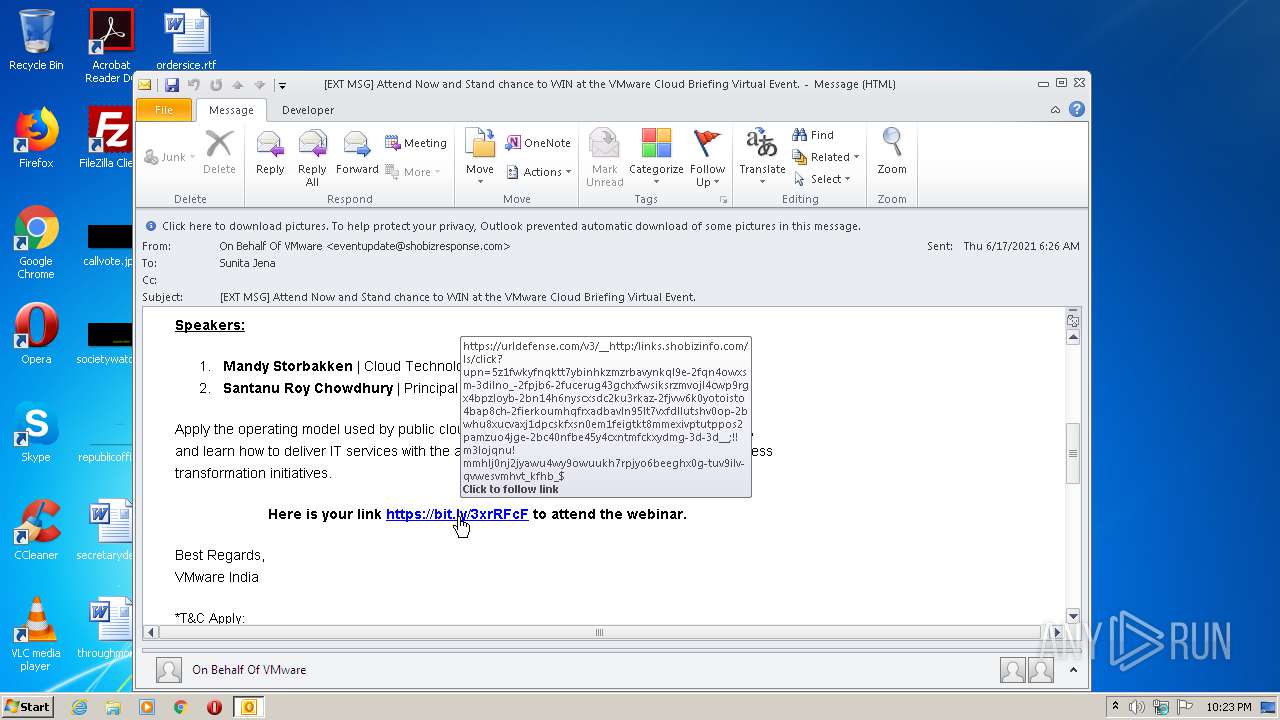
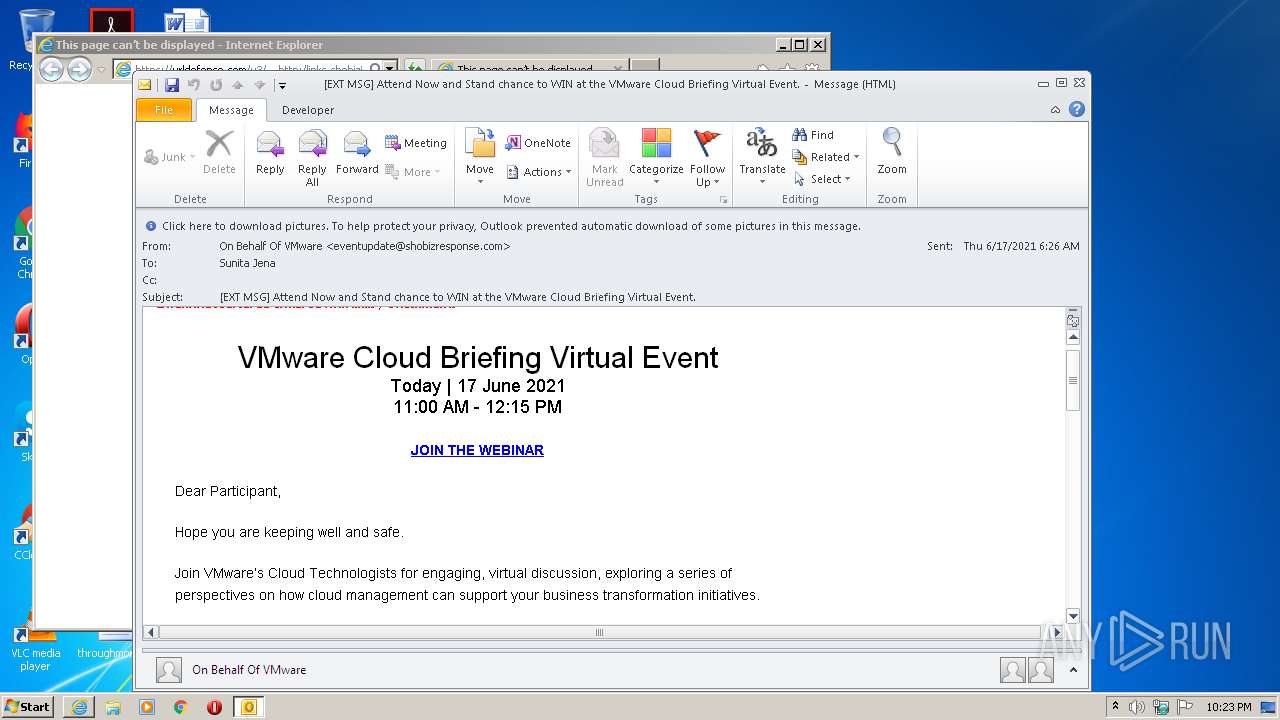
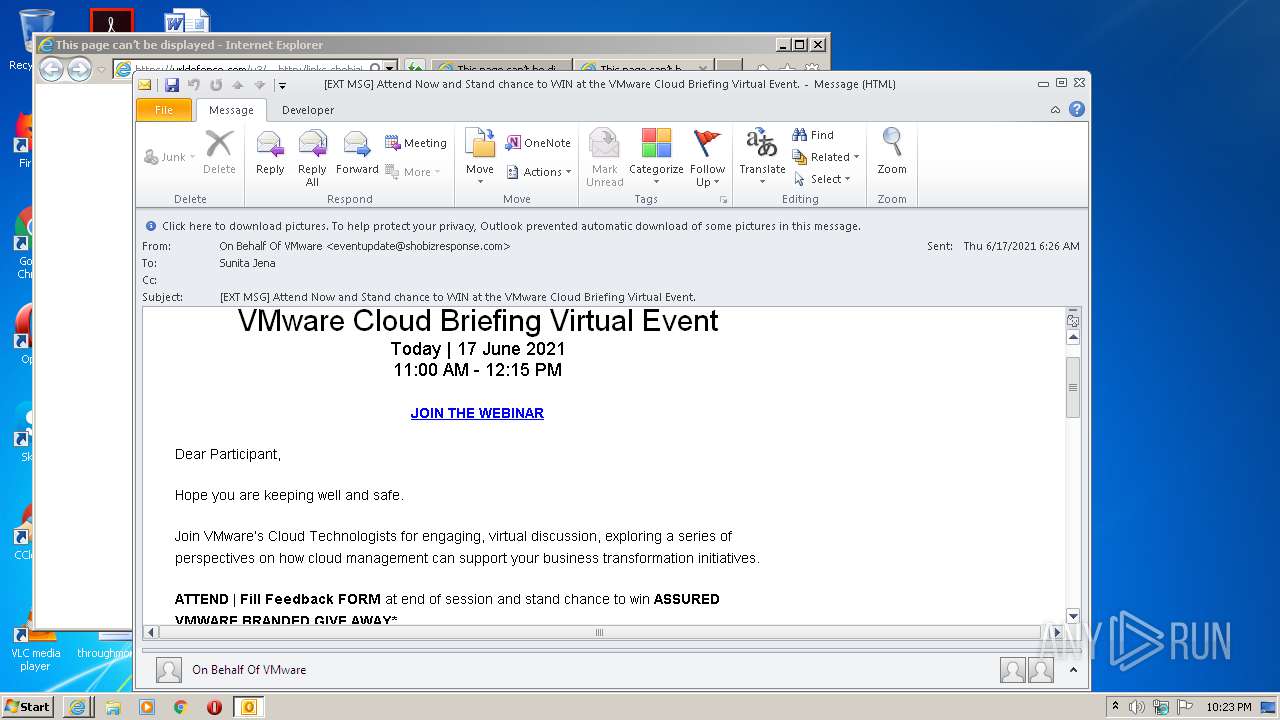
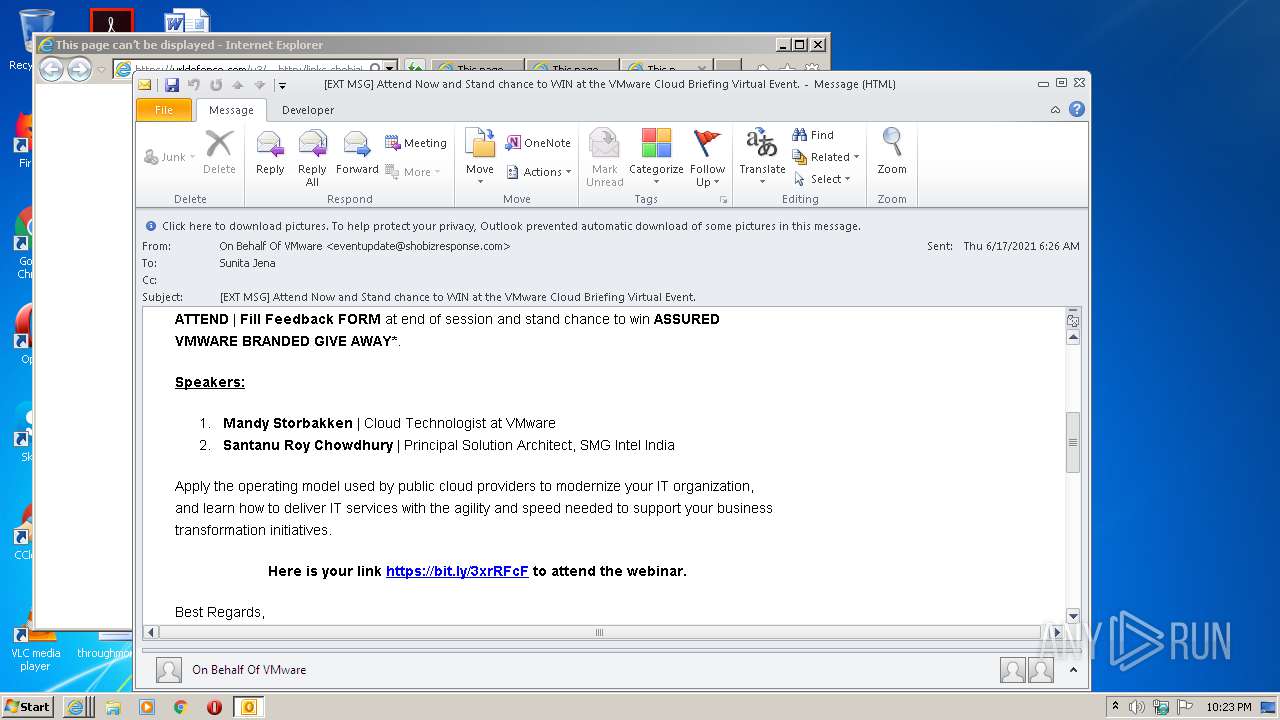
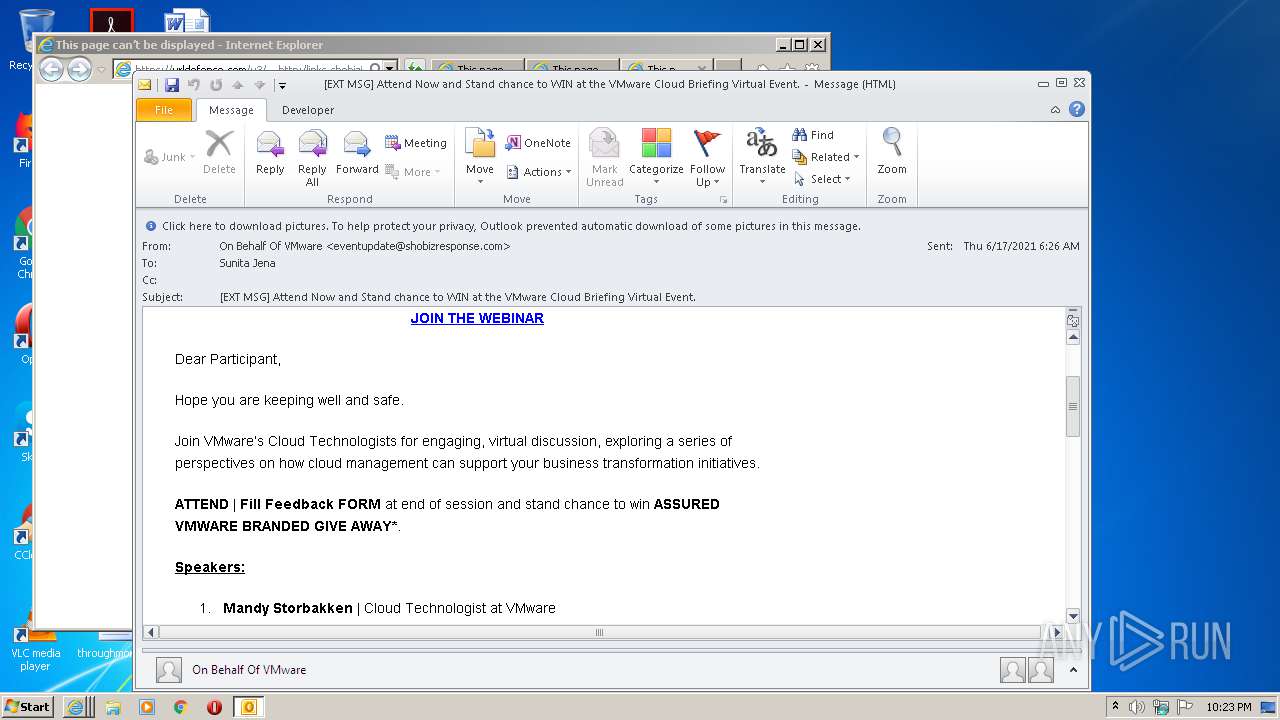
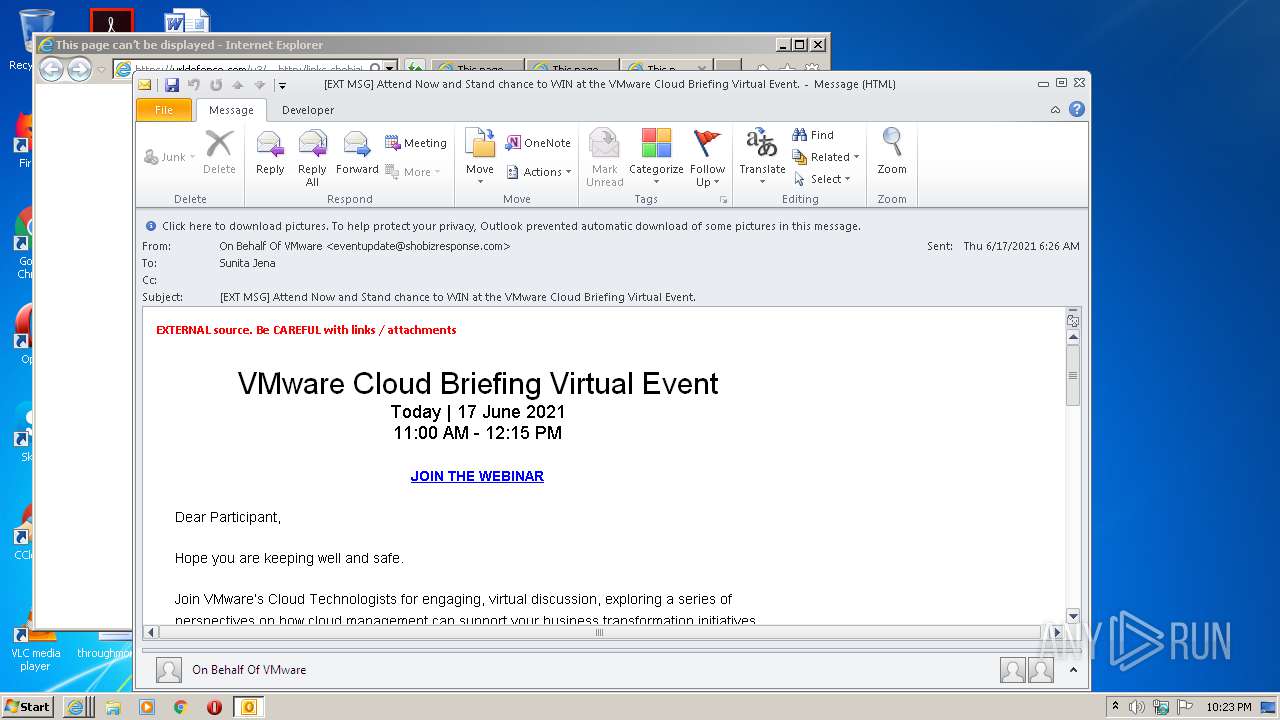
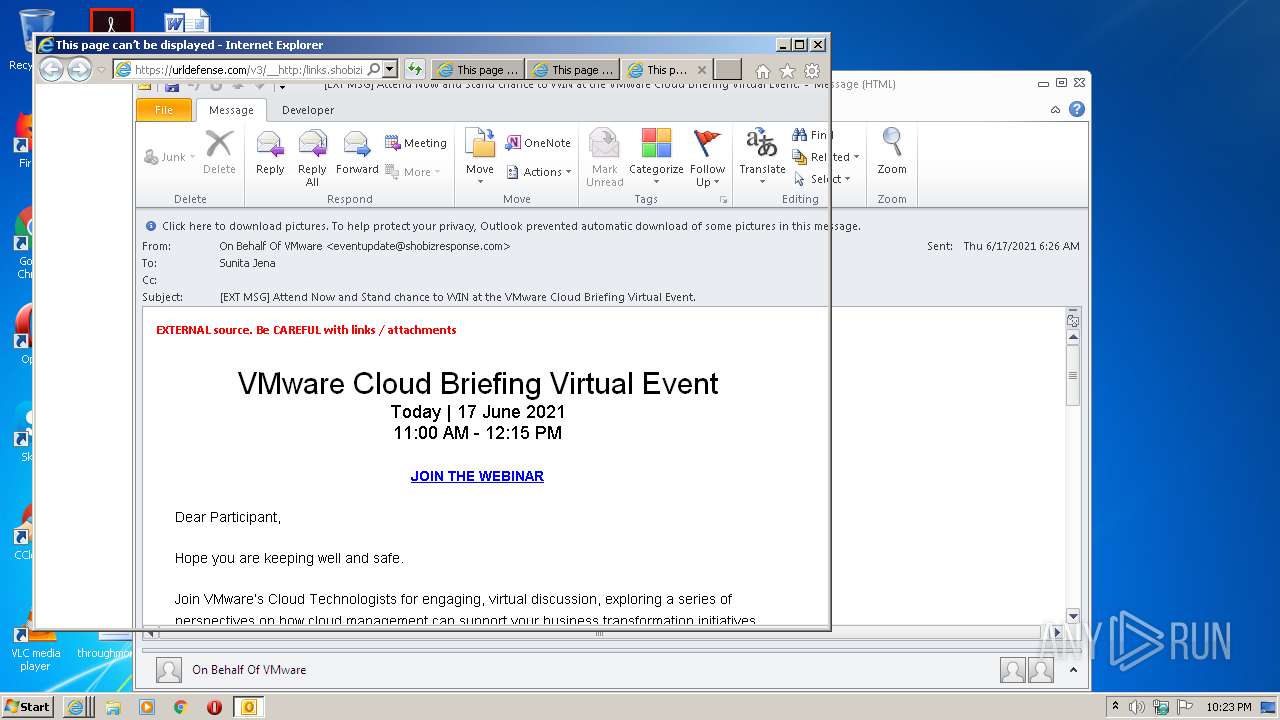
| File name: | EXT MSG Attend Now and Stand chance to WIN at the VMware Cloud Briefing Virtual Event.msg |
| Full analysis: | https://app.any.run/tasks/b391fb89-018f-49f8-8f97-5f2d39e5ce82 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2021, 21:22:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 06646E26F5AE222CFA2B6F05422AD1C6 |
| SHA1: | 9B708807CA9C68C35F32C2B55A77AB95DBE53CB4 |
| SHA256: | C0D5974A44EF4281C118B12B4C15D0AB38797289F877CF75EB14CF1F9499E52A |
| SSDEEP: | 3072:B2n47Dvu9uCSu1uxvwpwCFuqWRlhIiiKHgo0NBWB52KZLfcZB+VW11q:sn0nRl+SHgo0WqK |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2196)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2196)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2500)
Reads internet explorer settings
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 3884)
Application launched itself
- iexplore.exe (PID: 2500)
Reads settings of System Certificates
- iexplore.exe (PID: 2500)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2196)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2500)
Changes settings of System certificates
- iexplore.exe (PID: 2500)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\EXT MSG Attend Now and Stand chance to WIN at the VMware Cloud Briefing Virtual Event.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:202006 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
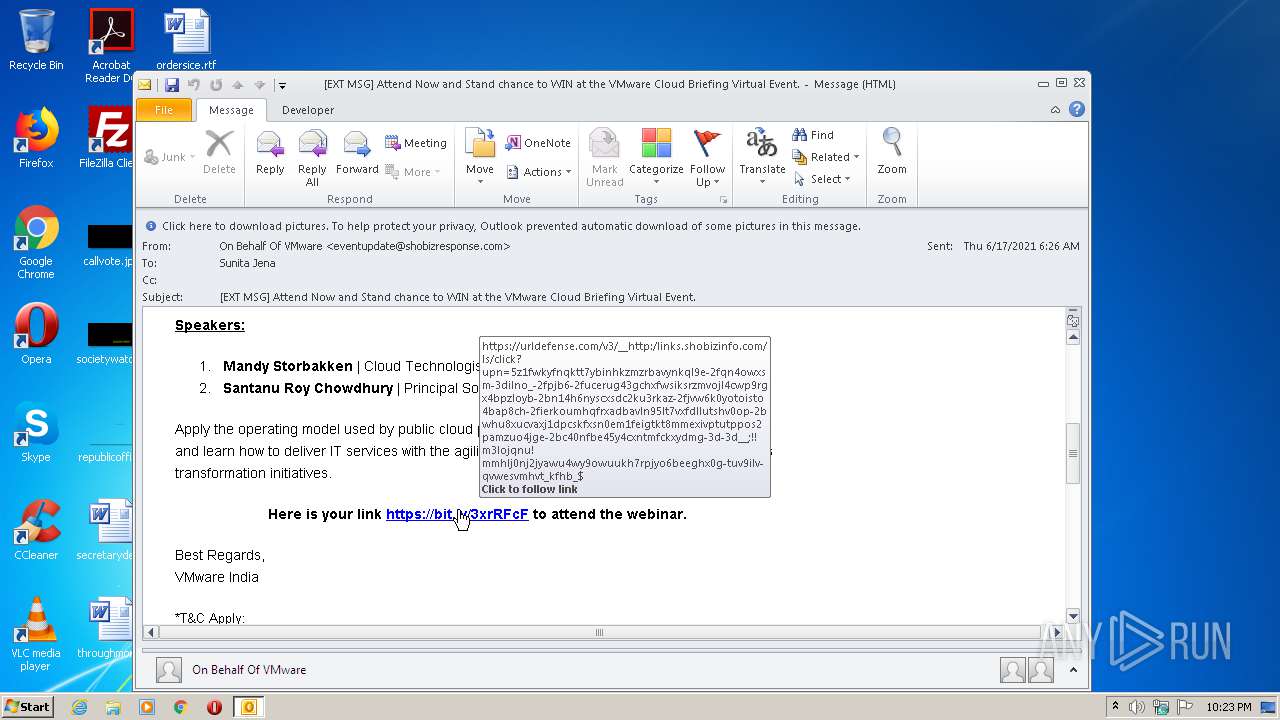
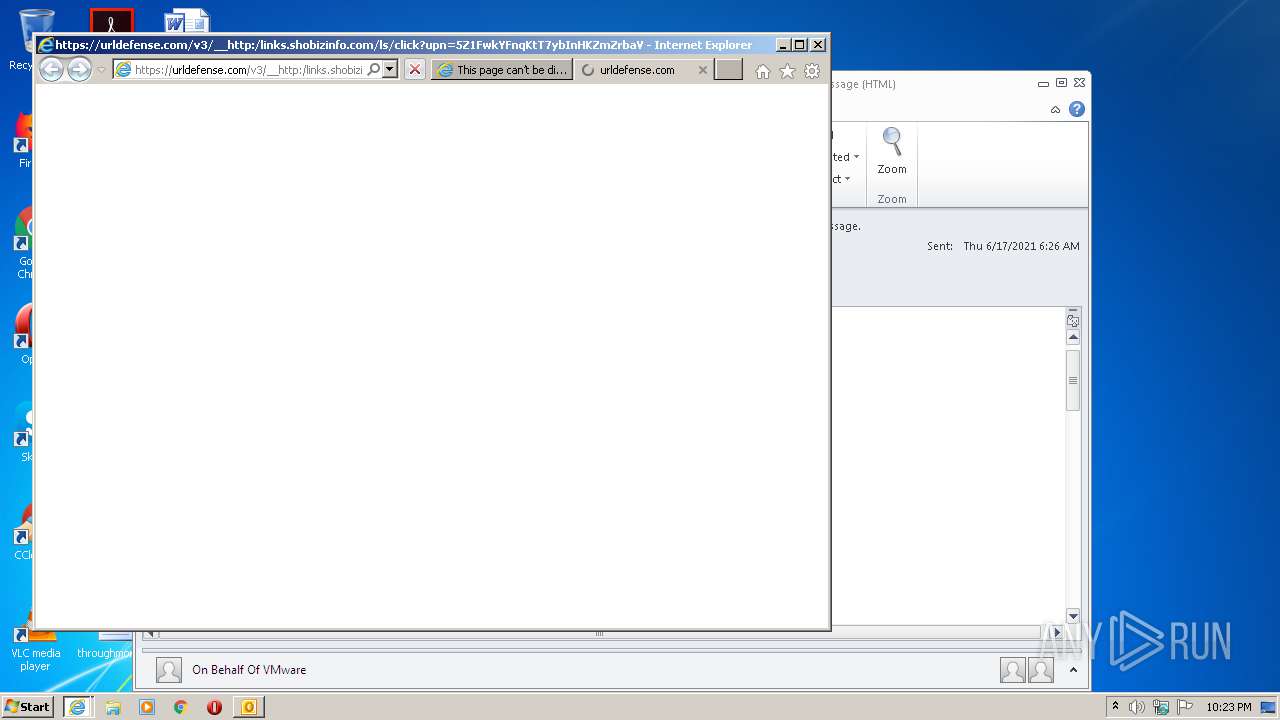
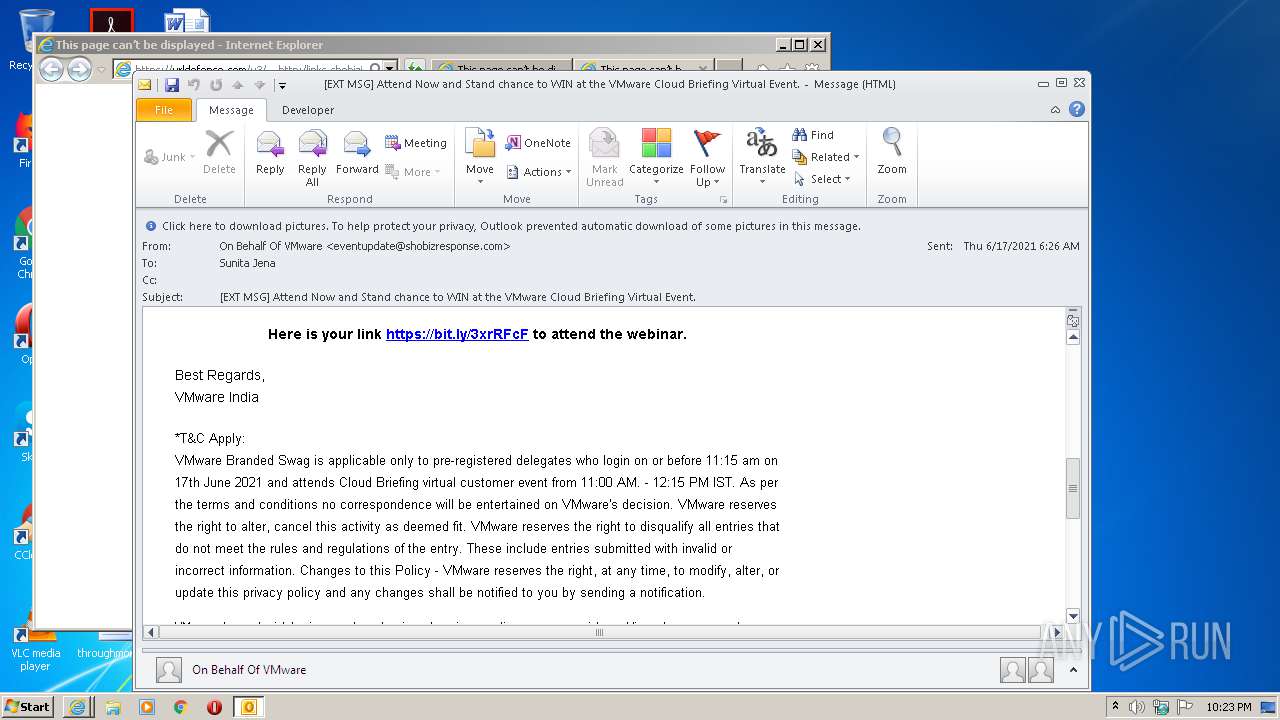
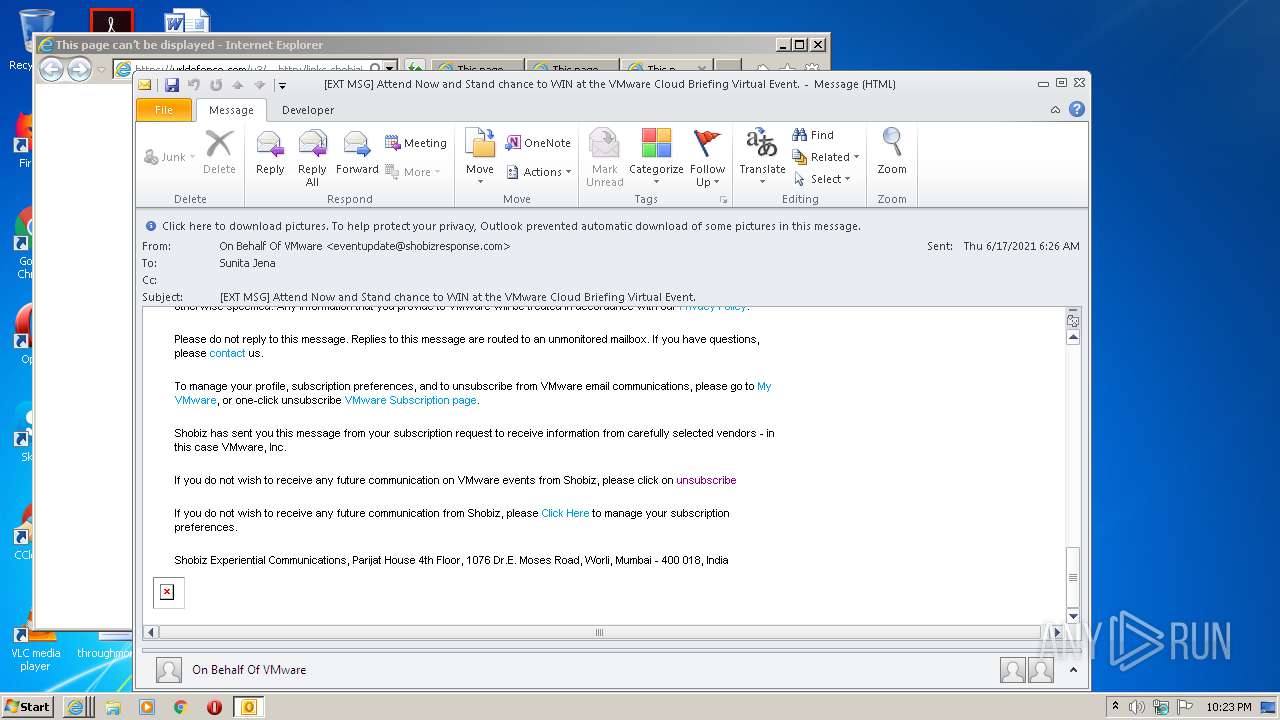
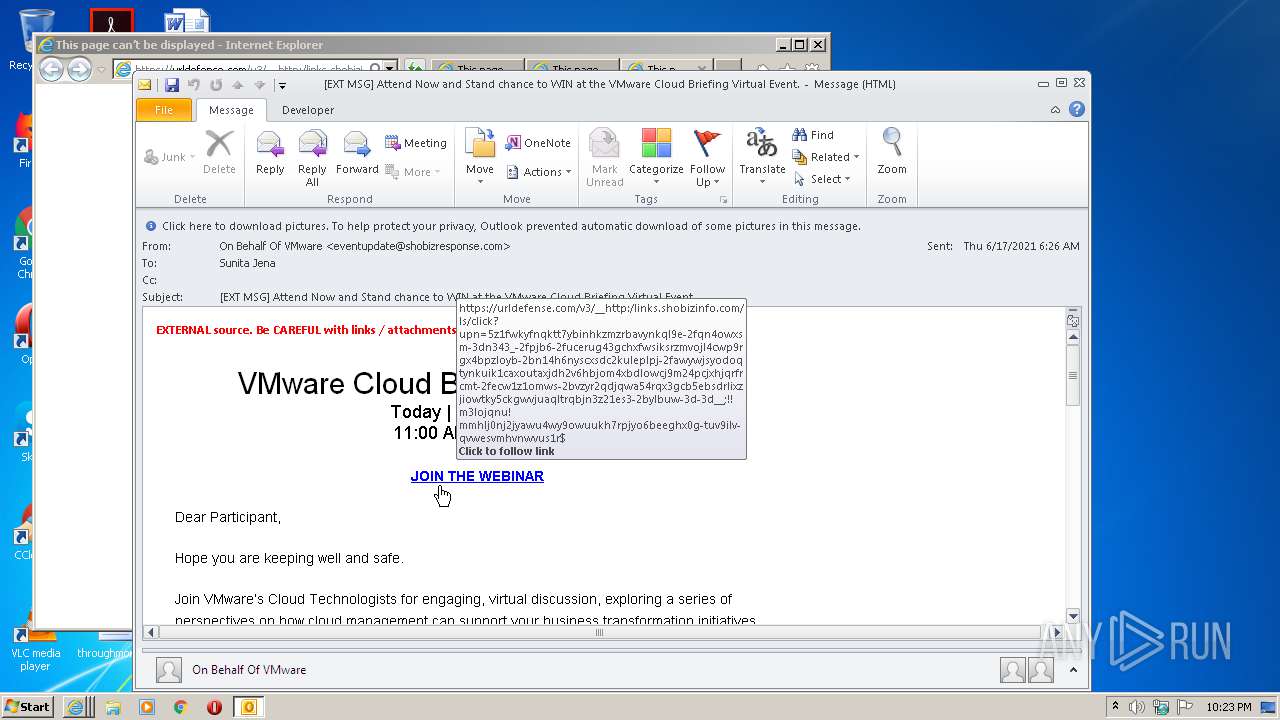
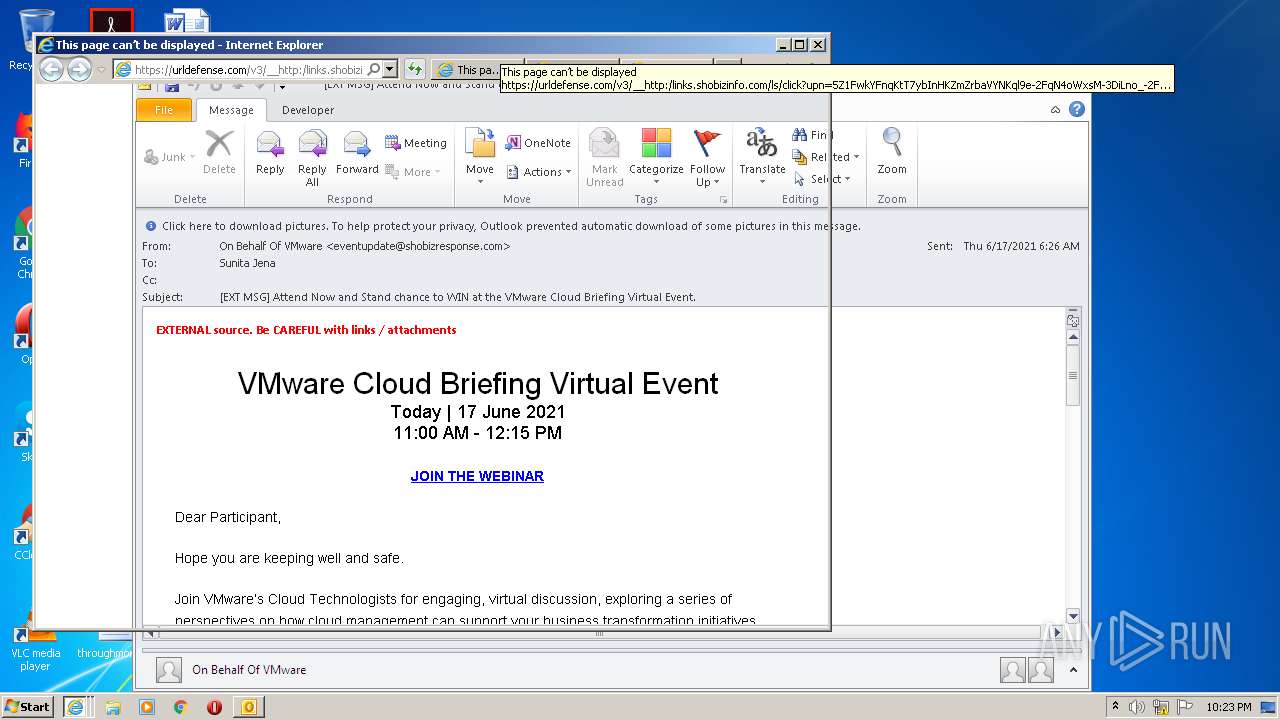
| 2500 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.com/v3/__http:/links.shobizinfo.com/ls/click?upn=5Z1FwkYFnqKtT7ybInHKZmZrbaVYNKql9e-2FqN4oWxsM-3DiLno_-2FpJB6-2FucERug43GCHXfwsiKsrZMvOJl4cwp9Rgx4bpzLoyb-2BN14h6NYsCXSDC2KU3RkaZ-2FJVW6K0YOTOiSto4BAP8Ch-2FiERkoUmhQFRxaDBAvln95Lt7VxFDLlUtshV0op-2BwHU8xuCvAXj1DPCsKFXsN0em1feIGtKt8mmExIVPtuTpPoS2Pamzuo4jGe-2BC40nfBe45y4CxnTMFcKXydMg-3D-3D__;!!M3LOjqNU!MmHLj0nJ2Jyawu4wy9OwUukH7RPjYo6beEGhX0g-tUv9Ilv-QVweSVMhVt_kfhB_$ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3884 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:464156 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 435
Read events
1 746
Write events
668
Delete events
21
Modification events
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
42
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF272.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\msoF7A3.tmp | — | |
MD5:— | SHA256:— | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_D87C65E60513F949AE13F20E4CE3CF9F.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{E6F9A07F-8329-44F7-A03E-646562D1E6DF}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_362C264E42A9F04F8A045E9268EF34AC.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_090953D84D2B754AA2A6A4F96338DBB6.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
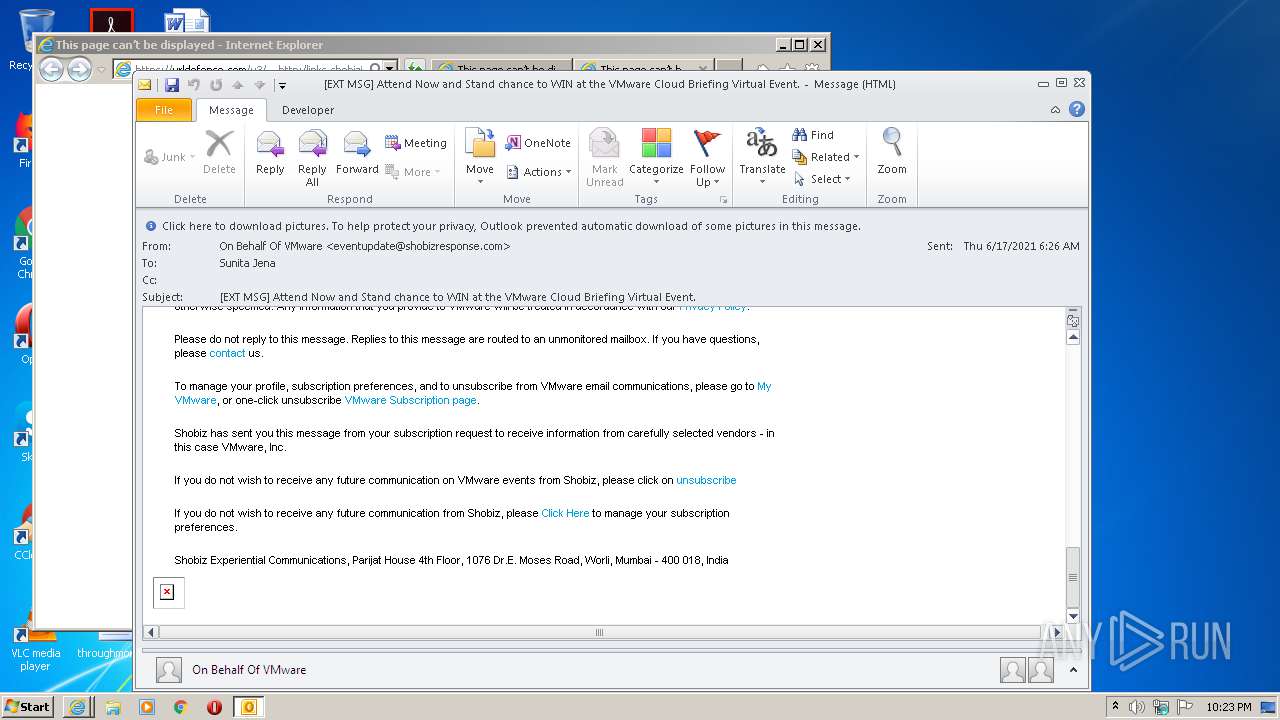
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
27
DNS requests
13
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2500 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 4.19 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2196 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
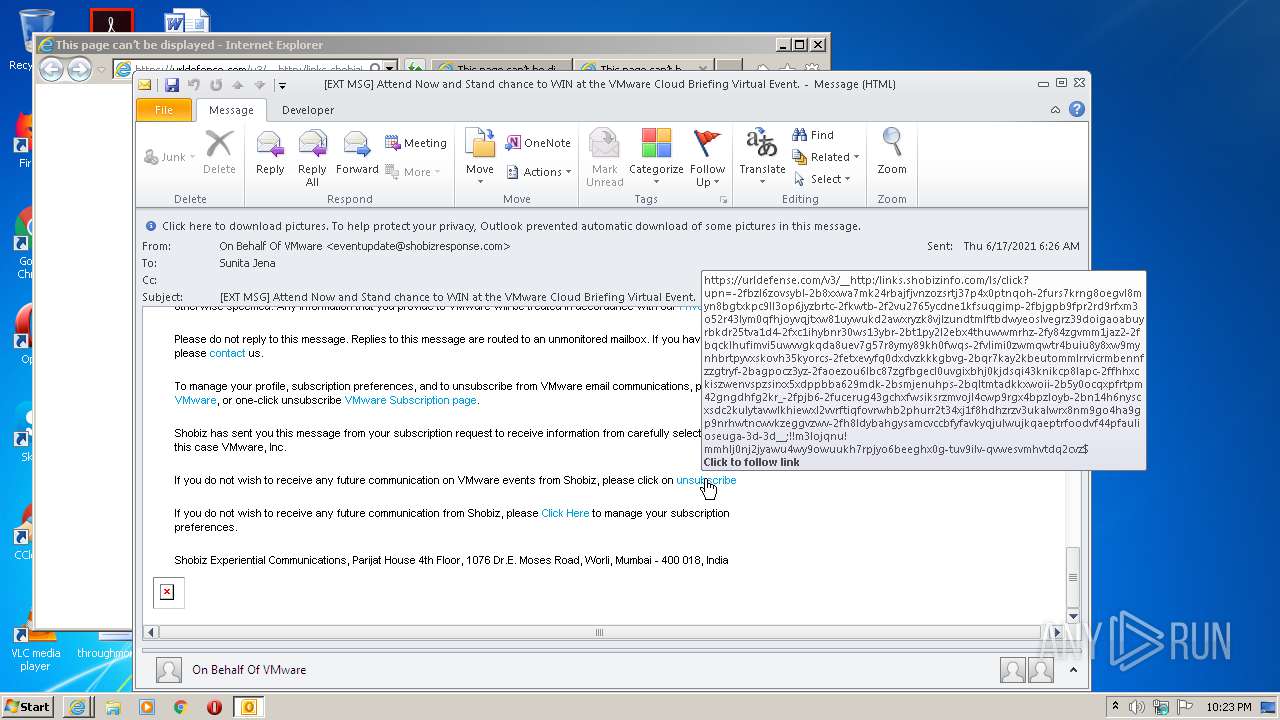
3456 | iexplore.exe | 52.71.28.102:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
— | — | 52.71.28.102:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
2500 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3884 | iexplore.exe | 52.71.28.102:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
2432 | iexplore.exe | 52.6.56.188:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
2500 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2500 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3456 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3456 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2432 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2432 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3884 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3884 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |