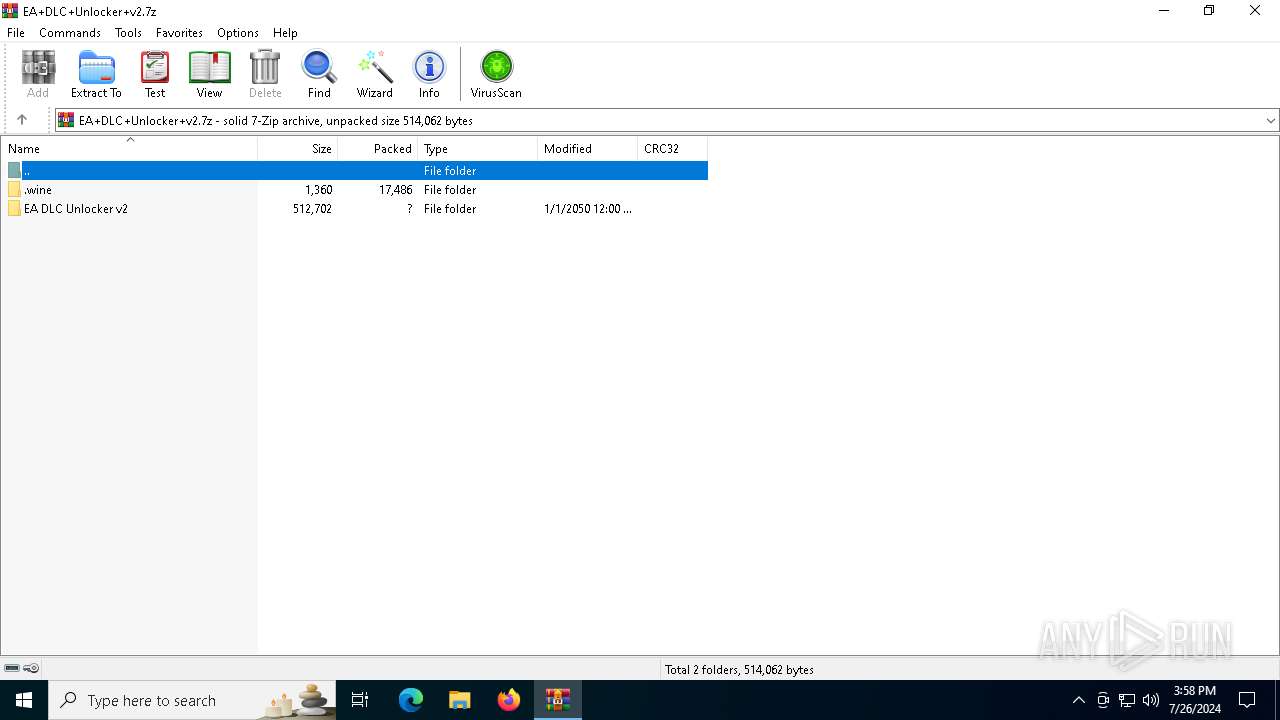
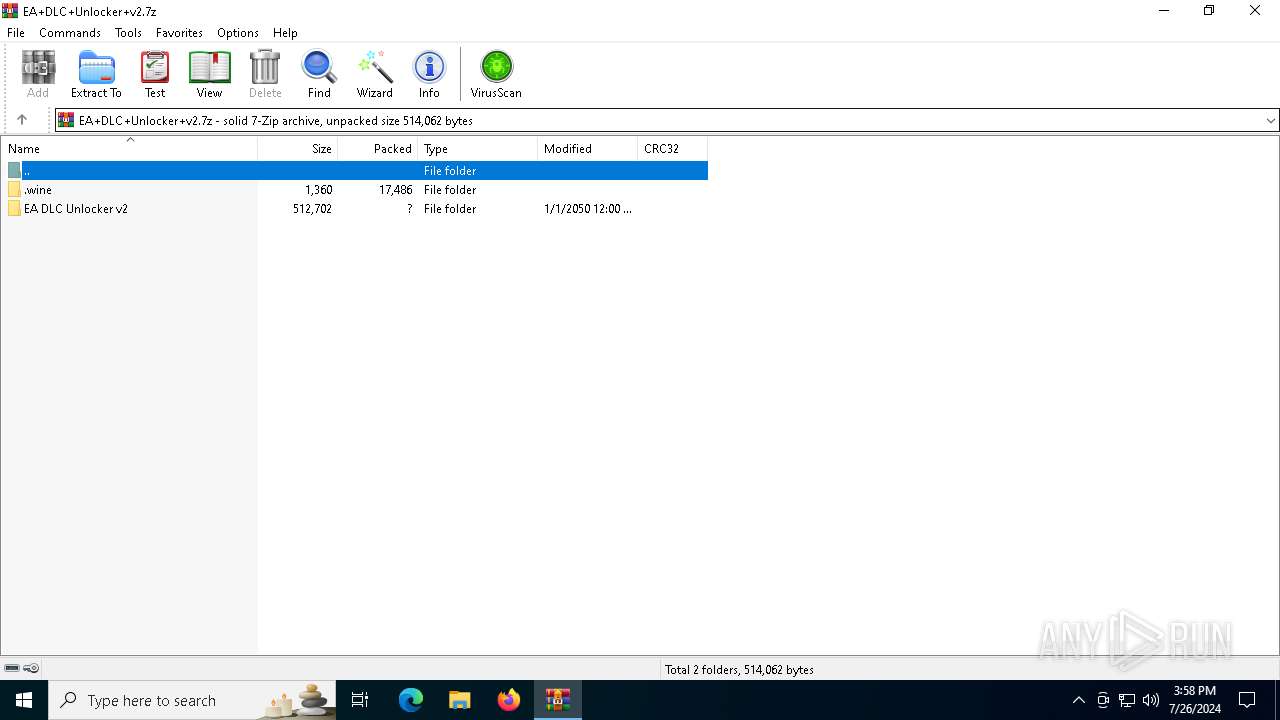
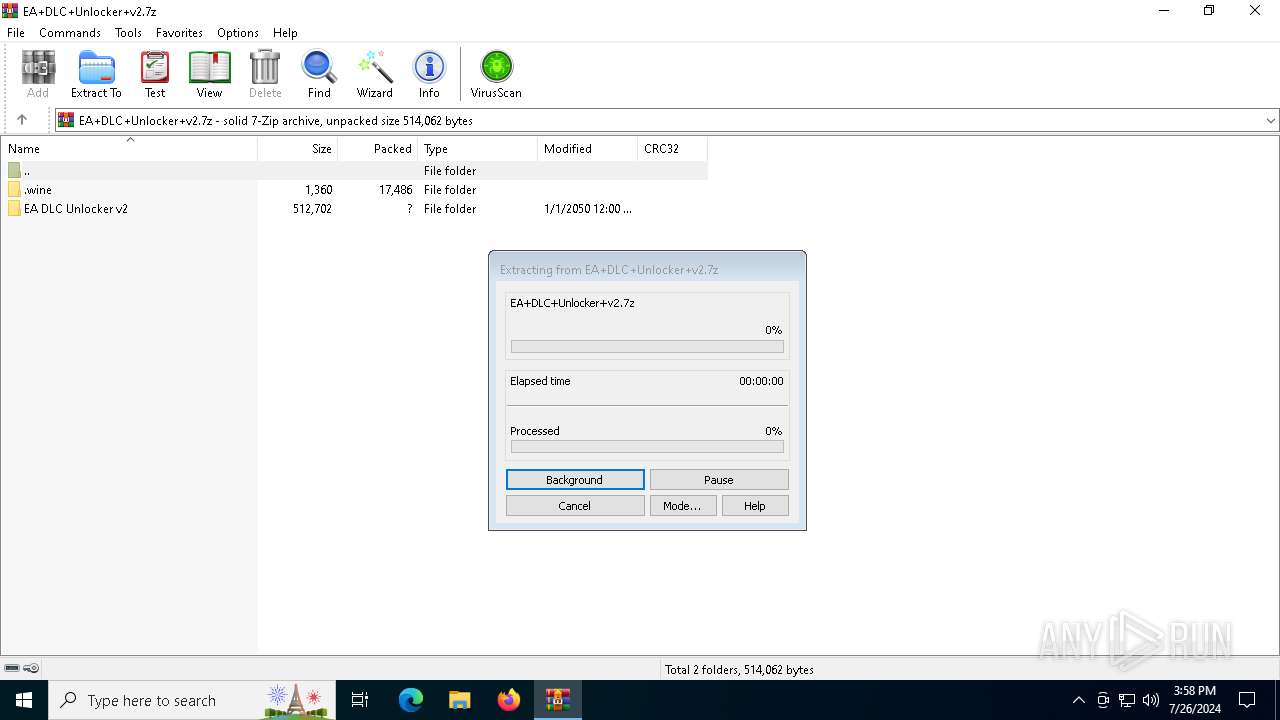
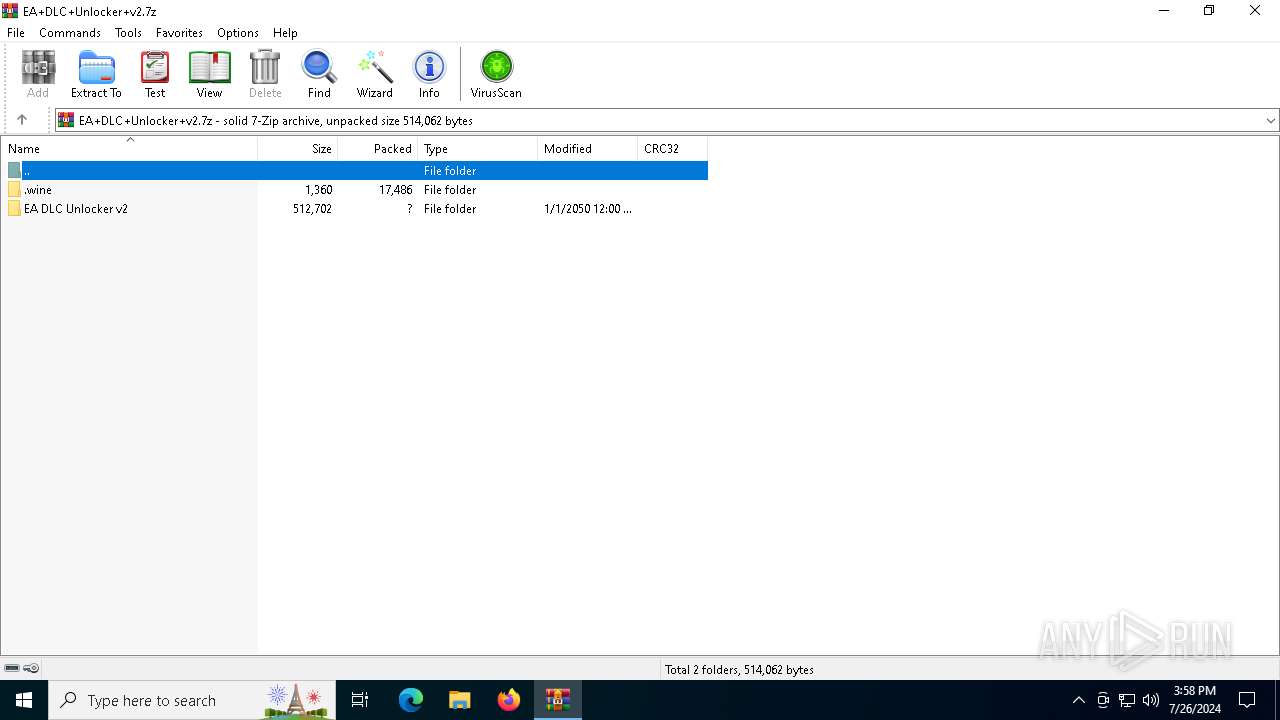
| File name: | EA+DLC+Unlocker+v2.7z |
| Full analysis: | https://app.any.run/tasks/b40d942b-030a-4a81-a860-580f612be2fd |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2024, 15:58:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 67602BF5588DC9608D2CB06F25A457ED |
| SHA1: | B5FE3BC19BB055CC046F949596A8A749AD060940 |
| SHA256: | C118A5E197F513DD36006474ADBDA475F6BFCC4B44EE3632A62C88AAAD94EBB5 |
| SSDEEP: | 6144:G+Th1+OLIuFYVc7kQA784g+Y8hFfz7oCSgw70Kqt+IE26bz:G+f+O8uFUcTQ8V27fYCSXMyj |
MALICIOUS
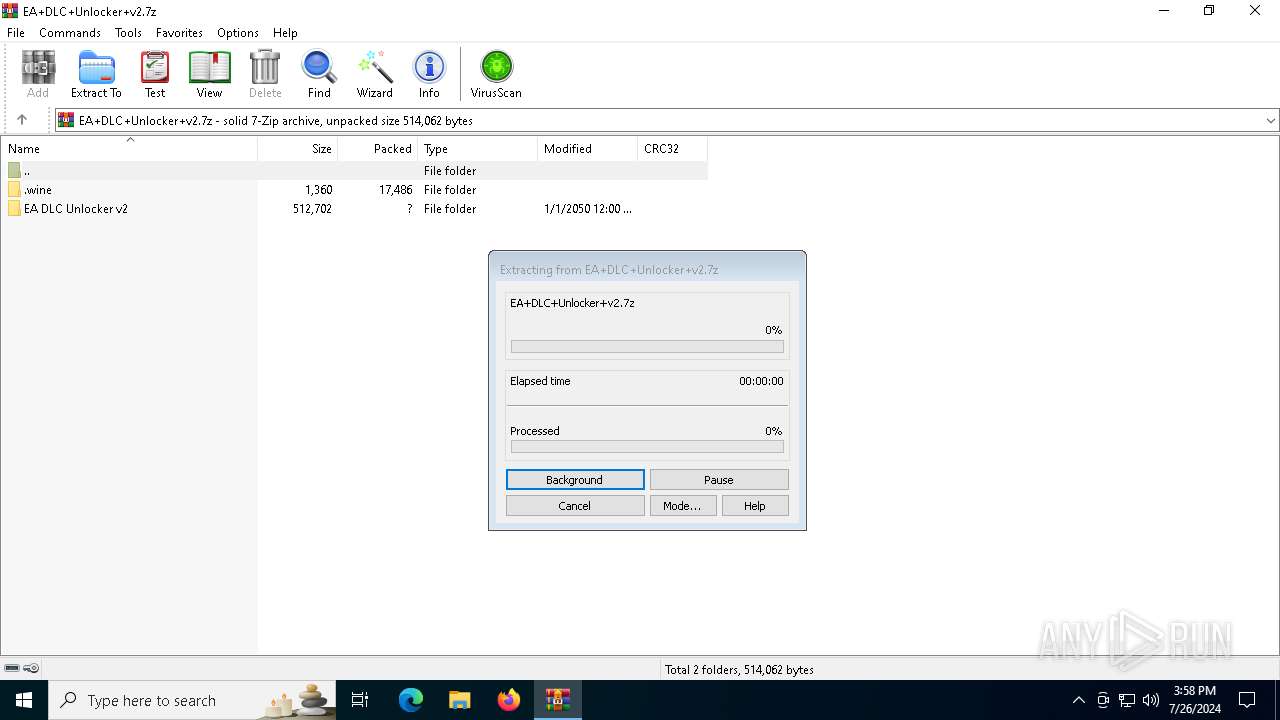
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1516)
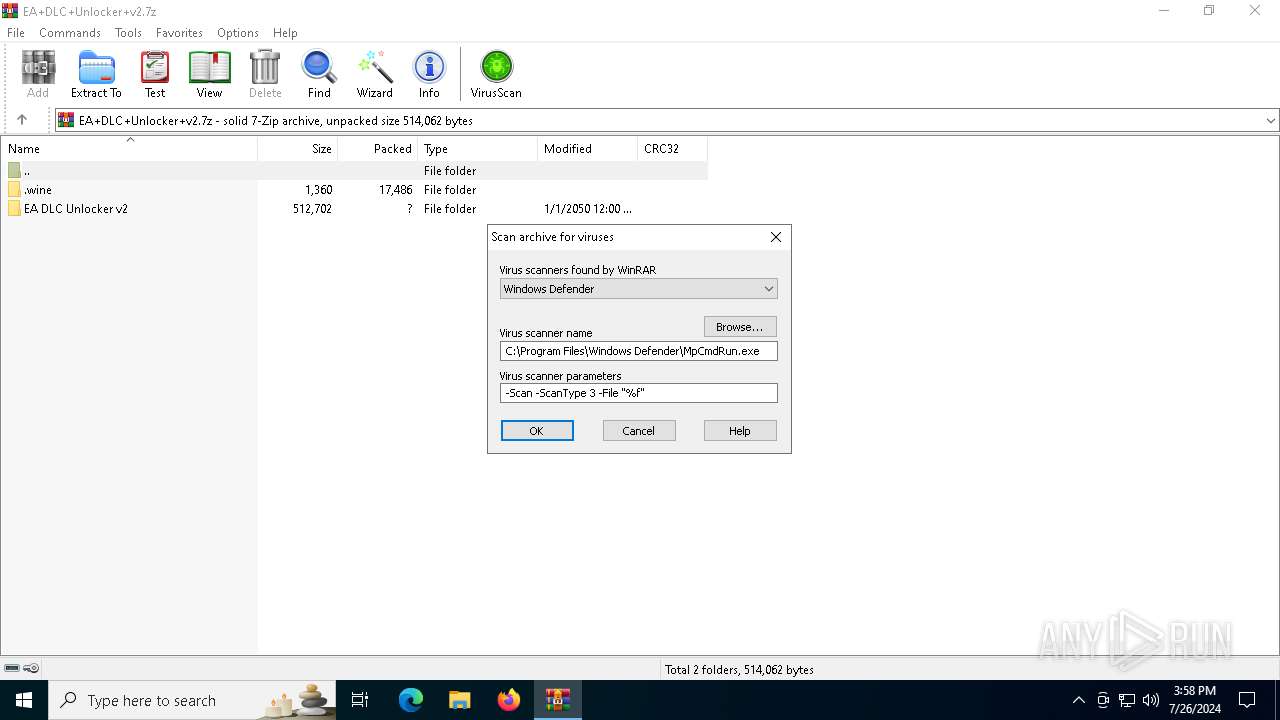
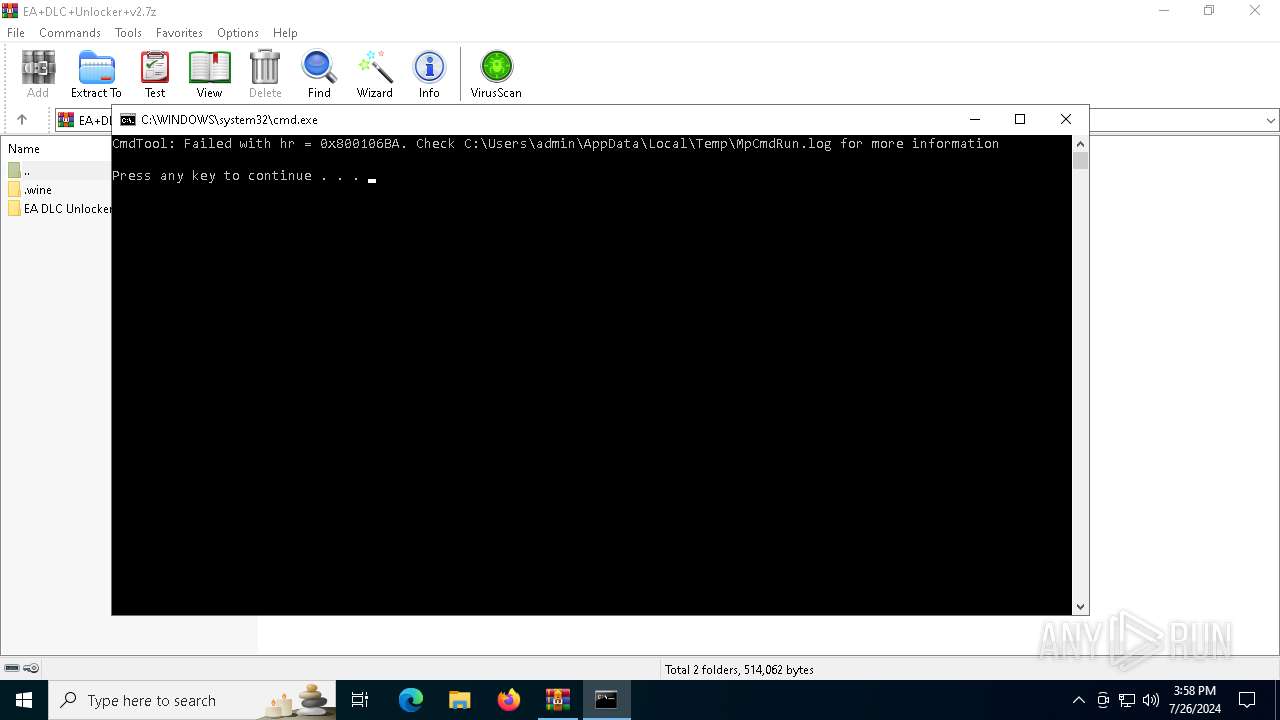
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 6164)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1516)
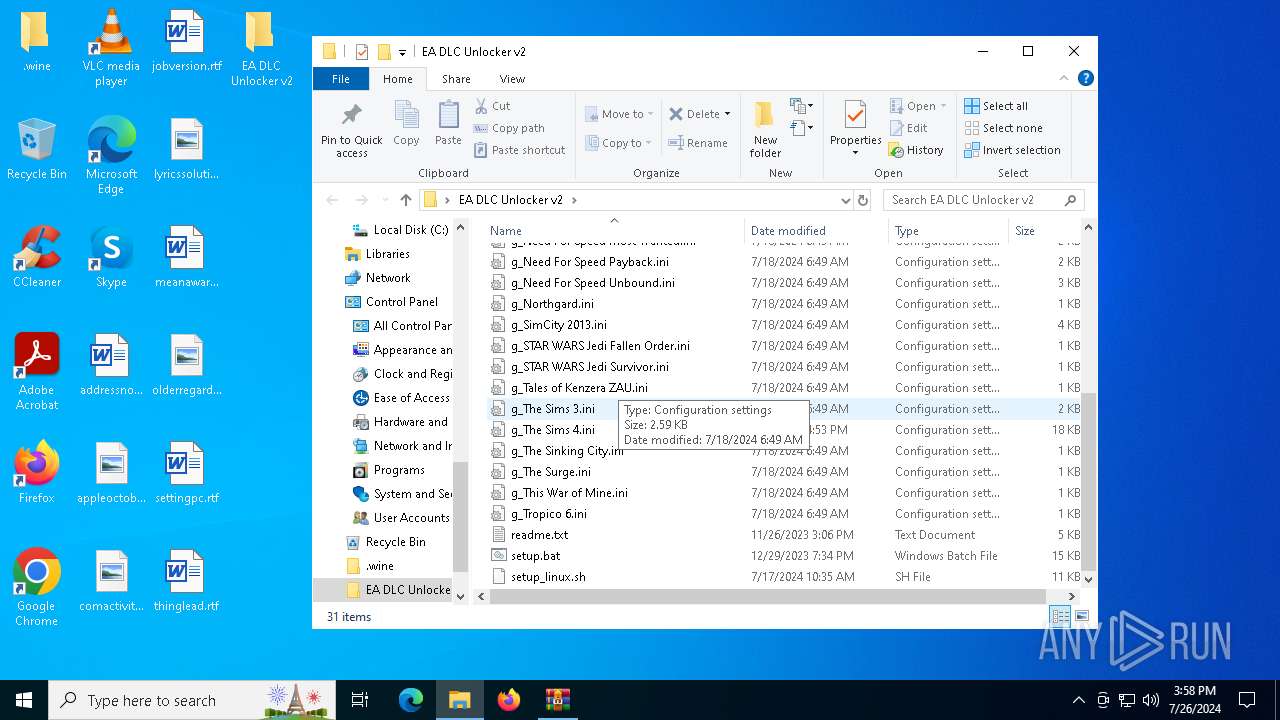
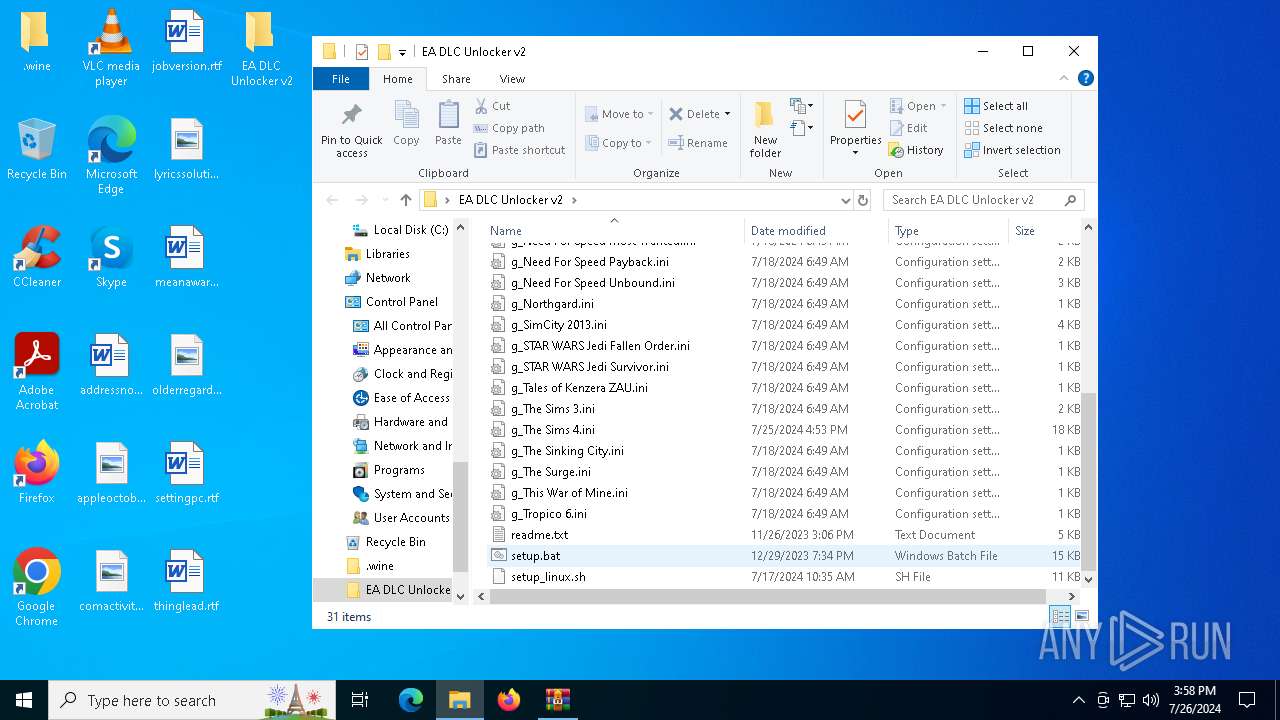
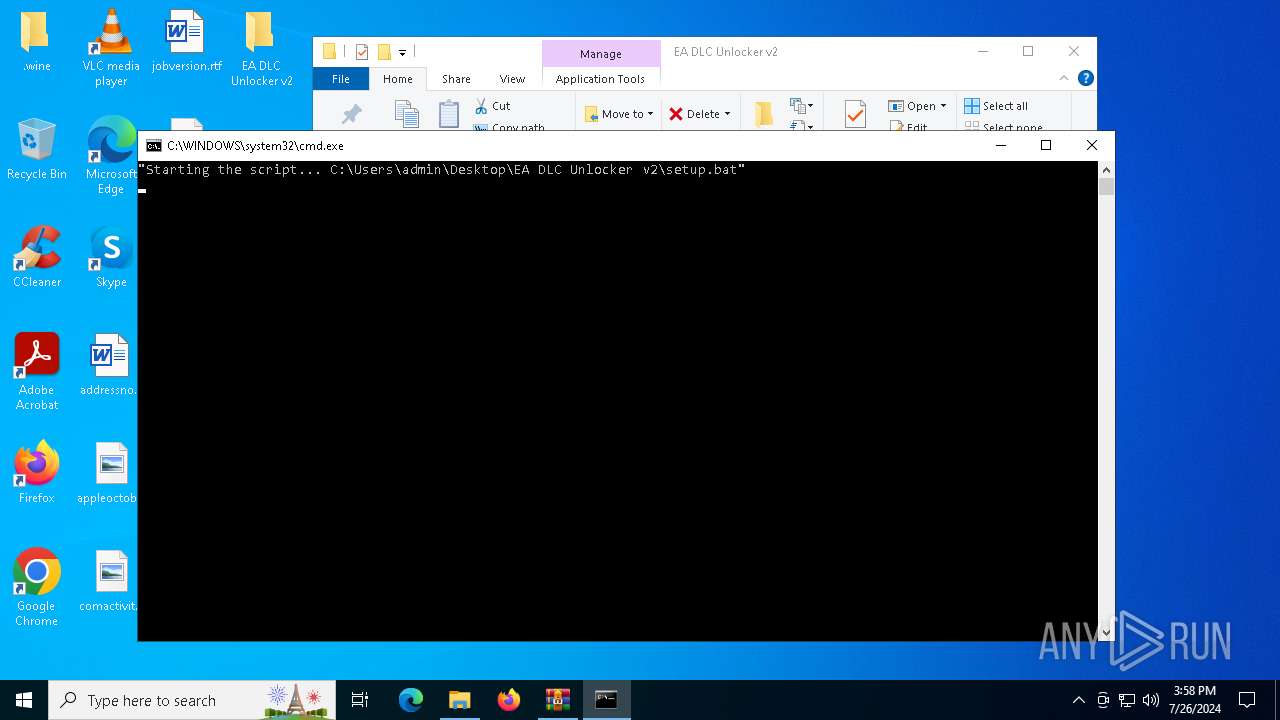
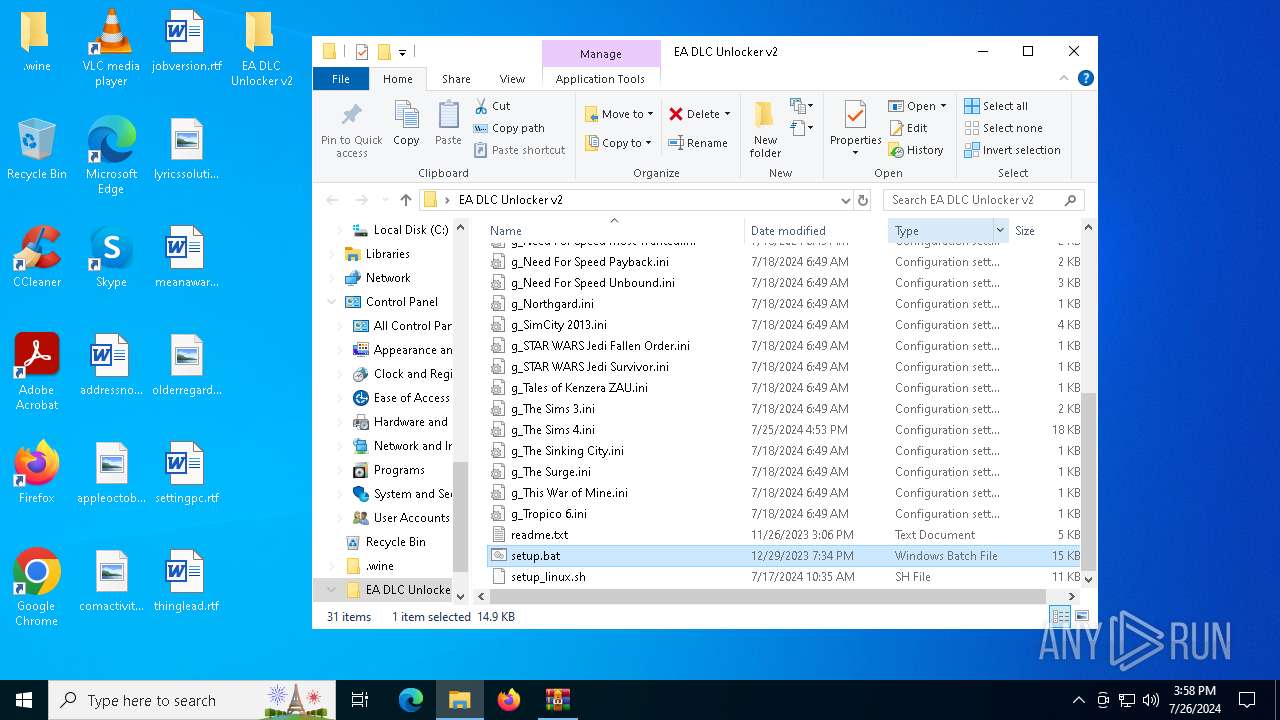
Executing commands from a ".bat" file
- WinRAR.exe (PID: 1516)
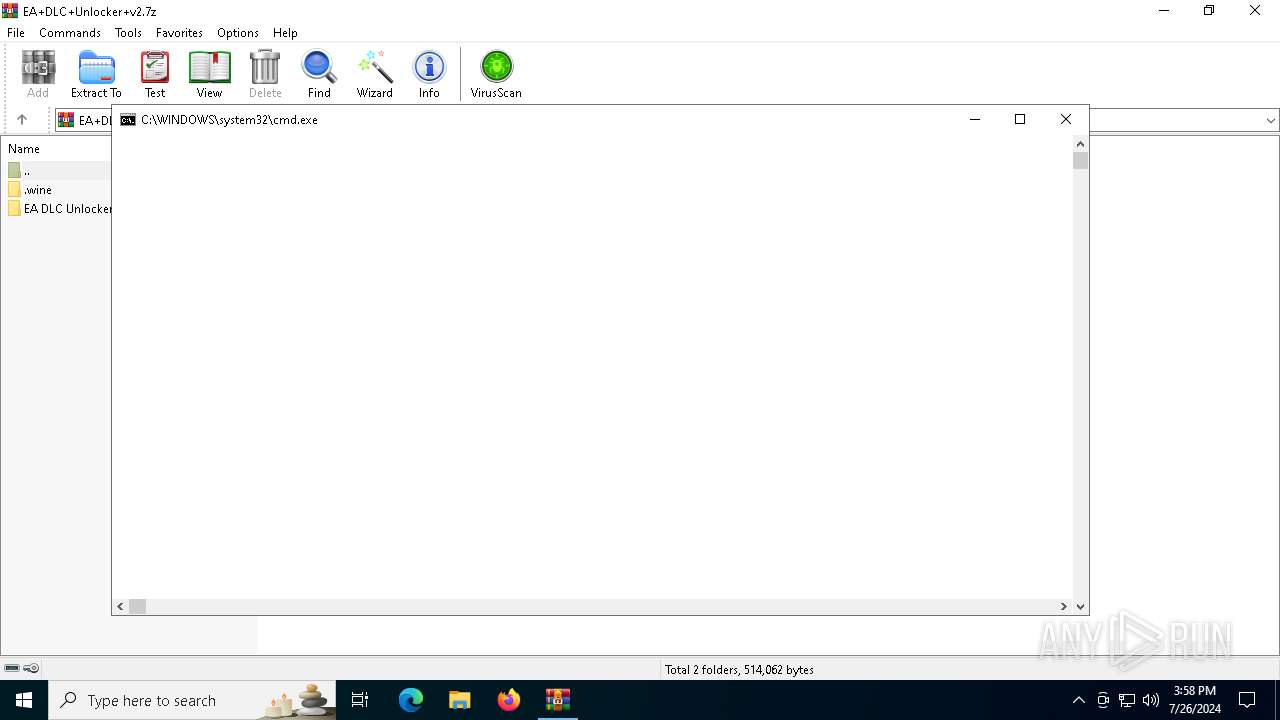
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 1516)
- cmd.exe (PID: 2976)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2976)
Application launched itself
- cmd.exe (PID: 2976)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2976)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2976)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2976)
INFO
Create files in a temporary directory
- MpCmdRun.exe (PID: 6164)
Reads the computer name
- MpCmdRun.exe (PID: 6164)
Manual execution by a user
- cmd.exe (PID: 2976)
Checks supported languages
- MpCmdRun.exe (PID: 6164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
155
Monitored processes
14
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
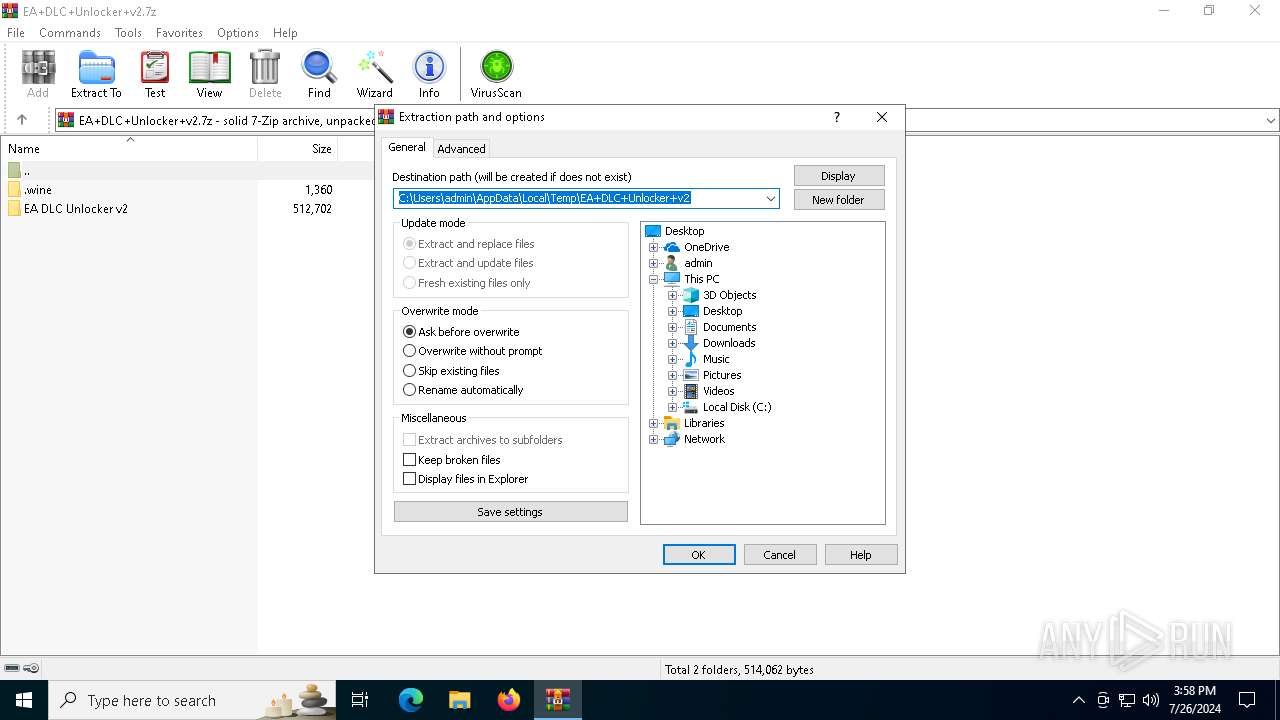
| 1516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\EA+DLC+Unlocker+v2.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1712 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\EA DLC Unlocker v2\setup.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | findstr /V /C:"polo" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3360 | findstr /C:"polo" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3392 | findstr /V /C:"C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4092 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\Rar$Scan6693.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4376 | powershell -noprofile "$_PSCommandPath = [Environment]::GetEnvironmentVariable('script_path', 'Process'); iex ((Get-Content -LiteralPath $_PSCommandPath) | out-string)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 200
Read events
11 182
Write events
18
Delete events
0
Modification events
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EA+DLC+Unlocker+v2.7z | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
| (PID) Process: | (1516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
1
Text files
64
Unknown types
0
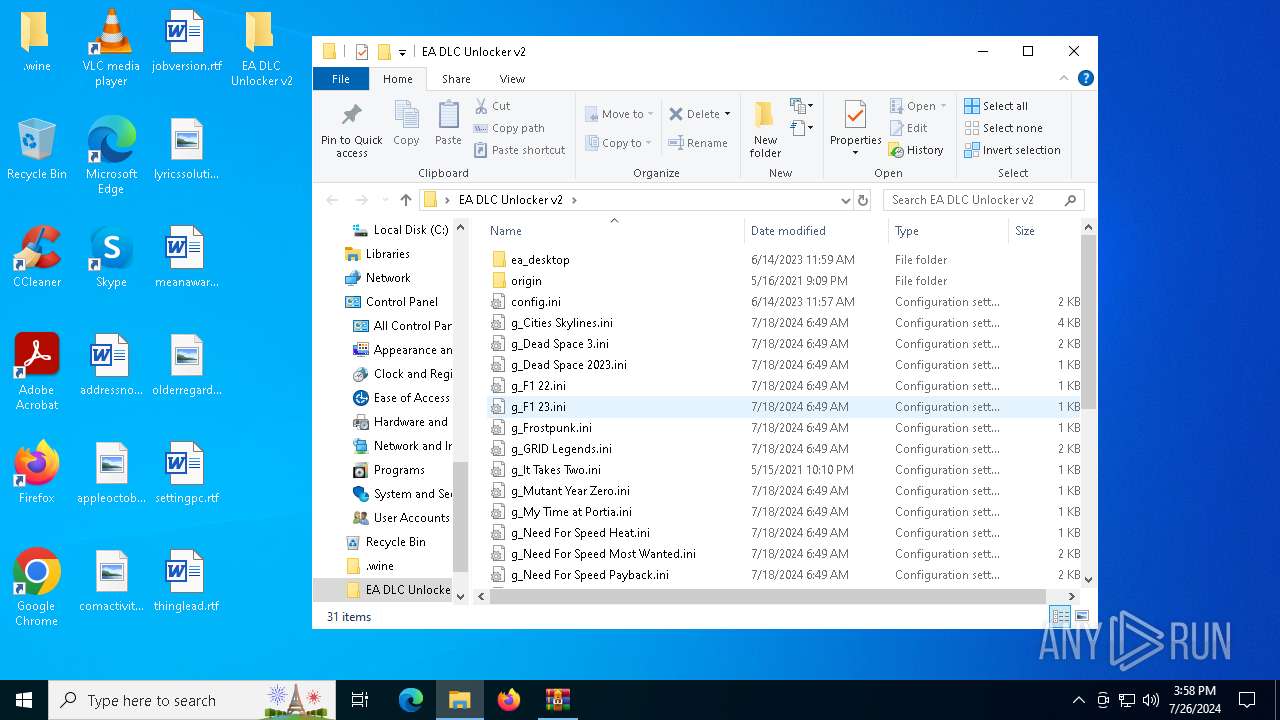
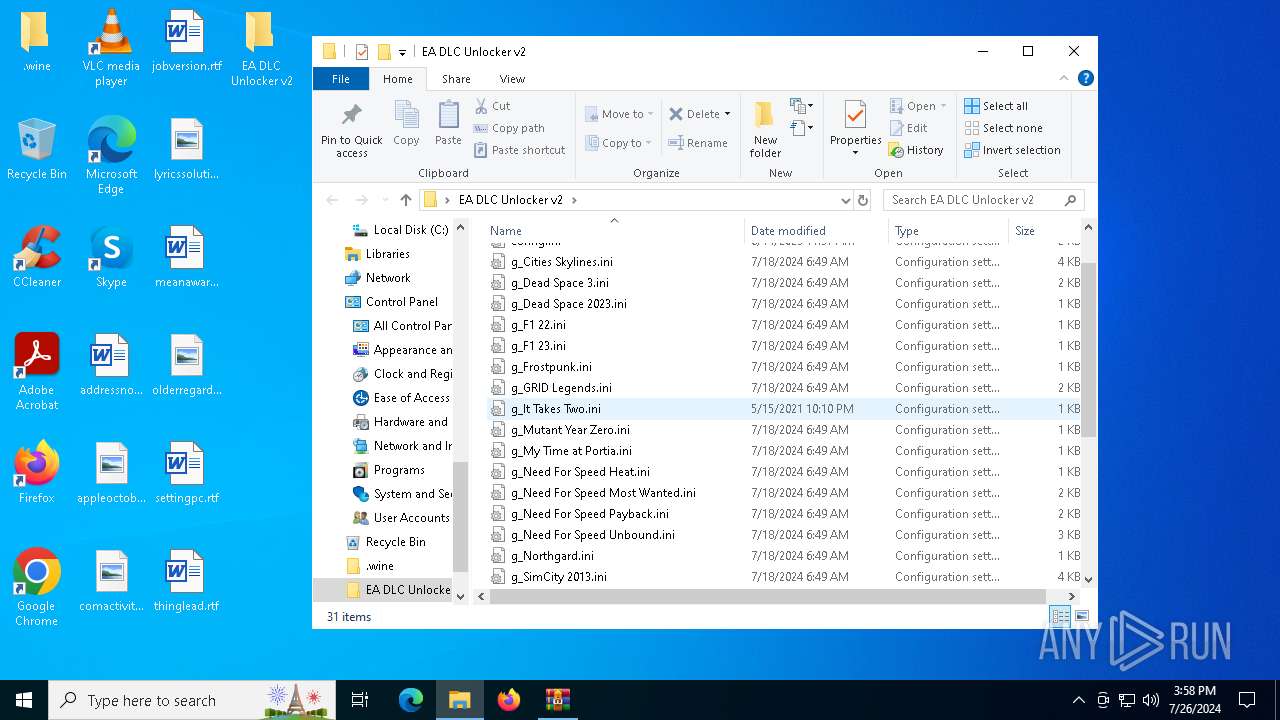
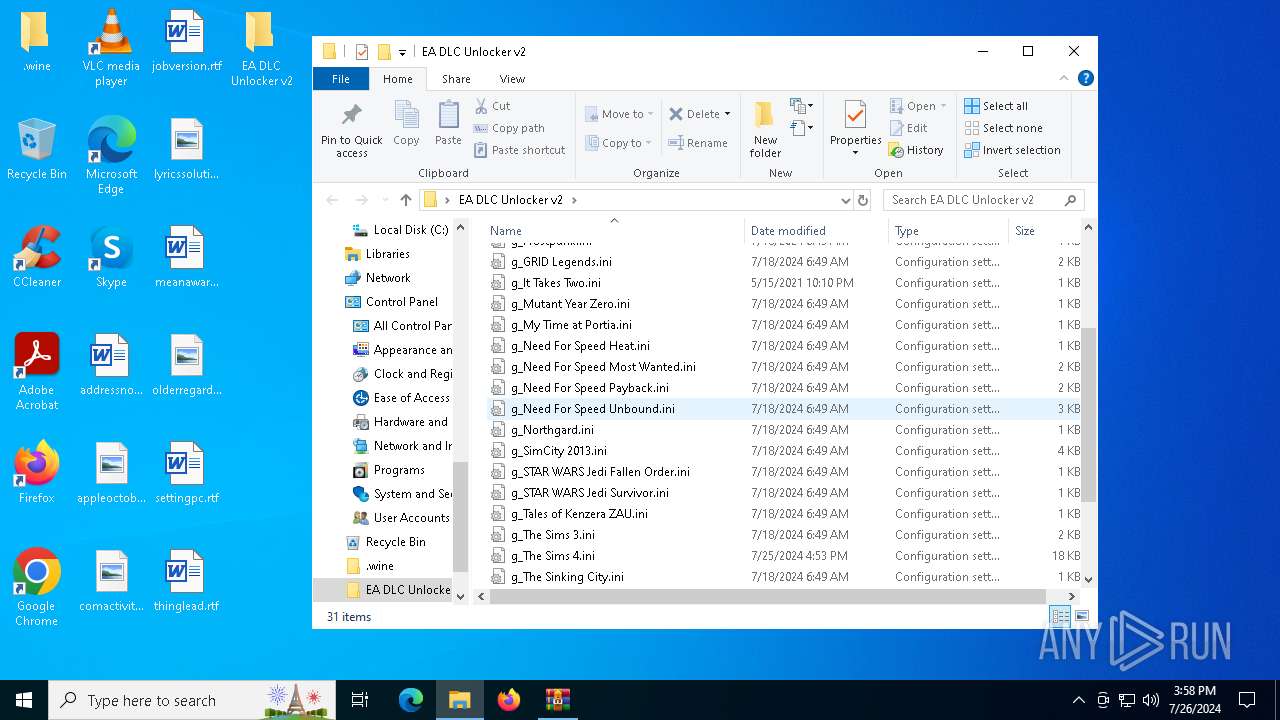
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
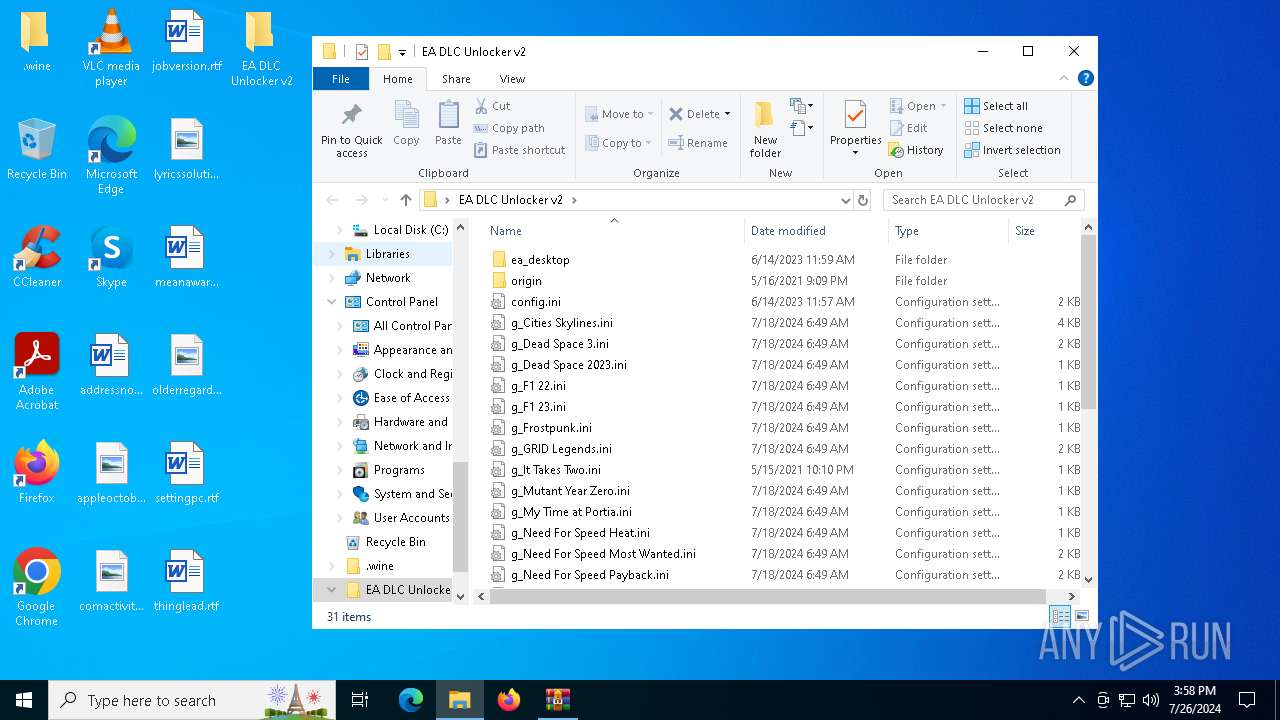
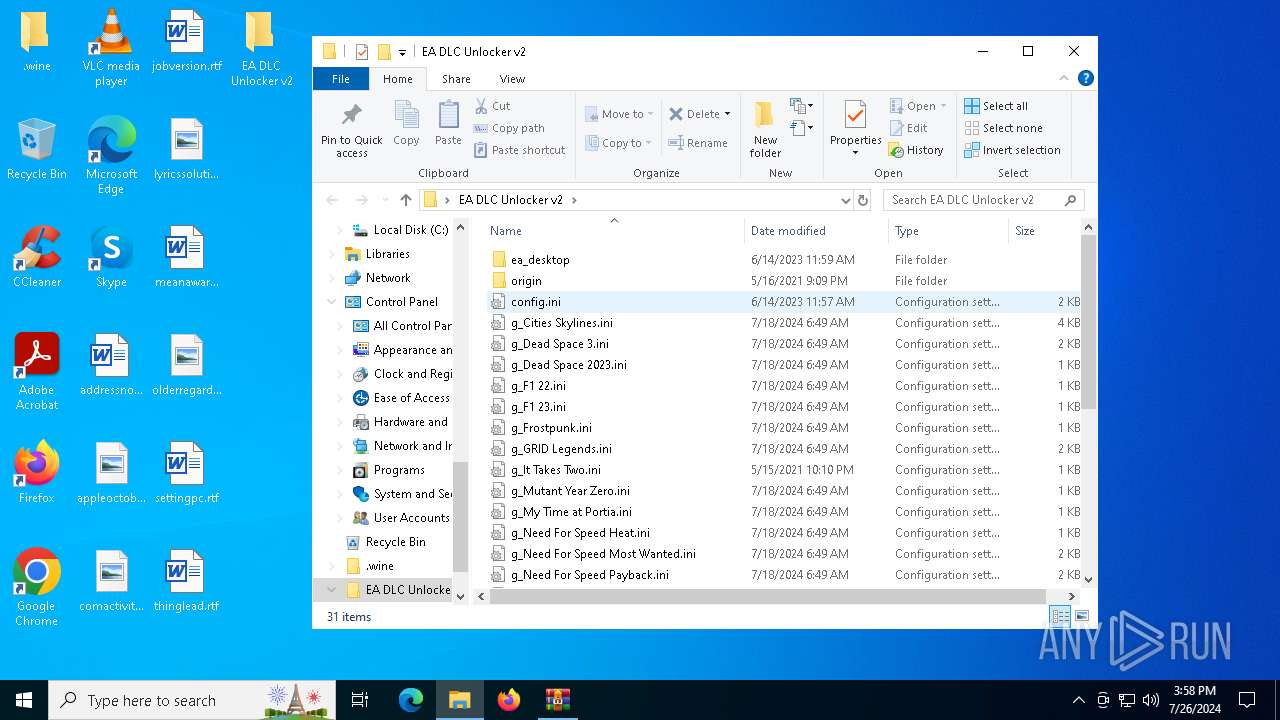
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_It Takes Two.ini | text | |
MD5:31561ACF01F495280B2E03EC26B7812F | SHA256:3435BE593EE7214A75789417B0B6E90FB7939B26DC43A8CCA197620E72EC48AF | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_Dead Space 3.ini | text | |
MD5:19F5DEDA4368C463D16687109ABF543D | SHA256:8996053E41CE56F0822A2A3E9449F3960FF1D395C6587ACDDB608AB306A3E6EE | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_Frostpunk.ini | text | |
MD5:FB2516CAACEBCDB02E9F2194BA72DE12 | SHA256:8A28296795FC669C047ED3AFBEB82791C4C86D3160B5A6843A144D814AE578C2 | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_F1 23.ini | text | |
MD5:18416EFA57D527355F065064172A821D | SHA256:CFBE14FC02F08A2B941DB25DE2379A5849CEDA301E529514004948D0088945FA | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_Dead Space 2023.ini | text | |
MD5:FC3F0C4D744A4310C775B2879399C468 | SHA256:934211FE00D6151381796B7001D7AEF5BC883DAA9F1B1F68AF60A7AF93EB1835 | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_My Time at Portia.ini | text | |
MD5:EDE7B7058E8C95575EF5517D36784FE2 | SHA256:D7812CD7633CBC13521C9D7A862541EB13A93A8F42D1E56137D4BE8D7225F90A | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_Cities Skylines.ini | text | |
MD5:B7F9BF30D6947AFF647B416DA0FD551F | SHA256:CCB99A4A44EAB034B26811D5E0902857667A73D113A246A67CCBF42517C3D65E | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_F1 22.ini | text | |
MD5:51FFF0FDF96929ECE2B1CA964D006550 | SHA256:8EE50A42AF9C0C5C2A9D520173B262C983E6DE716D5EB1C753687FF3170686DB | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\EA DLC Unlocker v2\g_Need For Speed Most Wanted.ini | text | |
MD5:53020D0FF8E79EE8305061D5D3964927 | SHA256:070AC609263921F4C91061F8C8DDD78A3305038EC3F13F4FE265AE715F2C0B89 | |||
| 1516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1516.30349\EA+DLC+Unlocker+v2.7z\.wine\drive_c\users\ubuntu\AppData\Roaming\anadius\EA DLC Unlocker v2\config.ini | ini | |
MD5:9CD8592F5B8934FEC8B47994C4FDA5B6 | SHA256:16C7A3A47096394E59F204FAB91360F71AA2157BB1EDCFCCF1824B3A0D9352FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
39
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7004 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3688 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 2.16.110.137:443 | www.bing.com | Akamai International B.V. | DE | unknown |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5284 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5080 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |