| File name: | file.ps1 |
| Full analysis: | https://app.any.run/tasks/a4adf9b2-76fb-437e-a1d4-432c1e949a4b |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 17:59:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 15E251DF54AC9FE193642CC2CDDED518 |
| SHA1: | EE6588E680D91A894B6E706C51413EED713BB9B7 |
| SHA256: | C0C39205B4CD5A1CEC172AAF979602FA4F13CBCD0036102E0CBC5FA83E2026D5 |
| SSDEEP: | 192:ZbawLYtvt7jktbdtGDHATqtCou7siSUKhqht+t+JL5453:ZbauYtvt7jktbdtGDgutCou71SUKyt+X |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1256)
Writes to a start menu file
- powershell.exe (PID: 2824)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2824)
Drop AutoIt3 executable file
- powershell.exe (PID: 2824)
Executable content was dropped or overwritten
- powershell.exe (PID: 2824)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1256 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
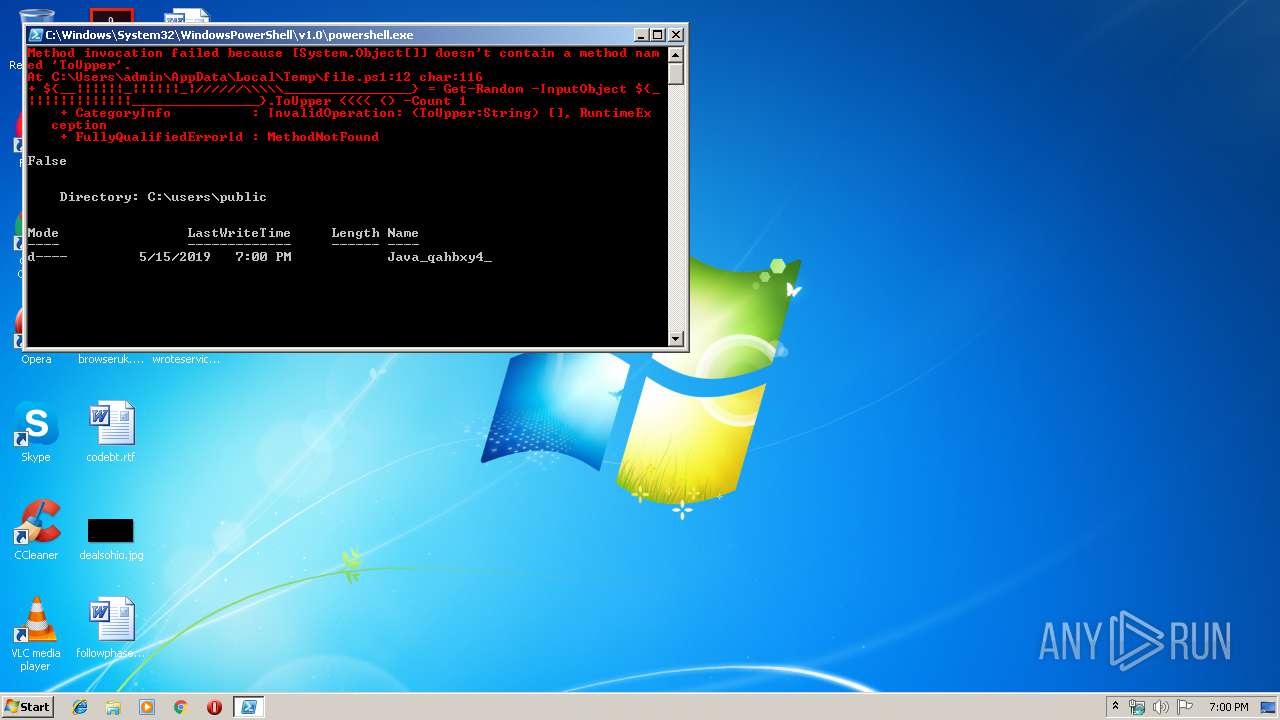
| 2824 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\file.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
701
Read events
628
Write events
73
Delete events
0
Modification events
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2824) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
7
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5I8B30Z0YBS6U2HN0EZ8.temp | — | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\Public\Java_qahbxy4_\pp.png | — | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14e9a3.TMP | binary | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\users\public\Java_qahbxy4_\Java_qahbxy4_.zip | compressed | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\users\public\Java_qahbxy4_\Java_qahbxy4_.LNS | executable | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\users\public\c.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\users\public\Java_qahbxy4_\Java_qahbxy4_1.LNS | text | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Java_qahbxy4_.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\Public\Java_qahbxy4_\ssleay32.dll | executable | |
MD5:CF2C57DDA3766C204C398430DA23693D | SHA256:492F045643354C8B9FA11673B6C32CDBB33779826A729CE55DE5901279C1F6D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | powershell.exe | GET | 200 | 144.202.68.139:80 | http://144.202.68.139/mds25/kk/md.zip | US | compressed | 11.4 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | powershell.exe | 144.202.68.139:80 | — | Baltimore Technology Park, LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2824 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |