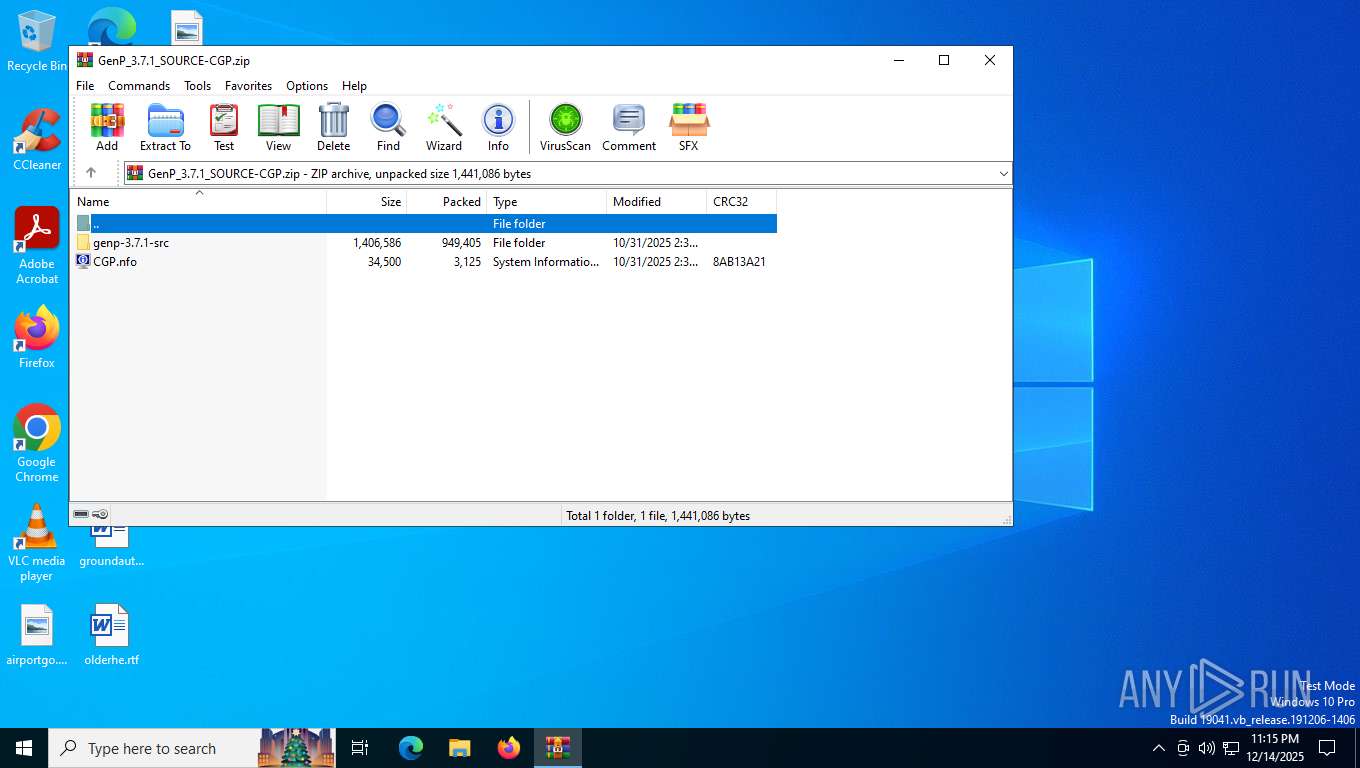
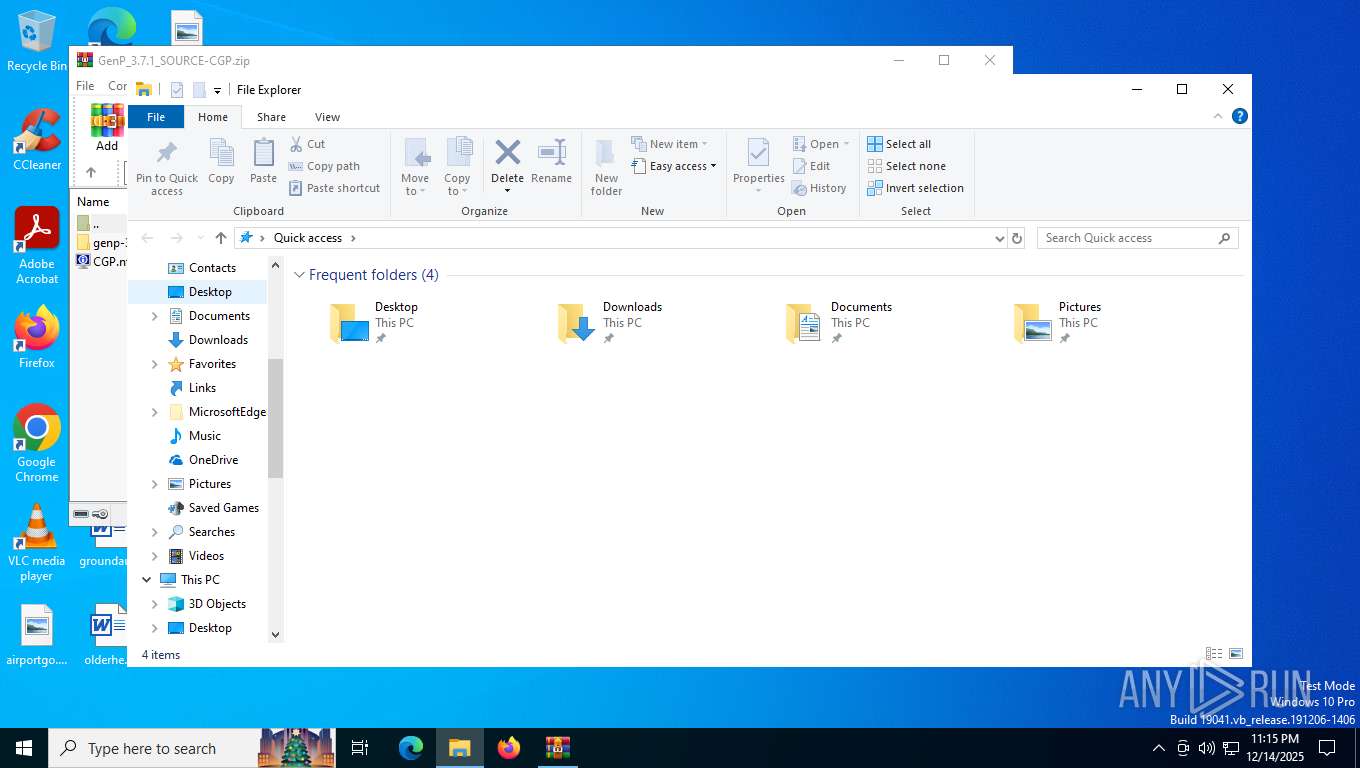
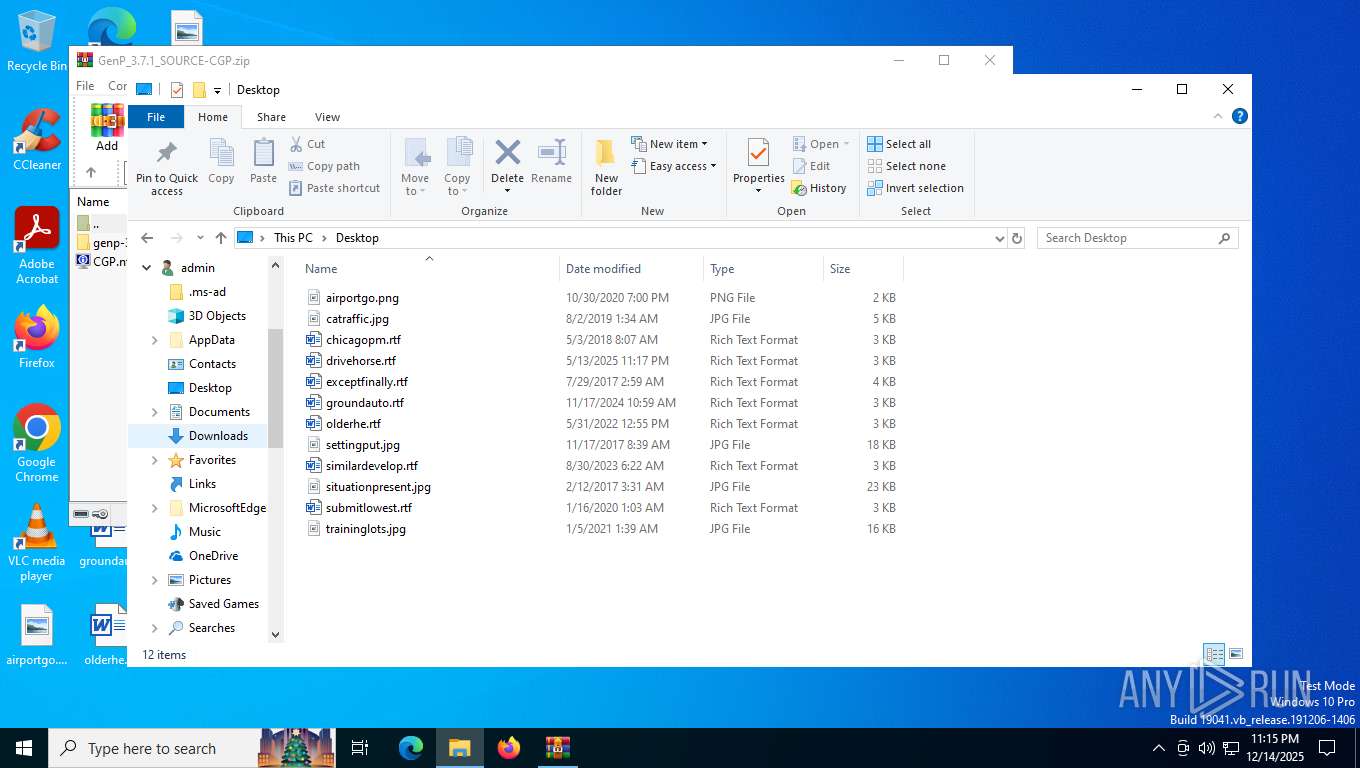
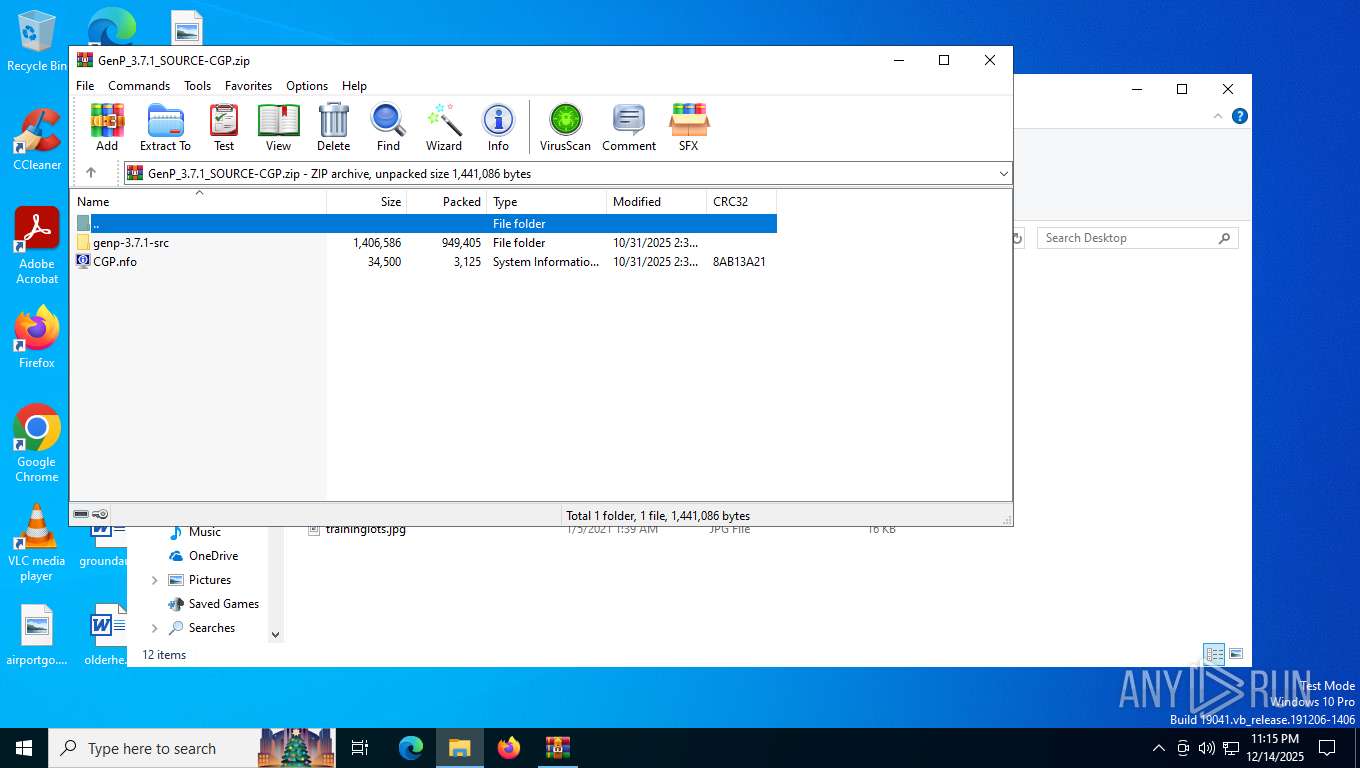
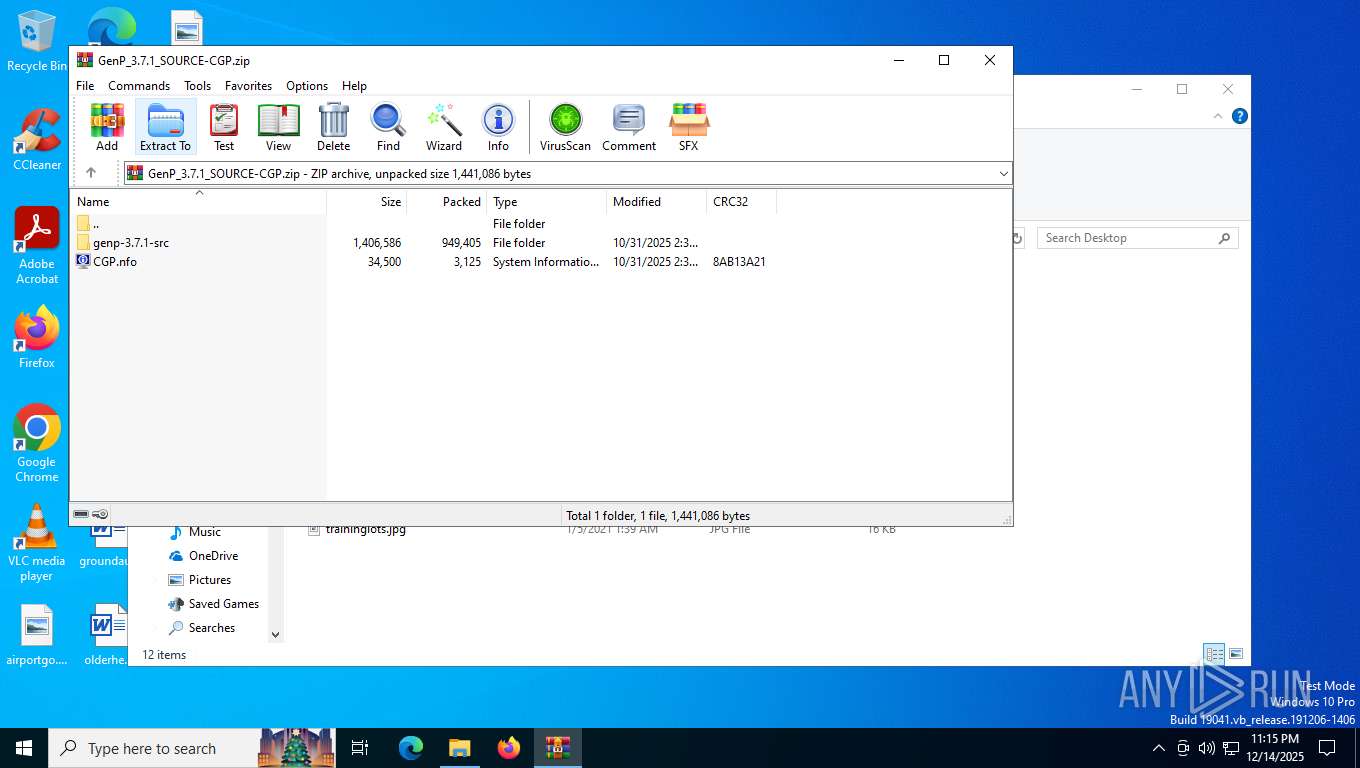
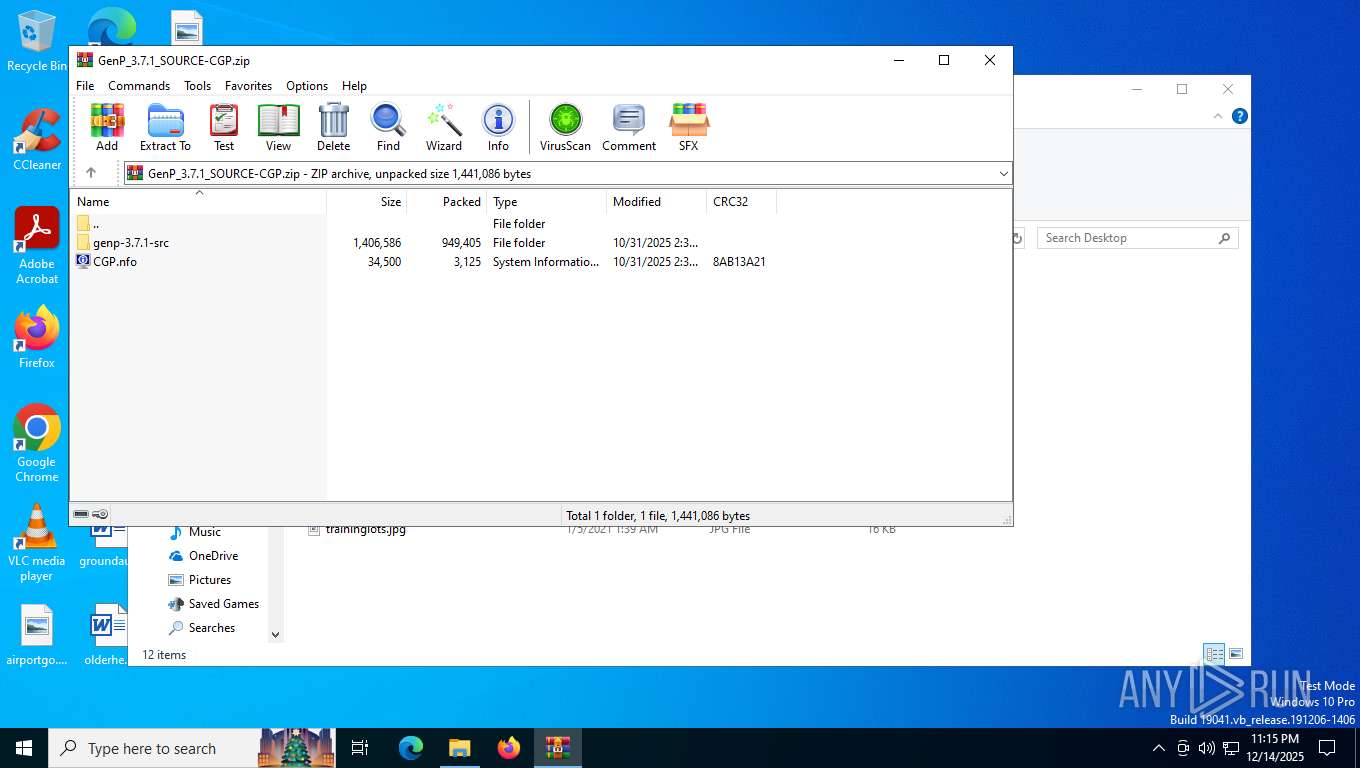
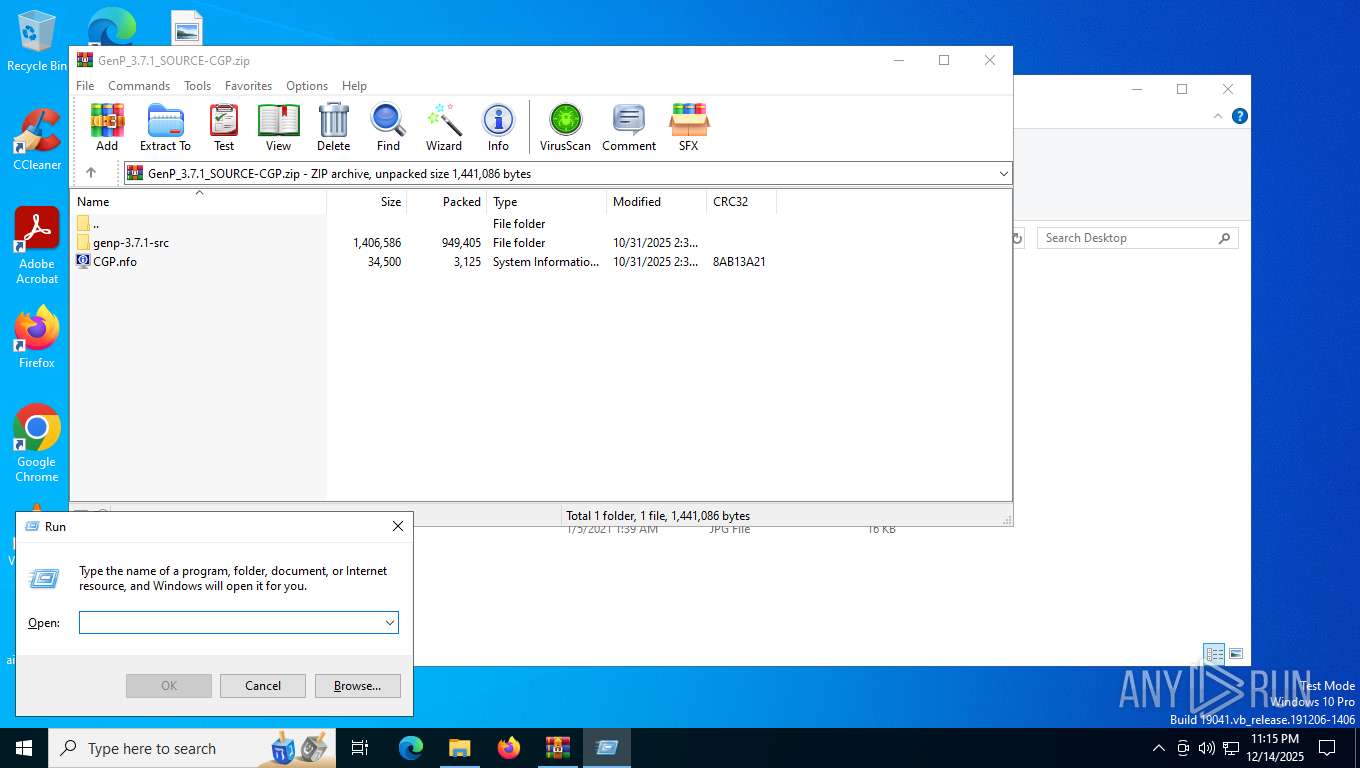
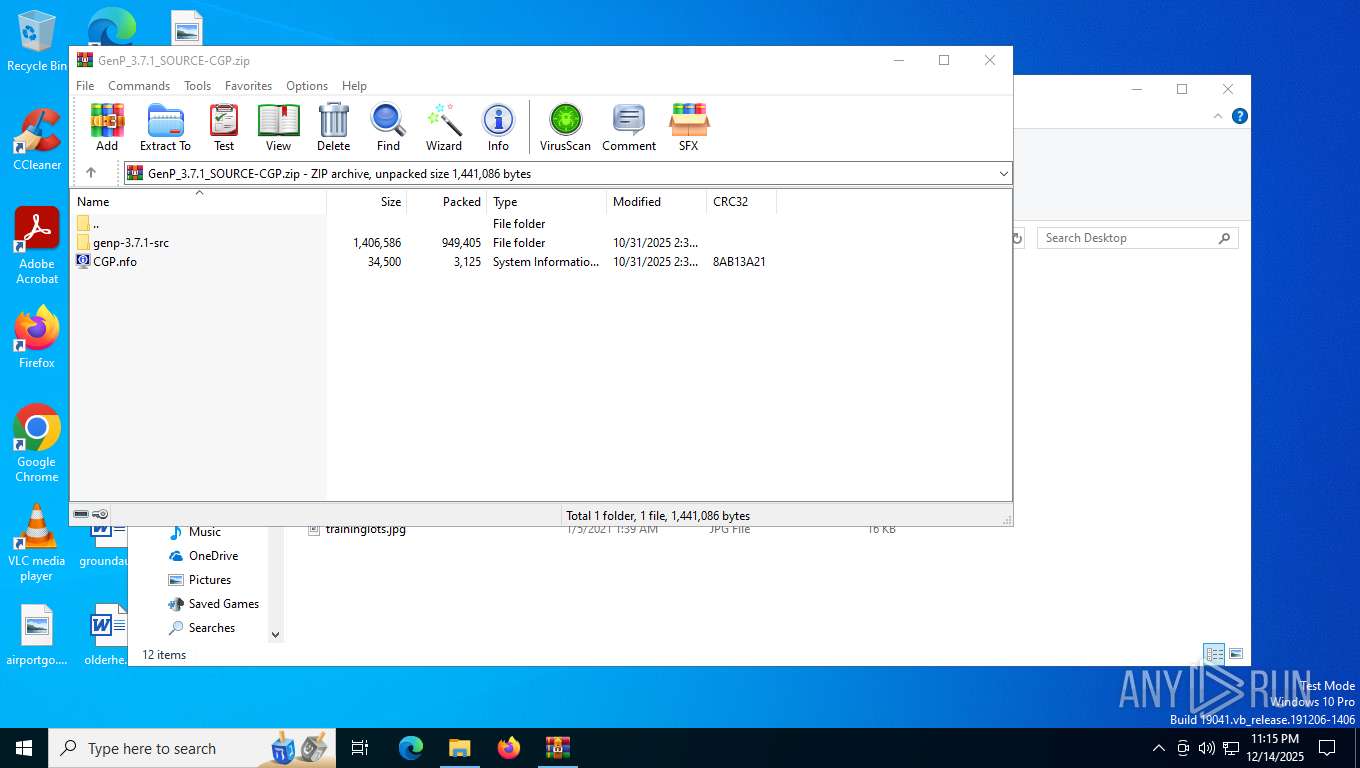
| File name: | GenP_3.7.1_SOURCE-CGP.zip |
| Full analysis: | https://app.any.run/tasks/fccde5a4-d7ae-4c55-a565-4dc4d1fe9c0c |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2025, 23:14:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 05F4A321A35AE3A72A9D08E7A3D6DC44 |
| SHA1: | EAA00446C15543E3298DA23EC79641F3E398180F |
| SHA256: | C10E71965AB11ADC57D641DEE97AFF3E535E3ABFAAD5A1DDC66F04B12D9BCCAC |
| SSDEEP: | 49152:xL1AmiLtKRwWBOEsB5YrAMmqUaPP84ORUva/lJGHw1p6v1EGSBsCLlEIBDrOBCQ7:xLumUtKRBB3c5YrA7qBPLMEelkJv1EJC |
MALICIOUS
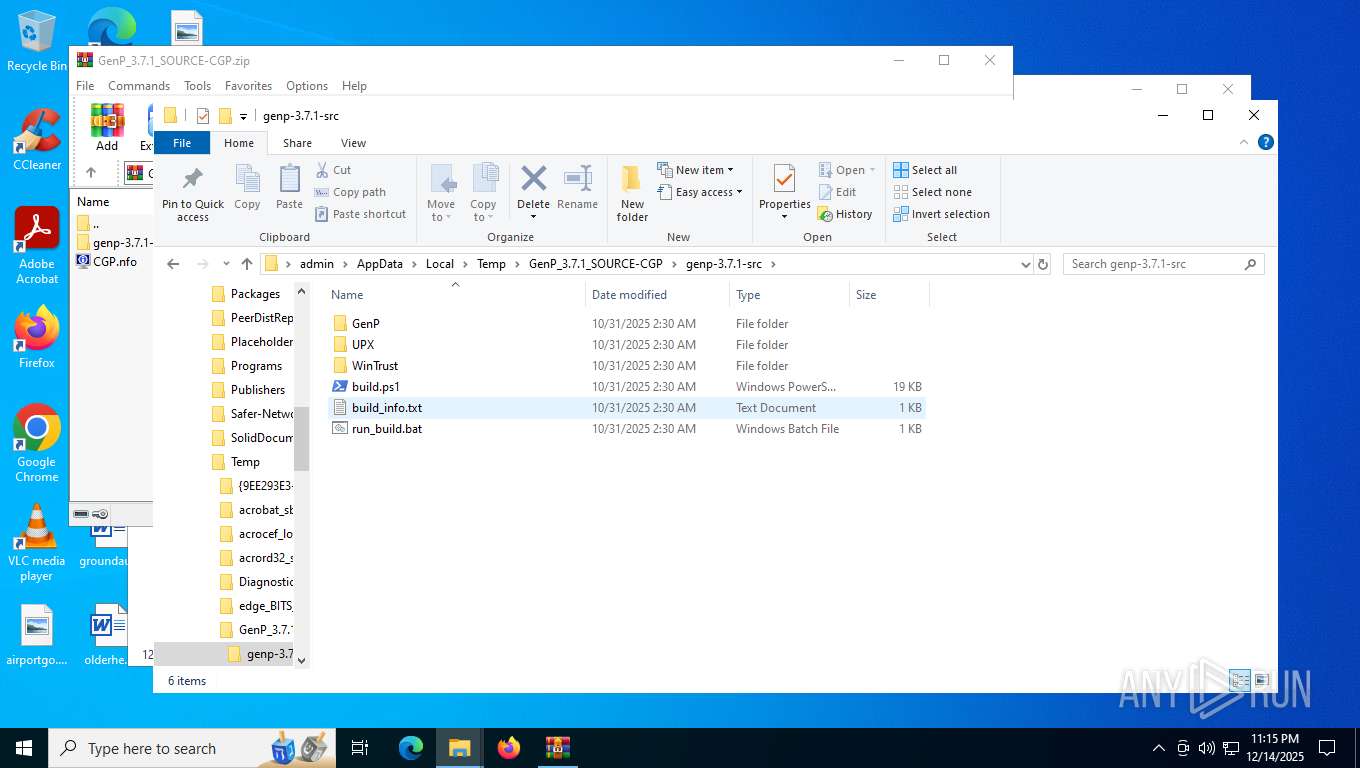
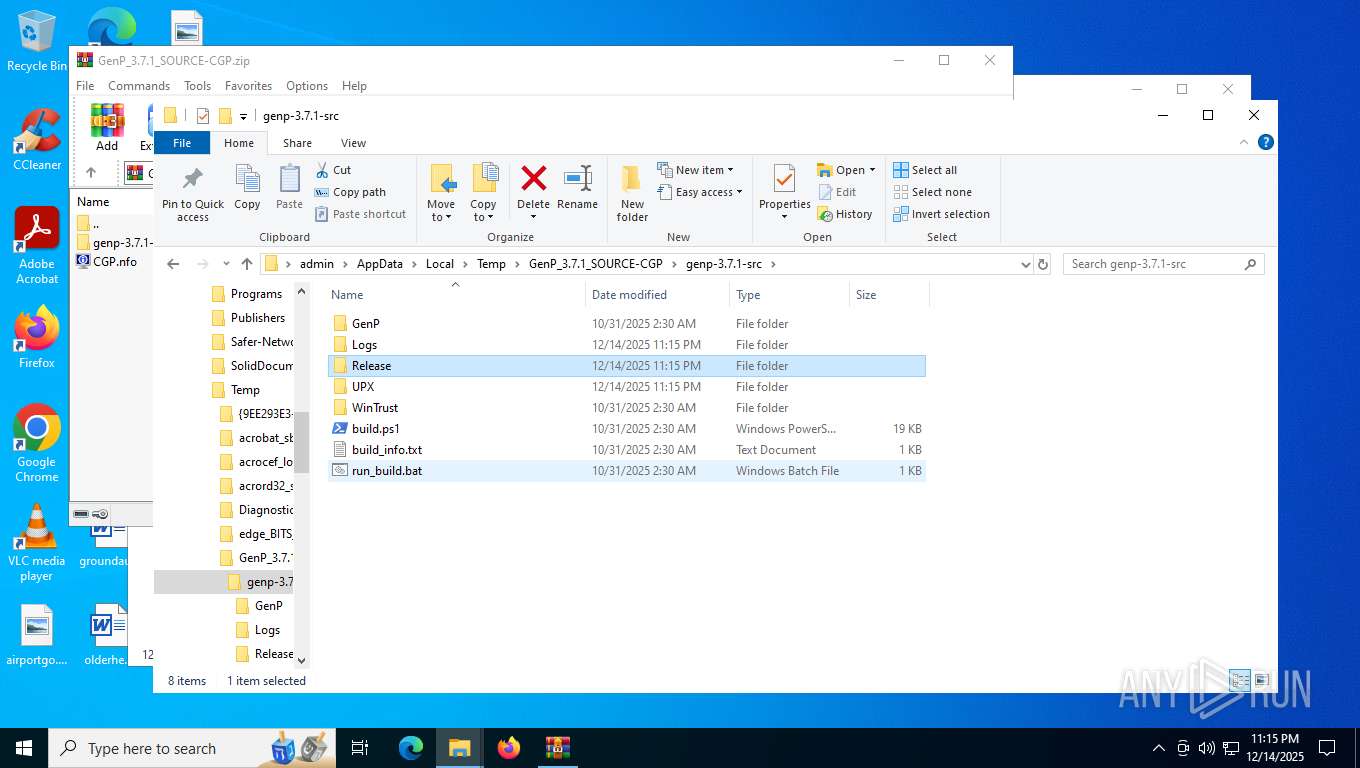
Generic archive extractor
- WinRAR.exe (PID: 7512)
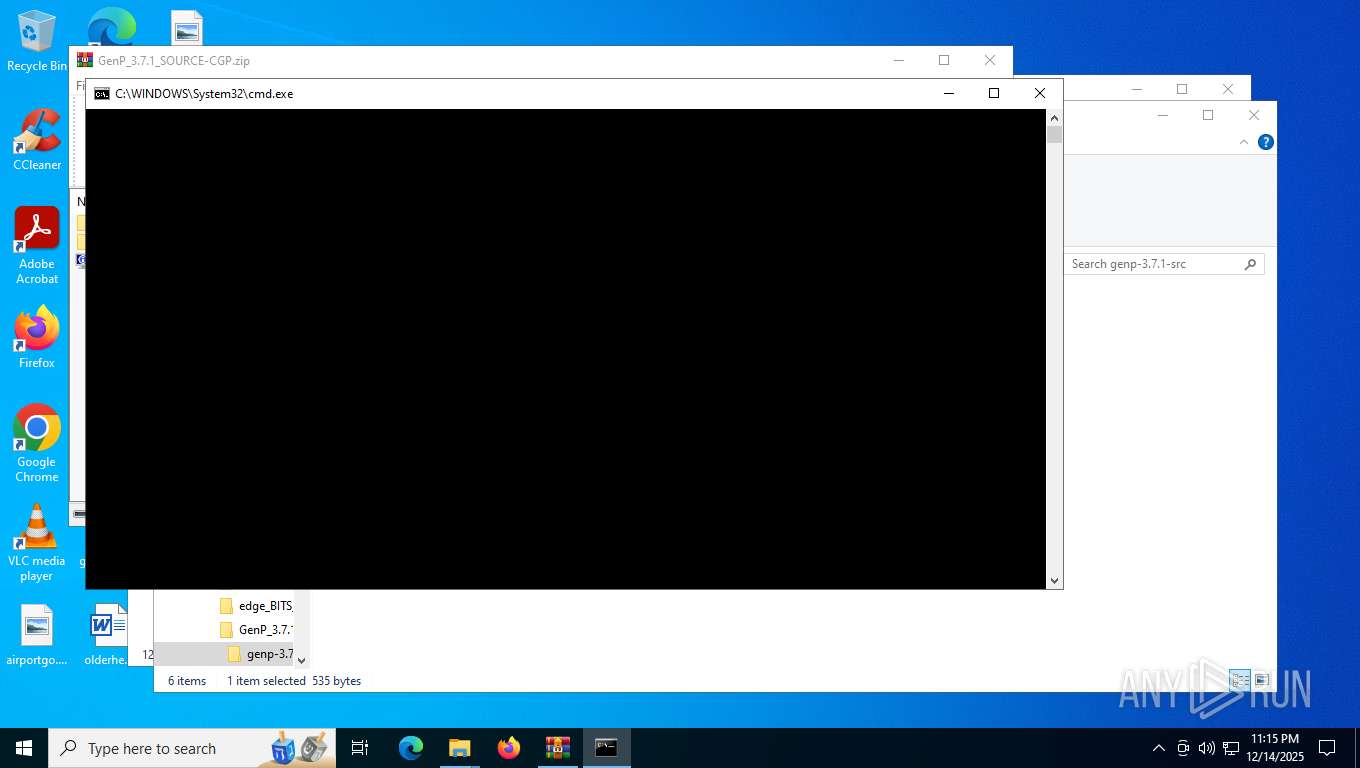
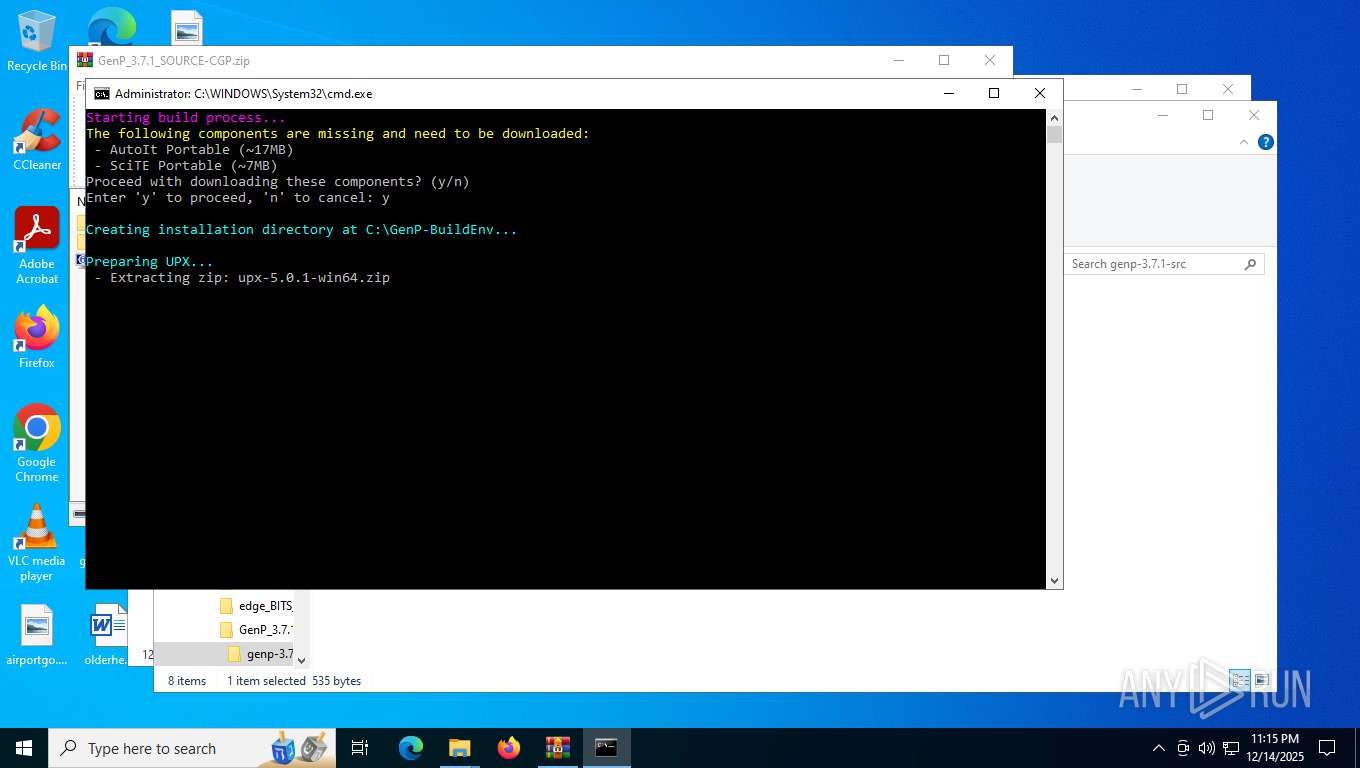
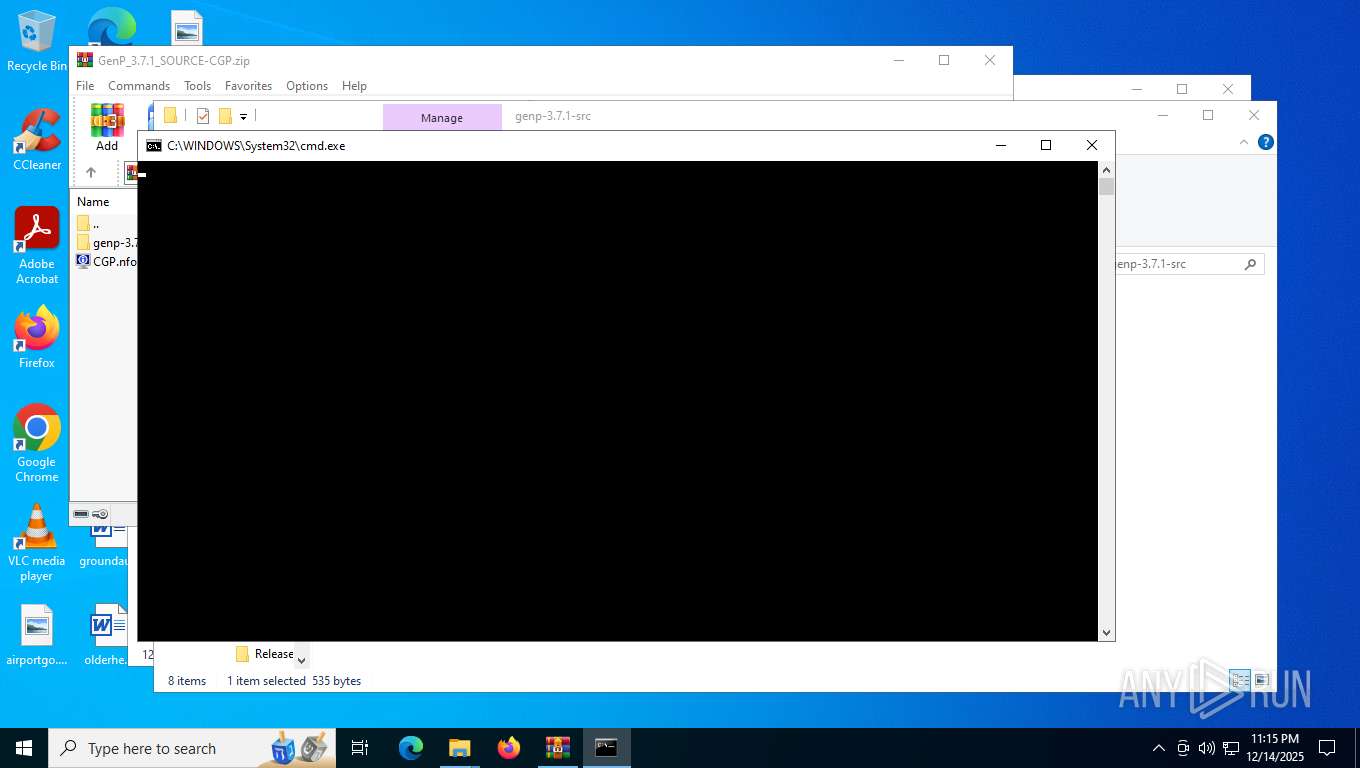
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 8096)
- powershell.exe (PID: 948)
Bypass execution policy to execute commands
- powershell.exe (PID: 7988)
- powershell.exe (PID: 948)
- powershell.exe (PID: 7224)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7512)
- powershell.exe (PID: 7224)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7872)
- net.exe (PID: 7880)
- cmd.exe (PID: 8096)
- net.exe (PID: 7376)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7872)
- cmd.exe (PID: 8096)
- powershell.exe (PID: 948)
The process executes Powershell scripts
- cmd.exe (PID: 7872)
- cmd.exe (PID: 8096)
- powershell.exe (PID: 948)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 948)
Application launched itself
- powershell.exe (PID: 948)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7224)
Executable content was dropped or overwritten
- powershell.exe (PID: 7224)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7512)
The sample compiled with english language support
- WinRAR.exe (PID: 7512)
- powershell.exe (PID: 7224)
Checks supported languages
- TextInputHost.exe (PID: 7444)
- tar.exe (PID: 7832)
Reads the computer name
- TextInputHost.exe (PID: 7444)
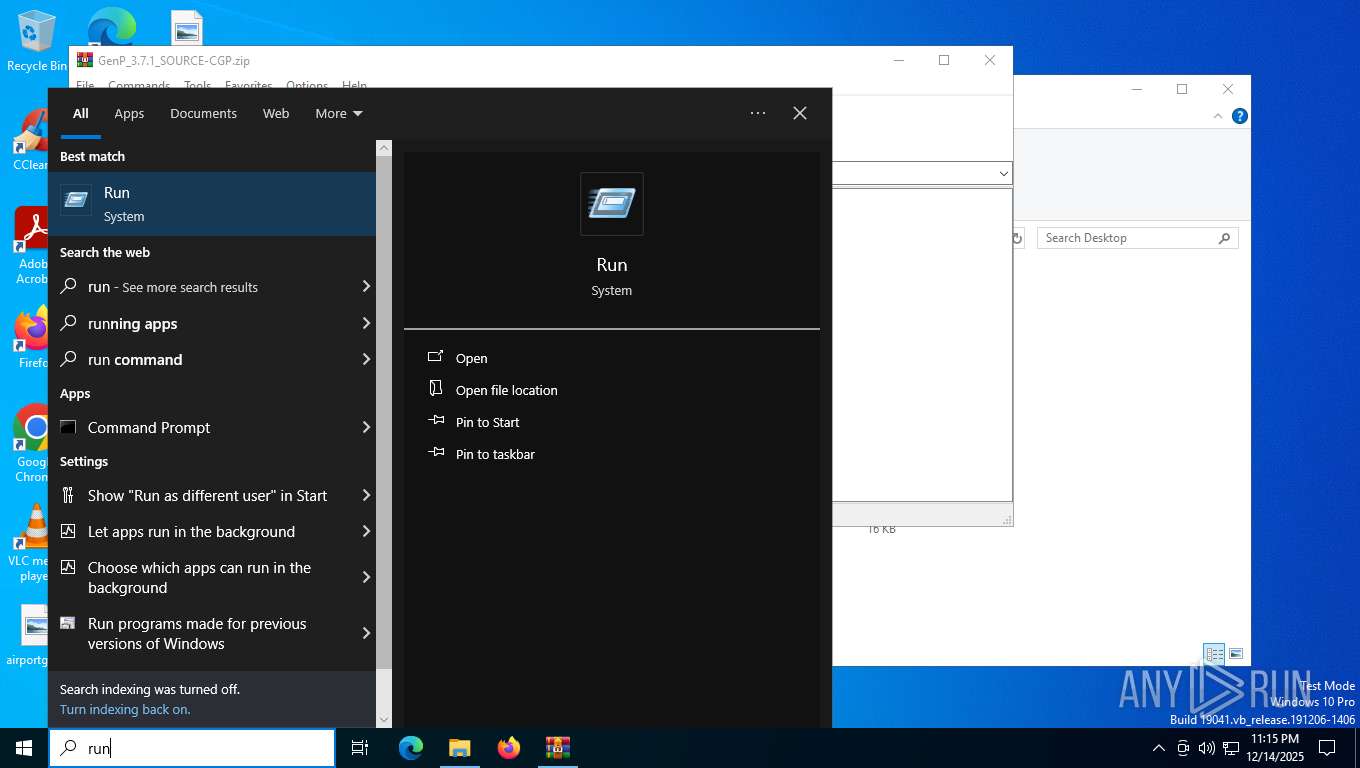
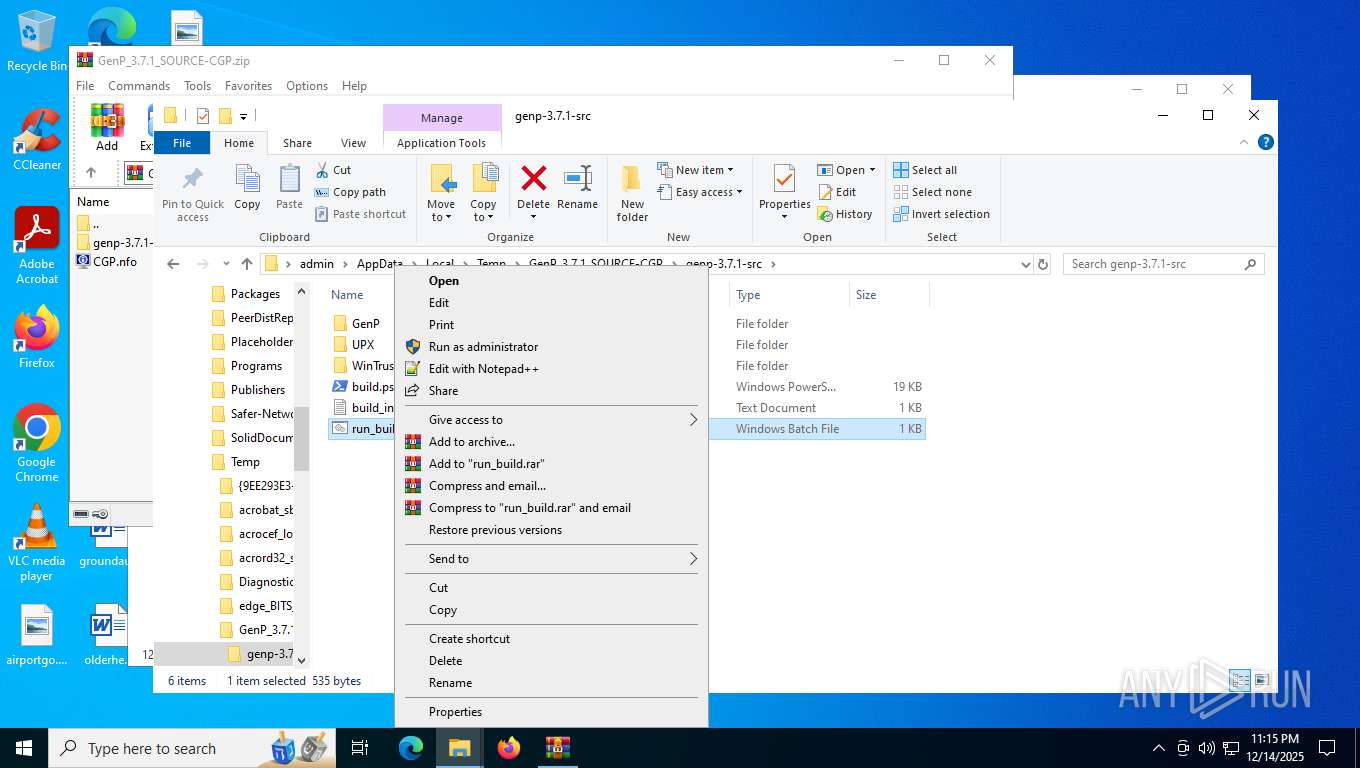
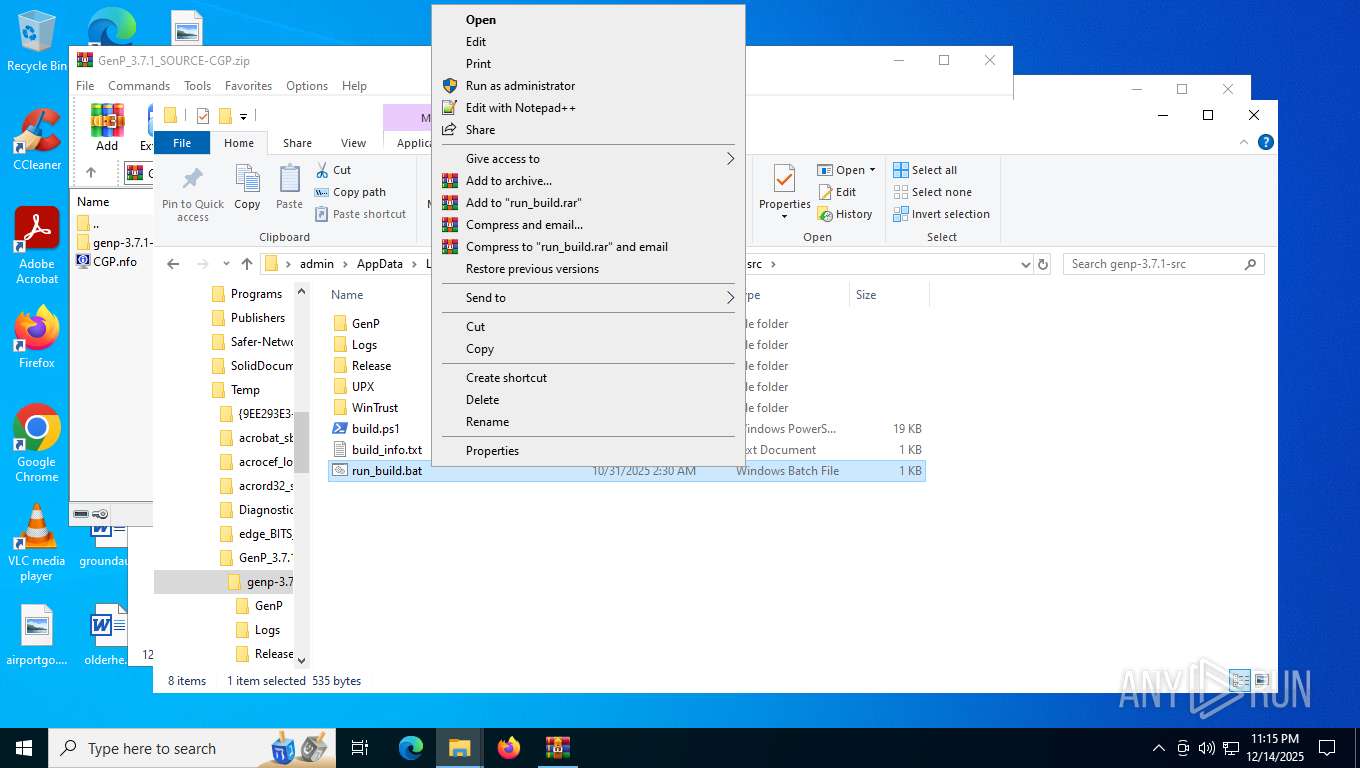
Manual execution by a user
- cmd.exe (PID: 7872)
- cmd.exe (PID: 8096)
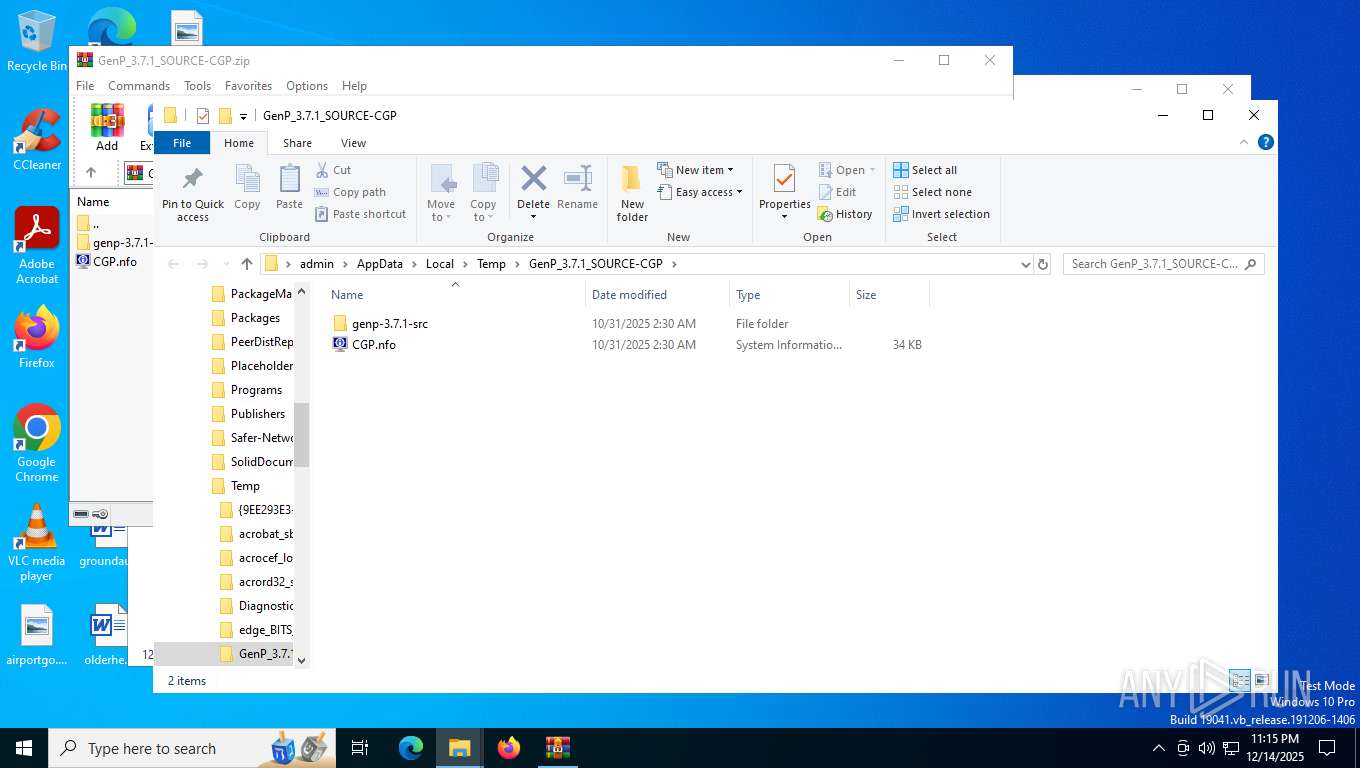
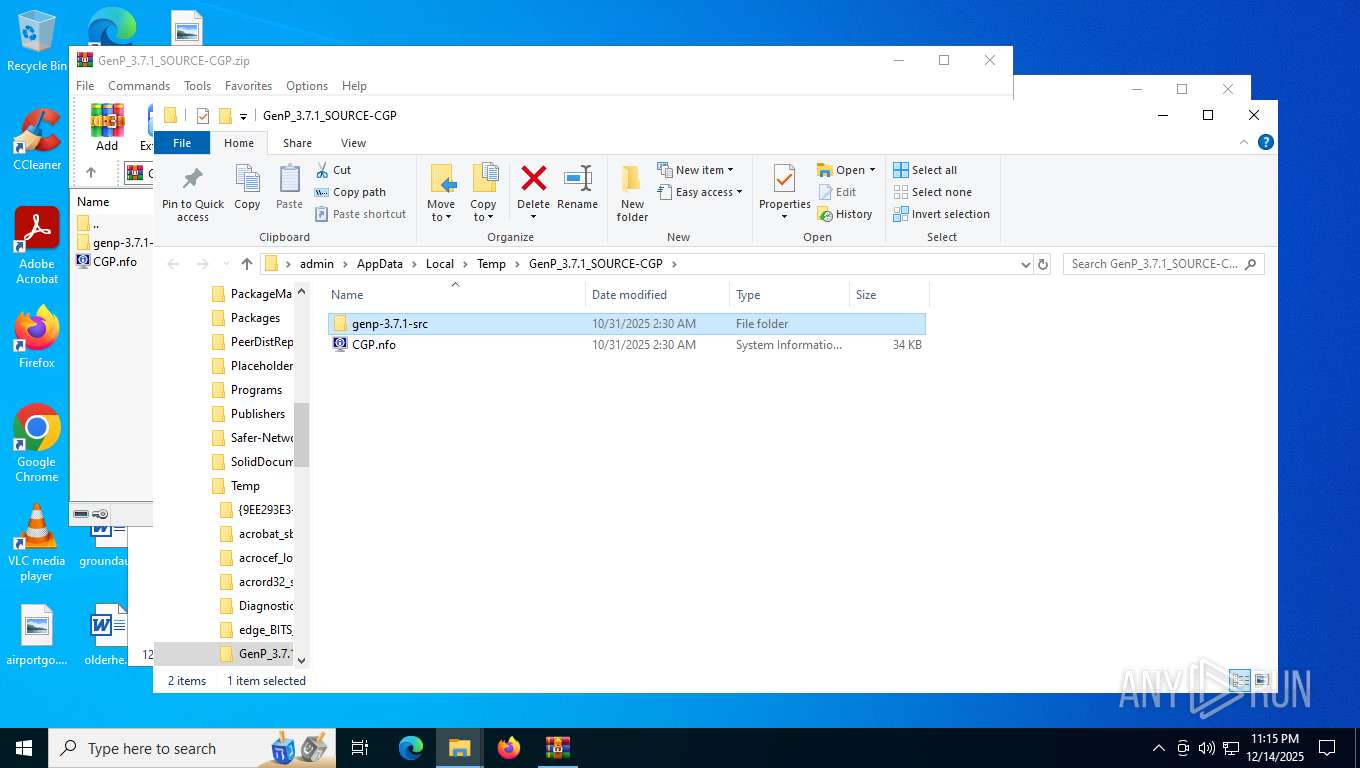
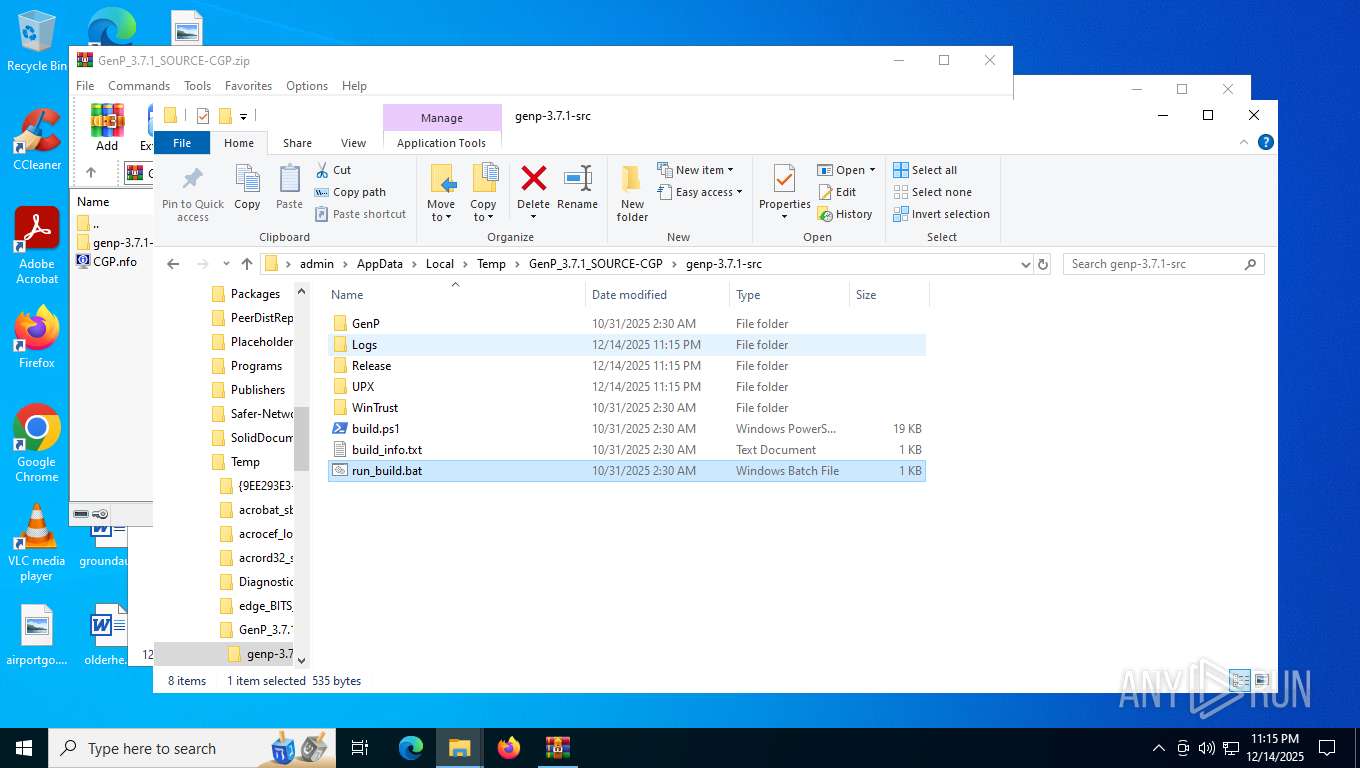
Create files in a temporary directory
- tar.exe (PID: 7832)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:10:31 06:30:30 |
| ZipCRC: | 0x8ab13a21 |
| ZipCompressedSize: | 3125 |
| ZipUncompressedSize: | 34500 |
| ZipFileName: | CGP.nfo |
Total processes
161
Monitored processes
16
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
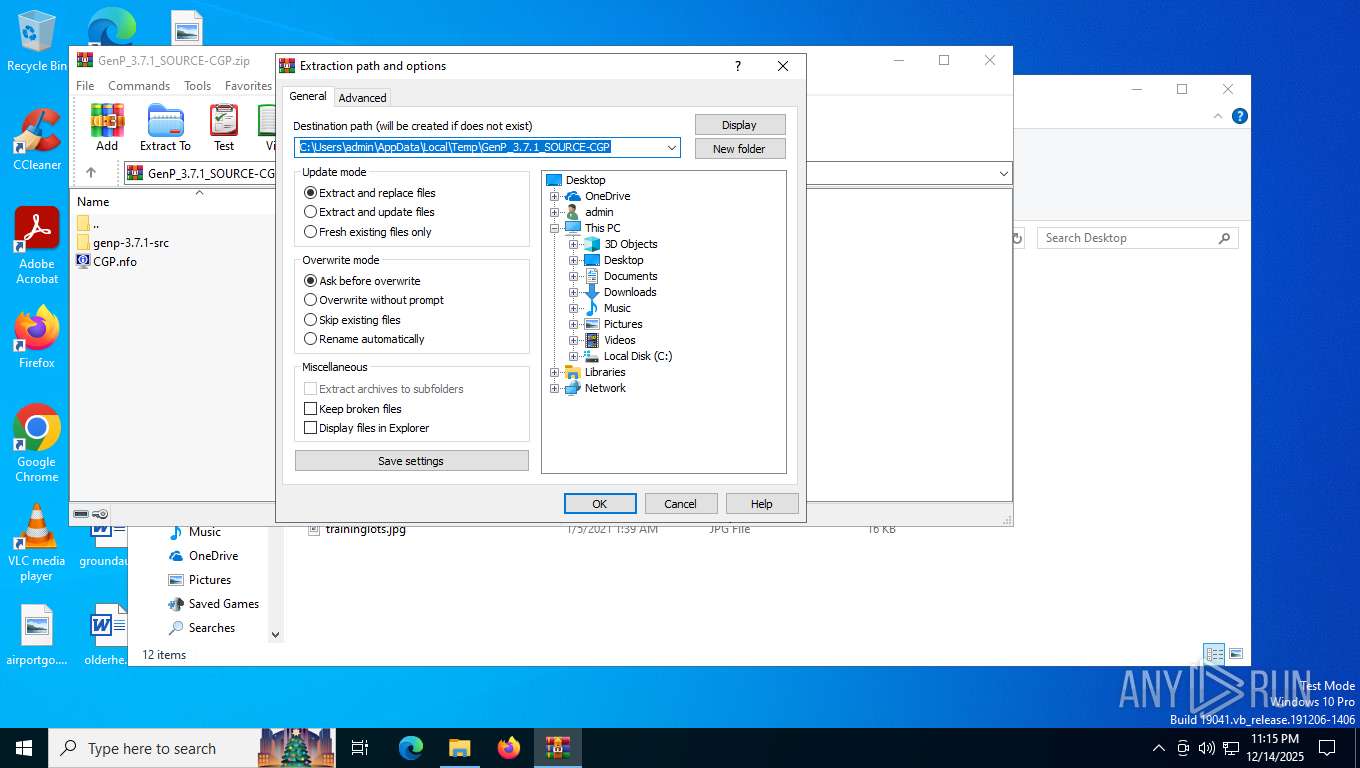
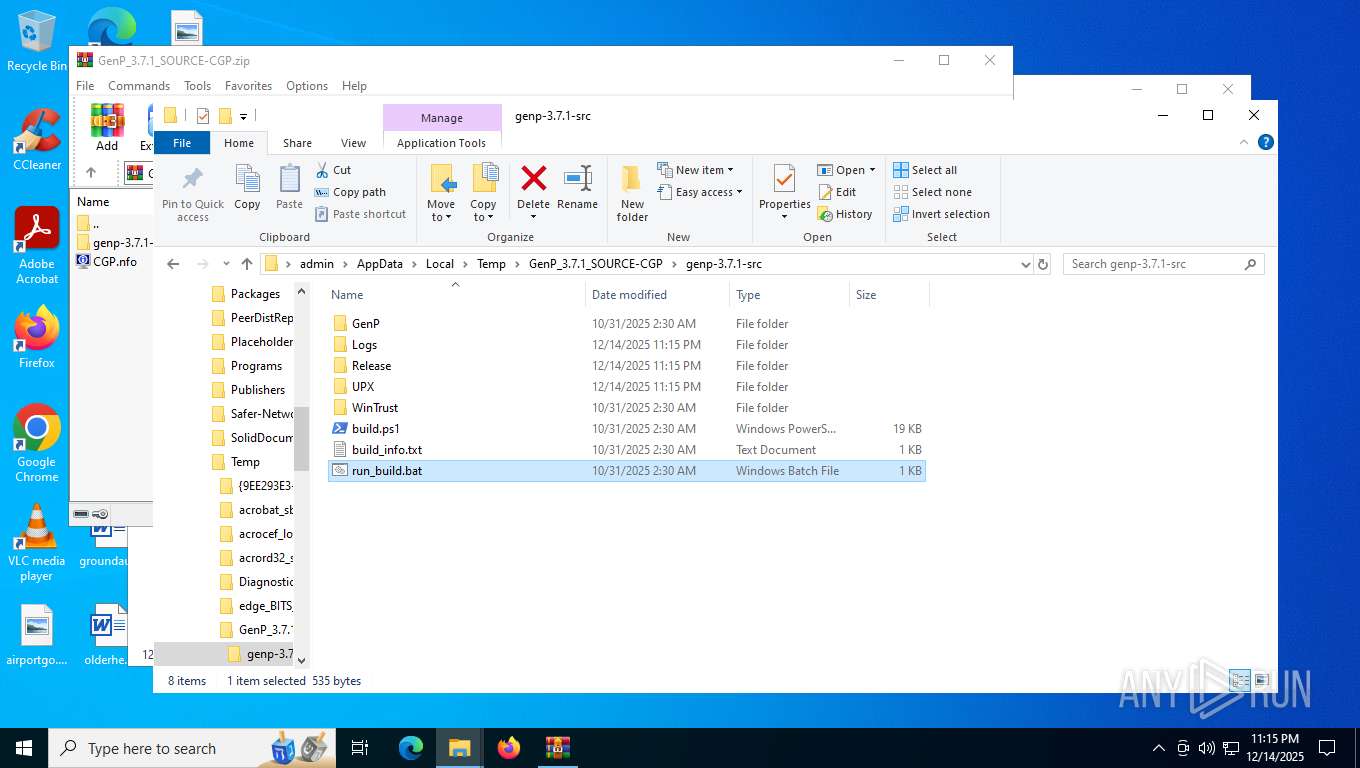
| 948 | powershell.exe -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\build.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2912 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5844 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6060 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
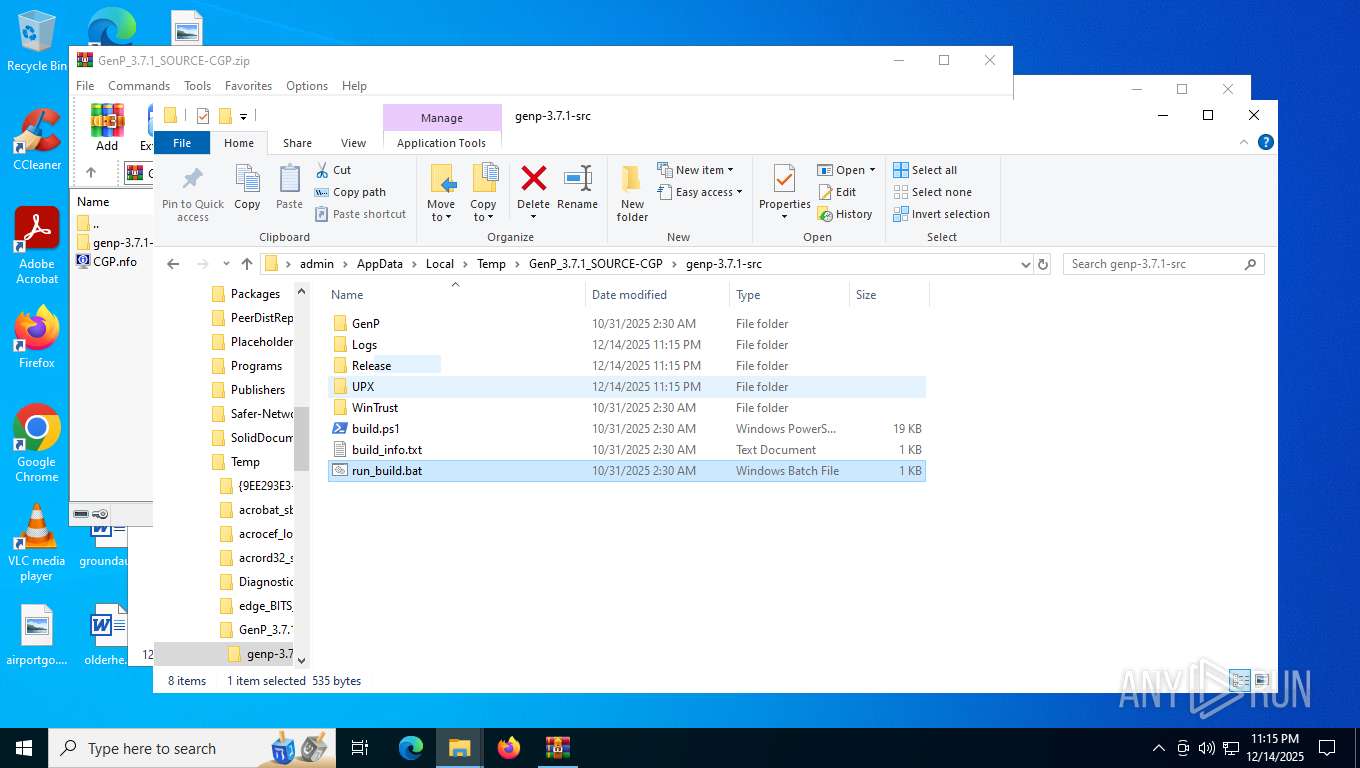
| 7224 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\WinTrust\patch_wintrust.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7444 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
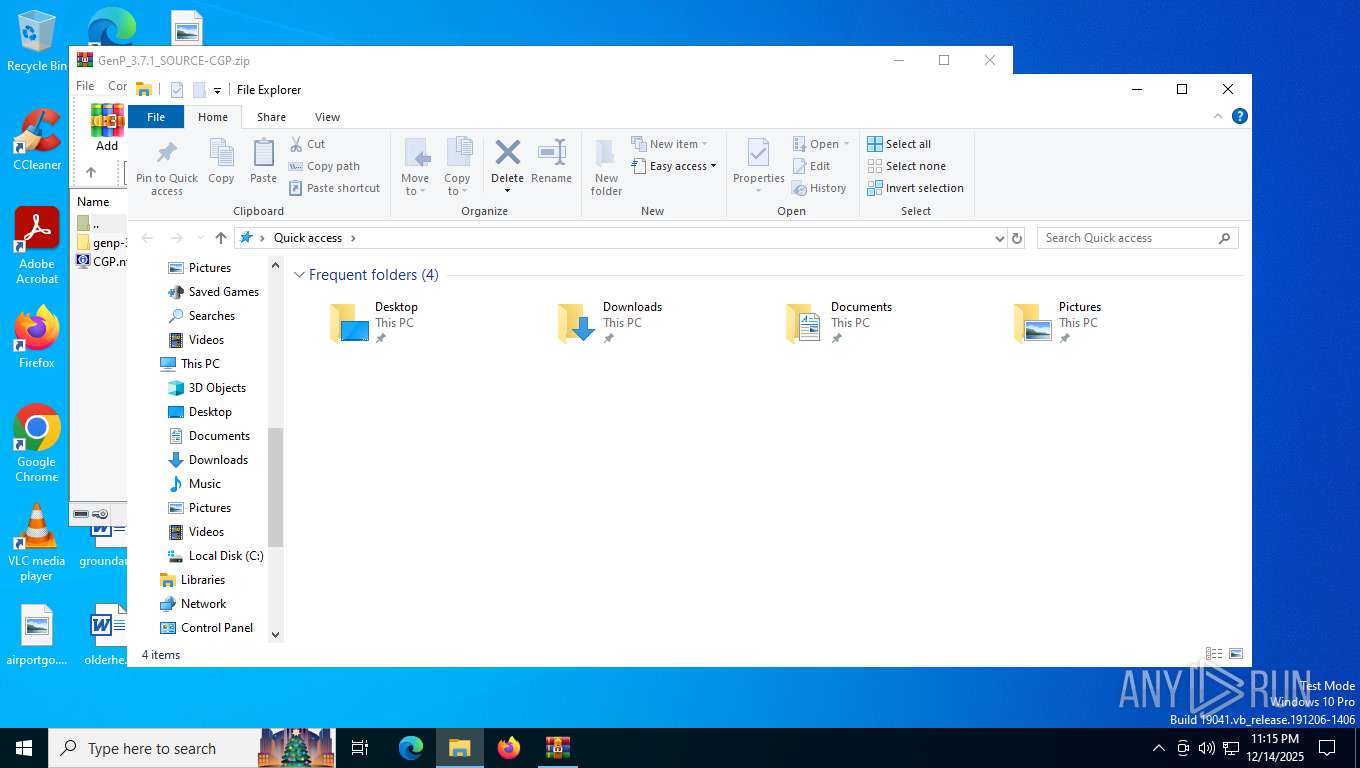
| 7512 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7816 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 690
Read events
16 666
Write events
11
Delete events
13
Modification events
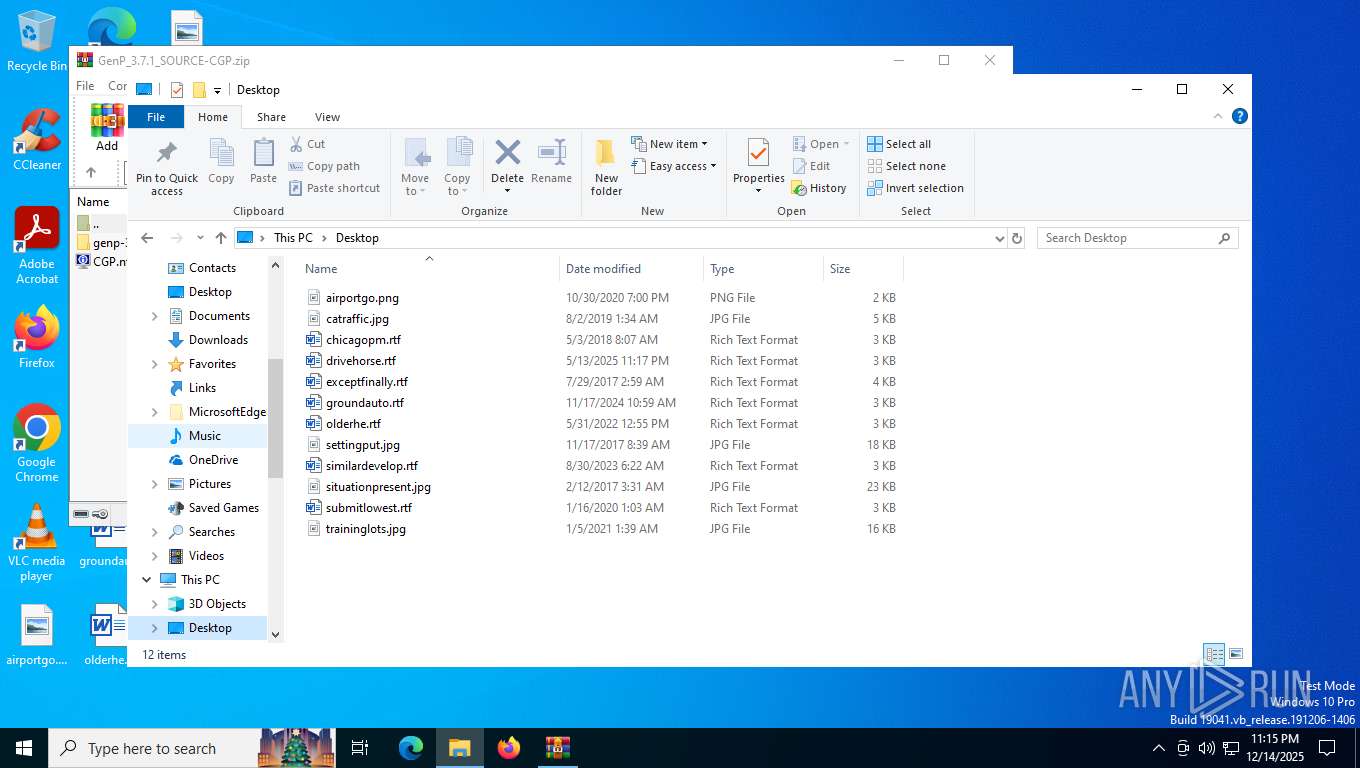
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP.zip | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
3
Suspicious files
3
Text files
17
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\CGP.nfo | text | |
MD5:7C884E9FEFBD2F7162DBAEC46612A0DE | SHA256:8F34B90843CFAB61D1A79B0B6FA47A2A22D41361D6AFCD47F5D40BC1E1FBF7C5 | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\GenP\Skull.ico | image | |
MD5:C37B537E533890560FE52664A7F1C1A0 | SHA256:1532311559D17CF7ECC0BE72FB47EC7D0EA086C414E2280566E0803133FD1D50 | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\build.ps1 | text | |
MD5:3489EE25B34B46DEABE8D371EE8B0D76 | SHA256:14BE137B4644140653363FA7B13ADA4B66E50A57257226BD231D62AADF8364AE | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\GenP\GenP-3.7.1.au3 | binary | |
MD5:9FAC089847B2228B01EBFF6D23C712CE | SHA256:BBC204ED91C9C8321851ADDFFC76FF335D6E562CF581AD883BC85B0E097C96B3 | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\run_build.bat | text | |
MD5:2A1B445614F030C40FB92204611C1034 | SHA256:E89150350B8B4D6957C180B8C044F367CDEA8D0D0B71C8F59DCA8F9EC99A2BE5 | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\UPX\upx-5.0.1-win64.zip | compressed | |
MD5:C7E44B194229B217D7E859C14714BA2F | SHA256:C288989437CE70646A62799A4DCF25B4EC7AD8FBB4F93A29E25C14856659C1A4 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xv4o3r2z.5qi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\WinTrust\patch_wintrust.ps1 | text | |
MD5:4C1563EB08376A1FC0979A18C1DF28FC | SHA256:A73B572BBF1DDBF7D9F5A03EA5ECF9E2C296ECBEFBC60104656F21644B20B2F2 | |||
| 7832 | tar.exe | C:\Users\admin\AppData\Local\Temp\GenP_3.7.1_SOURCE-CGP\genp-3.7.1-src\UPX\upx-5.0.1-win64\COPYING | binary | |
MD5:B234EE4D69F5FCE4486A80FDAF4A4263 | SHA256:8177F97513213526DF2CF6184D8FF986C675AFB514D4E68A404010521B880643 | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nasdzdbx.1sd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
38
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
6284 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6284 | svchost.exe | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
6284 | svchost.exe | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
872 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | binary | 5.48 Kb | whitelisted |
872 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
872 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6284 | svchost.exe | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
6284 | svchost.exe | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3136 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 92.123.104.11:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6284 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6284 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
872 | svchost.exe | 184.24.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
872 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5568 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
— | — | Misc activity | ET HUNTING Observed DNS Query to autoitscript .com |
— | — | Misc activity | ET HUNTING Observed Domain (autoitscript .com) in TLS SNI |