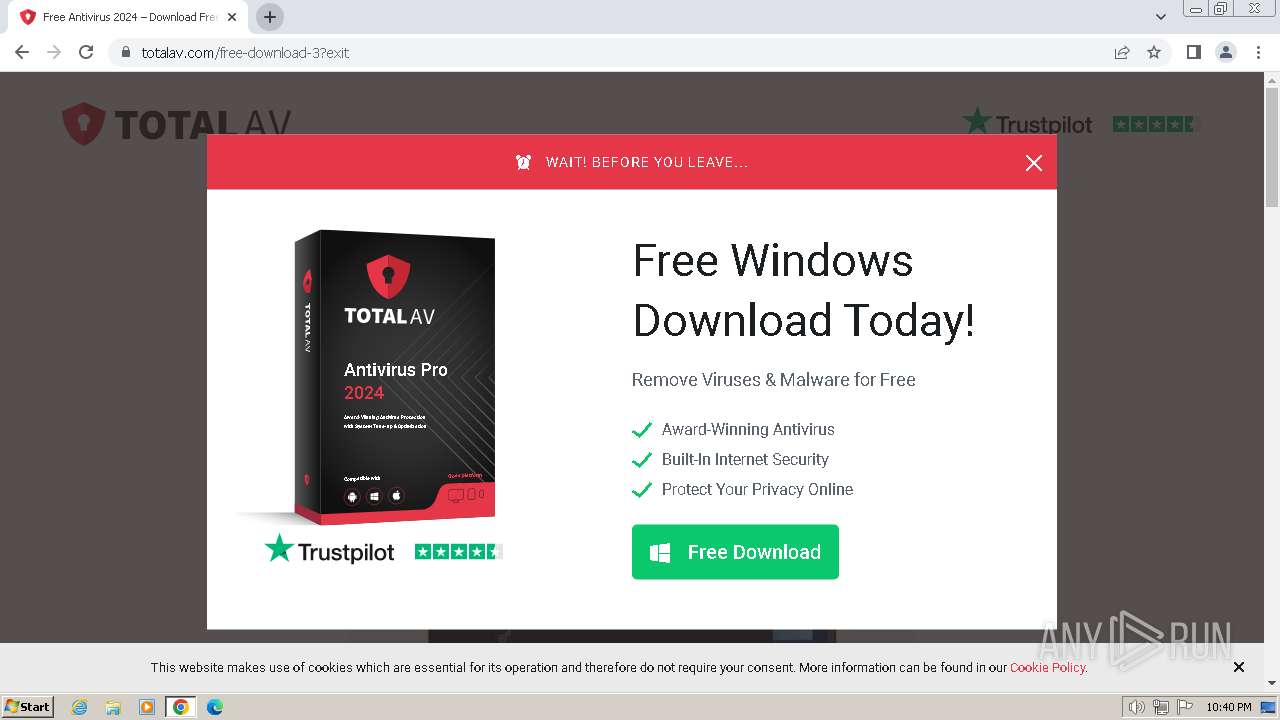
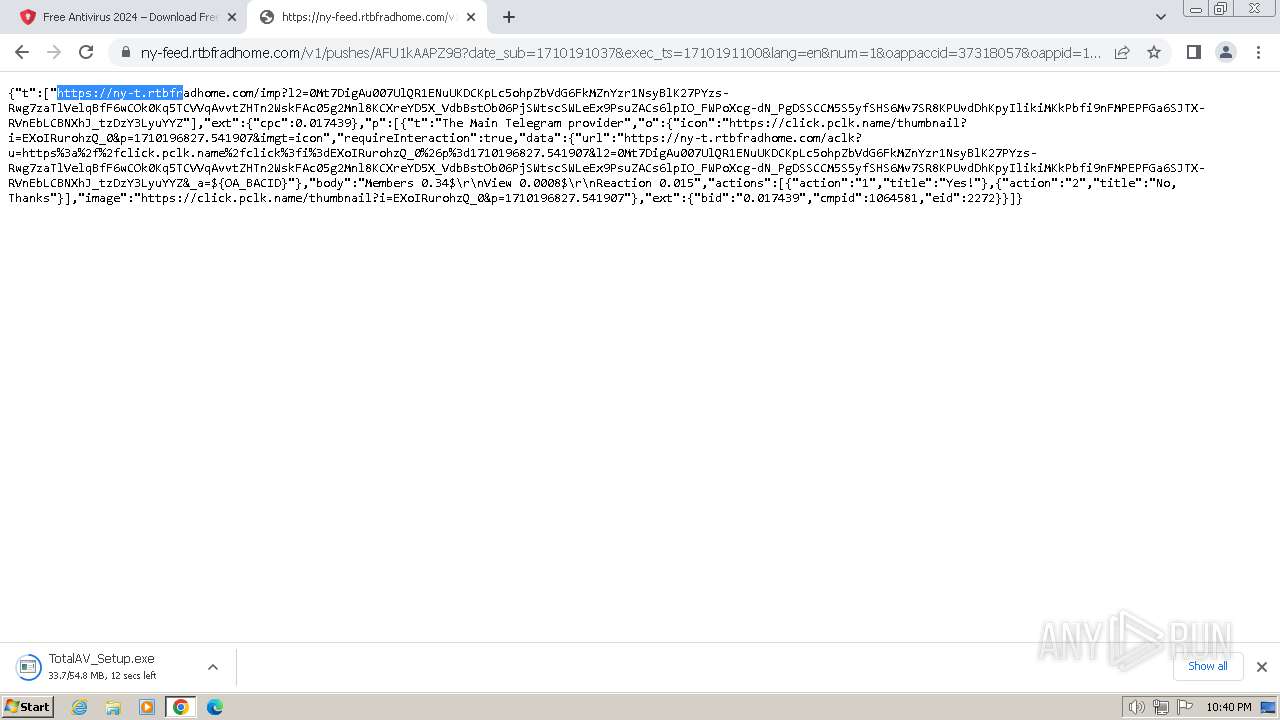
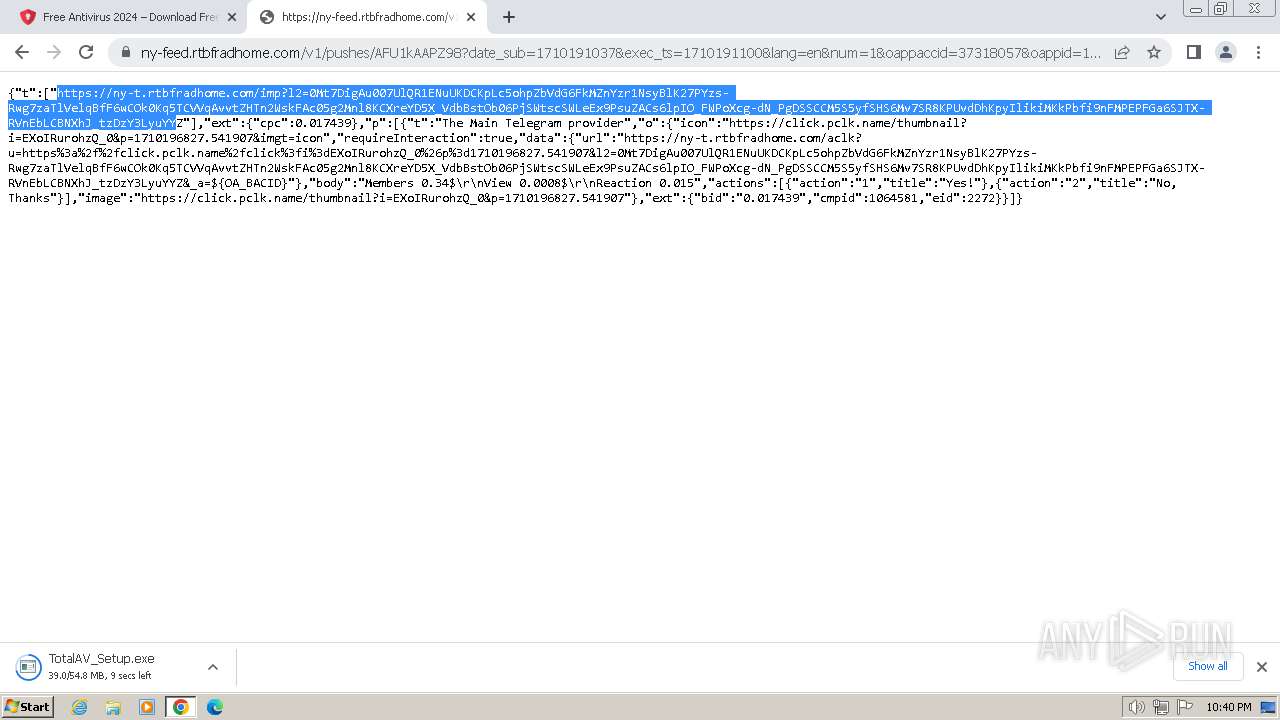
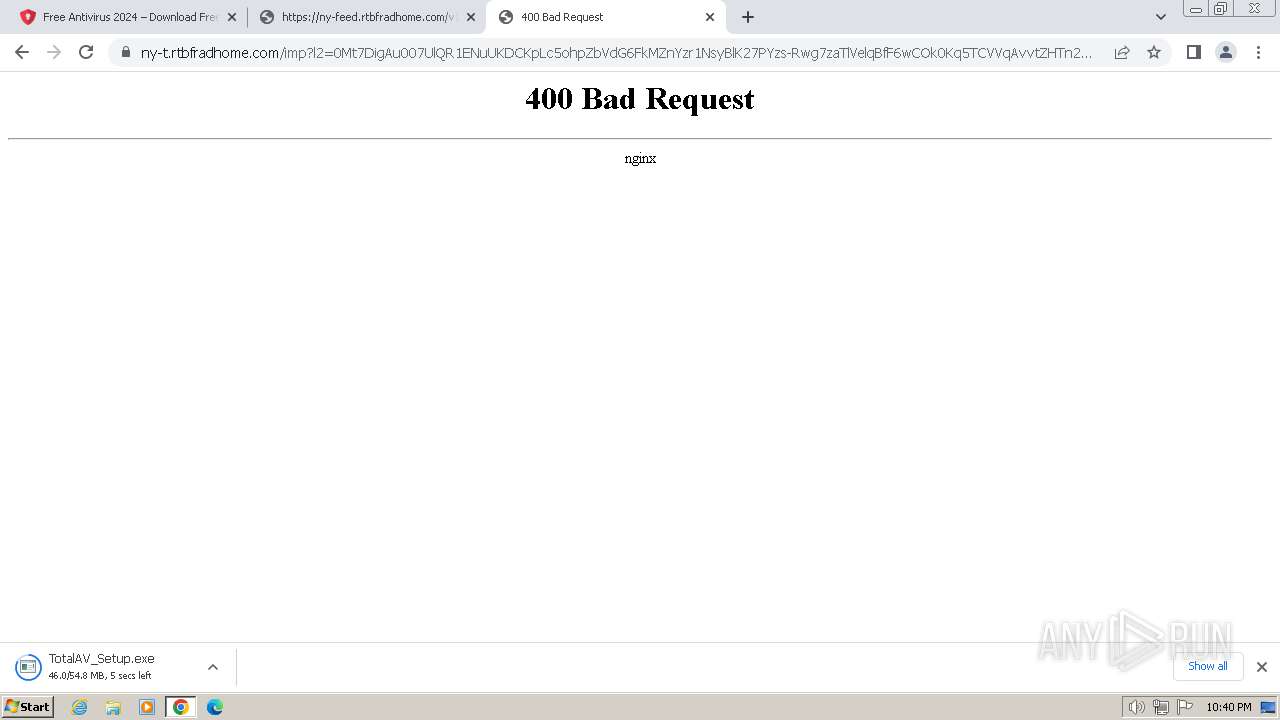
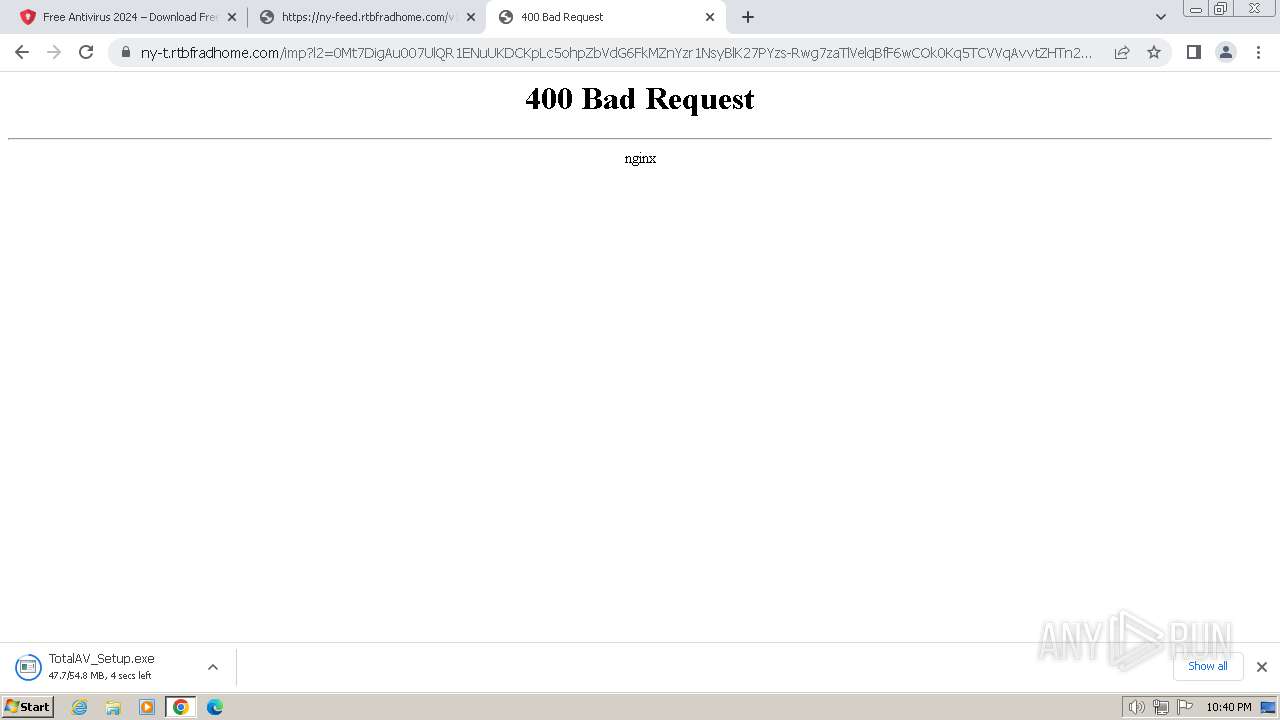
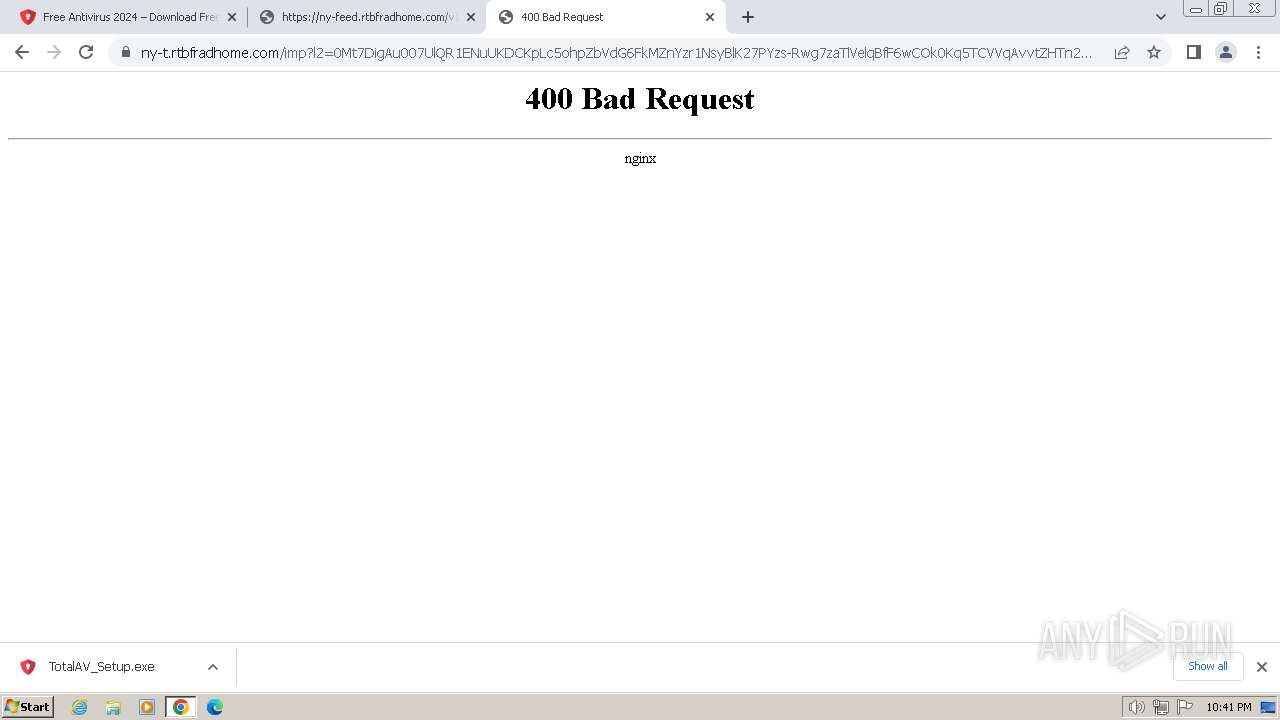
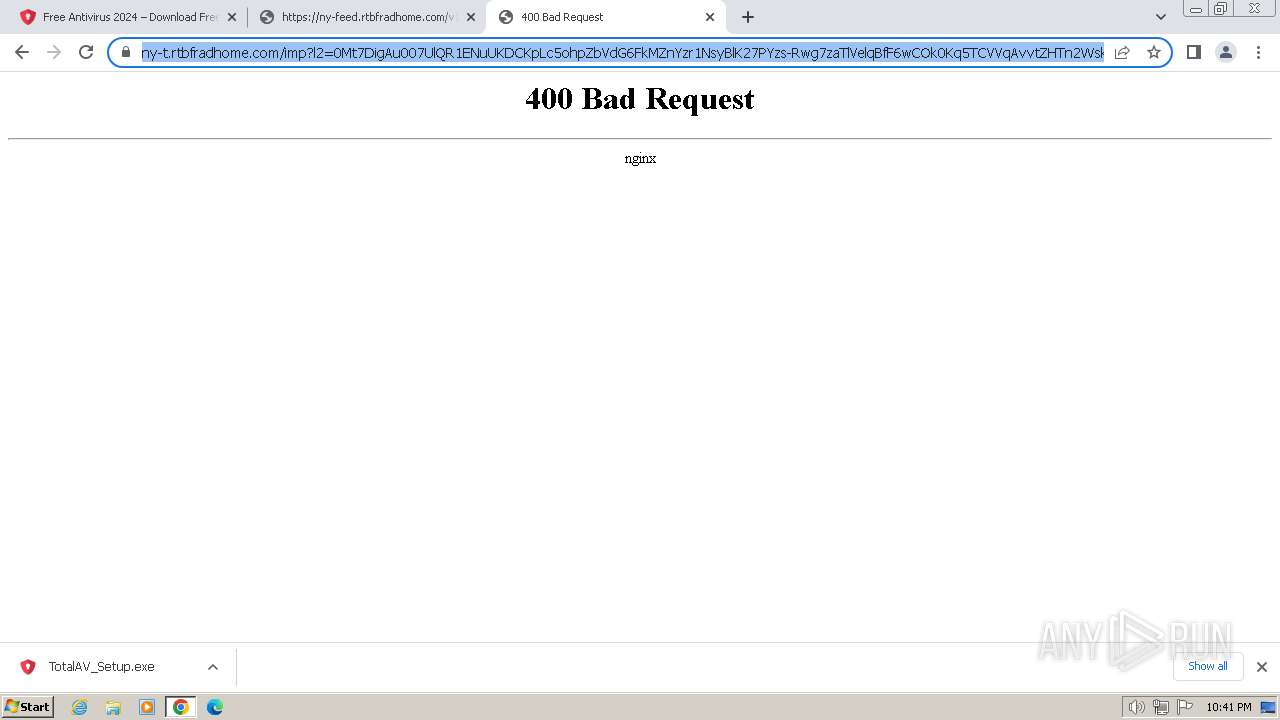
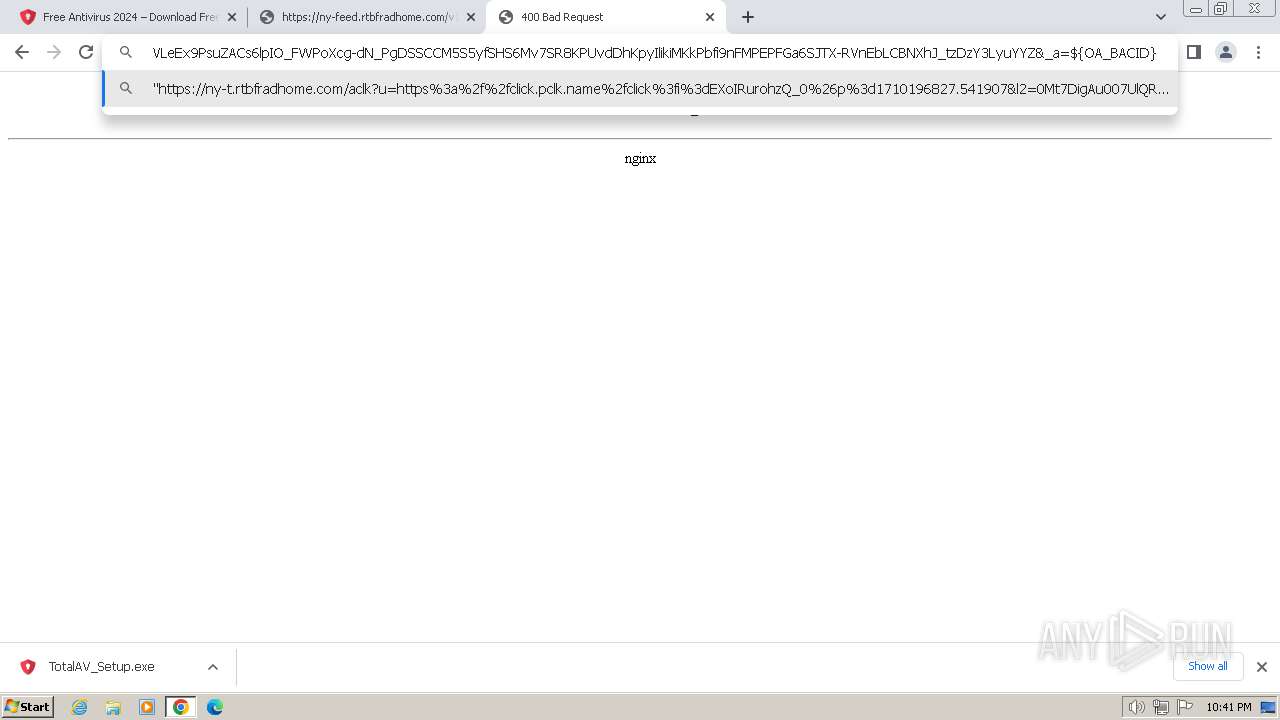
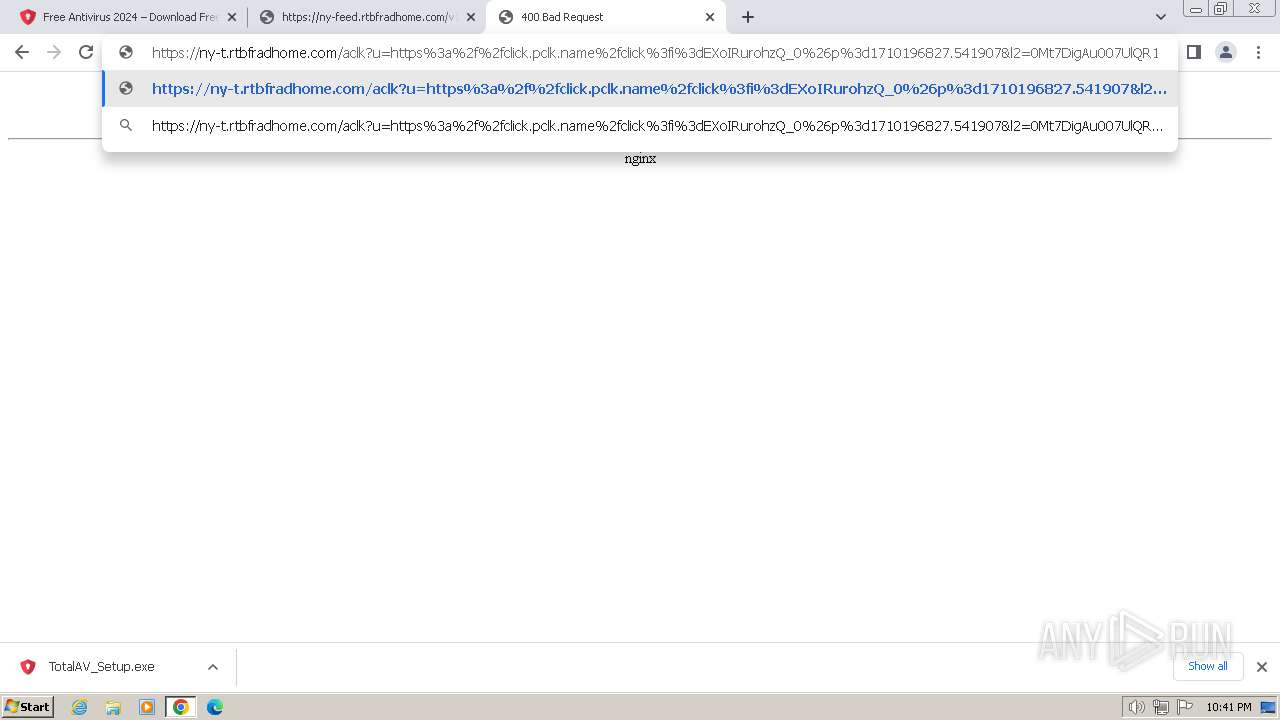
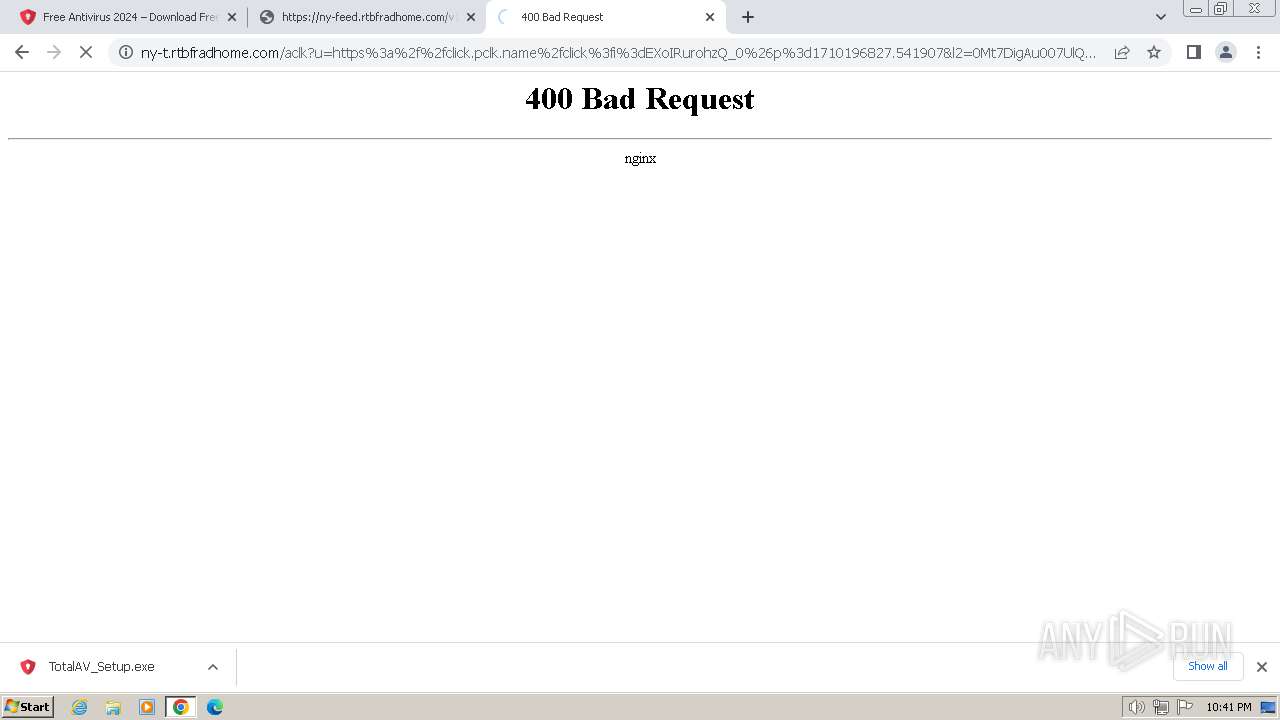
| URL: | https://t.ocmhood.com/v2/activity |
| Full analysis: | https://app.any.run/tasks/29c23e9d-9a2e-49ad-a981-6b3759eed0c2 |
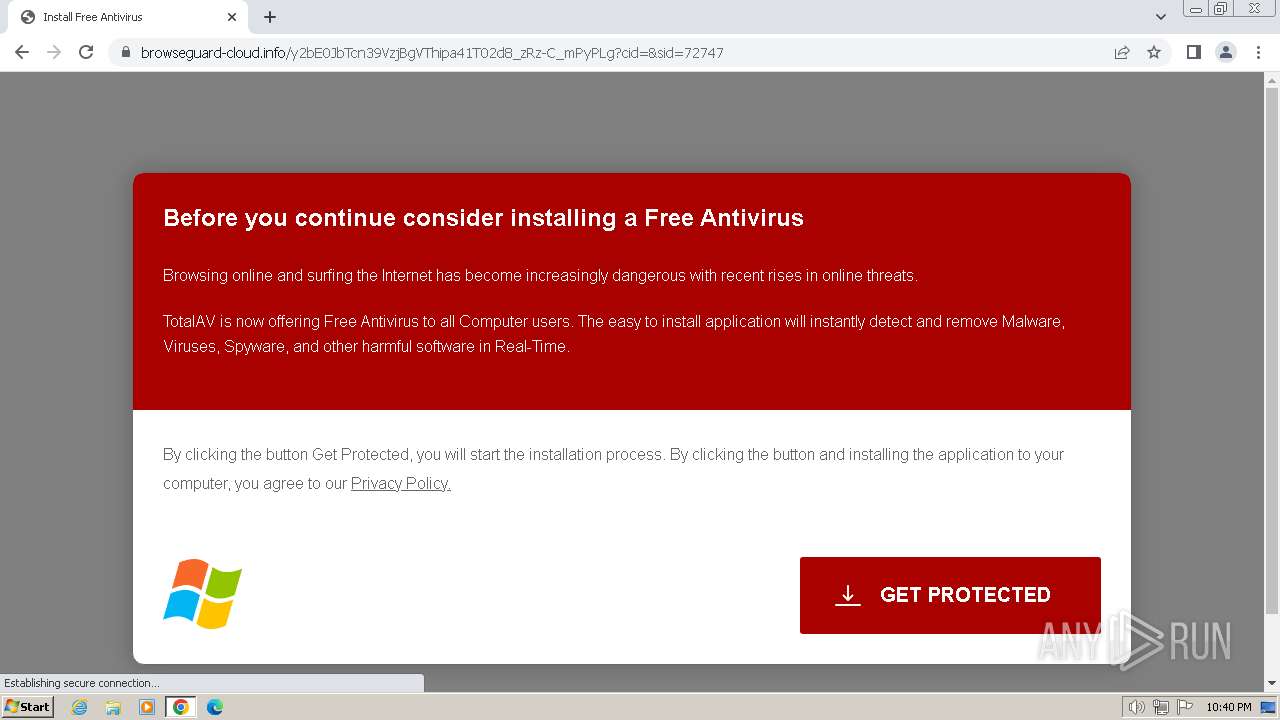
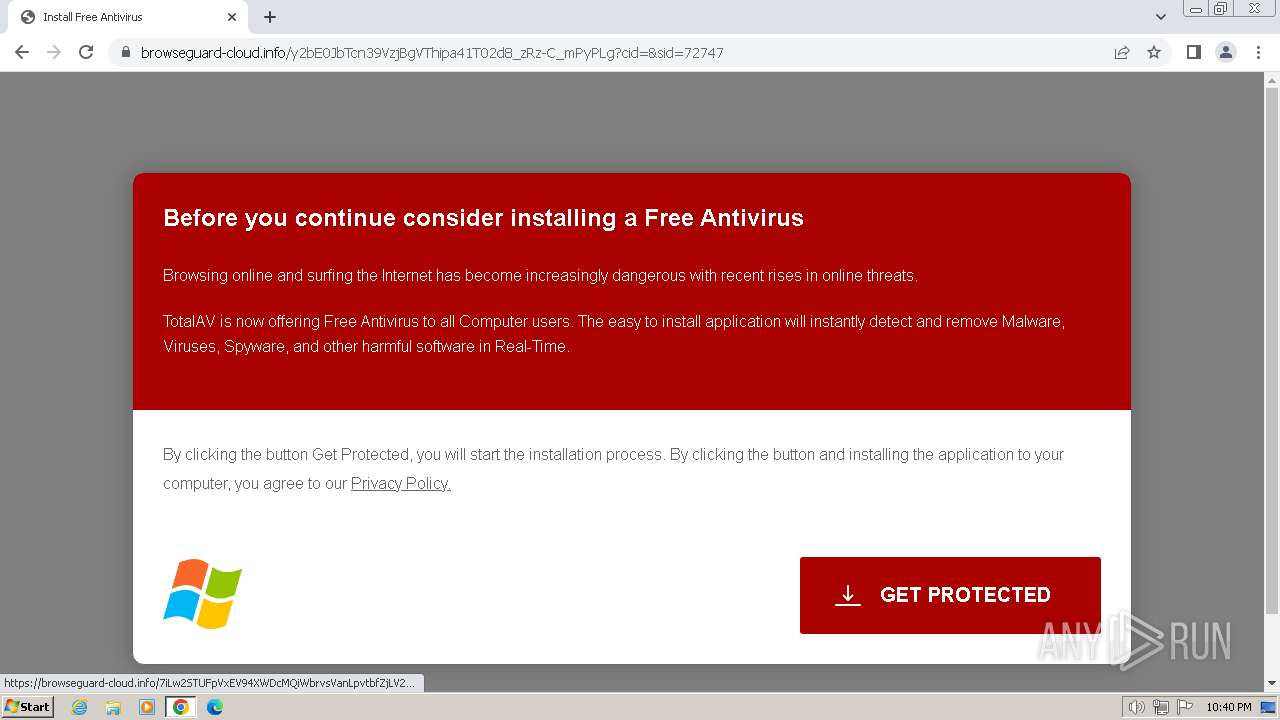
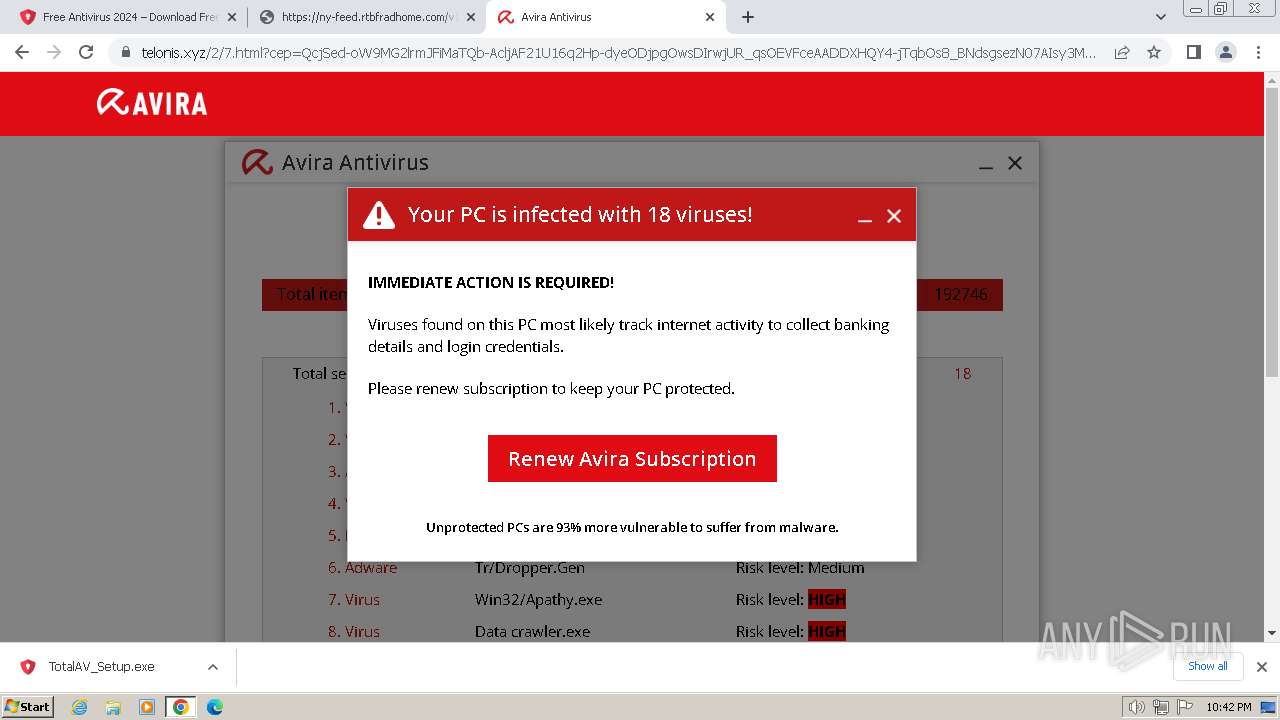
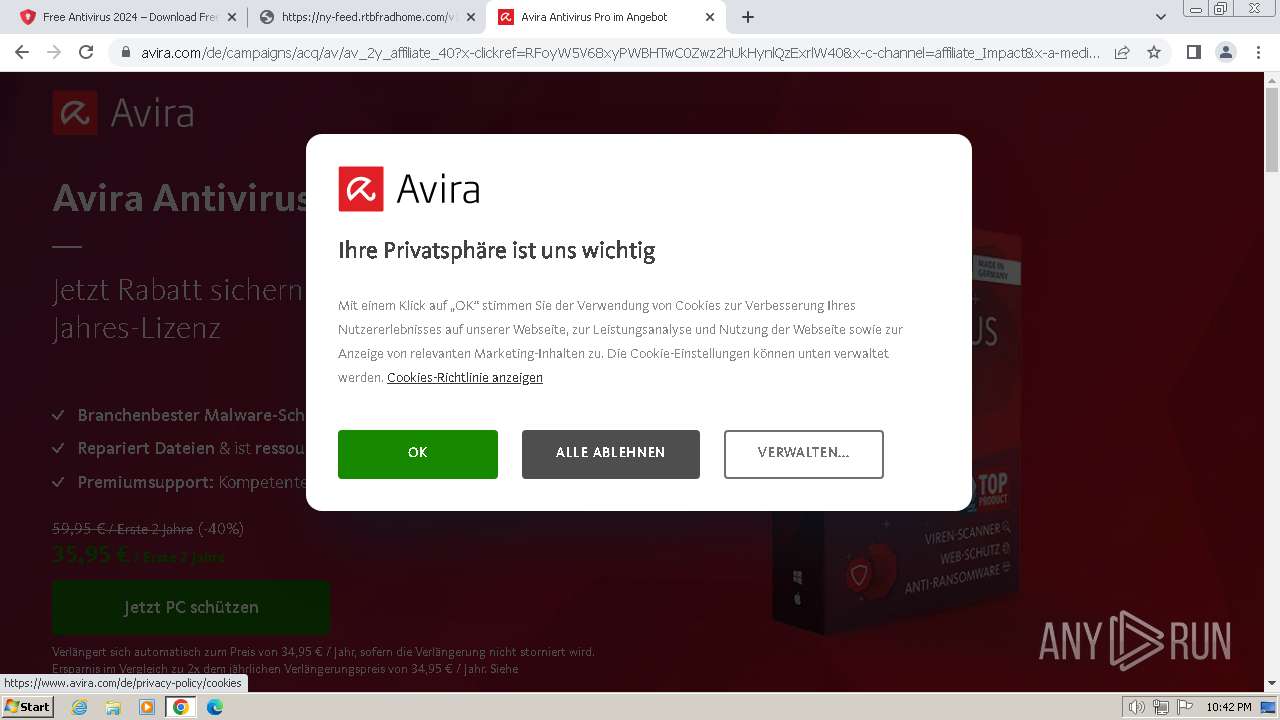
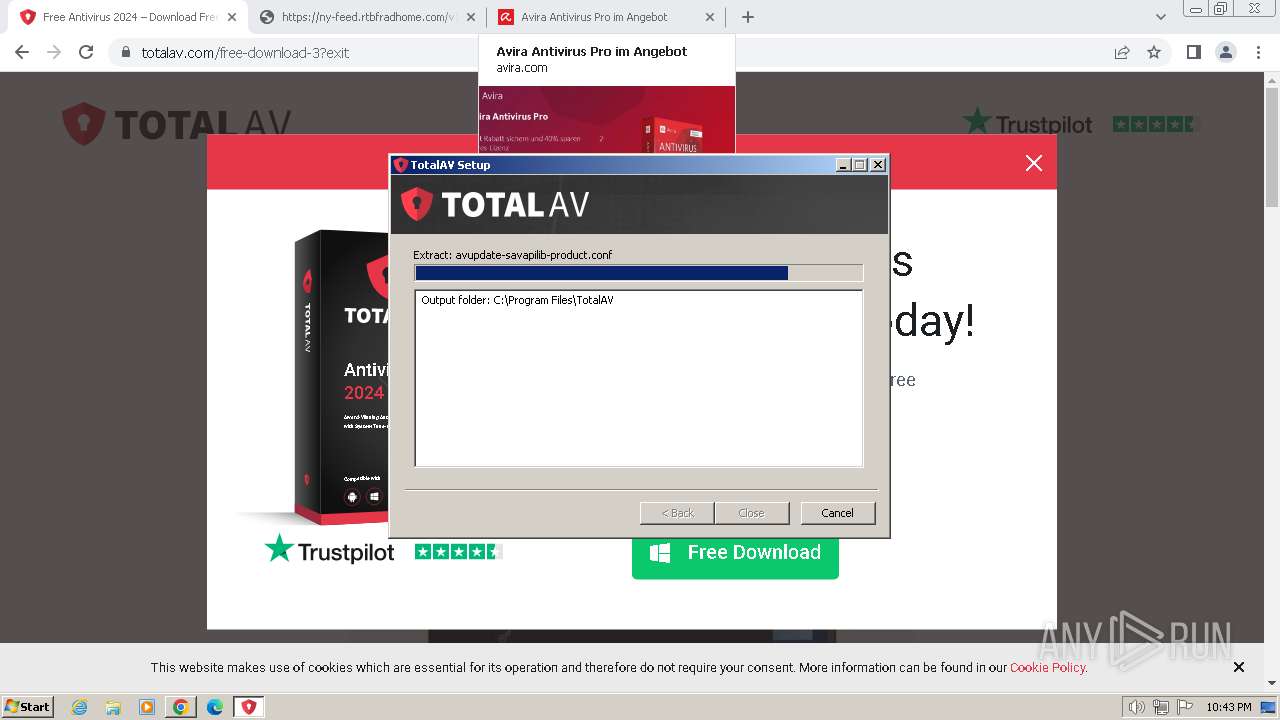
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2024, 22:38:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 175B3DD8064671779C3FE77C2CDD05F3 |
| SHA1: | AE9160145EA62FD4043678331BC9520CFF05DFE9 |
| SHA256: | C121124EB51EFA8B225FC4856BCEC0E9926A7AA6AD5817E2D5807EB521EADEA6 |
| SSDEEP: | 3:N8DWRBLd3bfGSJn:2s3L3Jn |
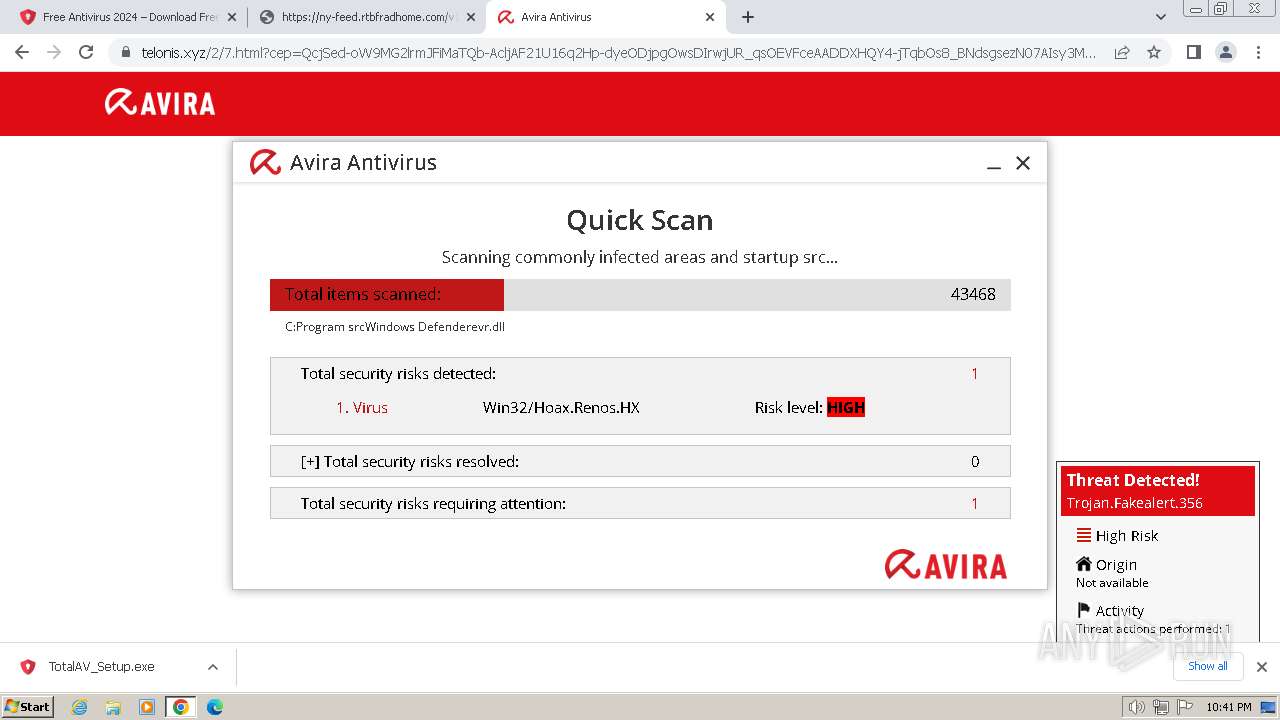
MALICIOUS
Drops the executable file immediately after the start
- TotalAV_Setup.exe (PID: 908)
Deletes shadow copies
- ns453.tmp (PID: 668)
SUSPICIOUS
The process creates files with name similar to system file names
- TotalAV_Setup.exe (PID: 908)
- Dism.exe (PID: 1832)
- Dism.exe (PID: 1776)
- Dism.exe (PID: 680)
Malware-specific behavior (creating "System.dll" in Temp)
- TotalAV_Setup.exe (PID: 908)
Starts CMD.EXE for commands execution
- nsF735.tmp (PID: 2124)
- ns100E.tmp (PID: 2056)
- ns22BC.tmp (PID: 2108)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2300)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 1216)
Starts application with an unusual extension
- TotalAV_Setup.exe (PID: 908)
Executable content was dropped or overwritten
- TotalAV_Setup.exe (PID: 908)
- Dism.exe (PID: 1832)
- Dism.exe (PID: 1776)
- Dism.exe (PID: 680)
Process drops legitimate windows executable
- Dism.exe (PID: 1832)
- Dism.exe (PID: 1776)
- Dism.exe (PID: 680)
- TotalAV_Setup.exe (PID: 908)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 1576)
- DismHost.exe (PID: 4056)
- DismHost.exe (PID: 1376)
Get information on the list of running processes
- TotalAV_Setup.exe (PID: 908)
- ns453.tmp (PID: 668)
Uses WMIC.EXE
- ns453.tmp (PID: 668)
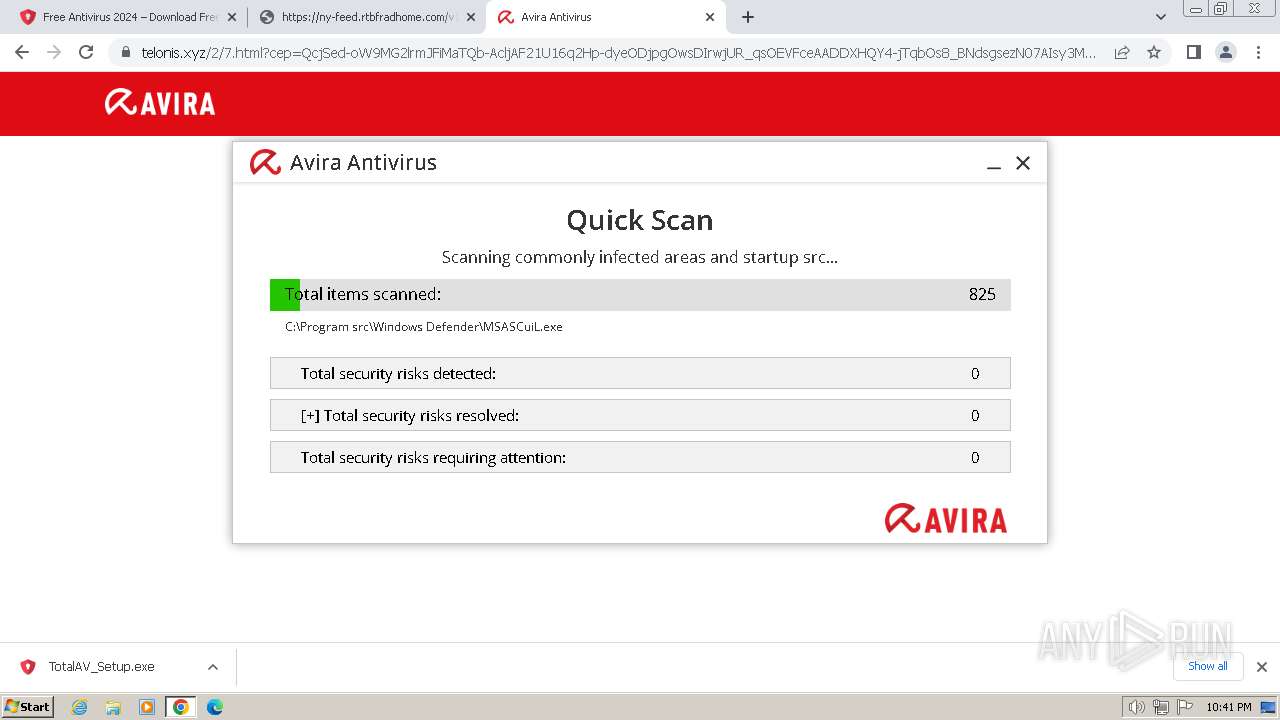
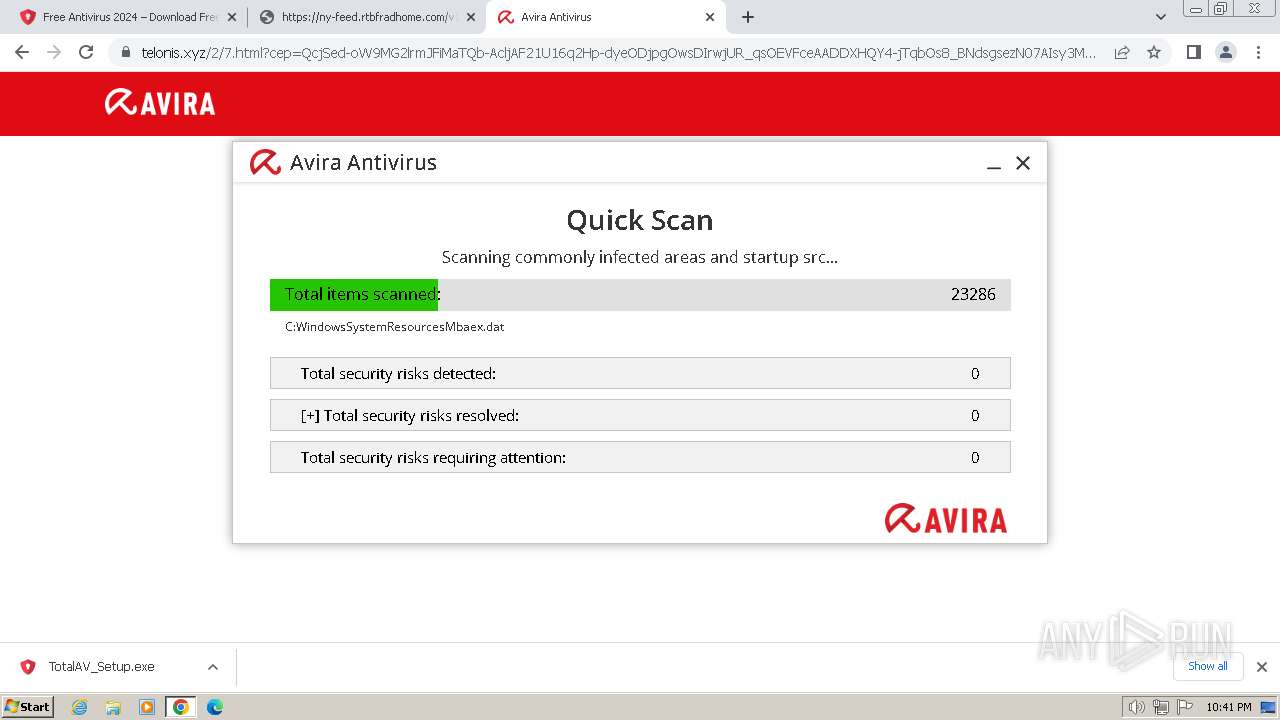
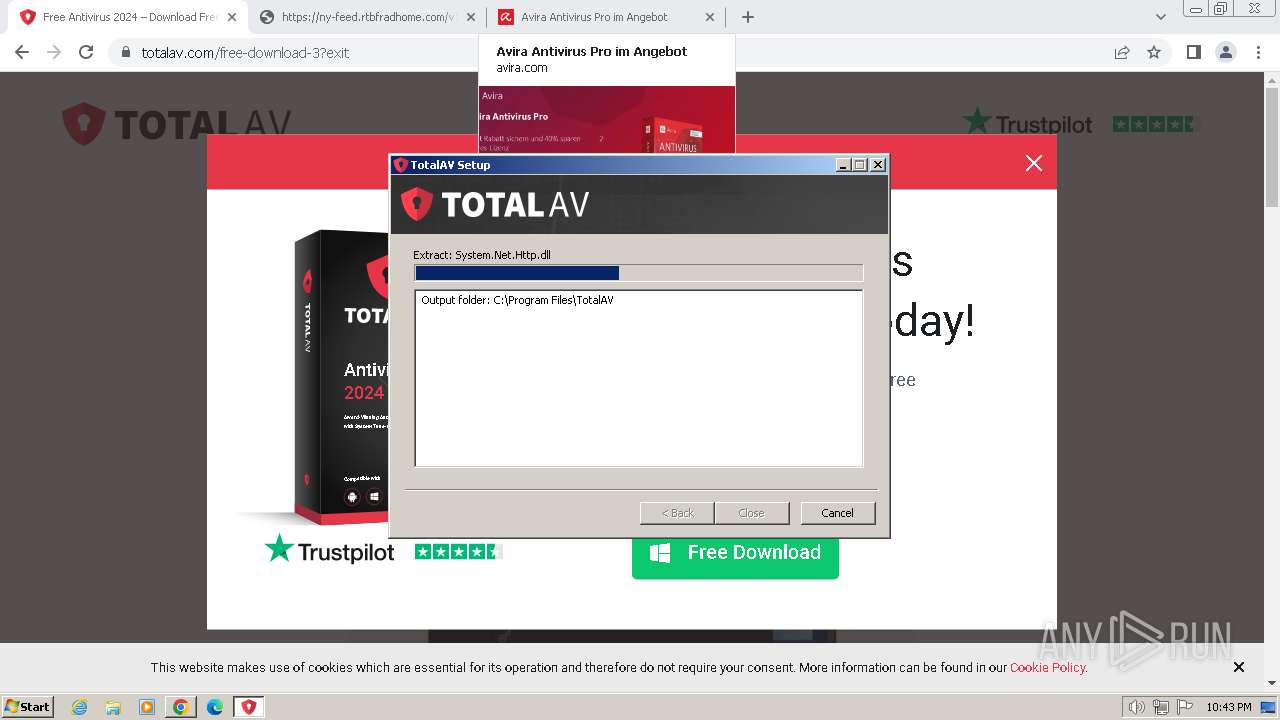
The process verifies whether the antivirus software is installed
- WMIC.exe (PID: 1808)
- ns54E.tmp (PID: 392)
- ns5CC.tmp (PID: 3932)
- taskkill.exe (PID: 2924)
- taskkill.exe (PID: 2032)
- ns63A.tmp (PID: 2528)
- taskkill.exe (PID: 2508)
- ns6B8.tmp (PID: 2988)
- ns453.tmp (PID: 668)
- ns7F93.tmp (PID: 4024)
- SecurityService.exe (PID: 2108)
- sc.exe (PID: 3632)
- subinacl.exe (PID: 3544)
- TotalAV.exe (PID: 2228)
- TotalAV_Setup.exe (PID: 908)
Reads the Internet Settings
- WMIC.exe (PID: 1808)
- TotalAV_Setup.exe (PID: 908)
Uses TASKKILL.EXE to kill process
- ns63A.tmp (PID: 2528)
- ns5CC.tmp (PID: 3932)
- ns54E.tmp (PID: 392)
Executes as Windows Service
- VSSVC.exe (PID: 924)
Searches for installed software
- TotalAV_Setup.exe (PID: 908)
- dllhost.exe (PID: 1748)
The process drops C-runtime libraries
- TotalAV_Setup.exe (PID: 908)
Creates a software uninstall entry
- TotalAV_Setup.exe (PID: 908)
Drops a system driver (possible attempt to evade defenses)
- TotalAV_Setup.exe (PID: 908)
Reads security settings of Internet Explorer
- TotalAV_Setup.exe (PID: 908)
Starts SC.EXE for service management
- SecurityService.exe (PID: 2108)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 1216)
- chrome.exe (PID: 3672)
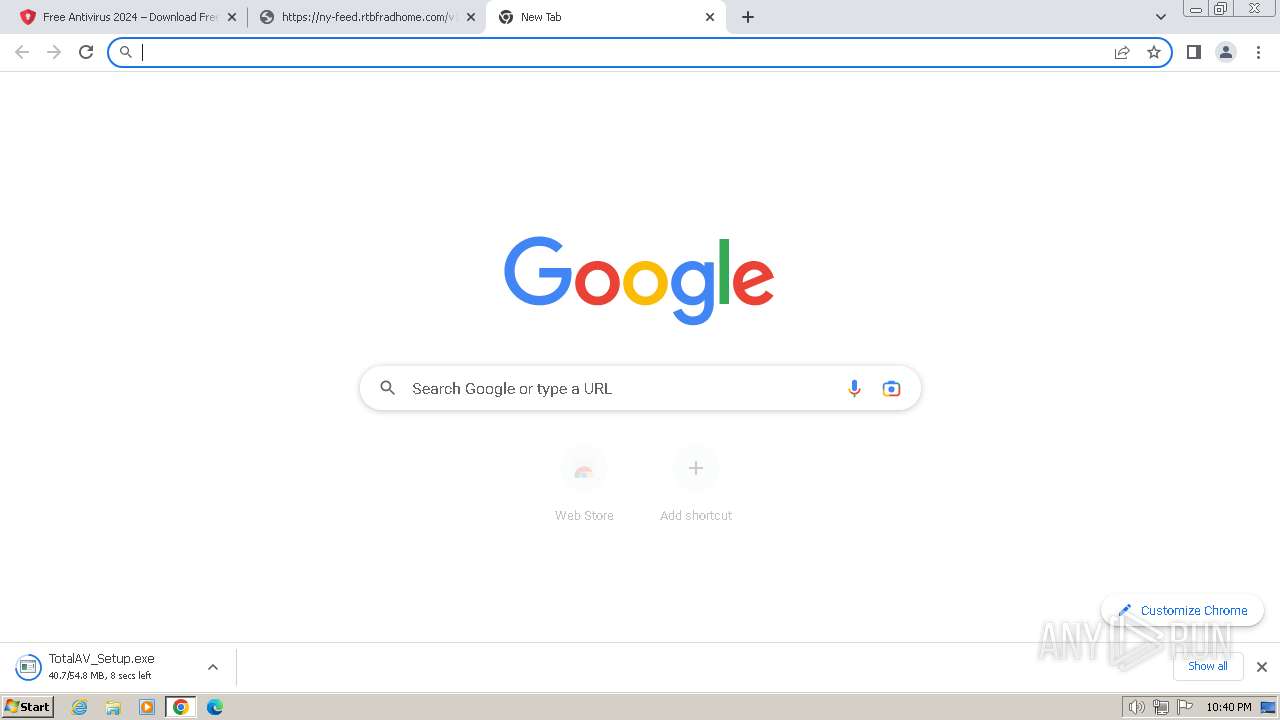
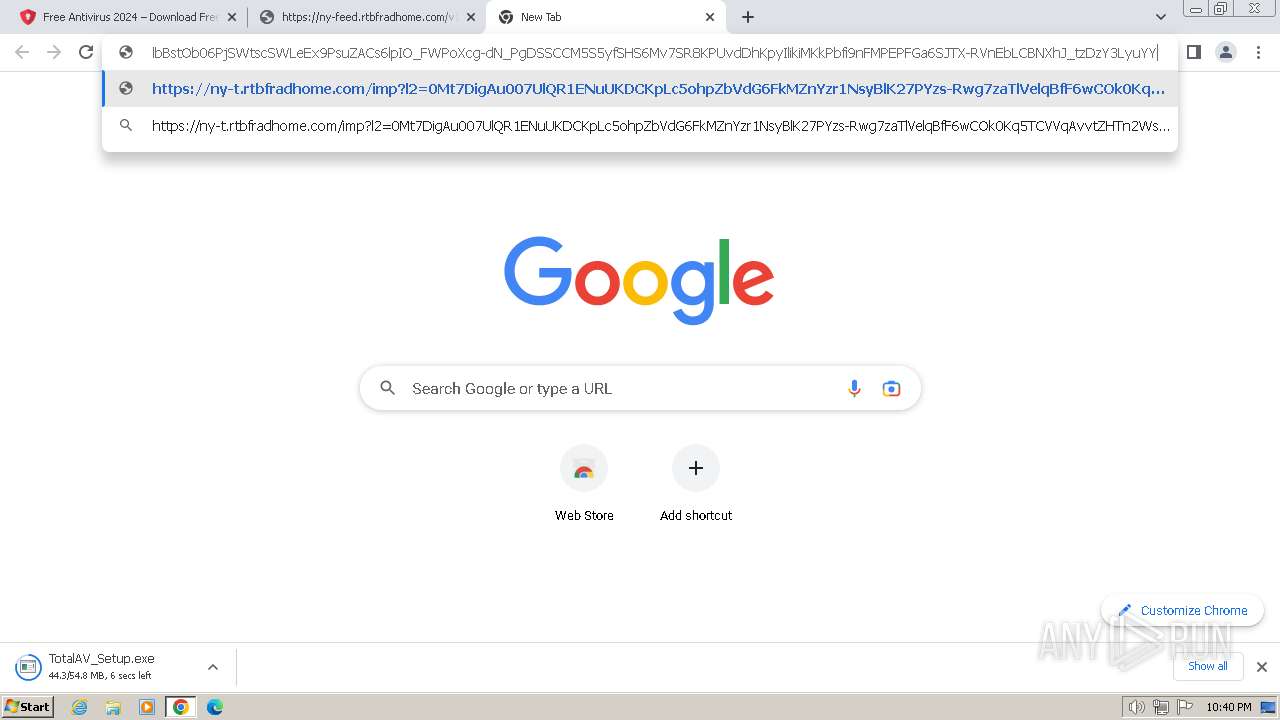
The process uses the downloaded file
- chrome.exe (PID: 2772)
- chrome.exe (PID: 3672)
Drops the executable file immediately after the start
- chrome.exe (PID: 1216)
- chrome.exe (PID: 3672)
- Dism.exe (PID: 1832)
- Dism.exe (PID: 1776)
- Dism.exe (PID: 680)
Connects to unusual port
- chrome.exe (PID: 3228)
Reads the computer name
- TotalAV_Setup.exe (PID: 908)
- DismHost.exe (PID: 1576)
- DismHost.exe (PID: 4056)
- DismHost.exe (PID: 1376)
- wmpnscfg.exe (PID: 4004)
- SecurityService.exe (PID: 2108)
- subinacl.exe (PID: 3544)
- TotalAV.exe (PID: 2228)
Checks supported languages
- TotalAV_Setup.exe (PID: 908)
- nsF735.tmp (PID: 2124)
- DismHost.exe (PID: 1576)
- ns100E.tmp (PID: 2056)
- DismHost.exe (PID: 4056)
- ns22BC.tmp (PID: 2108)
- DismHost.exe (PID: 1376)
- wmpnscfg.exe (PID: 4004)
- ns453.tmp (PID: 668)
- ns54E.tmp (PID: 392)
- ns5CC.tmp (PID: 3932)
- ns63A.tmp (PID: 2528)
- ns6B8.tmp (PID: 2988)
- ns7F93.tmp (PID: 4024)
- SecurityService.exe (PID: 2108)
- subinacl.exe (PID: 3544)
- TotalAV.exe (PID: 2228)
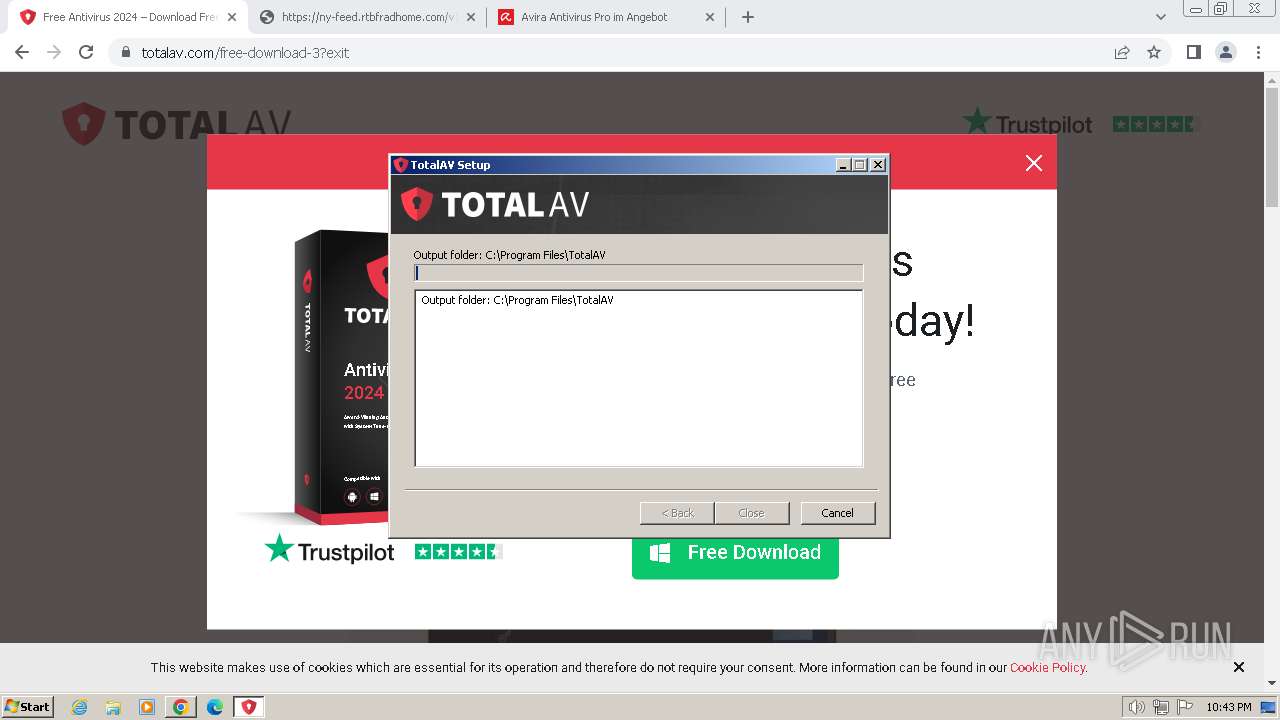
Create files in a temporary directory
- TotalAV_Setup.exe (PID: 908)
- Dism.exe (PID: 1832)
- Dism.exe (PID: 1776)
- Dism.exe (PID: 680)
Reads the machine GUID from the registry
- DismHost.exe (PID: 1576)
- DismHost.exe (PID: 4056)
- DismHost.exe (PID: 1376)
- TotalAV_Setup.exe (PID: 908)
Manual execution by a user
- wmpnscfg.exe (PID: 4004)
Creates files in the program directory
- TotalAV_Setup.exe (PID: 908)
- SecurityService.exe (PID: 2108)
- TotalAV.exe (PID: 2228)
Application launched itself
- chrome.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
84
Malicious processes
15
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3720 --field-trial-handle=1160,i,11144925105062216076,10602978617264485759,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\nsjF725.tmp\ns54E.tmp" "taskkill" /f /T /IM "avupdate.exe" | C:\Users\admin\AppData\Local\Temp\nsjF725.tmp\ns54E.tmp | — | TotalAV_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 668 | "C:\Users\admin\AppData\Local\Temp\nsjF725.tmp\ns453.tmp" wmic.exe path Win32_Process where executablepath="C:\\Program Files\\TotalAV\\TotalAV.exe" delete | C:\Users\admin\AppData\Local\Temp\nsjF725.tmp\ns453.tmp | — | TotalAV_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 680 | dism.exe /online /get-packages | C:\Windows\System32\Dism.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4952 --field-trial-handle=1160,i,11144925105062216076,10602978617264485759,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
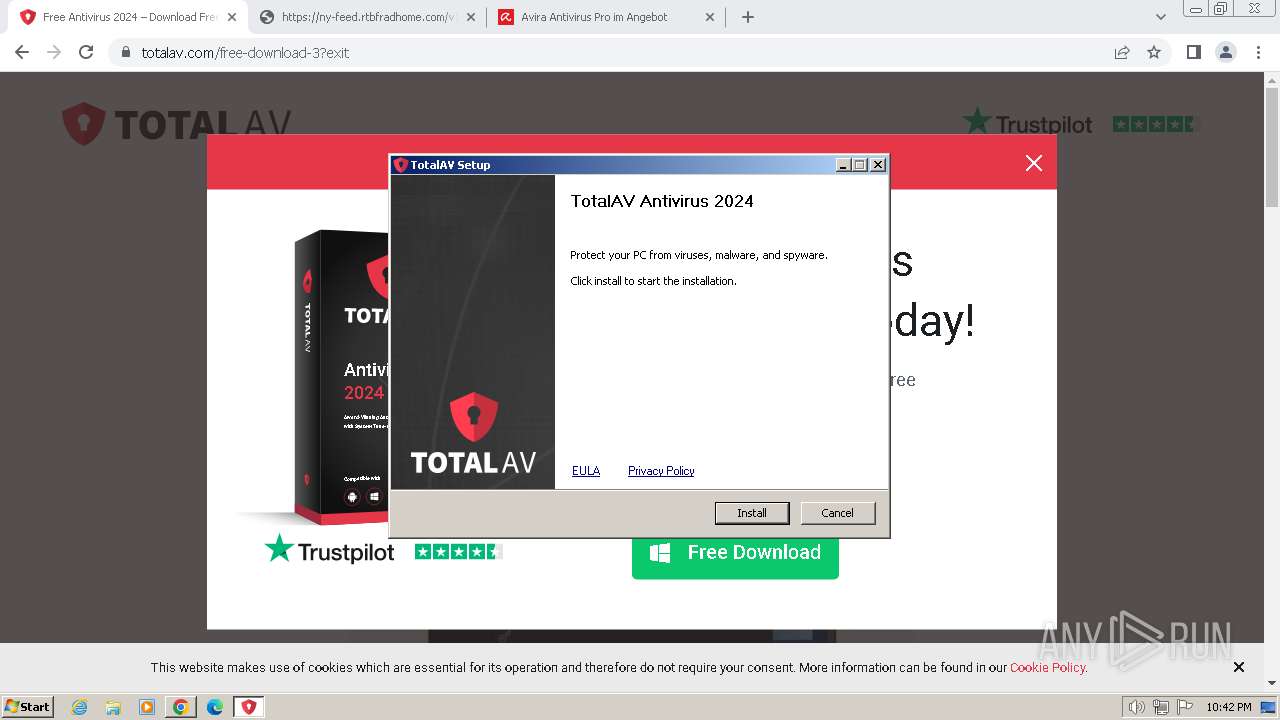
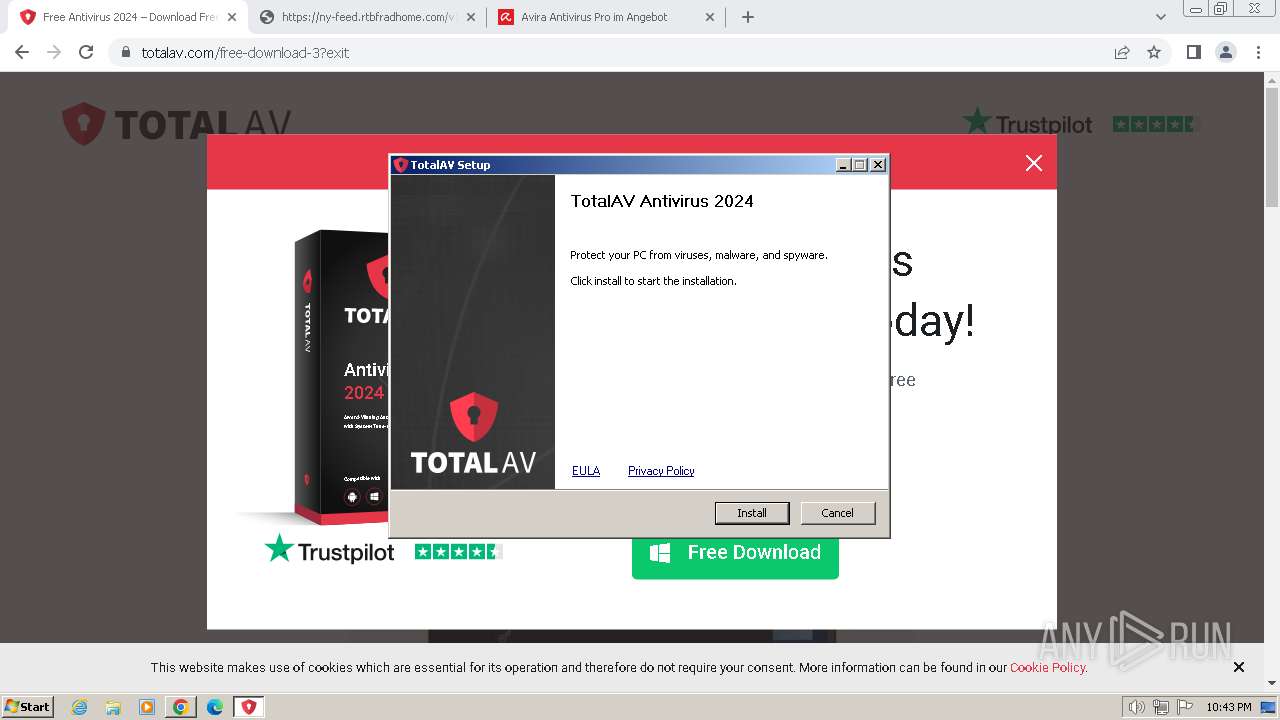
| 908 | "C:\Users\admin\Downloads\TotalAV_Setup.exe" | C:\Users\admin\Downloads\TotalAV_Setup.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TotalAV Ultimate Antivirus Installer Exit code: 0 Version: 5.24.38.0 Modules
| |||||||||||||||
| 924 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3796 --field-trial-handle=1160,i,11144925105062216076,10602978617264485759,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3220 --field-trial-handle=1160,i,11144925105062216076,10602978617264485759,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4956 --field-trial-handle=1160,i,11144925105062216076,10602978617264485759,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 695
Read events
19 335
Write events
353
Delete events
7
Modification events
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
605
Suspicious files
169
Text files
149
Unknown types
282
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f6b4.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f6c4.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF17f80c.TMP | text | |
MD5:8593E82FF8753DC10267243C51E8A91B | SHA256:FE9EE2D77D9EB5CBA707EDBCB7F1ABAA83418CDB66D66835B4B9A1B6CC5CC34F | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17fd2c.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2fe9be29-cfd6-47c1-8577-f308e4b05860.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180a0d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
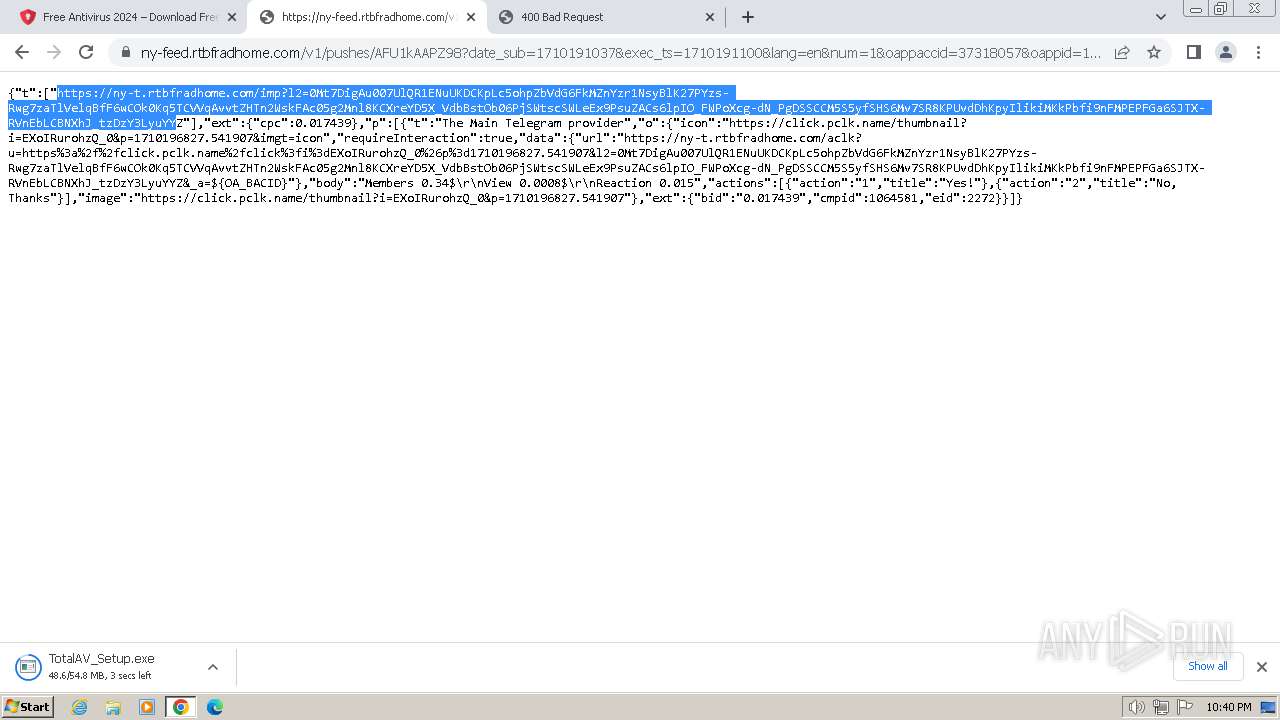
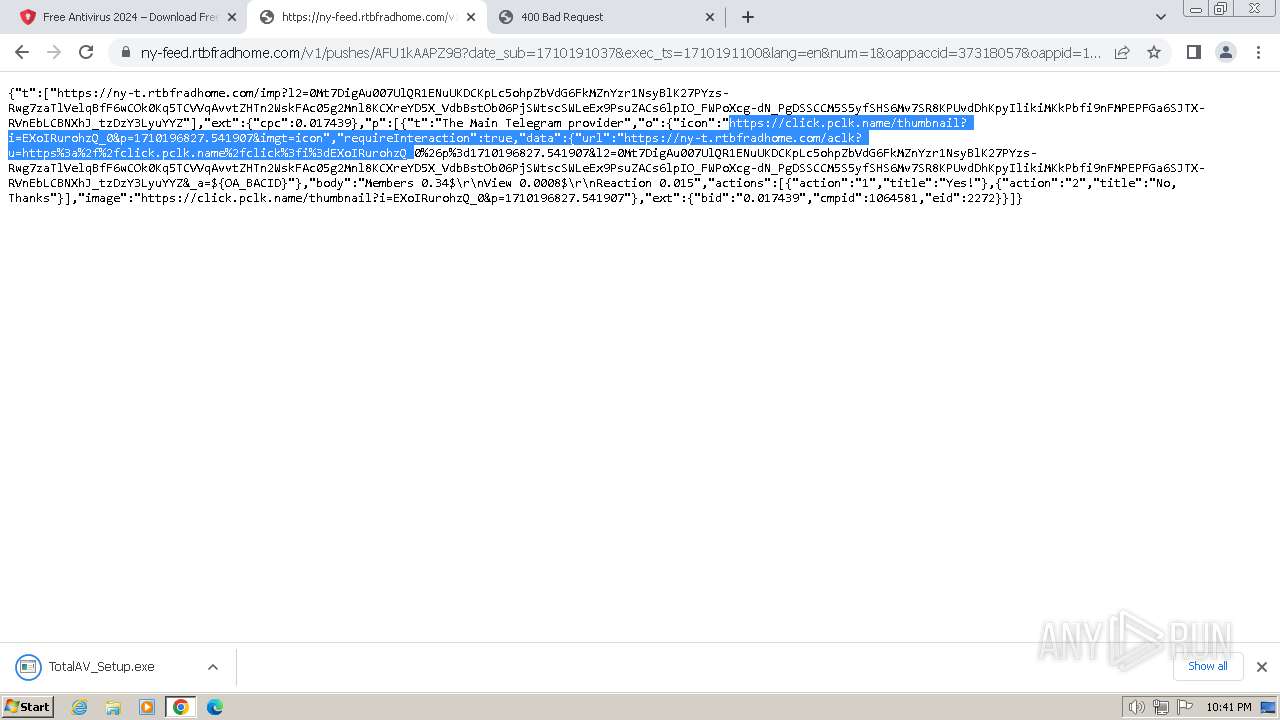
HTTP(S) requests
38
TCP/UDP connections
108
DNS requests
169
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 6.29 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 7.90 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 10.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.82 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 7.90 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | binary | 3.07 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | binary | 5.52 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 74.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3228 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
3672 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
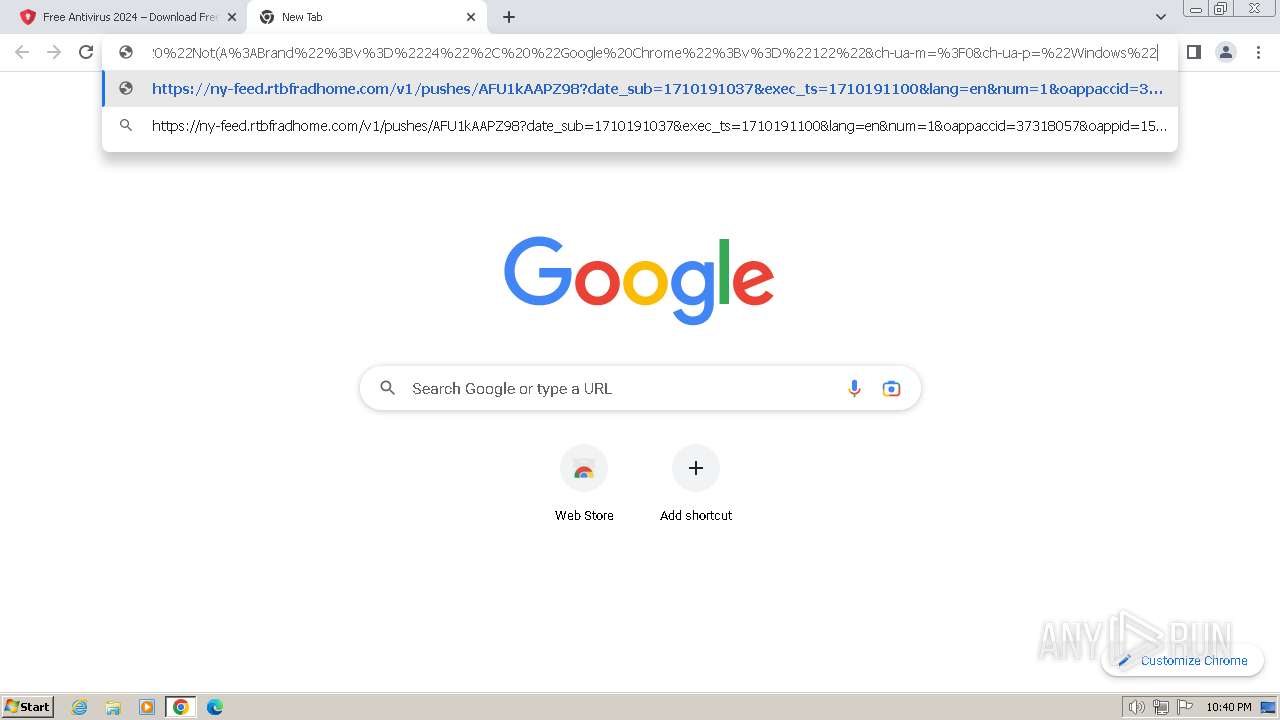
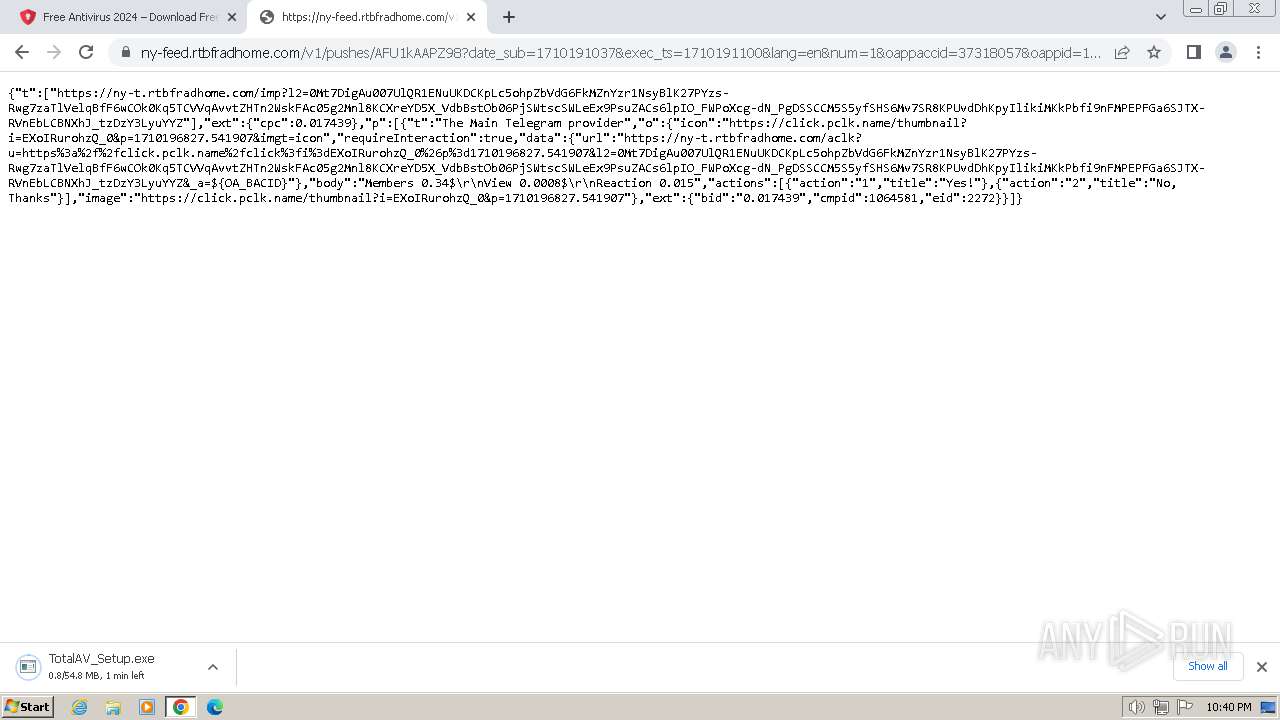
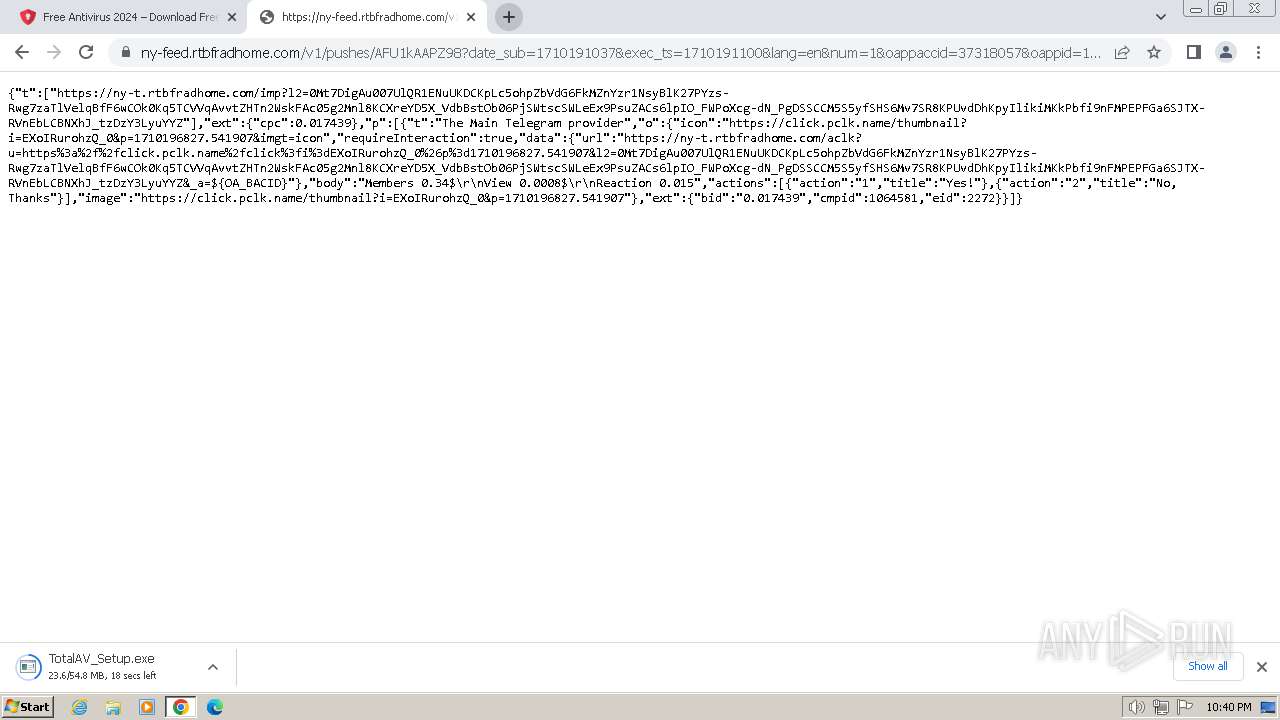
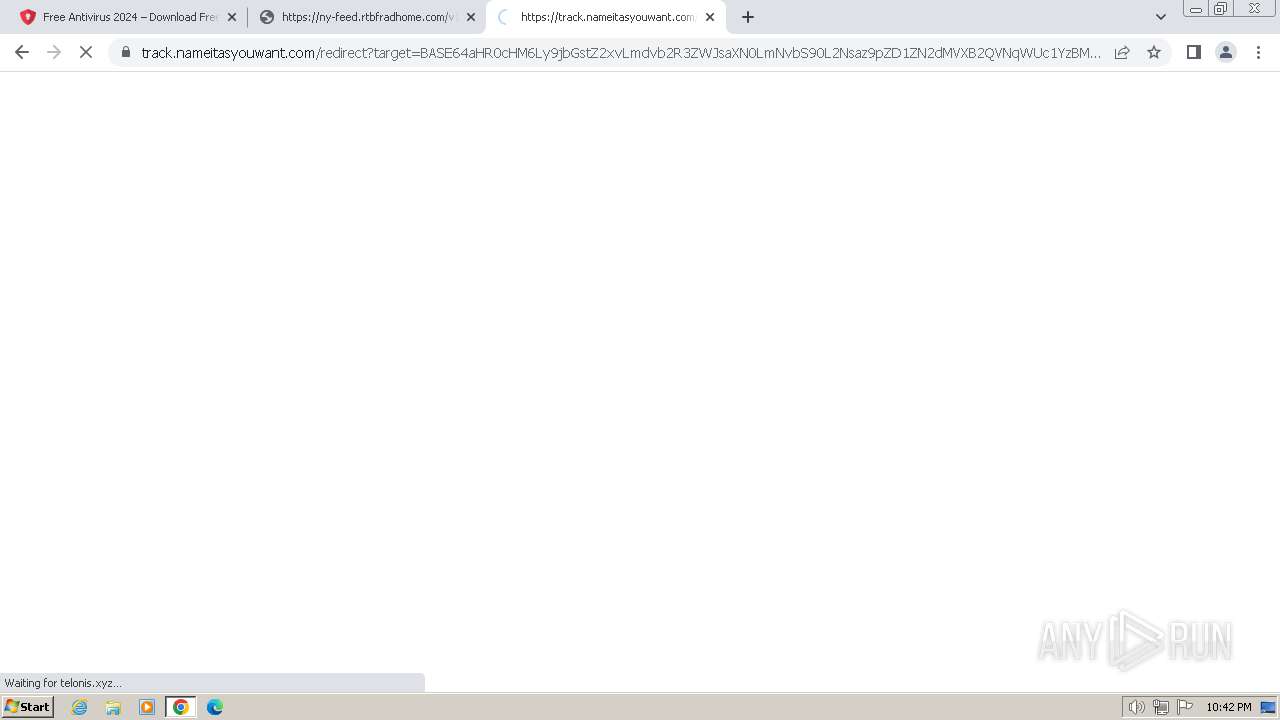
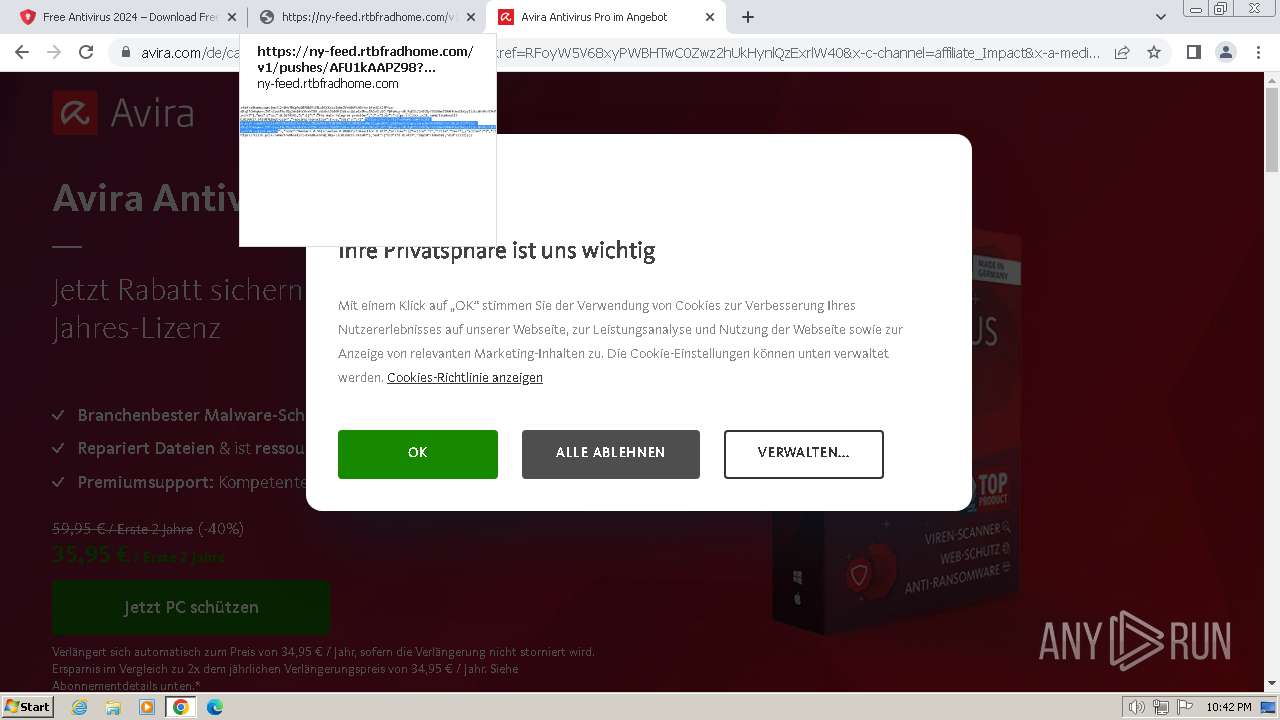
3228 | chrome.exe | 104.26.7.228:443 | t.ocmhood.com | CLOUDFLARENET | US | unknown |
3228 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | unknown |
3672 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3228 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 172.217.16.138:443 | www.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
t.ocmhood.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
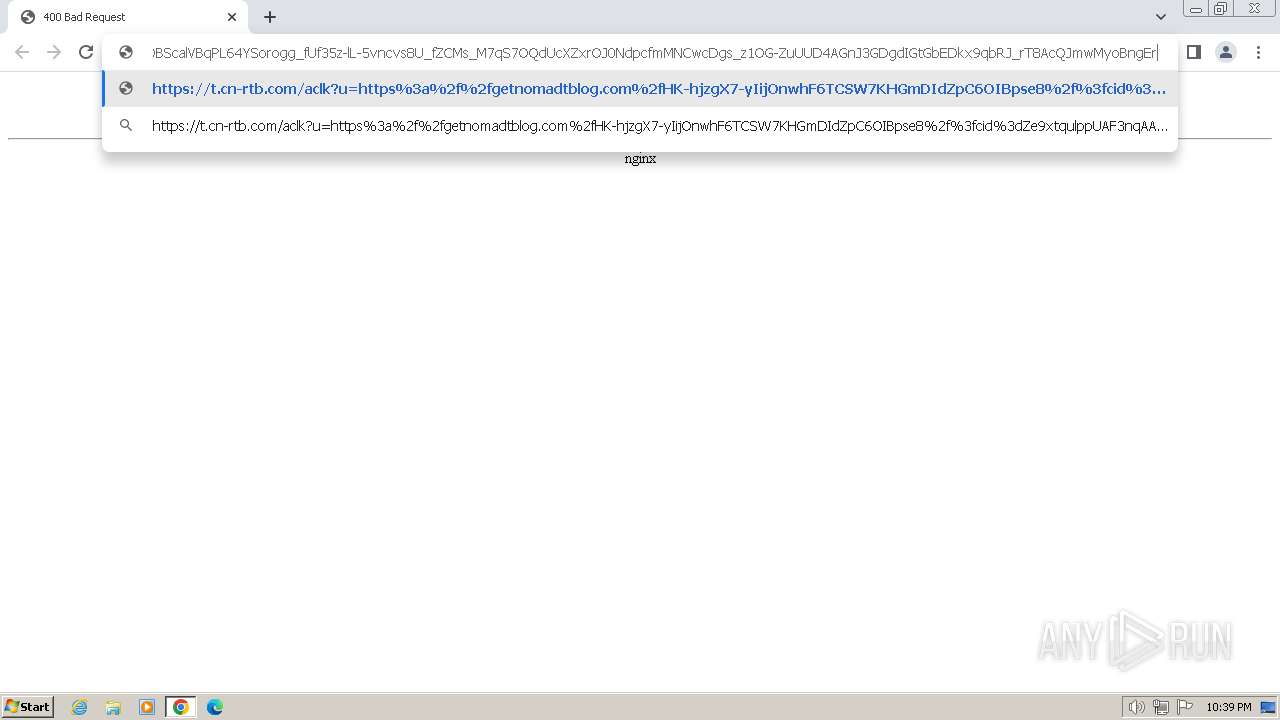
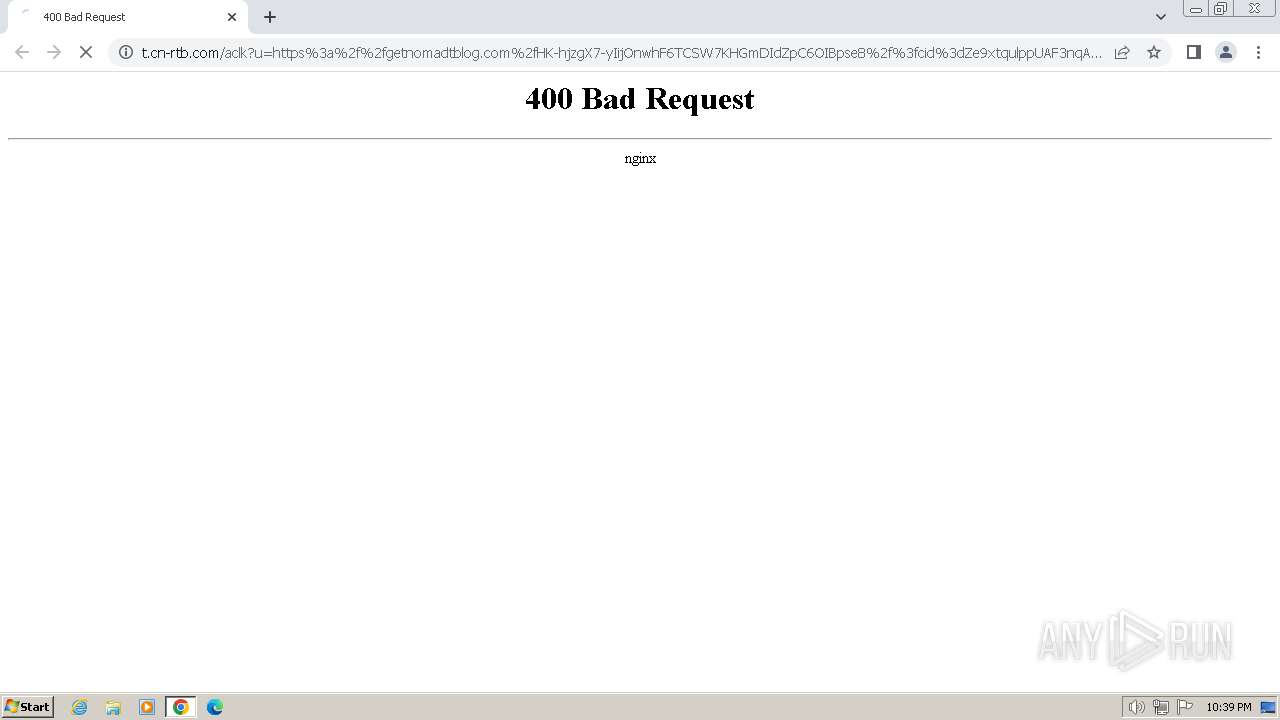
t.cn-rtb.com |
| unknown |
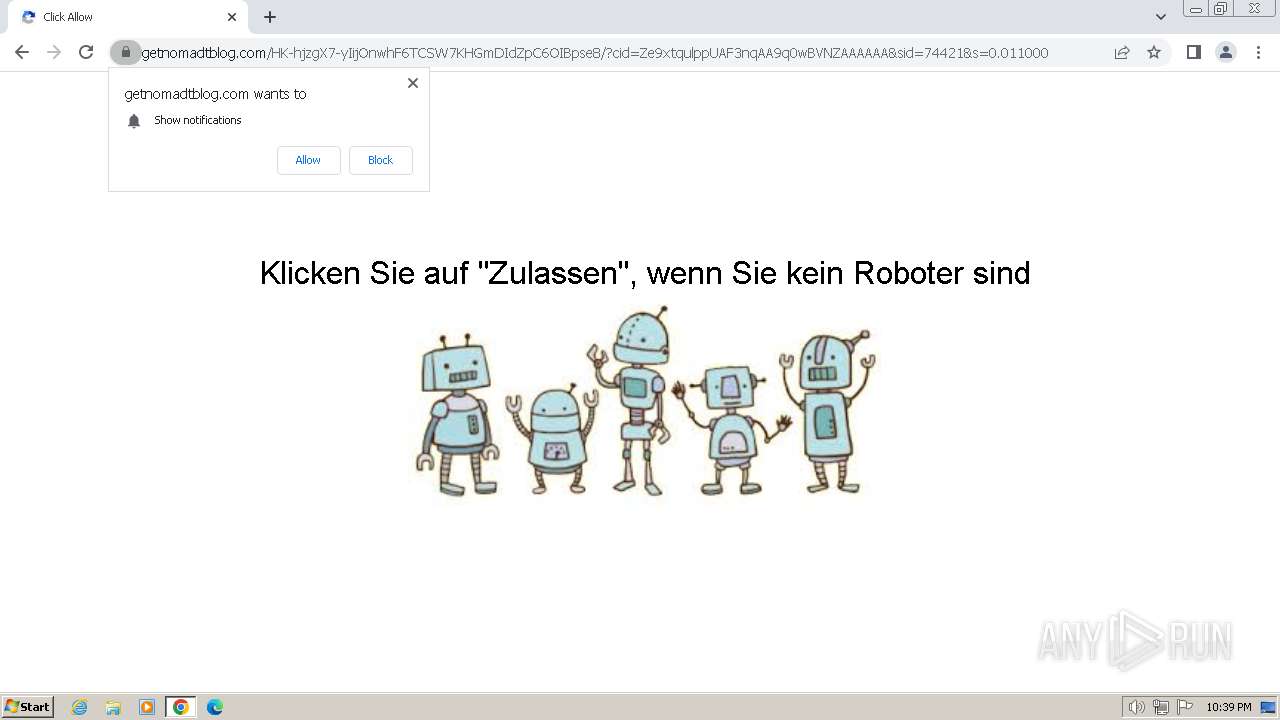
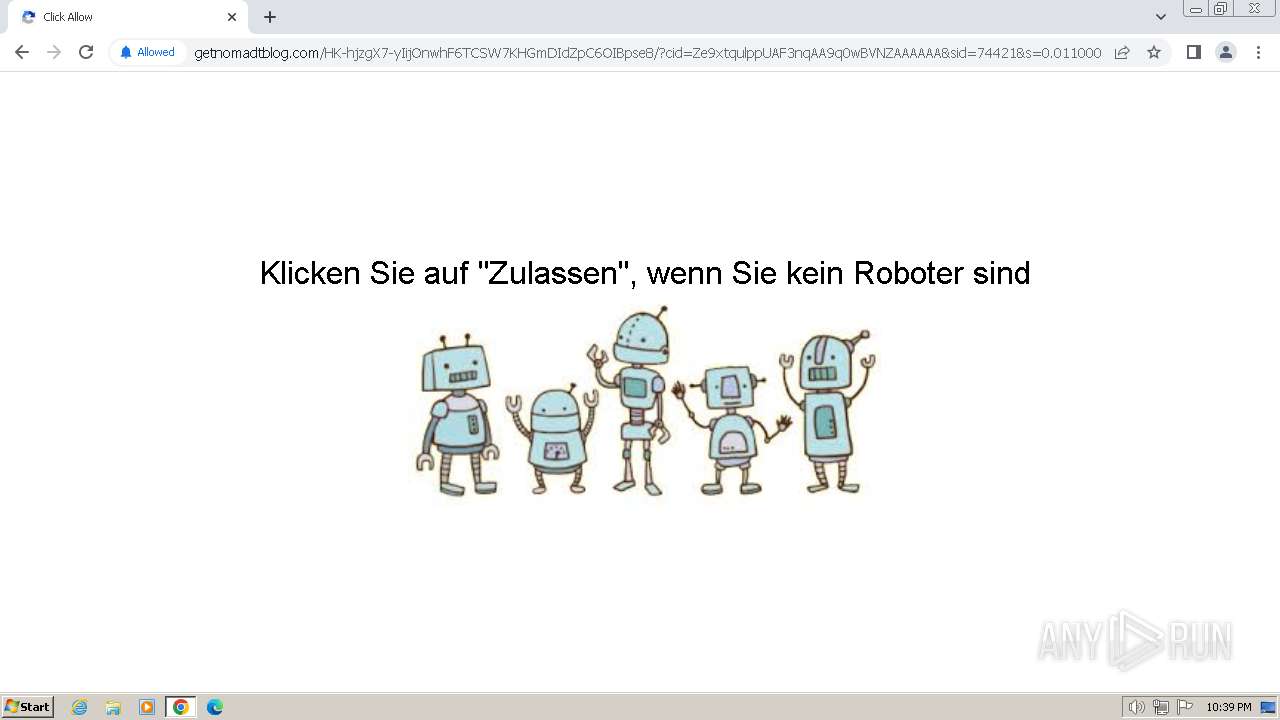
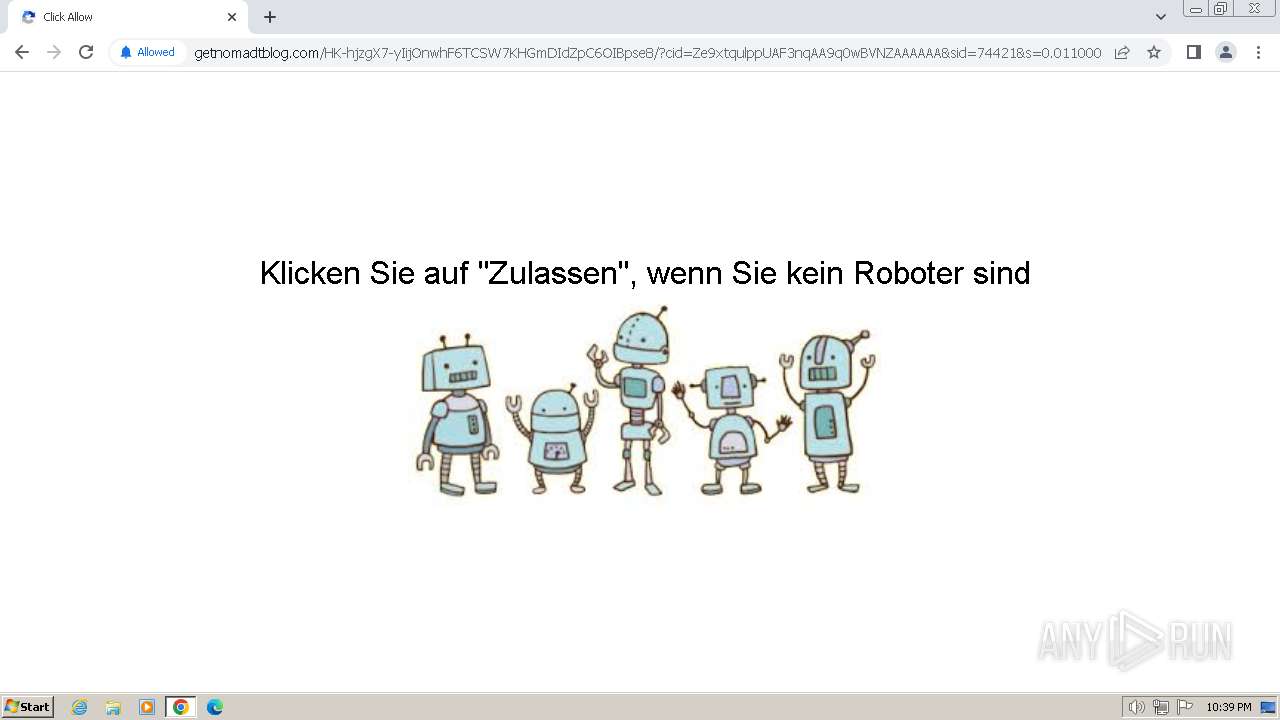
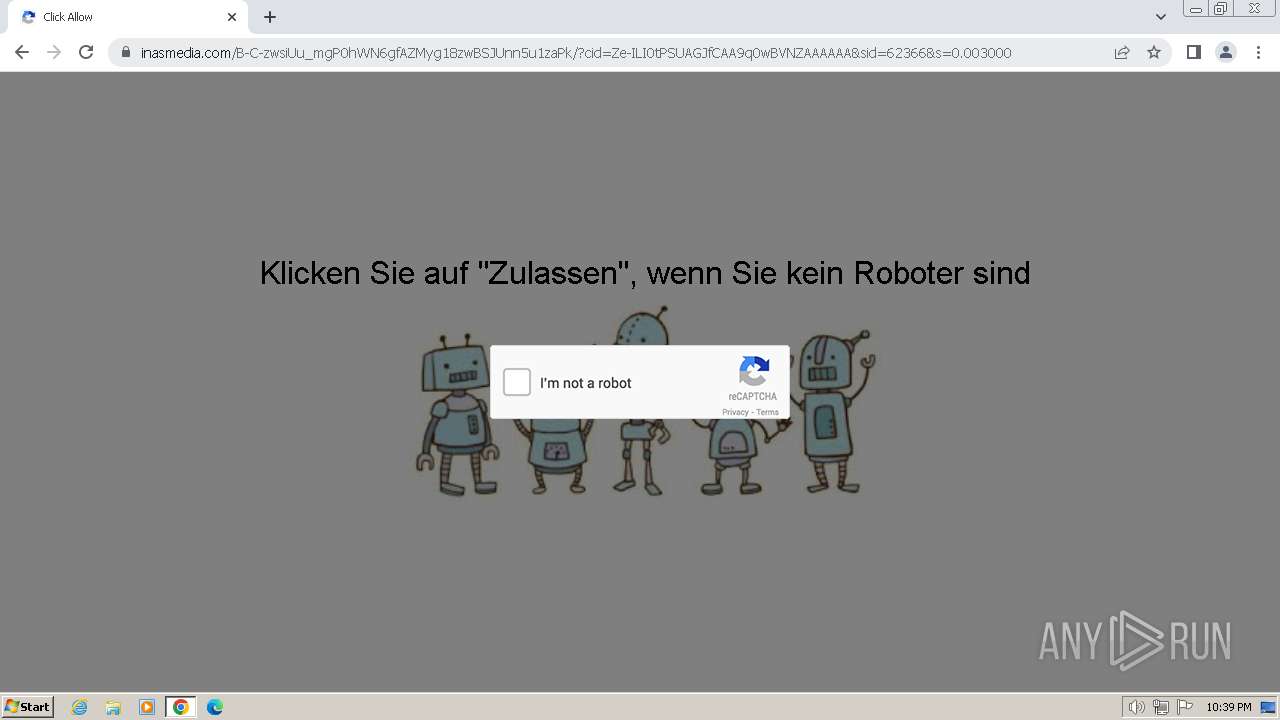
getnomadtblog.com |
| unknown |
sdk.ocmhood.com |
| unknown |
cdn.ocmtag.com |
| unknown |
cdn.ocmhood.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
Dism.exe | PID=1832 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=1832 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=1832 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=1832 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=1832 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=1832 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
Dism.exe | PID=1832 Getting Provider OSServices - CDISMProviderStore::GetProvider |
Dism.exe | PID=1832 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
Dism.exe | PID=1832 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |
DismHost.exe | PID=1576 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |