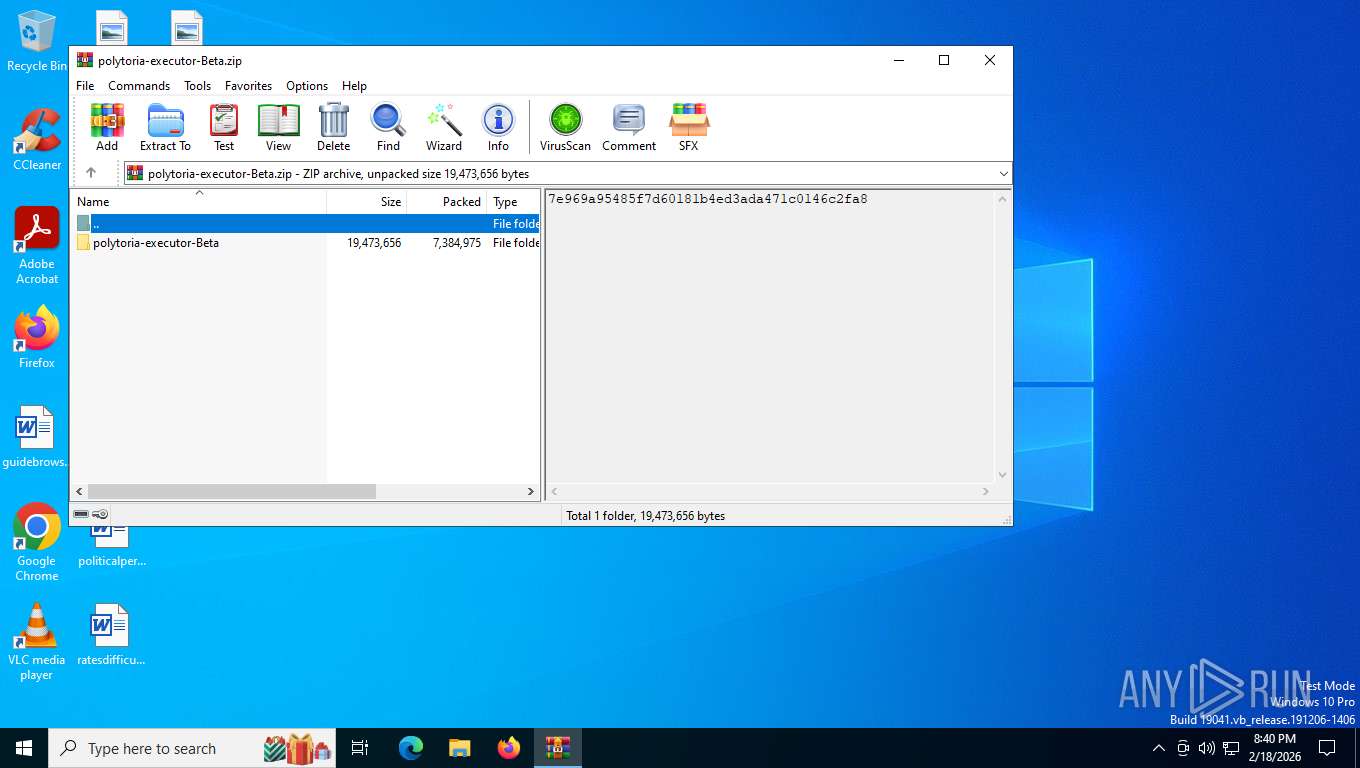
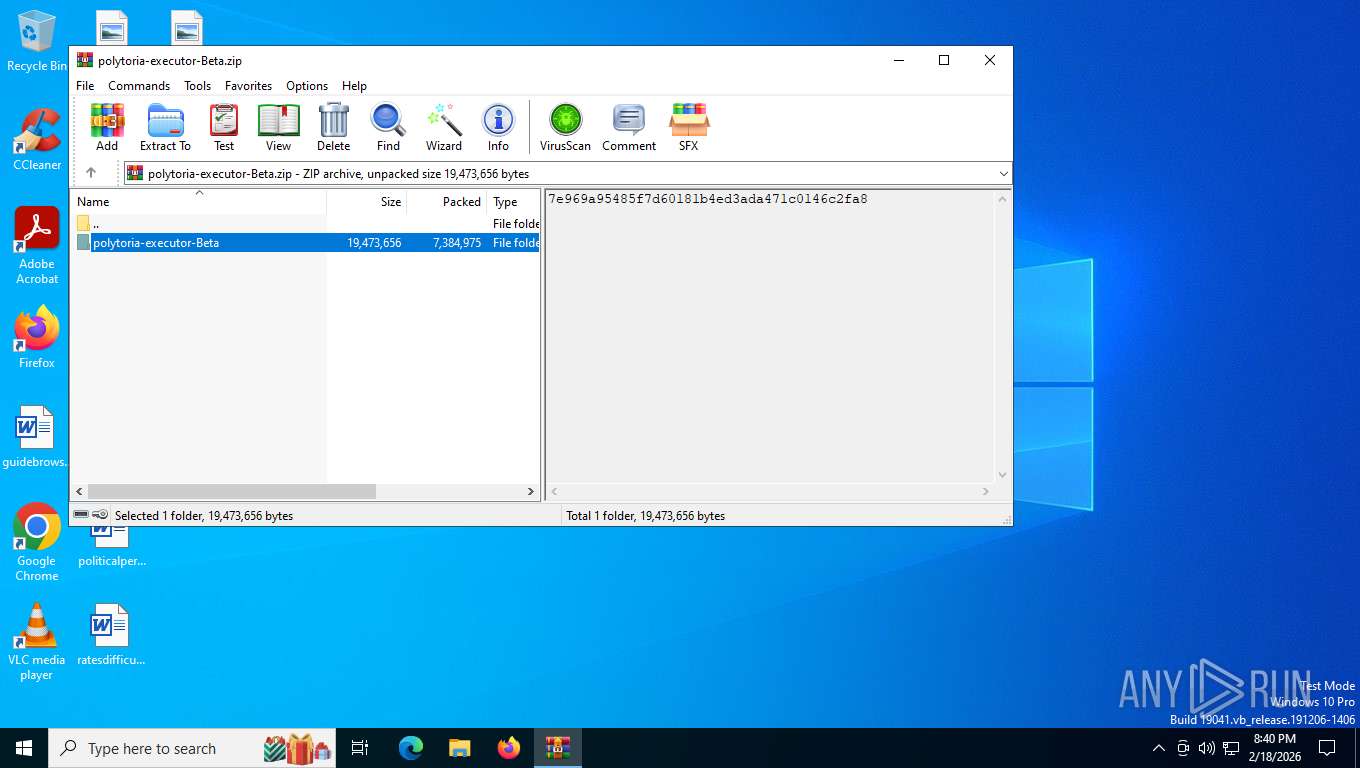
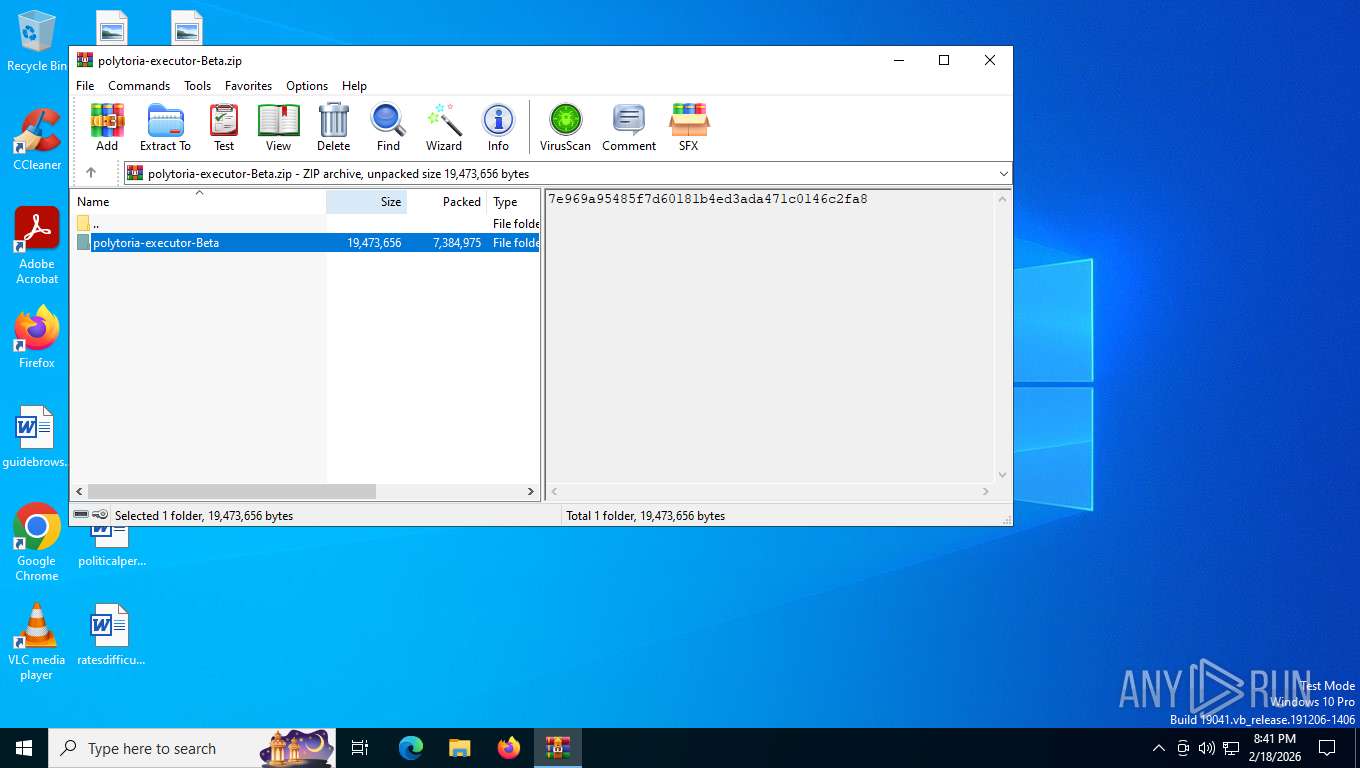
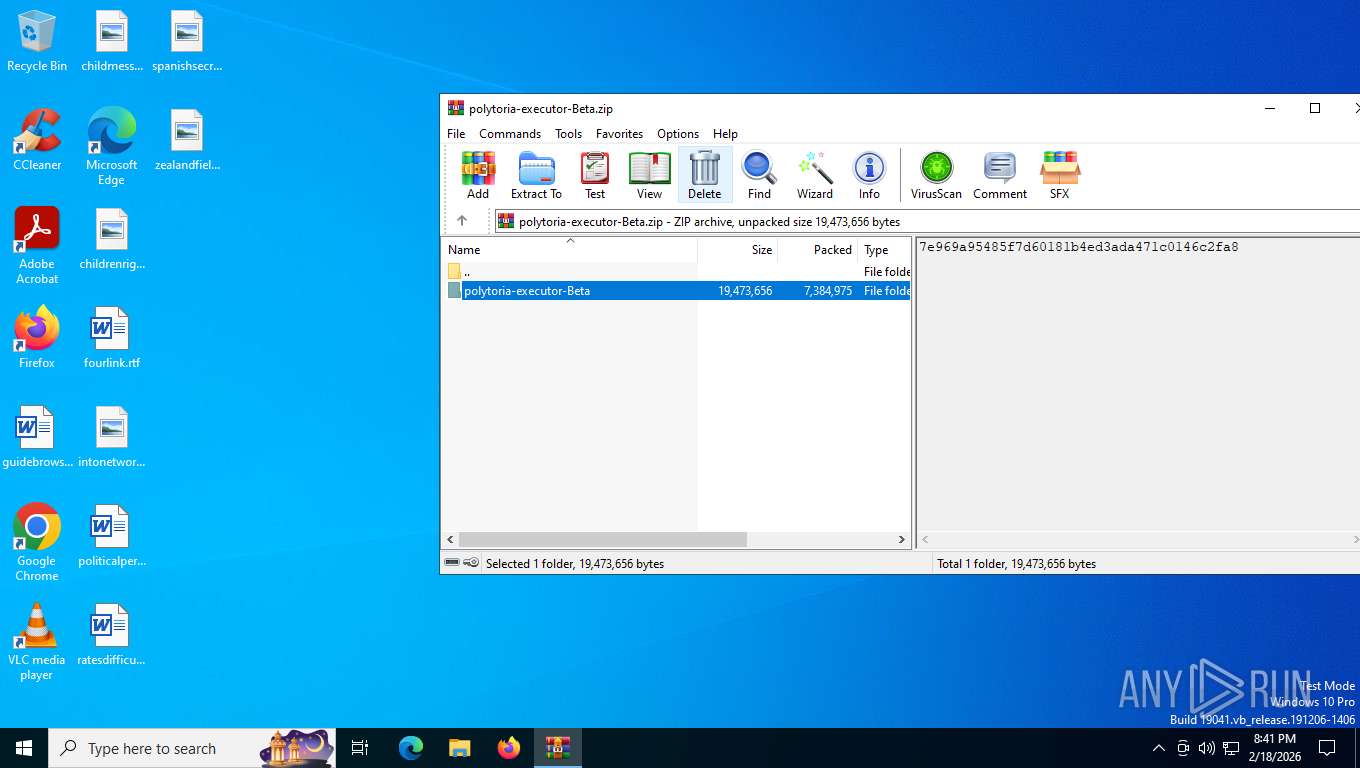
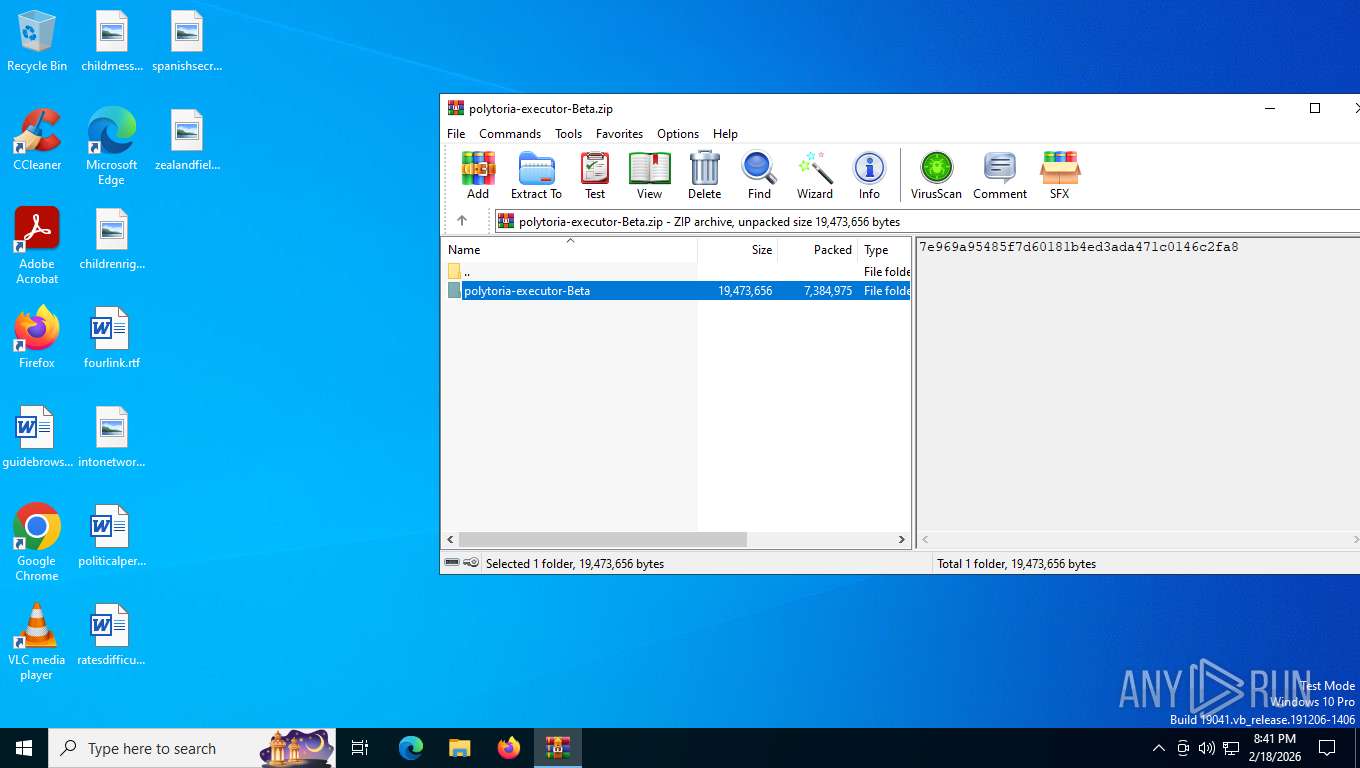
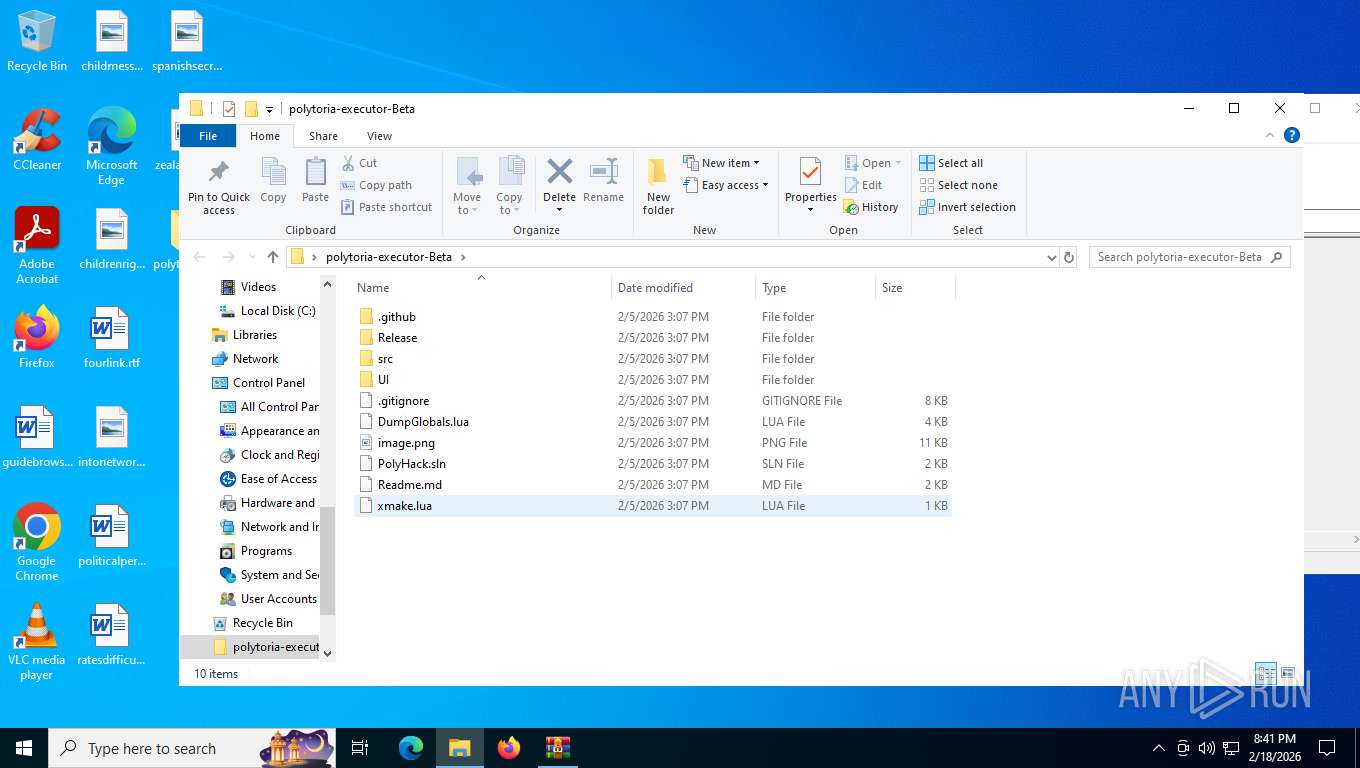
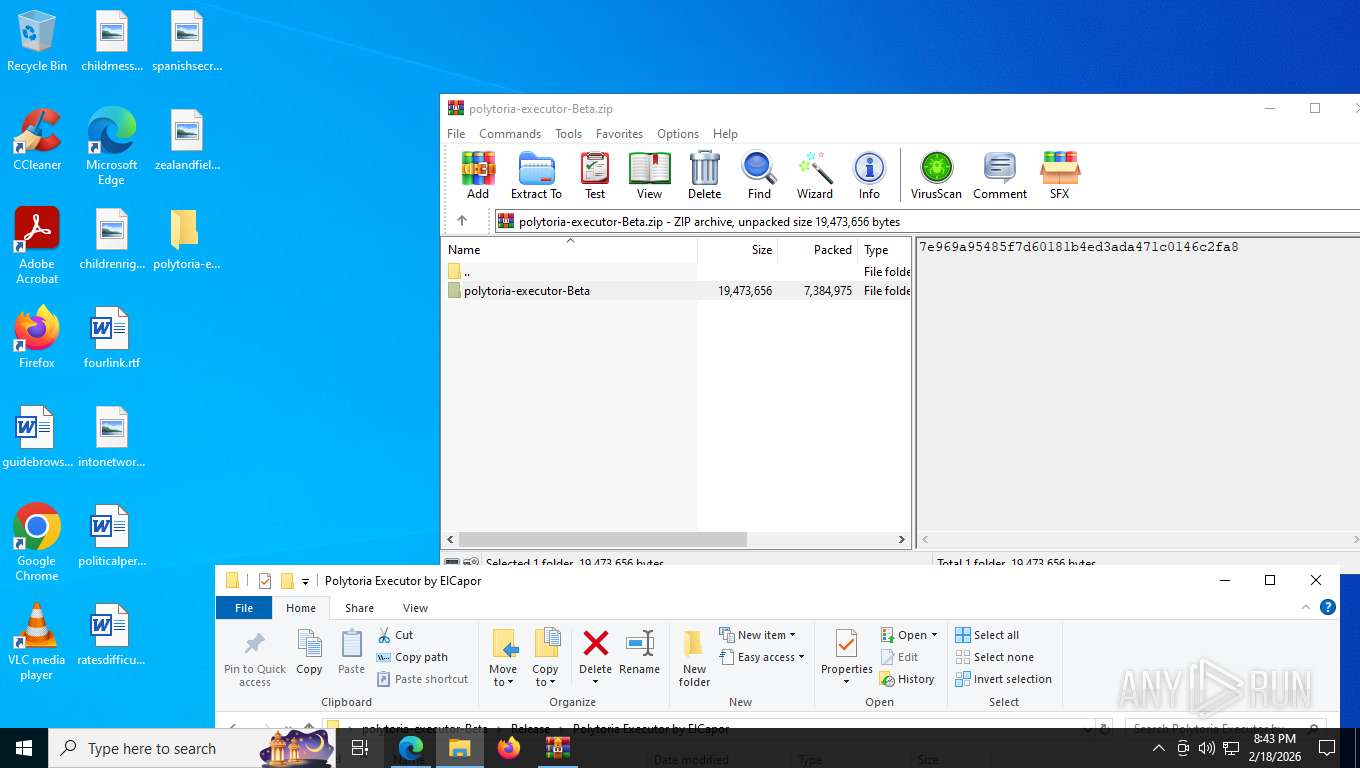
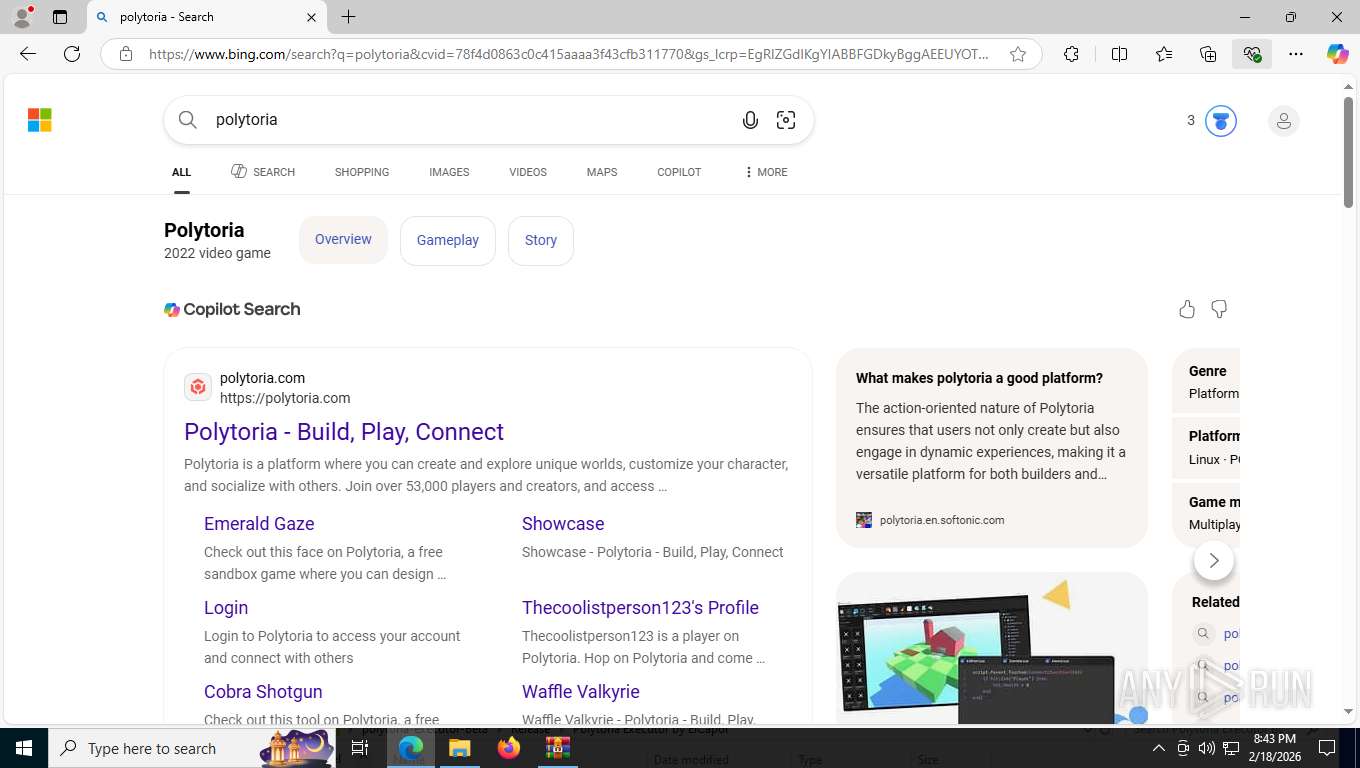
| File name: | polytoria-executor-Beta.zip |
| Full analysis: | https://app.any.run/tasks/3622424c-8830-4e4e-a9a9-bcaeab9b263f |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2026, 01:40:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 68C3C60B8A1CCE7C204E01D5BBF1CBD1 |
| SHA1: | 6DFD2A3C34B30C01BCF20B75FBF2E13D4E7B35E0 |
| SHA256: | C0D2B51260DE5F2C46C7033D58A1E3E2B3209850EEC2555E0A6275F0AC62728E |
| SSDEEP: | 98304:AFnygFQlyiaEhlC/jsvWfrc+E6HGz0w6NZgfzksBUZ6Bt6tAqqF/RZonONoH2XlE:QiqoiDEFFu |
MALICIOUS
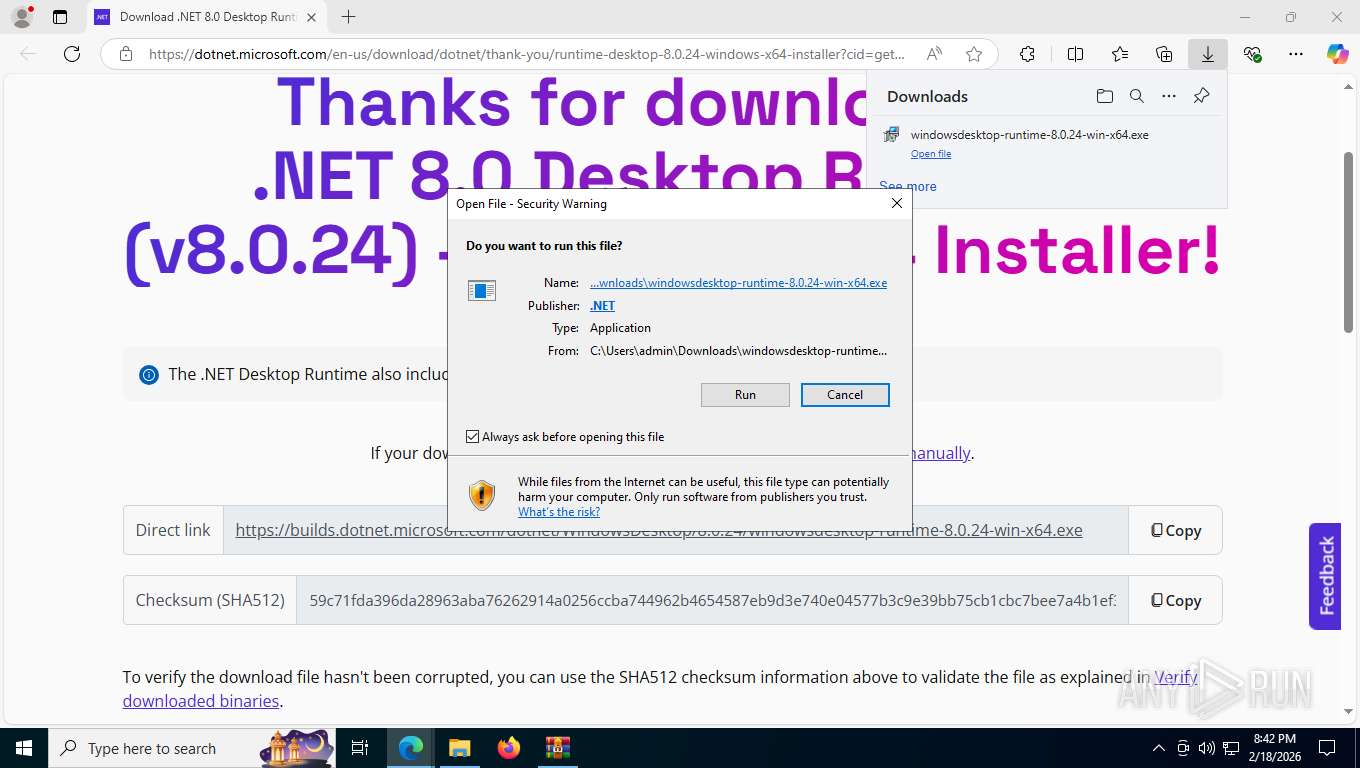
Changes the autorun value in the registry
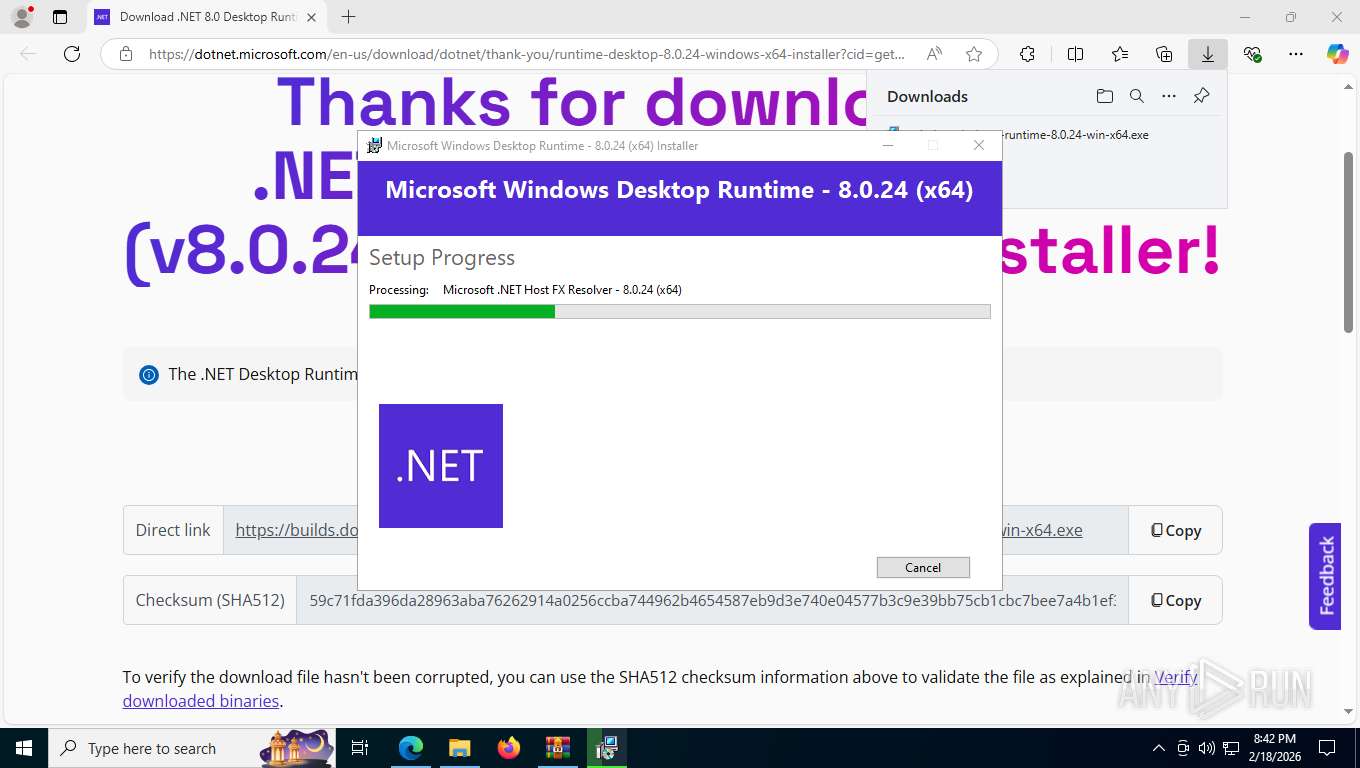
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
GENERIC has been found (auto)
- msiexec.exe (PID: 7028)
SUSPICIOUS
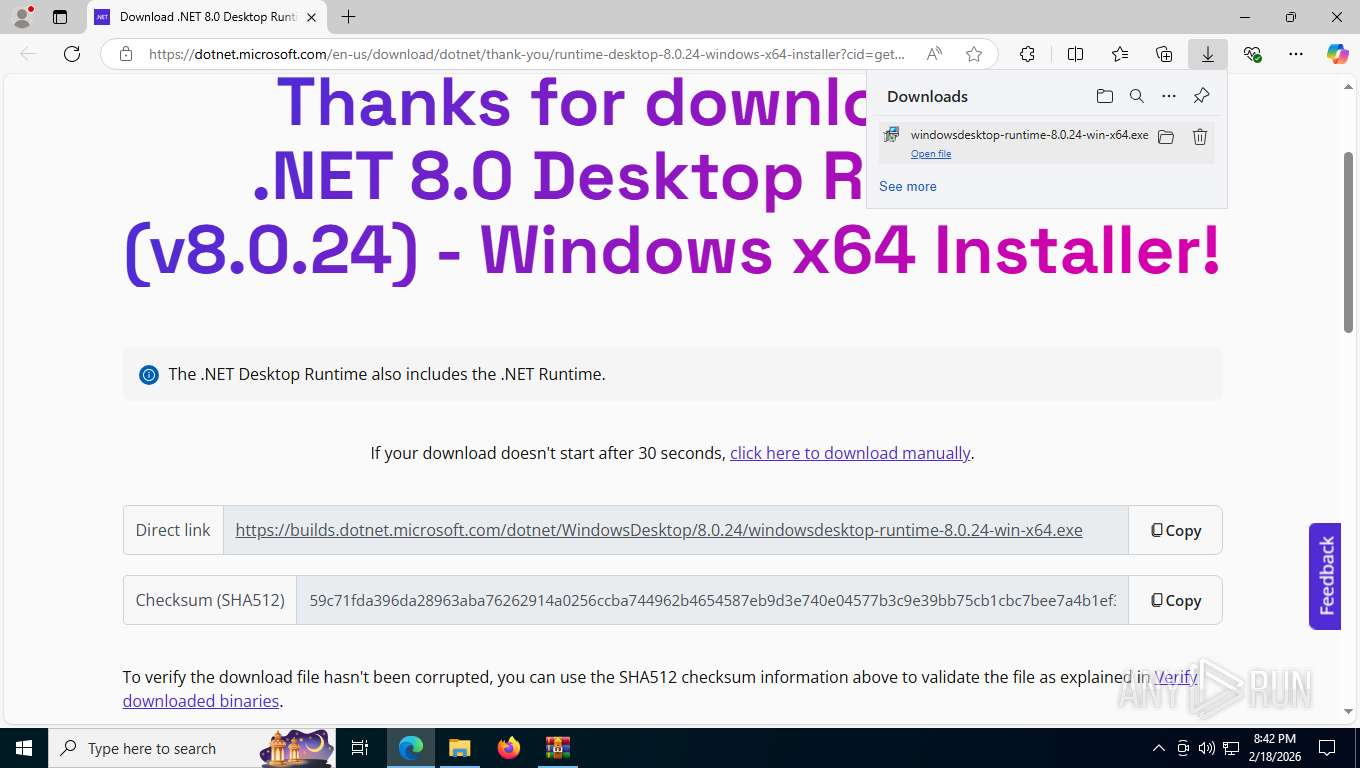
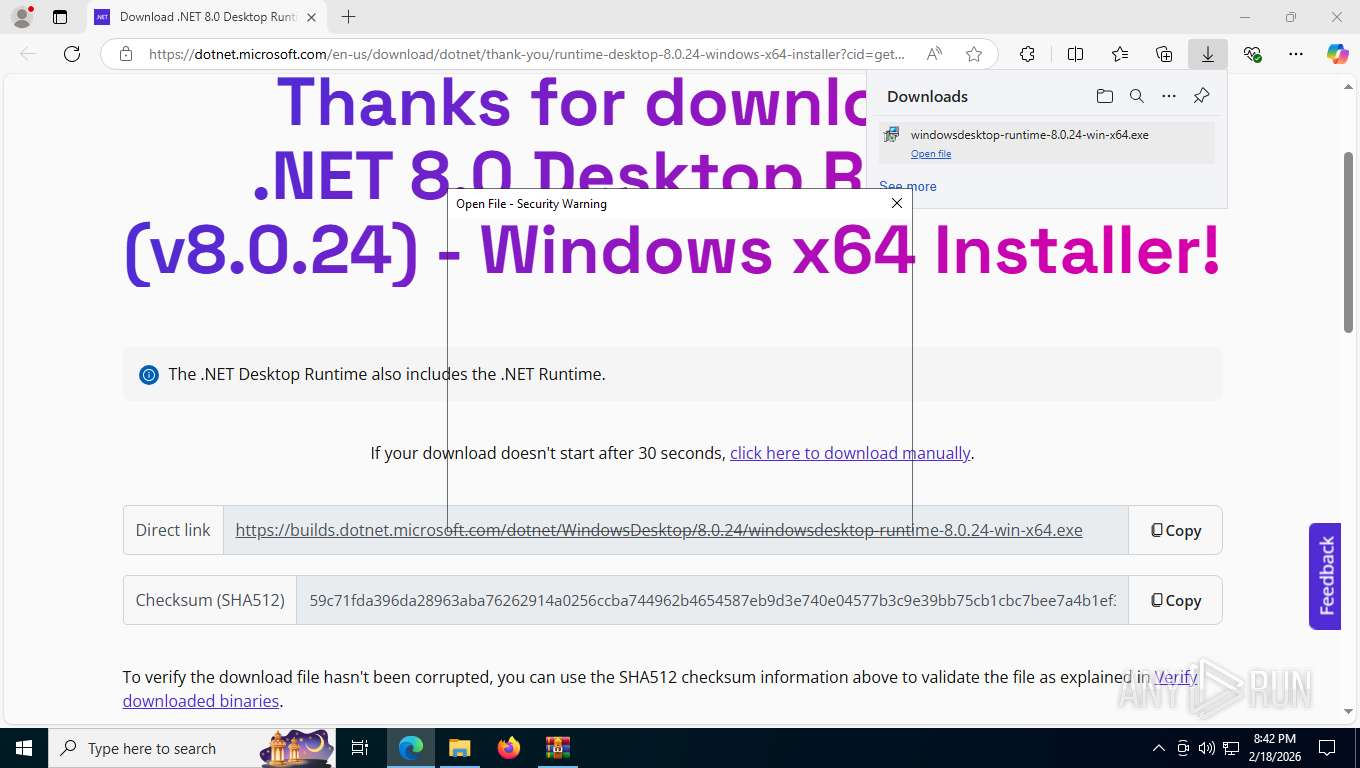
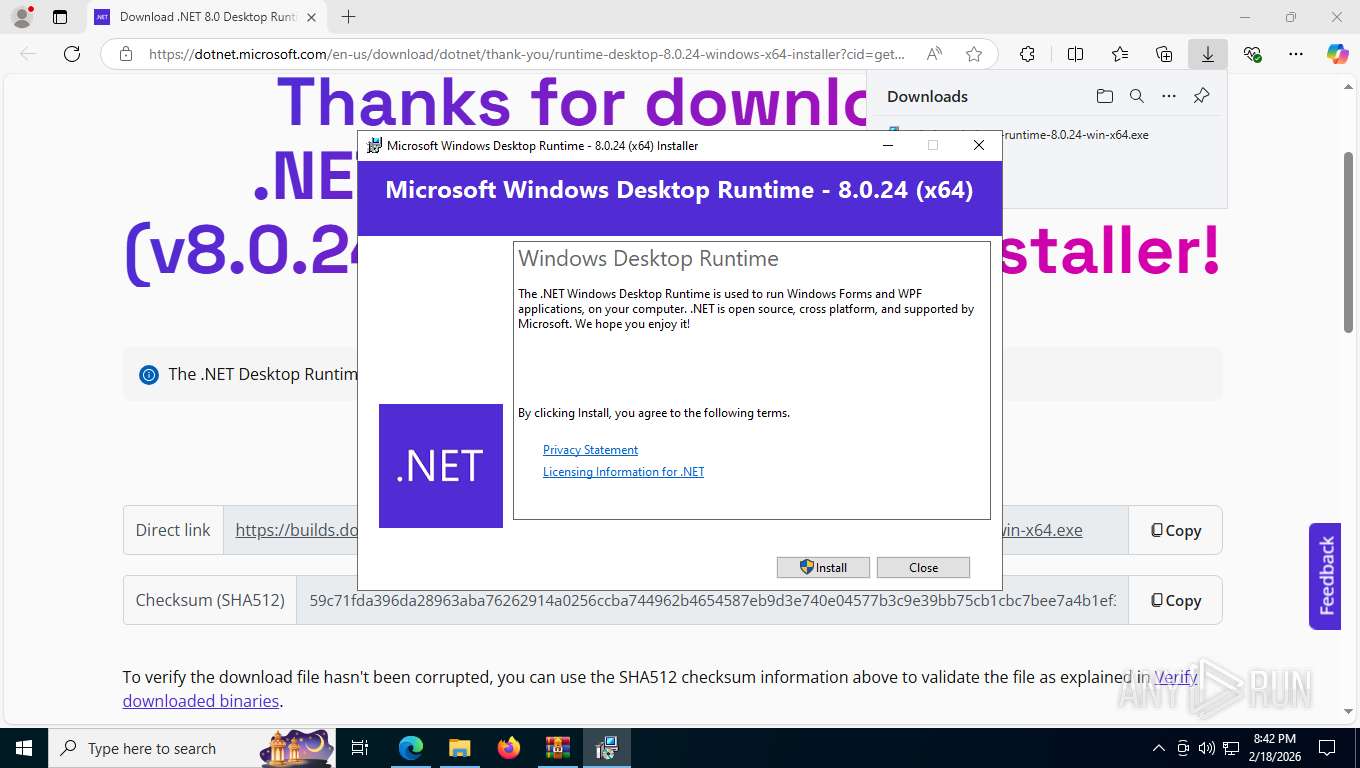
Starts itself from another location
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
Searches for installed software
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7028)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7028)
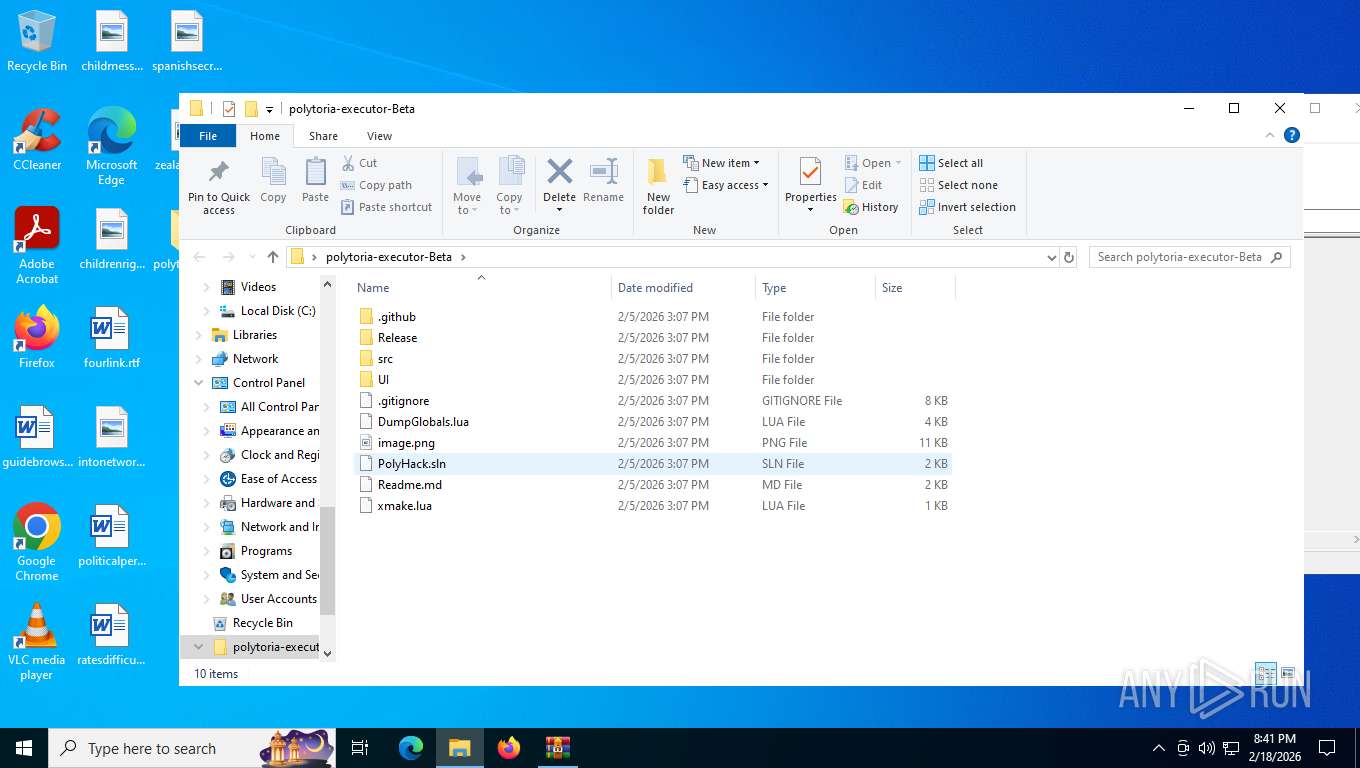
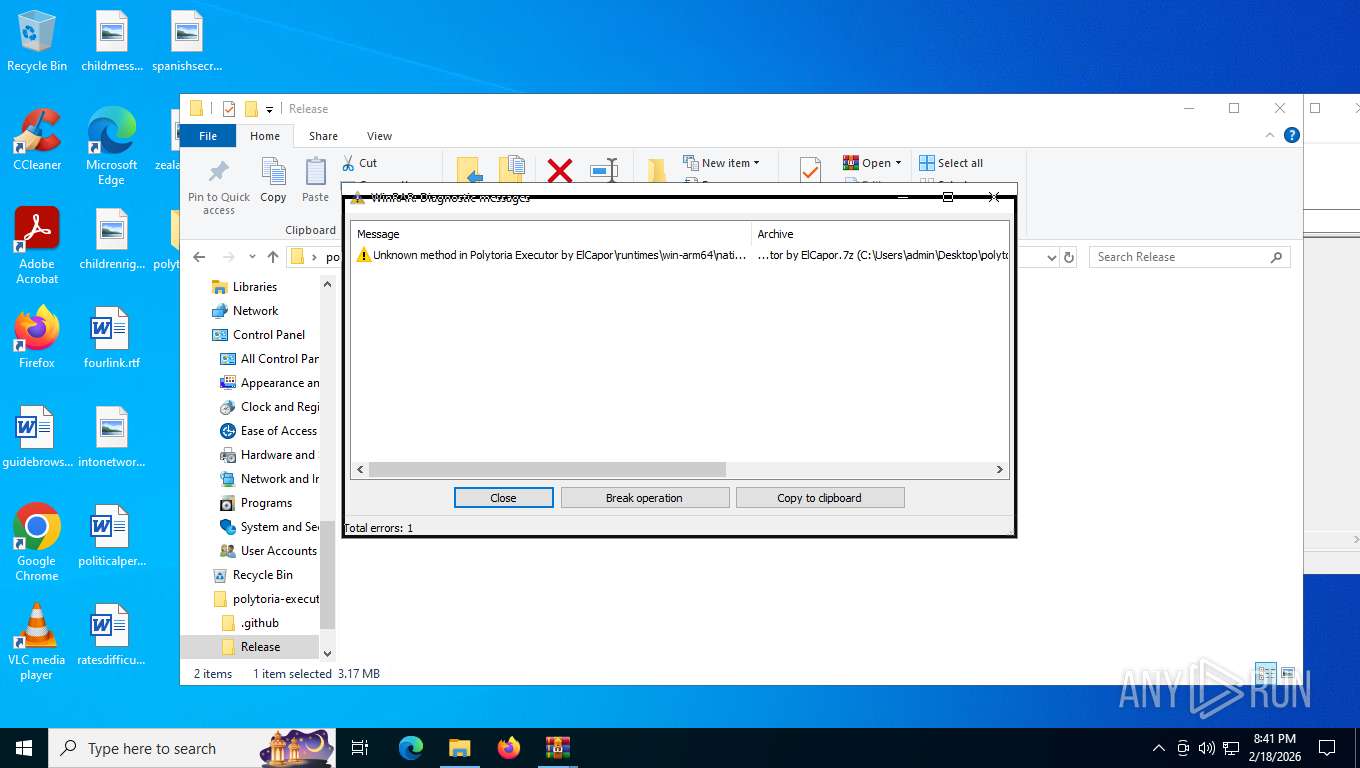
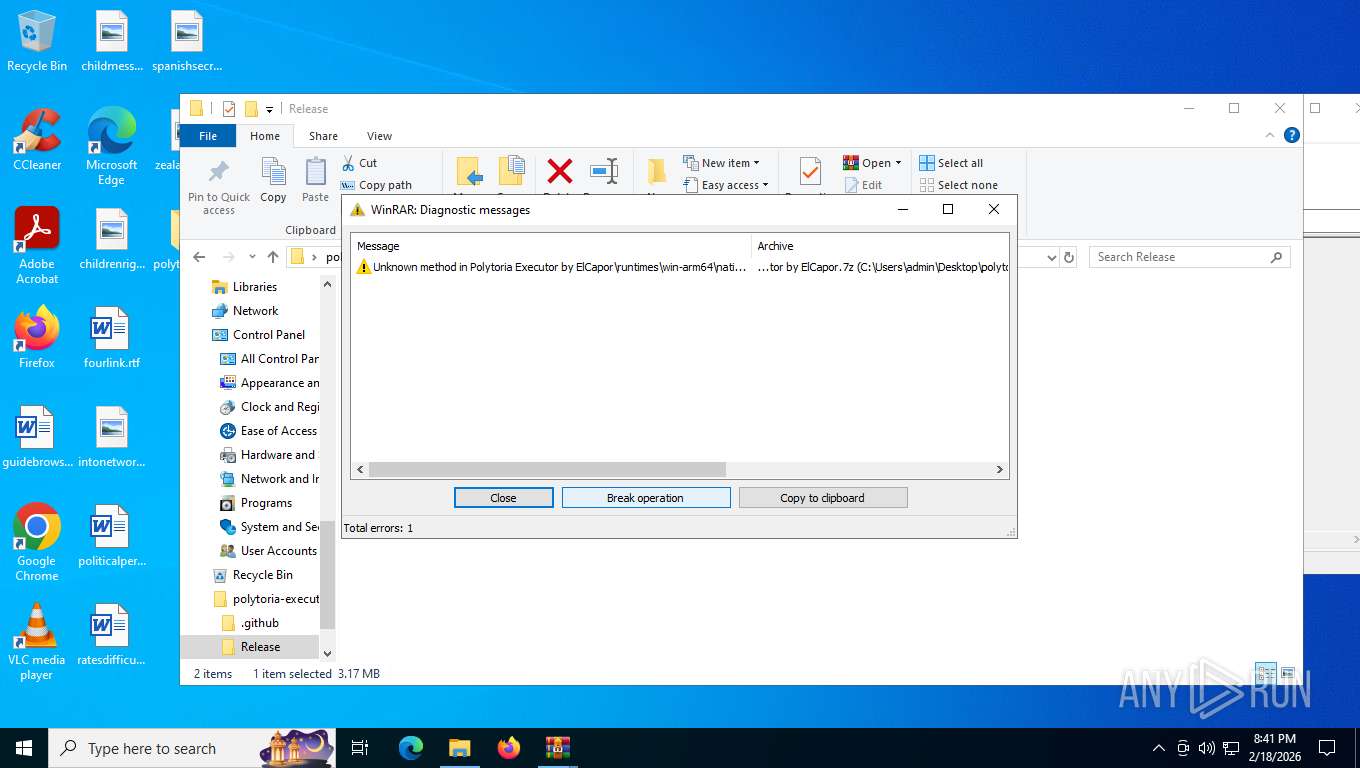
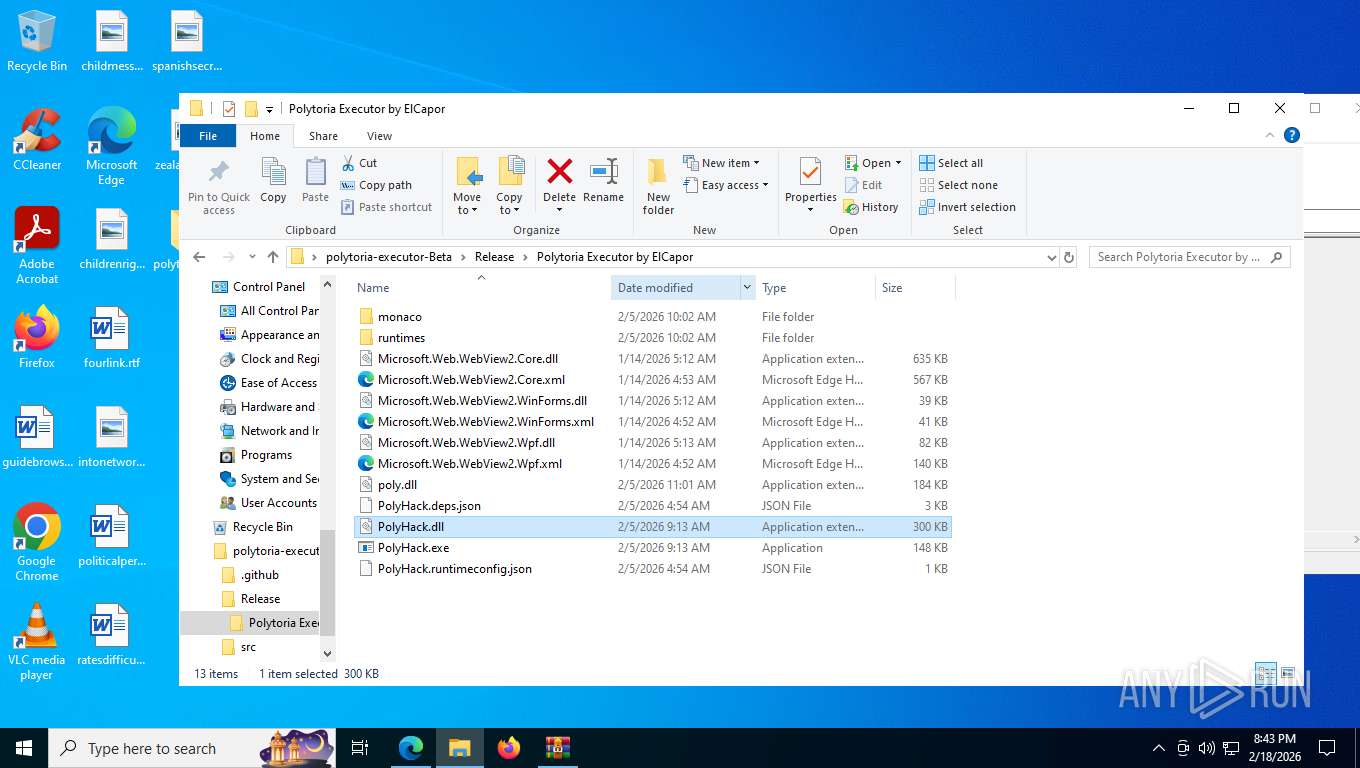
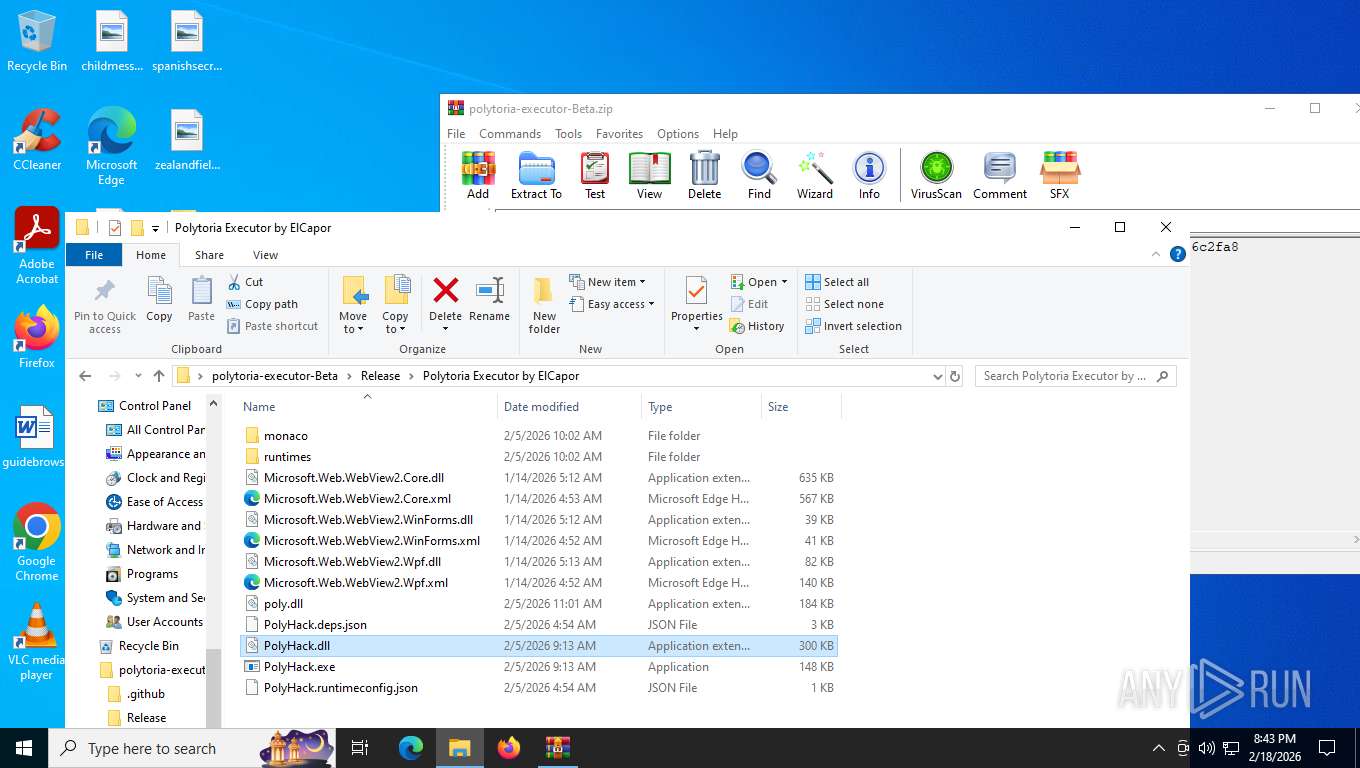
Executes application which crashes
- PolyHack.exe (PID: 3004)
INFO
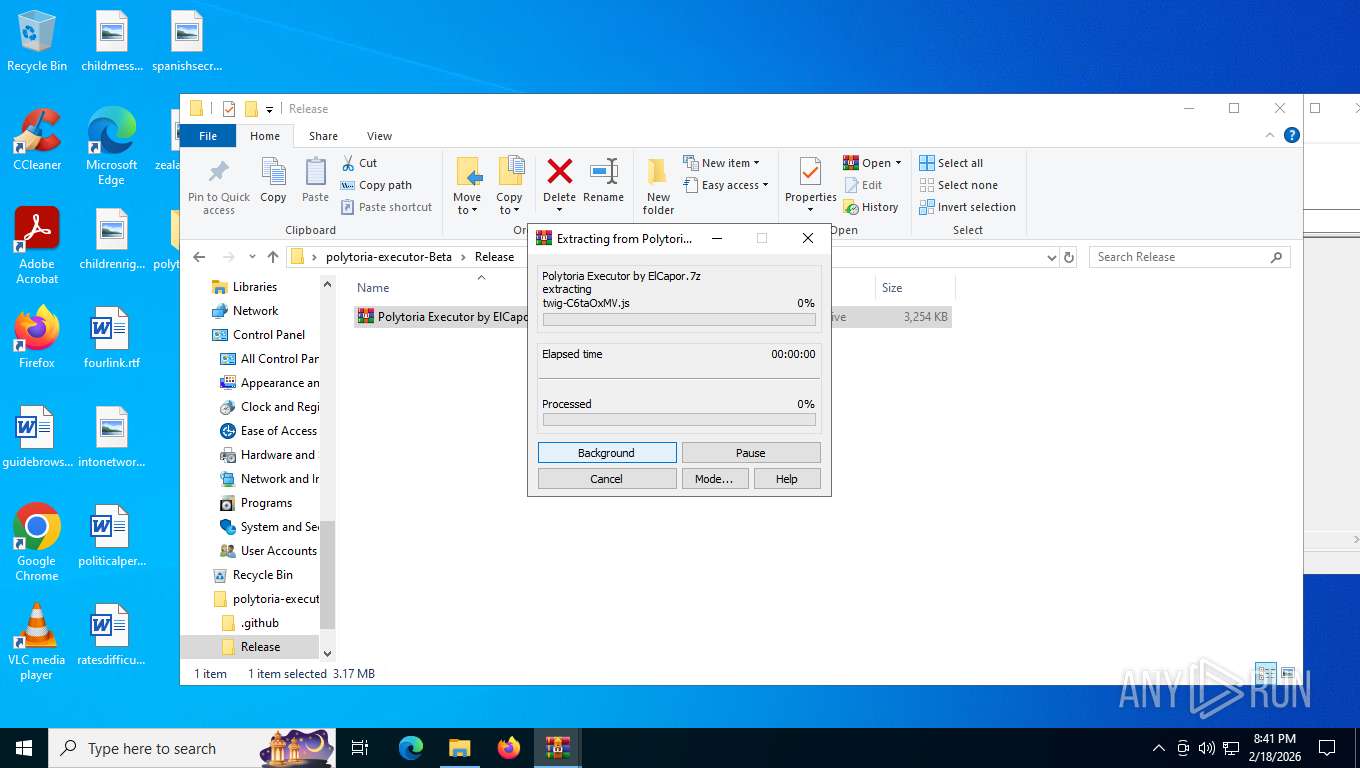
Drops script file
- msedge.exe (PID: 4104)
- WinRAR.exe (PID: 2976)
- WinRAR.exe (PID: 8344)
Application launched itself
- msedge.exe (PID: 7988)
- msedge.exe (PID: 4104)
Reads the computer name
- PolyHack.exe (PID: 6080)
- identity_helper.exe (PID: 8252)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
- msiexec.exe (PID: 7696)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
- msiexec.exe (PID: 7028)
- msiexec.exe (PID: 4408)
- PolyHack.exe (PID: 3004)
- msiexec.exe (PID: 8940)
- msiexec.exe (PID: 7736)
Checks supported languages
- identity_helper.exe (PID: 8252)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 5500)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
- PolyHack.exe (PID: 6080)
- msiexec.exe (PID: 7028)
- msiexec.exe (PID: 7696)
- msiexec.exe (PID: 4408)
- PolyHack.exe (PID: 3004)
- msiexec.exe (PID: 8940)
- msiexec.exe (PID: 7736)
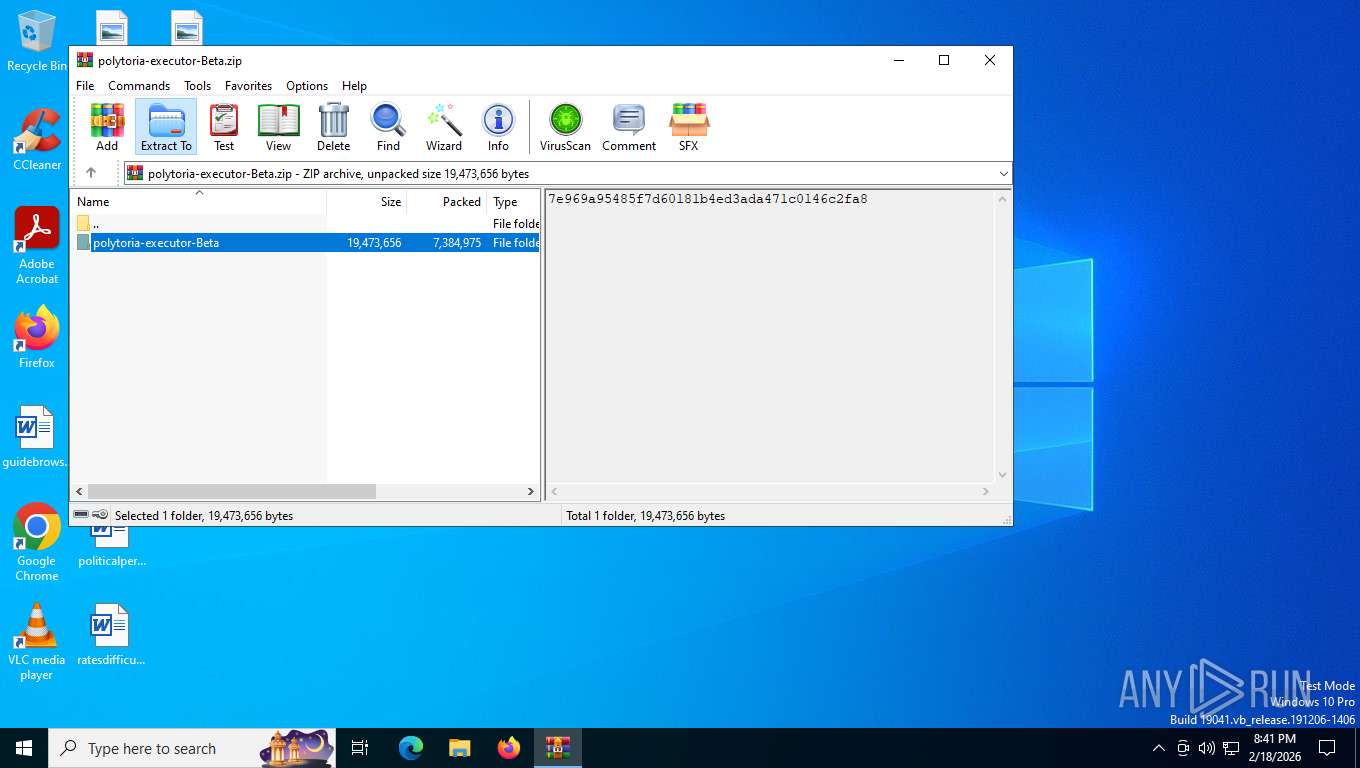
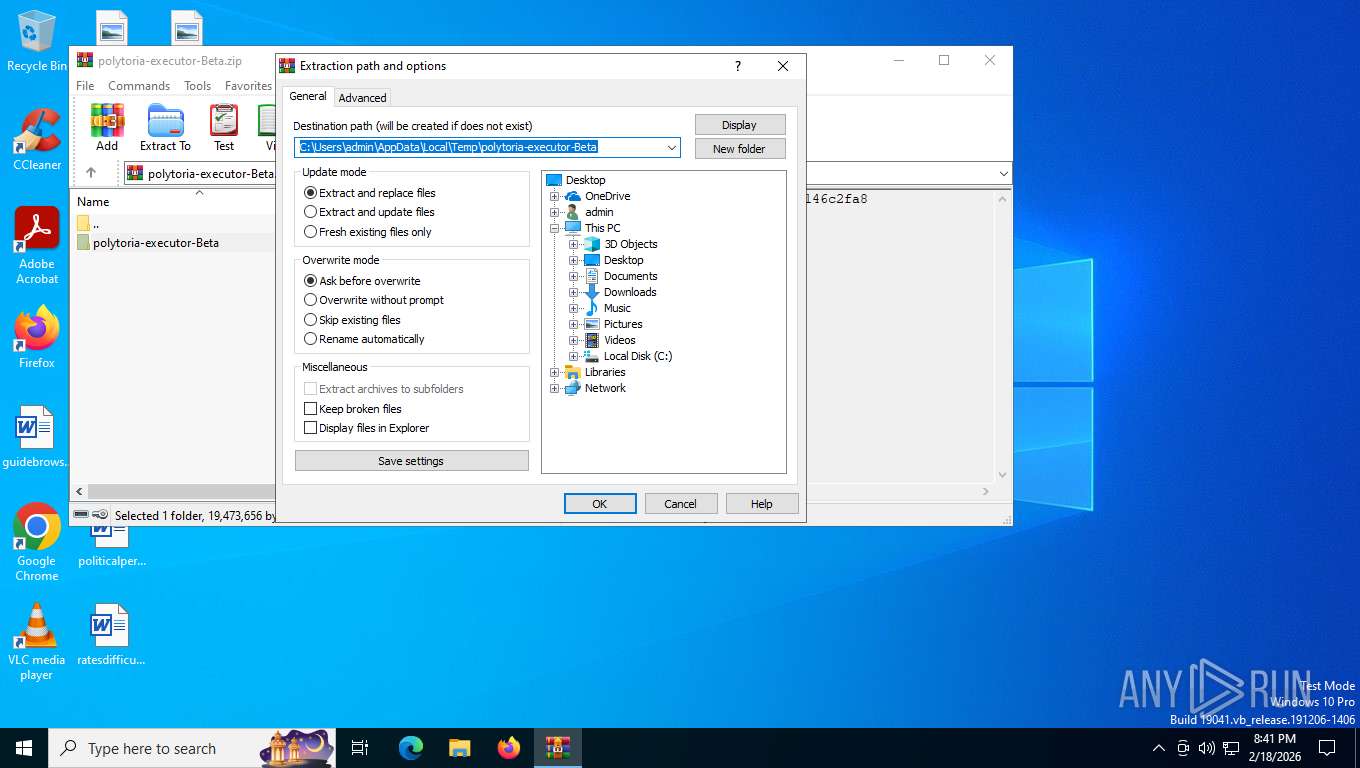
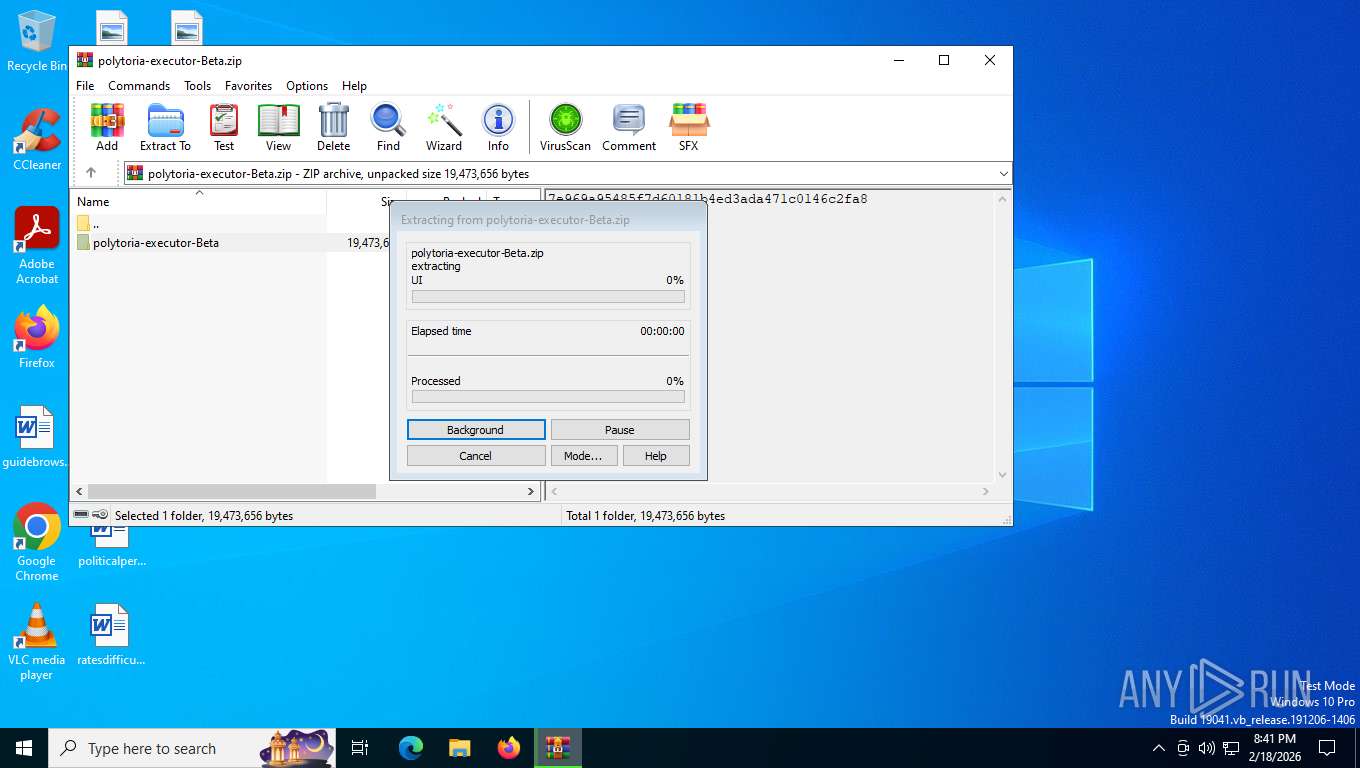
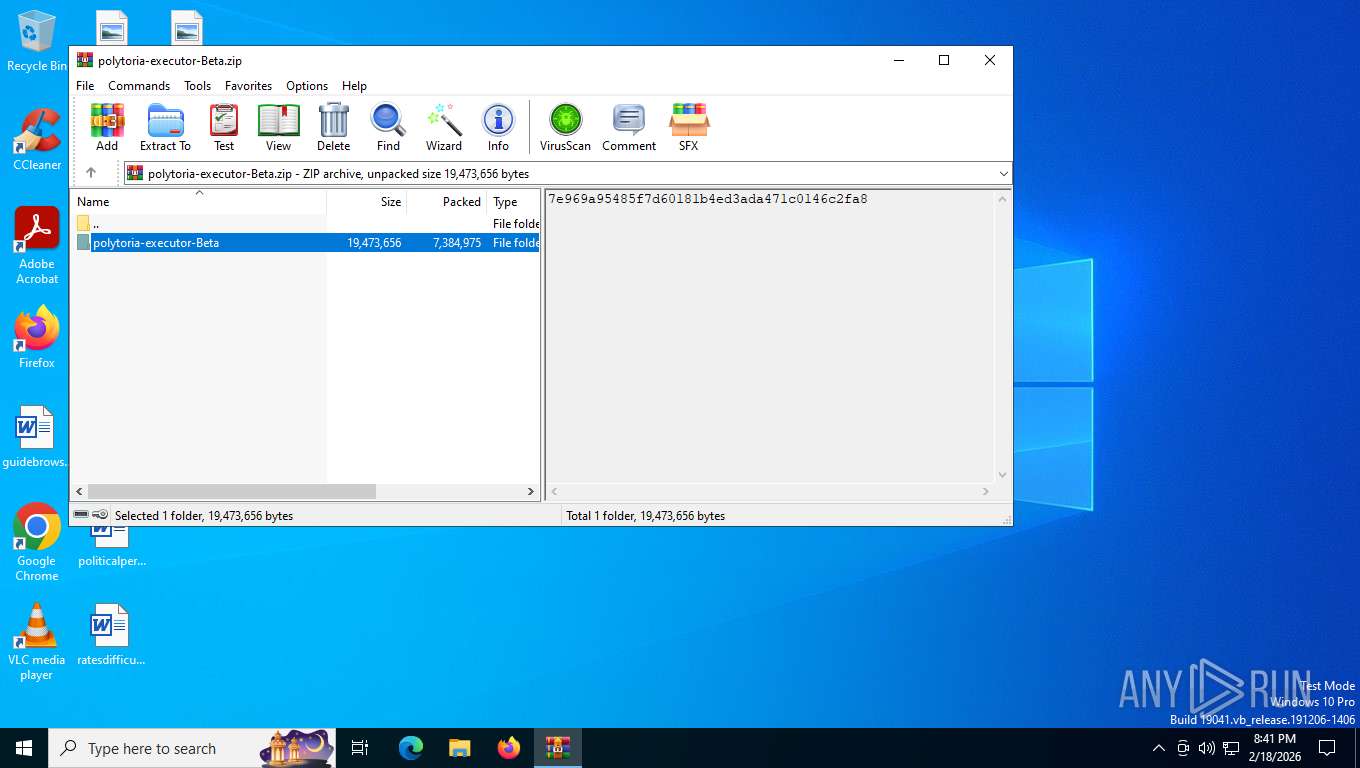
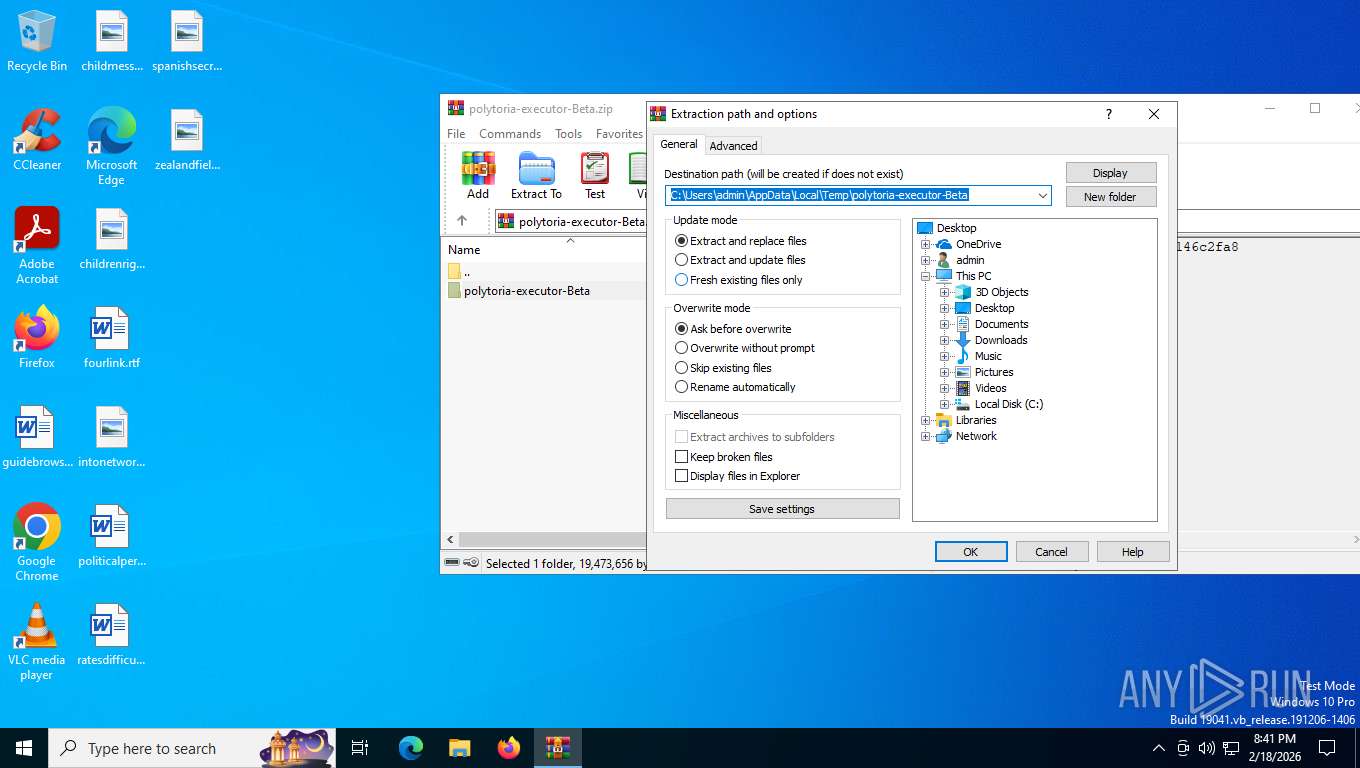
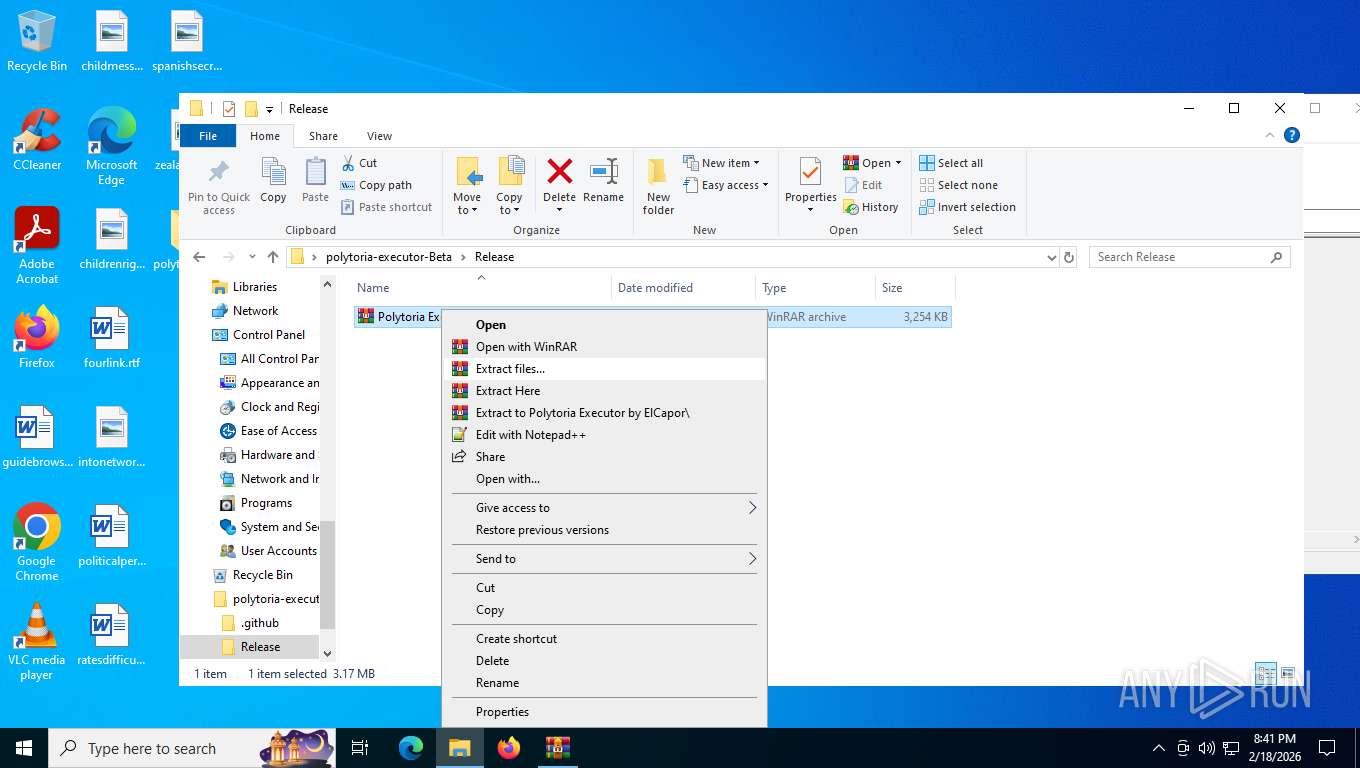
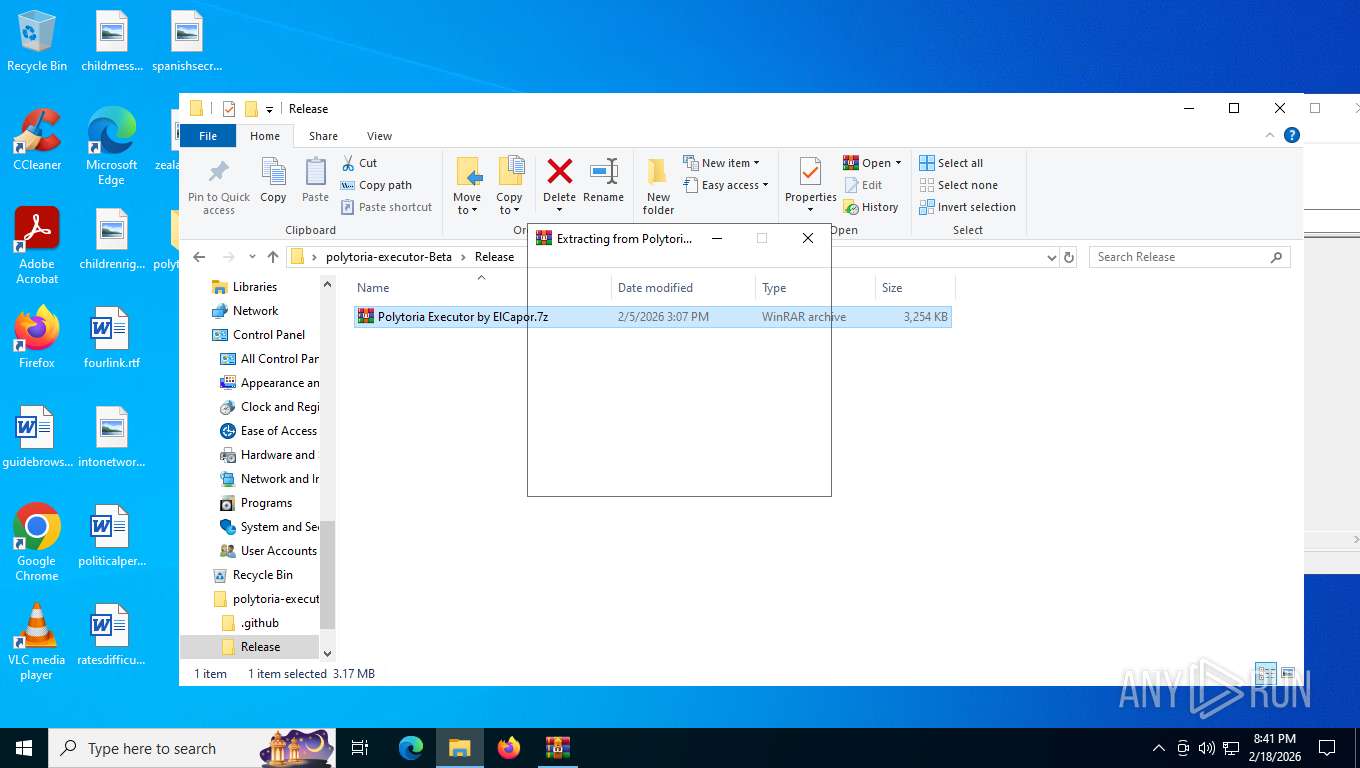
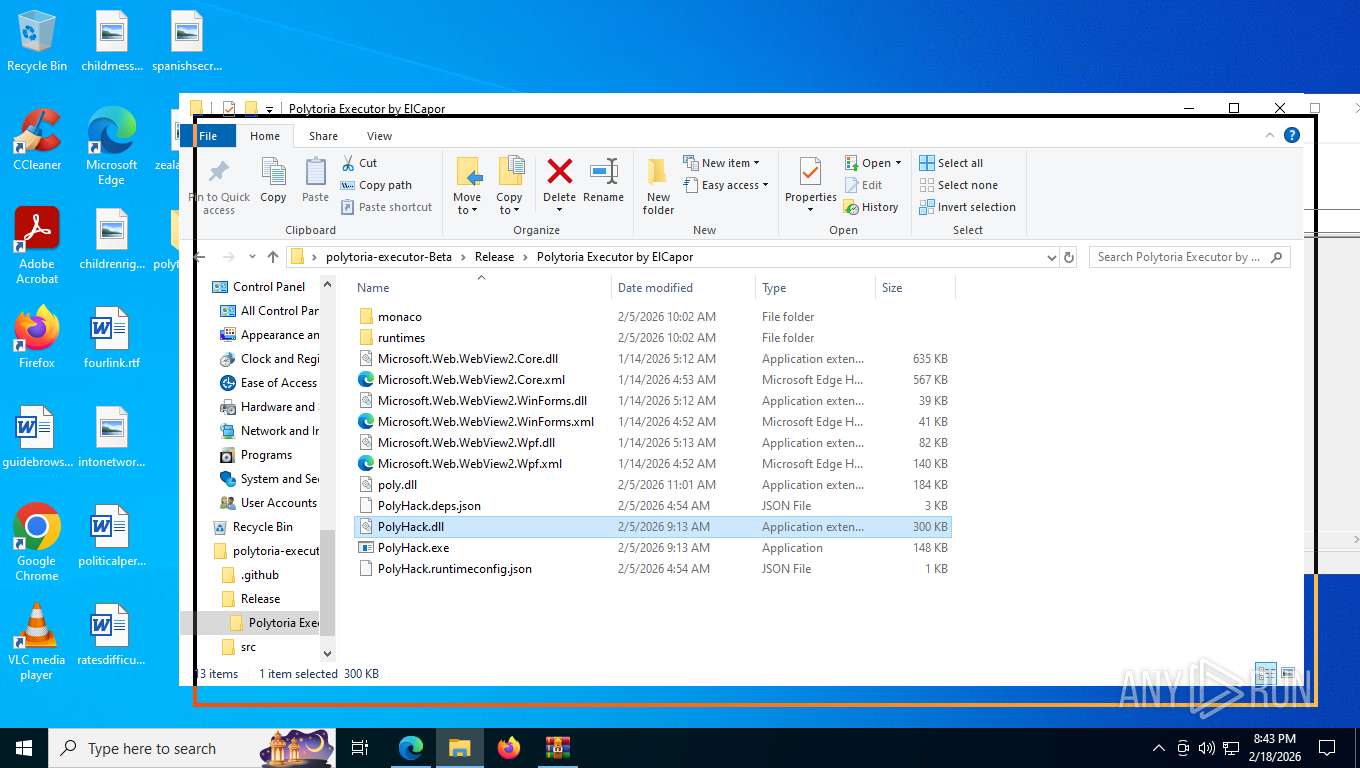
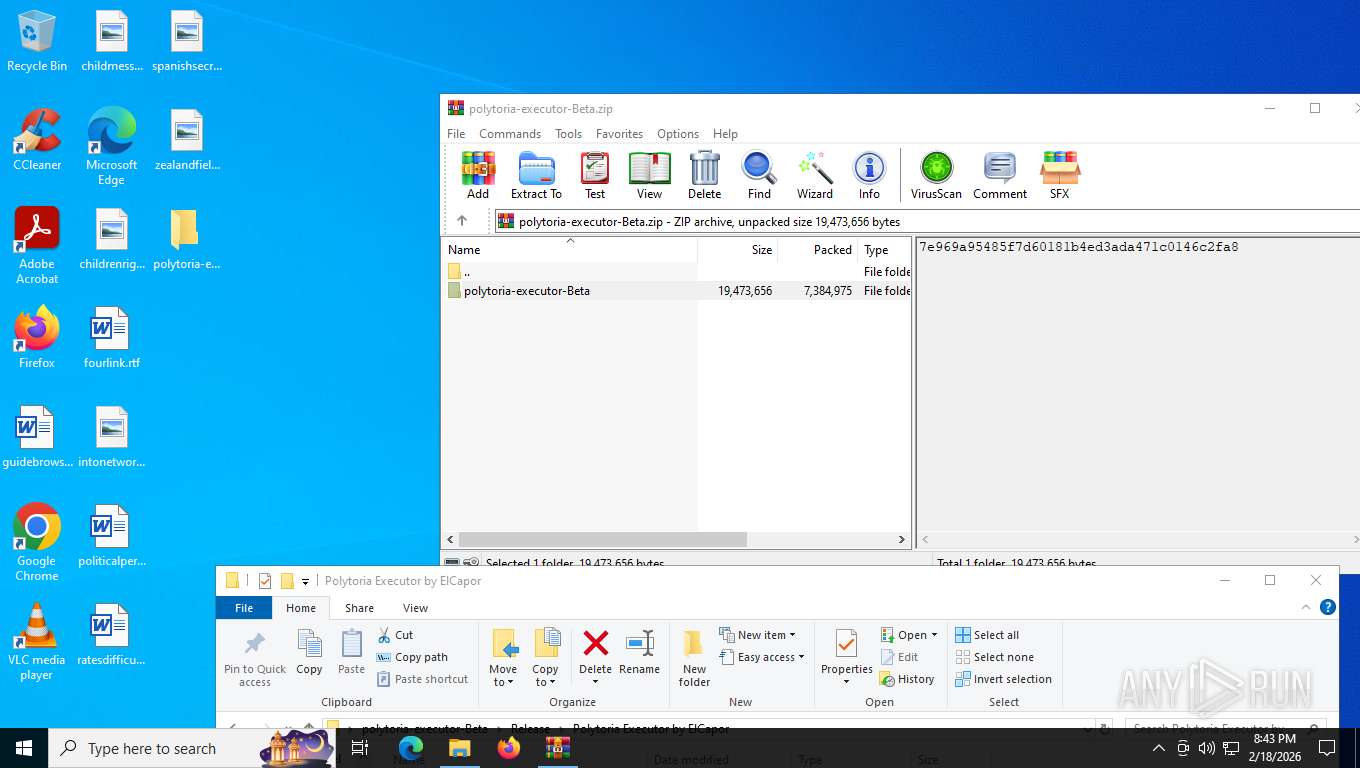
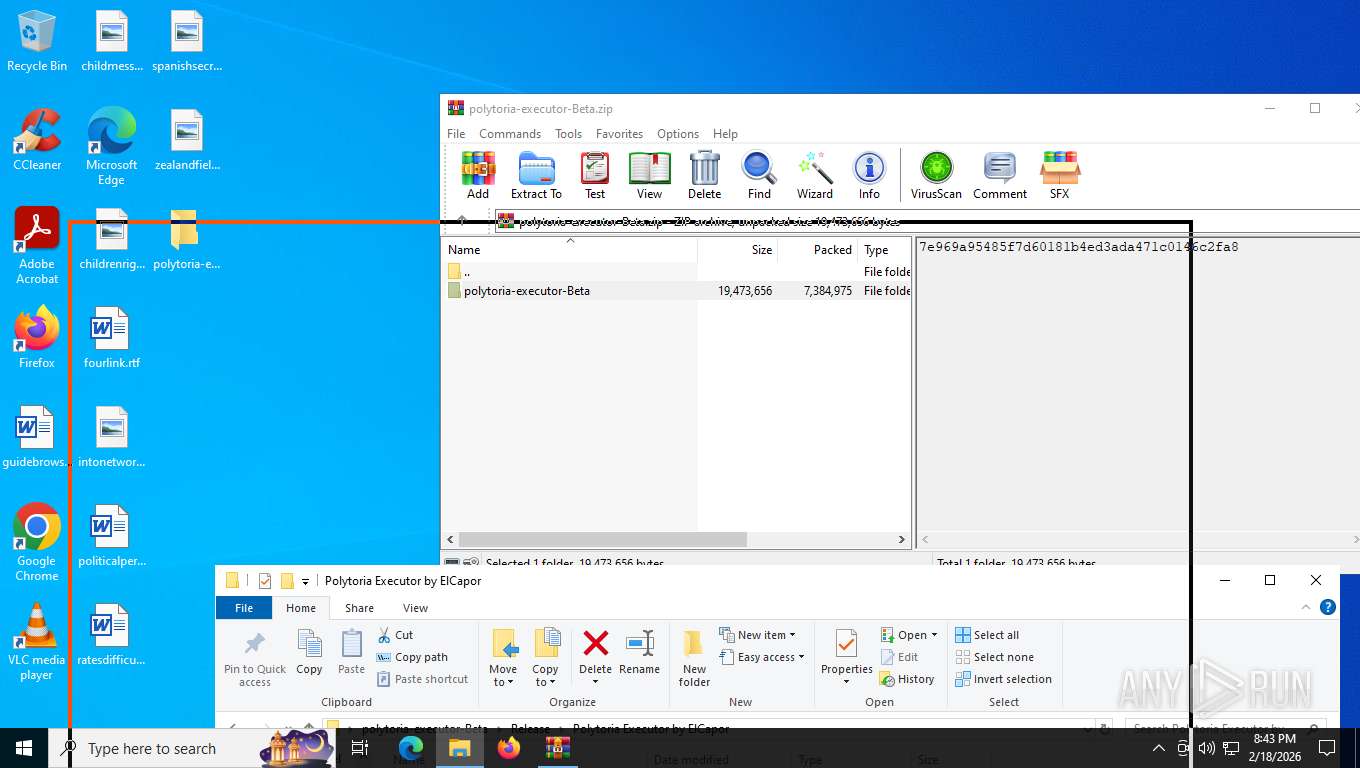
Manual execution by a user
- WinRAR.exe (PID: 2976)
- PolyHack.exe (PID: 6080)
- PolyHack.exe (PID: 3004)
Reads security settings of Internet Explorer
- PolyHack.exe (PID: 6080)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
- PolyHack.exe (PID: 3004)
Process checks computer location settings
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
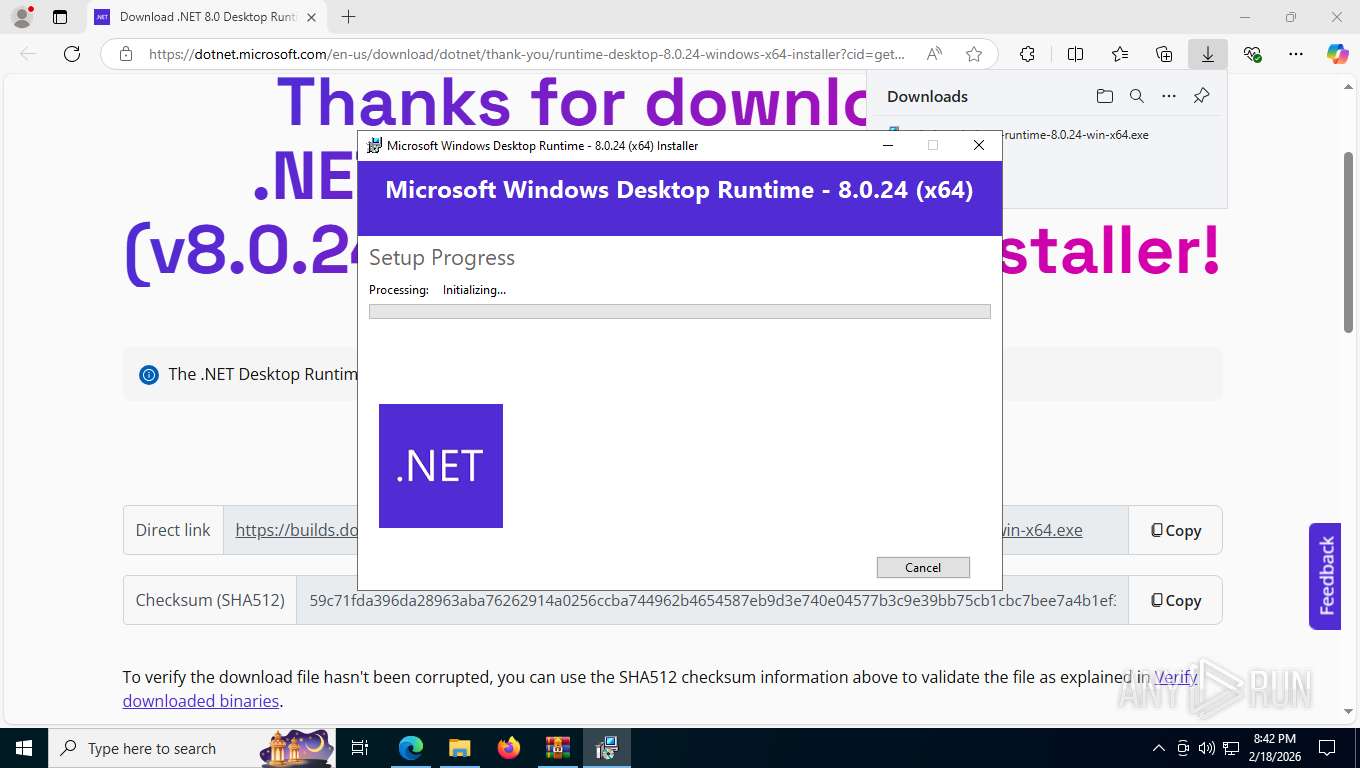
Create files in a temporary directory
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 768)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 5500)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
Reads Environment values
- identity_helper.exe (PID: 8252)
Creates files in the program directory
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
- PolyHack.exe (PID: 3004)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
- msiexec.exe (PID: 7028)
Checks proxy server information
- slui.exe (PID: 3092)
- WerFault.exe (PID: 2232)
Creates a software uninstall entry
- msiexec.exe (PID: 7028)
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.24-win-x64.exe (PID: 8992)
Creates files or folders in the user directory
- WerFault.exe (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2026:02:05 12:07:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | polytoria-executor-Beta/ |
Total processes
210
Monitored processes
51
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7912,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=5672 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Users\admin\AppData\Local\Temp\{9C14818A-F57F-484E-9DFF-22185FE4B9C6}\.cr\windowsdesktop-runtime-8.0.24-win-x64.exe" -burn.clean.room="C:\Users\admin\Downloads\windowsdesktop-runtime-8.0.24-win-x64.exe" -burn.filehandle.attached=664 -burn.filehandle.self=672 | C:\Users\admin\AppData\Local\Temp\{9C14818A-F57F-484E-9DFF-22185FE4B9C6}\.cr\windowsdesktop-runtime-8.0.24-win-x64.exe | — | windowsdesktop-runtime-8.0.24-win-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 8.0.24 (x64) Exit code: 0 Version: 8.0.24.35722 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4044,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=5528 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2728,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=2736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6908,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=6840 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6400,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=5280 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\WerFault.exe -u -p 3004 -s 1236 | C:\Windows\System32\WerFault.exe | PolyHack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2352,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=2500 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3608,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7080,i,3467589975758794356,15311094234887749398,262144 --variations-seed-version --mojo-platform-channel-handle=7440 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
20 225
Read events
19 260
Write events
896
Delete events
69
Modification events
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\polytoria-executor-Beta.zip | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8344) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
1
Suspicious files
7
Text files
171
Unknown types
1 257
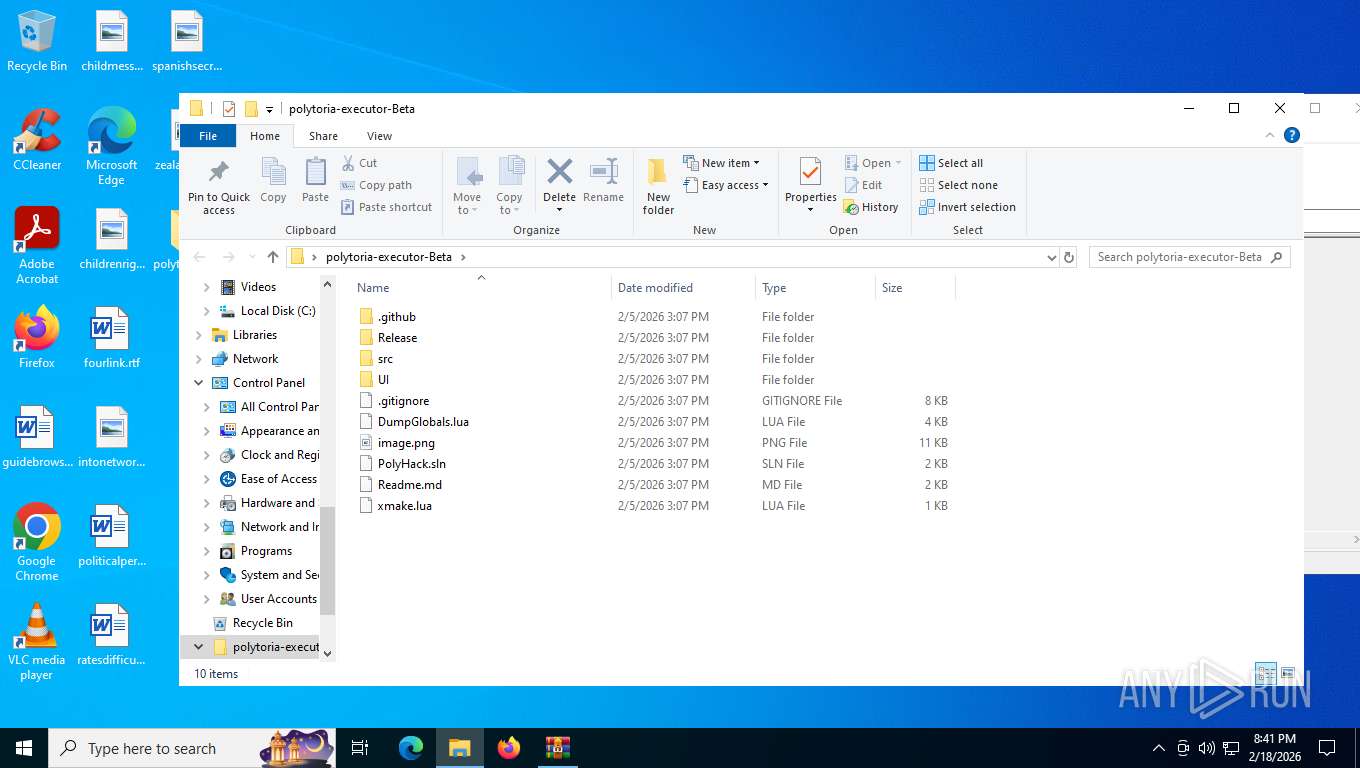
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
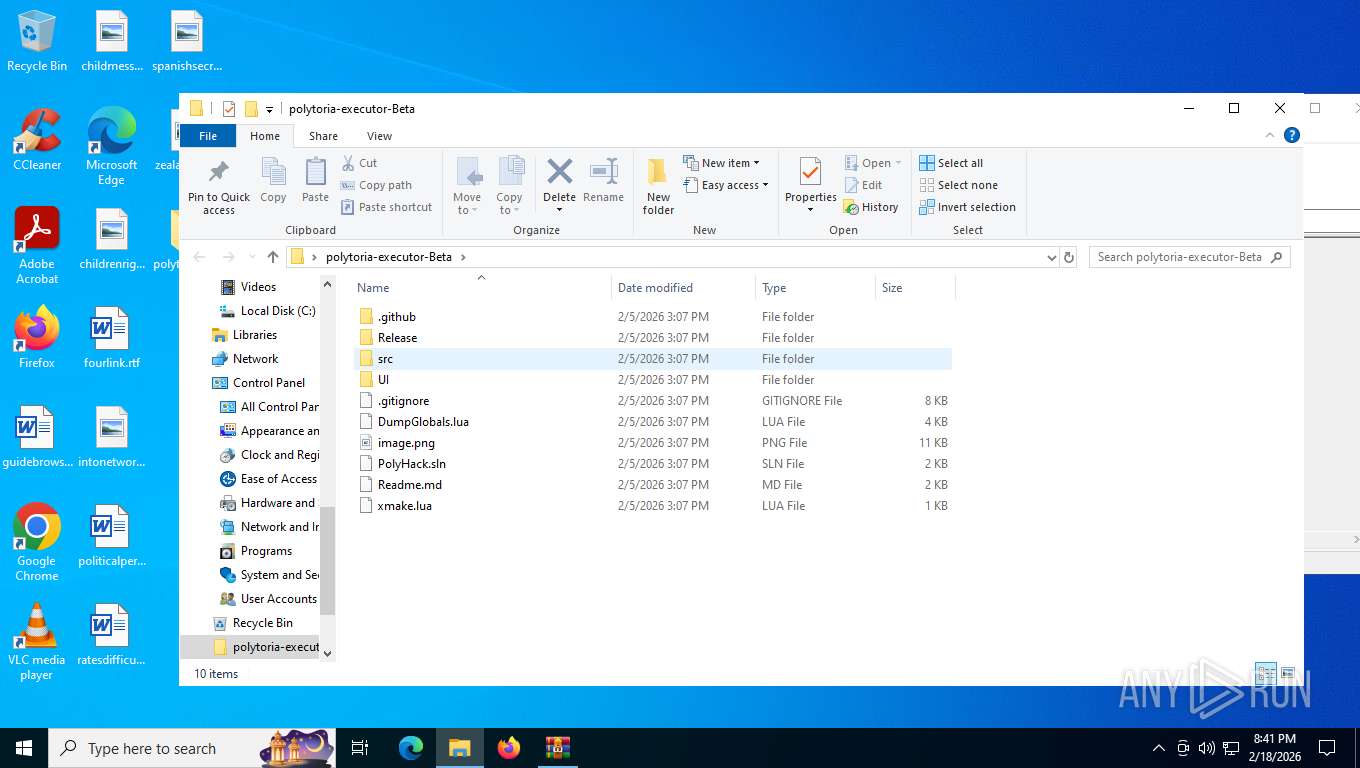
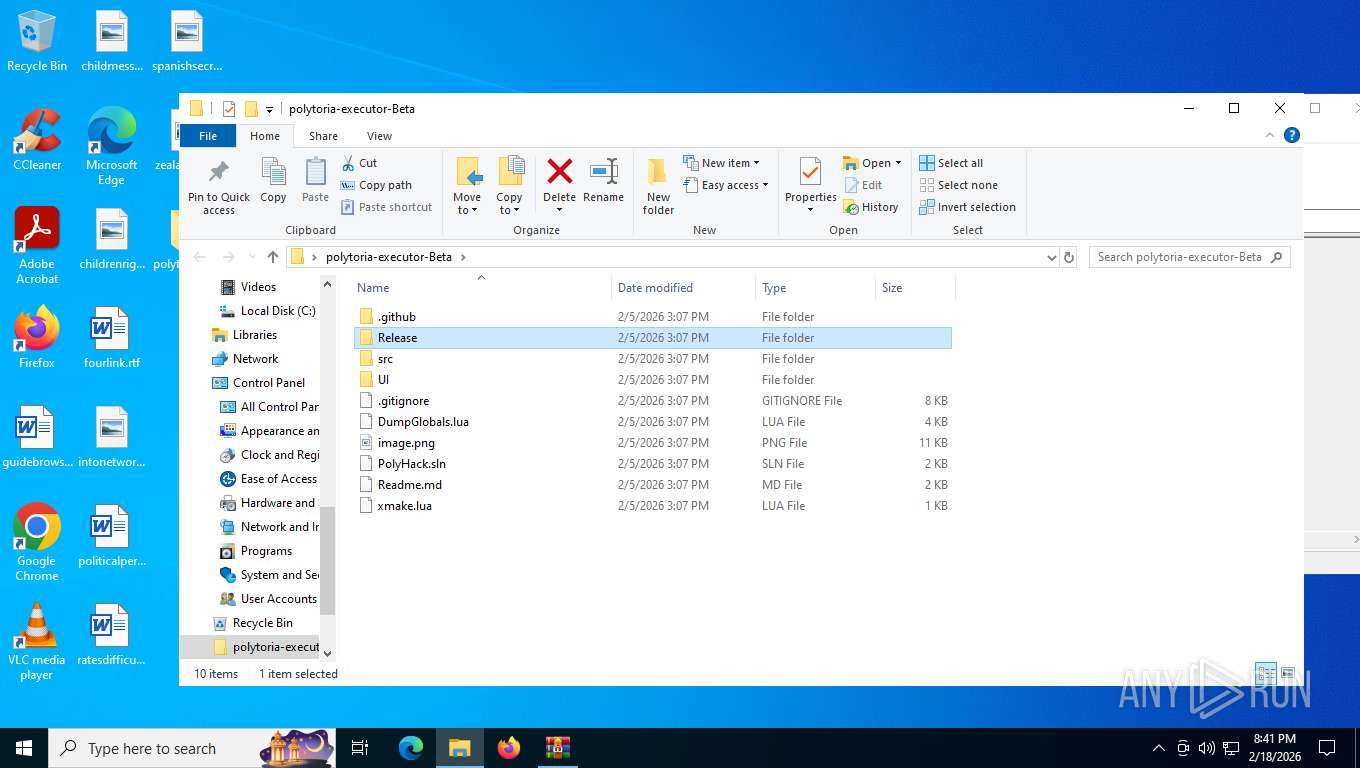
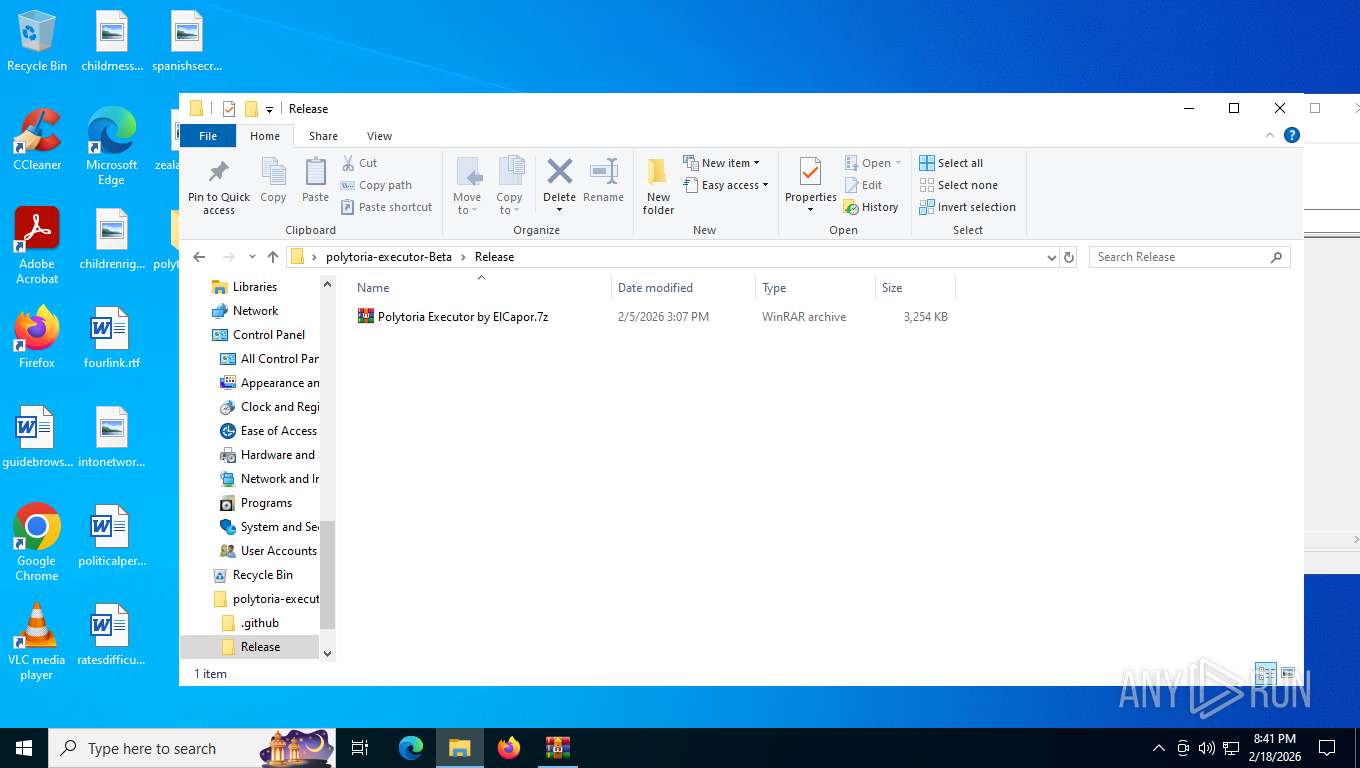
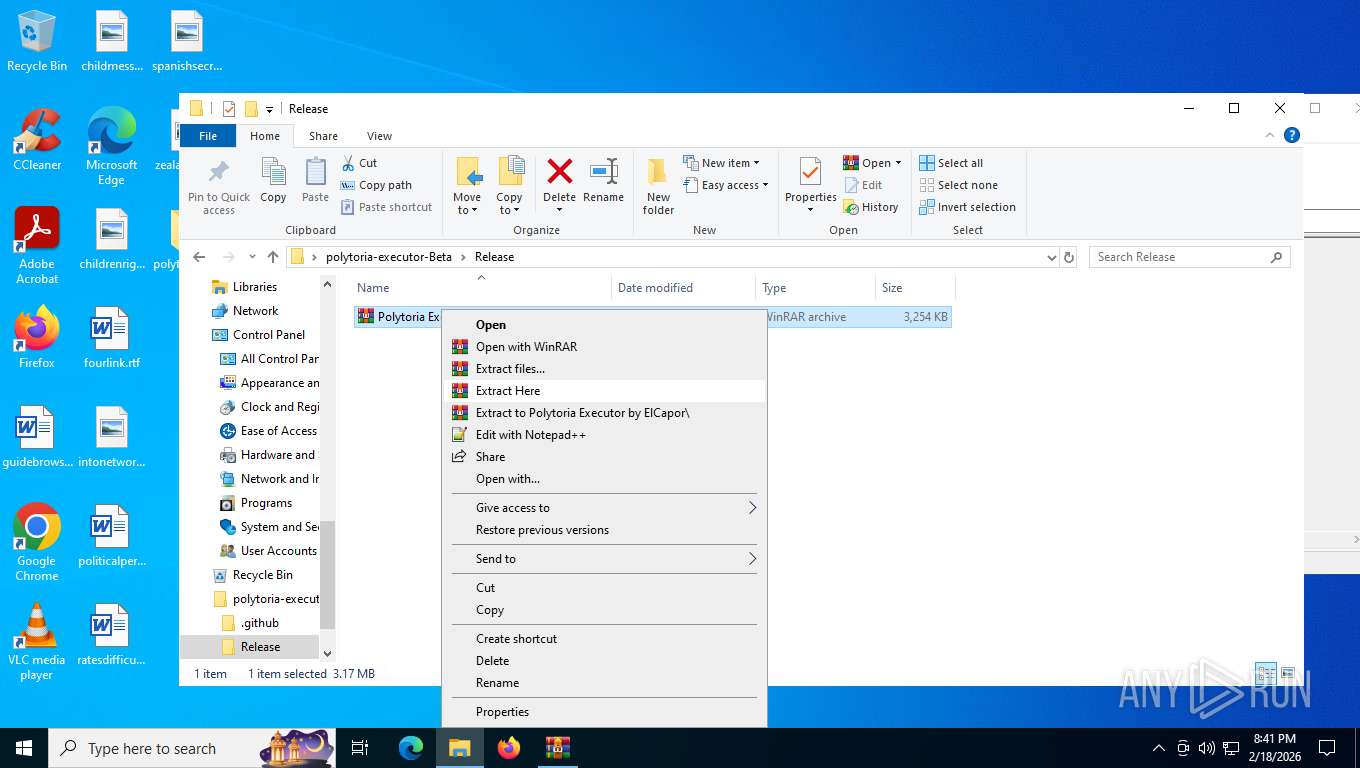
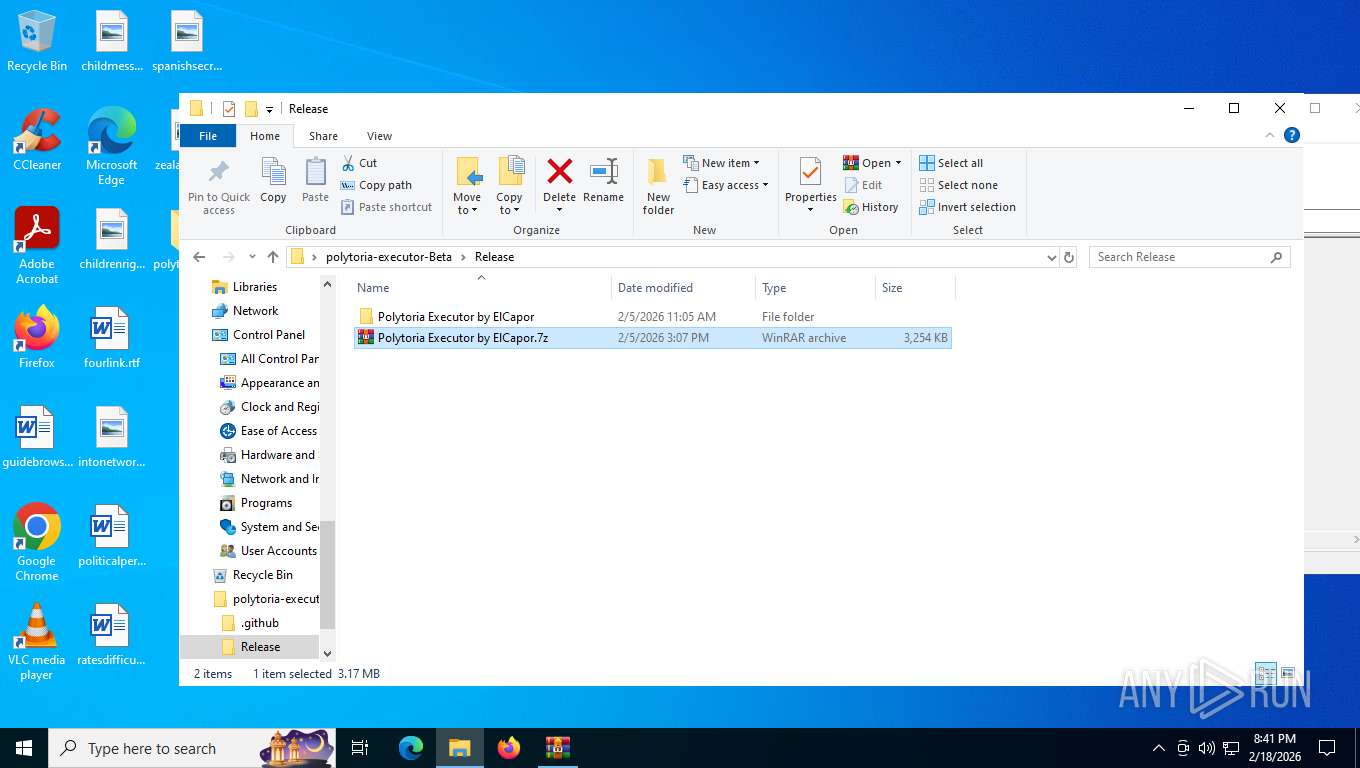
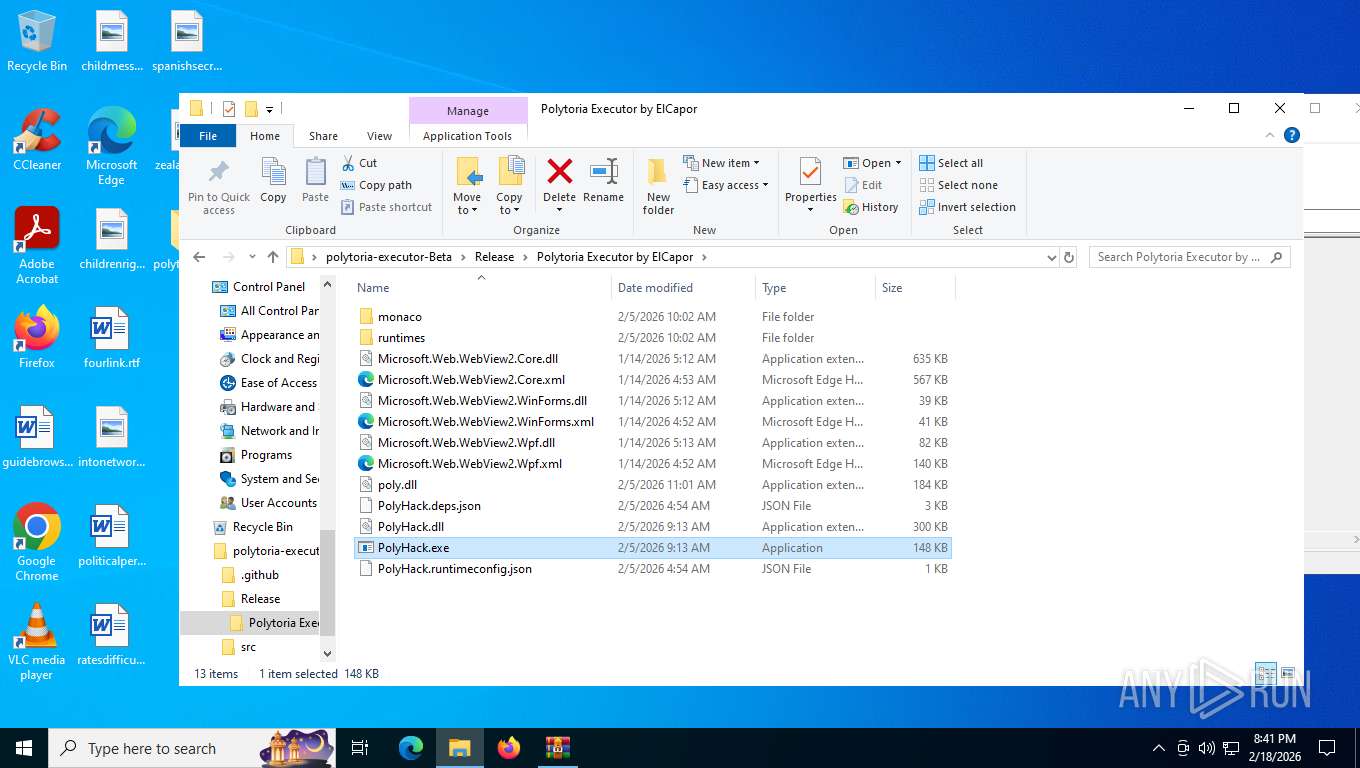
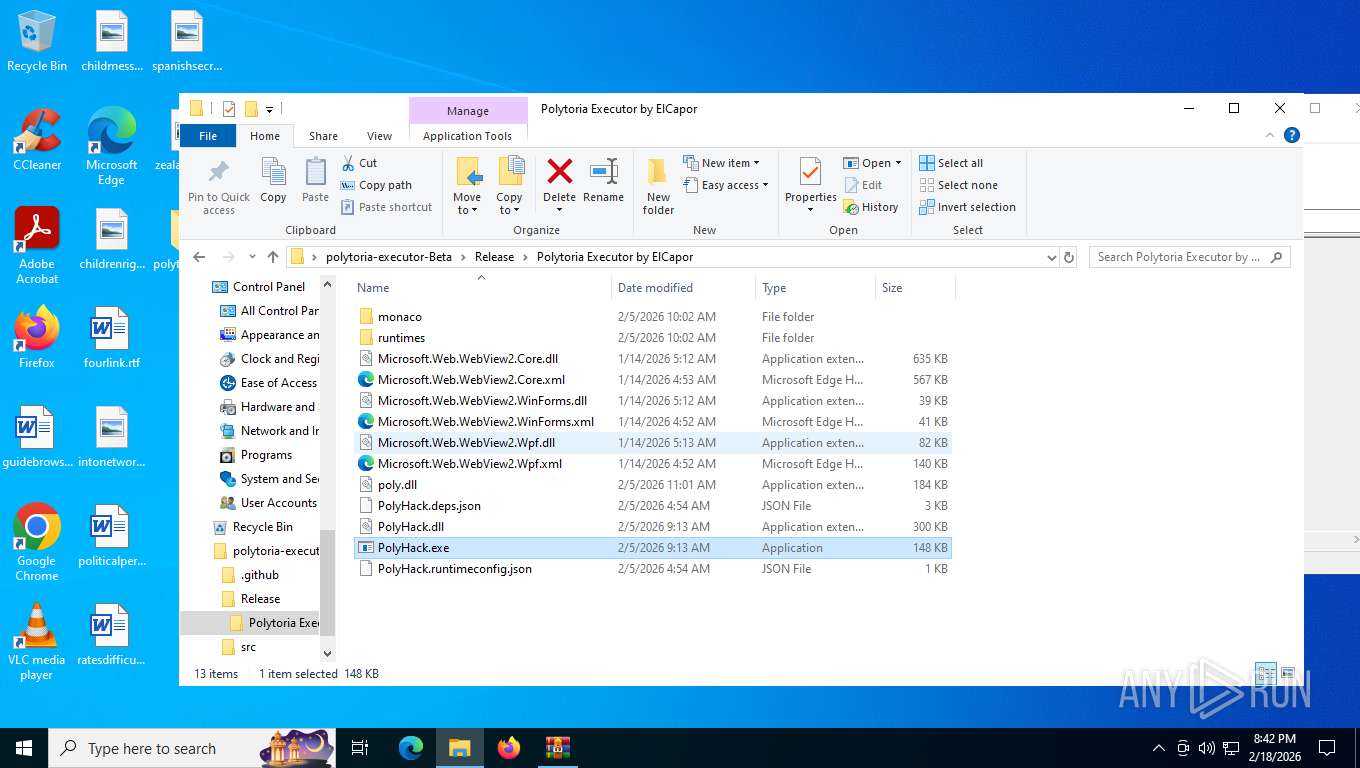
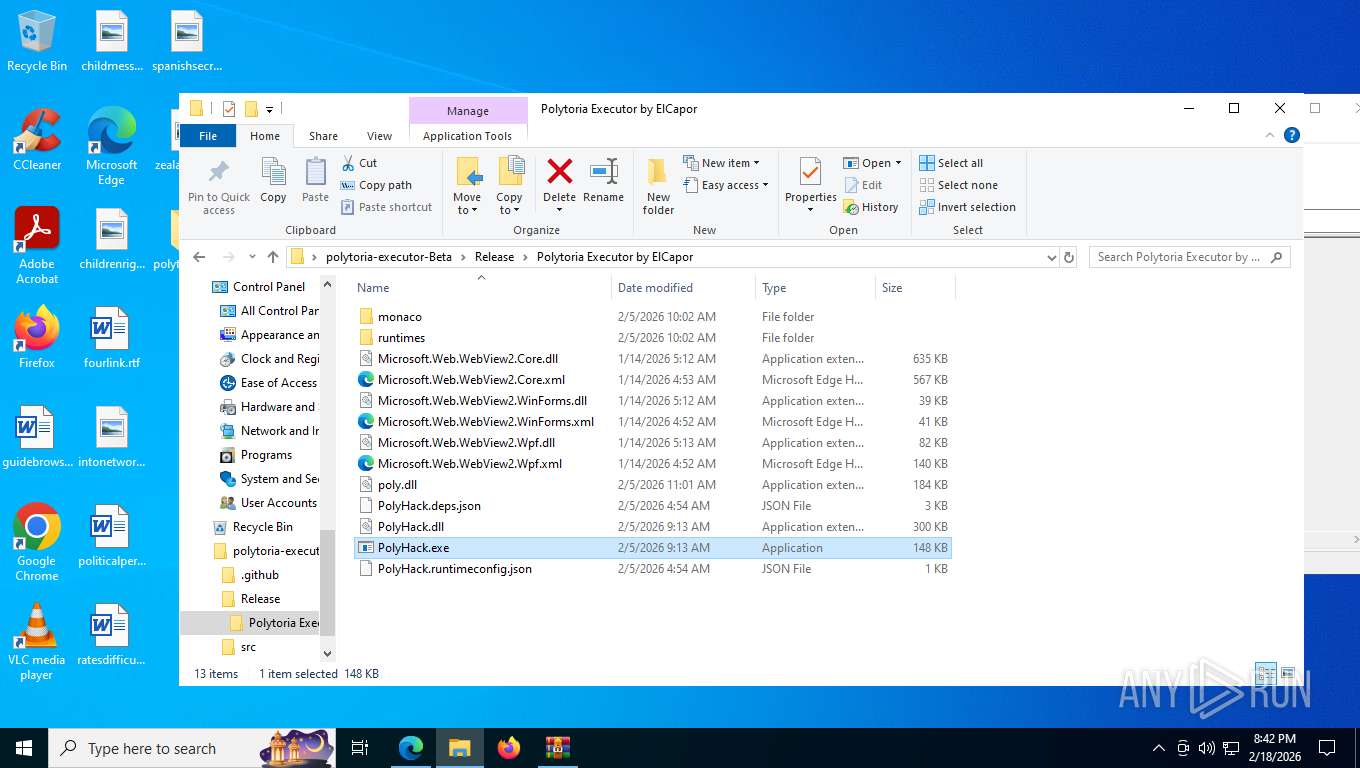
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\Release\Polytoria Executor by ElCapor.7z | binary | |
MD5:9CB4C72112904C93F9C6B1B79DC620ED | SHA256:329667CC0FEFEA2910A35247BA82458FE862C63930175882576D4F4BD75E15FC | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\Readme.md | text | |
MD5:278B36980503F4D3C9F82169BF6C0C60 | SHA256:4D70A250EB2D79CC7911BCF639B10B19C8BF11F9295E66FEC0F5AD47FC3FCA4A | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\DumpGlobals.lua | binary | |
MD5:ED5901B779737220B135F965E8C5090E | SHA256:8EC66C6260F1EDF1AC1C047DF4020A92575E7ADDCC5965BBF8B21B7E3D35C9C5 | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\App.xaml | text | |
MD5:DCC0C29531A53EDE6F1136D67170AEAA | SHA256:19EC3A5C1C212AA18C70BF9A28A5F7DEA4AAFFBAA30E6AB25C1CC67C7229B9E8 | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\MainWindow.xaml | binary | |
MD5:2DF256569F59487CFF1E9BF8EBEF3F00 | SHA256:C48020E1686C94A1F5666A54D44C68C16AB75F53FC8F1617B7A7624AB7E015A9 | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\.gitignore | binary | |
MD5:9921032EBEAEB778DE01D46CDD803157 | SHA256:37C5794488C56B974840201D72DD43B07C7AC60BBAA95ED4C841D16FC6010008 | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\monaco\base.txt | text | |
MD5:F069F825B4806BADF37BE238BF87DA99 | SHA256:498C9BEA257A3F6A3BDAFEC5D1DC7D2A9D439E94E1D88C4A2B7033FC8046AA78 | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\MainWindow.xaml.cs | binary | |
MD5:81FA4DDE5FAC4C1A28400623A7EFA76E | SHA256:D0A4B59F85E8D869CAB8D81E208FCA757BC8EDBCFF46924E7383E42DA2614C9F | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\monaco\lib\monaco\vs\assets\ts.worker-CMbG-7ft.js | — | |
MD5:— | SHA256:— | |||
| 8344 | WinRAR.exe | C:\Users\admin\Downloads\polytoria-executor-Beta\UI\monaco\classfunc.txt | text | |
MD5:10C4EE74B2ADC56598345A2D4562B298 | SHA256:AE3AB7BE7C331AB65C7C05A8B270AC37774833170F393A7781938BC37FD87872 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
342
TCP/UDP connections
129
DNS requests
155
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
492 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
7964 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7964 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
492 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.70 Kb | whitelisted |
492 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
492 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | US | binary | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
492 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5180 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
492 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
492 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
492 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
492 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2288 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Challenge-Platform Page Request to cdn-cgi |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
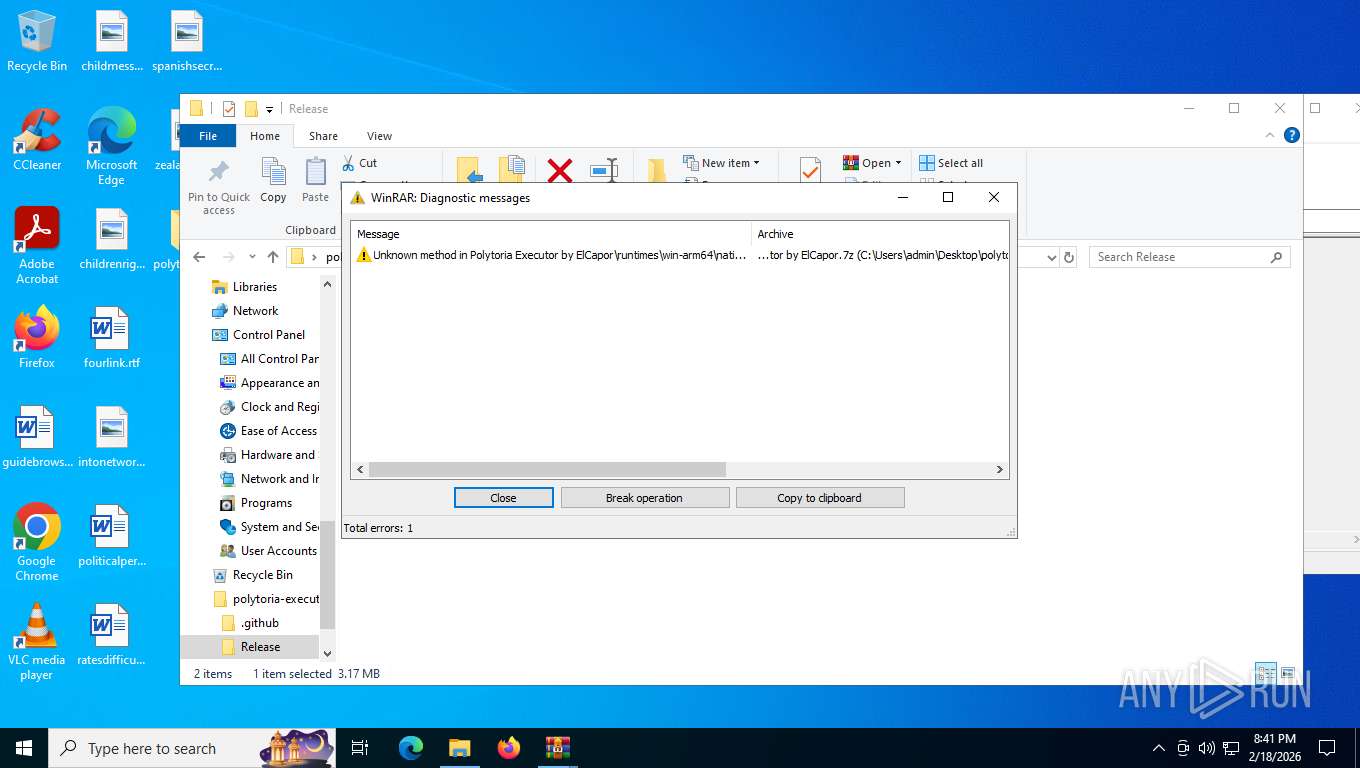
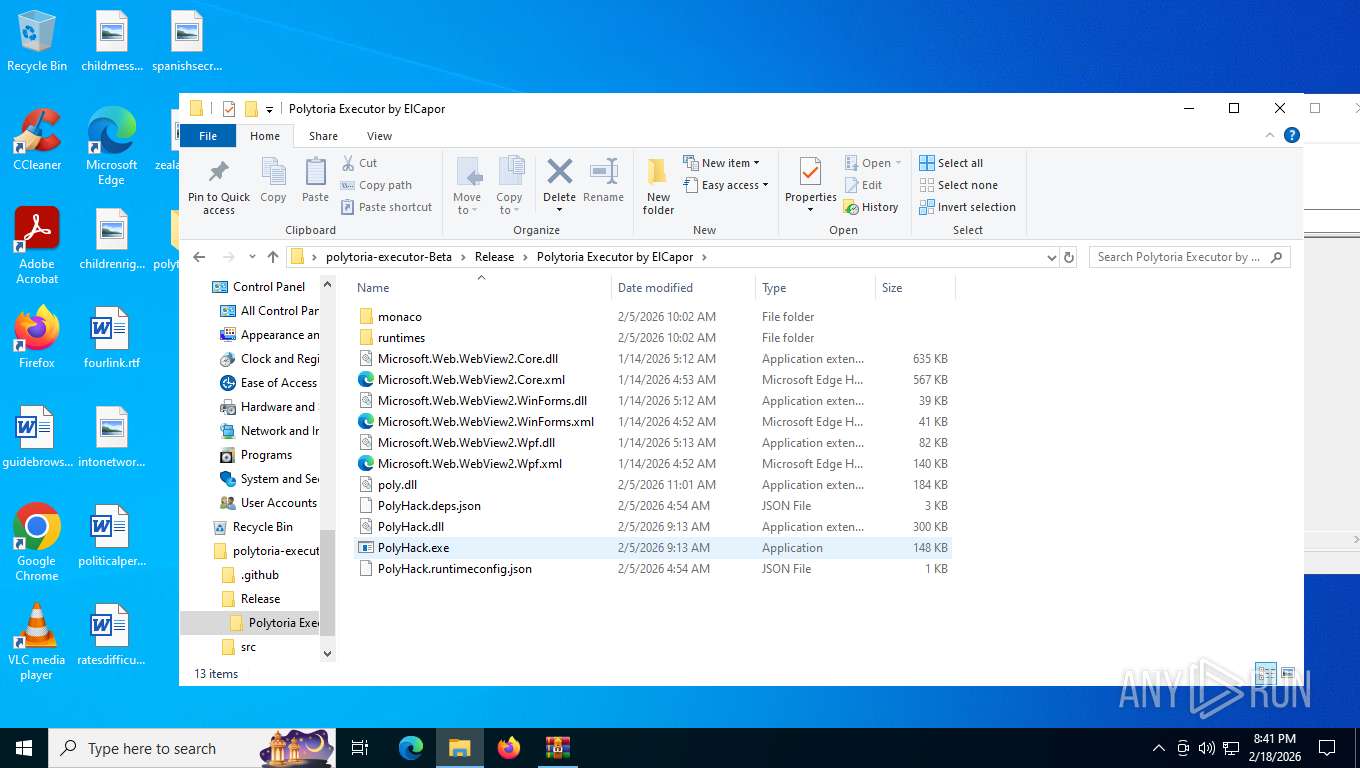
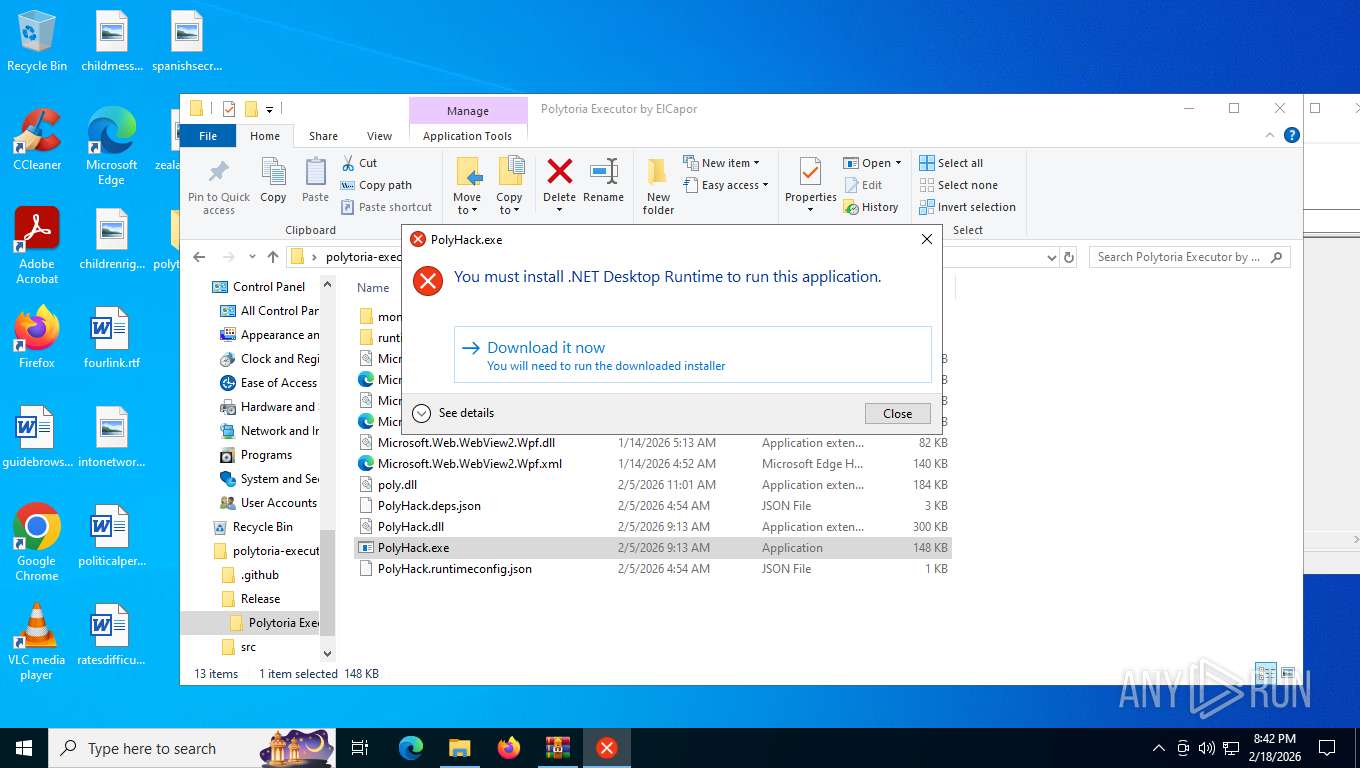
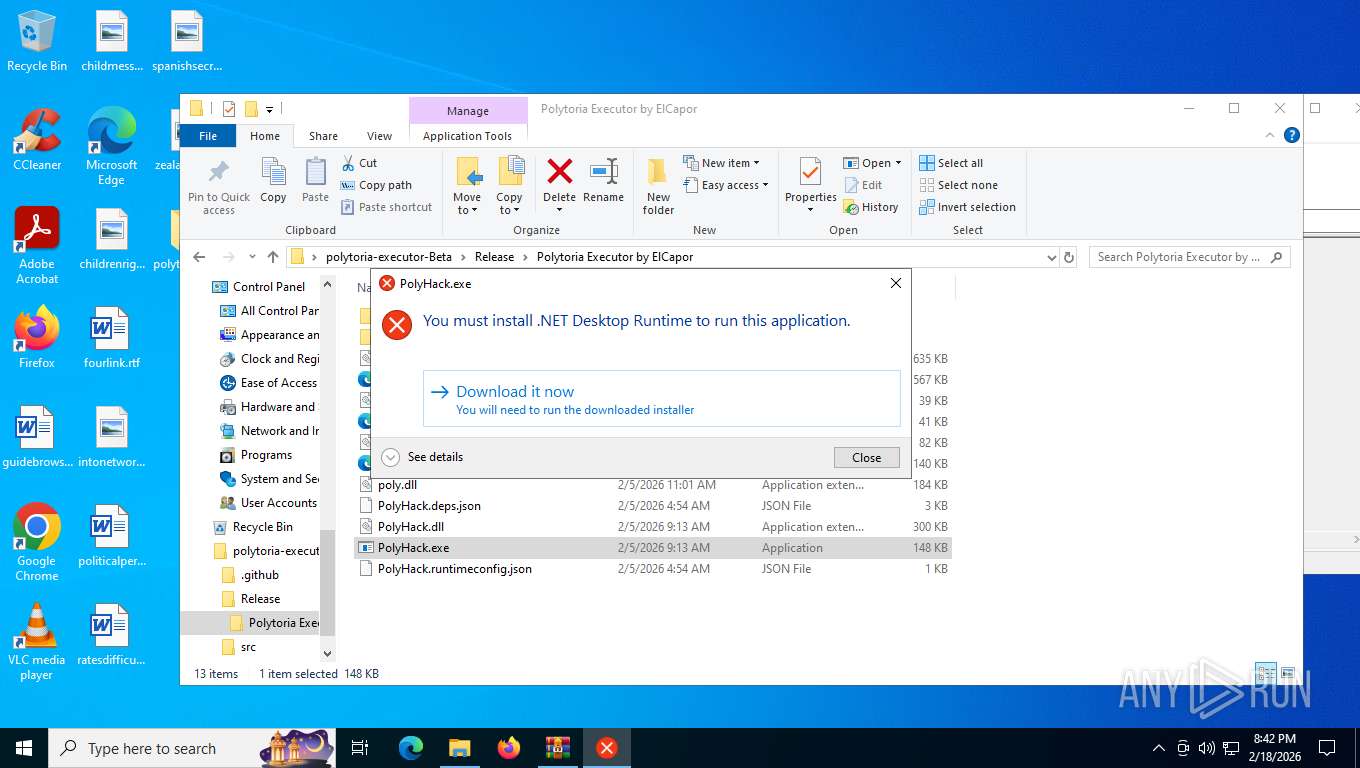
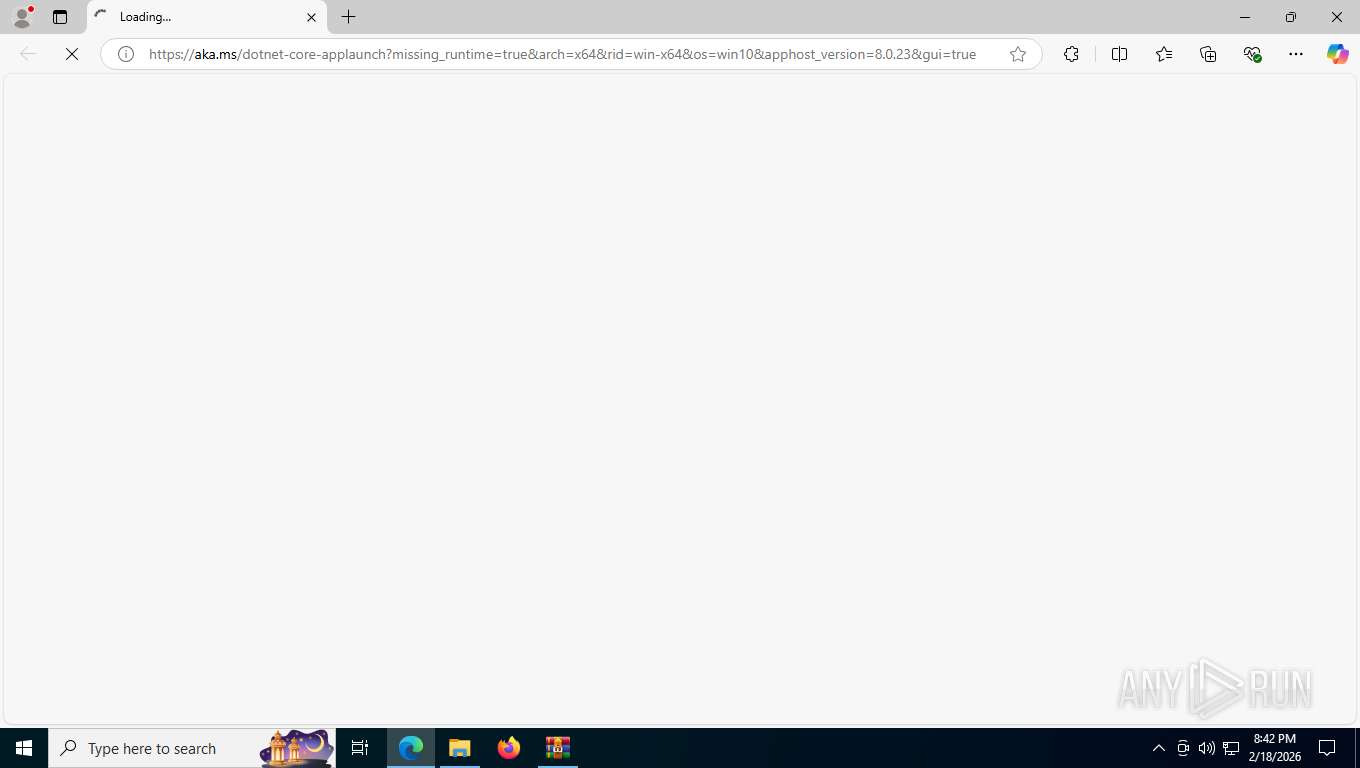
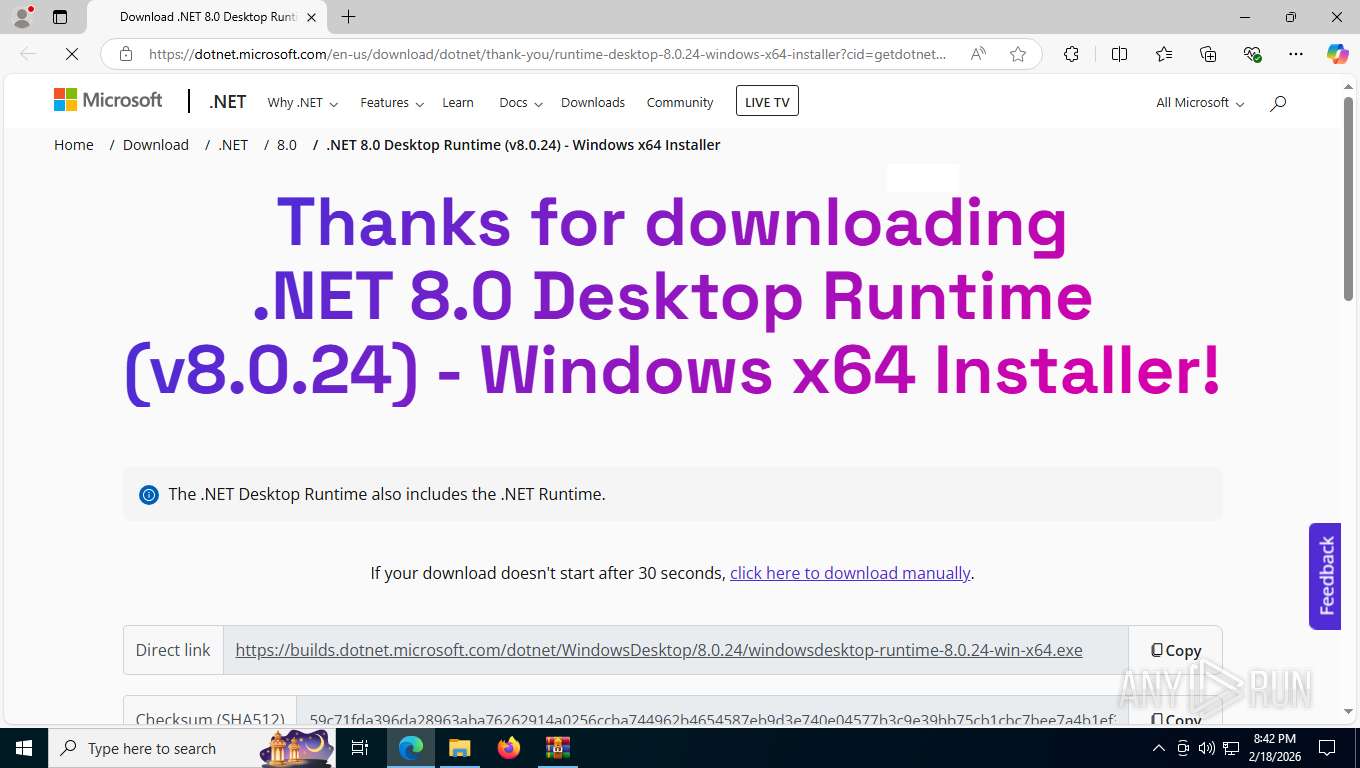
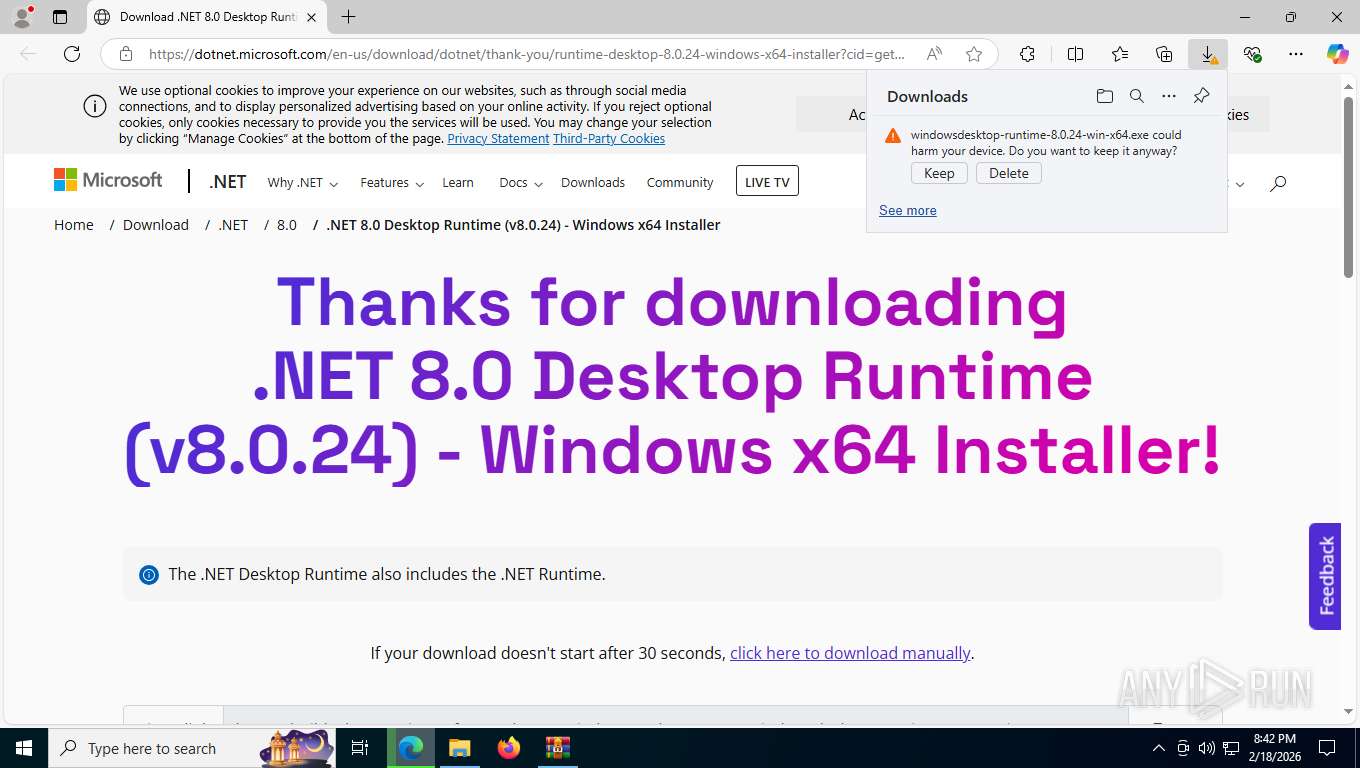
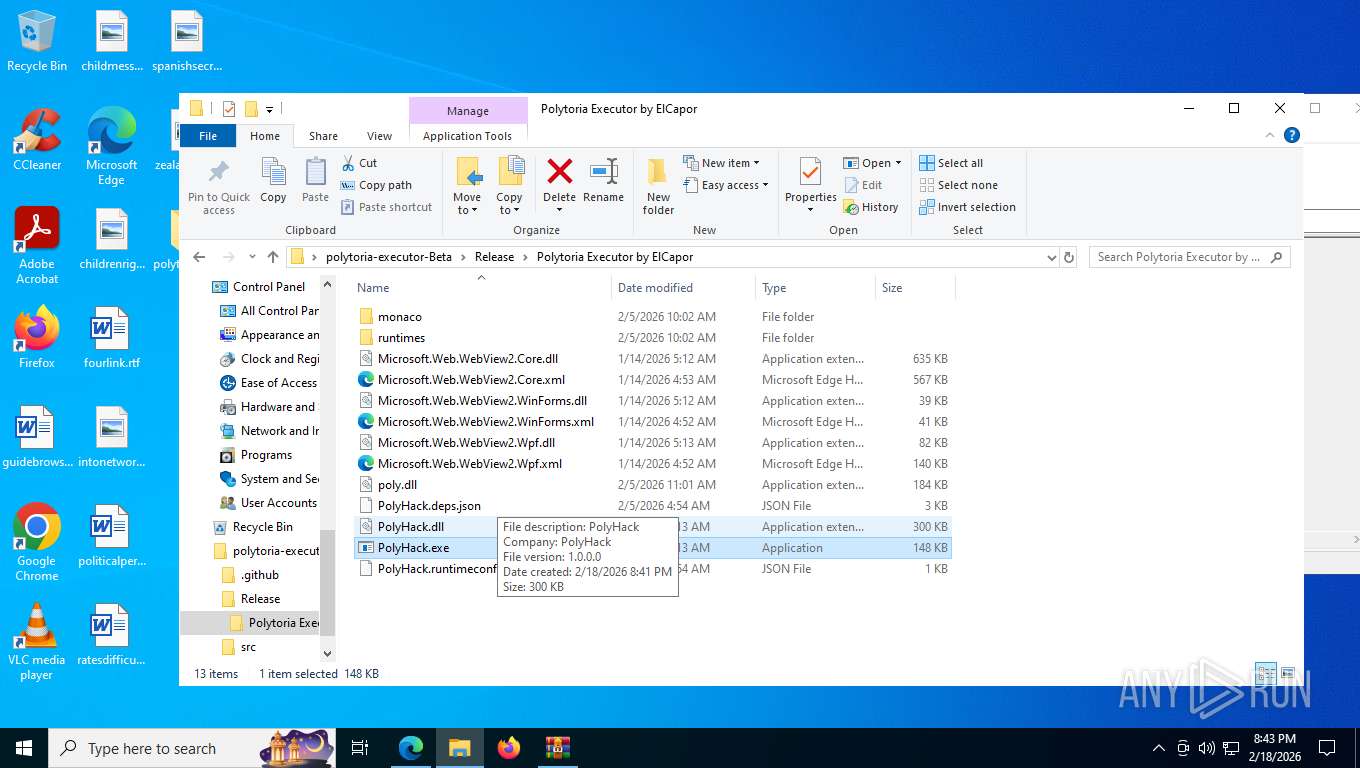
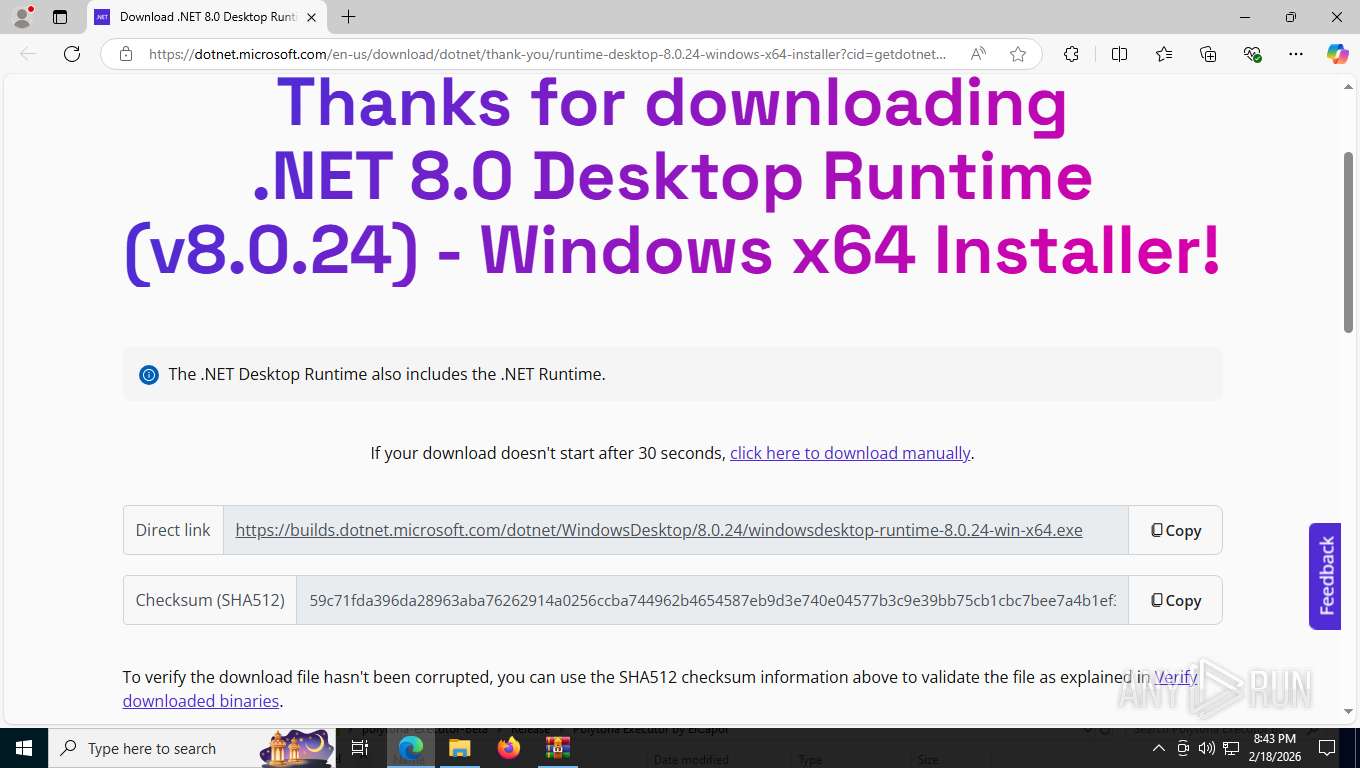
PolyHack.exe | Failed to resolve hostfxr.dll [not found]. Error code: 0x80008083 |
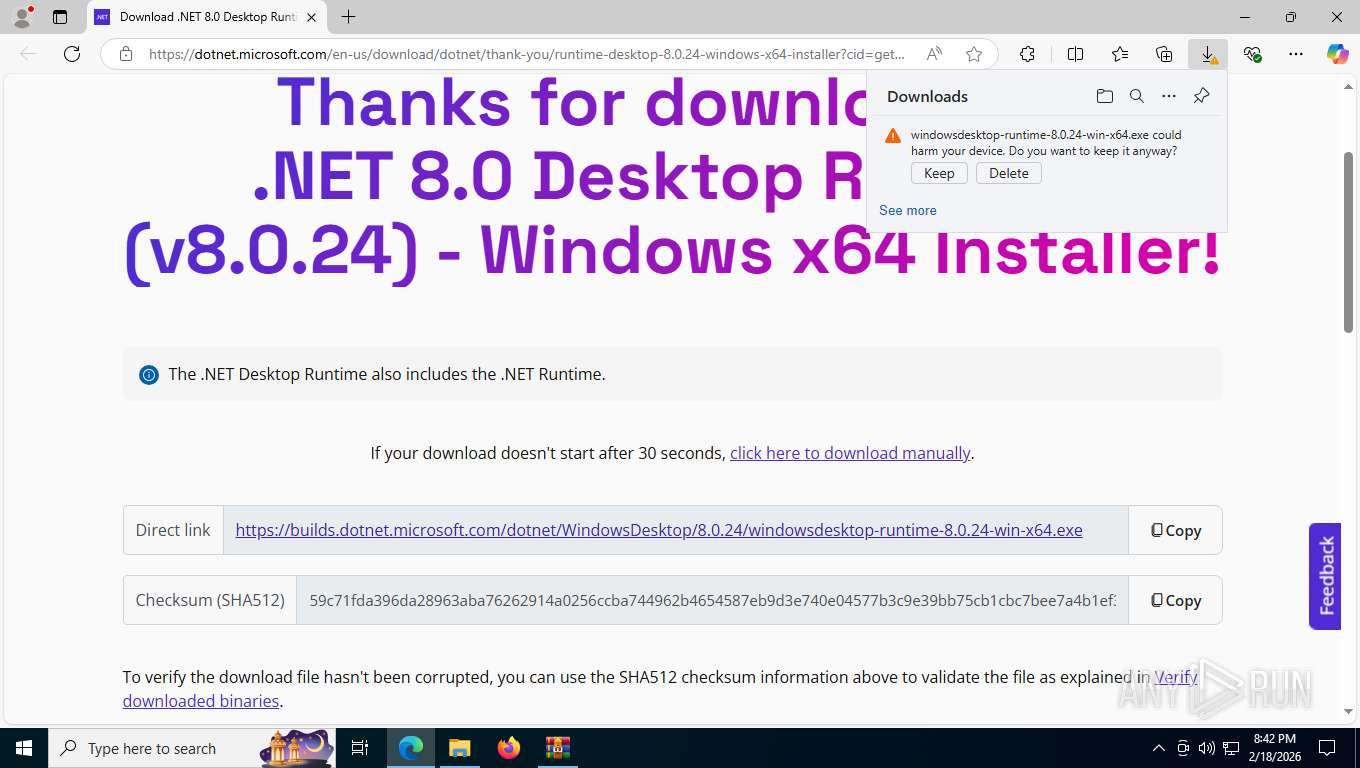
PolyHack.exe | You must install .NET to run this application.
App: C:\Users\admin\Desktop\polytoria-executor-Beta\Release\Polytoria Executor by ElCapor\PolyHack.exe
Architecture: x64
App host version: 8.0.23
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.23 |
PolyHack.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
PolyHack.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|