| File name: | crossout_launcher_1.0.3.110.exe |
| Full analysis: | https://app.any.run/tasks/c8e4b4db-1971-4177-9e23-6e25312e028c |
| Verdict: | Suspicious activity |
| Analysis date: | April 23, 2020, 09:32:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F90DAAC43A0F6EB2FF97CD803645C5C9 |
| SHA1: | 90F33FE77E3CBFC5F7F65DDFC2A3045ABACB5F08 |
| SHA256: | C108725A4E375CA0FB7666358543B34958D357D1B1DB76795E10F8BEC3C541F2 |
| SSDEEP: | 196608:s2F0EXVTb5BID2qHHAESQ5emT0S82MU25U0evQ:s25XVTbAiSAe5eKniU0R |
MALICIOUS
Loads dropped or rewritten executable
- launcher.exe (PID: 2756)
Application was dropped or rewritten from another process
- gjagent.exe (PID: 3284)
- launcher.exe (PID: 2756)
- gaijin_downloader.exe (PID: 3296)
Changes the autorun value in the registry
- launcher.exe (PID: 2756)
SUSPICIOUS
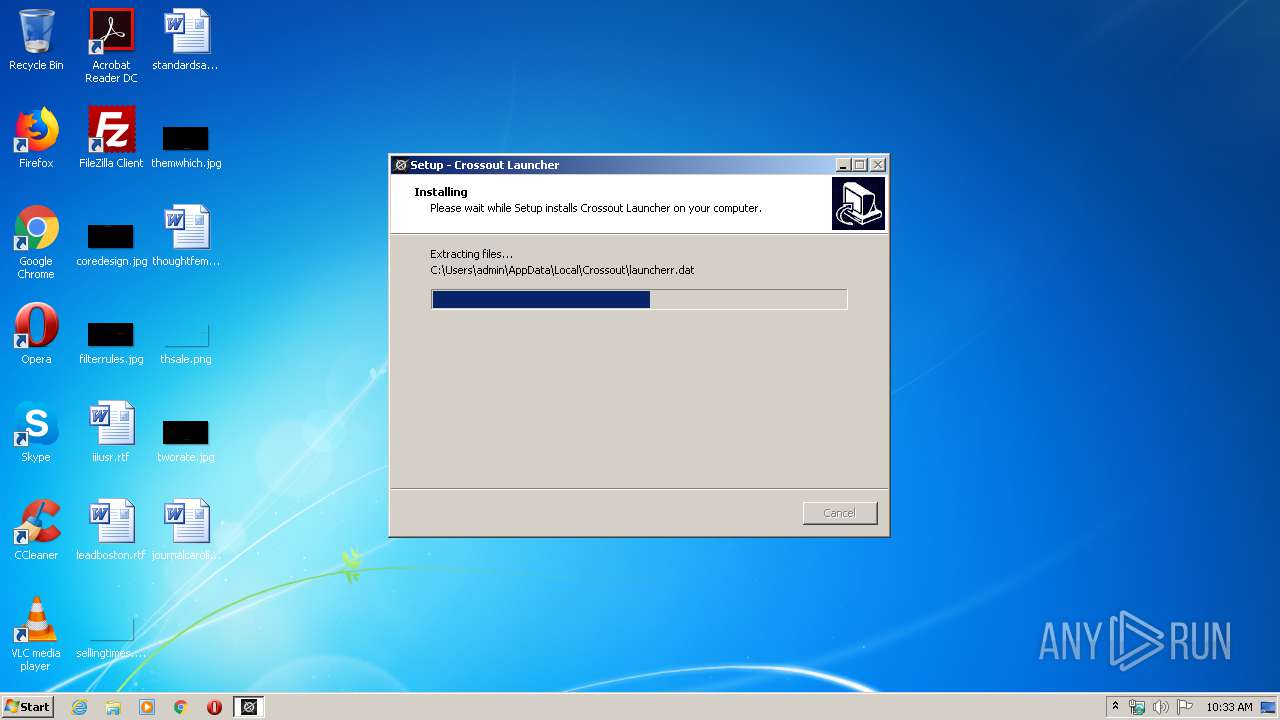
Executable content was dropped or overwritten
- crossout_launcher_1.0.3.110.exe (PID: 588)
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
- launcher.exe (PID: 2756)
- gaijin_downloader.exe (PID: 3296)
Reads the Windows organization settings
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
Reads Windows owner or organization settings
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
Creates files in the program directory
- launcher.exe (PID: 2756)
- gjagent.exe (PID: 3284)
Creates files in the user directory
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
Connects to unusual port
- launcher.exe (PID: 2756)
INFO
Dropped object may contain Bitcoin addresses
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
- gaijin_downloader.exe (PID: 3296)
Creates a software uninstall entry
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
Application was dropped or rewritten from another process
- crossout_launcher_1.0.3.110.tmp (PID: 1840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 330240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Crossout Launcher Setup |
| FileVersion: | |
| LegalCopyright: | Copyright В© 2016-2019 by Targem Inc. В© 2011-2019 by Gaijin Entertainment |
| ProductName: | Crossout Launcher |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Crossout Launcher Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright В© 2016-2019 by Targem Inc. В© 2011-2019 by Gaijin Entertainment |
| ProductName: | Crossout Launcher |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0004E808 | 0x0004EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.72698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.85138 | 51240 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 7.00292 | 12840 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.02586 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.0585 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.4741 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Users\admin\AppData\Local\Temp\crossout_launcher_1.0.3.110.exe" | C:\Users\admin\AppData\Local\Temp\crossout_launcher_1.0.3.110.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Crossout Launcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\is-PKE6I.tmp\crossout_launcher_1.0.3.110.tmp" /SL5="$C0202,5778899,397824,C:\Users\admin\AppData\Local\Temp\crossout_launcher_1.0.3.110.exe" | C:\Users\admin\AppData\Local\Temp\is-PKE6I.tmp\crossout_launcher_1.0.3.110.tmp | crossout_launcher_1.0.3.110.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\Crossout\launcher.exe" | C:\Users\admin\AppData\Local\Crossout\launcher.exe | crossout_launcher_1.0.3.110.tmp | ||||||||||||
User: admin Company: Gaijin Entertainment Integrity Level: MEDIUM Description: Gaijin Smart Launcher Exit code: 0 Version: 1.0.3.110 Modules
| |||||||||||||||
| 3284 | "C:\Users\admin\AppData\Local\Gaijin\Program Files (x86)\NetAgent\gjagent.exe" | C:\Users\admin\AppData\Local\Gaijin\Program Files (x86)\NetAgent\gjagent.exe | launcher.exe | ||||||||||||
User: admin Company: Gaijin Entertainment Integrity Level: MEDIUM Description: Gaijin.Net Updater Exit code: 0 Version: 1.0.27 Modules
| |||||||||||||||
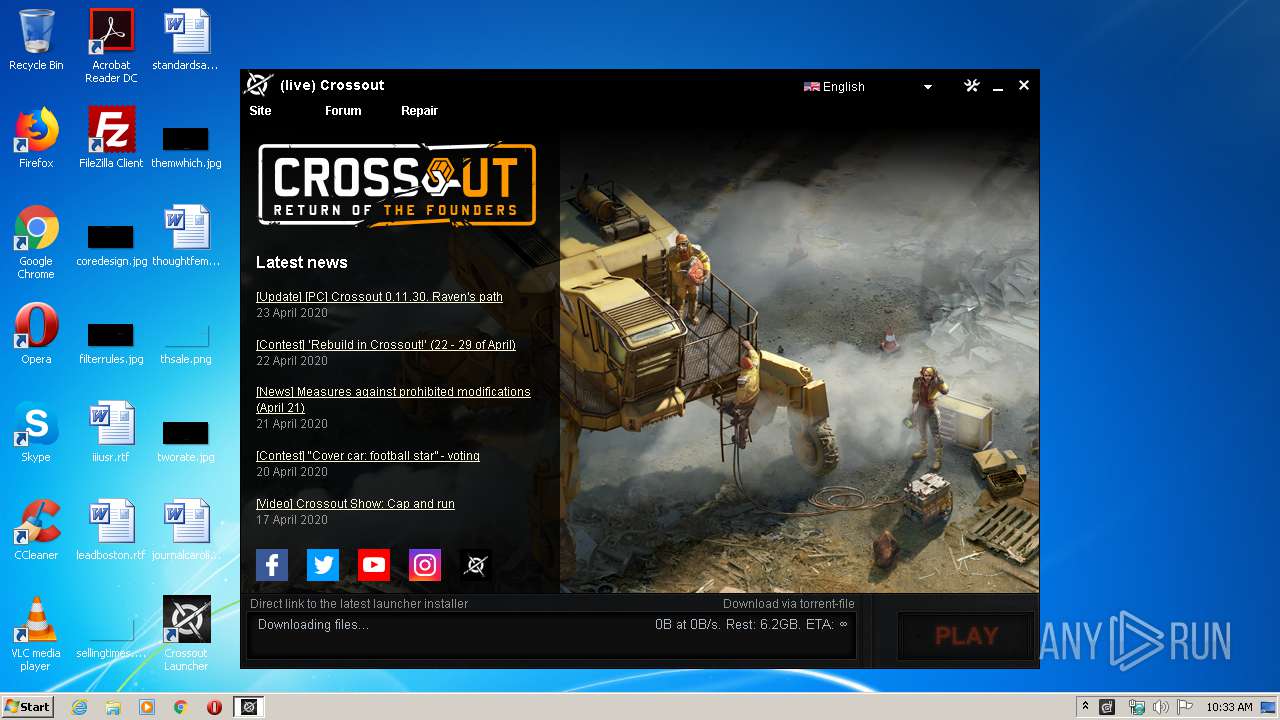
| 3296 | "C:\Users\admin\AppData\Local\Crossout\gaijin_downloader.exe" -appid CrossoutLauncherZip -localversion 1.0.3.110 -execpath launcher.exe -notify_user_about_failure -conditional_gui_app_restart | C:\Users\admin\AppData\Local\Crossout\gaijin_downloader.exe | launcher.exe | ||||||||||||
User: admin Company: Gaijin Entertainment Integrity Level: MEDIUM Description: Gaijin Downloader Exit code: 0 Modules
| |||||||||||||||
Total events
1 126
Read events
1 091
Write events
29
Delete events
6
Modification events
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 300700008203672F5219D601 | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C37F80261A392F00D399104F2457F8FD901230FB32C376666E1BAB04F85B1DB5 | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Crossout\launcher.exe | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: DB27495D3A8DC6115E7979A20436C280E1BA93FAE286F101CDEC1DE9A34AC734 | |||
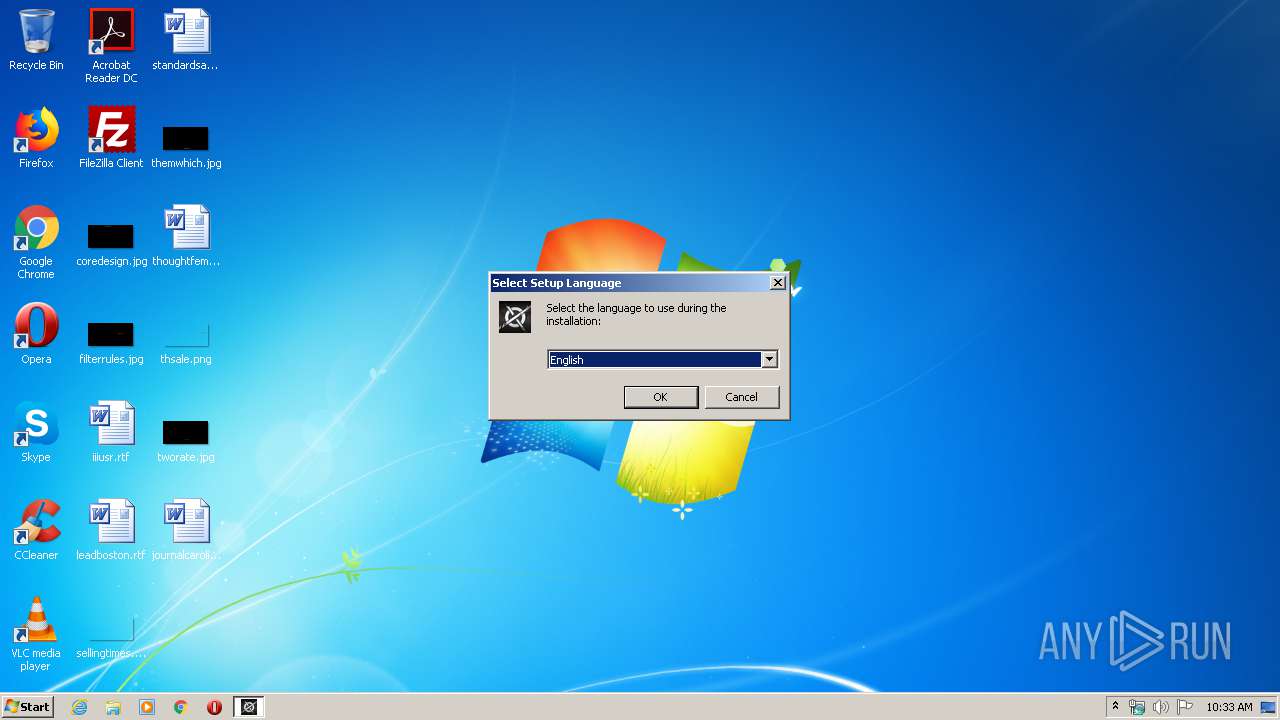
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Gaijin\Crossout |
| Operation: | write | Name: | language |
Value: English | |||
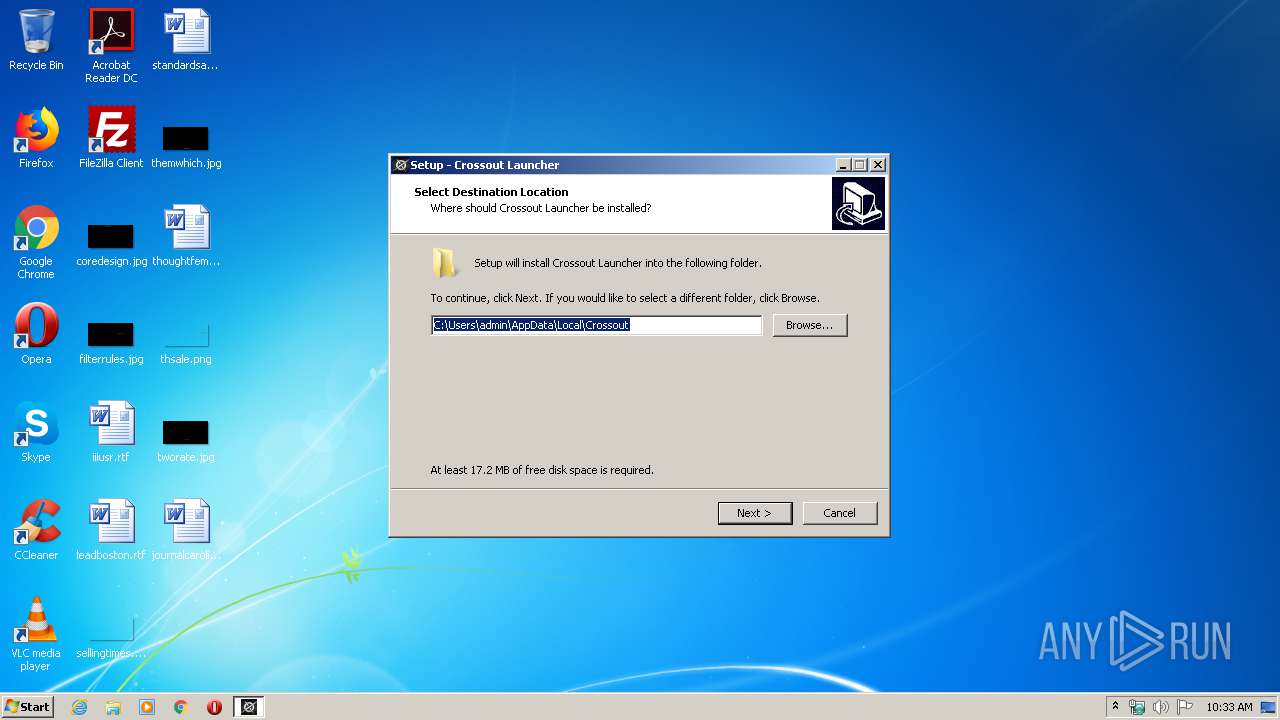
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\CrossOutLauncher_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (u) | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\CrossOutLauncher_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Crossout | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\CrossOutLauncher_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Crossout\ | |||
| (PID) Process: | (1840) crossout_launcher_1.0.3.110.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\CrossOutLauncher_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Crossout | |||
Executable files
15
Suspicious files
13
Text files
5
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-A06S9.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-CGBQ4.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-636AH.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-OES4Q.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-DT7HF.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-KPVV1.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-J8VA3.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\is-NUU5K.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | launcher.exe | C:\ProgramData\Gaijin\downloads\xo\84d8a690a9be7a9d8a7d78bf37c3b687c8d94785 | — | |
MD5:— | SHA256:— | |||
| 1840 | crossout_launcher_1.0.3.110.tmp | C:\Users\admin\AppData\Local\Crossout\launcher.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
3 035
DNS requests
16
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2756 | launcher.exe | GET | — | 8.253.95.117:80 | http://crossout-level3.cdn.gaijin.net/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | US | — | — | suspicious |
2756 | launcher.exe | GET | — | 92.223.89.40:80 | http://all-seed-gc-lx-02.cdn.gaijin.net/content/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | LU | — | — | unknown |
2756 | launcher.exe | GET | — | 8.253.95.117:80 | http://crossout-level3.cdn.gaijin.net/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | US | — | — | suspicious |
2756 | launcher.exe | GET | — | 8.253.95.117:80 | http://crossout-level3.cdn.gaijin.net/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | US | — | — | suspicious |
2756 | launcher.exe | GET | — | 92.223.89.40:80 | http://all-seed-gc-lx-02.cdn.gaijin.net/content/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | LU | — | — | unknown |
2756 | launcher.exe | GET | — | 8.253.95.117:80 | http://crossout-level3.cdn.gaijin.net/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | US | — | — | suspicious |
2756 | launcher.exe | GET | — | 92.223.89.37:80 | http://01-all-seed-gc-lx-01.cdn.gaijin.net/content/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | LU | — | — | unknown |
2756 | launcher.exe | GET | — | 92.223.89.40:80 | http://all-seed-gc-lx-02.cdn.gaijin.net/content/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | LU | — | — | unknown |
2756 | launcher.exe | GET | — | 8.253.95.117:80 | http://crossout-level3.cdn.gaijin.net/xo/0.11.30.138502/142ff5218668ba59b05c50a524914bffb7da1bd2/data/assets_props_trees_speedtree.grp | US | — | — | suspicious |
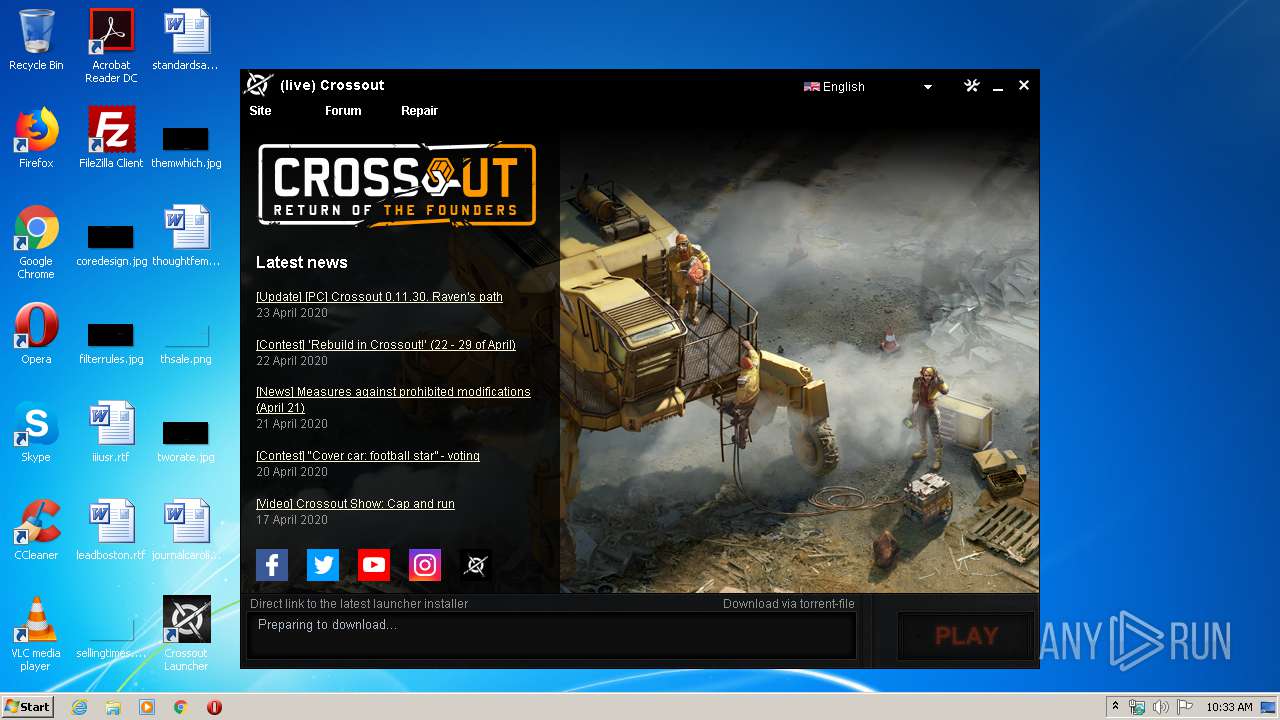
2756 | launcher.exe | GET | 200 | 185.11.75.54:80 | http://crossout.net/generated/news-en.html | RU | text | 600 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 95.37.249.147:51470 | — | PJSC Rostelecom | RU | unknown |
2756 | launcher.exe | 95.211.237.153:20010 | client-stats.gaijin.net | LeaseWeb Netherlands B.V. | NL | unknown |
2756 | launcher.exe | 52.17.233.228:443 | yupmaster.gaijinent.com | Amazon.com, Inc. | IE | unknown |
2756 | launcher.exe | 185.11.75.54:80 | crossout.net | OOO Network of data-centers Selectel | RU | unknown |
3296 | gaijin_downloader.exe | 95.211.237.153:20010 | client-stats.gaijin.net | LeaseWeb Netherlands B.V. | NL | unknown |
3296 | gaijin_downloader.exe | 52.17.233.228:443 | yupmaster.gaijinent.com | Amazon.com, Inc. | IE | unknown |
3296 | gaijin_downloader.exe | 185.40.155.13:443 | cdnnow-distr.gaijinent.com | Docker LTD | RU | suspicious |
3284 | gjagent.exe | 95.211.237.153:20010 | client-stats.gaijin.net | LeaseWeb Netherlands B.V. | NL | unknown |
2756 | launcher.exe | 143.204.207.243:443 | aws-yup-distr-01.gaijinent.com | — | US | unknown |
2756 | launcher.exe | 185.157.221.247:25401 | dht.libtorrent.org | — | SE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client-stats.gaijin.net |
| unknown |
crossout.net |
| whitelisted |
yupmaster.gaijinent.com |
| unknown |
client-stats.warthunder.com |
| unknown |
cdnnow-distr.gaijinent.com |
| suspicious |
aws-yup-distr-01.gaijinent.com |
| unknown |
dht.libtorrent.org |
| suspicious |
router.bittorrent.com |
| shared |
retracker.local |
| unknown |
yuptracker-eu.gaijinent.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent Traffic |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT announce_peers request |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
2756 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
Process | Message |
|---|---|
launcher.exe | Log path C:\Users\admin\AppData\Local\Crossout\.launcher_log\2020_04_23_10_33_18_2756.txt |
launcher.exe | |
launcher.exe | BUILD TIMESTAMP: Feb 5 2020 14:56:41
|
launcher.exe | 0.32 [D] TIMER freq: ticks/usec=3 ticks/msec=3515
|
launcher.exe | 0.40 [D] Creating thread "Watchdog thread"...
|
launcher.exe | ---$01 (null) ---
0.41 [D] $01 Thread "Watchdog thread" started
|
launcher.exe | 0.42 [D] statsd::connect: statsd server: client-stats.gaijin.net:20010
|
launcher.exe | 0.42 [D] statsd::set_prefix: setting statsd prefix: 'production.launcher.win.'
|
launcher.exe | 0.49 [D] Mounting C:\Users\admin\AppData\Local\Crossout\launcherr.dat...
|
launcher.exe | 0.49 [D] Sending stat. Bucket: on_launcher_start; Value: 1
|