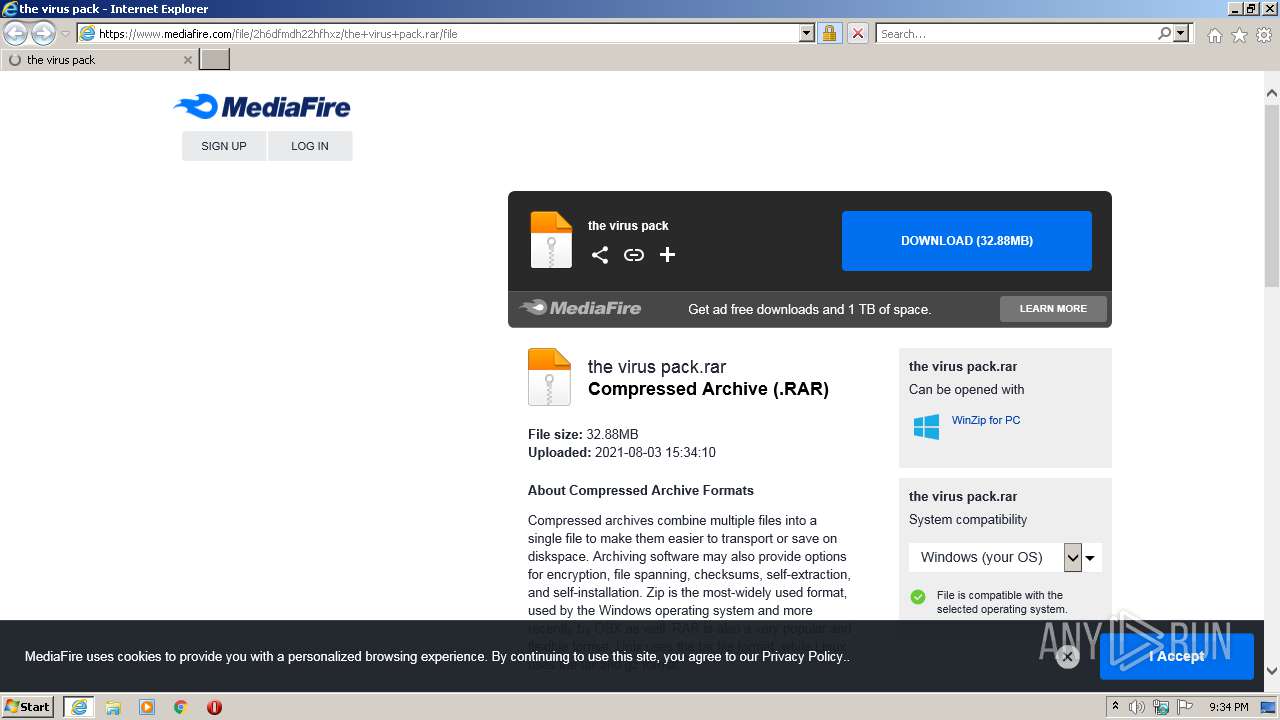
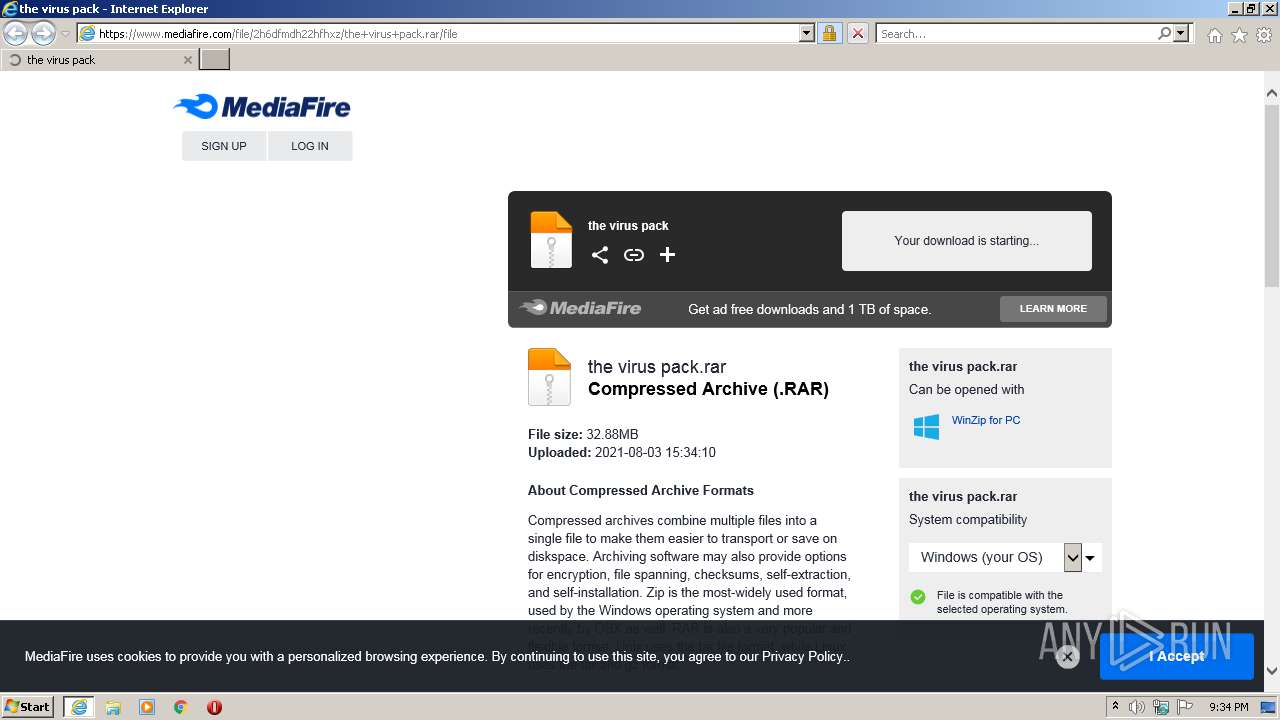
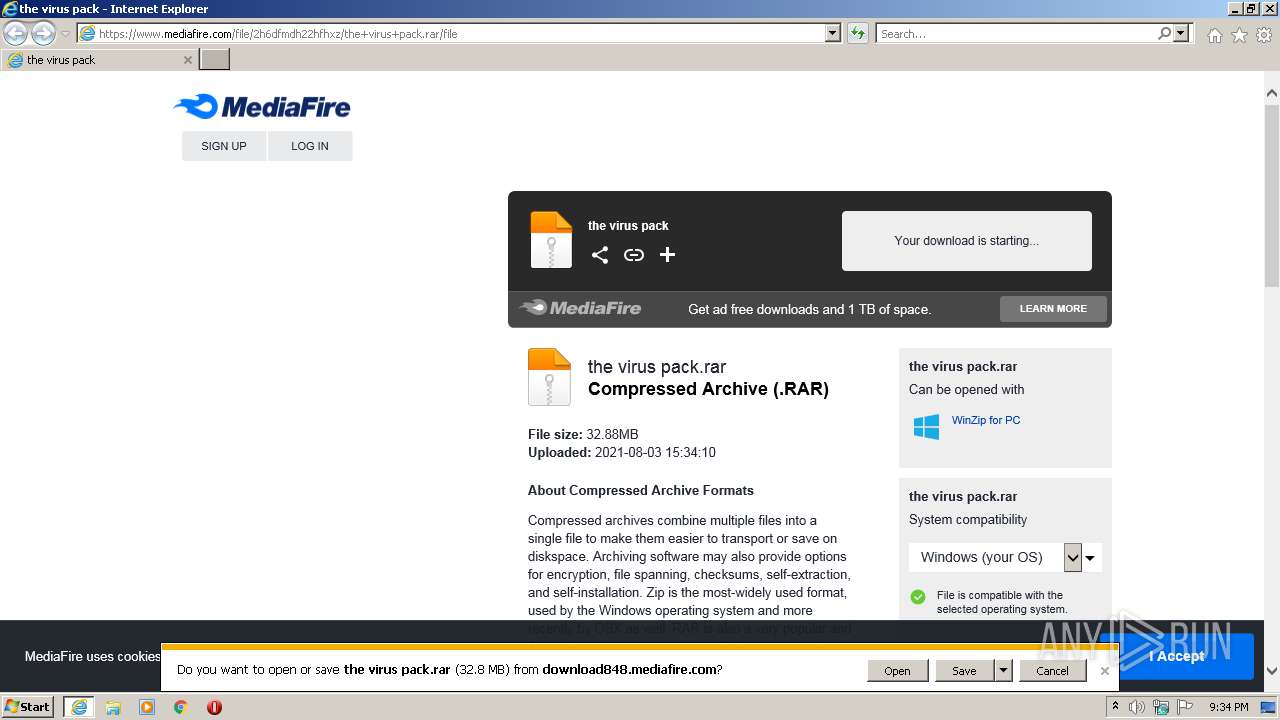
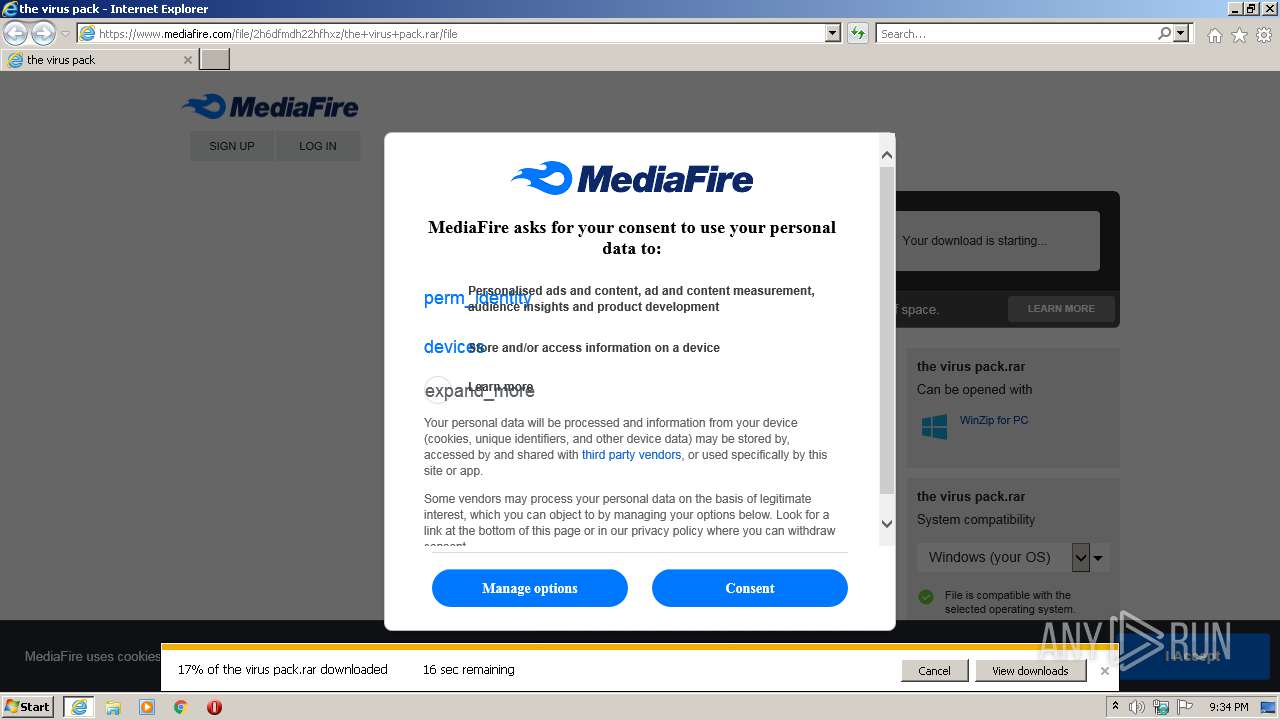
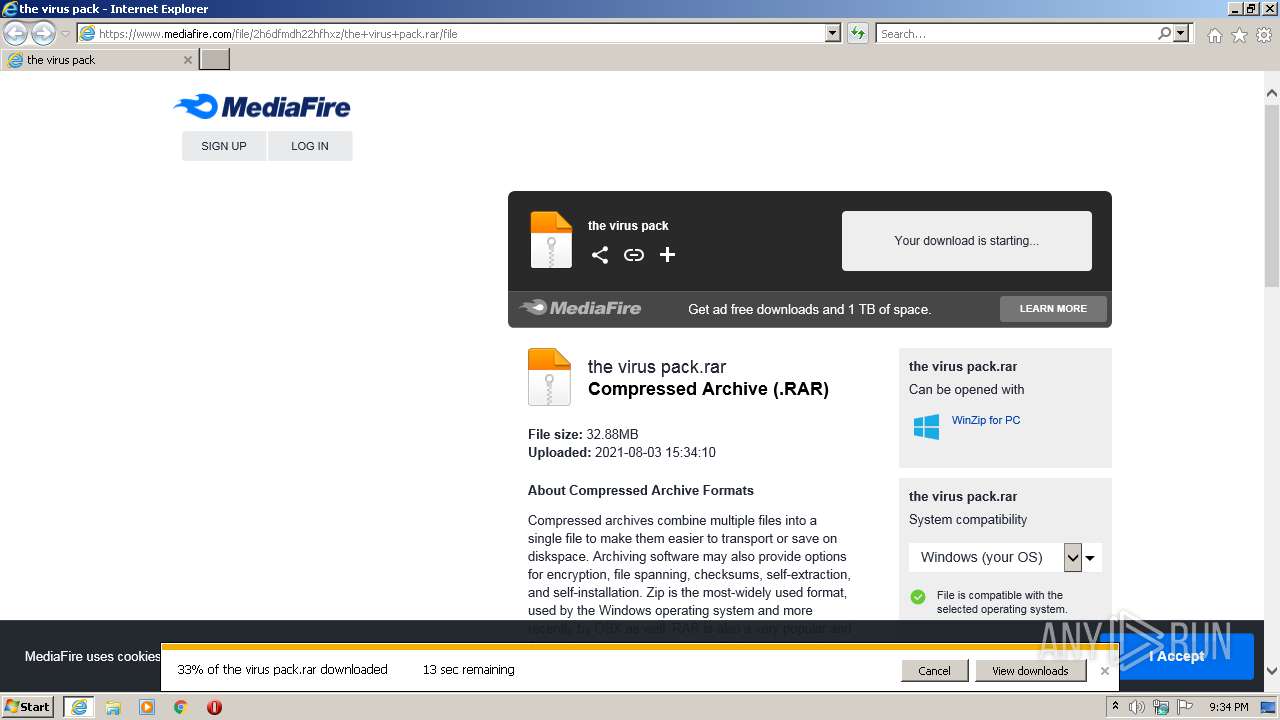
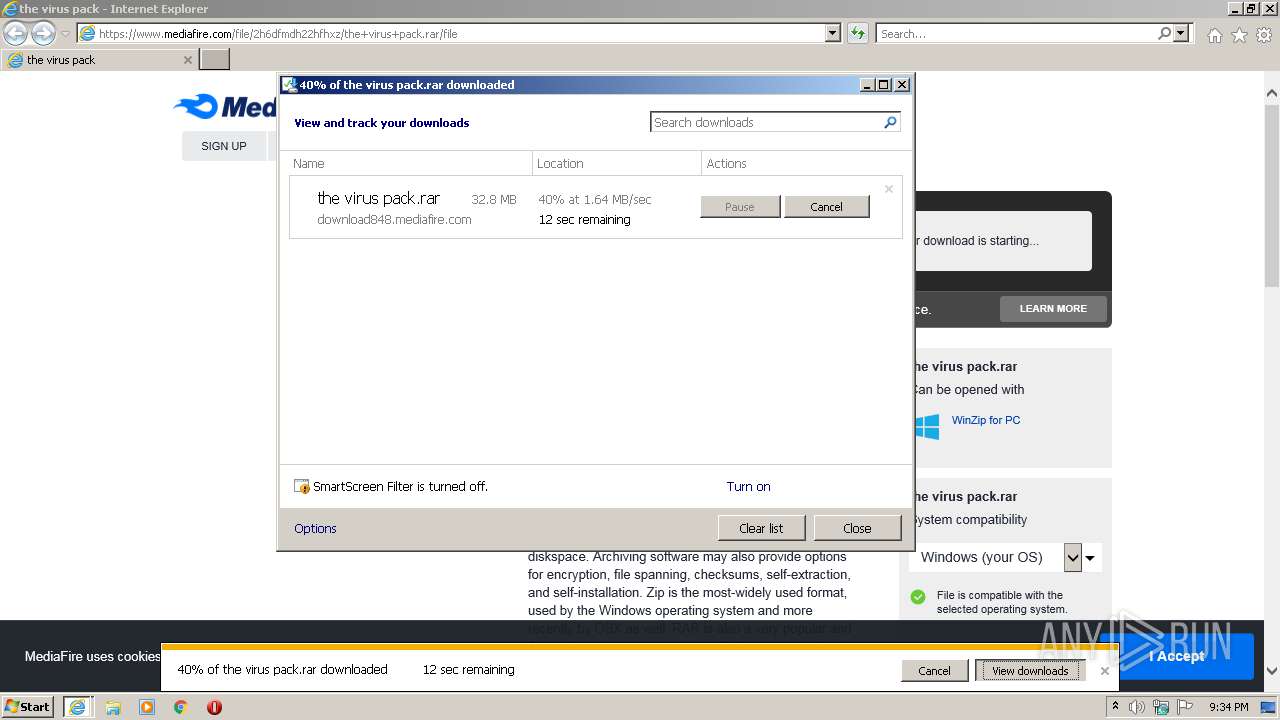
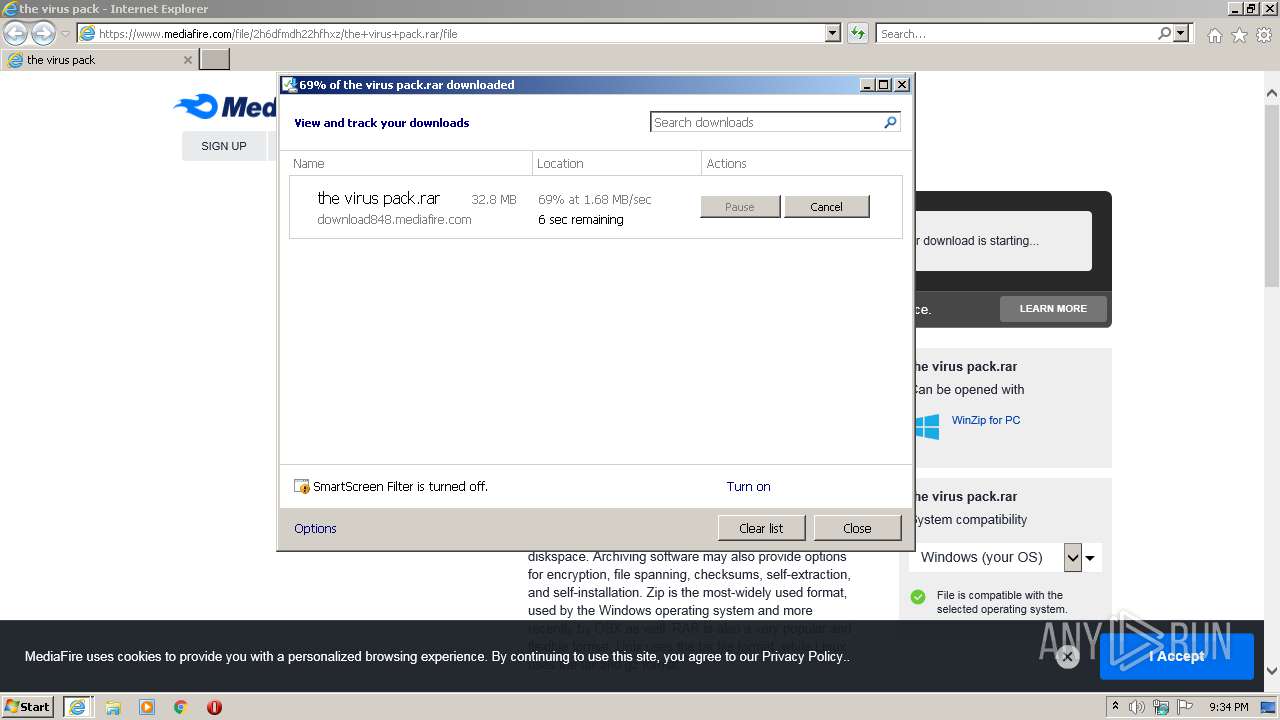
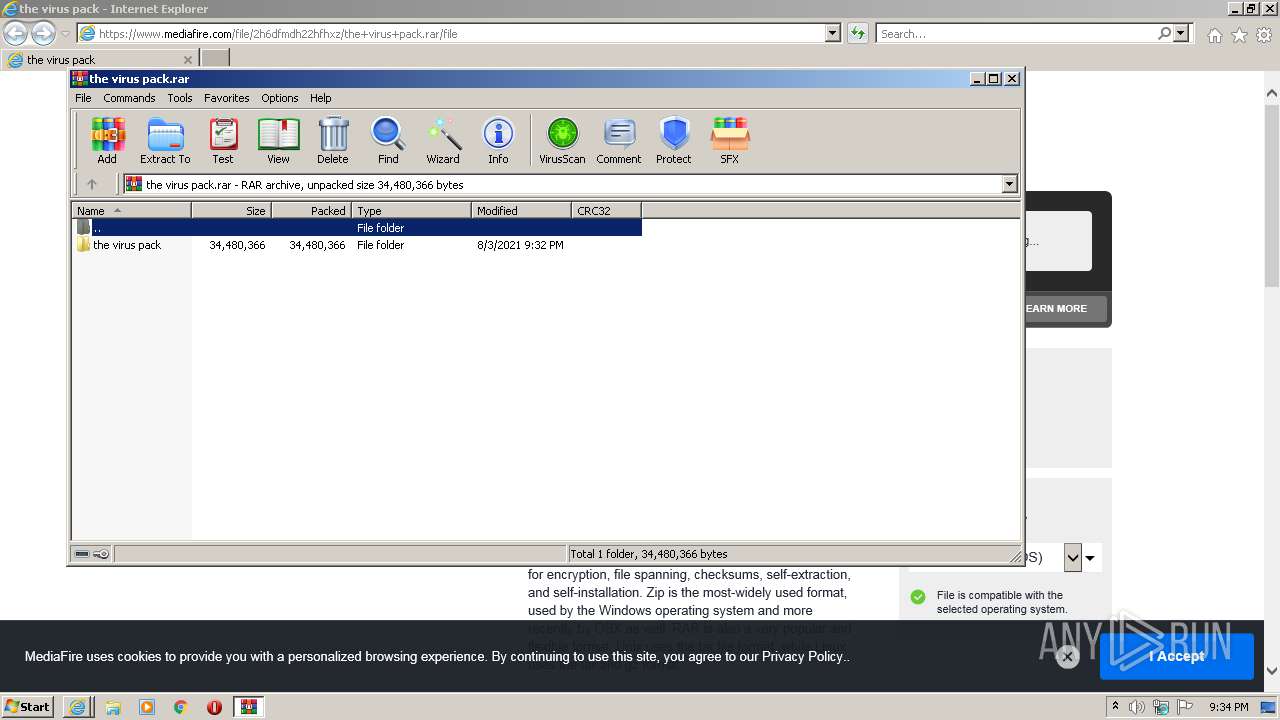
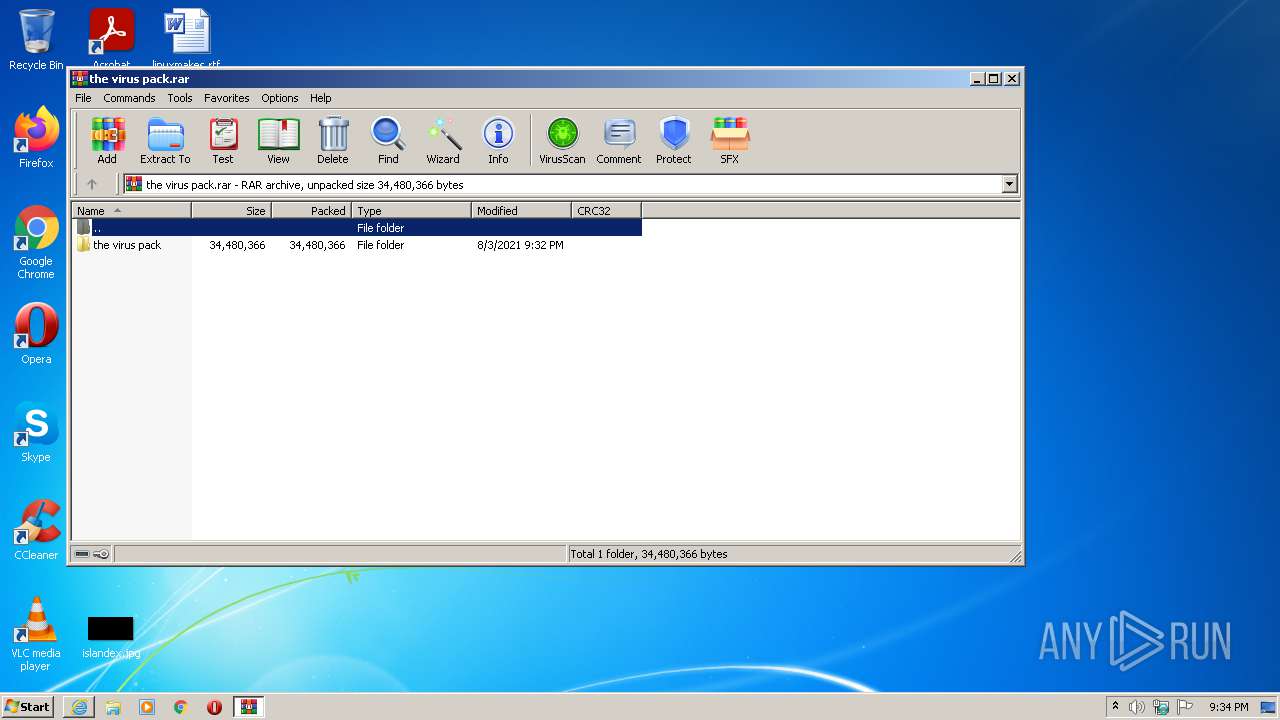
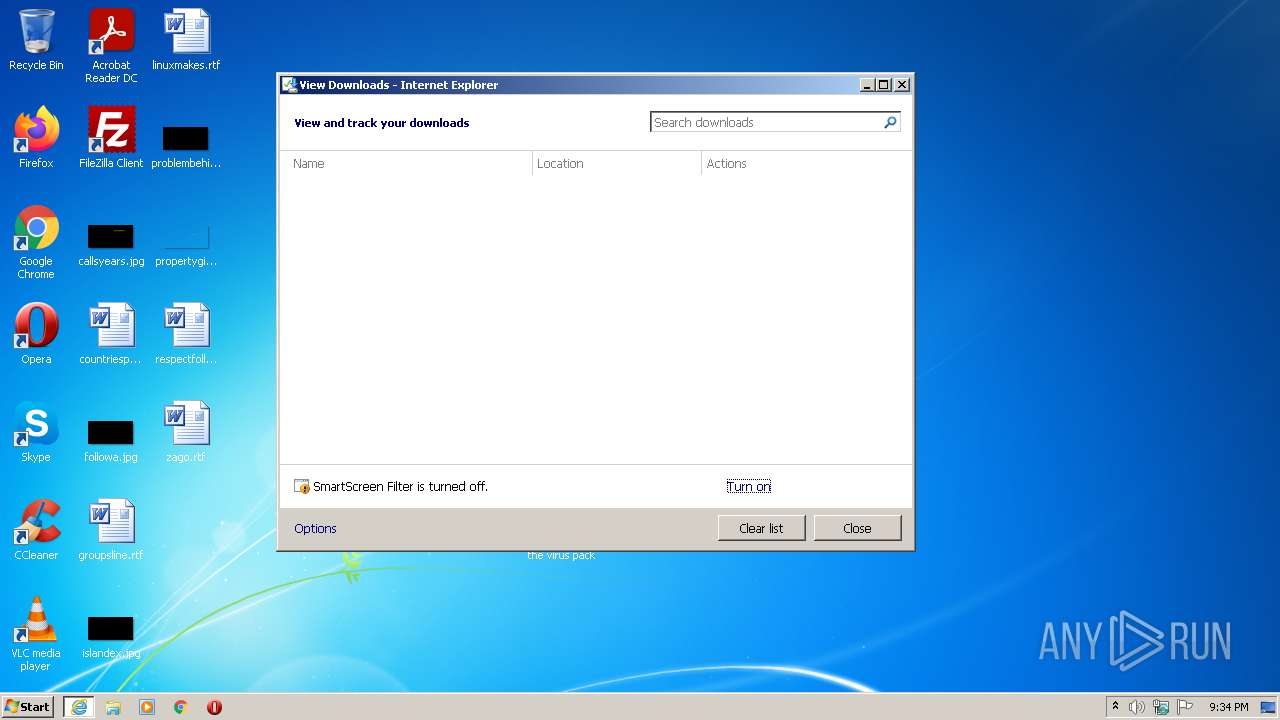
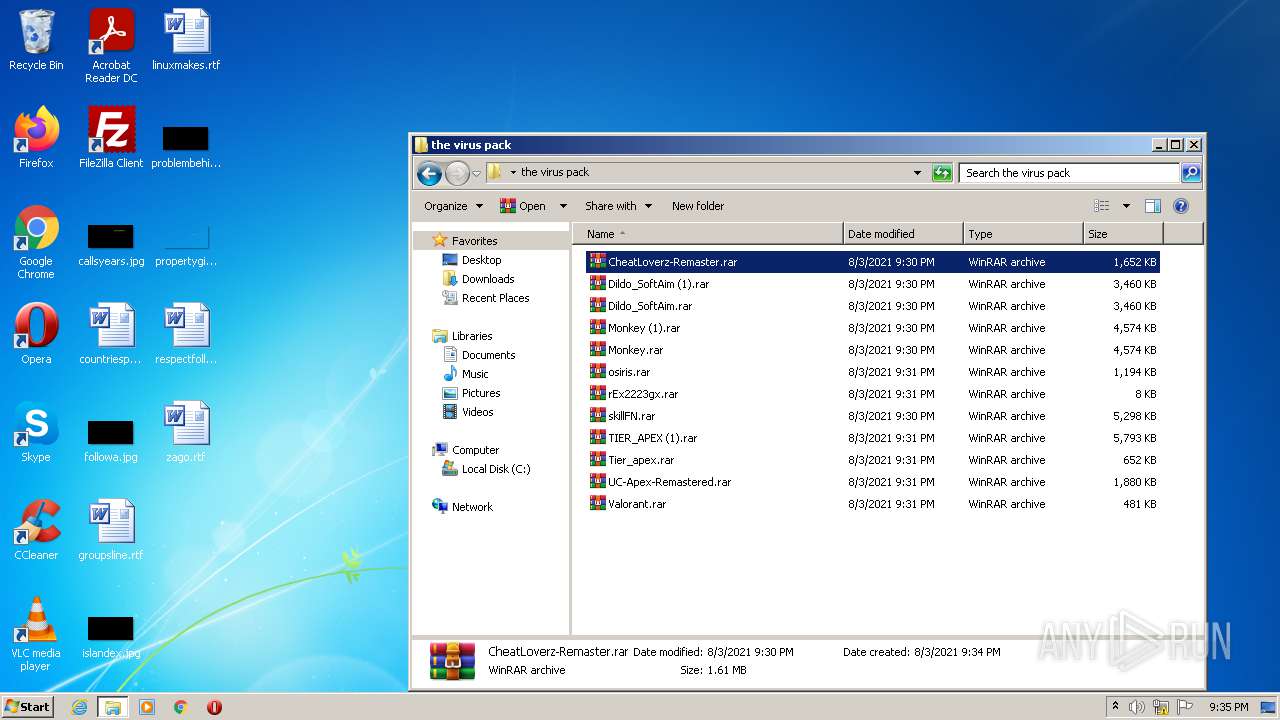
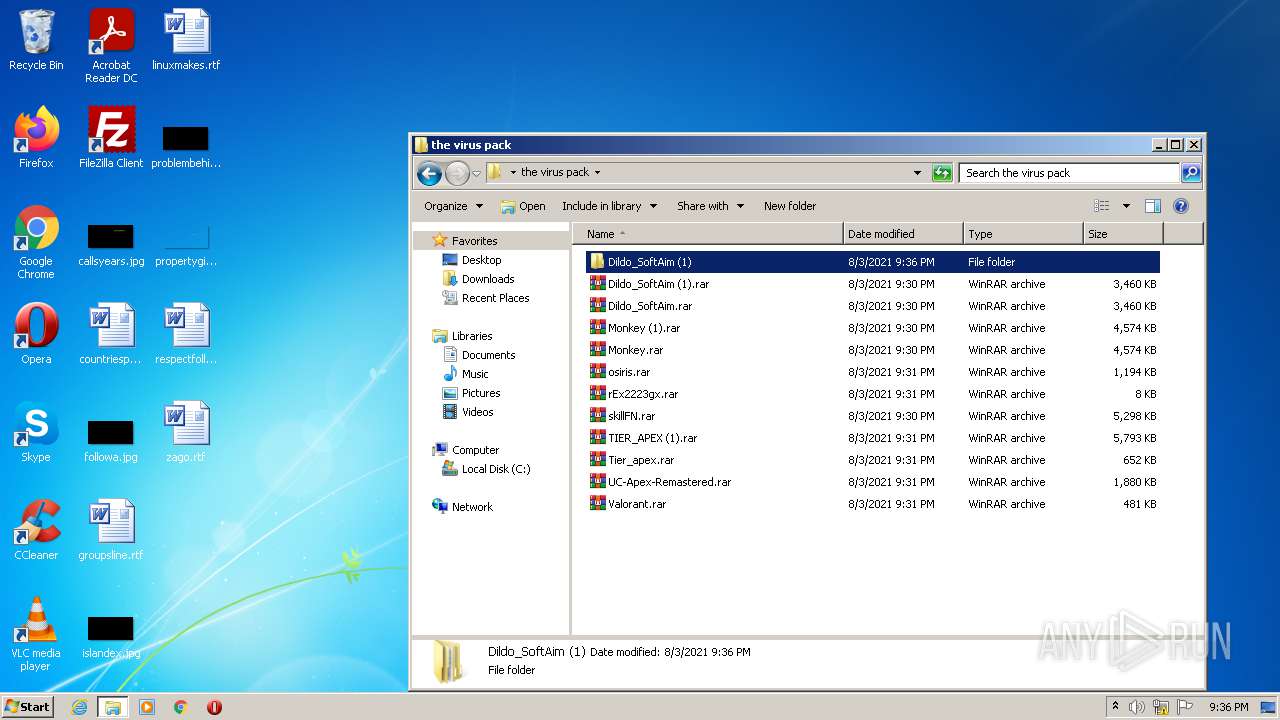
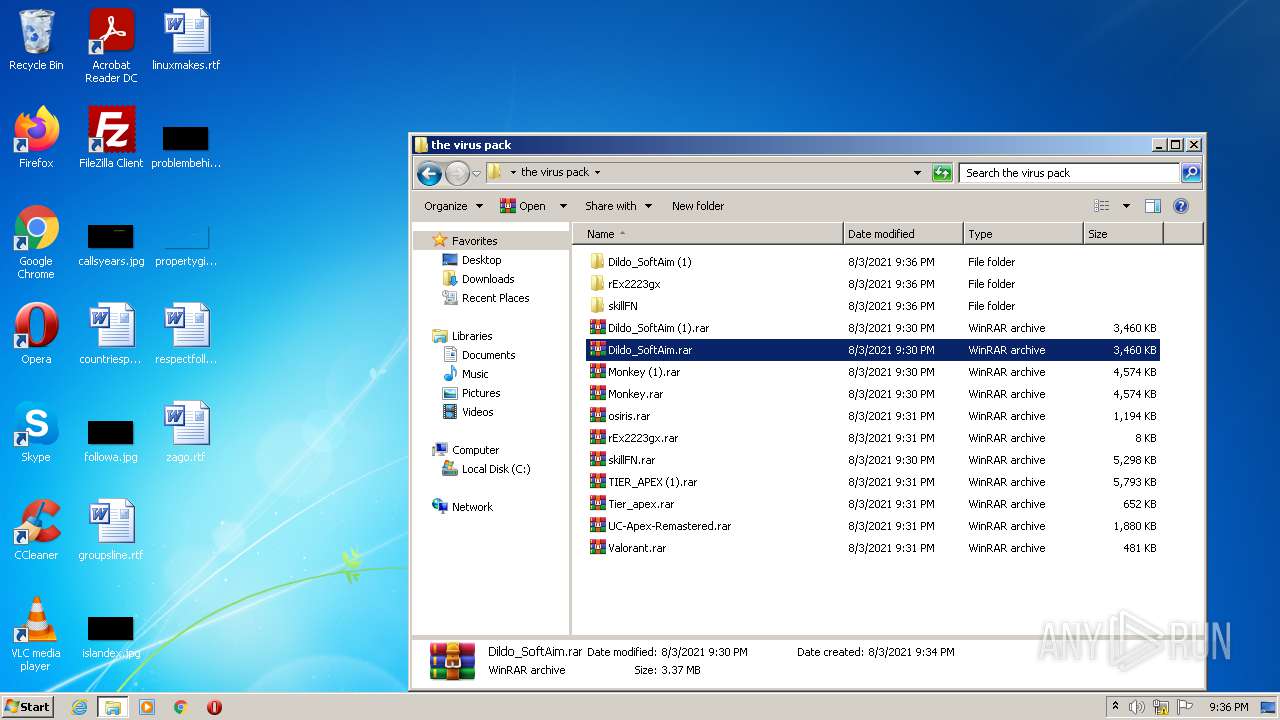
| URL: | https://www.mediafire.com/file/2h6dfmdh22hfhxz/the+virus+pack.rar/file |
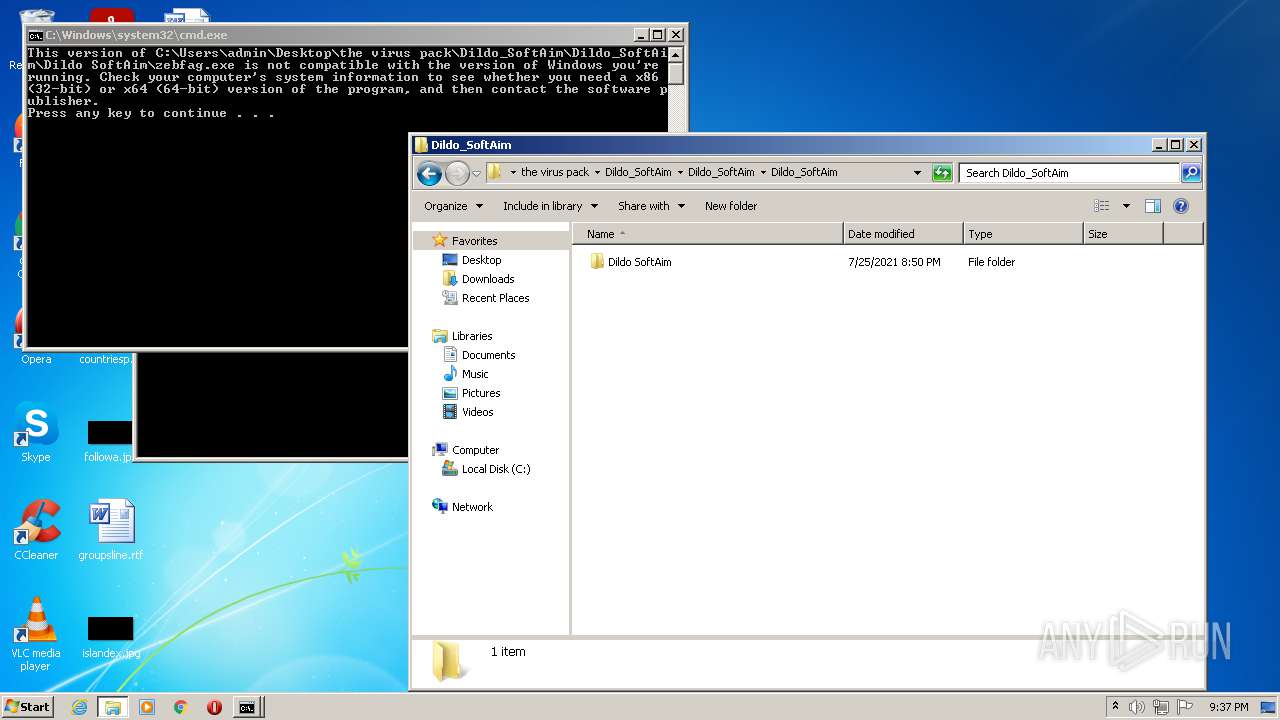
| Full analysis: | https://app.any.run/tasks/bd81b997-e118-4e8c-8680-843444c41ecd |
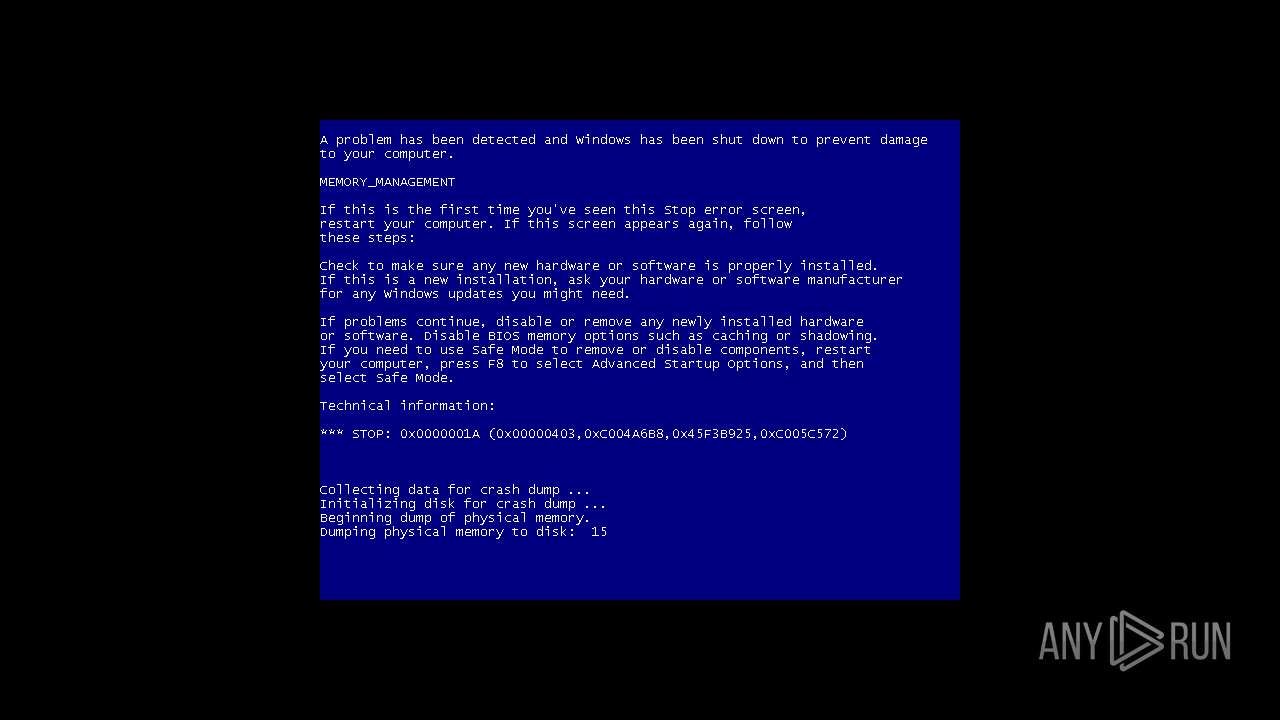
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2021, 20:33:53 |
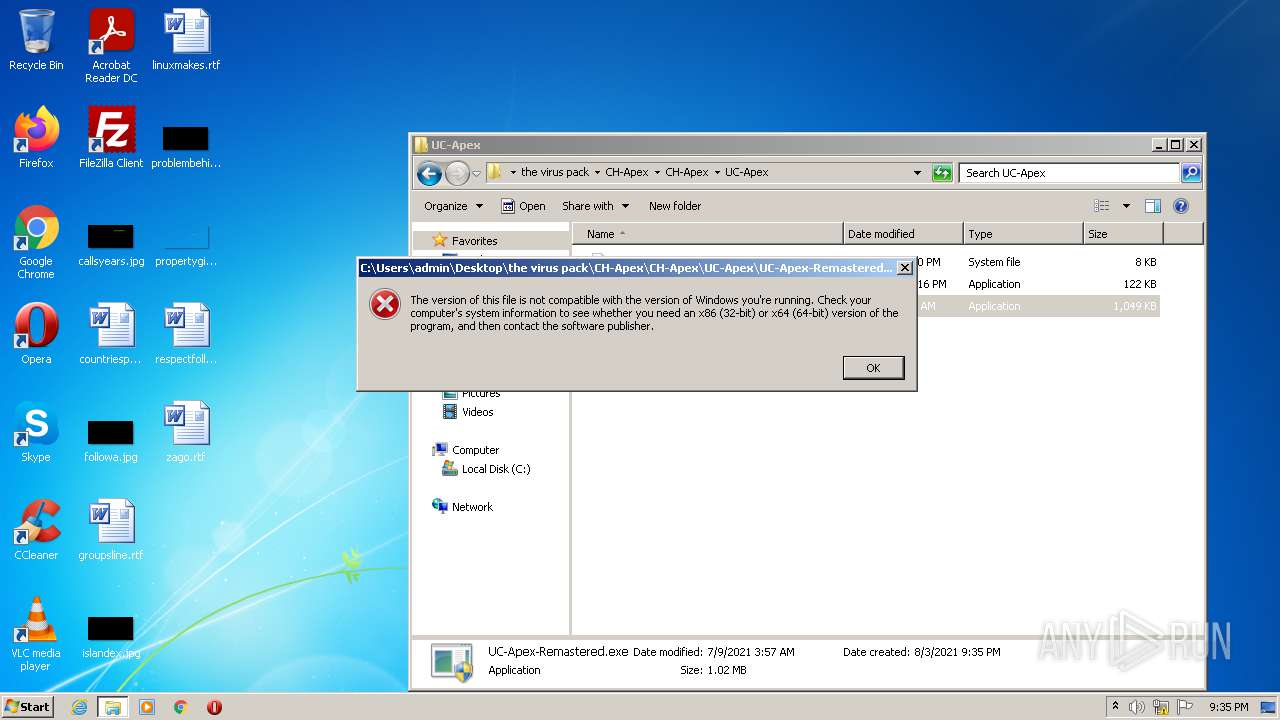
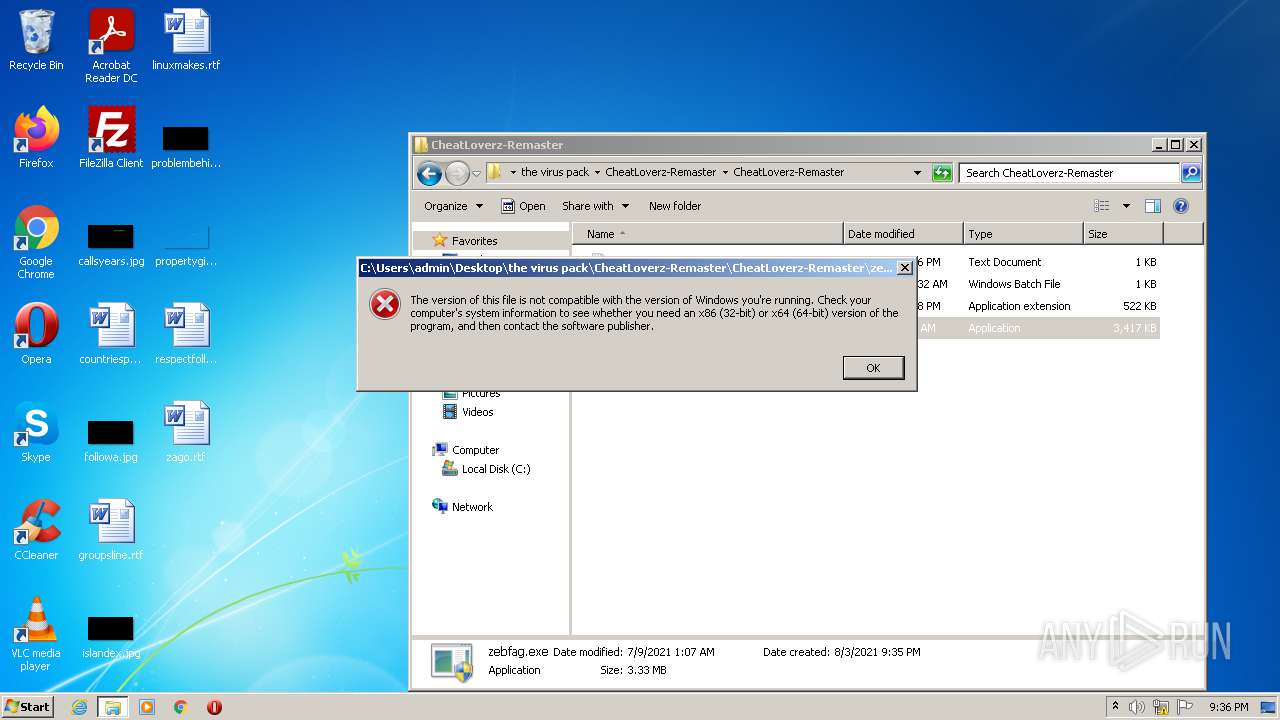
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ECA72607CB8F5BA8FBEA89B55E43B753 |
| SHA1: | 328DE4109C202020F001A74A278E43C73ED0E62E |
| SHA256: | C0C51AFD44AD063195536F21DD507226FE4A160CCF195B4C670947308E89C573 |
| SSDEEP: | 3:N8DSLw3eGUoXNNU09/EZjEPA:2OLw3eGz3U0RWjEPA |
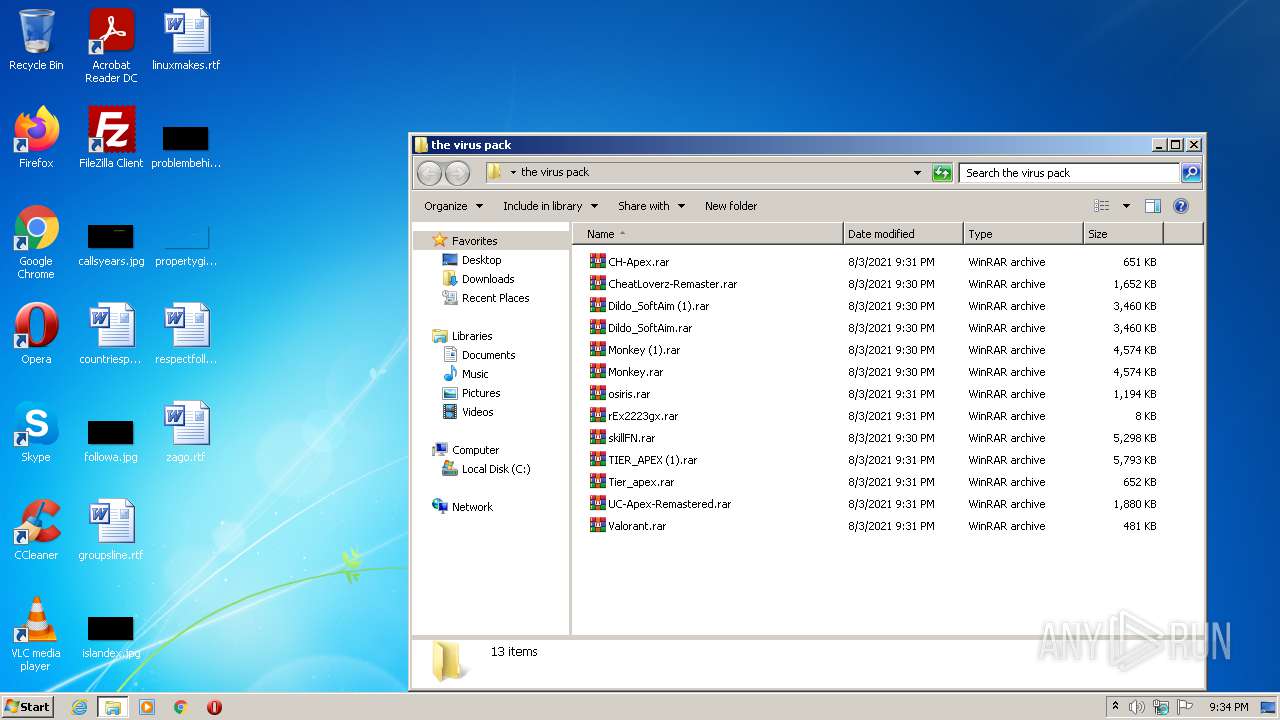
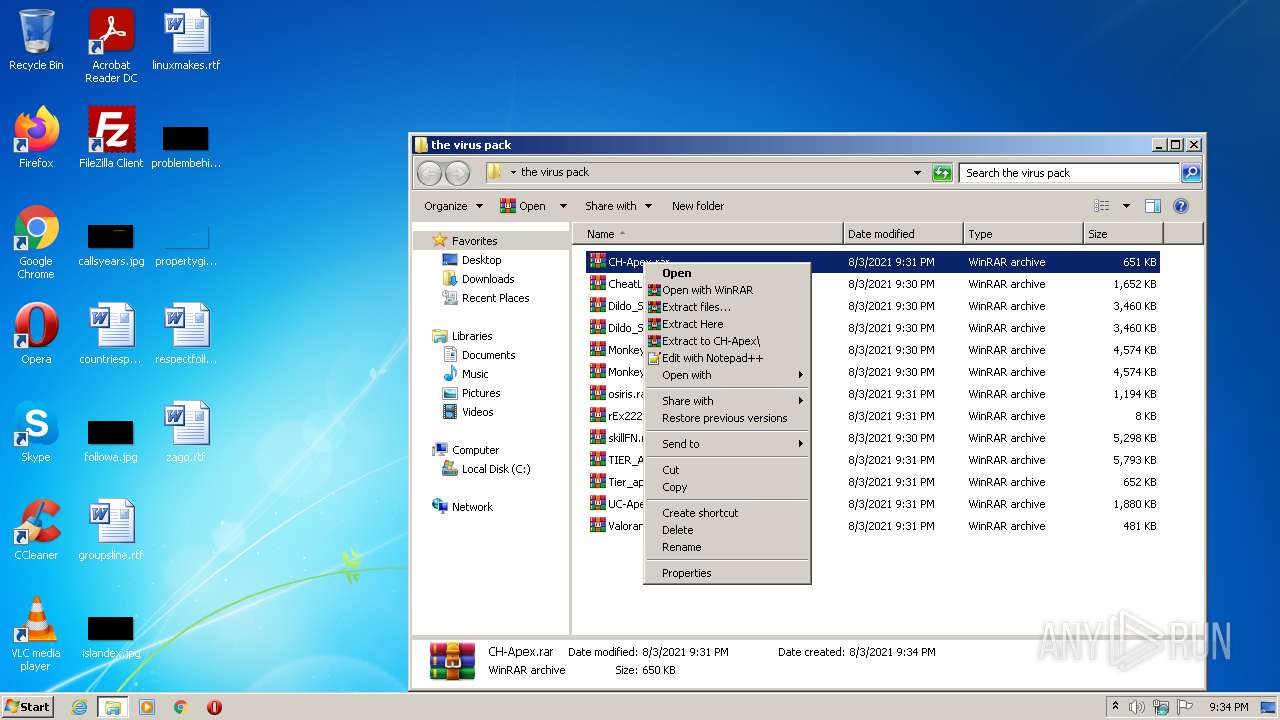
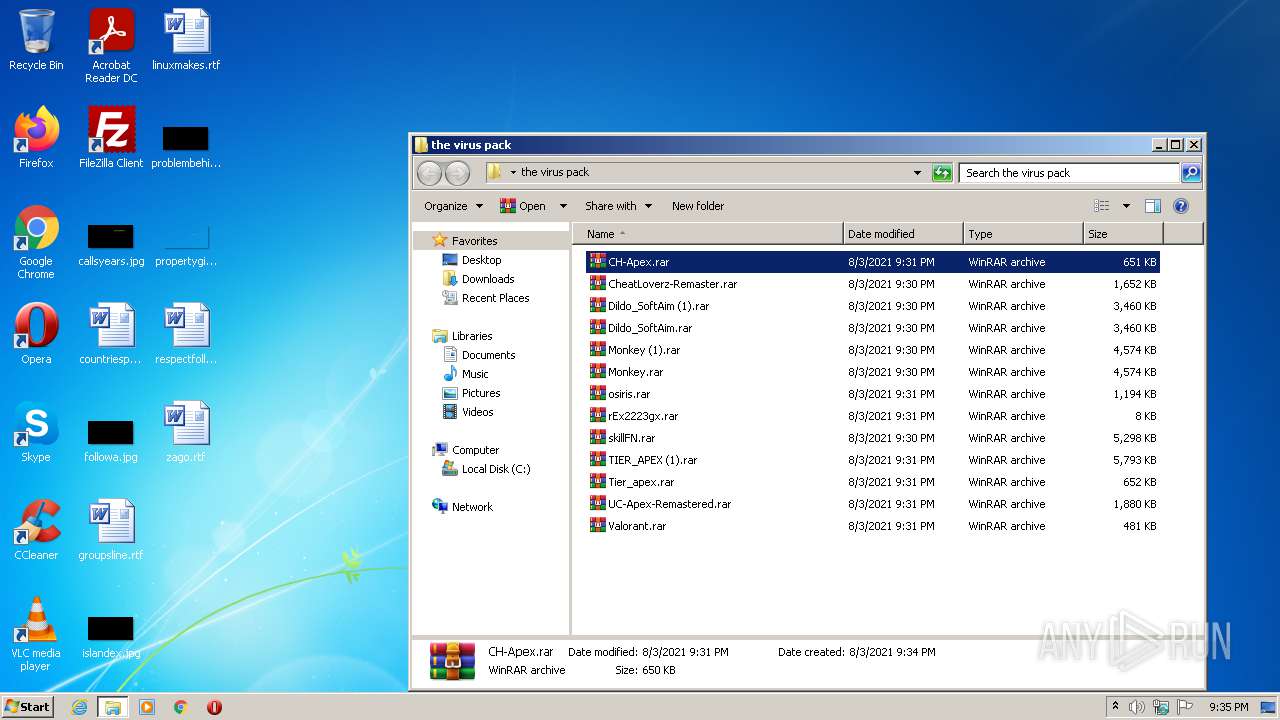
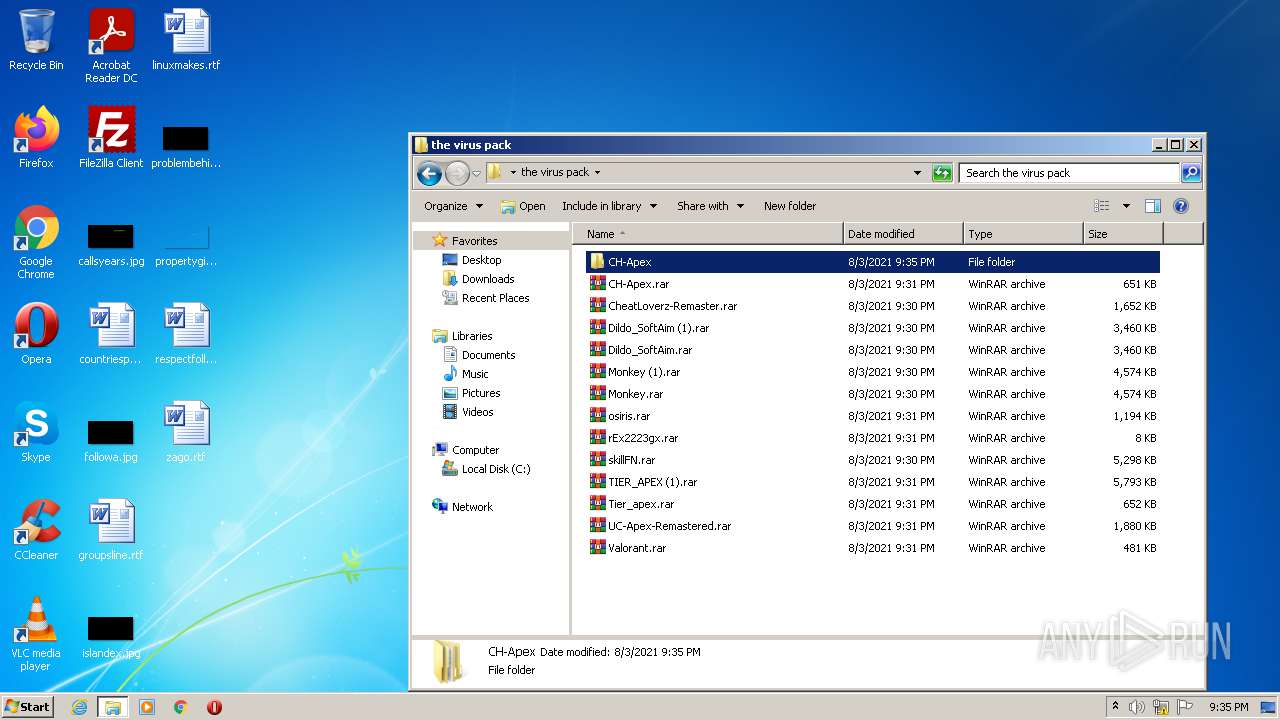
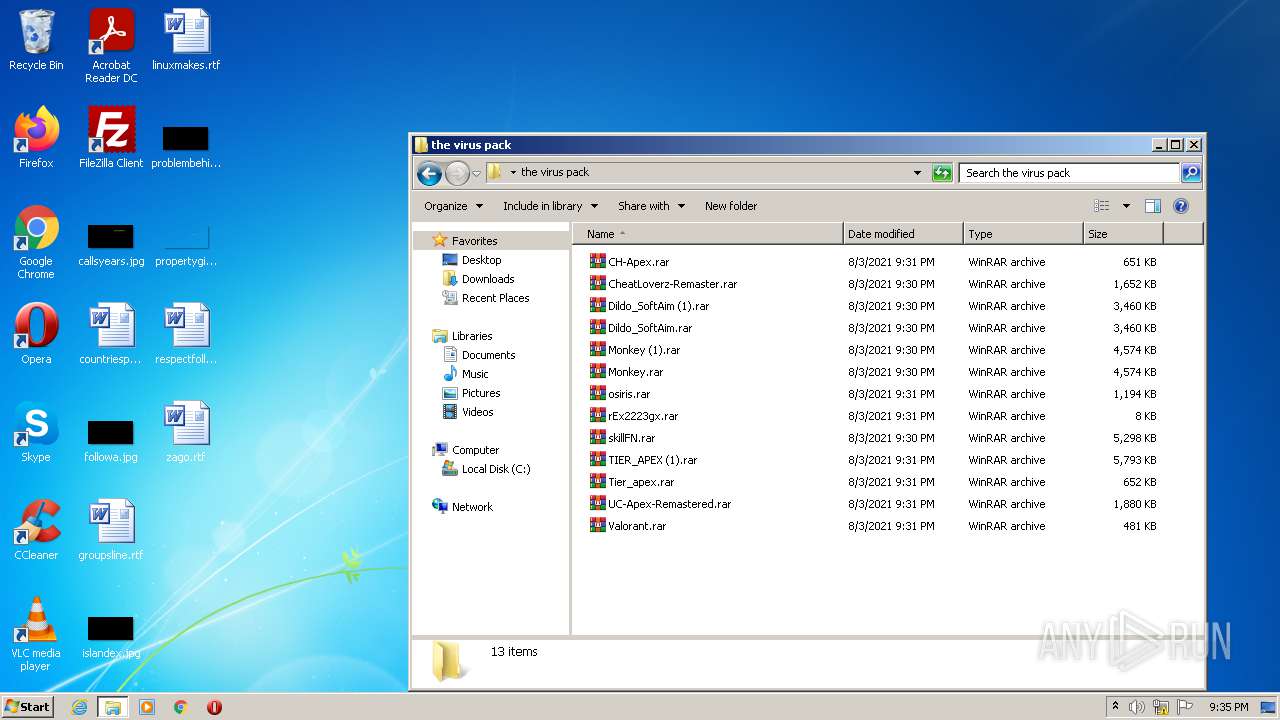
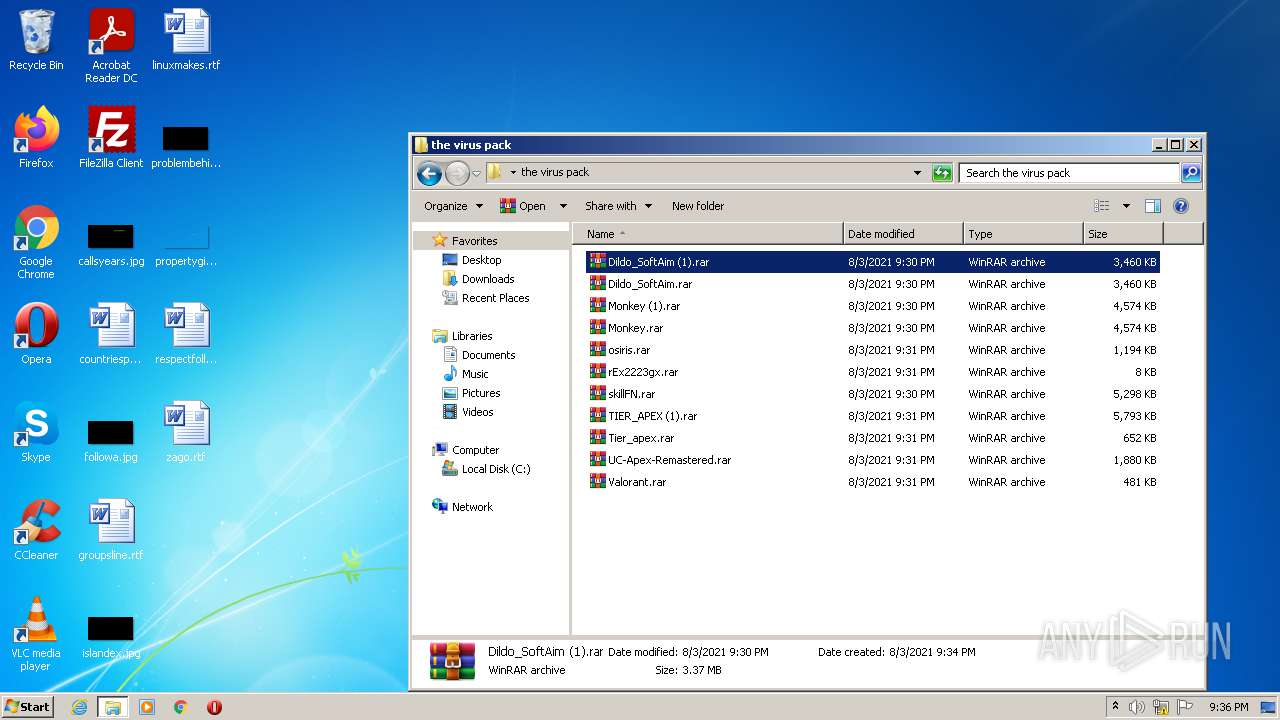
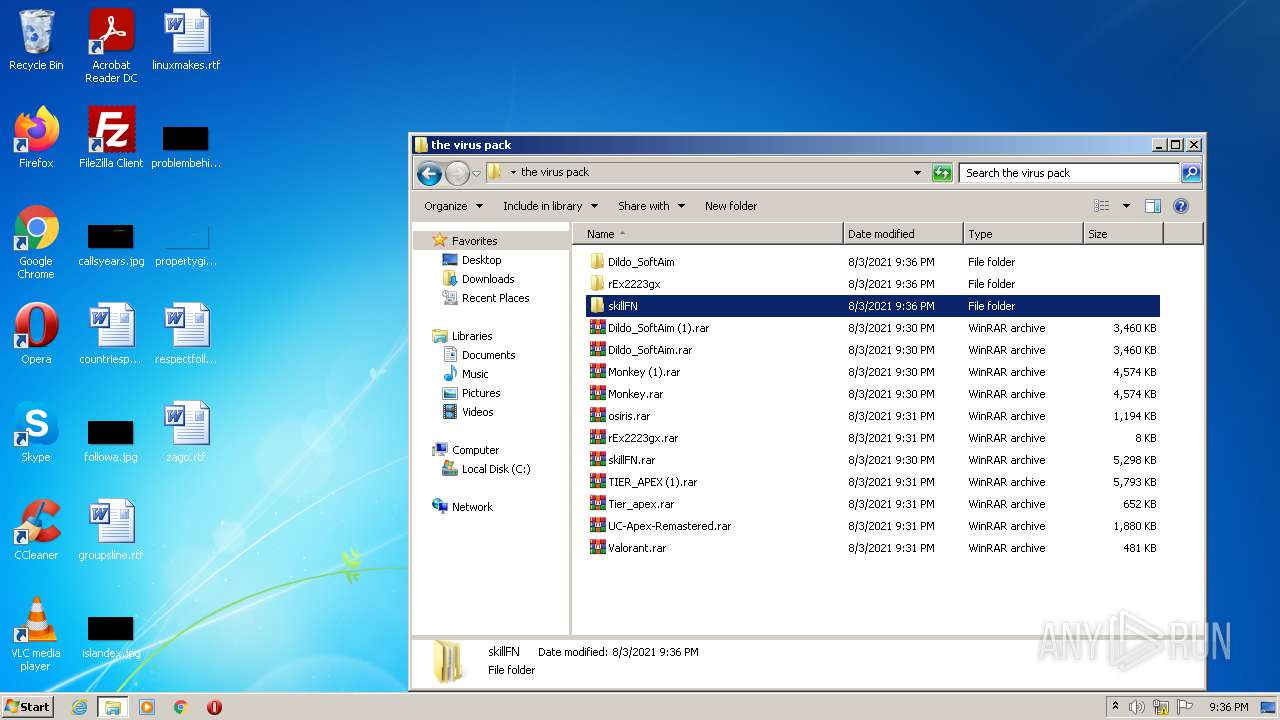
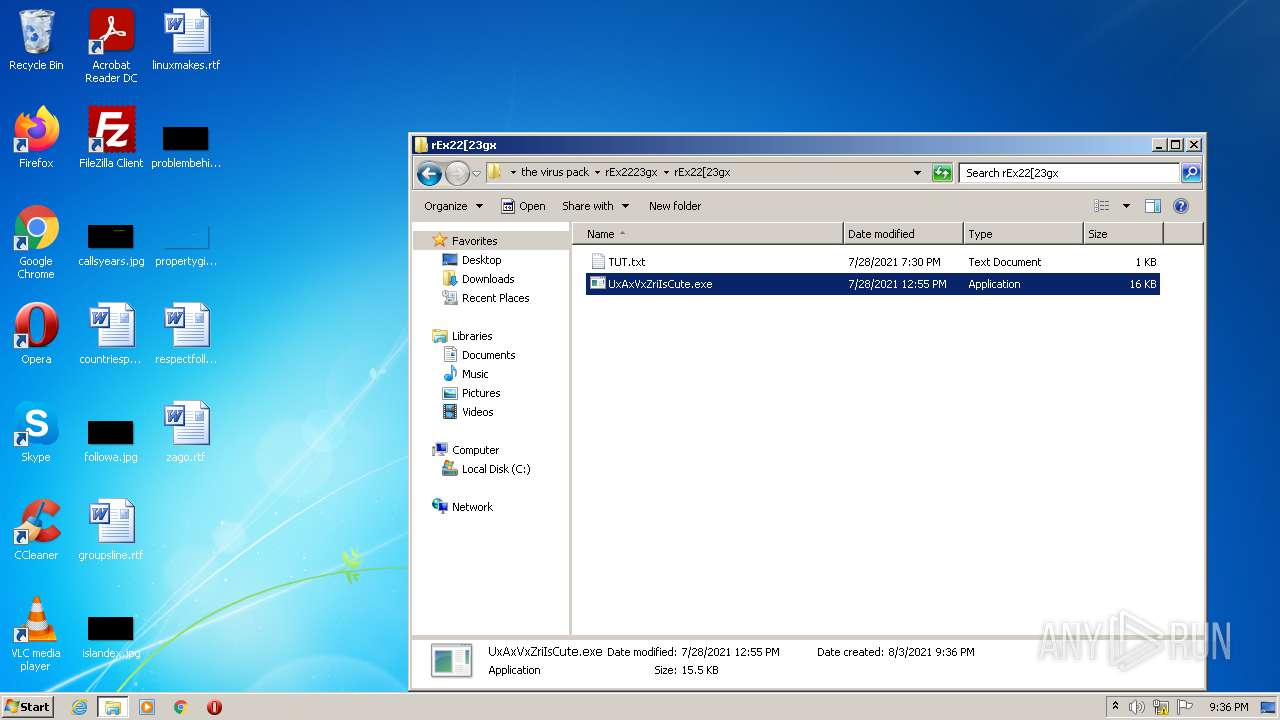
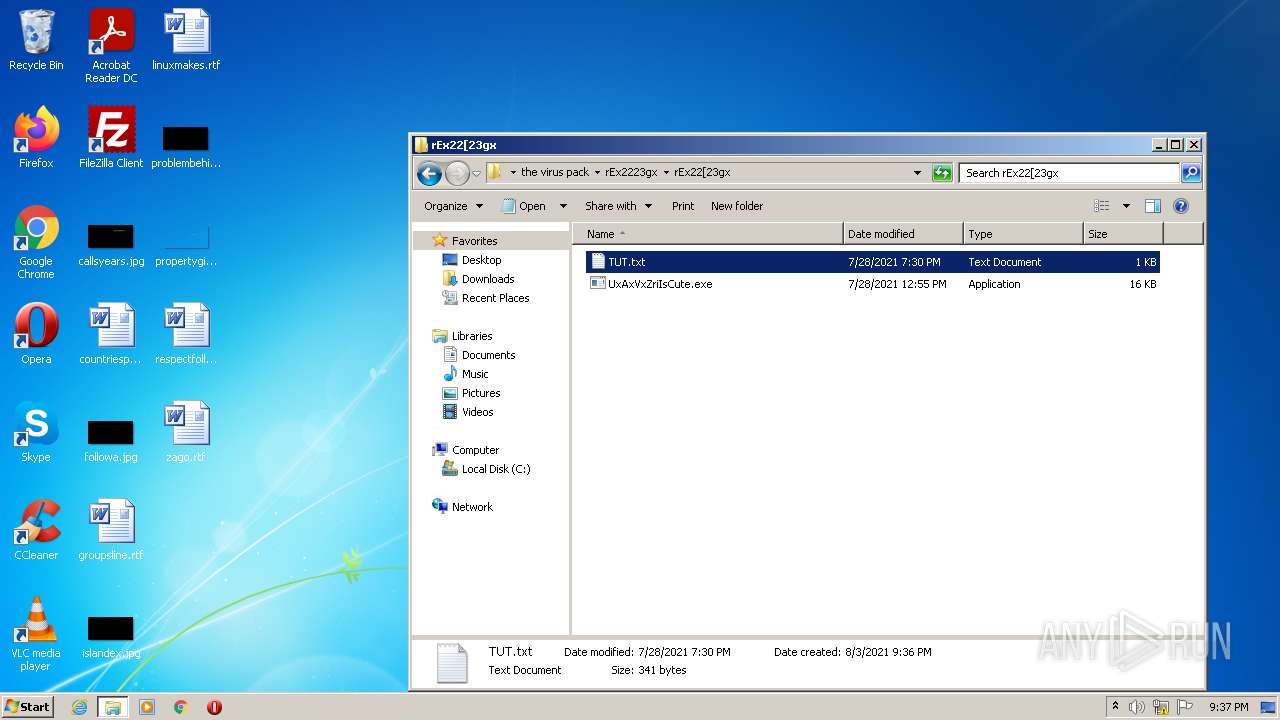
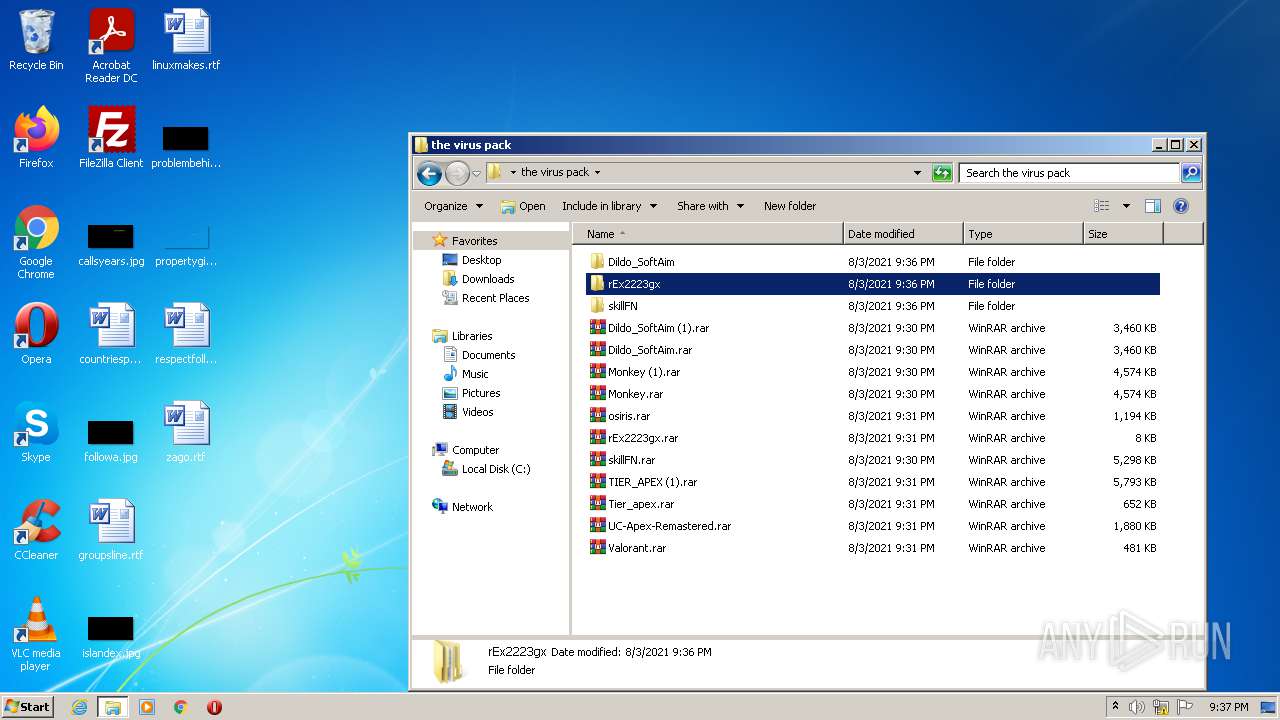
MALICIOUS
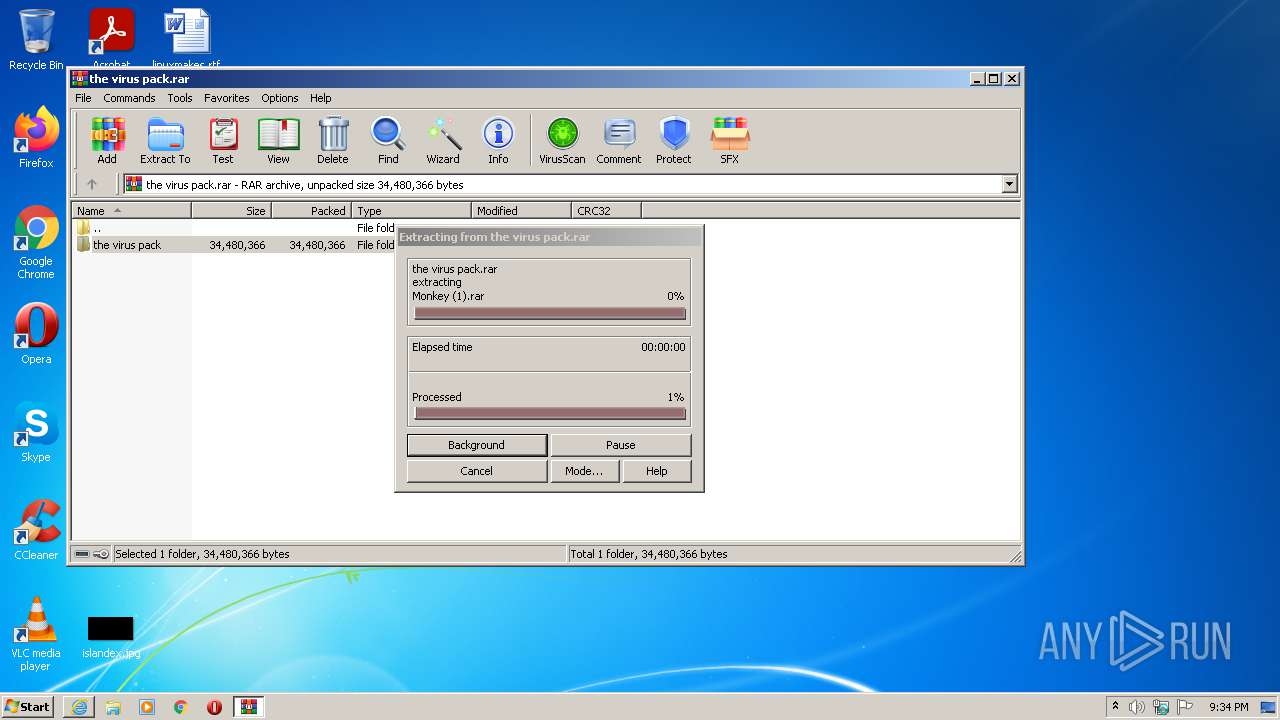
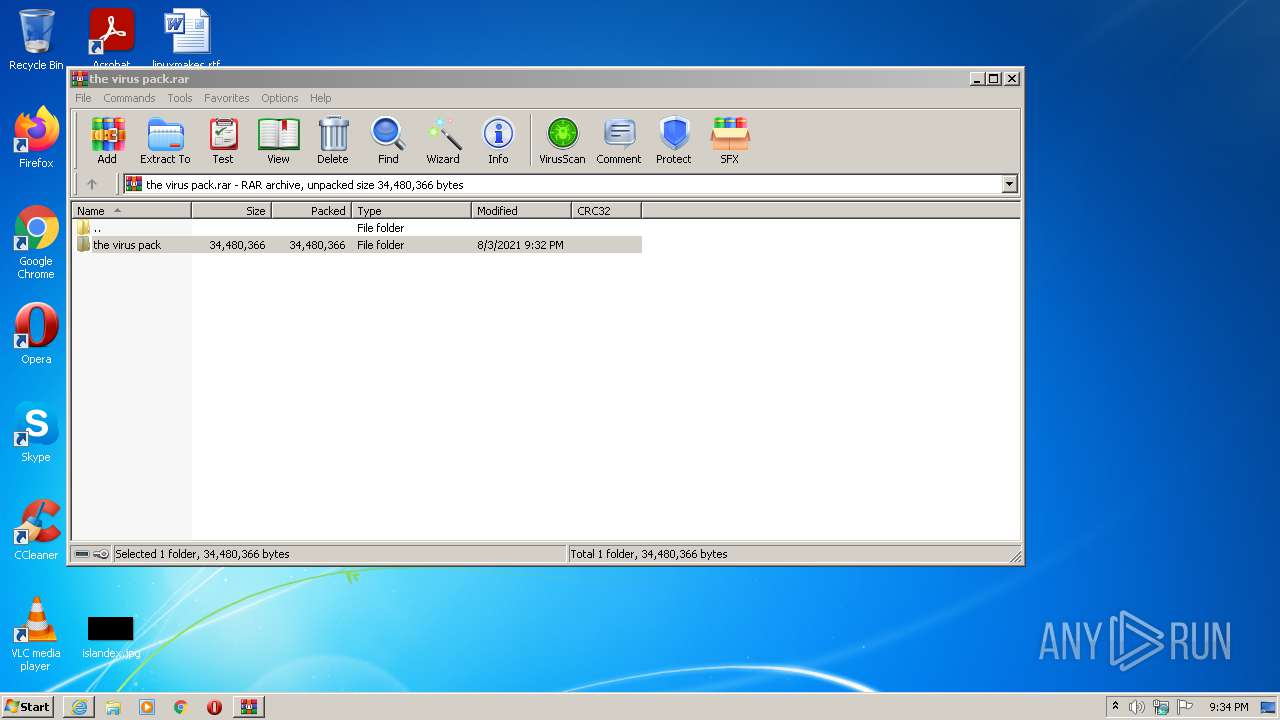
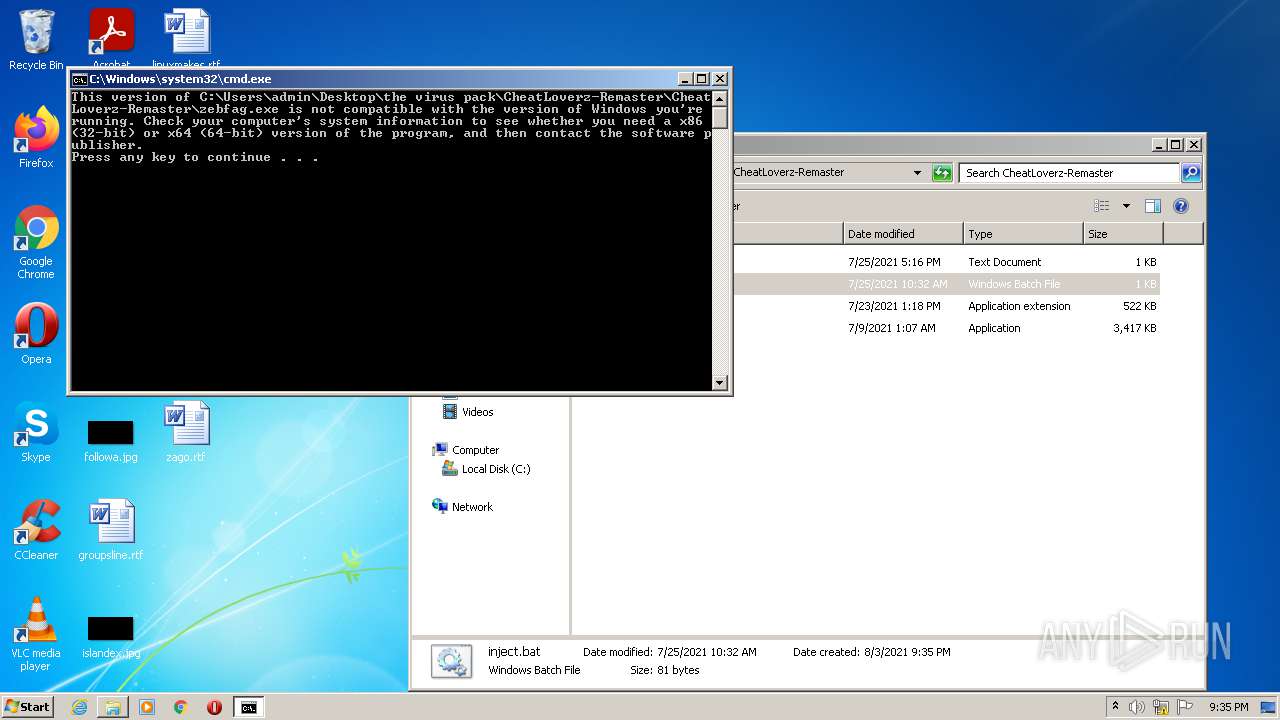
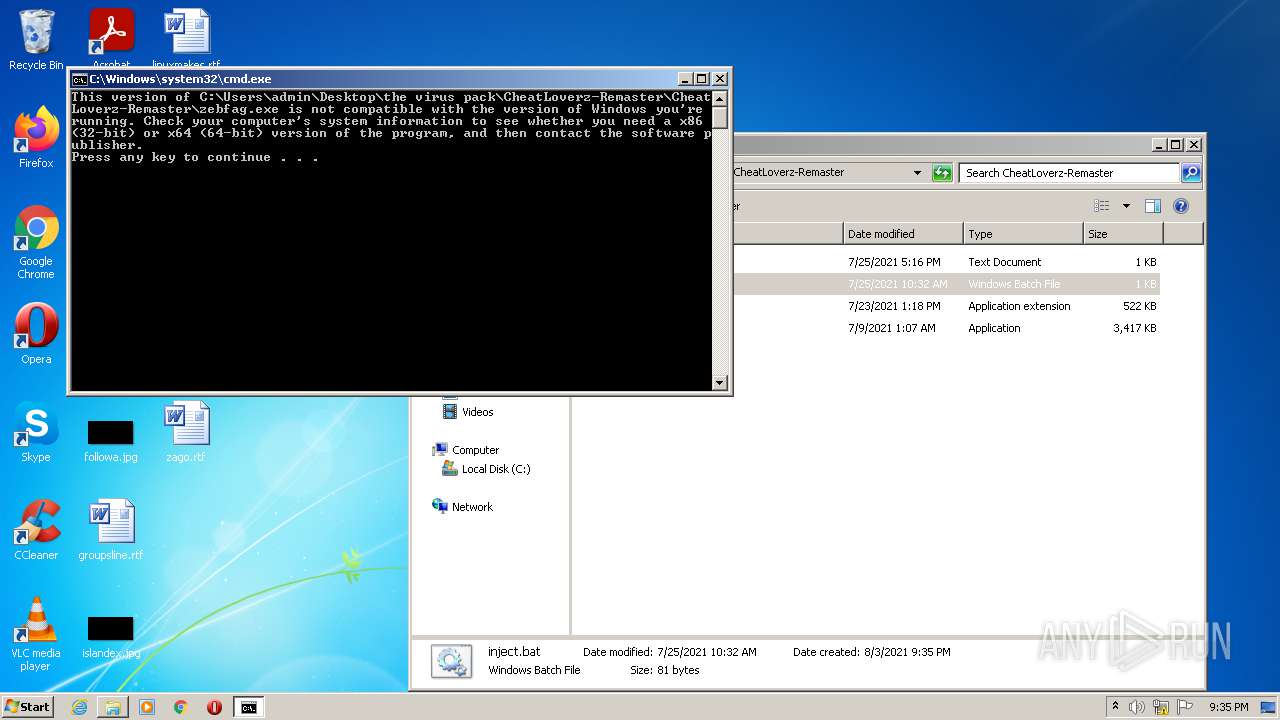
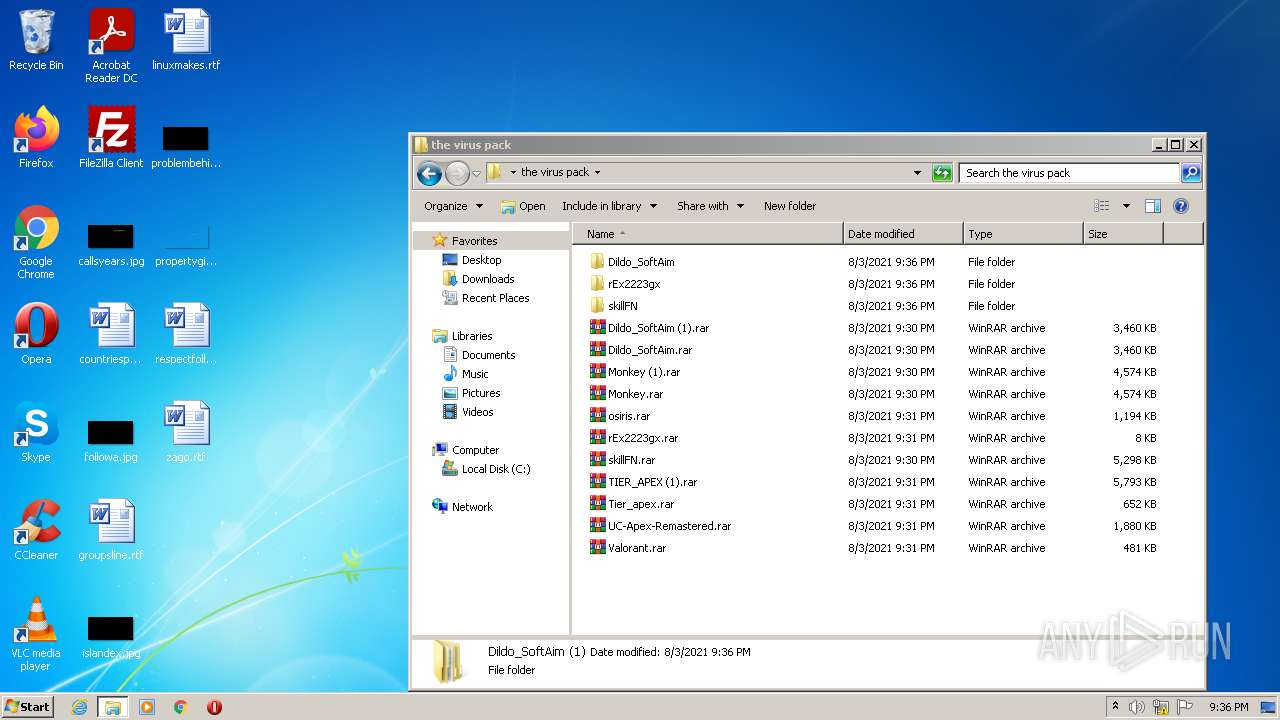
Drops executable file immediately after starts
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 3392)
- WinRAR.exe (PID: 2592)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2256)
Reads the computer name
- WinRAR.exe (PID: 2520)
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- cmd.exe (PID: 3296)
- WinRAR.exe (PID: 2668)
- cmd.exe (PID: 2680)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 2592)
- WinRAR.exe (PID: 3392)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 1664)
Checks supported languages
- WinRAR.exe (PID: 2520)
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- cmd.exe (PID: 3296)
- WinRAR.exe (PID: 2668)
- cmd.exe (PID: 2680)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 3392)
- WinRAR.exe (PID: 2592)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 1664)
- cmd.exe (PID: 2016)
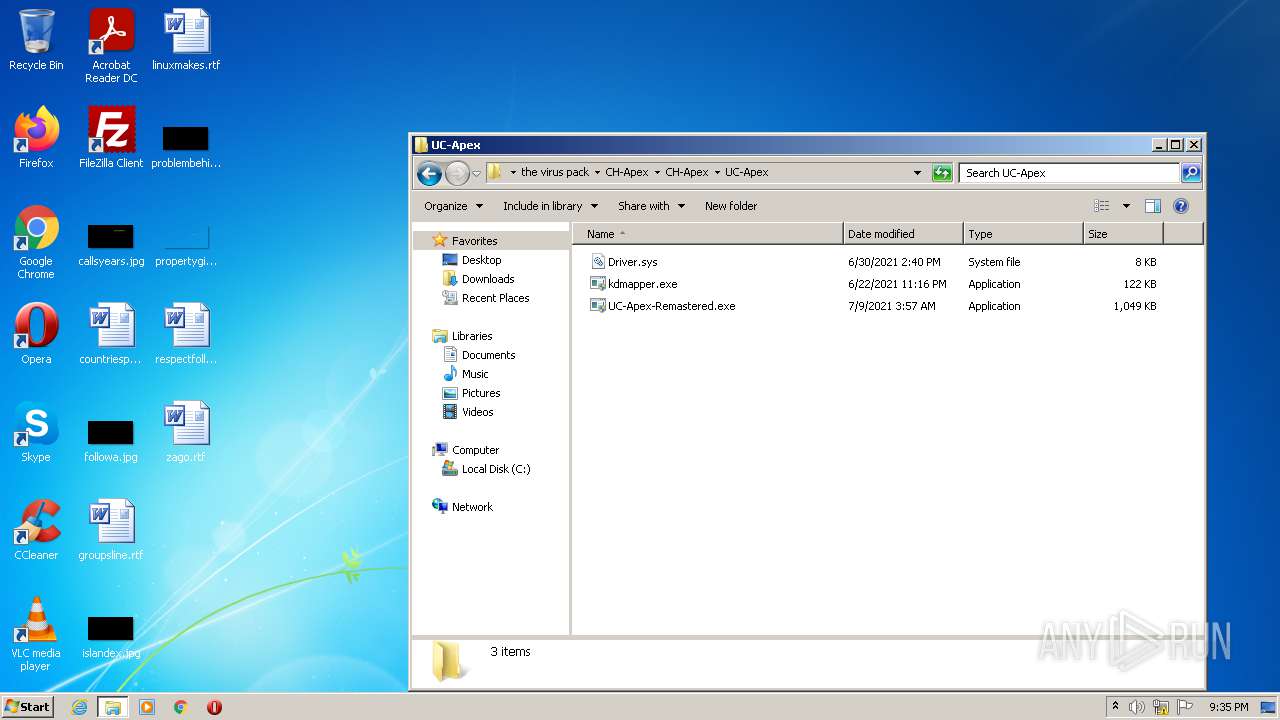
Drops a file with a compile date too recent
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 2592)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 2592)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 3392)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 696)
- WinRAR.exe (PID: 2092)
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 3392)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 2592)
Drops a file with too old compile date
- WinRAR.exe (PID: 3392)
INFO
Checks supported languages
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 2256)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3944)
- NOTEPAD.EXE (PID: 3560)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 340)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3344)
- NOTEPAD.EXE (PID: 1844)
- chrome.exe (PID: 2724)
Application launched itself
- iexplore.exe (PID: 4060)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 2040)
Changes internet zones settings
- iexplore.exe (PID: 4060)
Reads the computer name
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 4060)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 340)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3344)
Checks Windows Trust Settings
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 2256)
Reads settings of System Certificates
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 4060)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2568)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4060)
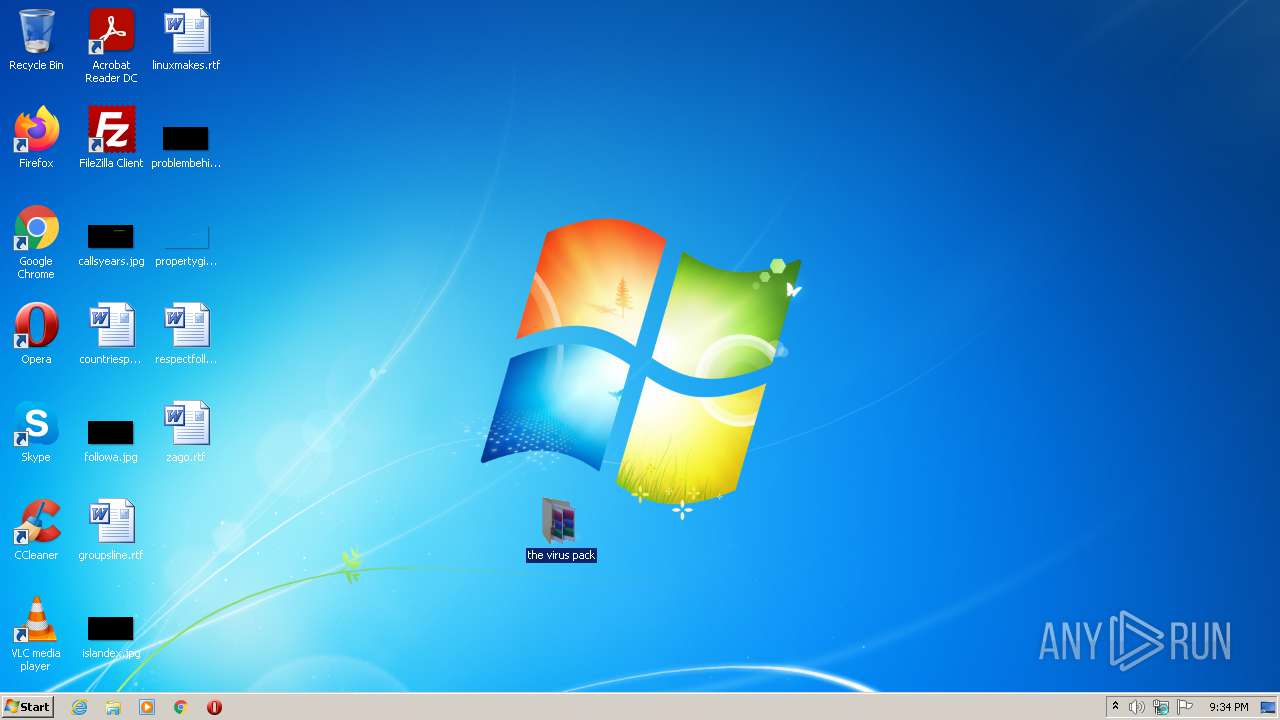
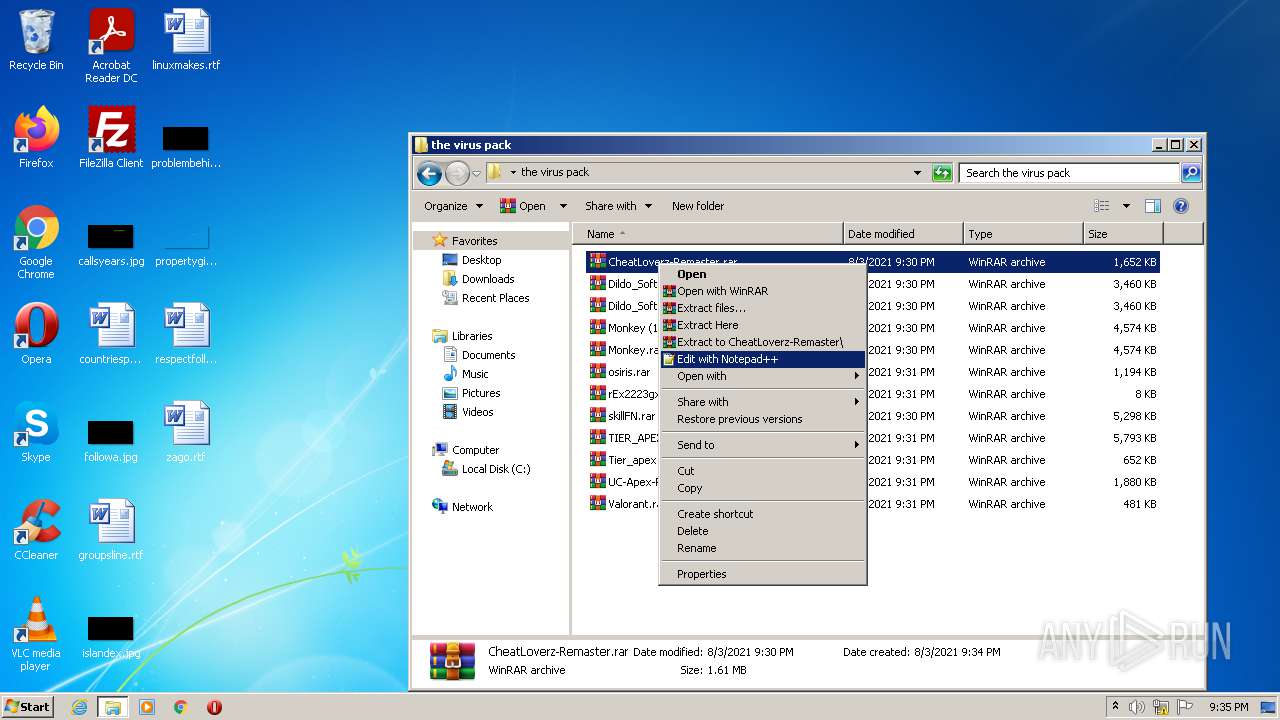
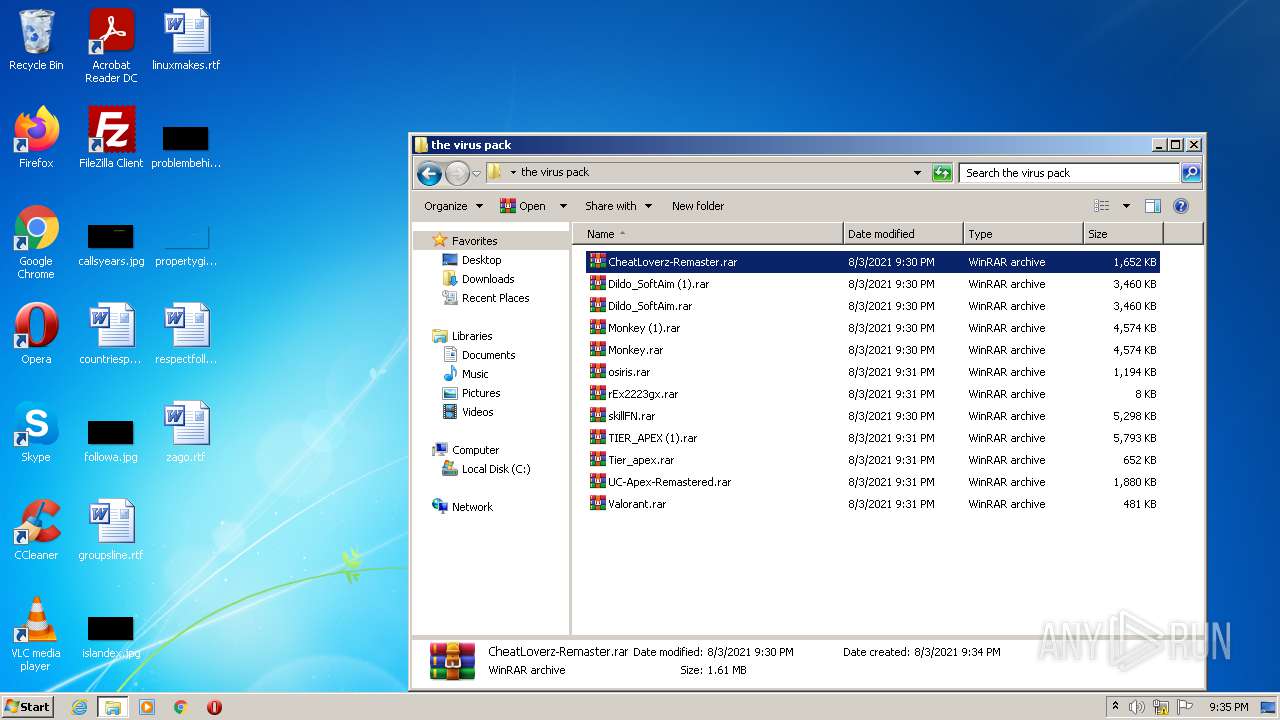
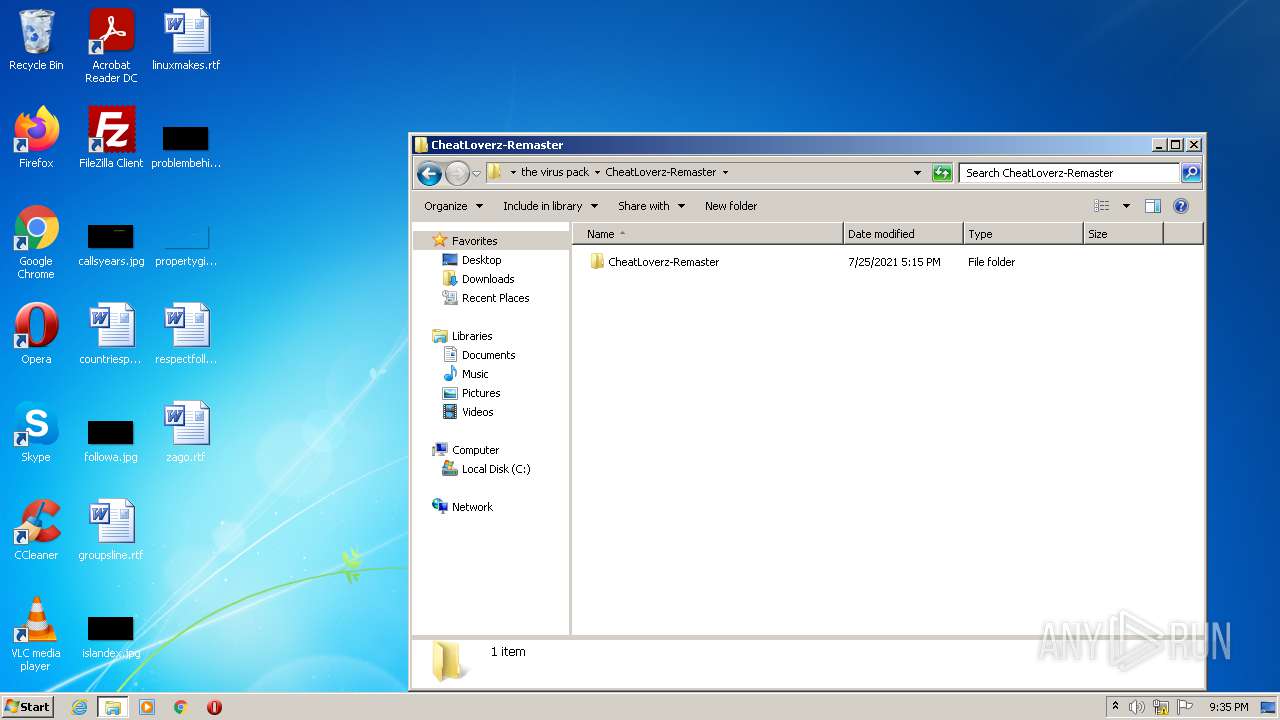
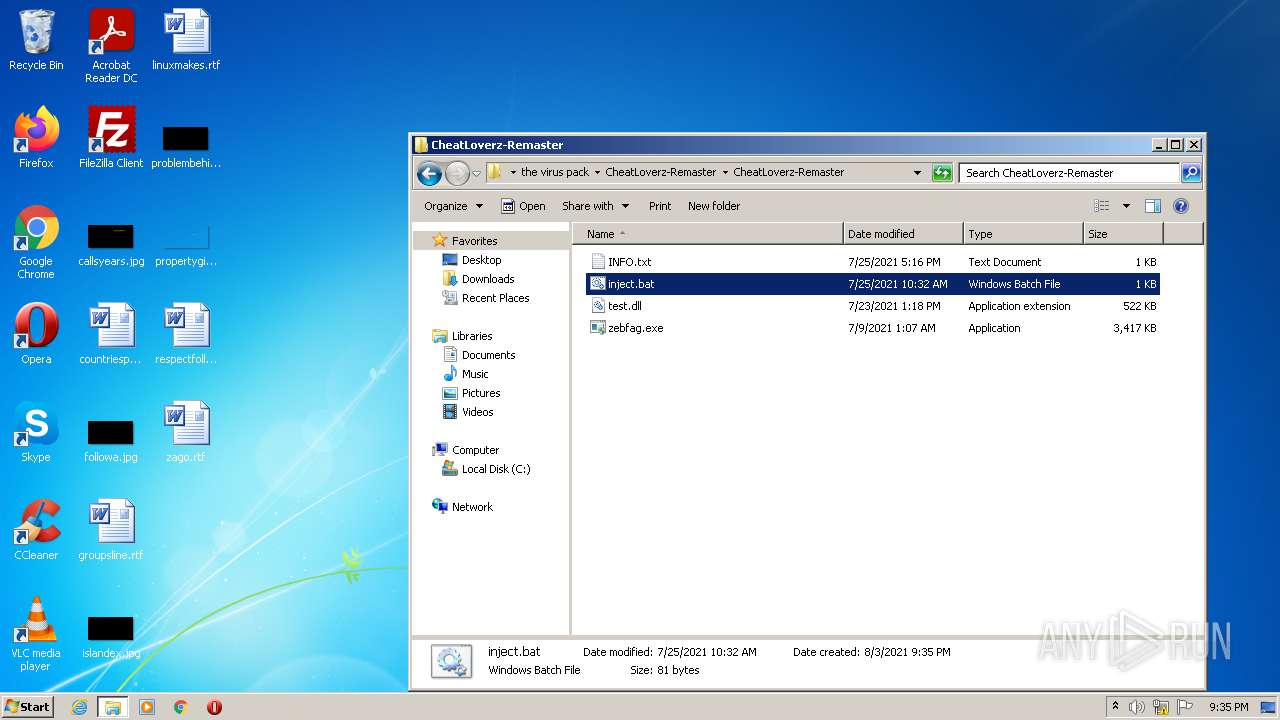
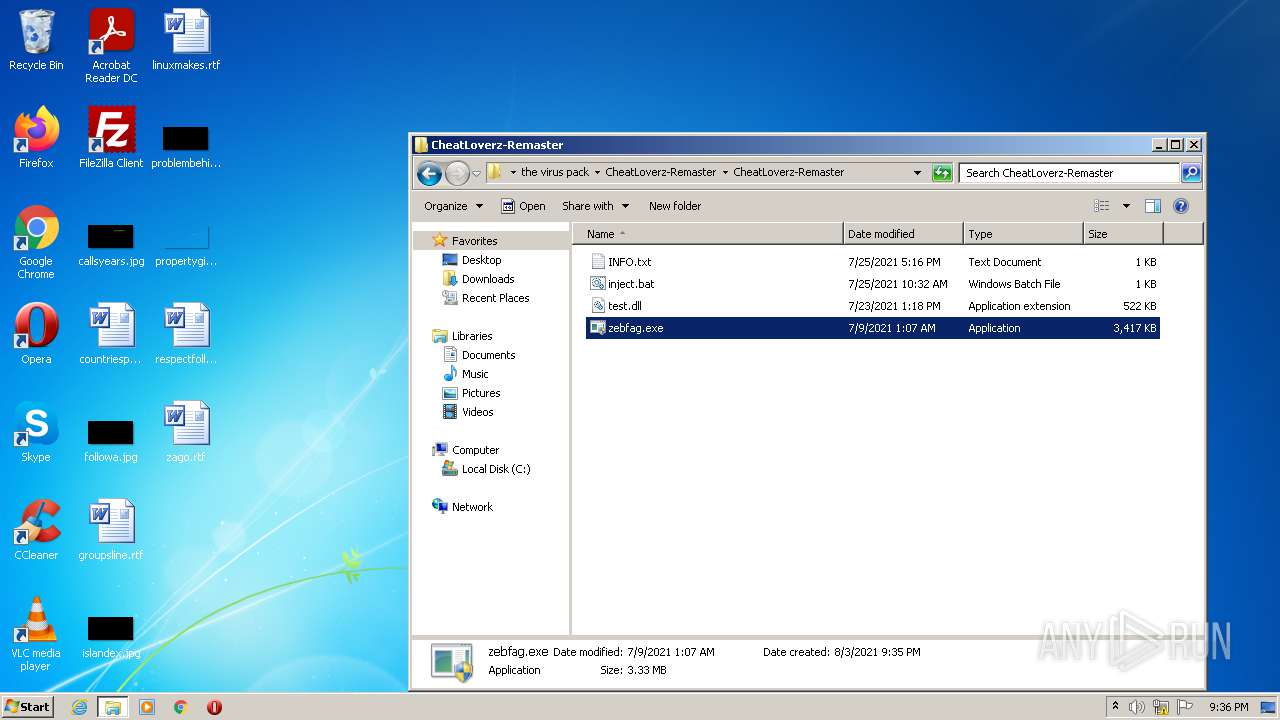
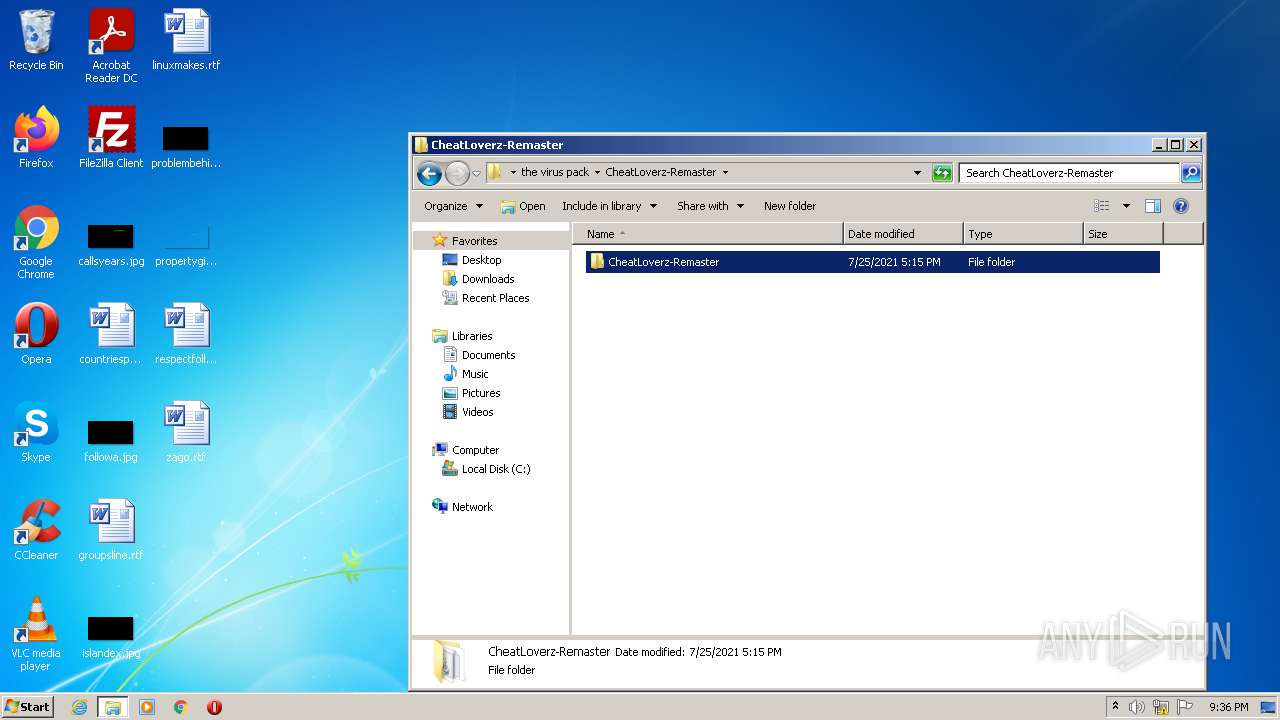
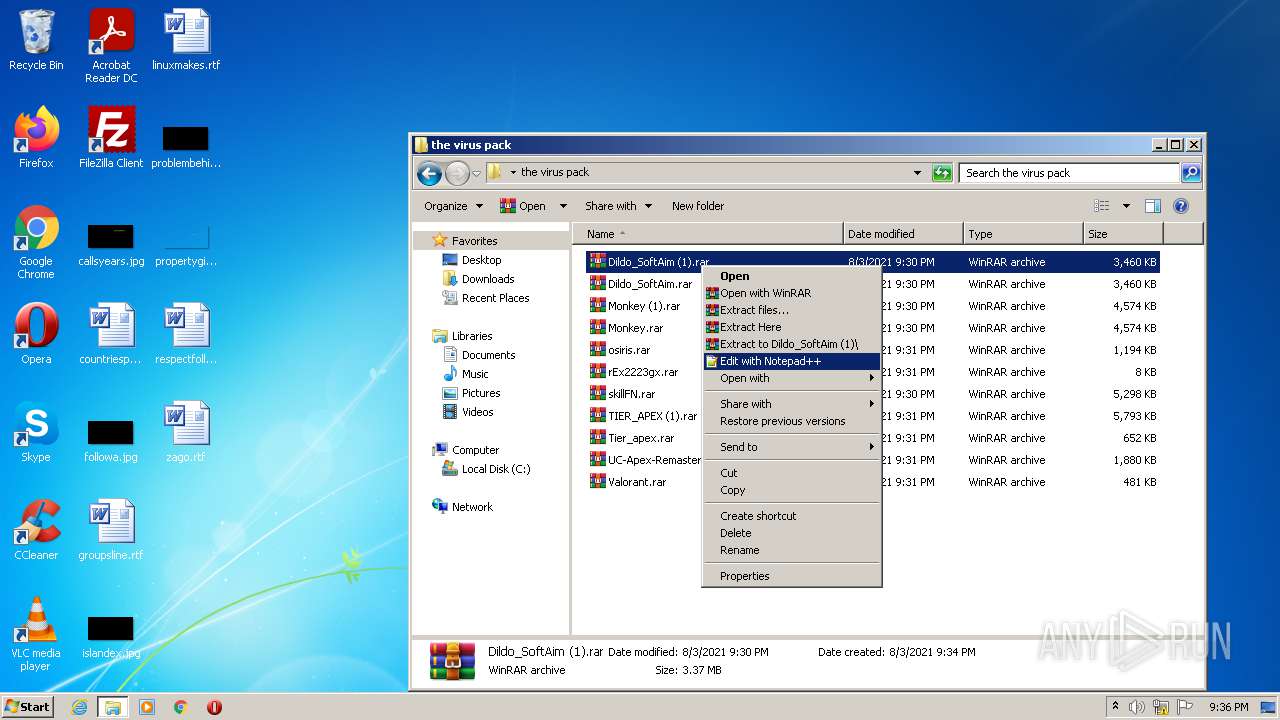
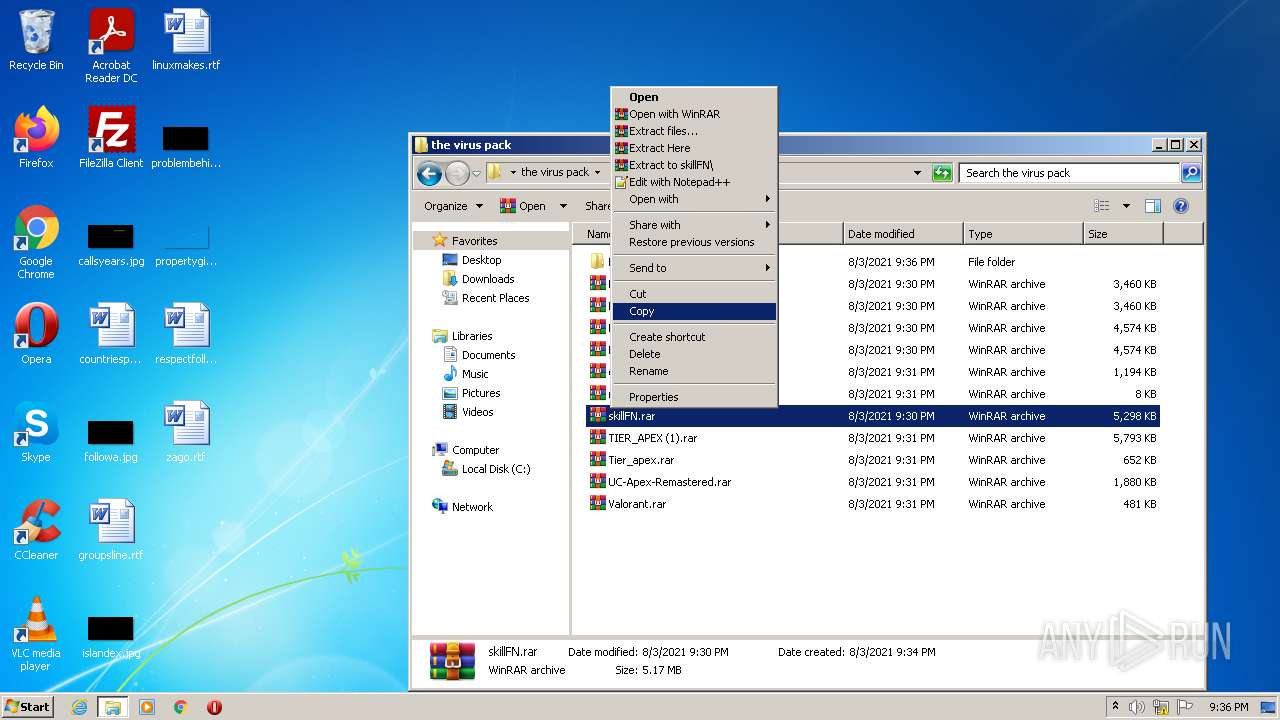
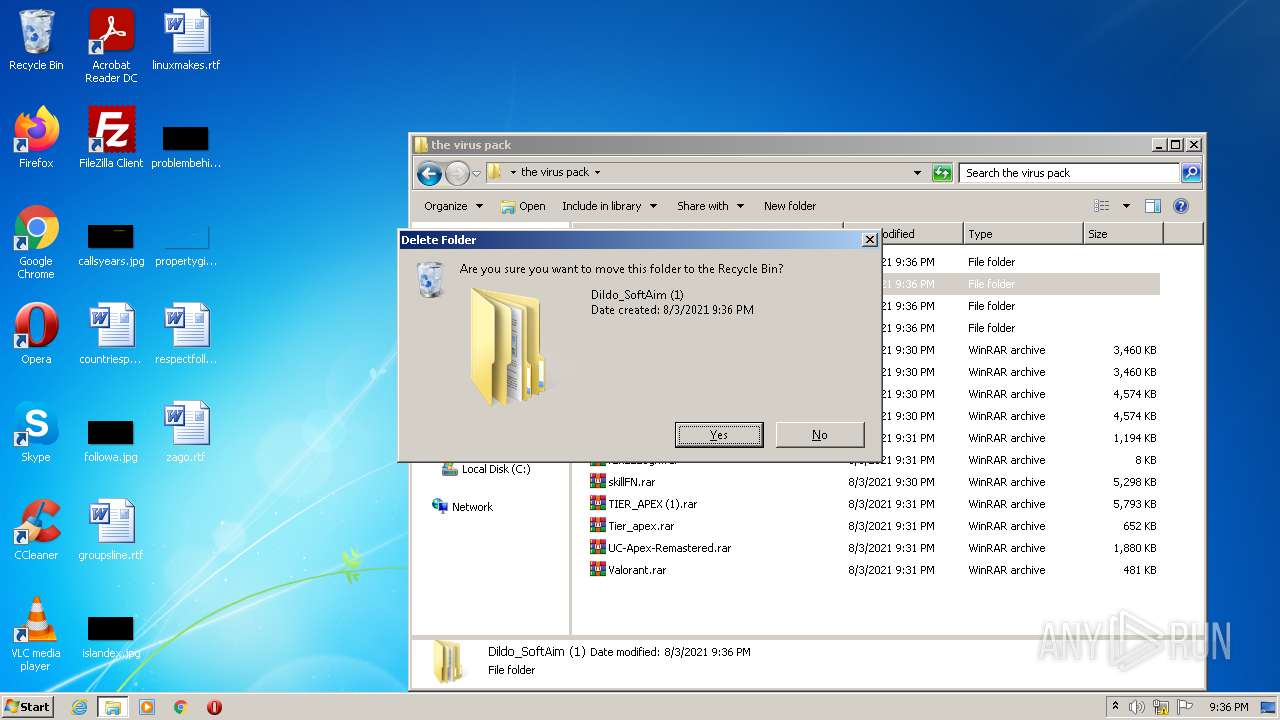
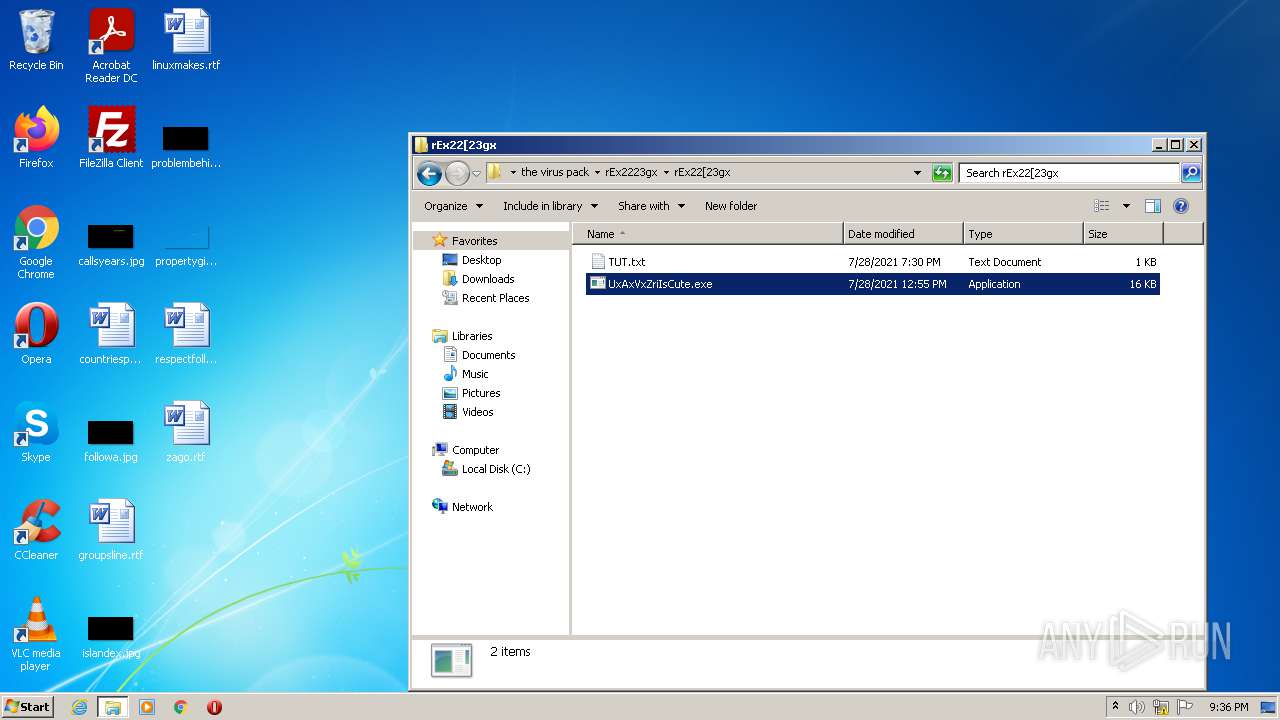
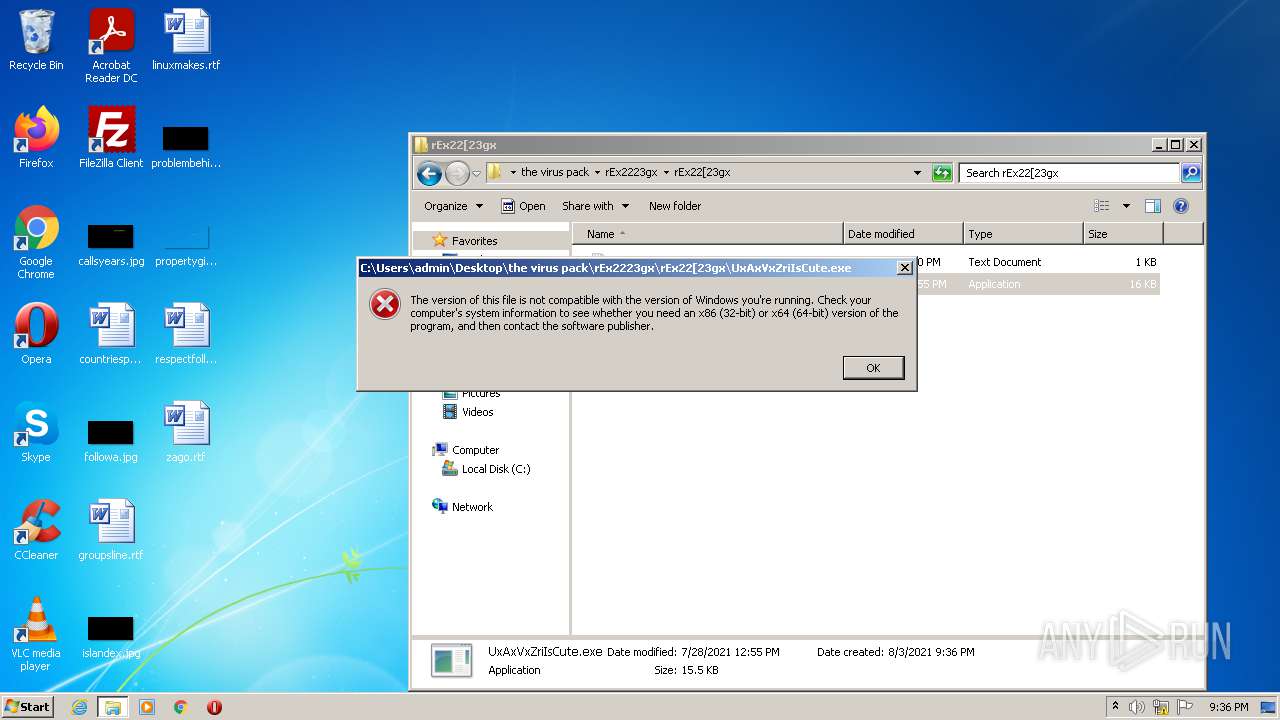
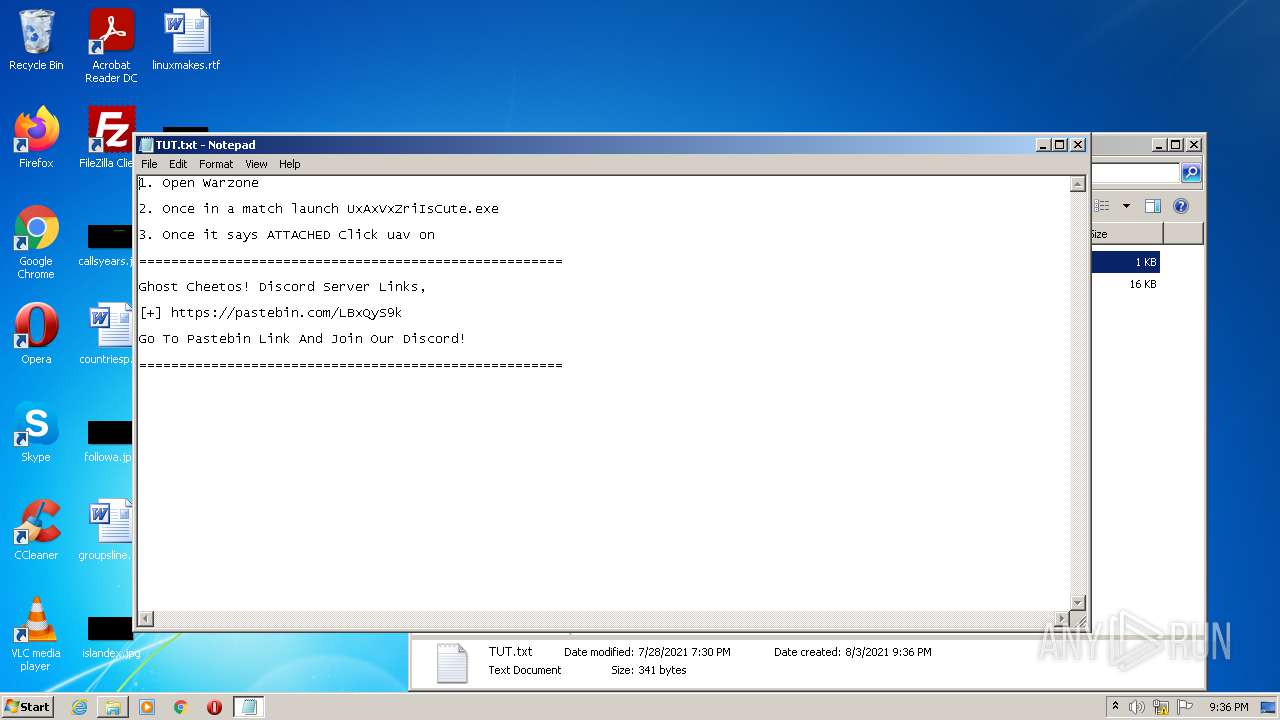
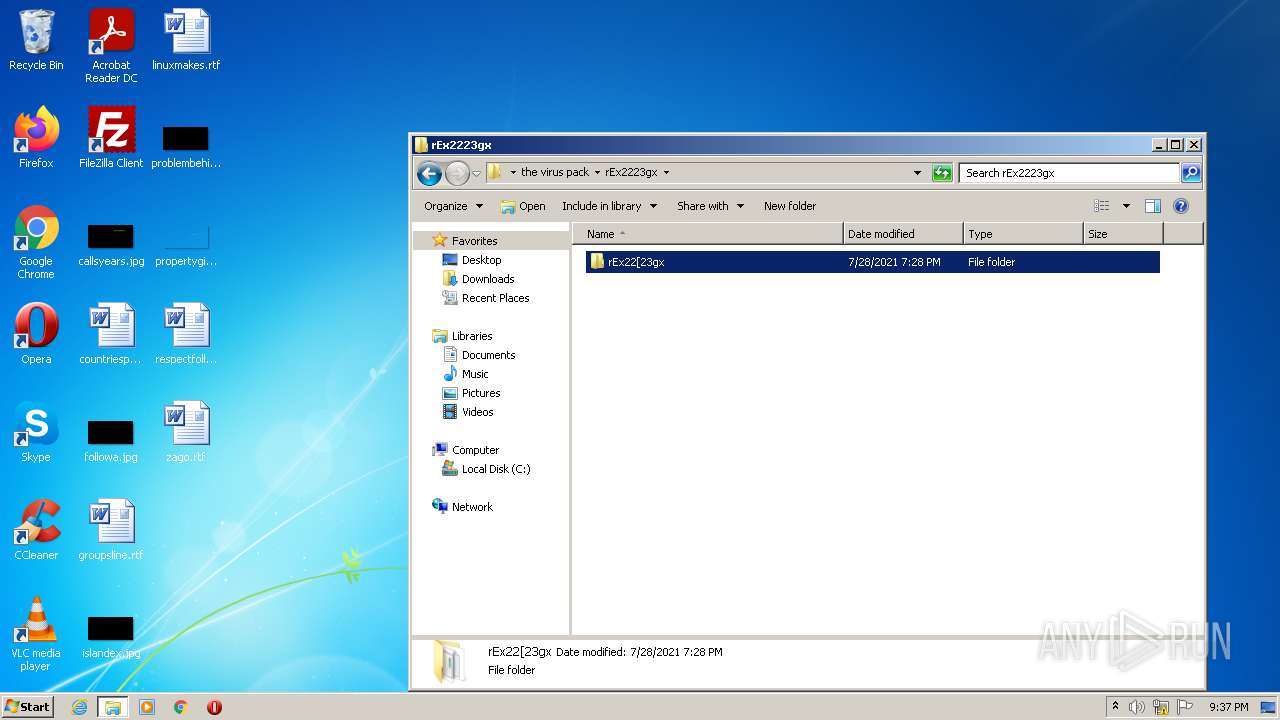
Manual execution by user
- WinRAR.exe (PID: 696)
- cmd.exe (PID: 3296)
- WinRAR.exe (PID: 2092)
- WinRAR.exe (PID: 2668)
- cmd.exe (PID: 2680)
- WinRAR.exe (PID: 3476)
- WinRAR.exe (PID: 3392)
- WinRAR.exe (PID: 2592)
- NOTEPAD.EXE (PID: 3560)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 1664)
- NOTEPAD.EXE (PID: 1844)
Reads the date of Windows installation
- iexplore.exe (PID: 4060)
Creates files in the user directory
- iexplore.exe (PID: 2256)
Reads internet explorer settings
- iexplore.exe (PID: 2256)
Reads the hosts file
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 2256)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
65
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,8093178686210324948,6192770892699774054,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1100 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
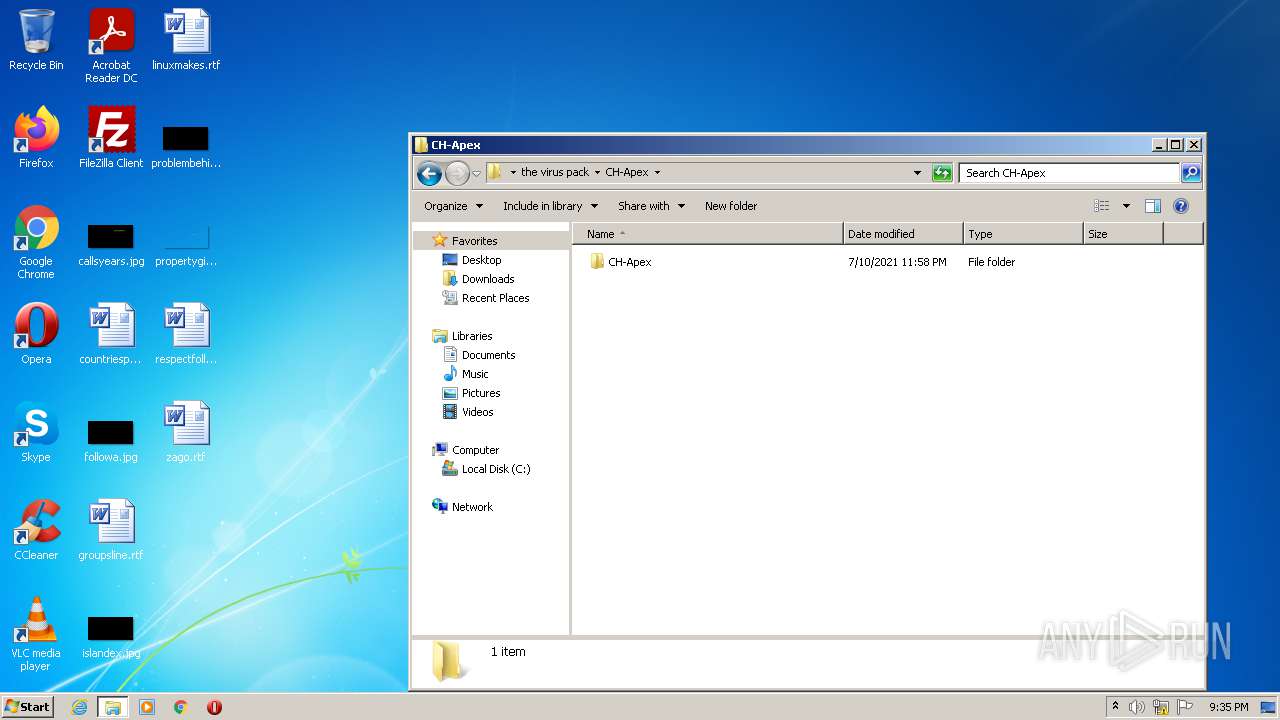
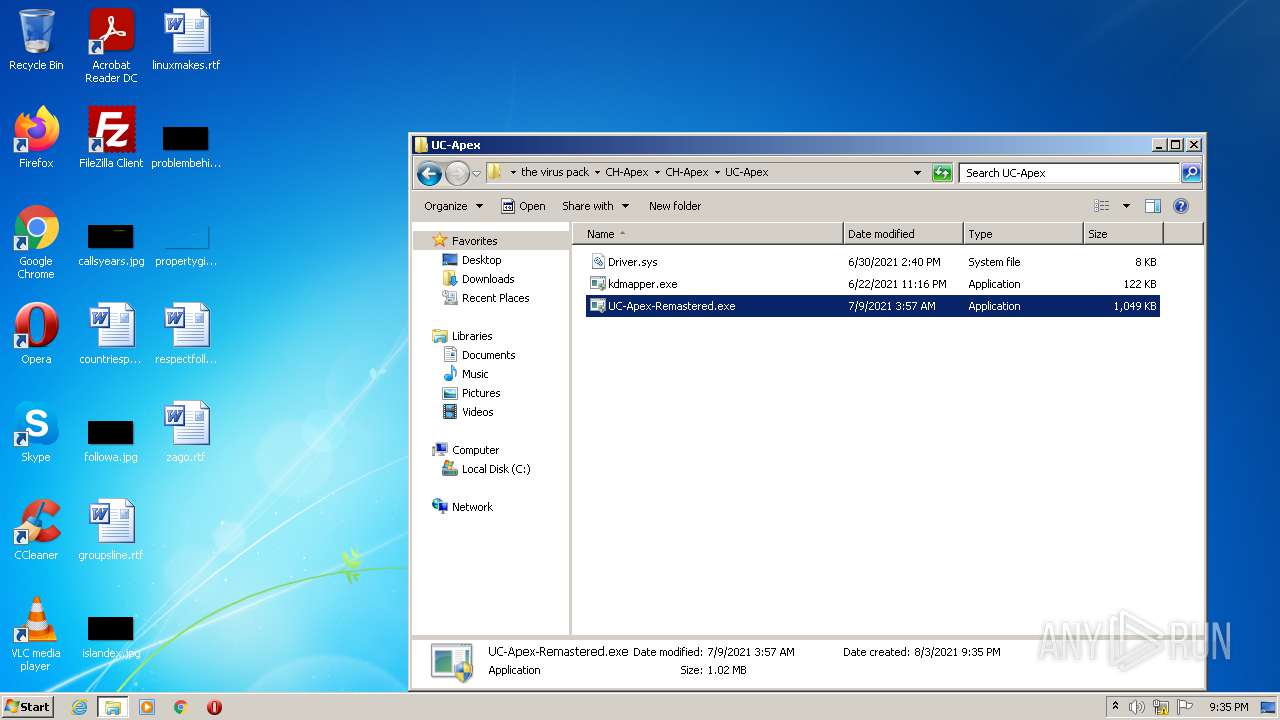
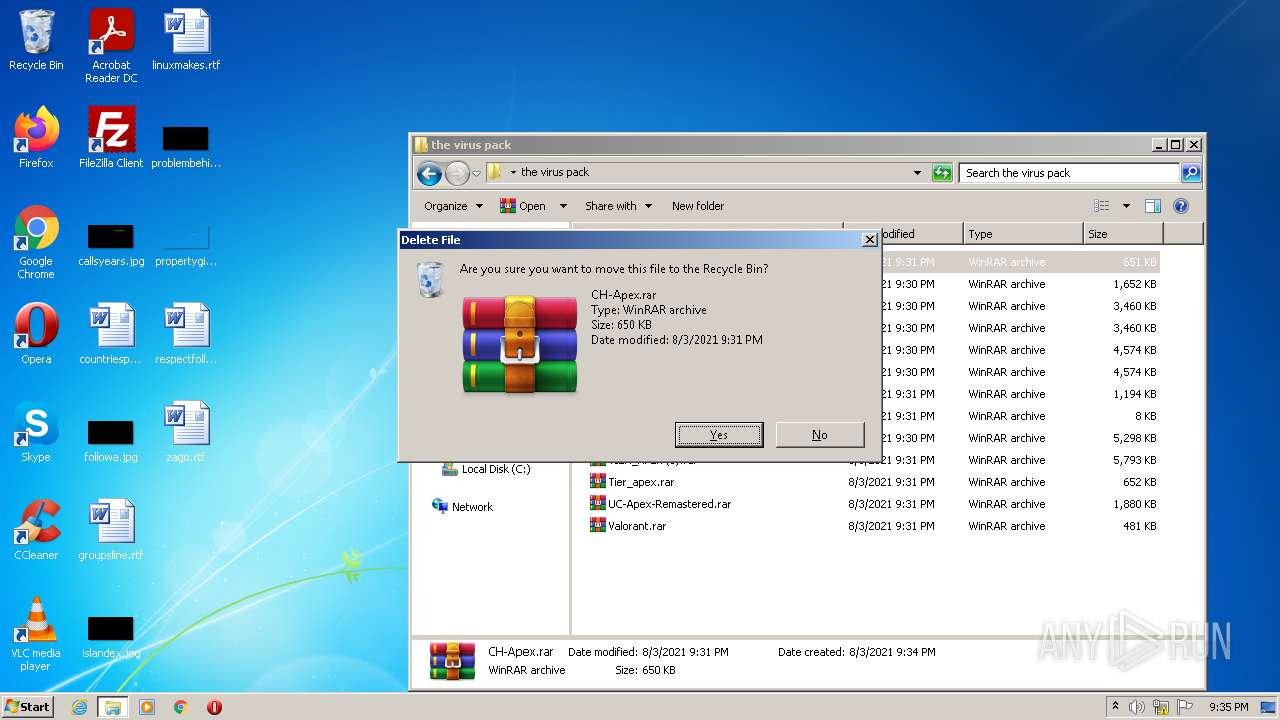
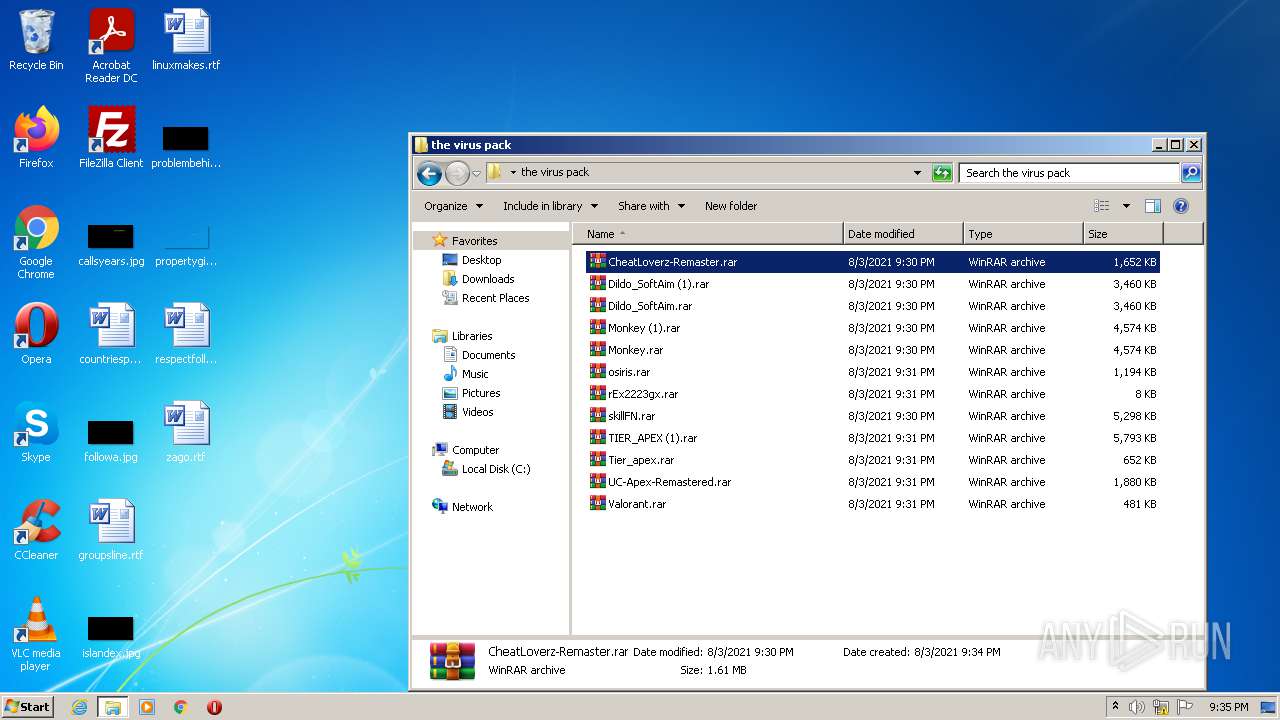
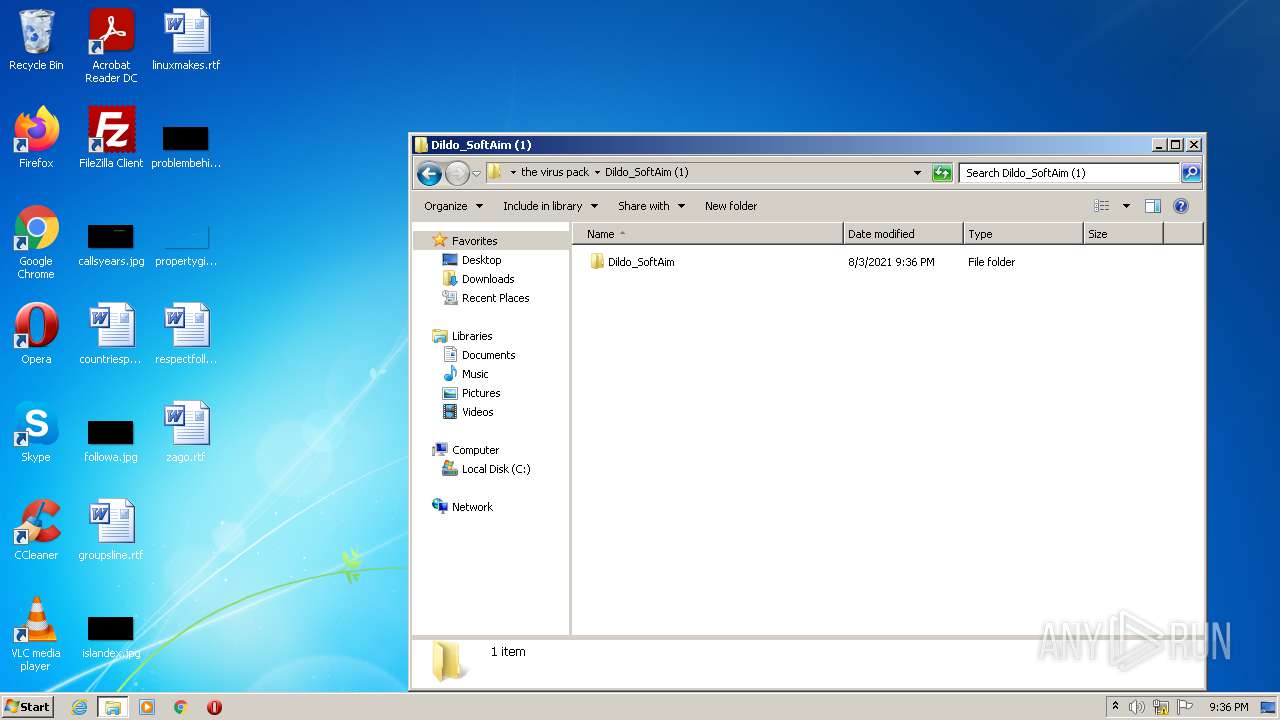
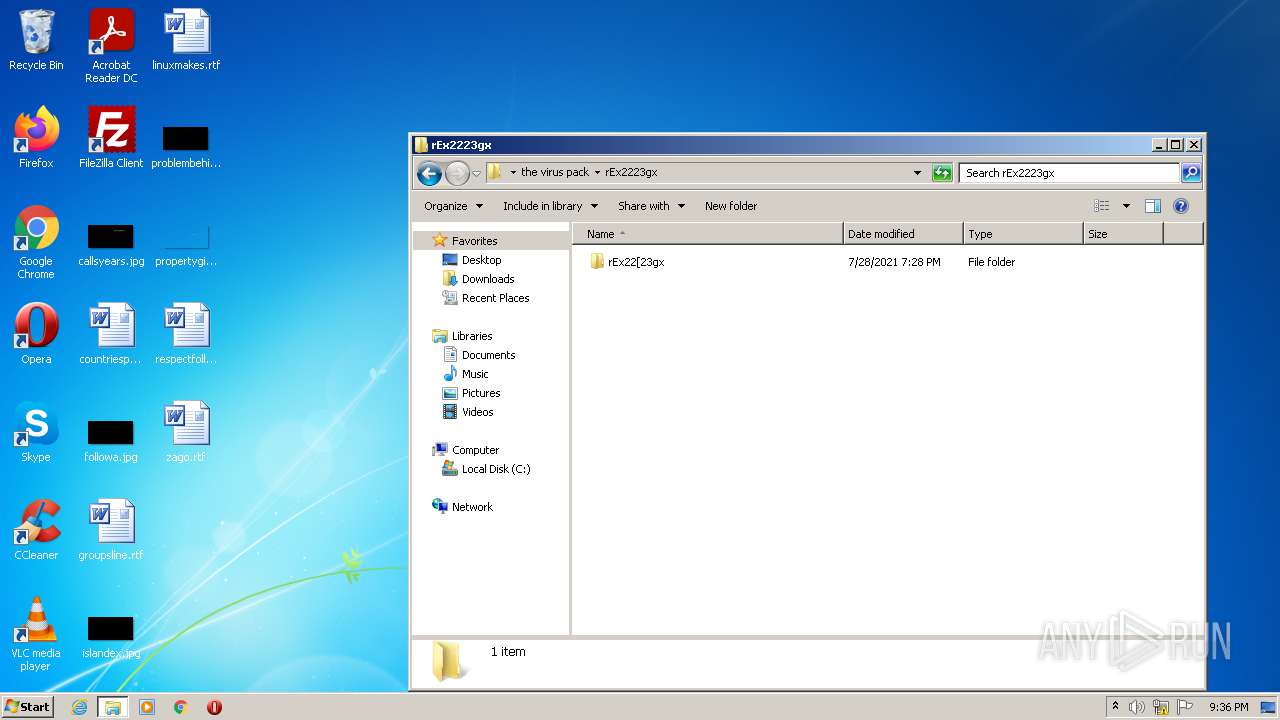
| 696 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\the virus pack\CH-Apex.rar" "C:\Users\admin\Desktop\the virus pack\CH-Apex\" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,10233983513077780358,1427299136919655004,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16810378302830936497,4036613833324357282,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,3399377800903861416,16647583446369369425,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,3399377800903861416,16647583446369369425,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1060,14554855897903734501,14264174327721057307,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3492 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1068,8093178686210324948,6192770892699774054,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
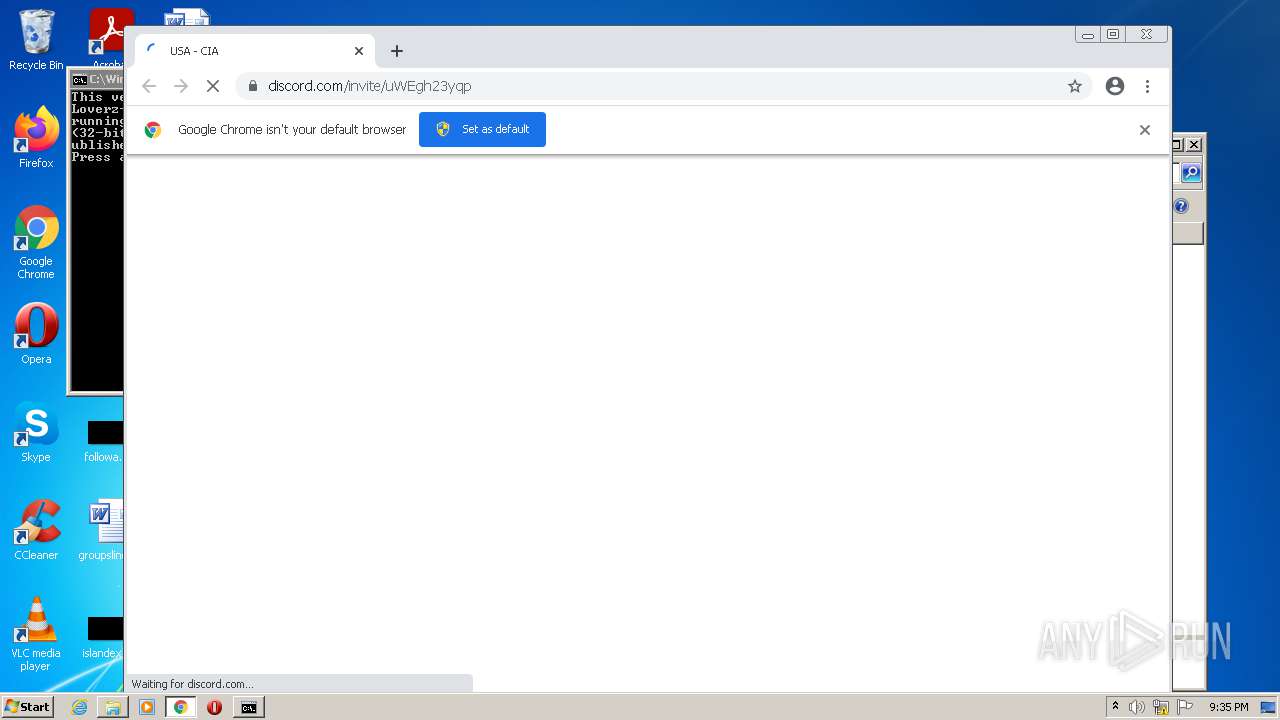
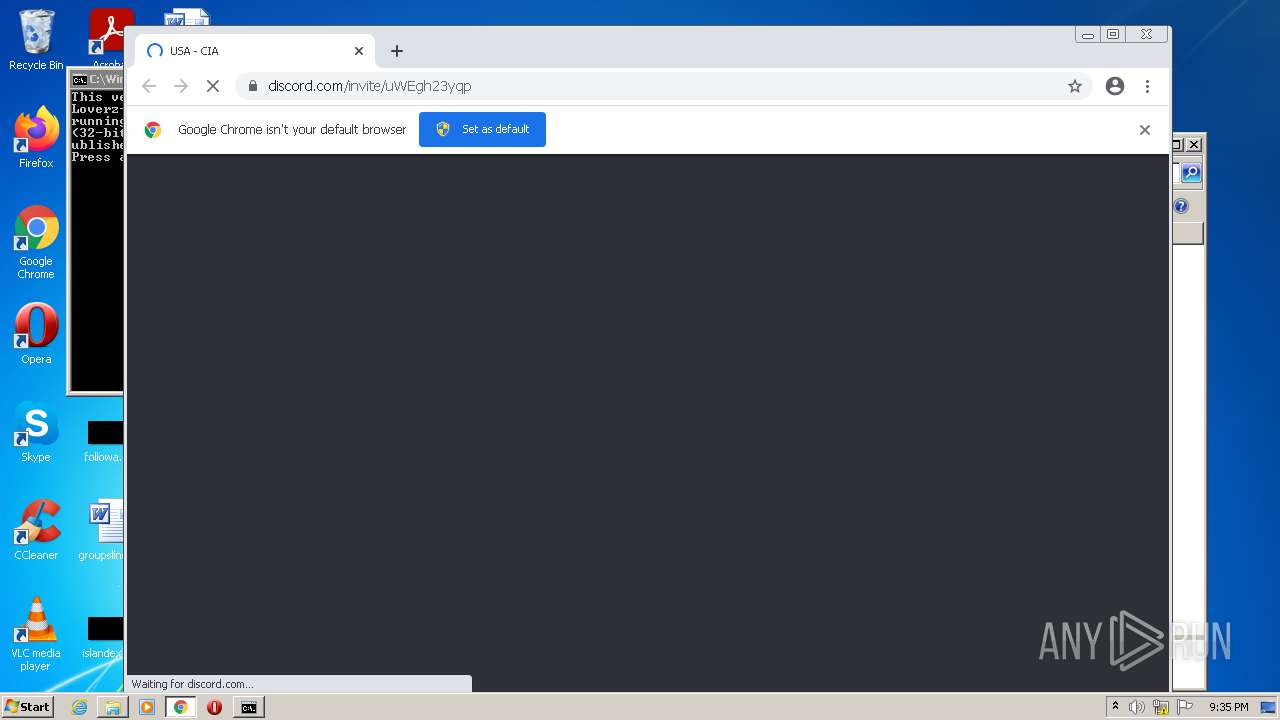
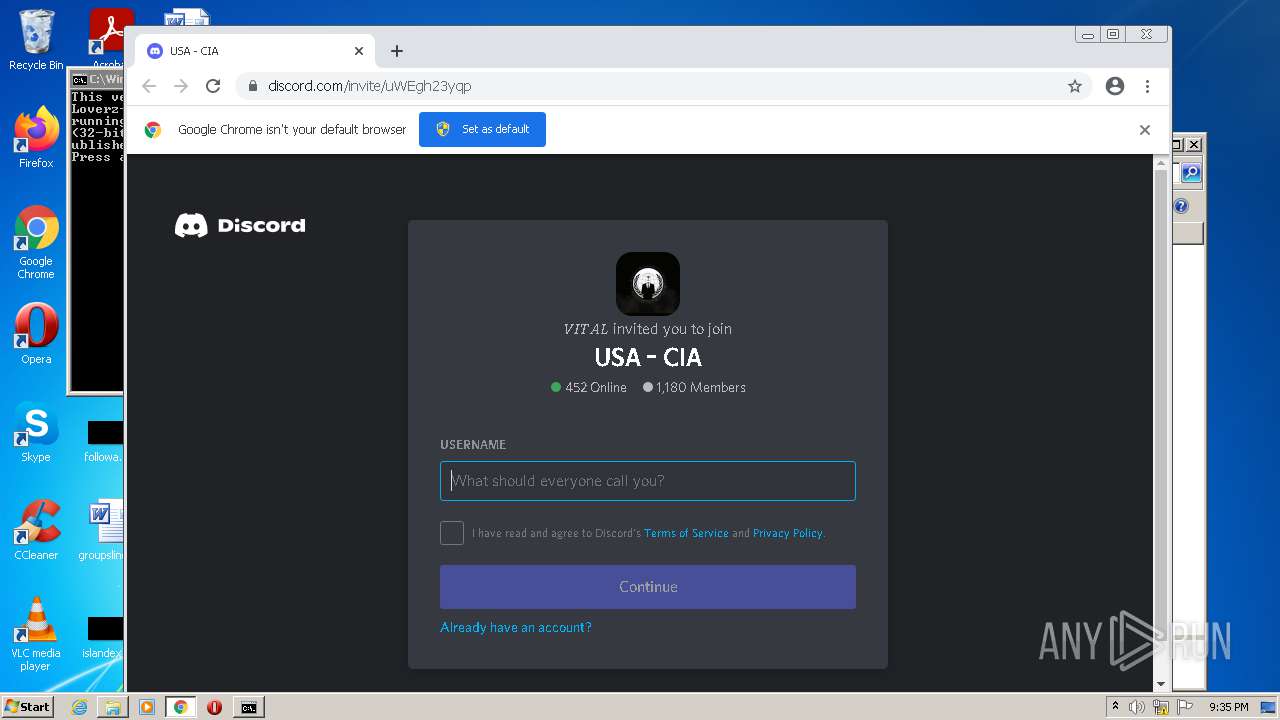
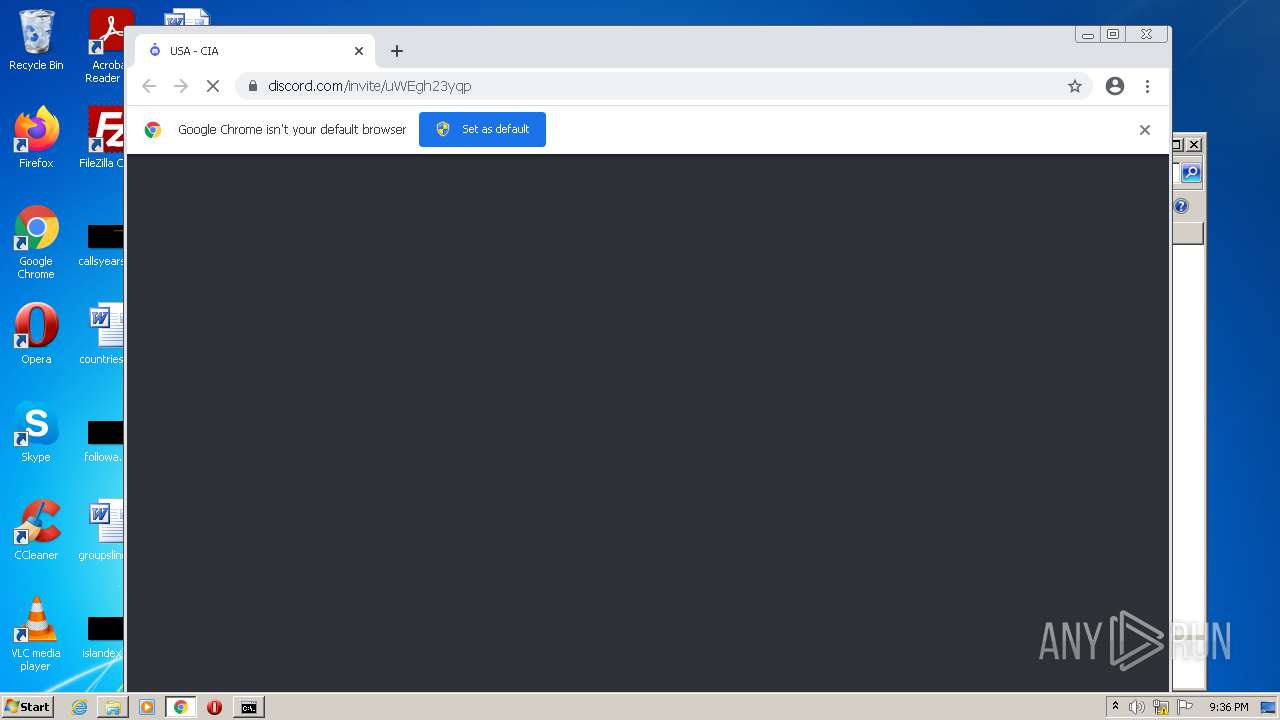
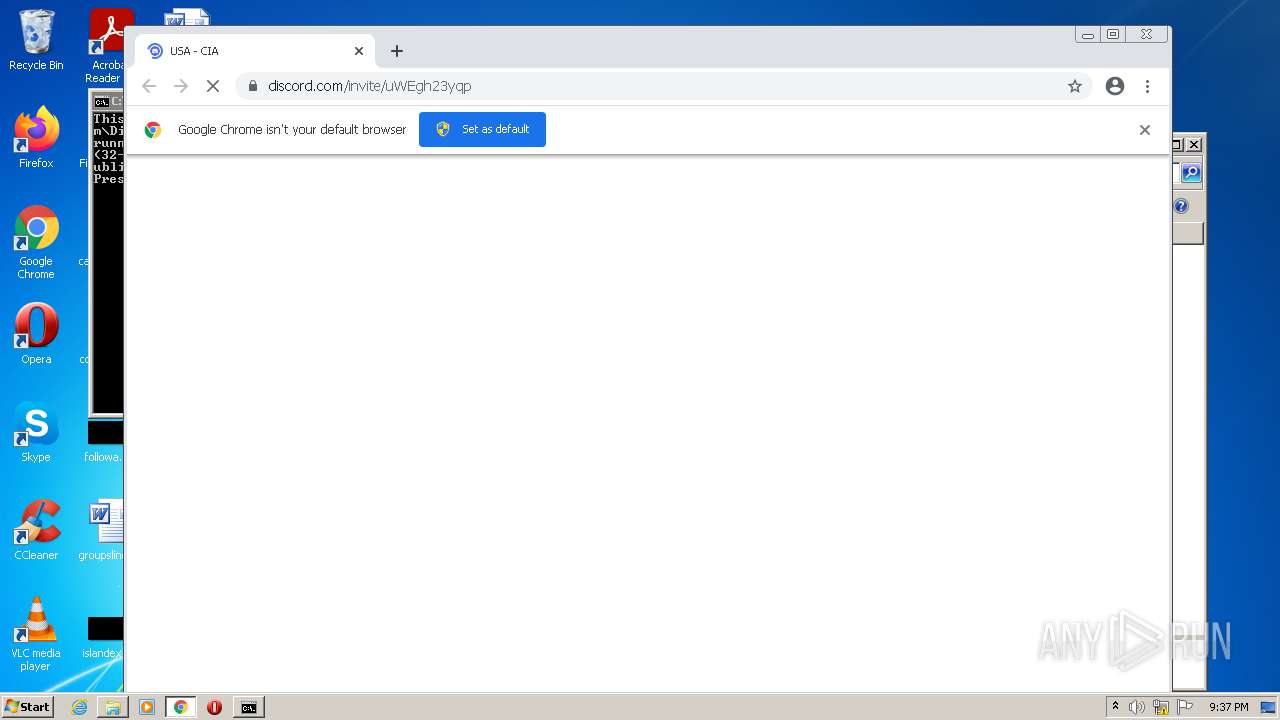
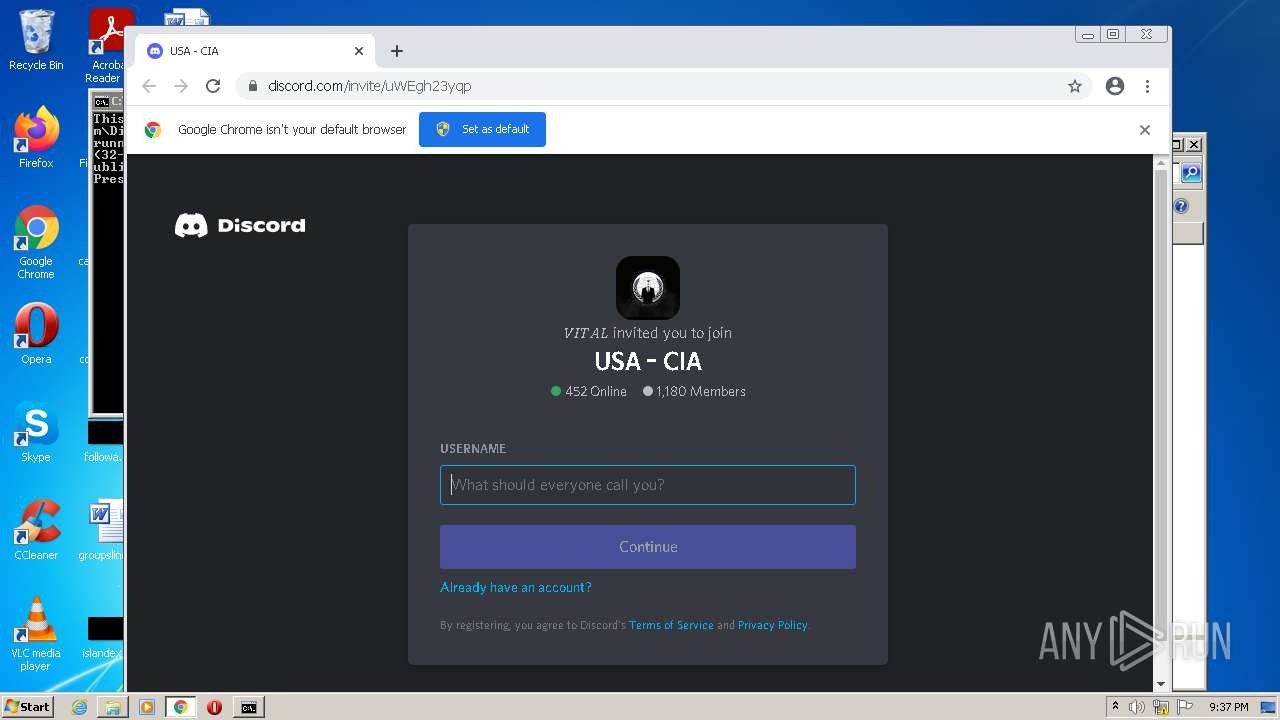
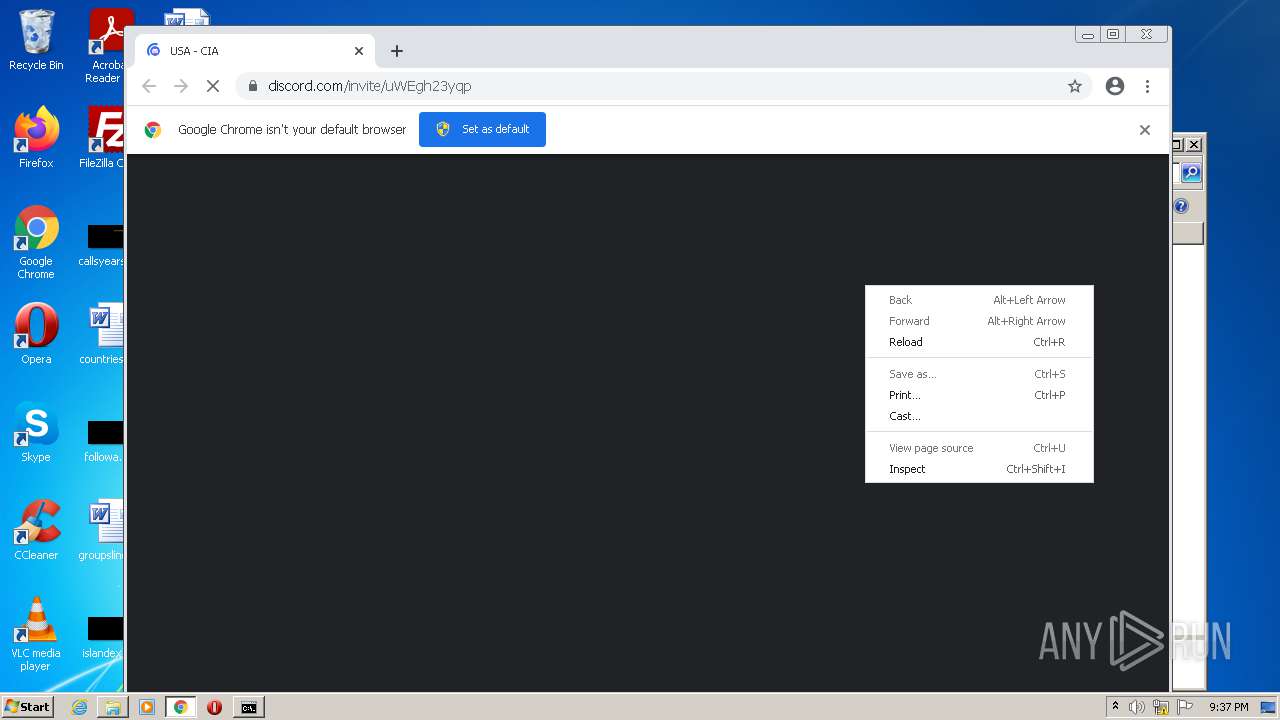
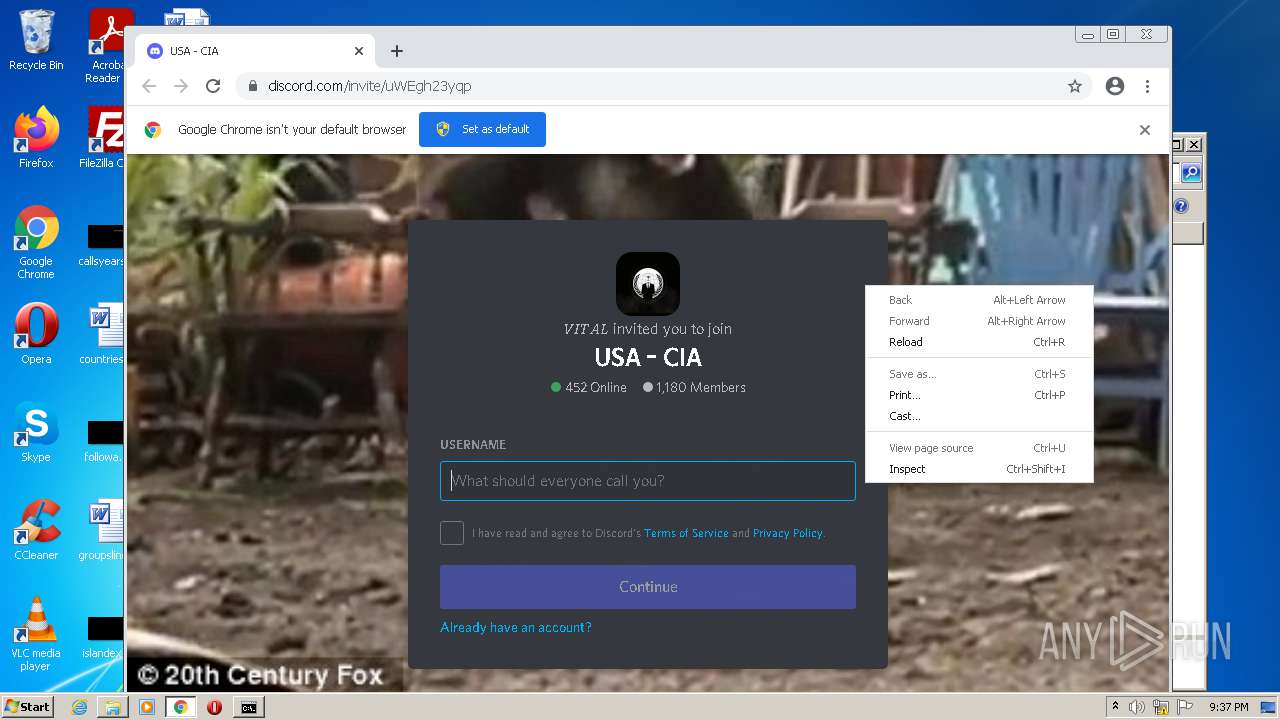
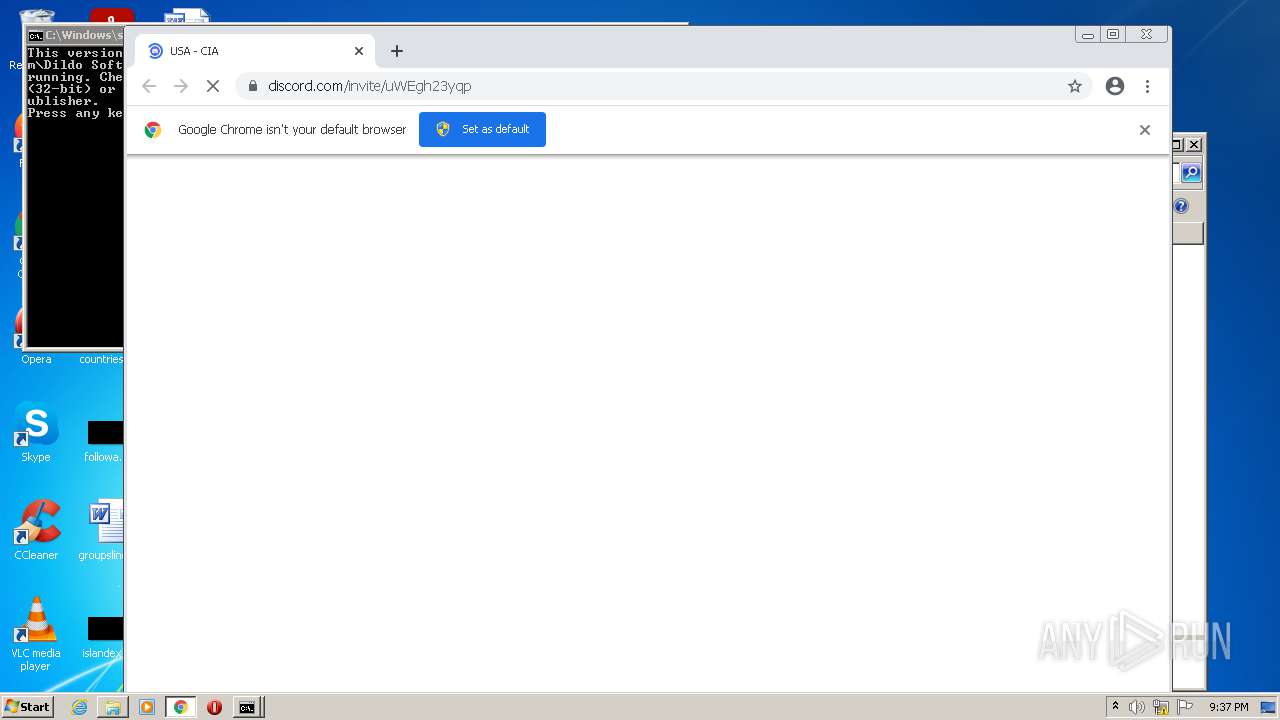
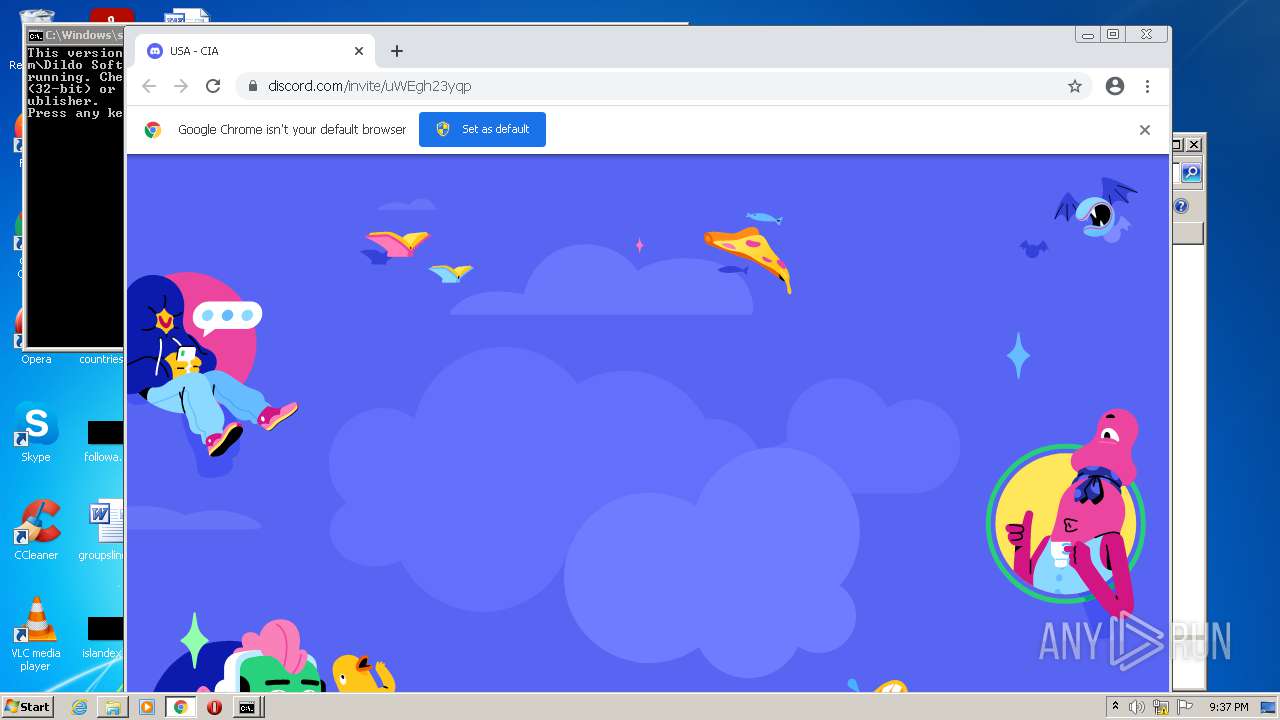
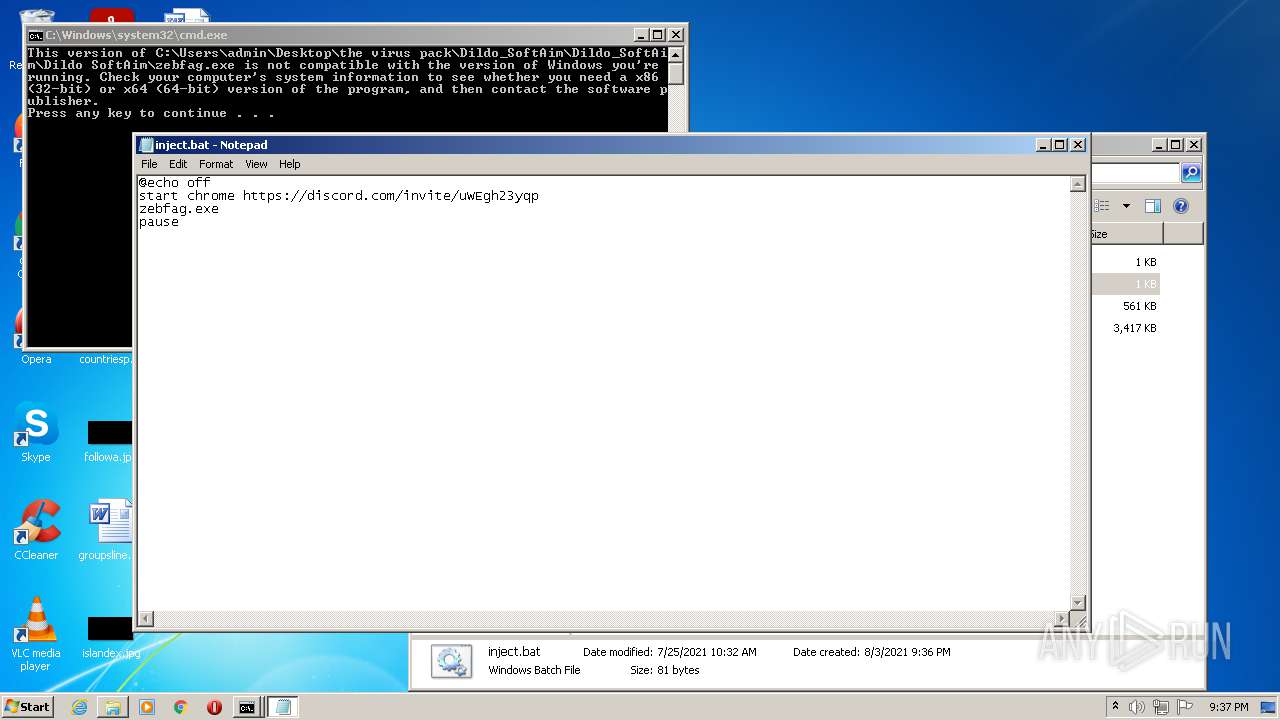
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://discord.com/invite/uWEgh23yqp | C:\Program Files\Google\Chrome\Application\chrome.exe | — | cmd.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
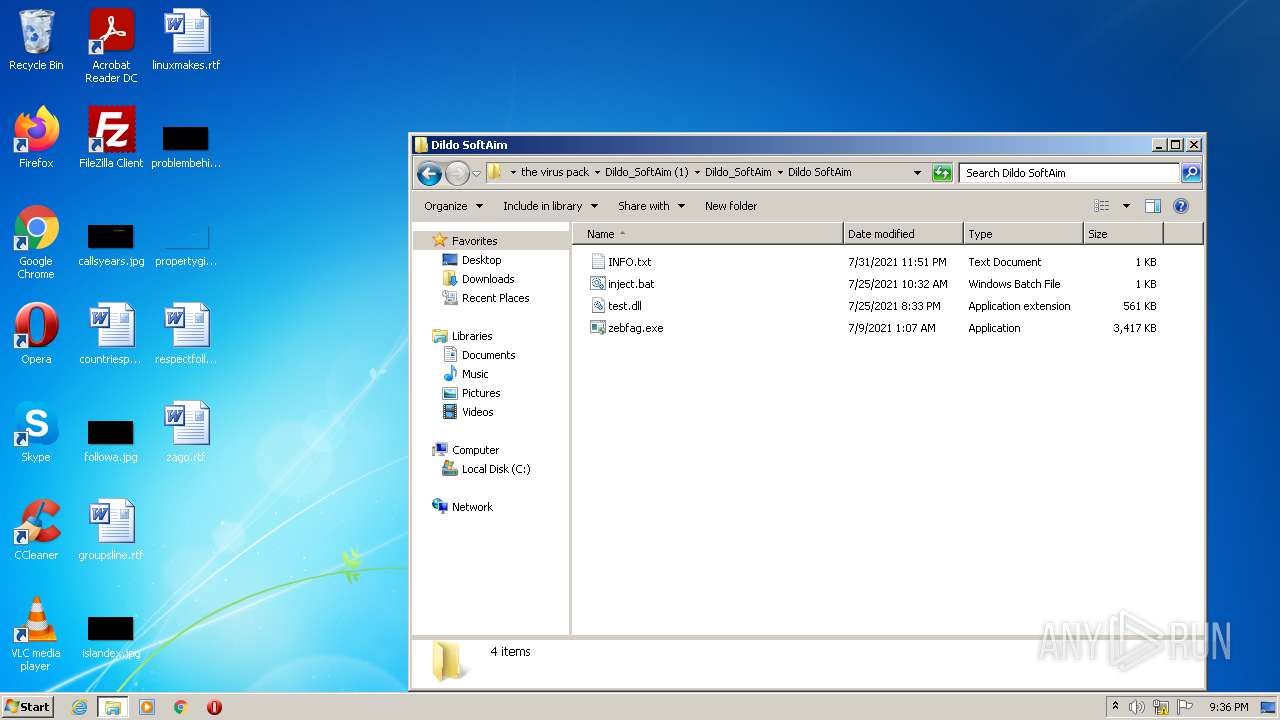
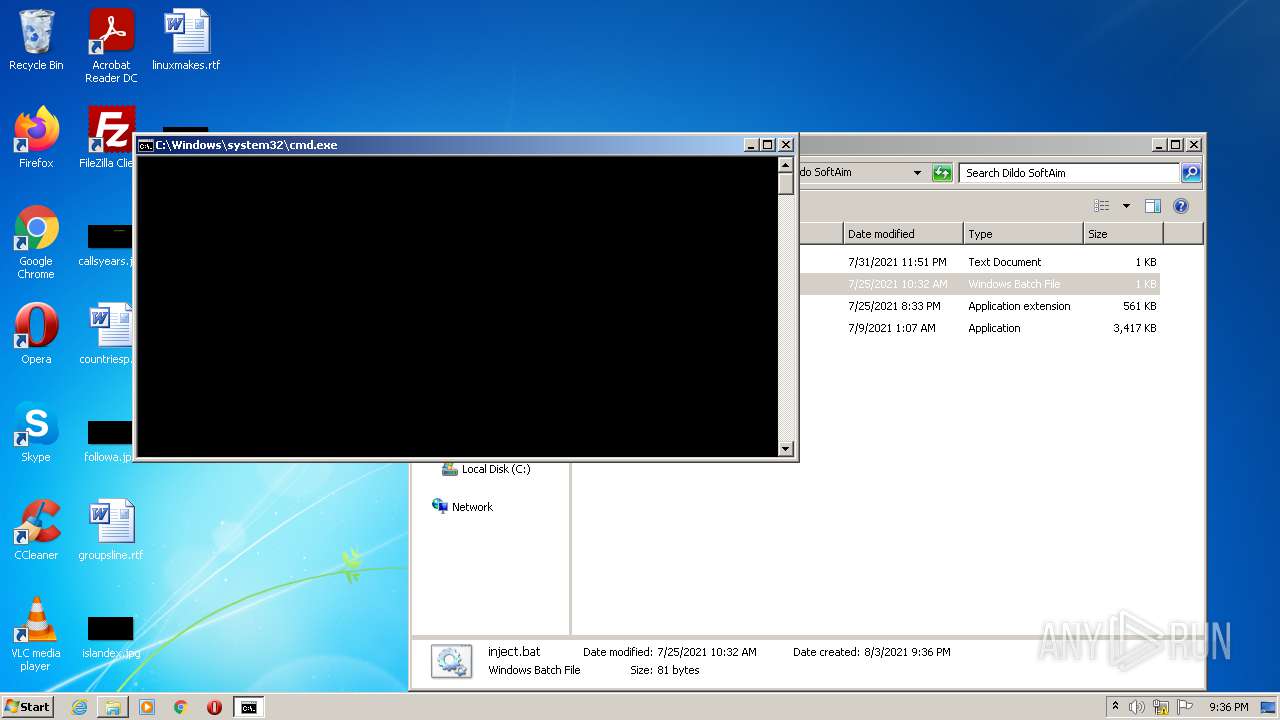
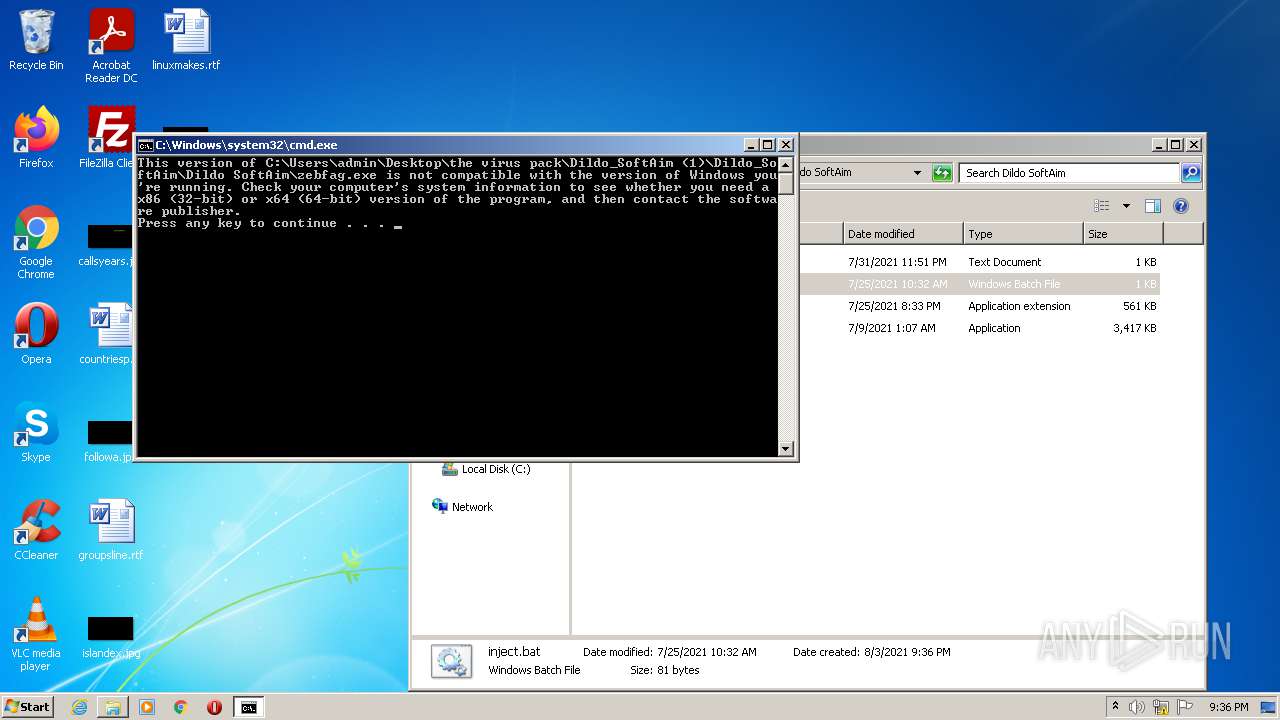
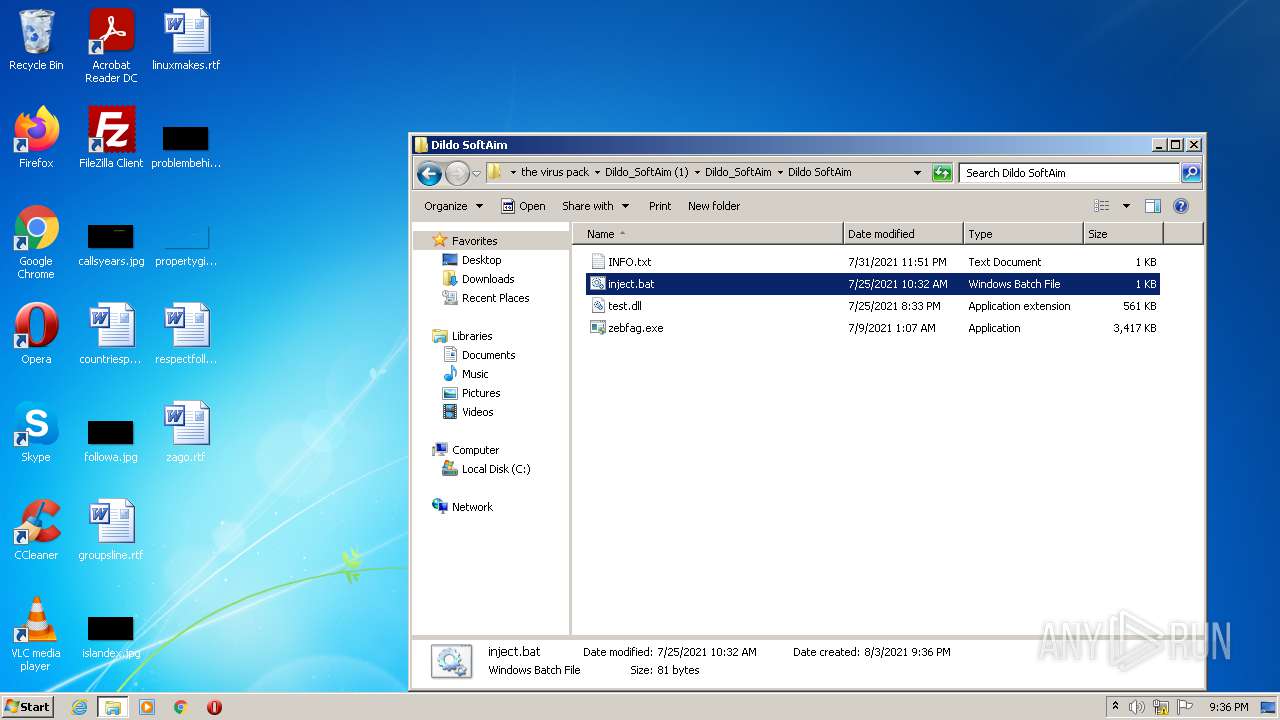
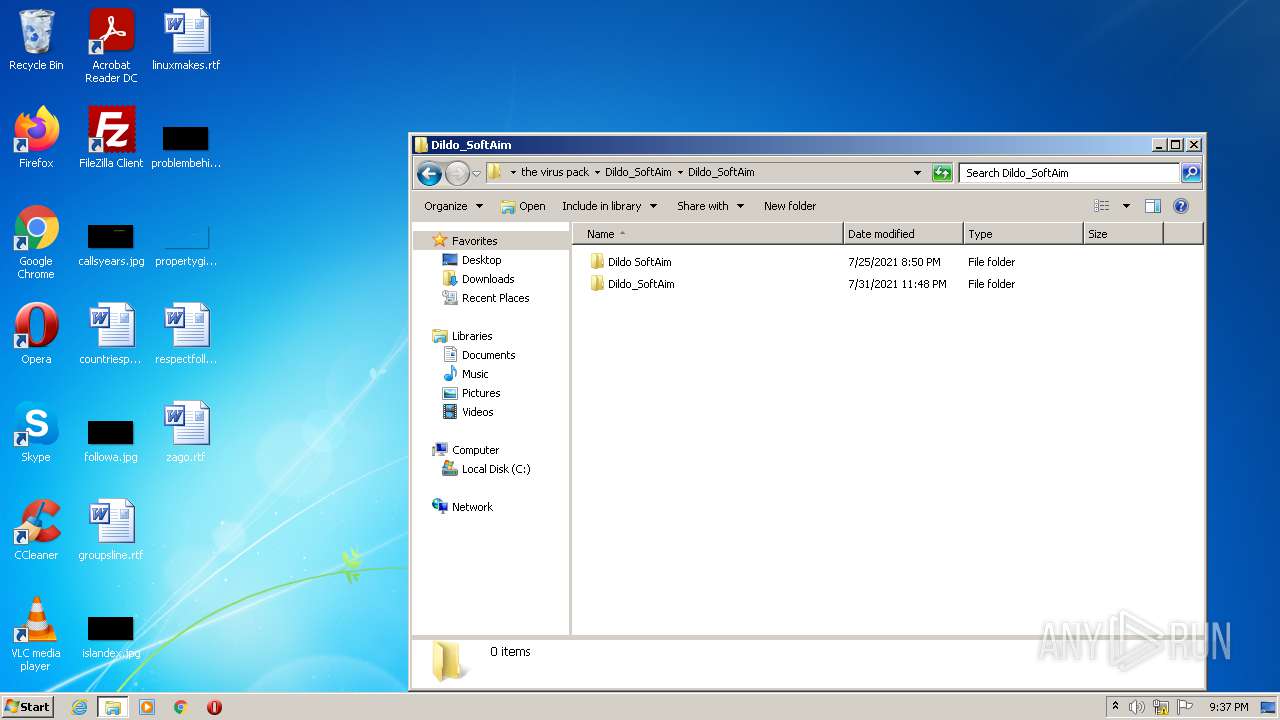
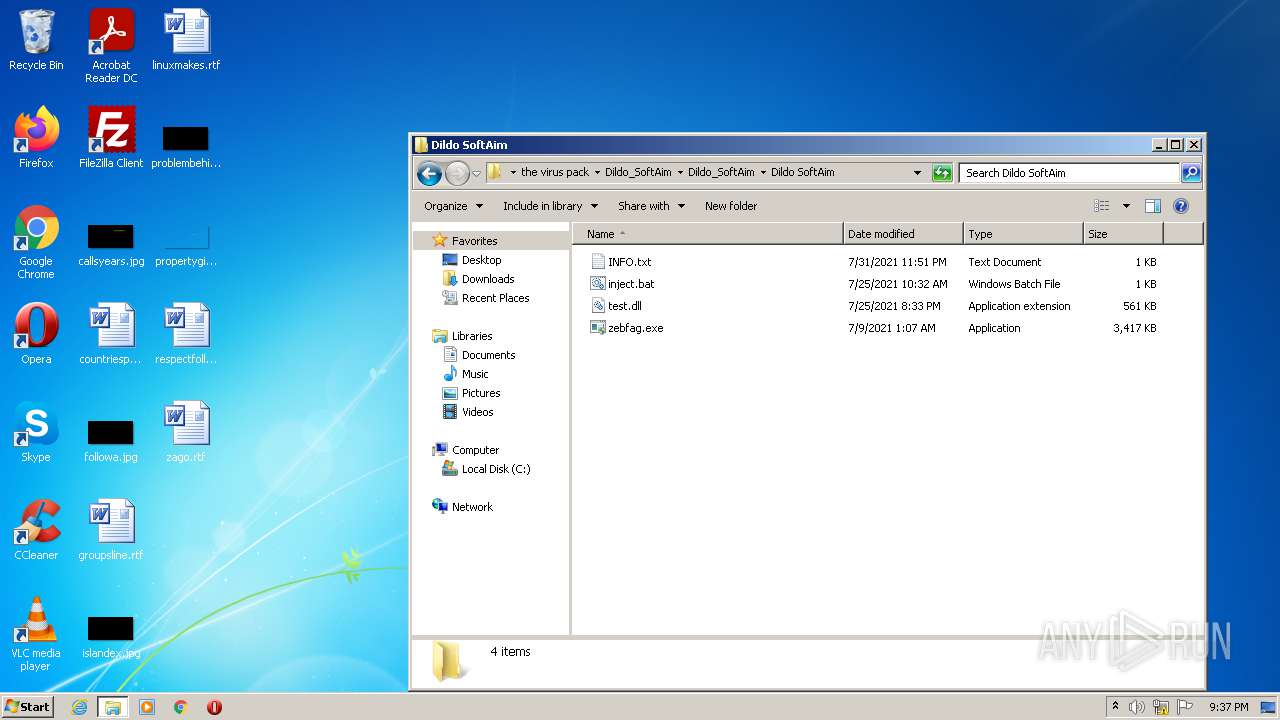
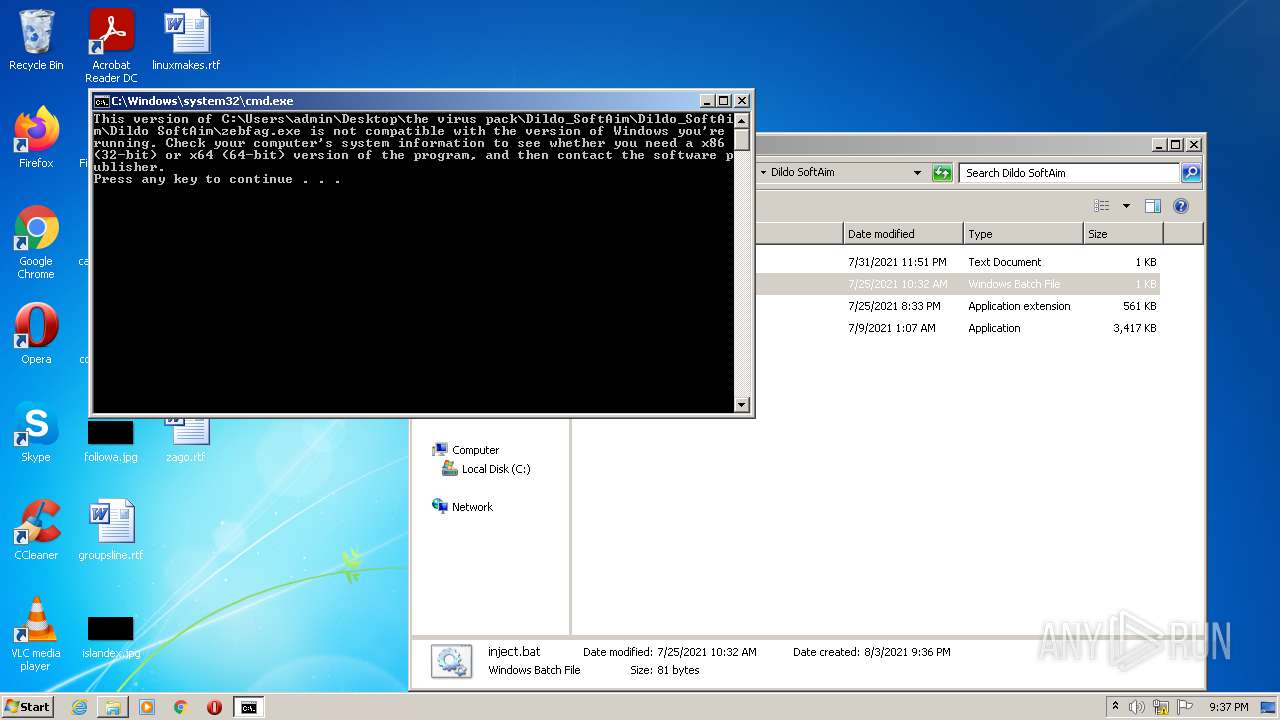
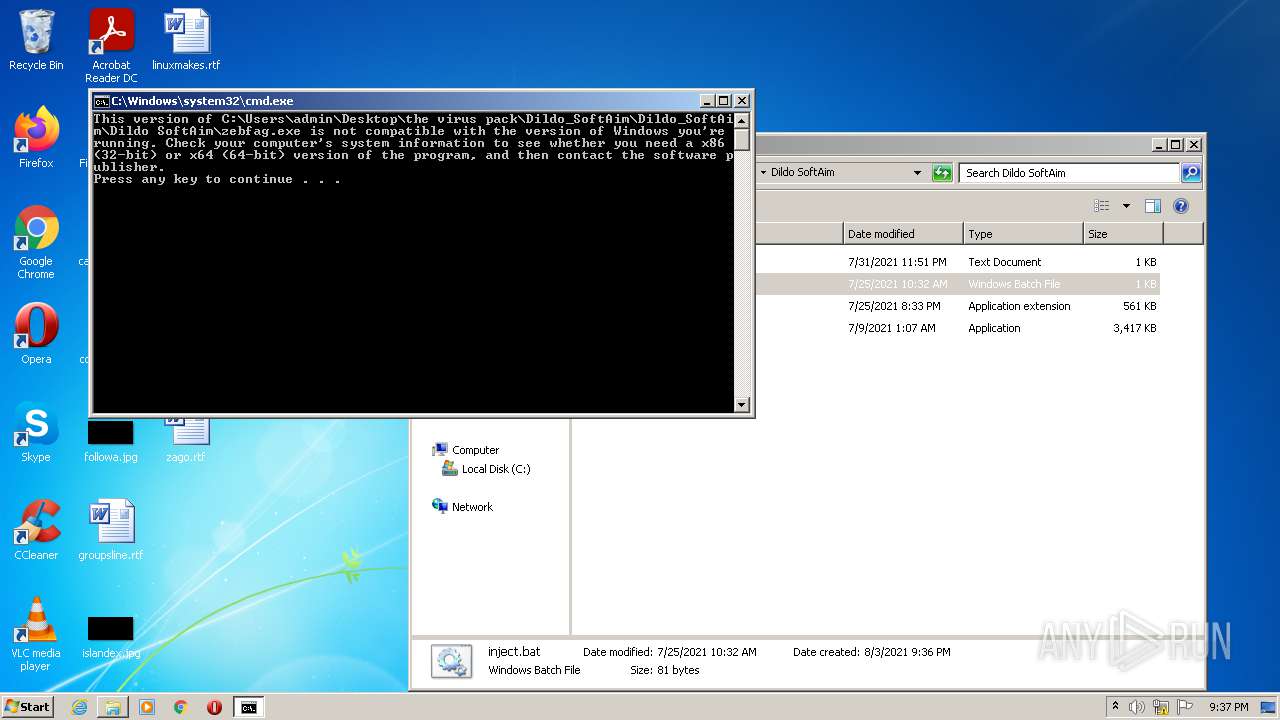
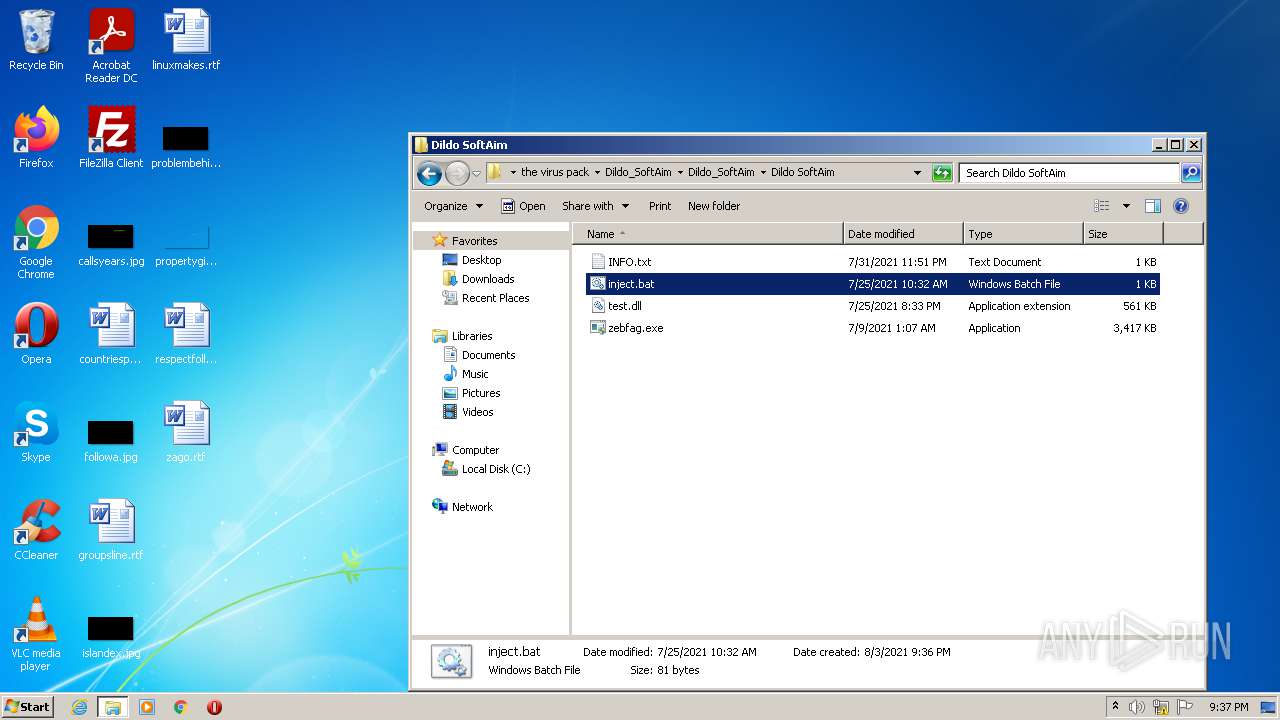
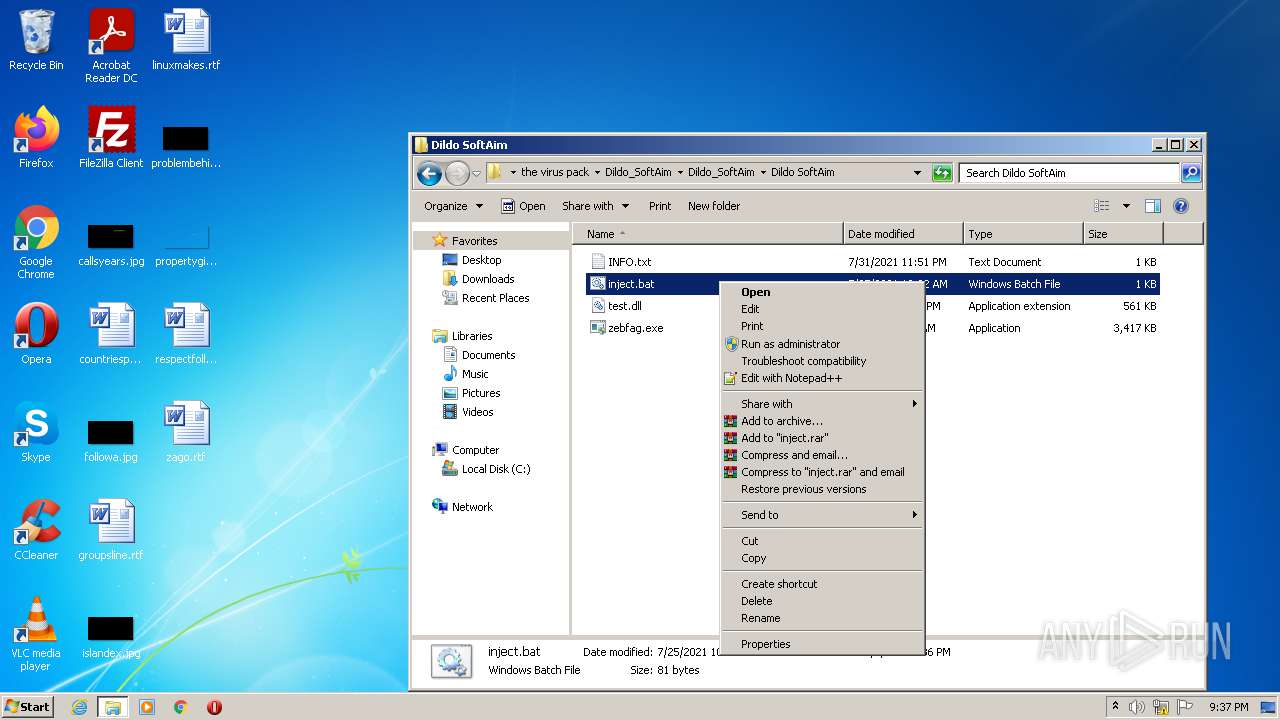
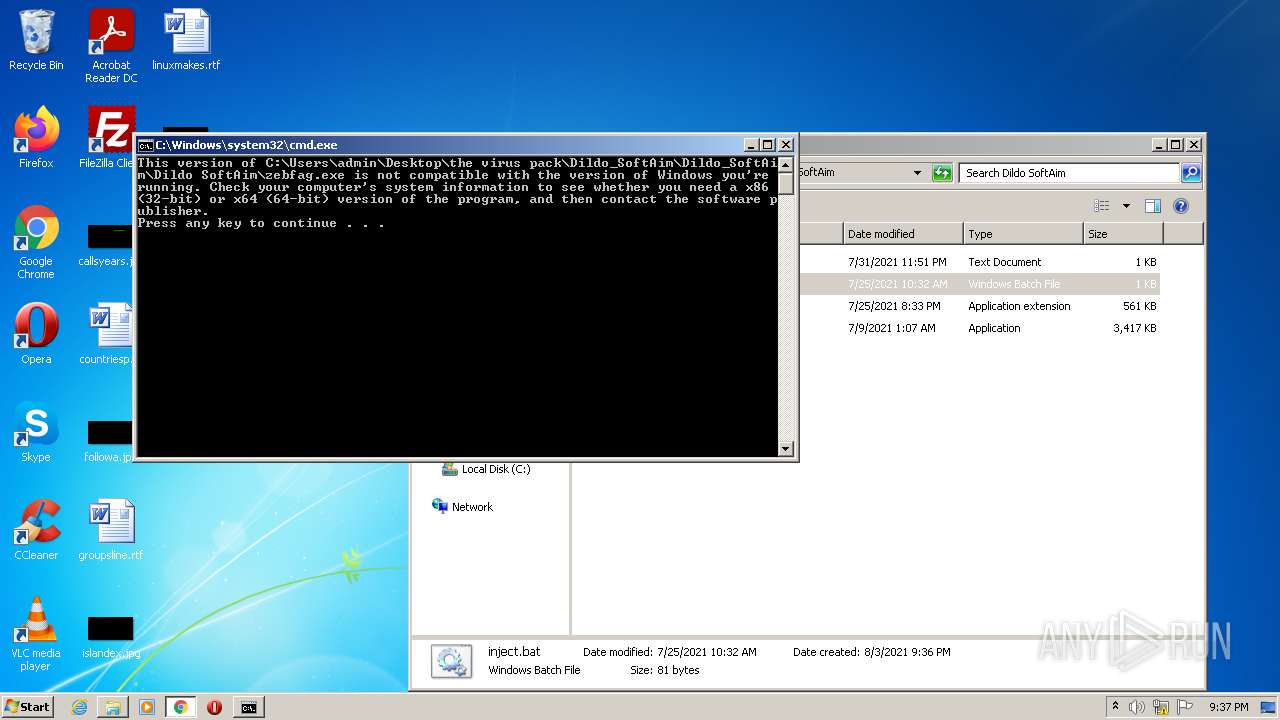
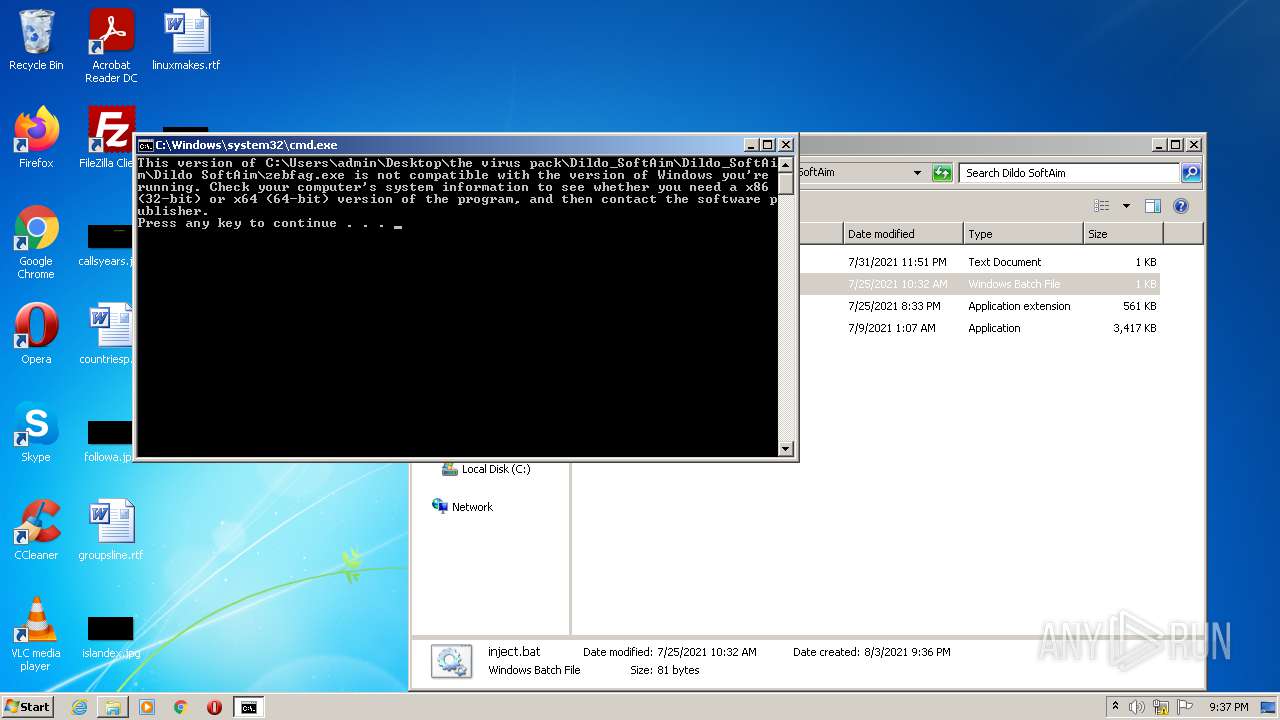
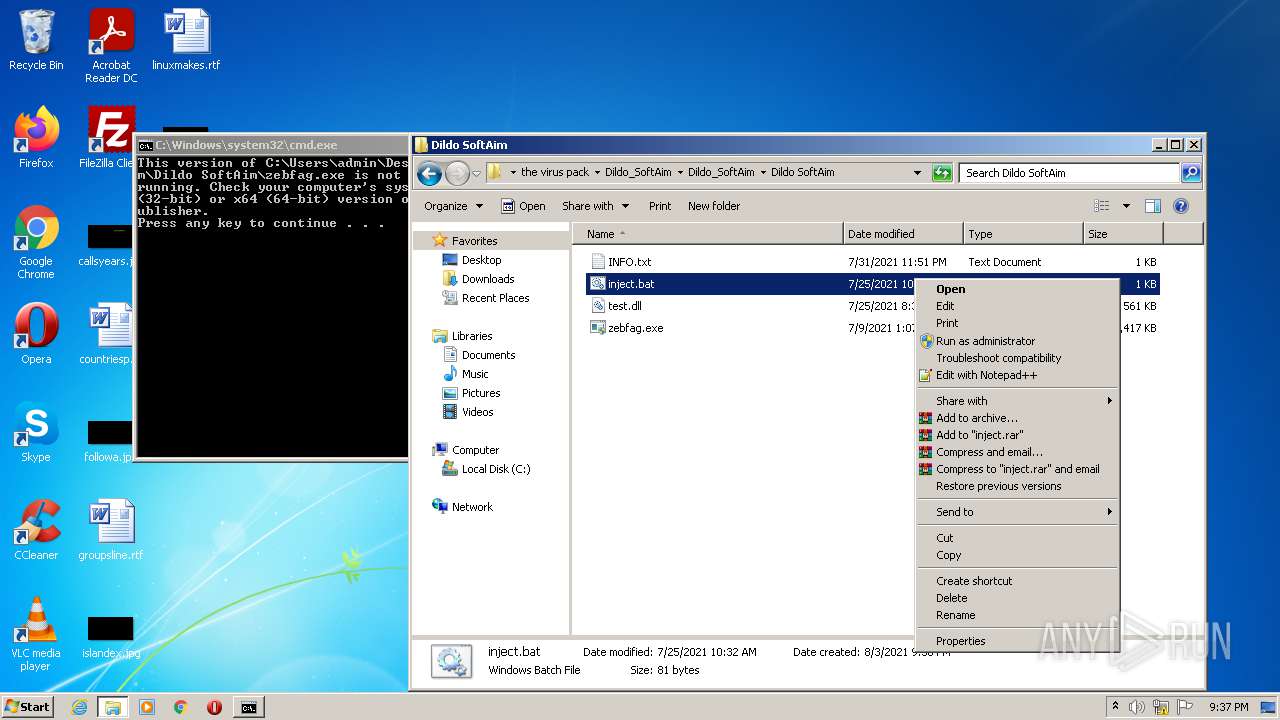
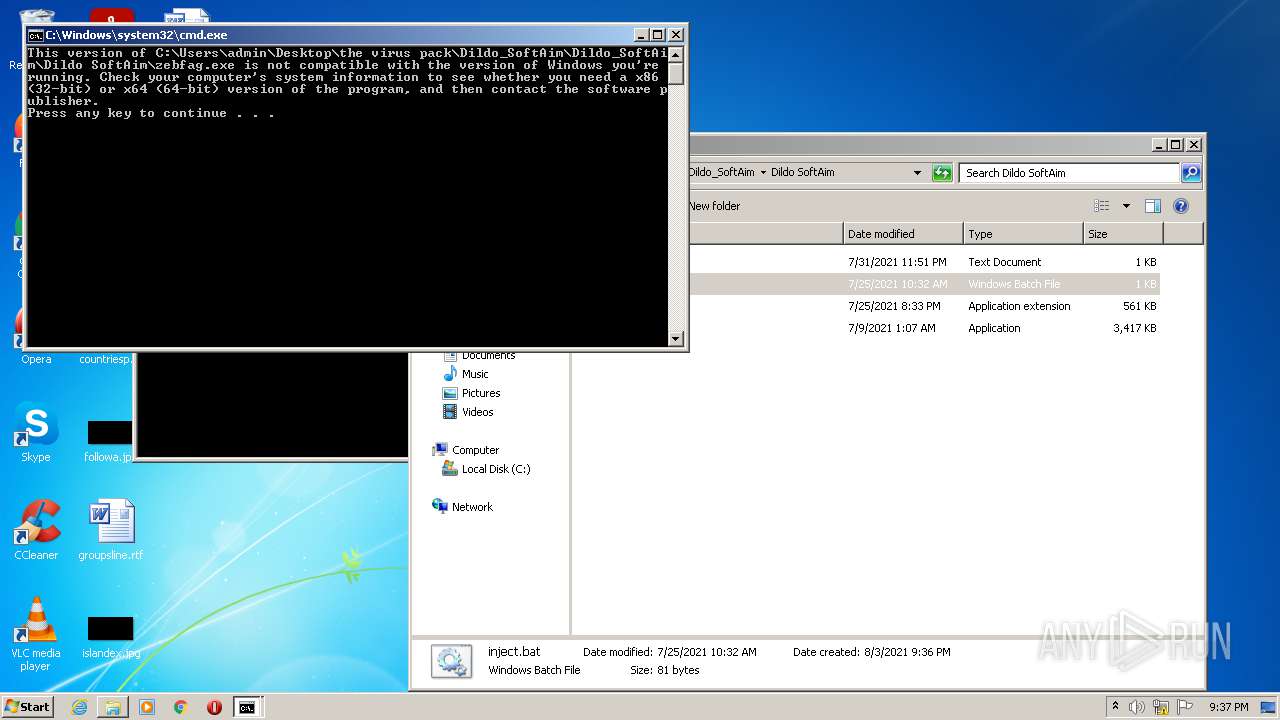
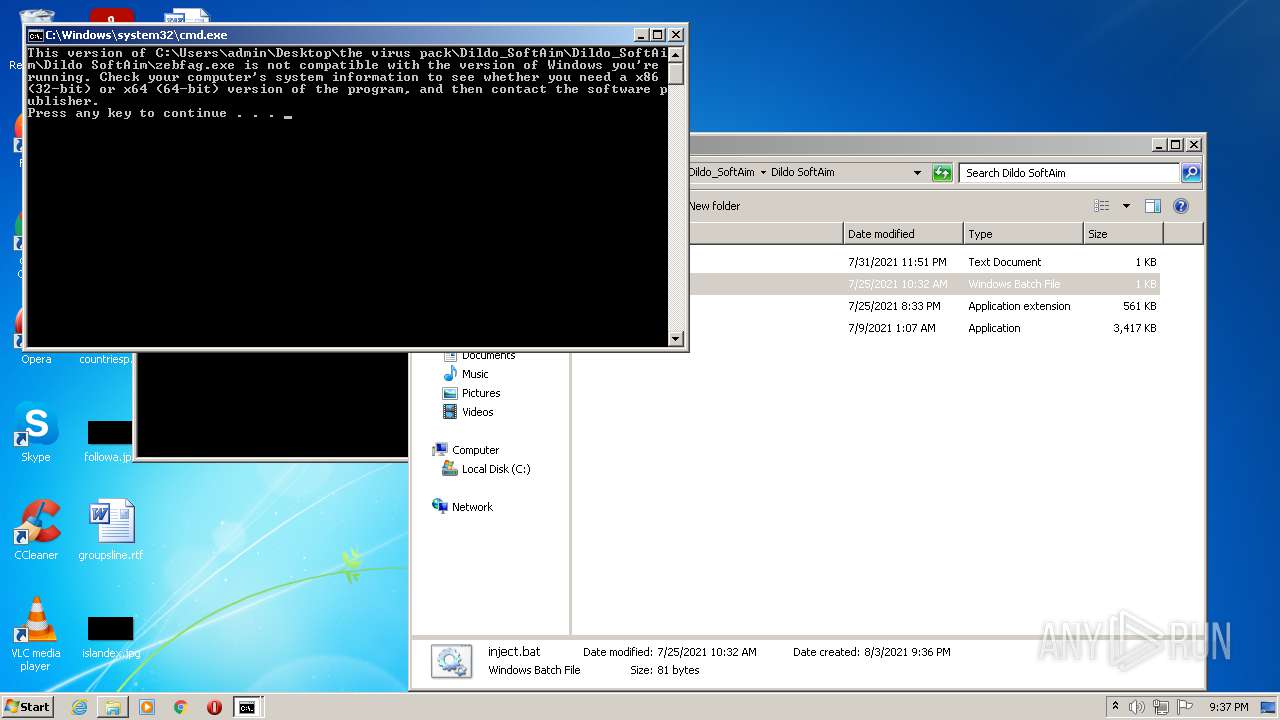
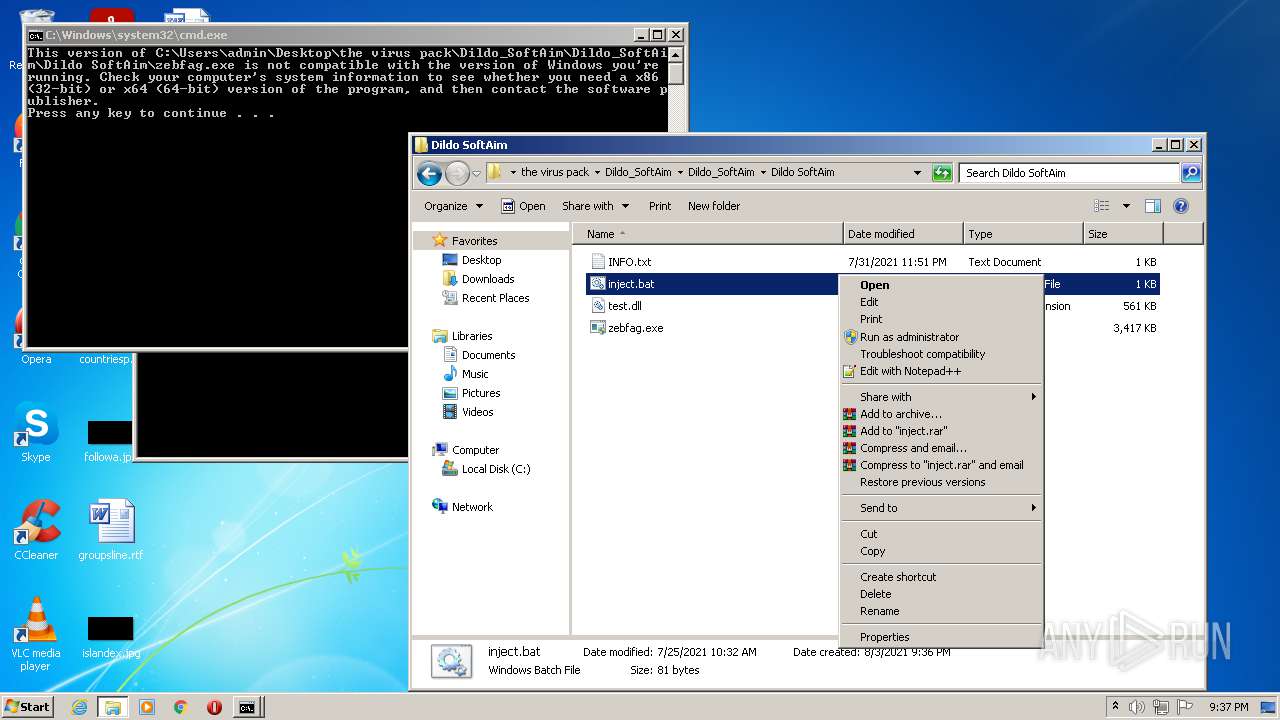
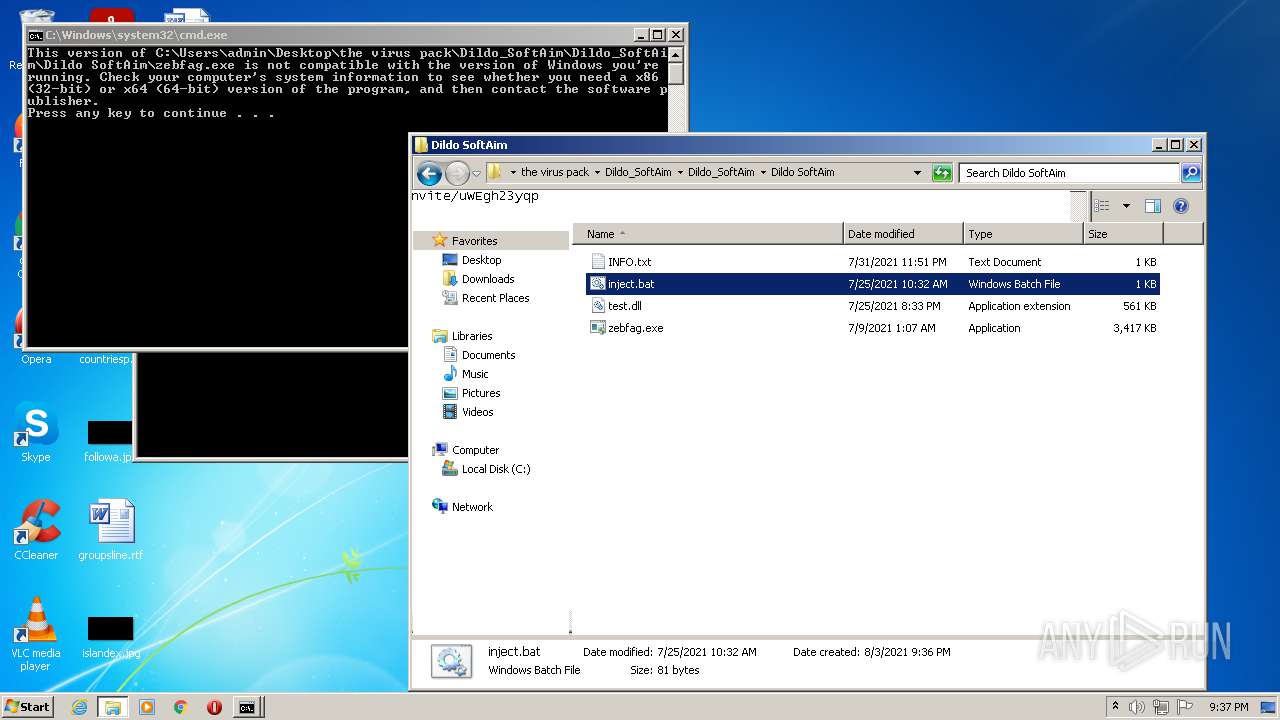
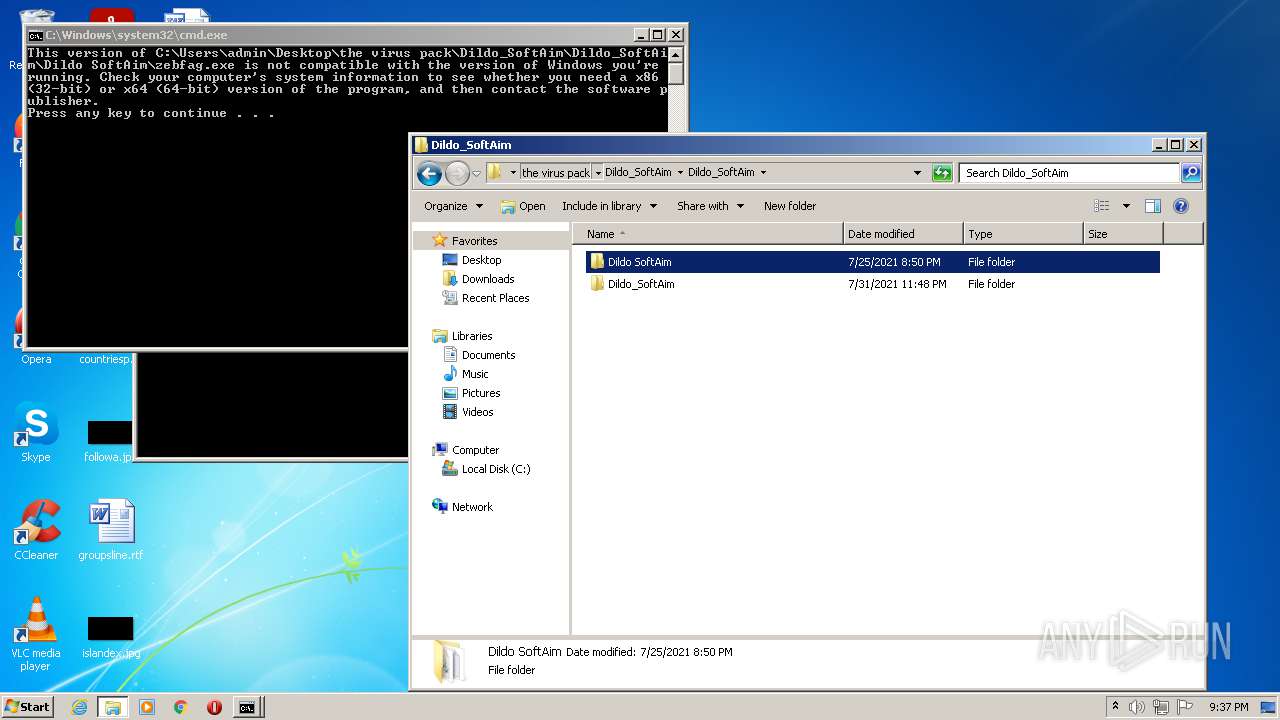
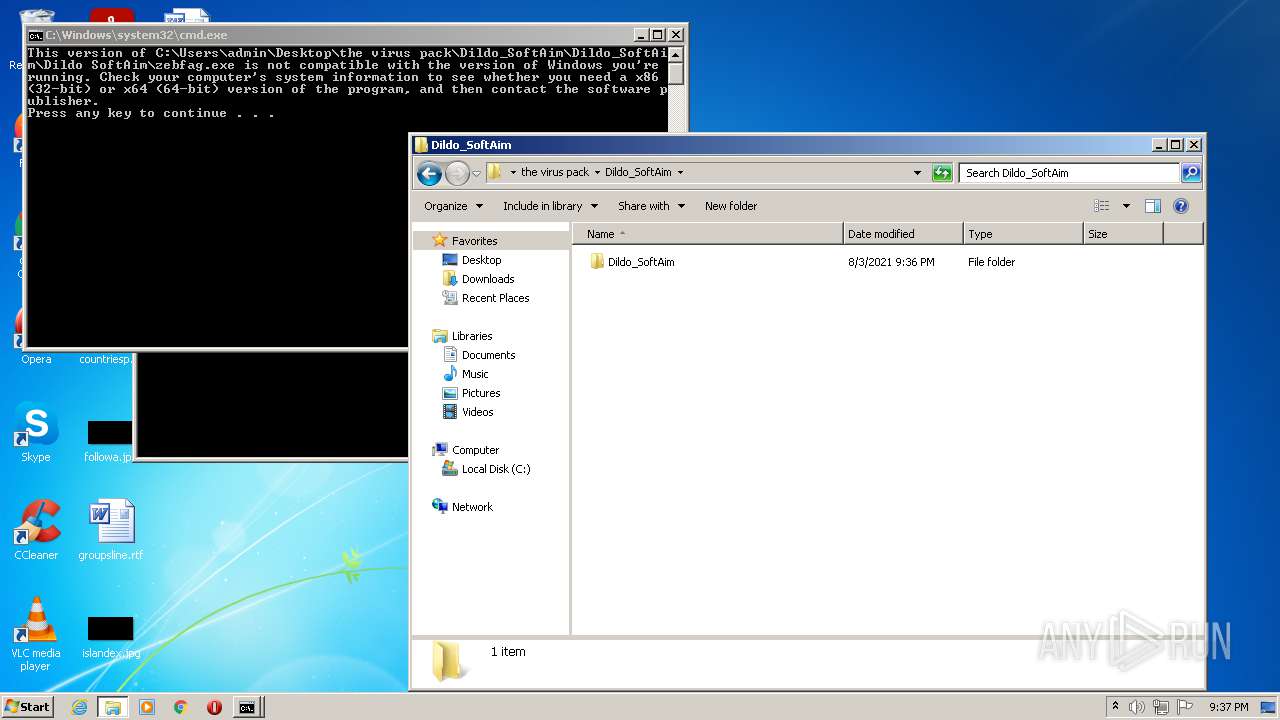
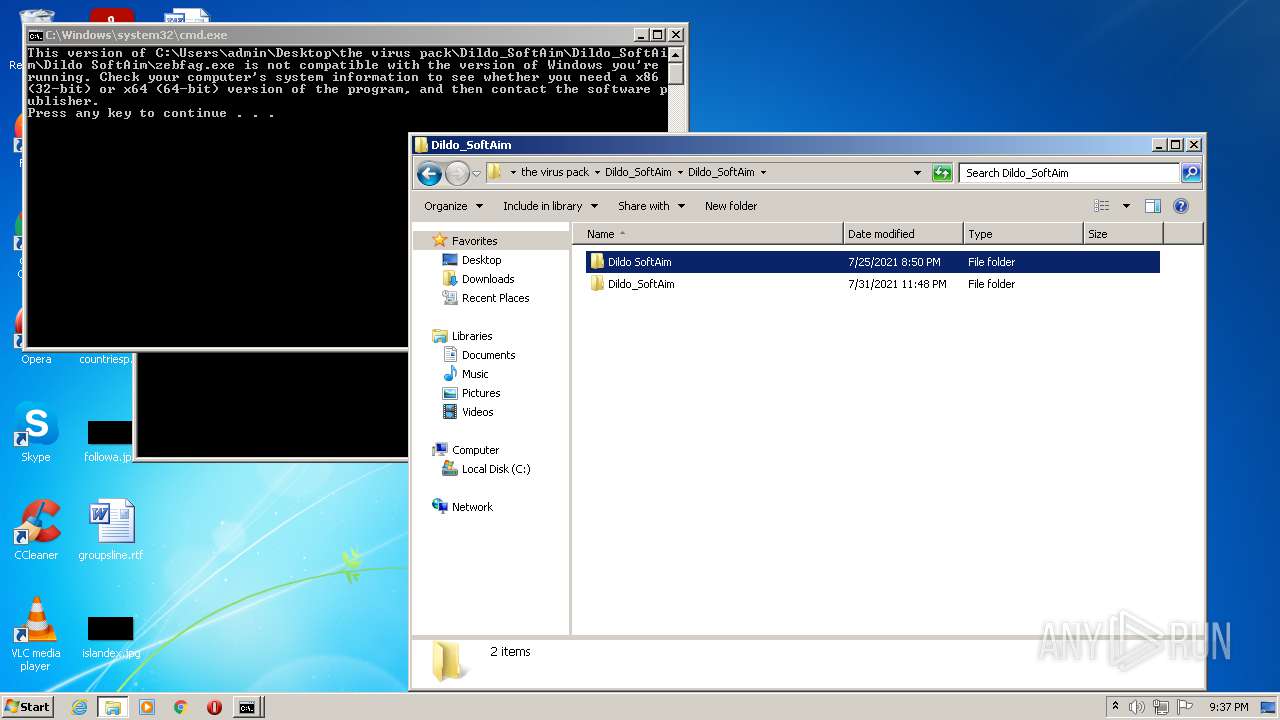
| 1664 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\the virus pack\Dildo_SoftAim\Dildo_SoftAim\Dildo SoftAim\inject.bat" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
51 380
Read events
51 020
Write events
359
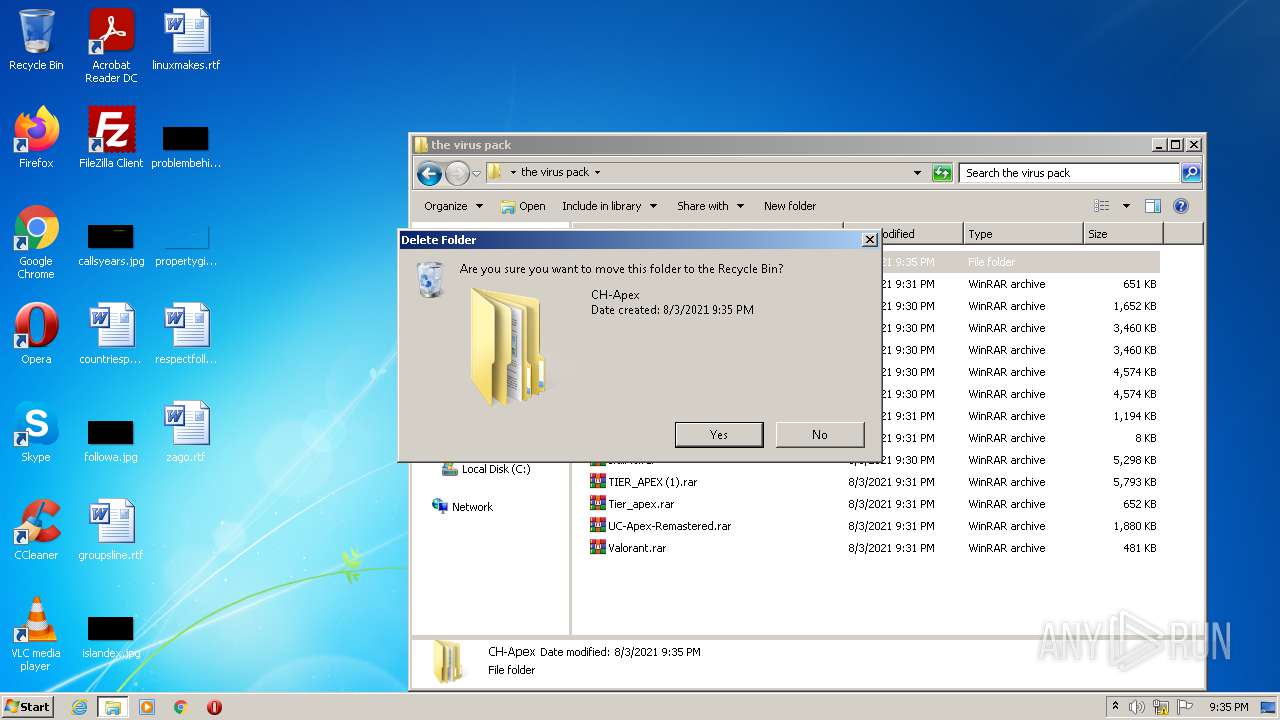
Delete events
1
Modification events
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902438 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902438 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
19
Suspicious files
102
Text files
242
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2256 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AHA5JBU3.txt | text | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AZ40LEPH.txt | text | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\file[1].htm | html | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DOO2KV3X.txt | text | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2256 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
96
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2256 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2256 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBtpDEx%2Fx4YJCgAAAADyw4g%3D | US | der | 471 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECh6GUYMxnYrCgAAAADrSus%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2256 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2256 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHFTDTdAe7AICgAAAADrSro%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2256 | iexplore.exe | 142.250.185.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2256 | iexplore.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
2256 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2256 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4060 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4060 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2256 | iexplore.exe | 142.250.185.78:443 | translate.google.com | Google Inc. | US | whitelisted |
2256 | iexplore.exe | 104.16.94.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
2256 | iexplore.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2256 | iexplore.exe | 142.250.181.238:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |