| URL: | http://www.mcewenmyerspark.com |
| Full analysis: | https://app.any.run/tasks/a6f018a8-d5ef-4618-9a87-2ada217acad1 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 03:11:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 92E11F7AC497A2C121271F1805F2D8A3 |
| SHA1: | 49D790AC35B84598A0DA27394F8B8FEE5FBEA792 |
| SHA256: | C12744D75BA344DD080E2B78600EE92A34B91328F416C3FC2A8CFC7F8B5AF864 |
| SSDEEP: | 3:N1KJS4EzNyb:Cc4Ezkb |
MALICIOUS
Creates a writable file the system directory
- printfilterpipelinesvc.exe (PID: 3928)
SUSPICIOUS
Checks Windows Trust Settings
- ONENOTE.EXE (PID: 1872)
Reads settings of System Certificates
- ONENOTE.EXE (PID: 1872)
Reads security settings of Internet Explorer
- ONENOTE.EXE (PID: 1872)
INFO
Reads the computer name
- ONENOTE.EXE (PID: 1872)
Application launched itself
- iexplore.exe (PID: 2304)
Creates files or folders in the user directory
- printfilterpipelinesvc.exe (PID: 3928)
- ONENOTE.EXE (PID: 1872)
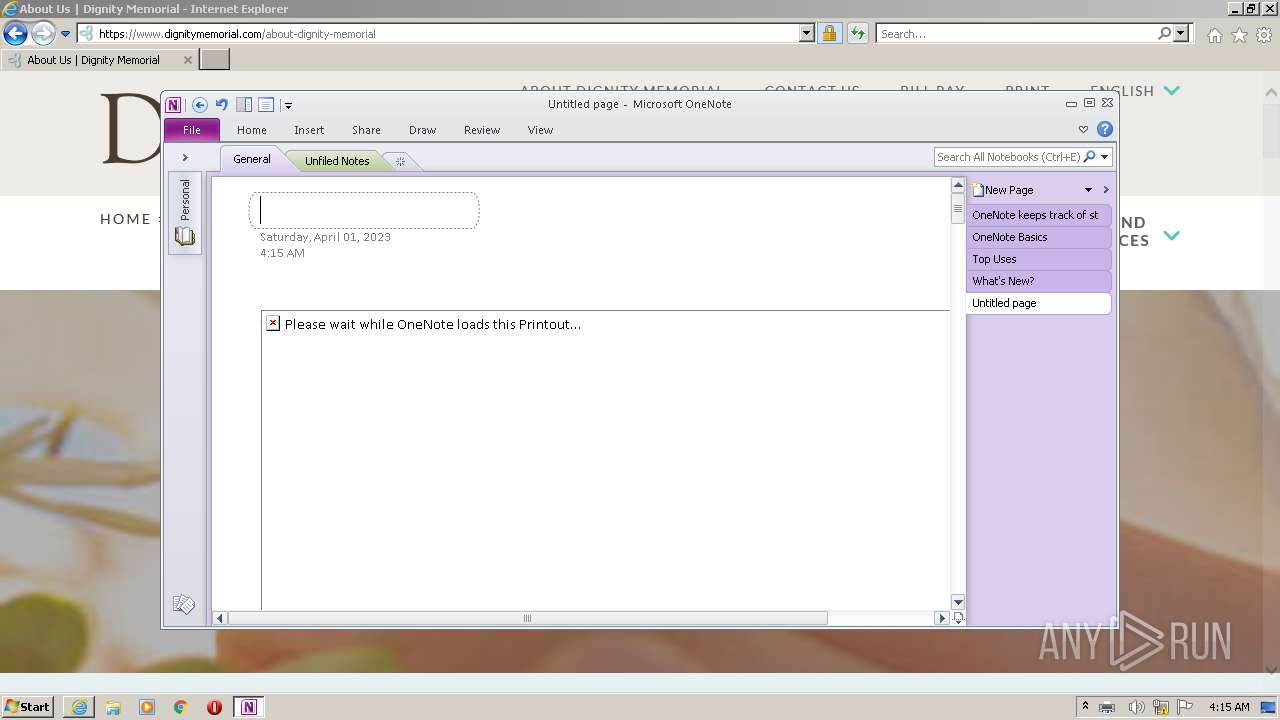
Create files in a temporary directory
- ONENOTE.EXE (PID: 1872)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 3052)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 1872)
The process checks LSA protection
- printfilterpipelinesvc.exe (PID: 3928)
- ONENOTE.EXE (PID: 1872)
Process checks computer location settings
- ONENOTE.EXE (PID: 1872)
Reads the machine GUID from the registry
- ONENOTE.EXE (PID: 1872)
Checks supported languages
- ONENOTE.EXE (PID: 1872)
- ONENOTEM.EXE (PID: 3580)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
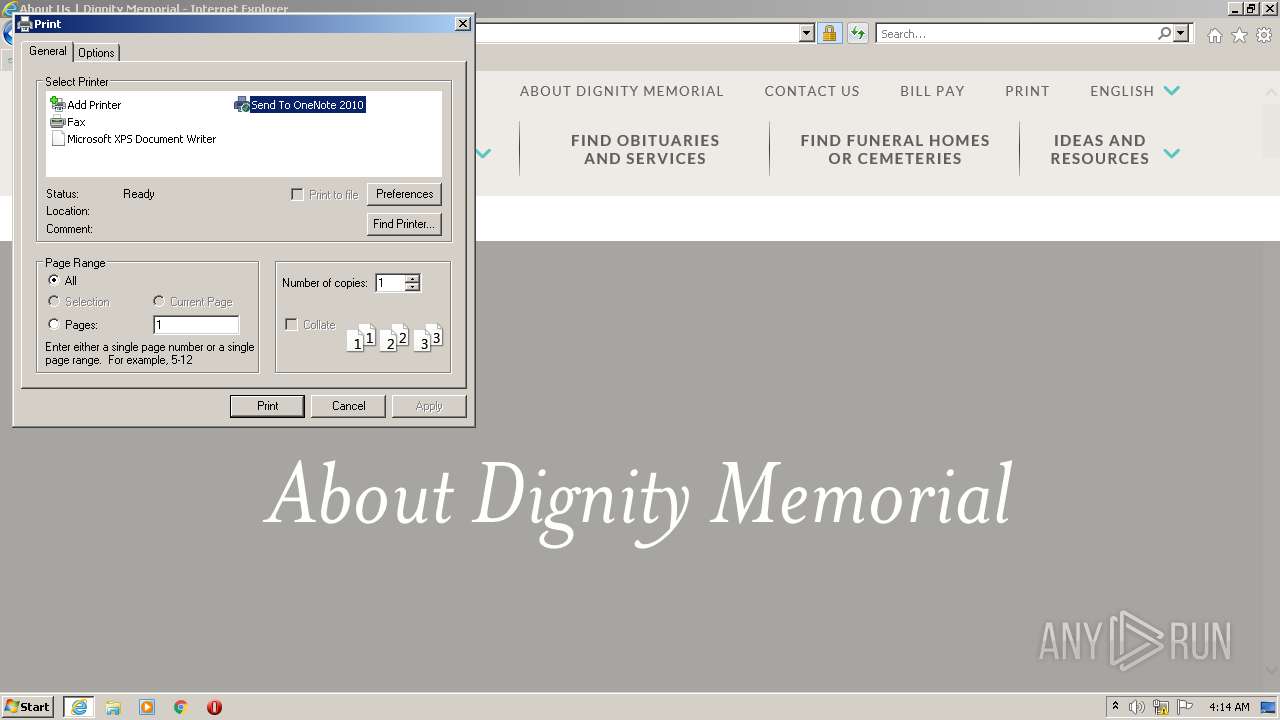
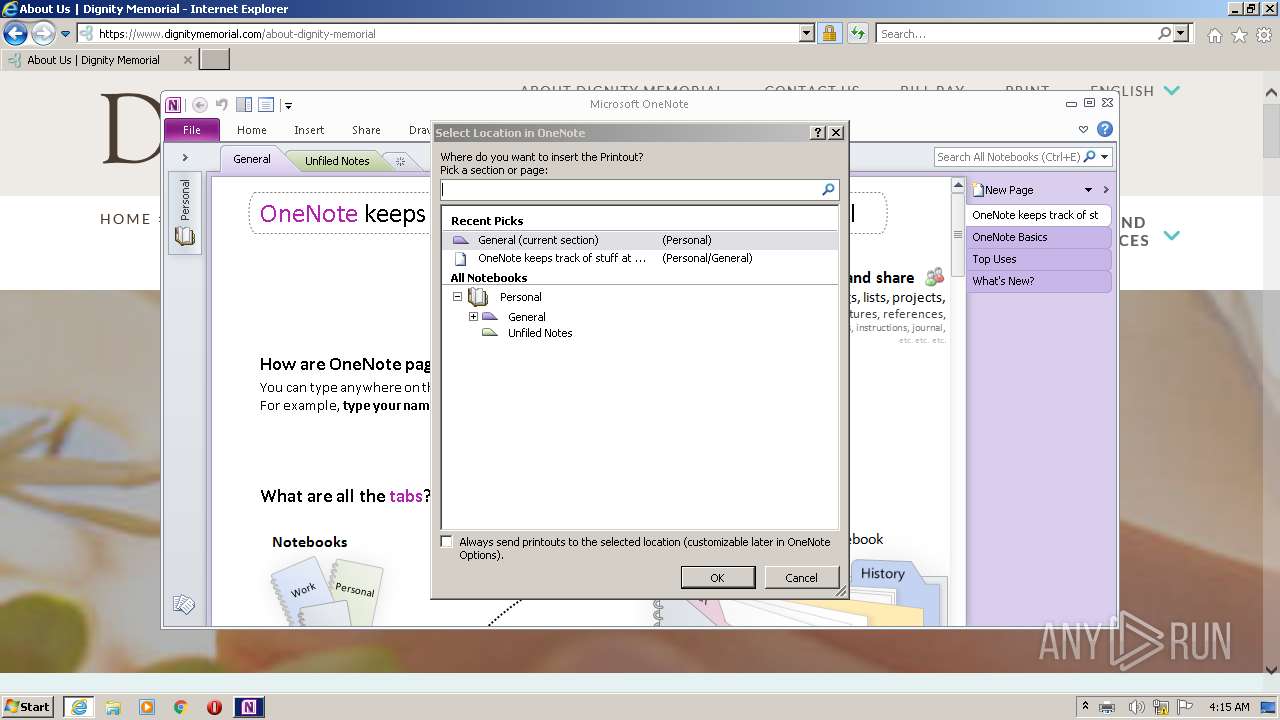
| 1872 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{AF421566-C931-4D1E-832A-C319126D8AA2}.xps" 133247925152120000 | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | printfilterpipelinesvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
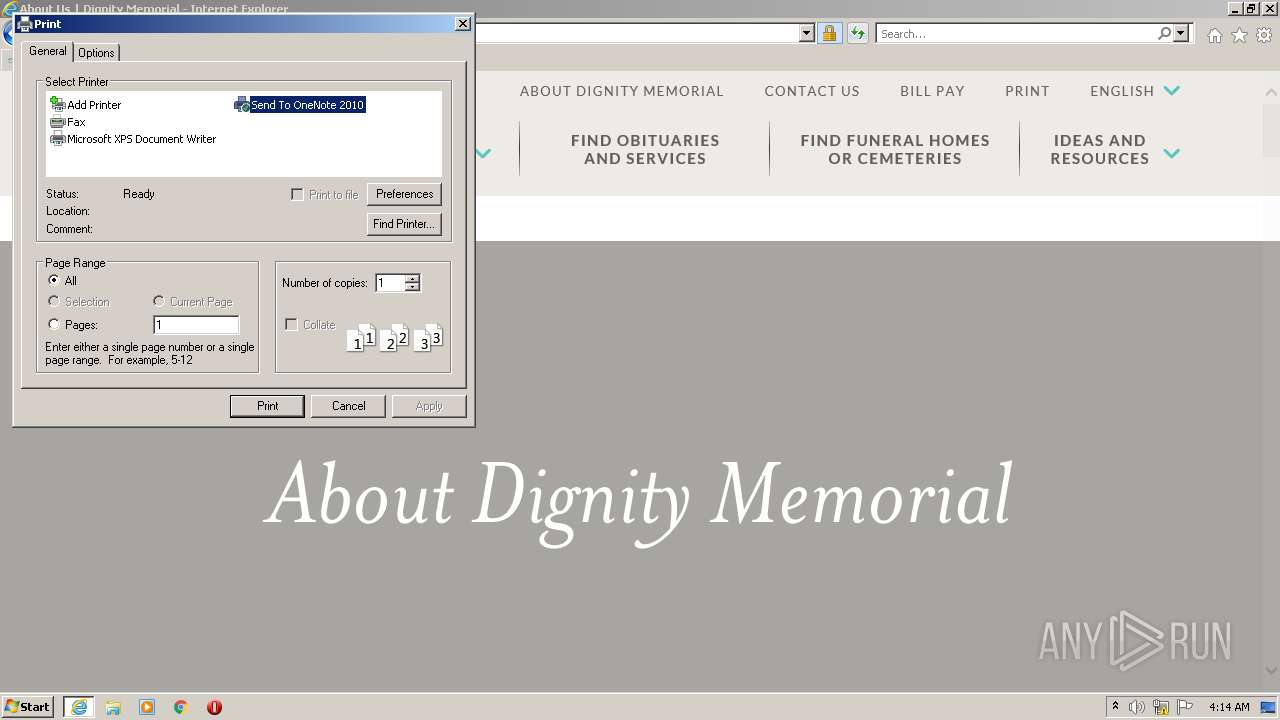
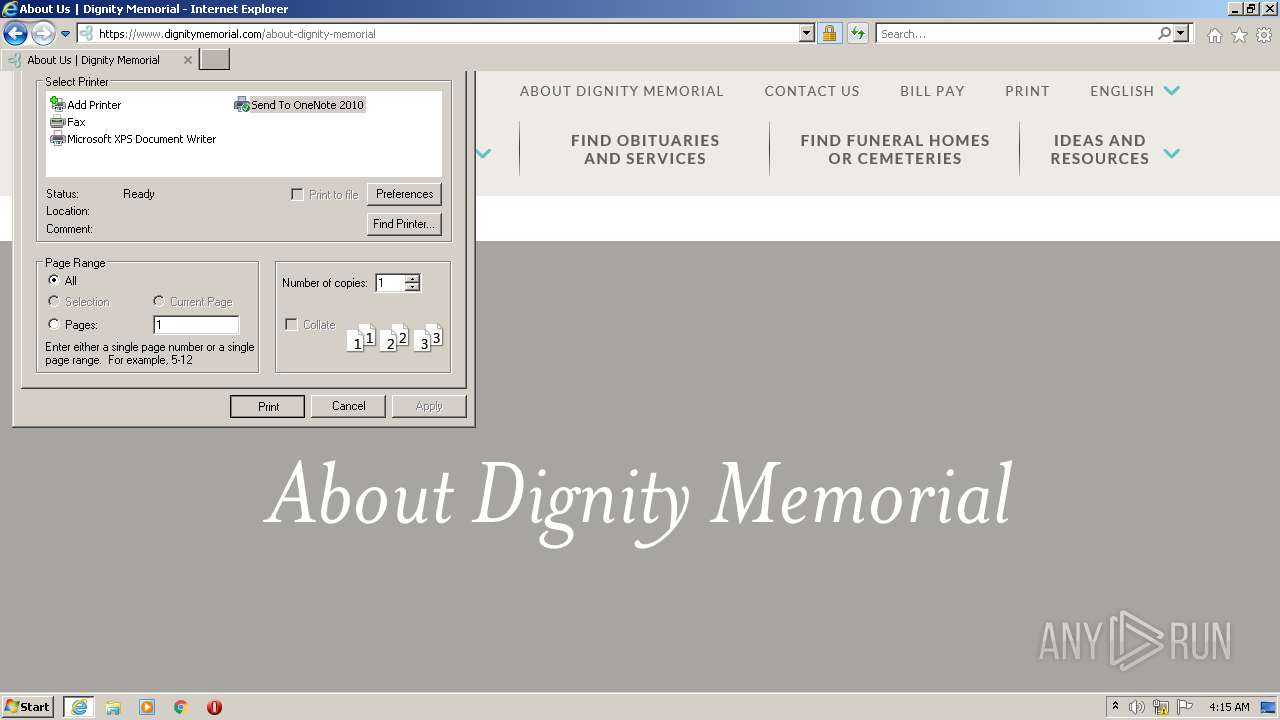
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.mcewenmyerspark.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2568 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2304 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3580 | /tsr | C:\Program Files\Microsoft Office\Office14\ONENOTEM.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Quick Launcher Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 3928 | C:\Windows\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\System32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Exit code: 0 Version: 6.1.7601.24537 (win7sp1_ldr_escrow.191114-1547) Modules
| |||||||||||||||
Total events
97 182
Read events
95 884
Write events
1 276
Delete events
22
Modification events
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
162
Text files
1 678
Unknown types
116
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\5HIZTOTR.htm | html | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_7600C8987BB28435A3D9B0CDCE9C55C6 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\572BF21E454637C9F000BE1AF9B1E1A9 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\572BF21E454637C9F000BE1AF9B1E1A9 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S7ELSBKV.txt | text | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\327FF3746805435DEF100D87972B74F9_97848BC61D68BAC7829D8B4492969C42 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\require.min[1].js | text | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\lazy-initializer.min[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
198
DNS requests
77
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3052 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.netsolssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS8pCdcdf7%2FBh5RMVRxuconLI9udwQUIDPNt2H2pYZP3MnXc2q8ClFlmOwCEHjrh4d1UasMHUtZJL8Lasw%3D | US | der | 471 b | whitelisted |
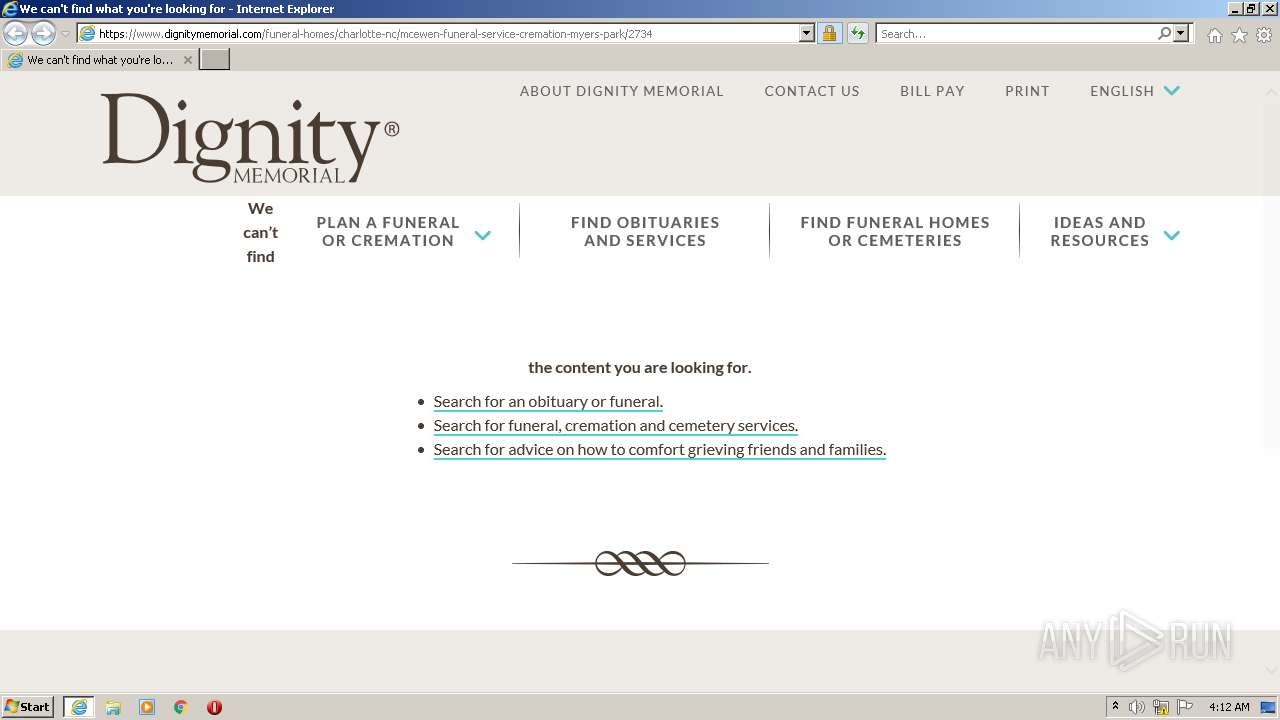
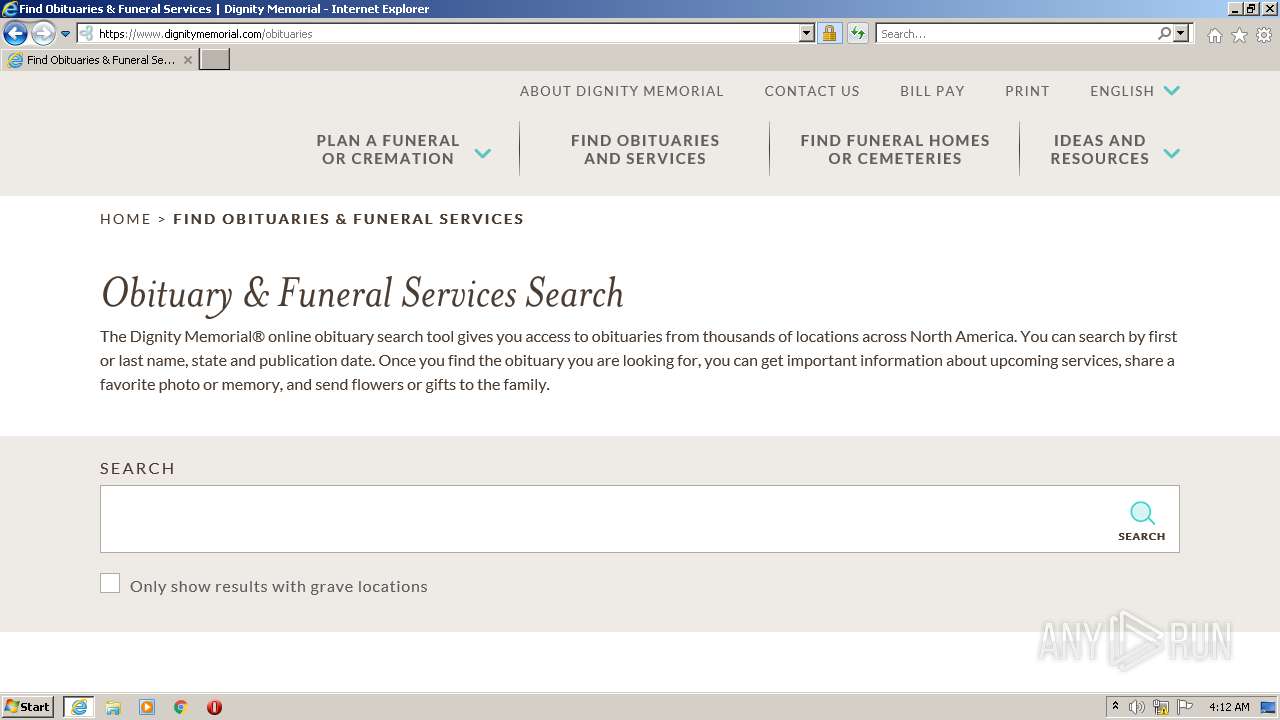
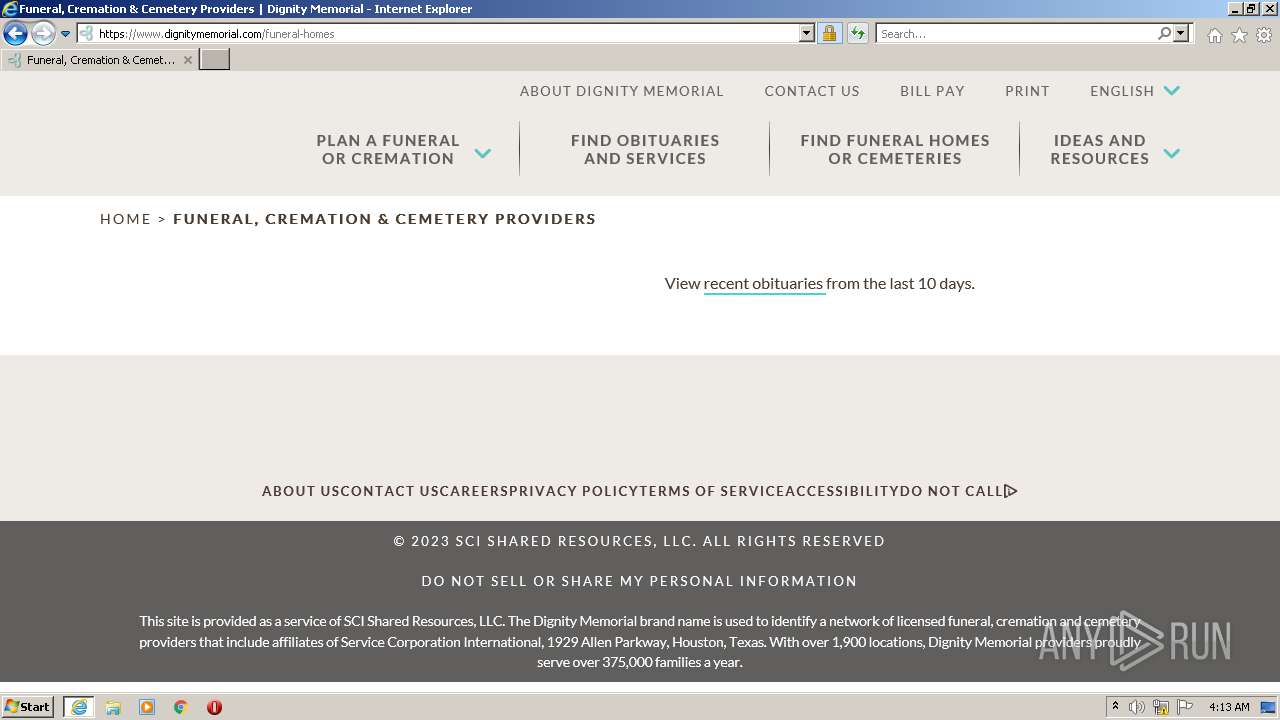
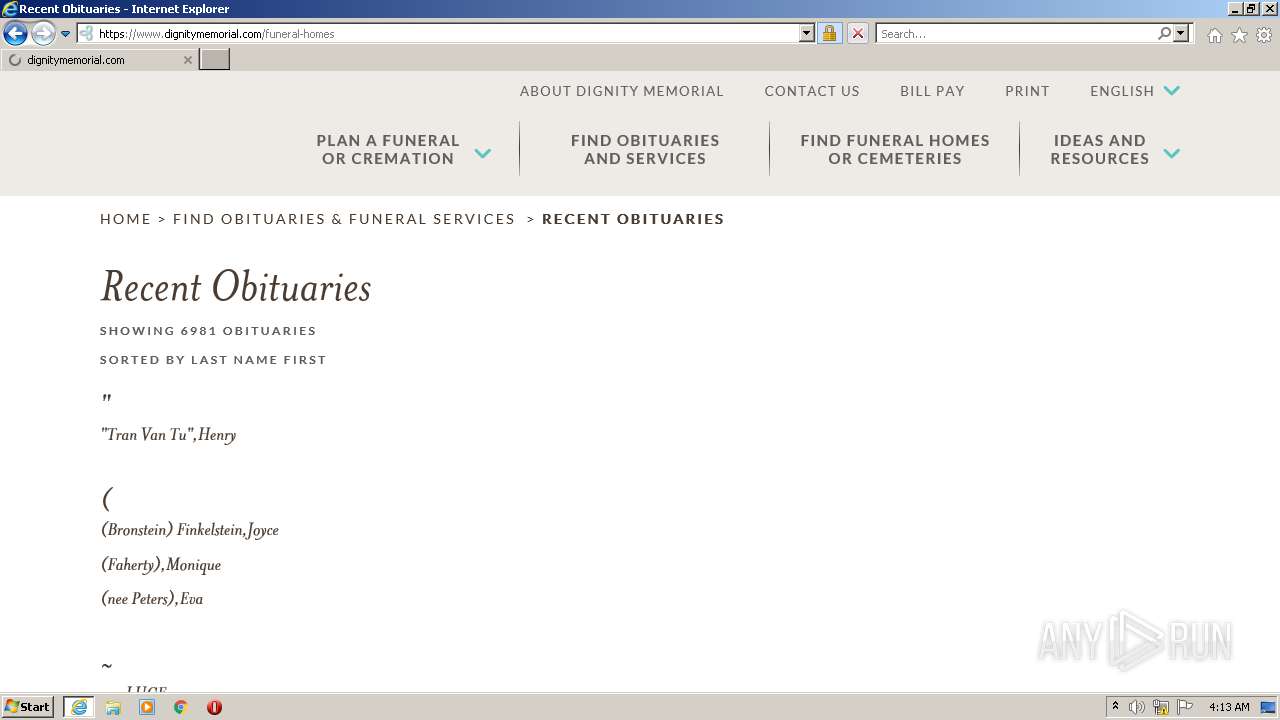
3052 | iexplore.exe | GET | 301 | 38.107.206.56:80 | http://www.mcewenmyerspark.com/ | US | html | 230 b | unknown |
3052 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FB2zZ7cy1JAocIdUzcD8Q | US | der | 472 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3052 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQDD3t92z9eGvqGvi%2B%2FvpN04 | US | der | 2.18 Kb | whitelisted |
3052 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHwqDCE%2FxlVTRckfGR%2B4Tvo%3D | US | der | 1.40 Kb | whitelisted |
3052 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/s/gts1d4/6iosam43dWE/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQC%2F9OLg5Ee65gmsrQ1uCxMm | US | der | 472 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3052 | iexplore.exe | 38.107.206.56:443 | www.dignitymemorial.com | SCI-ASN | US | unknown |
3052 | iexplore.exe | 178.79.242.11:80 | ctldl.windowsupdate.com | LLNW | DE | suspicious |
3052 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
3052 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
2304 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3052 | iexplore.exe | 151.101.1.131:443 | 8298c6bc3c0e43bf8ed959f185e3e2a0.js.ubembed.com | FASTLY | US | suspicious |
— | — | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
3052 | iexplore.exe | 152.199.21.175:443 | cdn.dignitymemorial.com | EDGECAST | DE | whitelisted |
3052 | iexplore.exe | 38.107.206.56:80 | www.dignitymemorial.com | SCI-ASN | US | unknown |
3052 | iexplore.exe | 2.19.33.139:443 | cdn-4.convertexperiments.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dignitymemorial.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.netsolssl.com |
| whitelisted |
www.googleoptimize.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ONENOTE.EXE |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ONENOTE.EXE |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ONENOTE.EXE |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ONENOTE.EXE |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ONENOTE.EXE |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ONENOTE.EXE |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ONENOTE.EXE |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ONENOTE.EXE |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
ONENOTE.EXE |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
ONENOTE.EXE |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|