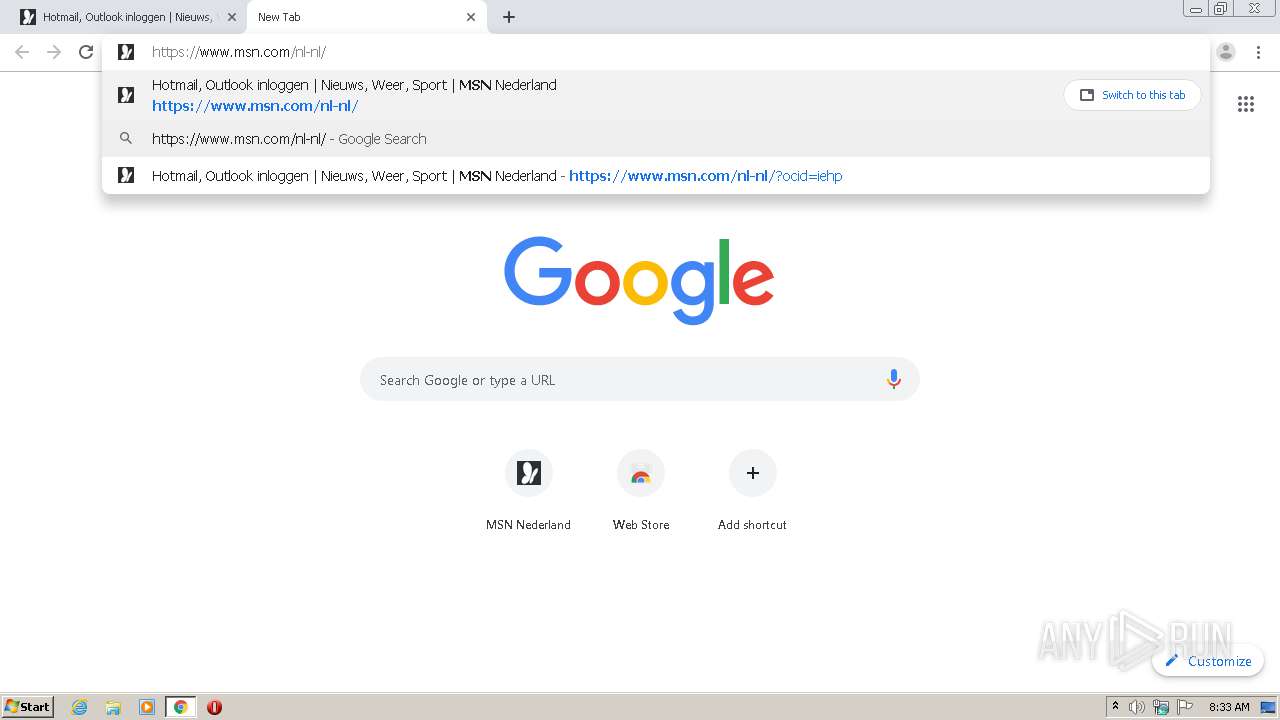
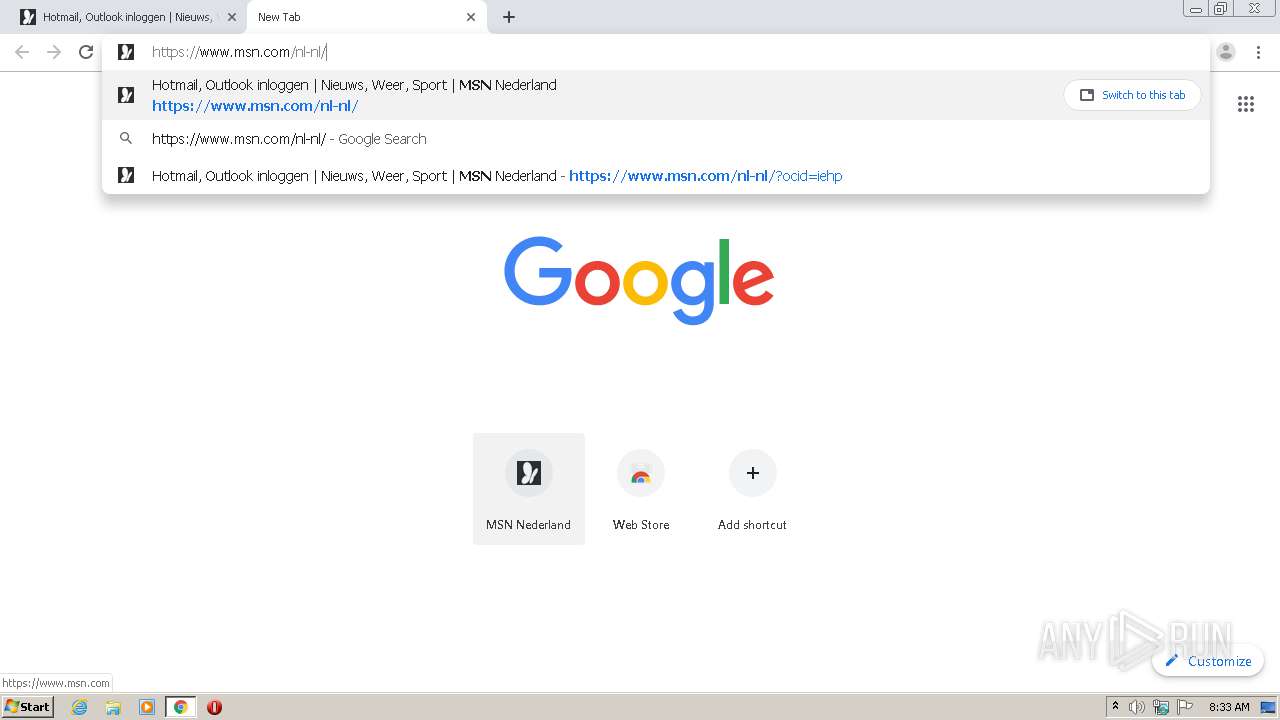
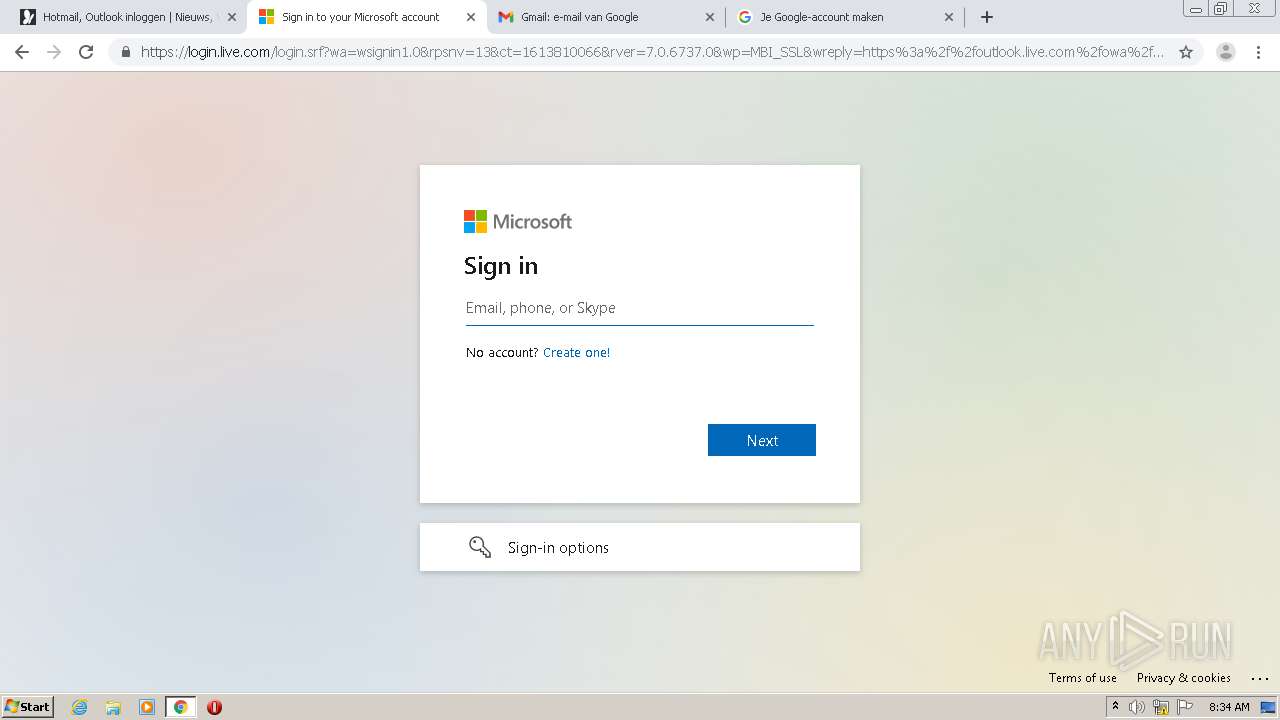
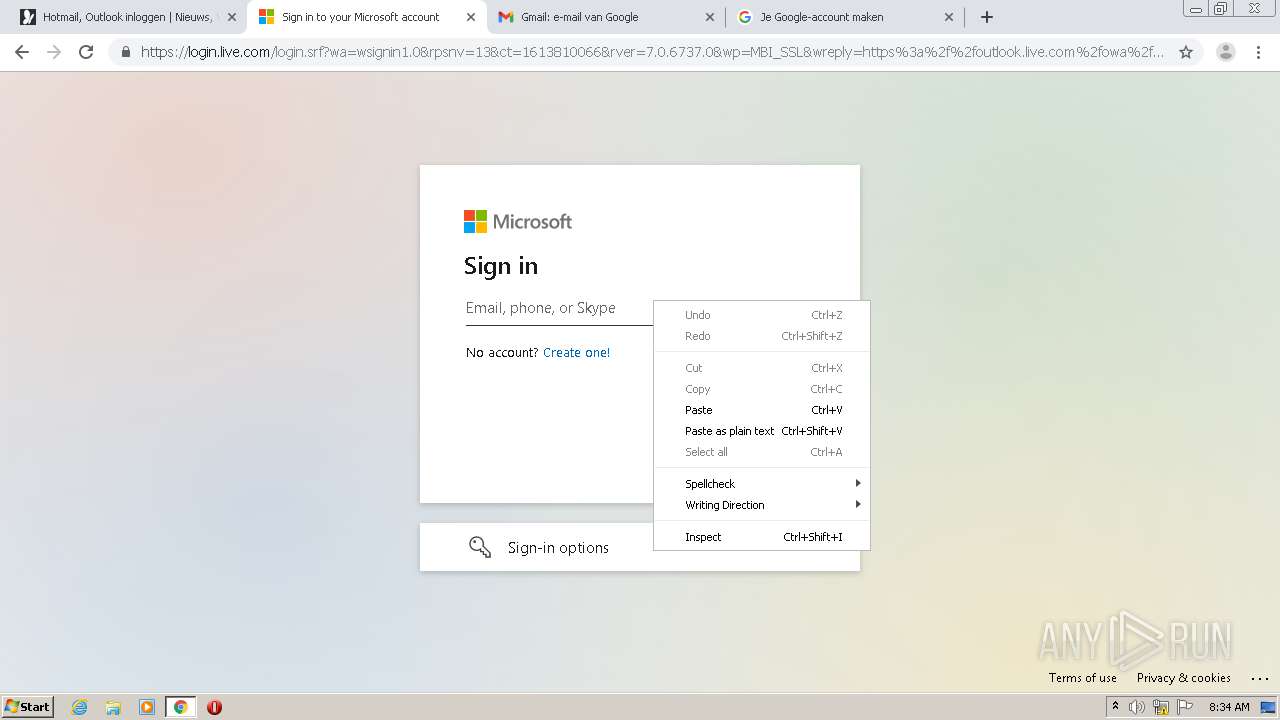
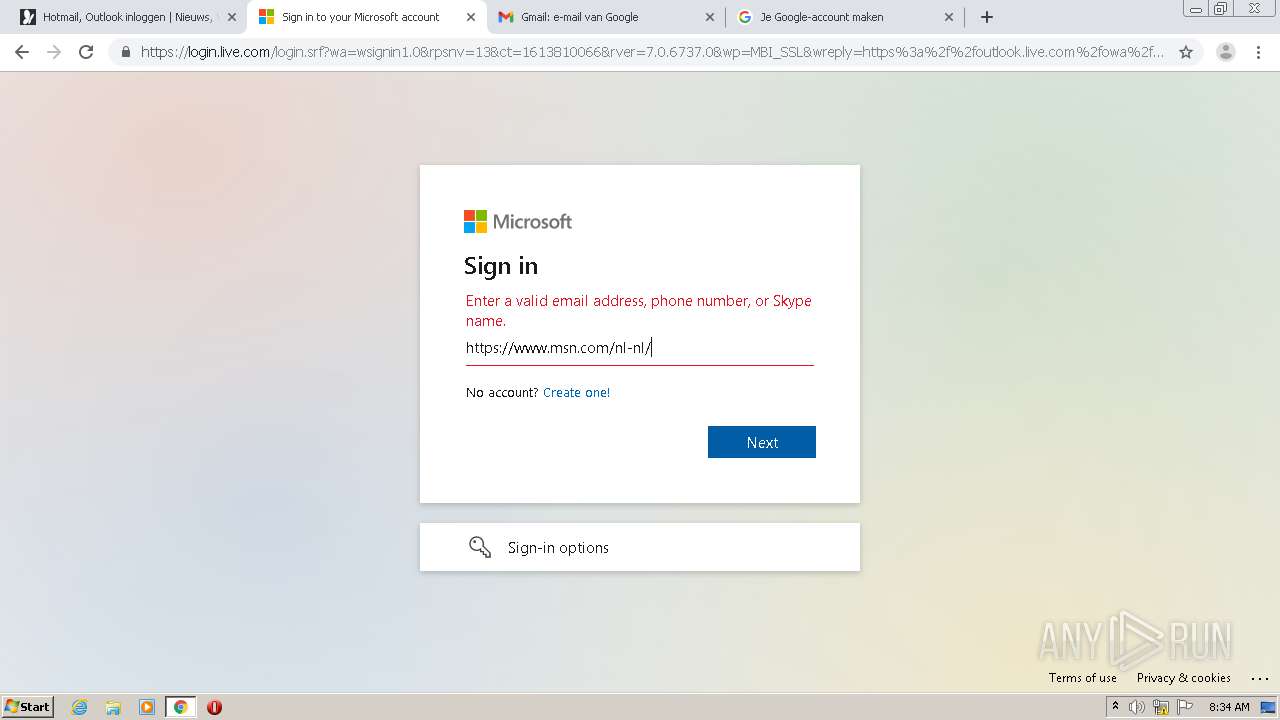
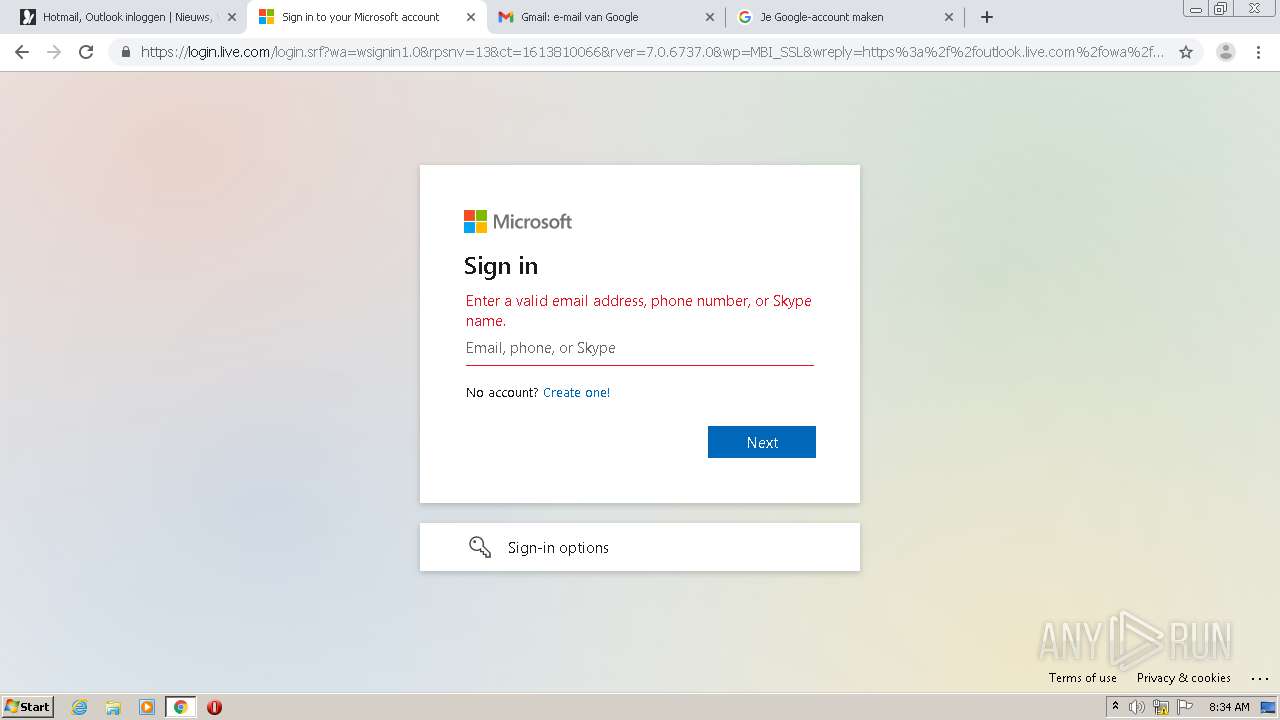
| URL: | http://go.microsoft.com/fwlink/p/?LinkId=255141 |
| Full analysis: | https://app.any.run/tasks/aeada460-572a-47ec-8410-06e445b0448f |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2021, 08:32:46 |
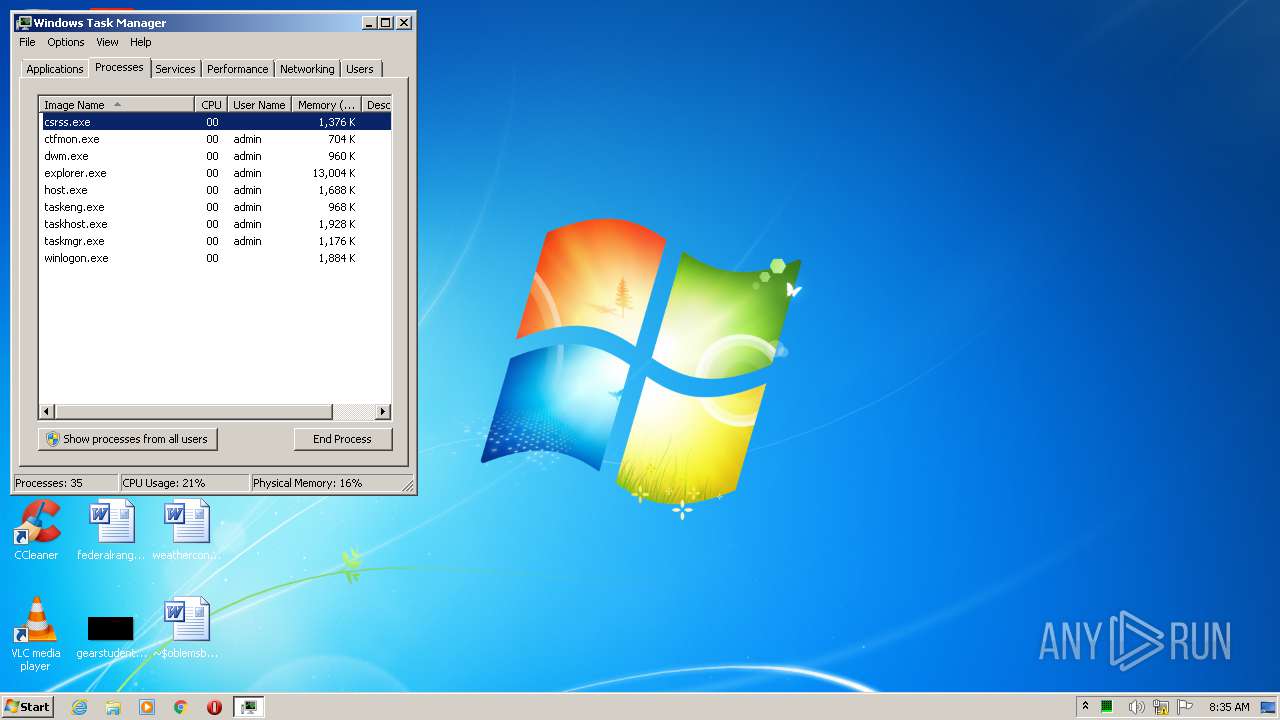
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C0ECFB97EC8F067F12B7B6DE29EB1A91 |
| SHA1: | DED4A54293DF8565534DD4EBD8FEC04CFFA6BA8D |
| SHA256: | C0CE90CB6ADD6E5CCF412C61DAC5AAAD1A2A0EA4EDA97DE57854DB4AFE3F1424 |
| SSDEEP: | 3:N1KZKLIetR7LOOKapMhI:C08eDPOOKaihI |
MALICIOUS
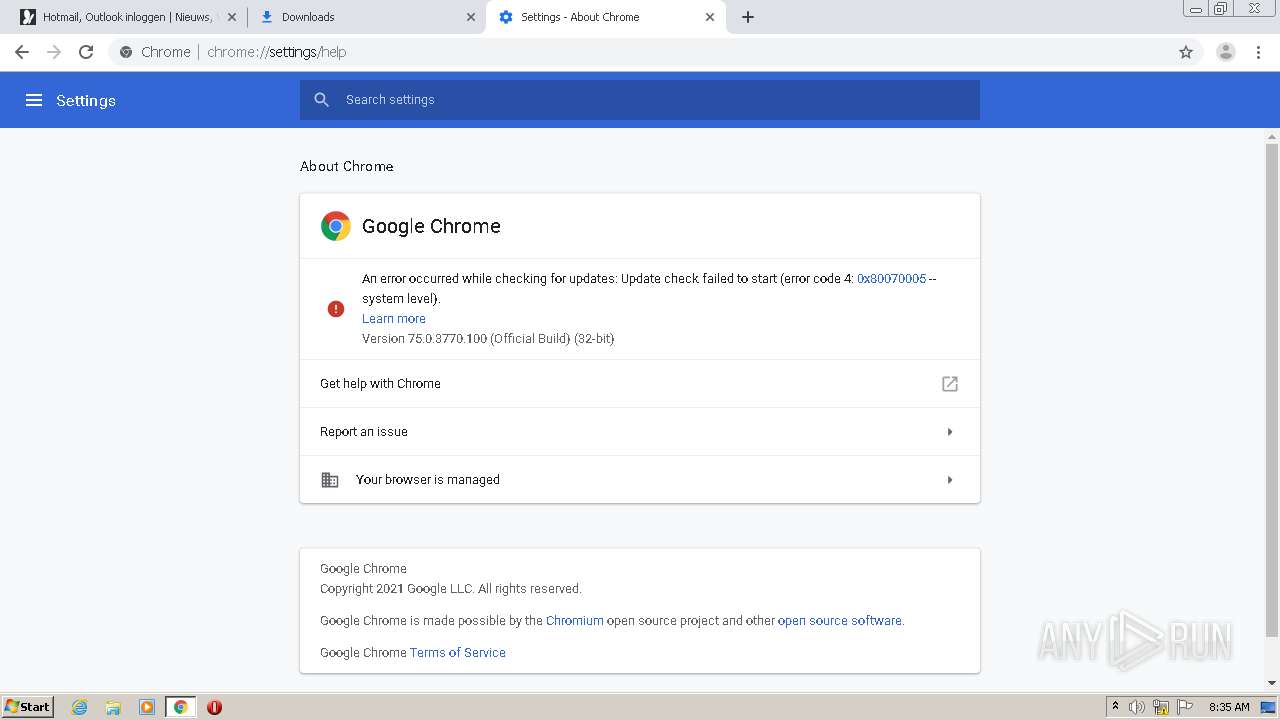
Changes settings of System certificates
- GoogleUpdate.exe (PID: 3292)
SUSPICIOUS
Executed via COM
- GoogleUpdateBroker.exe (PID: 1708)
- GoogleUpdateBroker.exe (PID: 3880)
- GoogleUpdateOnDemand.exe (PID: 2016)
- GoogleUpdateOnDemand.exe (PID: 3732)
- DllHost.exe (PID: 3772)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 3292)
INFO
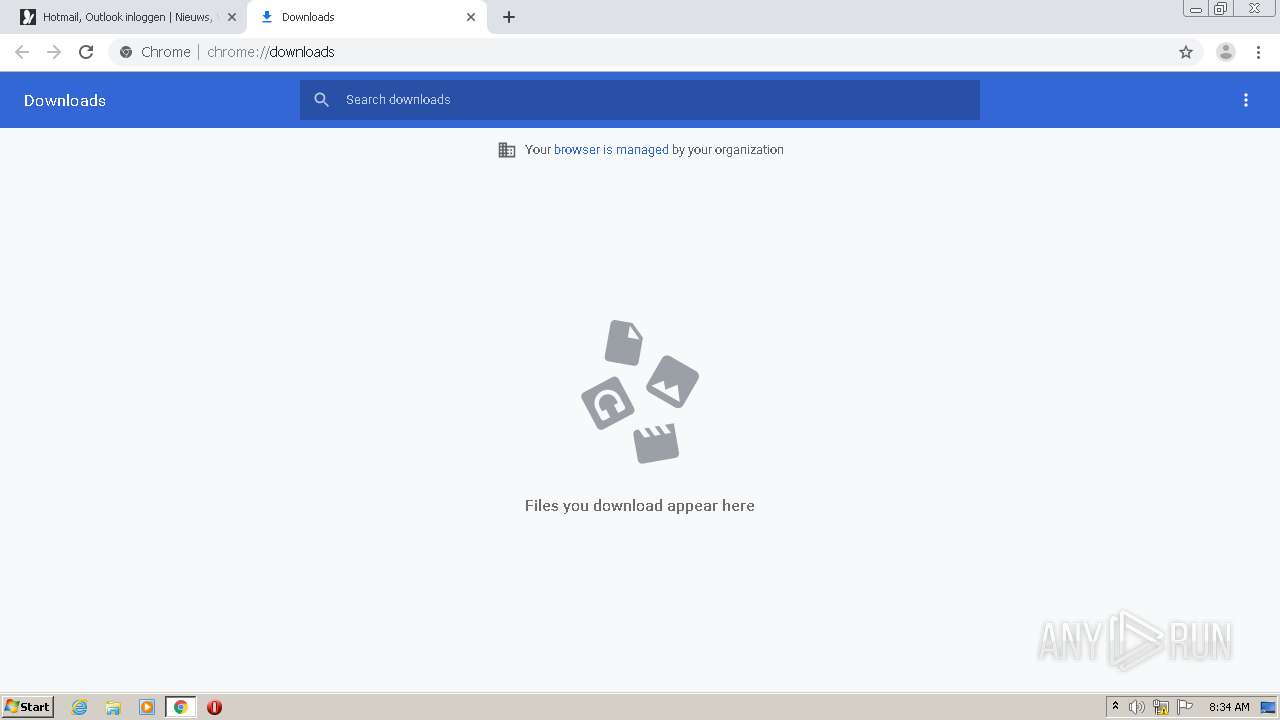
Reads the hosts file
- chrome.exe (PID: 1700)
- chrome.exe (PID: 2096)
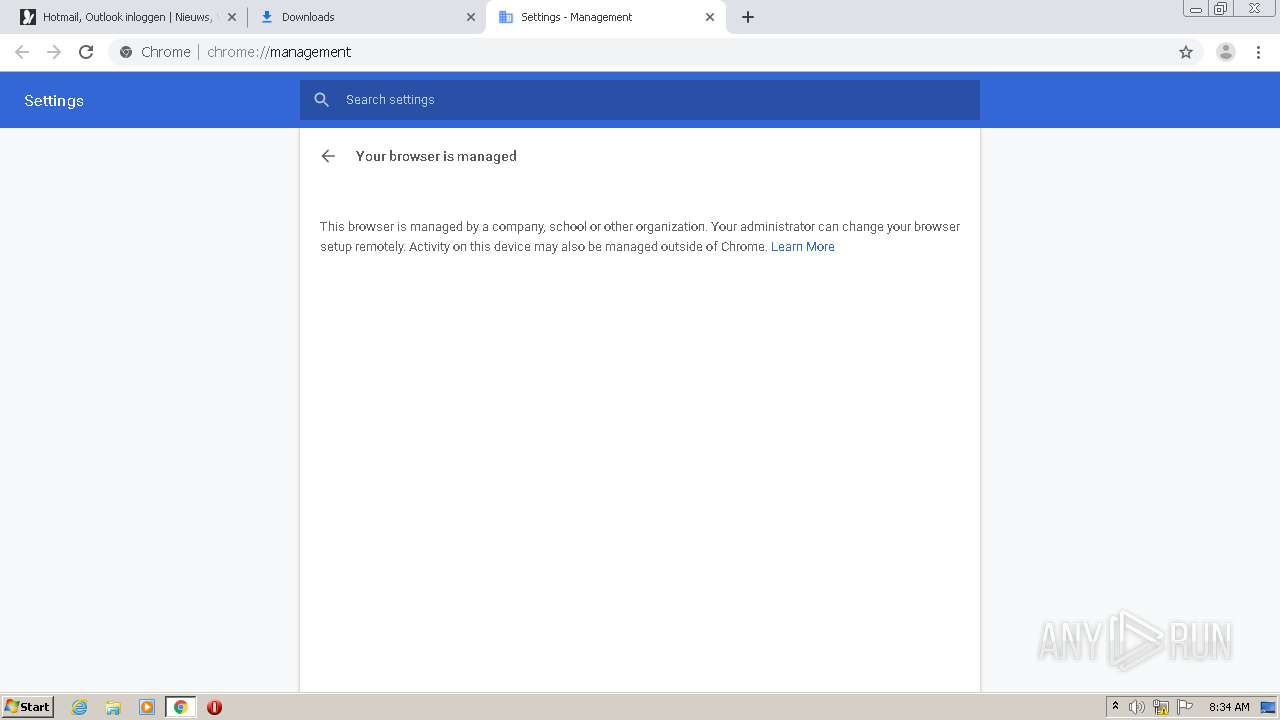
Reads settings of System Certificates
- chrome.exe (PID: 1700)
- GoogleUpdate.exe (PID: 3292)
Creates files in the user directory
- chrome.exe (PID: 2096)
- WINWORD.EXE (PID: 1460)
Application launched itself
- chrome.exe (PID: 2096)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1460)
Manual execution by user
- WINWORD.EXE (PID: 1460)
- taskmgr.exe (PID: 1104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
55
Malicious processes
0
Suspicious processes
0
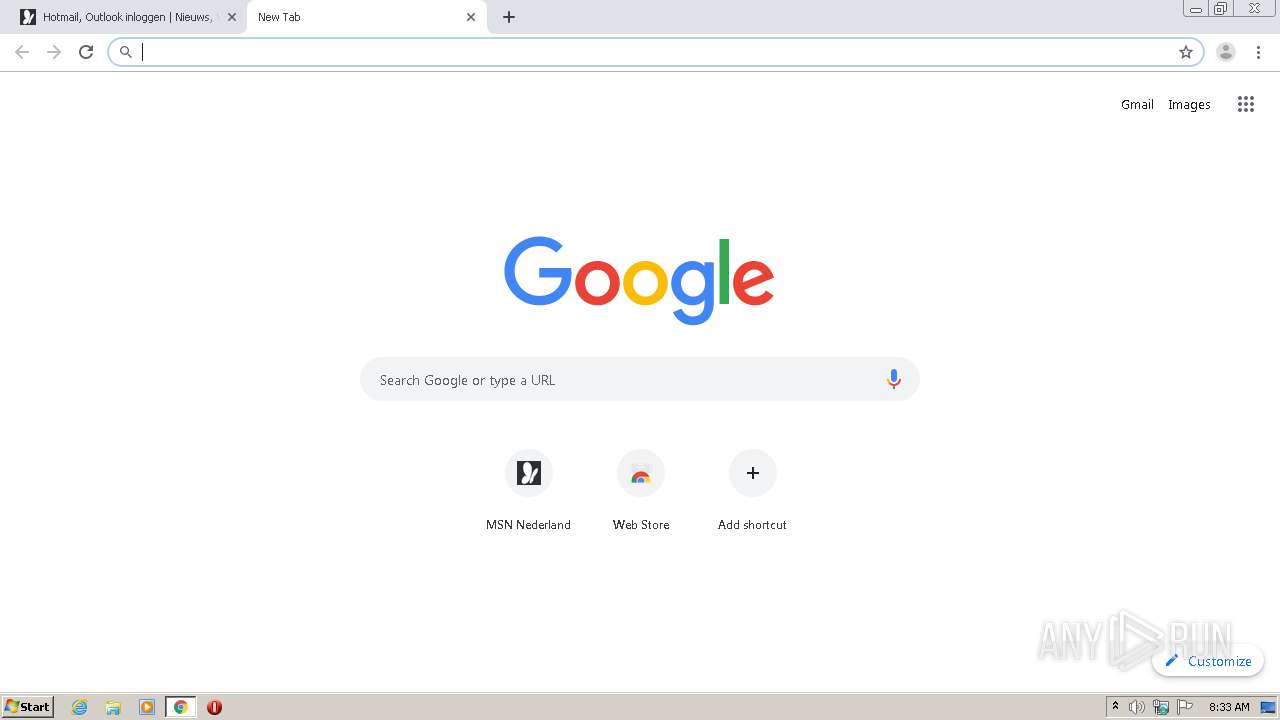
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
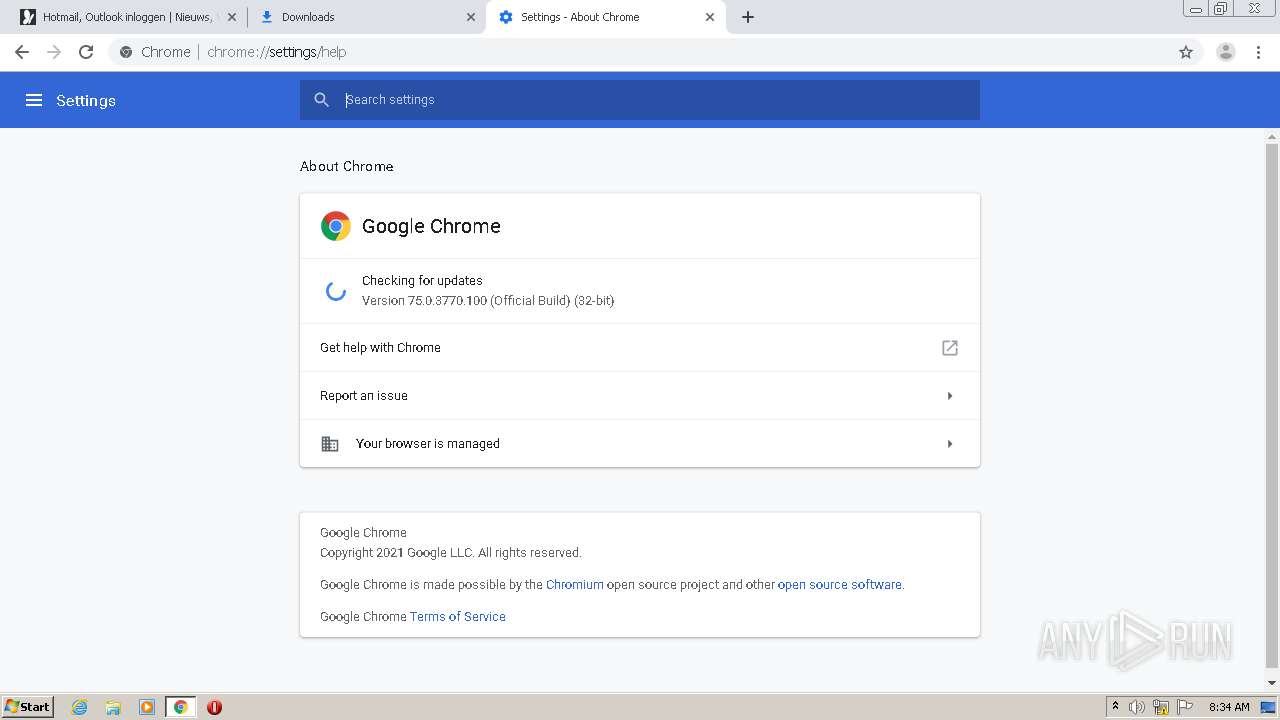
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi-broker --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=2119413795885150579 --mojo-platform-channel-handle=4908 /prefetch:4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16898888475974363545 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13210477375596654235 --mojo-platform-channel-handle=4428 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15329542474250897150 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1104 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12247527219293750975 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11890625328234953282 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\problemsbecause.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8084372998671908873 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,11944928239479706555,7326628992137898923,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5460908728132487850 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 198
Read events
1 734
Write events
316
Delete events
148
Modification events
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2096-13258283582206375 |
Value: 259 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
143
Text files
135
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6030C93E-830.pma | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\34757773-1498-455b-a82c-f4aef8bfec56.tmp | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFce9c9.TMP | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFcebdc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
190
DNS requests
121
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
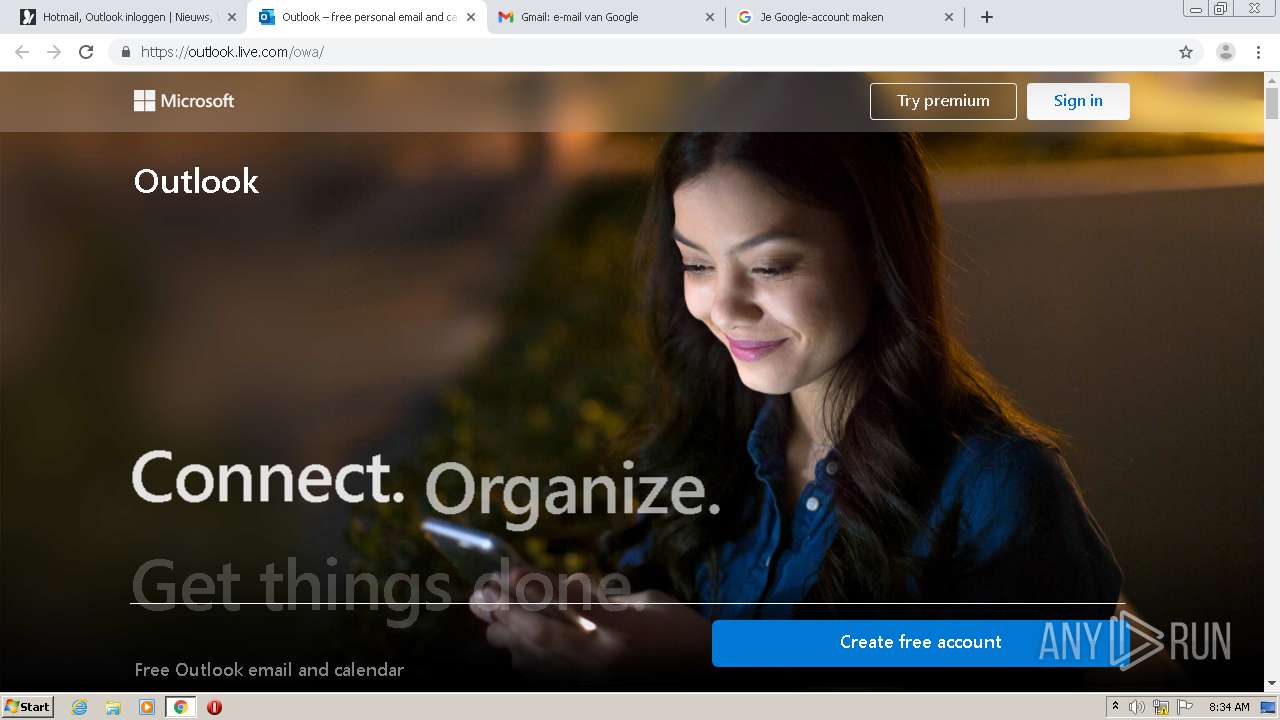
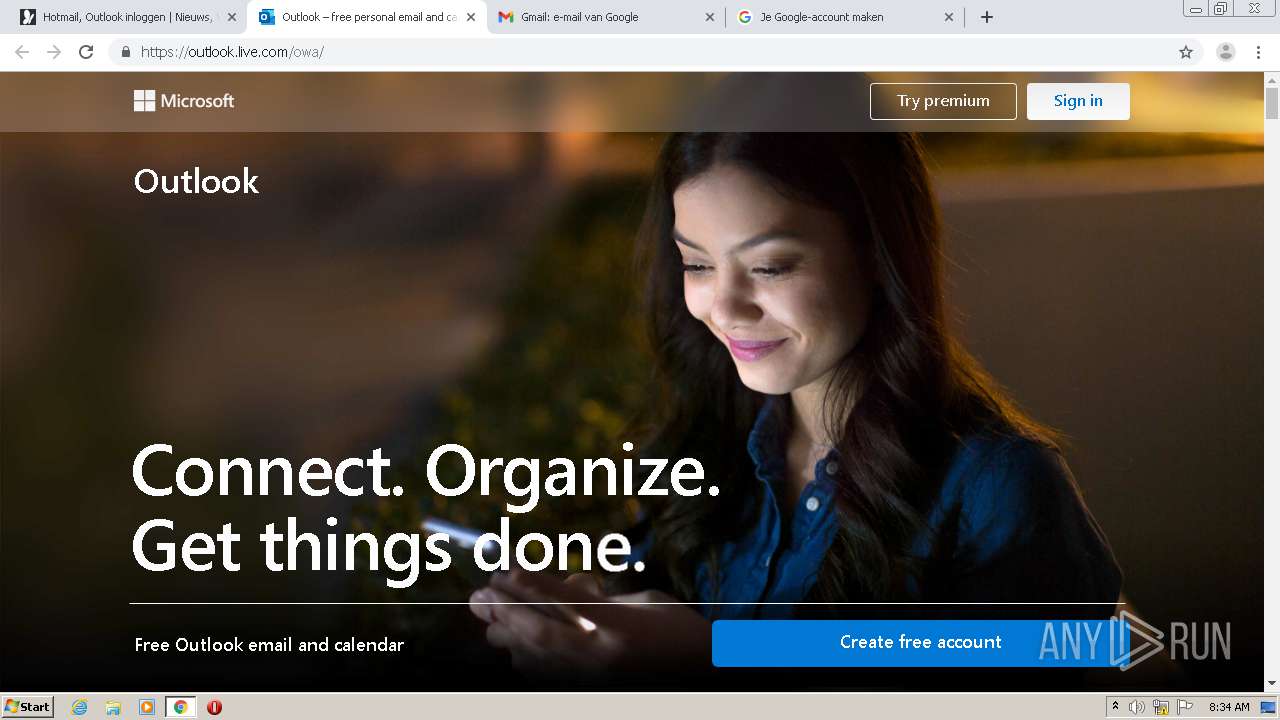
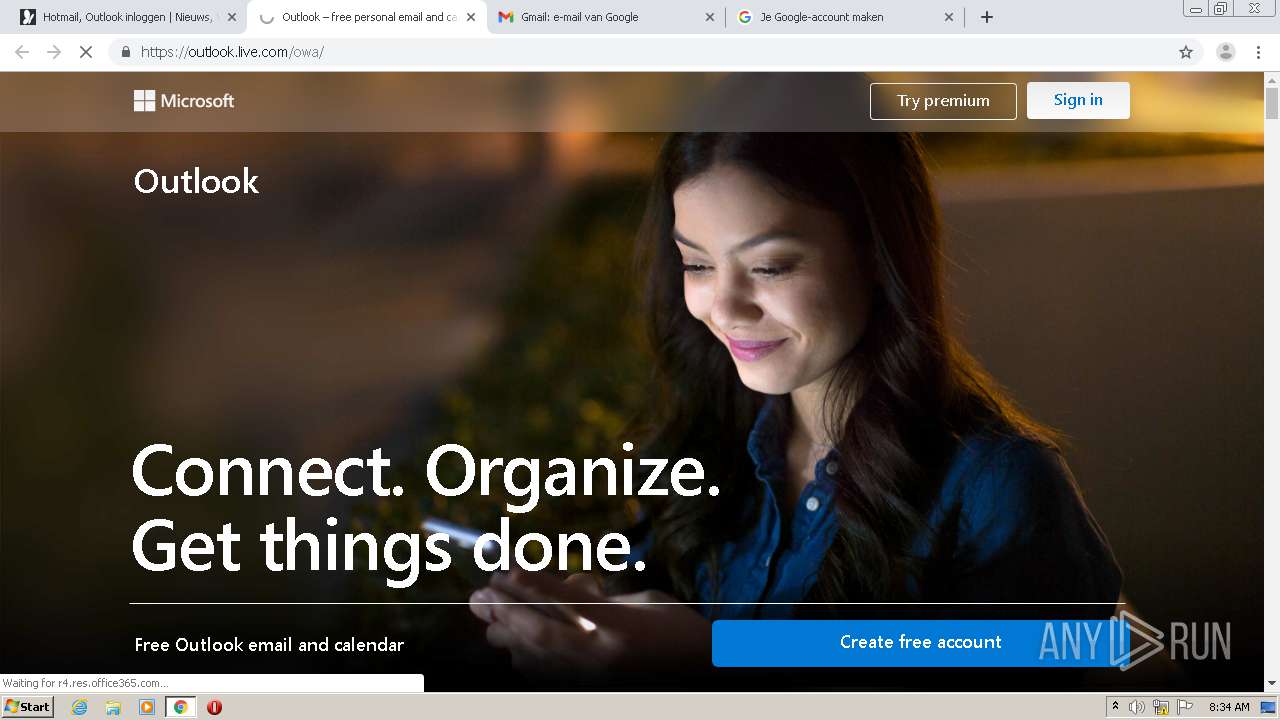
1700 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.7 Kb | whitelisted |
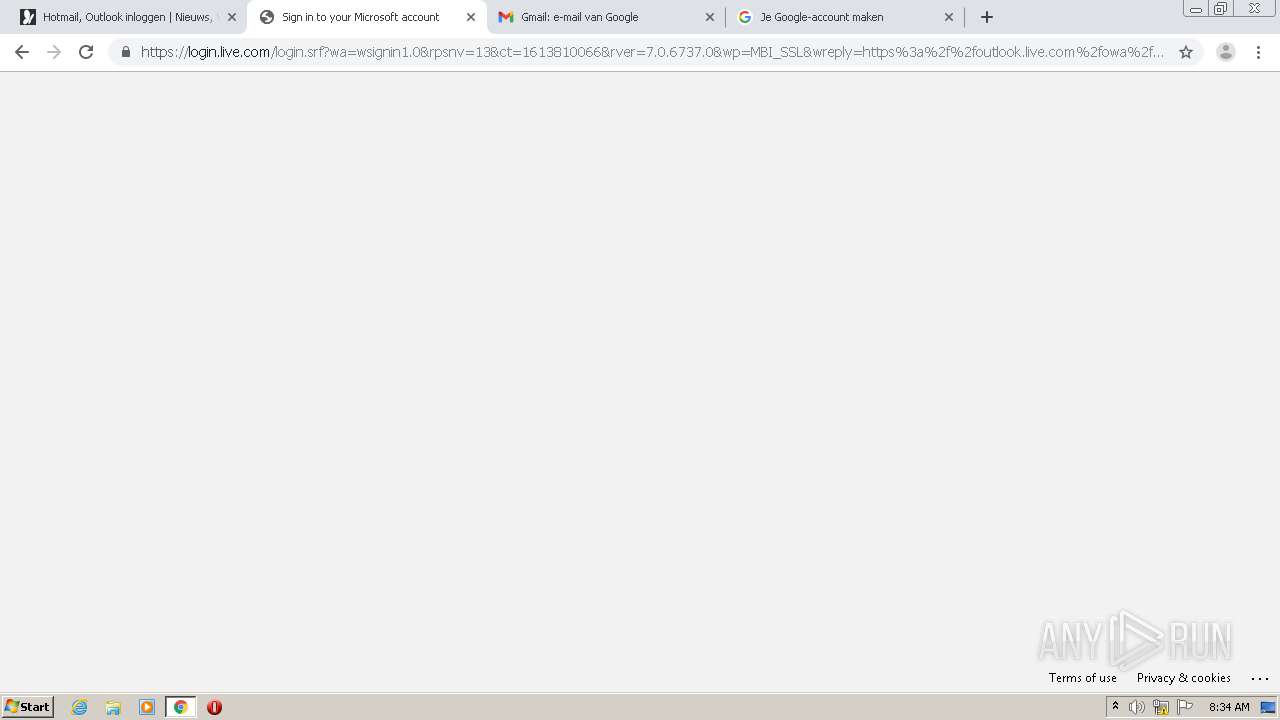
1700 | chrome.exe | GET | 301 | 104.109.95.91:80 | http://go.microsoft.com/fwlink/p/?LinkId=255141 | NL | — | — | whitelisted |
1700 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
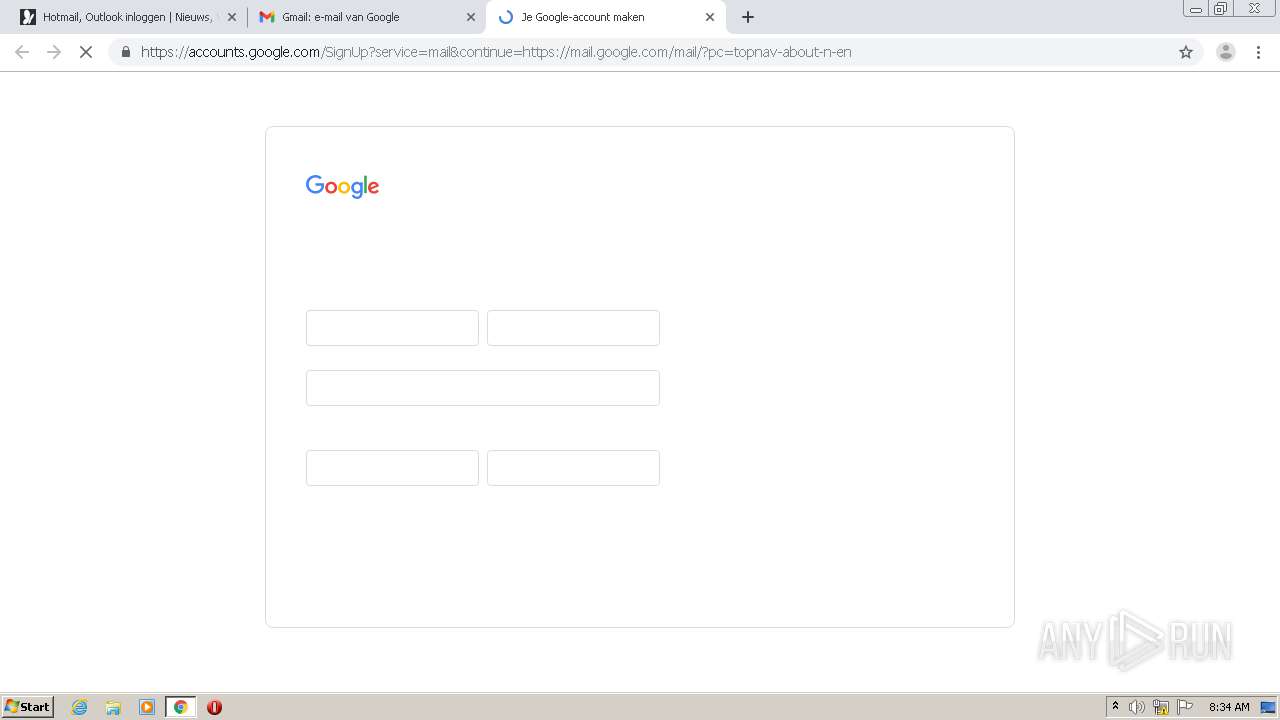
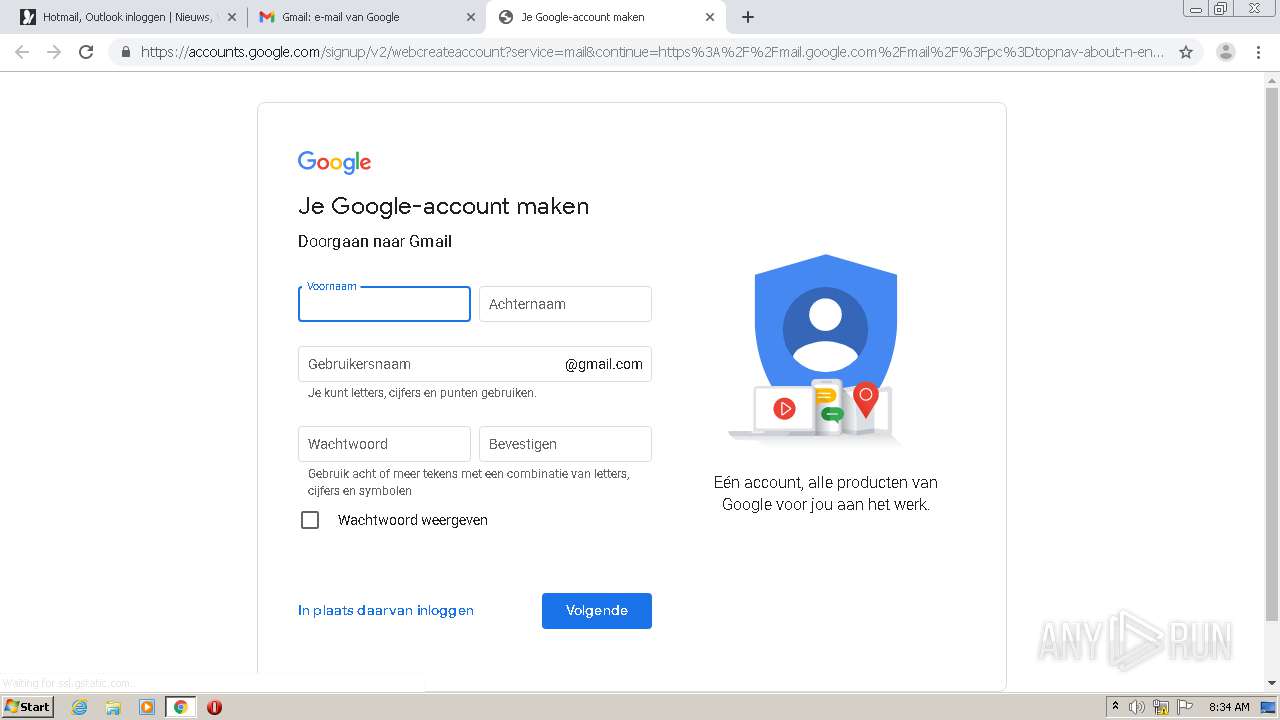
1700 | chrome.exe | 142.250.136.84:443 | accounts.google.com | Google Inc. | US | unknown |
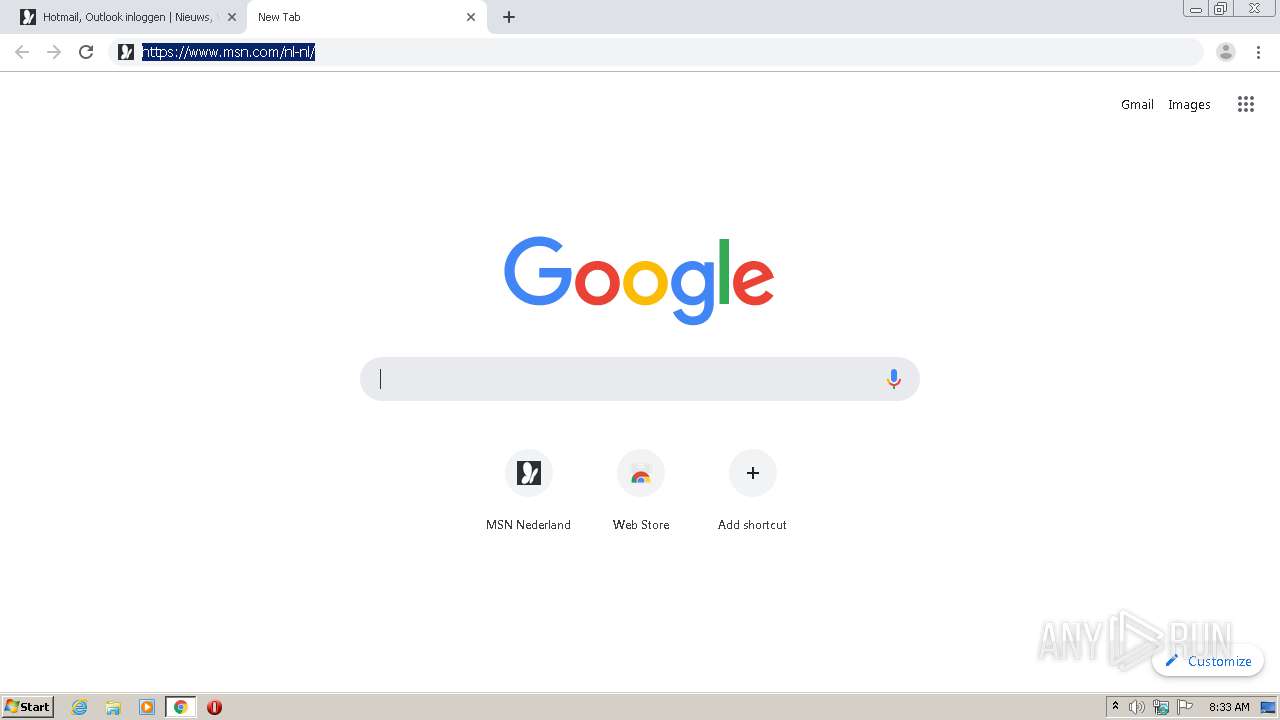
1700 | chrome.exe | 104.109.95.91:80 | go.microsoft.com | Akamai International B.V. | NL | unknown |
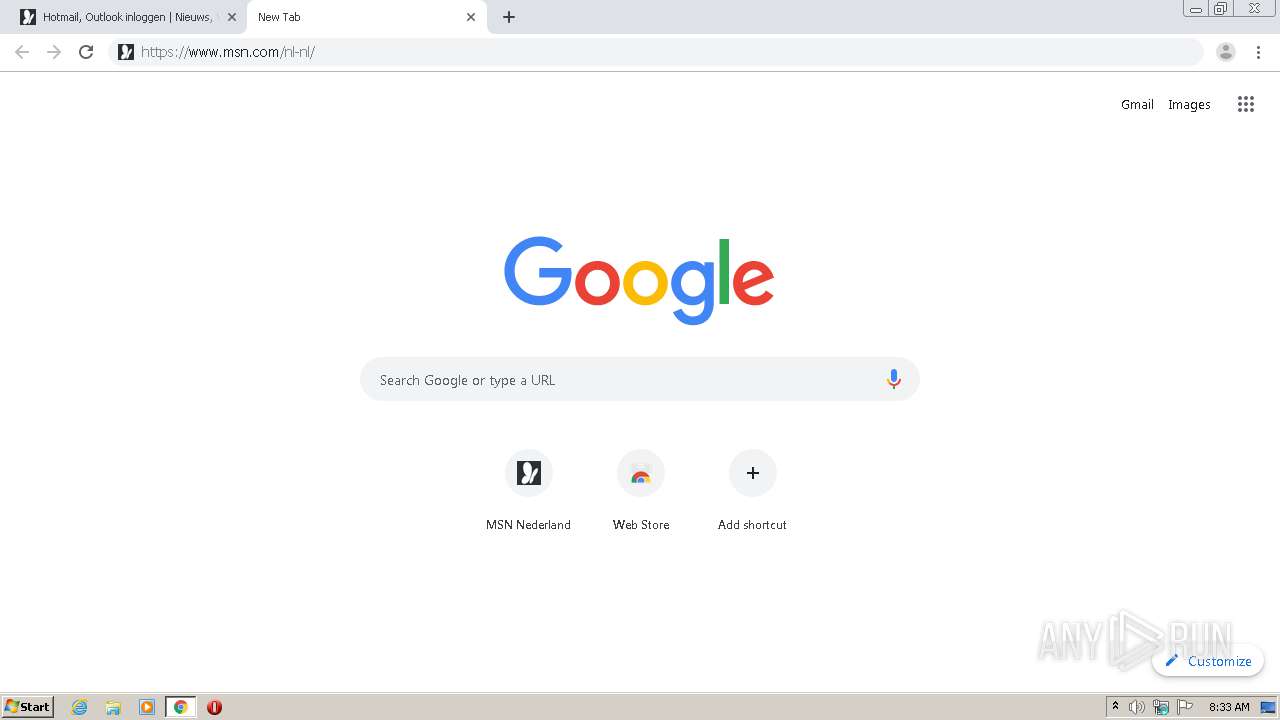
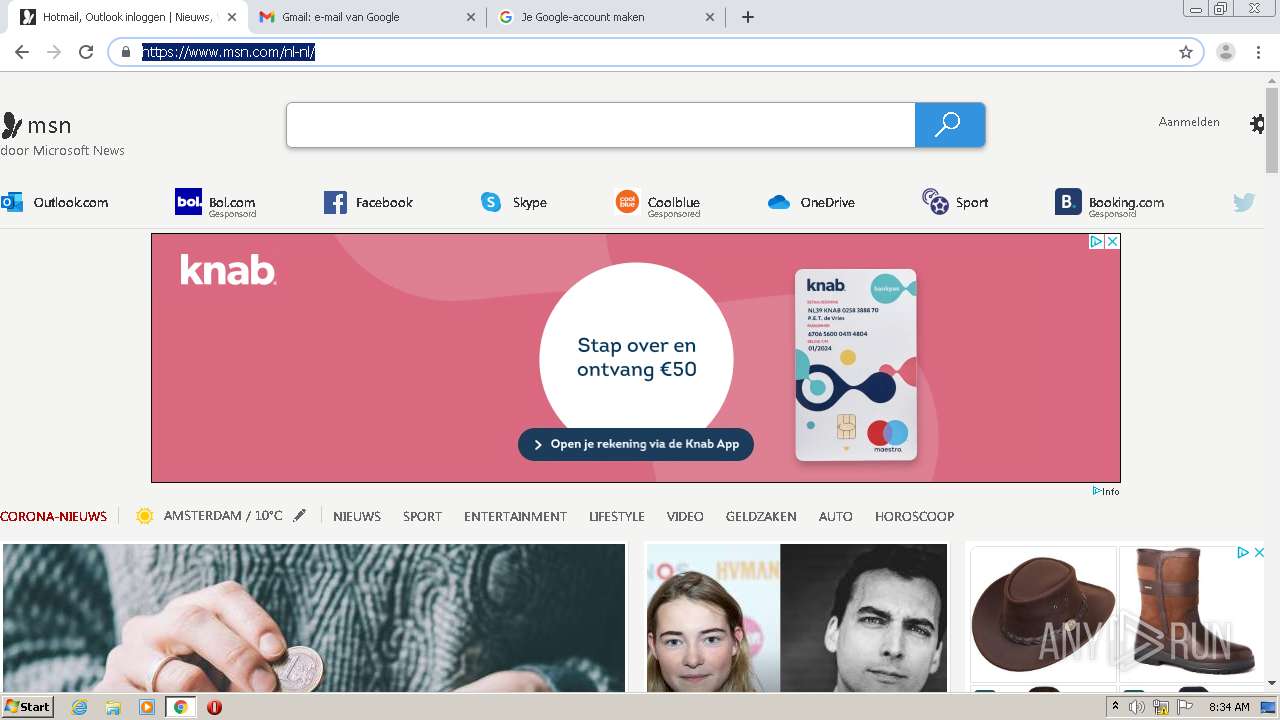
1700 | chrome.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
1700 | chrome.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1700 | chrome.exe | 40.77.226.250:443 | web.vortex.data.msn.com | Microsoft Corporation | IE | whitelisted |
1700 | chrome.exe | 104.20.185.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
1700 | chrome.exe | 108.177.121.100:443 | clients1.google.com | Google Inc. | US | unknown |
1700 | chrome.exe | 142.250.186.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 2.16.186.35:443 | static-global-s-msn-com.akamaized.net | Akamai International B.V. | — | whitelisted |
1700 | chrome.exe | 151.101.193.44:443 | img.img-taboola.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
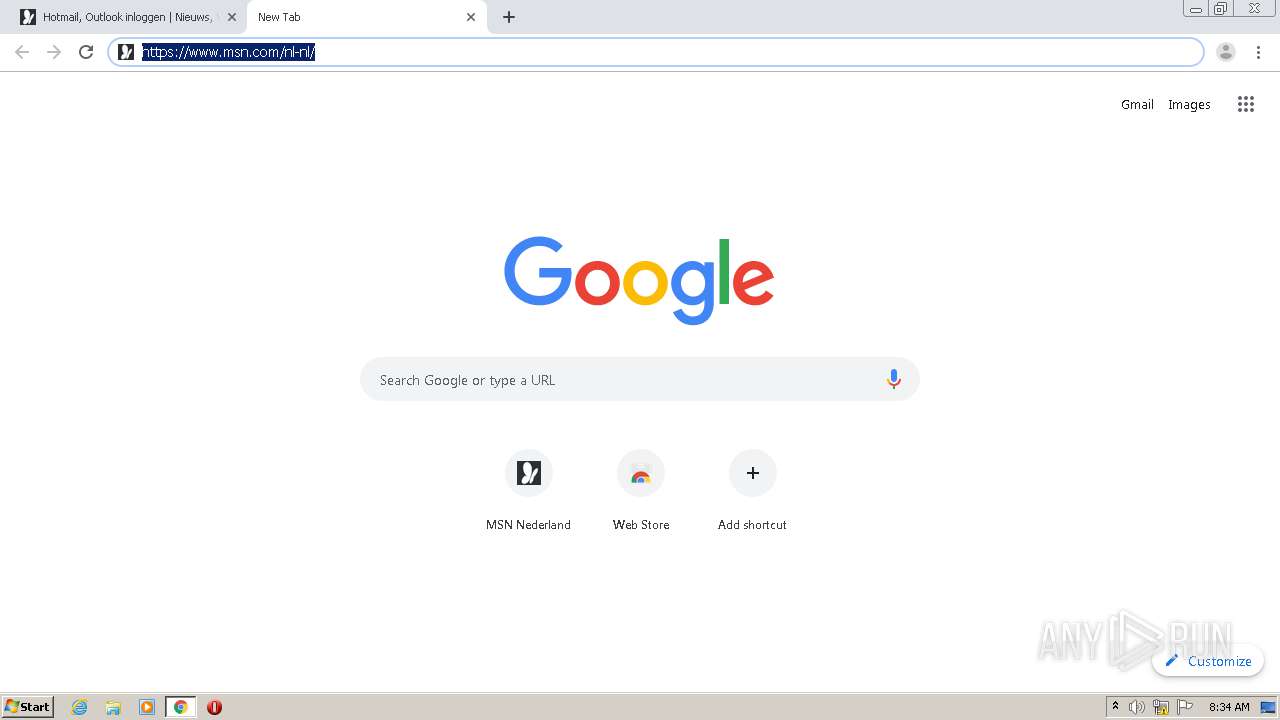
www.msn.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
static-global-s-msn-com.akamaized.net |
| whitelisted |
www.bing.com |
| whitelisted |
web.vortex.data.msn.com |
| whitelisted |
clients1.google.com |
| whitelisted |
srtb.msn.com |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |