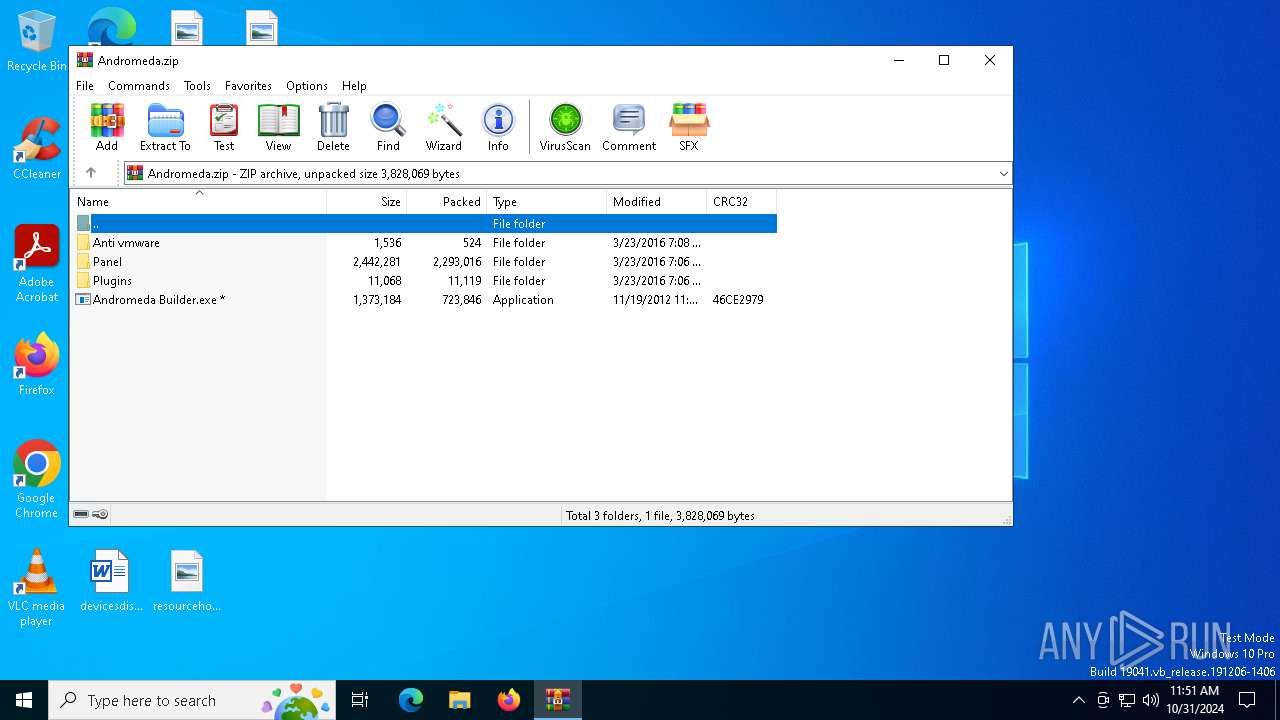
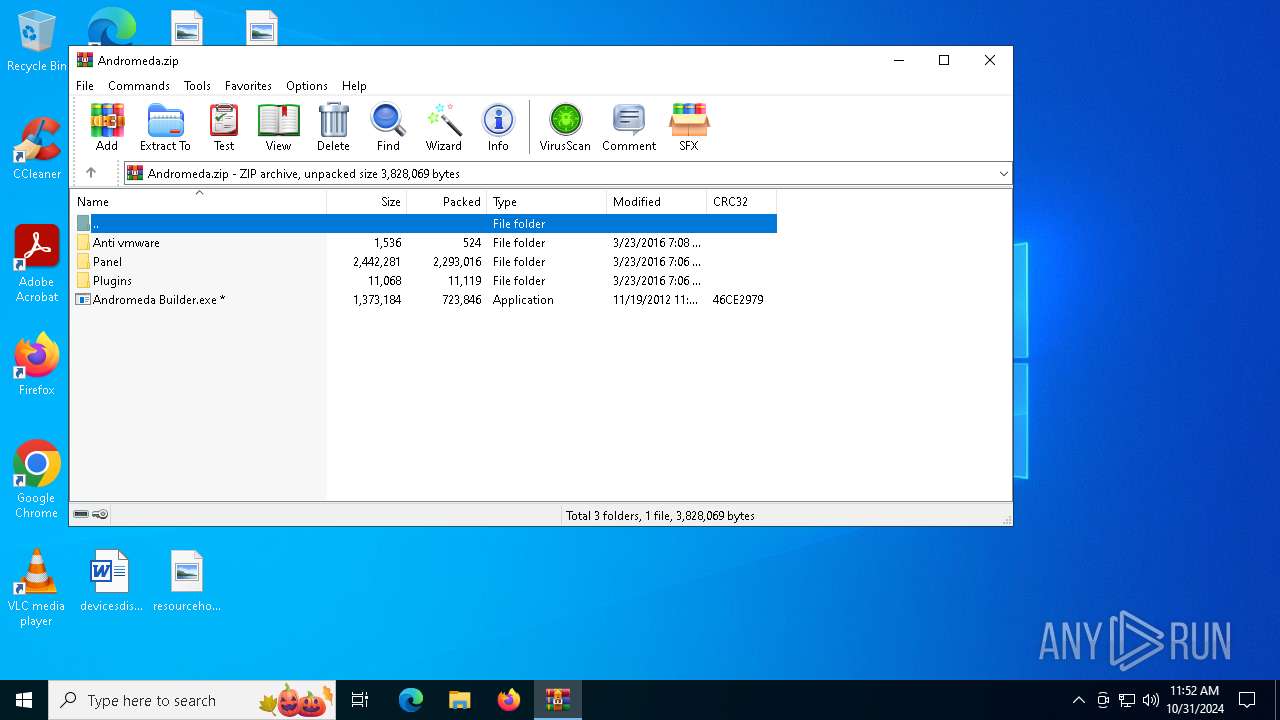
| File name: | Andromeda.zip |
| Full analysis: | https://app.any.run/tasks/cd80db49-2ae4-43d4-997c-045615593792 |
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2024, 11:51:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8AC33AB4D0E3CBB48E2249746748C155 |
| SHA1: | A7AA347C9F1969C06BEAF80D7ED3E77231A9C2D0 |
| SHA256: | C0C01F0AE0D0845F66B9C3FFF4058B3812DC82FE7AB6104E268E148AC2F7A1B6 |
| SSDEEP: | 49152:YGO1DiRhx3ZWzYwvBq9No4y/77Or6zwefUcGAJcPRg+jBt19iRbw:1OtOhtMBcMD7Or6zwp5PlBiw |
MALICIOUS
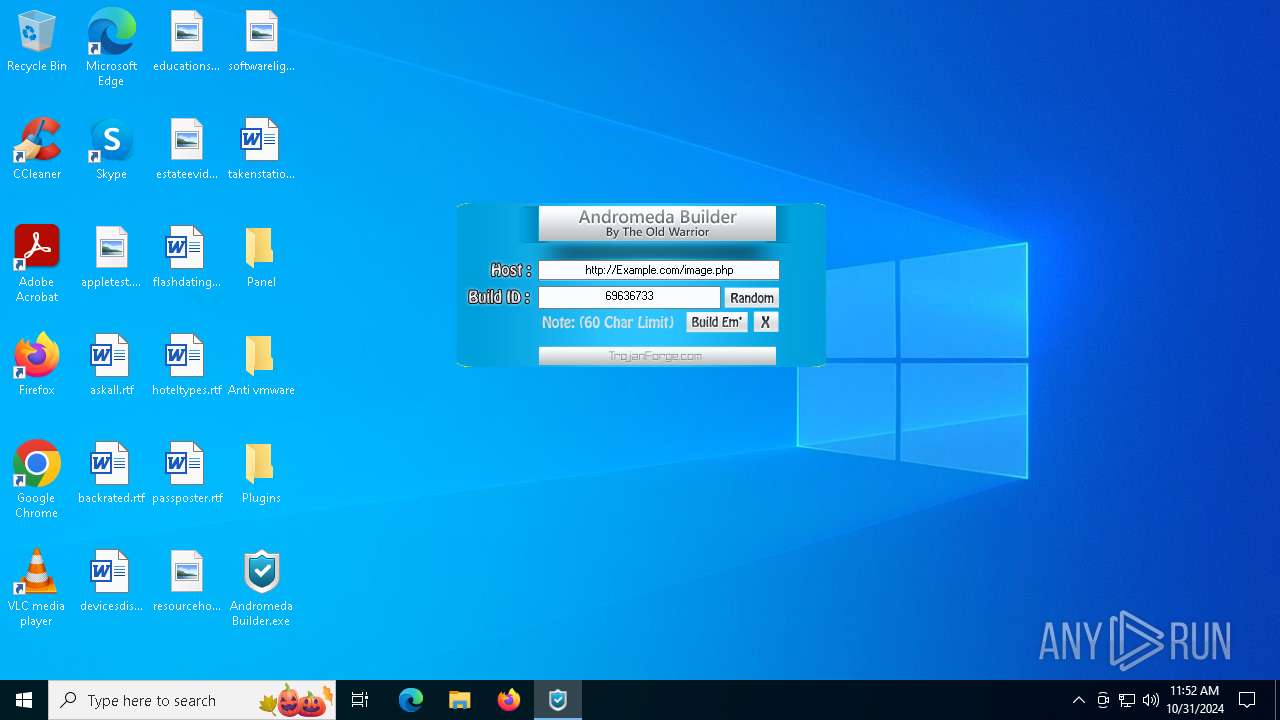
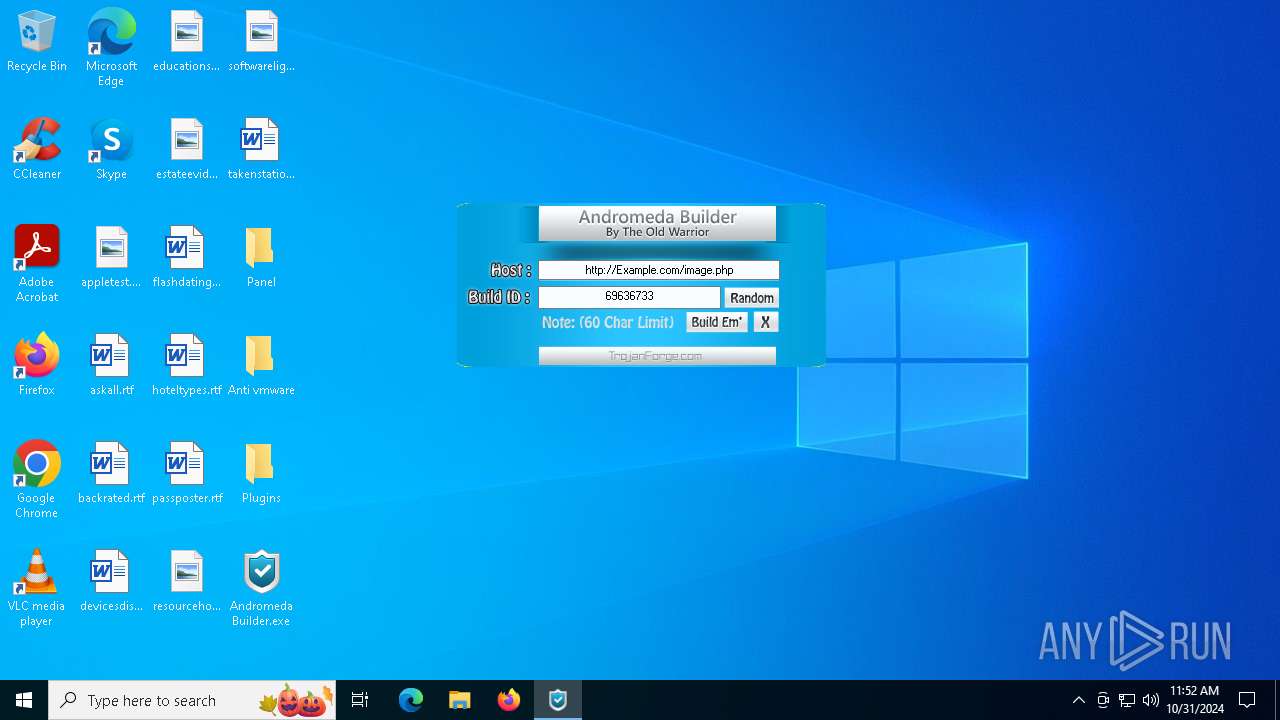
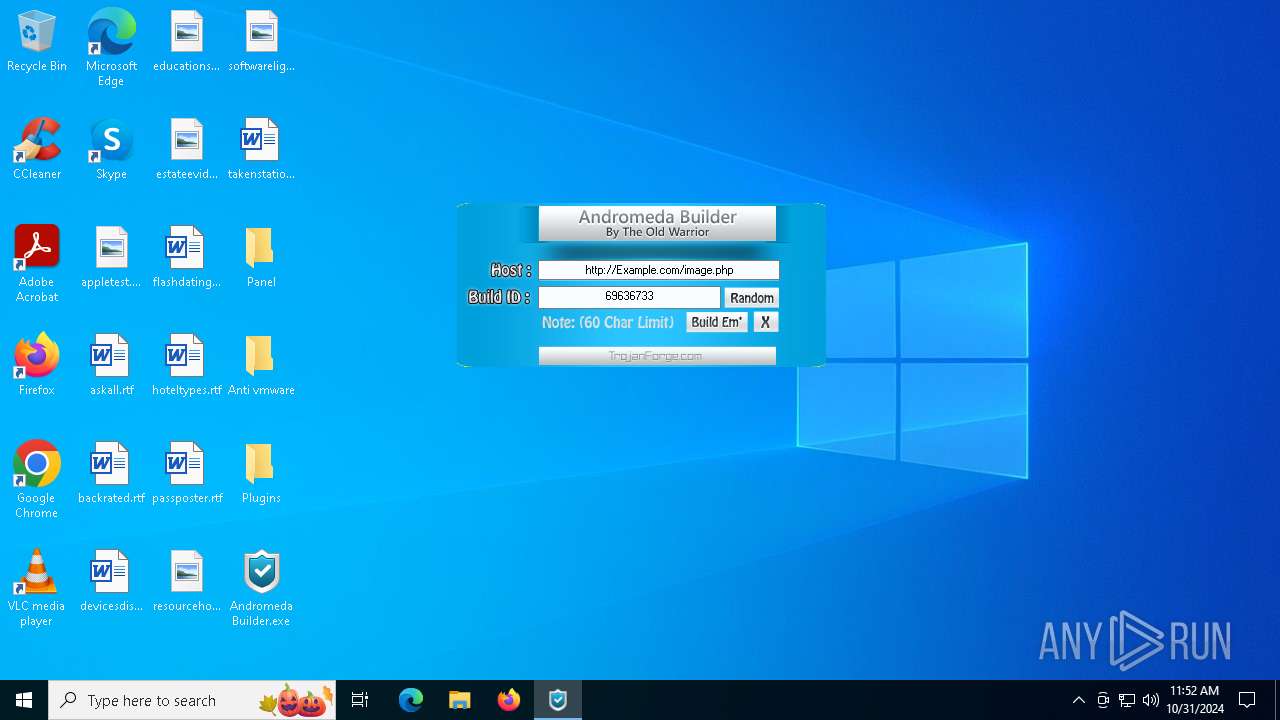
ANDROMEDA has been detected (SURICATA)
- svchost.exe (PID: 692)
Connects to the CnC server
- svchost.exe (PID: 692)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 692)
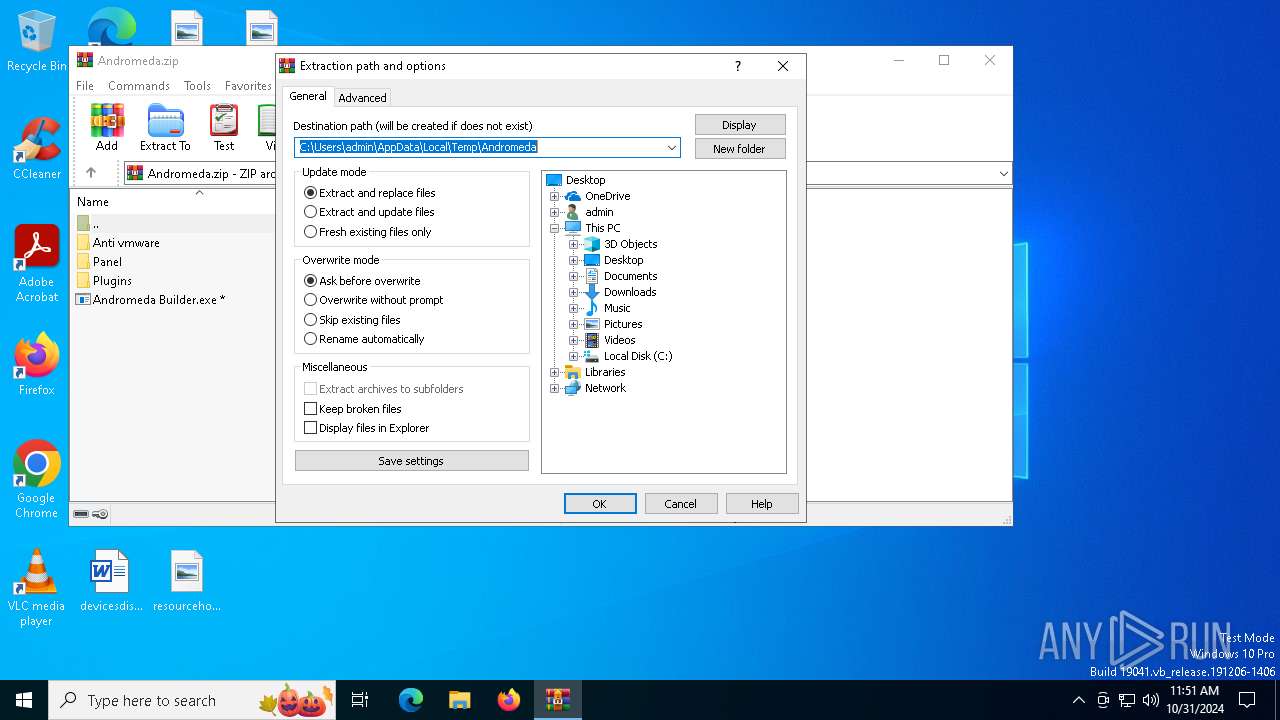
Generic archive extractor
- WinRAR.exe (PID: 6516)
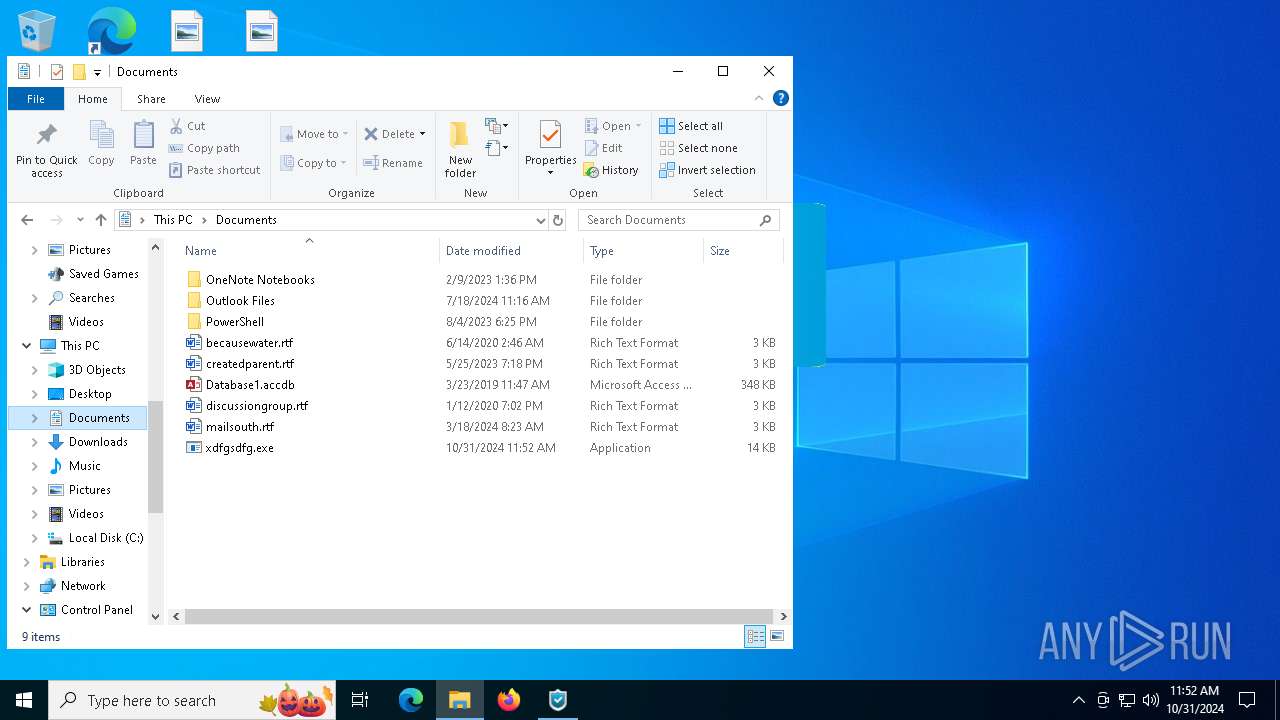
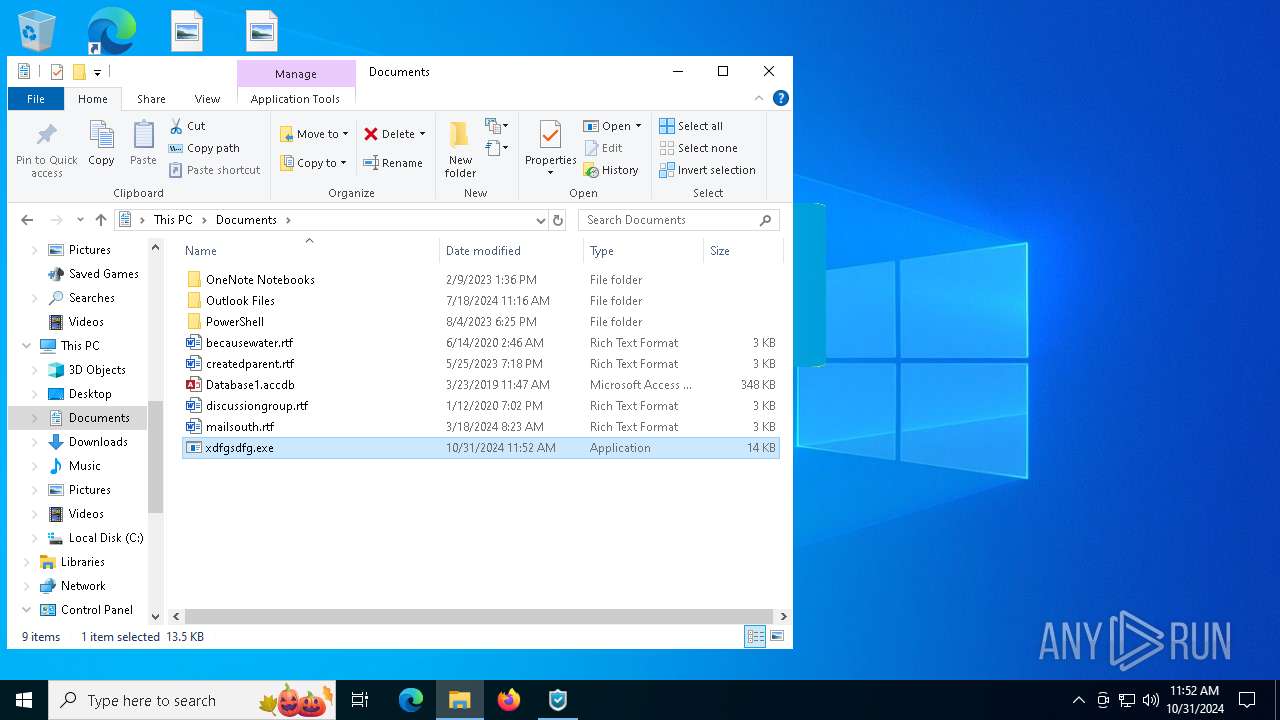
Executable content was dropped or overwritten
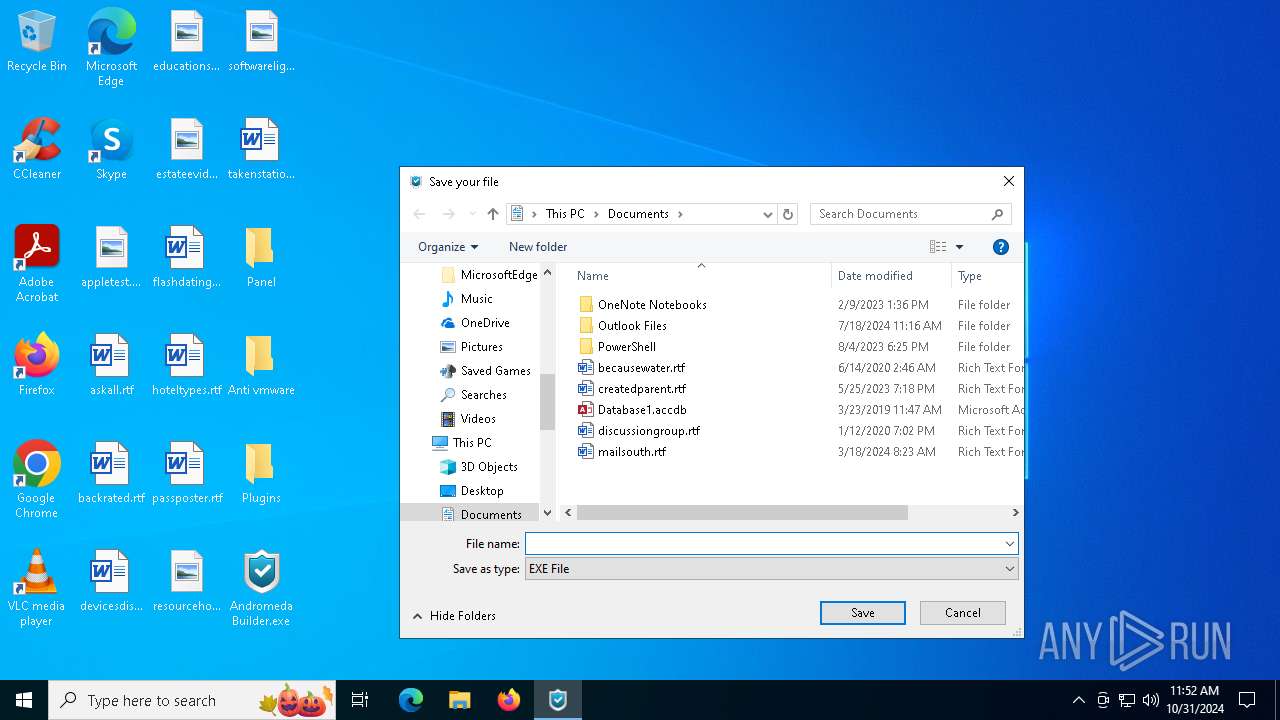
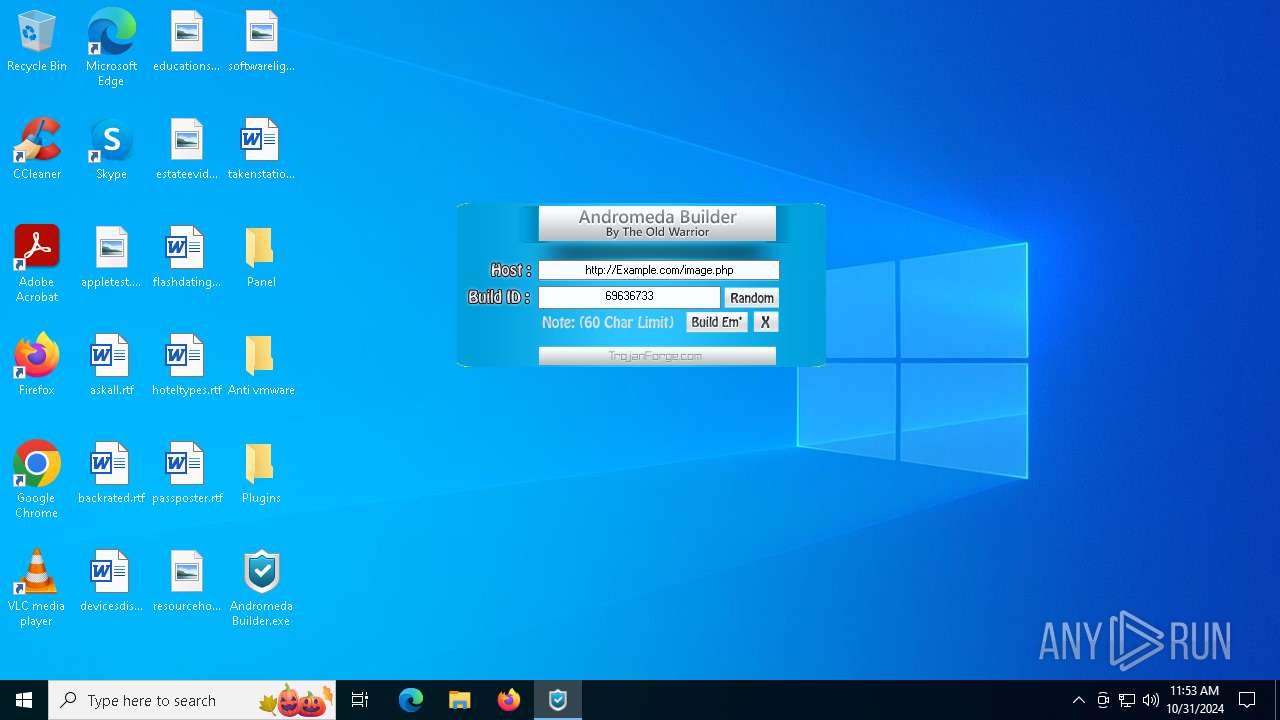
- Andromeda Builder.exe (PID: 6824)
- svchost.exe (PID: 692)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6516)
Manual execution by a user
- xdfgsdfg.exe (PID: 3568)
- Andromeda Builder.exe (PID: 6824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2016:03:23 21:06:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Panel/ |
Total processes
131
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | C:\WINDOWS\syswow64\svchost.exe | C:\Windows\SysWOW64\svchost.exe | xdfgsdfg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
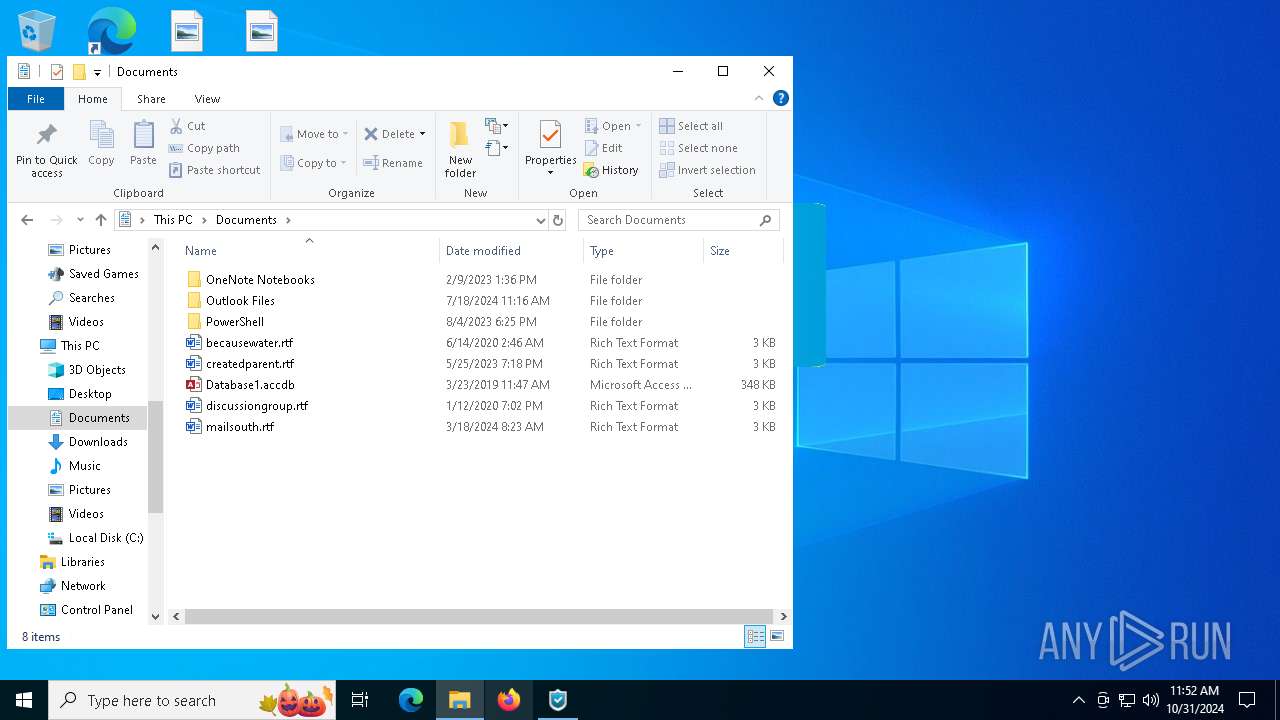
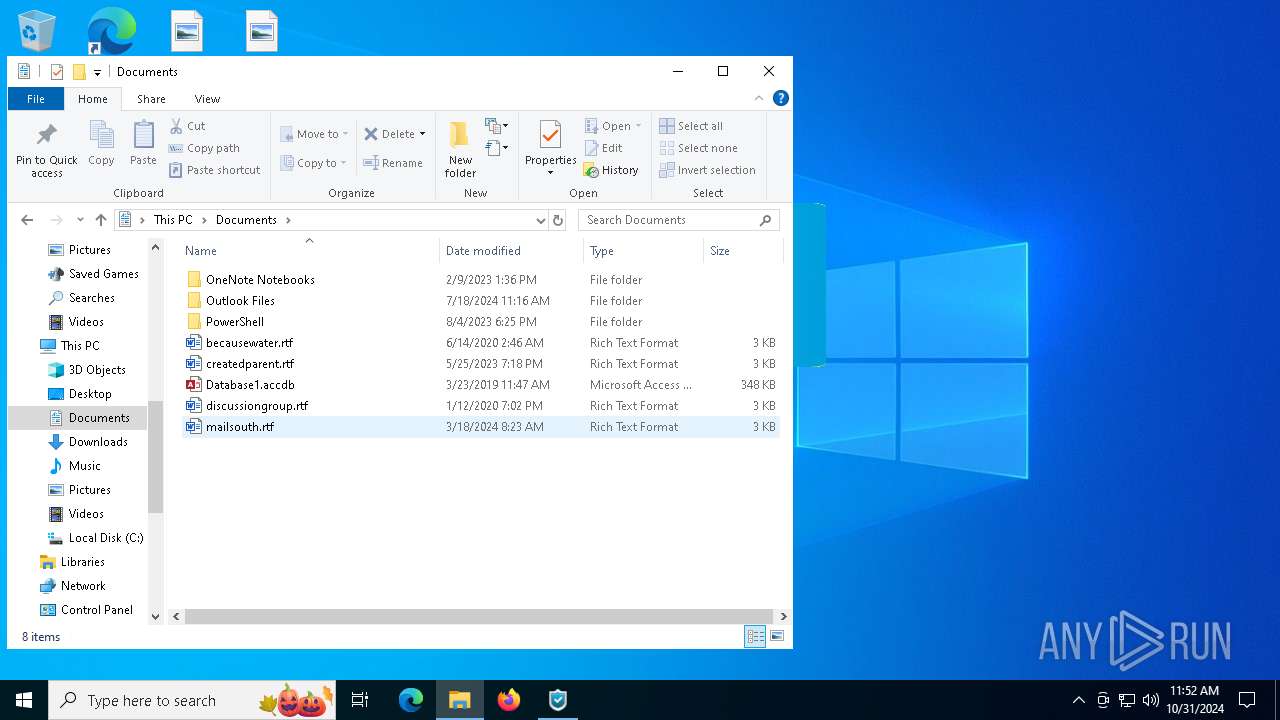
| 3568 | "C:\Users\admin\Documents\xdfgsdfg.exe" | C:\Users\admin\Documents\xdfgsdfg.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3848 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Andromeda.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
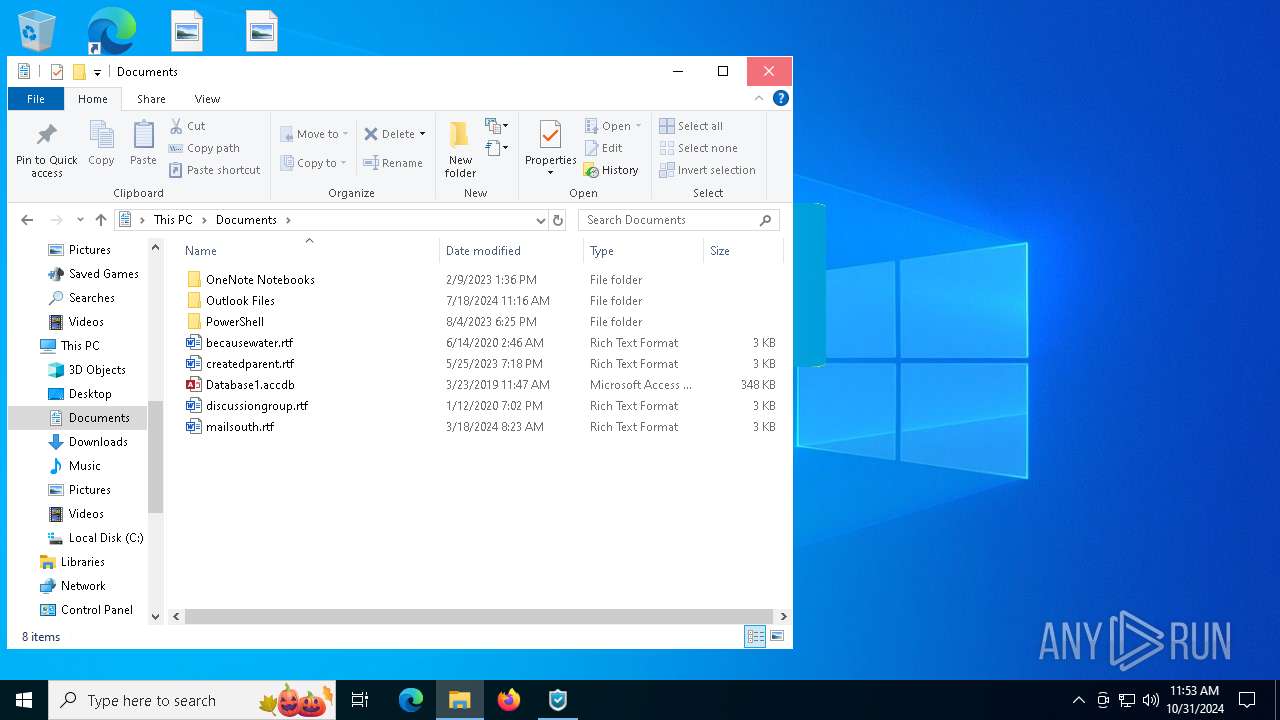
| 6824 | "C:\Users\admin\Desktop\Andromeda Builder.exe" | C:\Users\admin\Desktop\Andromeda Builder.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
5 799
Read events
5 727
Write events
58
Delete events
14
Modification events
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Andromeda.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
4
Suspicious files
4
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
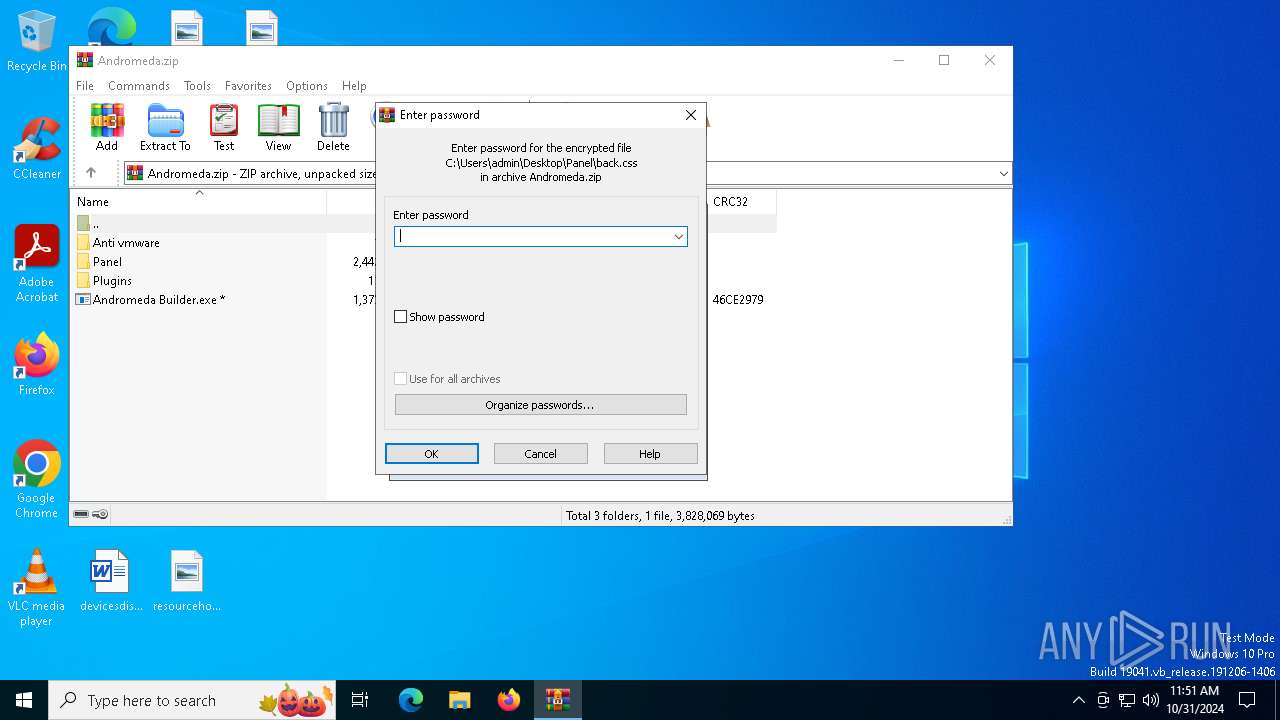
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\config.php | text | |
MD5:CE728E03960FC4DDA3DCDDB333F151D7 | SHA256:FA5AC7C2227D882E36D44E1FFC33D5E899A477DD91A8BC1B4D8A0B554854BE8F | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\geo.gif | image | |
MD5:045D01E30D052B833348259C28FC3B62 | SHA256:C6DD2D5A202E2746CF234C5F4C86E2F550F5D1CF2F3F0FA7A9F9B2E6256A6E06 | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\back.css | text | |
MD5:B43A32815C5D0F62EE2C98D99462D4E0 | SHA256:7194BCF2D9C5434D2BDAC3EB77DD9E73B4AE165F428611C285F0C53A48368262 | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\image.php | text | |
MD5:6F9BA5EFBC938C638EBB19B6EFC072E8 | SHA256:CAF971A21A4277CF87D00349093358A8E29E3FFE39BC72FF80A523B950636E19 | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\plugins\socks4\link.php | text | |
MD5:38BD0092F81B886C70F4F8ED7C70141F | SHA256:EC83404208BE457E03EE7AE543C7DE3CAD1354BD6A44984808F29772DFC052C3 | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\ifg.php | text | |
MD5:9C814C50E43C11E7657A044E52A1628F | SHA256:84E3C3B7CC88979707153DB05D075E88412B1C80994357BE159071965BC07AFF | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\plugins\fg\link.php | text | |
MD5:8F28D4A49456441193A6C71F00FA453D | SHA256:86DC5F221819CDE1B32DF3E2066E981F26578072BC16E9F6210E6C45DF31F0CD | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\style.css | text | |
MD5:5B5C0DFCEA3E245AD50CDFDBF2F54B8C | SHA256:B90C7B94C8BF6206F8636AEBE138E02C22E3110B281E03D3B2173DC831F0D0BC | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\plugins\socks4\index.php | text | |
MD5:8B934AB080056C27D14EF8EB27E5D6D0 | SHA256:DEE4791B6D4D26A037A6926E928016CE494A31ECA2893C1DE558E28D18AE811C | |||
| 6516 | WinRAR.exe | C:\Users\admin\Desktop\Panel\plugins\socks4\gate.php | text | |
MD5:3C0687B3A315FA295D4D72B569038E2F | SHA256:71C3F8F2CFEC12ECAB61116390EF11B2DBBF4AA92107CD85CF2C3B446AE59978 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
51
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5232 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4556 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6044 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6044 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
692 | svchost.exe | POST | 405 | 93.184.215.14:80 | http://Example.com/image.php | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 92.123.104.29:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
692 | svchost.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
692 | svchost.exe | Malware Command and Control Activity Detected | ET MALWARE Andromeda Checkin |