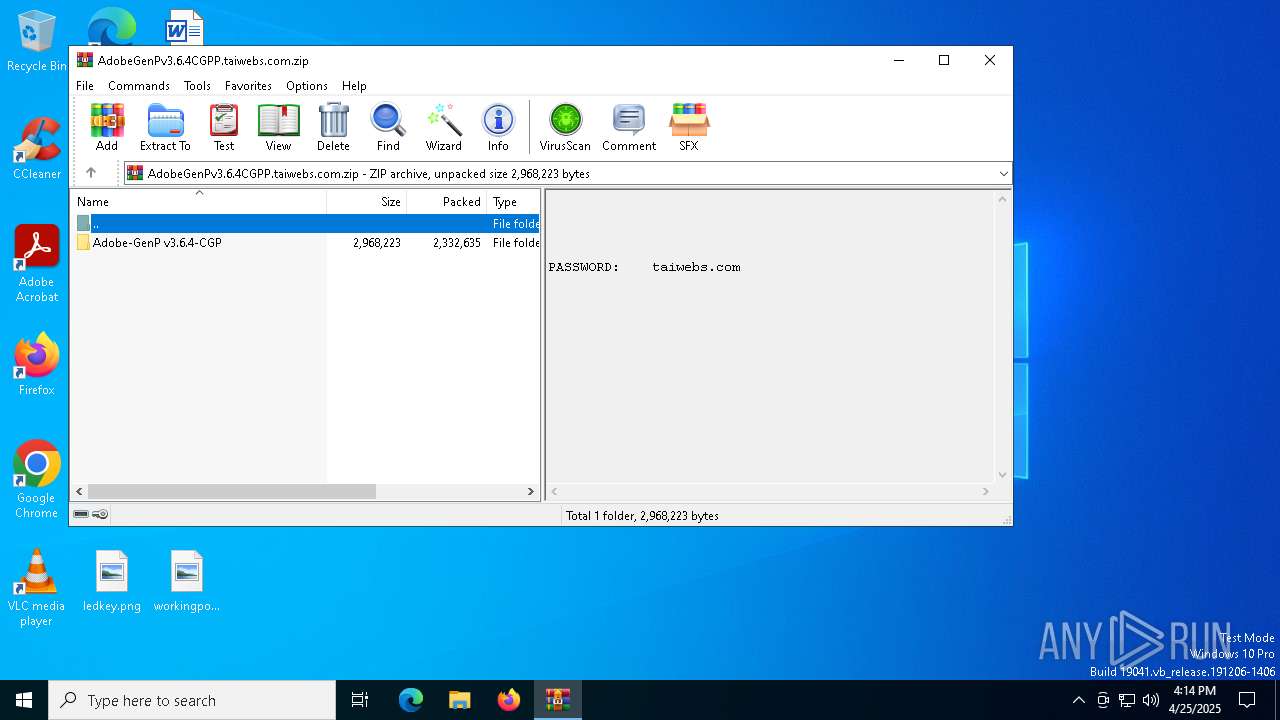
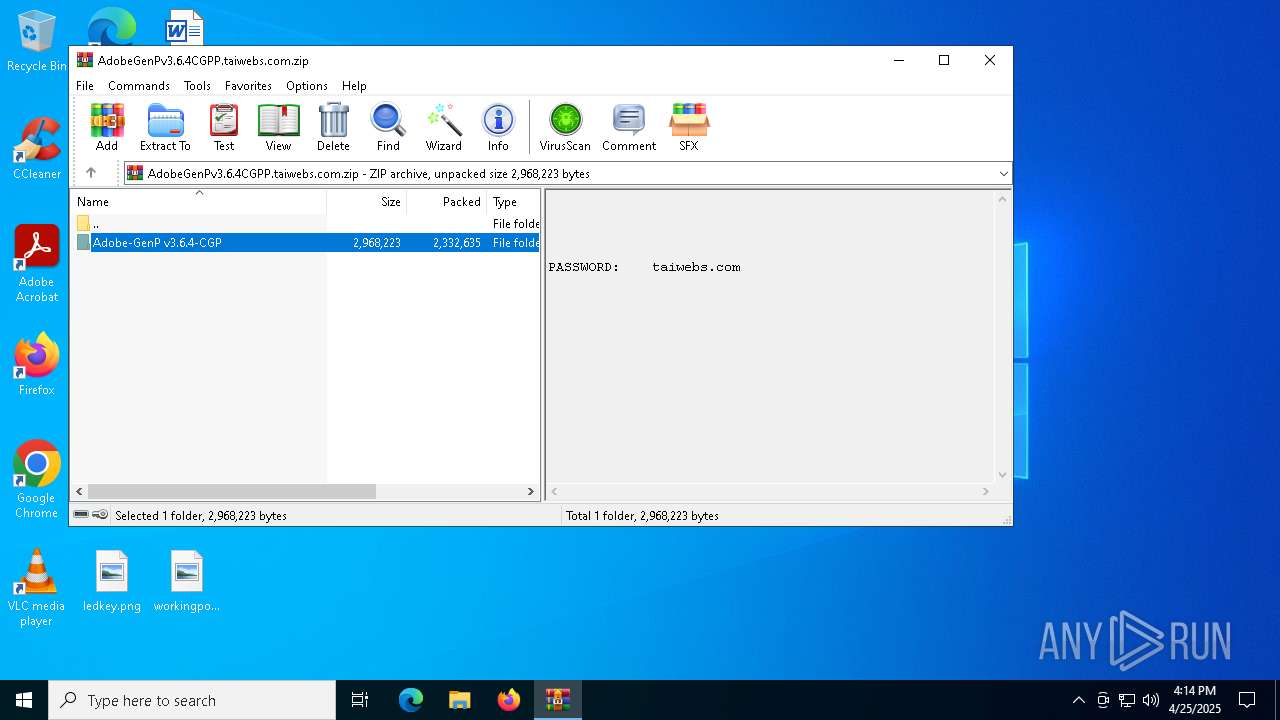
| File name: | AdobeGenPv3.6.4CGPP.taiwebs.com.zip |
| Full analysis: | https://app.any.run/tasks/c9fb24b0-e10b-4695-a6eb-3817b4977efc |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 16:14:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 2120B2170FB4D0FC9EA9ADFB3B9ED406 |
| SHA1: | F63B3A89D7B45D86CB87E4E461ECDF26021F4607 |
| SHA256: | C104D8E749684335AB42D61F61811994F71311A241E9FEC17650CEA4D0E78660 |
| SSDEEP: | 98304:WQpvinlRFSTYApPJxuAhCwa2+CA5dM1XnzK+sx+KdqGb8rCEpHiSNDk42NsMH4Tn://xYPZO |
MALICIOUS
No malicious indicators.SUSPICIOUS
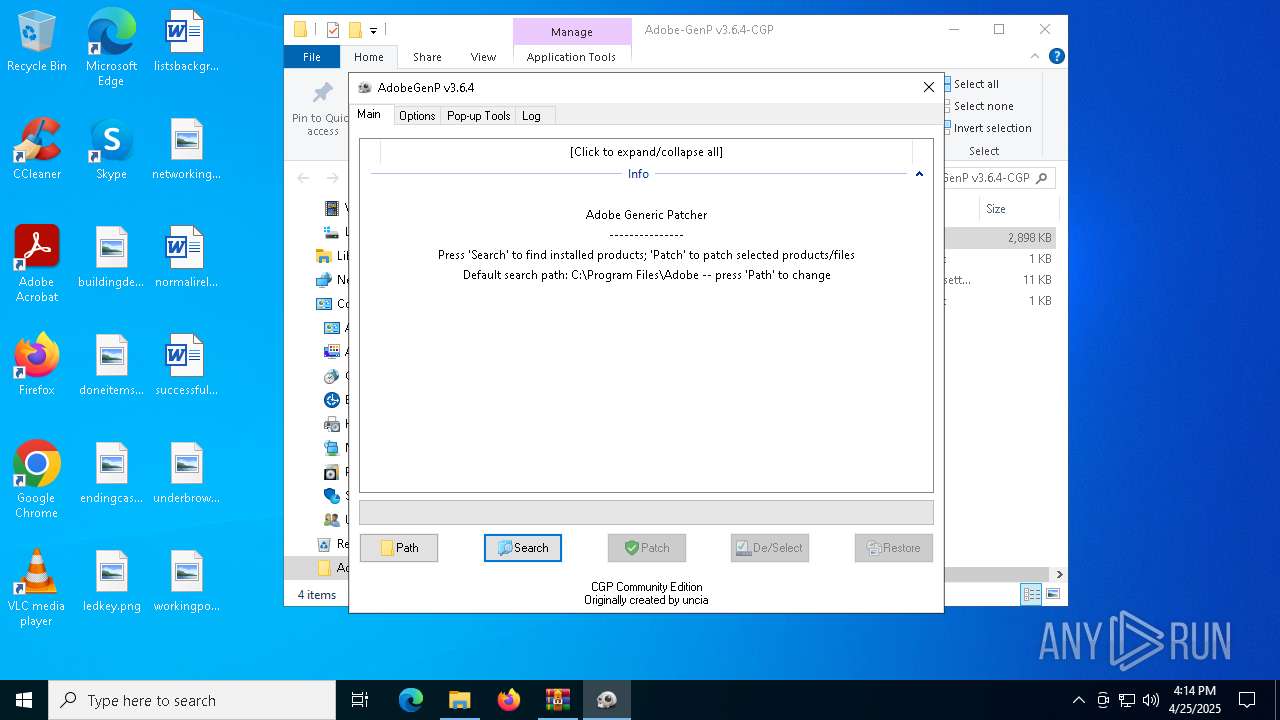
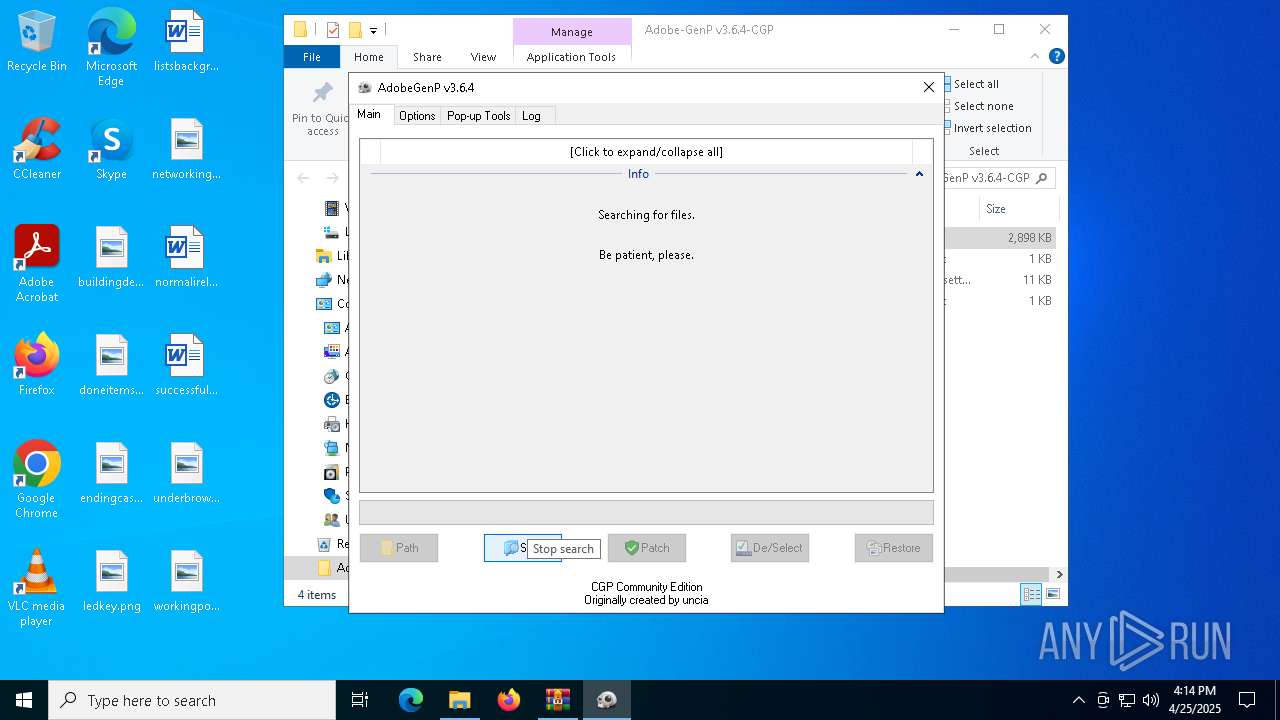
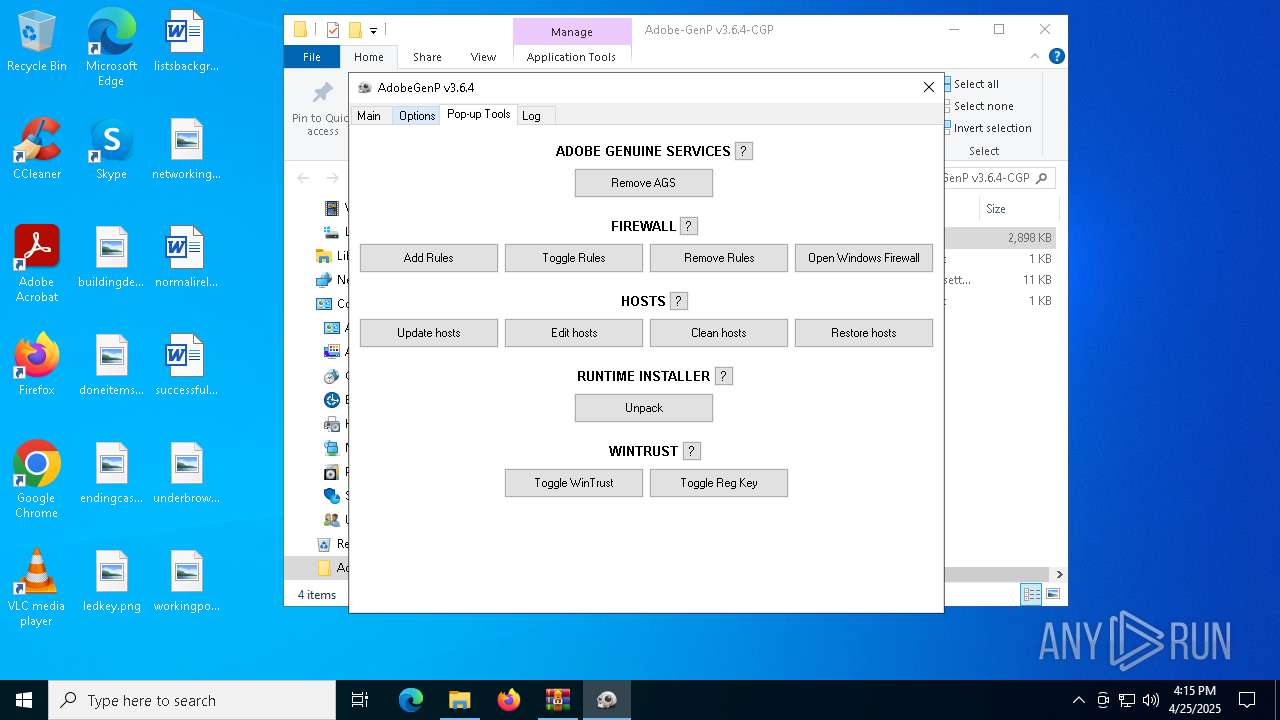
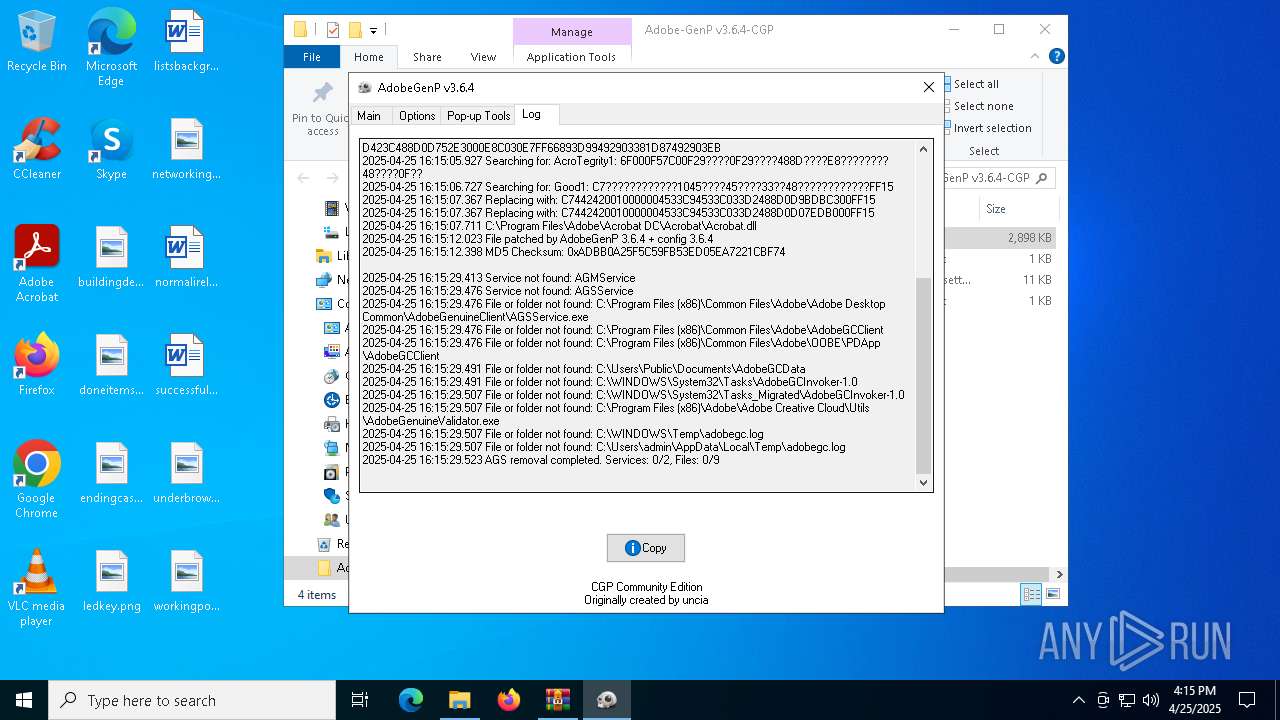
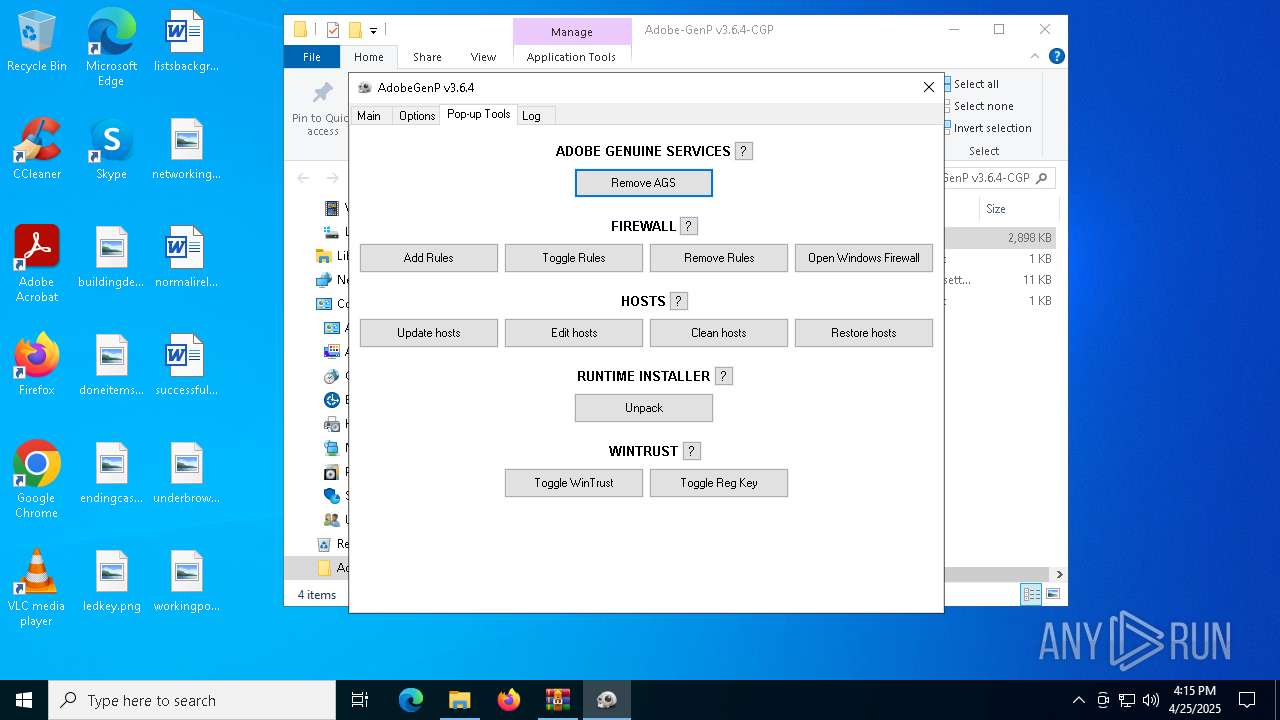
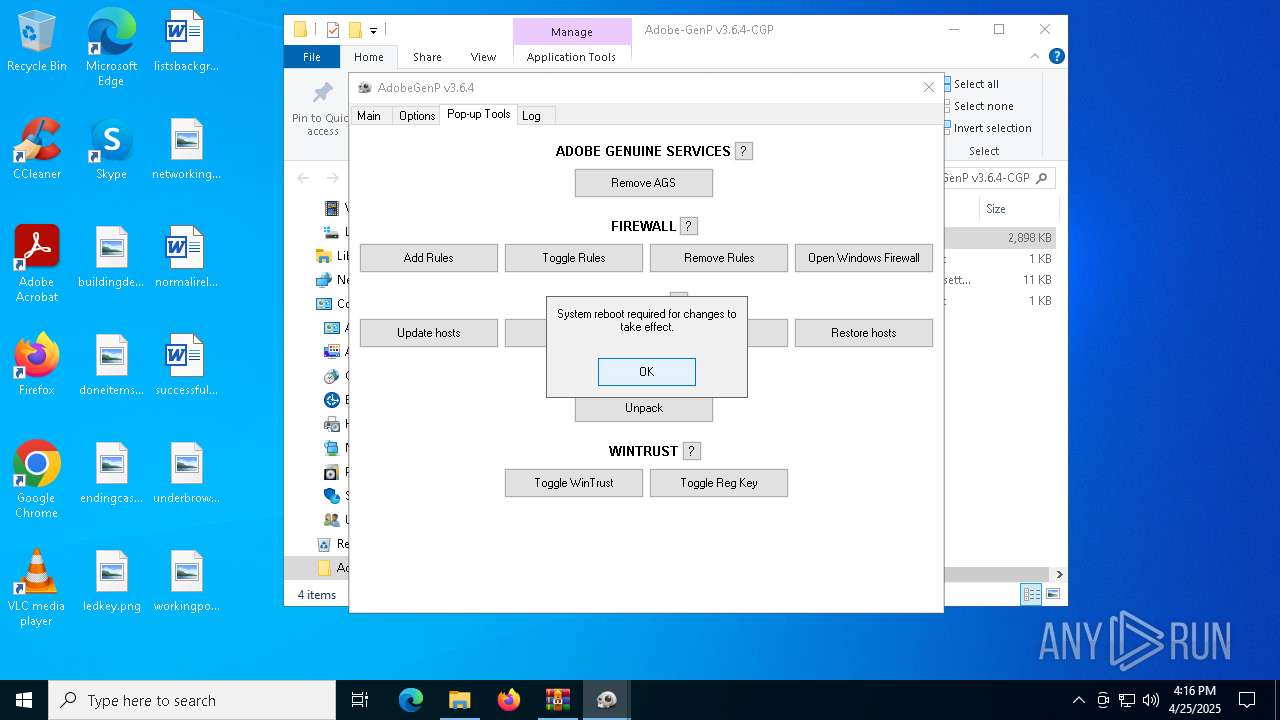
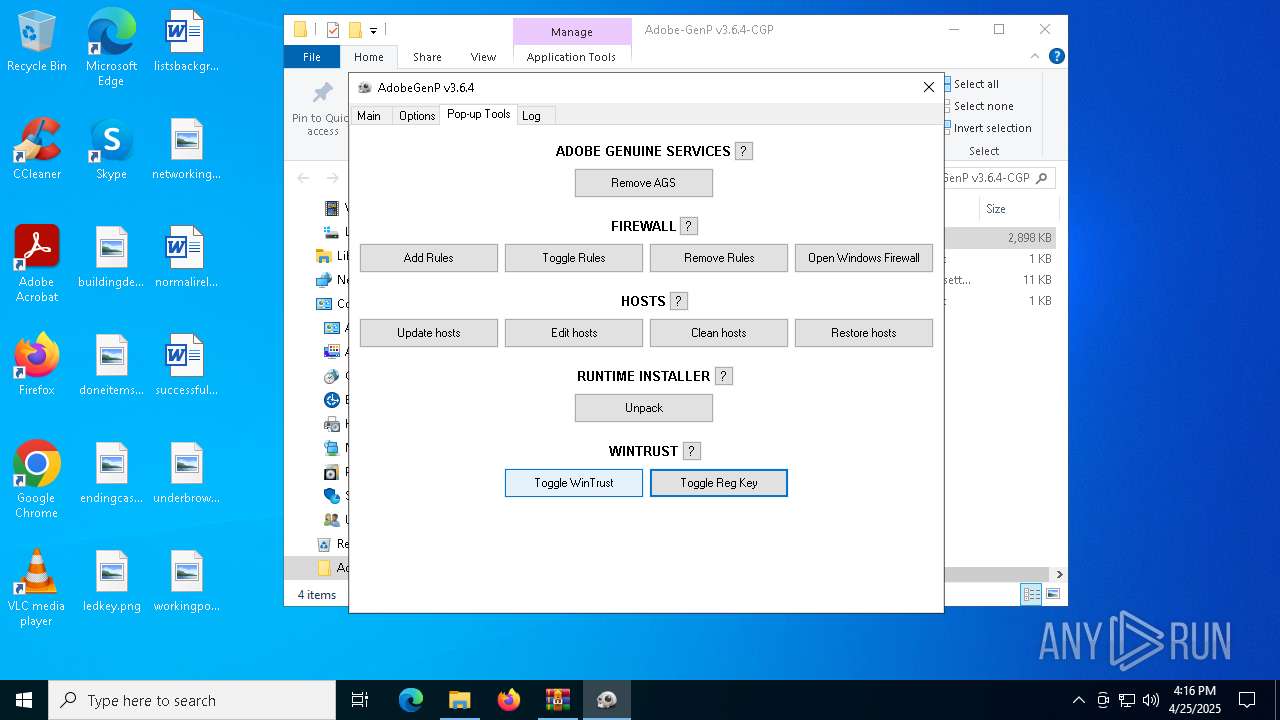
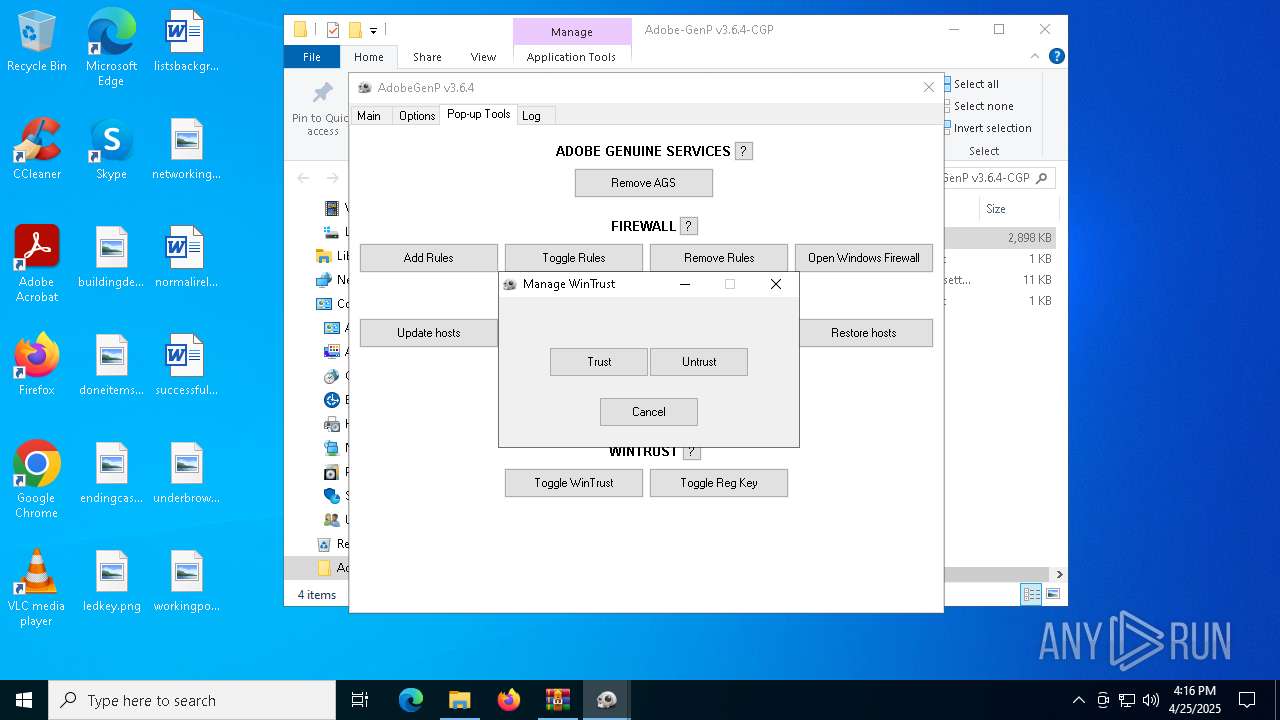
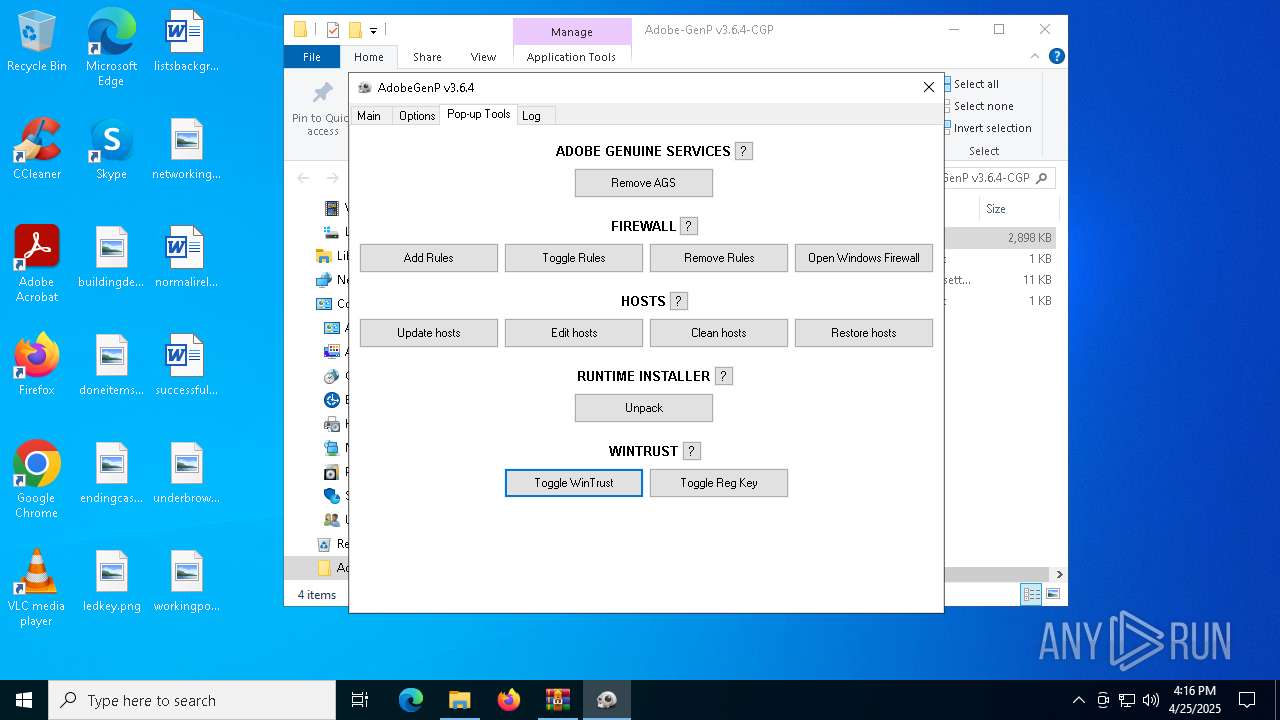
Starts SC.EXE for service management
- AdobeGenP.exe (PID: 7776)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6108)
- cmd.exe (PID: 4896)
- cmd.exe (PID: 7584)
- AdobeGenP.exe (PID: 7776)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 664)
- cmd.exe (PID: 7612)
Windows service management via SC.EXE
- sc.exe (PID: 8140)
- sc.exe (PID: 8076)
Starts CMD.EXE for commands execution
- AdobeGenP.exe (PID: 7776)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6620)
Checks supported languages
- AdobeGenP.exe (PID: 7776)
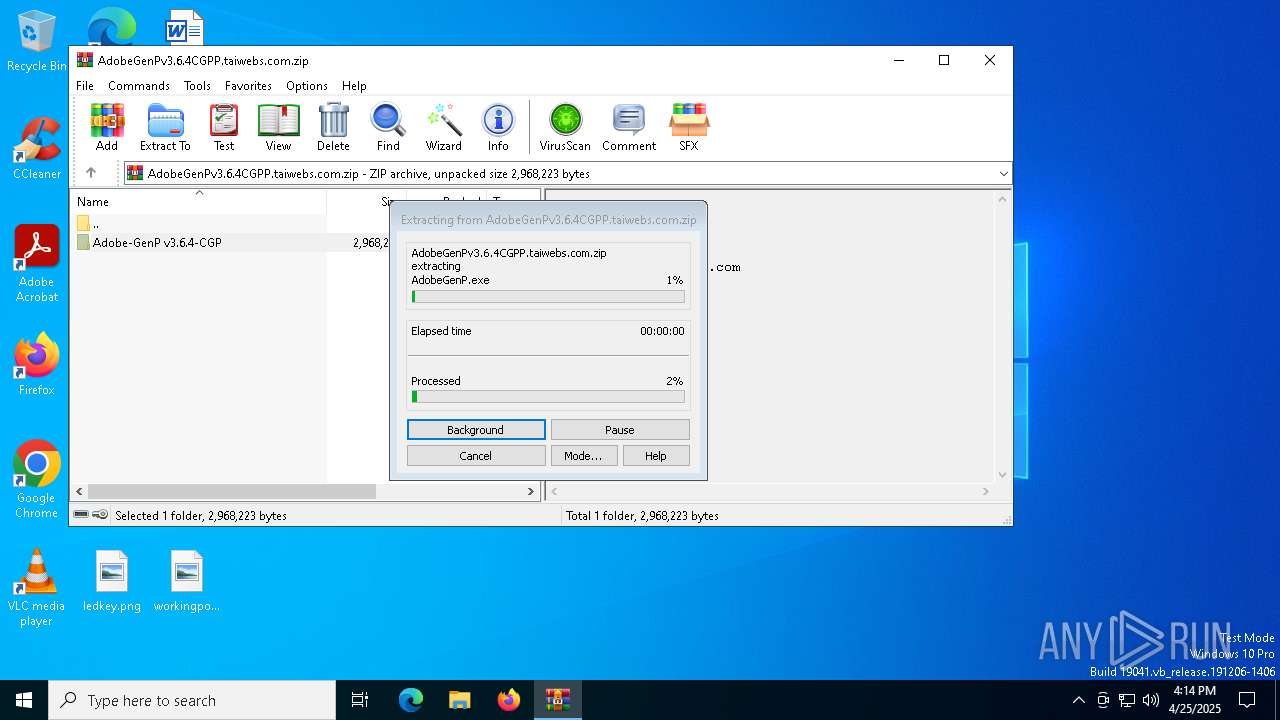
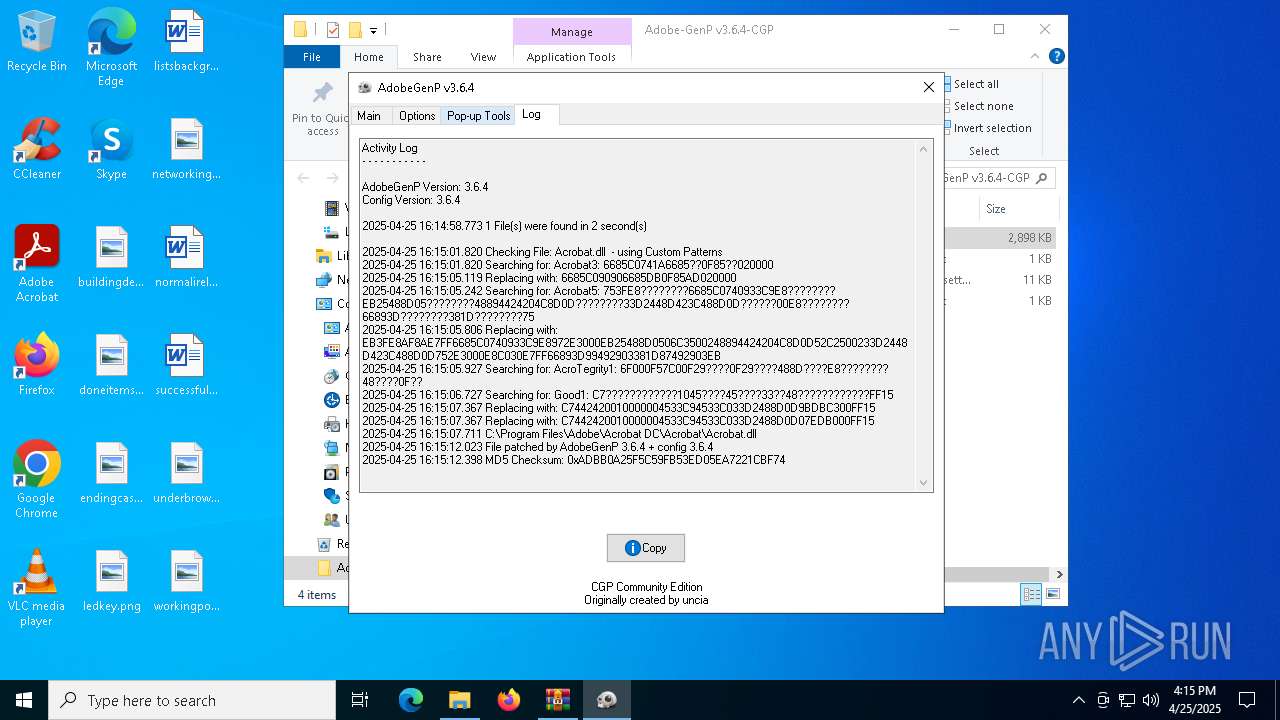
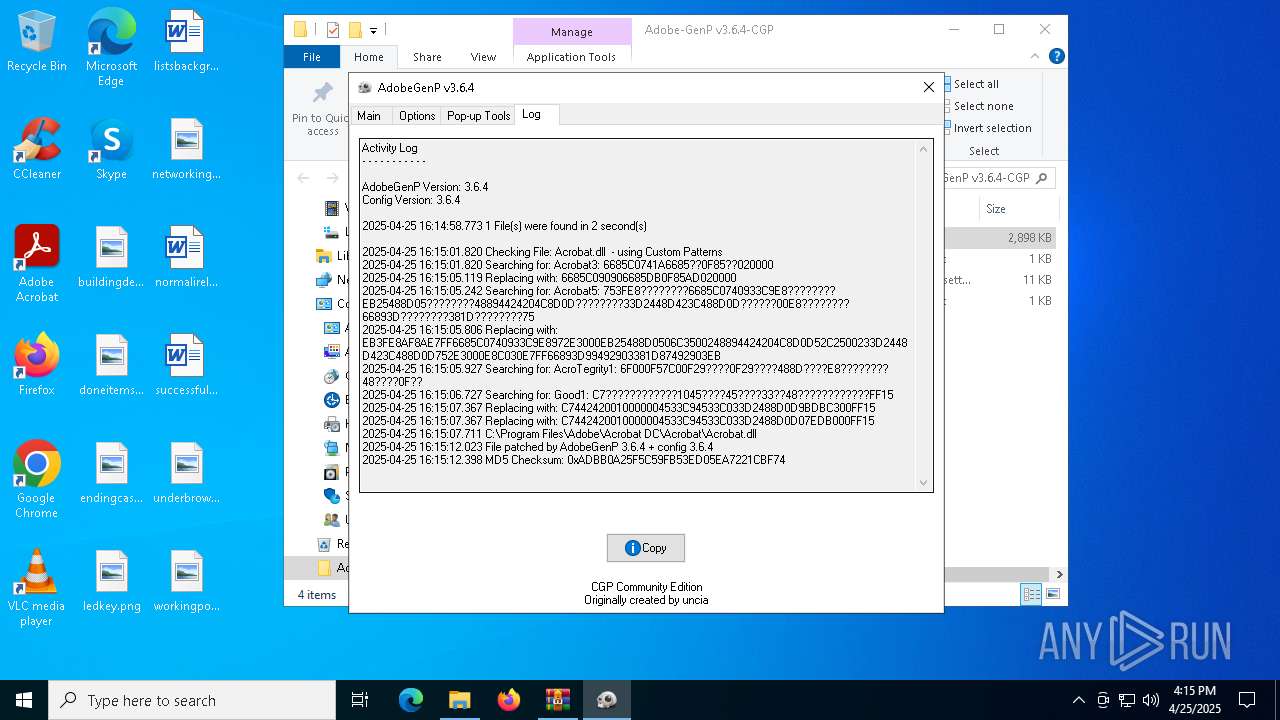
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6620)
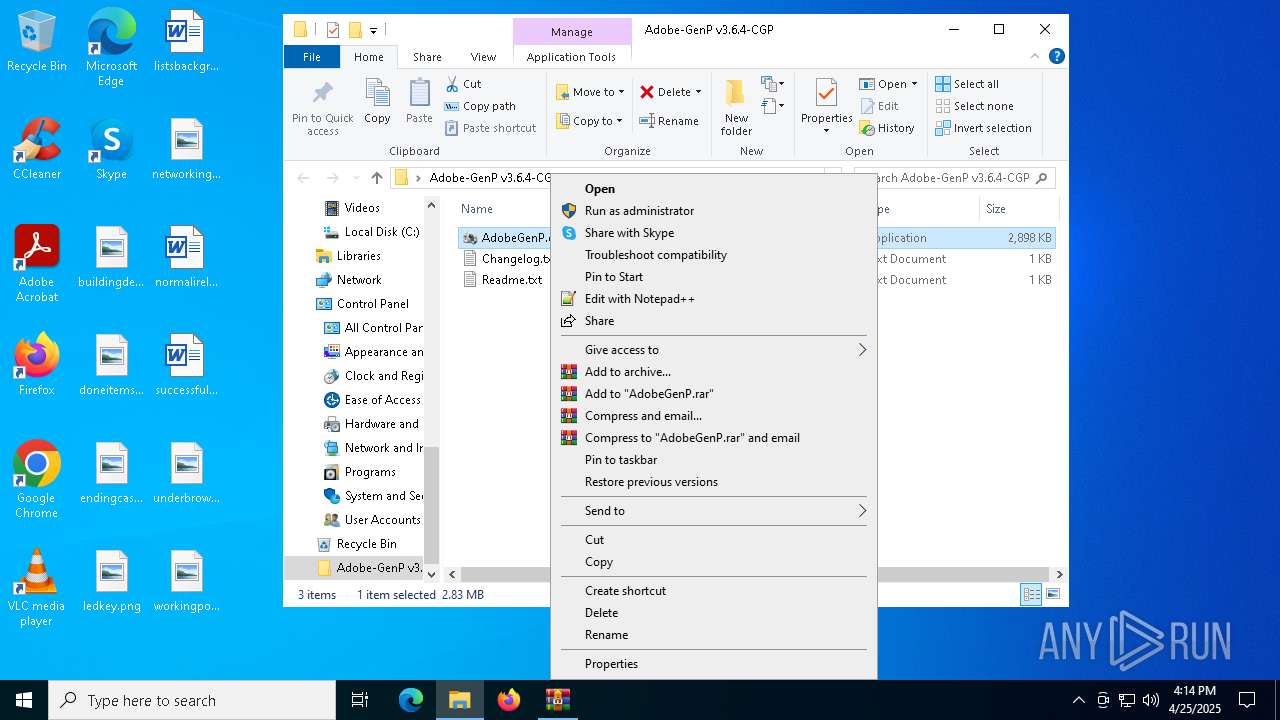
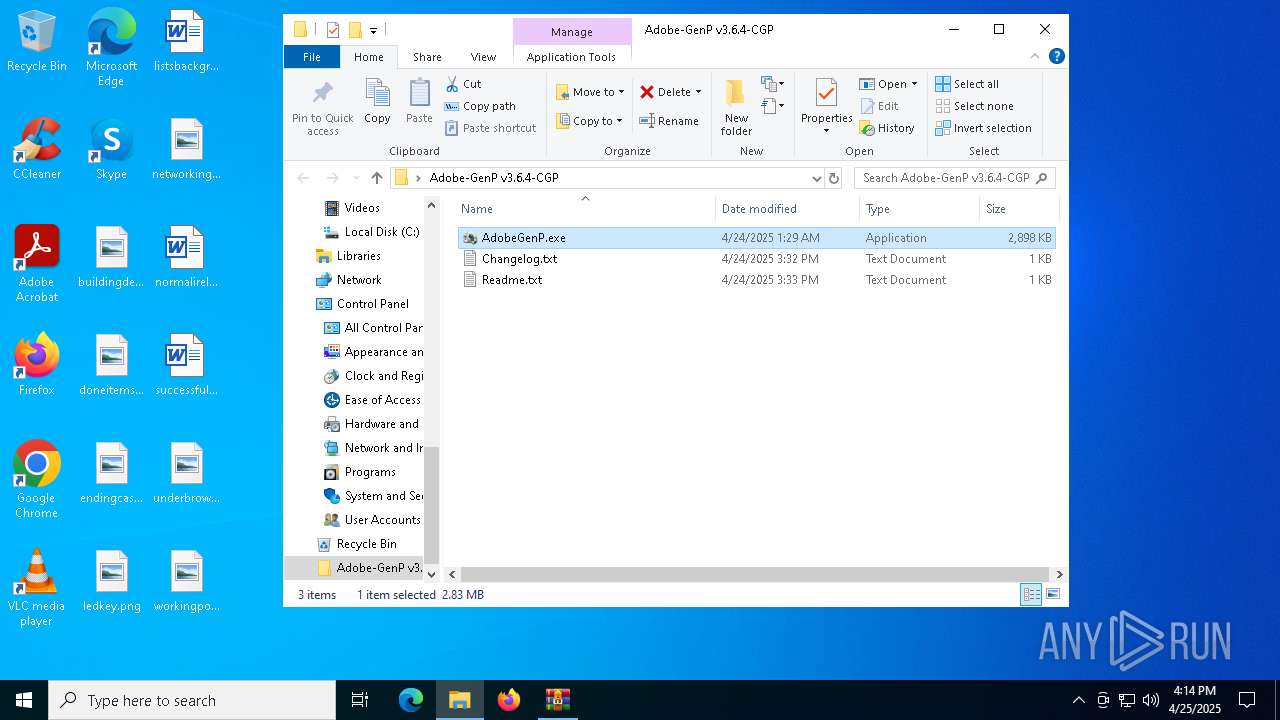
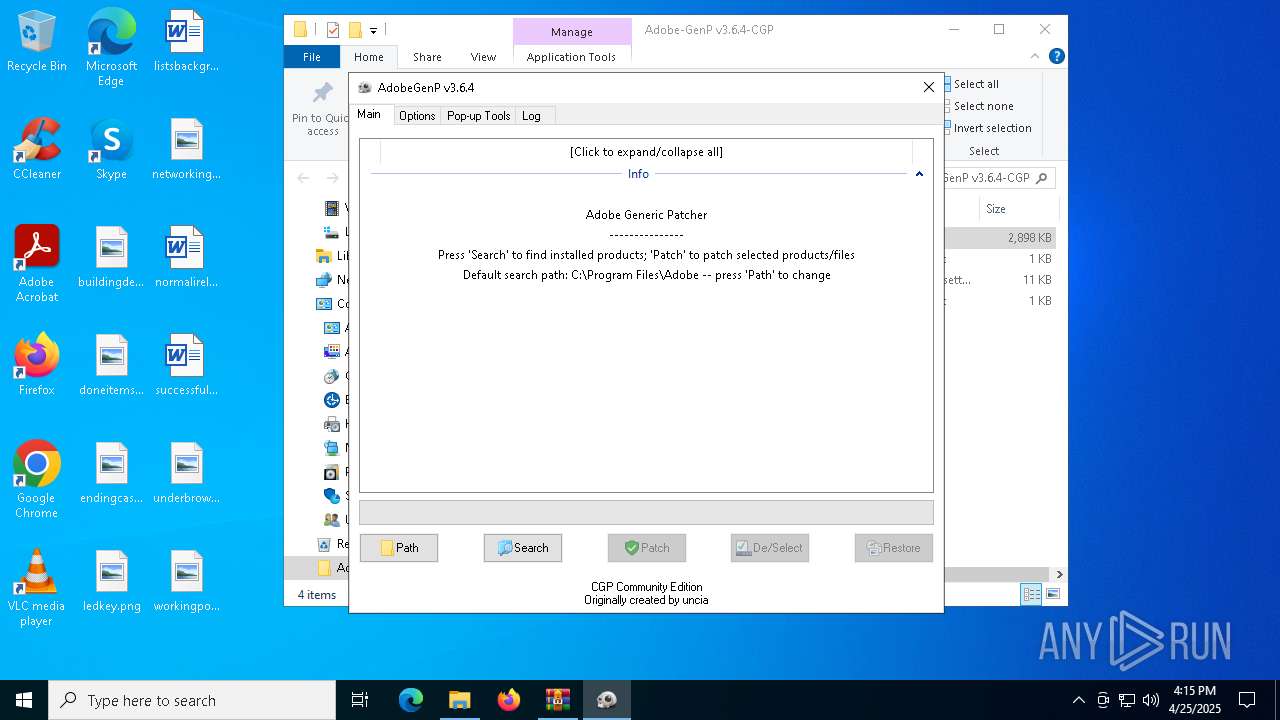
Manual execution by a user
- AdobeGenP.exe (PID: 7776)
Reads the computer name
- AdobeGenP.exe (PID: 7776)
Create files in a temporary directory
- AdobeGenP.exe (PID: 7776)
Reads the machine GUID from the registry
- AdobeGenP.exe (PID: 7776)
Reads mouse settings
- AdobeGenP.exe (PID: 7776)
Creates files in the program directory
- AdobeGenP.exe (PID: 7776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:24 15:33:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
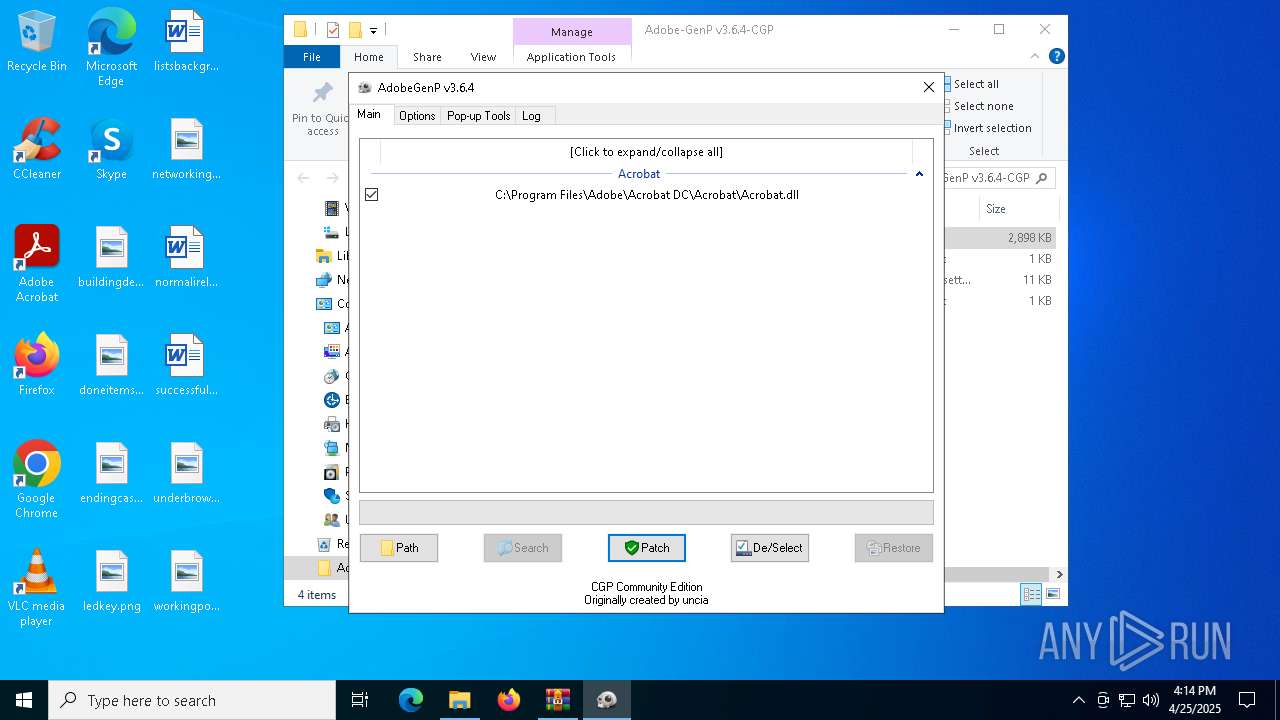
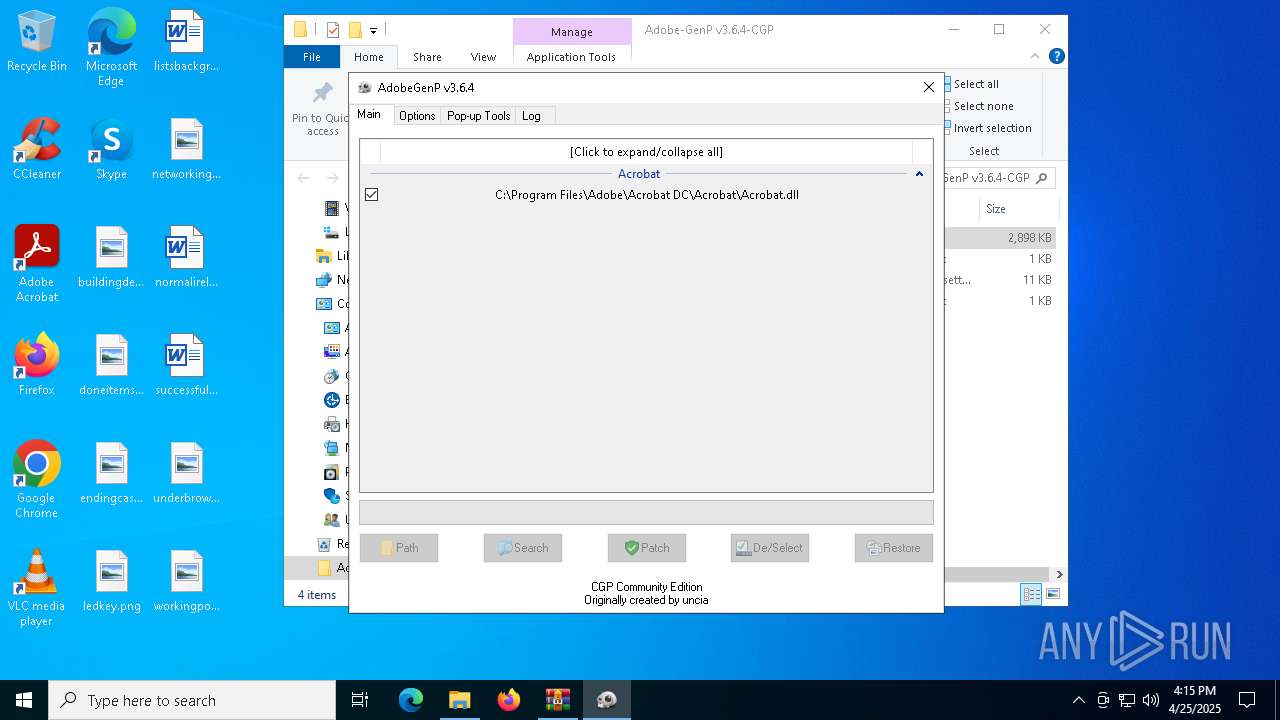
| ZipFileName: | Adobe-GenP v3.6.4-CGP/ |
Total processes
159
Monitored processes
30
Malicious processes
1
Suspicious processes
0
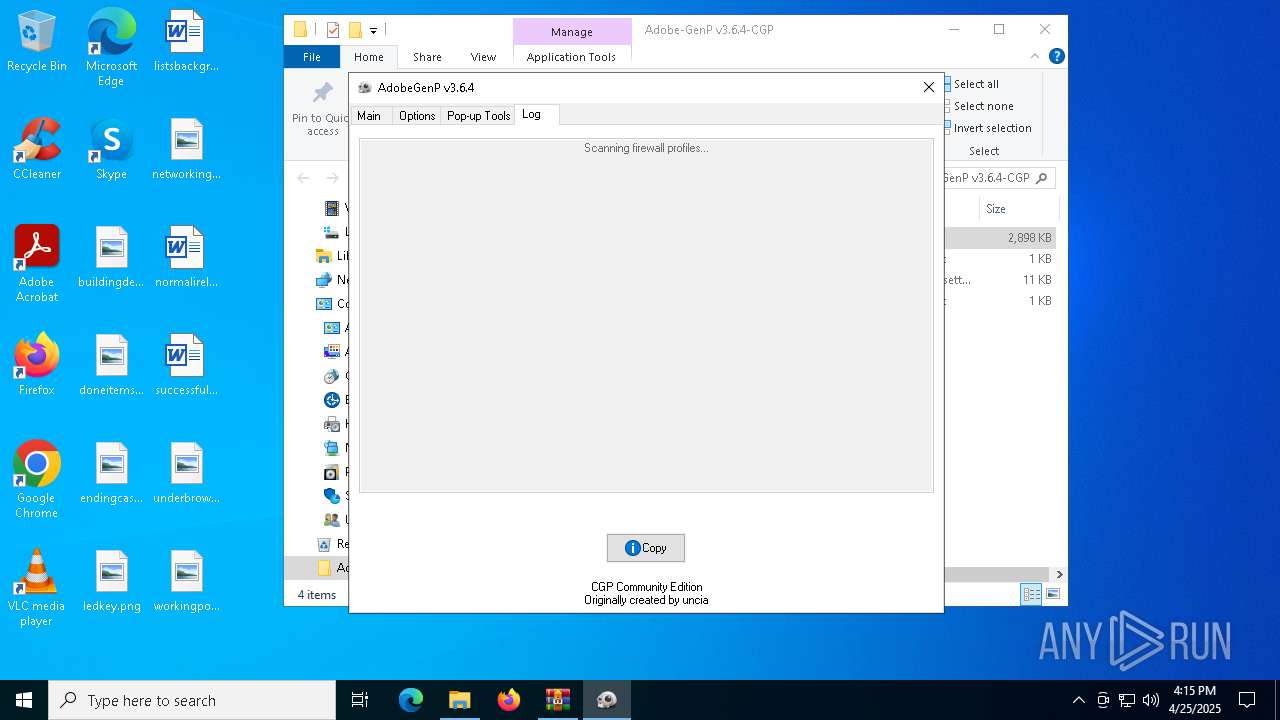
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | C:\WINDOWS\system32\cmd.exe /c powershell.exe -Command "Get-CimInstance -ClassName FirewallProduct -Namespace 'root\SecurityCenter2' | Where-Object { $_.ProductName -notlike '*Windows*' } | Select-Object -Property ProductName" | C:\Windows\System32\cmd.exe | — | AdobeGenP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
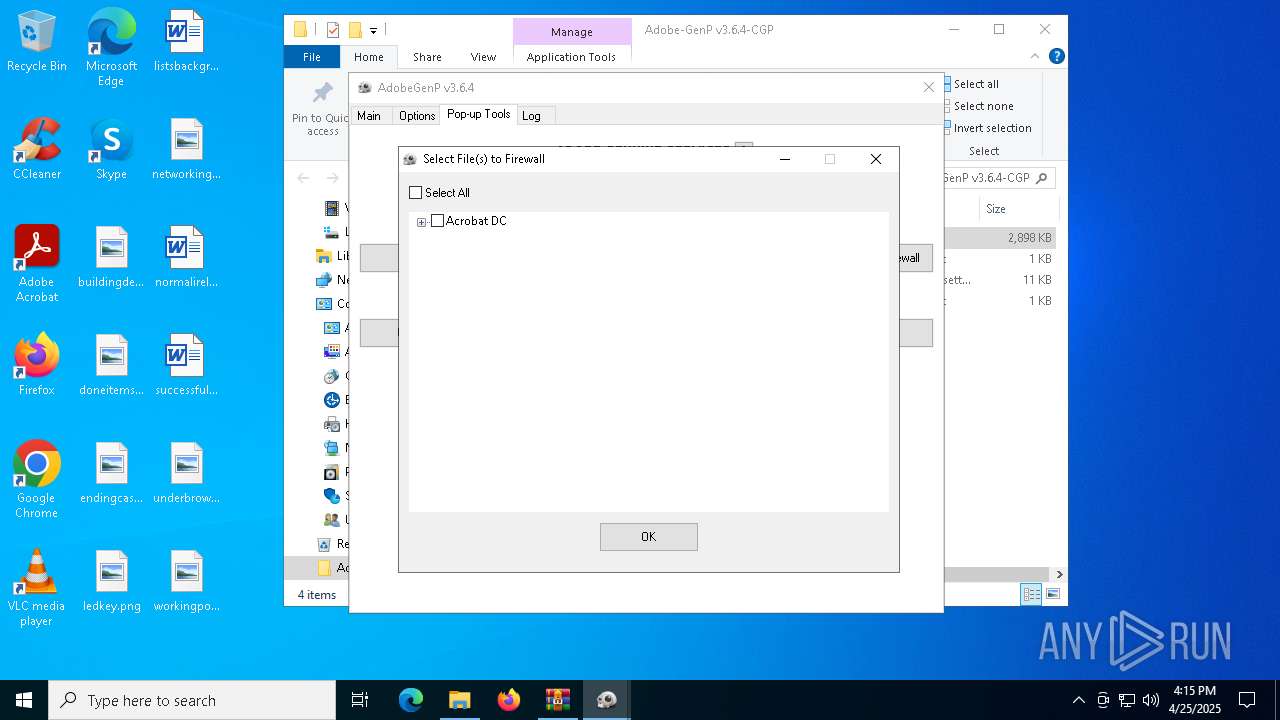
| 720 | powershell.exe -Command "Get-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe' | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | powershell.exe -Command "Get-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\AcroCEF.exe' | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | powershell.exe -Command "New-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe' -Direction Outbound -Program 'C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe' -Action Block;New-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\AcroCEF.exe' -Direction Outbound -Program 'C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\AcroCEF.exe' -Action Block;New-NetFirewallRule -DisplayName 'Adobe-Block - C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe' -Direction Outbound -Program 'C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe' -Action Block;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4108 | powershell.exe -Command "Get-CimInstance -ClassName FirewallProduct -Namespace 'root\SecurityCenter2' | Where-Object { $_.ProductName -notlike '*Windows*' } | Select-Object -Property ProductName" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 776
Read events
41 766
Write events
10
Delete events
0
Modification events
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AdobeGenPv3.6.4CGPP.taiwebs.com.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
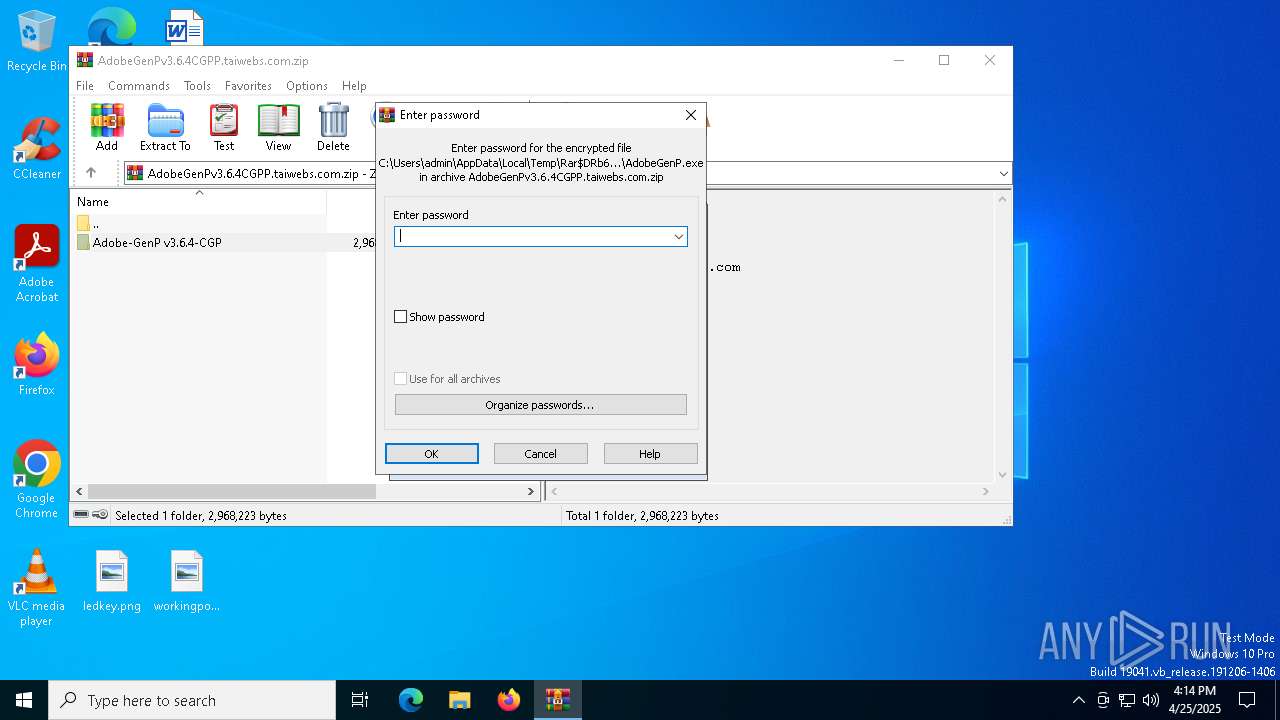
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
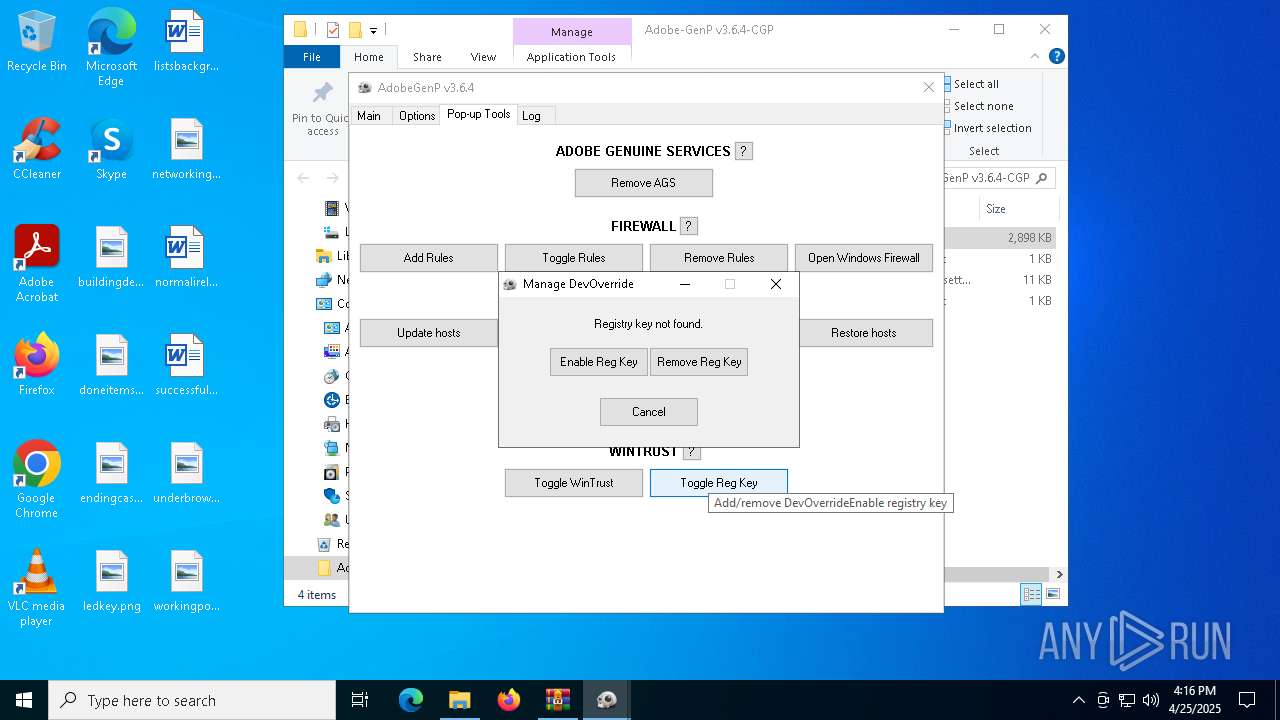
| (PID) Process: | (7776) AdobeGenP.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options |
| Operation: | write | Name: | DevOverrideEnable |
Value: 1 | |||
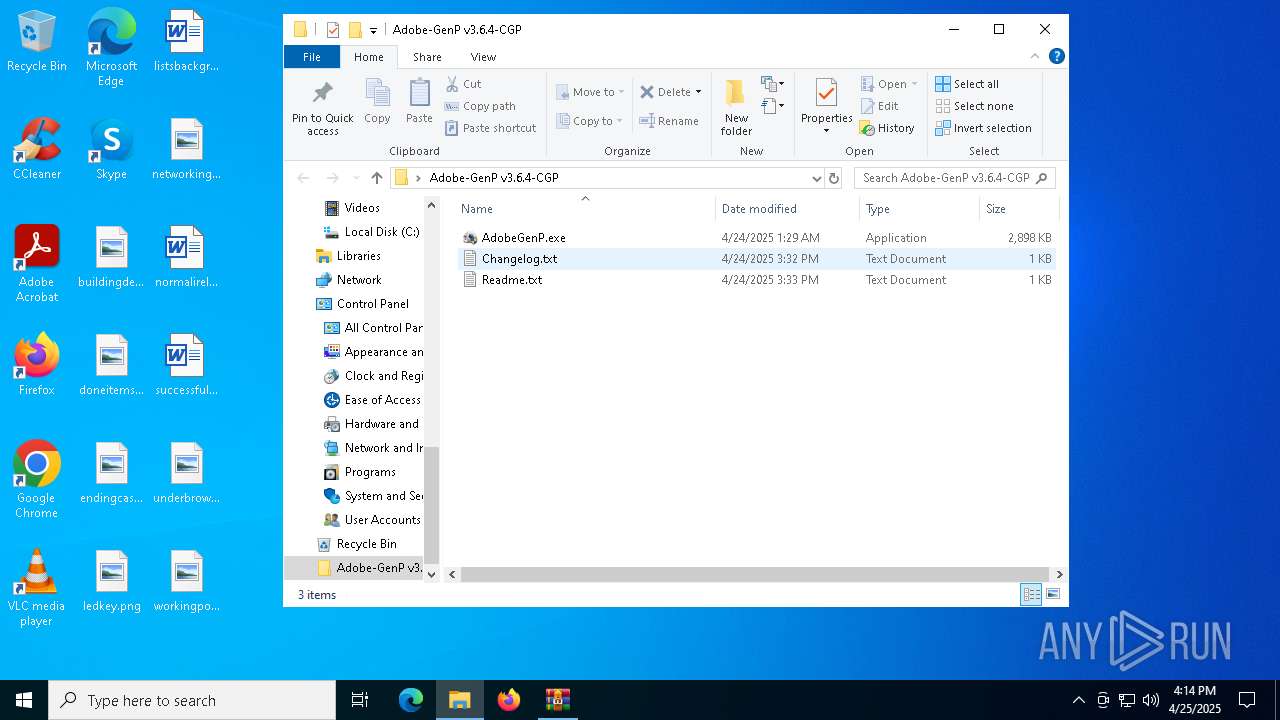
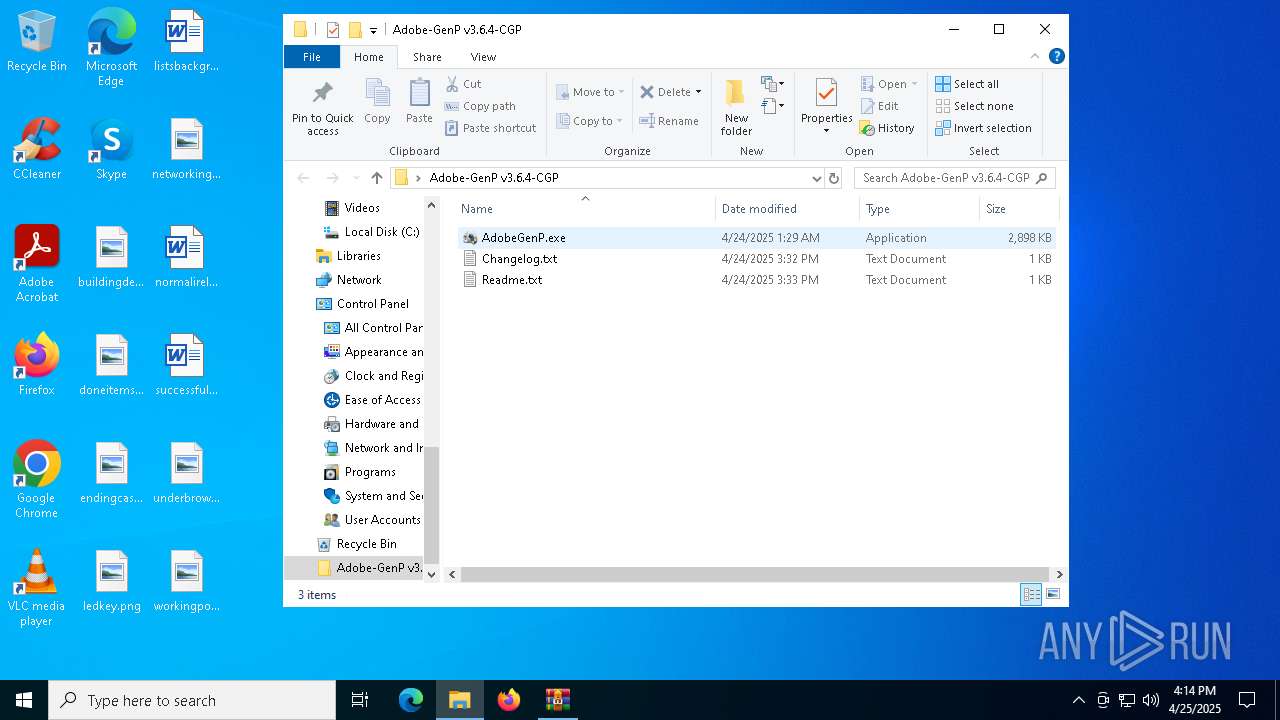
Executable files
2
Suspicious files
2
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
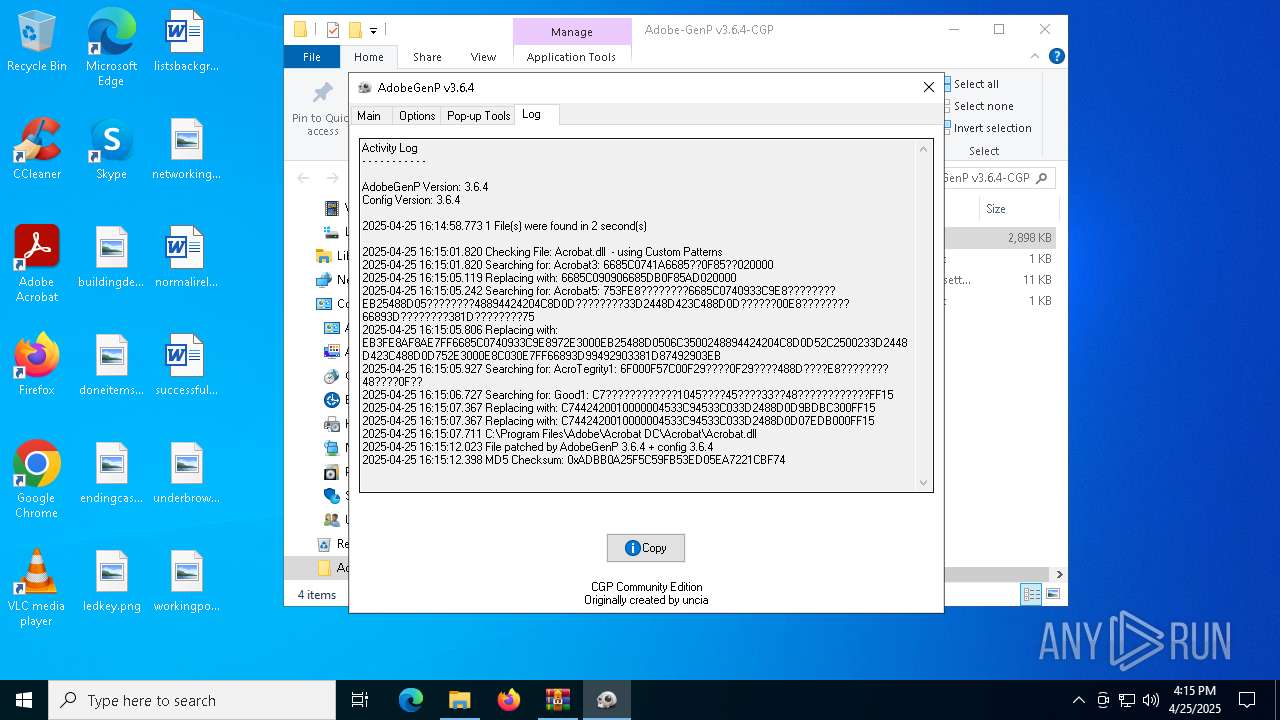
| 7776 | AdobeGenP.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 7776 | AdobeGenP.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 7776 | AdobeGenP.exe | C:\Users\admin\Desktop\Adobe-GenP v3.6.4-CGP\config.ini | text | |
MD5:FABC1F7F0E77C6882B9A16851E7D7E77 | SHA256:5E9A06AB44D12EC8AAAF3918859E8ED807E76CC58B7FEEB9B25741DE8AC4C56D | |||
| 4108 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4tn3l3hn.zsb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6620.48849\Adobe-GenP v3.6.4-CGP\Readme.txt | text | |
MD5:EC9A25B909B5DE50069A61BF73BFE9A5 | SHA256:2481A396D8EA2D76F43726B7882D490EA7C0F5826DE29DB50480DAA551930281 | |||
| 4108 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:742B5A285B7CC6530B9DA359E814159E | SHA256:21F45A3A3DA2A67BF0BBEA7D8F310A6415754148D716E34B9F84179BC44FFDDF | |||
| 7392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vji0tlc3.lpg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6620.48849\Adobe-GenP v3.6.4-CGP\AdobeGenP.exe | executable | |
MD5:859E24EAF9E2B231CF7FADF25D8DB232 | SHA256:B92860632A6DDAE2532206833CC0C4A18548D469136271ACDBD760E4986E260B | |||
| 4108 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j5i5ofai.mab.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5xin1bak.ecm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.151:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7872 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
7872 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.151:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |