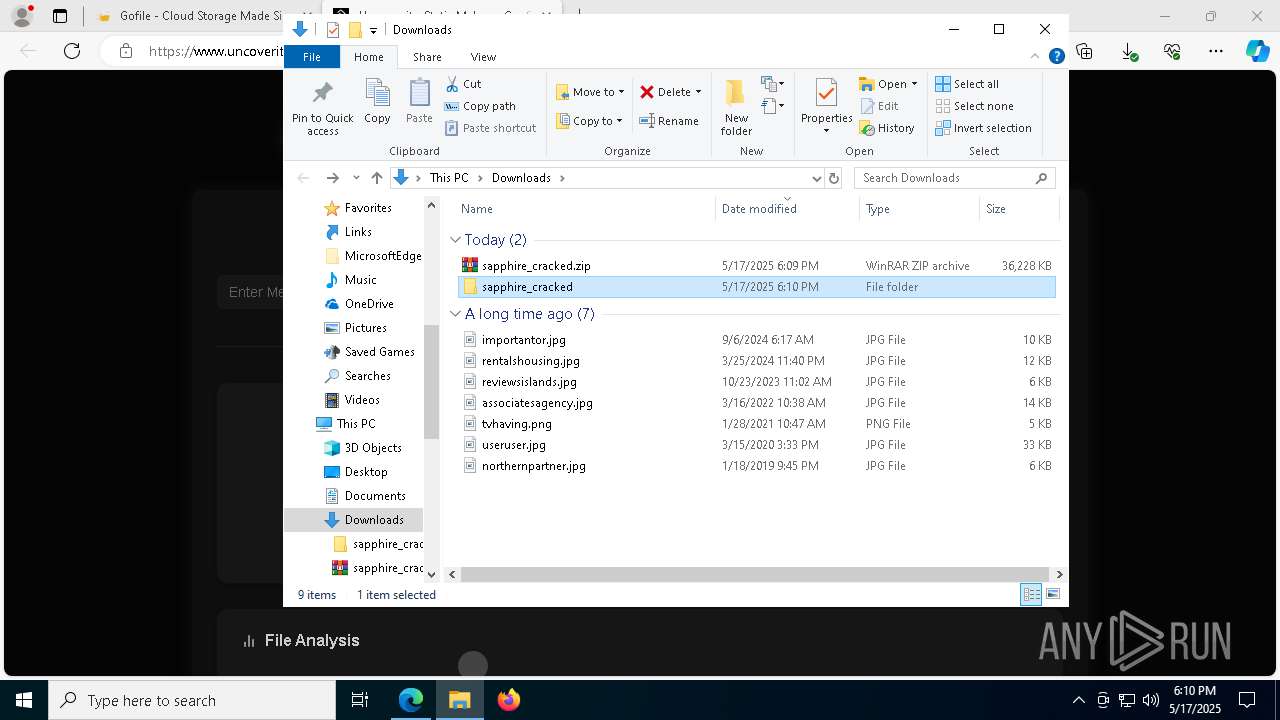
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5072)
Reads the computer name
- identity_helper.exe (PID: 4892)
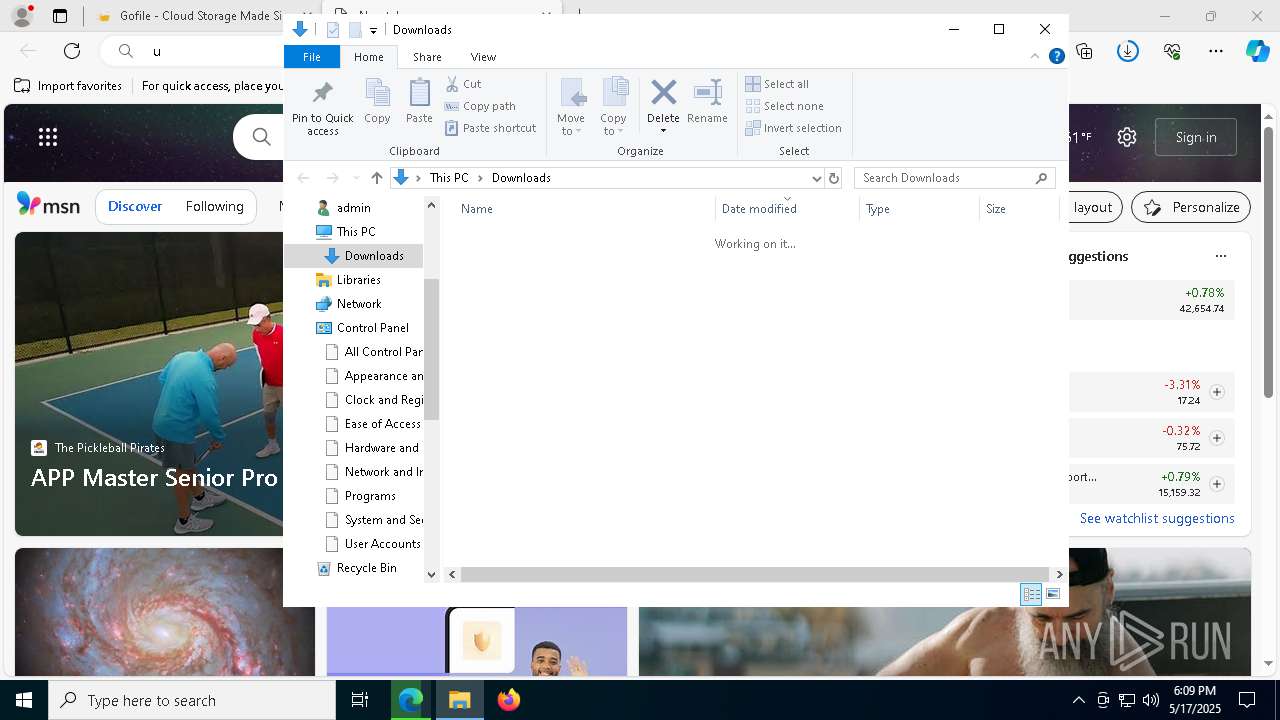
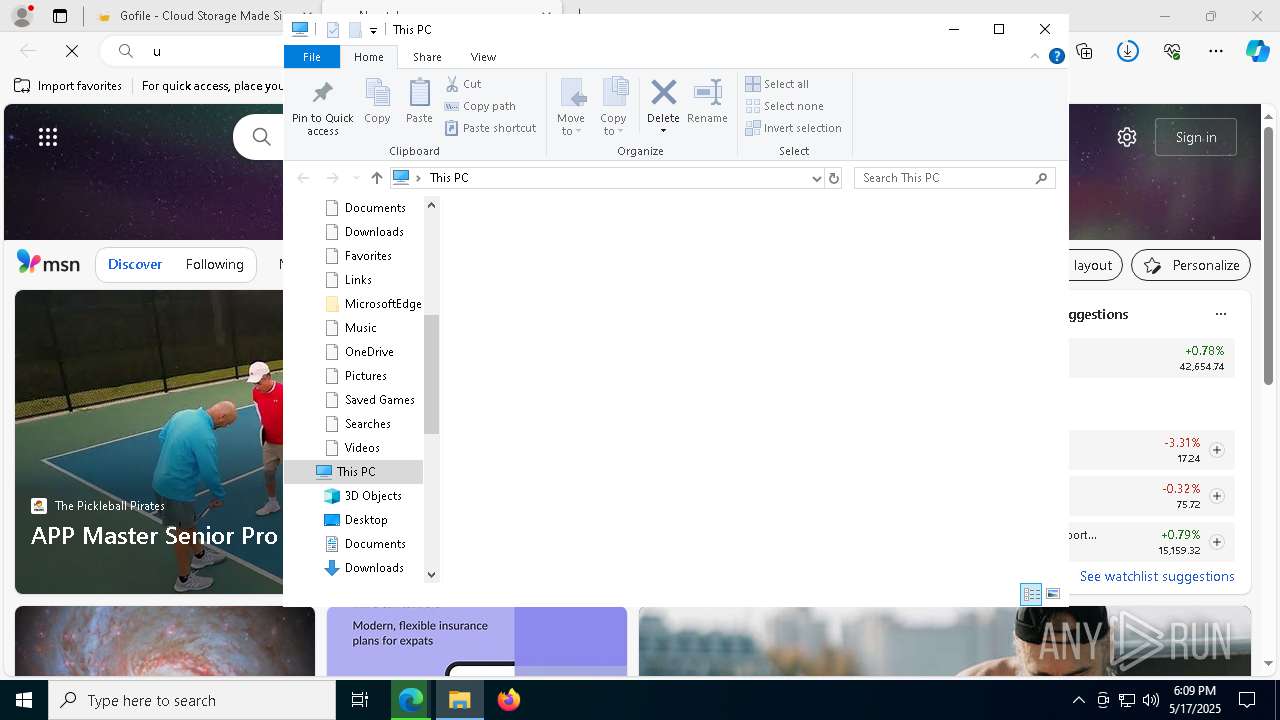
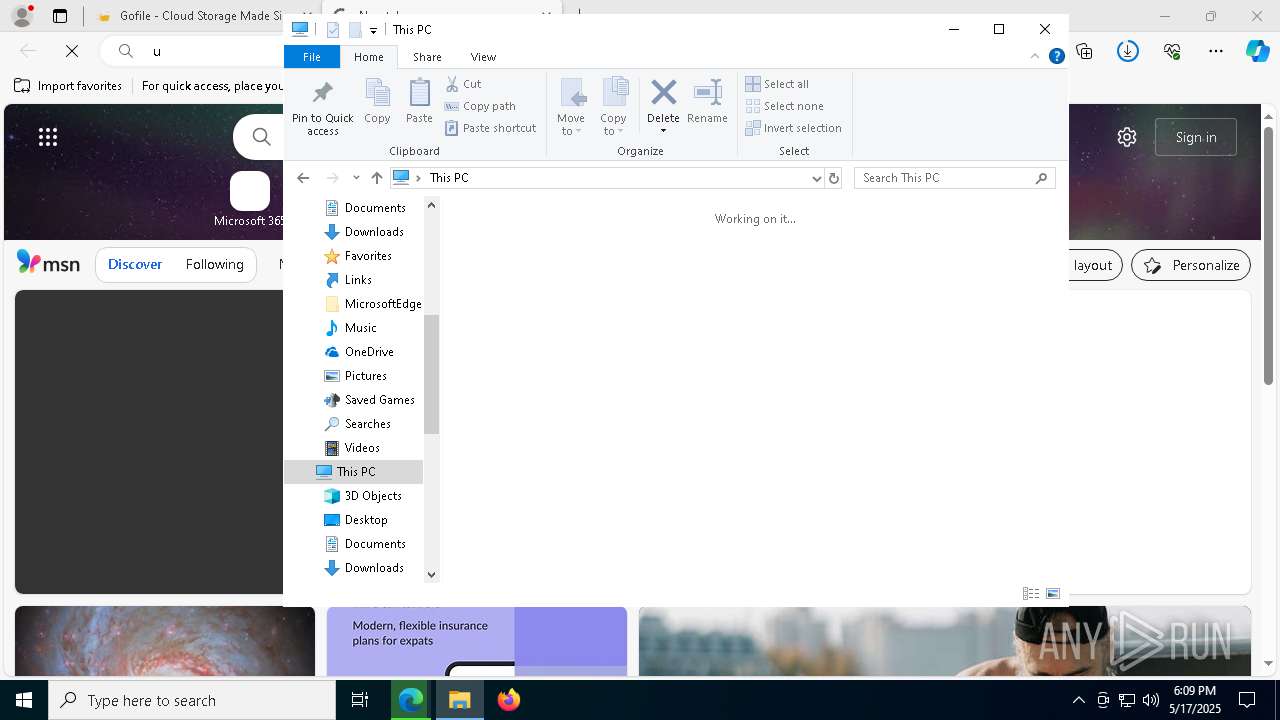
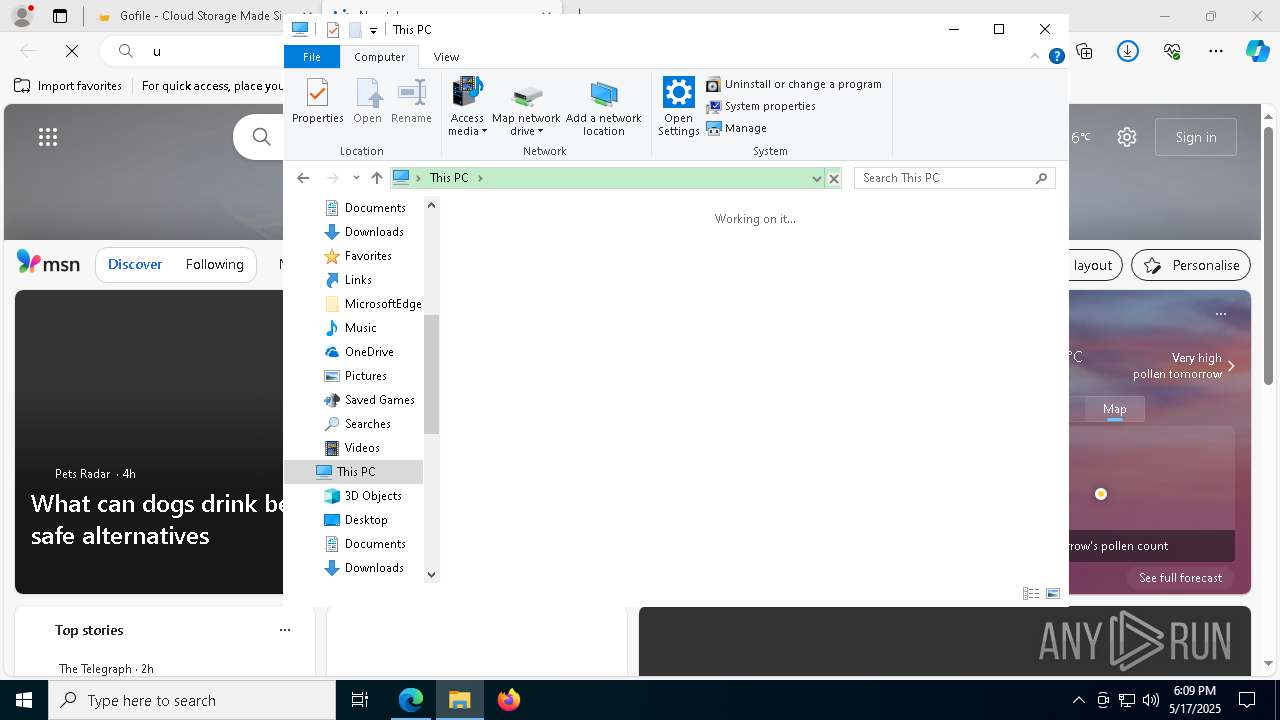
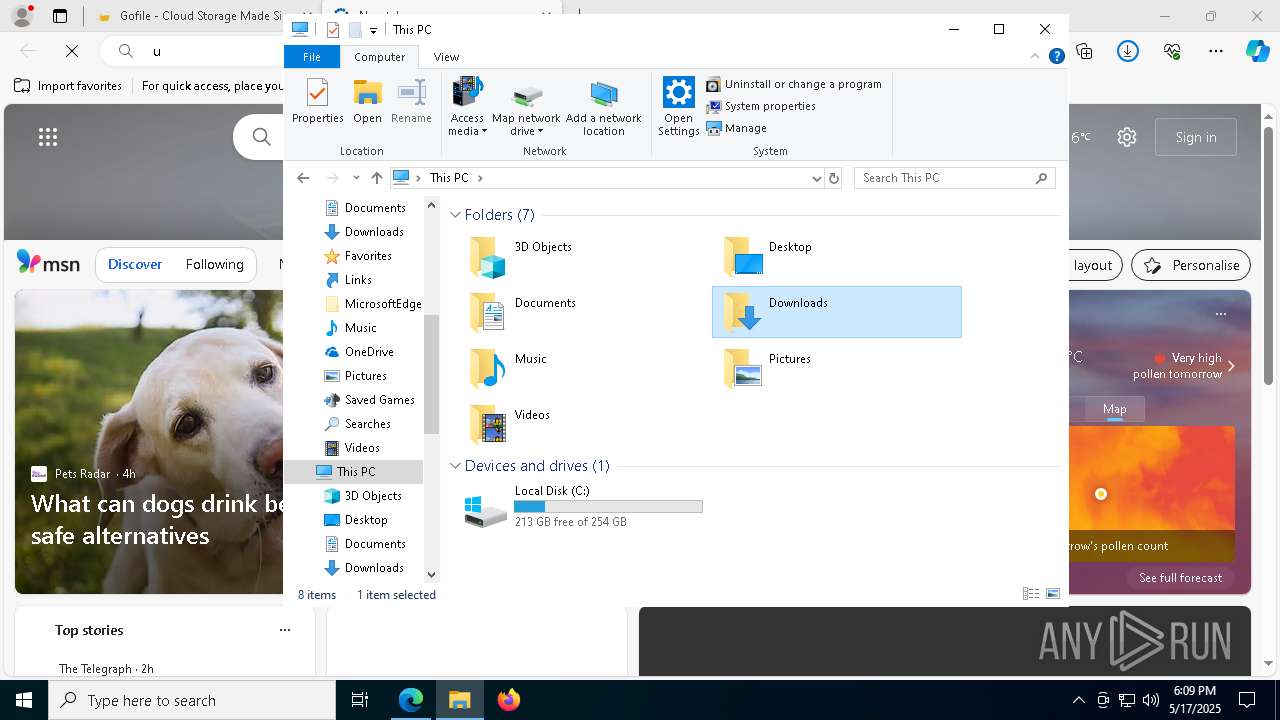
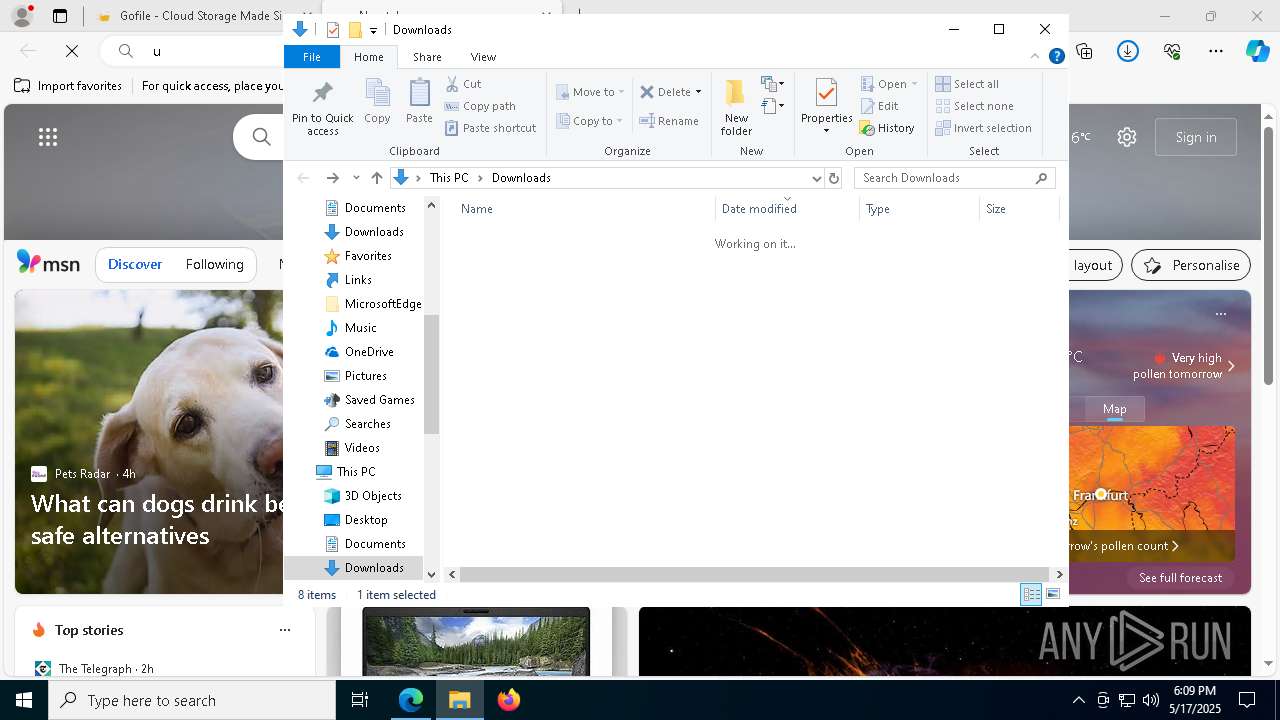
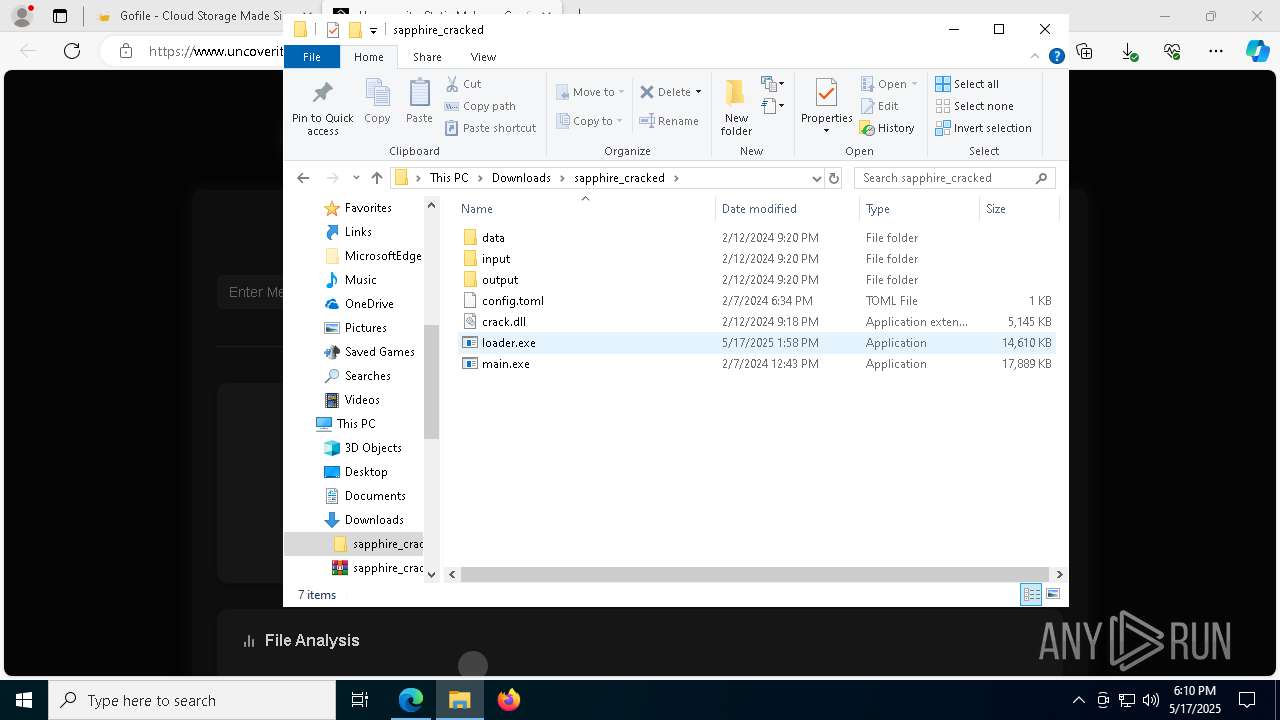
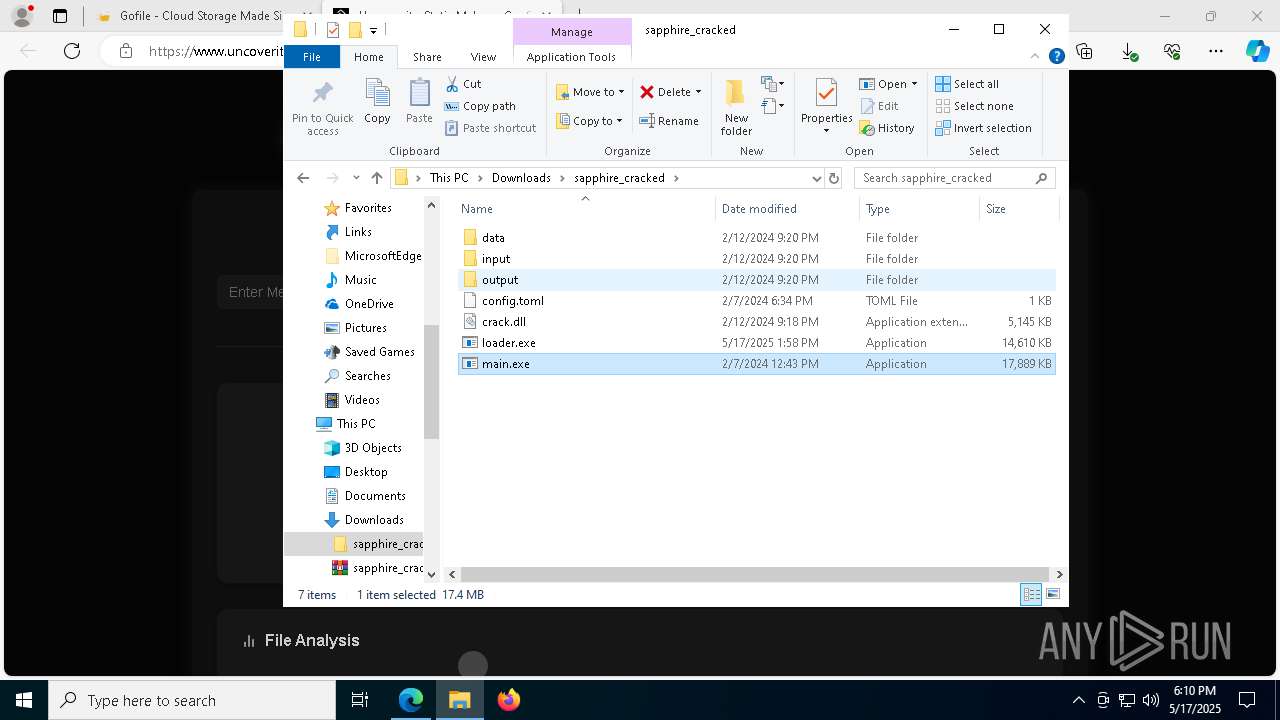
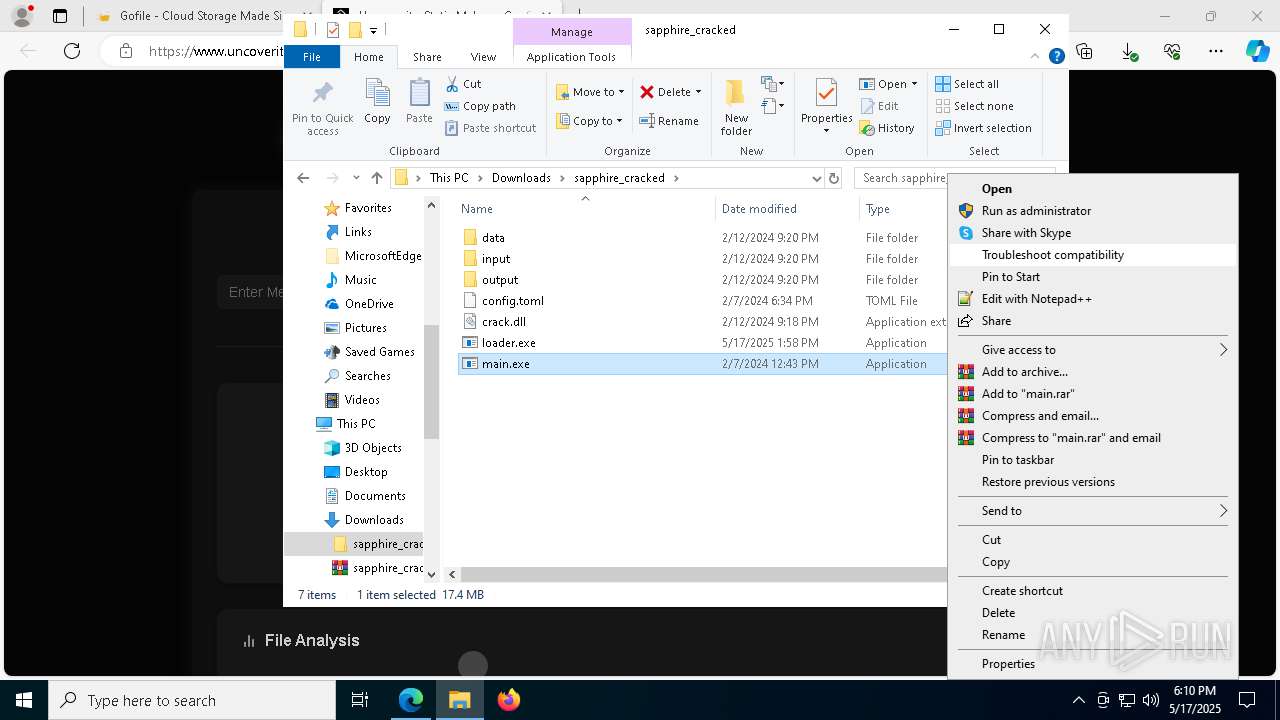
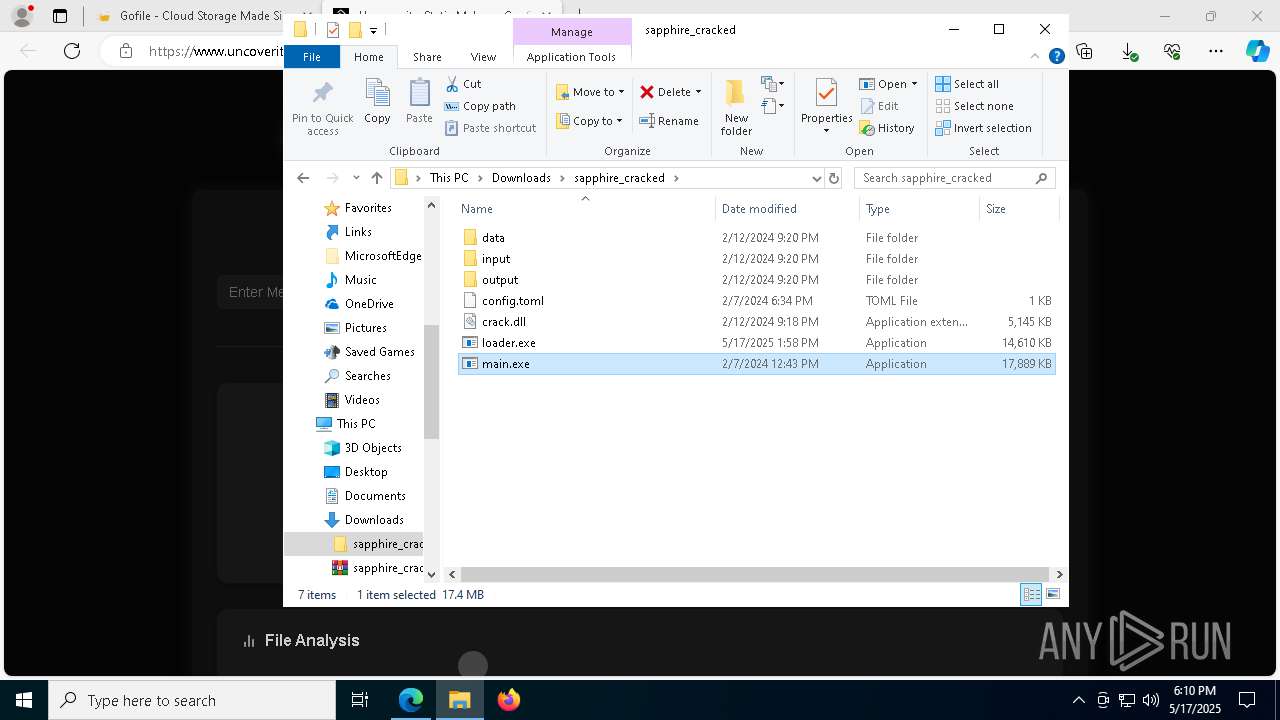
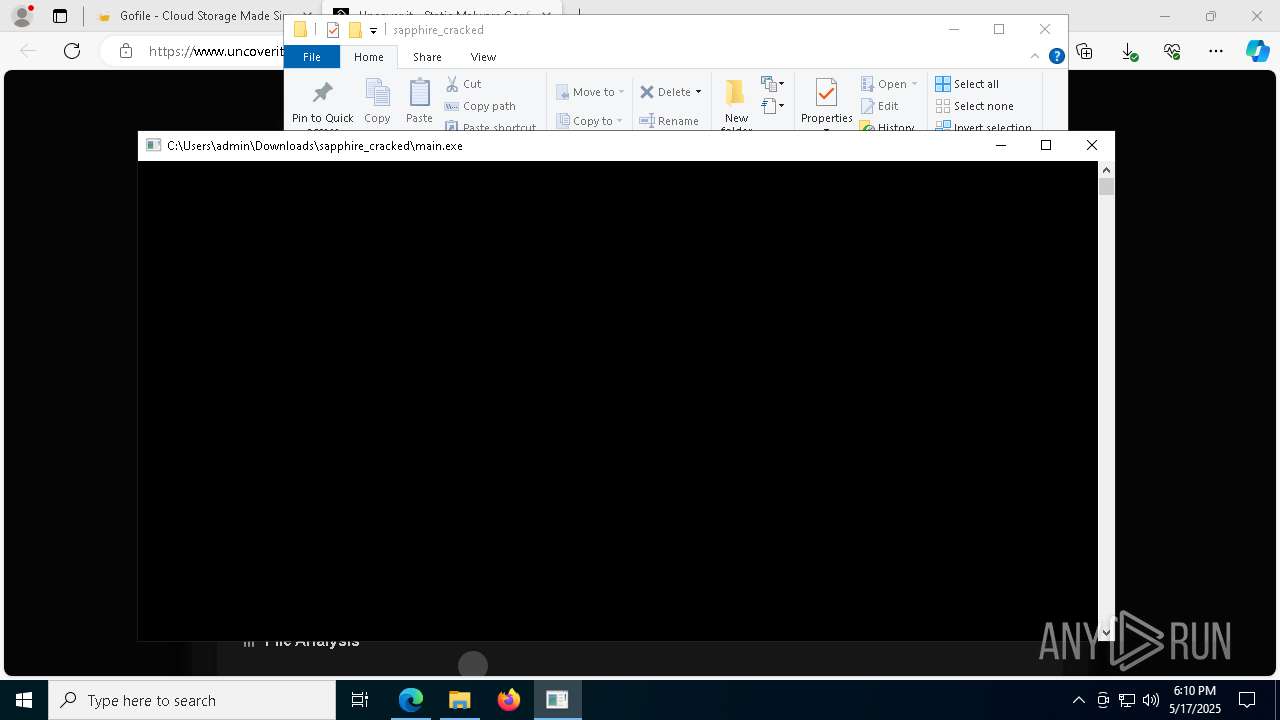
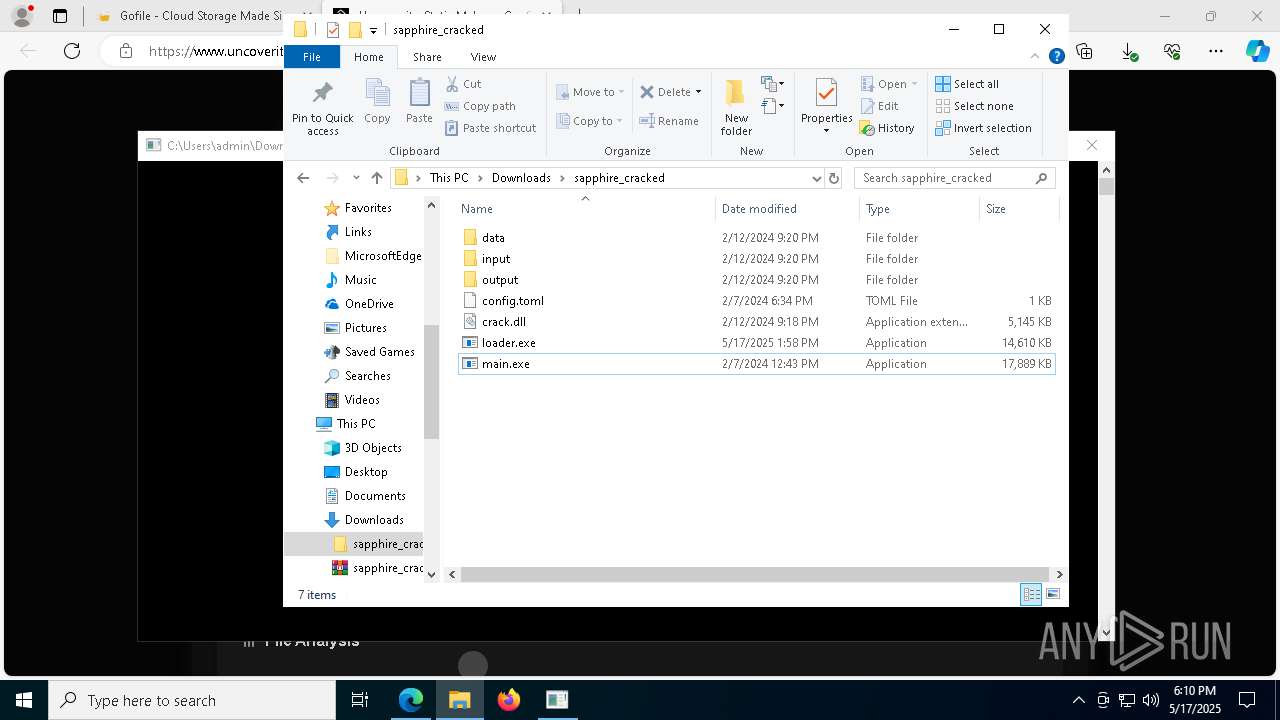
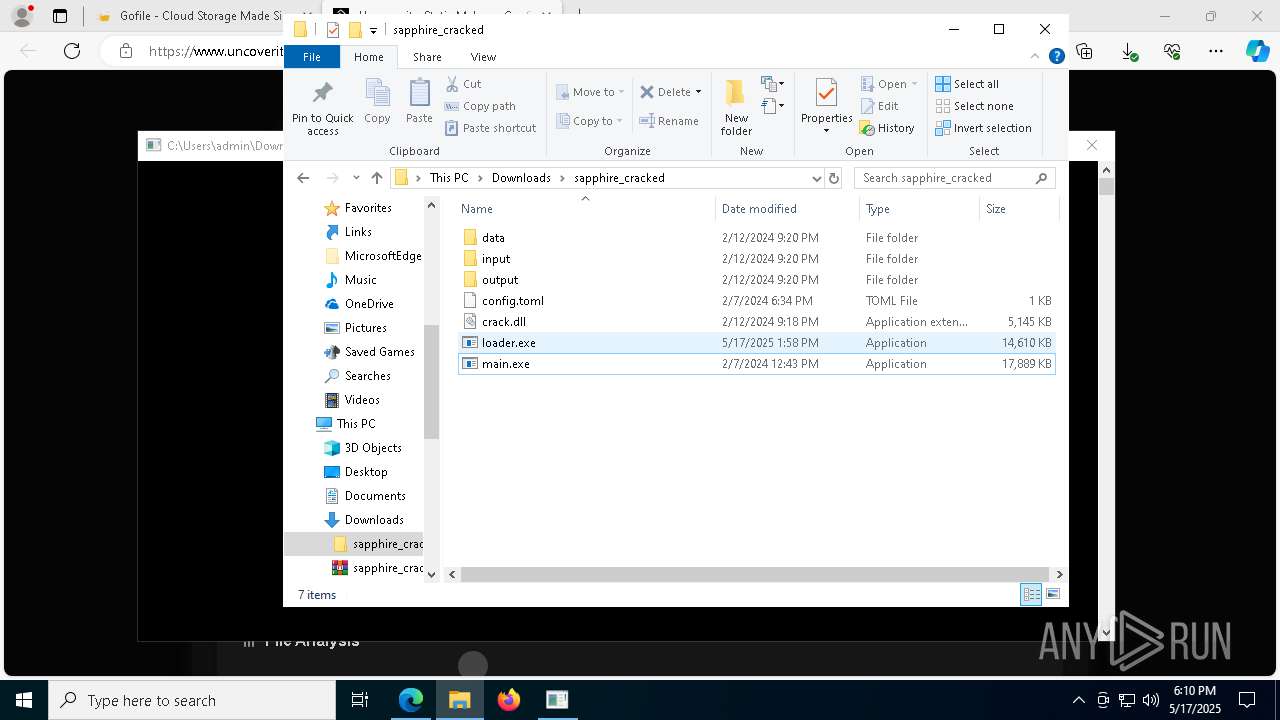
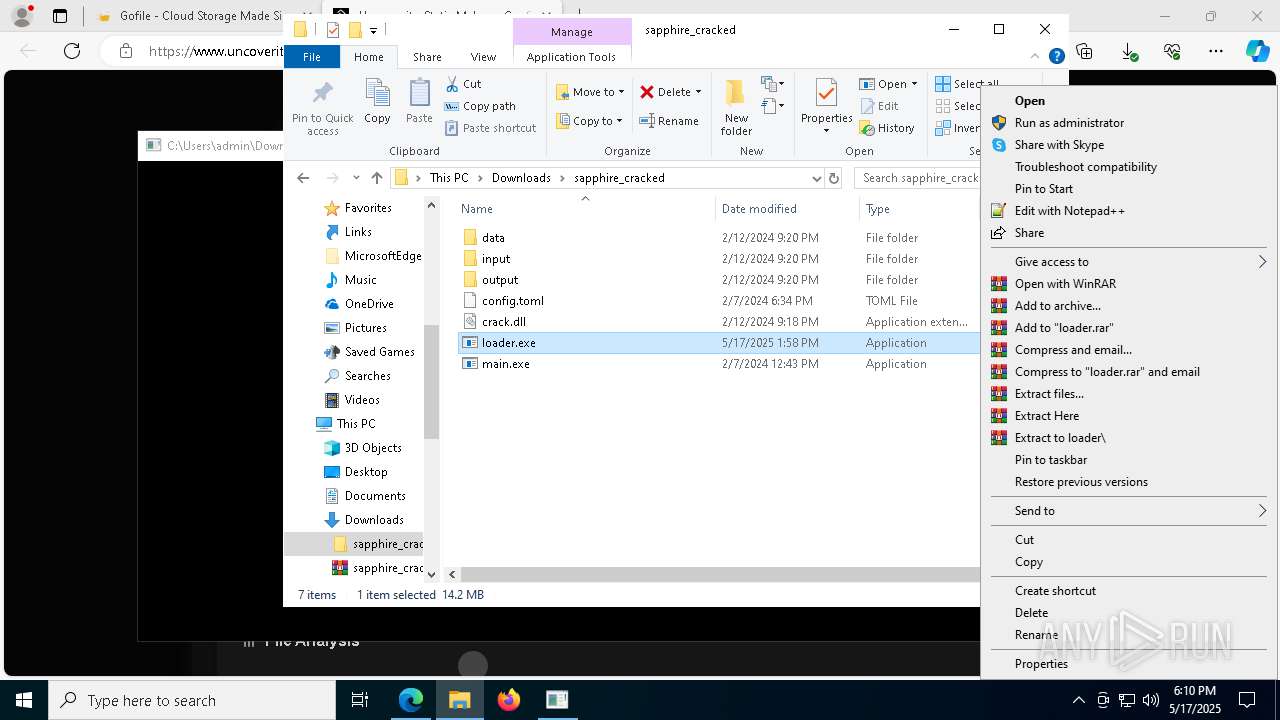
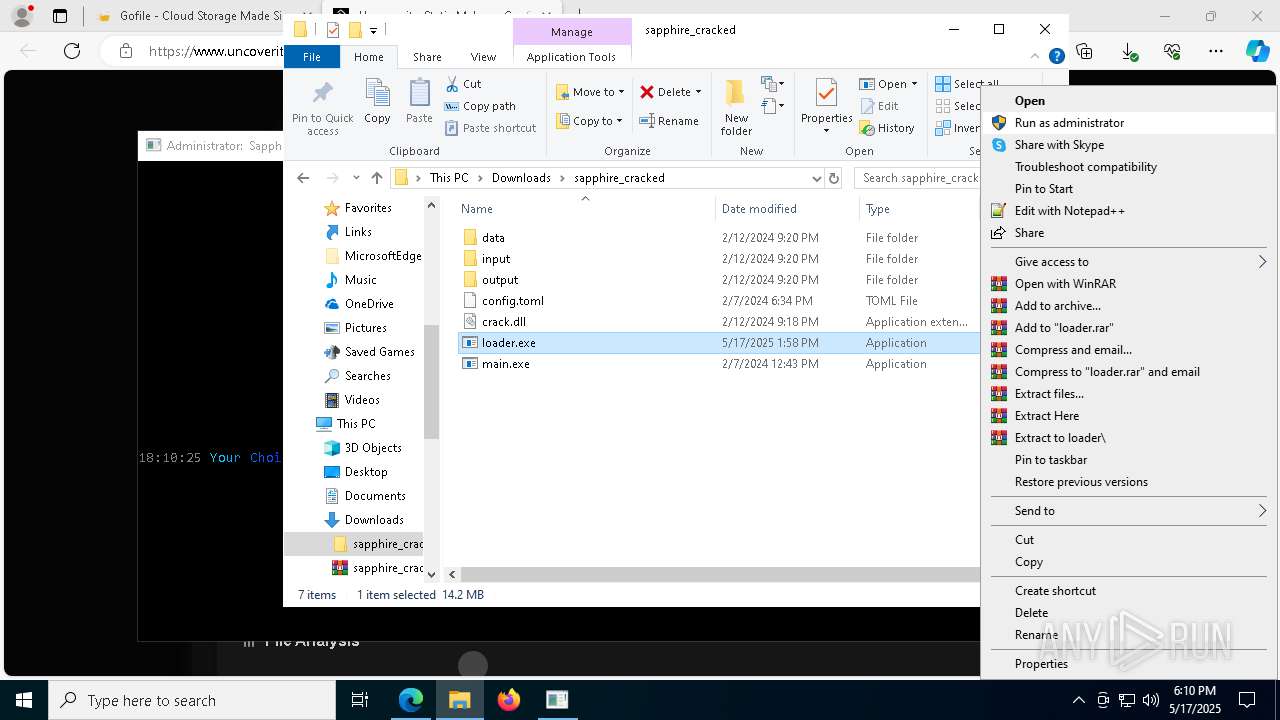
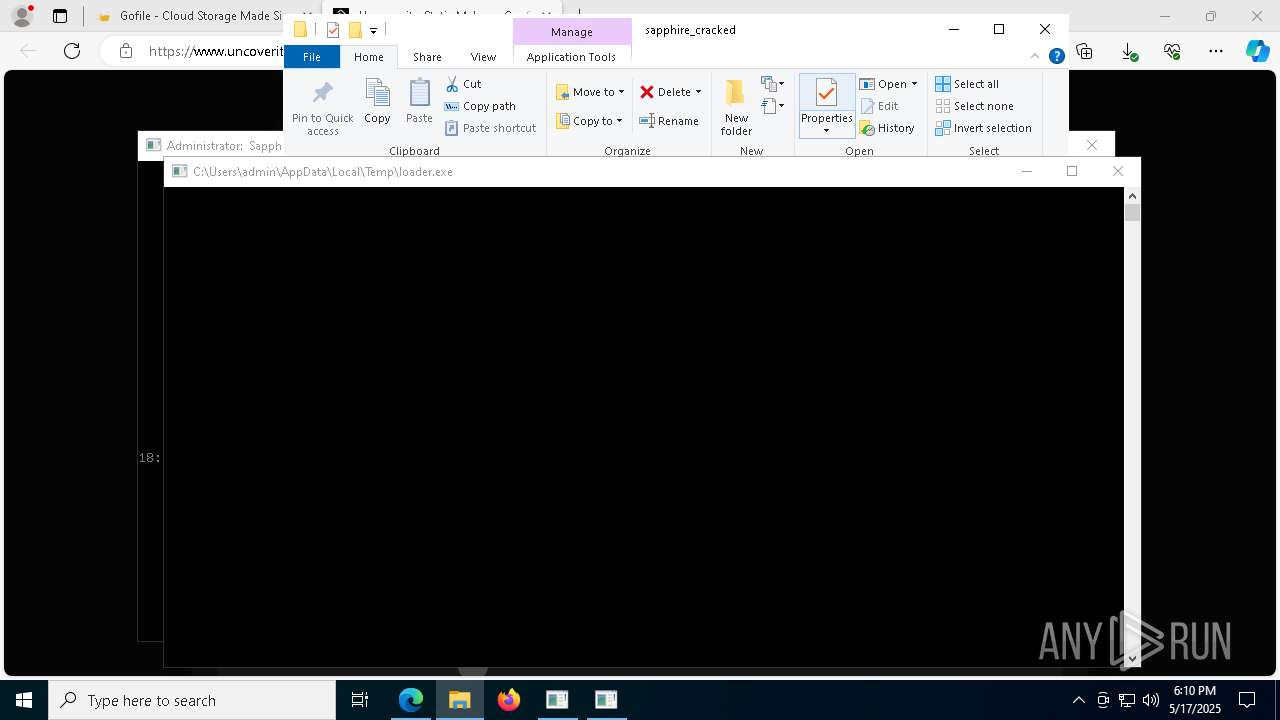
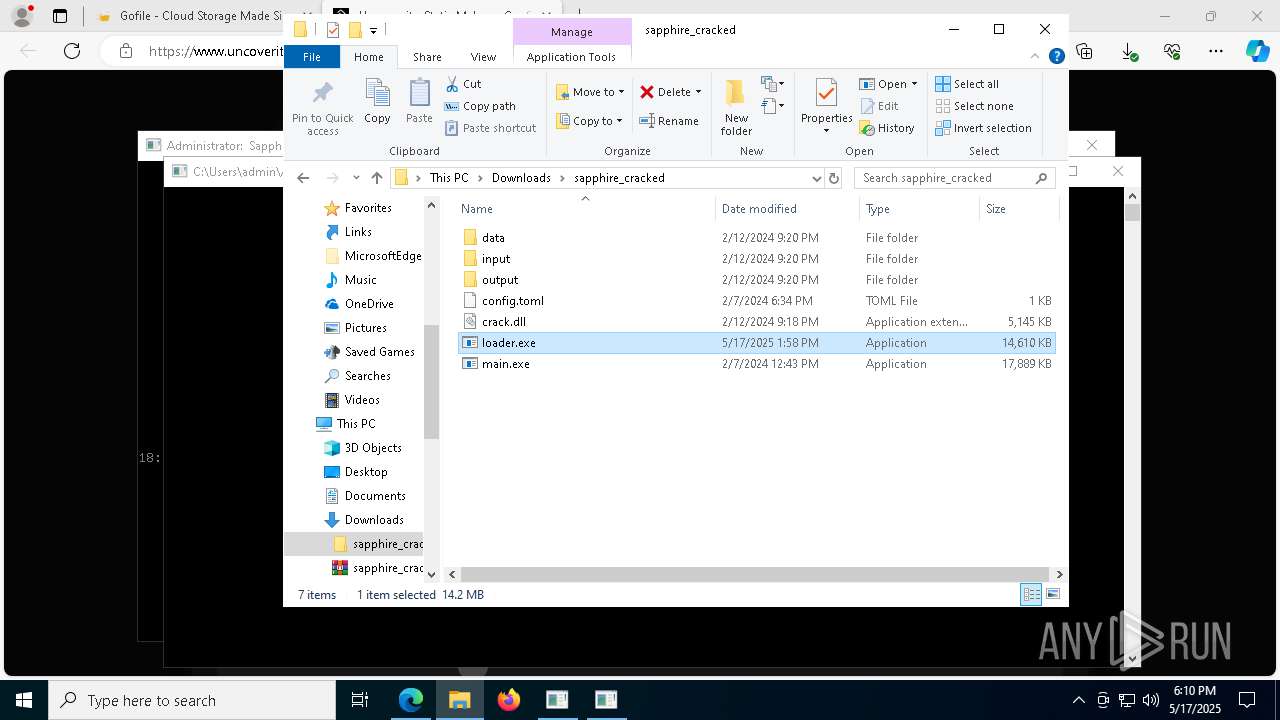
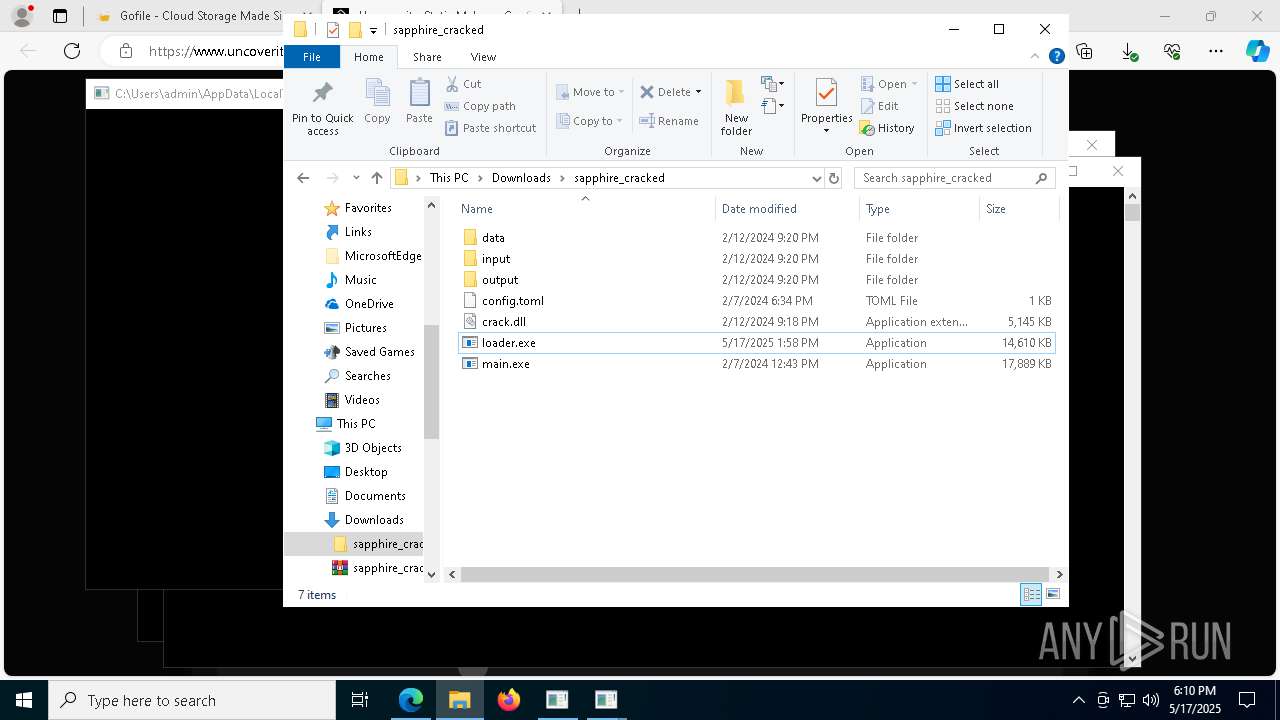
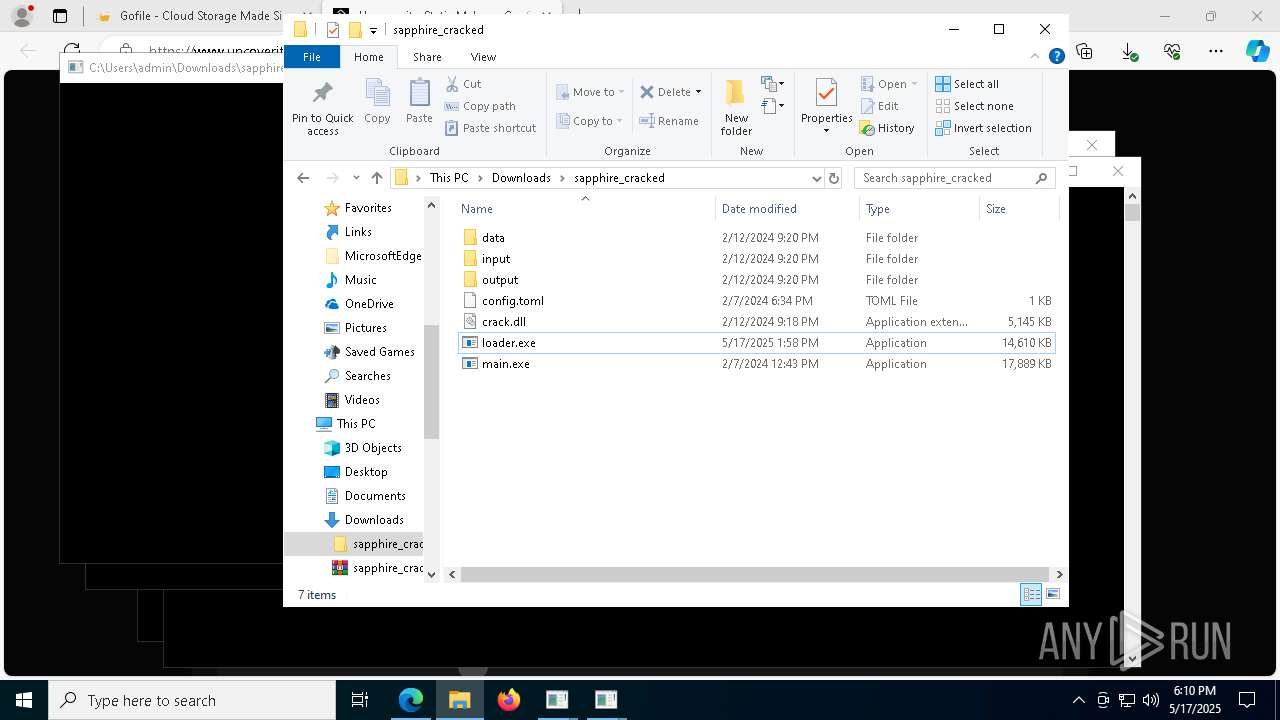
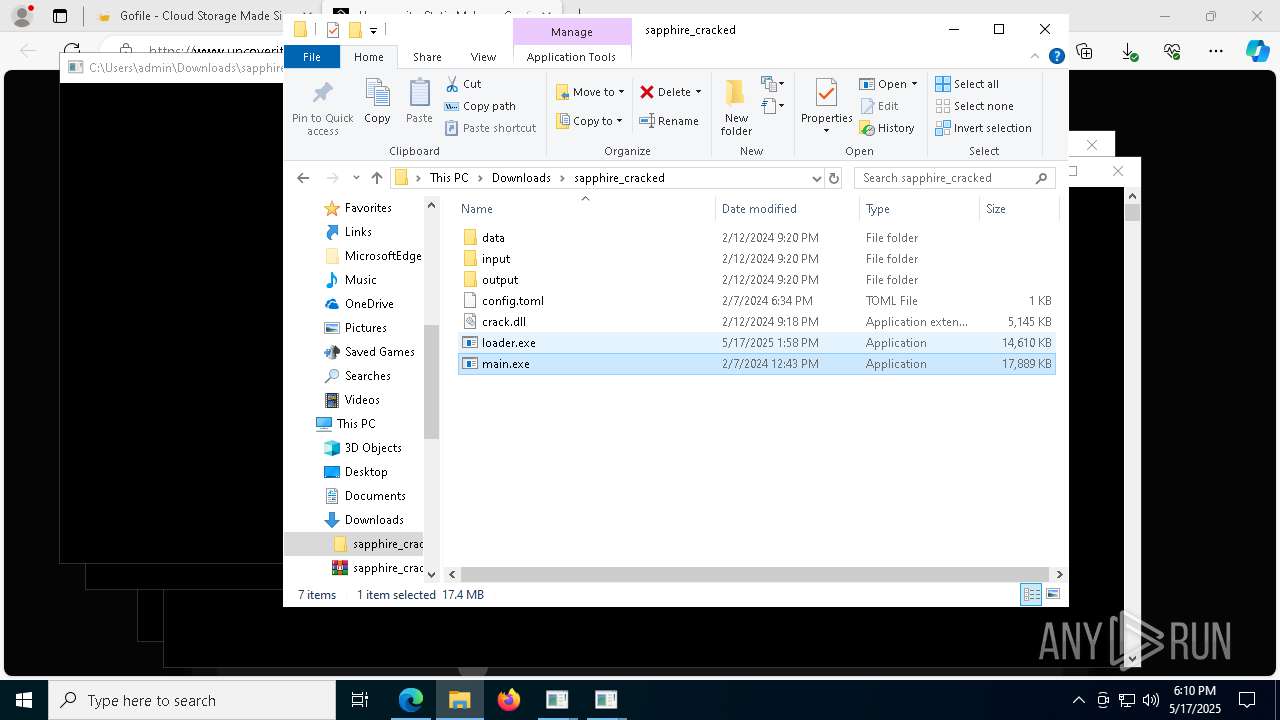
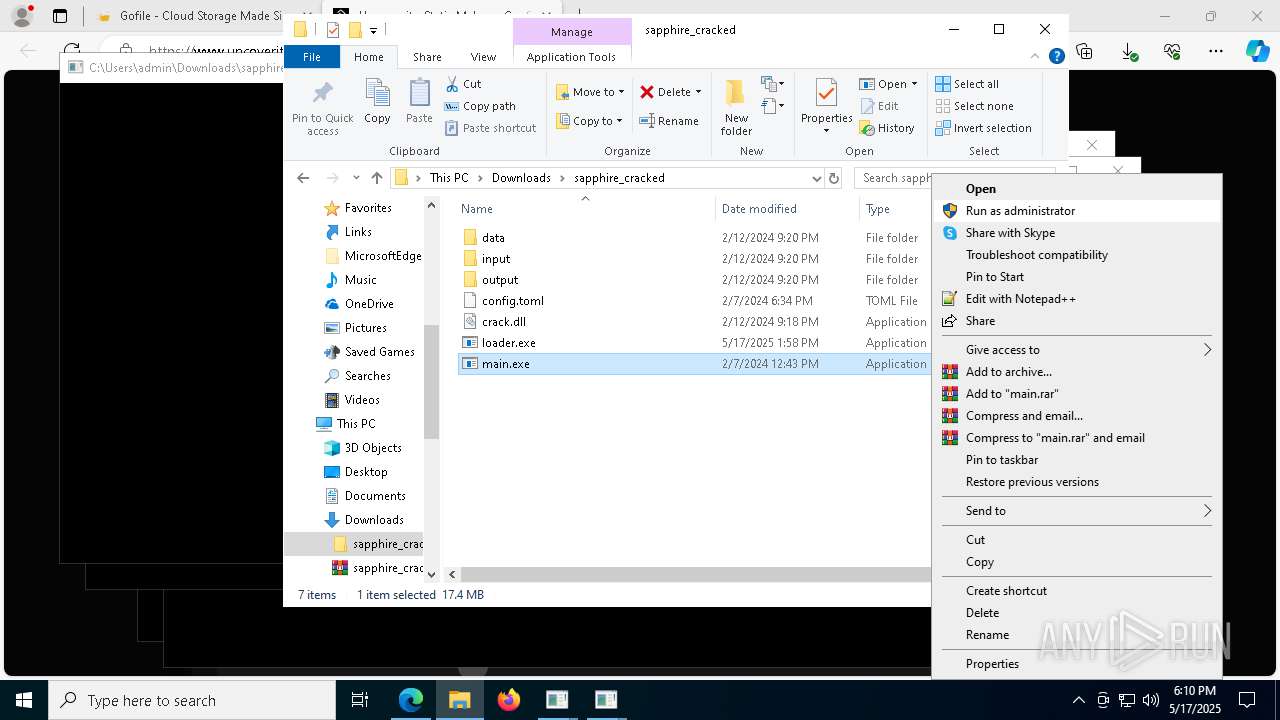
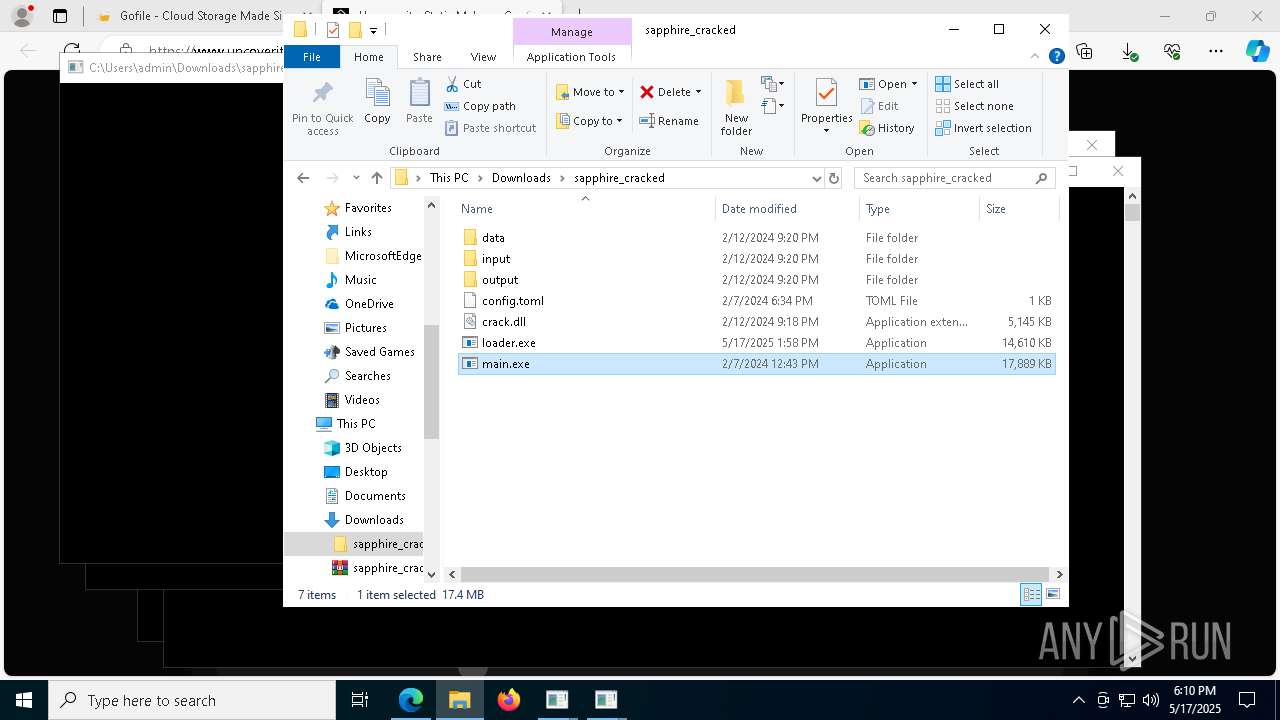
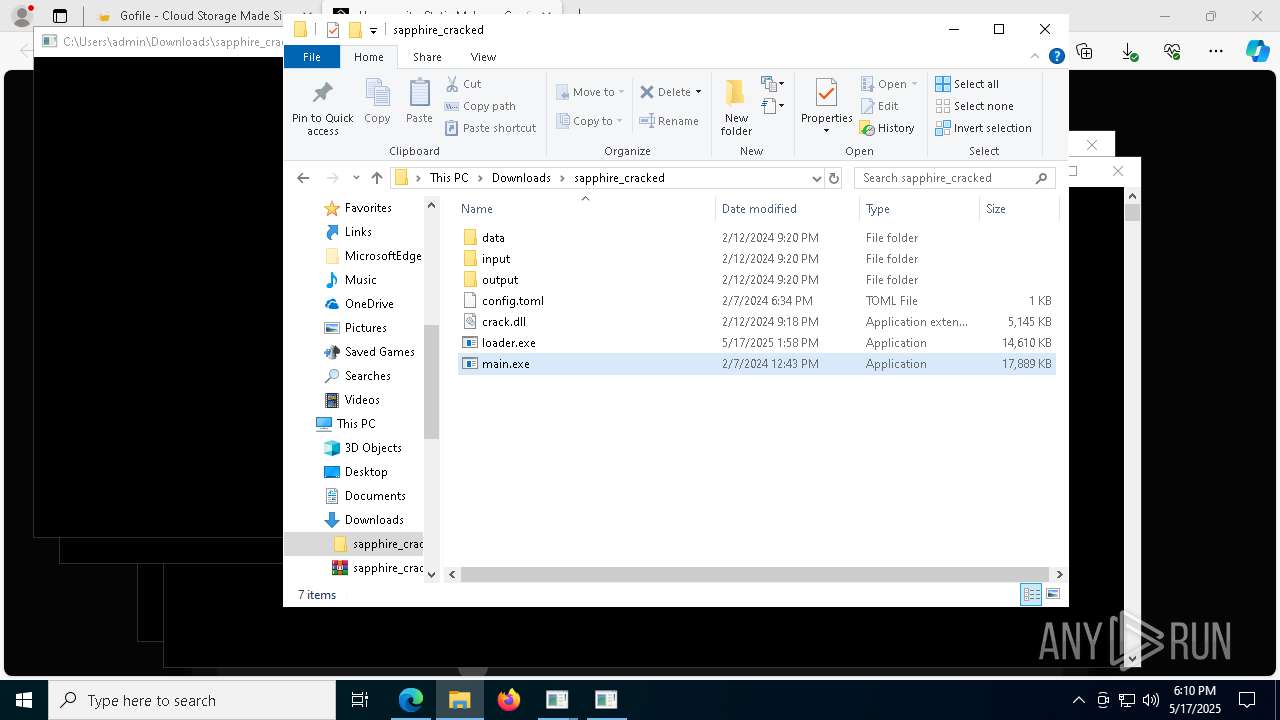
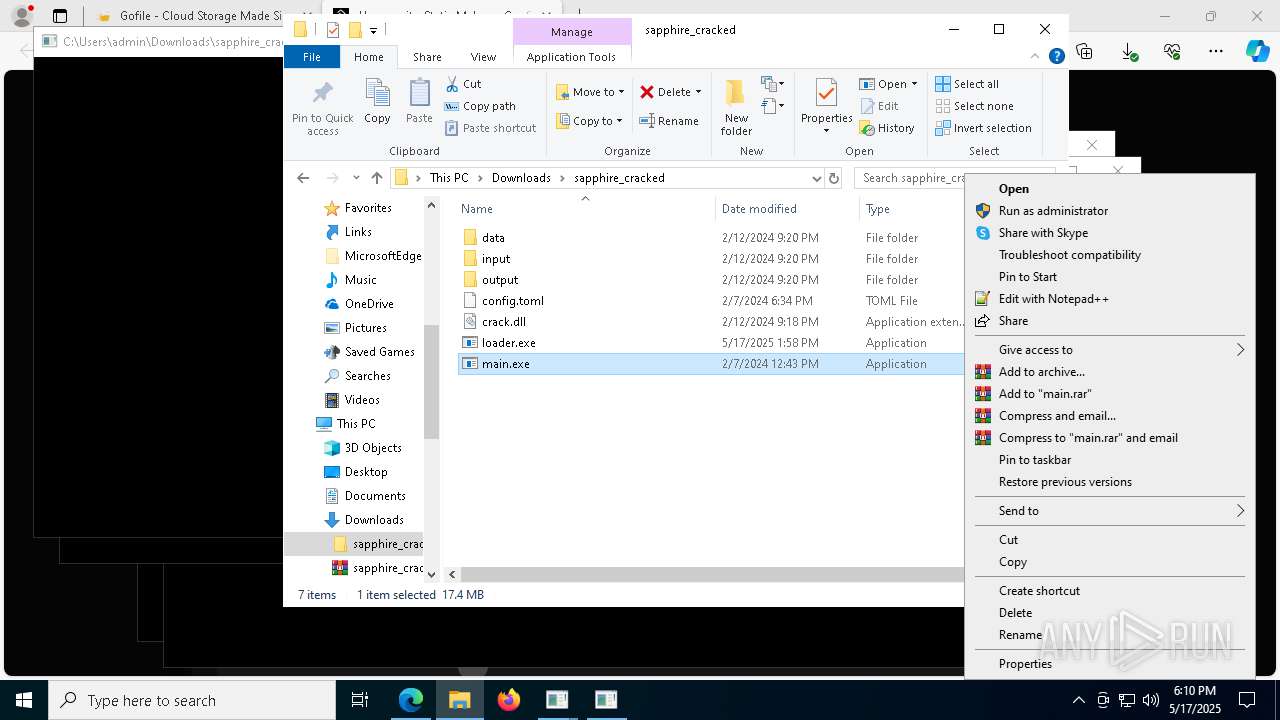
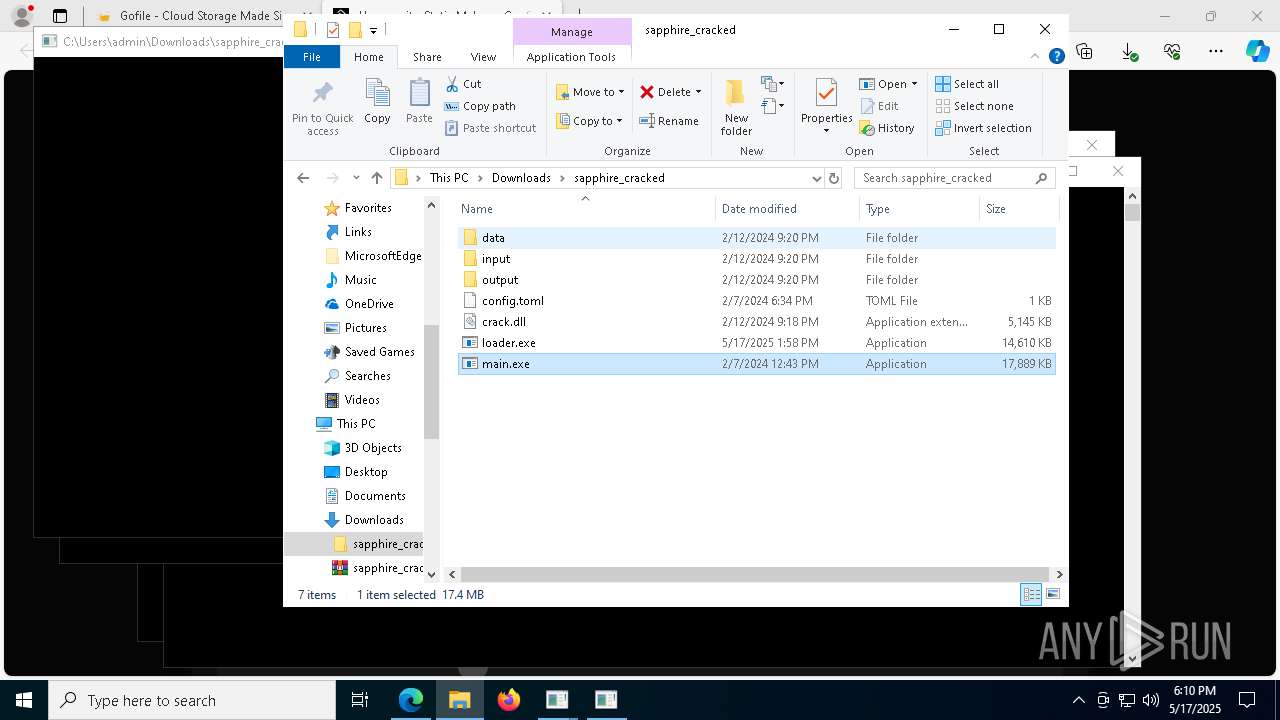
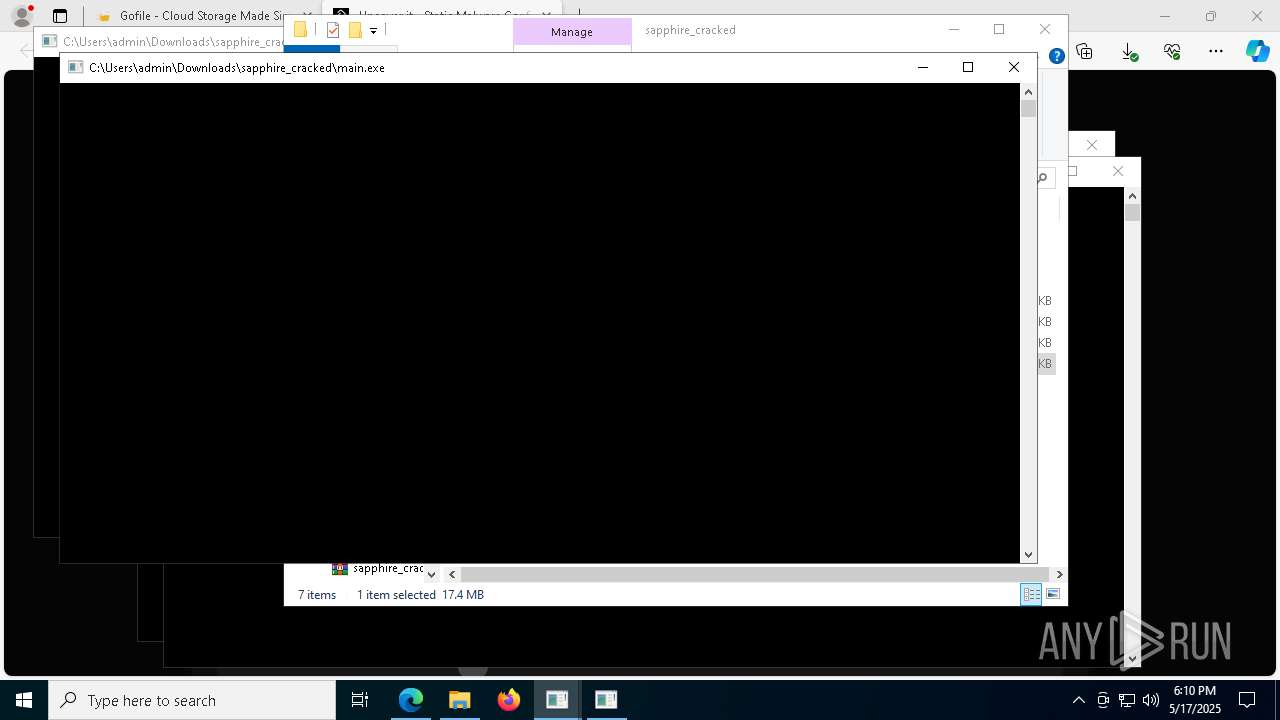
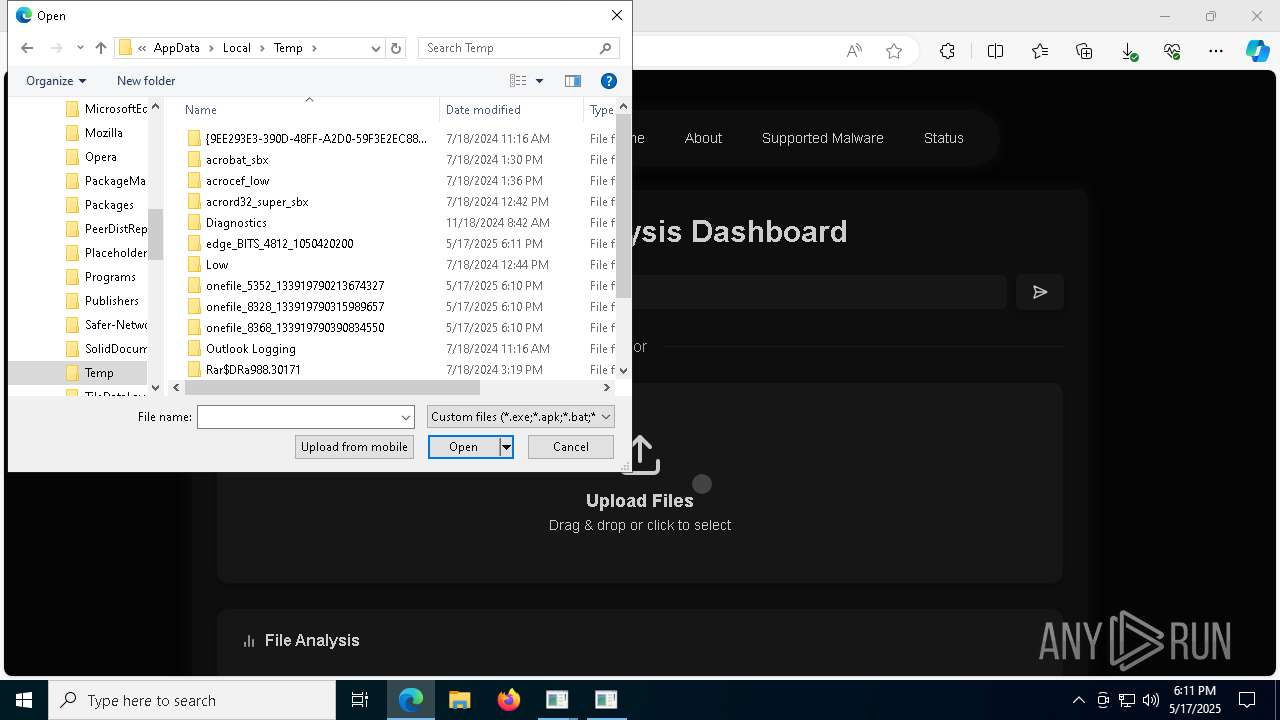
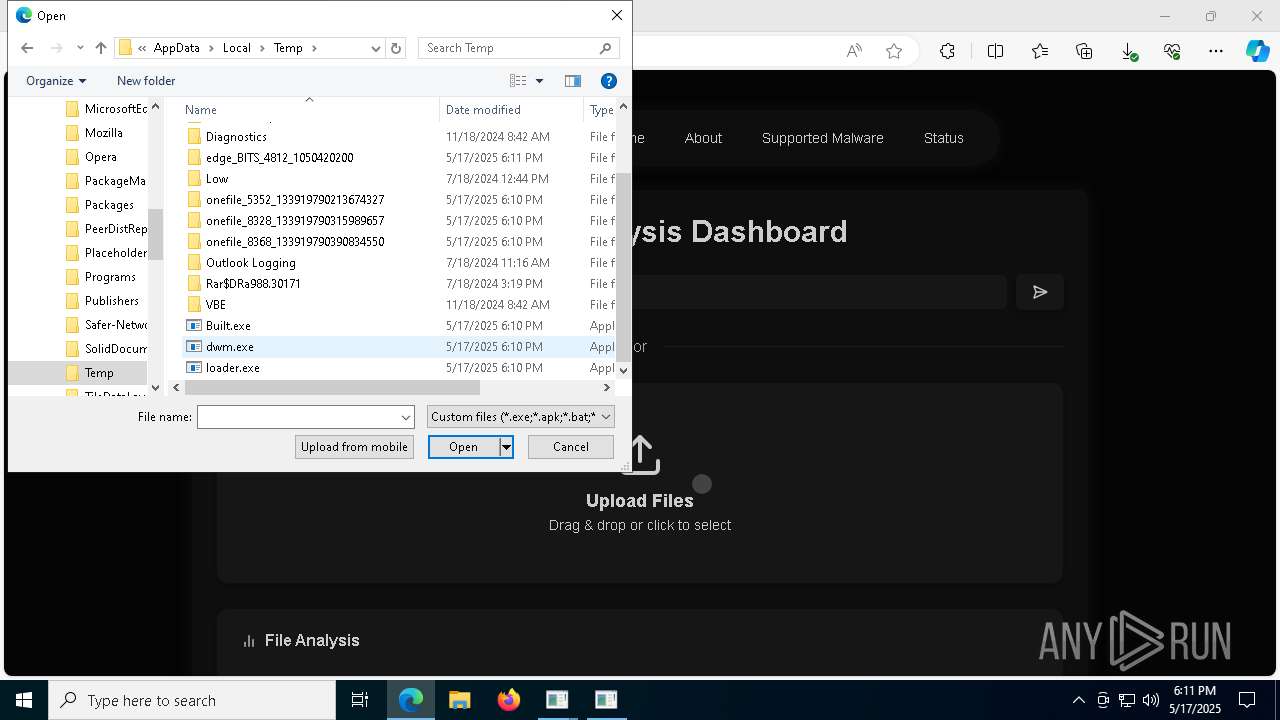
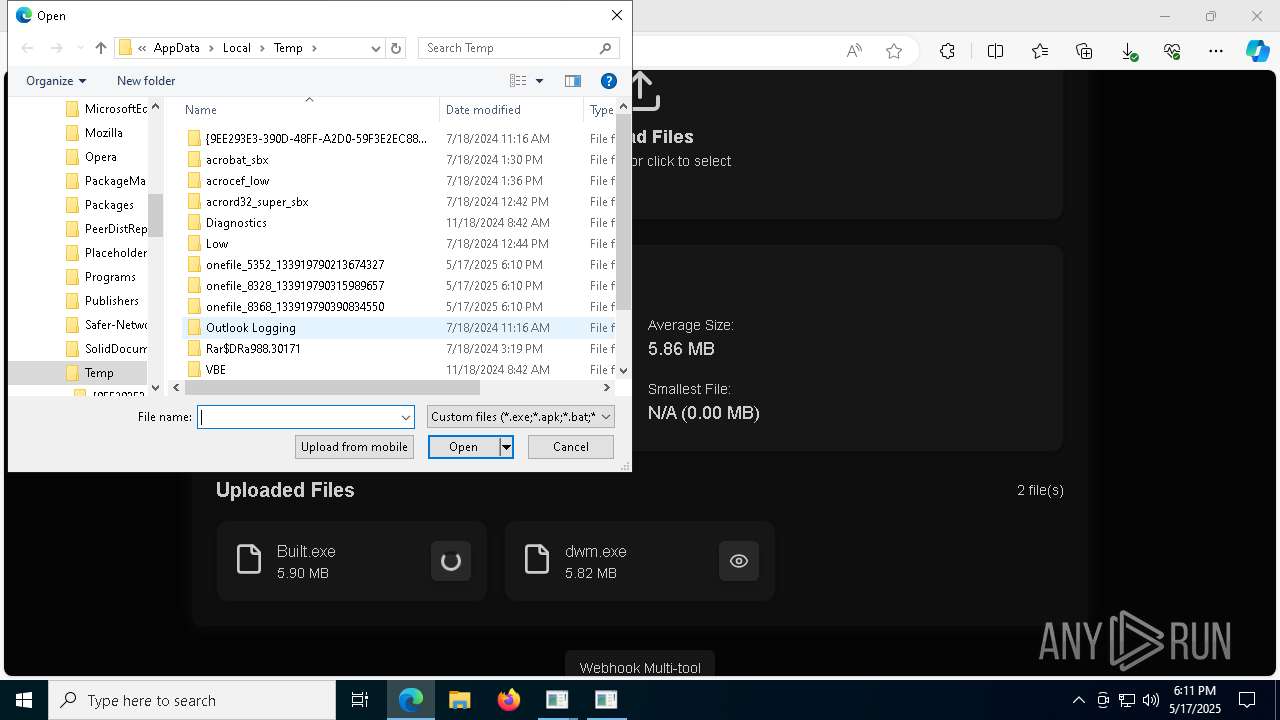
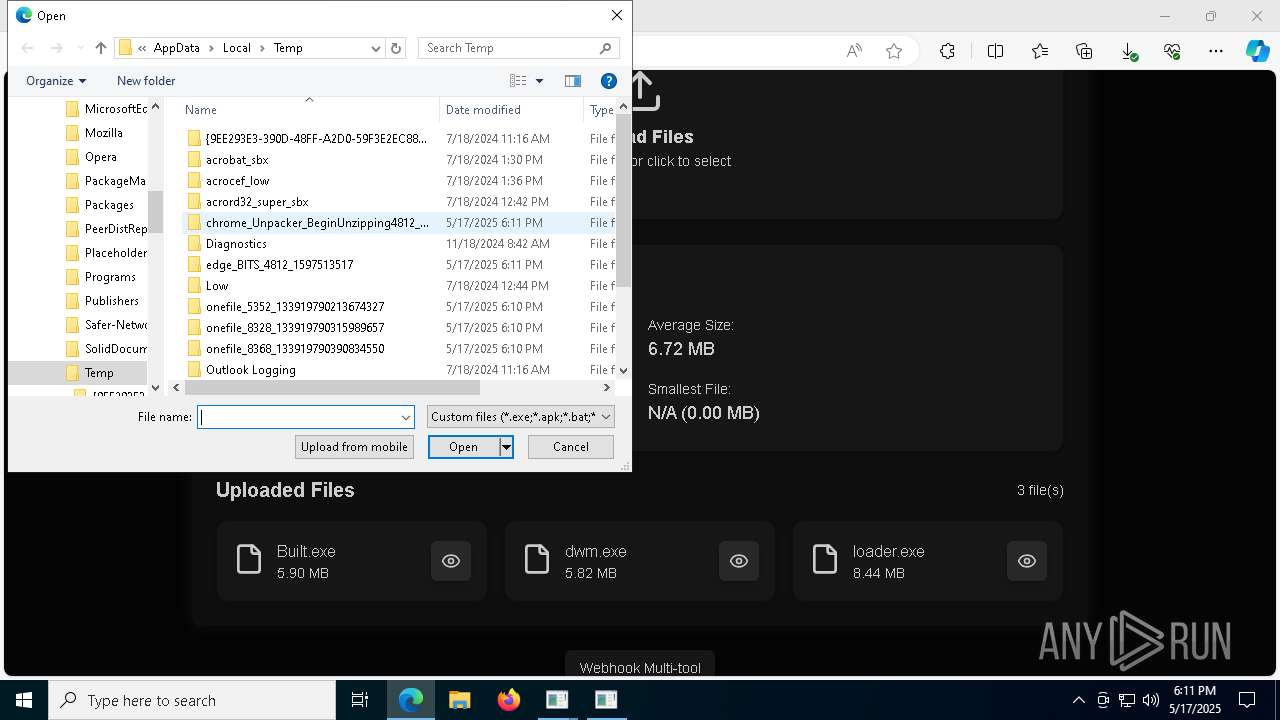
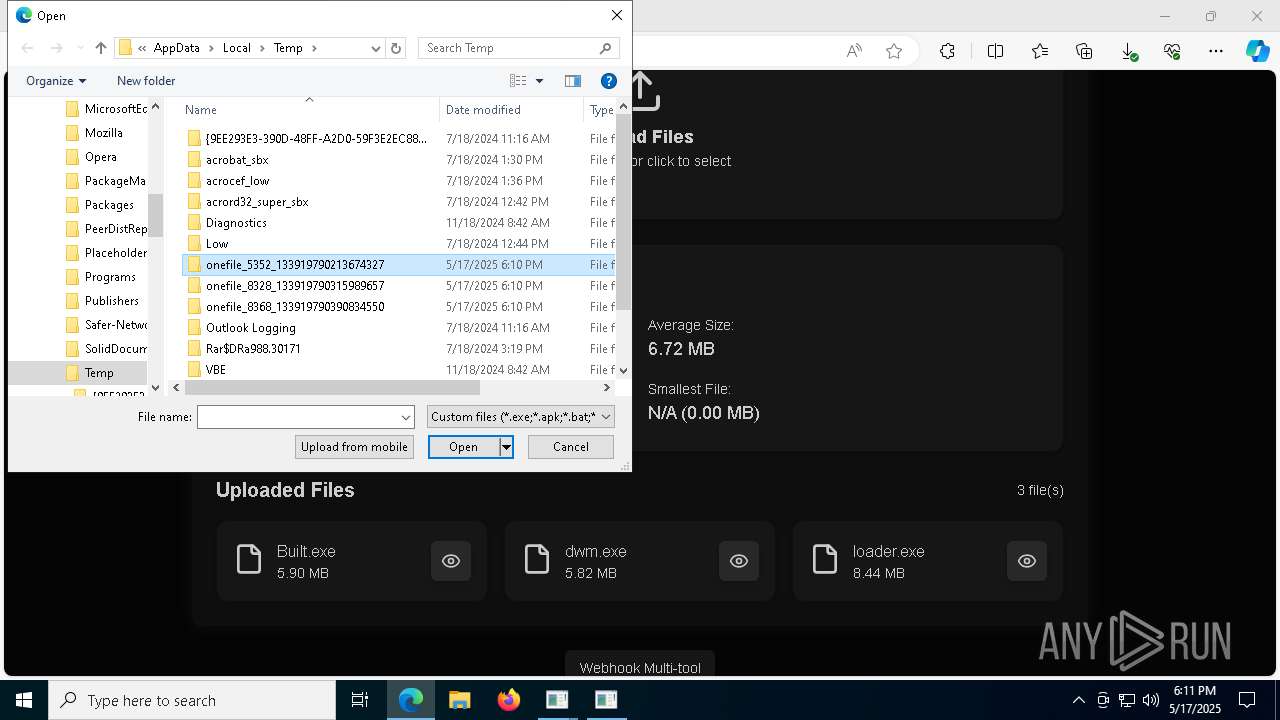
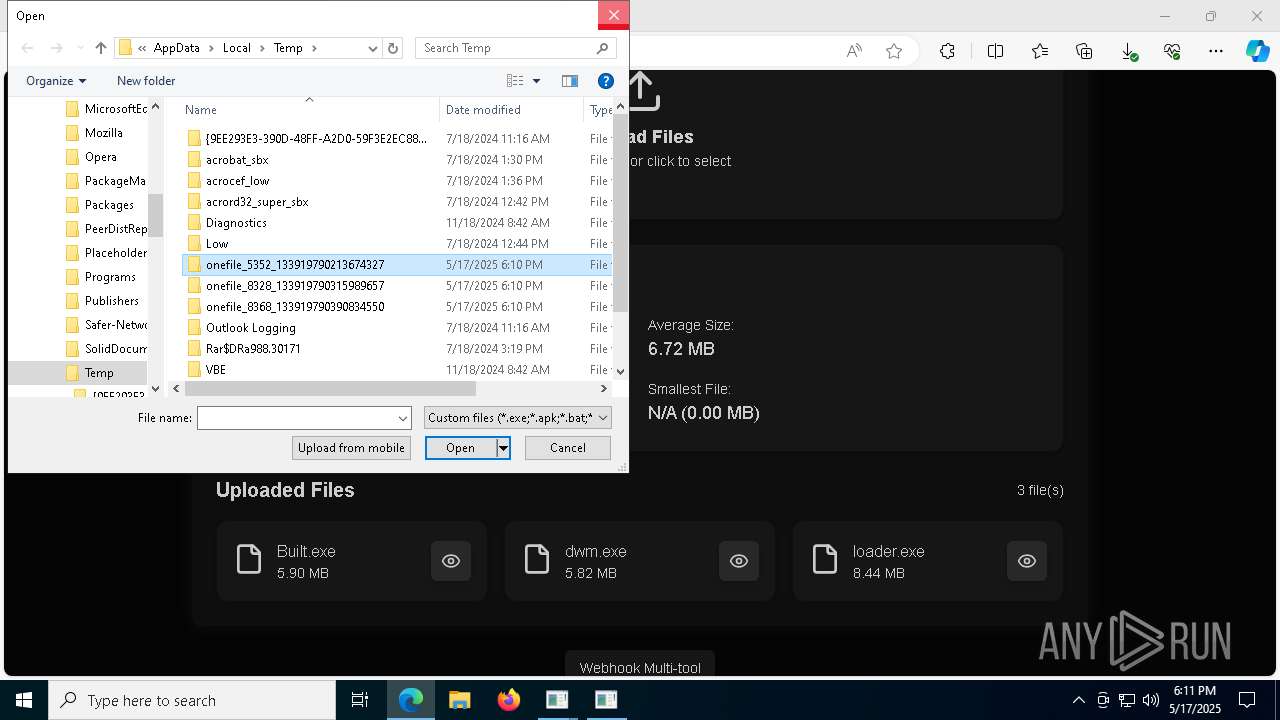
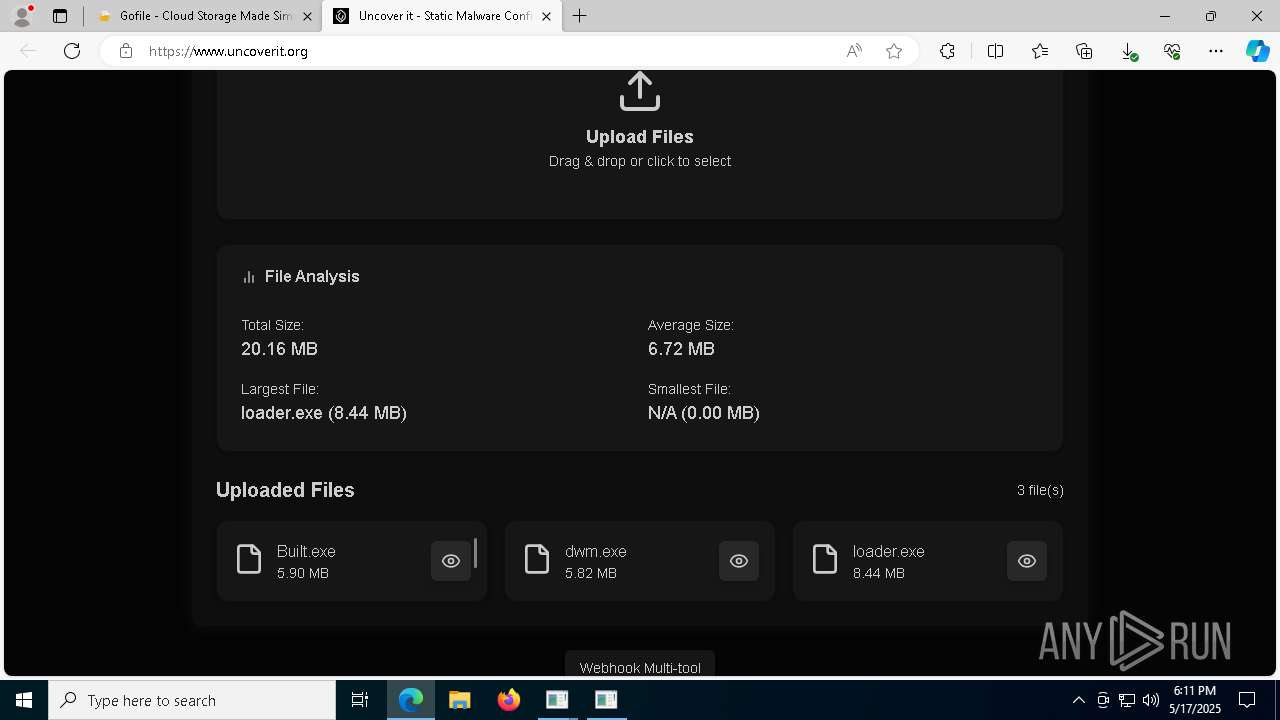
Manual execution by a user
- loader.exe (PID: 5048)
- WinRAR.exe (PID: 5072)
- main.exe (PID: 5352)
- loader.exe (PID: 7836)
- main.exe (PID: 8368)
- main.exe (PID: 8816)
Checks supported languages
- identity_helper.exe (PID: 4892)
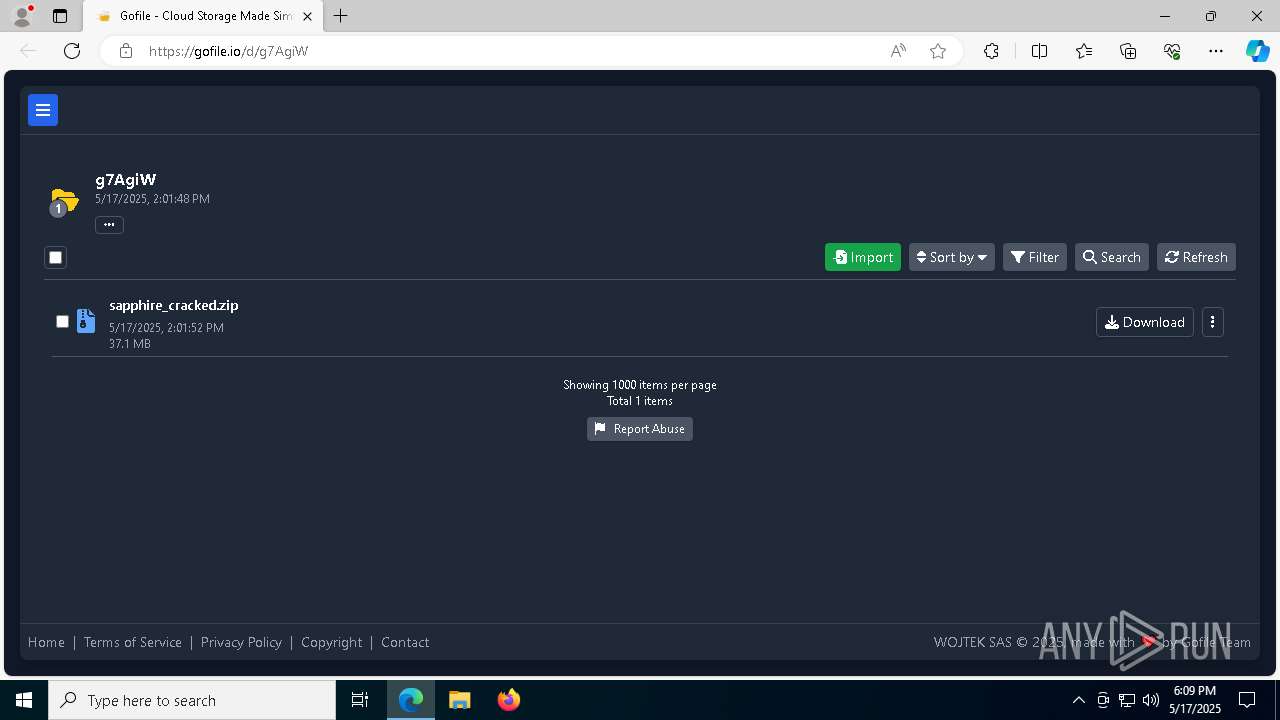
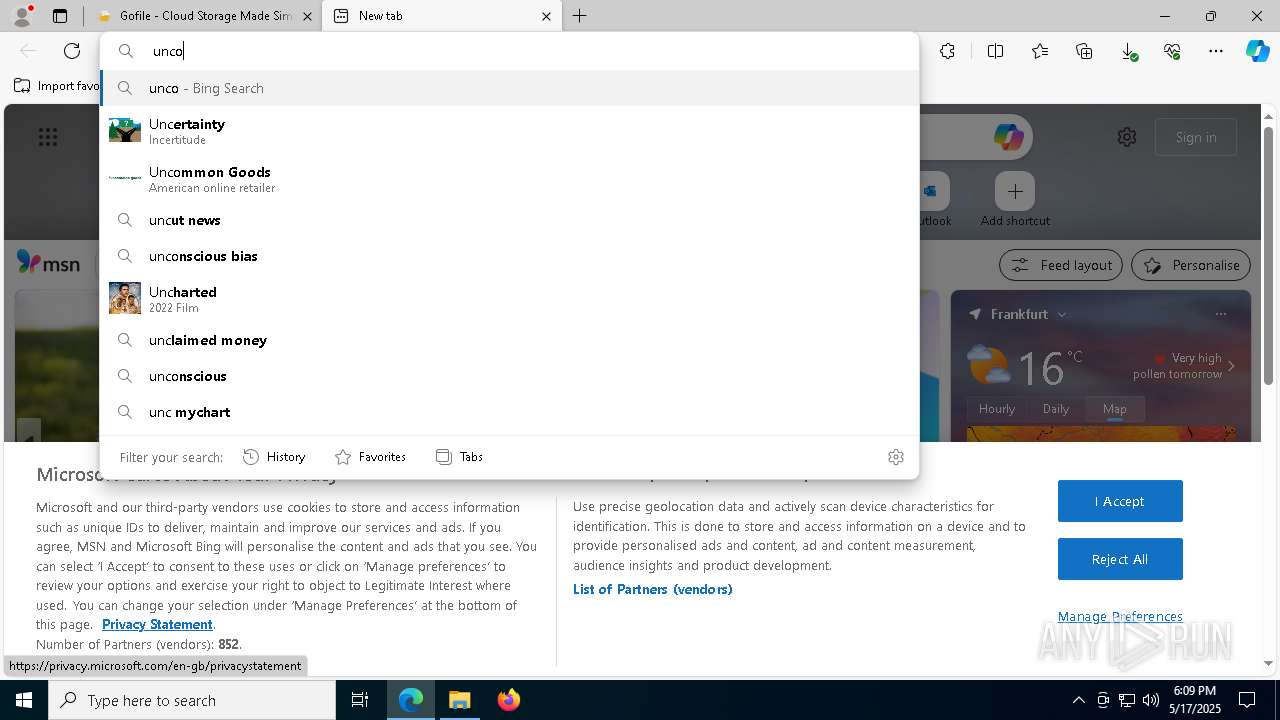
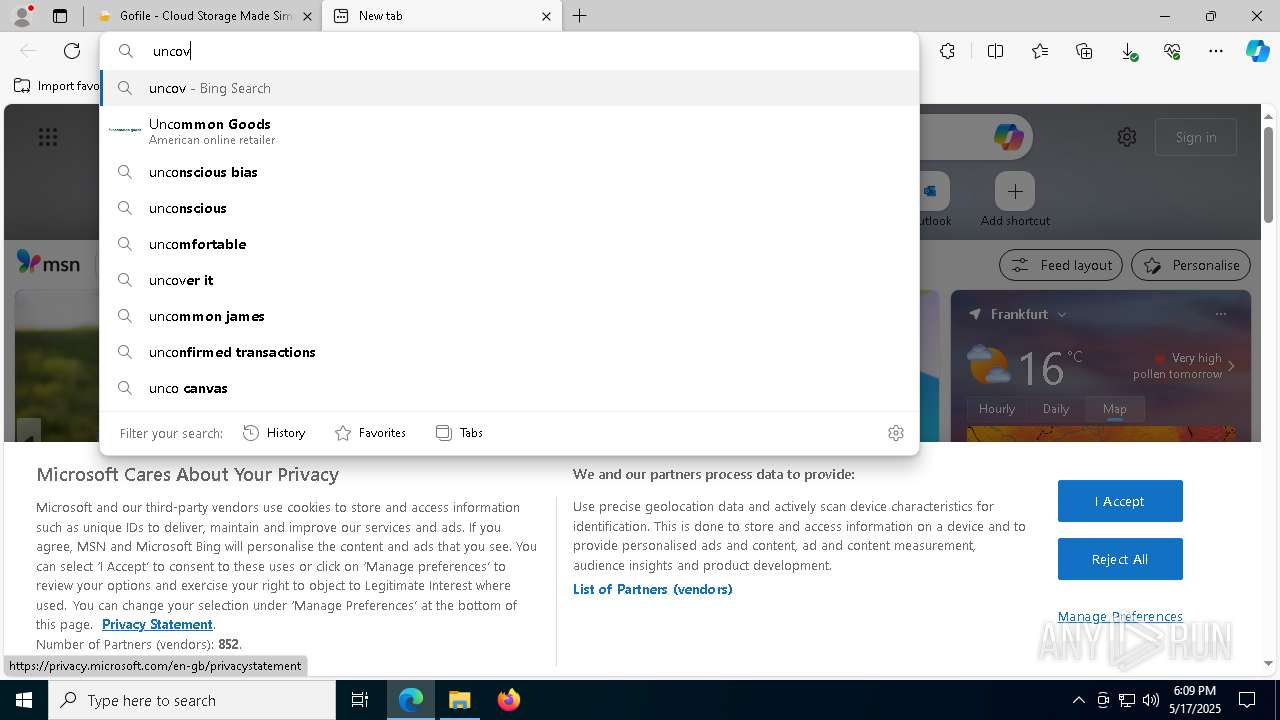
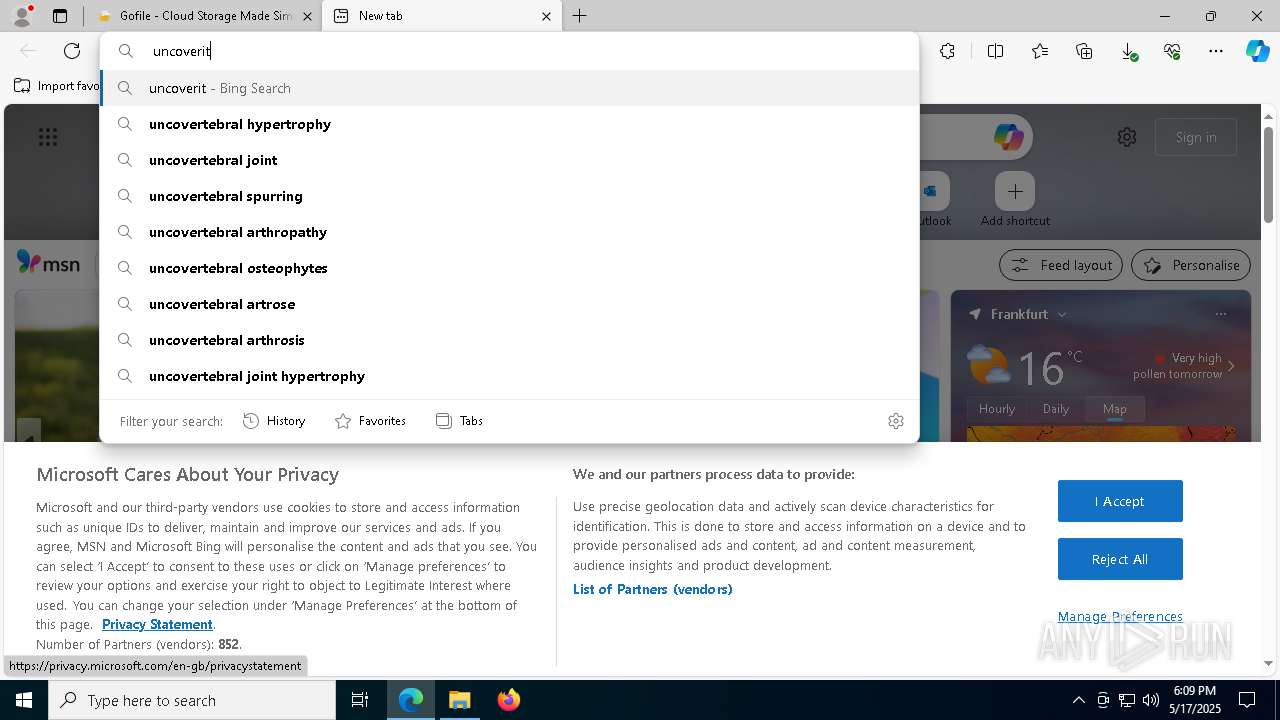
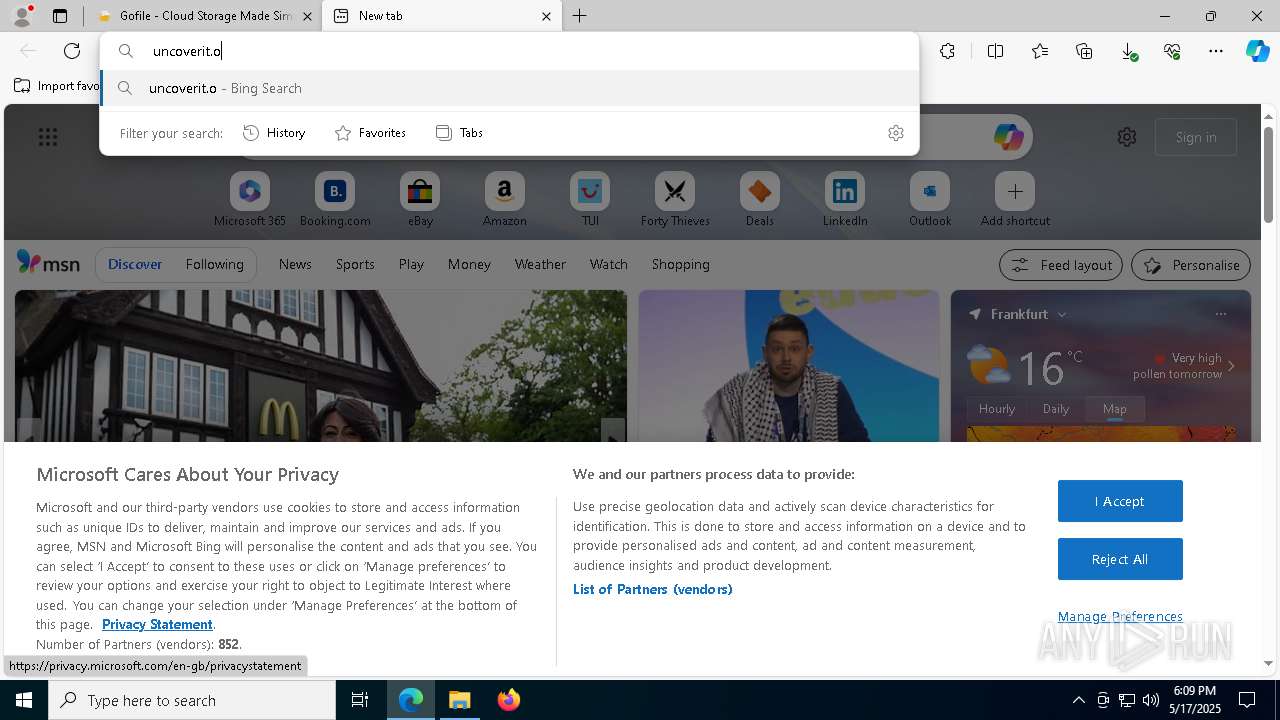
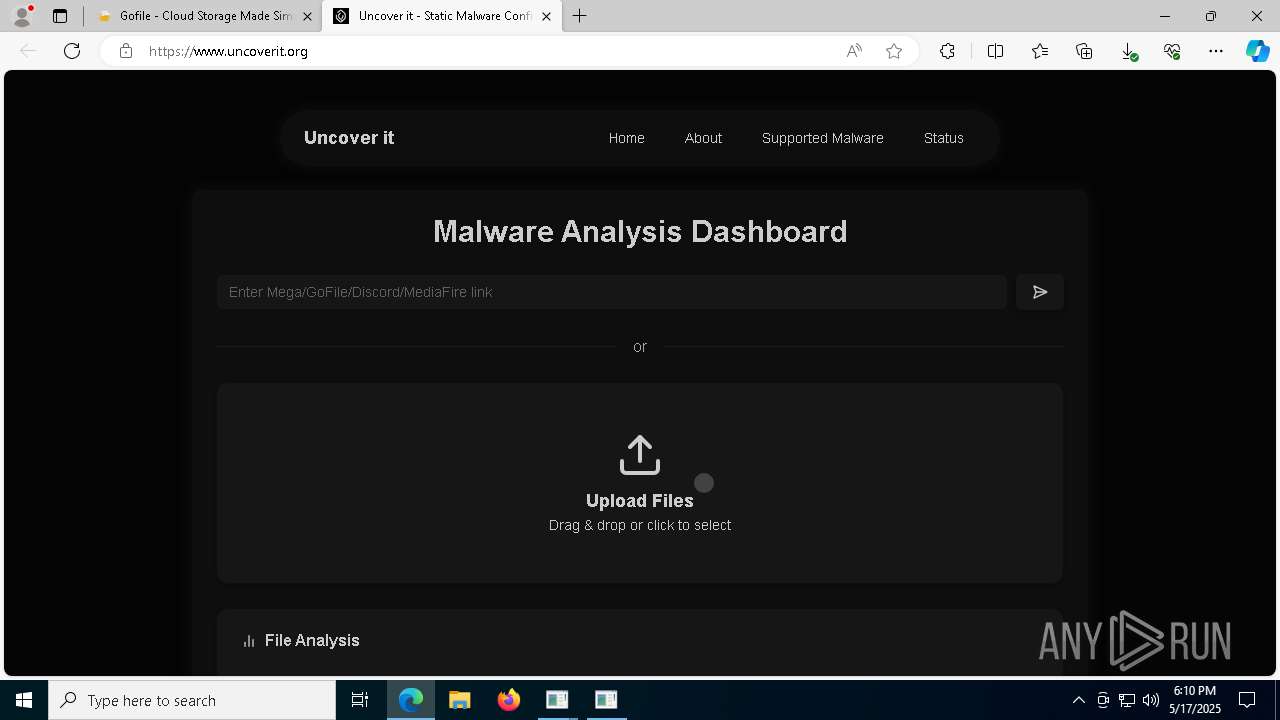
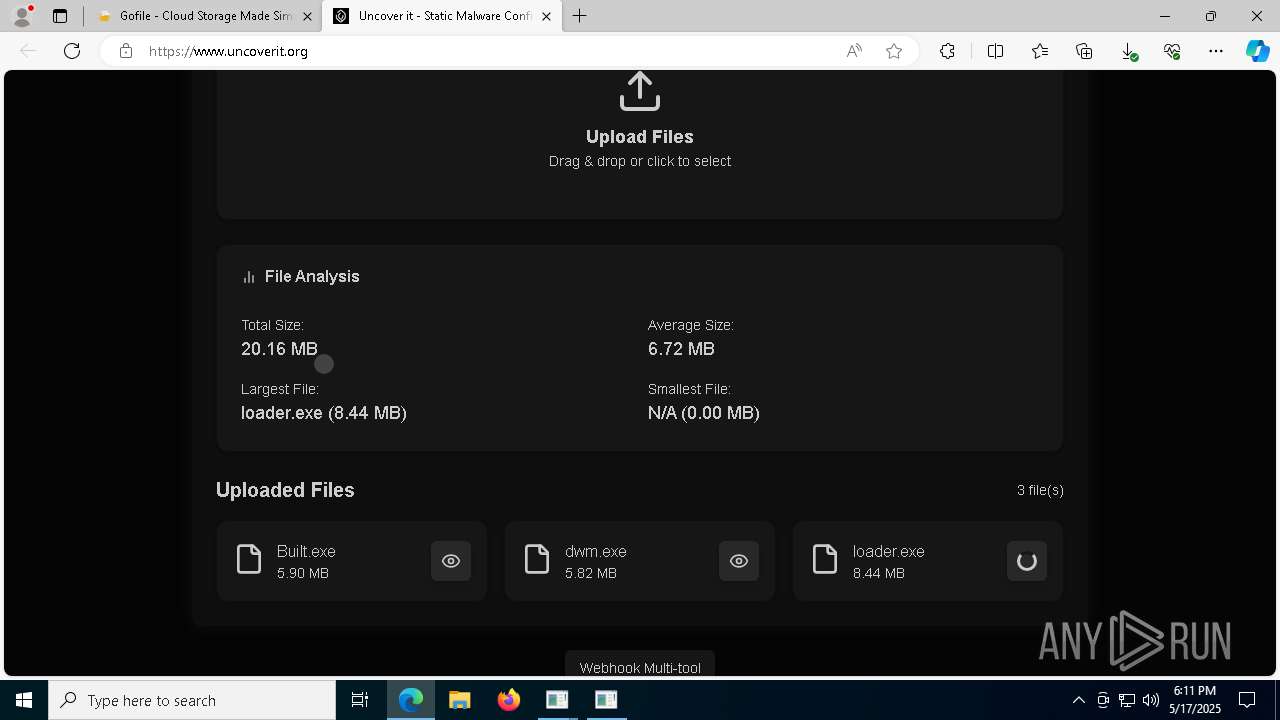
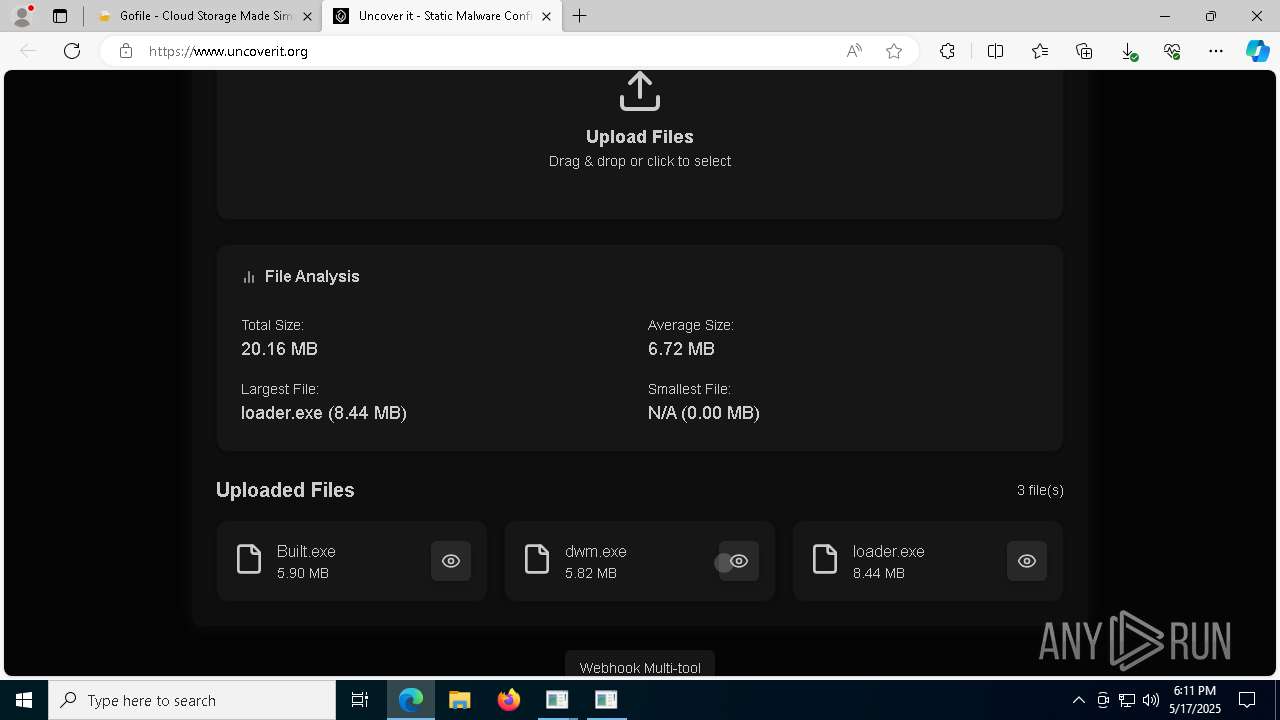
Attempting to use file storage service
- msedge.exe (PID: 7344)
The sample compiled with english language support
- main.exe (PID: 5352)
- loader.exe (PID: 5608)
- dwm.exe (PID: 4736)
- Built.exe (PID: 6584)
- loader.exe (PID: 1748)
- Built.exe (PID: 8444)
- main.exe (PID: 8328)
- main.exe (PID: 8816)
- main.exe (PID: 8368)
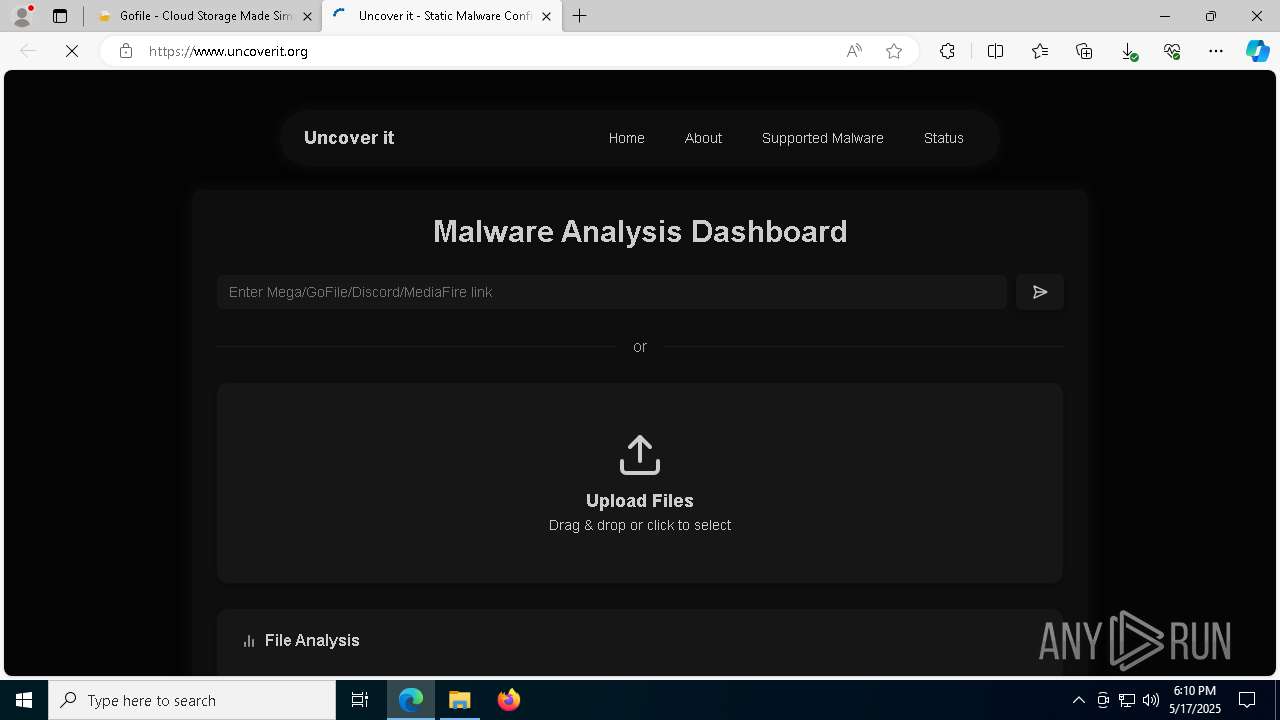
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
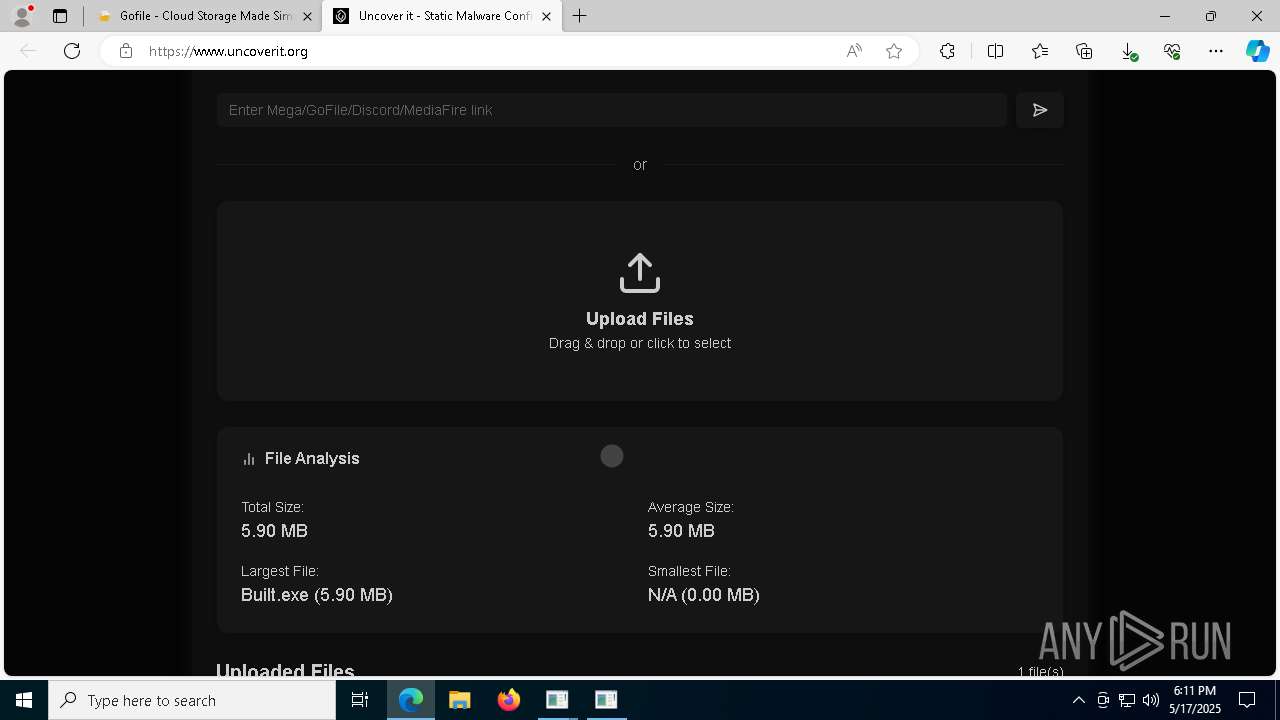
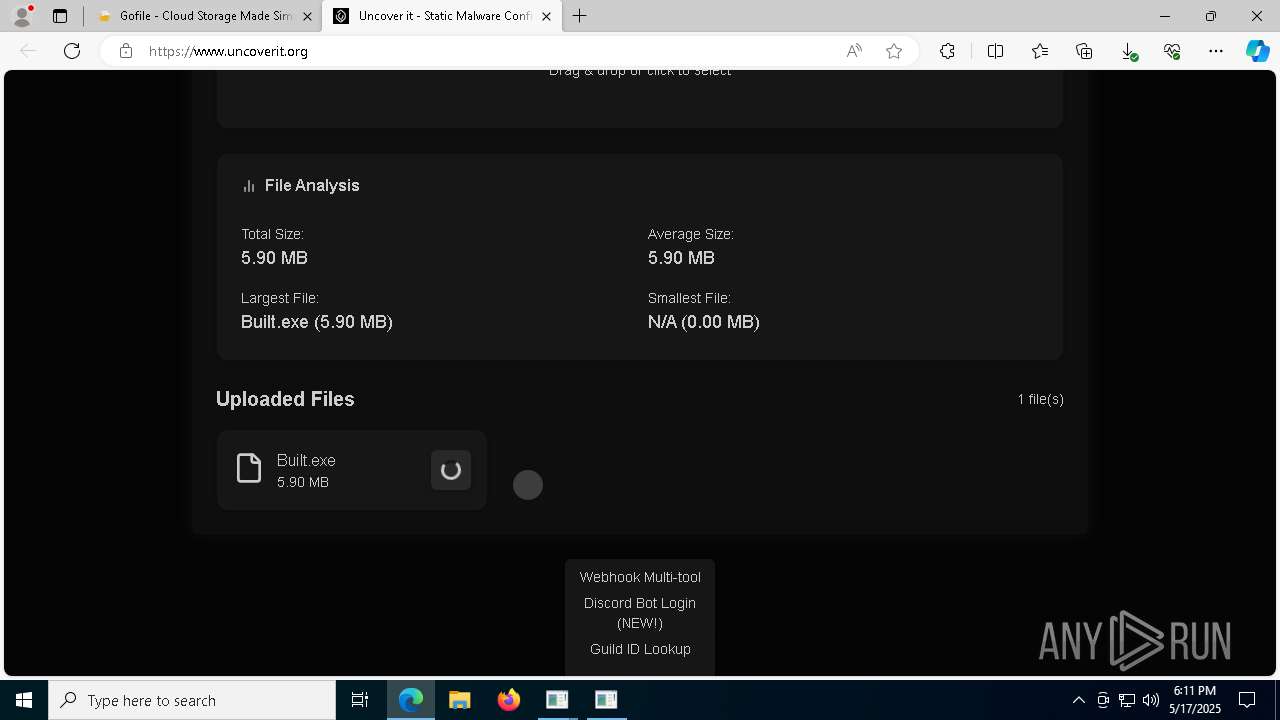
Total processes
283
Monitored processes
144
Malicious processes
21
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4344 --field-trial-handle=2284,i,4431545097335266699,5985805286455633878,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
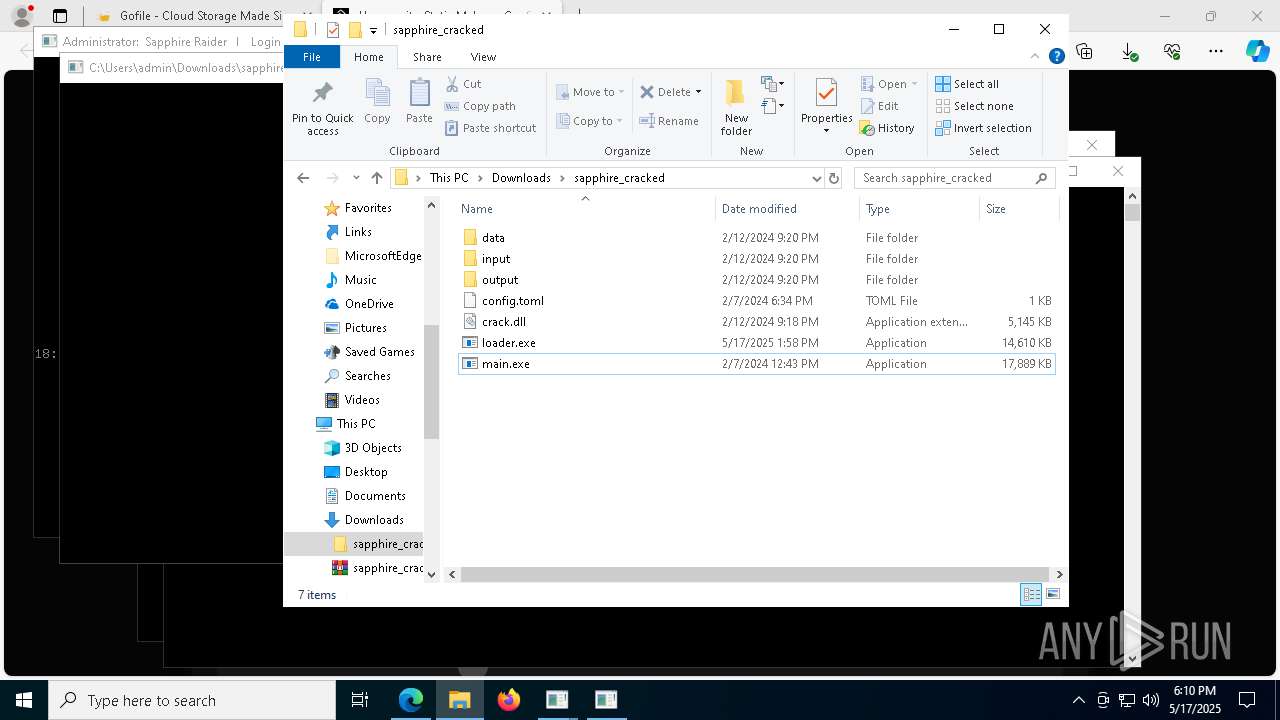
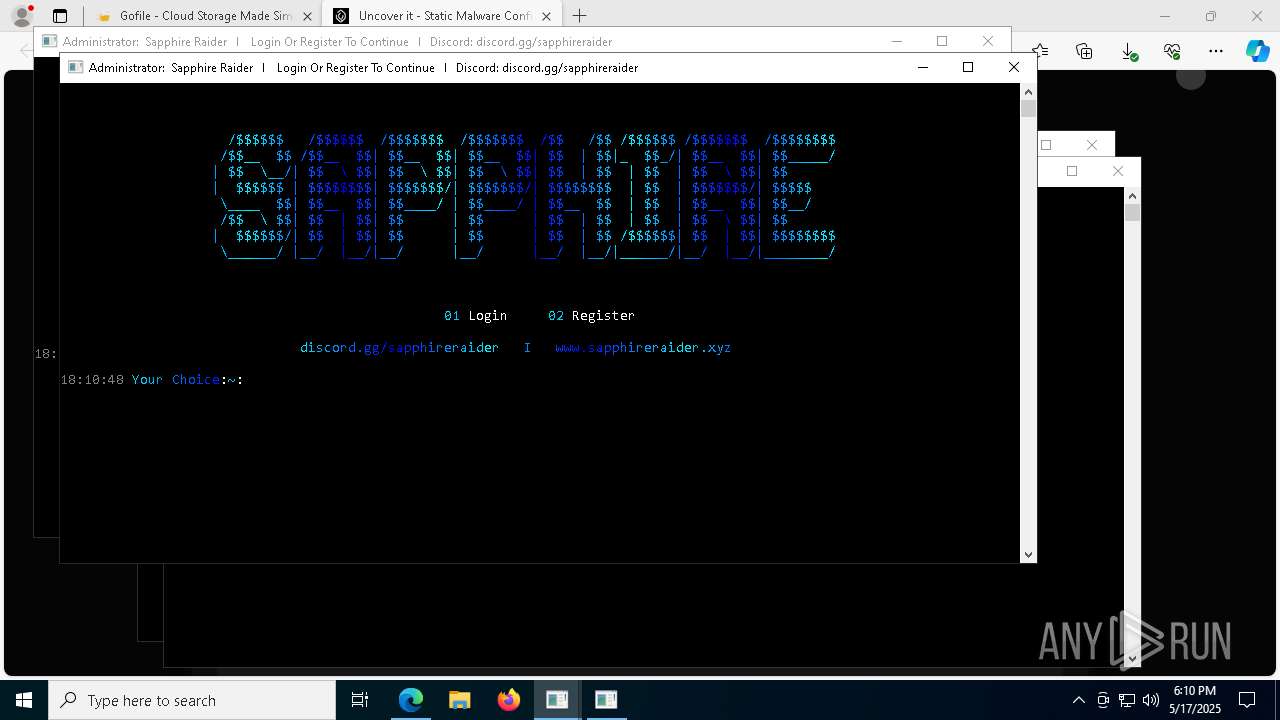
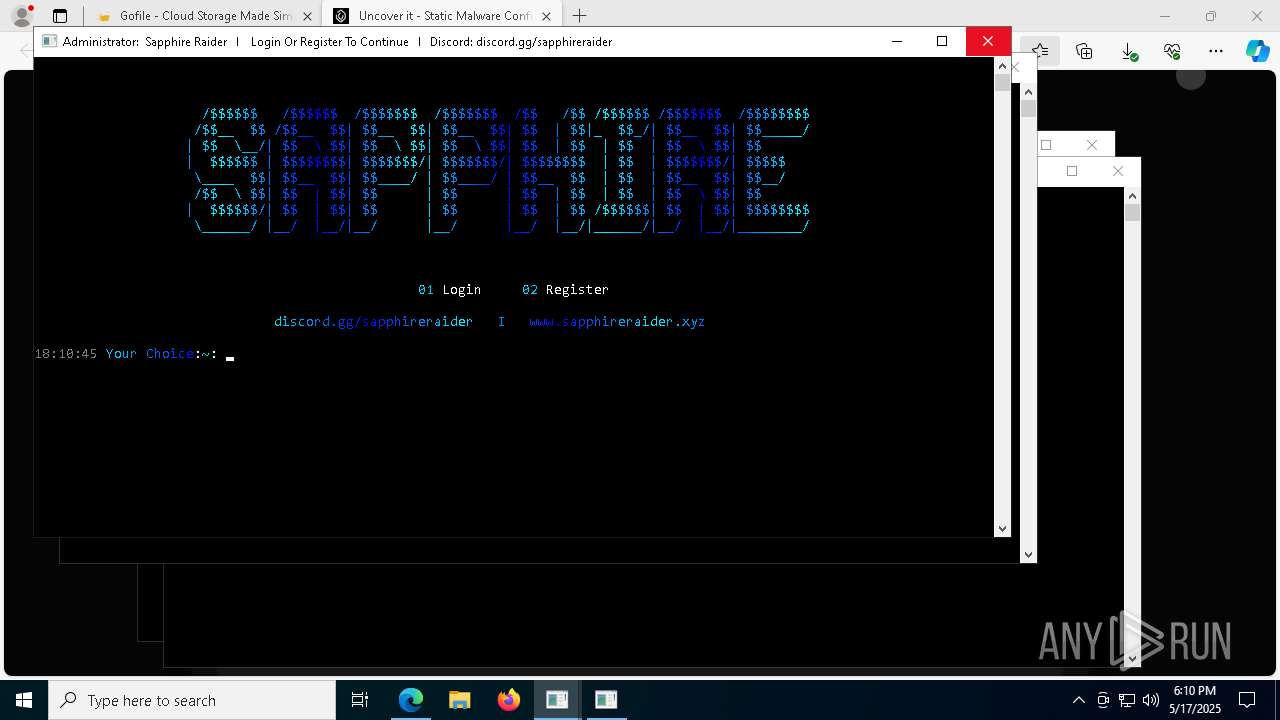
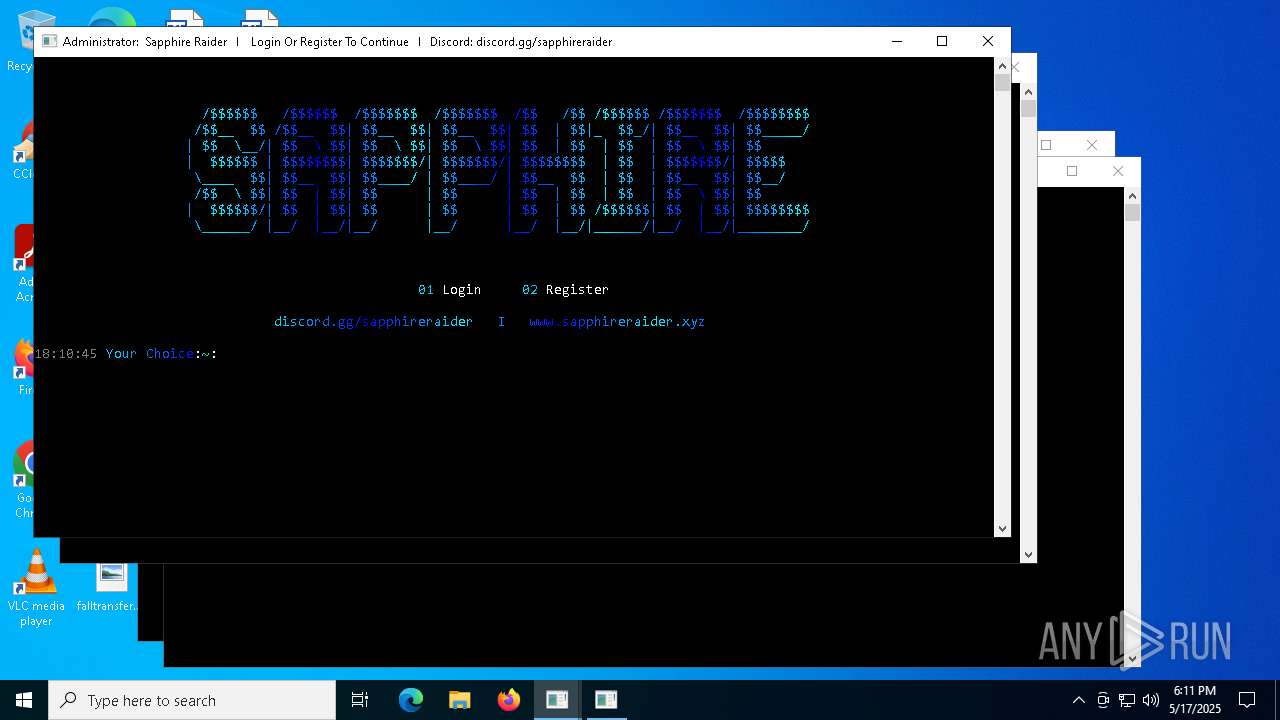
| 616 | C:\WINDOWS\system32\cmd.exe /c title Sapphire Raider I Login Or Register To Continue I Discord: discord.gg/sapphireraider | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc88765fd8,0x7ffc88765fe4,0x7ffc88765ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3844 --field-trial-handle=2308,i,5381160710220175398,2571170067880291276,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2468 --field-trial-handle=2284,i,4431545097335266699,5985805286455633878,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | mshta vbscript:Execute("CreateObject(""WScript.Shell"").Run ""taskkill /IM cmstp.exe /F"", 0, true:close") | C:\Windows\System32\mshta.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5752 --field-trial-handle=2308,i,5381160710220175398,2571170067880291276,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Local\Temp\Built.exe" | C:\Users\admin\AppData\Local\Temp\Built.exe | Built.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5284 --field-trial-handle=2284,i,4431545097335266699,5985805286455633878,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 860
Read events
55 590
Write events
245
Delete events
25
Modification events
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D1A79415EF932F00 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7D2CA115EF932F00 | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EC744305-A3C0-4B8F-8D6A-042DAA3836E1} | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {33BFF92F-DAE4-4DD9-820A-676A58006E3D} | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CB59A887-0721-4E89-8821-0ED35D3DA73C} | |||
| (PID) Process: | (4812) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4E4932D7-2100-4A9D-A472-2D8EC735B624} | |||
Executable files
310
Suspicious files
717
Text files
145
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c8a1.TMP | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c8a1.TMP | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 4812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
158
DNS requests
160
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1272 | Built.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6816 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/41ffe24d-c581-450f-a817-829eec3cba9a?P1=1747713198&P2=404&P3=2&P4=m8fsZ5KOyJ7r5o3YQxh46CXEyo1o65MkeZk9YfusKoBYneaRjC8ZtLofKi6b3e63%2bZ7SBdW9oIdM3LtINp9qDg%3d%3d | unknown | — | — | whitelisted |
8568 | Built.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/41ffe24d-c581-450f-a817-829eec3cba9a?P1=1747713198&P2=404&P3=2&P4=m8fsZ5KOyJ7r5o3YQxh46CXEyo1o65MkeZk9YfusKoBYneaRjC8ZtLofKi6b3e63%2bZ7SBdW9oIdM3LtINp9qDg%3d%3d | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/41ffe24d-c581-450f-a817-829eec3cba9a?P1=1747713198&P2=404&P3=2&P4=m8fsZ5KOyJ7r5o3YQxh46CXEyo1o65MkeZk9YfusKoBYneaRjC8ZtLofKi6b3e63%2bZ7SBdW9oIdM3LtINp9qDg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4812 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
7344 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |