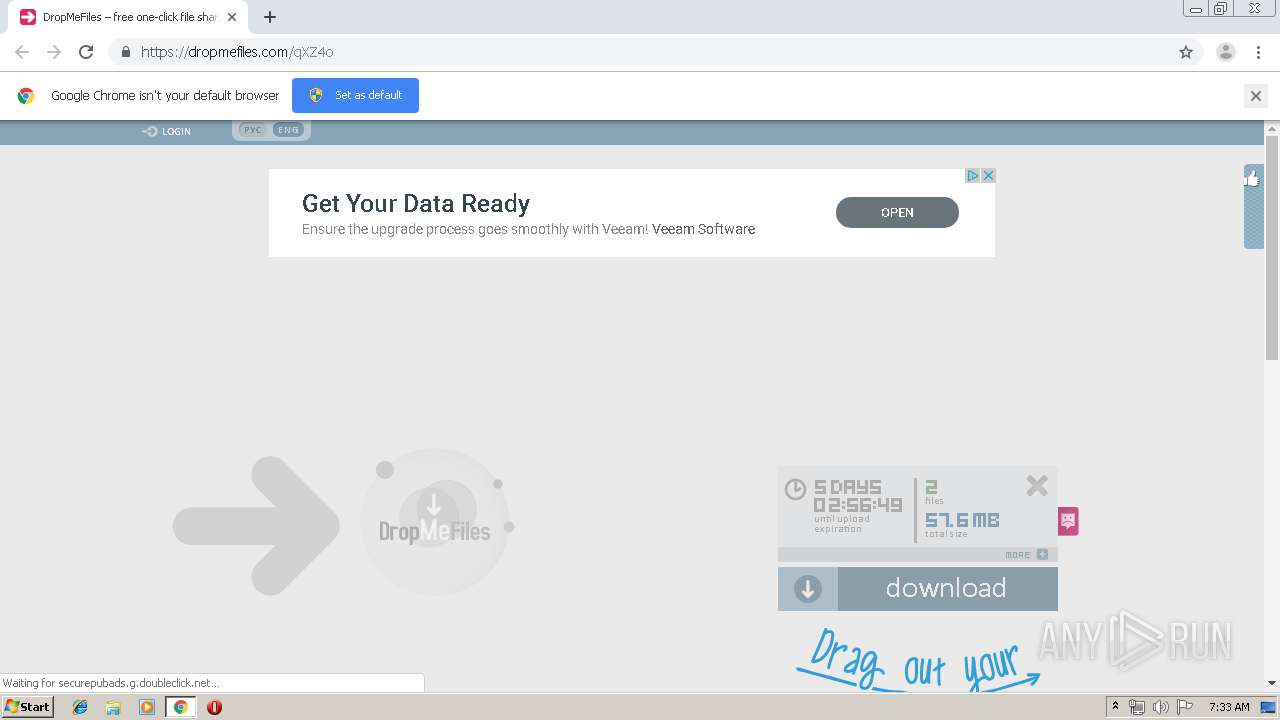
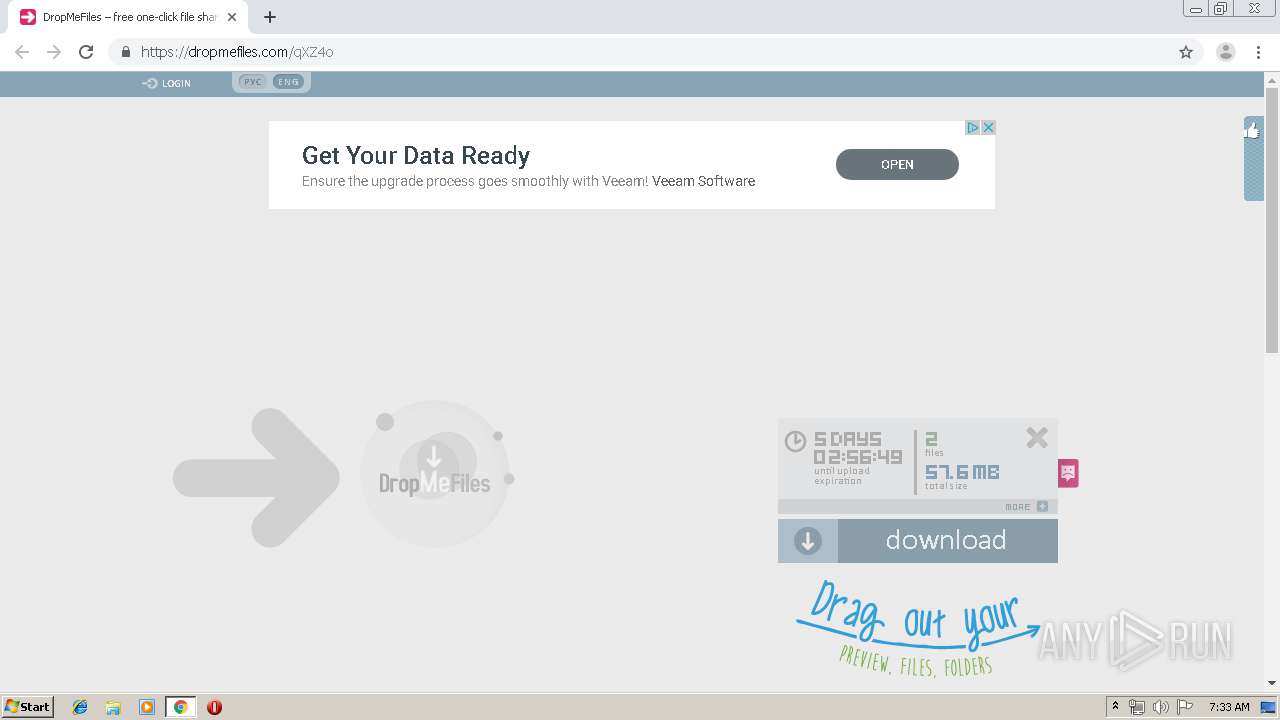
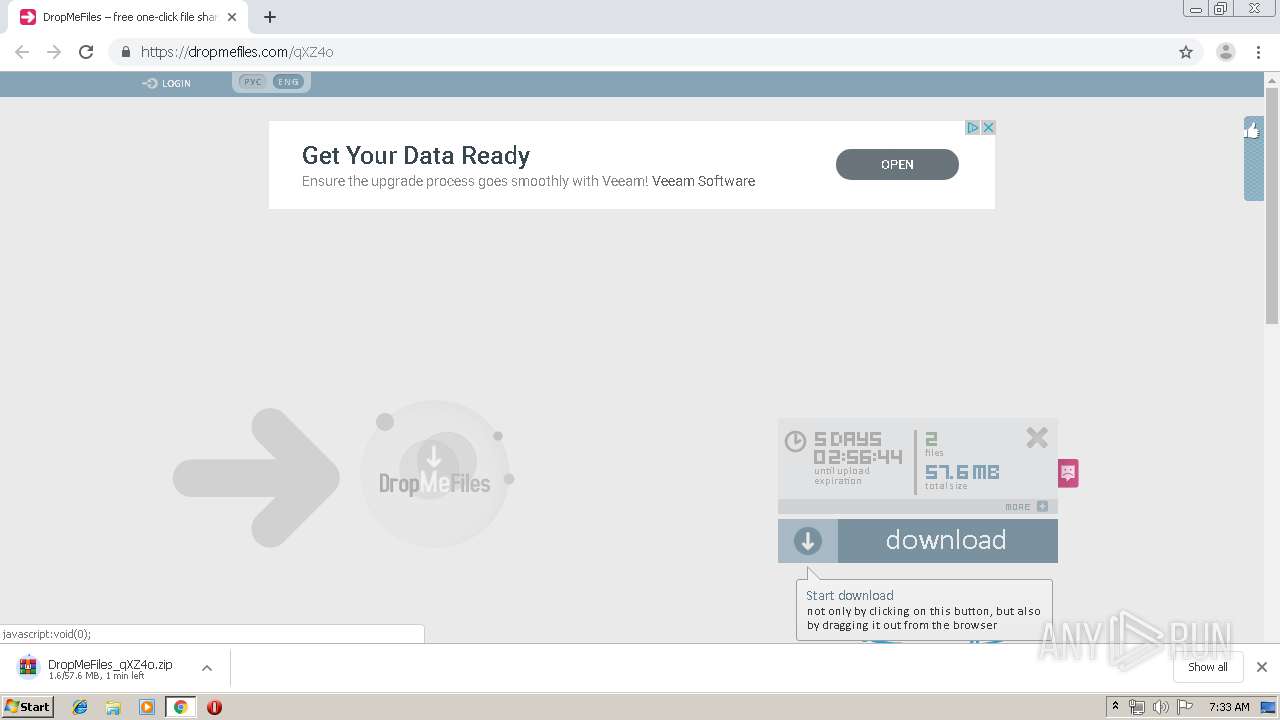
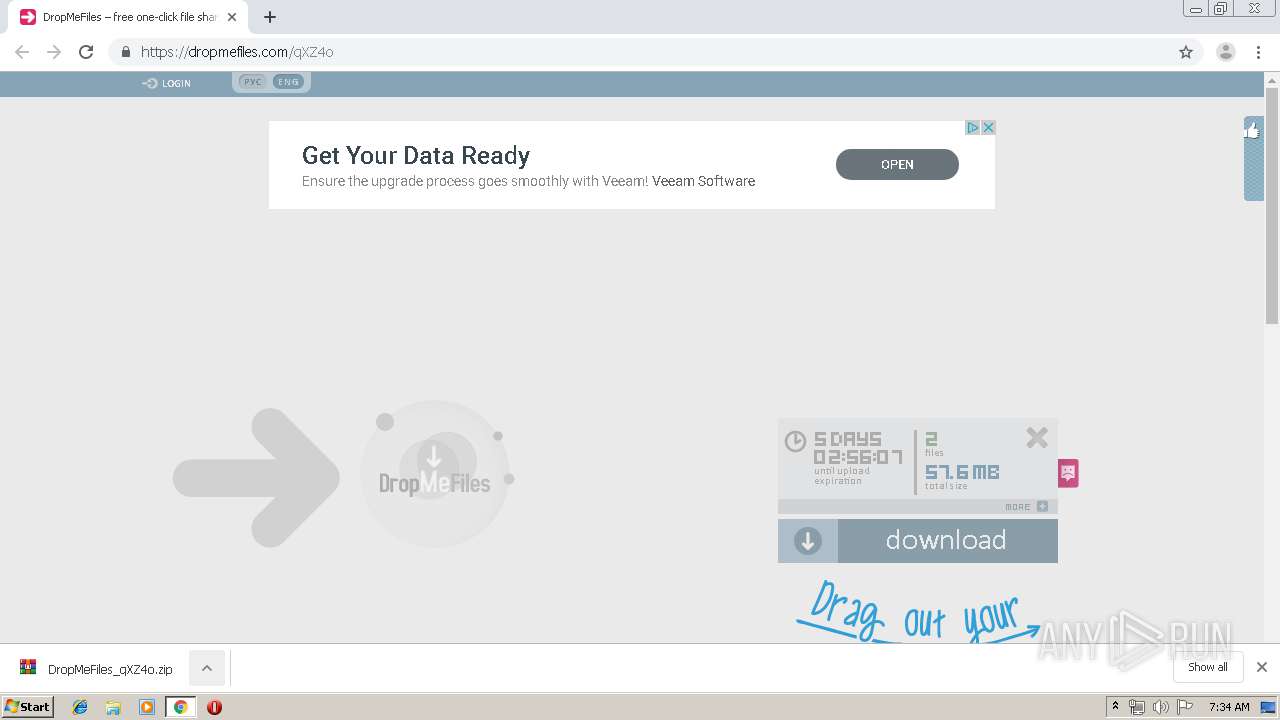
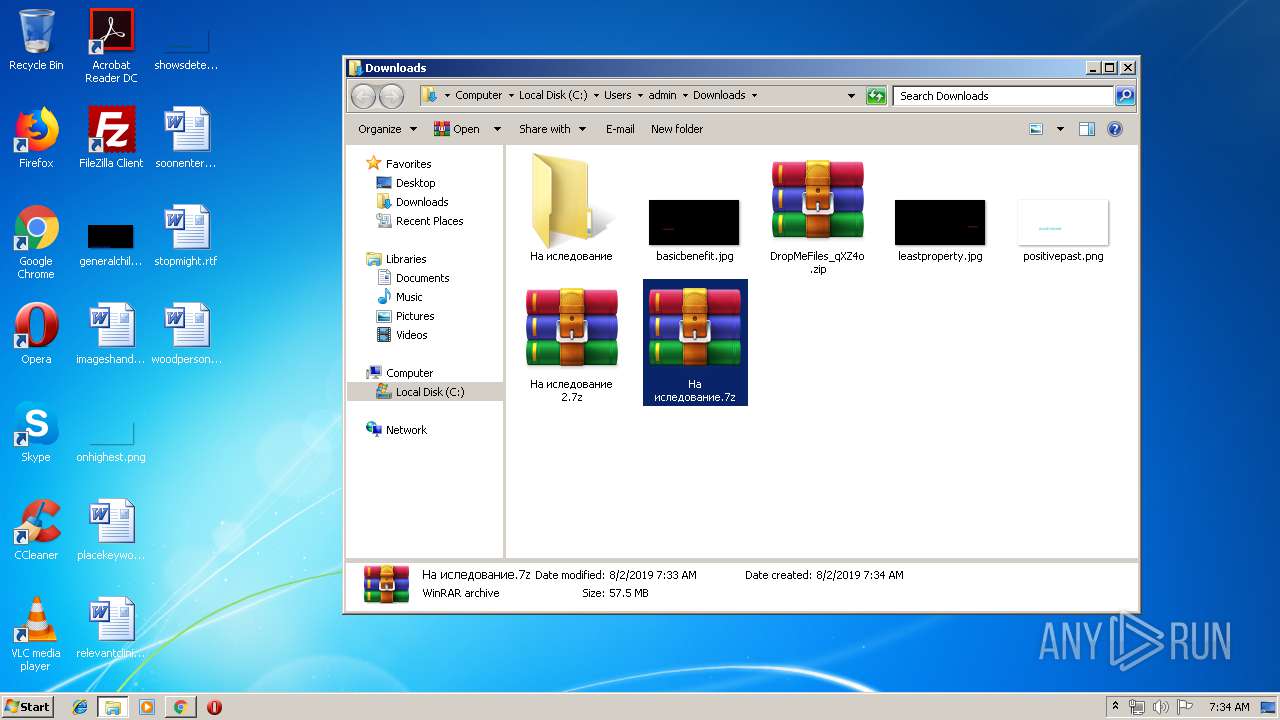
| URL: | https://dropmefiles.com/qXZ4o |
| Full analysis: | https://app.any.run/tasks/edd27cf4-1663-4790-b776-af404af015cb |
| Verdict: | Suspicious activity |
| Analysis date: | August 02, 2019, 06:32:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 00A06EB08AD84D8299DFB7D16DFC7325 |
| SHA1: | 130EA82B2D101E8FC0FDCD6ABEE65A8F2675F683 |
| SHA256: | C0CC89990024008C0C38BF125F783CD89093C60B7D84A70893FC42855A50A920 |
| SSDEEP: | 3:N8PKV9DNP9ZK:2oDNP90 |
MALICIOUS
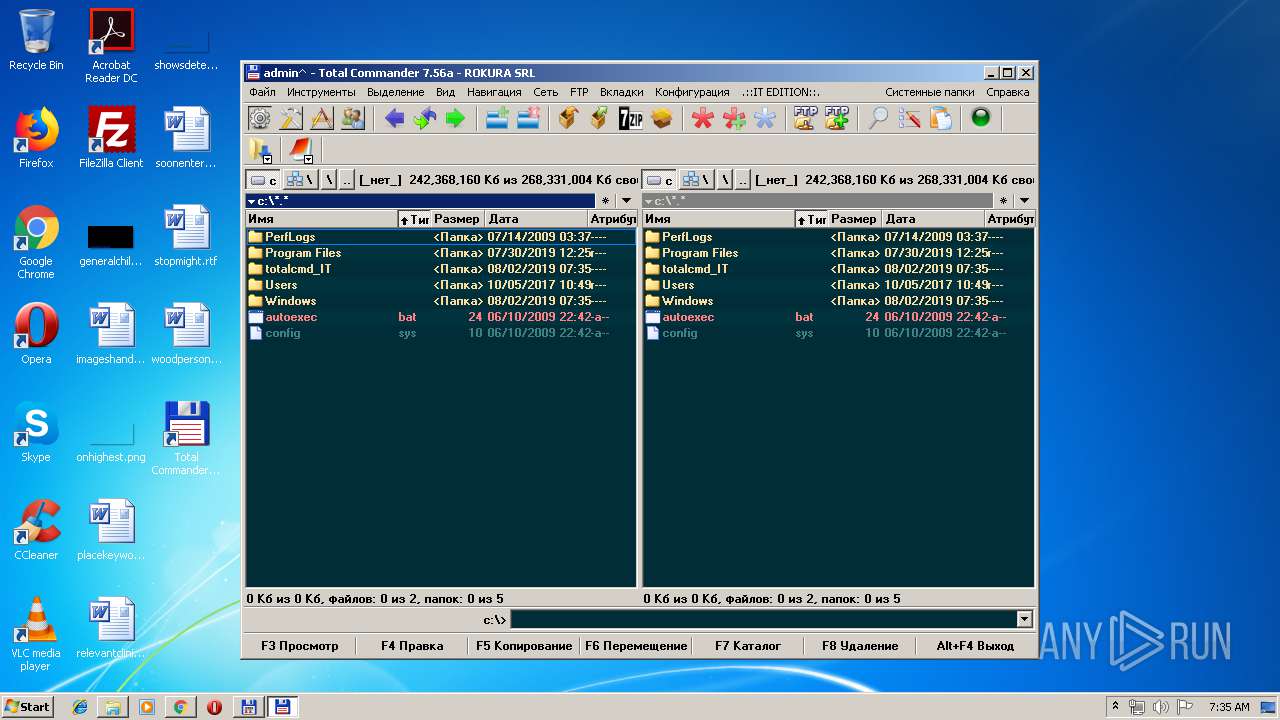
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 592)
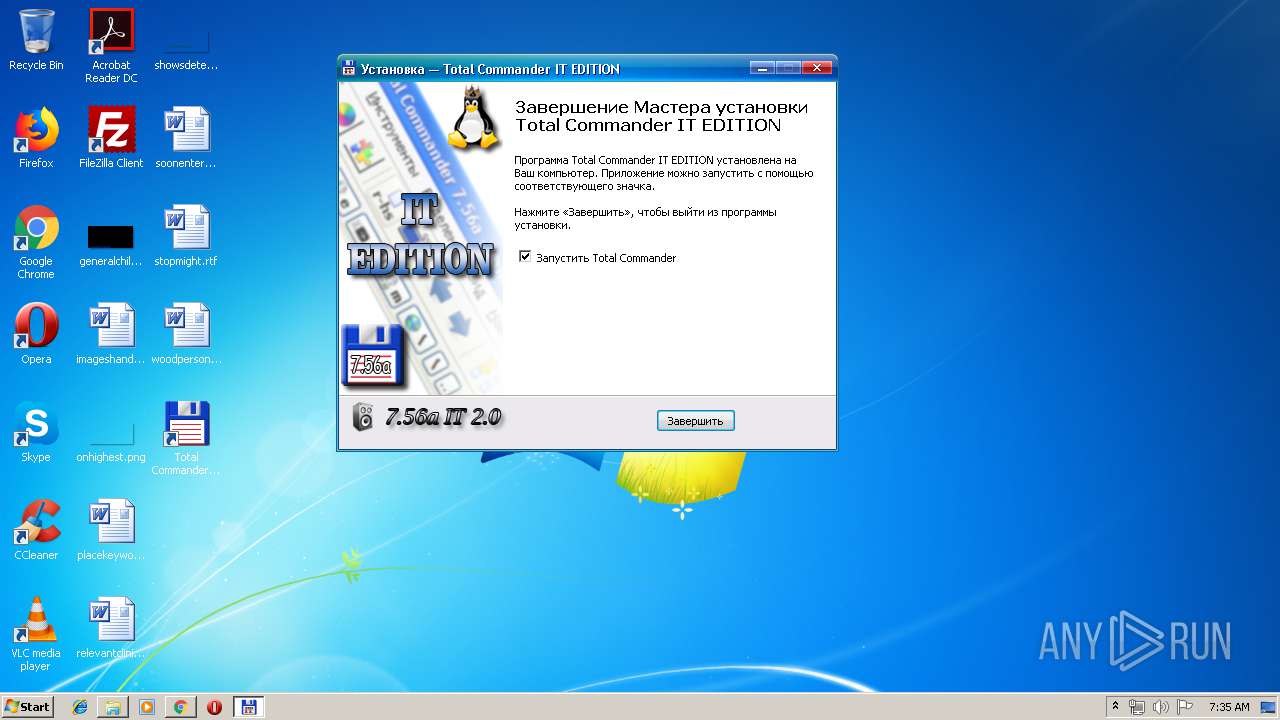
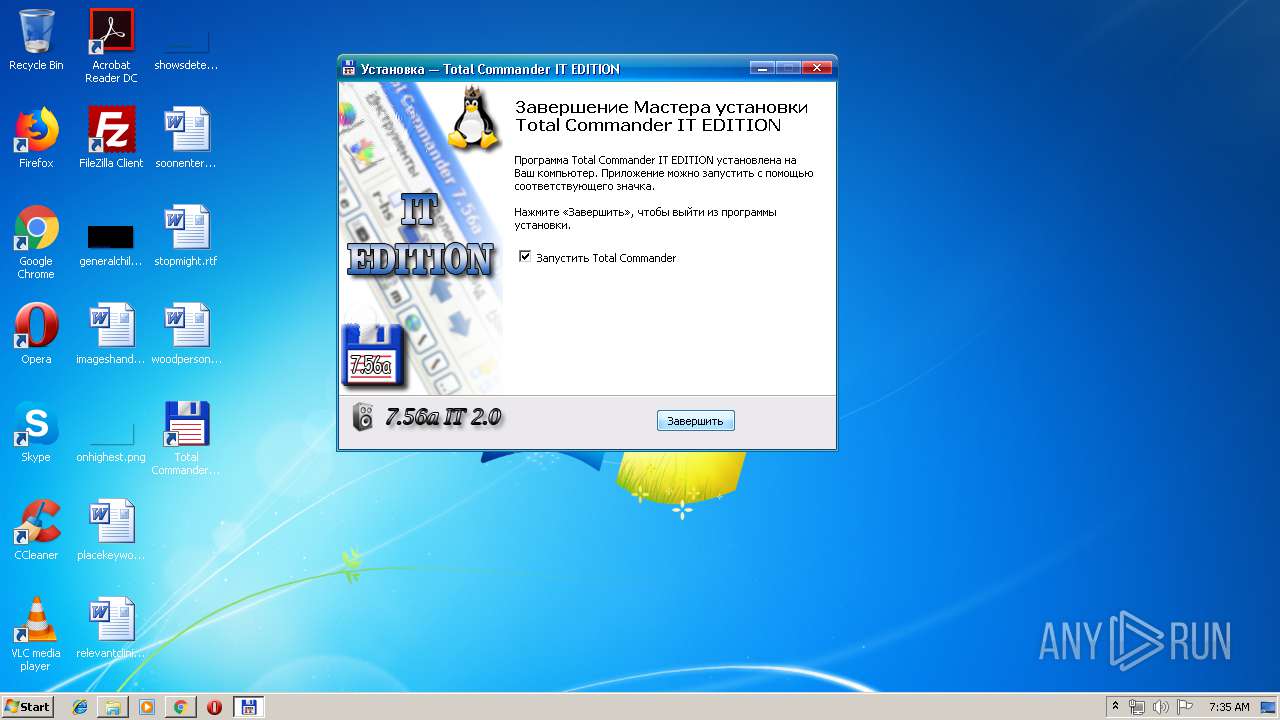
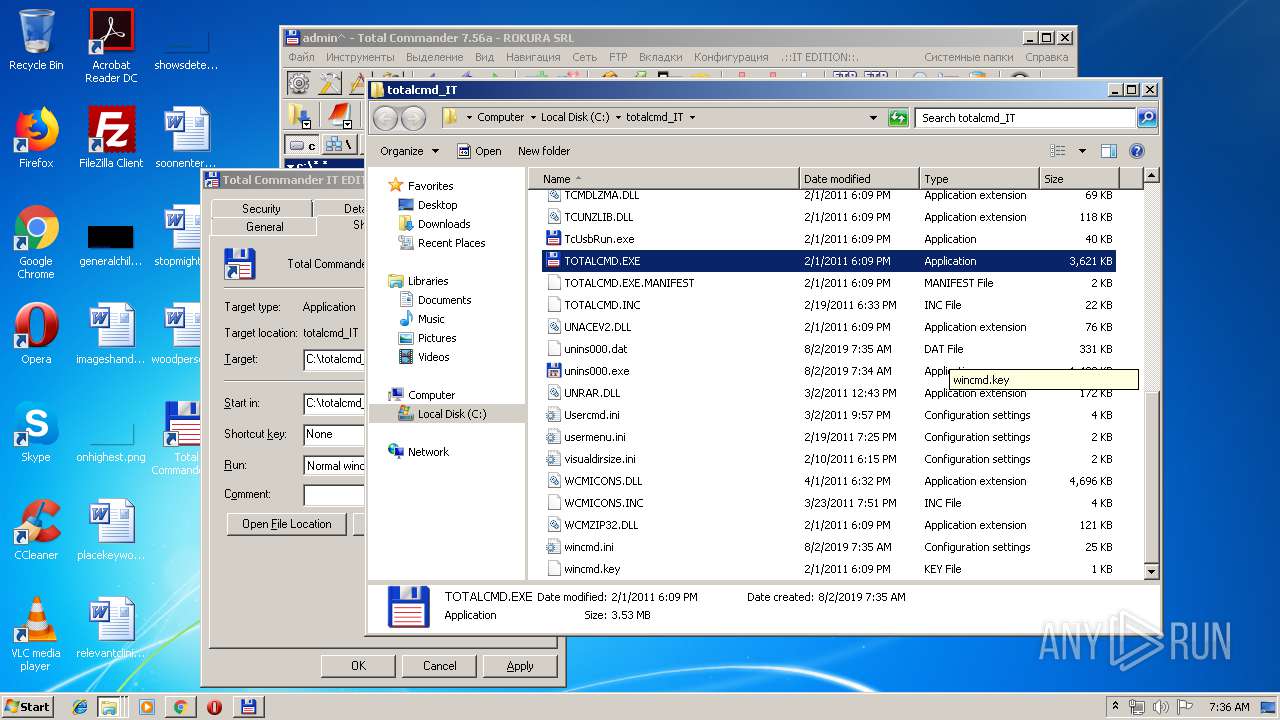
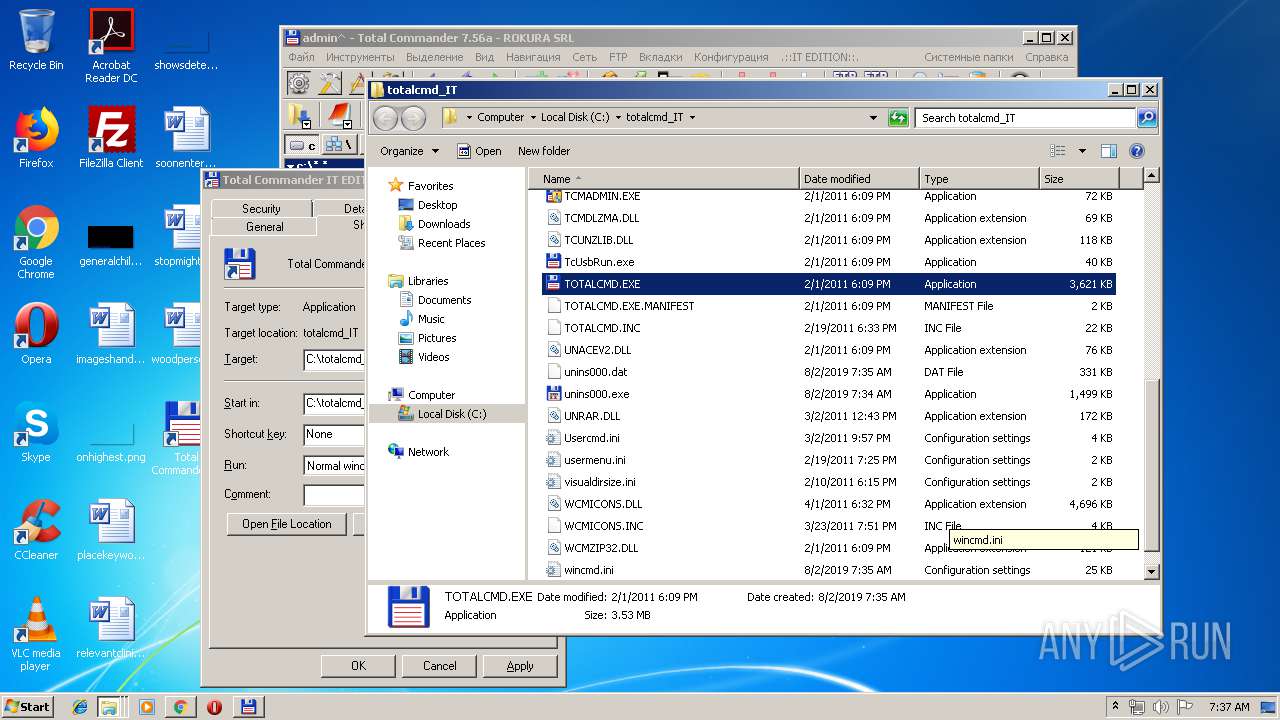
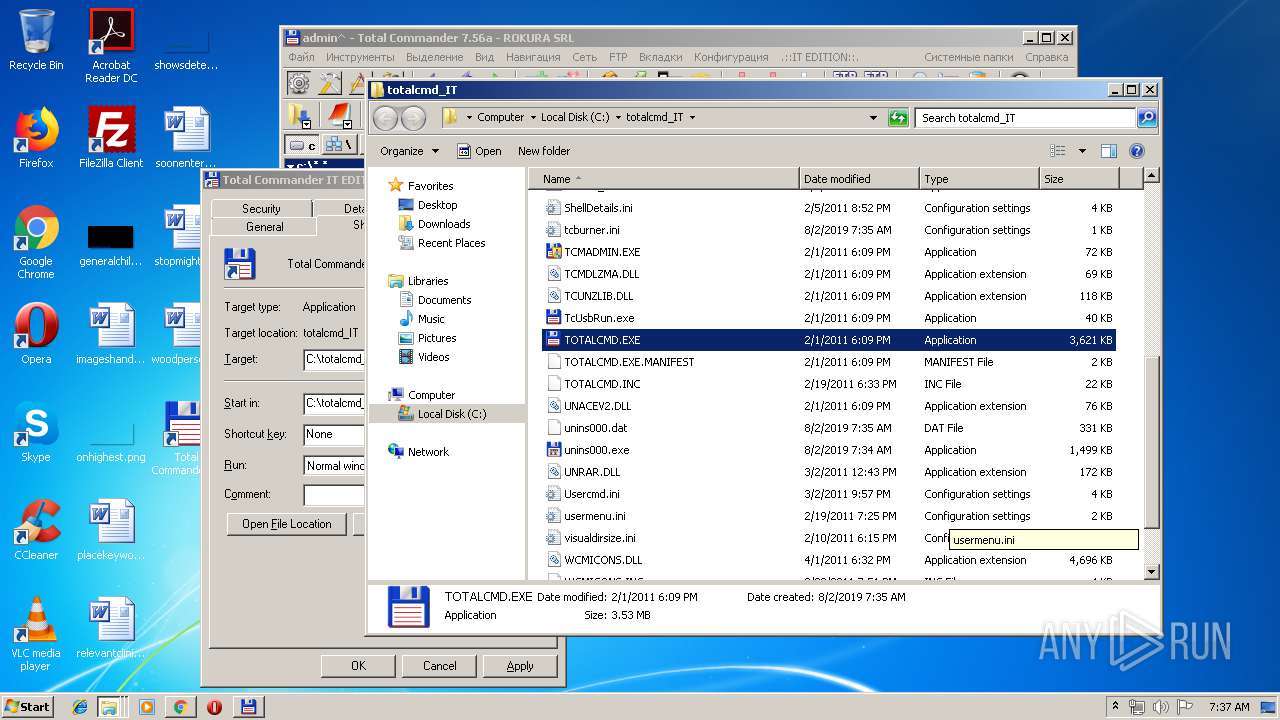
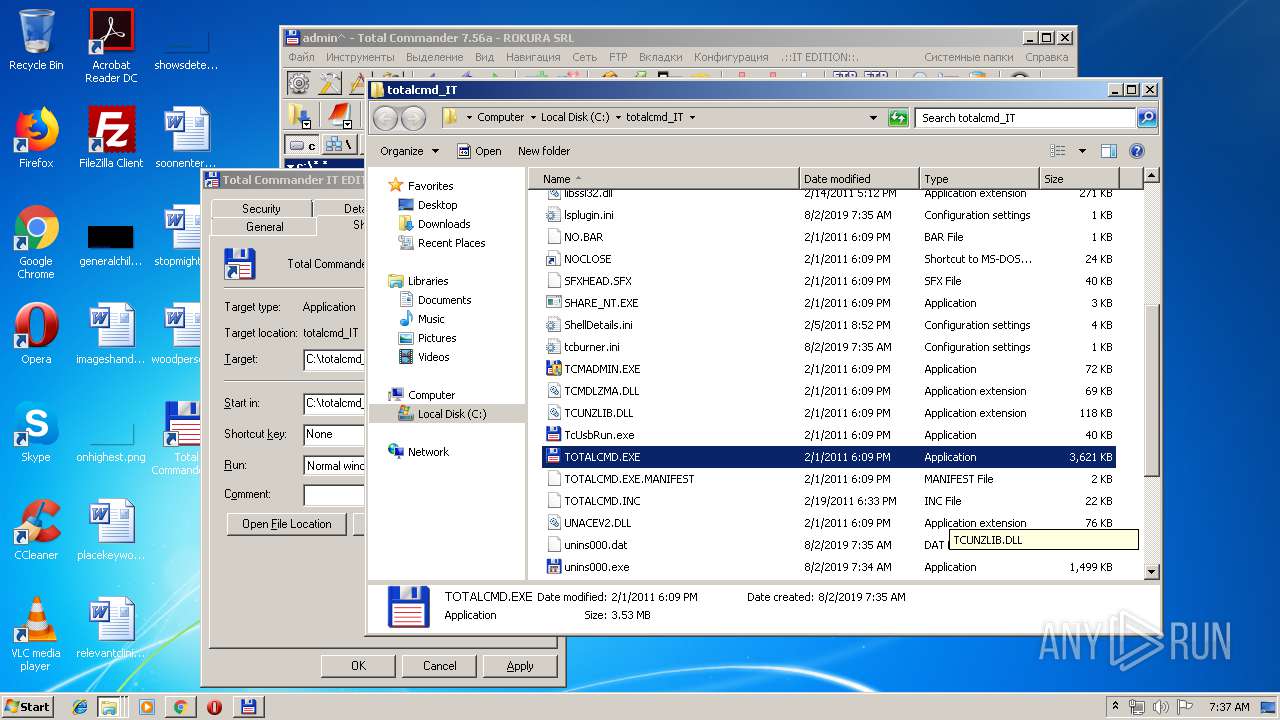
Application was dropped or rewritten from another process
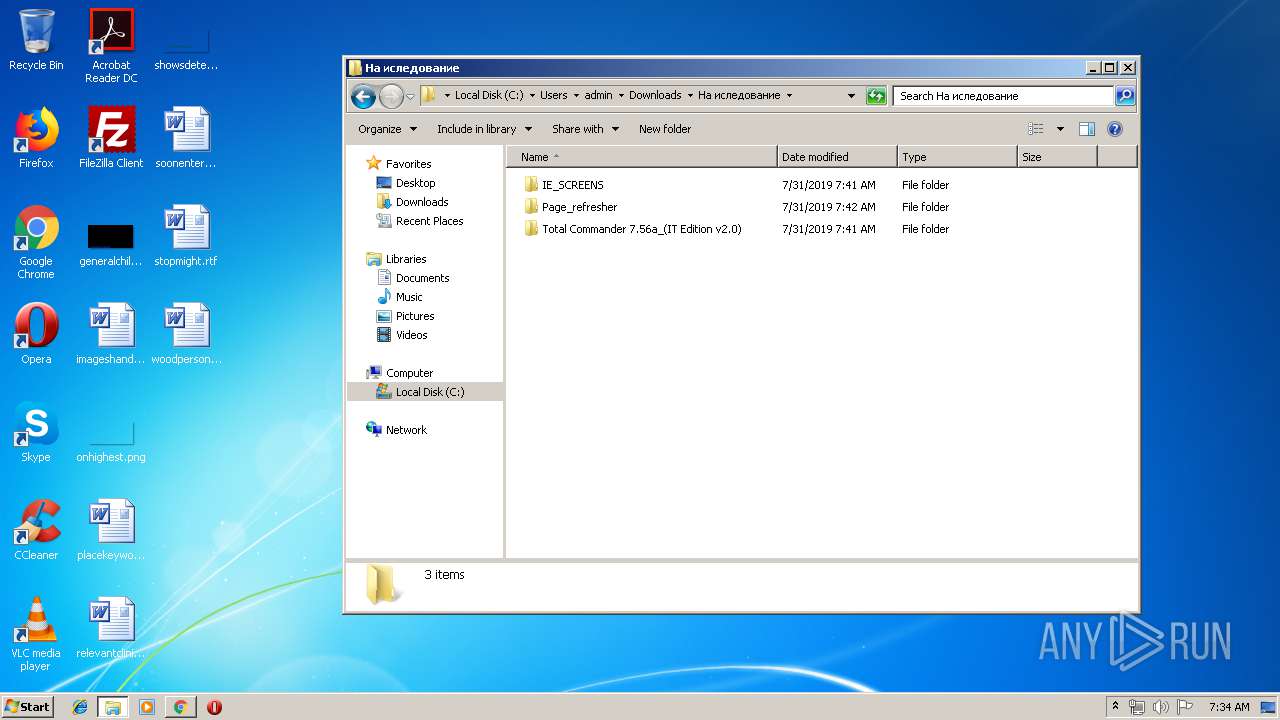
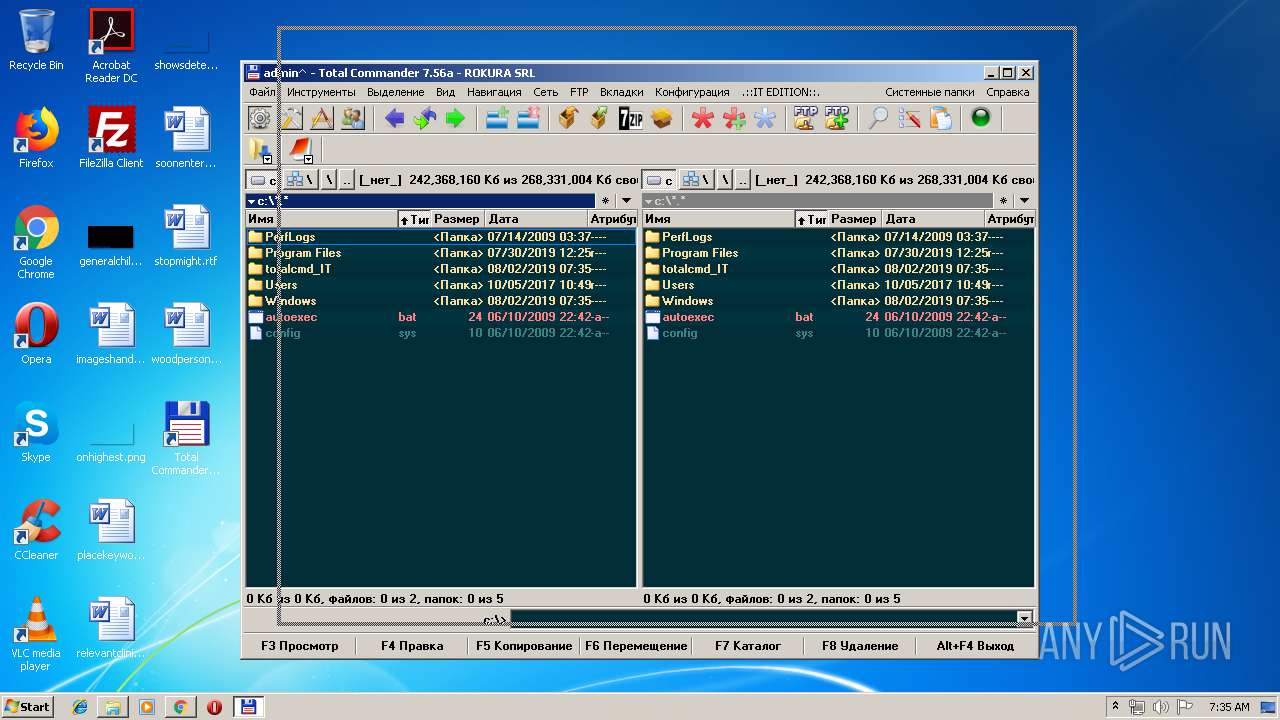
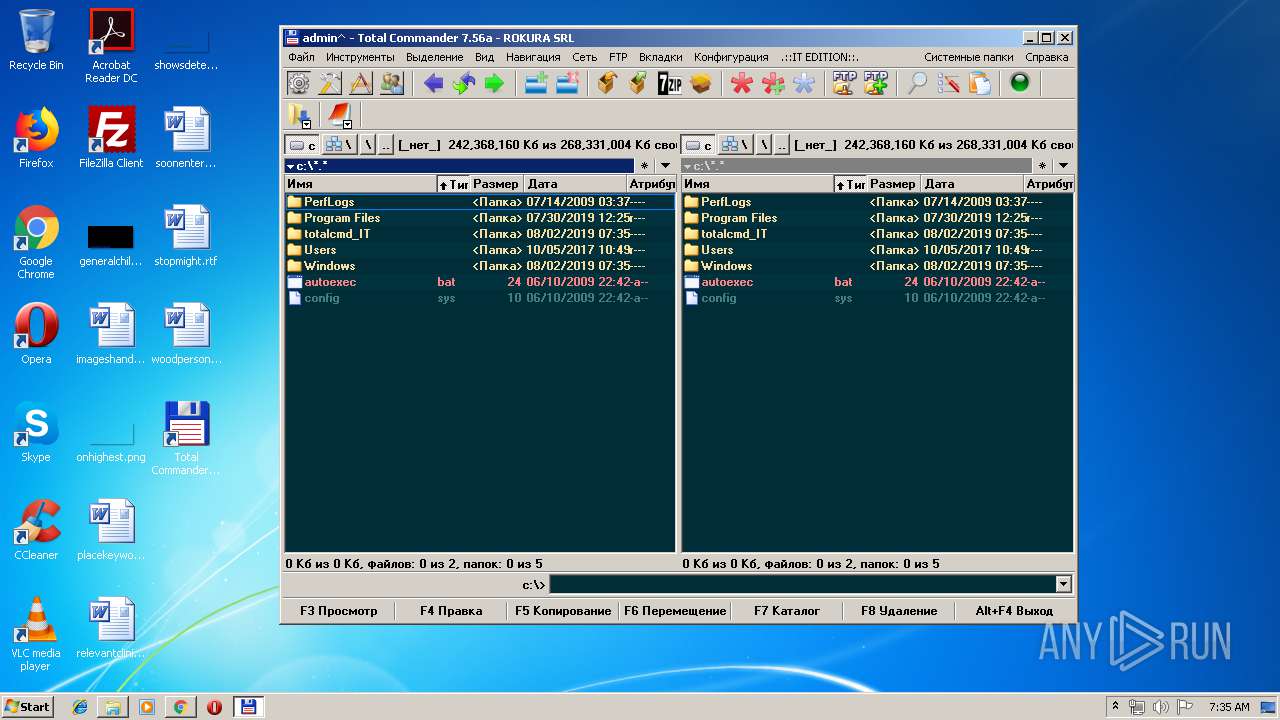
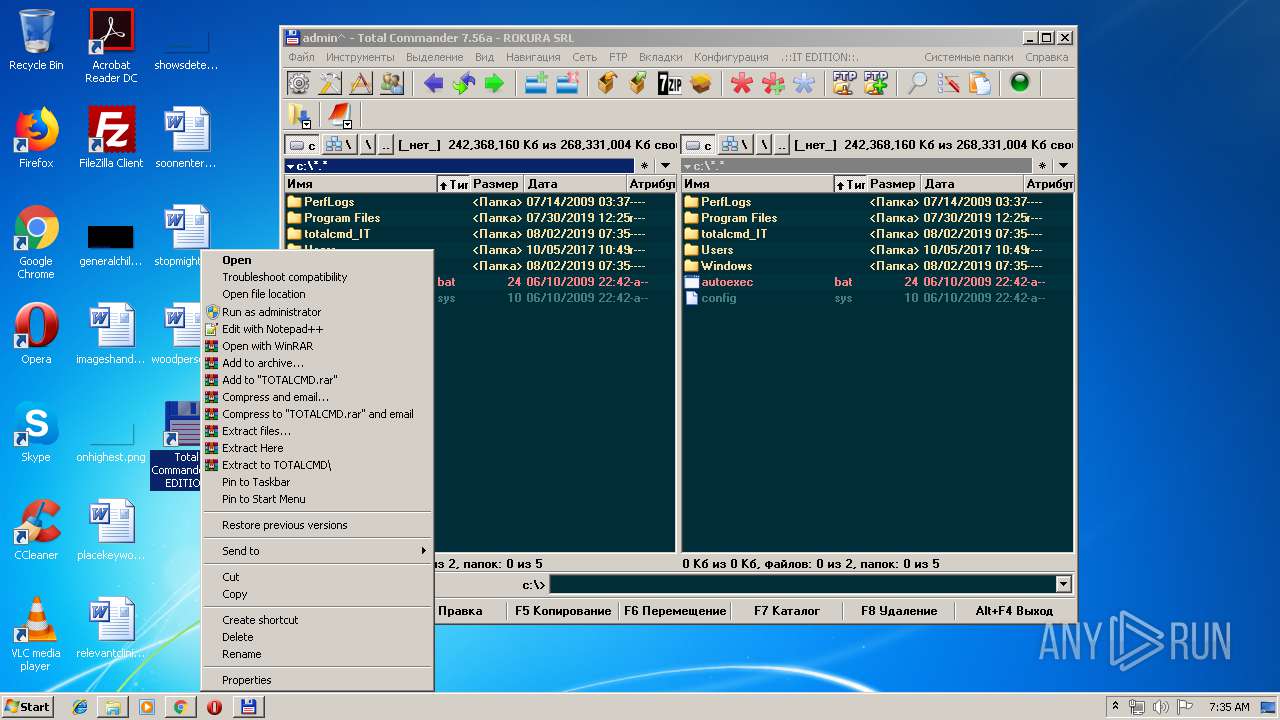
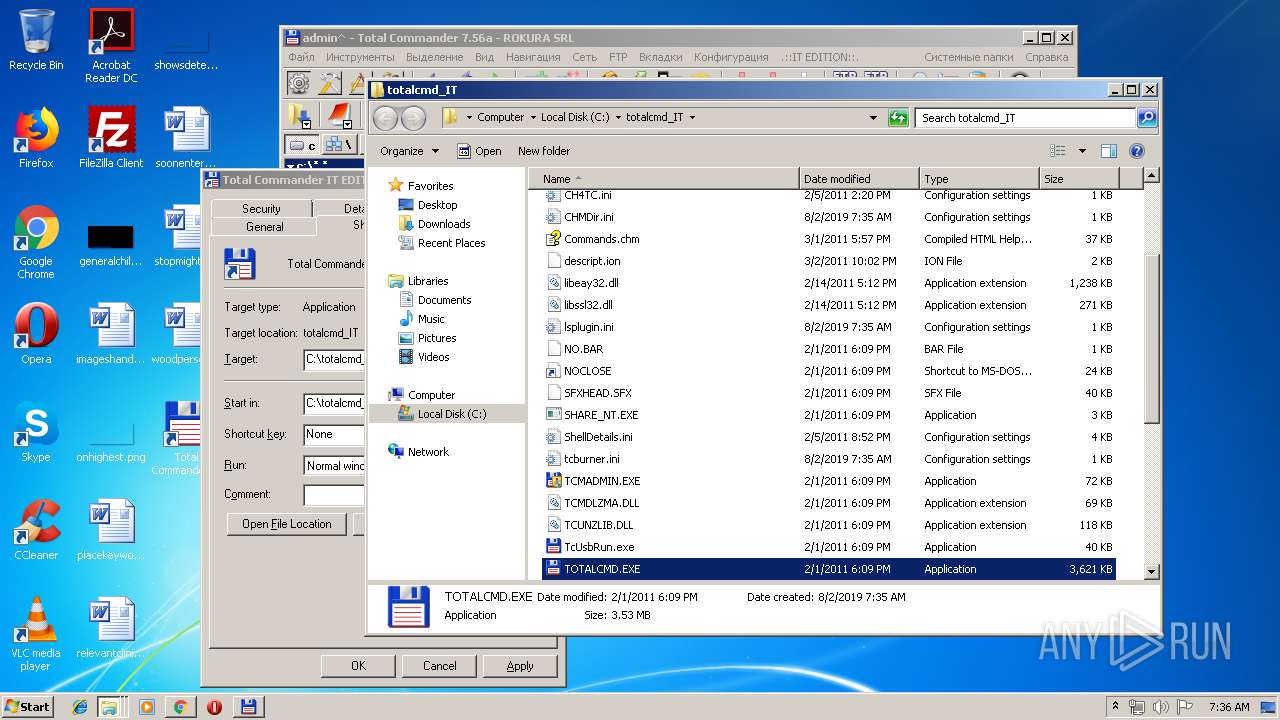
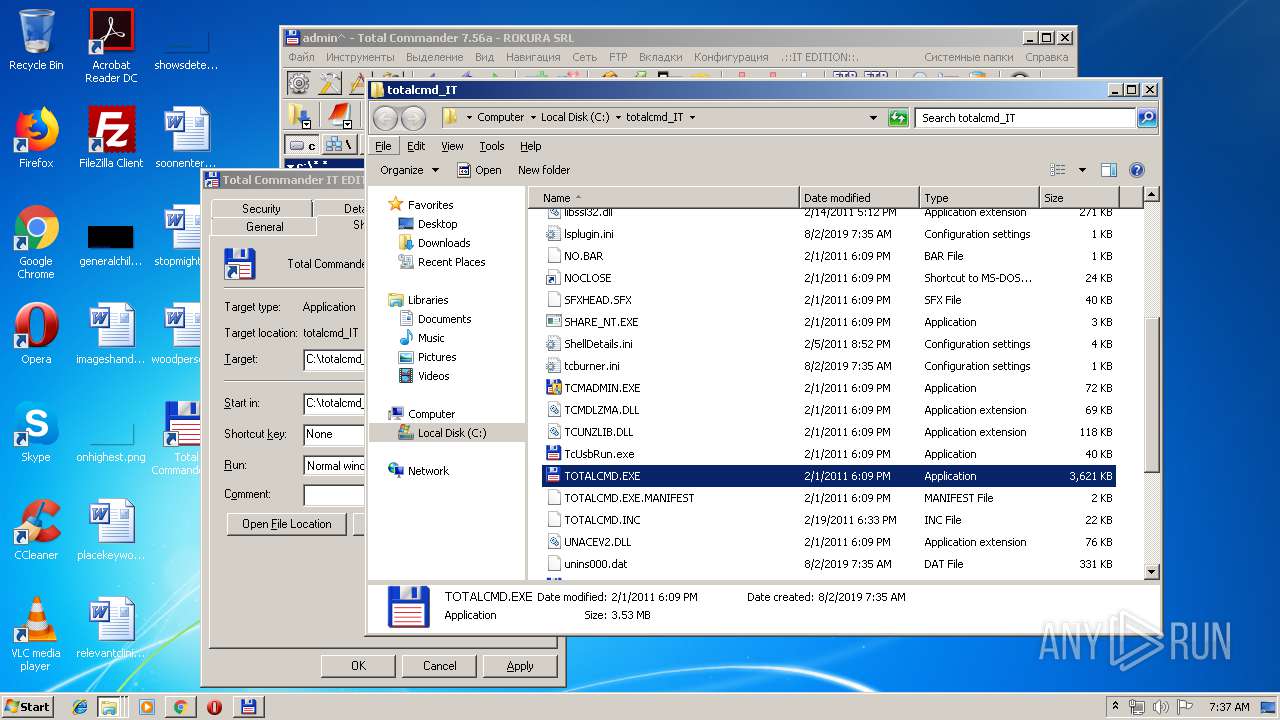
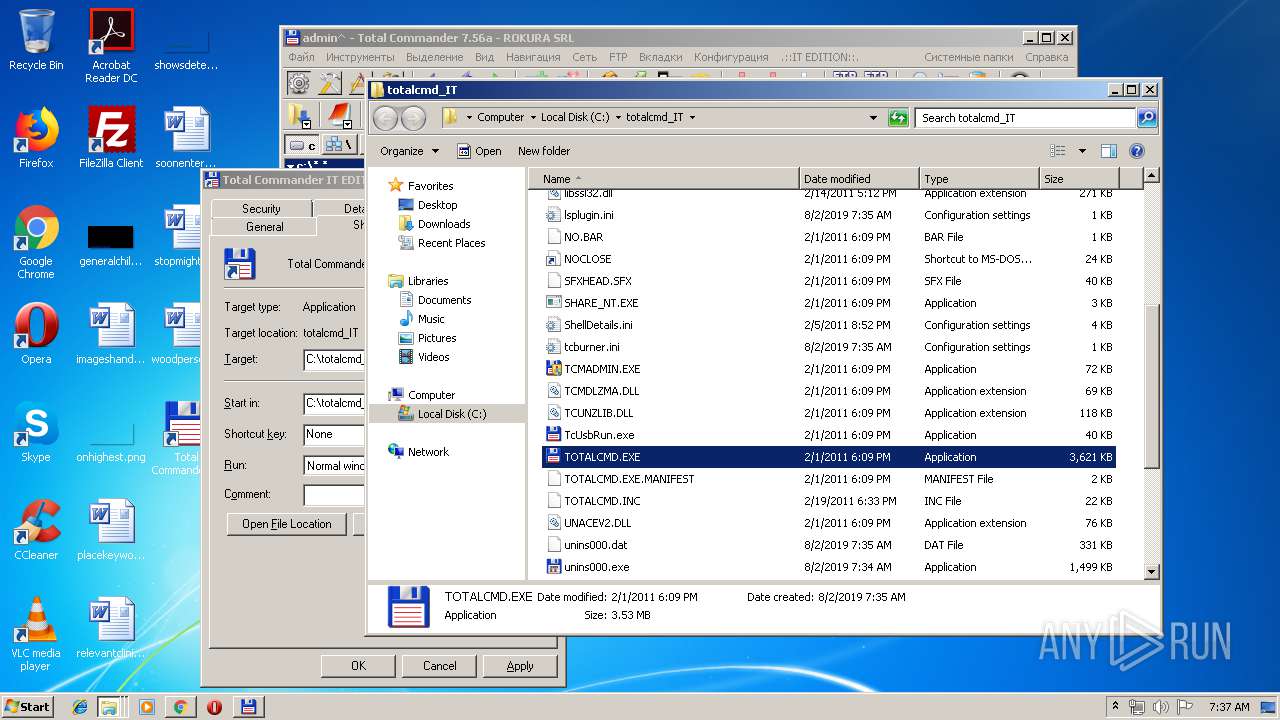
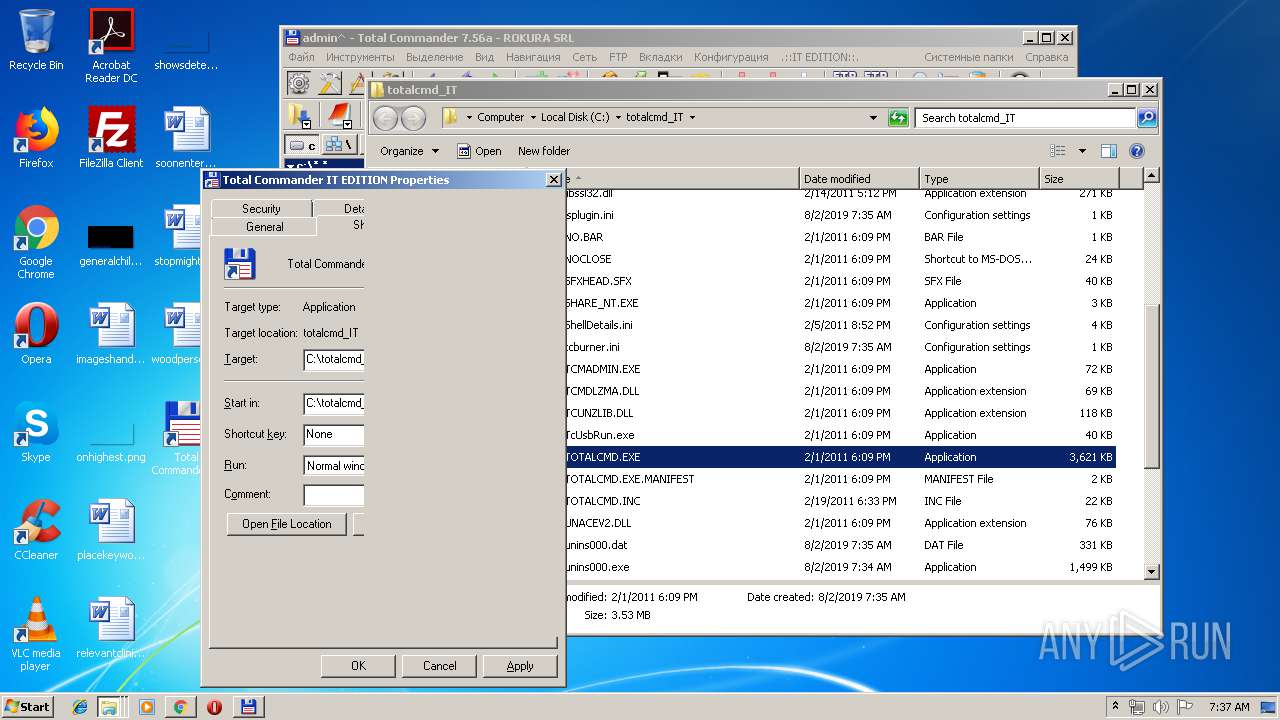
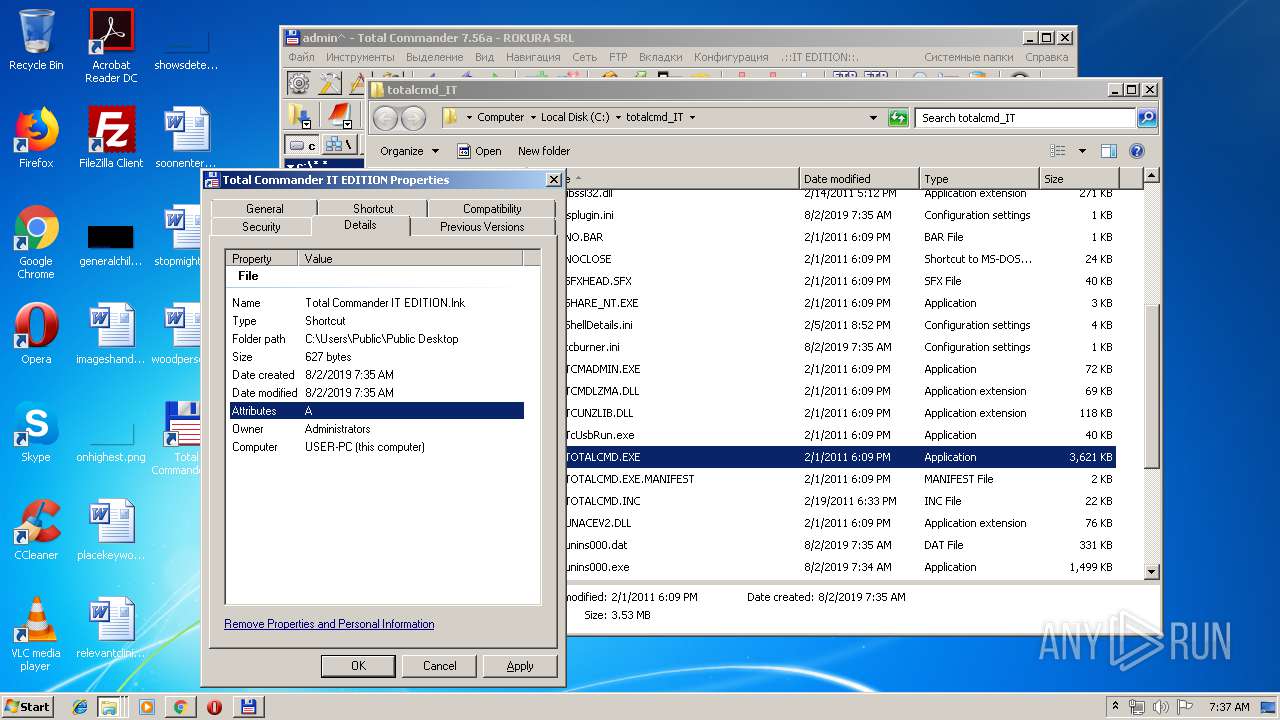
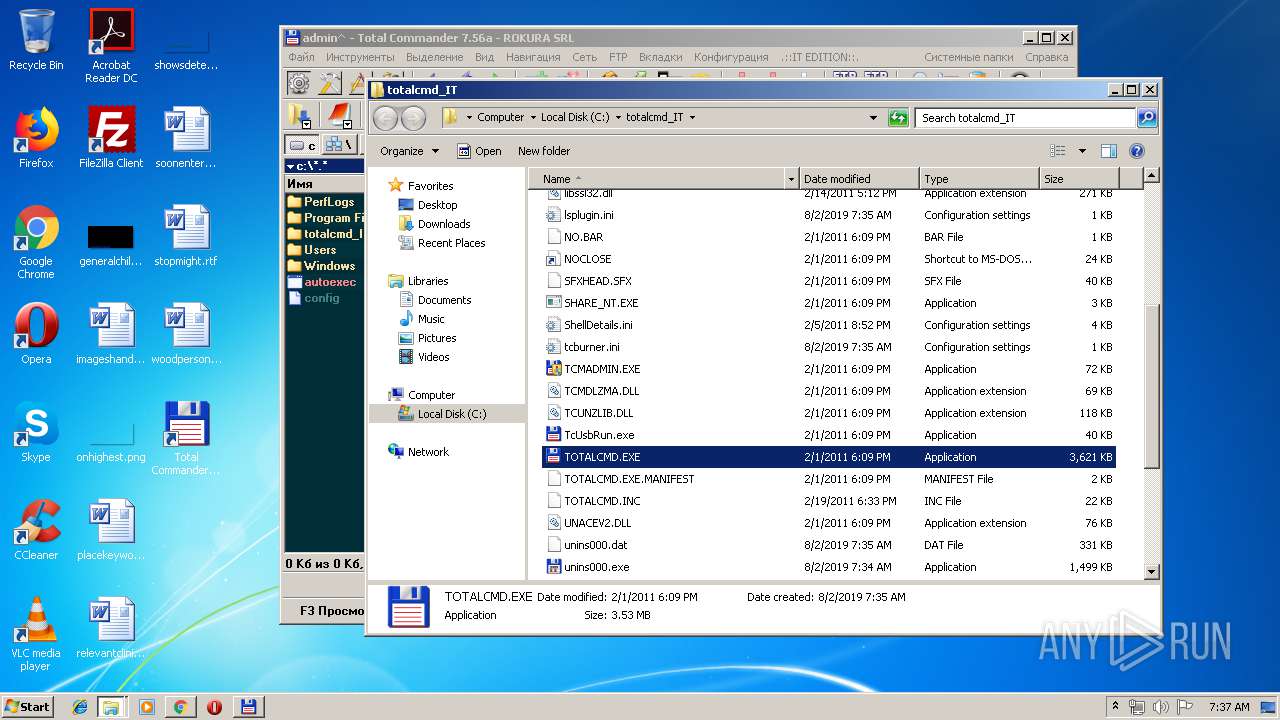
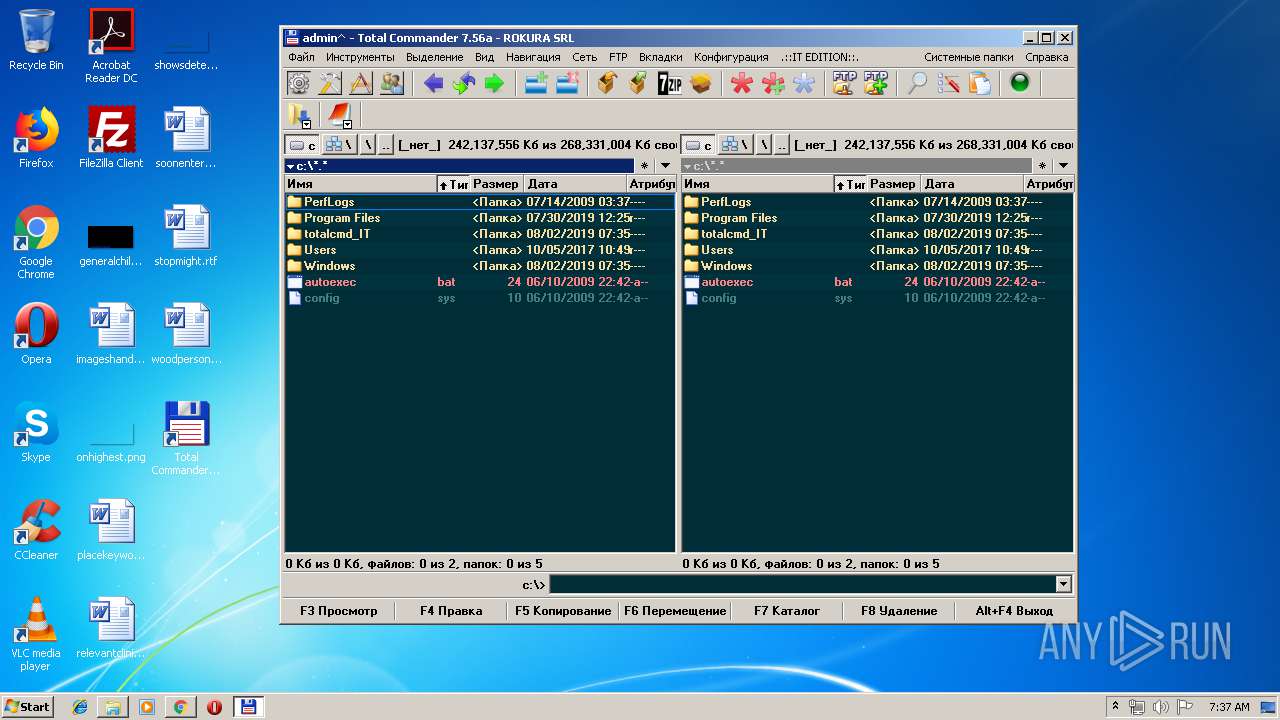
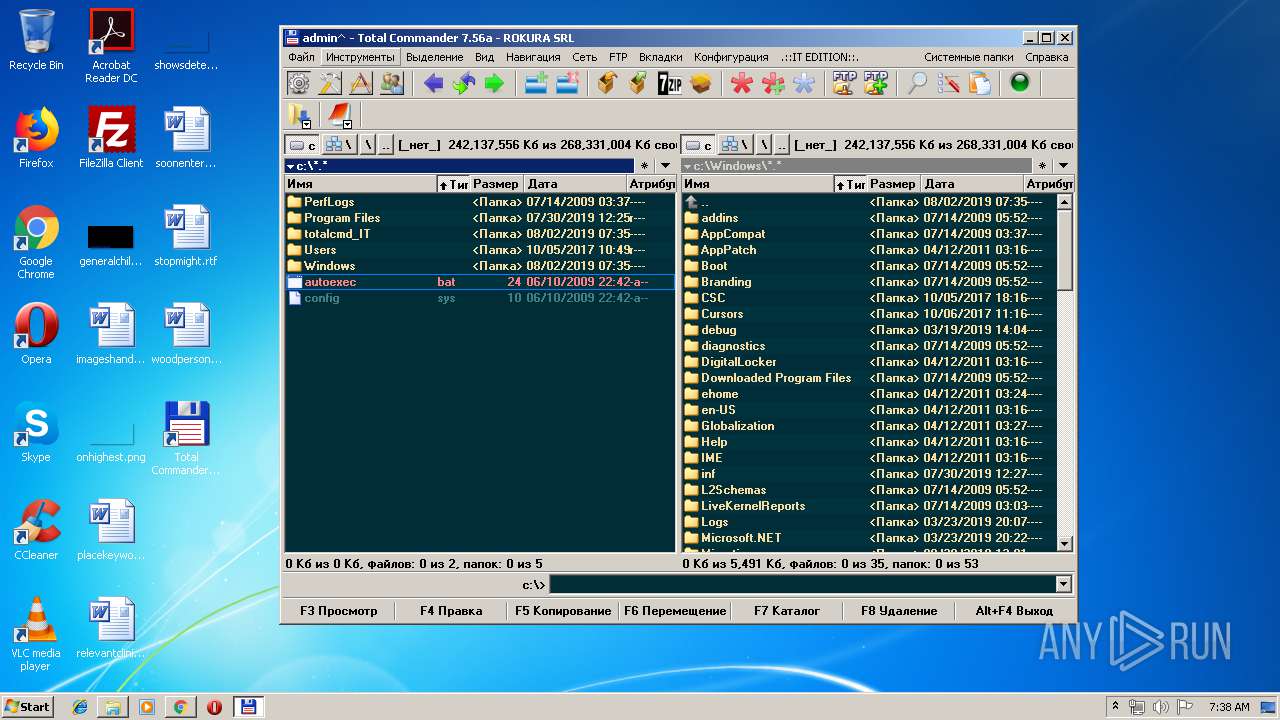
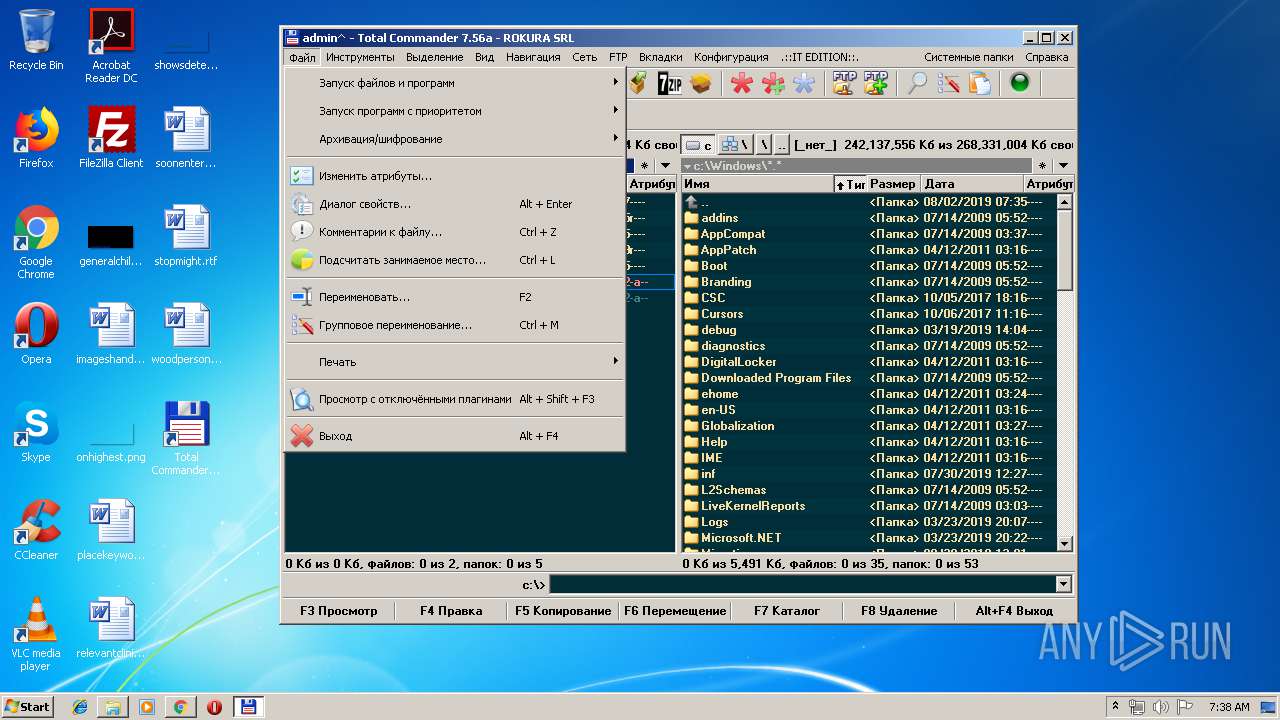
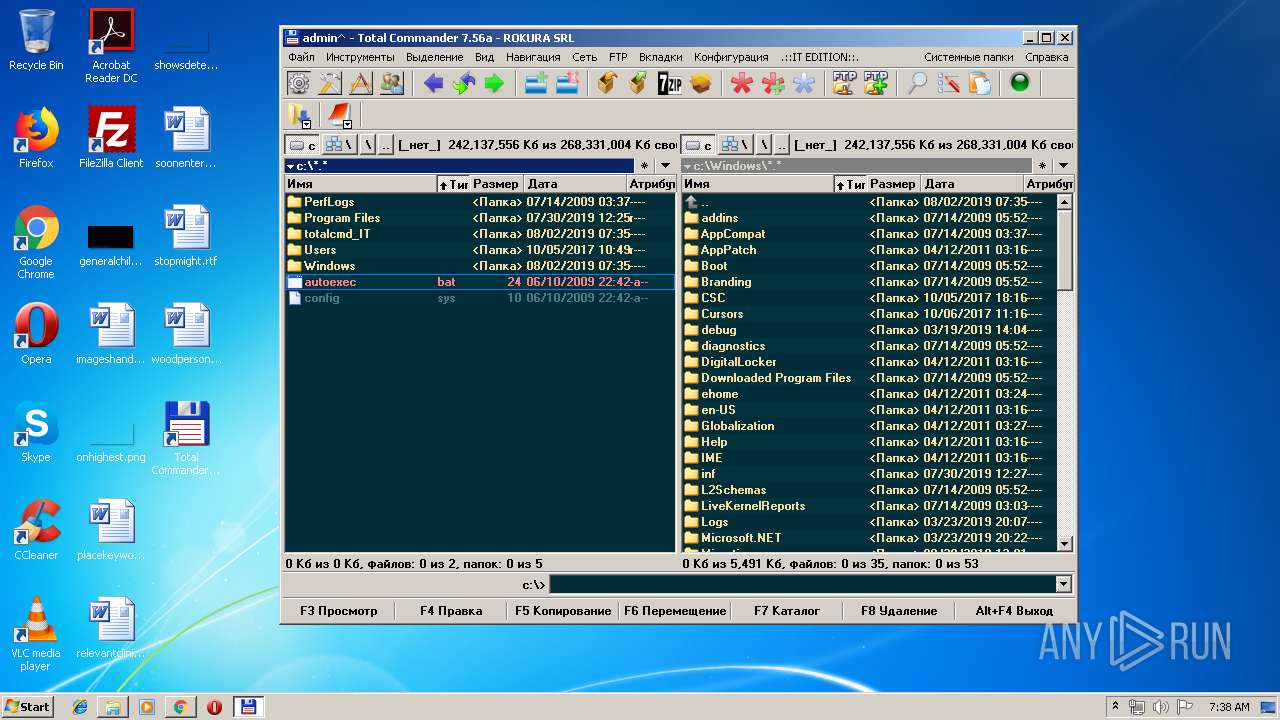
- totalcmd.exe (PID: 4028)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3568)
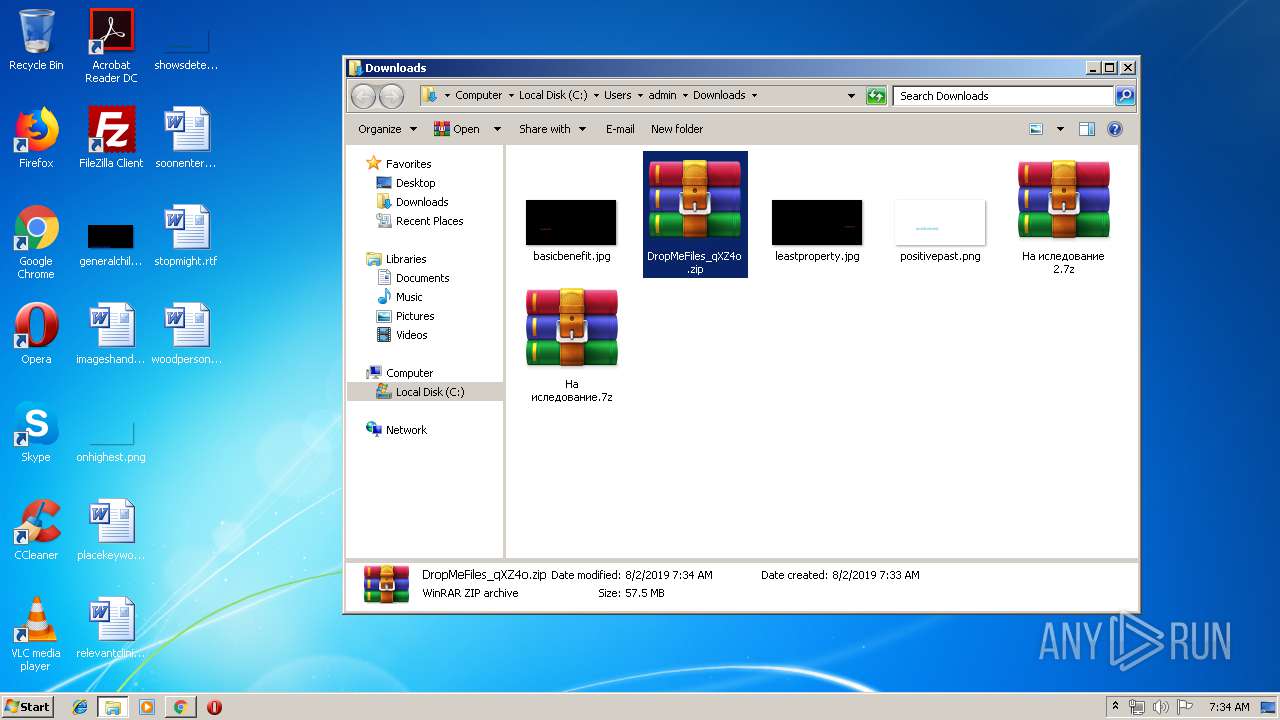
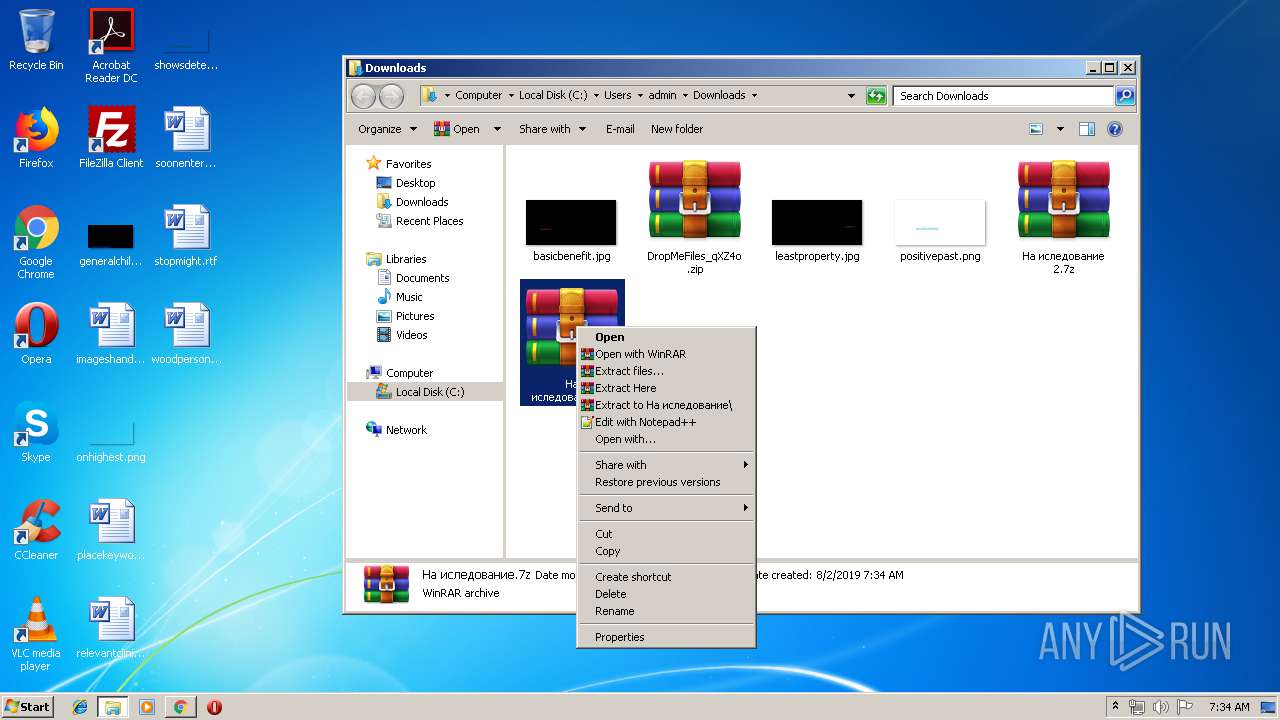
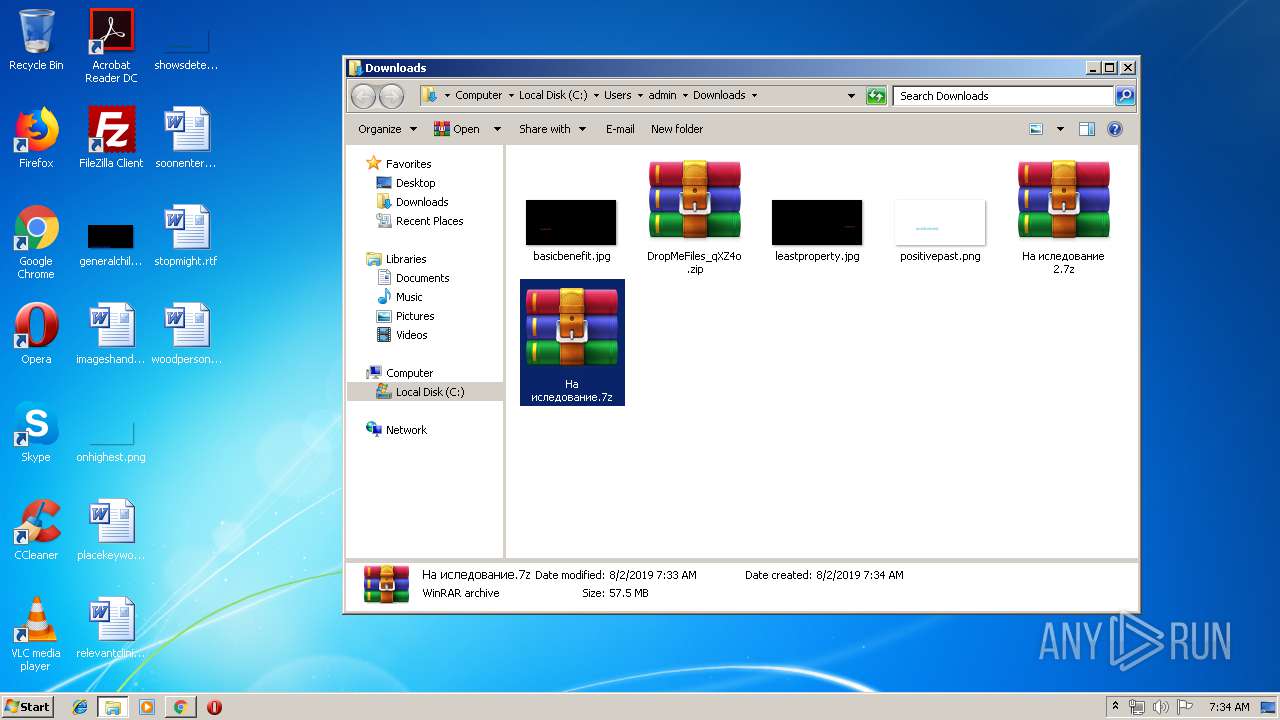
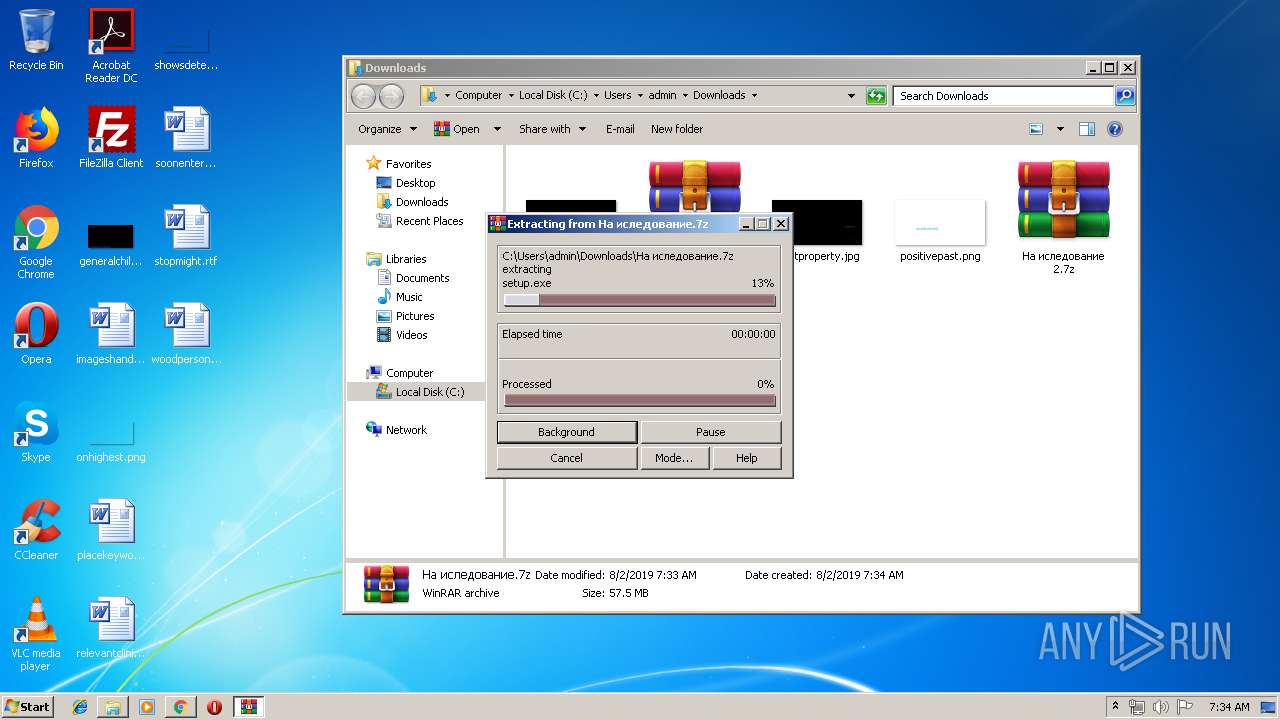
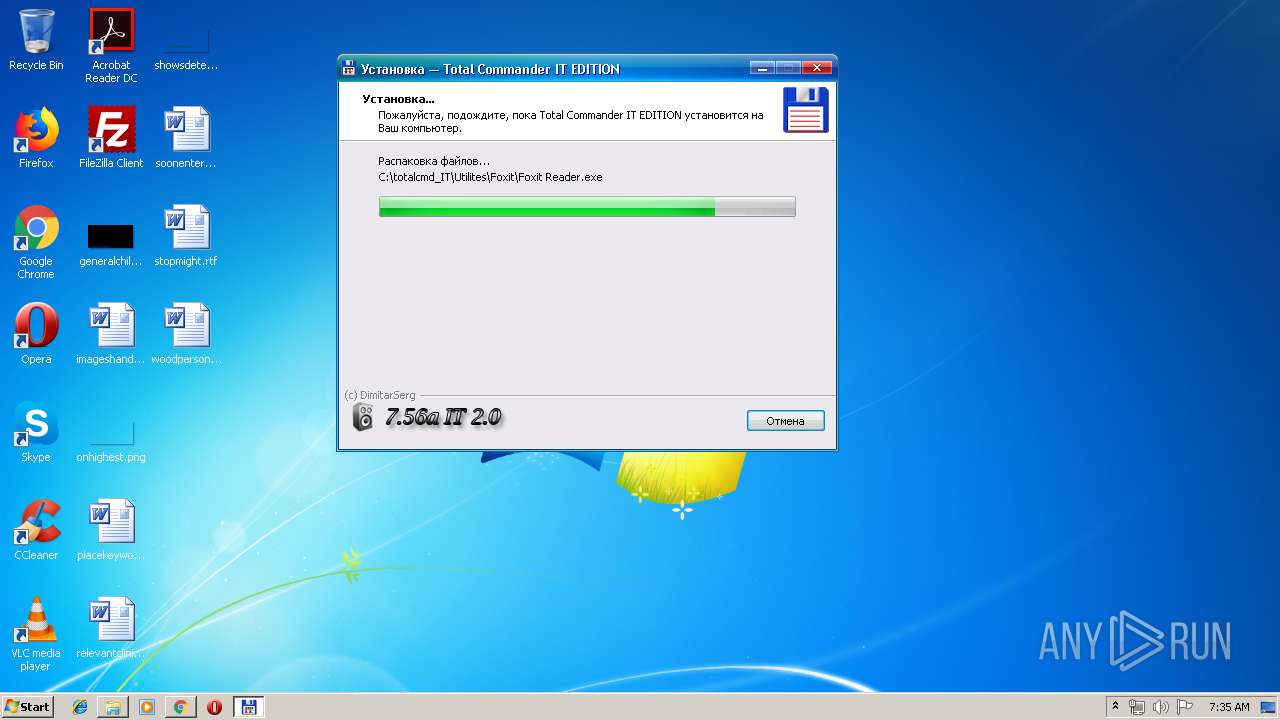
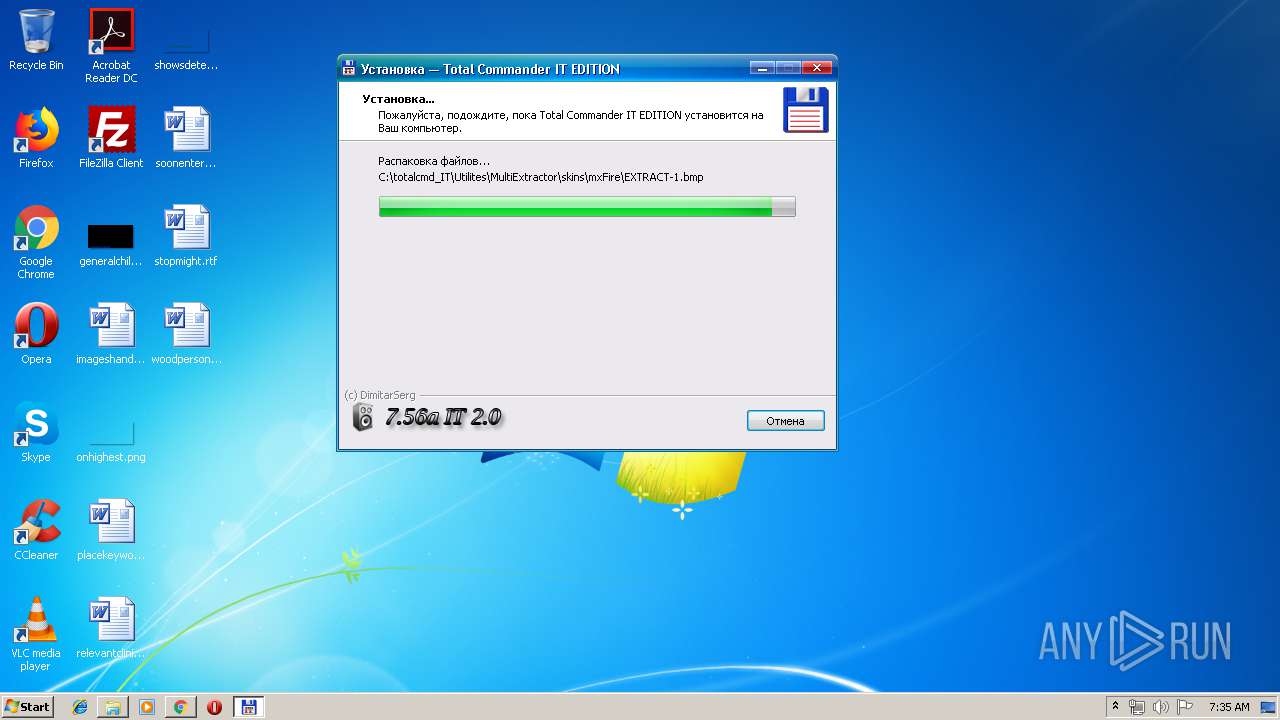
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2940)
- setup.exe (PID: 2264)
- setup.tmp (PID: 2844)
Reads the Windows organization settings
- setup.tmp (PID: 2844)
Reads Windows owner or organization settings
- setup.tmp (PID: 2844)
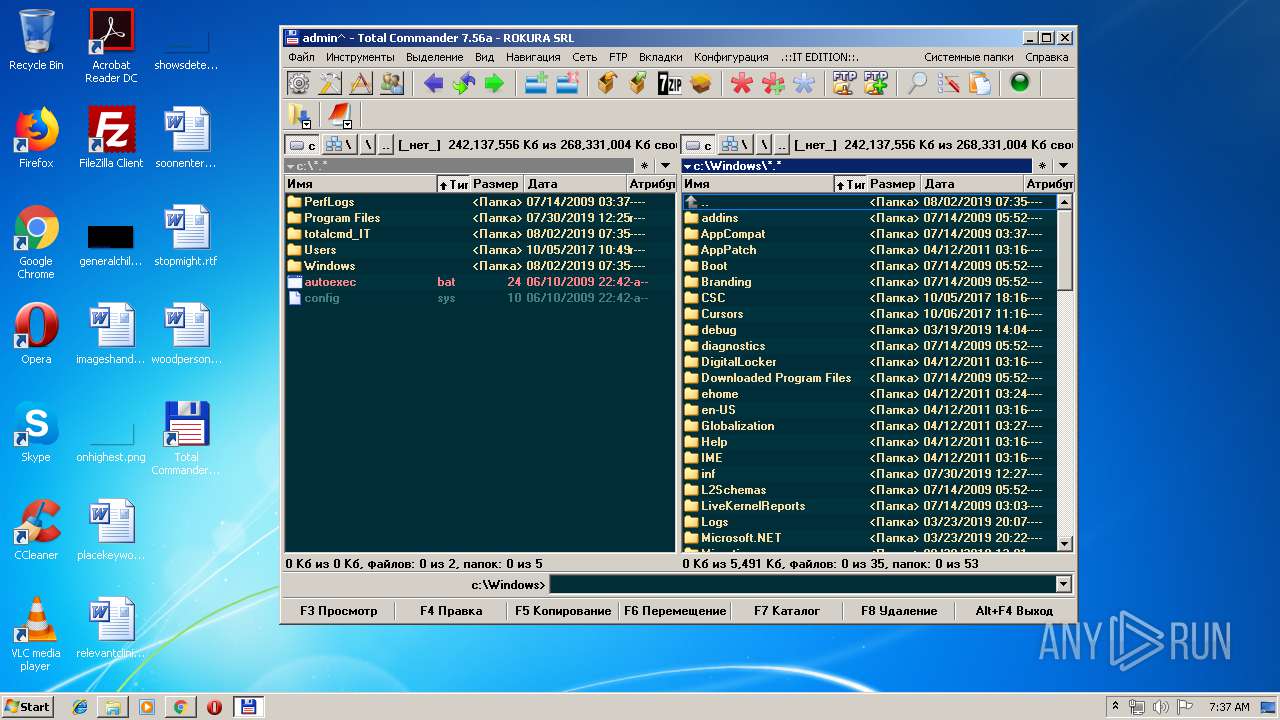
Creates files in the Windows directory
- setup.tmp (PID: 2844)
Creates files in the user directory
- setup.tmp (PID: 2844)
Starts CMD.EXE for commands execution
- totalcmd.exe (PID: 4028)
INFO
Application launched itself
- chrome.exe (PID: 3568)
Reads Internet Cache Settings
- chrome.exe (PID: 3568)
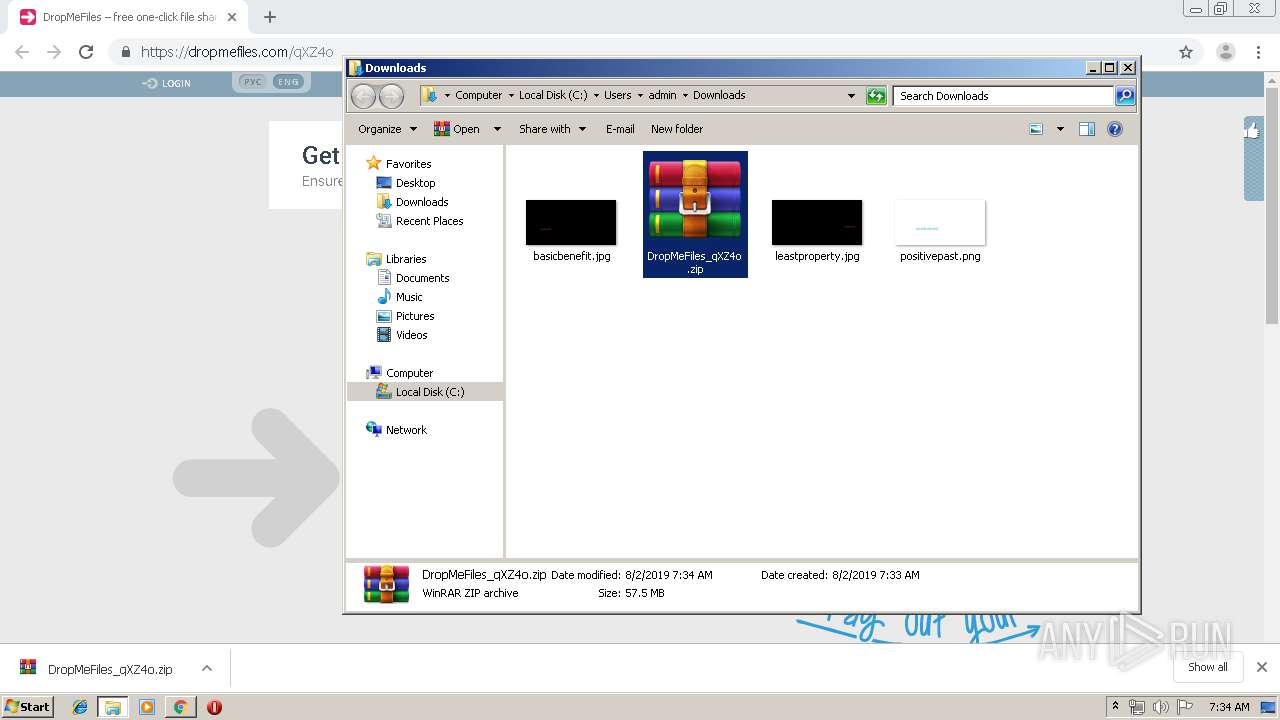
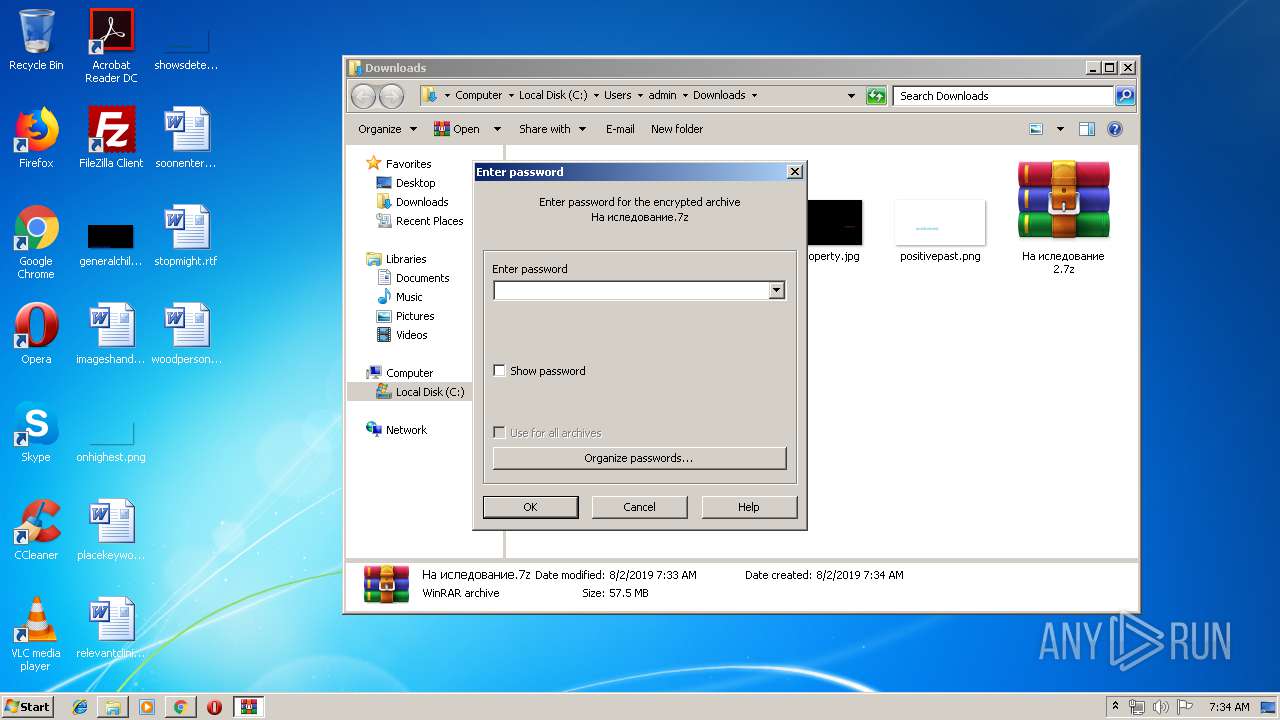
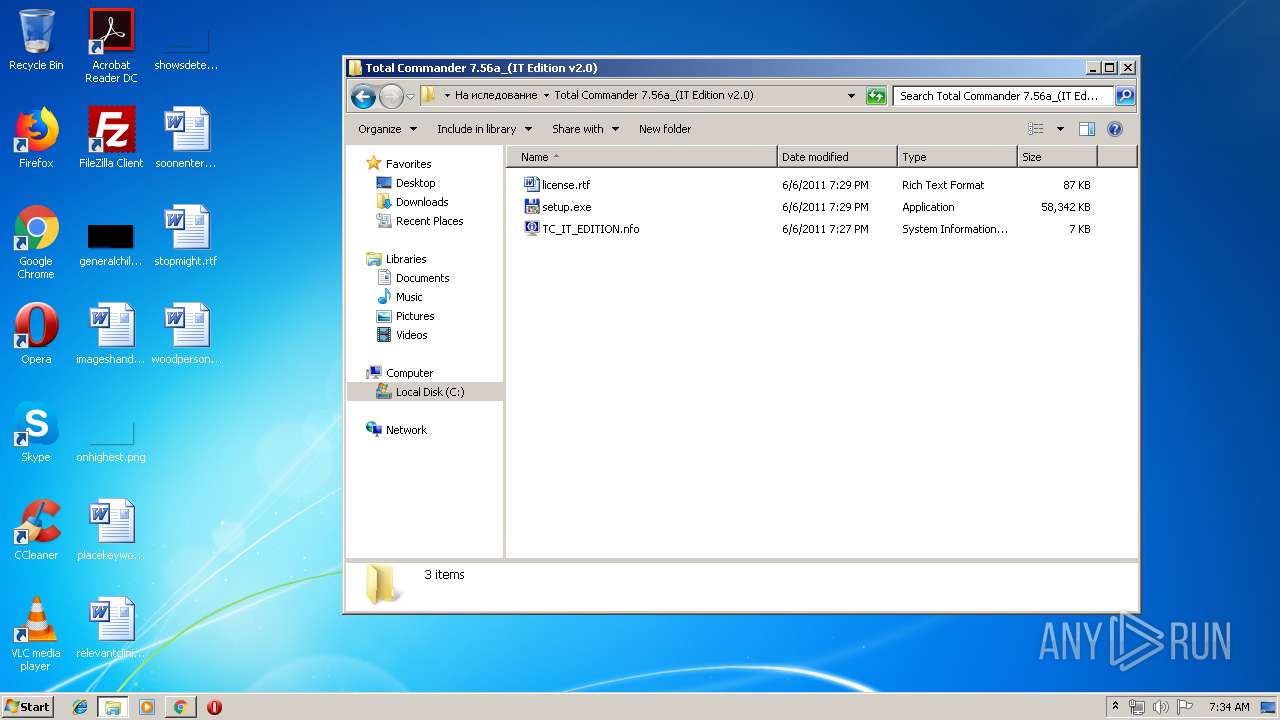
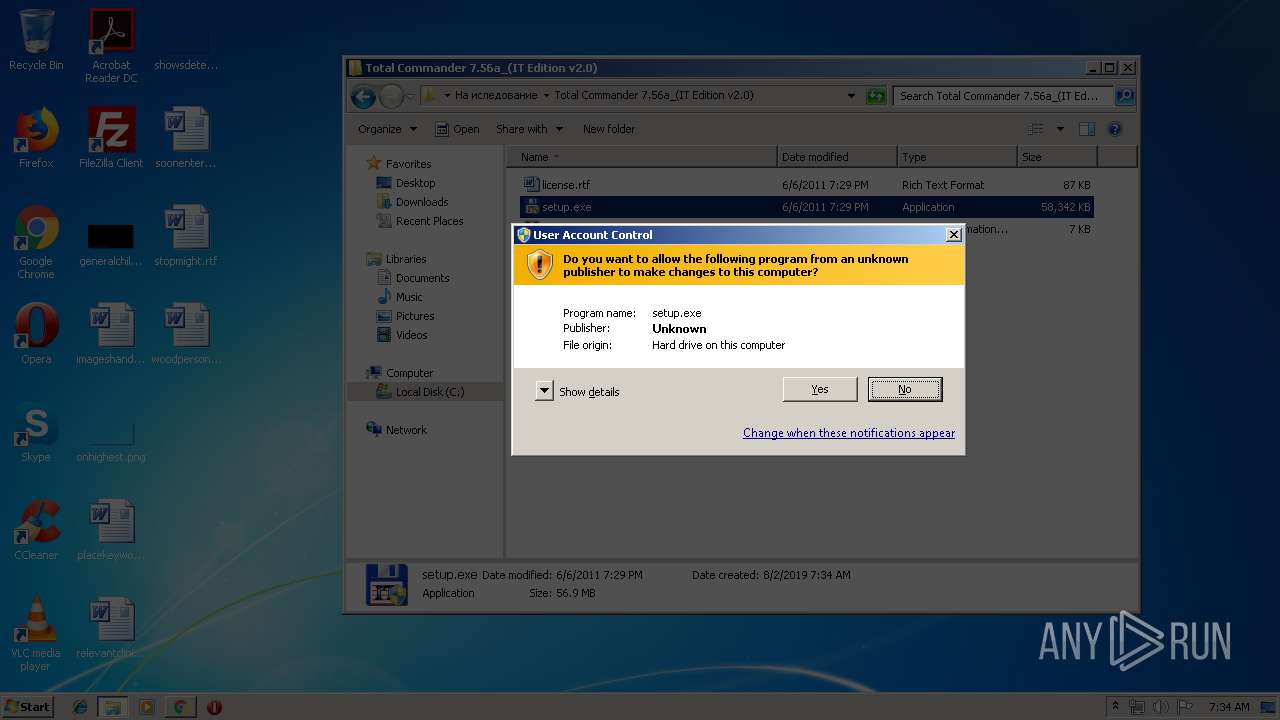
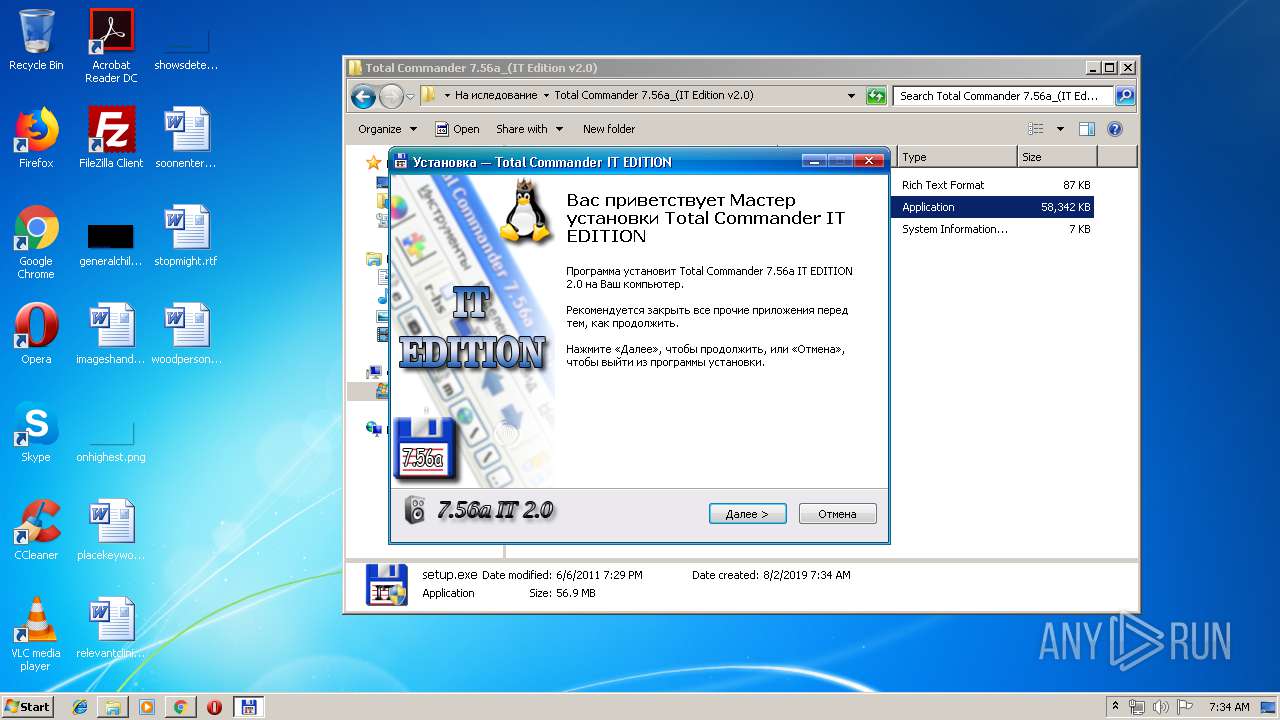
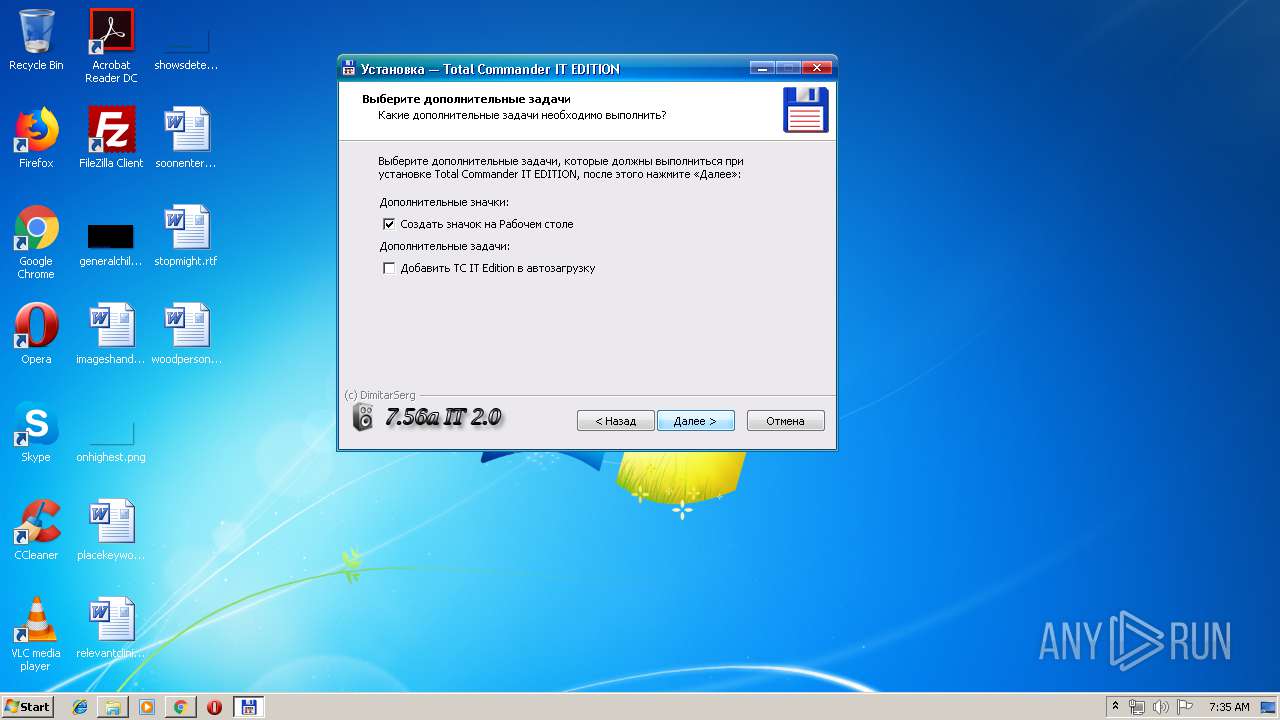
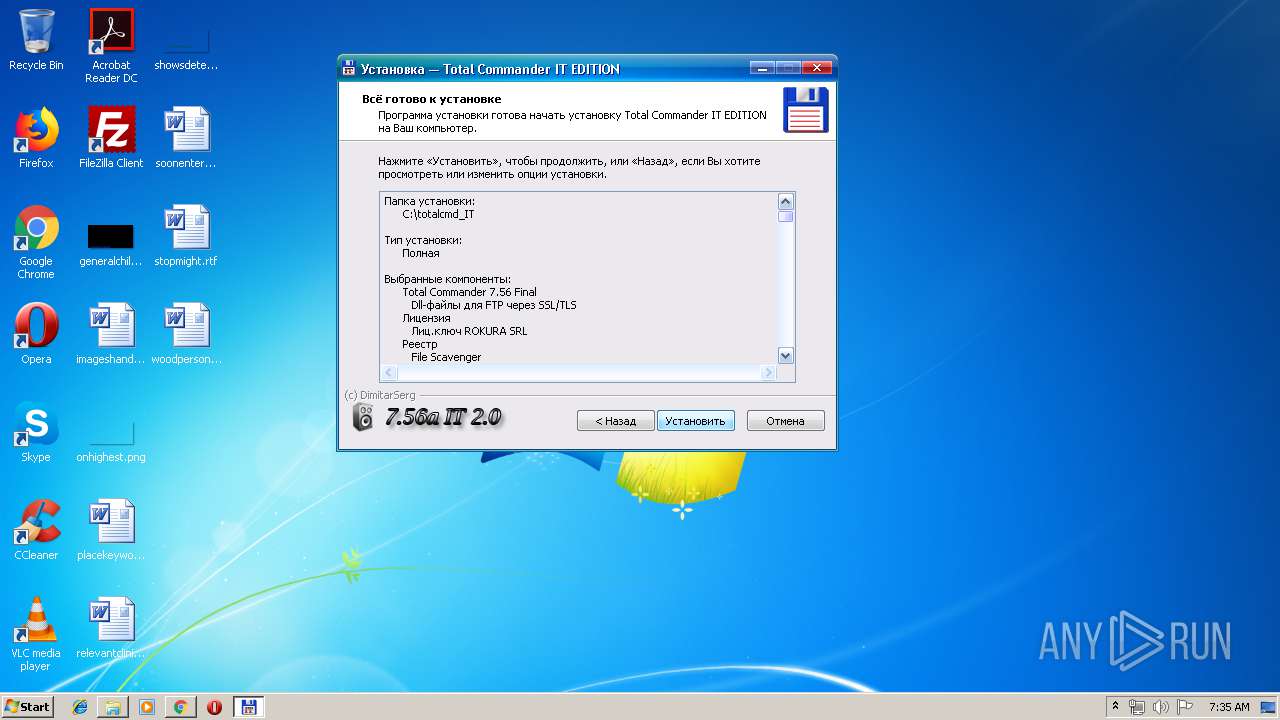
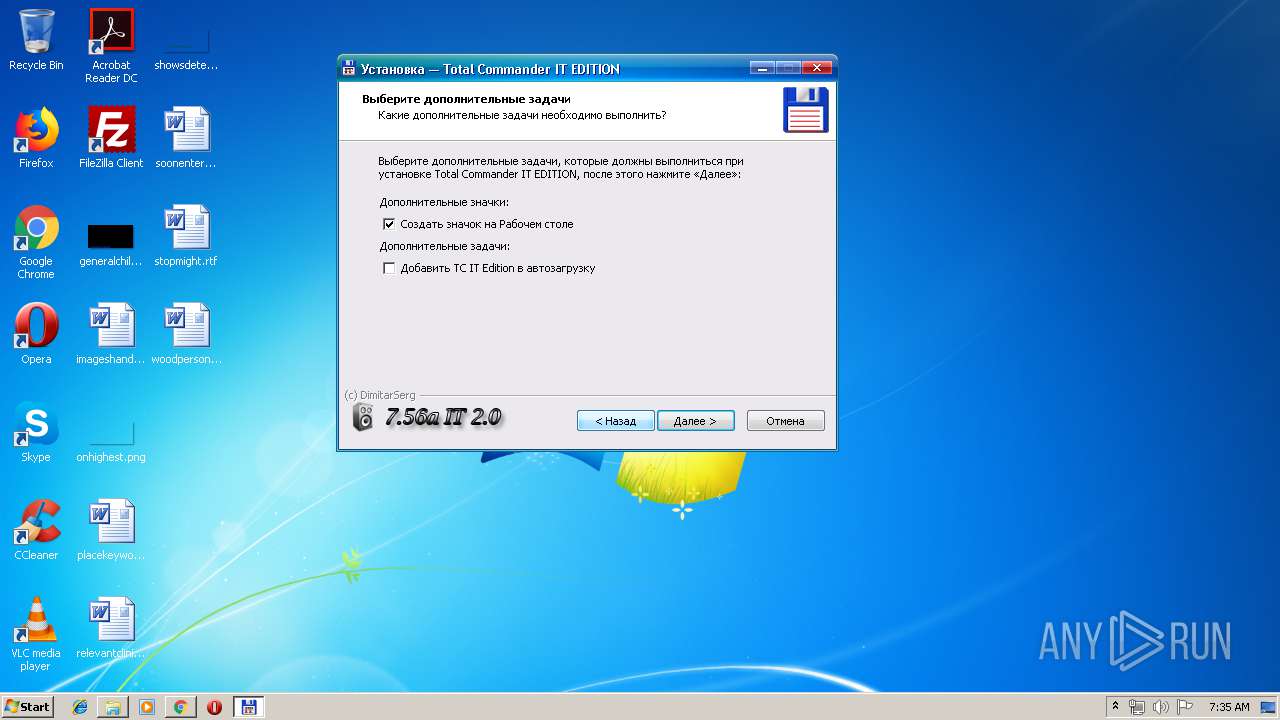
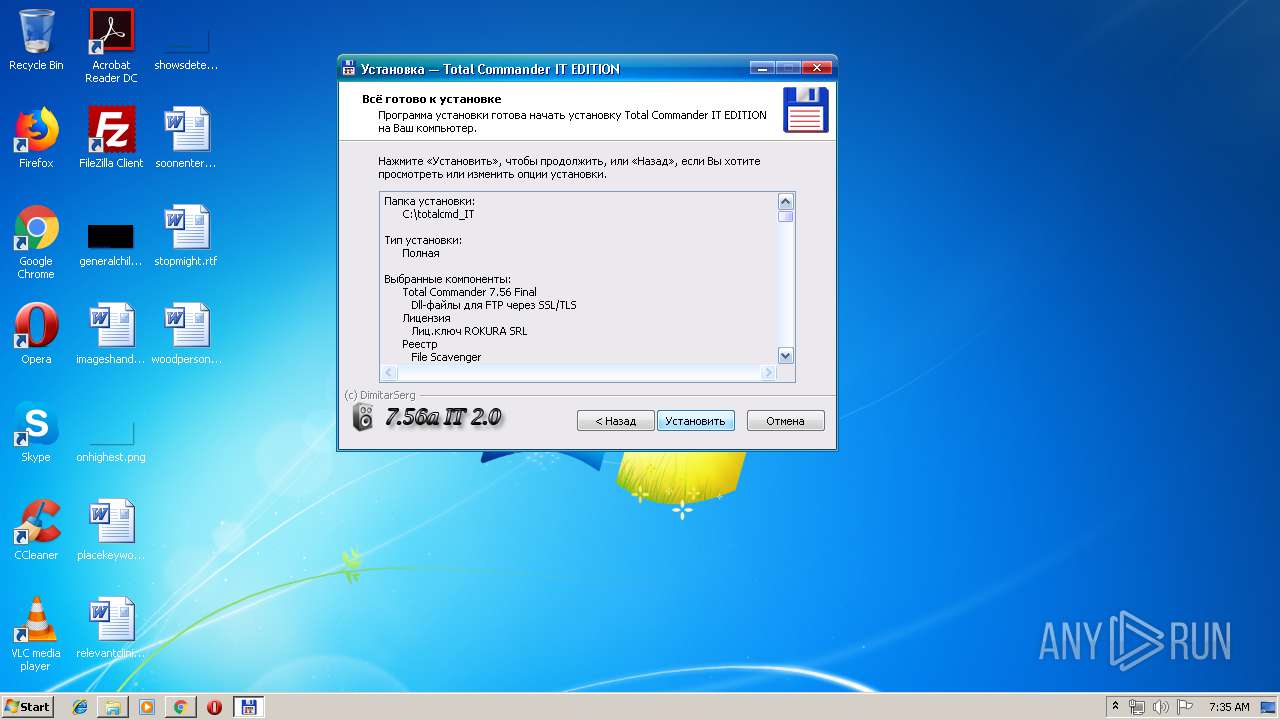
Manual execution by user
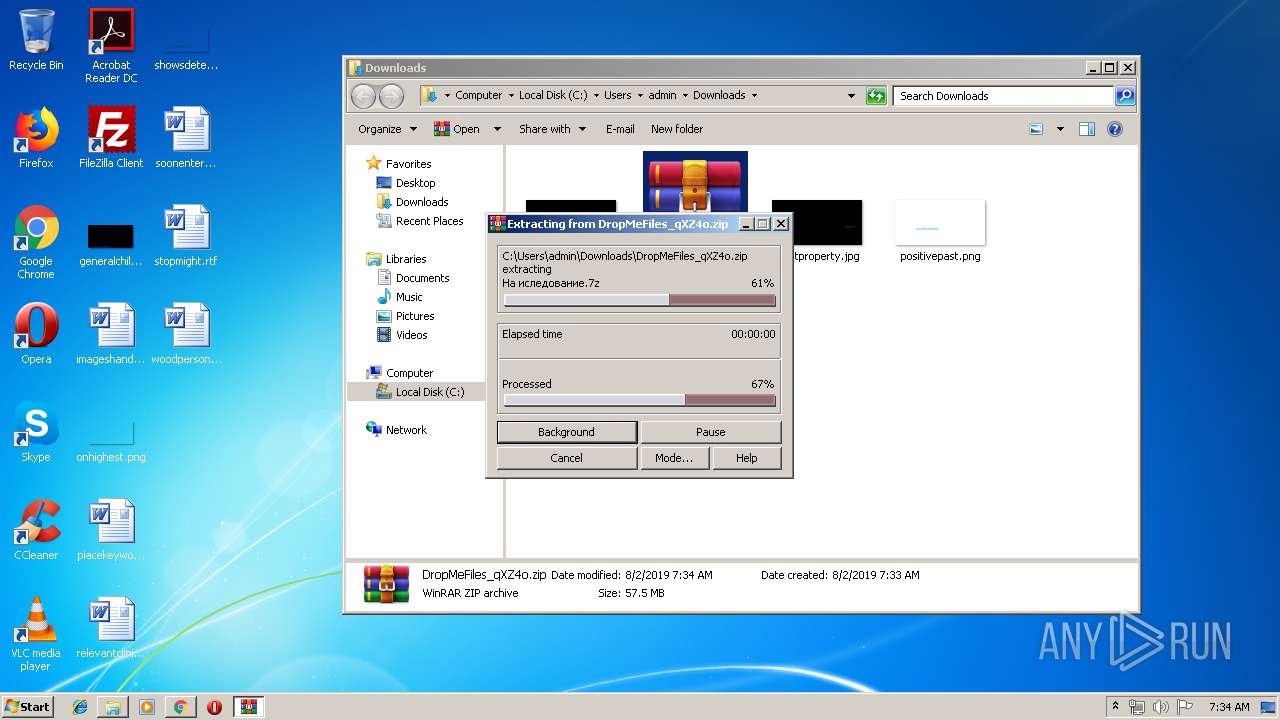
- WinRAR.exe (PID: 3988)
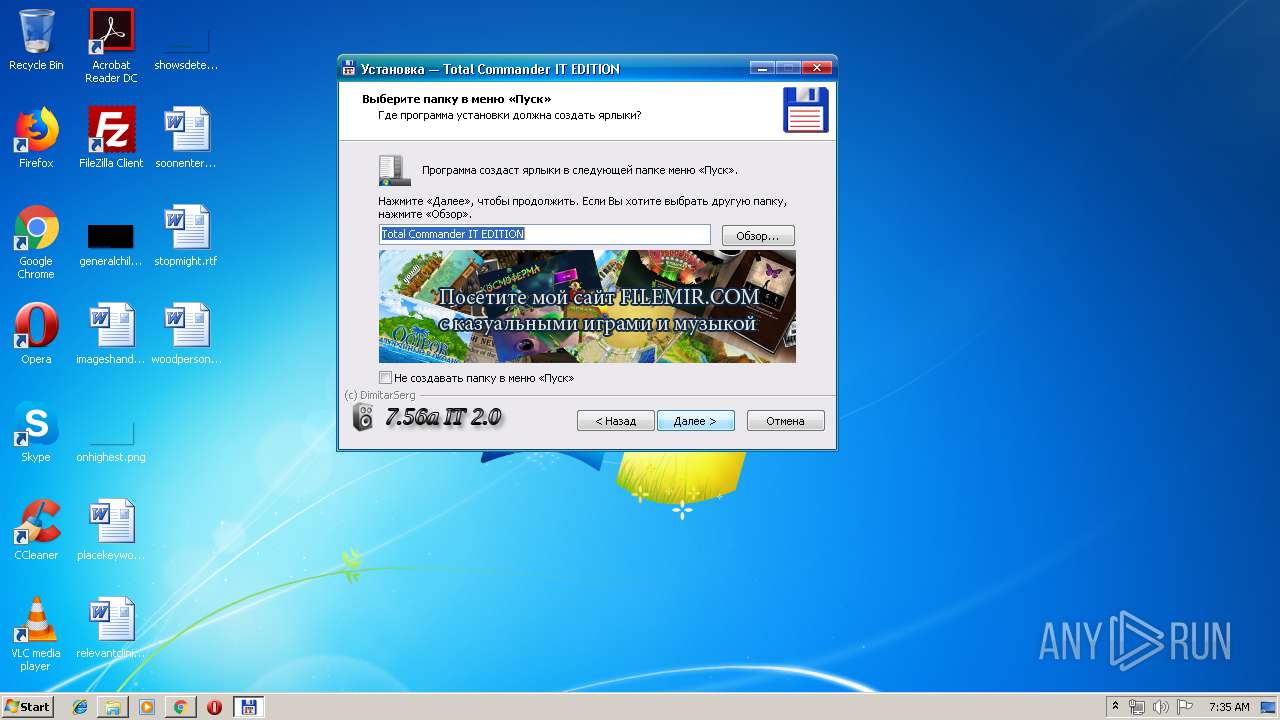
- setup.exe (PID: 1388)
- WinRAR.exe (PID: 2940)
- setup.exe (PID: 2264)
Reads settings of System Certificates
- chrome.exe (PID: 3192)
Loads dropped or rewritten executable
- setup.tmp (PID: 2844)
Application was dropped or rewritten from another process
- setup.tmp (PID: 2844)
Dropped object may contain Bitcoin addresses
- setup.tmp (PID: 2844)
Creates files in the program directory
- setup.tmp (PID: 2844)
Creates a software uninstall entry
- setup.tmp (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
31
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11467774015517752154 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe13_ Global\UsGthrCtrlFltPipeMssGthrPipe13 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6706728232425964567 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11768468311074717506 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11362861577796627458 --mojo-platform-channel-handle=2776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x70fea9d0,0x70fea9e0,0x70fea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14585352772922620330 --mojo-platform-channel-handle=3884 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5779446331474420908 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
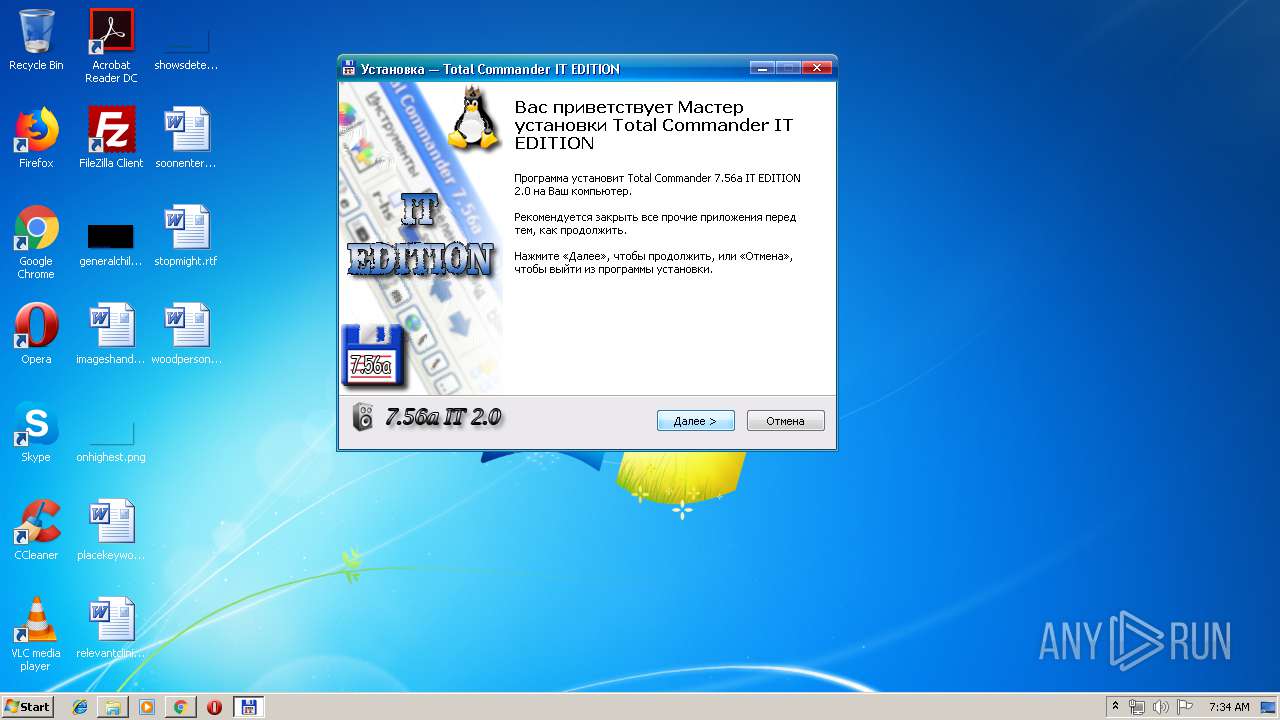
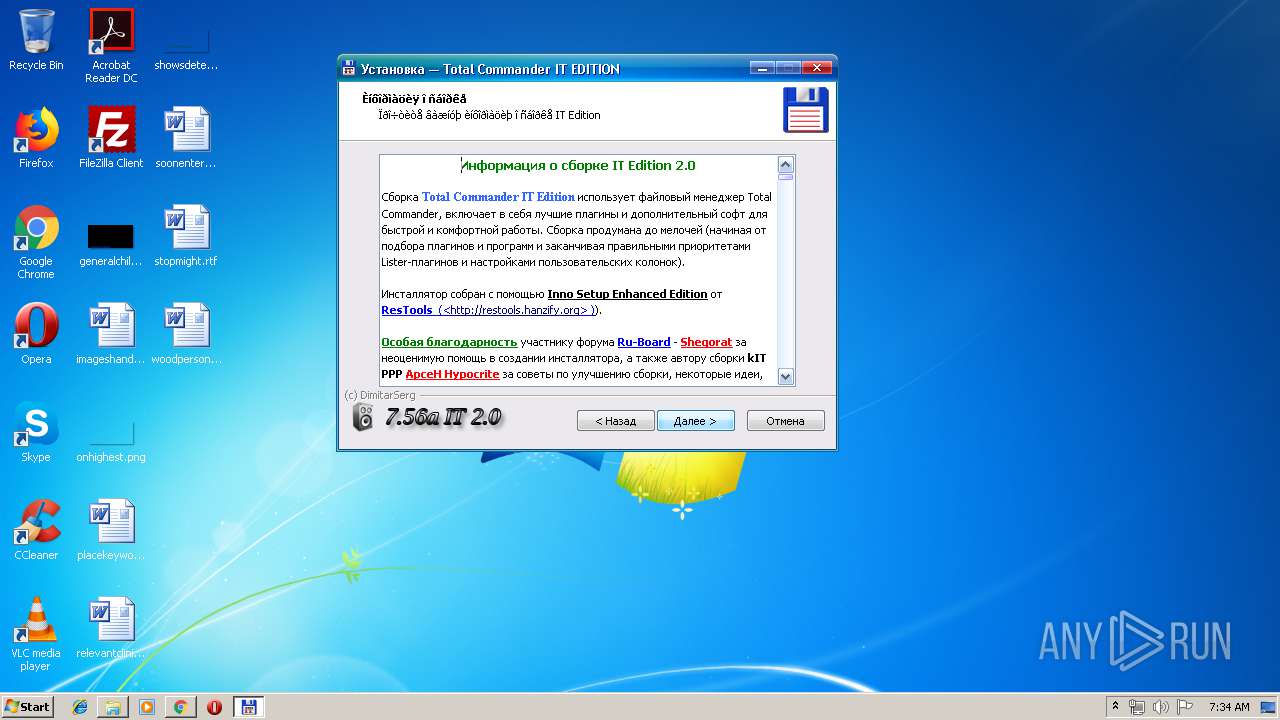
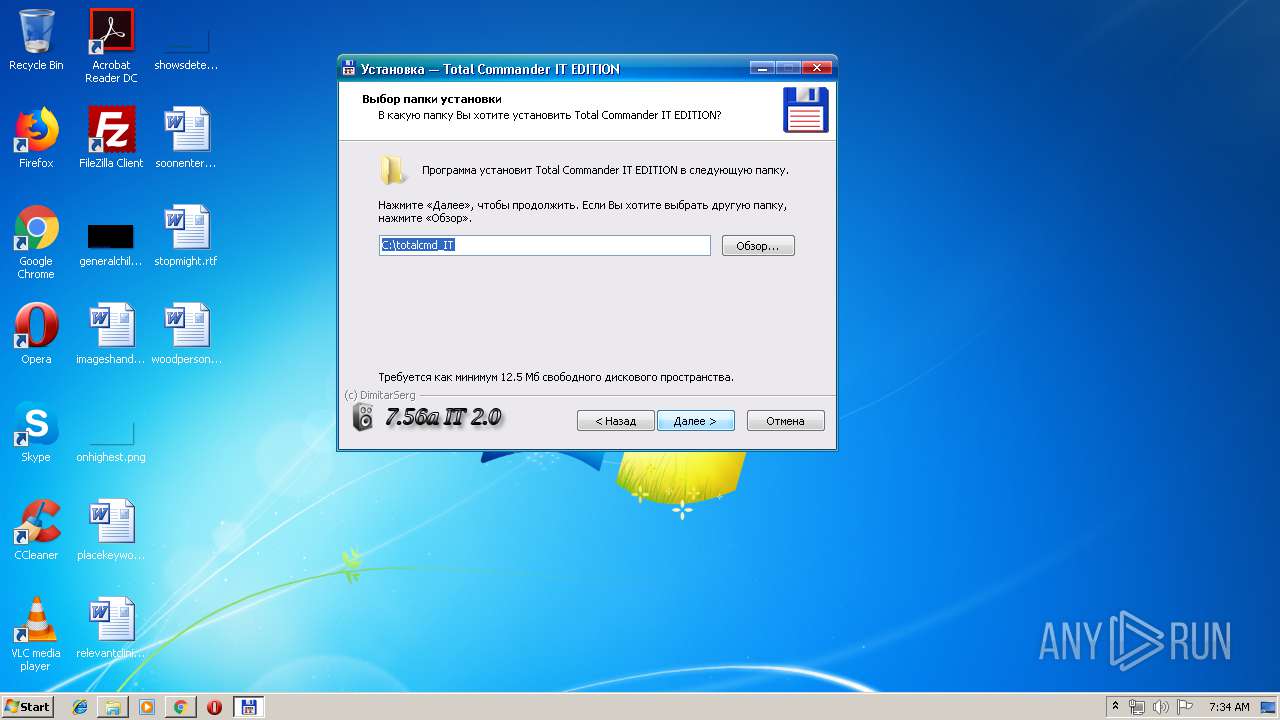
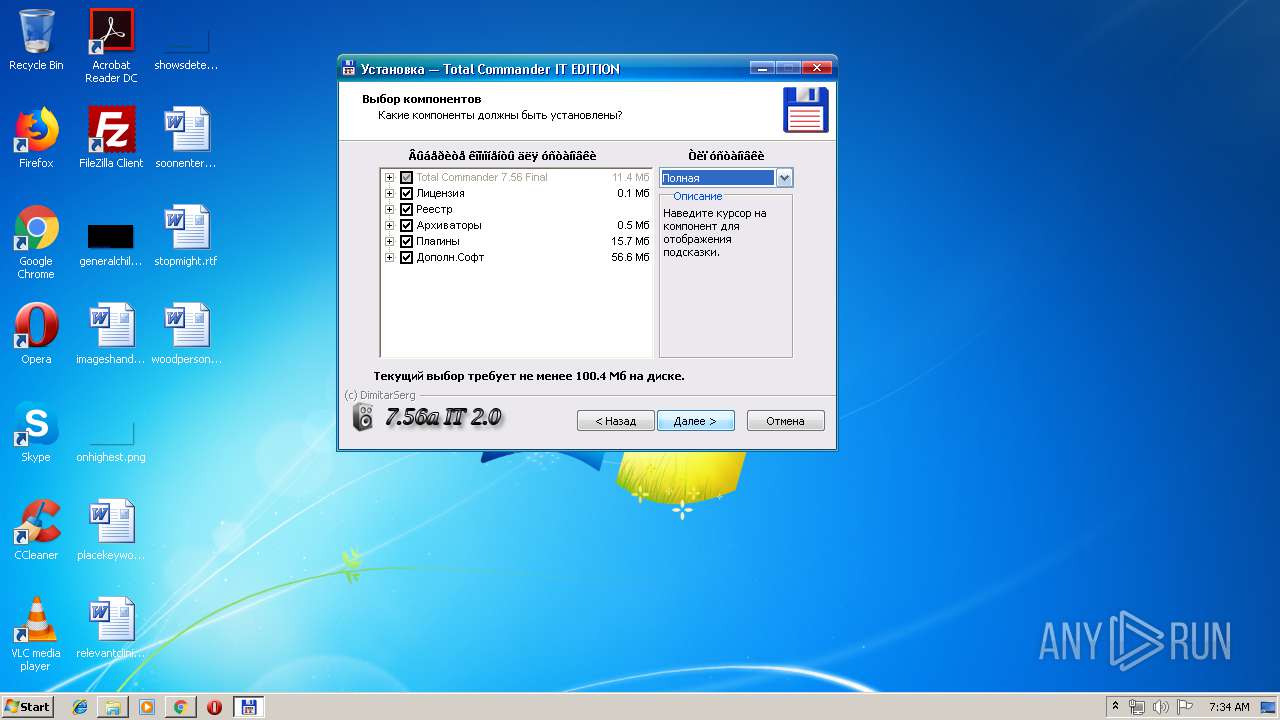
| 1388 | "C:\Users\admin\Downloads\На иследование\Total Commander 7.56a_(IT Edition v2.0)\setup.exe" | C:\Users\admin\Downloads\На иследование\Total Commander 7.56a_(IT Edition v2.0)\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: DimitarSerg, Inc. Integrity Level: MEDIUM Description: Total Commander IT EDITION Setup Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9818369171082694979 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 075
Read events
1 856
Write events
214
Delete events
5
Modification events
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3568-13209201191976500 |
Value: 259 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3568-13209201191976500 |
Value: 259 | |||
Executable files
242
Suspicious files
102
Text files
1 143
Unknown types
101
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47604fa3-d1db-426d-9afc-c6a2177f8a38.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF36e8b3.TMP | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36e7e8.TMP | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36e807.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
46
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | chrome.exe | GET | 200 | 176.99.128.38:80 | http://drop3.dropmefile.com/zip/qXZ4o | RU | compressed | 57.5 Mb | suspicious |
3192 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3192 | chrome.exe | GET | 200 | 172.217.132.106:80 | http://r5---sn-5hne6nsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-5hne6nsy&ms=nvh&mt=1564727274&mv=u&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3192 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3192 | chrome.exe | 172.217.16.170:443 | imasdk.googleapis.com | Google Inc. | US | whitelisted |
3192 | chrome.exe | 216.58.208.34:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
3192 | chrome.exe | 172.217.18.2:443 | adservice.google.ch | Google Inc. | US | whitelisted |
3192 | chrome.exe | 172.217.16.194:443 | adservice.google.com | Google Inc. | US | whitelisted |
3192 | chrome.exe | 172.217.18.98:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3192 | chrome.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3192 | chrome.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3192 | chrome.exe | 216.58.205.225:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dropmefiles.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
imasdk.googleapis.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
adservice.google.ch |
| whitelisted |
adservice.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |